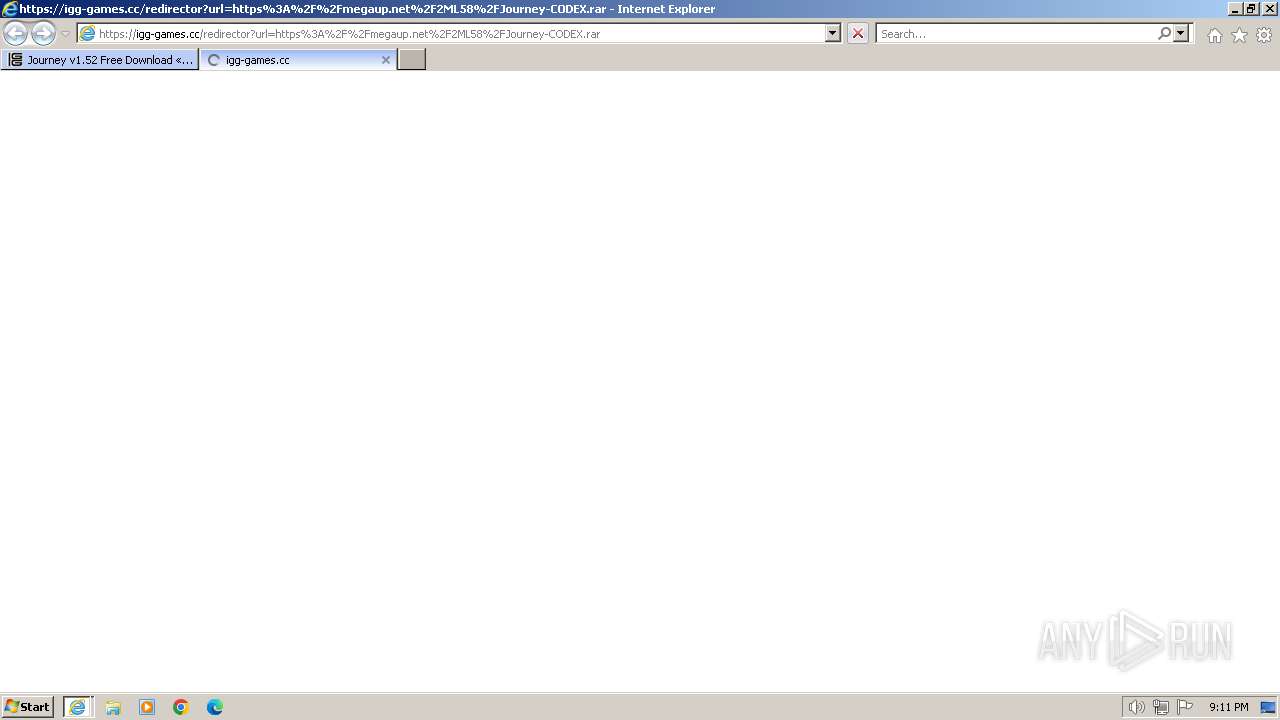
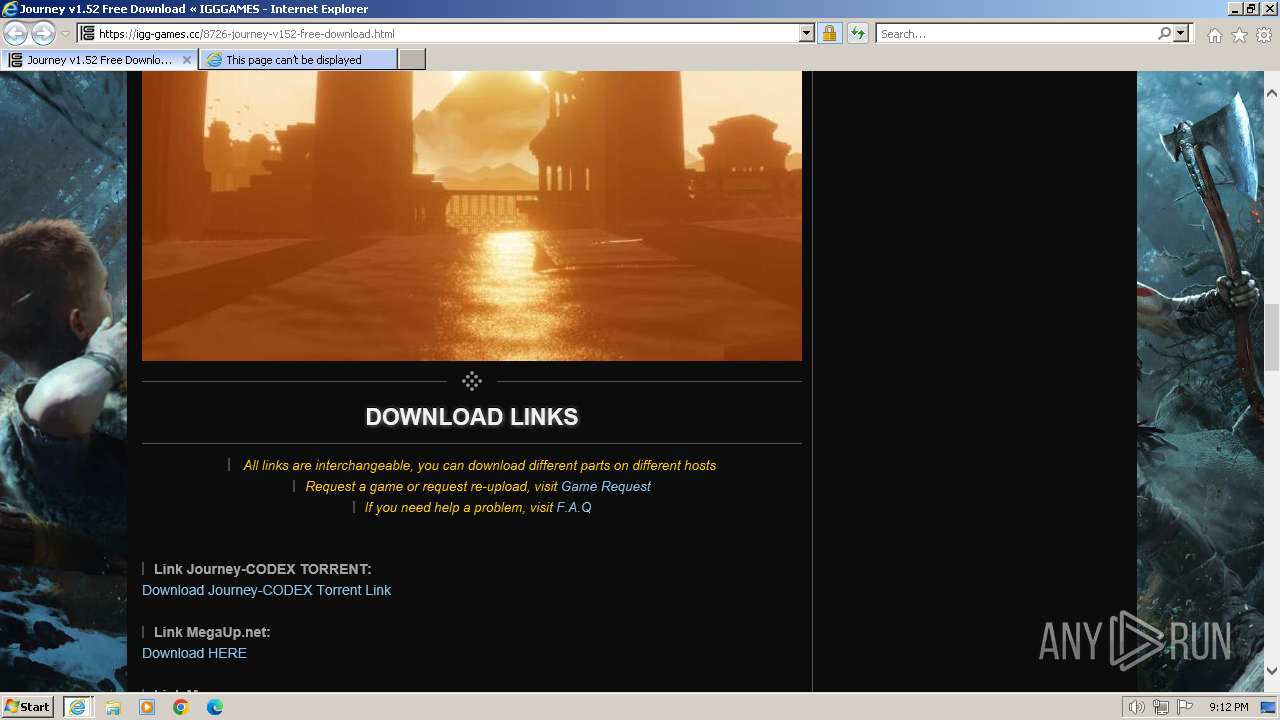
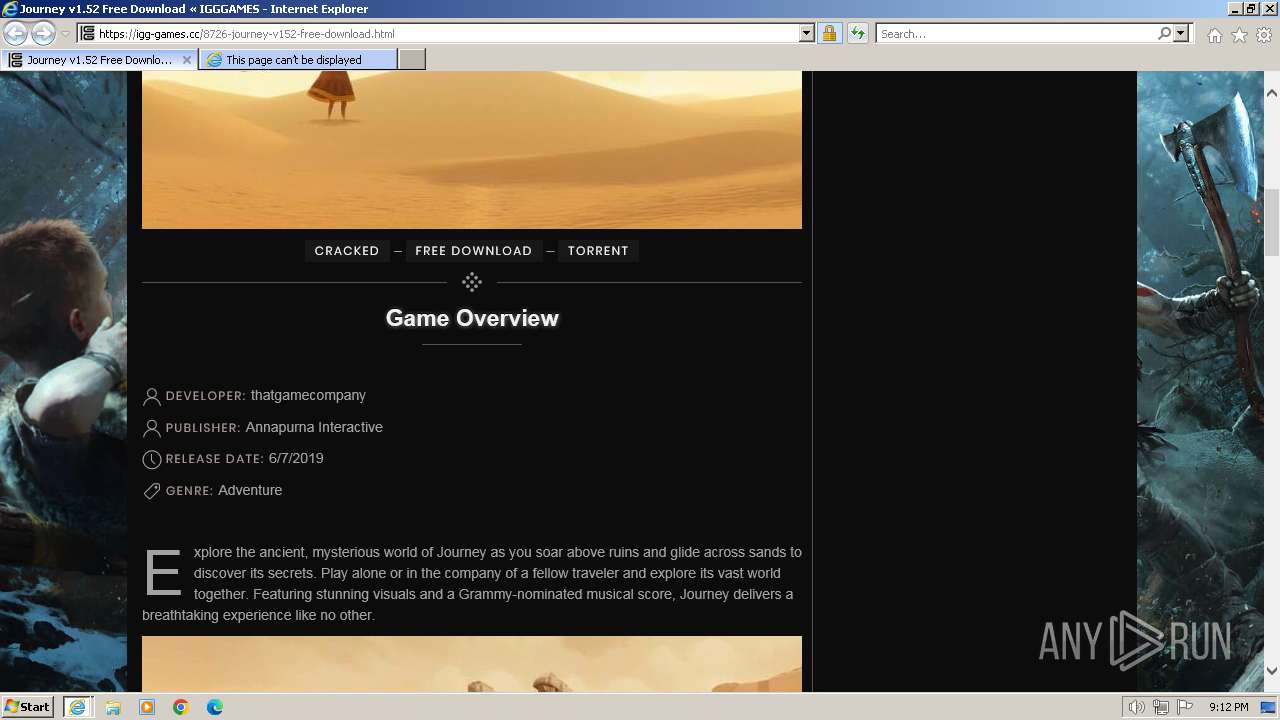
| URL: | https://igg-games.cc/8726-journey-v152-free-download.html |
| Full analysis: | https://app.any.run/tasks/23fd20a0-9289-48d6-af29-6dbdfb28ccd6 |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2024, 21:11:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 87942BFFACBCE7C516F132E9E6E98A1D |
| SHA1: | 1FA3F485EA95229D21A4CADC41152FE9C1F2FBCE |
| SHA256: | 44B9090909A2039B151958A2CE9A11C0A09586546805631375FC48553EBC5726 |
| SSDEEP: | 3:N8igdSDZClu2LyFnQ:2pdaYlHLwQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1740 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3672 CREDAT:922906 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3672 CREDAT:267557 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3672 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://igg-games.cc/8726-journey-v152-free-download.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3692 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3672 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
44 098
Read events
43 934
Write events
119
Delete events
45
Modification events
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31093551 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31093551 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
49
Text files
98
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:0C30D19A17A2E136BDBBF5A9BFA50F0A | SHA256:722DD0FA2B47DE542F5734EDE60E8582E5F5E3199A575BF6771F86FD2C7F3A7B | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\clock[1].svg | image | |
MD5:259D0F1A2B7042877F7F31E7E7FFBC9C | SHA256:F73597AF2EF246AA0E45E16AD21C89EE90B85025DF1D6F1EA7CF460D9DBF7038 | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\8726-journey-v152-free-download[1].htm | html | |
