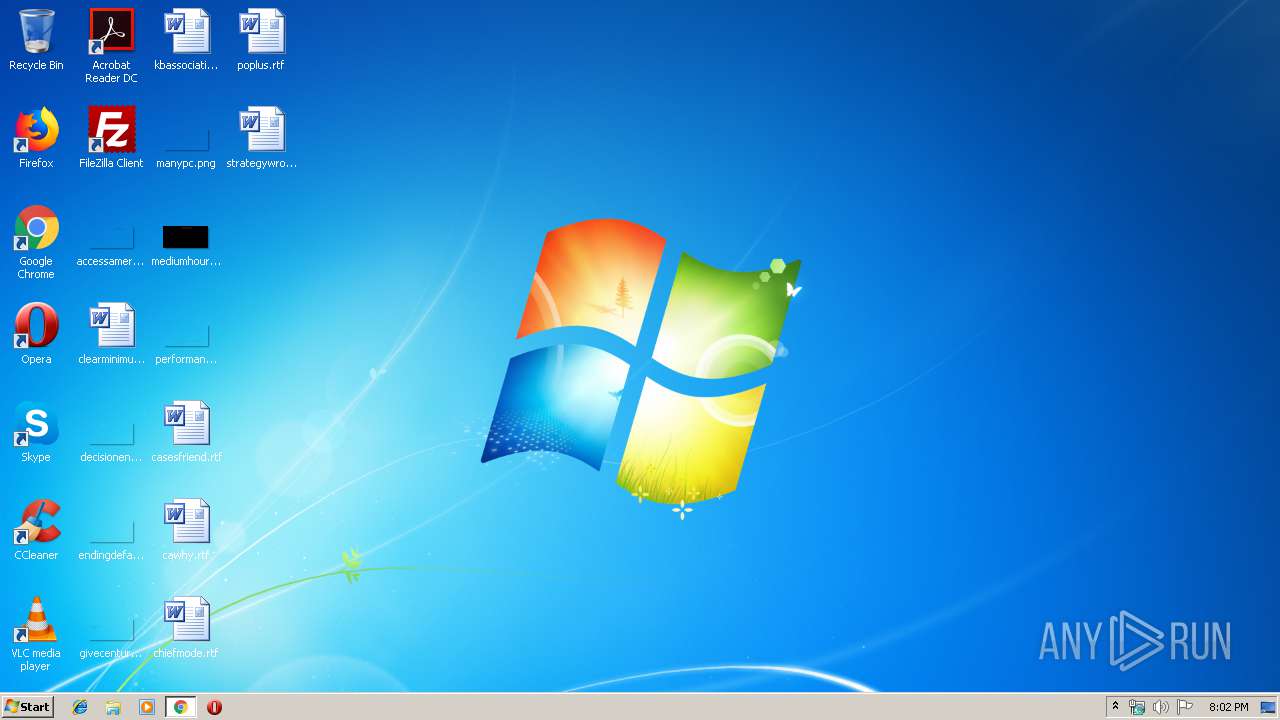
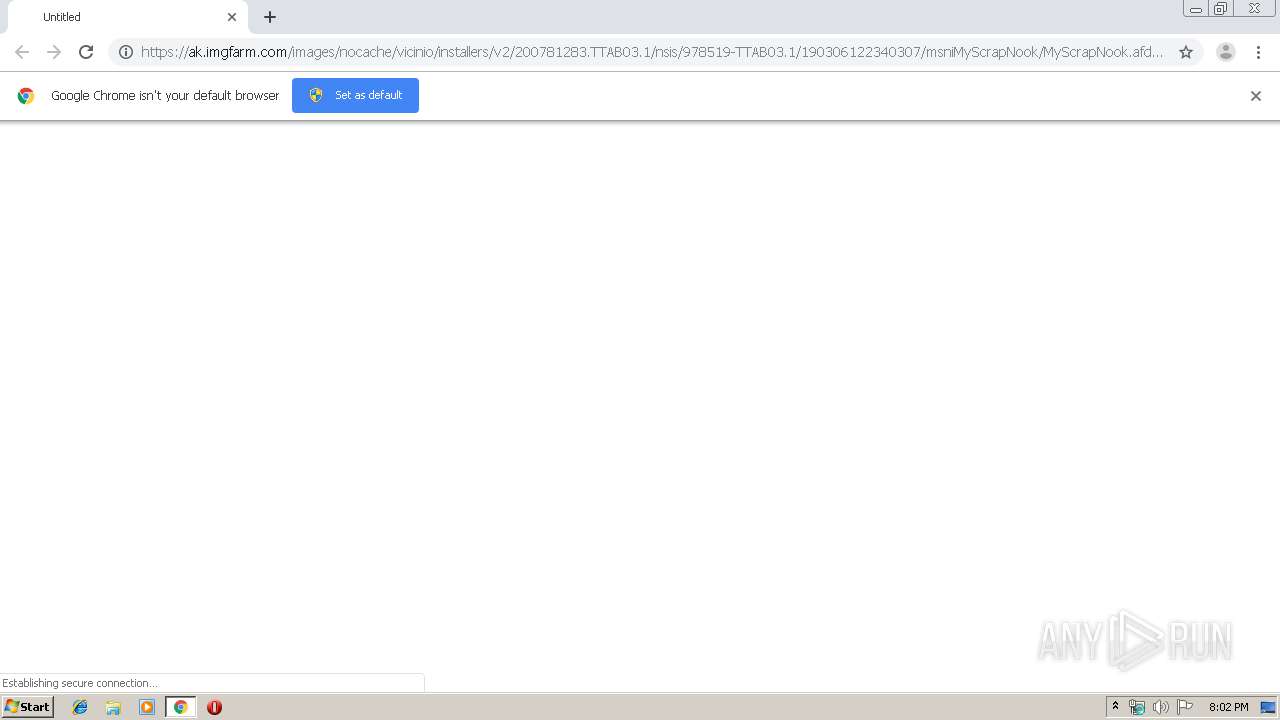
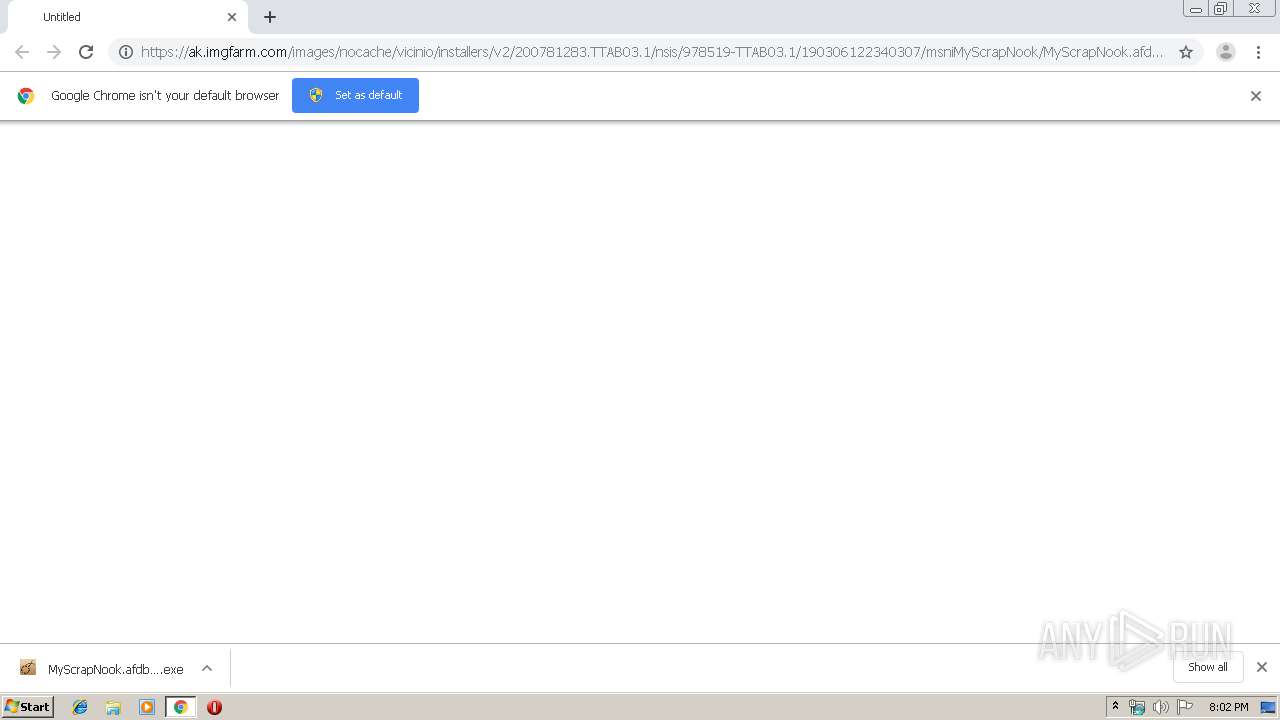
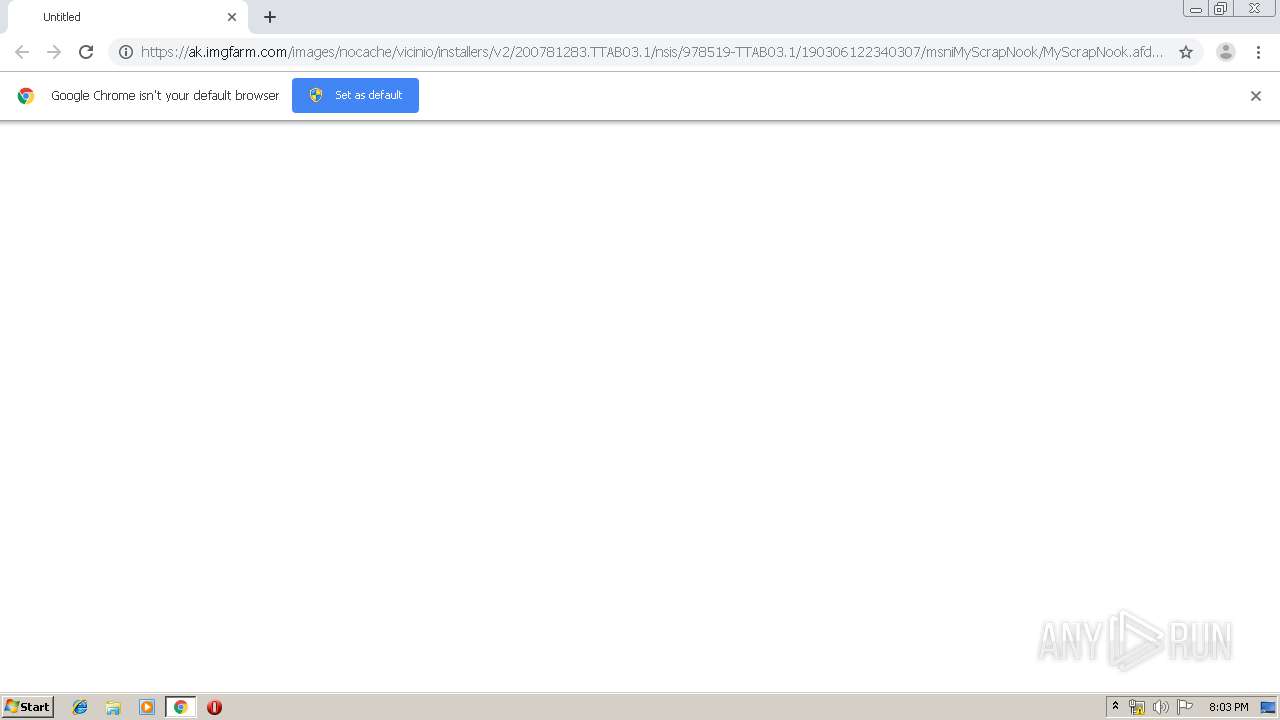
| URL: | https://ak.imgfarm.com/images/nocache/vicinio/installers/v2/200781283.TTAB03.1/nsis/978519-TTAB03.1/190306122340307/msniMyScrapNook/MyScrapNook.afdb8f3d192143faba4b8ce803115f49.exe |
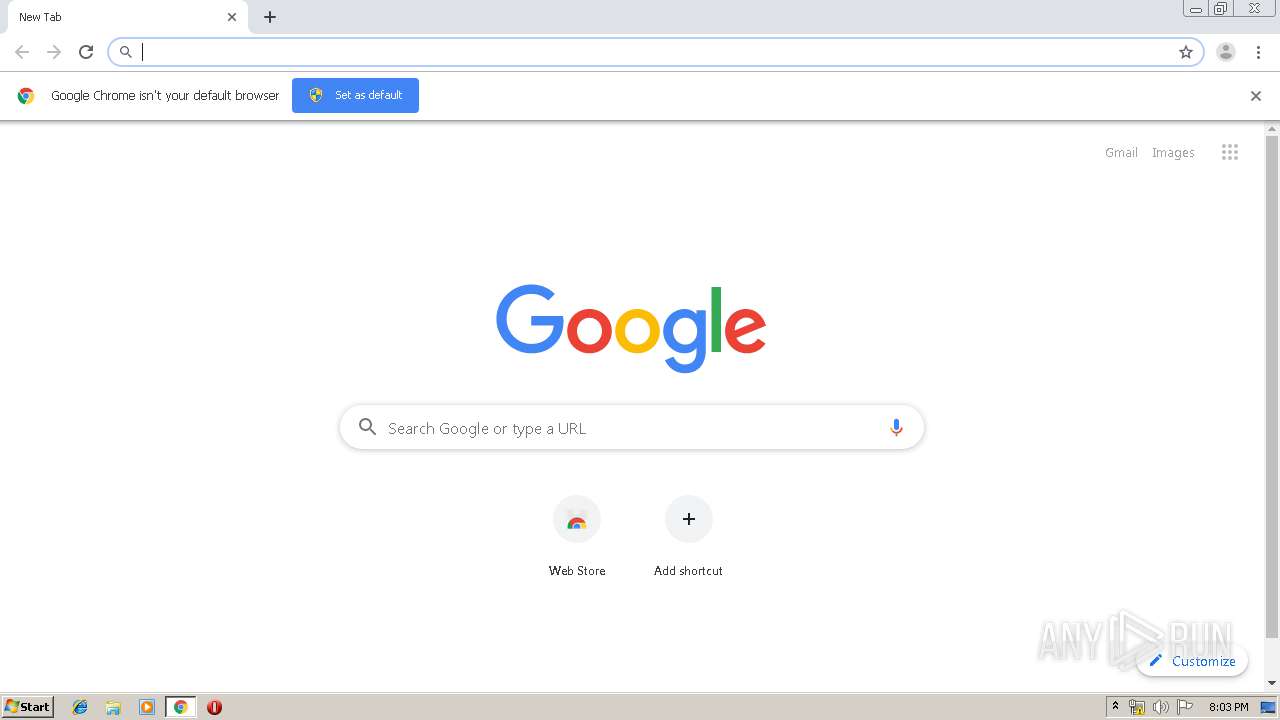
| Full analysis: | https://app.any.run/tasks/3c74c469-431c-4581-a175-575121786ed6 |
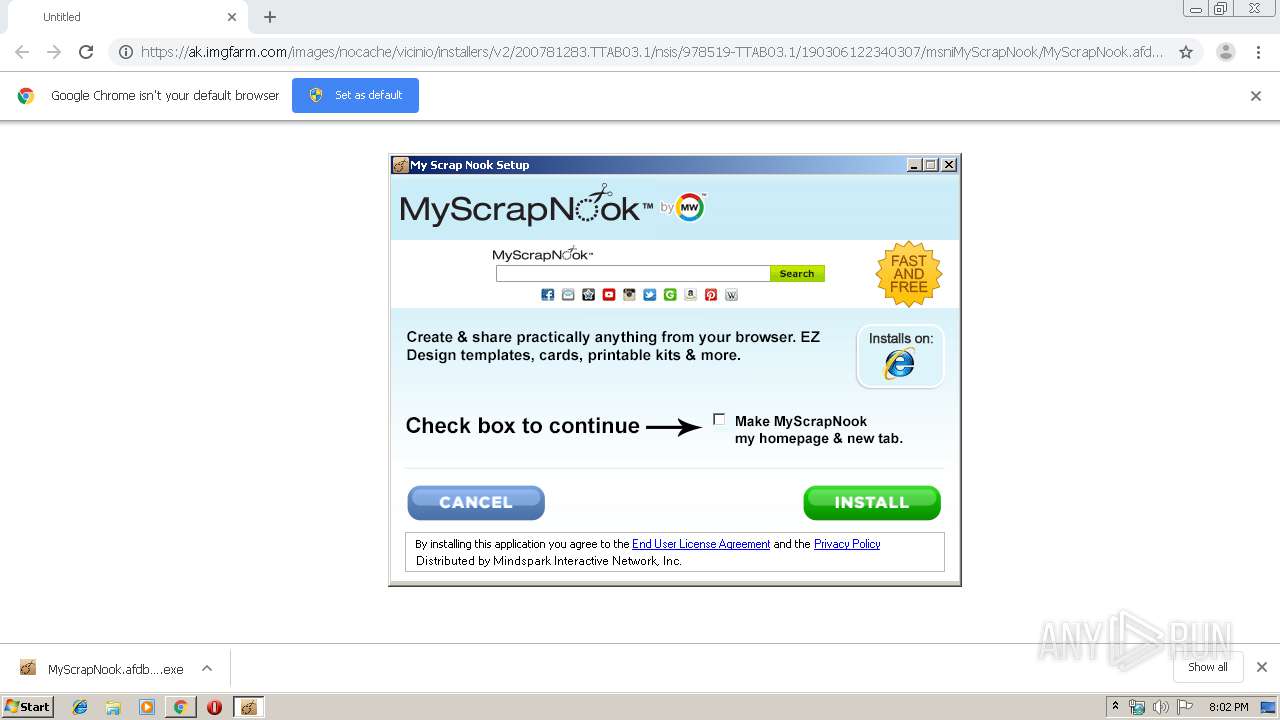
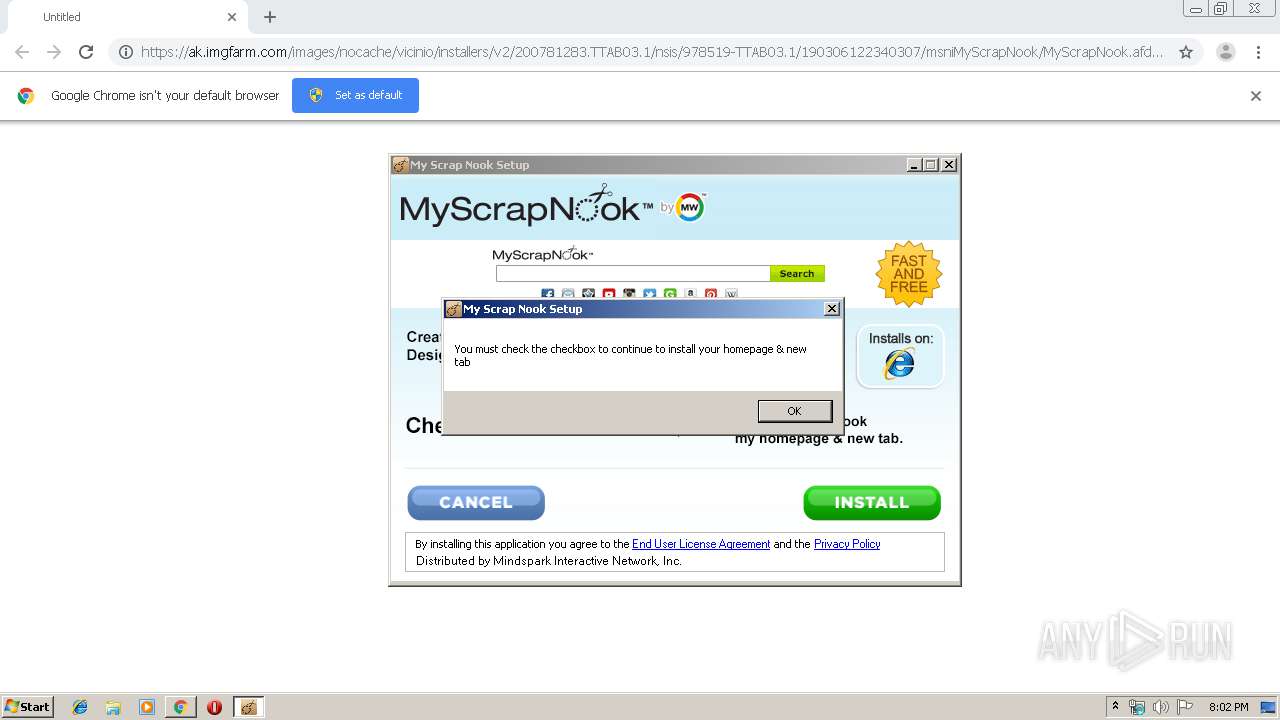
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 20:02:13 |
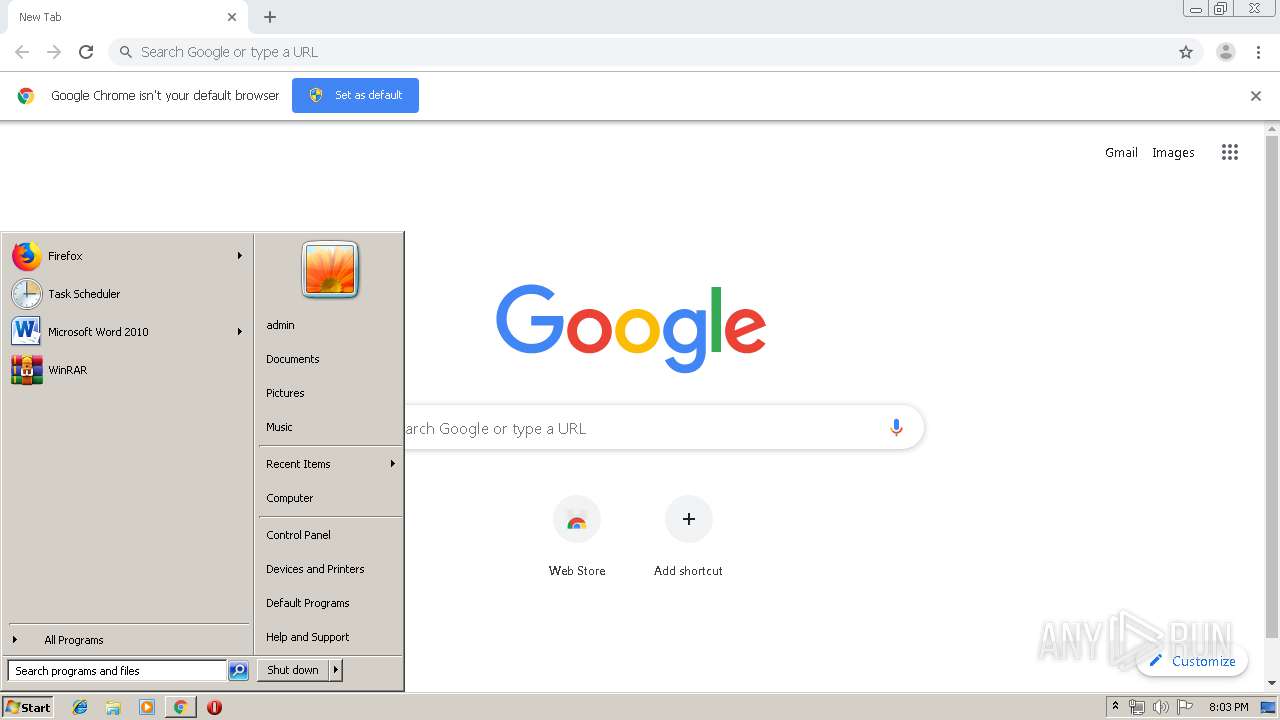
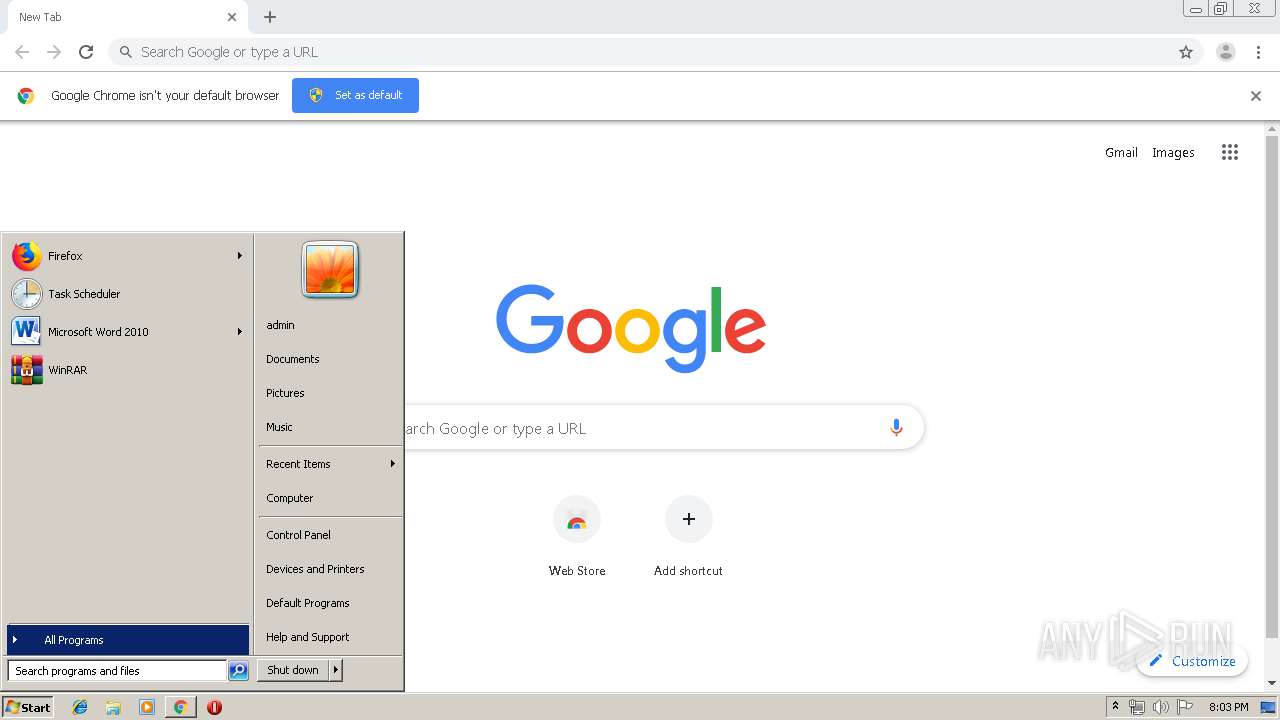
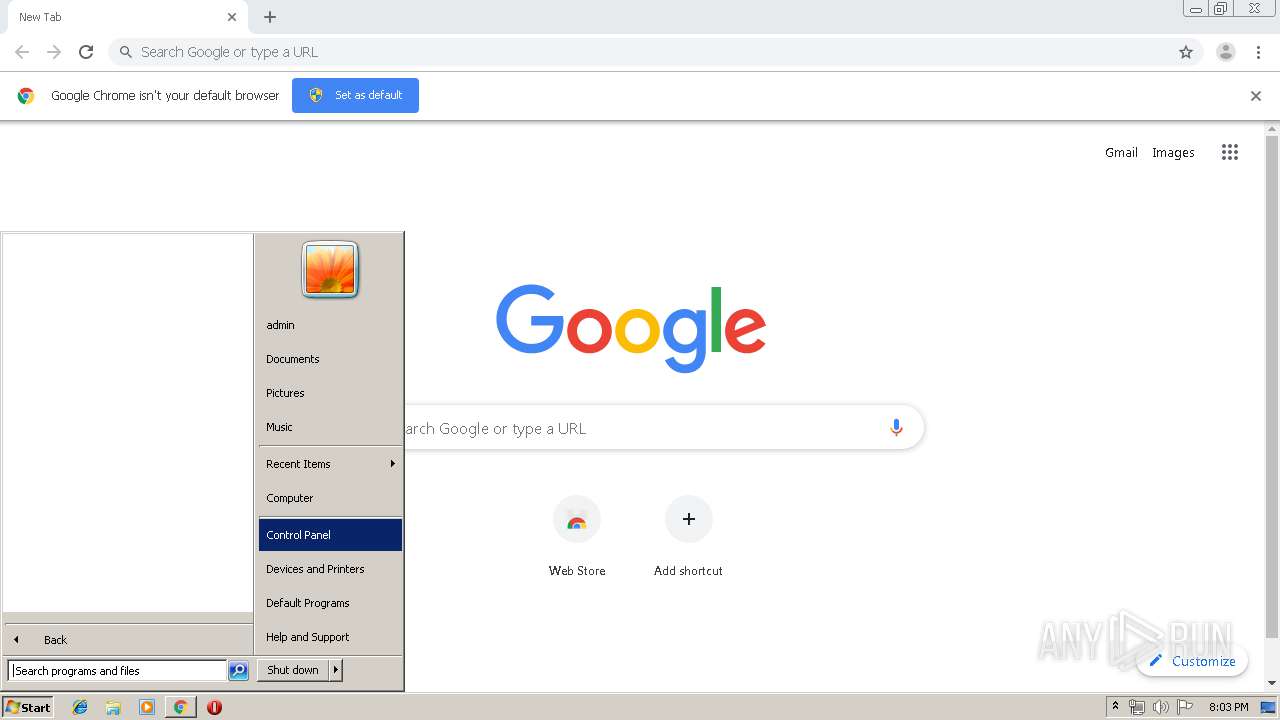
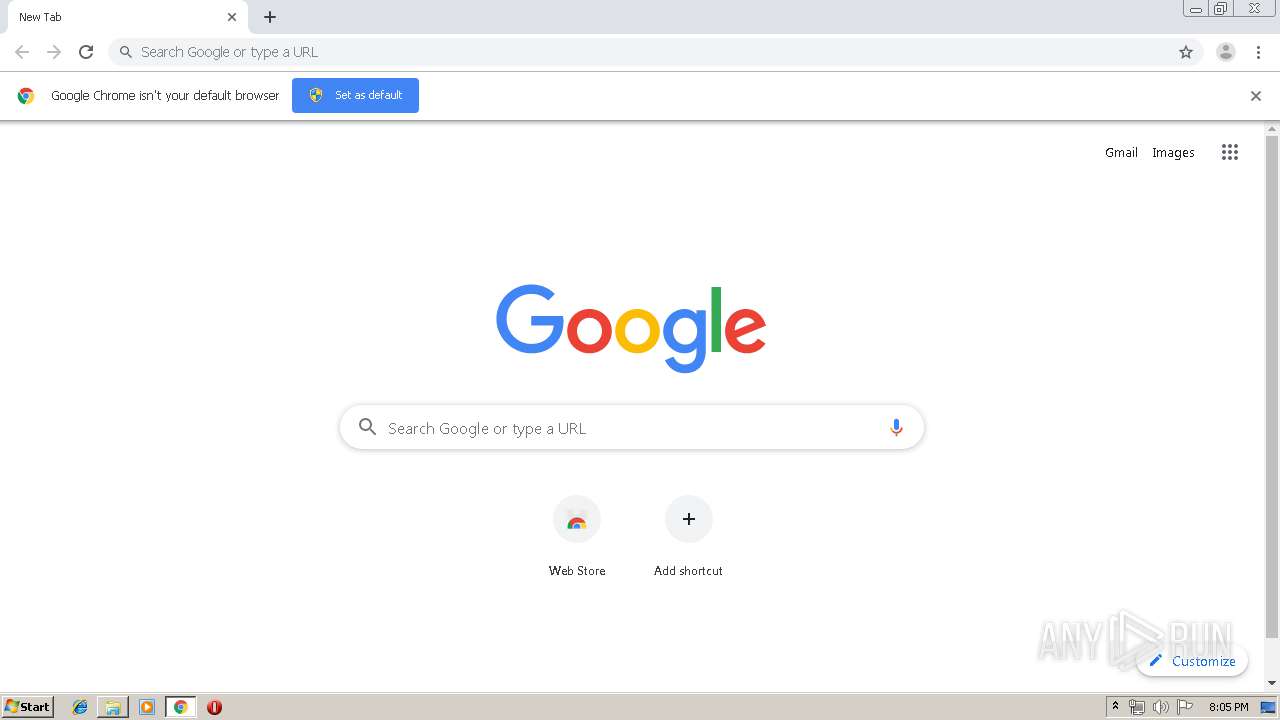
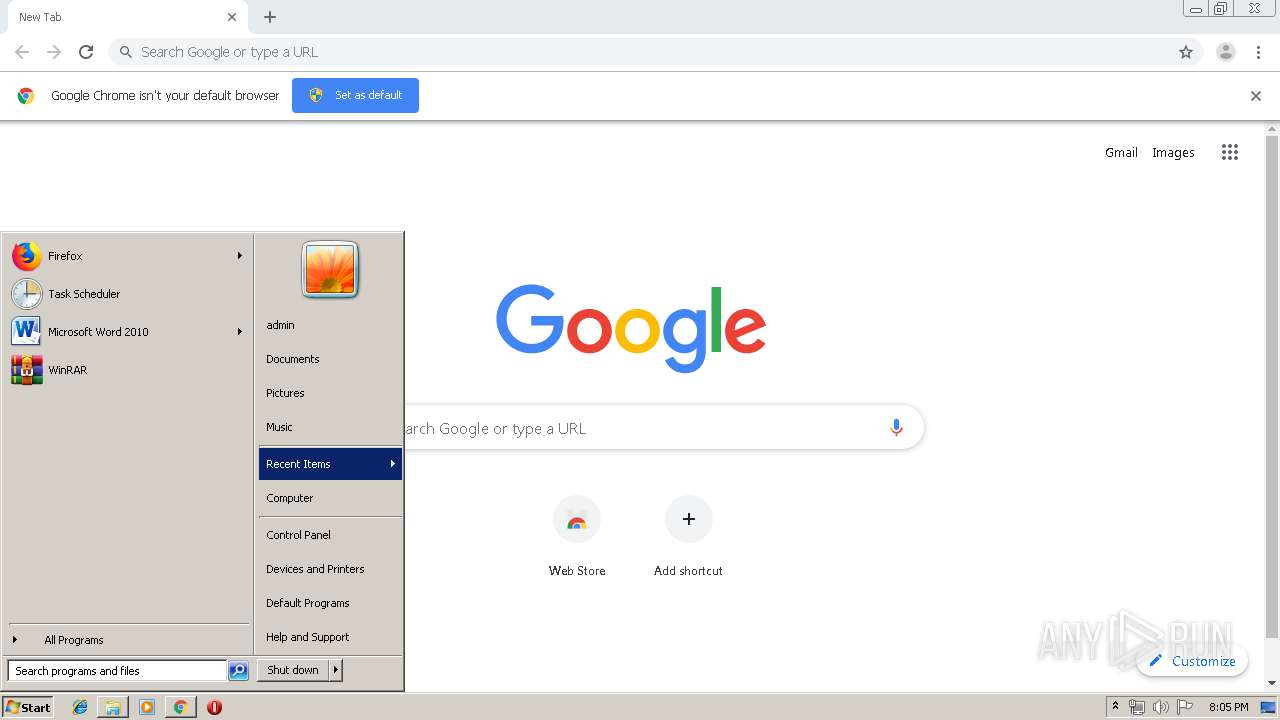
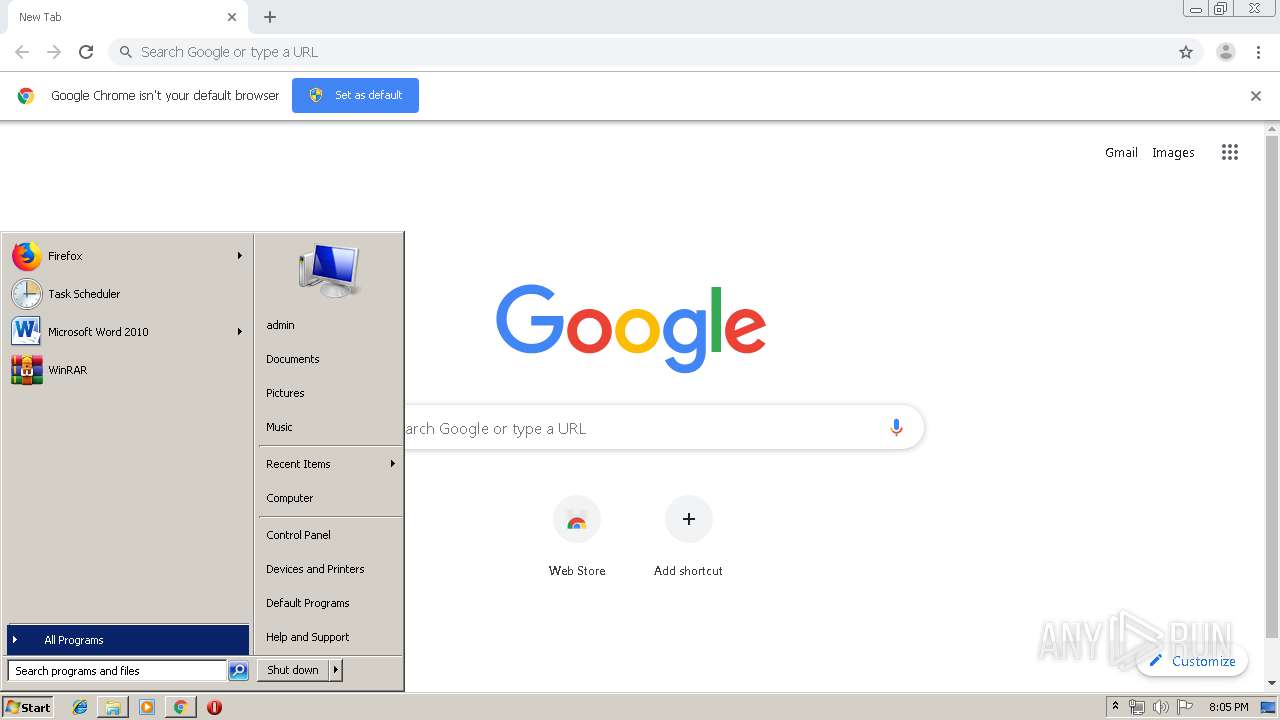
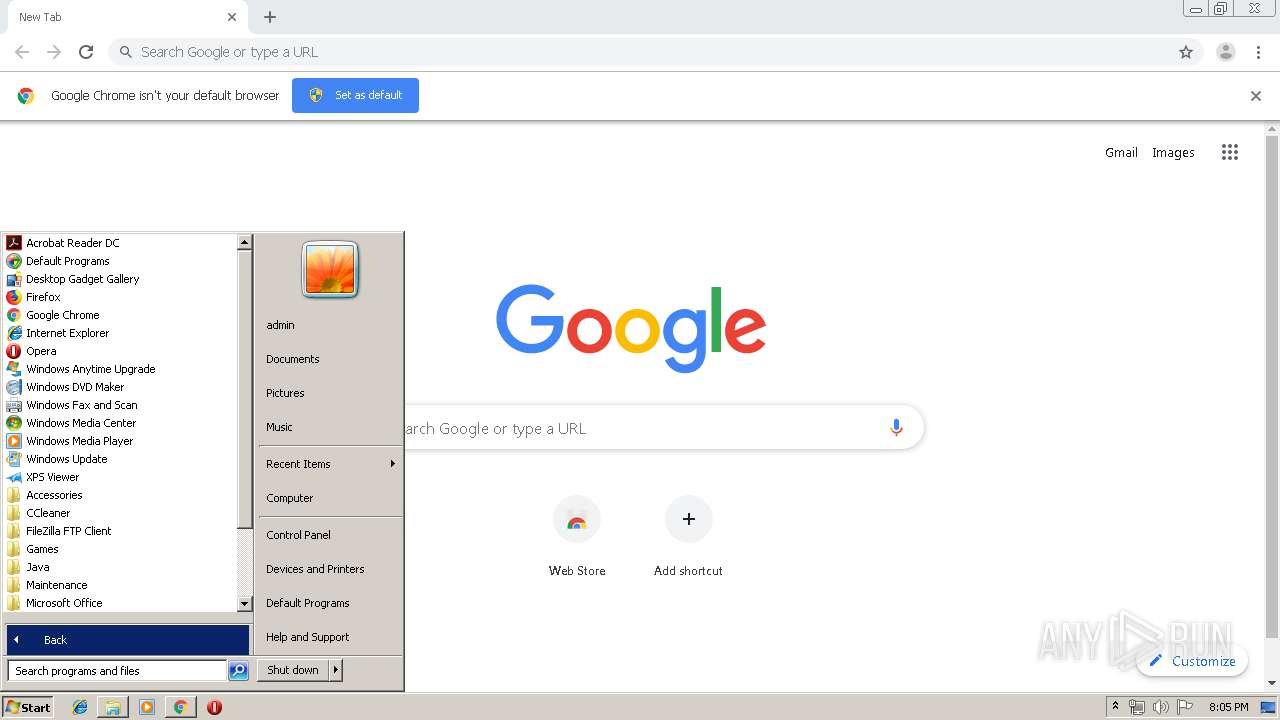
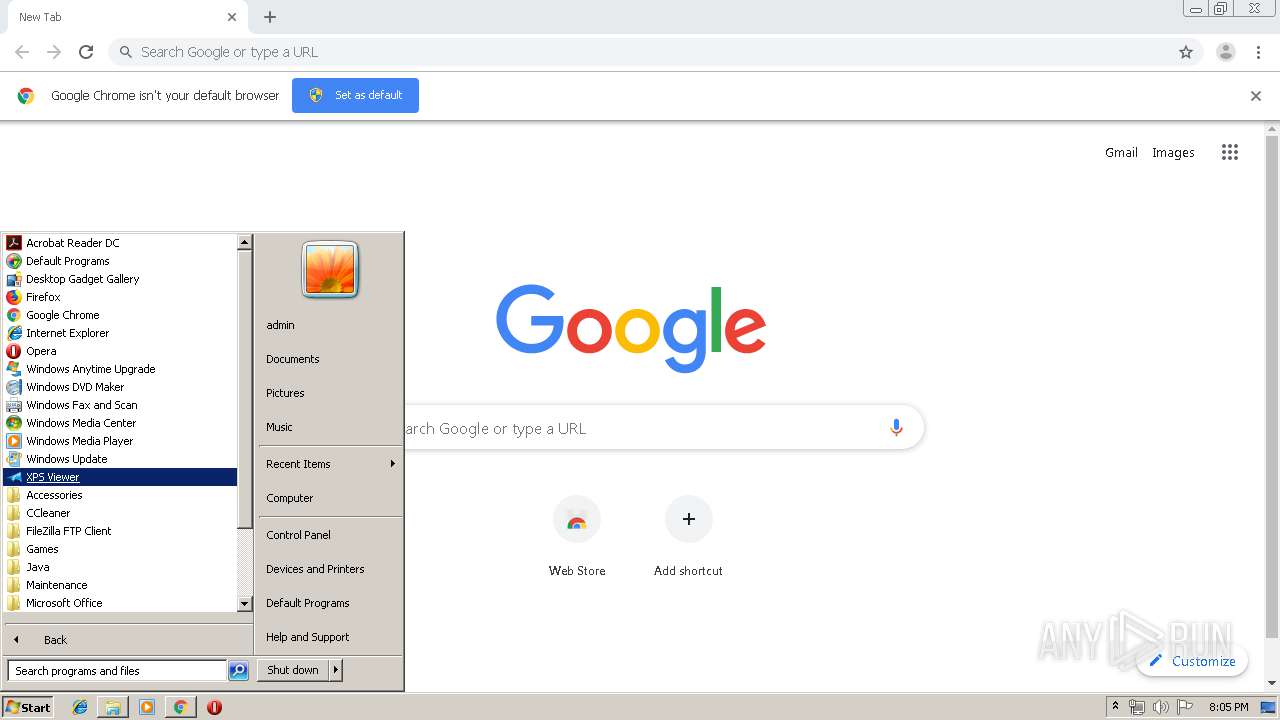
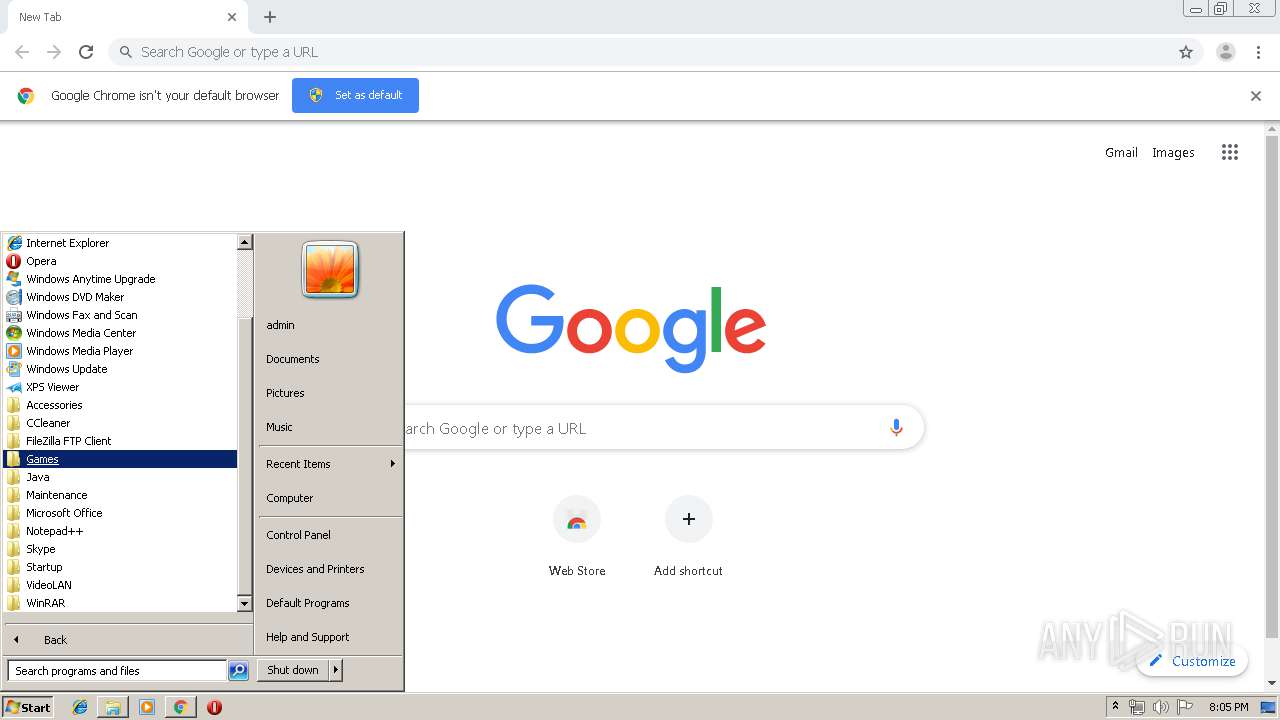
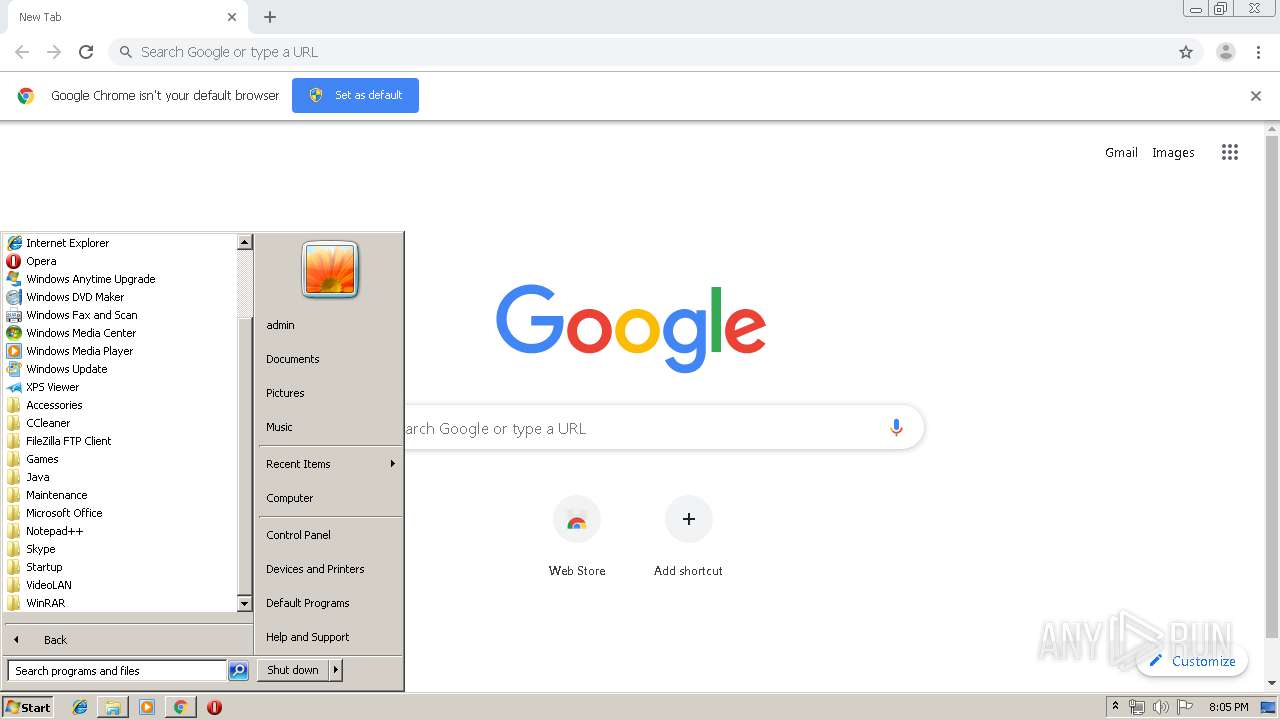
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9B24C3808F05499A6C955BD9FB0E2FF0 |
| SHA1: | BCD82520CE775839270CCFADEADC78617AAF180C |
