| File name: | ABC.exe |
| Full analysis: | https://app.any.run/tasks/086e0c80-deb7-4c35-bfbd-5048950d140f |
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2026, 02:49:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 2B213F8350691FBF76113478B5AE1F7E |
| SHA1: | 1CF956D0579D0646563005767888A3FD9EBF2350 |
| SHA256: | 44FEDB44F9C108227C38A779D76CD2DA3ADE880A96ED8357D90E57D85ABA0837 |
| SSDEEP: | 393216:G9t/DtChynkpCMyH0tMi/2m/oecAAqdEvKbX:U10hRpCMyH0tn2mwXqdLbX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops python dynamic module
- ABC.exe (PID: 7408)
Executable content was dropped or overwritten
- ABC.exe (PID: 7408)
Application launched itself
- ABC.exe (PID: 7408)
Loads Python modules
- ABC.exe (PID: 7428)
The process drops C-runtime libraries
- ABC.exe (PID: 7408)
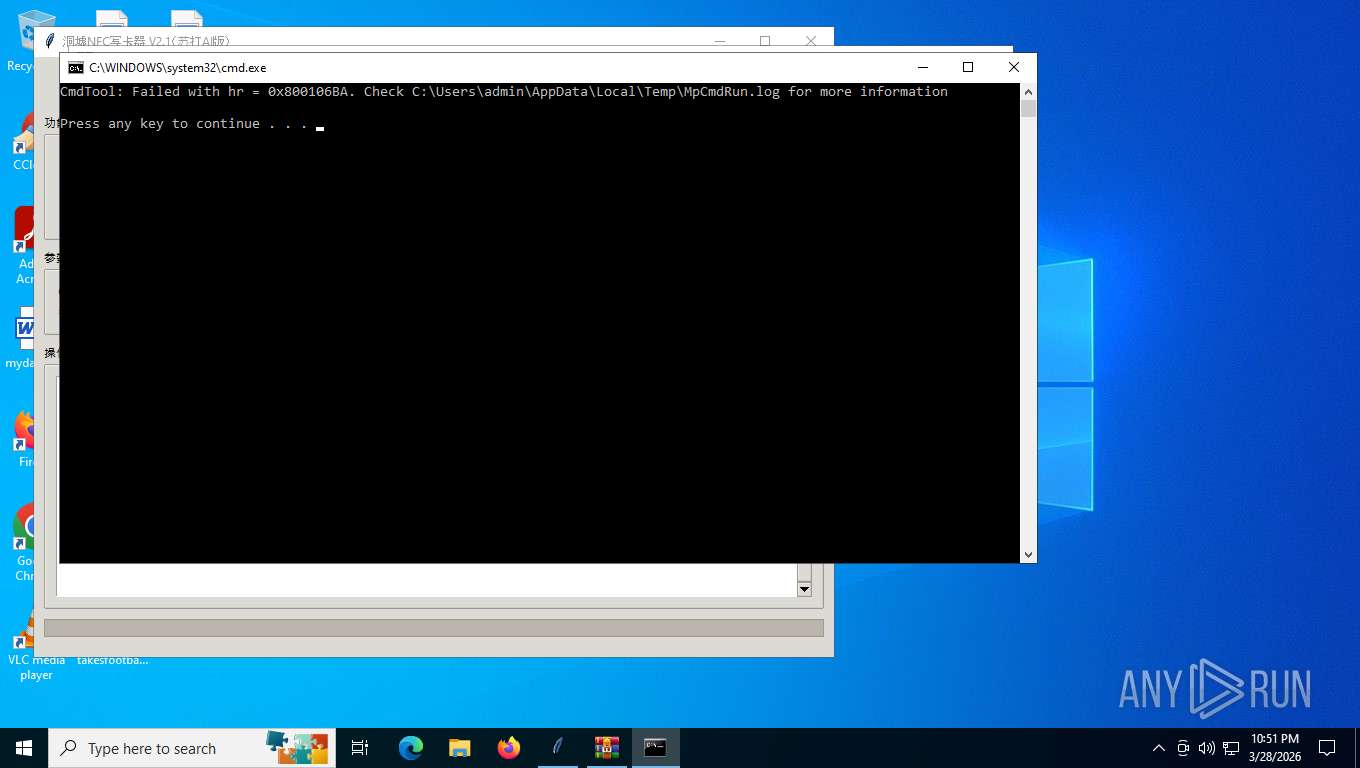
Starts CMD.EXE for commands execution
- cmd.exe (PID: 488)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 4276)
INFO
Checks supported languages
- ABC.exe (PID: 7408)
- ABC.exe (PID: 7428)
- MpCmdRun.exe (PID: 2940)
Reads the computer name
- ABC.exe (PID: 7408)
- ABC.exe (PID: 7428)
- MpCmdRun.exe (PID: 2940)
The sample compiled with english language support
- ABC.exe (PID: 7408)
Create files in a temporary directory
- ABC.exe (PID: 7408)
- MpCmdRun.exe (PID: 2940)
There is functionality for taking screenshot (YARA)
- ABC.exe (PID: 7408)
- ABC.exe (PID: 7428)
PyInstaller has been detected (YARA)
- ABC.exe (PID: 7408)
- ABC.exe (PID: 7428)
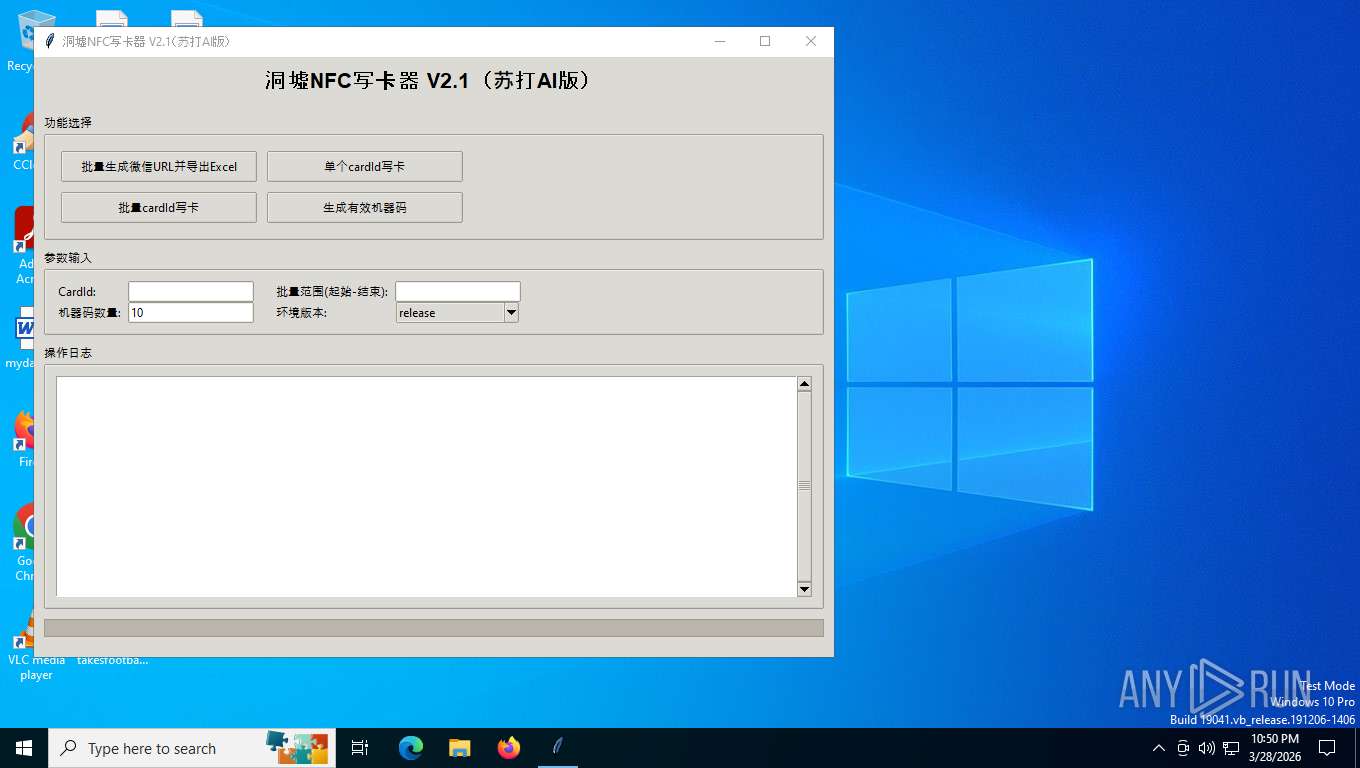
Manual execution by a user
- WinRAR.exe (PID: 4276)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:10:14 08:24:52+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 179712 |
| InitializedDataSize: | 165376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xda30 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
133
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 488 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR4276.32274\Rar$Scan17610.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR4276.32274" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
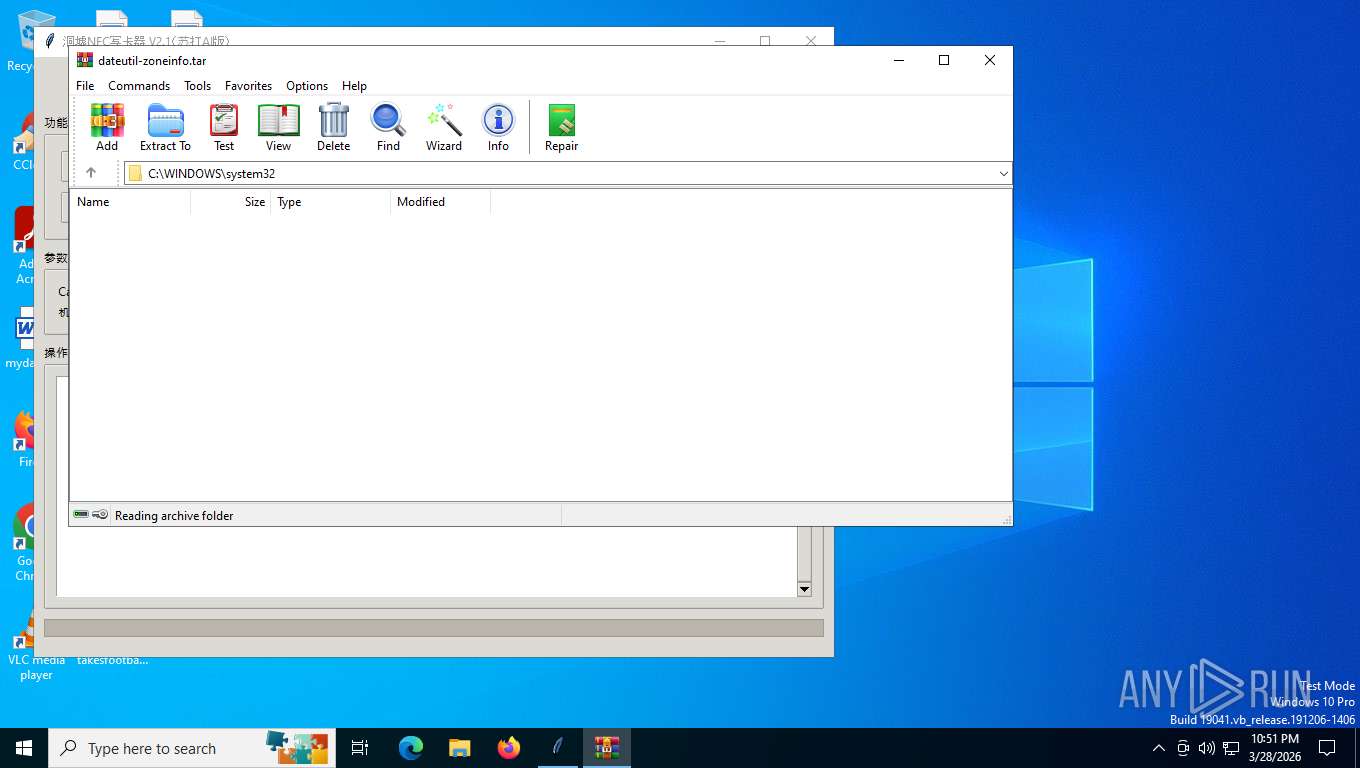
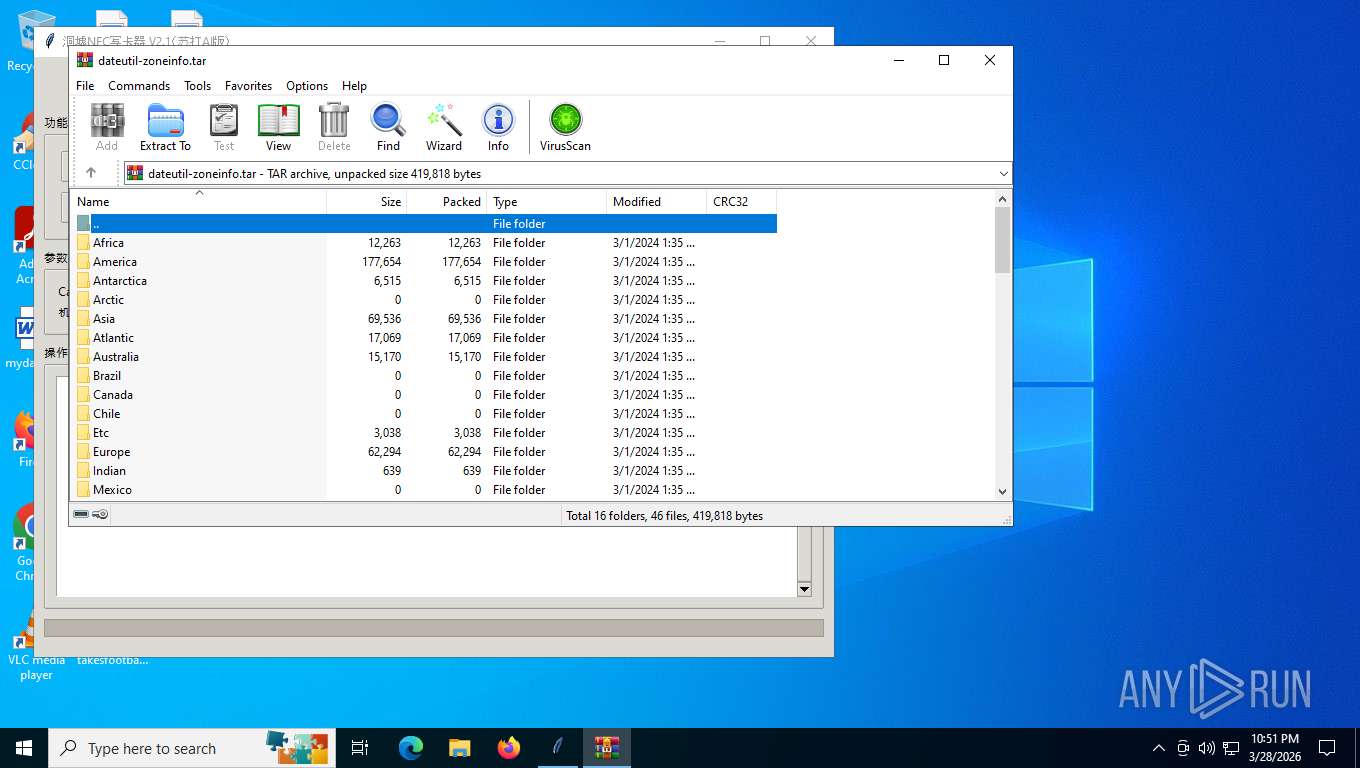
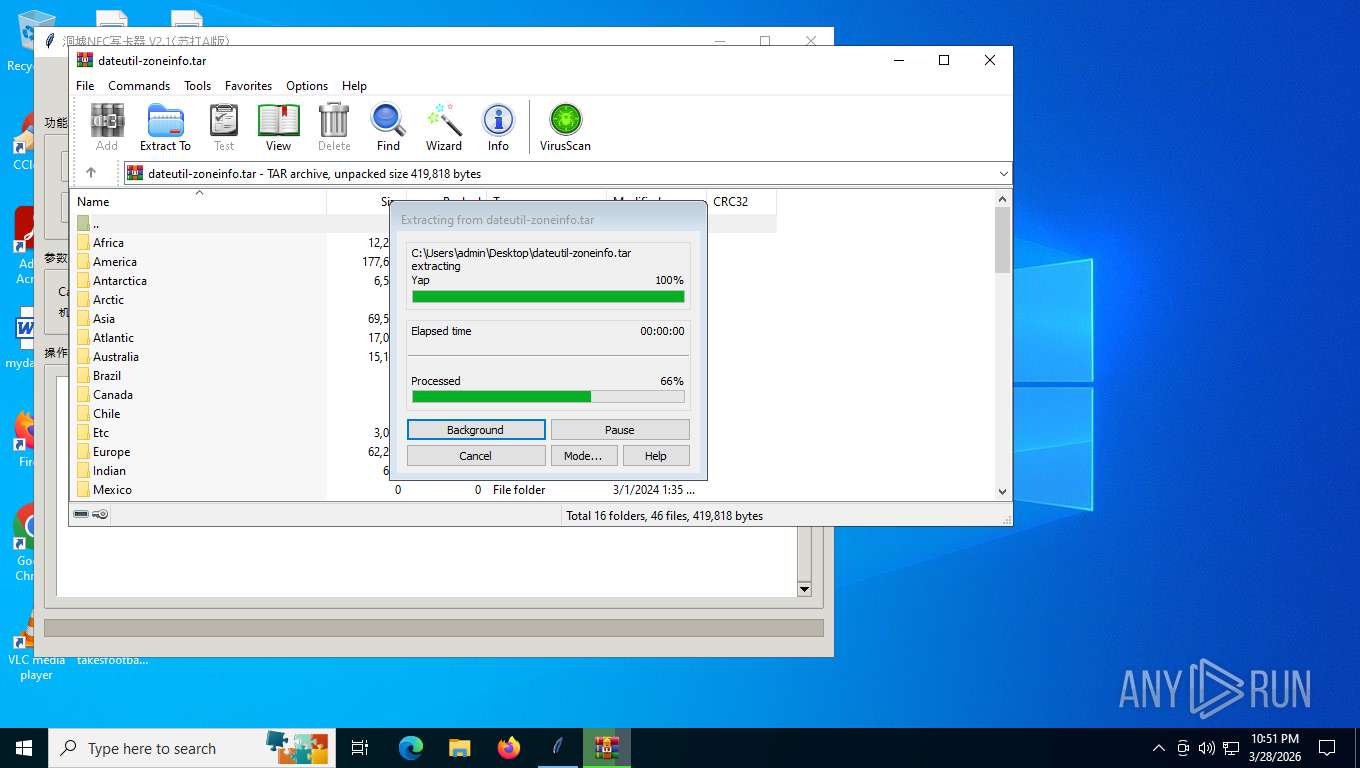
| 4276 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\dateutil-zoneinfo.tar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7408 | "C:\Users\admin\Desktop\ABC.exe" | C:\Users\admin\Desktop\ABC.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7428 | "C:\Users\admin\Desktop\ABC.exe" | C:\Users\admin\Desktop\ABC.exe | — | ABC.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 734
Read events
1 725
Write events
9
Delete events
0
Modification events
| (PID) Process: | (4276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (4276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\dateutil-zoneinfo.tar | |||
| (PID) Process: | (4276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
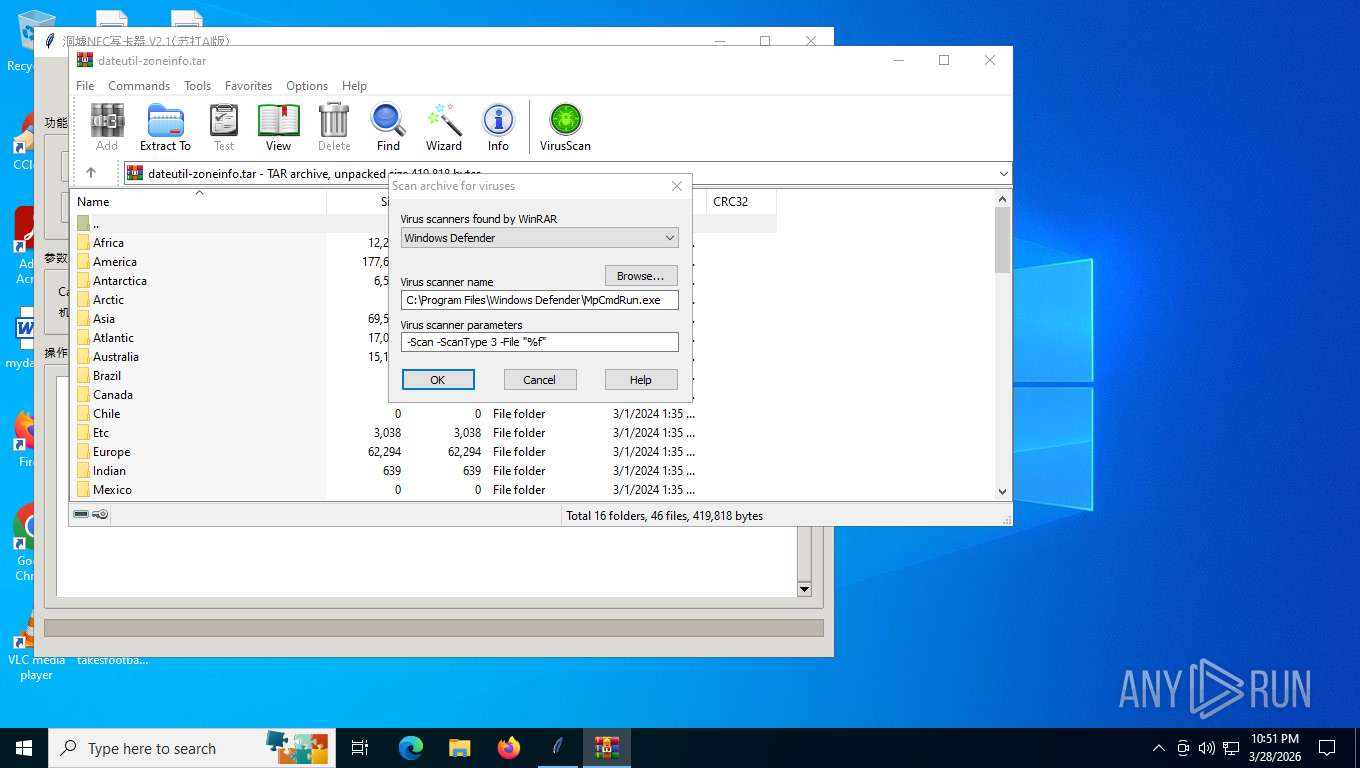
| (PID) Process: | (4276) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
Executable files
135
Suspicious files
955
Text files
948
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7408 | ABC.exe | C:\Users\admin\AppData\Local\Temp\_MEI74082\_asyncio.pyd | executable | |
MD5:756798492975EFE3B4803F1E0910DDFB | SHA256:998818E9D22D80C173CBC39511E99126C7369260BBD6B4AF9F4F7E9425966A96 | |||
| 7408 | ABC.exe | C:\Users\admin\AppData\Local\Temp\_MEI74082\_lzma.pyd | executable | |
MD5:568388719AFBDE6DE975F12A40160BA5 | SHA256:F774450ADBCCAFDEEA67EBB497FEFB57E45049E85A58C69E90D03D11B58DE72F | |||
| 7408 | ABC.exe | C:\Users\admin\AppData\Local\Temp\_MEI74082\_hashlib.pyd | executable | |