MD5:524DF4965B677FB6A05536C6AD4B3569 | SHA256:3E24CC634735BA5E76157C711A1D5AB81F1C0990D77266AFB73900EEF1FF6244 | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:5AE8478AF8DD6EEC7AD4EDF162DD3DF1 | SHA256:FE42AC92EAE3B2850370B73C3691CCF394C23AB6133DE39F1697A6EBAC4BEDCA | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:013AF7F01CAA5CB61FA6326705AD9979 | SHA256:E529E0A5BF2D387F826CBB1B9FA9BEC3DCE36F324B1AF1FB4D74B323FA0C7E6F | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\logo-1[1].png | image | |
MD5:2A0E3B5067B0262FF4D8B05CF51EFD53 | SHA256:949143C983BC5A7ABFE2907F53A238E29D4B80CCB50FA843FA2AB1DD6009EDE6 | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\user[1].svg | image | |
MD5:E4284B298A505CEFCF161336A272063B | SHA256:F507D345BC6BB9120B23AEAB6CC16CD60A0CADA262F8A93A68E5CAAF0359CE67 | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:7E8F359F842F63D4F8E11B673E763622 | SHA256:F04843E27AB3A622E565EEA01945462567D713146B1CBCA62C89D2495E924450 | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\tag[1].svg | image | |
MD5:3BFD34B8BD231637F4444E640AE09218 | SHA256:4C803F4FCE9D559A2DD22476D5054E7568D48A4EA762697FC09933A38042EF73 | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\all.min[1].css | text | |
MD5:38E4D309F12D379C31871E9495DA2BAA | SHA256:2E1098483F9DC17D6A773CA59551FA45290DEE7F3F4A548F62D4623BE99C04D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
101
DNS requests
40
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3692 | iexplore.exe | GET | 304 | 92.123.121.47:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?148aa66c17cd606b | CL | — | — | unknown |
3692 | iexplore.exe | GET | 304 | 92.123.121.47:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5b0325f31ae0f9b6 | CL | — | — | unknown |
3692 | iexplore.exe | GET | 200 | 92.123.121.47:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?545e1839169dd0e6 | CL | compressed | 67.5 Kb | unknown |
3692 | iexplore.exe | GET | 200 | 92.123.121.47:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a08f35fbea17b647 | CL | compressed | 67.5 Kb | unknown |
3692 | iexplore.exe | GET | 200 | 92.123.121.47:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5918840f29737909 | CL | compressed | 67.5 Kb | unknown |
3692 | iexplore.exe | GET | 200 | 2.20.144.232:80 | http://x1.c.lencr.org/ | BR | binary | 717 b | unknown |
3692 | iexplore.exe | GET | 200 | 2.20.144.232:80 | http://x2.c.lencr.org/ | BR | binary | 299 b | unknown |
3692 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
3692 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | US | binary | 724 b | unknown |
3692 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | binary | 1.42 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3692 | iexplore.exe | 188.114.97.3:443 | igg-games.cc | CLOUDFLARENET | NL | unknown |
3692 | iexplore.exe | 92.123.121.47:80 | ctldl.windowsupdate.com | Akamai International B.V. | CL | unknown |
3692 | iexplore.exe | 2.20.144.232:80 | x1.c.lencr.org | Akamai International B.V. | BR | unknown |
3692 | iexplore.exe | 104.26.4.60:443 | igg-games.com | CLOUDFLARENET | US | unknown |
3692 | iexplore.exe | 172.217.18.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3692 | iexplore.exe | 192.243.59.20:443 | pennilesscomingall.com | DataWeb Global Group B.V. | US | unknown |
3692 | iexplore.exe | 199.232.192.134:443 | igggames-cc.disqus.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
igg-games.cc |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
igg-games.com |
| whitelisted |
pennilesscomingall.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
igggames-cc.disqus.com |
| unknown |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |