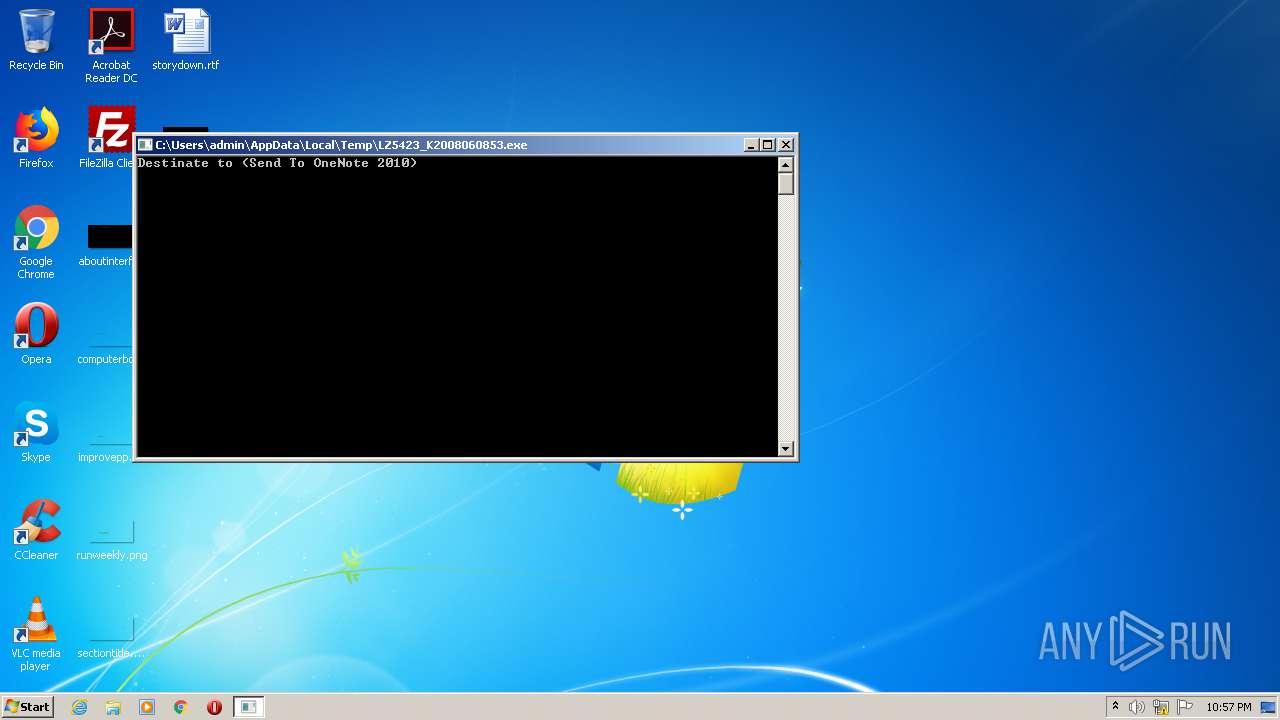
| File name: | LZ5423_K2008060853.exe |
| Full analysis: | https://app.any.run/tasks/7db43a04-aaa4-40cc-9ada-5bb8d17b6f83 |
| Verdict: | Malicious activity |
| Analysis date: | November 10, 2020, 22:56:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | E72FB14B463517B95043898A5EFCD43B |
| SHA1: | 3E4ED3FE212C5618ACCC0F9F5E0A714CBF0264C8 |
| SHA256: | 44C2DE471B0602C60C32763ADD5DD29920D1EDFF5A8876634520D5A3B1660701 |
| SSDEEP: | 98304:98iAvgQPOXL/P5Vjaffc9T+49rEWlQ6h4OkVy9vWdTyI+wxquObDnG:BAIQidVj6c9T+4OWx4OOde0qrbb |
MALICIOUS
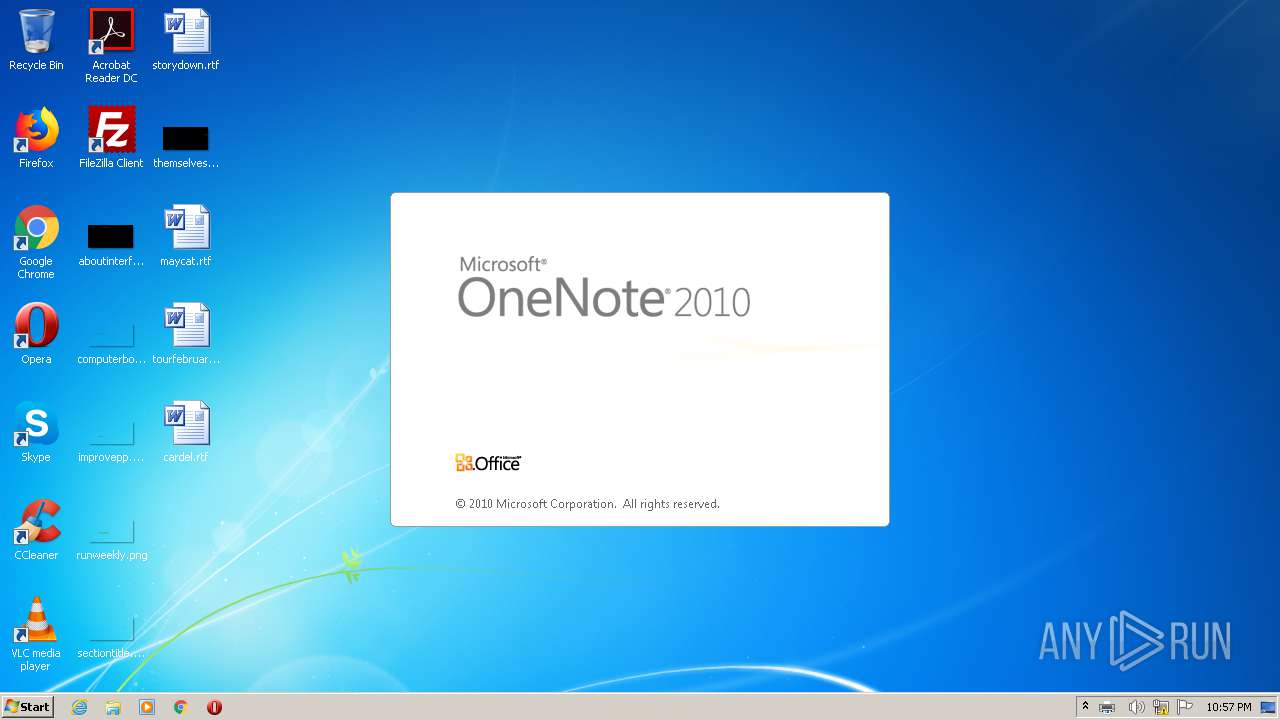
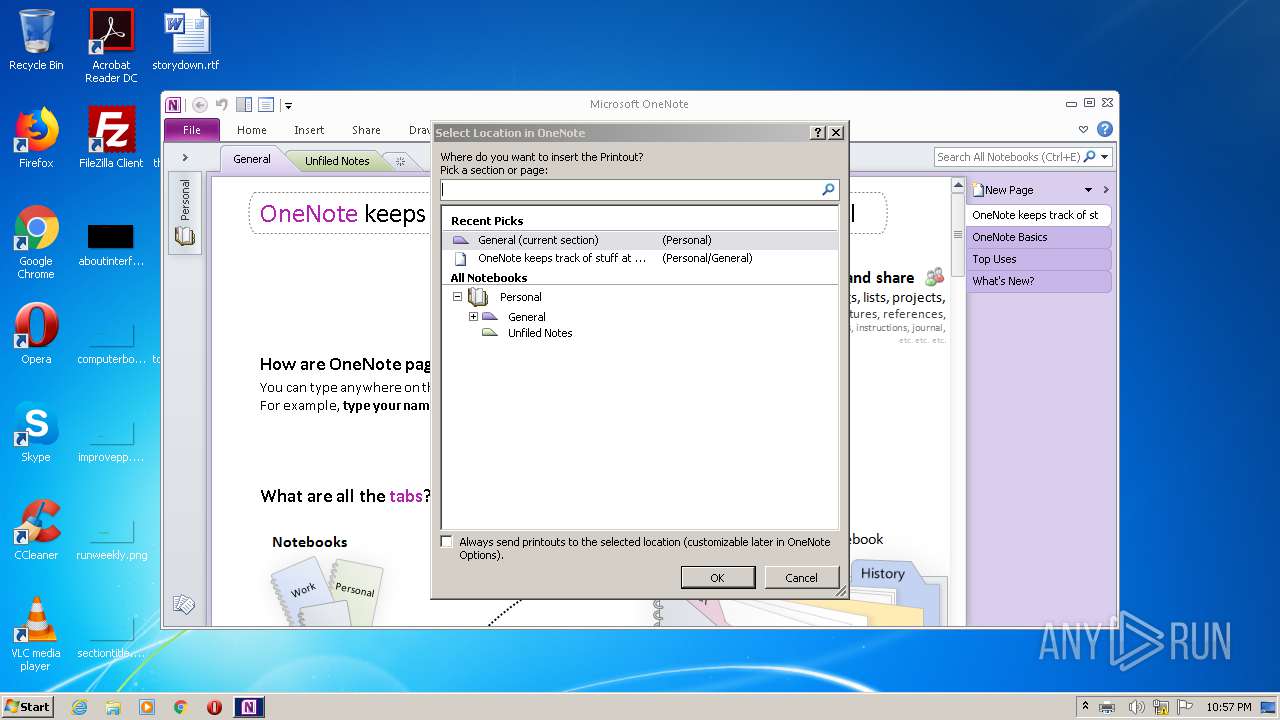
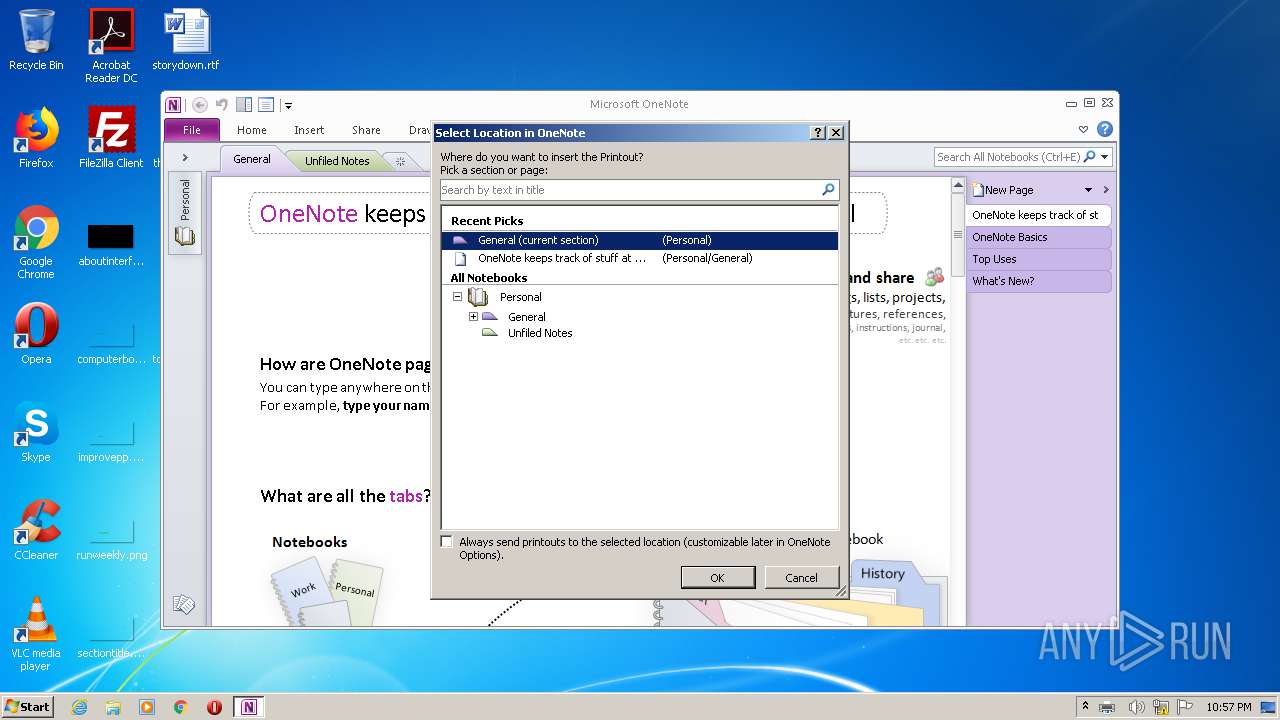
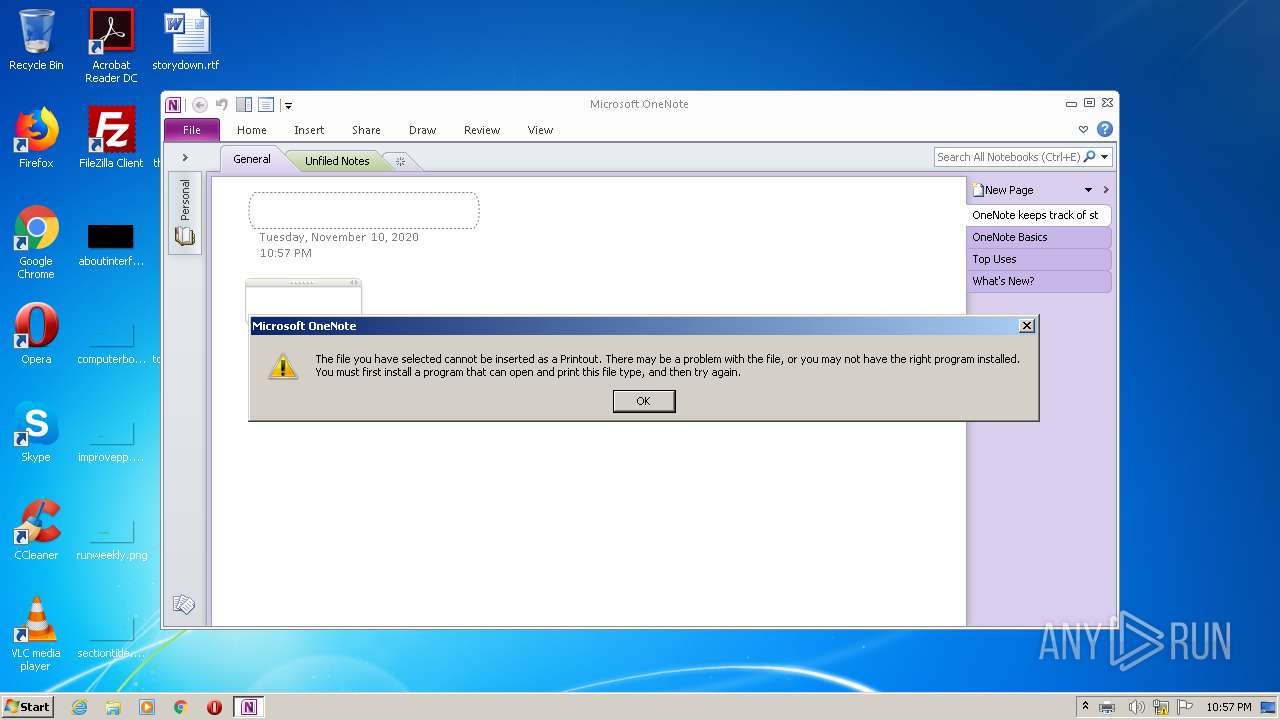
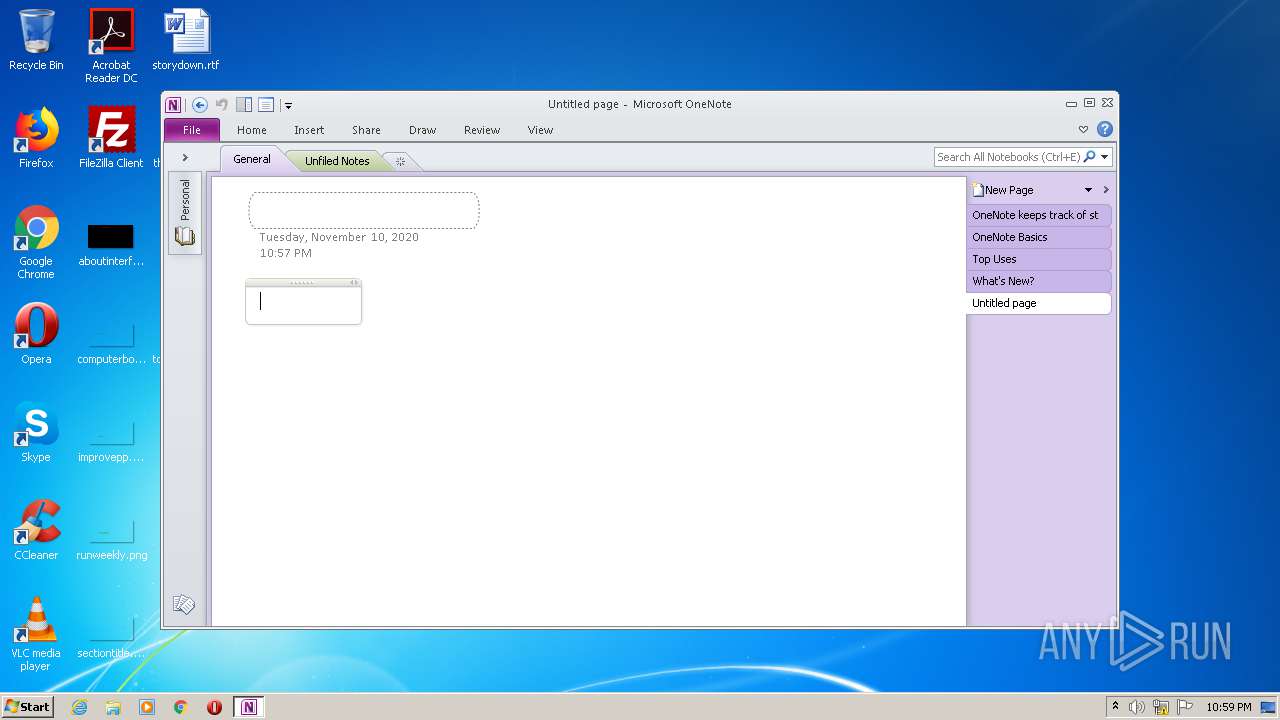
Unusual execution from Microsoft Office
- ONENOTE.EXE (PID: 2852)
Writes to a start menu file
- ONENOTE.EXE (PID: 2852)
SUSPICIOUS
Creates files in the Windows directory
- printfilterpipelinesvc.exe (PID: 3388)
- LZ5423_K2008060853.exe (PID: 3404)
Starts Microsoft Office Application
- printfilterpipelinesvc.exe (PID: 3388)
- ONENOTE.EXE (PID: 2852)
Executed via COM
- printfilterpipelinesvc.exe (PID: 3388)
Removes files from Windows directory
- printfilterpipelinesvc.exe (PID: 3388)
Creates files in the user directory
- ONENOTE.EXE (PID: 2852)
INFO
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 2852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:06 10:37:10+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 69632 |
| InitializedDataSize: | 6817280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16d6 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 06-Aug-2020 08:37:10 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Aug-2020 08:37:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00010EBB | 0x00011000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63915 |
.rdata | 0x00012000 | 0x00006600 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.29474 |
.data | 0x00019000 | 0x000012E0 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.83868 |
.rsrc | 0x0001B000 | 0x00677BF8 | 0x00677C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99858 |
.reloc | 0x00693000 | 0x00000F38 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.39739 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
PRNOUTDATA | 7.99858 | 6781816 | UNKNOWN | English - United States | RAW_DAT |
Imports
KERNEL32.dll |
WINSPOOL.DRV |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2852 | /insertdoc "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{DDC88B30-8003-463E-90BF-A700FE5BF2E8}.xps" 132495226365300000 | C:\Program Files\Microsoft Office\Office14\ONENOTE.EXE | printfilterpipelinesvc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Exit code: 0 Version: 14.0.6022.1000 Modules
| |||||||||||||||
| 3388 | C:\Windows\system32\printfilterpipelinesvc.exe -Embedding | C:\Windows\system32\printfilterpipelinesvc.exe | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Print Filter Pipeline Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3404 | "C:\Users\admin\AppData\Local\Temp\LZ5423_K2008060853.exe" | C:\Users\admin\AppData\Local\Temp\LZ5423_K2008060853.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3772 | /tsr | C:\Program Files\Microsoft Office\Office14\ONENOTEM.EXE | — | ONENOTE.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Quick Launcher Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
Total events
625
Read events
574
Write events
47
Delete events
4
Modification events
| (PID) Process: | (2852) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2852) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2852) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2852) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2852) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2852) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2852) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2852) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2852) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2852) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3404 | LZ5423_K2008060853.exe | C:\Windows\system32\spool\PRINTERS\00002.SPL | — | |
MD5:— | SHA256:— | |||
| 3388 | printfilterpipelinesvc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{DDC88B30-8003-463E-90BF-A700FE5BF2E8}.xps | — | |
MD5:— | SHA256:— | |||
| 3388 | printfilterpipelinesvc.exe | C:\Windows\System32\spool\PRINTERS\PP077i6ksxjh726fwy7ex7fn94b.TMP | — | |
MD5:— | SHA256:— | |||
| 3388 | printfilterpipelinesvc.exe | C:\Windows\System32\spool\PRINTERS\PP75ivp0elvd0ku0rf_1_rntc0b.TMP | — | |
MD5:— | SHA256:— | |||
| 3388 | printfilterpipelinesvc.exe | C:\Windows\System32\spool\PRINTERS\PPrgrnuq_fnrv85kq45n70kkdxc.TMP | — | |
MD5:— | SHA256:— | |||
| 2852 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\CVR6459.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2852 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Microsoft\OneNote\14.0\Backup\Personal\~Unfiled Notes.one.onebackupconstruction | — | |
MD5:— | SHA256:— | |||
| 2852 | ONENOTE.EXE | C:\Users\admin\Documents\OneNote Notebooks\Personal\General.one | one | |
MD5:— | SHA256:— | |||
| 2852 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Microsoft\OneNote\14.0\Backup\Personal\~General.one.onebackupconstruction | one | |
MD5:— | SHA256:— | |||
| 2852 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Microsoft\OneNote\14.0\Backup\Personal\Unfiled Notes.one (On 11-10-2020).one | one | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report