MD5:8FE3240B546859872B9D1A191F8EE4C2 | SHA256:5E8531D96BADDEDF7C1DD19B57A047CC449E77FAD5F32422FF10D9BEA70310D8 | |||
| 7408 | ABC.exe | C:\Users\admin\AppData\Local\Temp\_MEI74082\_multiprocessing.pyd | executable | |
MD5:FCCB149050914CE19B78058EEDB8A6EE | SHA256:B013FFE8116DFF35B16326635A39C5DC138467A864F5F331BE643514186CCD58 | |||
| 7408 | ABC.exe | C:\Users\admin\AppData\Local\Temp\_MEI74082\_bz2.pyd | executable | |
MD5:82AED08D3F1AD39771FCBFD23221C83B | SHA256:00FD6E83C621C70A45158A910B8D5009C821881971FF638D63A00DC43CABB130 | |||
| 7408 | ABC.exe | C:\Users\admin\AppData\Local\Temp\_MEI74082\_elementtree.pyd | executable | |
MD5:6F6A6BF74B93CB1ED6351EDABD0DC45F | SHA256:265F65F58C39242BDE9C0FA77A85F361EA24F06EE368580E329B6E89D3052A9A | |||
| 7408 | ABC.exe | C:\Users\admin\AppData\Local\Temp\_MEI74082\_ctypes.pyd | executable | |
MD5:F70335E08010C30740E4C8BE9D56B5F4 | SHA256:62FF5427CB9A9FA23C159E38A23002901493E4009E482FF3B085649214A9D32C | |||
| 7408 | ABC.exe | C:\Users\admin\AppData\Local\Temp\_MEI74082\VCRUNTIME140_1.dll | executable | |
MD5:F4987110E3468EA8050F4E17C756CDAD | SHA256:963E45EDD064545962E216C12D68071CED94DC8E11862A18F07F14EB2690A57C | |||
| 7408 | ABC.exe | C:\Users\admin\AppData\Local\Temp\_MEI74082\LIBBZ2.dll | executable | |
MD5:71E7C0F84D0A3D8EE0FFBDB60A36E504 | SHA256:25A4AAE35DD89709620106DB311AF5BCA7C868182B961E106A895AE14D2FC98A | |||
| 7408 | ABC.exe | C:\Users\admin\AppData\Local\Temp\_MEI74082\_decimal.pyd | executable | |
MD5:487068EC5ABE91A53DC529EBA70D550A | SHA256:7AC3A21513BF8E0FC6323F80AAFEAE1DD1B7F007473A83E39951132265BF571B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
39
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5712 | SIHClient.exe | GET | 304 | 20.165.94.63:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
5712 | SIHClient.exe | GET | 200 | 20.165.94.54:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
5484 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5484 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5316 | svchost.exe | POST | 200 | 20.190.160.130:443 | https://login.live.com/RST2.srf | unknown | text | 1.24 Kb | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 48.192.1.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | text | 512 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.130:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
5712 | SIHClient.exe | GET | 200 | 20.165.94.63:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.130:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 2.16.241.218:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5484 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5484 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |