| File name: | Sample1.zip |
| Full analysis: | https://app.any.run/tasks/c9f0e7af-7d86-4638-ac7e-07770f92cca2 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 15:51:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
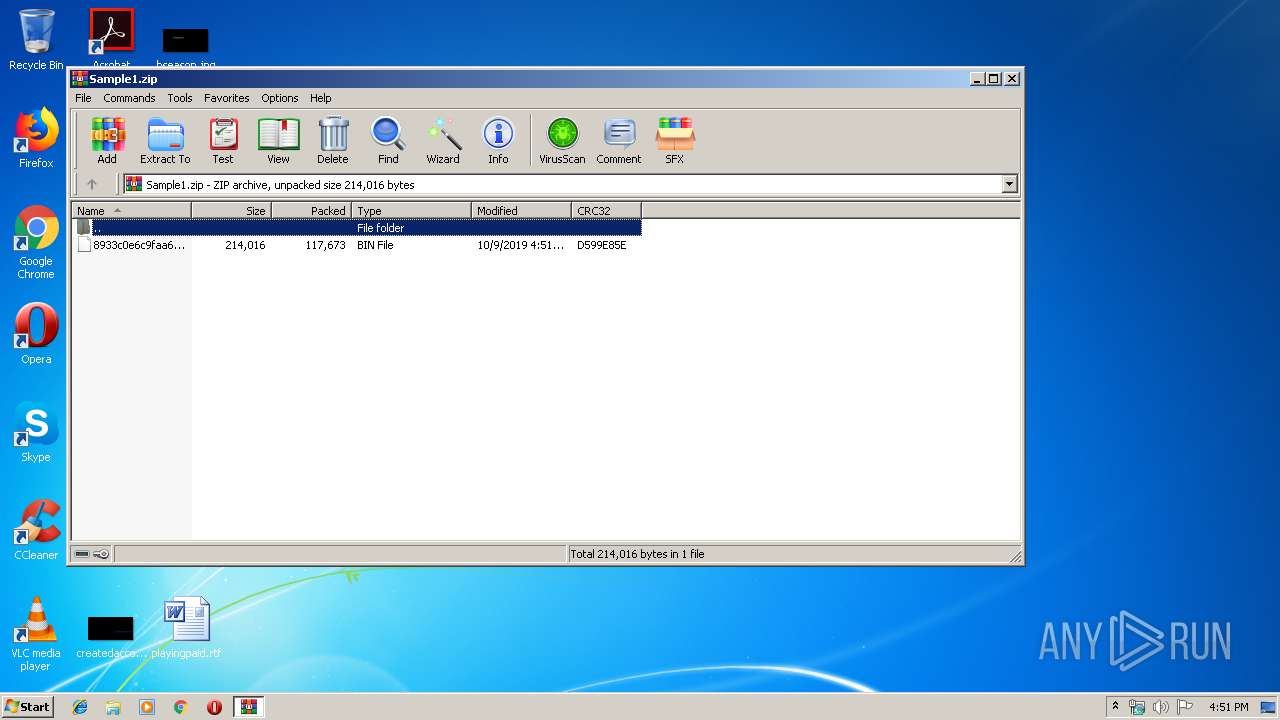
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 0A45EC12B46DD39CB110AD51795C8046 |
| SHA1: | F0E0D169C31336C9B091335FA0F51FD85A5C08D8 |
| SHA256: | 44C818EBFF53A75E6DDFA2AC9D4BBDC889E9756F51E09B36244C02528AF8C2D0 |
| SSDEEP: | 1536:E7gCRKhAqFcjVeRJ2pMcDxRDtLasa2L/6C1tj1/OtktRvwhpEhkK9xnemNy6Gdrm:wjvwfc/tL825j1EktRvk2hkgfQZrm |
MALICIOUS
Application was dropped or rewritten from another process
- 805.exe (PID: 684)
- msptermsizes.exe (PID: 2740)
- msptermsizes.exe (PID: 1760)
- 805.exe (PID: 1004)
- 8puw.exe (PID: 2208)
- msptermsizes.exe (PID: 904)
- msptermsizes.exe (PID: 2140)
- 8pUW.exe (PID: 2136)
Emotet process was detected
- 805.exe (PID: 684)
- 8puw.exe (PID: 2208)
Downloads executable files from the Internet
- powershell.exe (PID: 3324)
Connects to CnC server
- msptermsizes.exe (PID: 1760)
- msptermsizes.exe (PID: 904)
Changes the autorun value in the registry
- msptermsizes.exe (PID: 1760)
- msptermsizes.exe (PID: 904)
