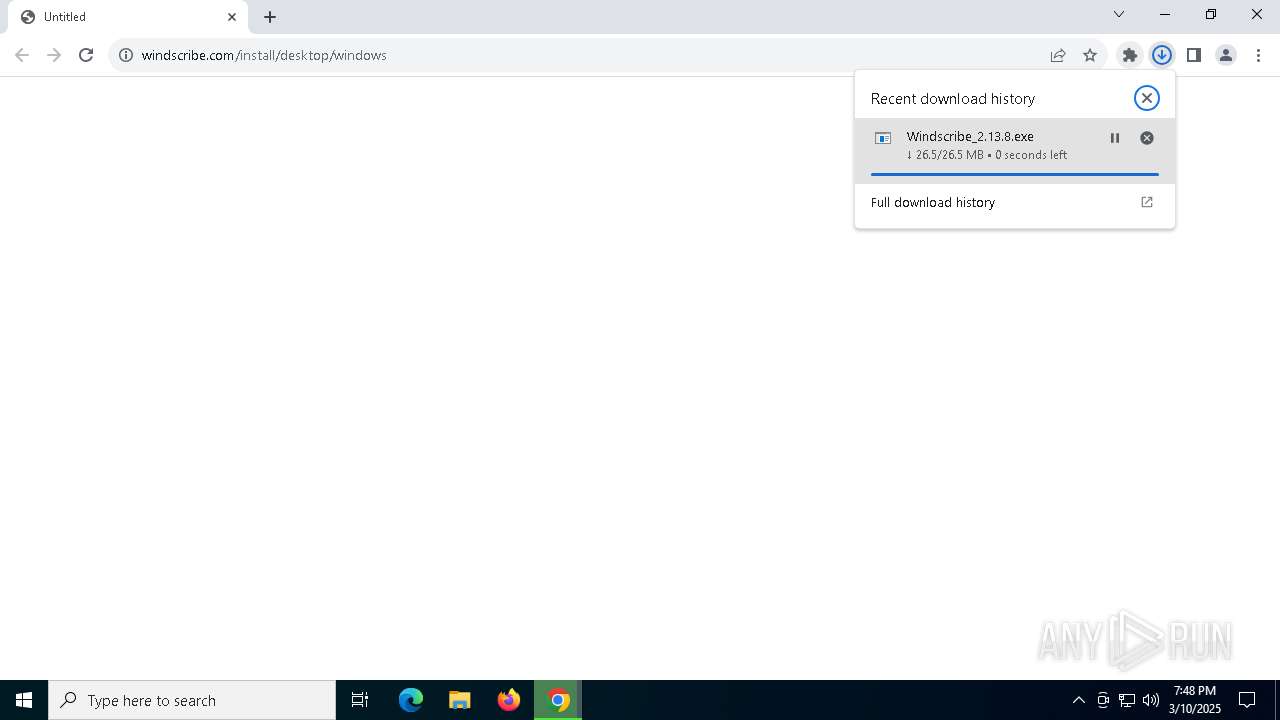
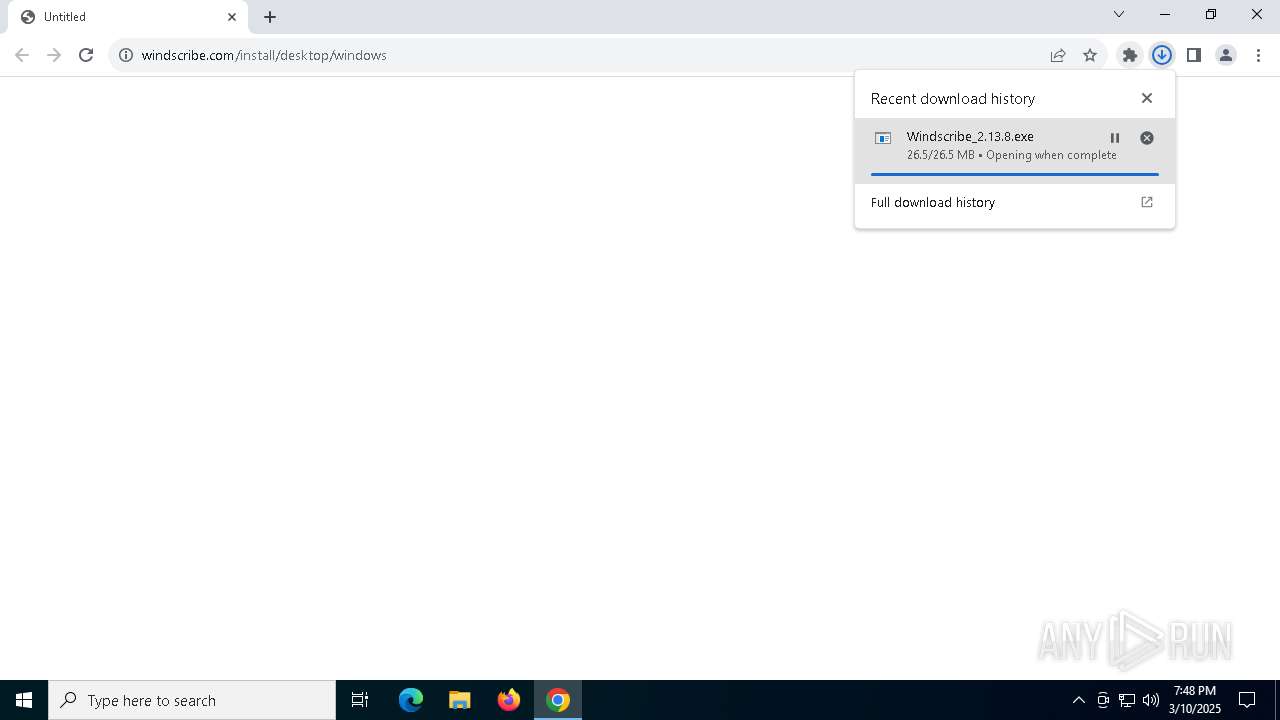
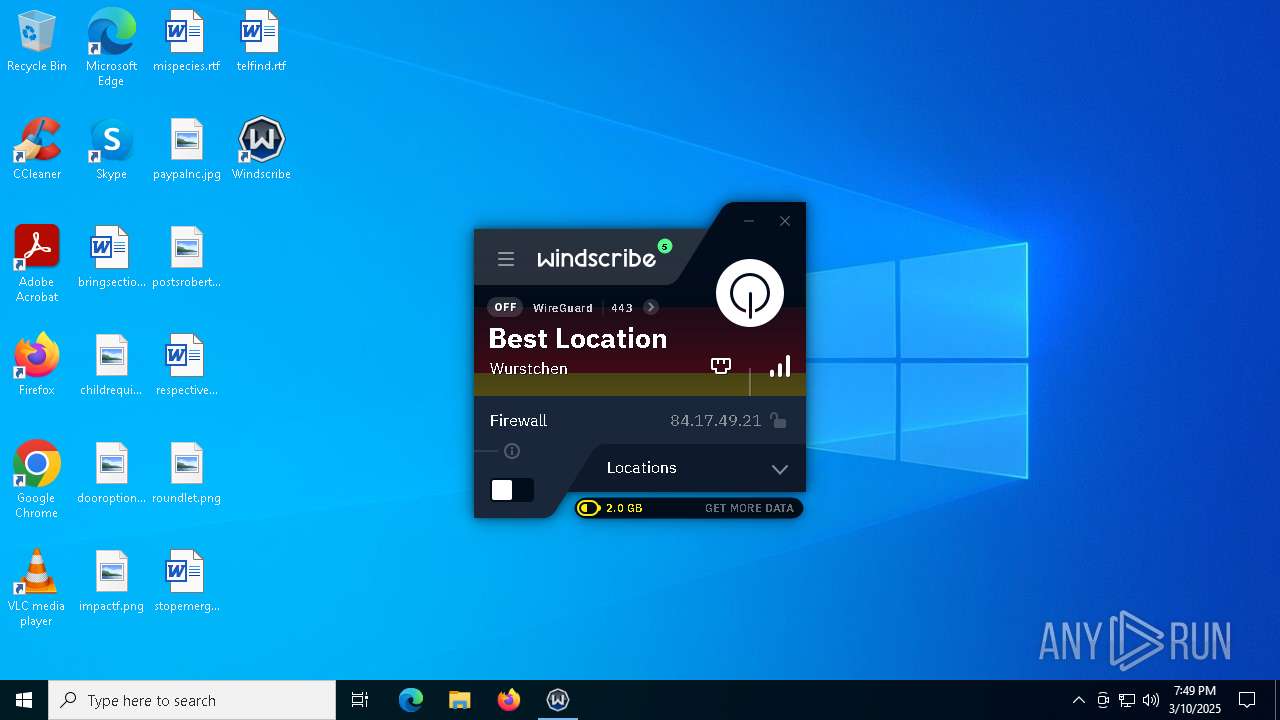
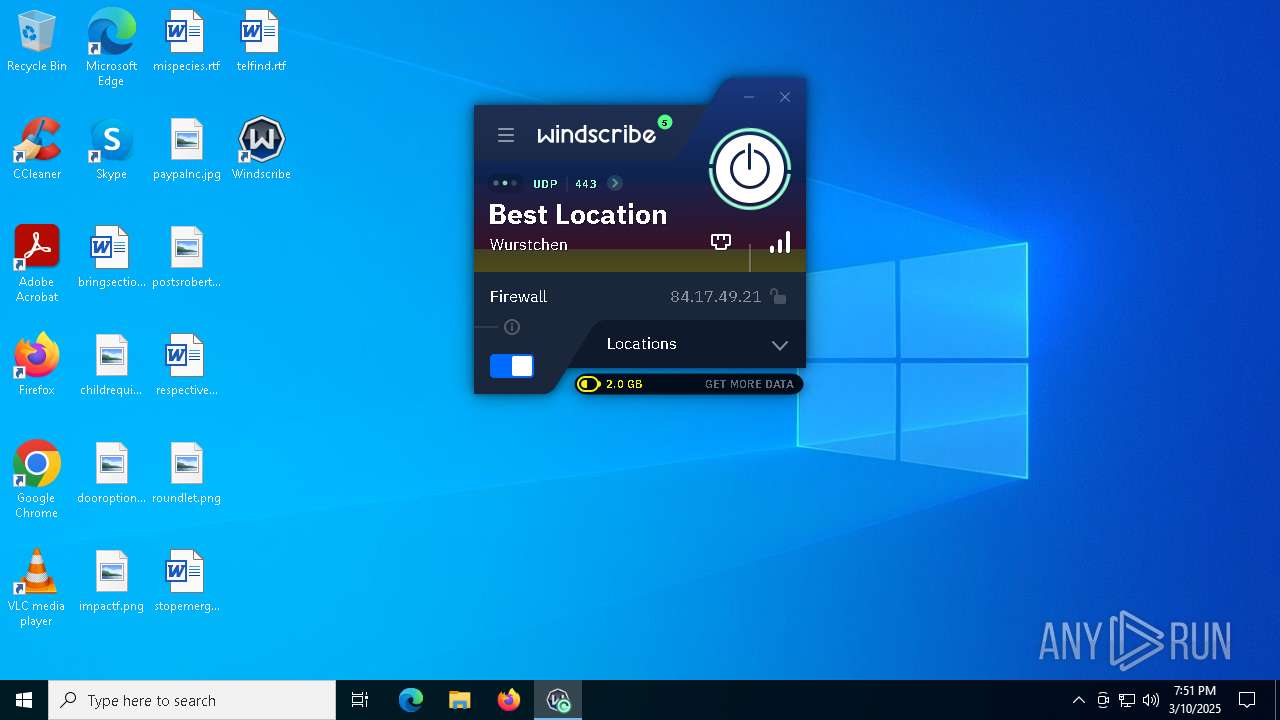
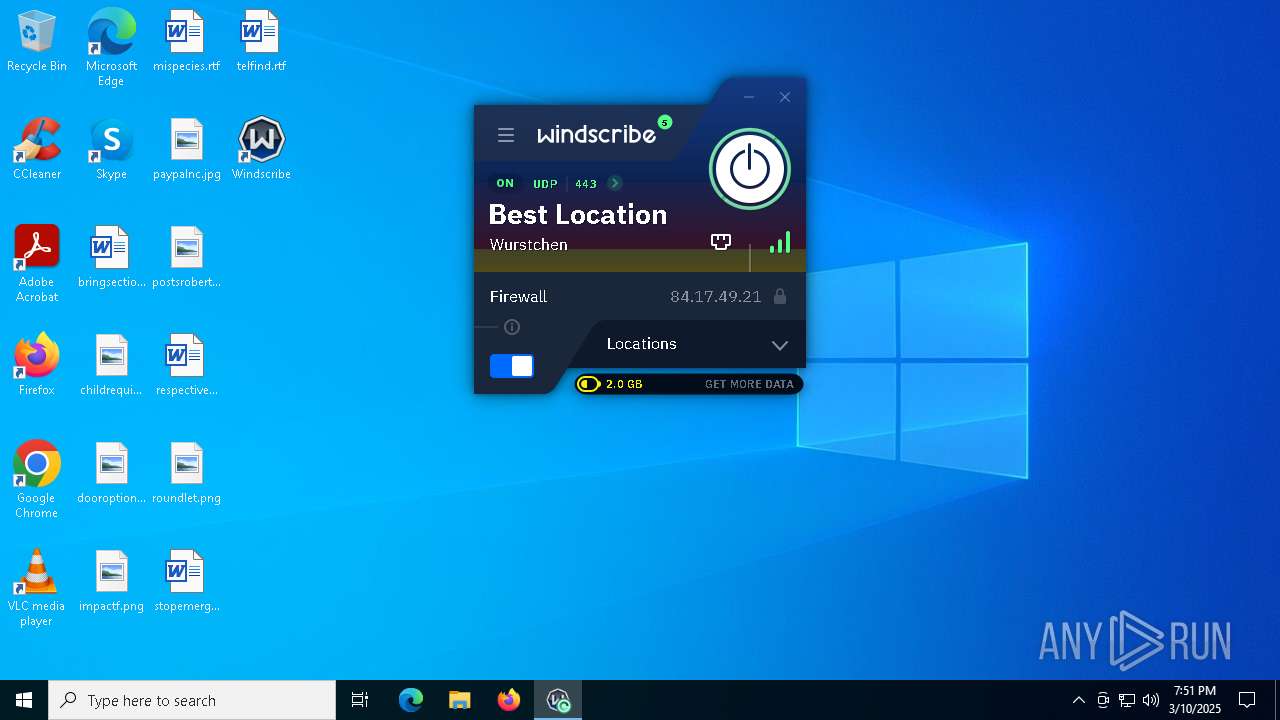
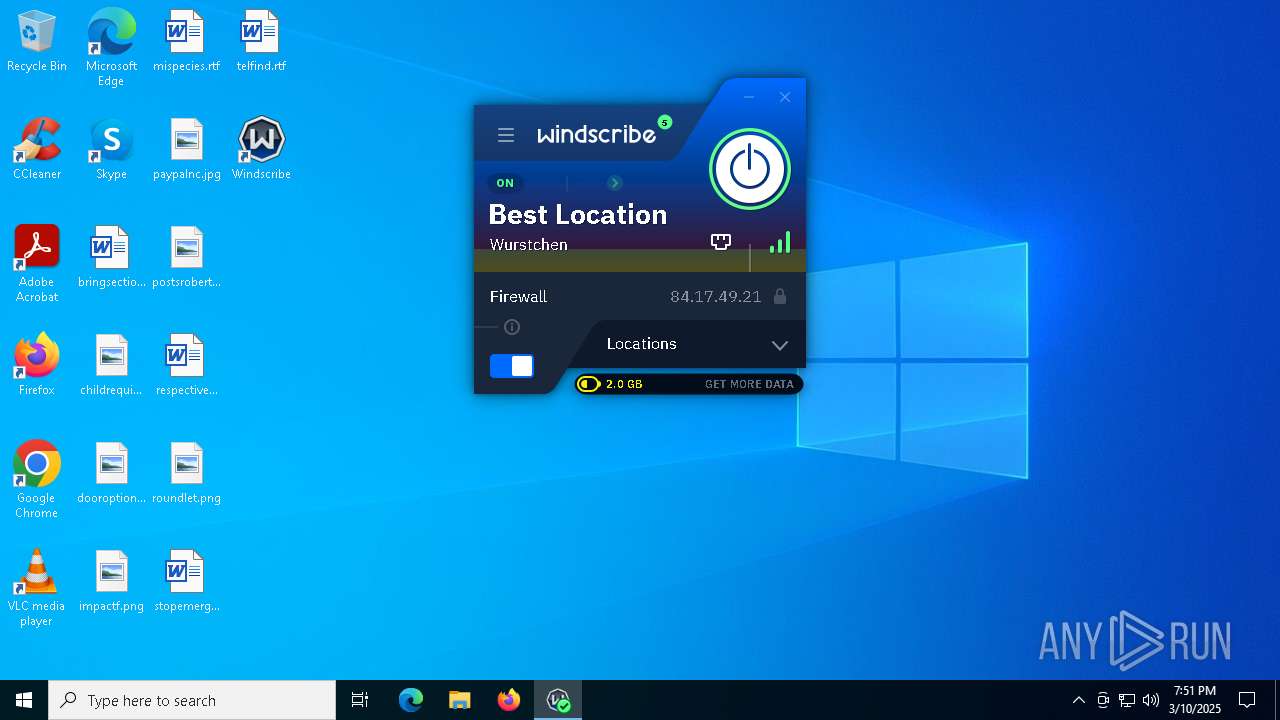
| URL: | https://windscribe.com/install/desktop/windows |
| Full analysis: | https://app.any.run/tasks/e4d0409e-7590-4eff-8e9b-9aeb85eb7375 |
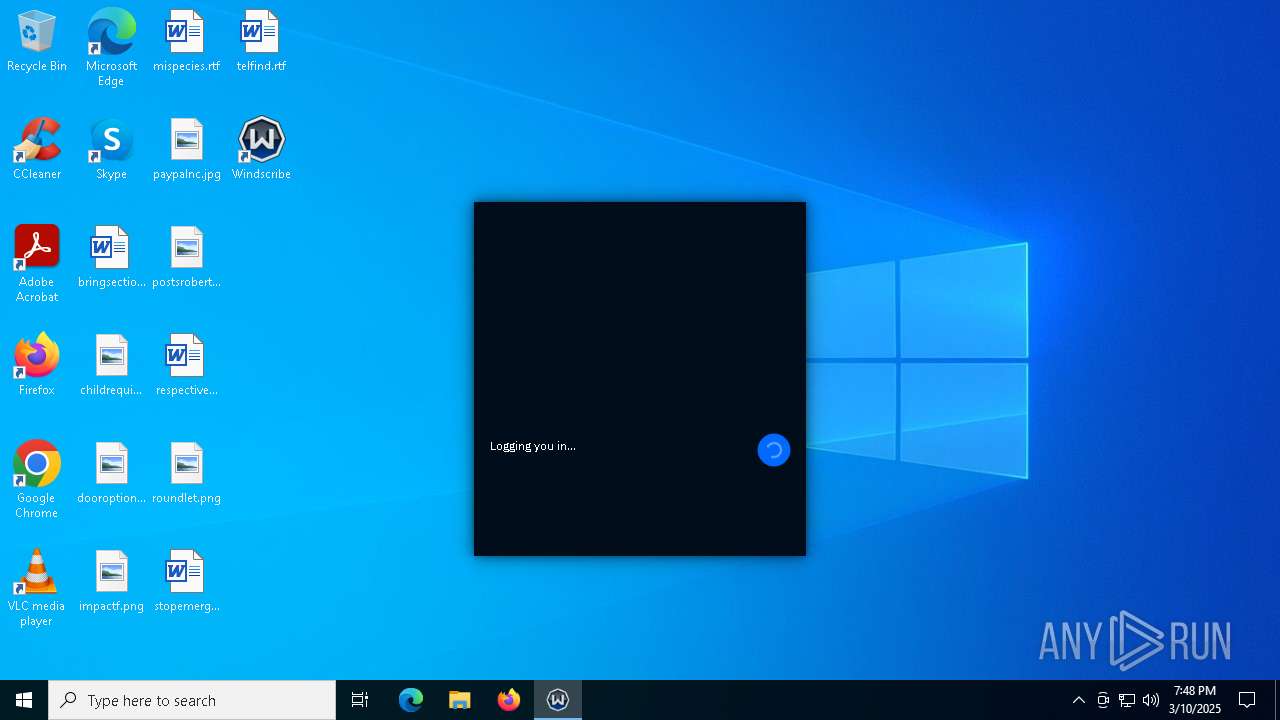
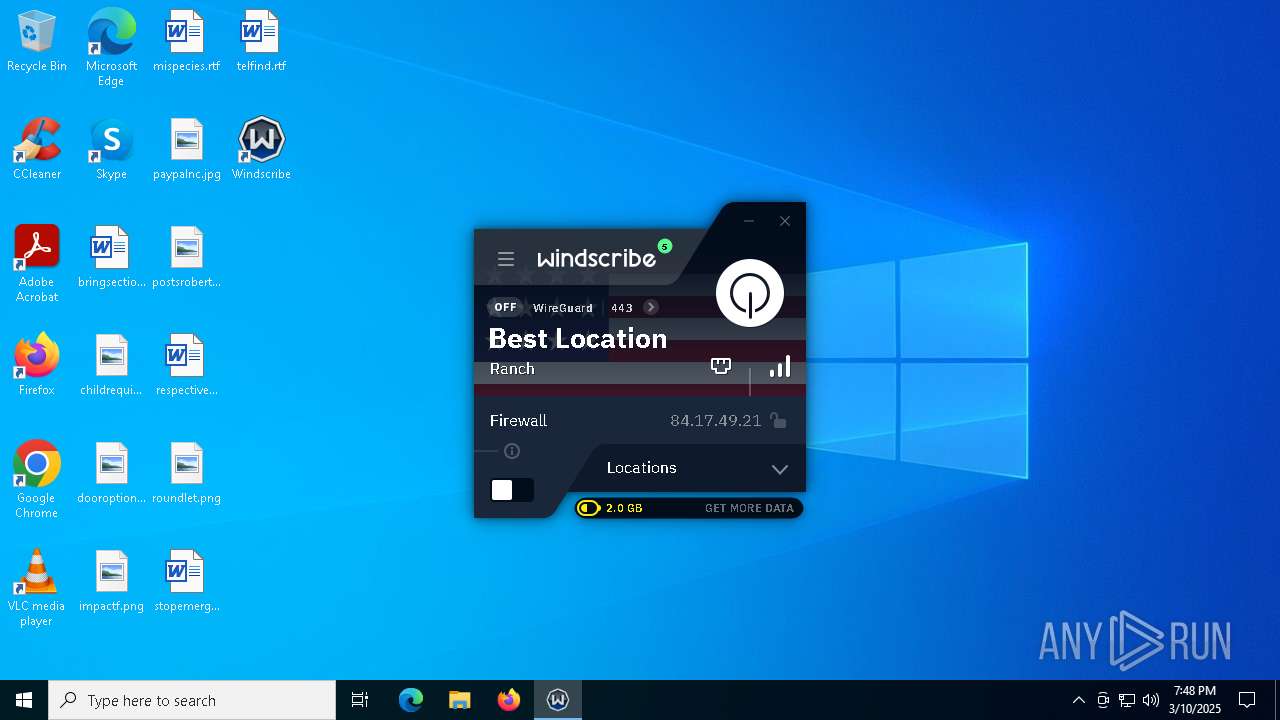
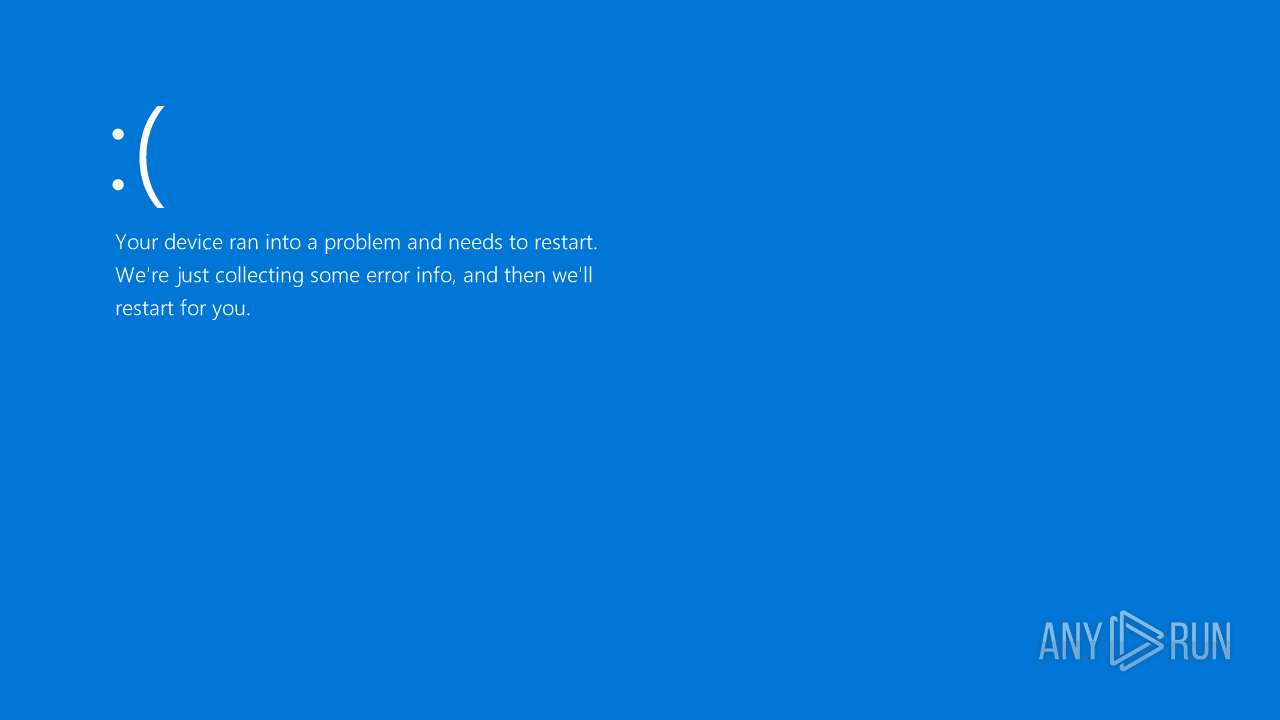
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2025, 19:48:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 45308E7CA50B6F538B29F84229DF5BB0 |
| SHA1: | 0A810AE9E169A2141351E9AD955E651A4857B334 |
| SHA256: | 44DBA4A9E38331B97AB41B65E4A1B2909D939A99148E3844080CB5623BA0A5C7 |
| SSDEEP: | 3:N8dnMBKMygEIRKVKSMm:2oygEsOx |
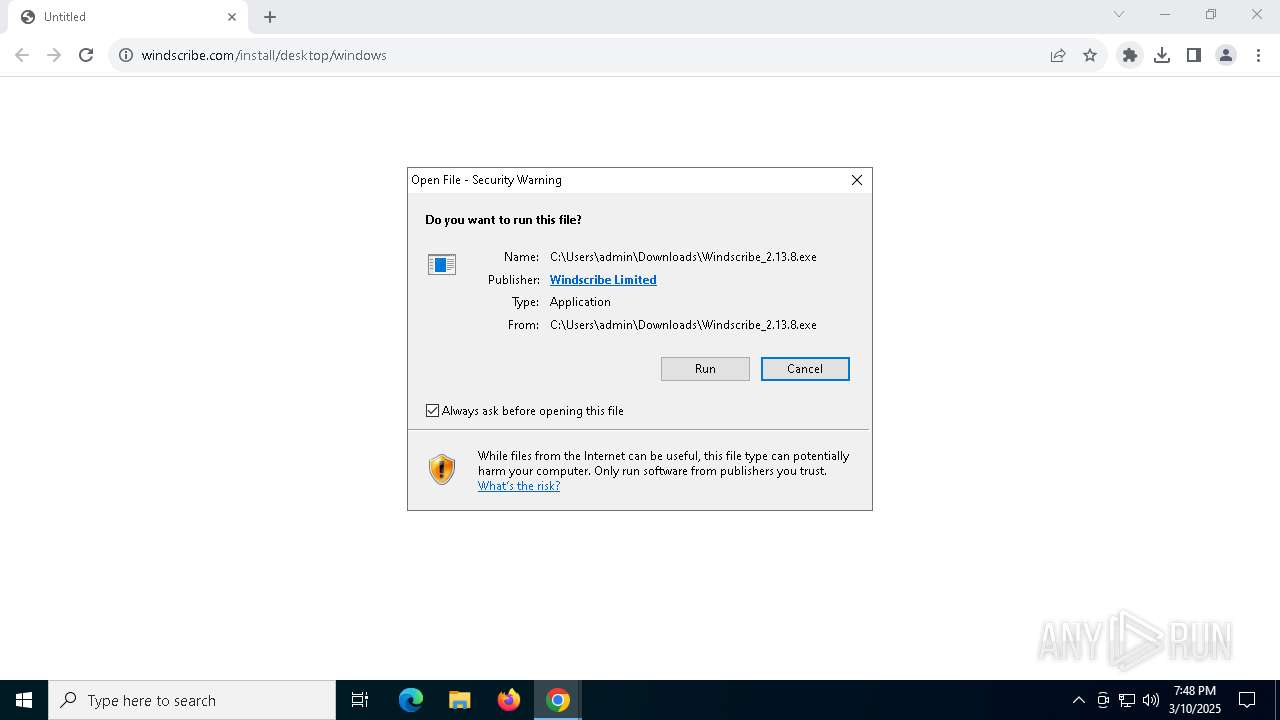
MALICIOUS
Executing a file with an untrusted certificate
- Windscribe_2.13.8.exe (PID: 6964)
- Windscribe_2.13.8.exe (PID: 4896)
- 7zr.exe (PID: 4488)
- Windscribe_2.13.8.exe (PID: 4696)
- WindscribeService.exe (PID: 5544)
- 7zr.exe (PID: 6512)
- Windscribe.exe (PID: 1676)
- devcon.exe (PID: 7380)
- tapctl.exe (PID: 5204)
- windscribeopenvpn.exe (PID: 7576)
- Windscribe.exe (PID: 6100)
SUSPICIOUS
Reads security settings of Internet Explorer
- Windscribe_2.13.8.exe (PID: 6964)
- Windscribe_2.13.8.exe (PID: 4896)
Cleans NTFS data stream (Zone Identifier)
- chrome.exe (PID: 7300)
Reads the date of Windows installation
- Windscribe_2.13.8.exe (PID: 6964)
- Windscribe_2.13.8.exe (PID: 4896)
Application launched itself
- Windscribe_2.13.8.exe (PID: 6964)
Executable content was dropped or overwritten
- Windscribe_2.13.8.exe (PID: 4896)
- 7zr.exe (PID: 4488)
- 7zr.exe (PID: 6512)
- Windscribe_2.13.8.exe (PID: 4696)
- devcon.exe (PID: 7380)
- drvinst.exe (PID: 7148)
- drvinst.exe (PID: 8012)
Drops 7-zip archiver for unpacking
- Windscribe_2.13.8.exe (PID: 4896)
Process drops legitimate windows executable
- 7zr.exe (PID: 4488)
- 7zr.exe (PID: 6512)
- Windscribe_2.13.8.exe (PID: 4696)
The process drops C-runtime libraries
- 7zr.exe (PID: 4488)
- Windscribe_2.13.8.exe (PID: 4696)
- 7zr.exe (PID: 6512)
Drops a system driver (possible attempt to evade defenses)
- 7zr.exe (PID: 6512)
- devcon.exe (PID: 7380)
- drvinst.exe (PID: 7148)
- Windscribe_2.13.8.exe (PID: 4696)
- drvinst.exe (PID: 8012)
Executes as Windows Service
- WindscribeService.exe (PID: 5544)
Uses TASKKILL.EXE to kill process
- Windscribe_2.13.8.exe (PID: 4696)
- WindscribeService.exe (PID: 5544)
Searches for installed software
- Windscribe_2.13.8.exe (PID: 4696)
Creates files in the driver directory
- Windscribe_2.13.8.exe (PID: 4696)
- drvinst.exe (PID: 7148)
Creates/Modifies COM task schedule object
- Windscribe_2.13.8.exe (PID: 4696)
Creates a software uninstall entry
- Windscribe_2.13.8.exe (PID: 4696)
There is functionality for taking screenshot (YARA)
- Windscribe.exe (PID: 1676)
Suspicious use of NETSH.EXE
- tapctl.exe (PID: 5204)
- windscribeopenvpn.exe (PID: 7576)
- WindscribeService.exe (PID: 5544)
The process checks if it is being run in the virtual environment
- Windscribe.exe (PID: 1676)
Uses ROUTE.EXE to obtain the routing table information
- Windscribe.exe (PID: 6100)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 3980)
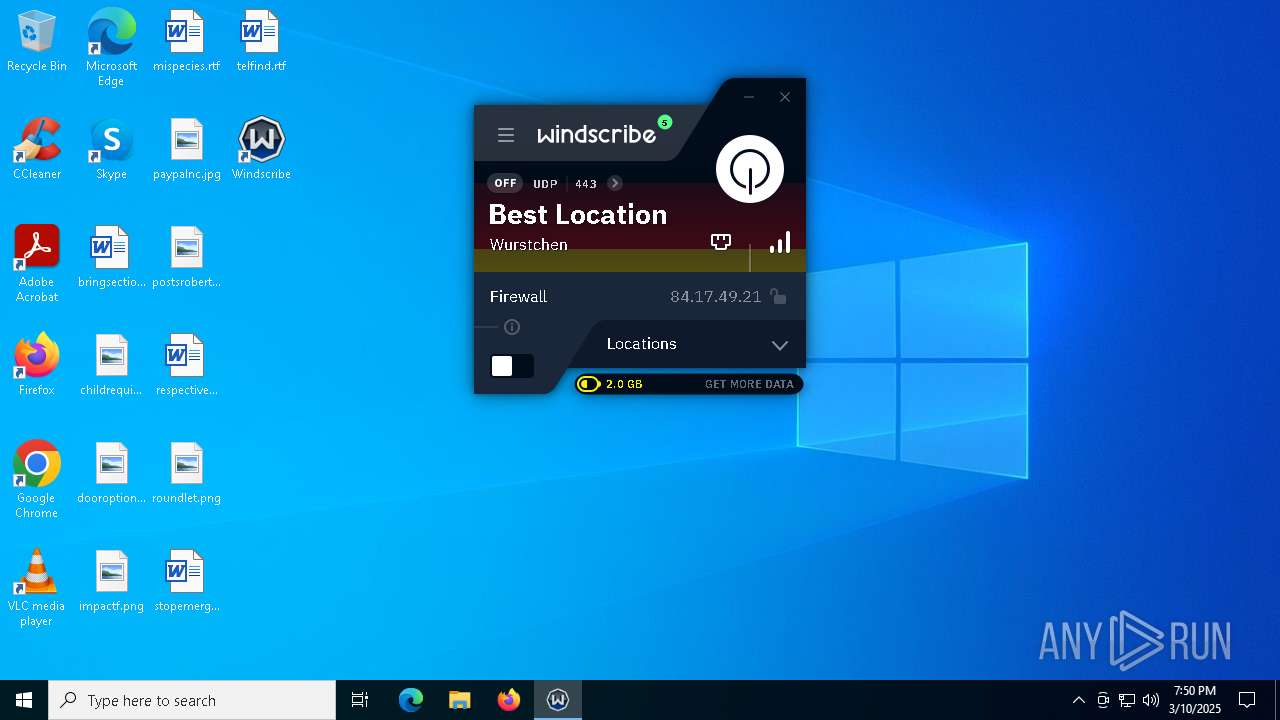
Connects to unusual port
- Windscribe.exe (PID: 6100)
- Windscribe.exe (PID: 1676)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 7300)
Checks supported languages
- Windscribe_2.13.8.exe (PID: 6964)
- Windscribe_2.13.8.exe (PID: 4696)
- 7zr.exe (PID: 4488)
- Windscribe_2.13.8.exe (PID: 4896)
- WindscribeService.exe (PID: 5544)
- devcon.exe (PID: 7380)
- drvinst.exe (PID: 7148)
- Windscribe.exe (PID: 1676)
Application launched itself
- chrome.exe (PID: 7300)
- msedge.exe (PID: 8064)
- msedge.exe (PID: 5036)
The sample compiled with english language support
- chrome.exe (PID: 7300)
- Windscribe_2.13.8.exe (PID: 4896)
- 7zr.exe (PID: 4488)
- 7zr.exe (PID: 6512)
- Windscribe_2.13.8.exe (PID: 4696)
- drvinst.exe (PID: 7148)
- devcon.exe (PID: 7380)
- drvinst.exe (PID: 8012)
Process checks computer location settings
- Windscribe_2.13.8.exe (PID: 6964)
- Windscribe_2.13.8.exe (PID: 4896)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7272)
- BackgroundTransferHost.exe (PID: 5376)
- BackgroundTransferHost.exe (PID: 6392)
- BackgroundTransferHost.exe (PID: 208)
- BackgroundTransferHost.exe (PID: 5048)
Reads the computer name
- Windscribe_2.13.8.exe (PID: 6964)
- Windscribe_2.13.8.exe (PID: 4696)
- Windscribe_2.13.8.exe (PID: 4896)
- 7zr.exe (PID: 4488)
- drvinst.exe (PID: 7148)
- WindscribeService.exe (PID: 5544)
- Windscribe.exe (PID: 1676)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5376)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5376)
- WindscribeService.exe (PID: 5544)
- Windscribe.exe (PID: 1676)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5376)
- Windscribe.exe (PID: 1676)
Creates files in the program directory
- 7zr.exe (PID: 6512)
- Windscribe_2.13.8.exe (PID: 4696)
- WindscribeService.exe (PID: 5544)
Create files in a temporary directory
- devcon.exe (PID: 7380)
Reads the machine GUID from the registry
- drvinst.exe (PID: 7148)
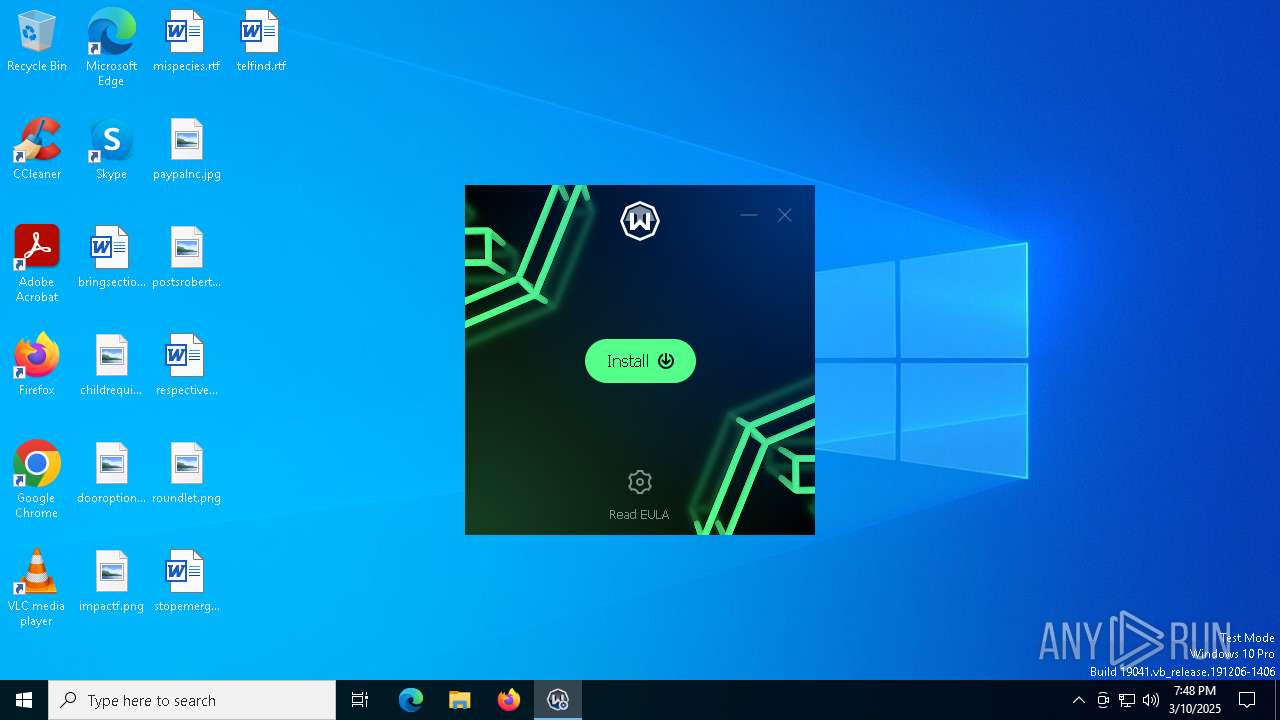
Manual execution by a user
- Windscribe.exe (PID: 1676)
- Windscribe.exe (PID: 6100)
Disables trace logs
- Windscribe.exe (PID: 1676)
Prints a route via ROUTE.EXE
- ROUTE.EXE (PID: 4468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
406
Monitored processes
122
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4804 --field-trial-handle=1936,i,1780235347149246386,4635483584691267976,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 900 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=NetworkAvailable | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2520 --field-trial-handle=2336,i,9030400742179662146,5543707637006169130,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 928 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5248 --field-trial-handle=2336,i,9030400742179662146,5543707637006169130,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5376 --field-trial-handle=2336,i,9030400742179662146,5543707637006169130,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2716 --field-trial-handle=2336,i,9030400742179662146,5543707637006169130,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | windscribeopenvpn.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7zr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5500 --field-trial-handle=2336,i,9030400742179662146,5543707637006169130,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
36 865
Read events
36 673
Write events
175
Delete events
17
Modification events
| (PID) Process: | (7300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7300) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7300) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5056) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000700F3E61F591DB01 | |||
| (PID) Process: | (7272) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7272) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7272) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5376) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
145
Suspicious files
512
Text files
109
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c073.TMP | — | |
MD5:— | SHA256:— | |||
| 7300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c083.TMP | — | |
MD5:— | SHA256:— | |||
| 7300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c083.TMP | — | |
MD5:— | SHA256:— | |||
| 7300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c083.TMP | — | |
MD5:— | SHA256:— | |||
| 7300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c093.TMP | — | |
MD5:— | SHA256:— | |||
| 7300 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
321
TCP/UDP connections
483
DNS requests
90
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7300 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | DE | binary | 727 b | whitelisted |
7300 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | DE | binary | 471 b | whitelisted |
7300 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA5kzqbbIJqWv8QbTCfUCNk%3D | DE | binary | 727 b | whitelisted |
5376 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 312 b | whitelisted |
3896 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | CL | binary | 419 b | whitelisted |
3896 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | CL | binary | 408 b | whitelisted |
1676 | Windscribe.exe | GET | 200 | 185.253.96.2:6464 | http://nl-008.whiskergalaxy.com:6464/latency | NL | binary | 16 b | unknown |
1676 | Windscribe.exe | GET | 200 | 185.246.210.1:6464 | http://cz-002.whiskergalaxy.com:6464/latency | CZ | binary | 16 b | unknown |
1676 | Windscribe.exe | GET | 200 | 84.17.46.1:6464 | http://nl-011.whiskergalaxy.com:6464/latency | NL | binary | 16 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7300 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7628 | chrome.exe | 104.20.1.154:443 | windscribe.com | CLOUDFLARENET | — | unknown |
7628 | chrome.exe | 74.125.143.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7628 | chrome.exe | 104.24.30.5:443 | deploy.totallyacdn.com | CLOUDFLARENET | US | unknown |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
windscribe.com |
| unknown |
accounts.google.com |
| whitelisted |
deploy.totallyacdn.com |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |