| File name: | 74b88a6f-d2f1-2b54-f72c-4cd5a9bdb975.eml |
| Full analysis: | https://app.any.run/tasks/821d2cea-83d1-4415-91b8-b63828bdc29f |
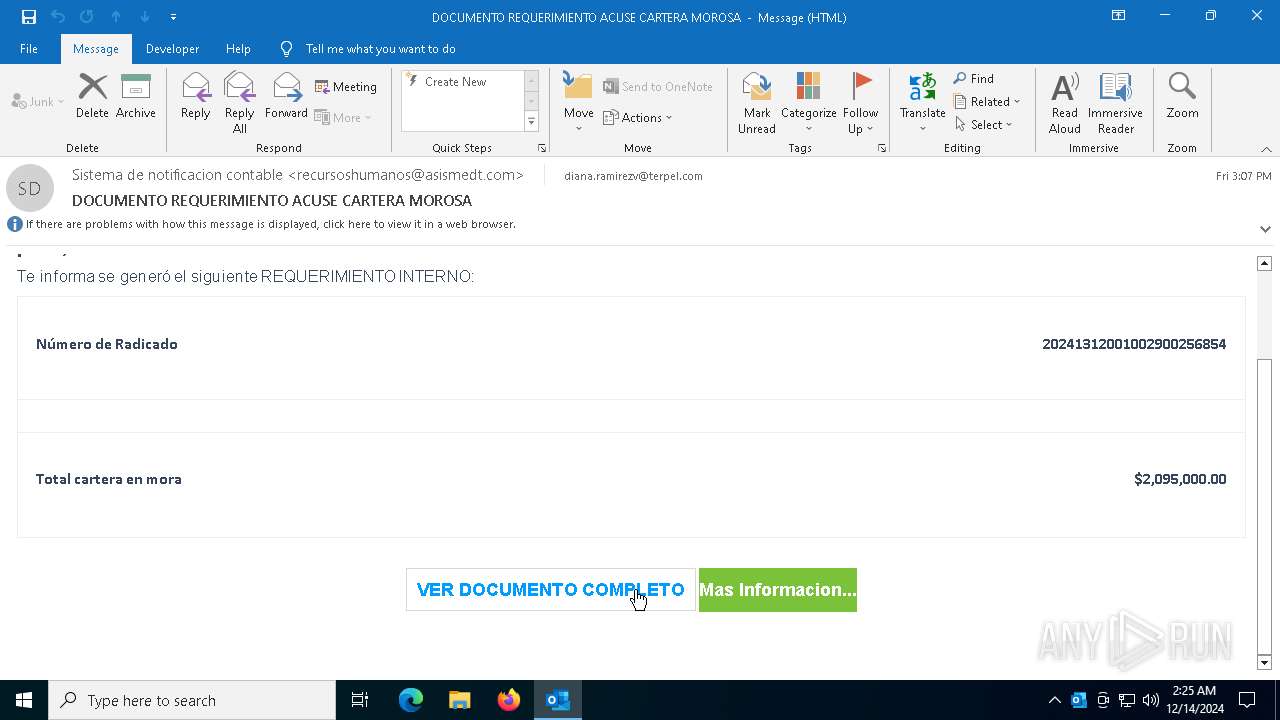
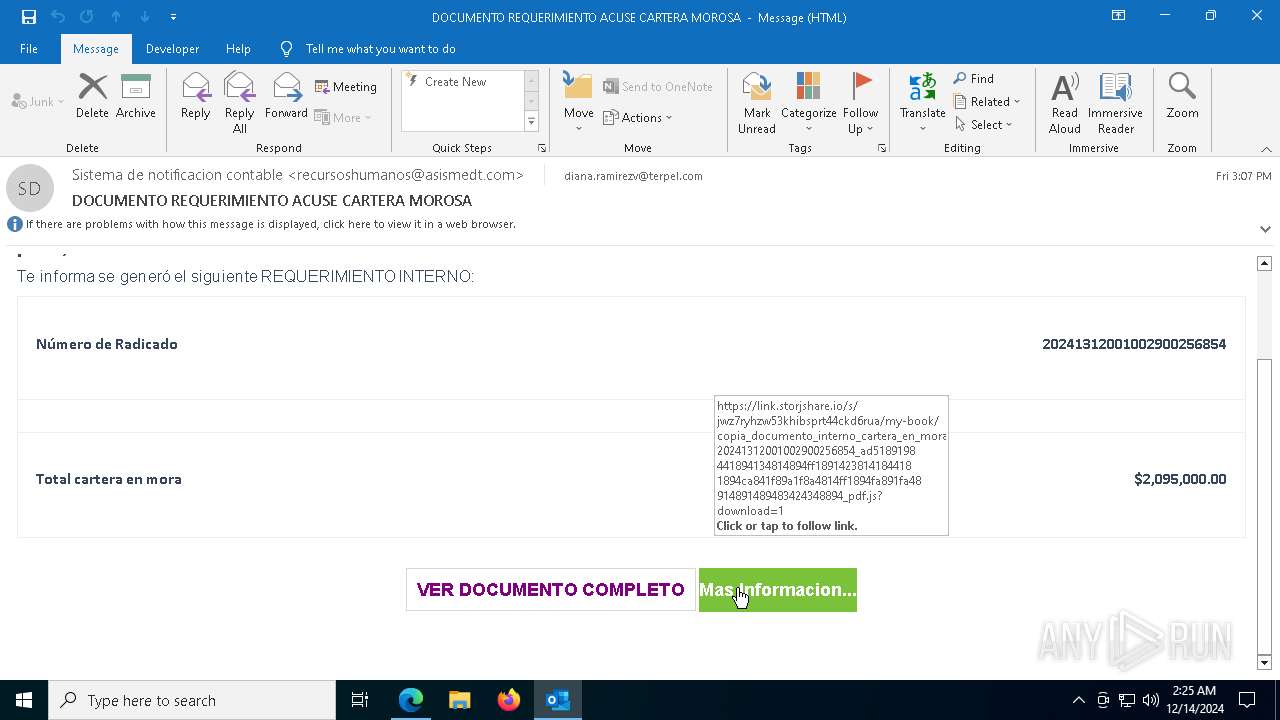
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 02:24:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (347), with CRLF line terminators |
| MD5: | EE1FDC0FBAB5B521EFB4120D45B9F651 |
| SHA1: | 8C1750CA9319998324702A9C55CC98BE2BFCE871 |
| SHA256: | 44E1EEB7E57C39410540089FCB9C85826969CED92016460F963B8BF8734F358D |
| SSDEEP: | 384:b4cJuqRRtUagduPzLuZqUMc8J7Dfv5g/8XNwocKUEtaIyzQjHzQdsYUq6ybTEHiY:b1JuqRRuagIPzKZgpvK/8XtcTWaIyzQR |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 8148)
- wscript.exe (PID: 1200)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 8148)
- wscript.exe (PID: 1200)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 8148)
- wscript.exe (PID: 1200)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 8148)
- powershell.exe (PID: 7380)
- wscript.exe (PID: 1200)
- powershell.exe (PID: 7624)
Run PowerShell with an invisible window
- powershell.exe (PID: 7380)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 7624)
Bypass execution policy to execute commands
- powershell.exe (PID: 7480)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 7380)
Stego campaign has been detected
- powershell.exe (PID: 7480)
- powershell.exe (PID: 7564)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 7564)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 7564)
SUSPICIOUS
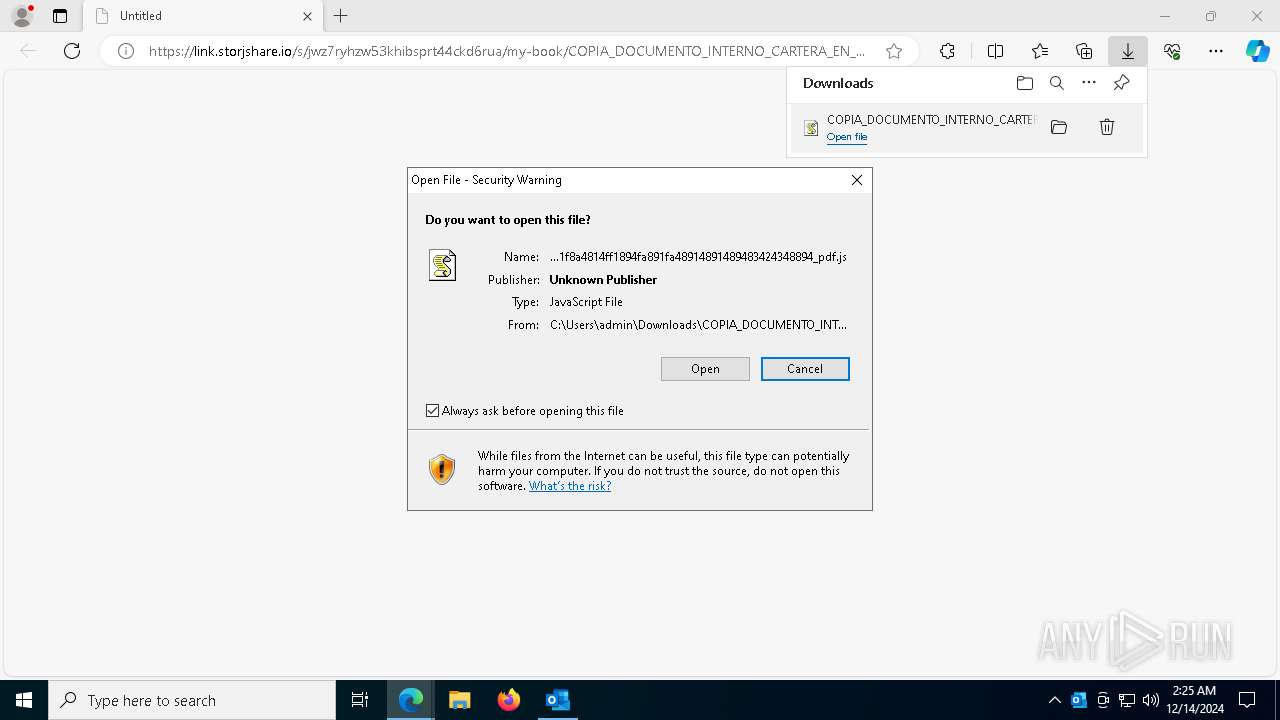
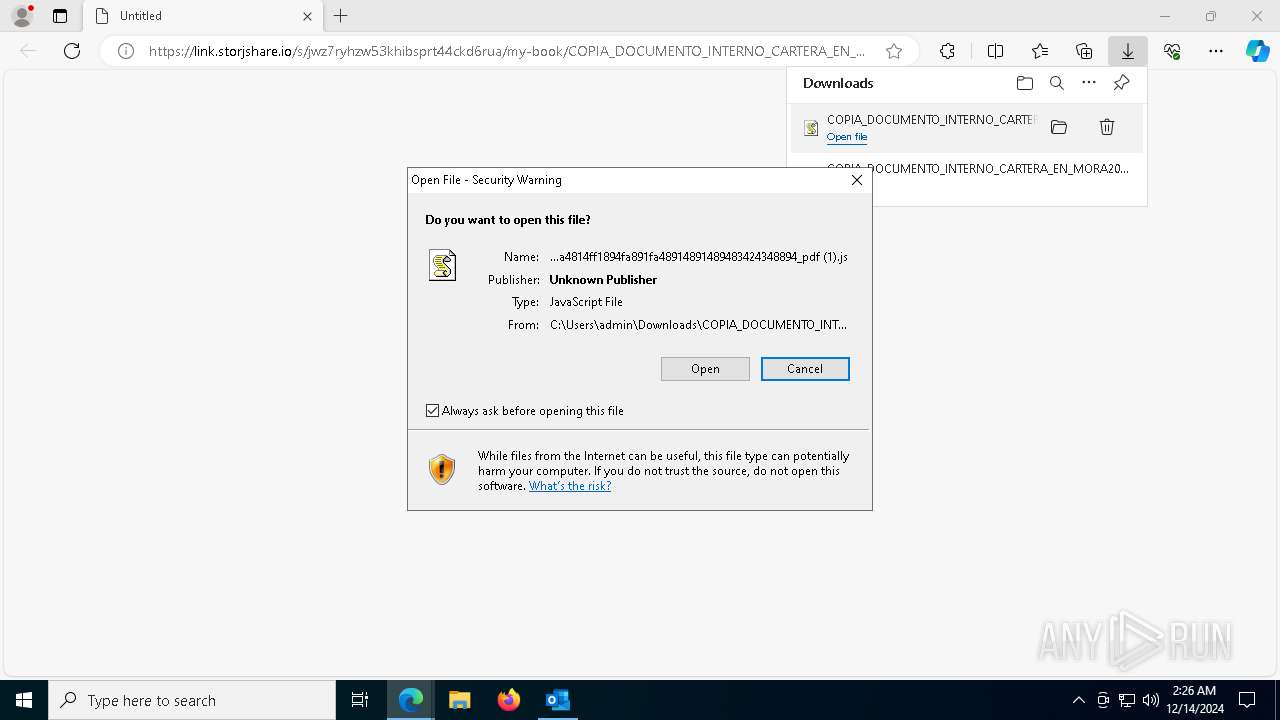
The process executes JS scripts
- msedge.exe (PID: 5252)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 8148)
- powershell.exe (PID: 7380)
- wscript.exe (PID: 1200)
- powershell.exe (PID: 7624)
Base64-obfuscated command line is found
- wscript.exe (PID: 8148)
- wscript.exe (PID: 1200)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 8148)
- powershell.exe (PID: 7380)
- wscript.exe (PID: 1200)
- powershell.exe (PID: 7624)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 7564)
Application launched itself
- powershell.exe (PID: 7380)
- powershell.exe (PID: 7624)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 7564)
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 7380)
- powershell.exe (PID: 7624)
Probably download files using WebClient
- powershell.exe (PID: 7380)
- powershell.exe (PID: 7624)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8148)
- wscript.exe (PID: 1200)
Connects to unusual port
- AddInProcess32.exe (PID: 8076)
INFO
Checks supported languages
- identity_helper.exe (PID: 7608)
- AddInProcess32.exe (PID: 8076)
- AddInProcess32.exe (PID: 3640)
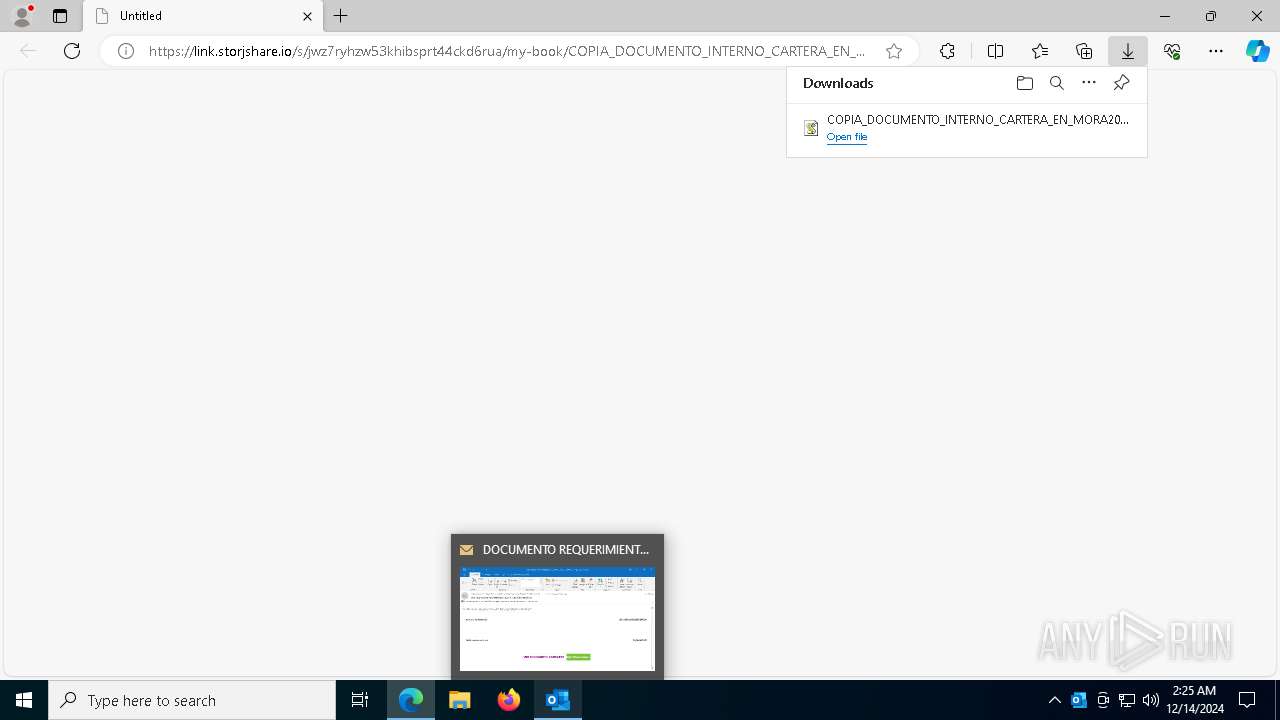
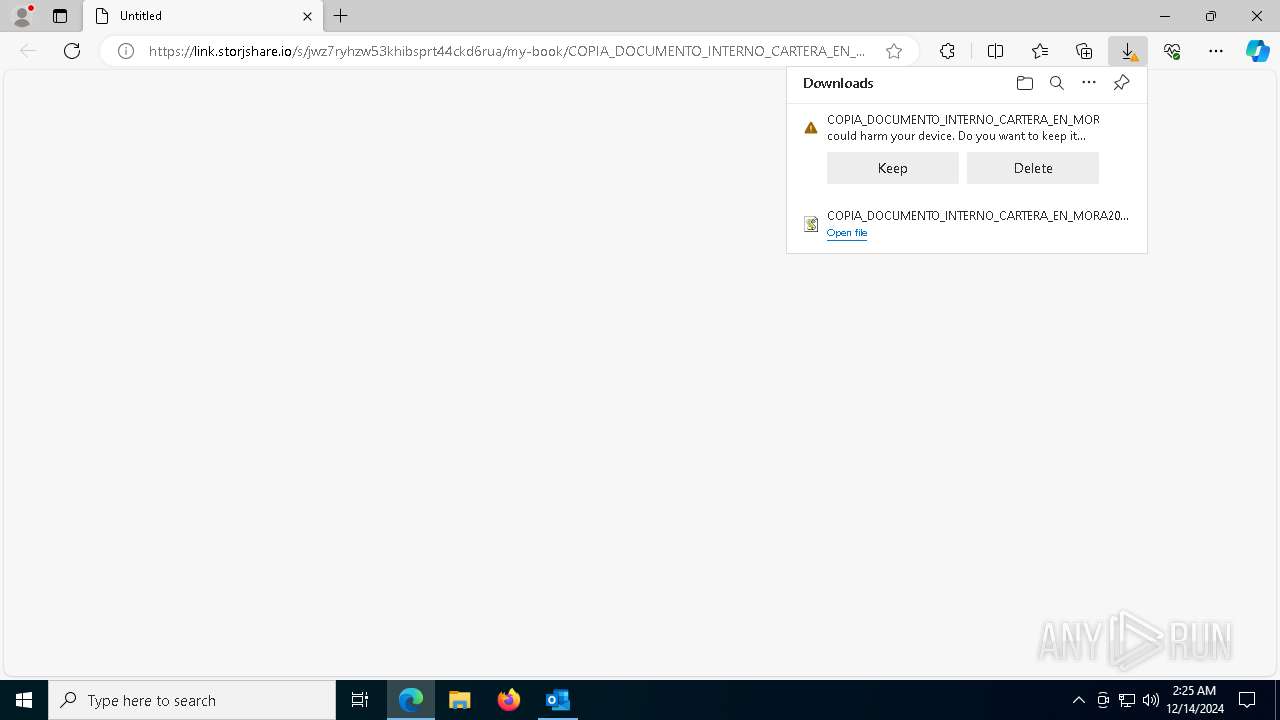
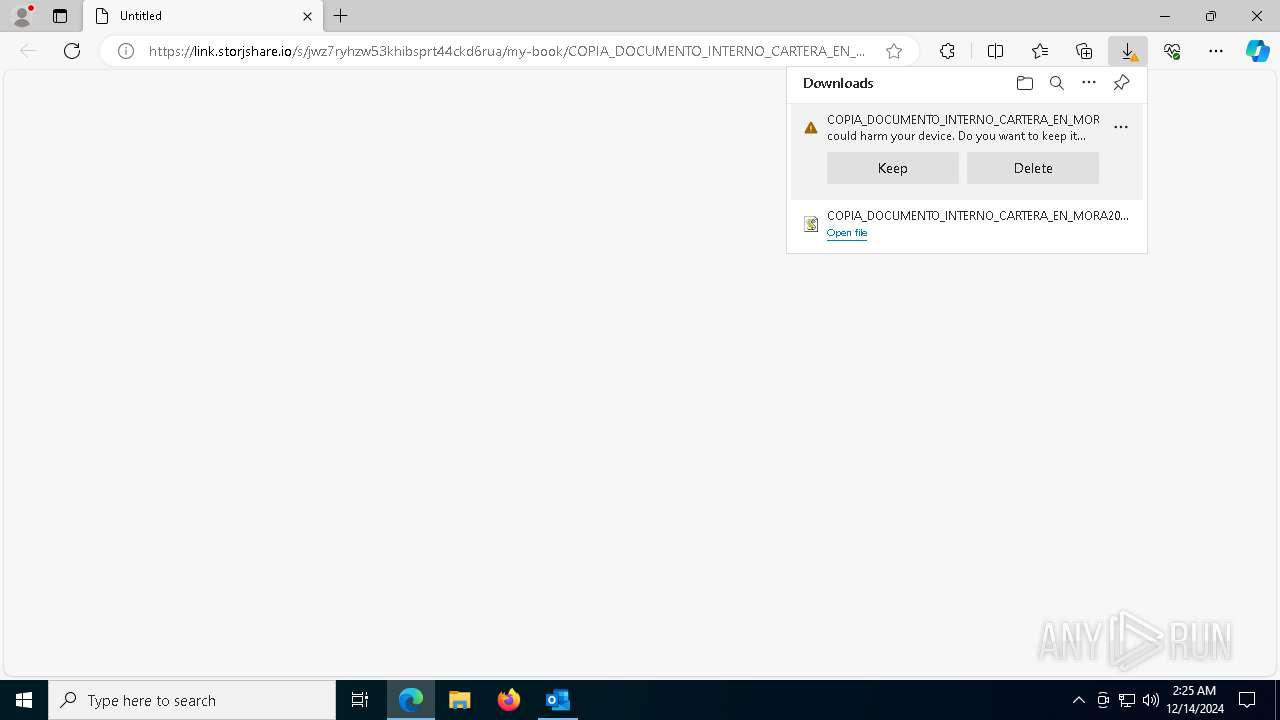
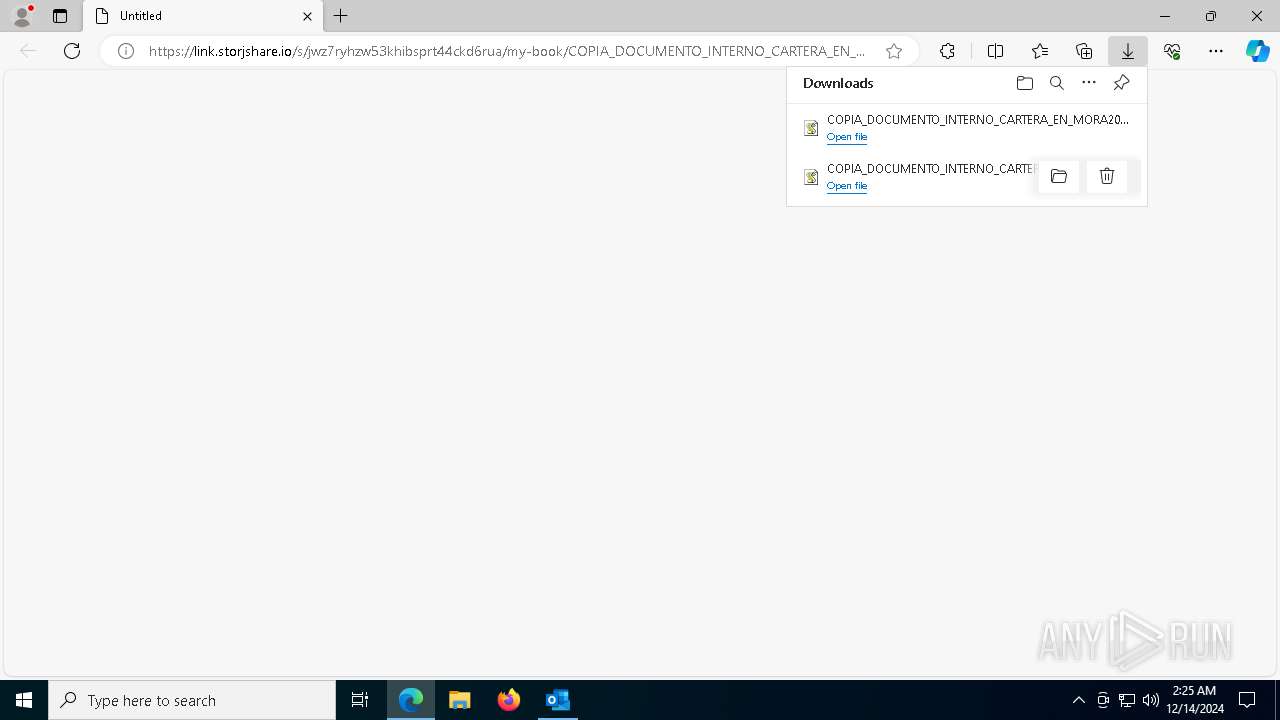
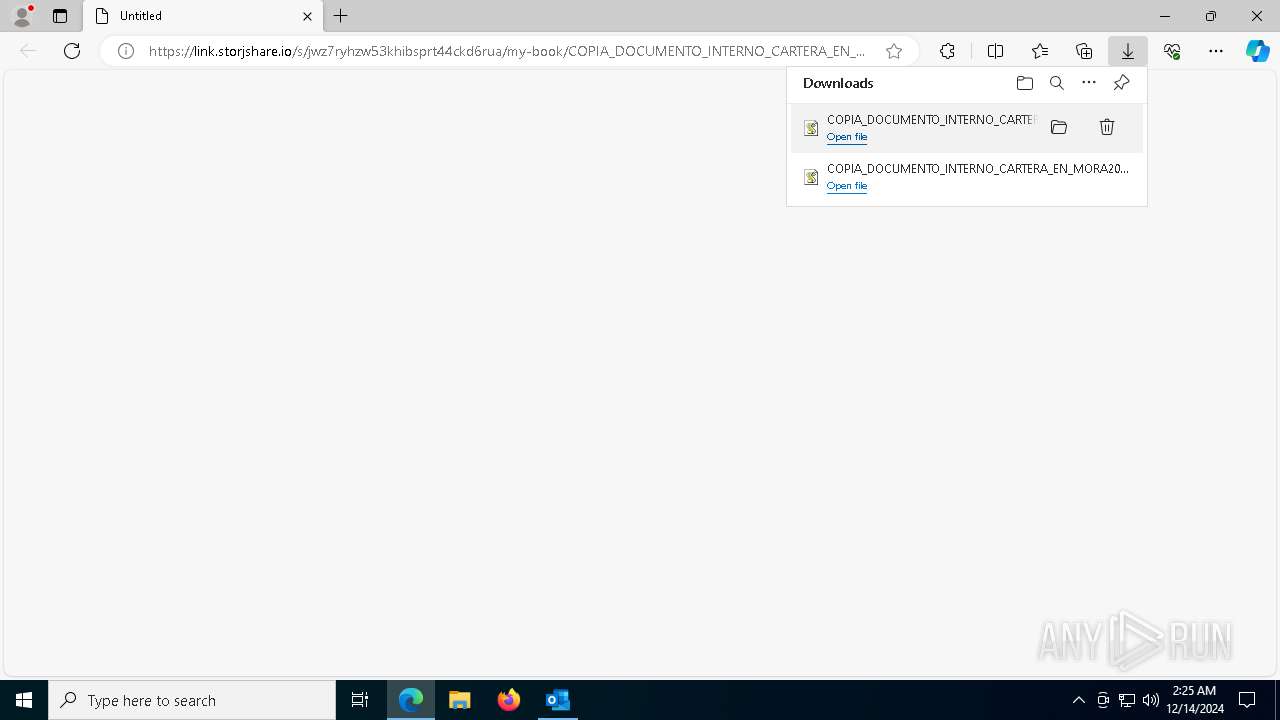
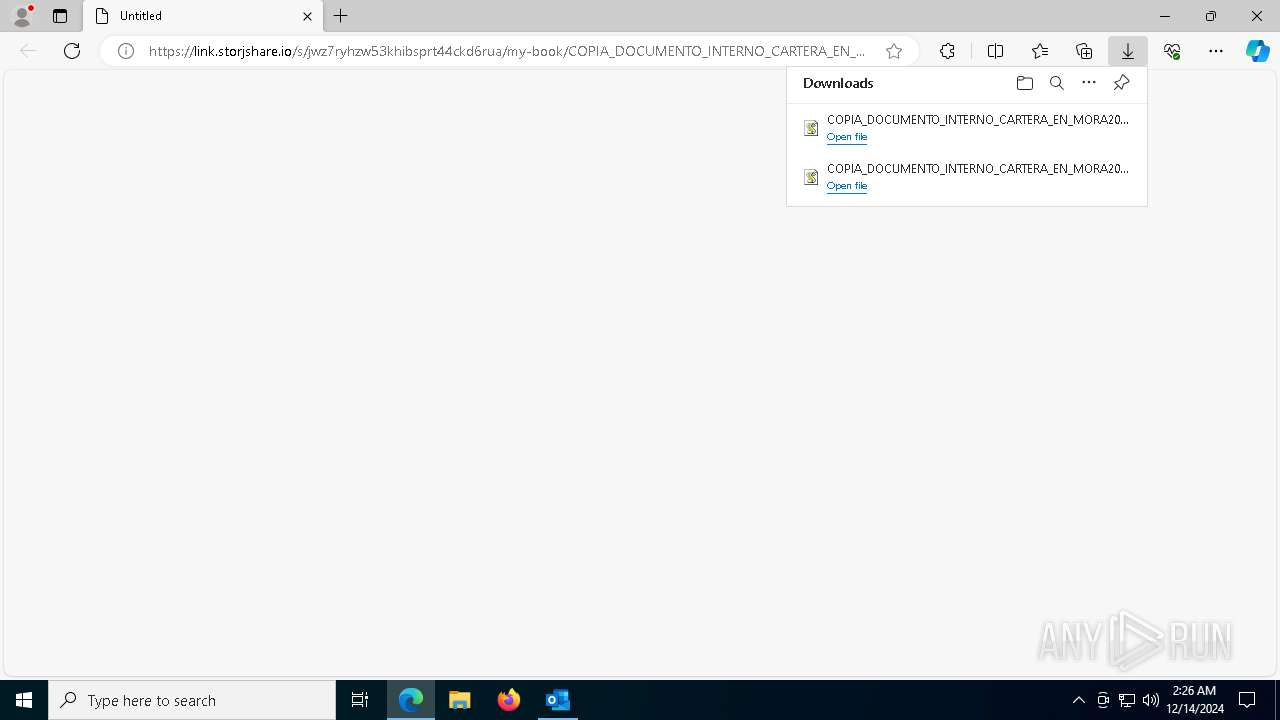
The process uses the downloaded file
- OUTLOOK.EXE (PID: 6160)
- msedge.exe (PID: 8024)
- msedge.exe (PID: 5252)
- wscript.exe (PID: 8148)
- msedge.exe (PID: 3140)
- wscript.exe (PID: 1200)
Reads Environment values
- identity_helper.exe (PID: 7608)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5252)
Reads the computer name
- identity_helper.exe (PID: 7608)
- AddInProcess32.exe (PID: 8076)
- AddInProcess32.exe (PID: 3640)
Checks proxy server information
- wscript.exe (PID: 8148)
- powershell.exe (PID: 7480)
- wscript.exe (PID: 1200)
- powershell.exe (PID: 7564)
Application launched itself
- msedge.exe (PID: 5252)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 7624)
Disables trace logs
- powershell.exe (PID: 7480)
- powershell.exe (PID: 7564)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 7380)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 7564)
Reads the machine GUID from the registry
- AddInProcess32.exe (PID: 8076)
- AddInProcess32.exe (PID: 3640)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 7380)
The sample compiled with english language support
- msedge.exe (PID: 6096)
Executable content was dropped or overwritten
- msedge.exe (PID: 6096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
184
Monitored processes
54
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7108 --field-trial-handle=2296,i,4708771165240155717,11707053537621051287,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
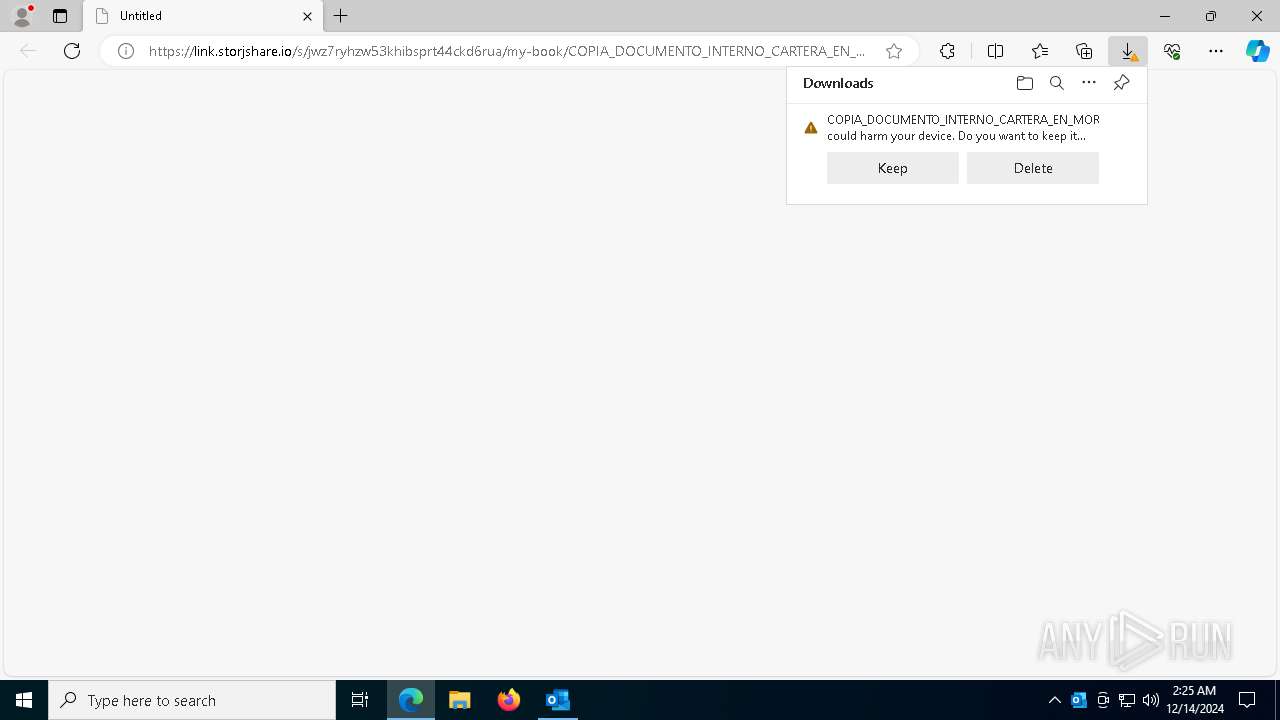
| 1200 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\COPIA_DOCUMENTO_INTERNO_CARTERA_EN_MORA20241312001002900256854_ad5189198441894134814894ff18914238141844181894ca841f89a1f8a4814ff1894fa891fa48914891489483424348894_pdf (1).js" | C:\Windows\System32\wscript.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --mojo-platform-channel-handle=5760 --field-trial-handle=2296,i,4708771165240155717,11707053537621051287,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2408 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5516 --field-trial-handle=2296,i,4708771165240155717,11707053537621051287,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2676 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
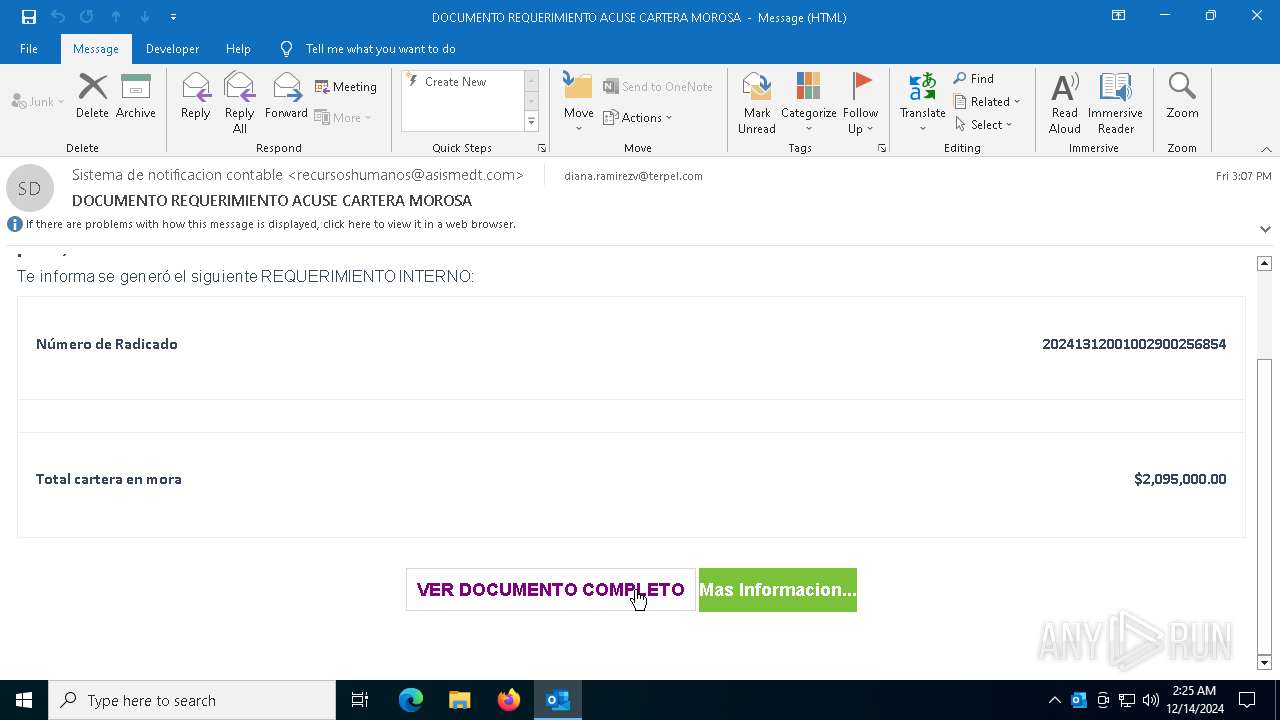
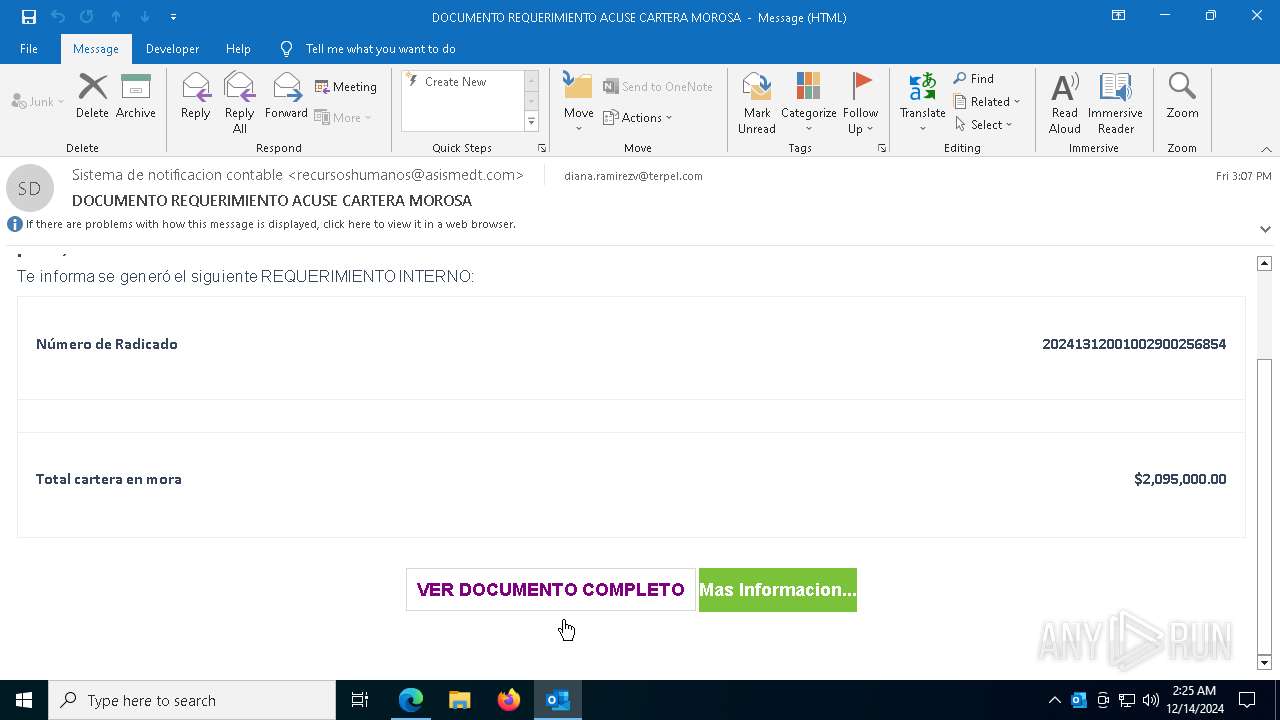
| 2736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://link.storjshare.io/s/jwz7ryhzw53khibsprt44ckd6rua/my-book/COPIA_DOCUMENTO_INTERNO_CARTERA_EN_MORA20241312001002900256854_ad5189198441894134814894ff18914238141844181894ca841f89a1f8a4814ff1894fa891fa48914891489483424348894_pdf.js?download=1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6776 --field-trial-handle=2296,i,4708771165240155717,11707053537621051287,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3640 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
38 726
Read events
38 258
Write events
399
Delete events
69
Modification events
| (PID) Process: | (6160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (6160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\6160 |
| Operation: | write | Name: | 0 |
Value: 0B0E10AA0BAFE15C59F7479E3BA64E224A6DED230046C8D79EDCF5B9D3ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C5119030D2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (6160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (6160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (6160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (6160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (6160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (6160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (6160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
Executable files
4
Suspicious files
123
Text files
66
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6160 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 5252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF13b420.TMP | — | |
MD5:— | SHA256:— | |||
| 5252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13b420.TMP | — | |
MD5:— | SHA256:— | |||
| 5252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13b420.TMP | — | |
MD5:— | SHA256:— | |||
| 5252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6160 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | der | |
MD5:030B68DB7EE1939DAC0DF0FF6BE92092 | SHA256:A6B2F0E5C0E4CDACD904DD7119223715ED87B7D350463664C3FB97BF3FBB84B4 | |||
| 5252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:C7E2197BAE099B13BBB3ADEB1433487D | SHA256:3460EEAF45D581DD43A6E4E17AF8102DDAFF5AEAA88B10099527CF85211629E9 | |||
| 5252 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:1C42329800C95BC1DB27E7657711FF1E | SHA256:D58993216FB0CBF52CED6DA4FCAEBFC8FCC7C1A37191954397BA77951B16BE9B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
80
DNS requests
69
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1328 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ed1297e-f6c9-4355-aec4-433ea371b116?P1=1734366243&P2=404&P3=2&P4=k2ANU%2fTnyOdybIi8rxEoYRzLyp0Jm%2f4SuExrtv0fRPp6gDJ7lFXUws4weVo34OZeeUtM%2bZwO1AjamUuU%2fktpVg%3d%3d | unknown | — | — | whitelisted |
1328 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ed1297e-f6c9-4355-aec4-433ea371b116?P1=1734366243&P2=404&P3=2&P4=k2ANU%2fTnyOdybIi8rxEoYRzLyp0Jm%2f4SuExrtv0fRPp6gDJ7lFXUws4weVo34OZeeUtM%2bZwO1AjamUuU%2fktpVg%3d%3d | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1468 | svchost.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1468 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6160 | OUTLOOK.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6160 | OUTLOOK.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1468 | svchost.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1468 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6160 | OUTLOOK.EXE | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6796 | msedge.exe | Potentially Bad Traffic | ET INFO File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
6796 | msedge.exe | Potentially Bad Traffic | ET INFO File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
6796 | msedge.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Domain (link .storjshare .io in TLS SNI) |
6796 | msedge.exe | Misc activity | ET INFO Commonly Actor Abused Online Service Domain (storjshare .io) |
6796 | msedge.exe | Misc activity | ET INFO Commonly Actor Abused Online Service Domain (storjshare .io) |
6796 | msedge.exe | Misc activity | ET INFO Observed Commonly Actor Abused Online Service Domain (storjshare .io in TLS SNI) |
7480 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
7564 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
2 ETPRO signatures available at the full report