| SHA256: | 44C5753D9AB481E810933522398EDA6B923273BA35DC2DD71C50D5CB4F0A55DC |
| SSDEEP: | 3:N8VEKCA0GEaAp3LWgOXBcVBCdgbuBcRfPkWVTUX/STMAVw2GU8VJ8RWDEKFO:2eTLpigOXBkBCYuqRvVTUX/KV18VJ82W |
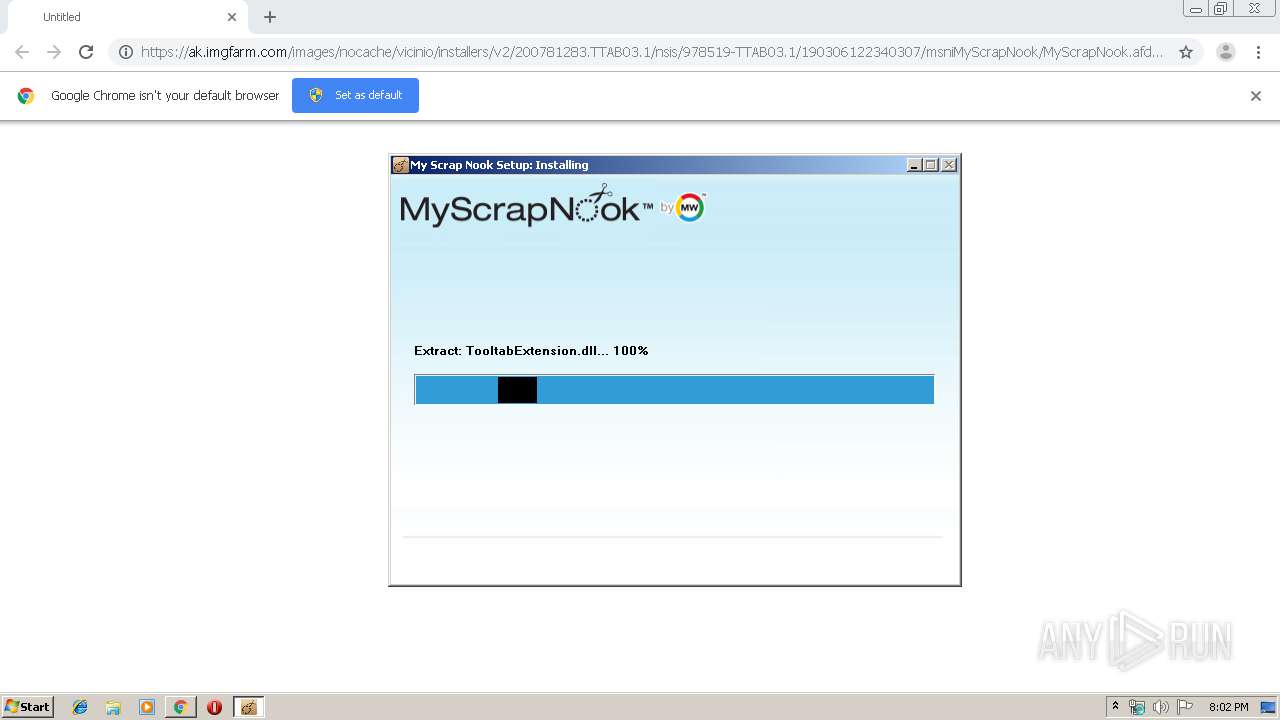
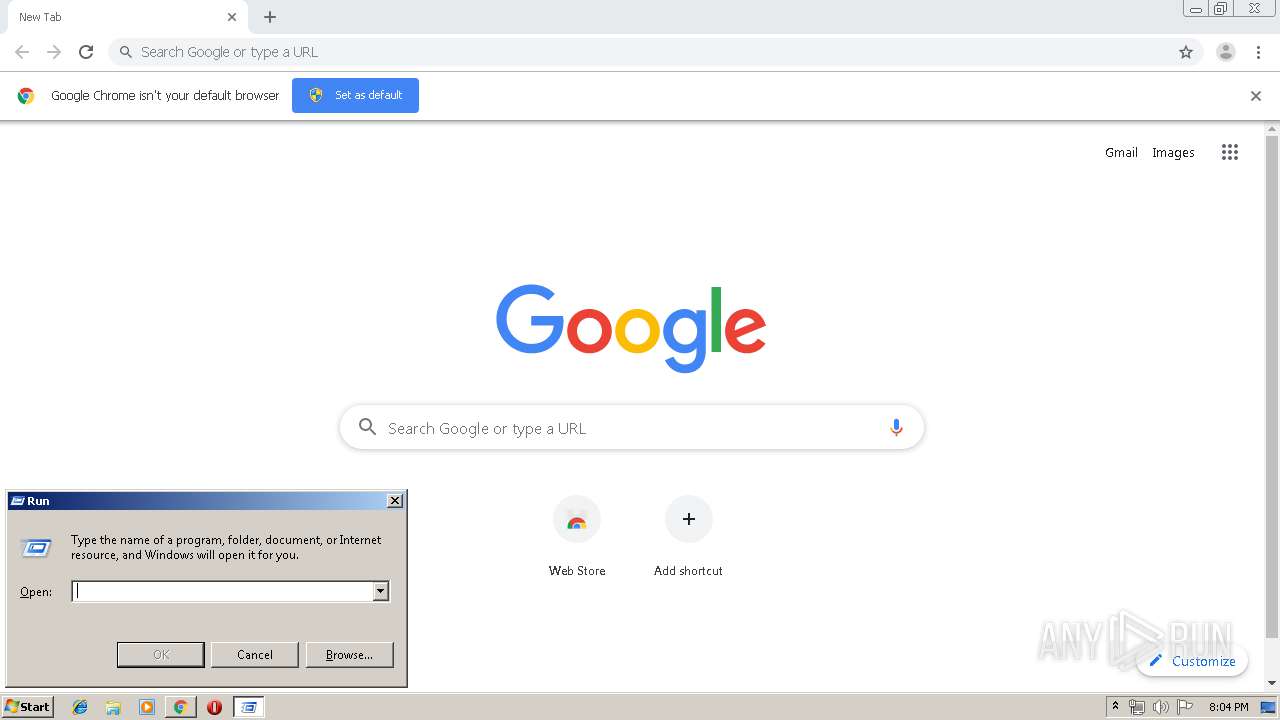
MALICIOUS
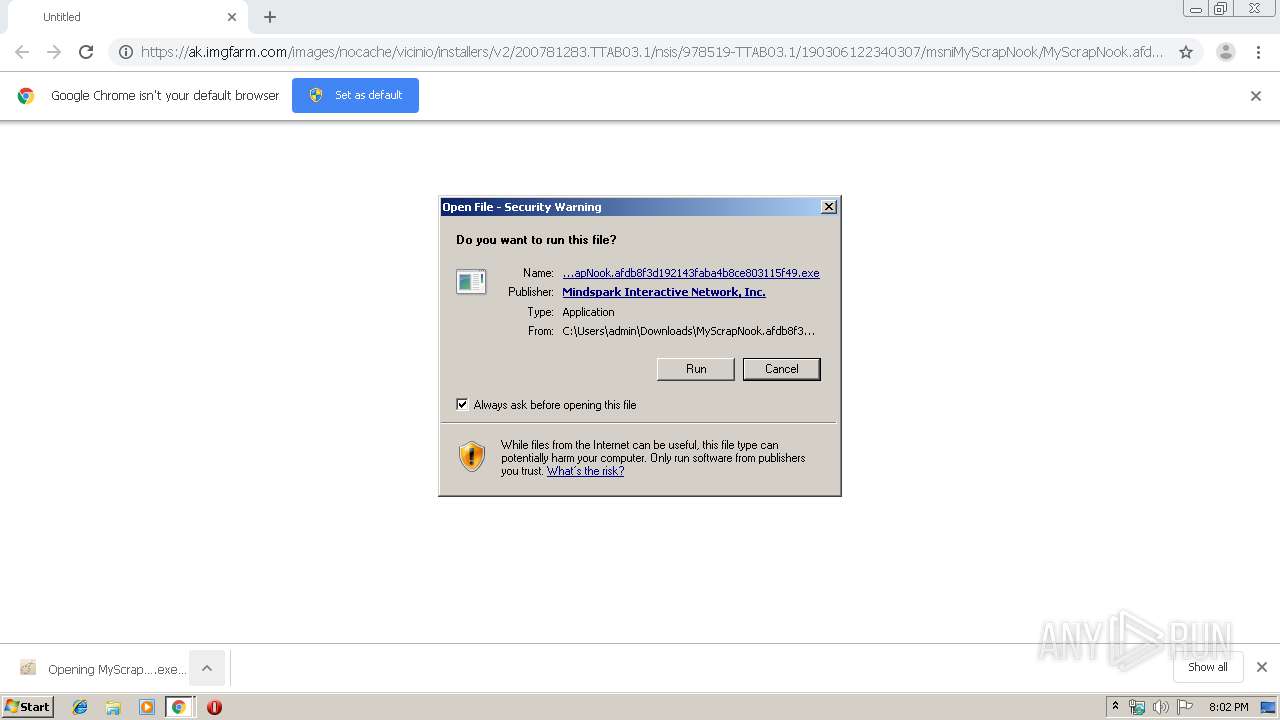
Loads dropped or rewritten executable
- MyScrapNook.afdb8f3d192143faba4b8ce803115f49.exe (PID: 2380)
Application was dropped or rewritten from another process
- MyScrapNook.afdb8f3d192143faba4b8ce803115f49.exe (PID: 2380)
SUSPICIOUS
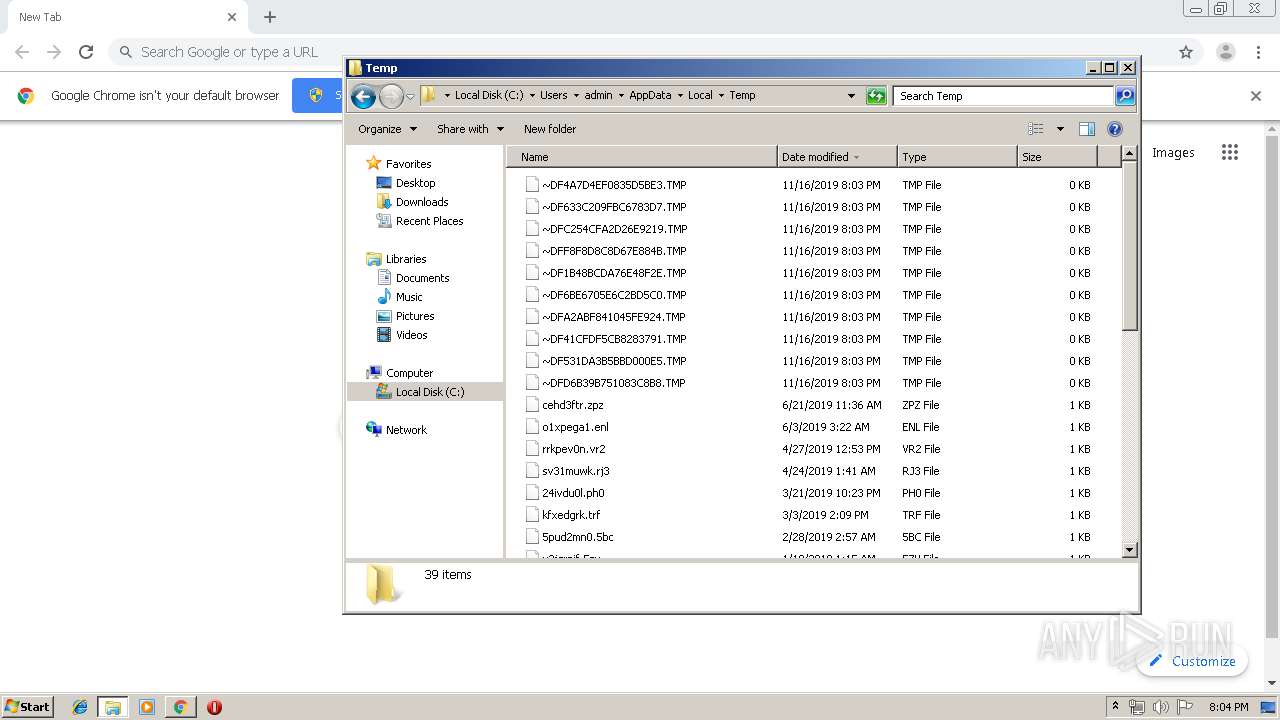
Executable content was dropped or overwritten
- chrome.exe (PID: 1576)
- chrome.exe (PID: 4056)
- MyScrapNook.afdb8f3d192143faba4b8ce803115f49.exe (PID: 2380)
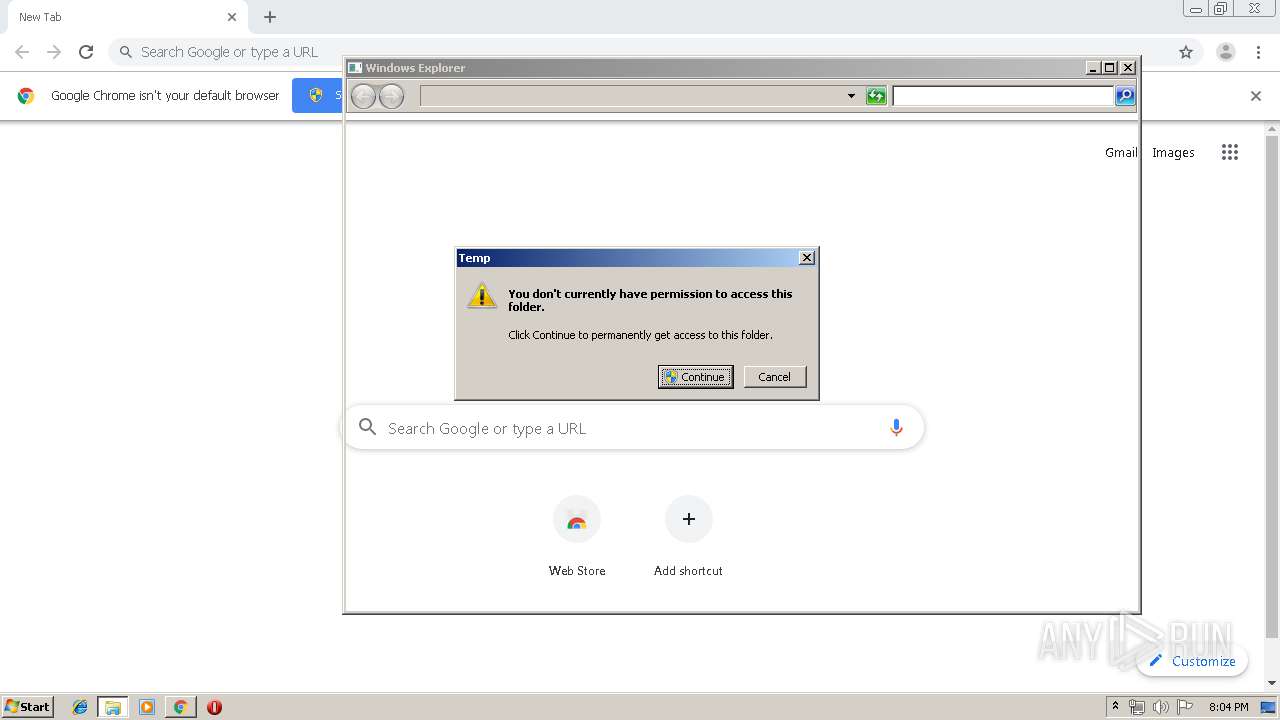
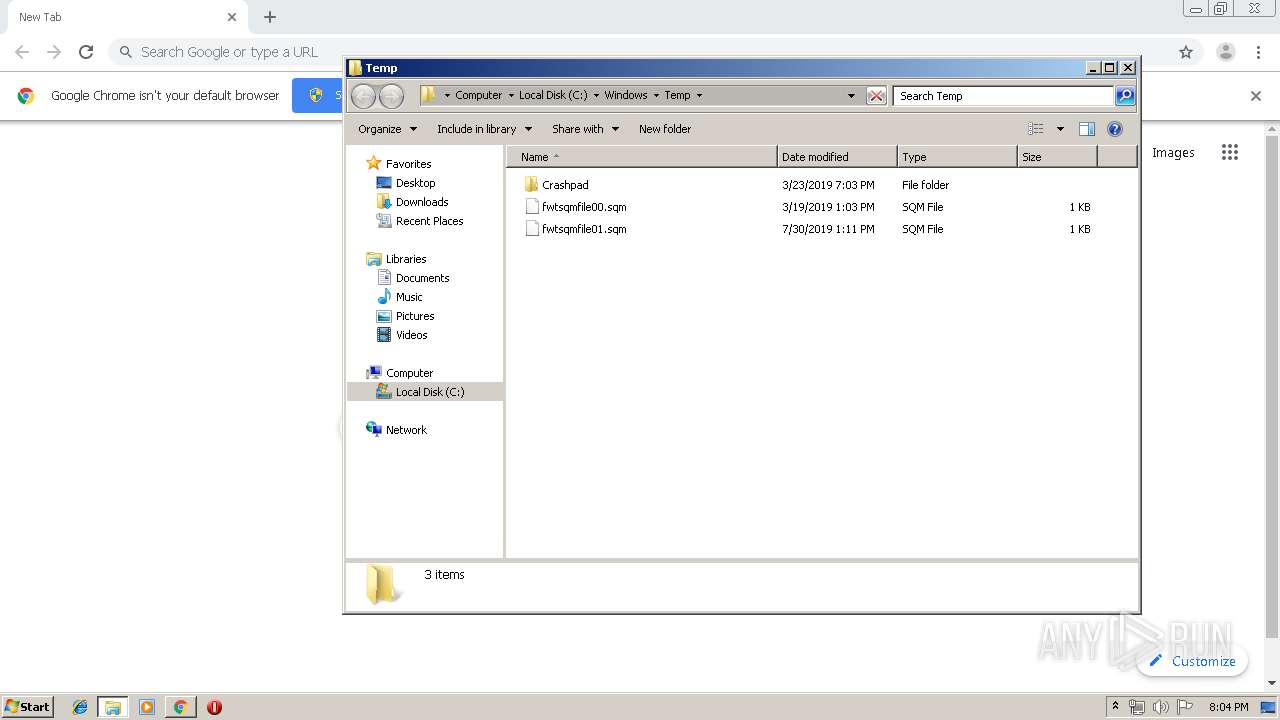
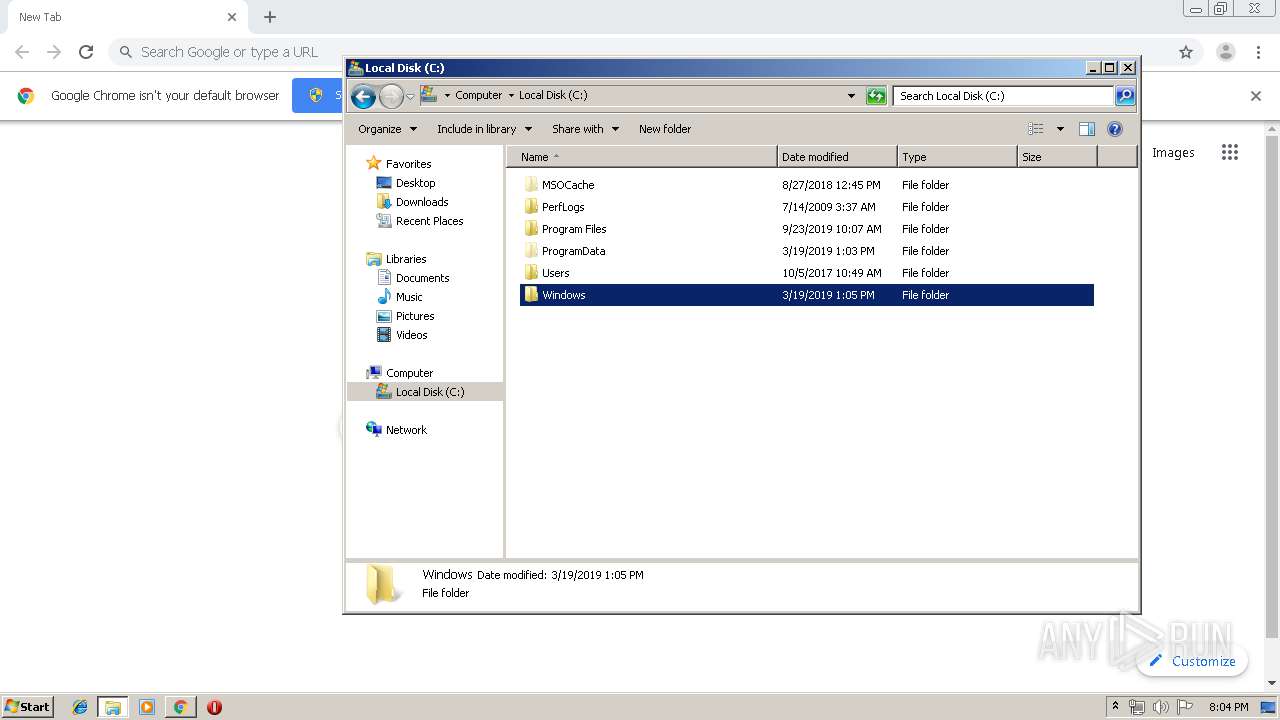
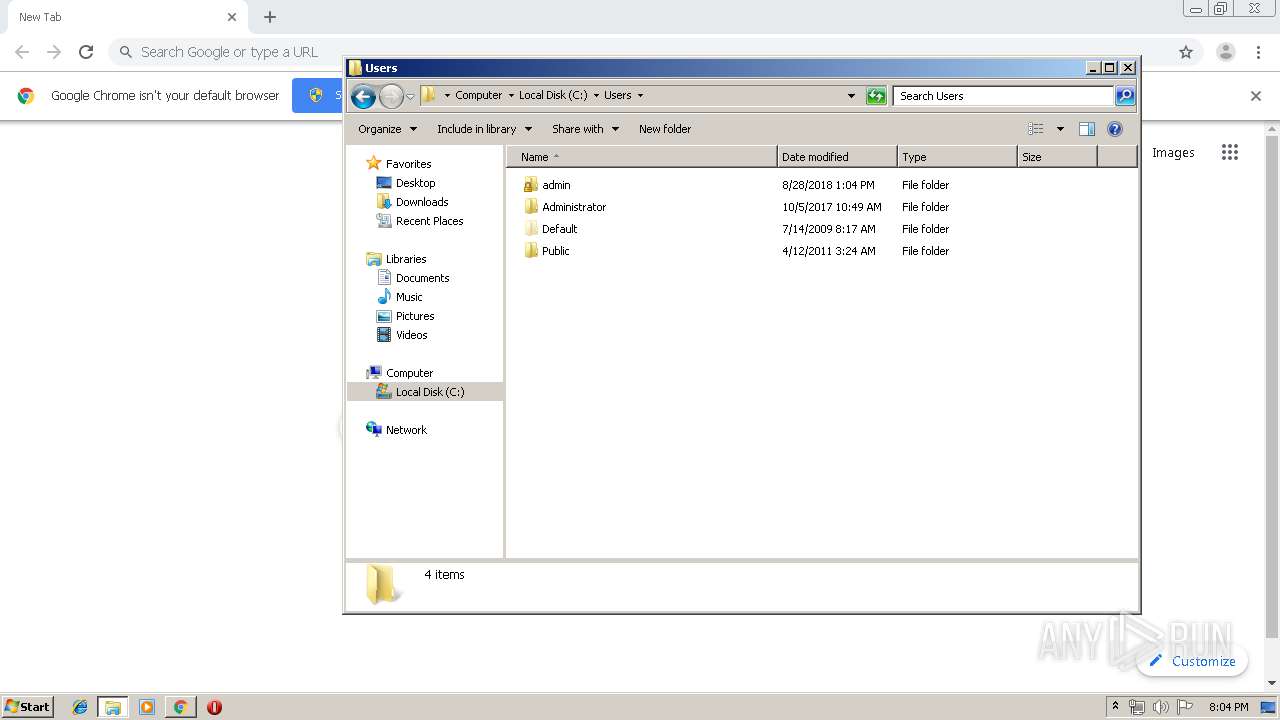
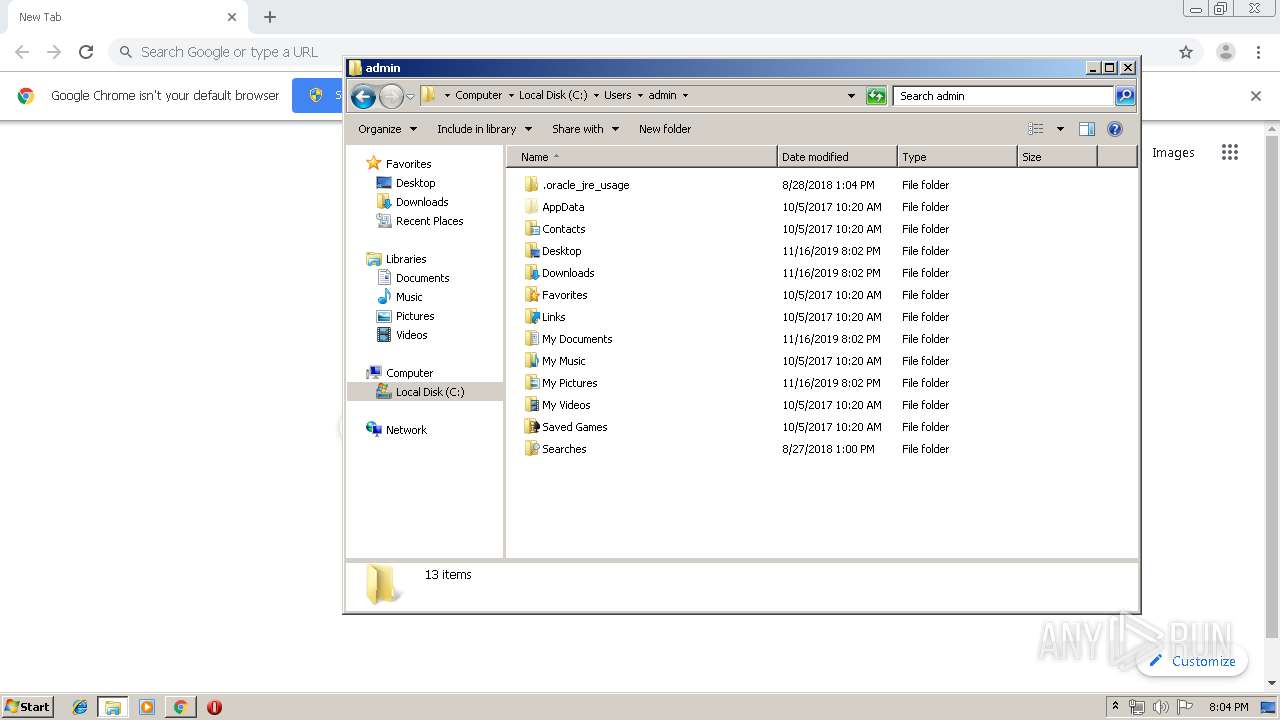
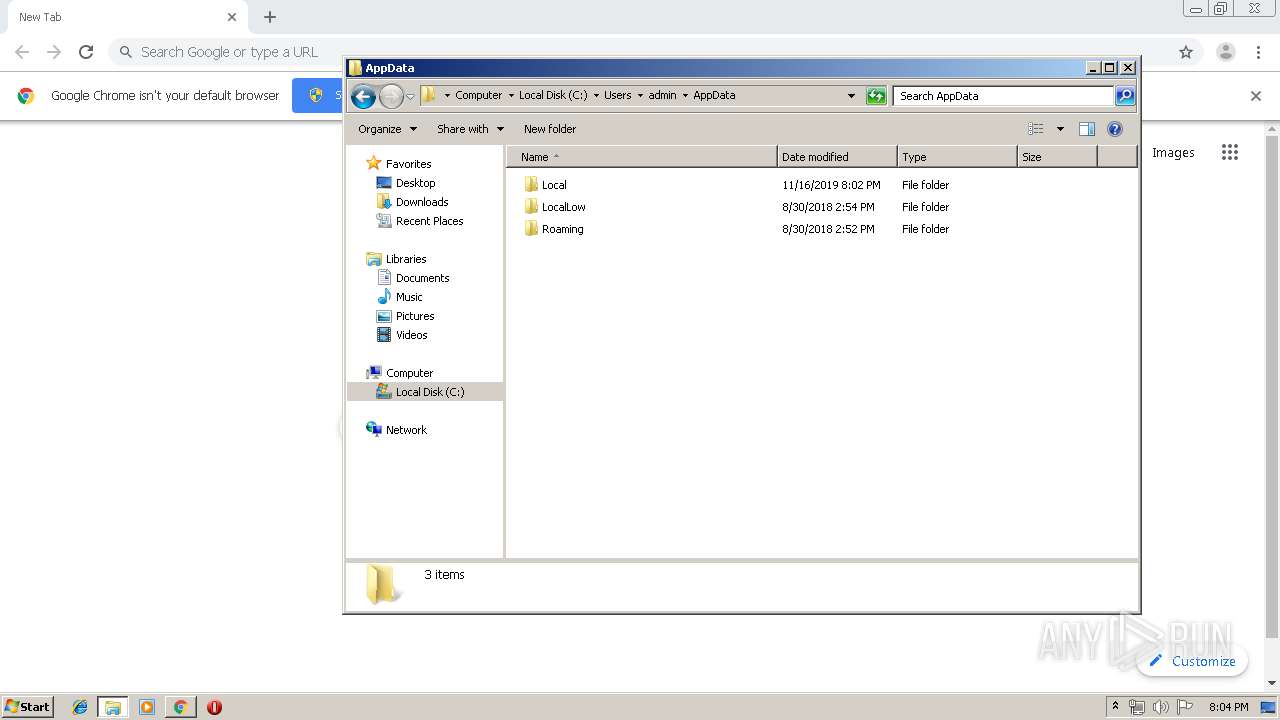
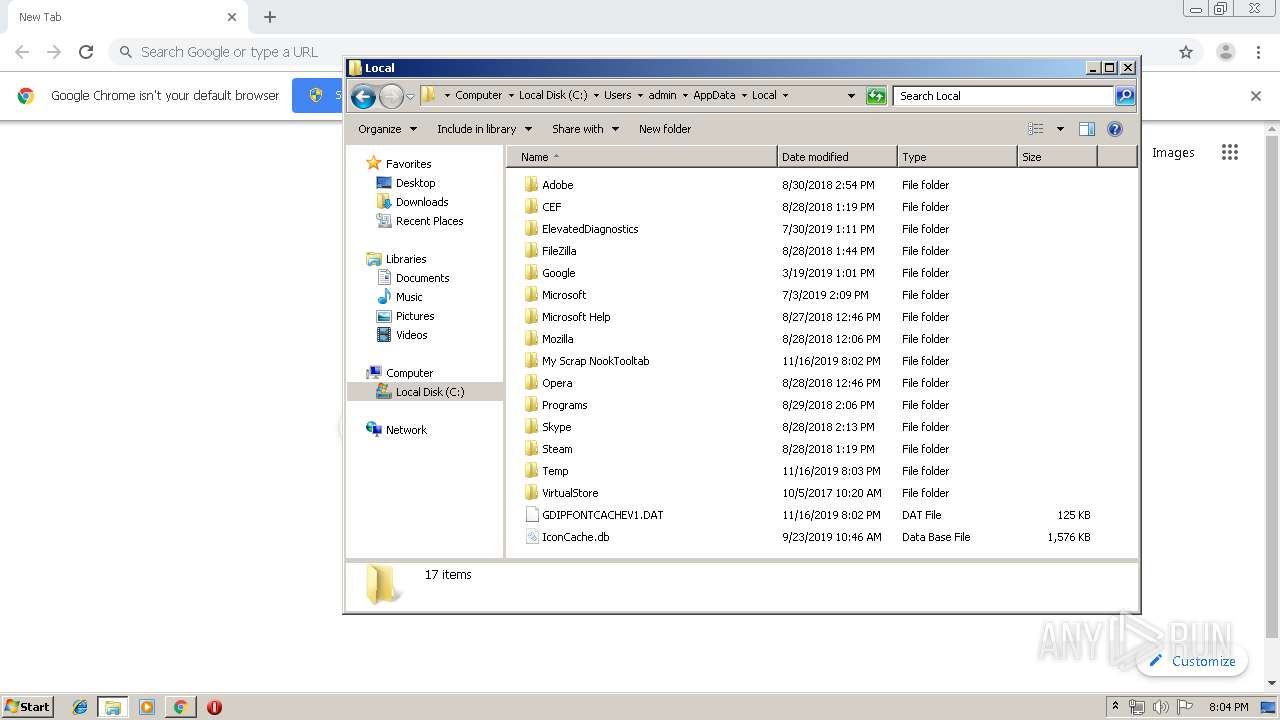
Creates files in the user directory
- MyScrapNook.afdb8f3d192143faba4b8ce803115f49.exe (PID: 2380)
Creates a software uninstall entry
- MyScrapNook.afdb8f3d192143faba4b8ce803115f49.exe (PID: 2380)
