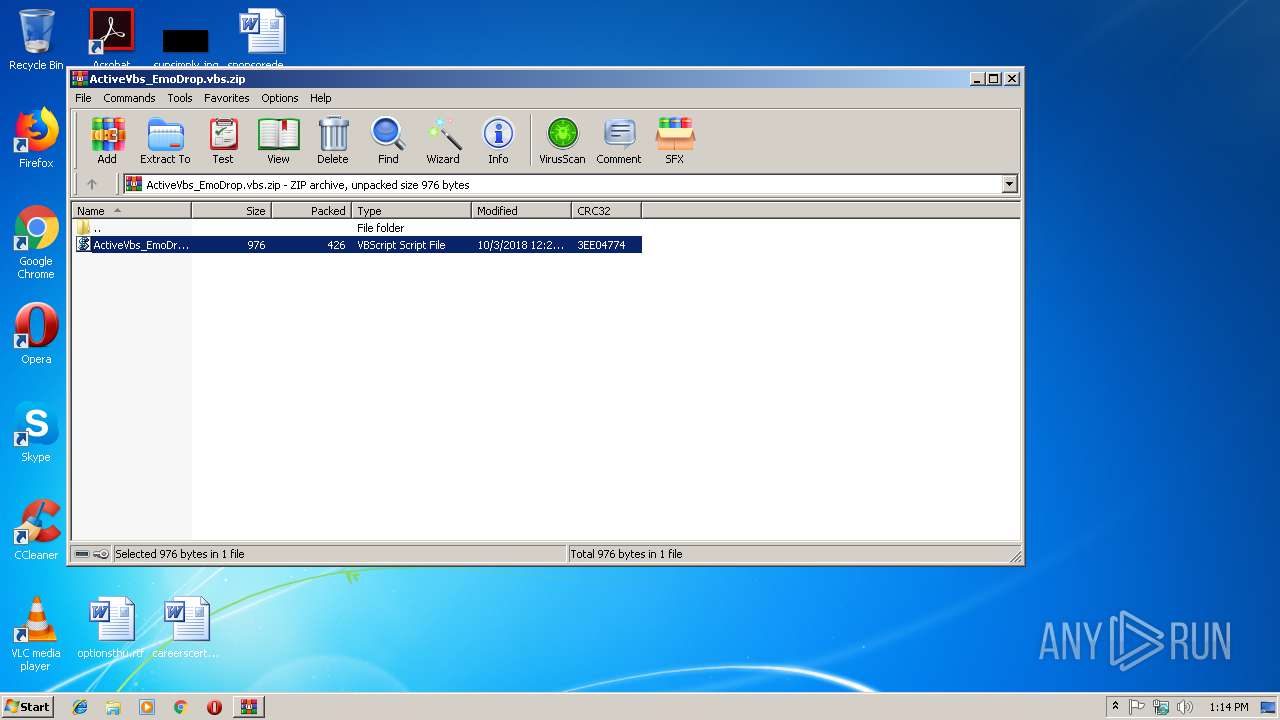
| File name: | ActiveVbs_EmoDrop.vbs.zip |
| Full analysis: | https://app.any.run/tasks/e952a4d6-1364-4ec8-9ee9-bff0bc784704 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 13:13:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
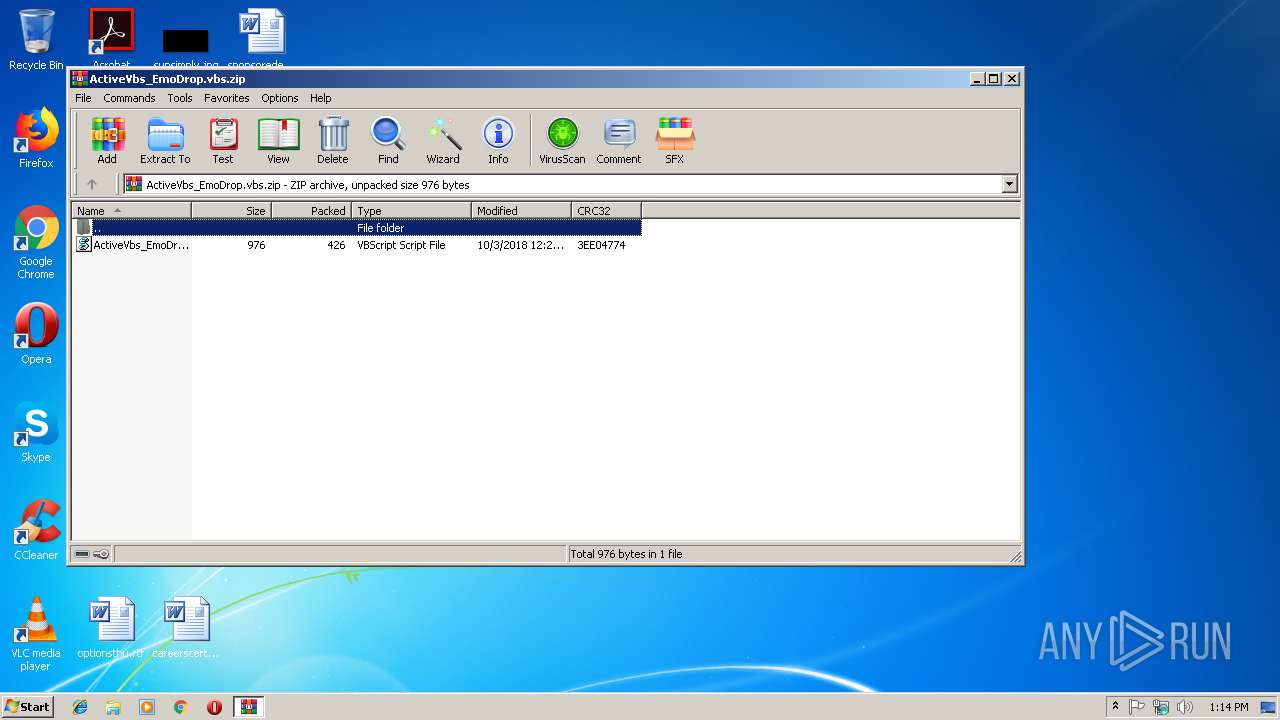
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 935134545F76CE891E4B3706F01FC246 |
| SHA1: | 339E712FFCB2227E4E01CA22741E8E40519350BB |
| SHA256: | 44FAE066B95D46B99C15ADF1C592BEF45526260C40498EAA25CC81CCD849A32E |
| SSDEEP: | 12:5BqvBlWanQs785O6wHowraQisXXTBVCPsUlEOJcMaOkn:Hq64UO6MJrbiK3xUla |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes scripts
- WinRAR.exe (PID: 2936)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:10:03 13:26:15 |
| ZipCRC: | 0x3ee04774 |
| ZipCompressedSize: | 426 |
| ZipUncompressedSize: | 976 |
| ZipFileName: | ActiveVbs_EmoDrop.vbs |
Total processes
33
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
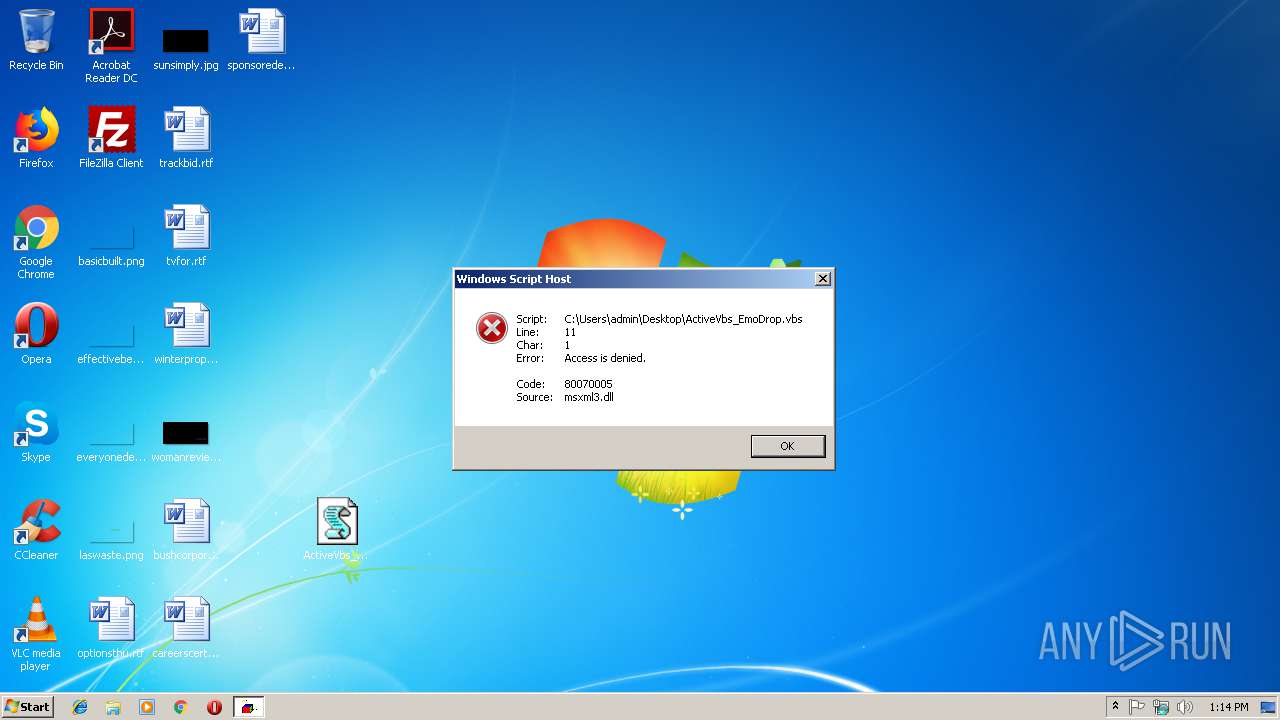
| 2736 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\ActiveVbs_EmoDrop.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
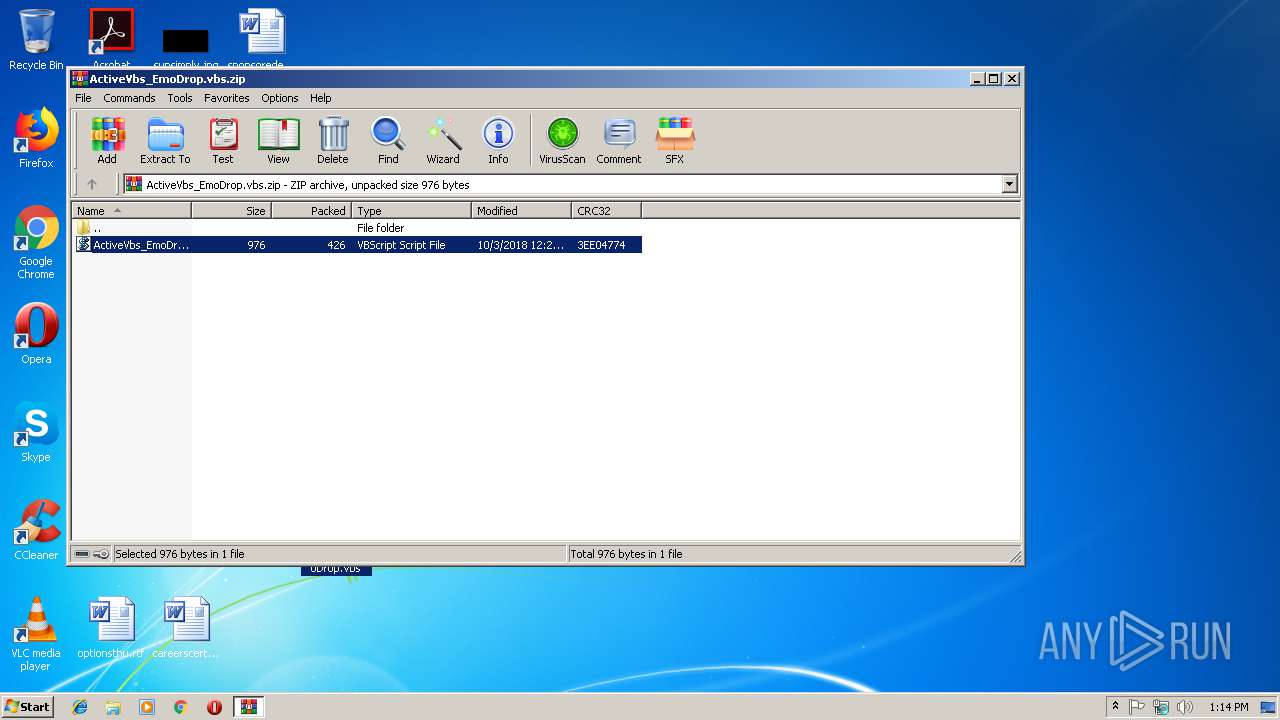
| 2936 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ActiveVbs_EmoDrop.vbs.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
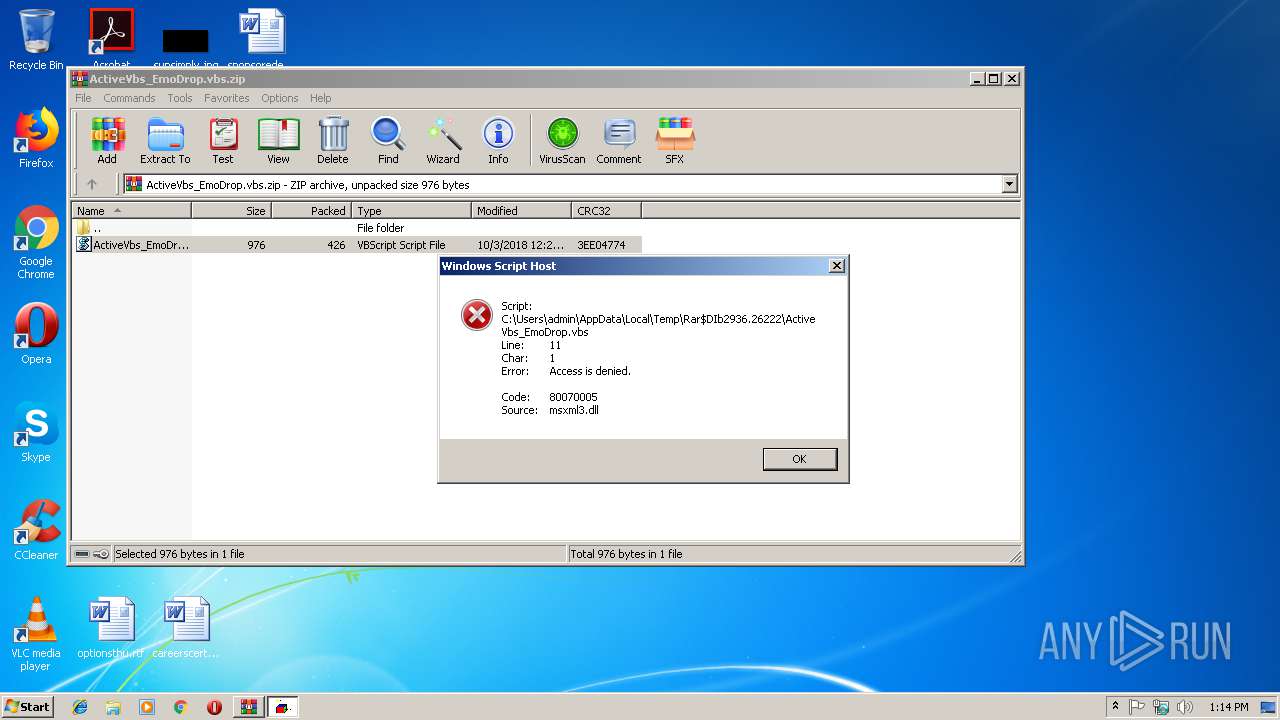
| 3140 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb2936.26222\ActiveVbs_EmoDrop.vbs" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
687
Read events
636
Write events
51
Delete events
0
Modification events
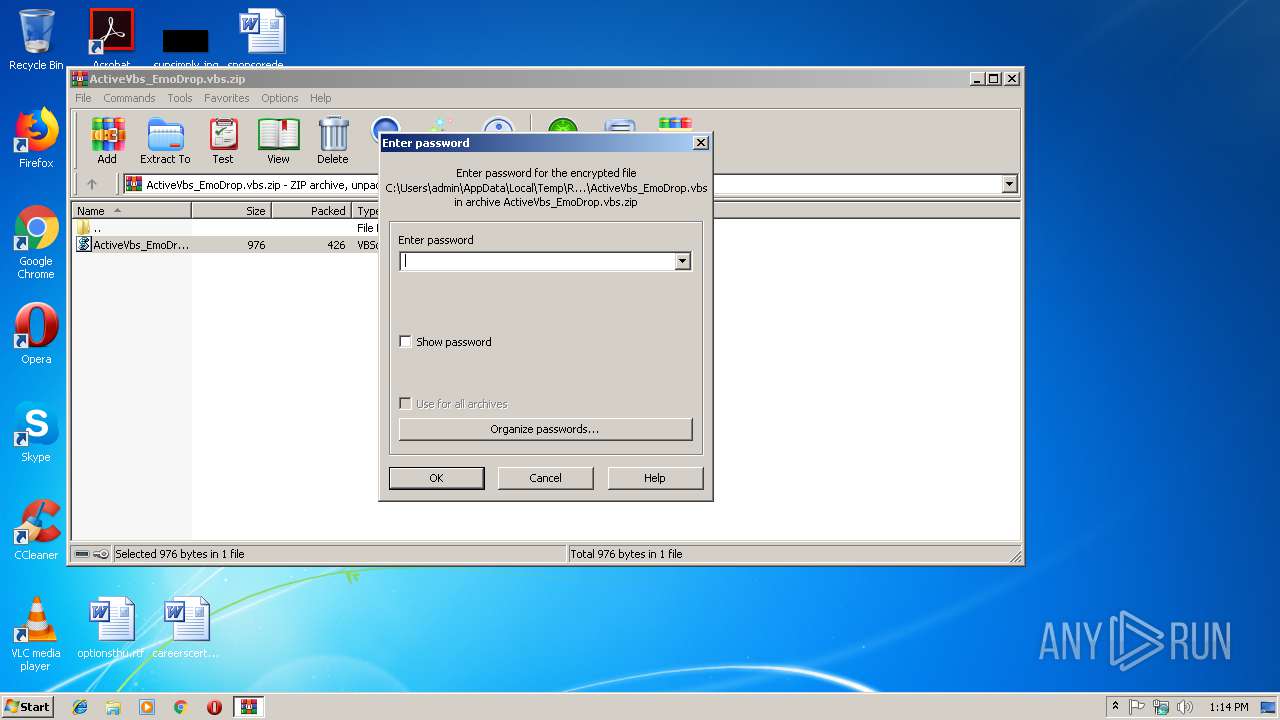
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ActiveVbs_EmoDrop.vbs.zip | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
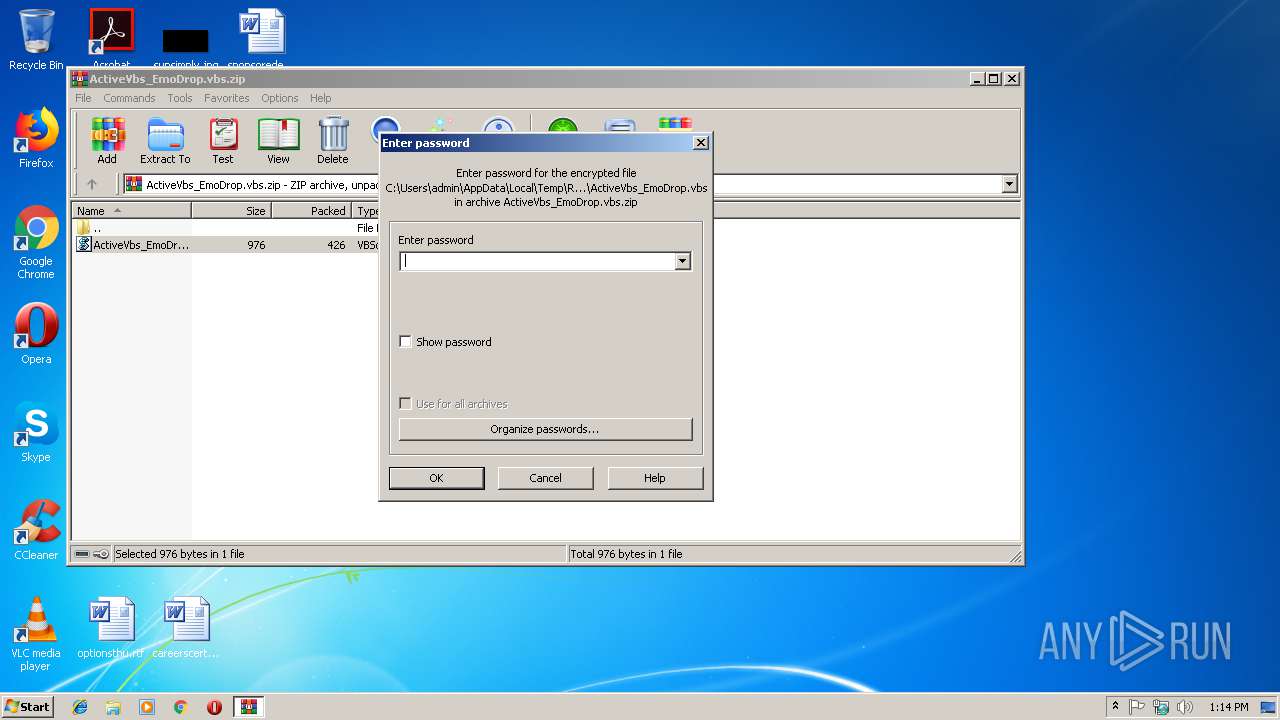
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2936.27663\ActiveVbs_EmoDrop.vbs | — | |
MD5:— | SHA256:— | |||
| 2936 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2936.26222\ActiveVbs_EmoDrop.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2736 | WScript.exe | GET | 301 | 23.229.231.33:80 | http://bsrcellular.com/zhm65KeNd | US | html | 241 b | malicious |
3140 | WScript.exe | GET | 301 | 23.229.231.33:80 | http://bsrcellular.com/zhm65KeNd | US | html | 241 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3140 | WScript.exe | 23.229.231.33:80 | bsrcellular.com | GoDaddy.com, LLC | US | malicious |
2736 | WScript.exe | 23.229.231.33:80 | bsrcellular.com | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bsrcellular.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3140 | WScript.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader MacroLoader MSOffice |
2736 | WScript.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader MacroLoader MSOffice |