EMOTET was detected
- msptermsizes.exe (PID: 904)
- msptermsizes.exe (PID: 1760)
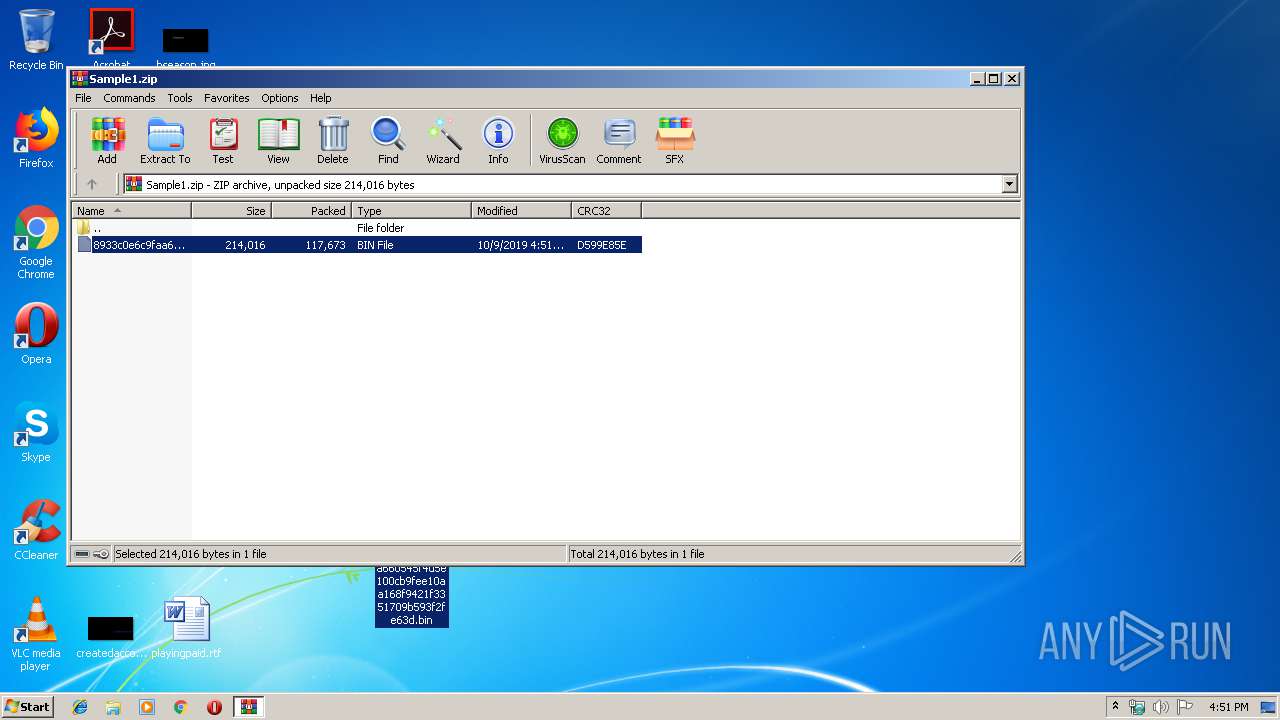
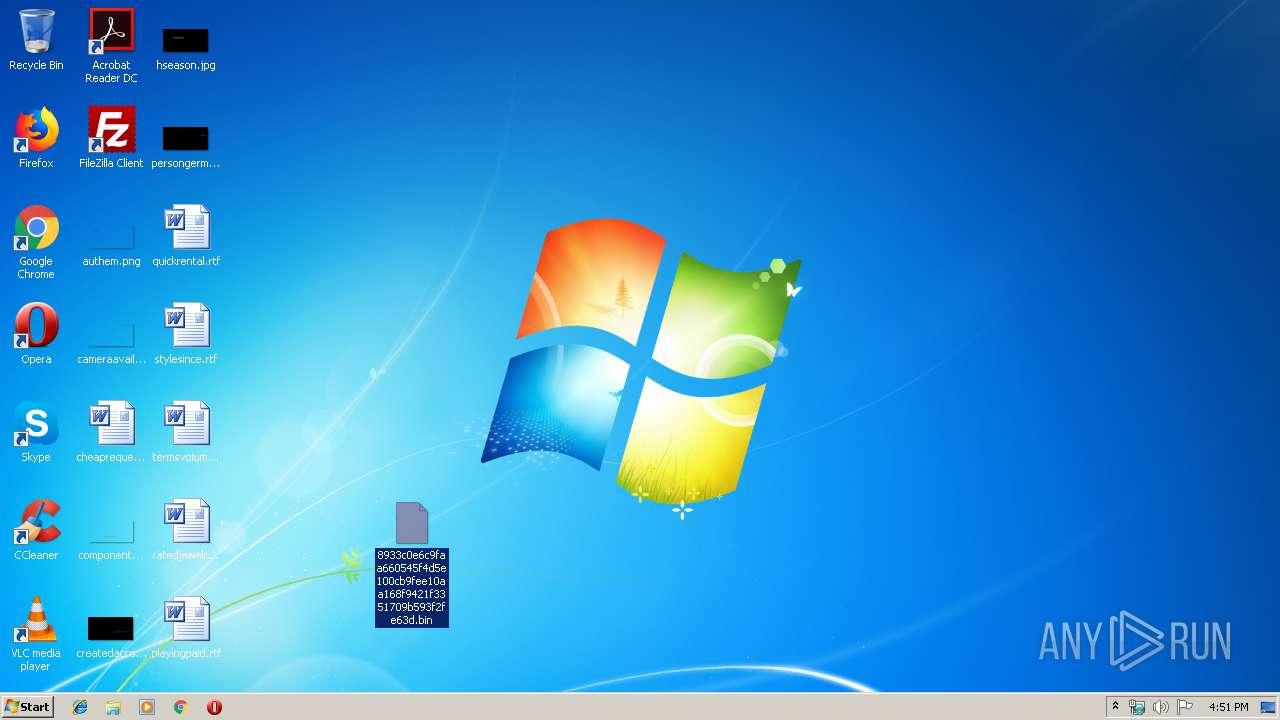
Drops known malicious document
- WinRAR.exe (PID: 3060)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3324)
Executable content was dropped or overwritten
- powershell.exe (PID: 3324)
- 805.exe (PID: 684)
- msptermsizes.exe (PID: 1760)
- 8puw.exe (PID: 2208)
Application launched itself
- 805.exe (PID: 1004)
- msptermsizes.exe (PID: 2740)
Starts itself from another location
- 805.exe (PID: 684)
- msptermsizes.exe (PID: 1760)
- 8puw.exe (PID: 2208)
PowerShell script executed
- powershell.exe (PID: 3324)
Creates files in the user directory
- powershell.exe (PID: 3324)
INFO
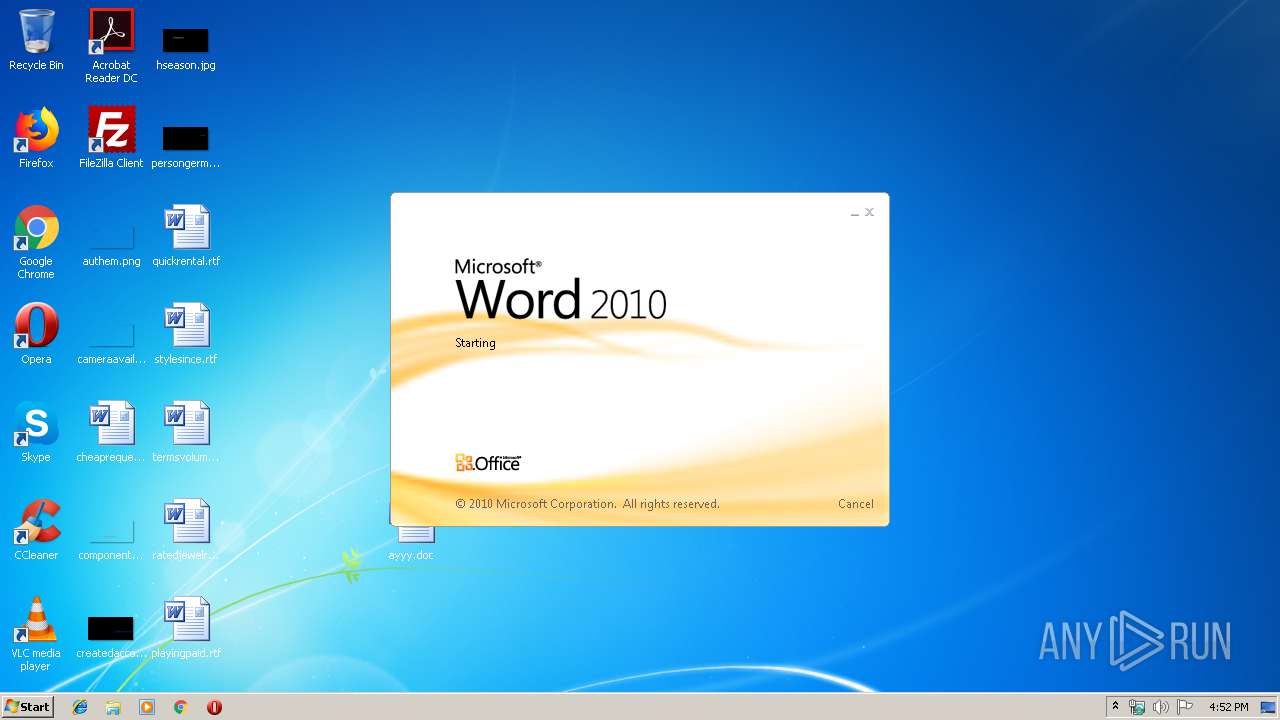
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3152)
Creates files in the user directory
- WINWORD.EXE (PID: 3152)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3060)
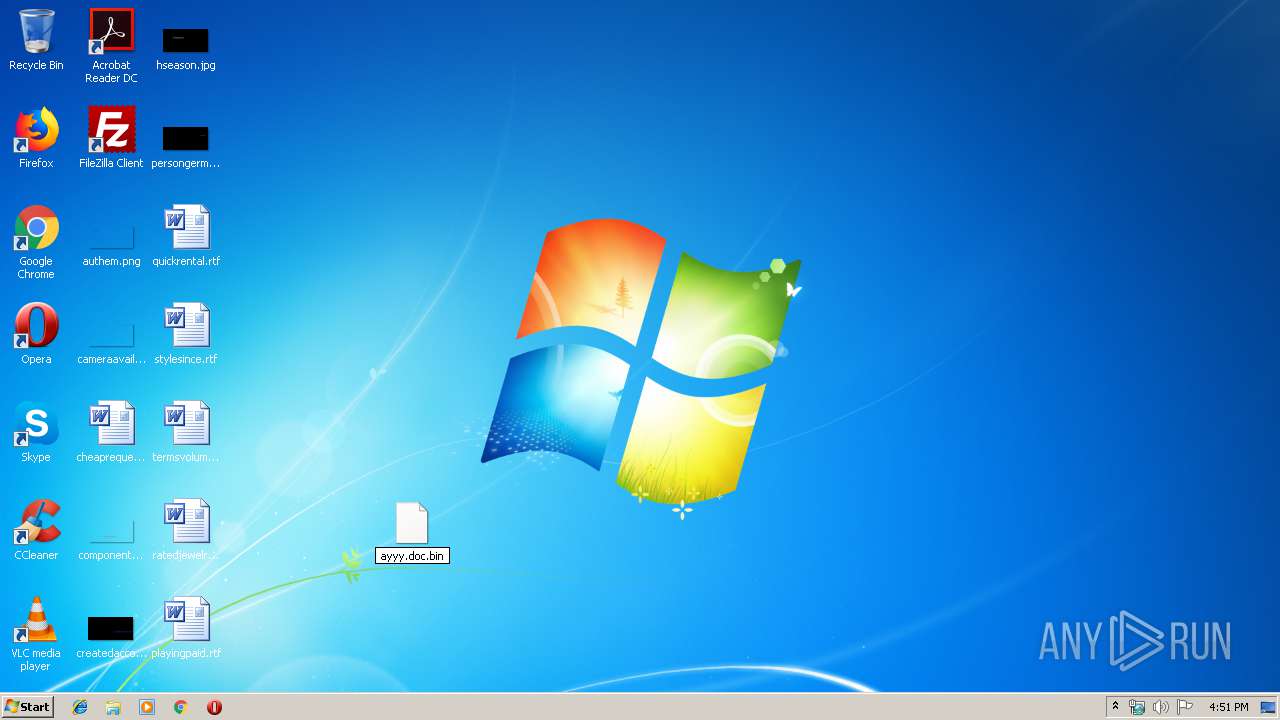
Manual execution by user
- WINWORD.EXE (PID: 3152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:09 15:51:02 |
| ZipCRC: | 0xd599e85e |
| ZipCompressedSize: | 117673 |
| ZipUncompressedSize: | 214016 |
| ZipFileName: | 8933c0e6c9faa660545f4d5e100cb9fee10aa168f9421f3351709b593f2fe63d.bin |
Total processes
48
Monitored processes
11
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | --ae5f3ebb | C:\Users\admin\805.exe | 805.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 904 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1004 | "C:\Users\admin\805.exe" | C:\Users\admin\805.exe | — | powershell.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1760 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\AppData\Local\msptermsizes\8pUW.exe" | C:\Users\admin\AppData\Local\msptermsizes\8pUW.exe | — | msptermsizes.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 8puw.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2208 | --bb33c236 | C:\Users\admin\AppData\Local\msptermsizes\8puw.exe | 8pUW.exe | ||||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2740 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 805.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3060 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Sample1.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3152 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\ayyy.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 313
Read events
2 032
Write events
244
Delete events
37
Modification events
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Sample1.zip | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
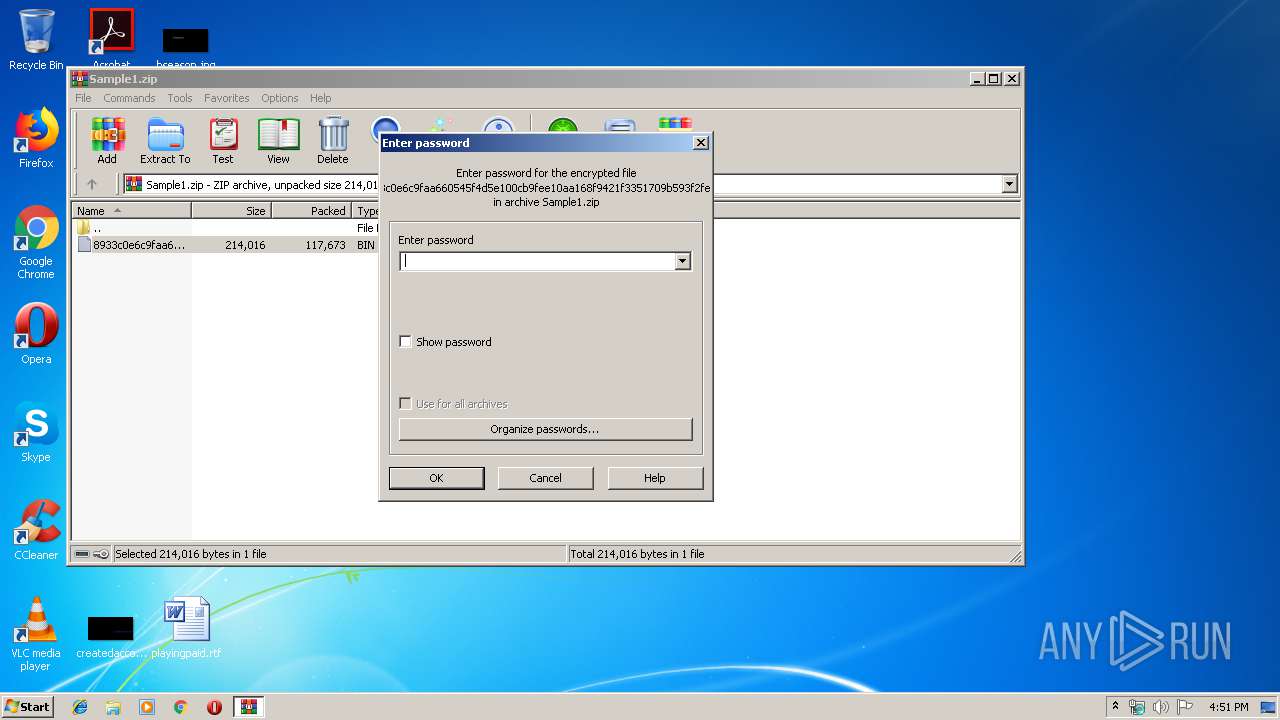
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
4
Suspicious files
3
Text files
2
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR73DA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3324 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CS3VAXCZEPLIM1UBGJ0I.temp | — | |
MD5:— | SHA256:— | |||
| 3152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3837A046.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF15C6A3372D73F61D.TMP | — | |
MD5:— | SHA256:— | |||
| 3152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{373C1289-91BF-495F-BC3C-AFFA8C032F7F}.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{F80722CF-1EC8-4B55-A61B-47BF368D5760}.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\73BB5C44.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3152 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\905D1E4B.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
10
DNS requests
3
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3324 | powershell.exe | GET | 200 | 132.148.42.109:80 | http://scribo-cameroon.com/css/2f3142/ | US | executable | 612 Kb | suspicious |
904 | msptermsizes.exe | POST | 200 | 91.83.93.105:8080 | http://91.83.93.105:8080/pdf/ | HU | binary | 1.38 Mb | malicious |
904 | msptermsizes.exe | GET | 200 | 37.187.5.82:8080 | http://37.187.5.82:8080/whoami.php | FR | text | 11 b | malicious |
1760 | msptermsizes.exe | POST | 200 | 91.83.93.105:8080 | http://91.83.93.105:8080/json/devices/ | HU | binary | 142 Kb | malicious |
904 | msptermsizes.exe | POST | 200 | 91.83.93.105:8080 | http://91.83.93.105:8080/loadan/enabled/ringin/ | HU | binary | 148 b | malicious |
904 | msptermsizes.exe | POST | 200 | 37.187.5.82:8080 | http://37.187.5.82:8080/odbc/sym/ringin/merge/ | FR | binary | 132 b | malicious |
904 | msptermsizes.exe | GET | 200 | 37.187.5.82:8080 | http://37.187.5.82:8080/whoami.php | FR | text | 11 b | malicious |
904 | msptermsizes.exe | POST | 200 | 37.187.5.82:8080 | http://37.187.5.82:8080/ban/ | FR | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3324 | powershell.exe | 67.227.172.210:443 | retos-enformaherbal.com | Liquid Web, L.L.C | US | unknown |
3324 | powershell.exe | 146.66.89.114:443 | georgereports.com | — | US | unknown |
3324 | powershell.exe | 132.148.42.109:80 | scribo-cameroon.com | GoDaddy.com, LLC | US | suspicious |
1760 | msptermsizes.exe | 91.83.93.105:8080 | — | Invitech Megoldasok Zrt. | HU | malicious |
904 | msptermsizes.exe | 91.83.93.105:8080 | — | Invitech Megoldasok Zrt. | HU | malicious |
904 | msptermsizes.exe | 37.187.5.82:8080 | — | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
retos-enformaherbal.com |
| unknown |
georgereports.com |
| unknown |
scribo-cameroon.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3324 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3324 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3324 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1760 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
1760 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
904 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
904 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
904 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
904 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
10 ETPRO signatures available at the full report