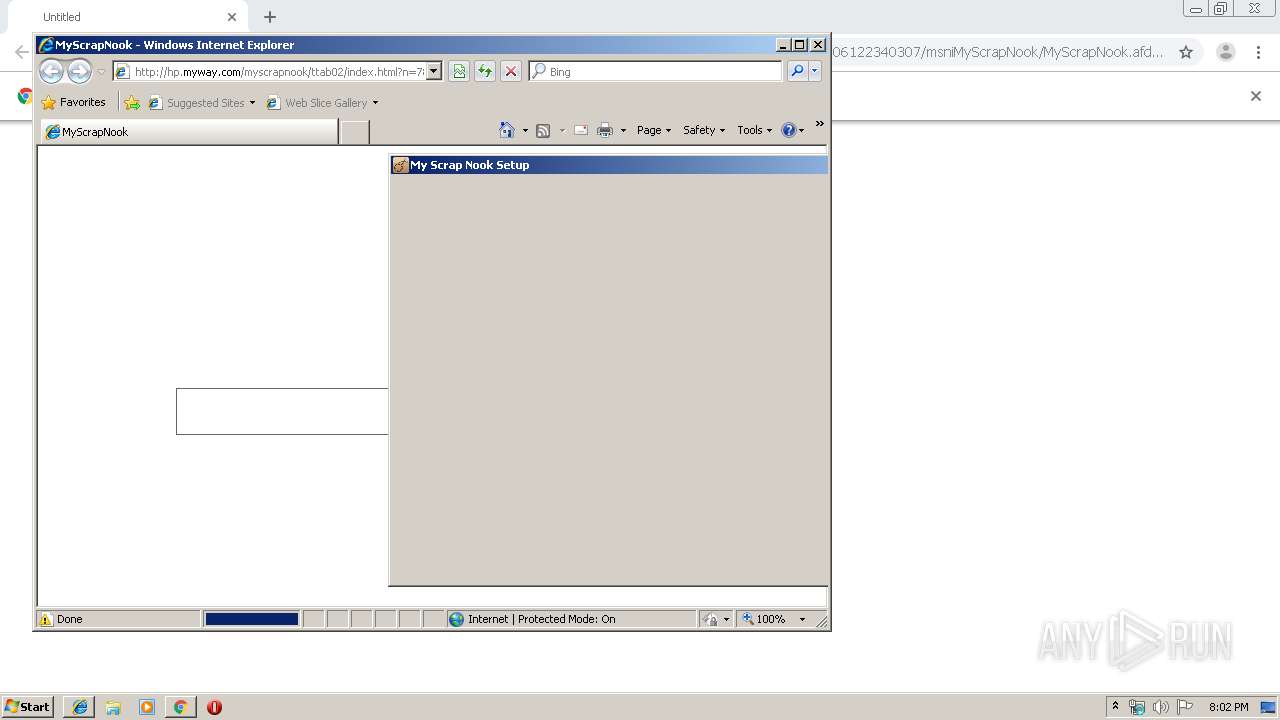
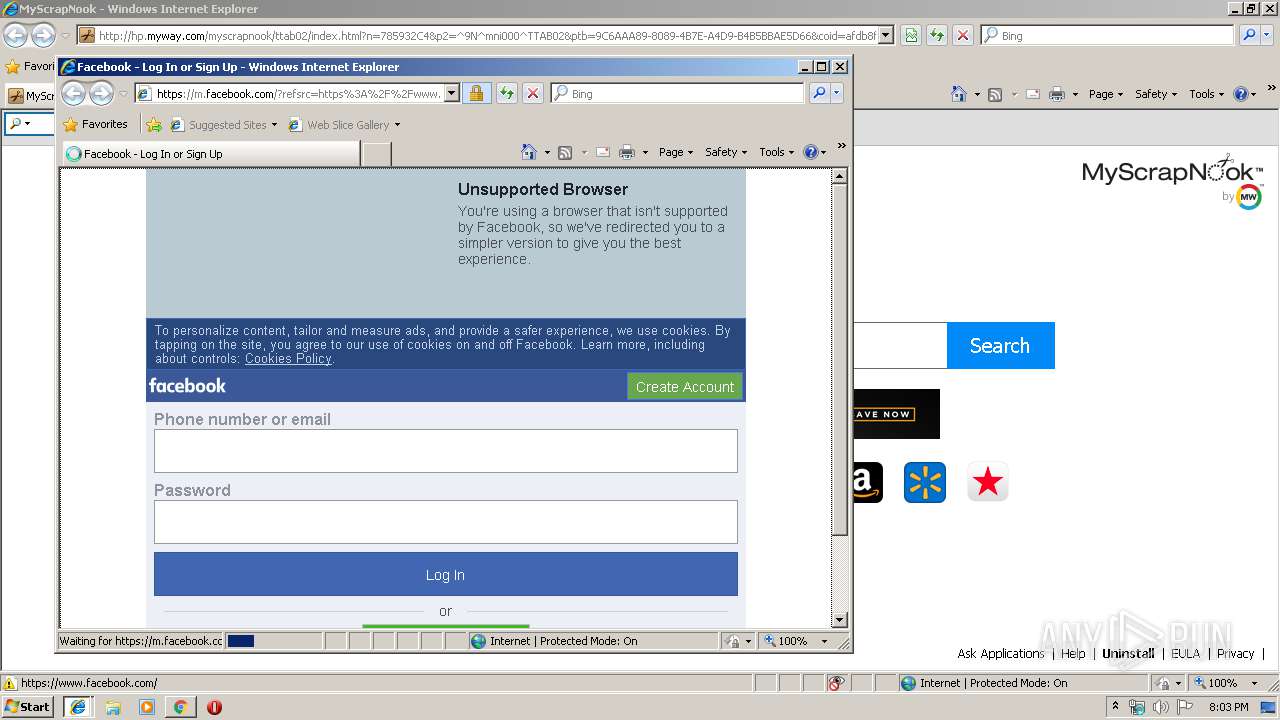
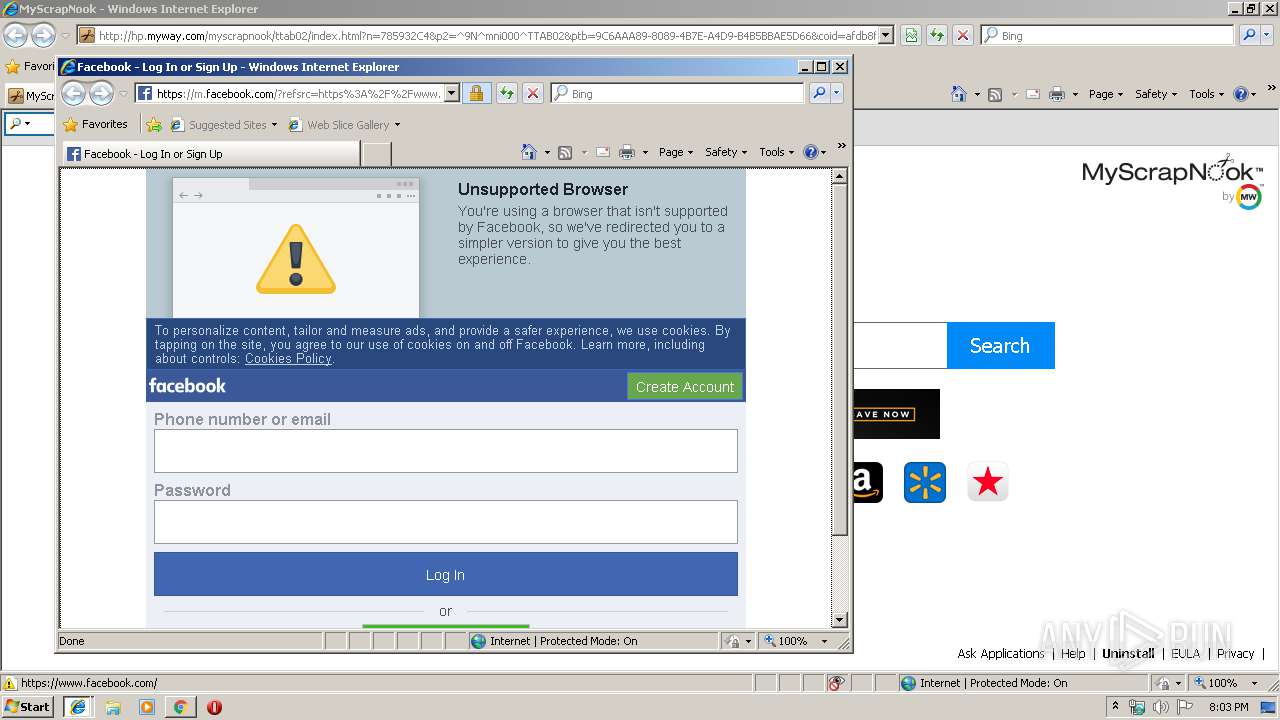
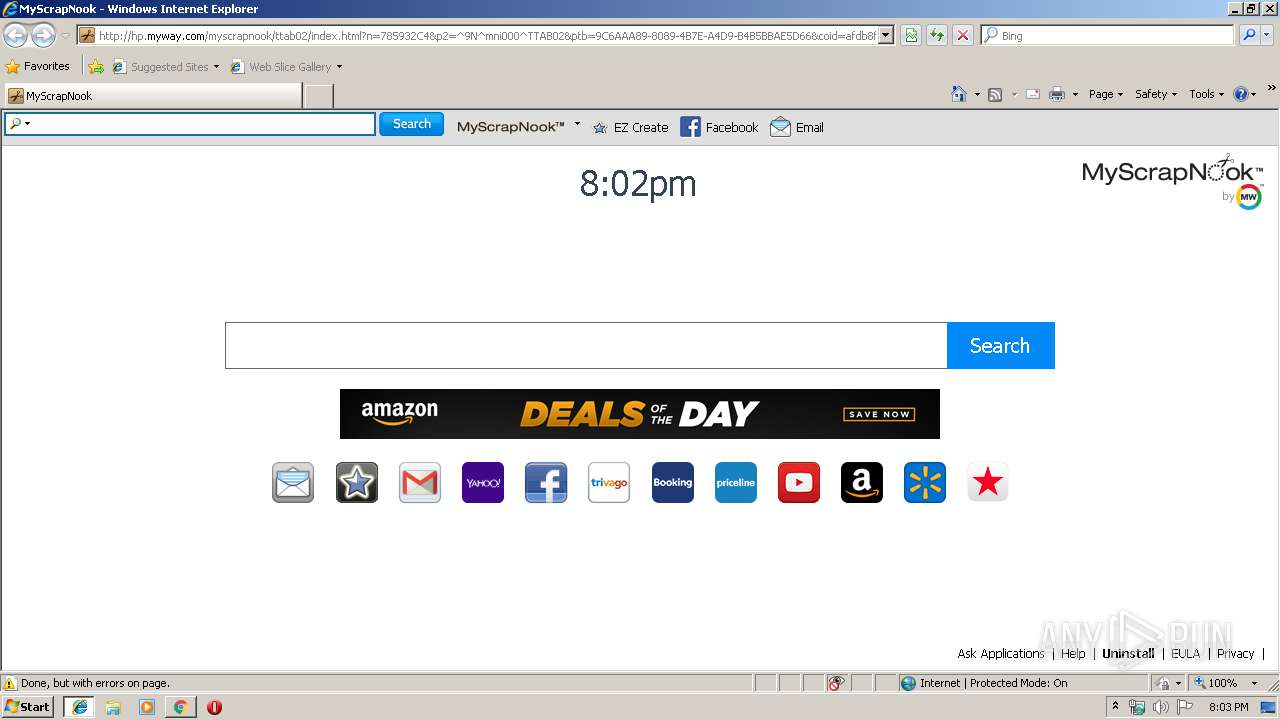
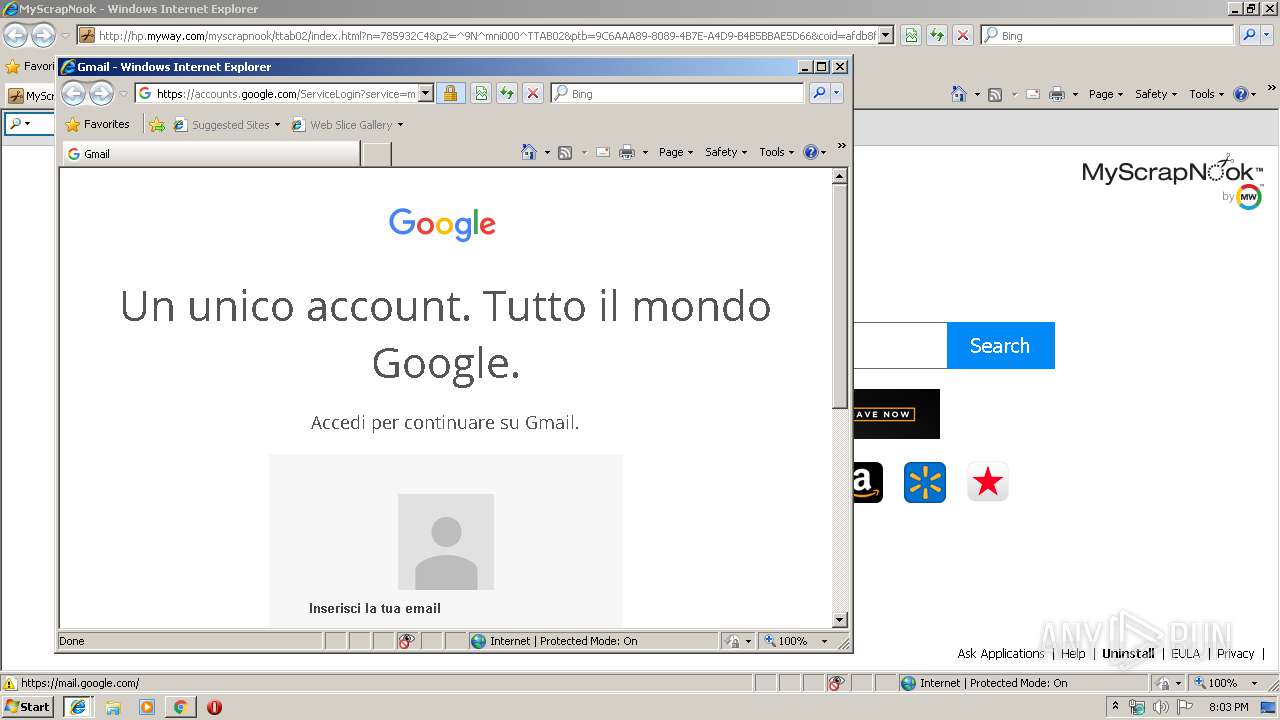
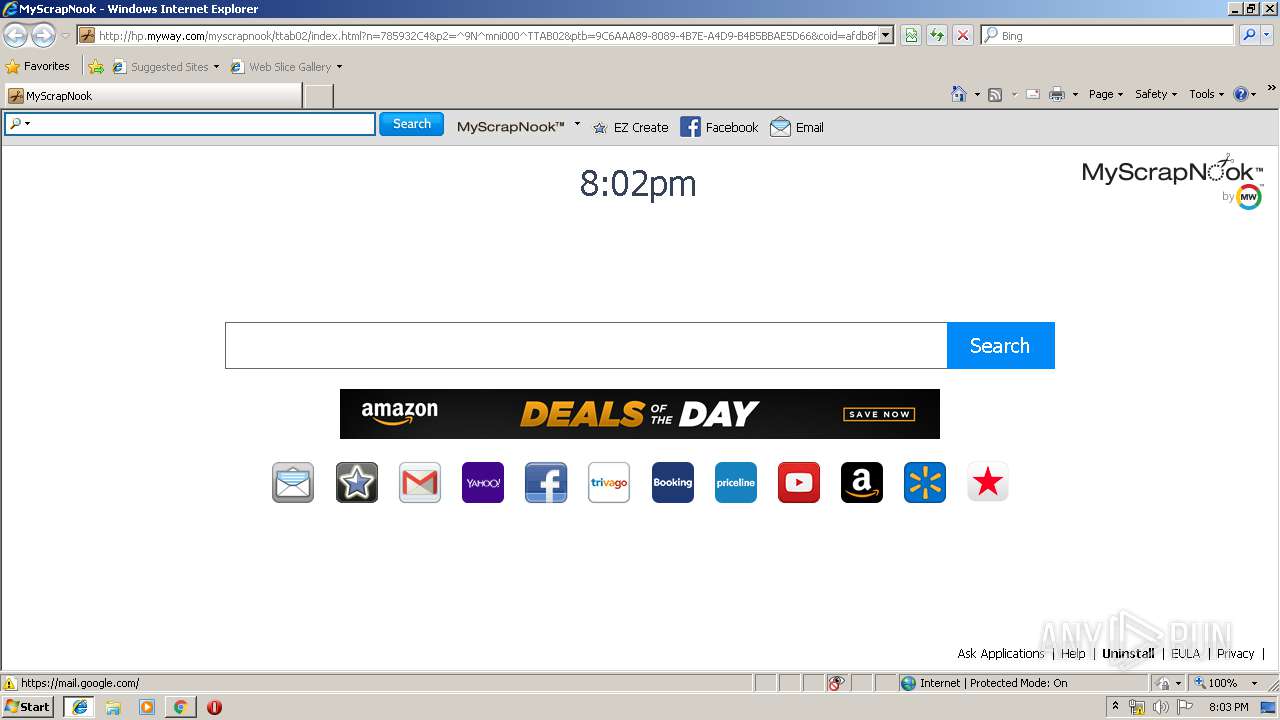
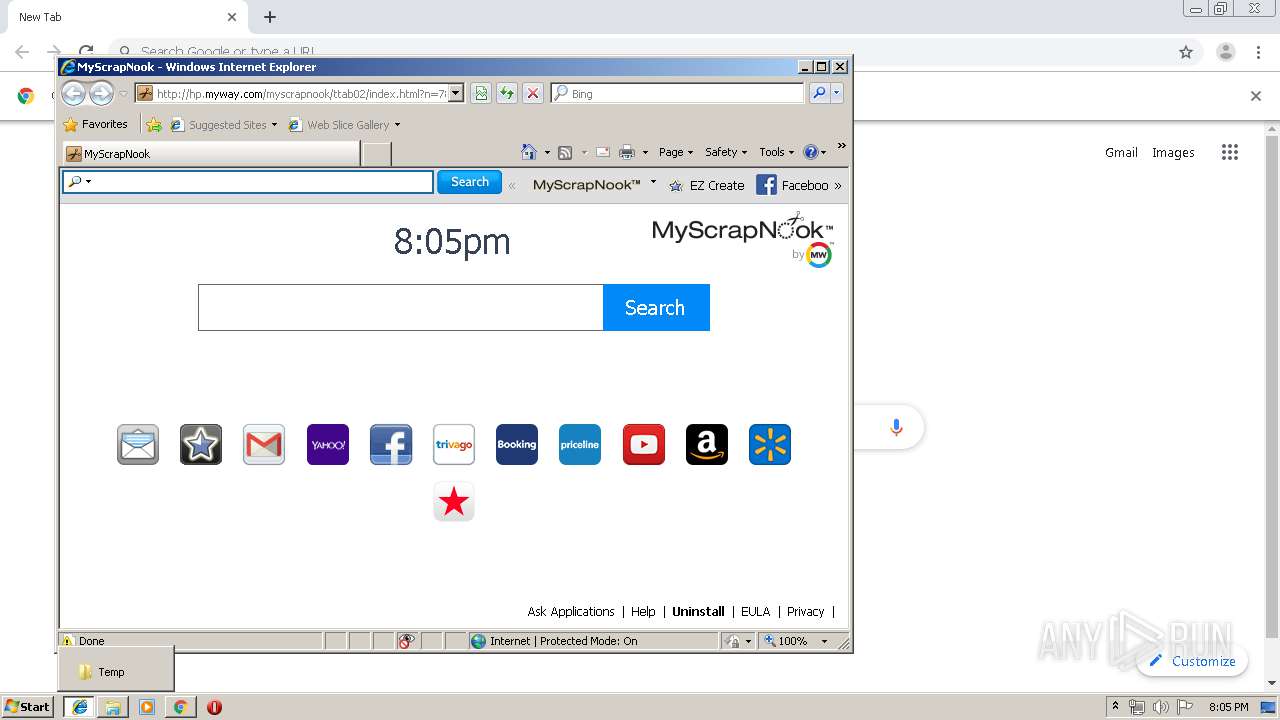
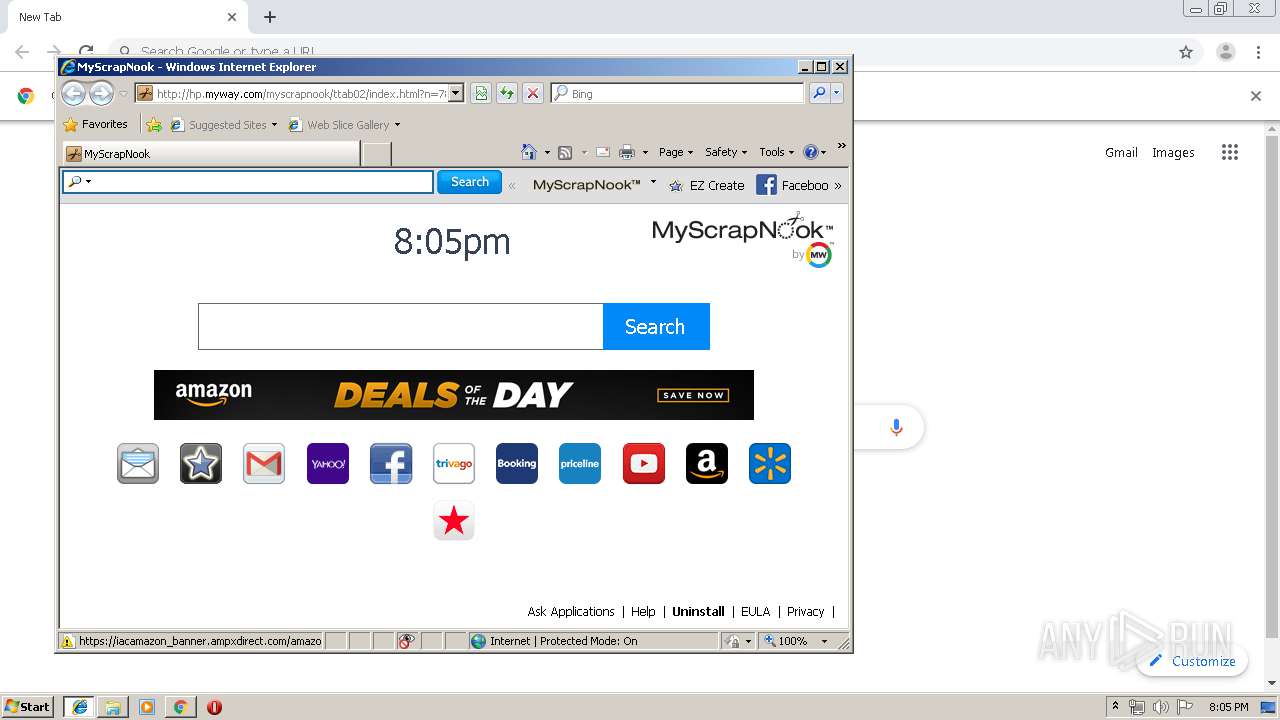
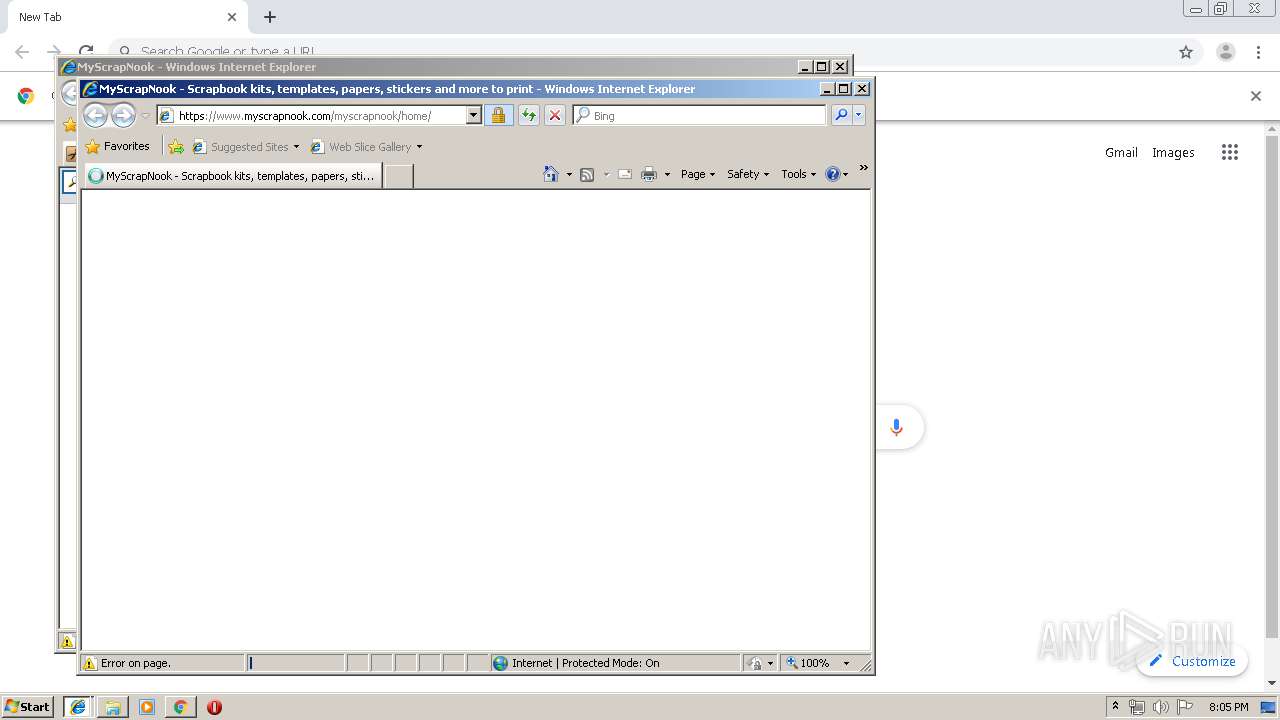
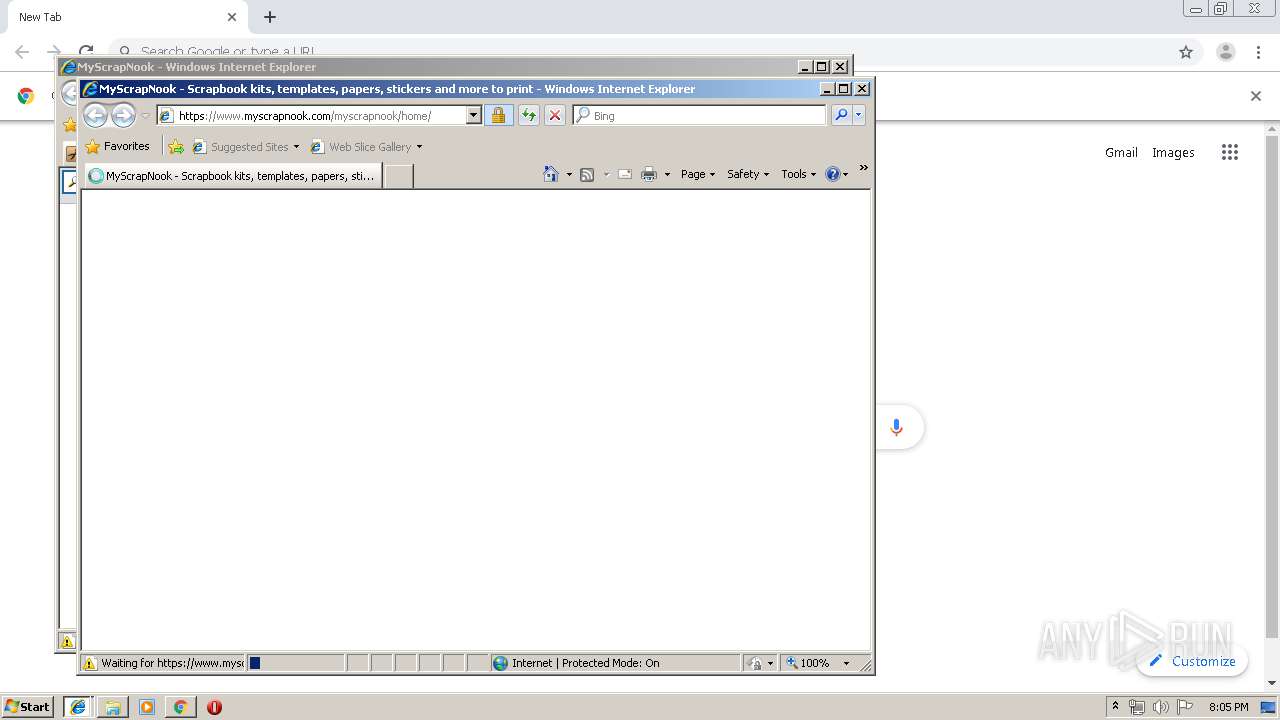
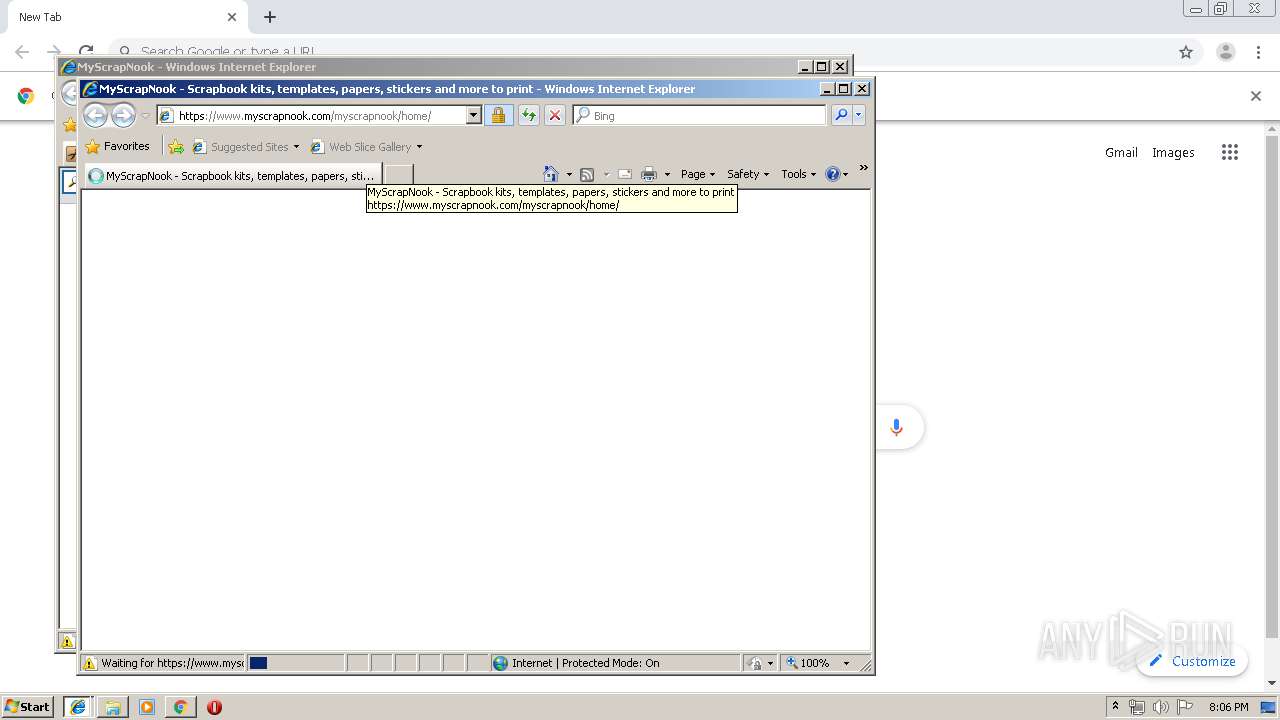
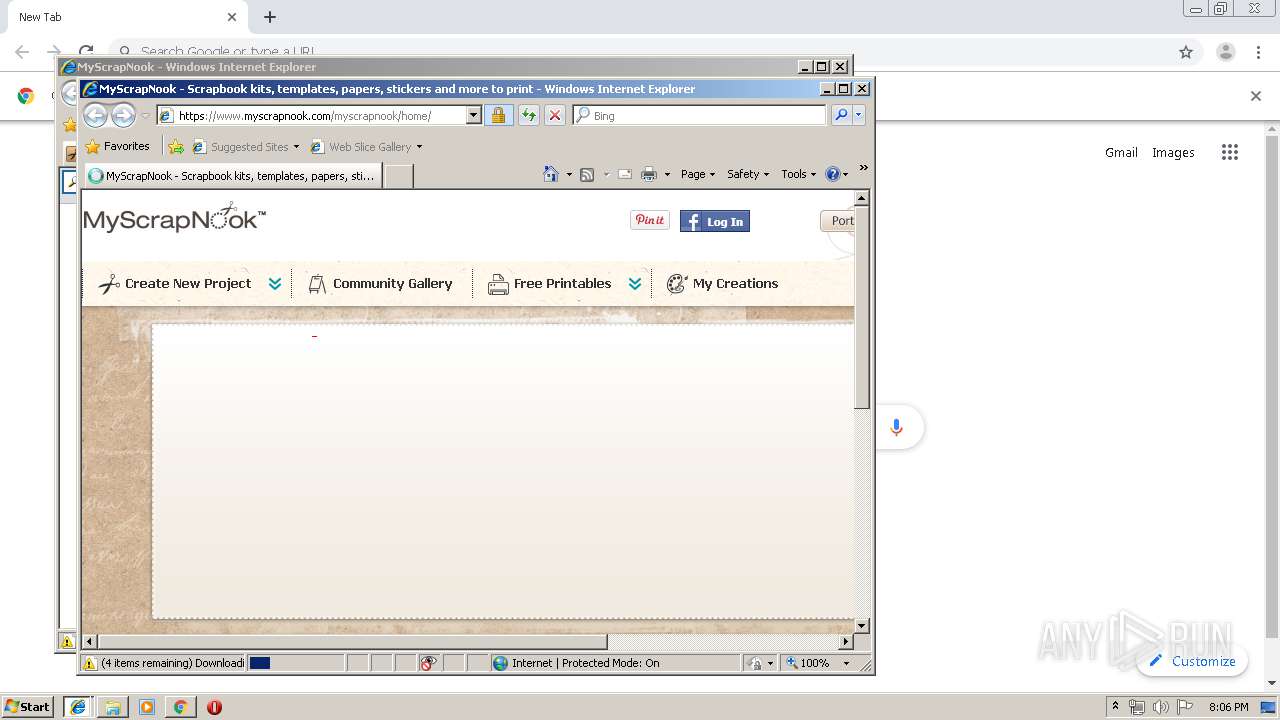
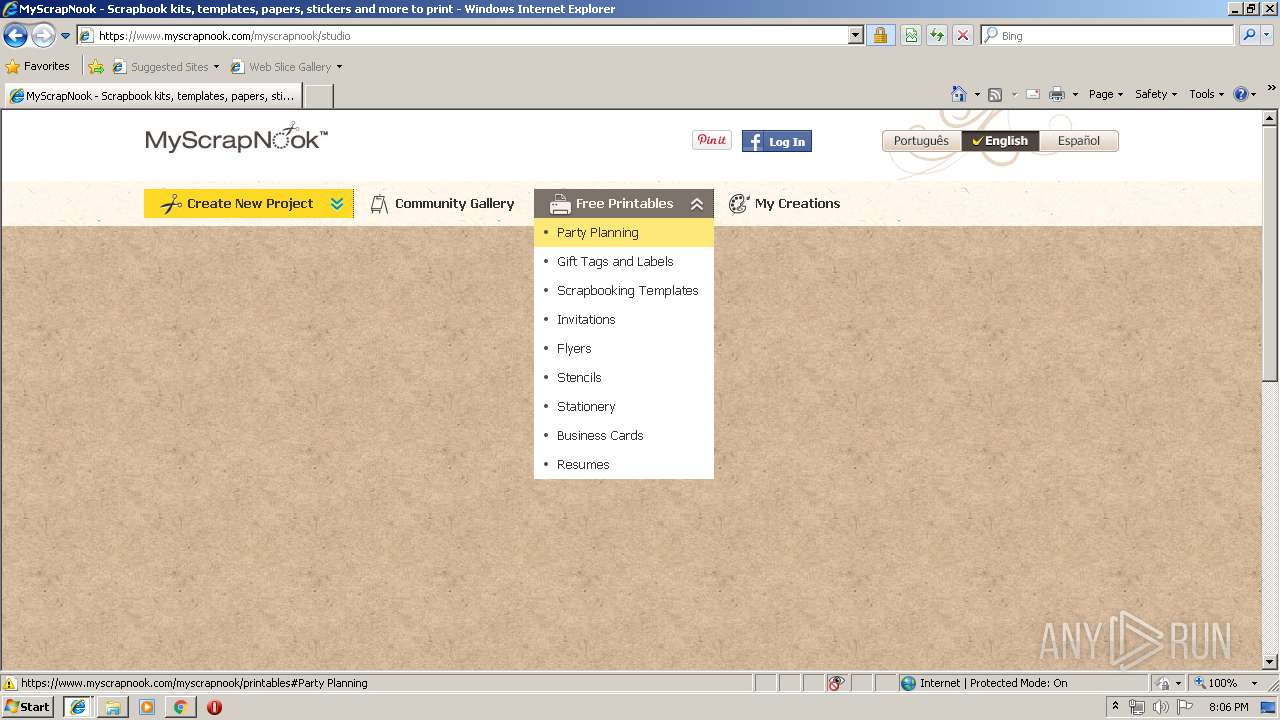
Changes the started page of IE
- MyScrapNook.afdb8f3d192143faba4b8ce803115f49.exe (PID: 2380)
Executed via COM
- iexplore.exe (PID: 320)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2536)
- DllHost.exe (PID: 3636)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2516)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3584)
INFO
Reads the hosts file
- chrome.exe (PID: 4056)
- chrome.exe (PID: 1576)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 3812)
Reads settings of System Certificates
- chrome.exe (PID: 4056)
- chrome.exe (PID: 1576)
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 320)
- iexplore.exe (PID: 1848)
- iexplore.exe (PID: 1728)
