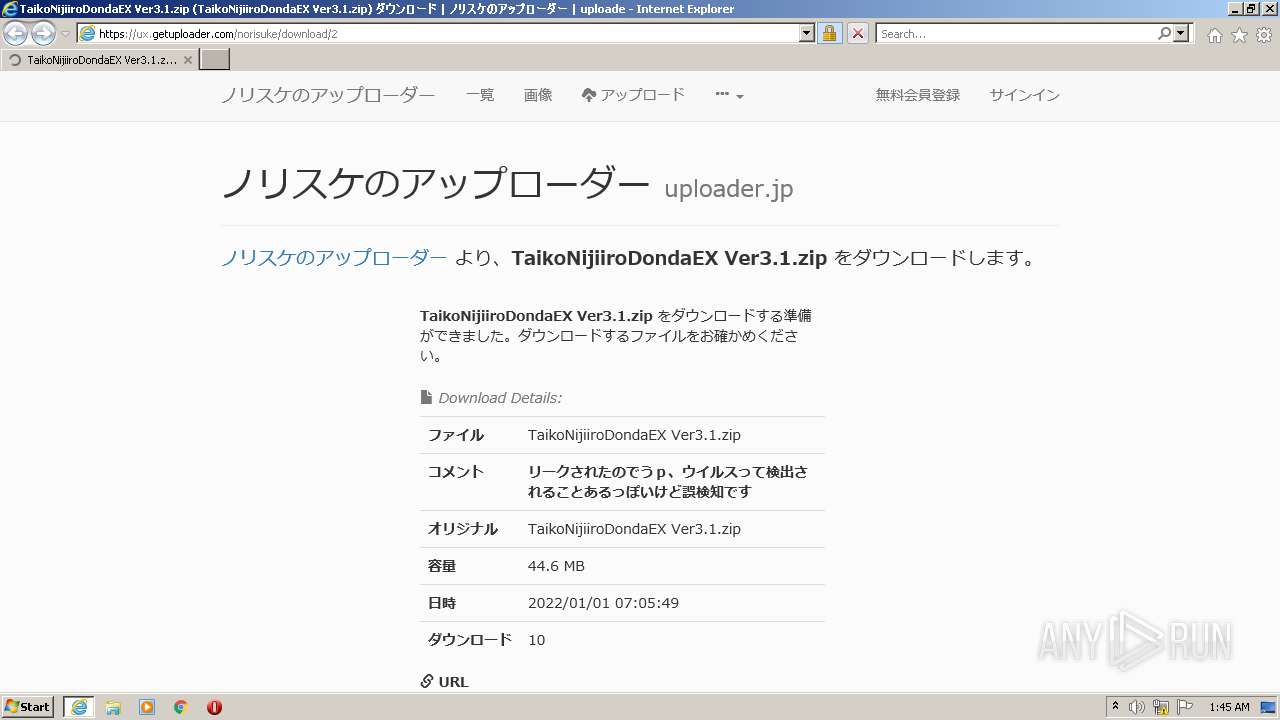
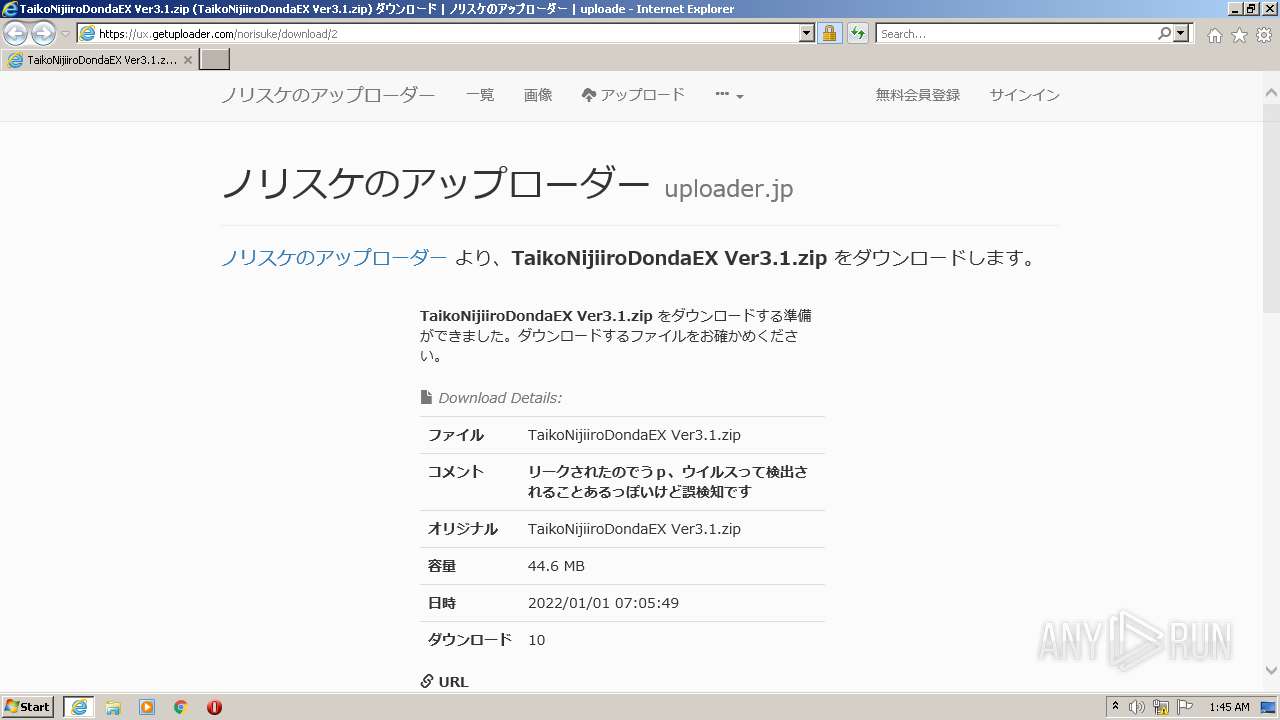
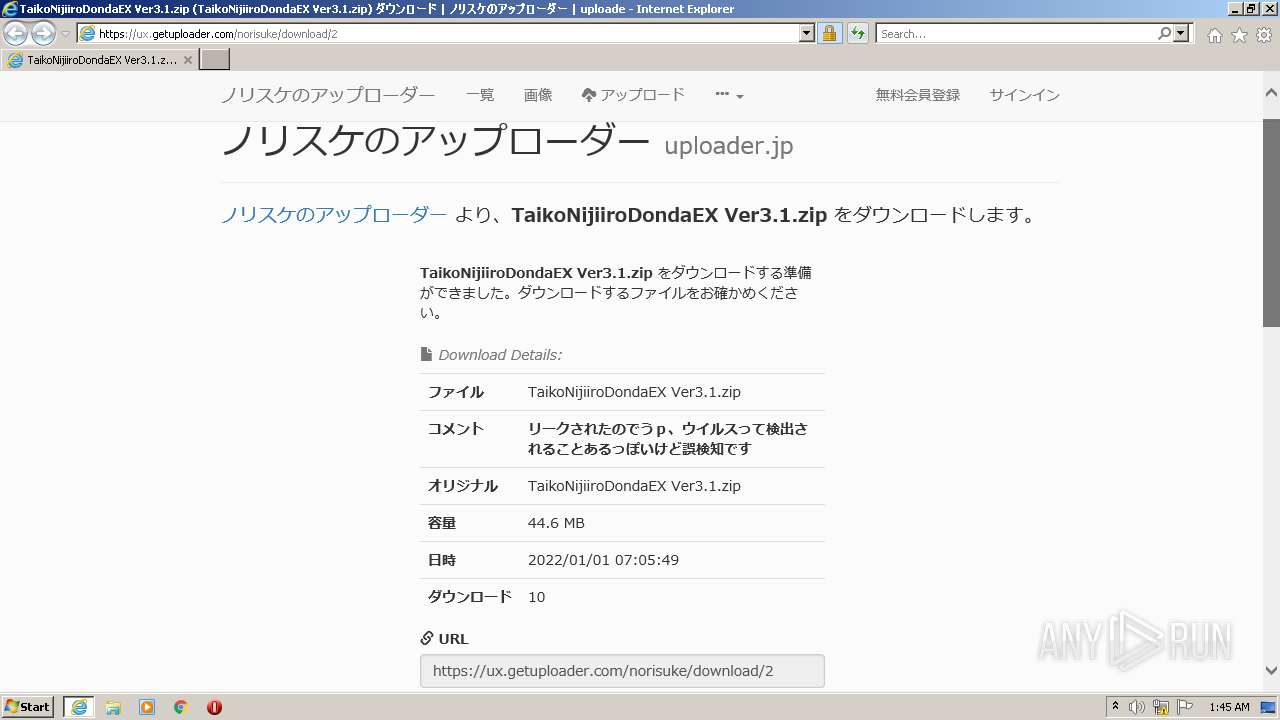
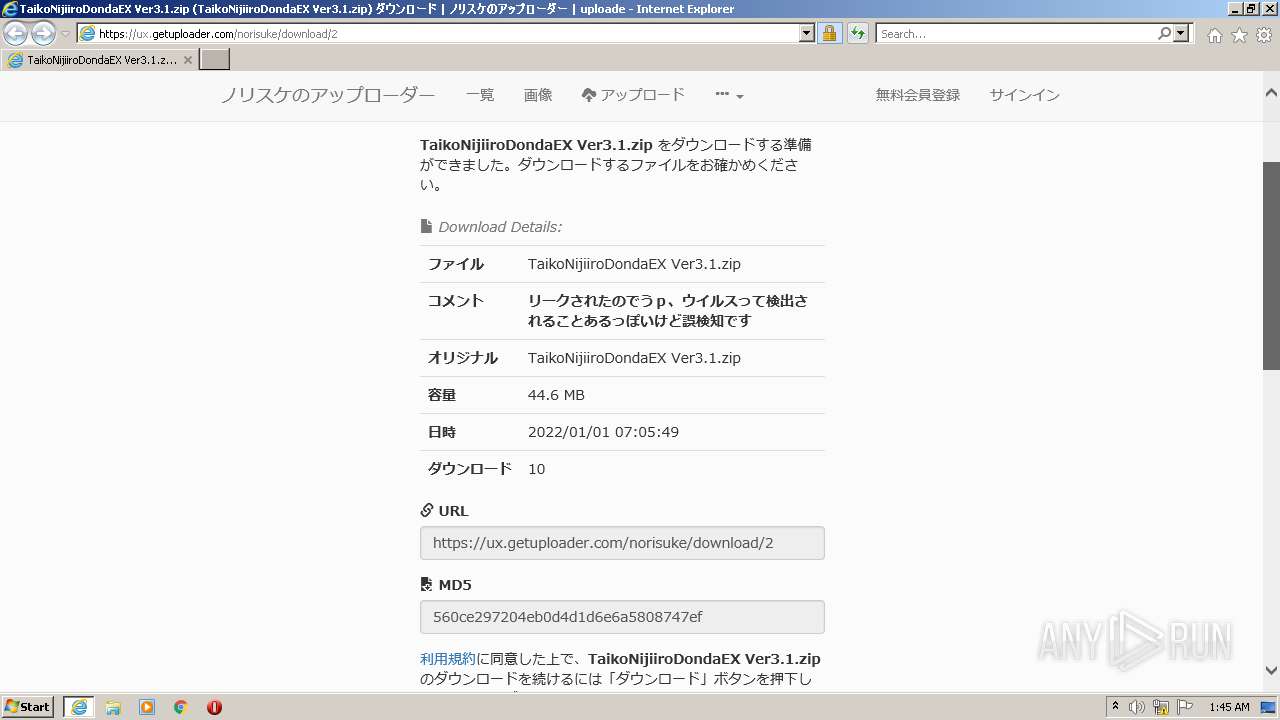
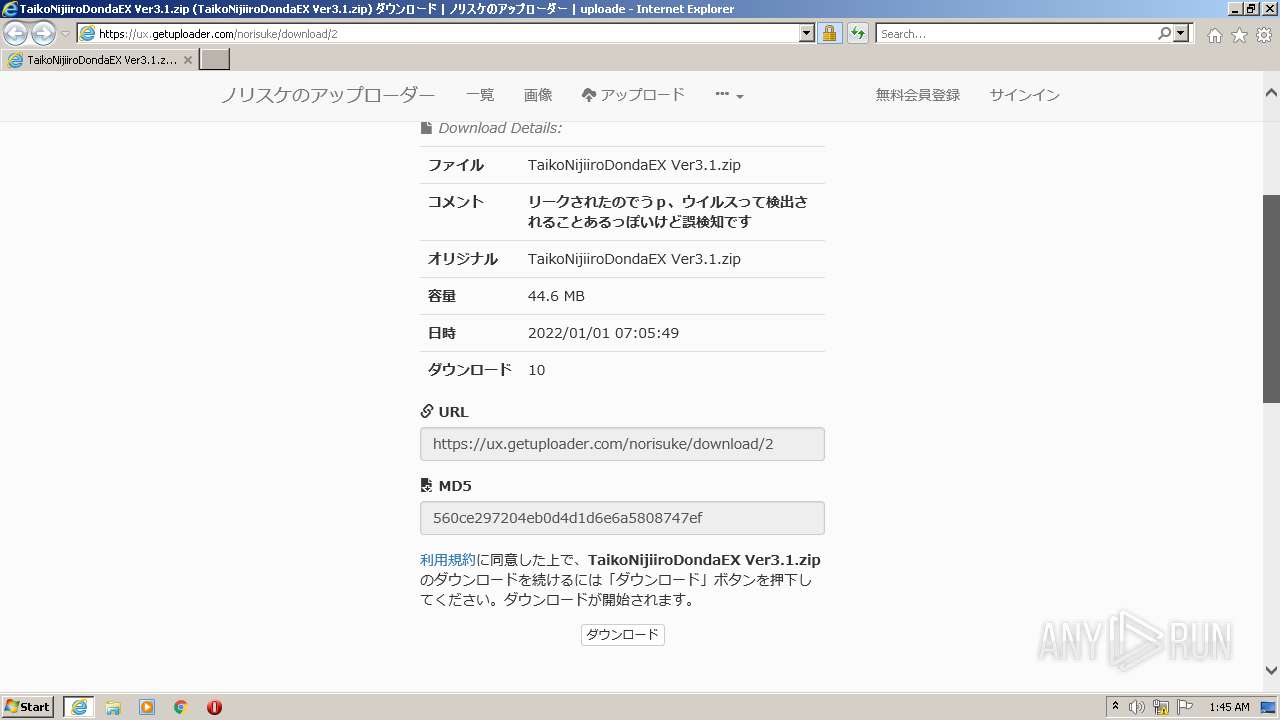
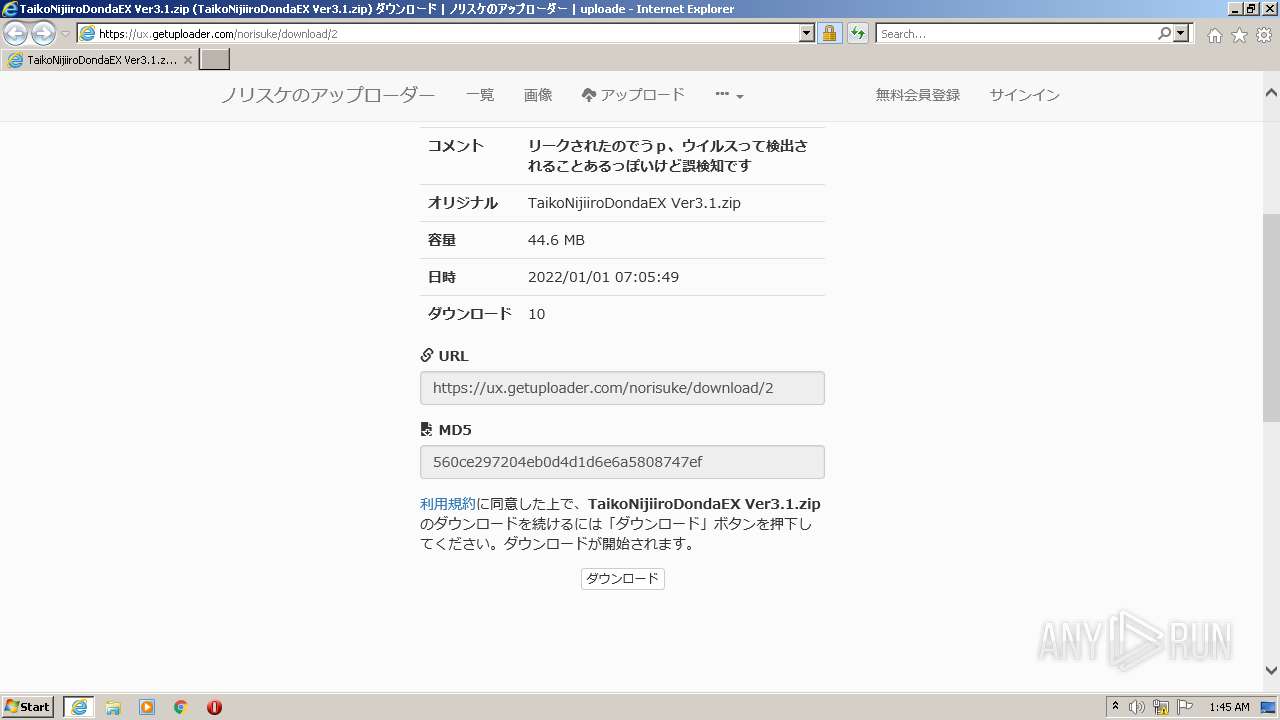
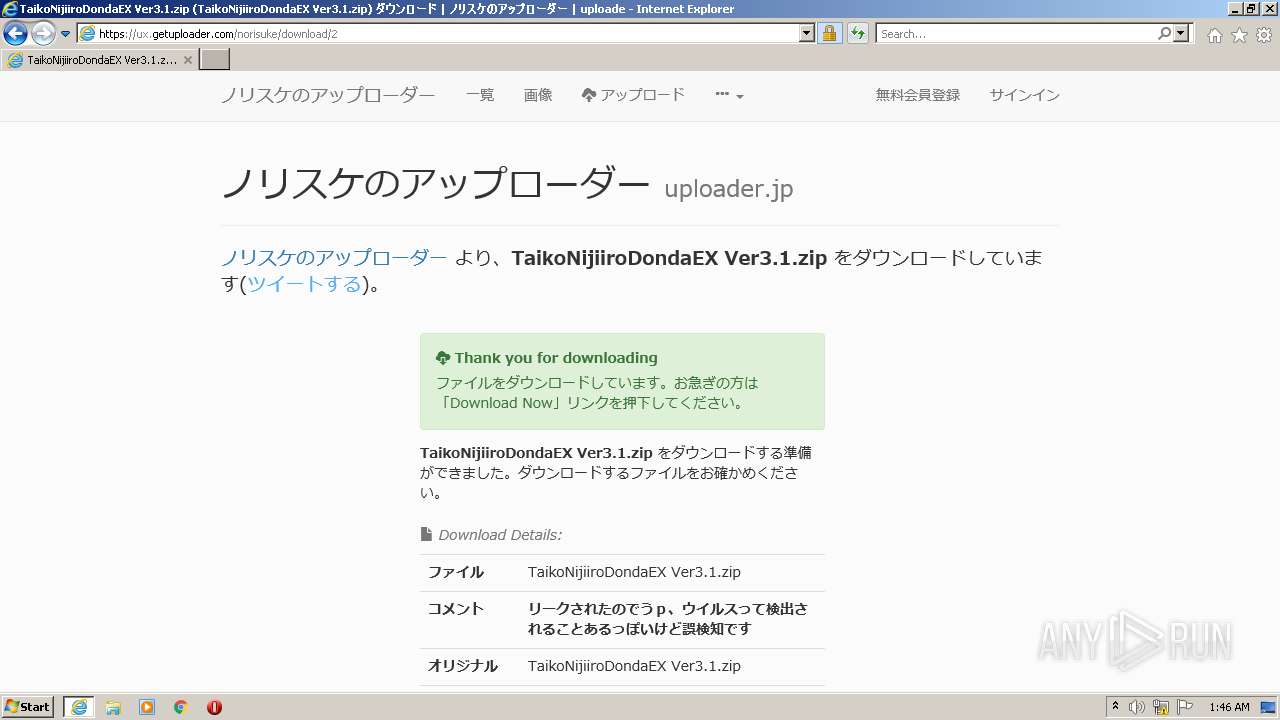
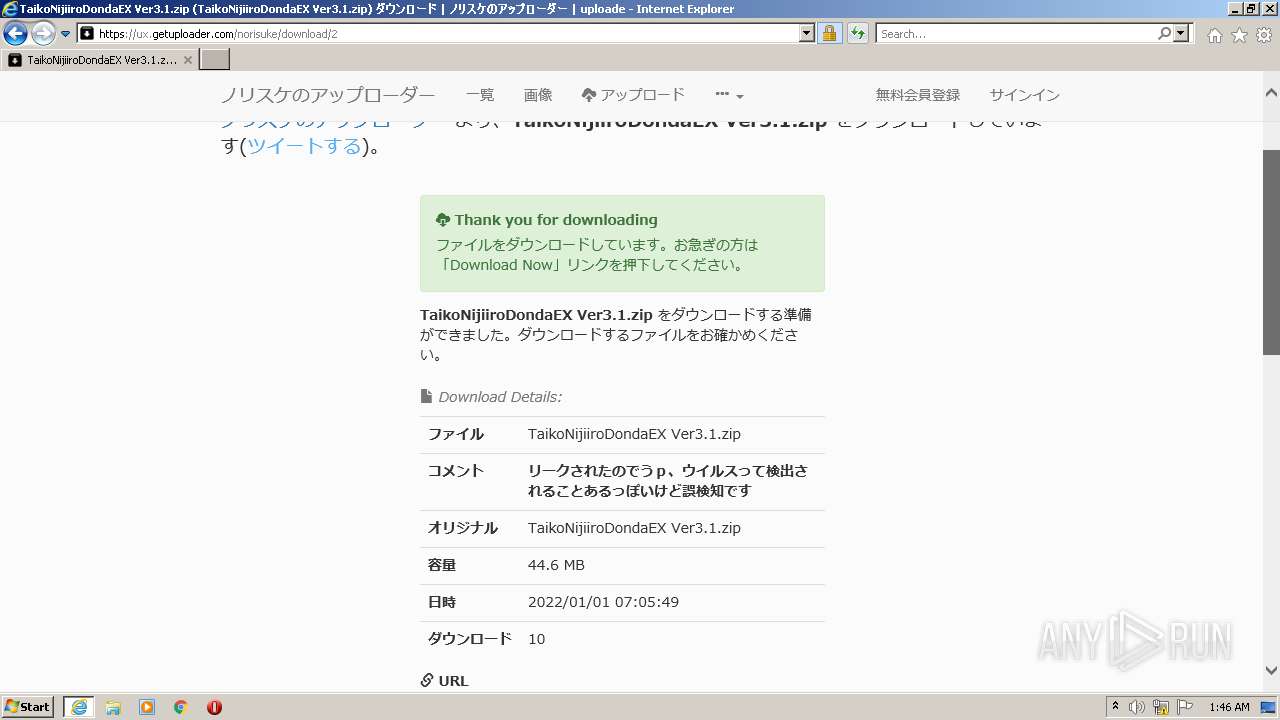
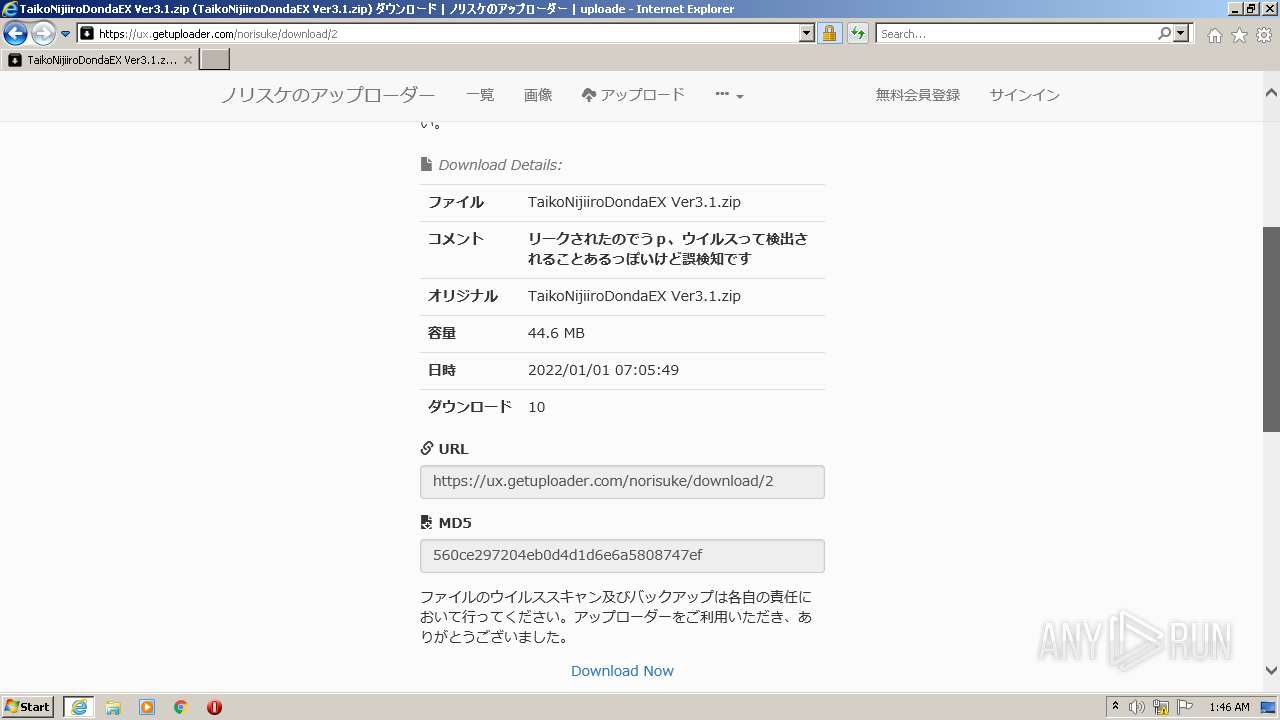
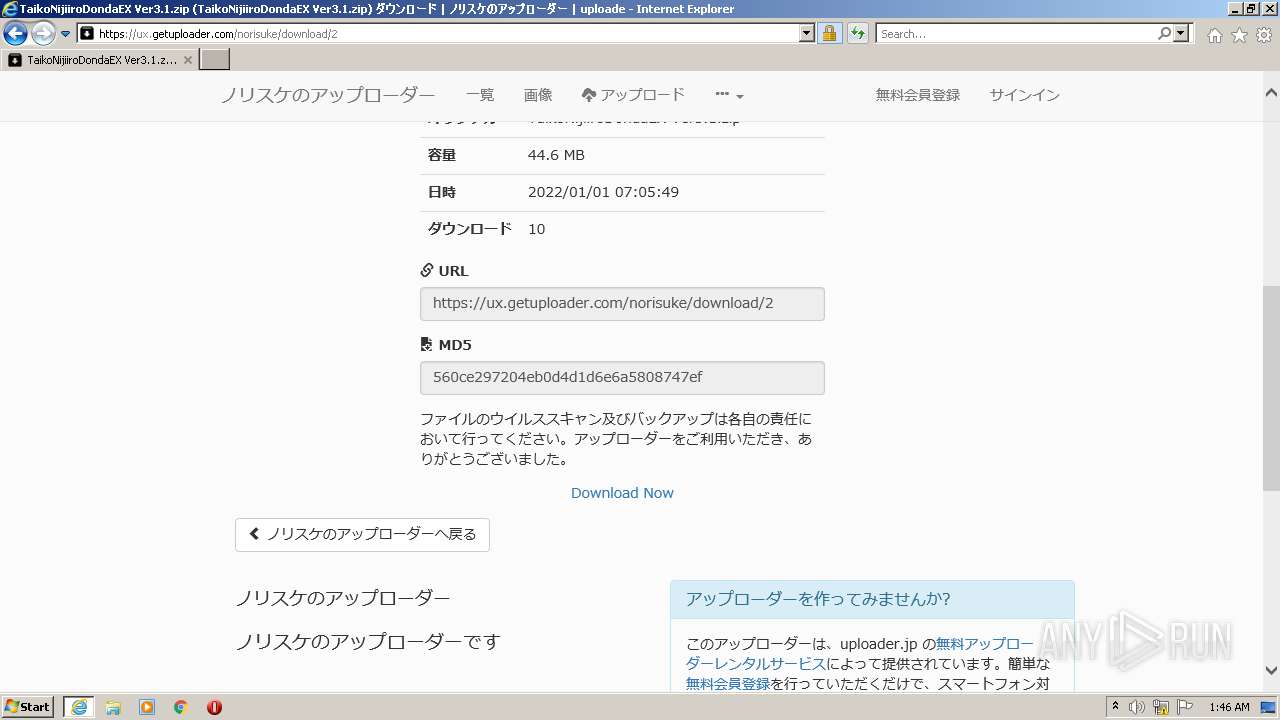
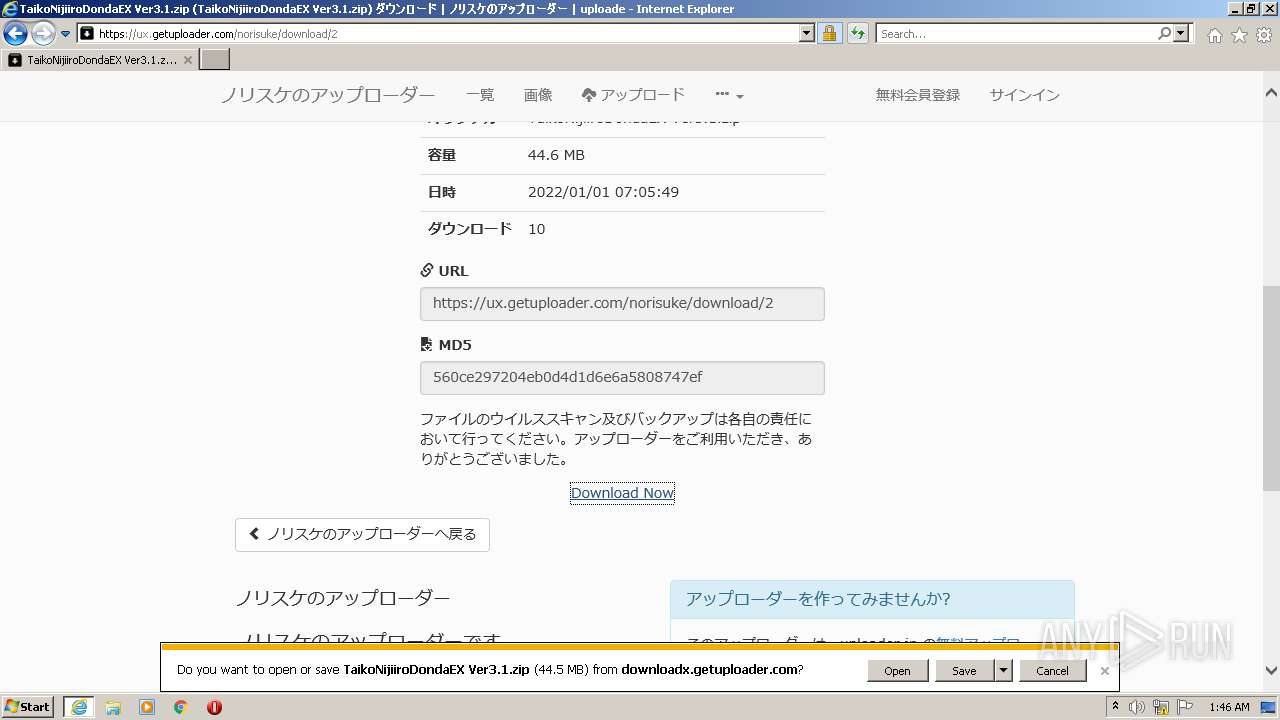
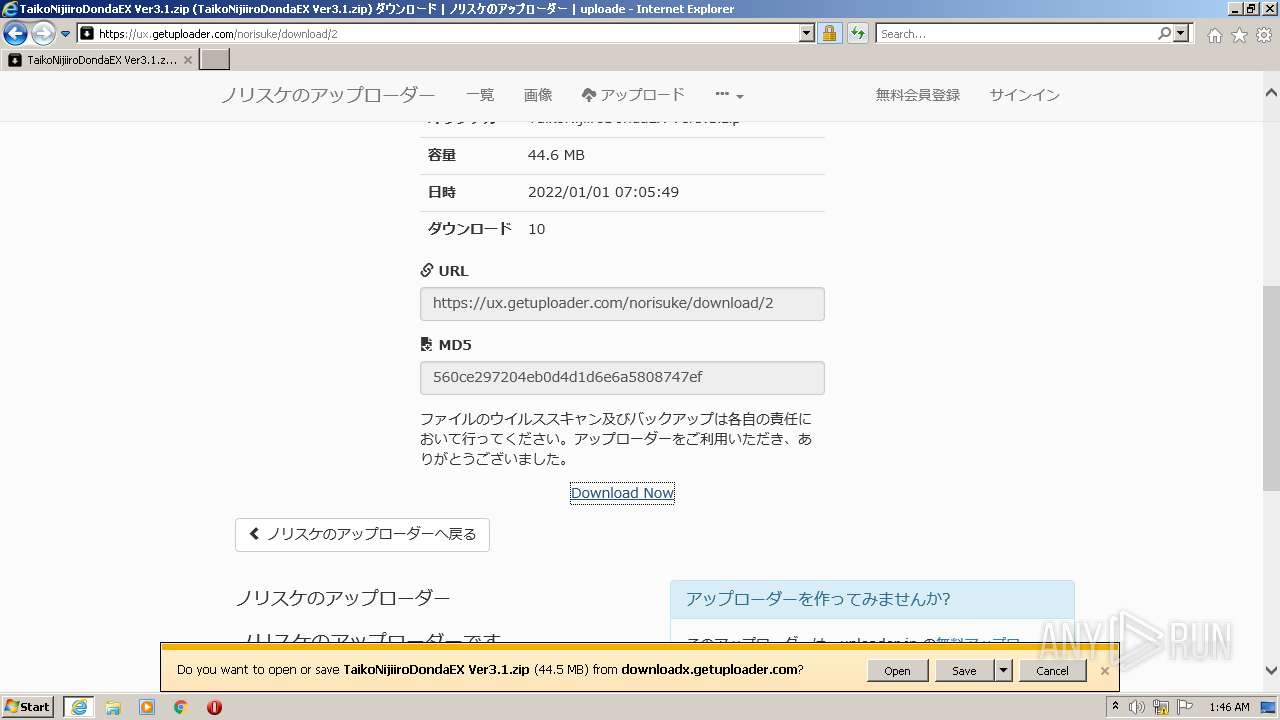
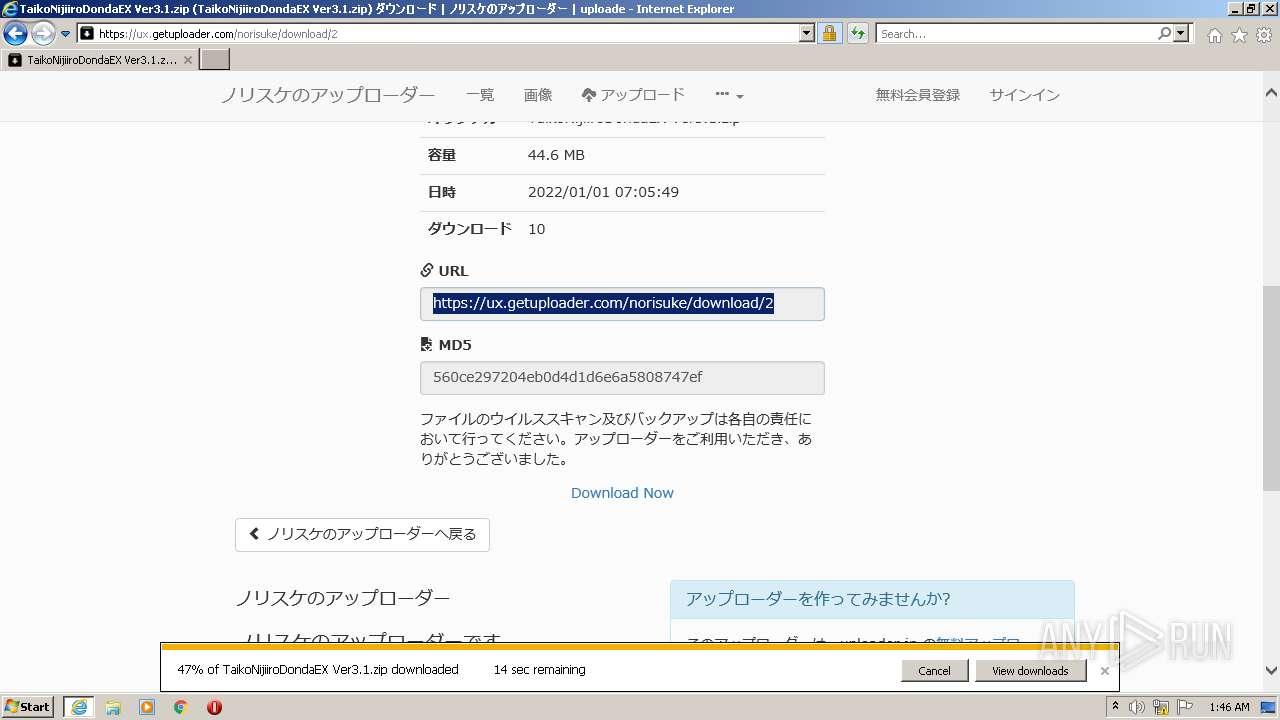
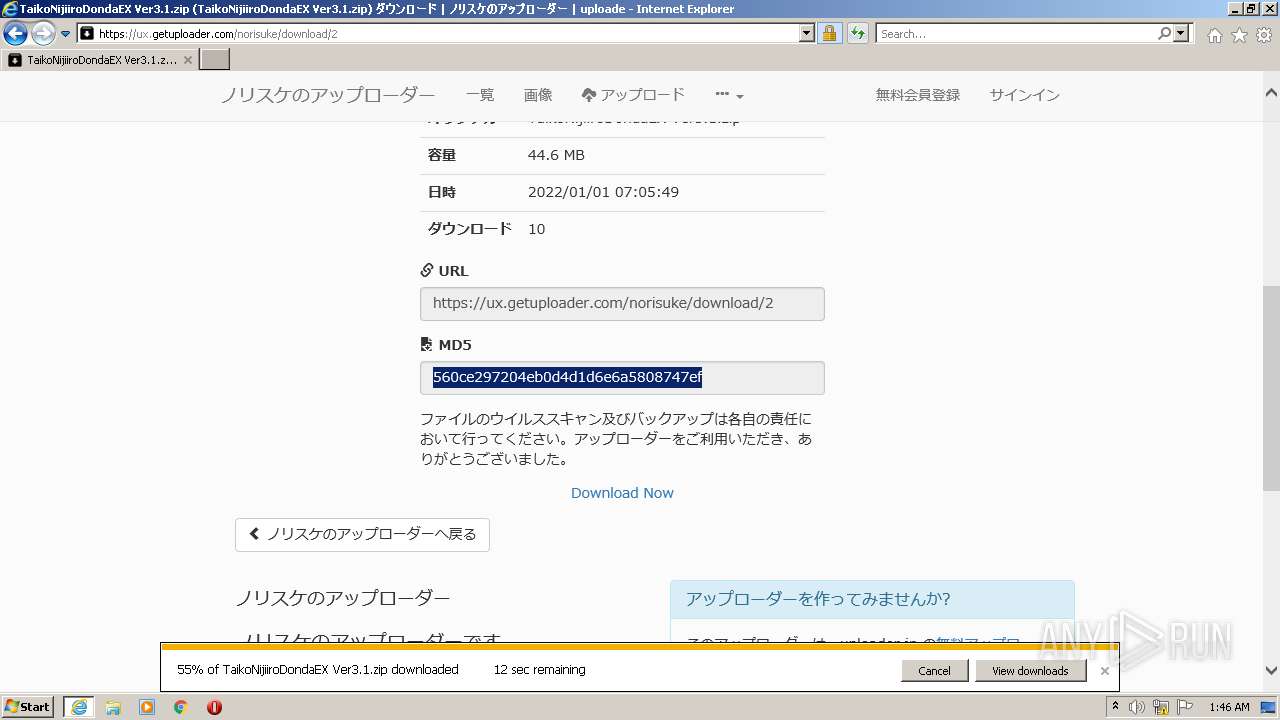
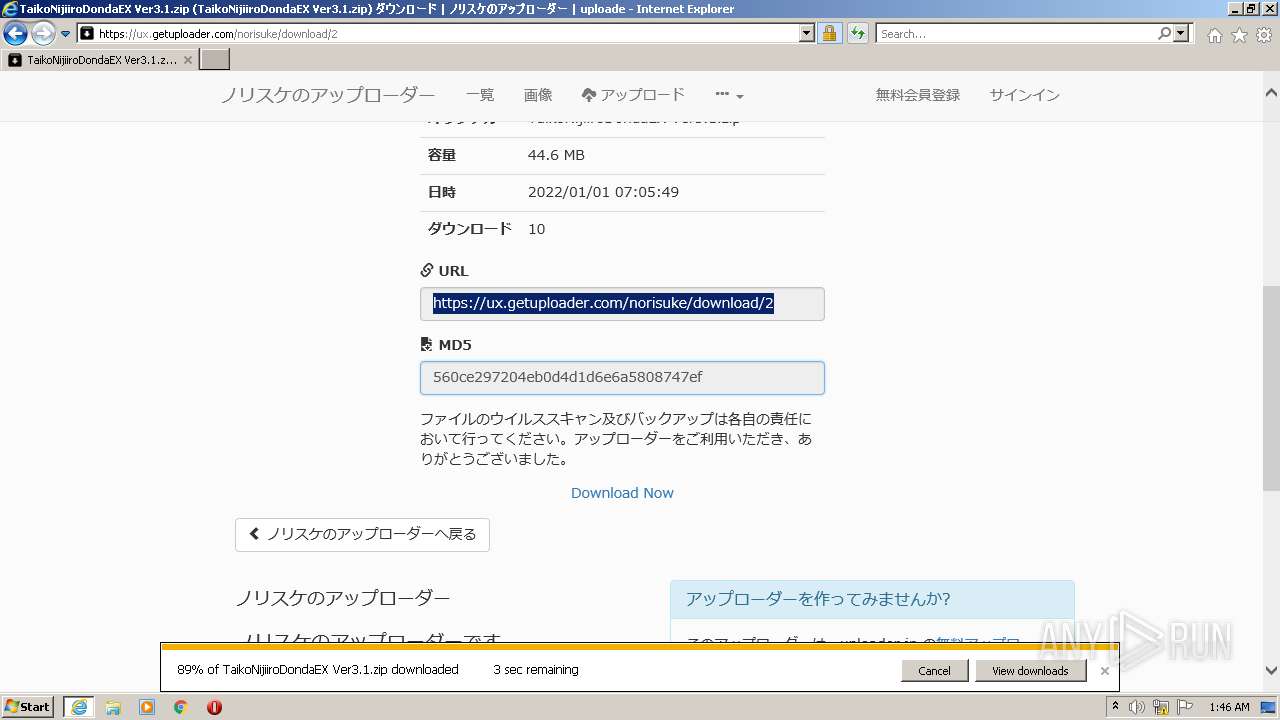
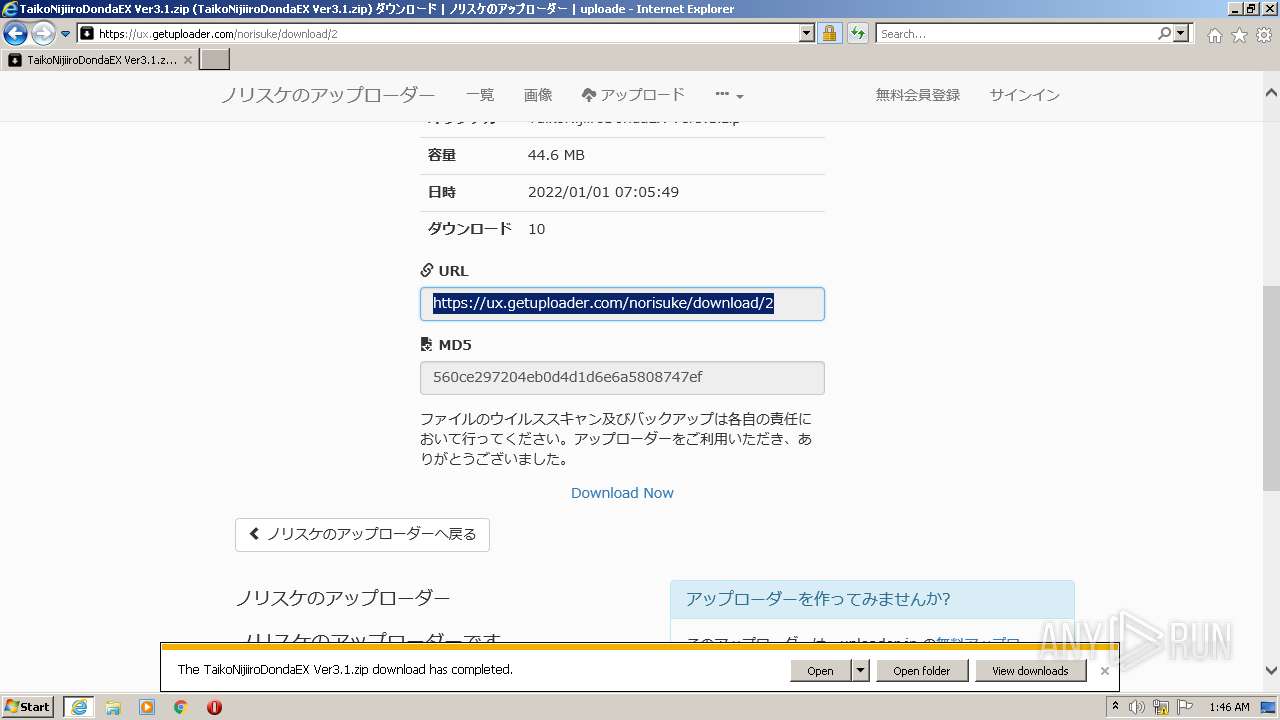
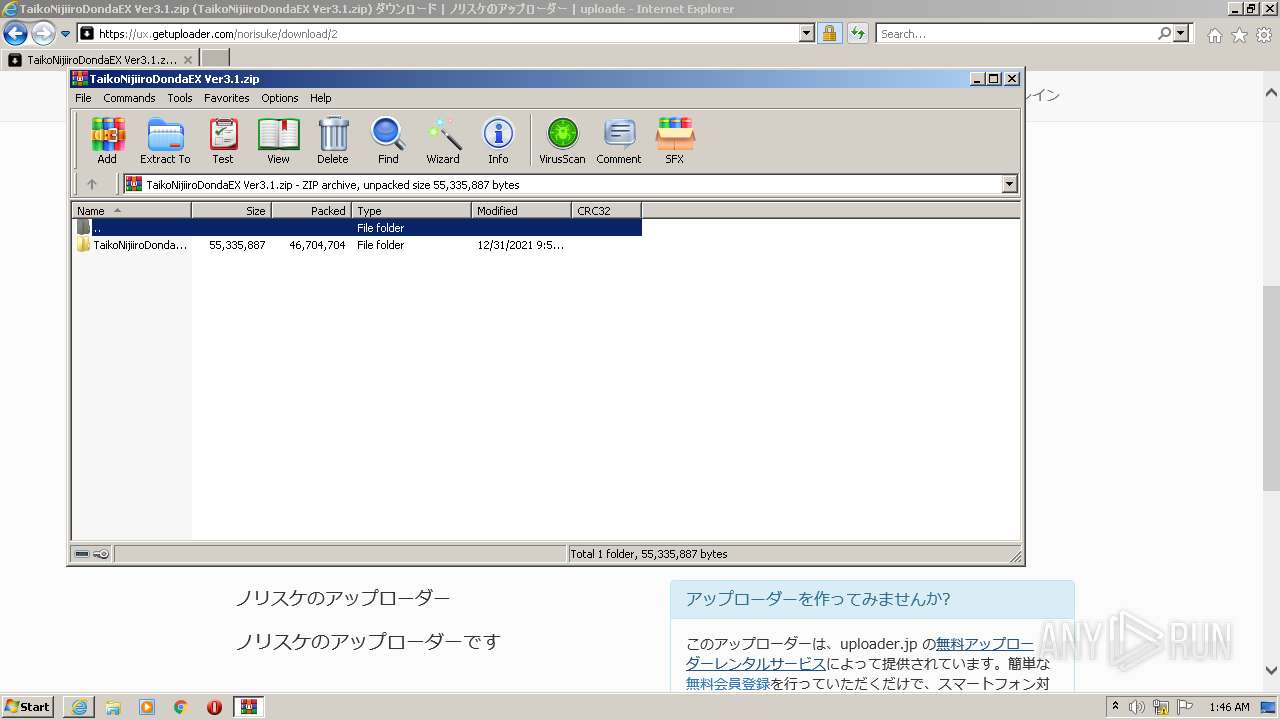
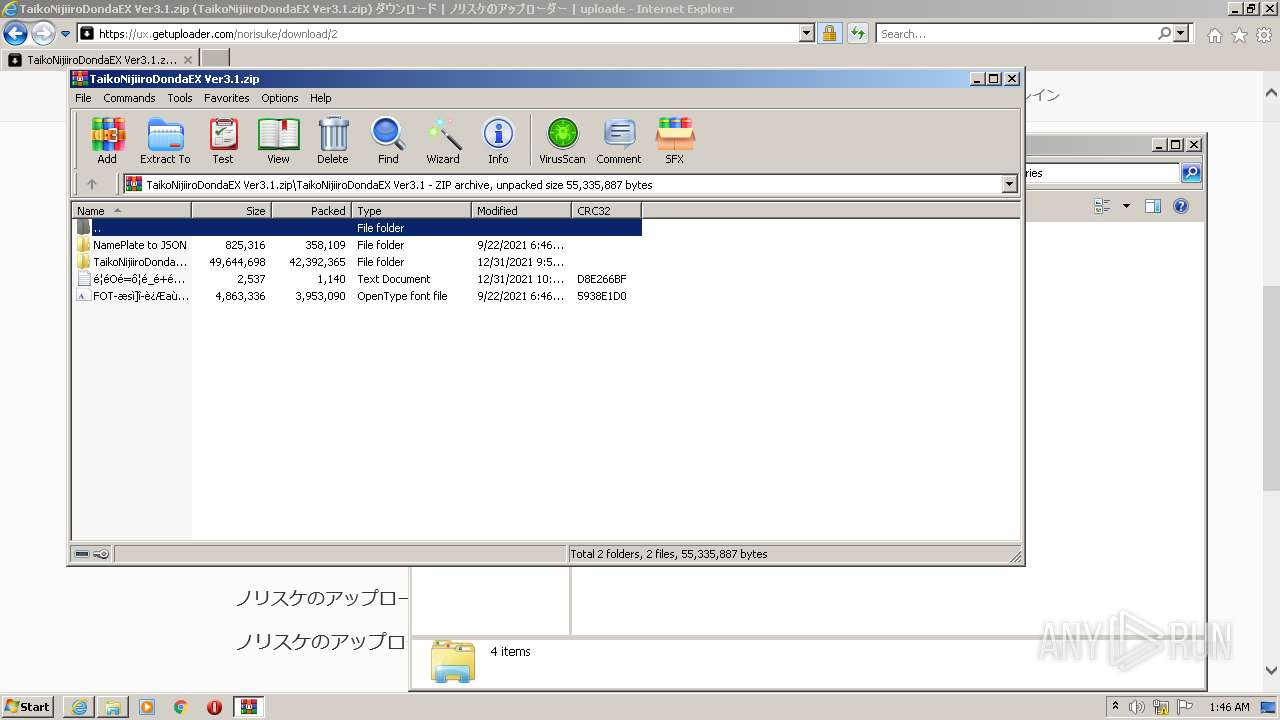
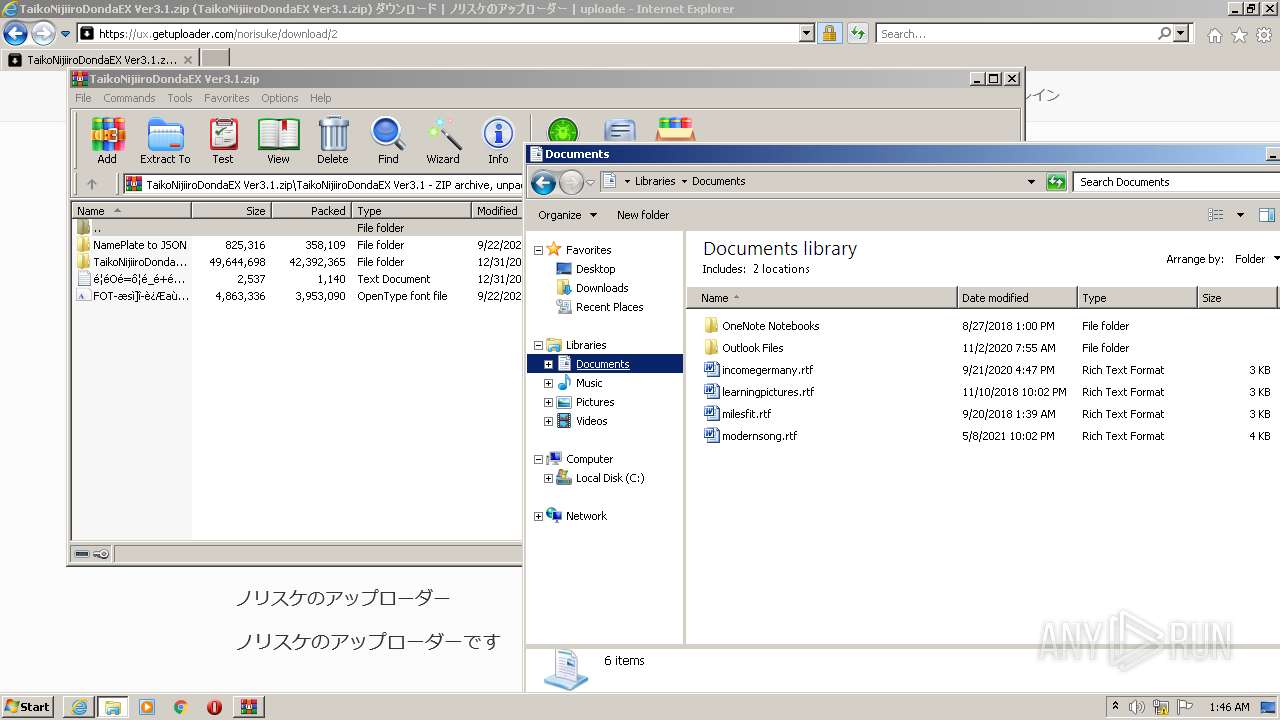
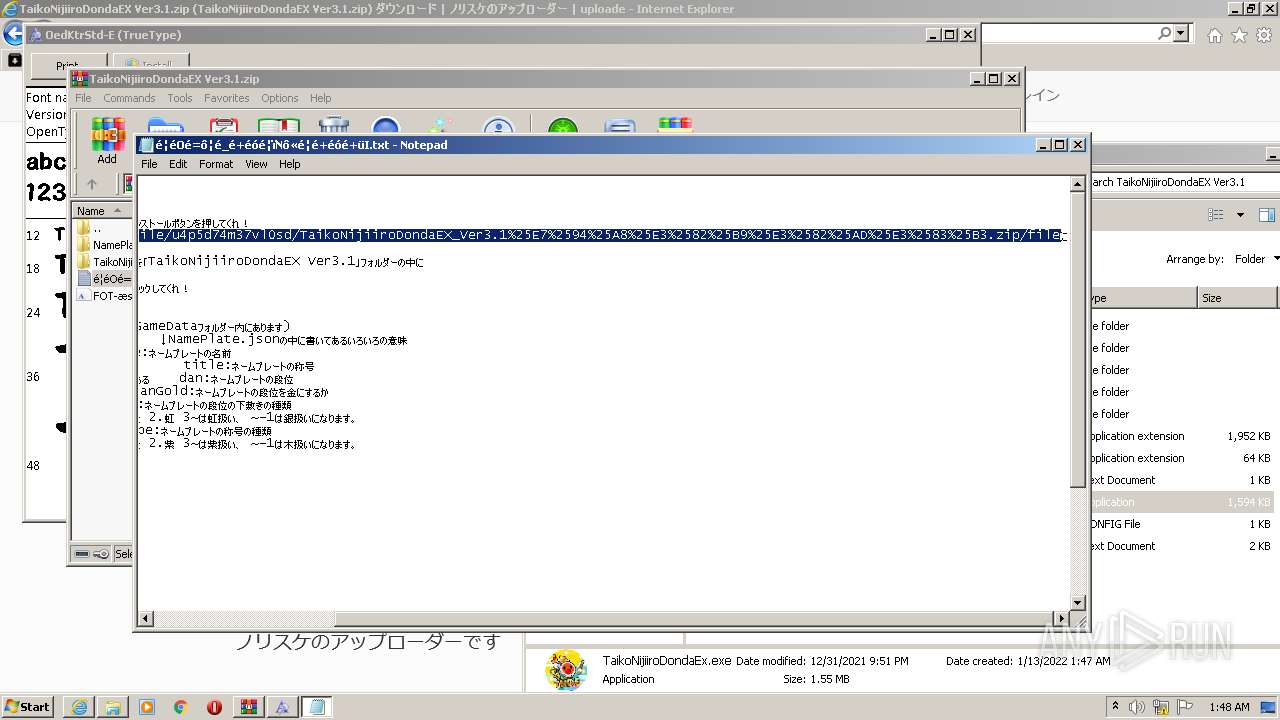
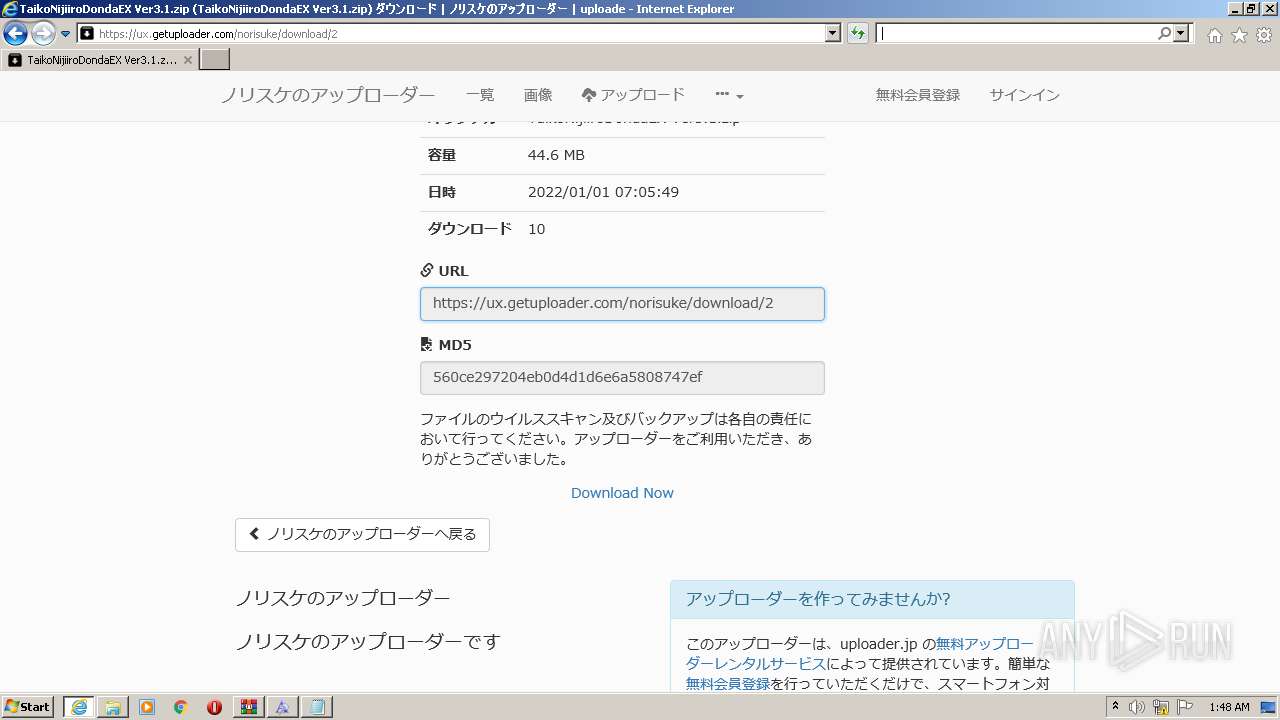
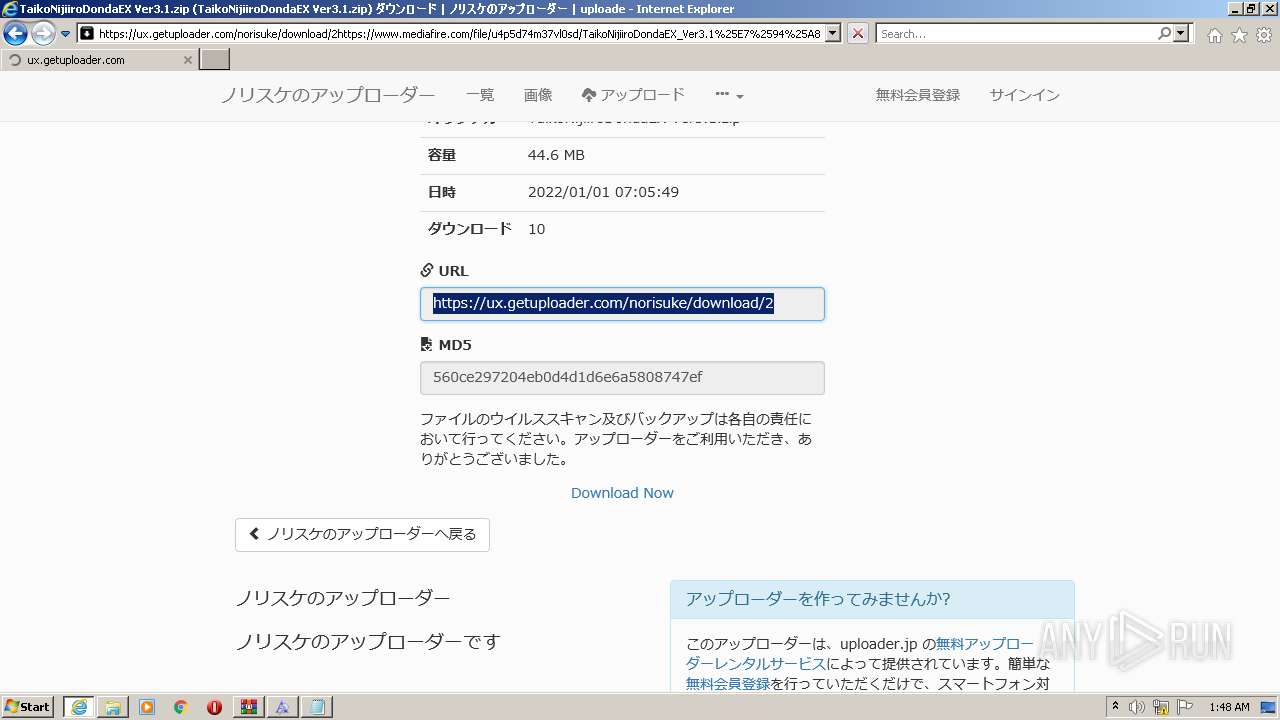
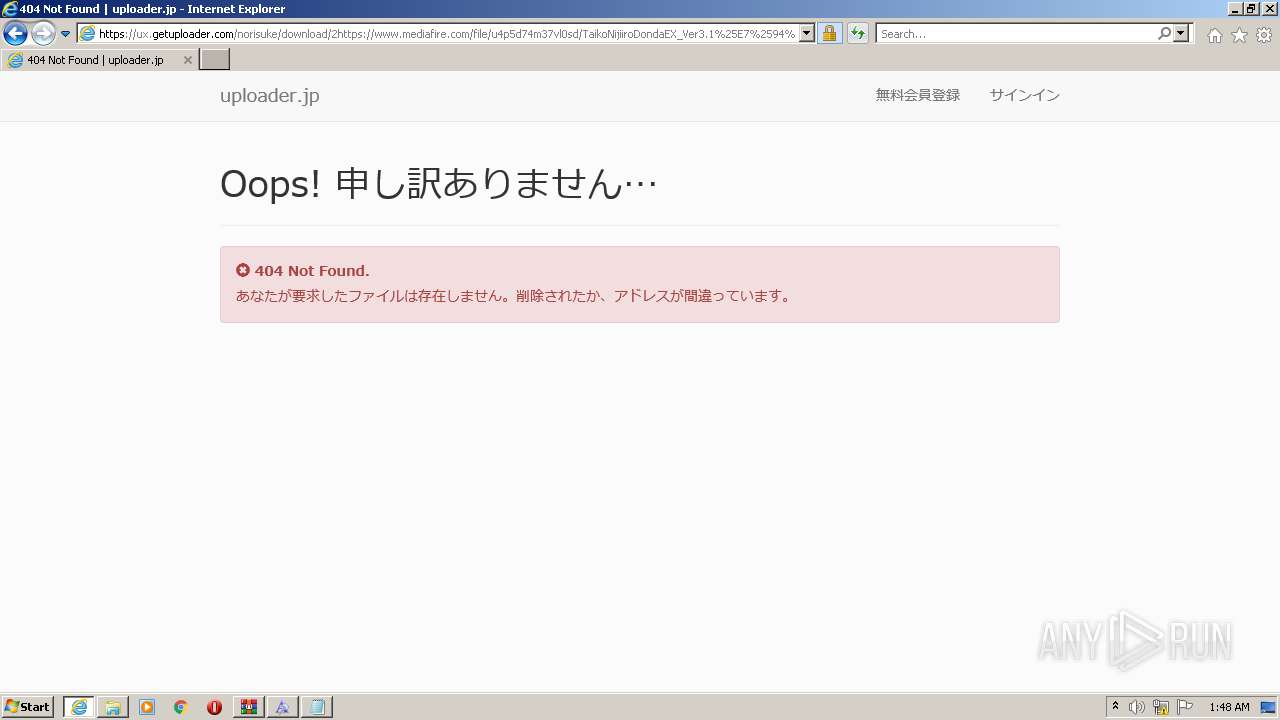
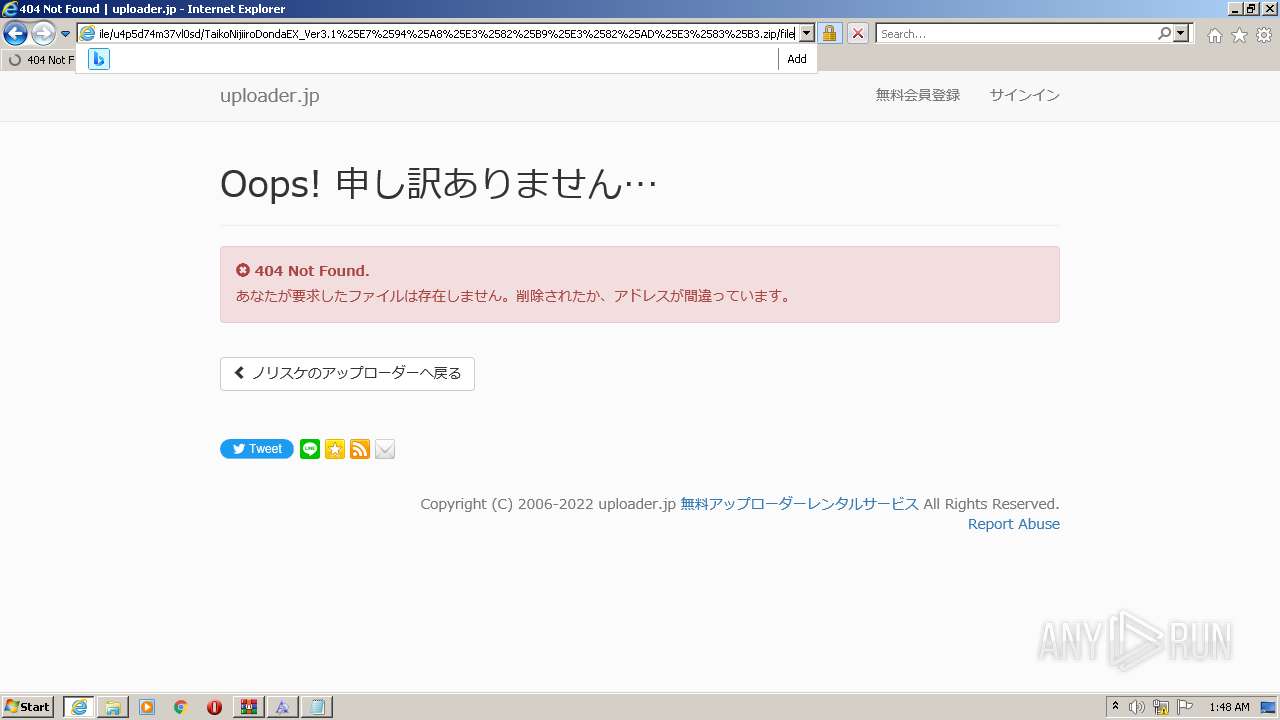
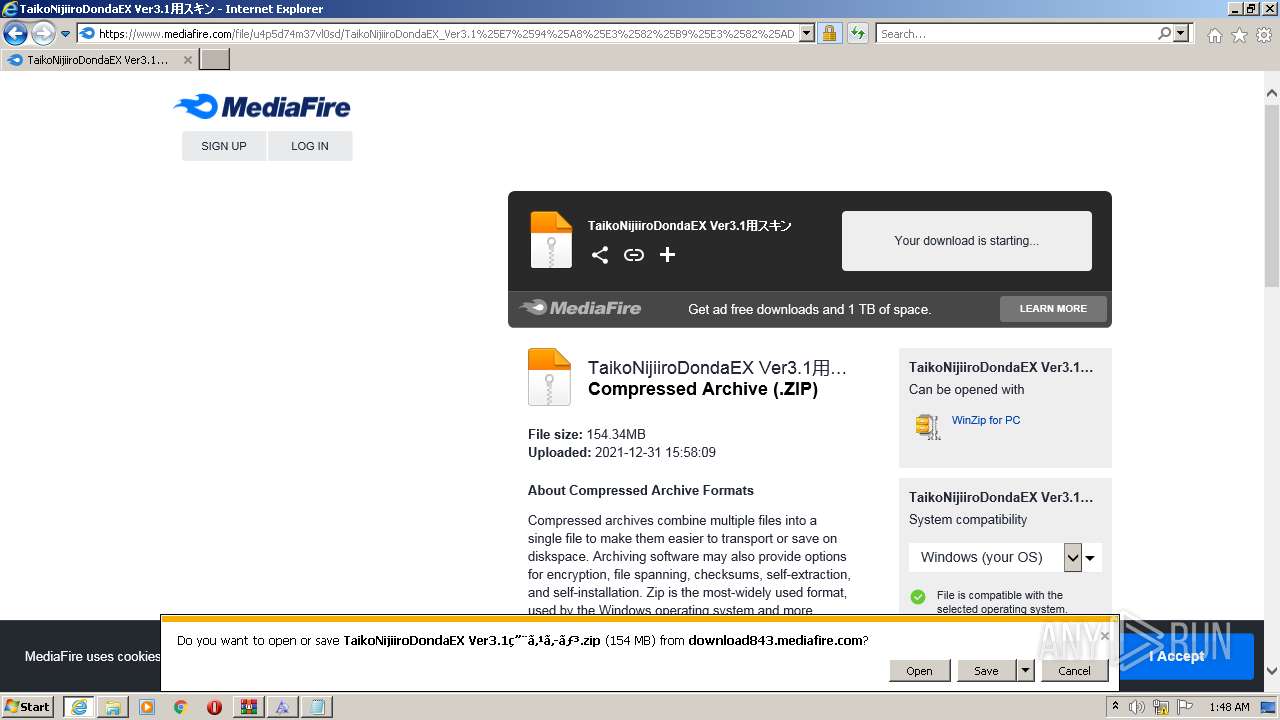
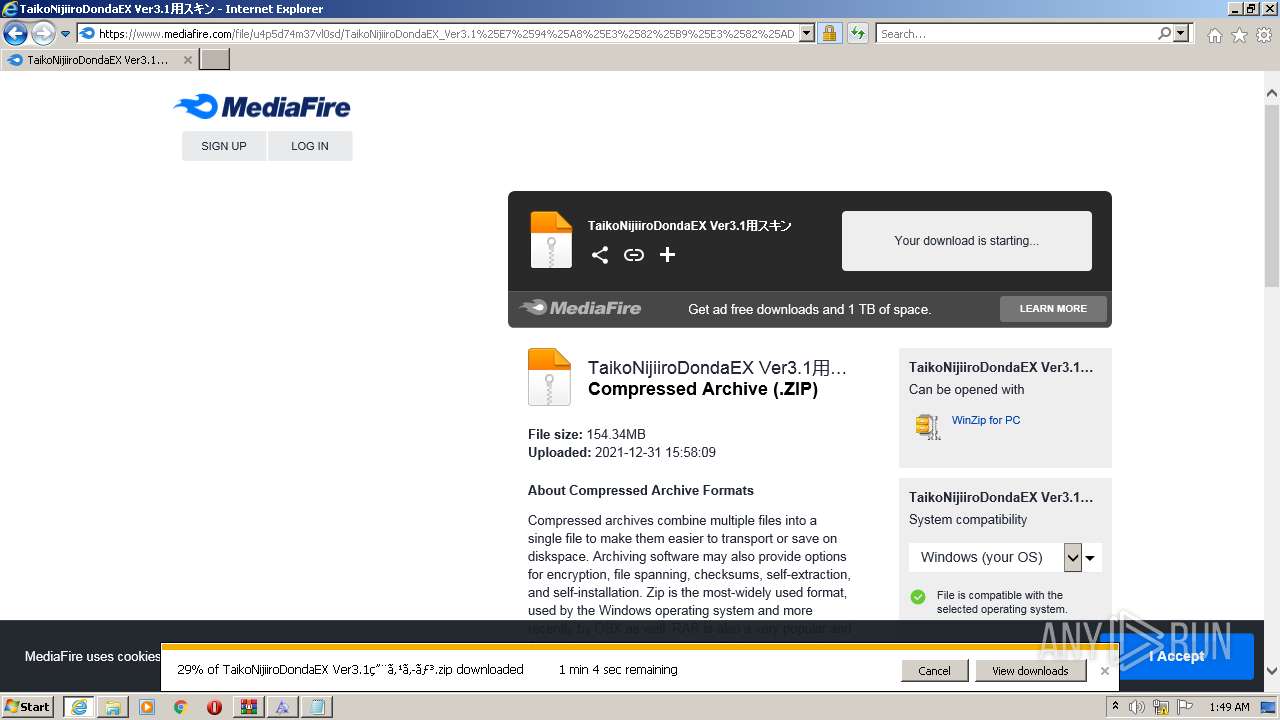
| URL: | https://ux.getuploader.com/norisuke/download/2 |
| Full analysis: | https://app.any.run/tasks/f6e57f33-e4aa-4828-a2f4-2f7ed106f3a9 |
| Verdict: | Malicious activity |
| Analysis date: | January 13, 2022, 01:45:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F3FF0DA046F7970BD923272CE4D9F981 |
| SHA1: | 0AA67A8ABD0EE3E3601485699827ABE9EE8B7D05 |
| SHA256: | 44CF574DFD5EAF470231A27AB445C8288A2AA3A609DC6E2C5DE665EDEF5EFBA7 |
| SSDEEP: | 3:N8f0pyKVS8SCXn:2fDsj |
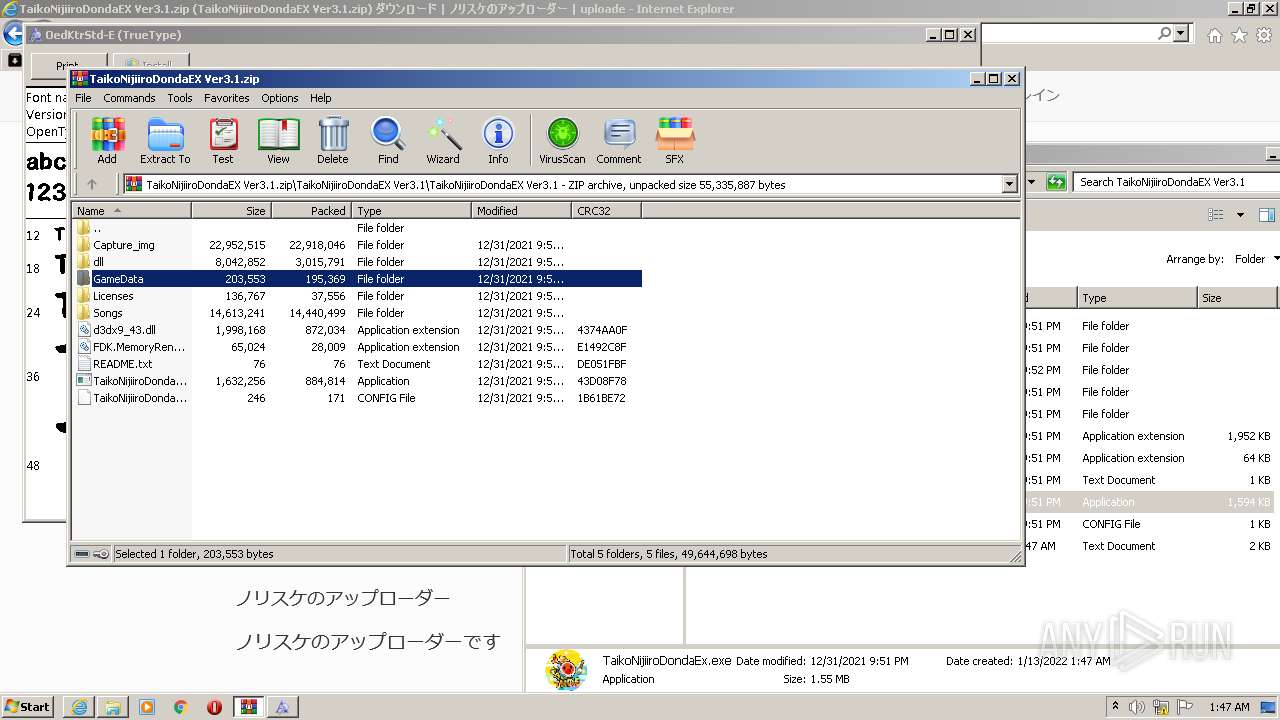
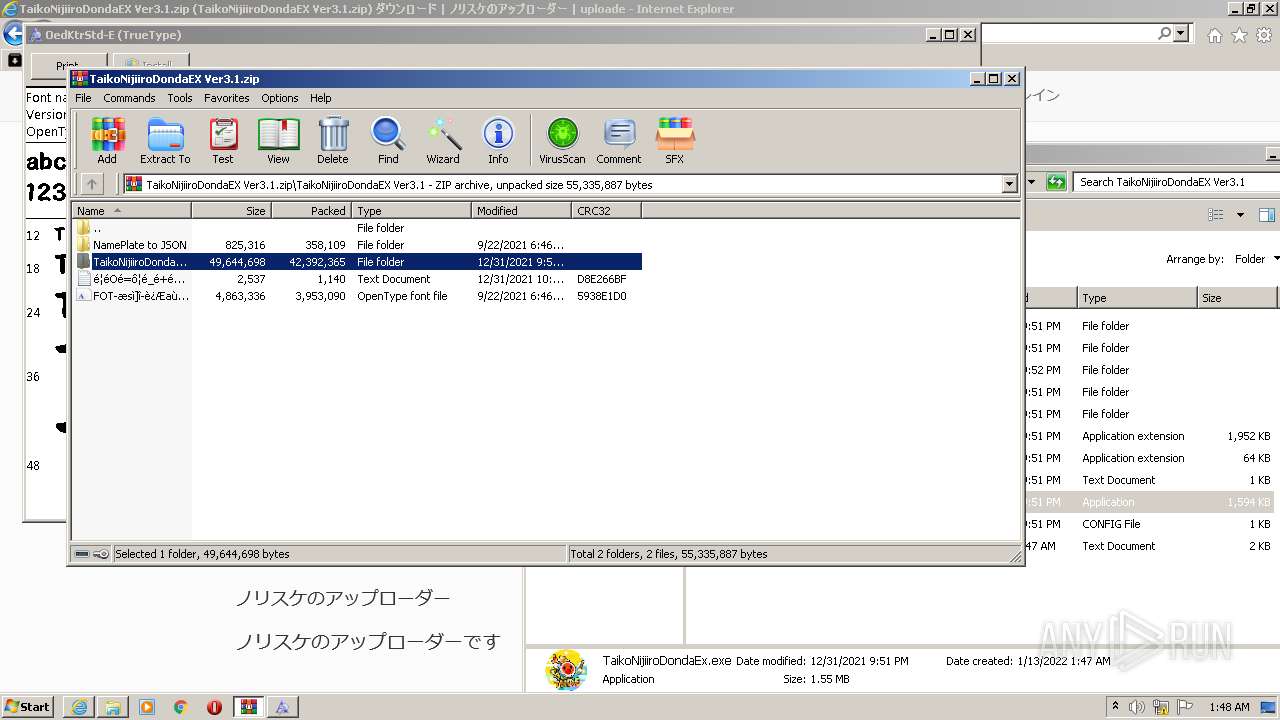
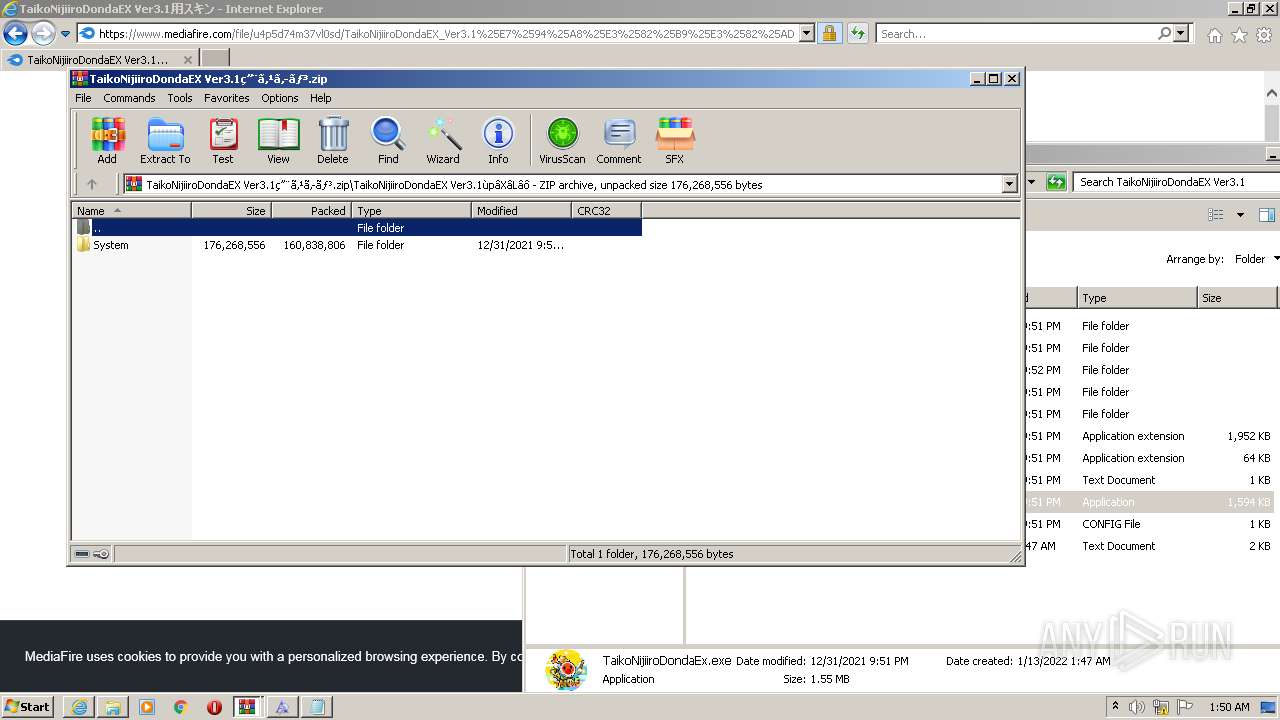
MALICIOUS
Loads dropped or rewritten executable
- SearchFilterHost.exe (PID: 3648)
- csrss.exe (PID: 668)
- SearchProtocolHost.exe (PID: 3604)
- Explorer.EXE (PID: 1108)
- csrss.exe (PID: 544)
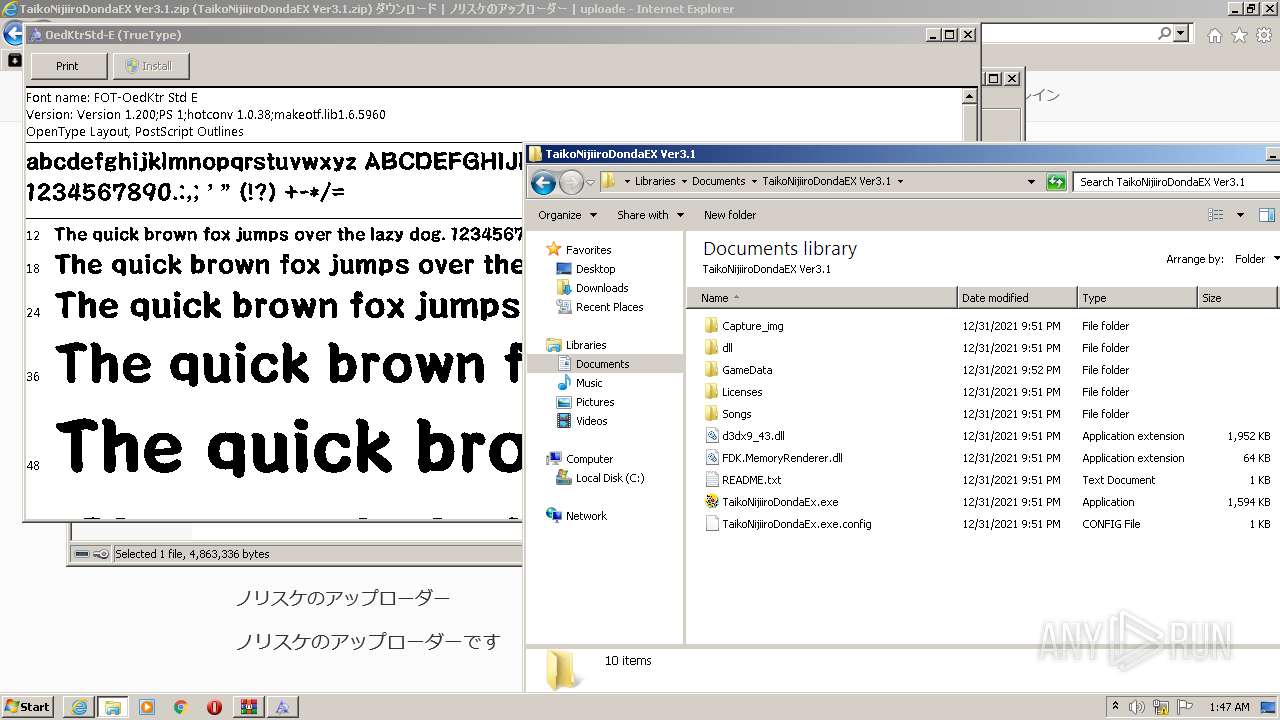
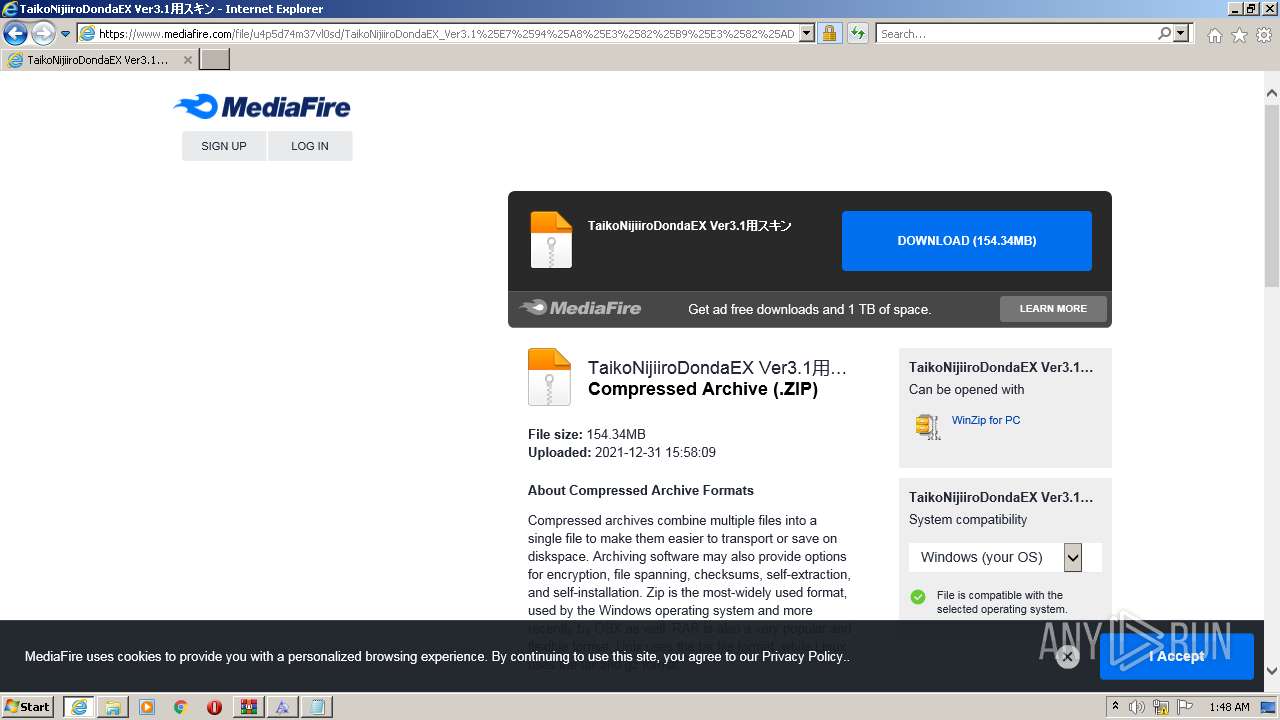
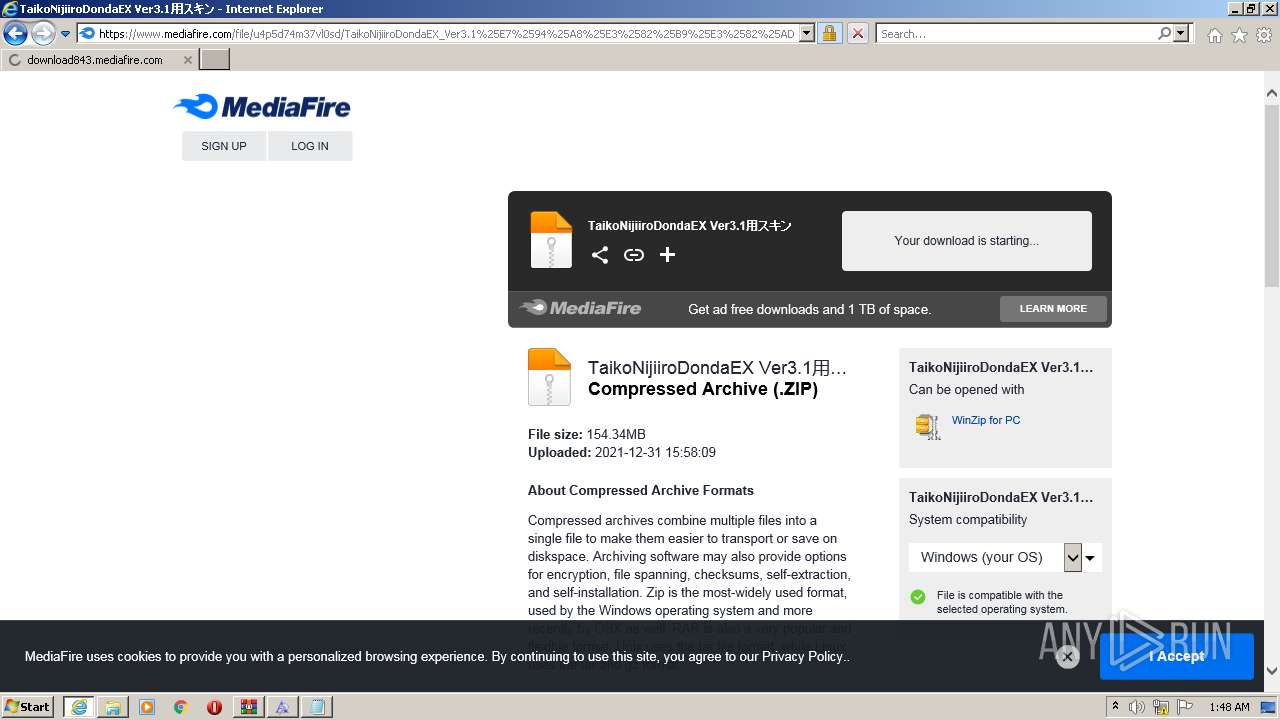
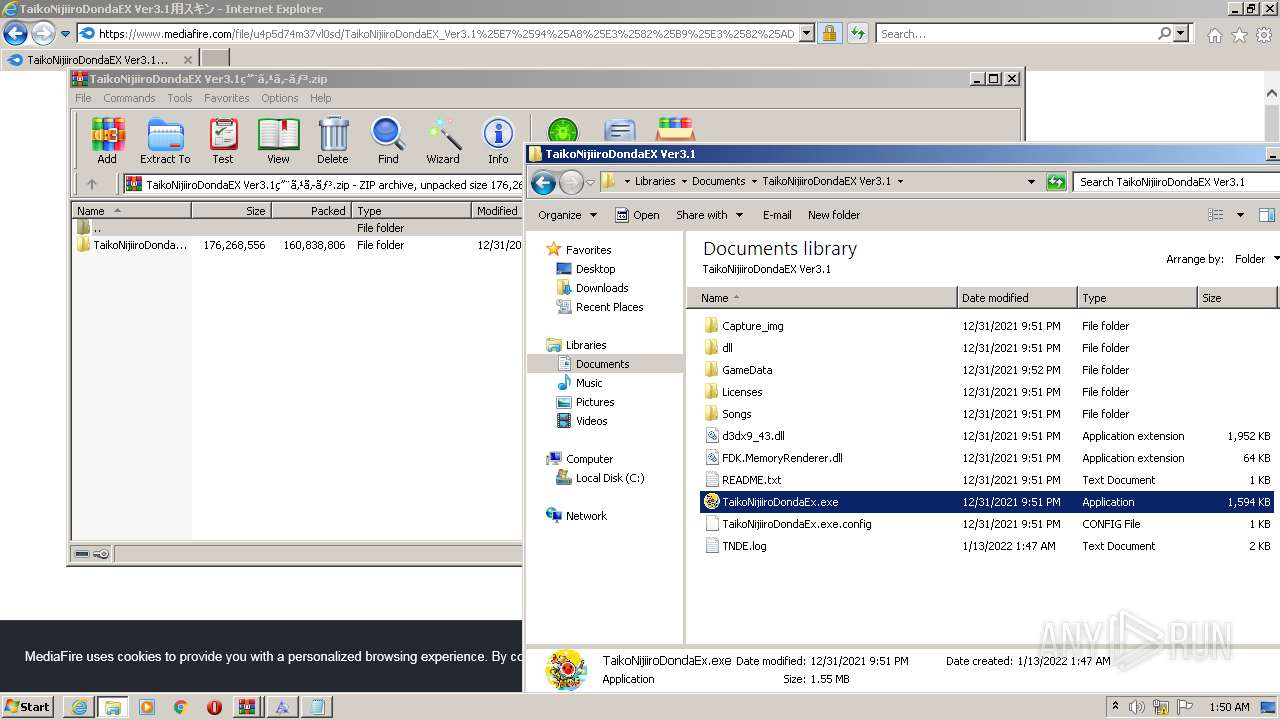
- TaikoNijiiroDondaEx.exe (PID: 2640)
- SearchFilterHost.exe (PID: 2564)
Application was dropped or rewritten from another process
- TaikoNijiiroDondaEx.exe (PID: 2640)
SUSPICIOUS
Starts Internet Explorer
- Explorer.EXE (PID: 1108)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2064)
Checks supported languages
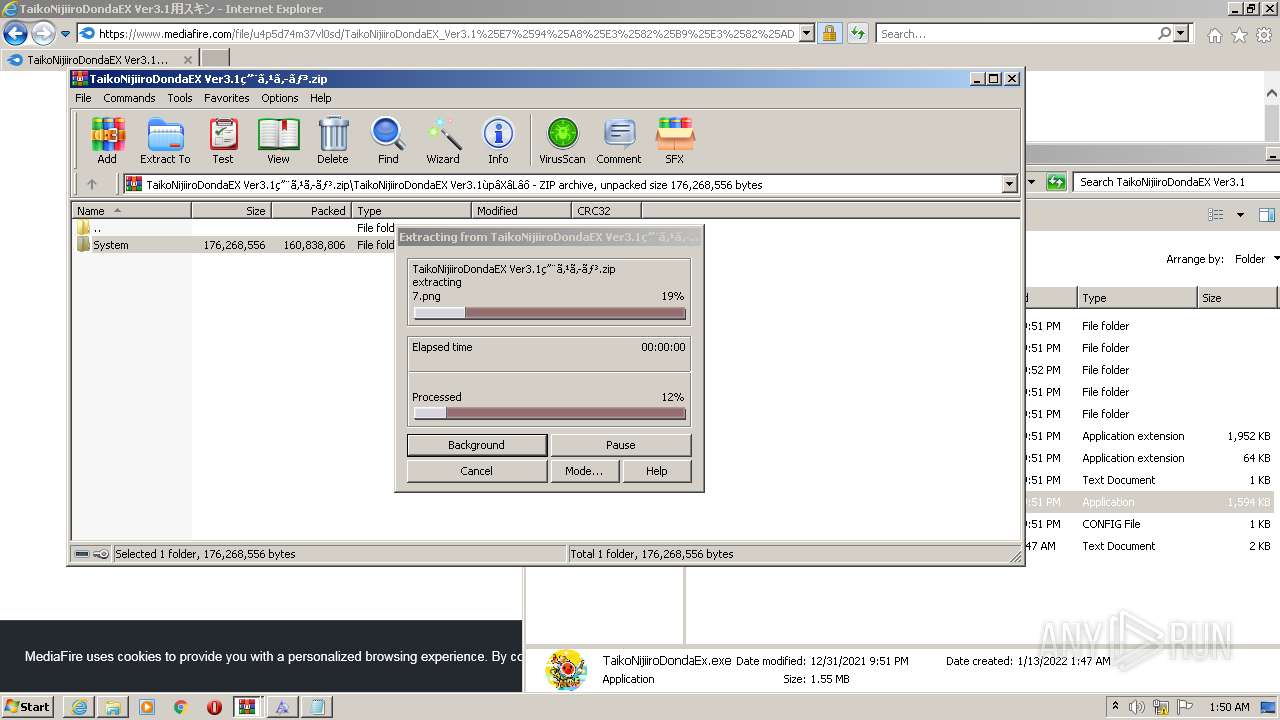
- WinRAR.exe (PID: 3032)
- TaikoNijiiroDondaEx.exe (PID: 2640)
- WinRAR.exe (PID: 3796)
Reads the computer name
- WinRAR.exe (PID: 3032)
- TaikoNijiiroDondaEx.exe (PID: 2640)
- WinRAR.exe (PID: 3796)
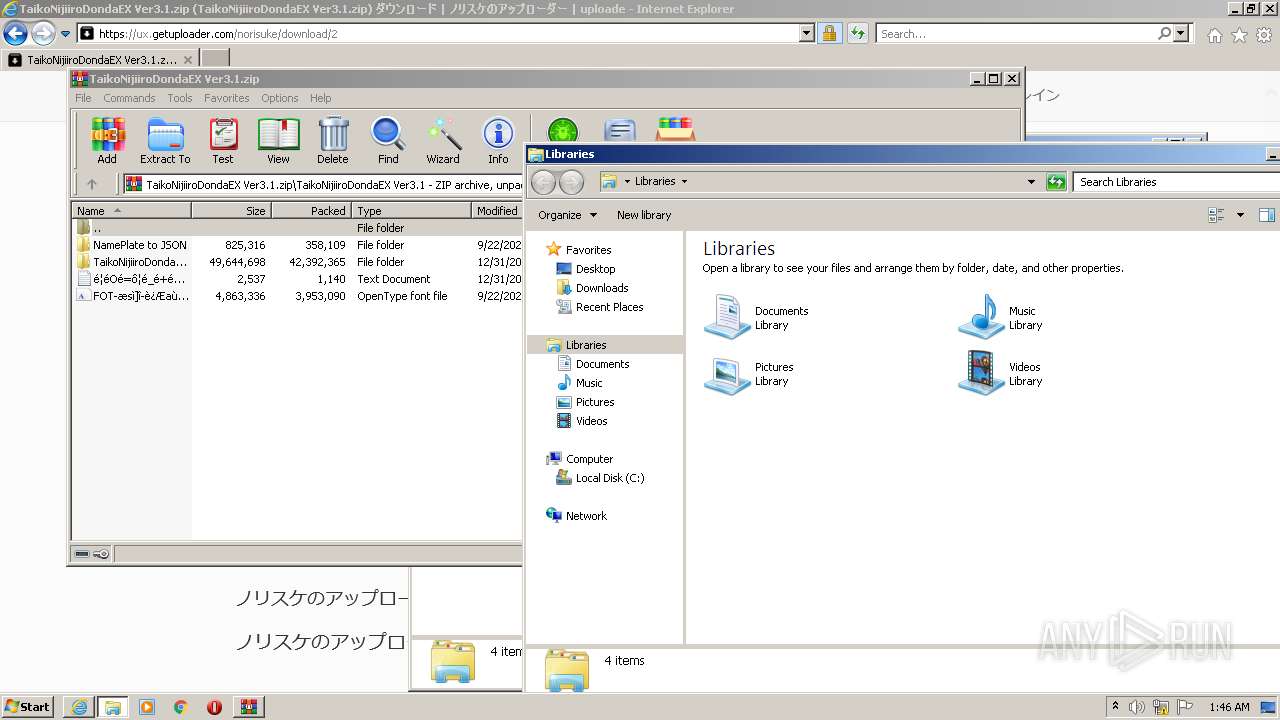
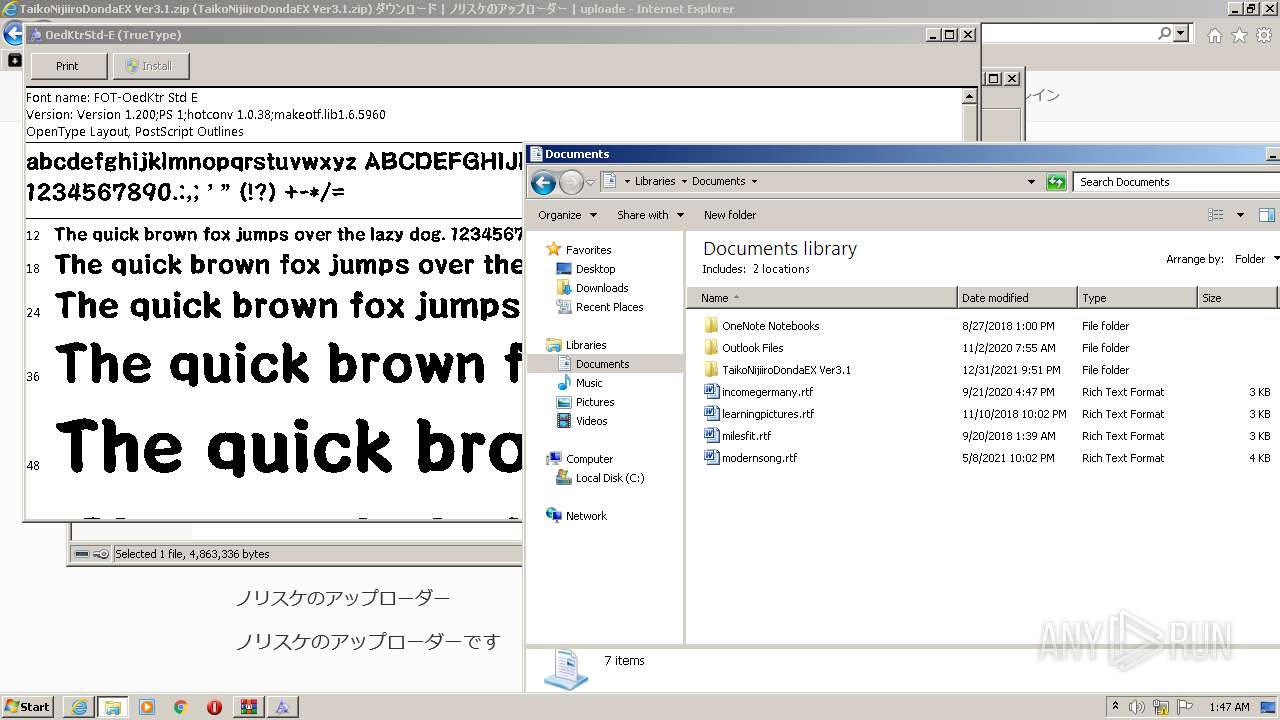
Creates files in the user directory
- Explorer.EXE (PID: 1108)
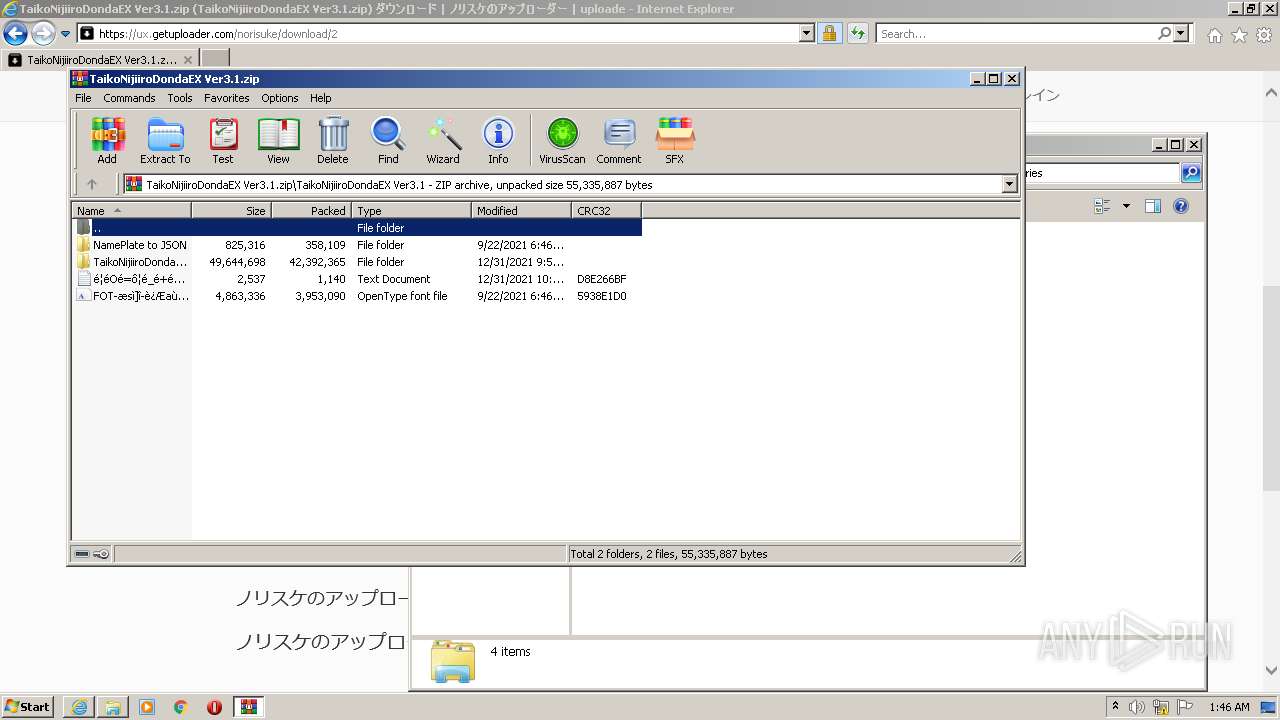
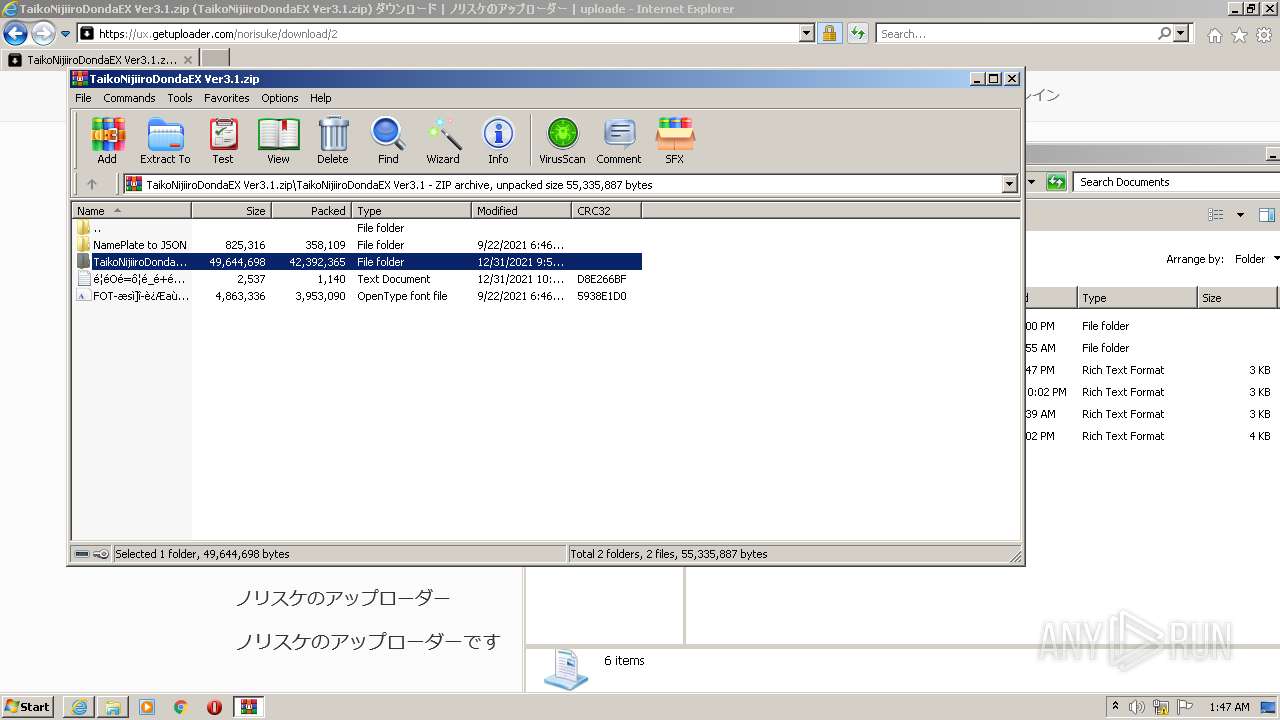
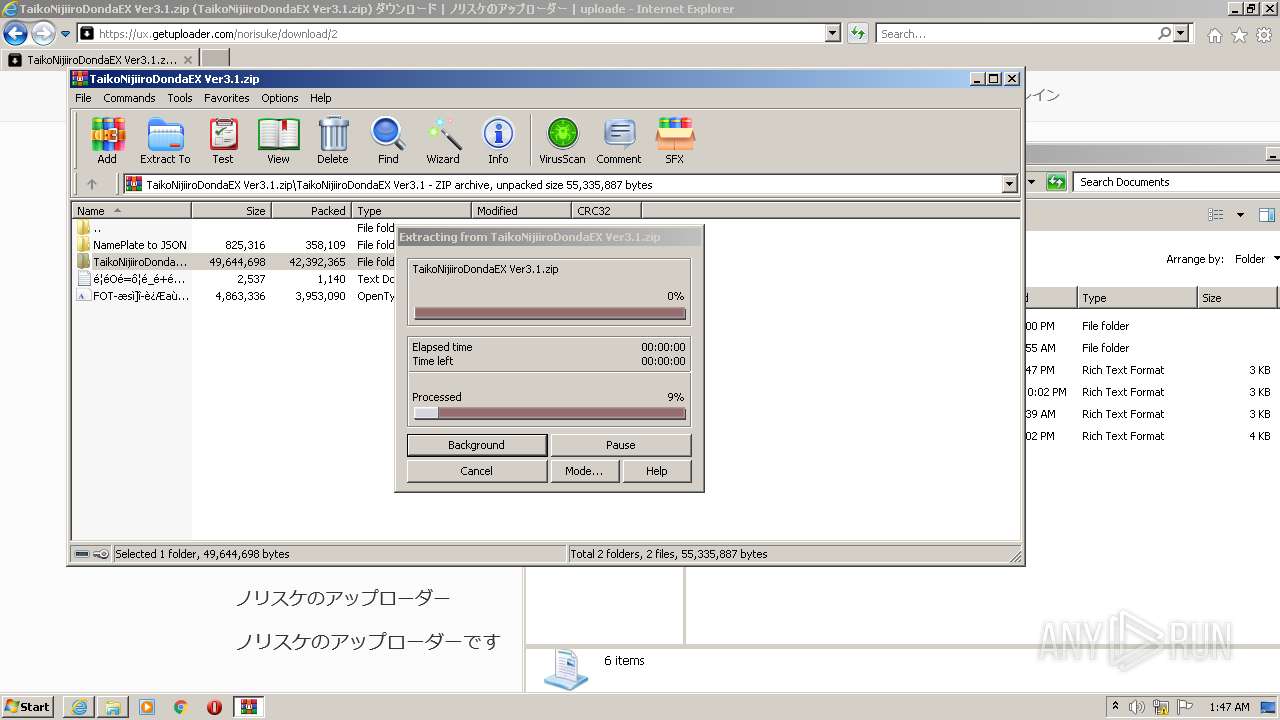
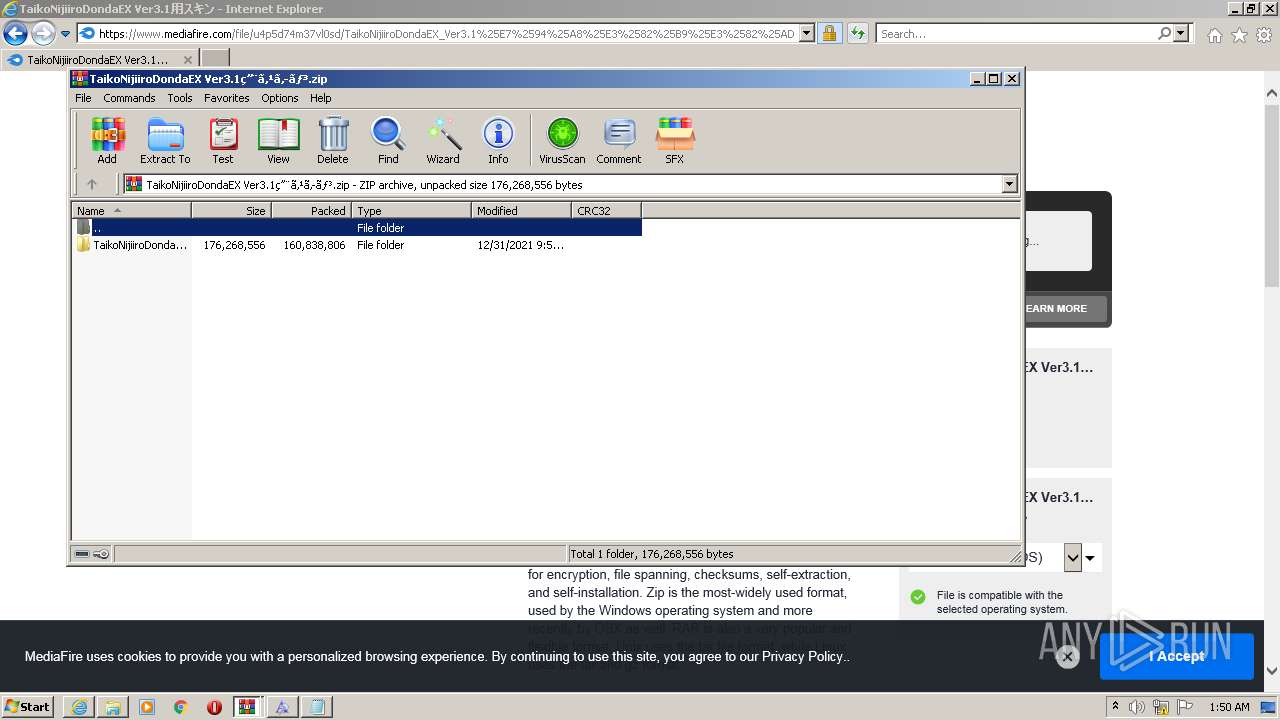
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3032)
Executed via COM
- DllHost.exe (PID: 1124)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3032)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3032)
Creates files in the Windows directory
- DllHost.exe (PID: 1124)
Reads default file associations for system extensions
- Explorer.EXE (PID: 1108)
Drops a file with too old compile date
- WinRAR.exe (PID: 3032)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3032)
INFO
Reads the computer name
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 2064)
- explorer.exe (PID: 2520)
- fontview.exe (PID: 2612)
- DllHost.exe (PID: 1124)
- SearchFilterHost.exe (PID: 2564)
Checks supported languages
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 2064)
- fontview.exe (PID: 2612)
- explorer.exe (PID: 2520)
- DllHost.exe (PID: 1124)
- NOTEPAD.EXE (PID: 2604)
- SearchFilterHost.exe (PID: 2564)
- rundll32.exe (PID: 3796)
Changes internet zones settings
- iexplore.exe (PID: 2632)
Application launched itself
- iexplore.exe (PID: 2632)
Reads settings of System Certificates
- iexplore.exe (PID: 2064)
- iexplore.exe (PID: 2632)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2632)
Checks Windows Trust Settings
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 2064)
Reads internet explorer settings
- iexplore.exe (PID: 2064)
Creates files in the user directory
- iexplore.exe (PID: 2064)
- iexplore.exe (PID: 2632)
Changes settings of System certificates
- iexplore.exe (PID: 2632)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2632)
Manual execution by user
- explorer.exe (PID: 2520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
16
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 544 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\system32\csrss.exe | — | — | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\system32\csrss.exe | — | — | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1108 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1124 | C:\Windows\system32\DllHost.exe /Processid:{642EF9D6-48A5-476B-919A-A507CFD02C0F} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2632 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2520 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2564 | "C:\Windows\system32\SearchFilterHost.exe" 0 520 524 532 65536 528 | C:\Windows\system32\SearchFilterHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Filter Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
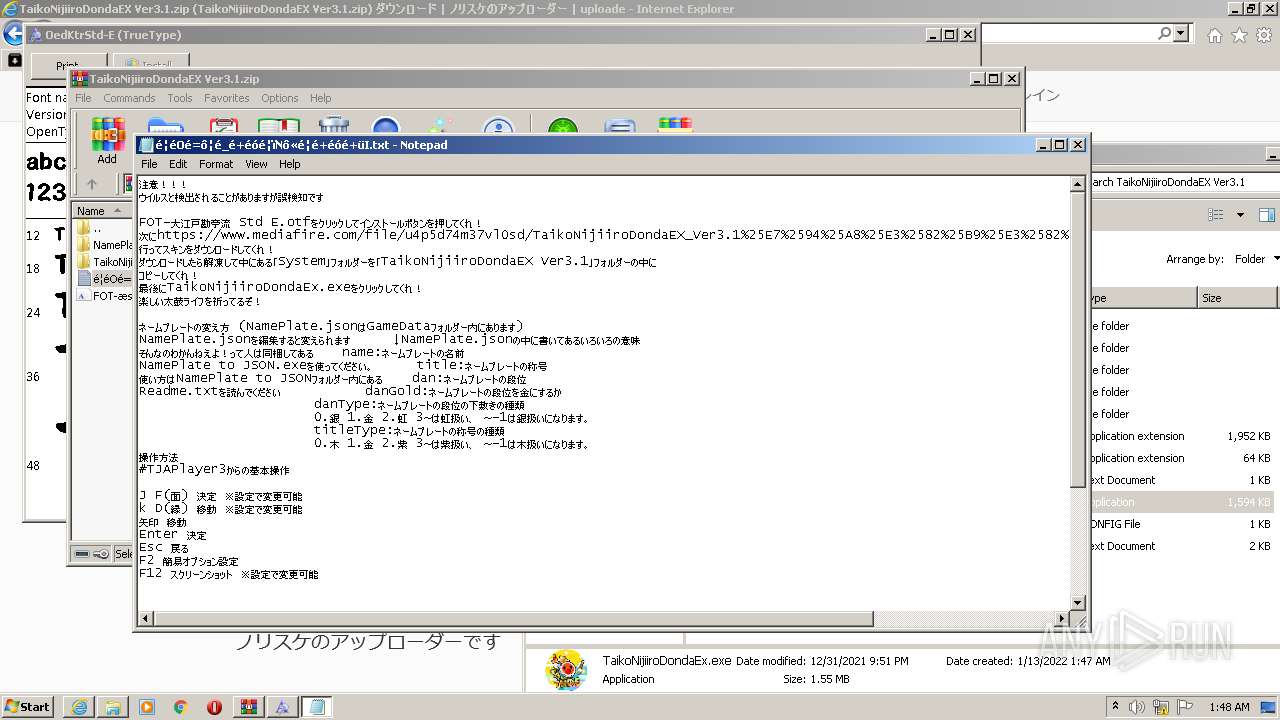
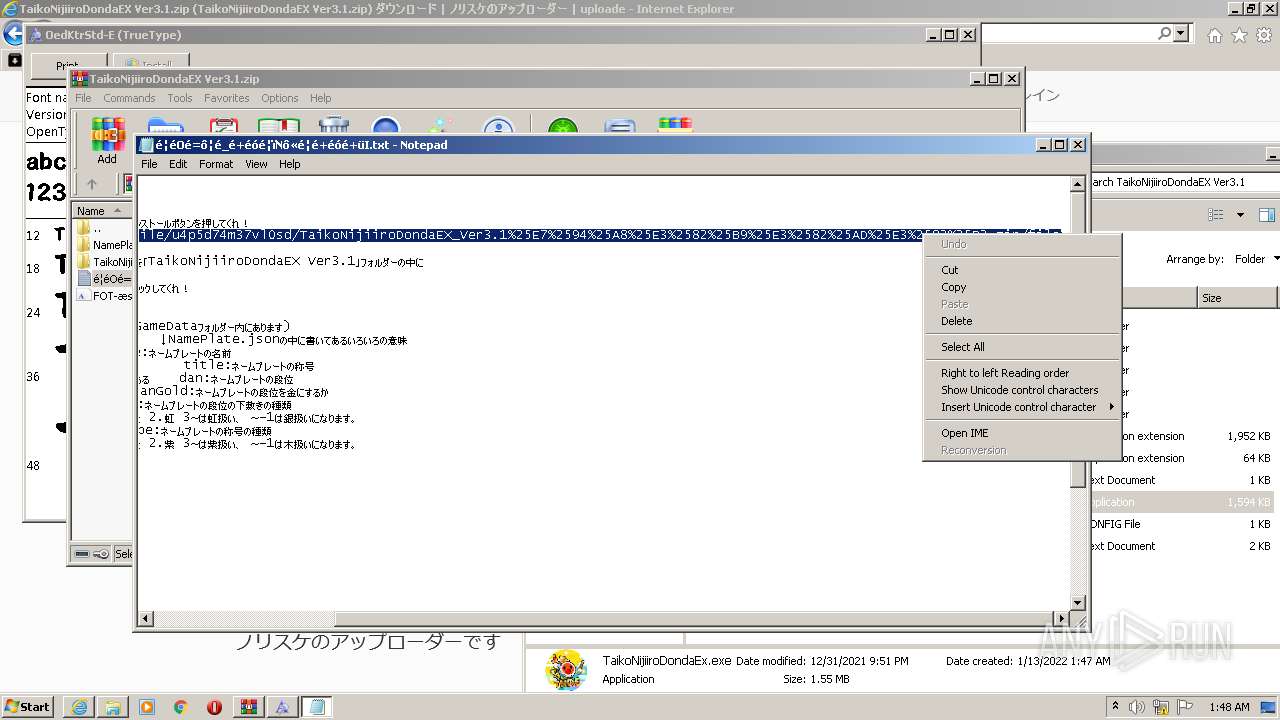
| 2604 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa3032.14000\��O�=���_�+����N����+���+�I.txt | C:\Windows\system32\NOTEPAD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
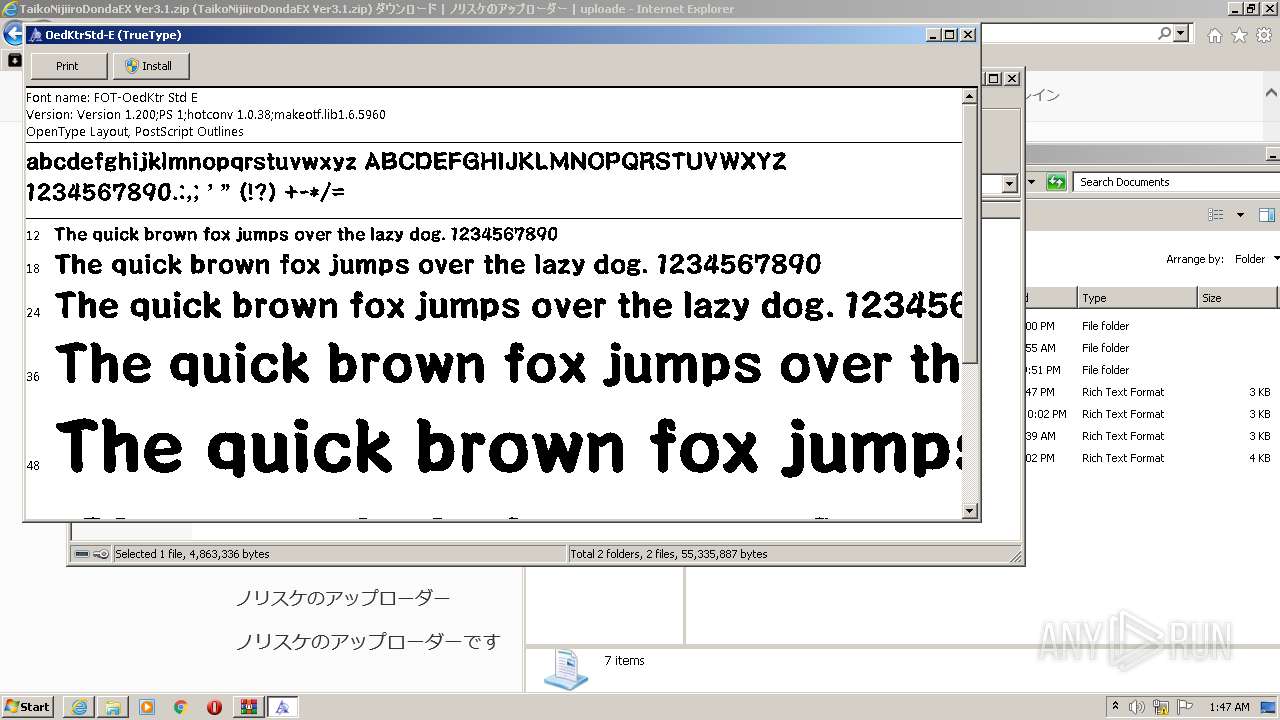
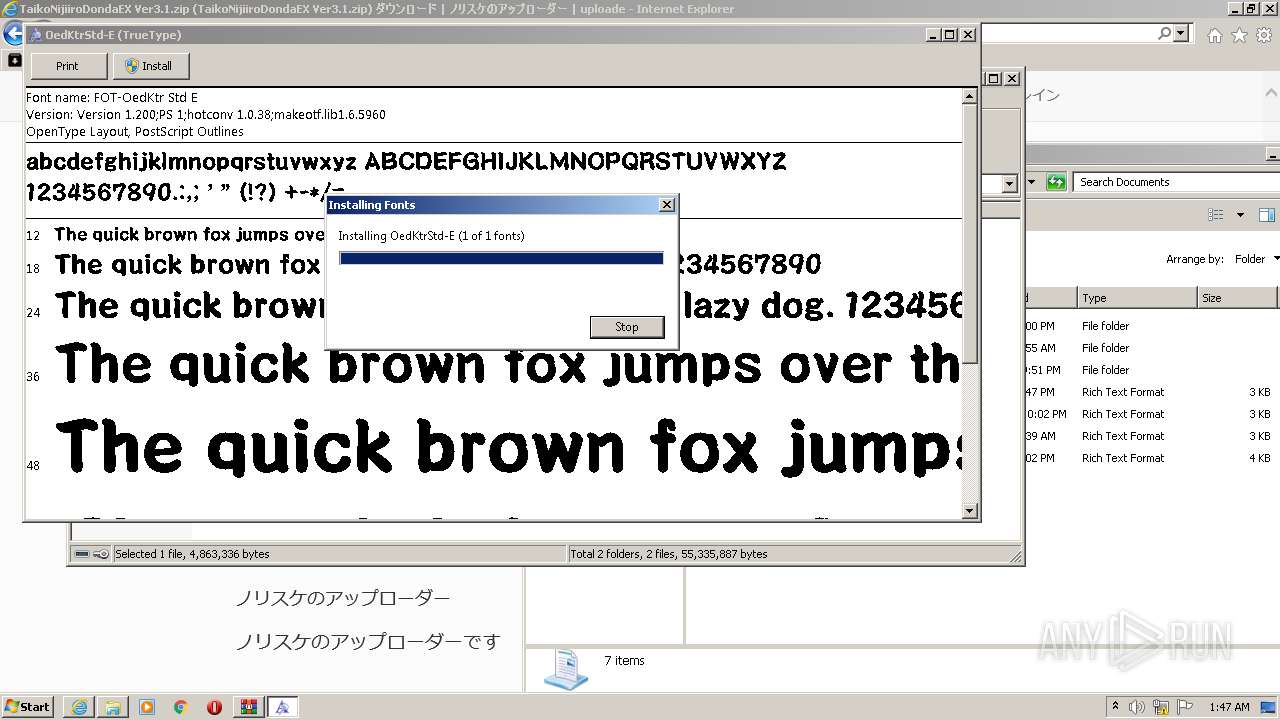
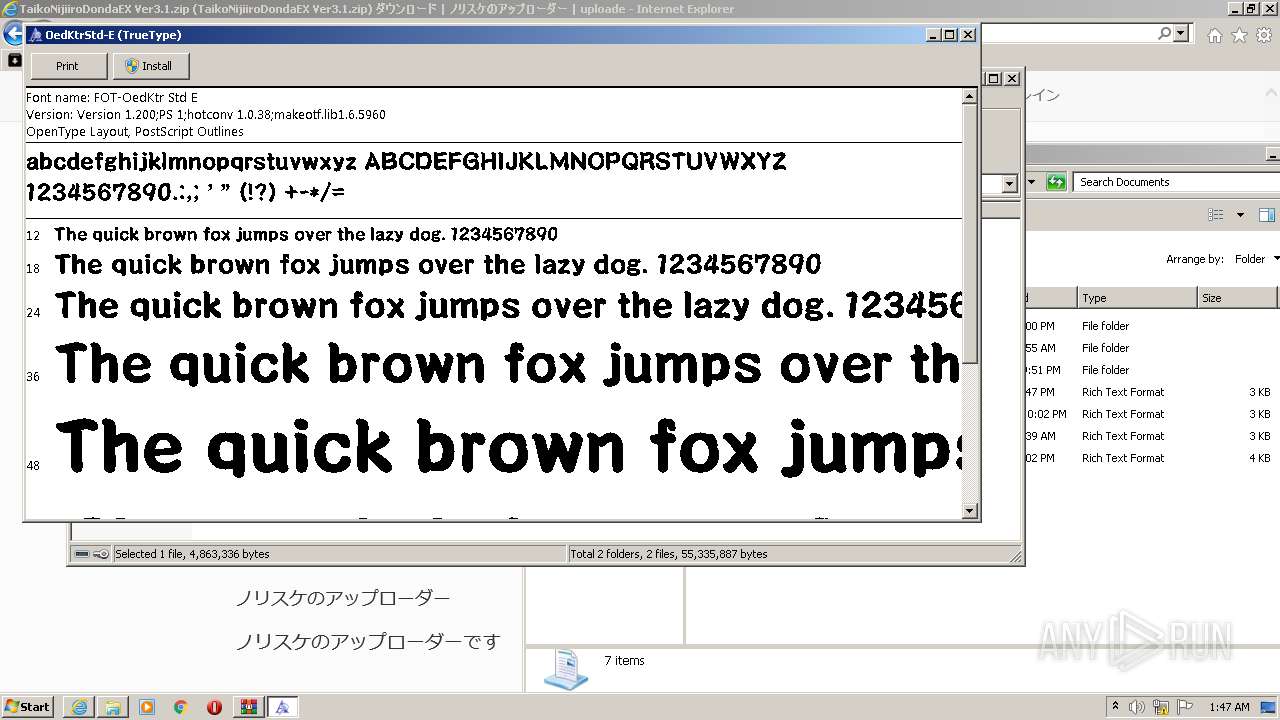
| 2612 | "C:\Windows\System32\fontview.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa3032.8901\FOT-�s�]�-��a�� Std E.otf | C:\Windows\System32\fontview.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Font Viewer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ux.getuploader.com/norisuke/download/2" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
33 512
Read events
32 939
Write events
563
Delete events
10
Modification events
| (PID) Process: | (2632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30935071 | |||
| (PID) Process: | (2632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30935071 | |||
| (PID) Process: | (2632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
22
Suspicious files
59
Text files
776
Unknown types
56
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\2[1].htm | html | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:— | SHA256:— | |||
| 2064 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\invisible[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
191
DNS requests
77
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2064 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2064 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD6vIn3vzMQlAoAAAABJf0y | US | der | 472 b | whitelisted |
2064 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGmSmALa8169CgAAAAEn3NM%3D | US | der | 471 b | whitelisted |
2064 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
2064 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2064 | iexplore.exe | GET | 200 | 143.204.101.74:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEA22xe%2FWLqE8IEfkGfaeUMw%3D | US | der | 471 b | whitelisted |
2064 | iexplore.exe | GET | 200 | 143.204.101.177:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2064 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAdcEVSwgb112LyBBg7h6uQ%3D | US | der | 471 b | whitelisted |
2064 | iexplore.exe | GET | 200 | 143.204.101.74:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEA6tB6B6%2B7D1zF3Ayn6DQCY%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2064 | iexplore.exe | 2.16.186.81:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2064 | iexplore.exe | 172.67.186.59:443 | ux.getuploader.com | — | US | suspicious |
2632 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2632 | iexplore.exe | 2.16.186.81:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2632 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2064 | iexplore.exe | 104.21.80.152:443 | ux.getuploader.com | Cloudflare Inc | US | suspicious |
2064 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2064 | iexplore.exe | 2.16.186.56:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2064 | iexplore.exe | 130.211.14.194:443 | cdn-fluct.sh.adingo.jp | Google Inc. | US | whitelisted |
2064 | iexplore.exe | 104.18.10.207:443 | maxcdn.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ux.getuploader.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
r.getuploader.com |
| suspicious |
ajax.googleapis.com |
| whitelisted |
cdn-fluct.sh.adingo.jp |
| unknown |
translate.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
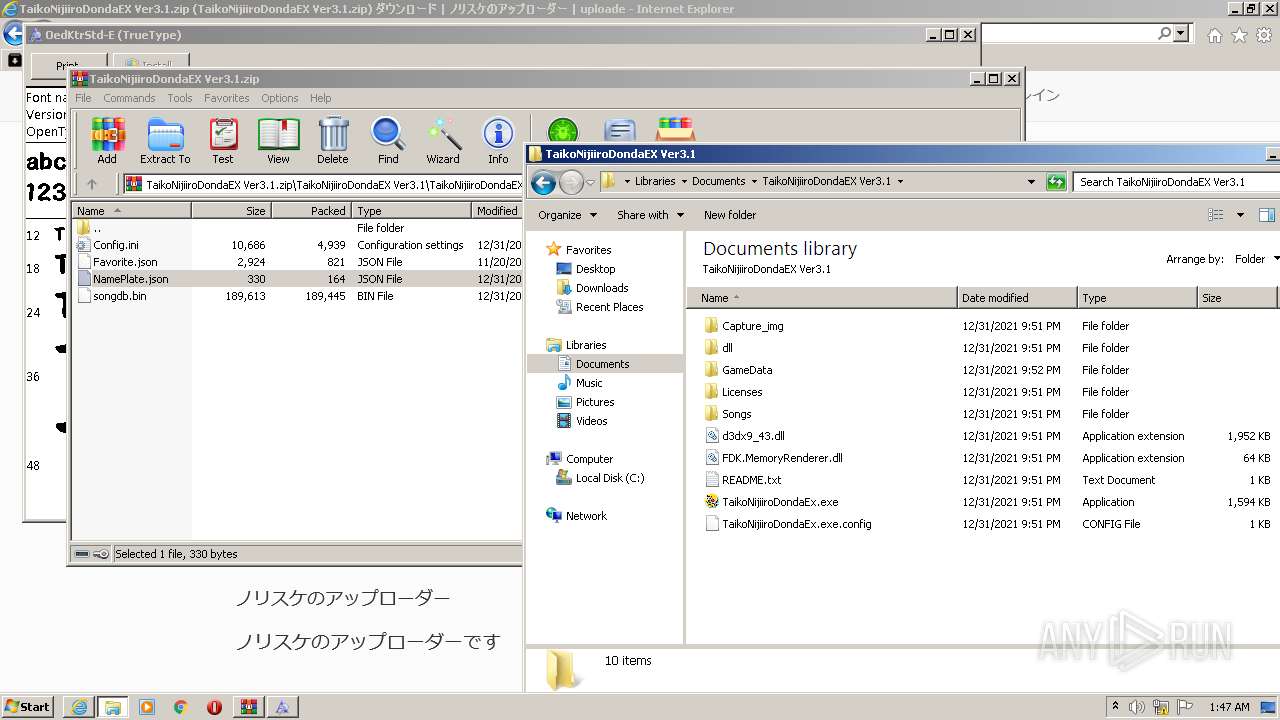
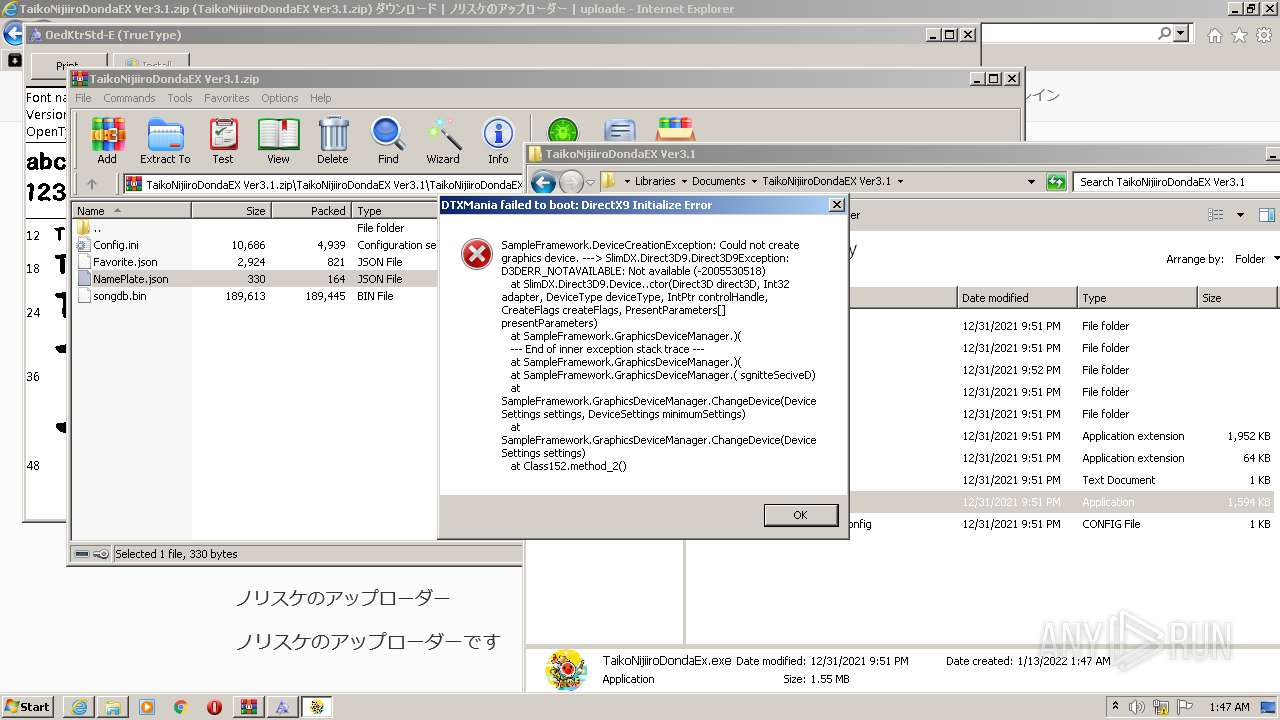
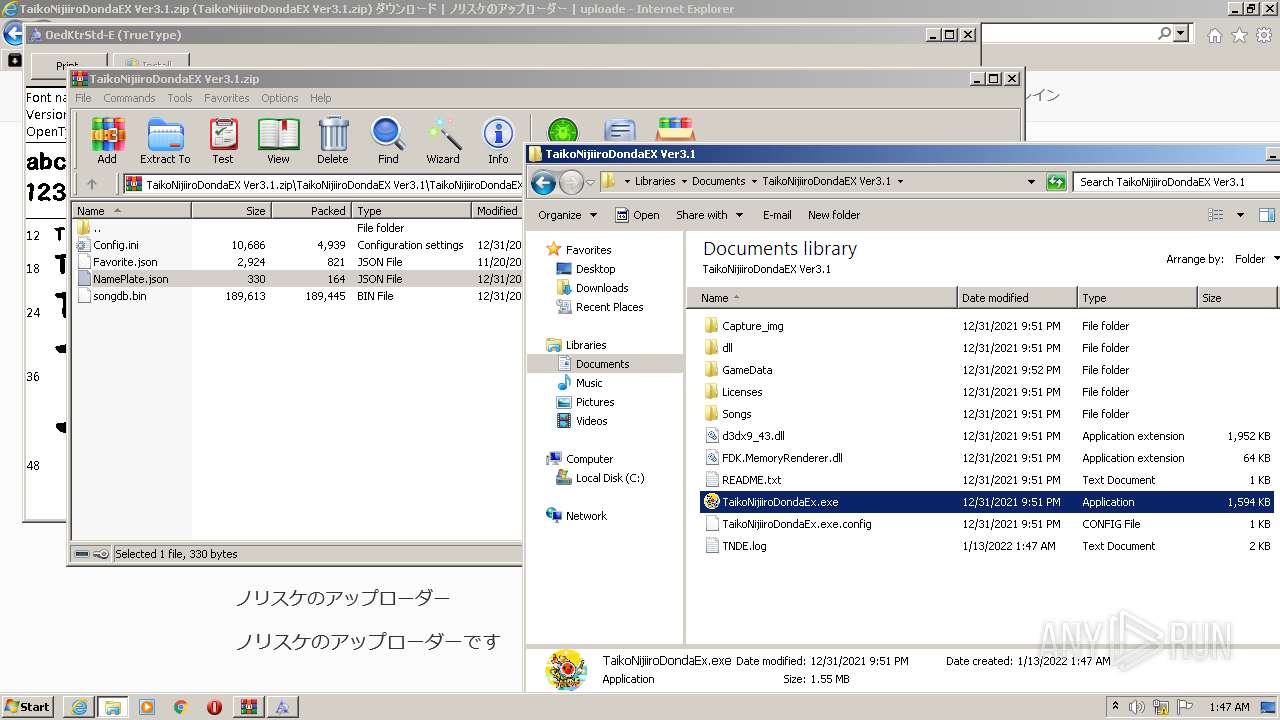
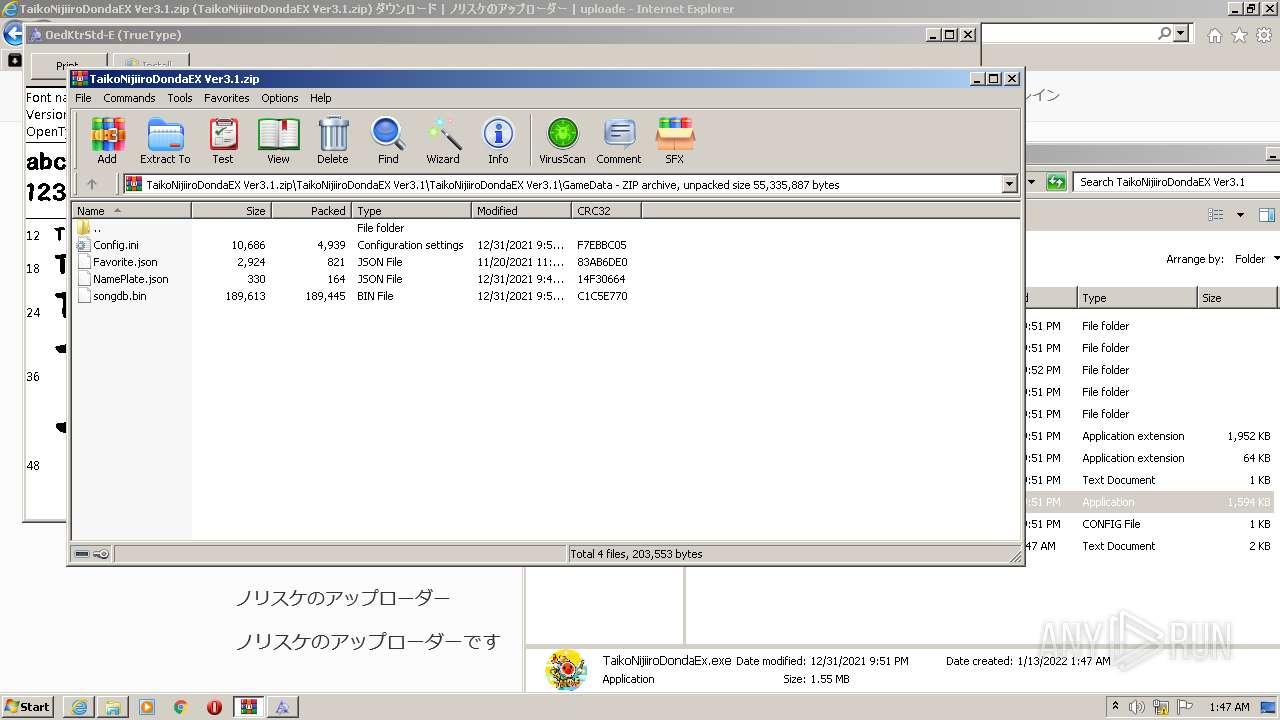
TaikoNijiiroDondaEx.exe | Current Directory: C:\Users\admin\Documents\TaikoNijiiroDondaEX Ver3.1
|
TaikoNijiiroDondaEx.exe | EXE???????: C:\Users\admin\Documents\TaikoNijiiroDondaEX Ver3.1
|
TaikoNijiiroDondaEx.exe | |
TaikoNijiiroDondaEx.exe | DTXMania powered by YAMAHA Silent Session Drums
|
TaikoNijiiroDondaEx.exe | Release: 3.1.0
|
TaikoNijiiroDondaEx.exe | |
TaikoNijiiroDondaEx.exe | TaikoNijiiroDondaEx.exe Information: 0 : |
TaikoNijiiroDondaEx.exe | ----------------------
|
TaikoNijiiroDondaEx.exe | TaikoNijiiroDondaEx.exe Information: 0 : |
TaikoNijiiroDondaEx.exe | � ????????????
|