Application launched itself
- chrome.exe (PID: 1576)
- iexplore.exe (PID: 320)
- chrome.exe (PID: 3584)
- iexplore.exe (PID: 1728)
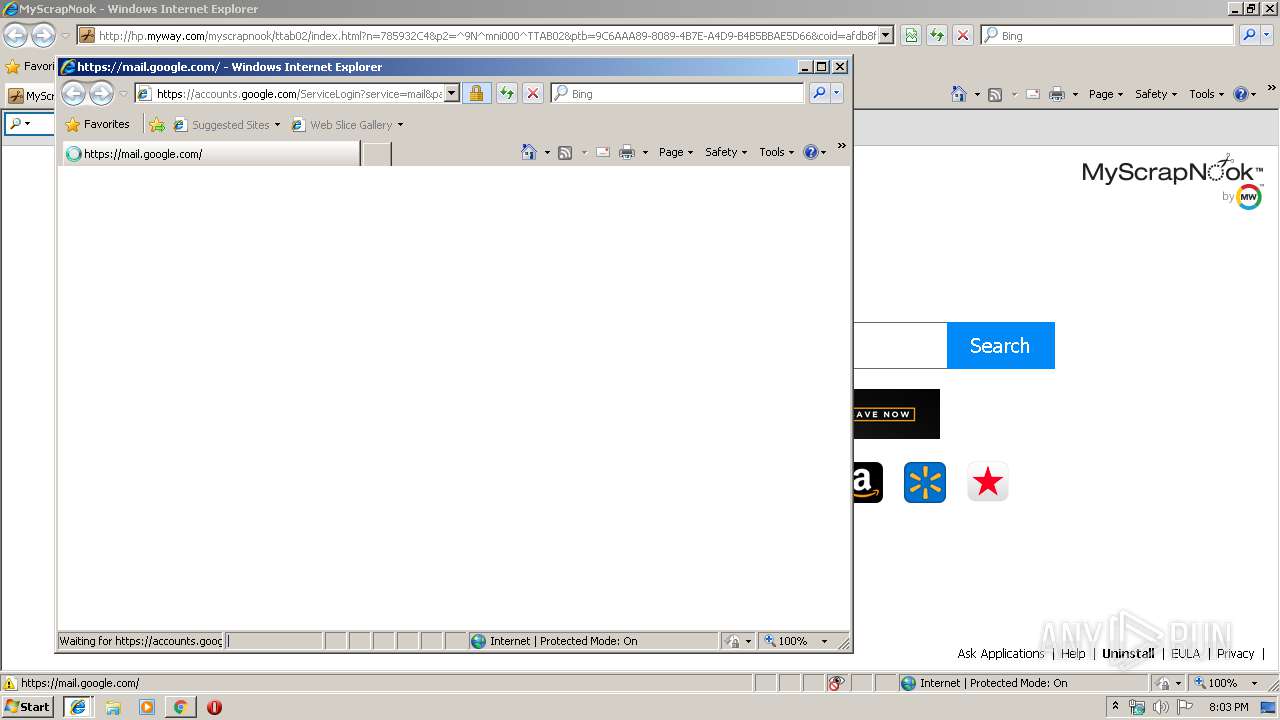
Reads Internet Cache Settings
- chrome.exe (PID: 1576)
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 1848)
- iexplore.exe (PID: 3196)
Changes internet zones settings
- iexplore.exe (PID: 320)
- iexplore.exe (PID: 1728)
Reads internet explorer settings
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 1848)
- iexplore.exe (PID: 3196)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2536)
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 320)
- iexplore.exe (PID: 1848)
- iexplore.exe (PID: 3196)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2516)
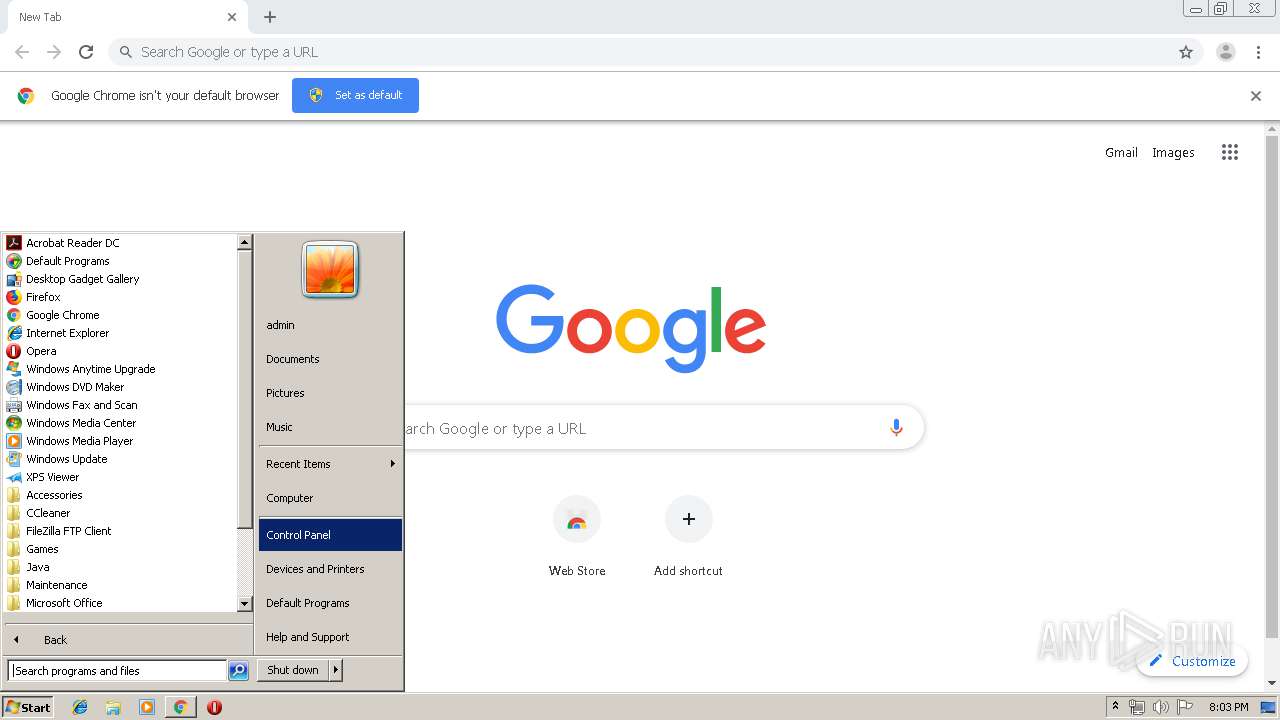
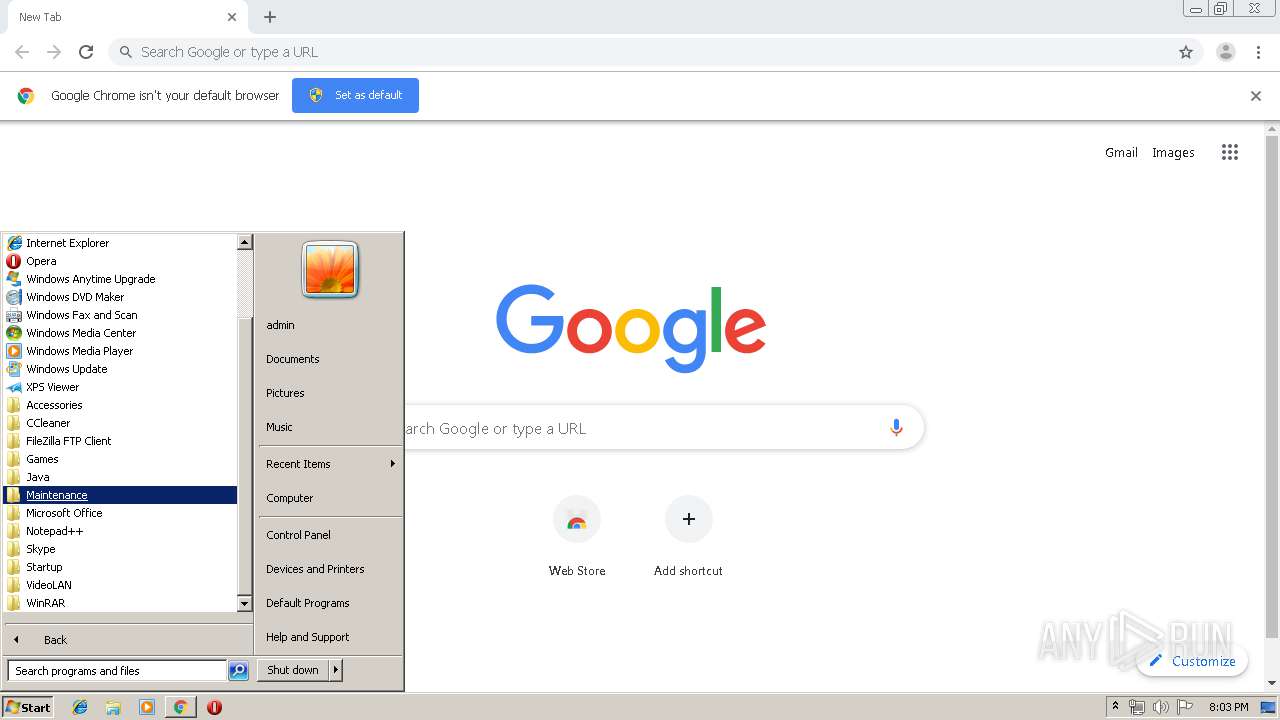
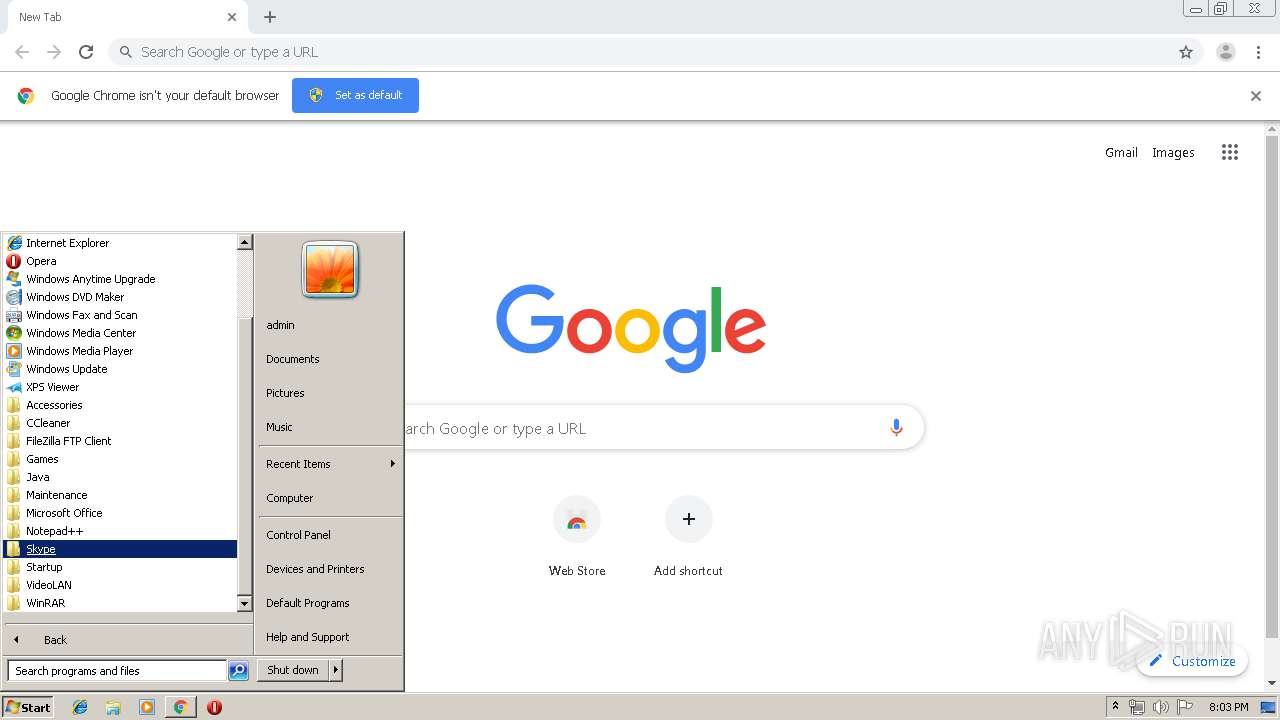
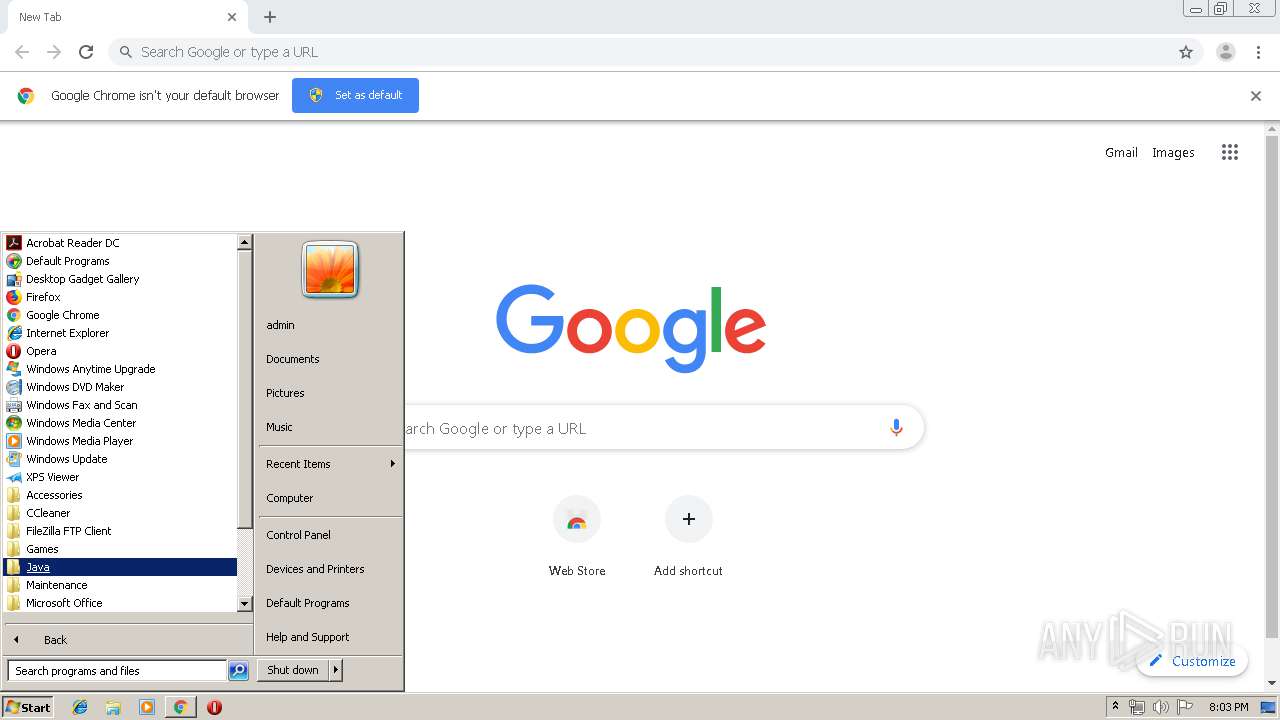
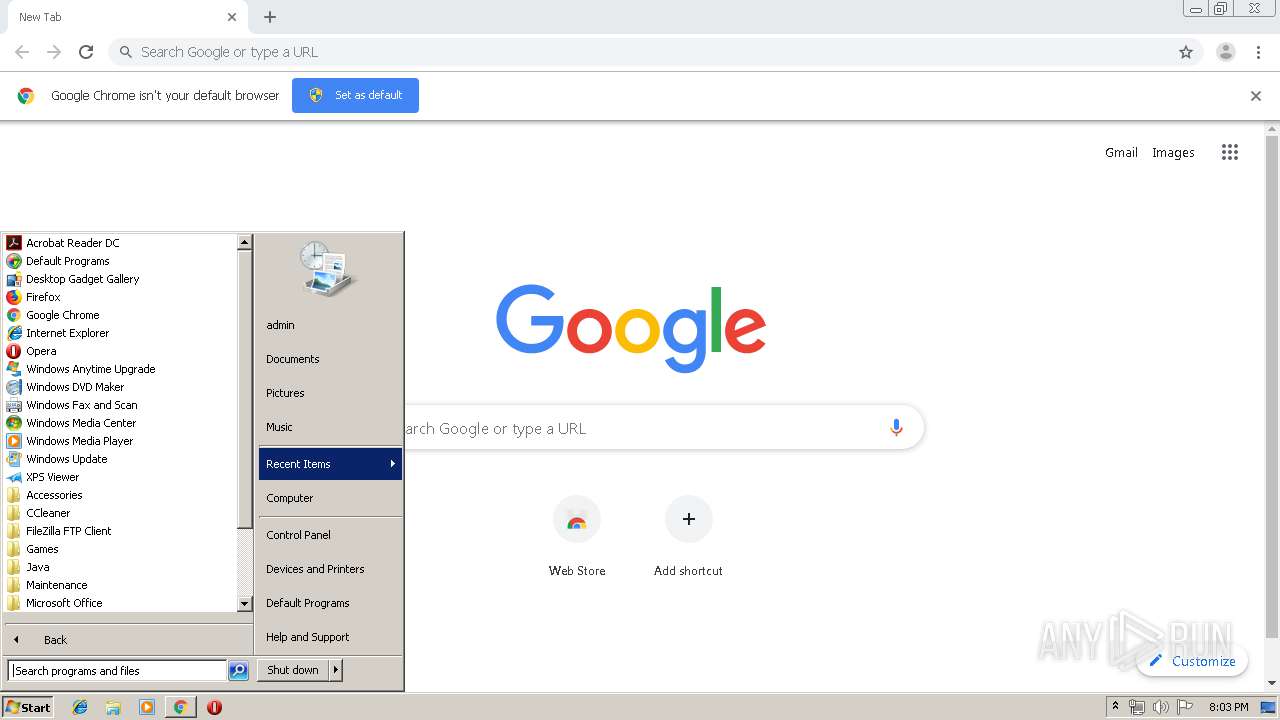
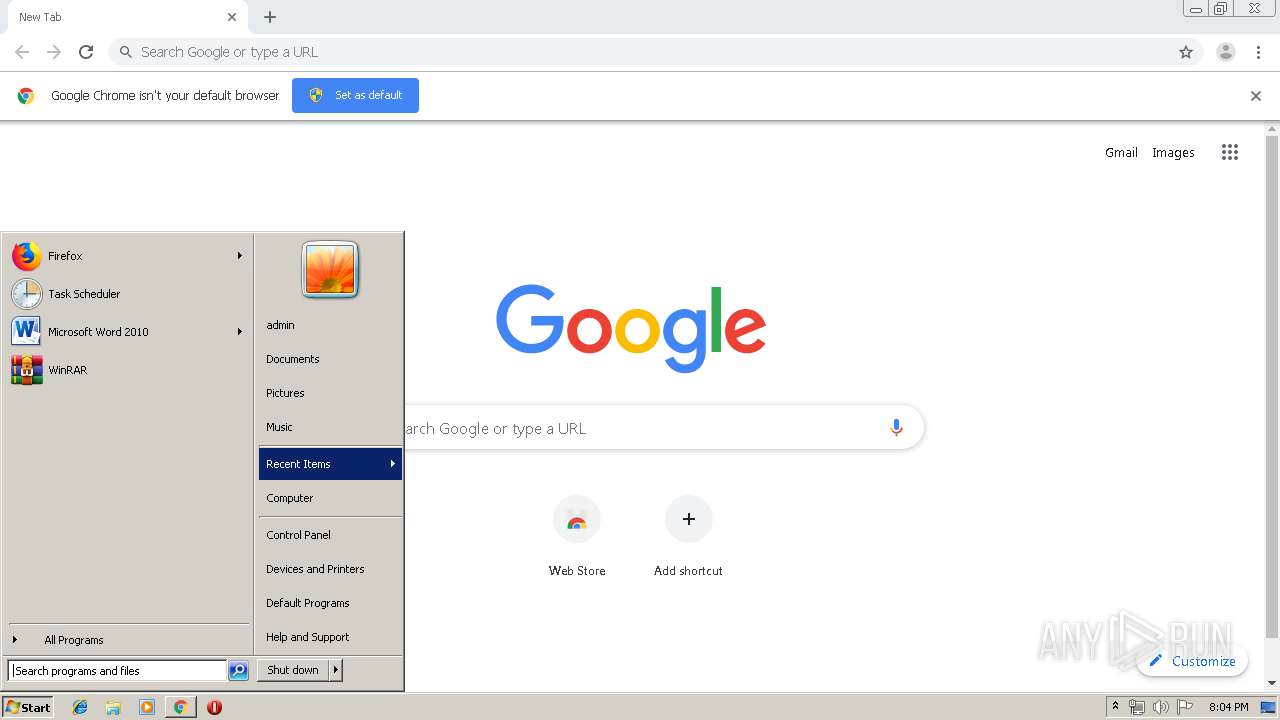
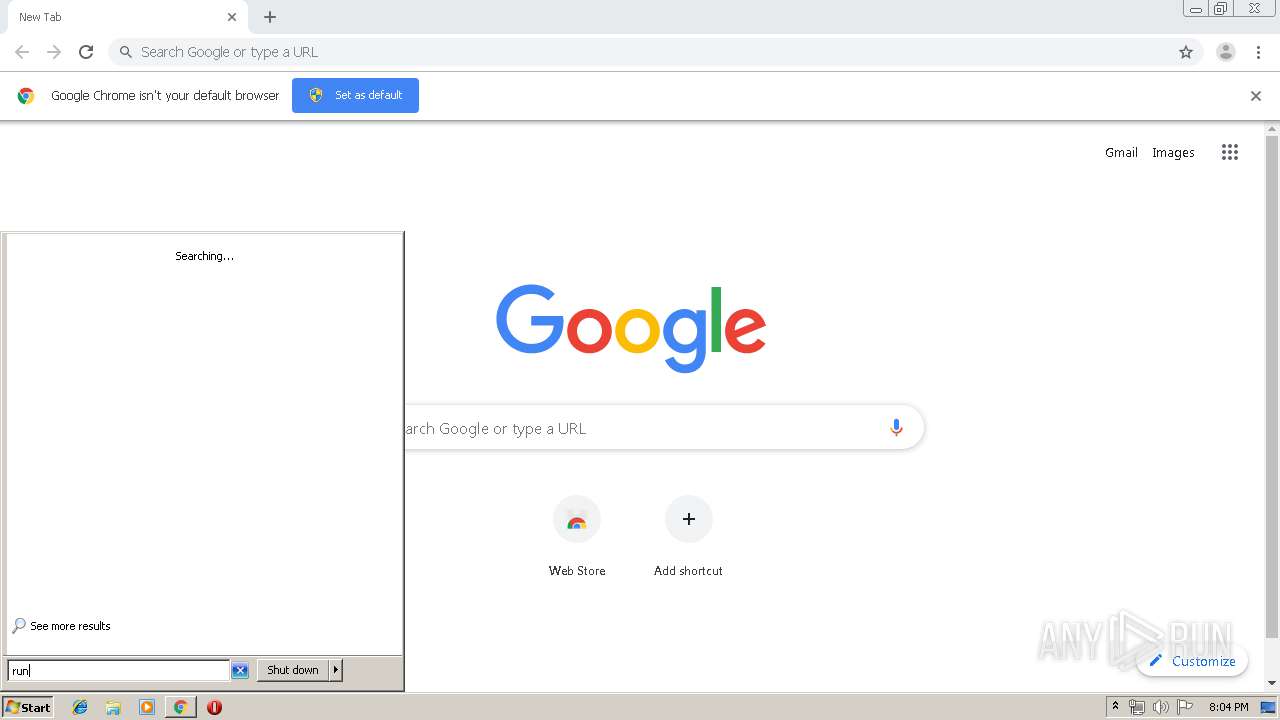
Manual execution by user
- chrome.exe (PID: 3584)
- iexplore.exe (PID: 1728)
Changes settings of System certificates
- iexplore.exe (PID: 1728)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
50
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7606463125271942866 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,13983369033606555855,18204131475982775065,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11528267964651820373 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,13983369033606555855,18204131475982775065,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13574357034153054365 --mojo-platform-channel-handle=2420 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,13983369033606555855,18204131475982775065,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7368572157332853248 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,13983369033606555855,18204131475982775065,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3522083356241517466 --mojo-platform-channel-handle=4156 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3960 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://ak.imgfarm.com/images/nocache/vicinio/installers/v2/200781283.TTAB03.1/nsis/978519-TTAB03.1/190306122340307/msniMyScrapNook/MyScrapNook.afdb8f3d192143faba4b8ce803115f49.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,13983369033606555855,18204131475982775065,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17588393126895722134 --mojo-platform-channel-handle=3732 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 613
Read events
3 136
Write events
464
Delete events
13
Modification events
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1576-13218408148156750 |
Value: 259 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1576) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
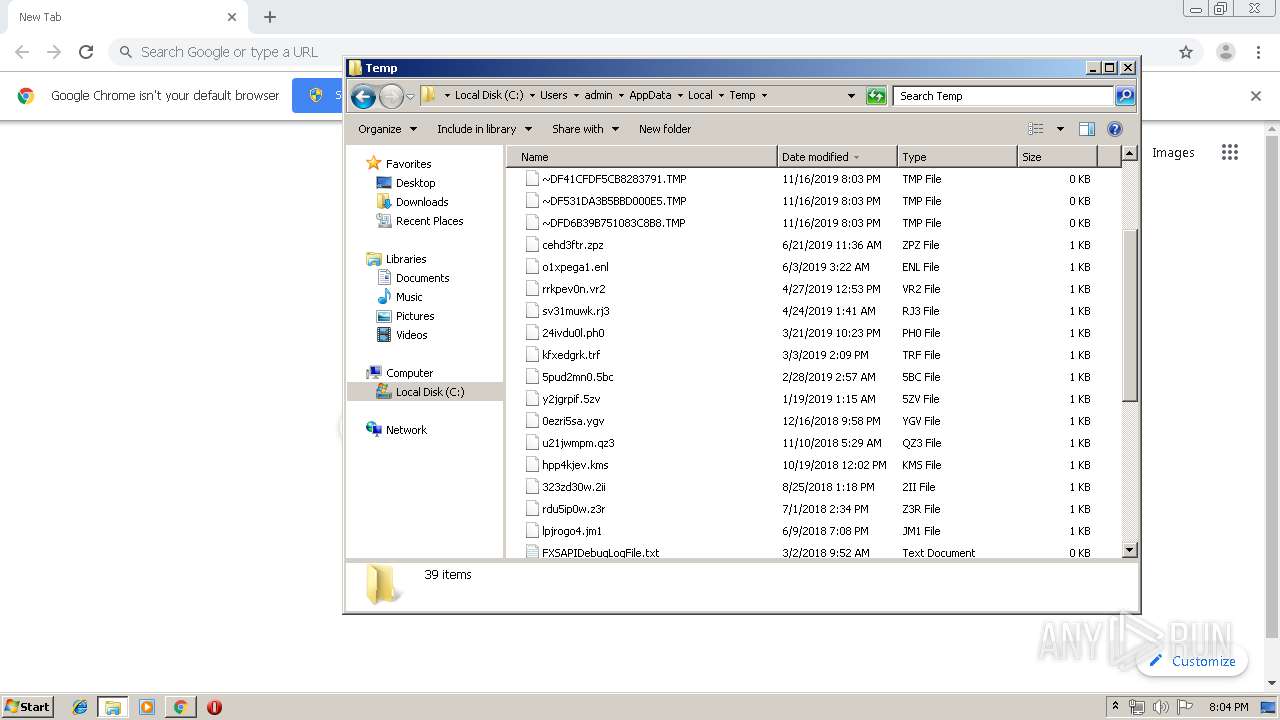
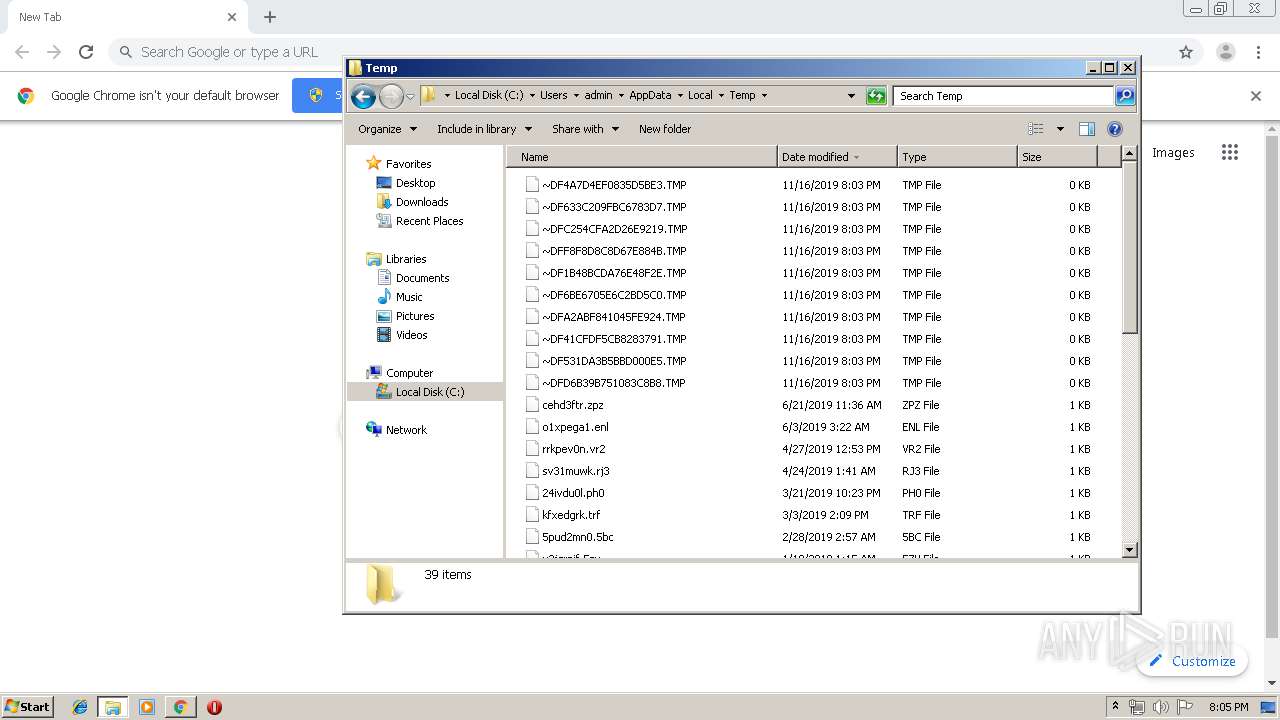
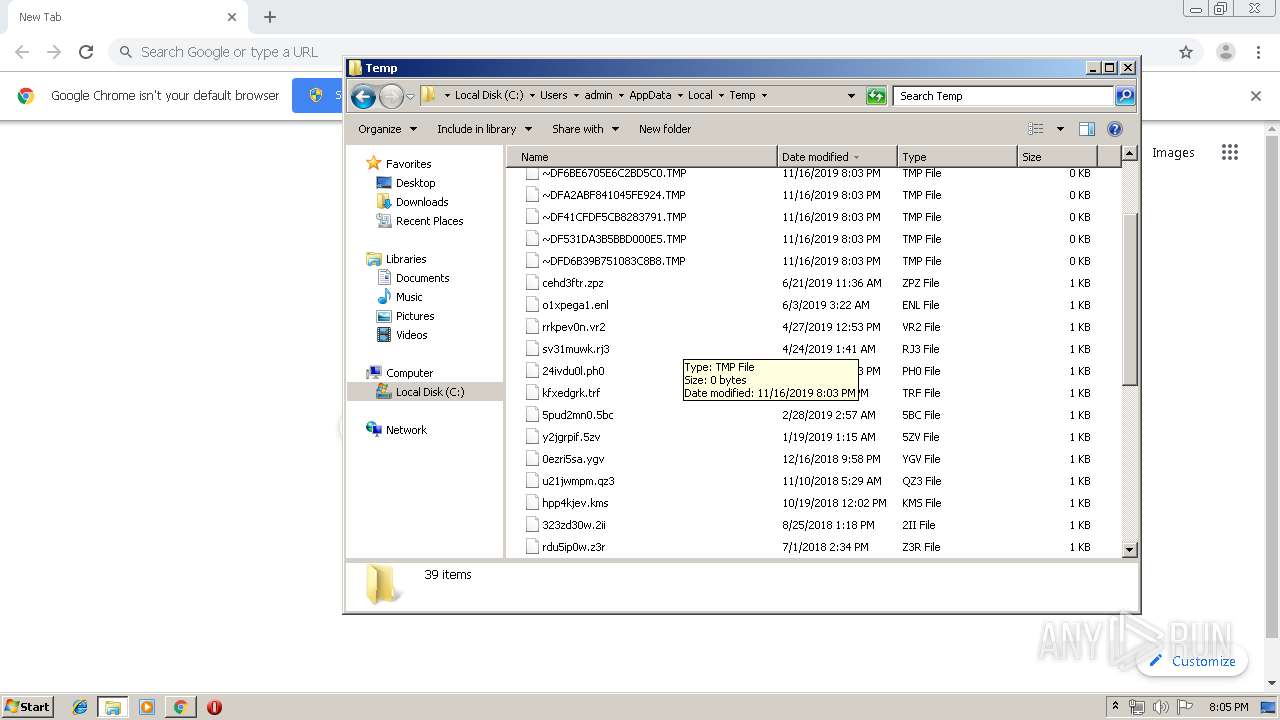
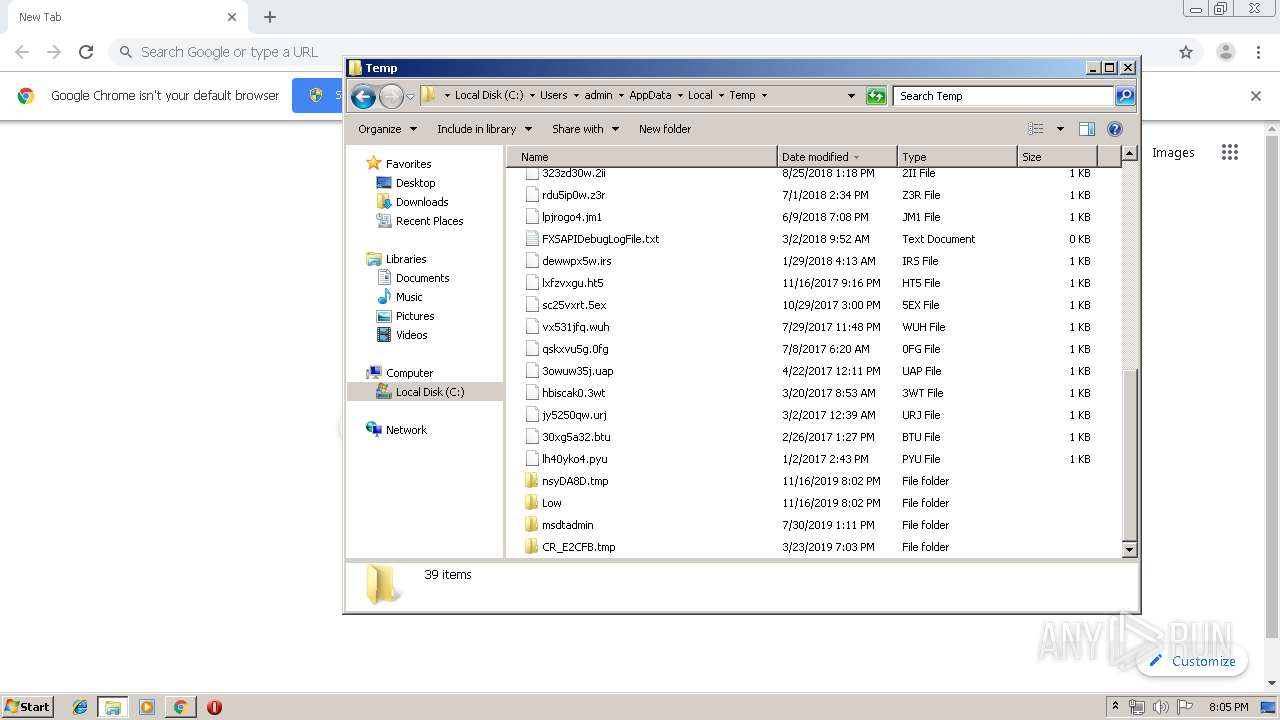
Executable files
8
Suspicious files
65
Text files
483
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f1ceb523-5ba3-421e-895b-4000e520a7b0.tmp | — | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a92b.TMP | text | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a989.TMP | text | |
MD5:— | SHA256:— | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
163
DNS requests
52
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3184 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://hp.myway.com/myscrapnook/ttab02/assets/1571860532755/ie8.js | NL | html | 871 b | whitelisted |
3184 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://hp.myway.com/myscrapnook/ttab02/assets/1571860532755/app.js | NL | text | 115 Kb | whitelisted |
3184 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://hp.myway.com/myscrapnook/ttab02/index.html?n=785932C4&p2=^9N^mni000^TTAB02&ptb=9C6AAA89-8089-4B7E-A4D9-B4B5BBAE5D66&coid=afdb8f3d192143faba4b8ce803115f49 | NL | html | 3.45 Kb | whitelisted |
3184 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/assets/logos/9N.png | NL | image | 6.25 Kb | whitelisted |
3184 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/assets/searchbar/223756111.png | NL | image | 813 b | whitelisted |
3184 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/ttdetect-2/prd/ttdetect.html | NL | html | 4.23 Kb | whitelisted |
3184 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/chiclets/YourTemplateFinder/YTF_chiclet_email.png | NL | image | 2.73 Kb | whitelisted |
3184 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/assets/searchbar/223756096.png | NL | image | 1.76 Kb | whitelisted |
3184 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/chiclets/MyScrapNook/MSN_chiclets_ezcreate.png | NL | image | 2.50 Kb | whitelisted |
3184 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/chiclets/youtube.png | NL | image | 824 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4056 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4056 | chrome.exe | 23.38.53.120:443 | ak.imgfarm.com | Akamai International B.V. | NL | whitelisted |
4056 | chrome.exe | 172.217.16.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
4056 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
4056 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
4056 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2380 | MyScrapNook.afdb8f3d192143faba4b8ce803115f49.exe | 34.102.222.207:443 | anx.mindspark.com | — | US | malicious |
2380 | MyScrapNook.afdb8f3d192143faba4b8ce803115f49.exe | 35.244.218.203:443 | dp.tb.ask.com | — | US | whitelisted |
320 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3184 | iexplore.exe | 23.38.53.120:80 | ak.imgfarm.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
ak.imgfarm.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
anx.mindspark.com |
| whitelisted |
dp.tb.ask.com |
| whitelisted |
hp.myway.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3196 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |