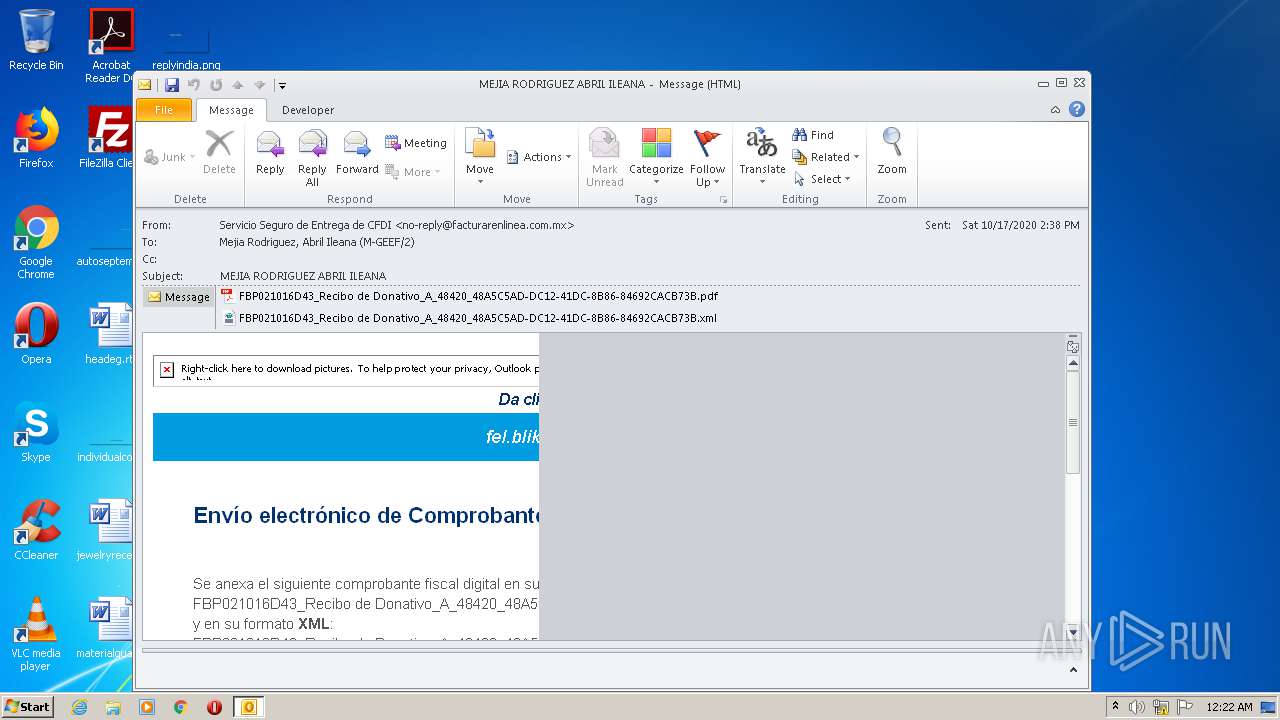
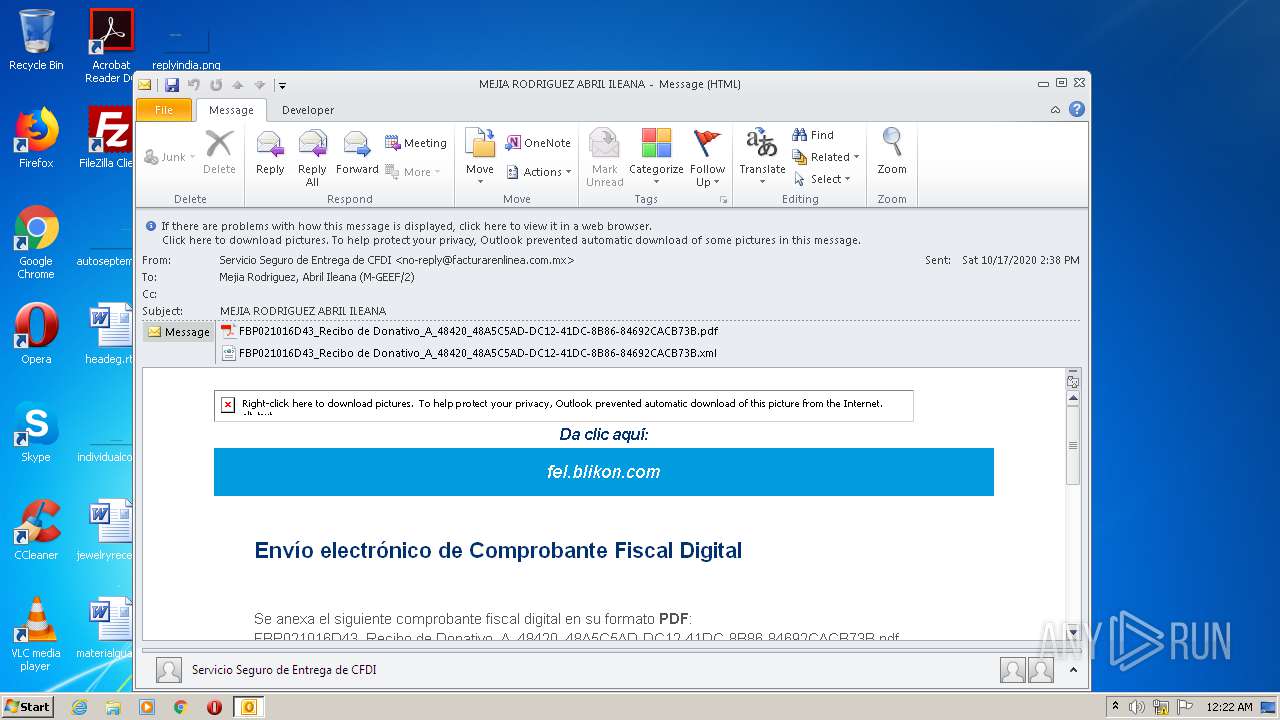
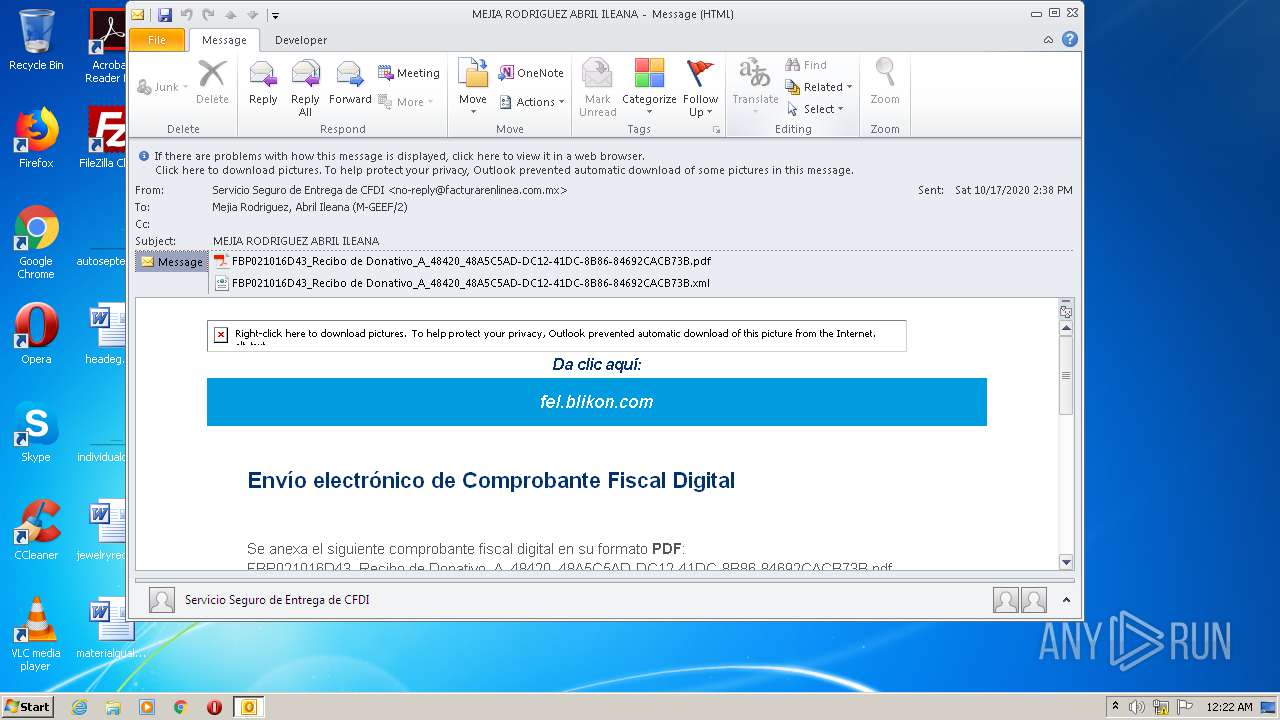
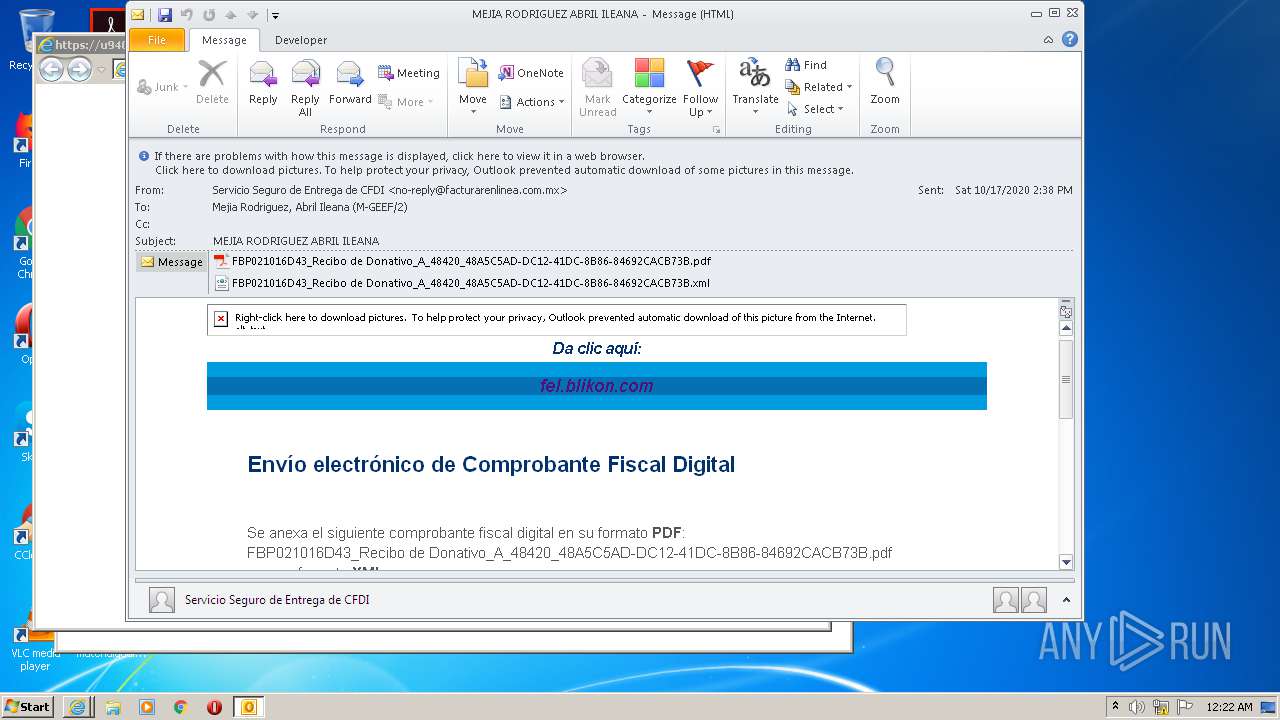
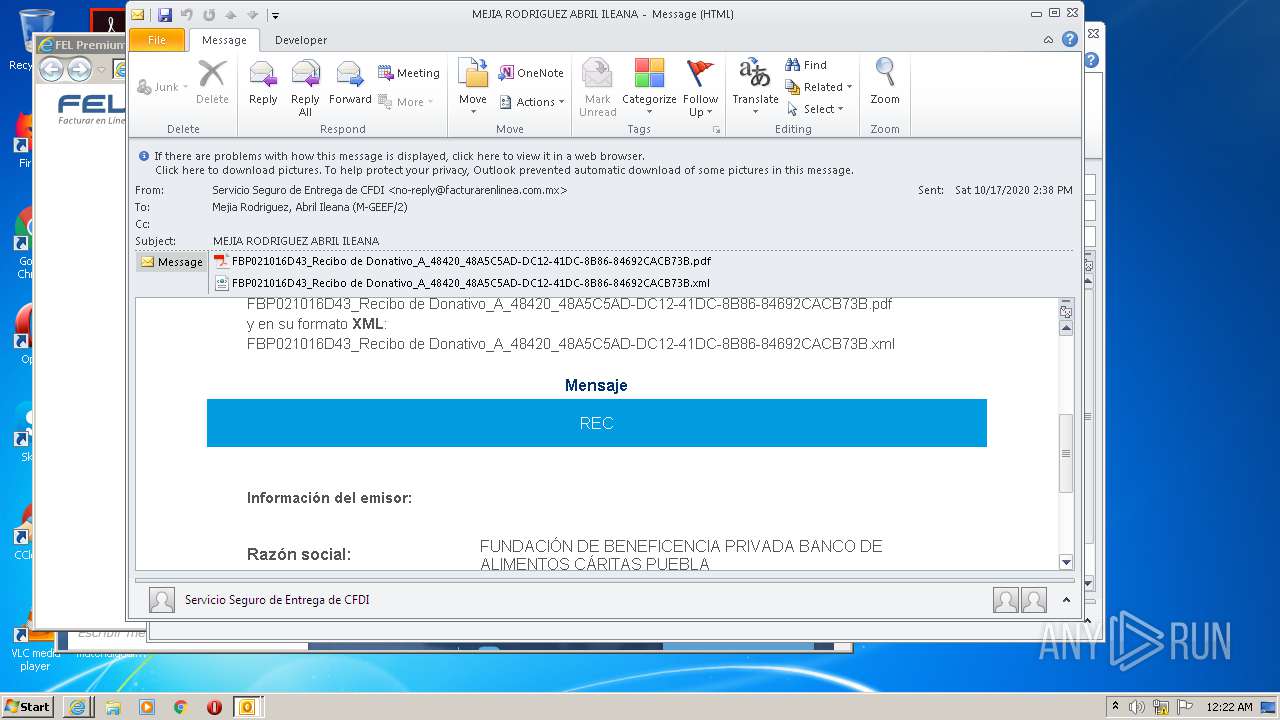
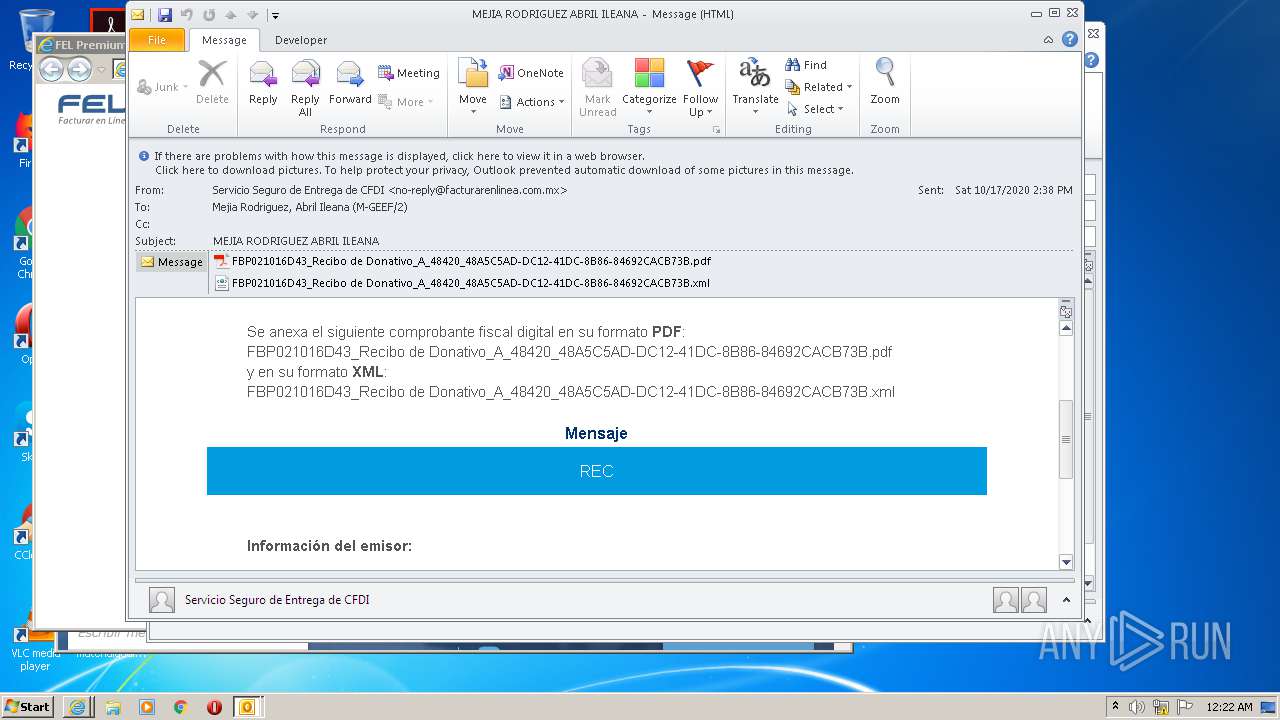
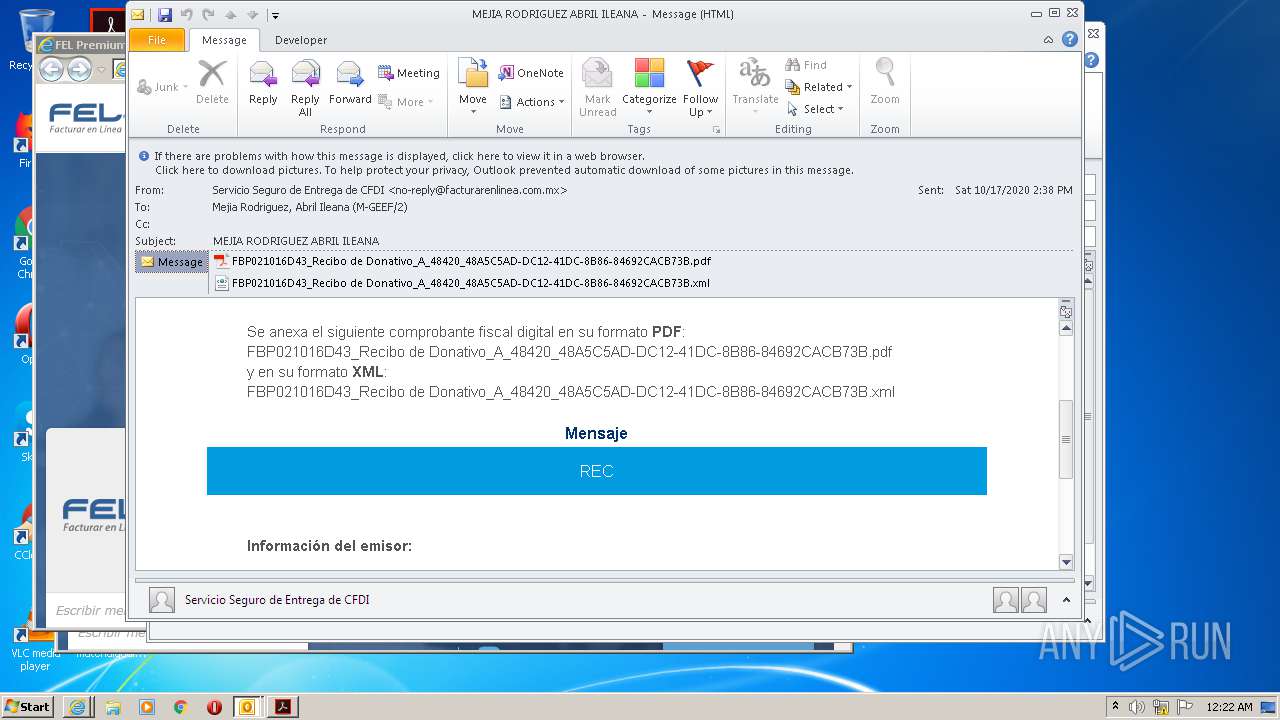
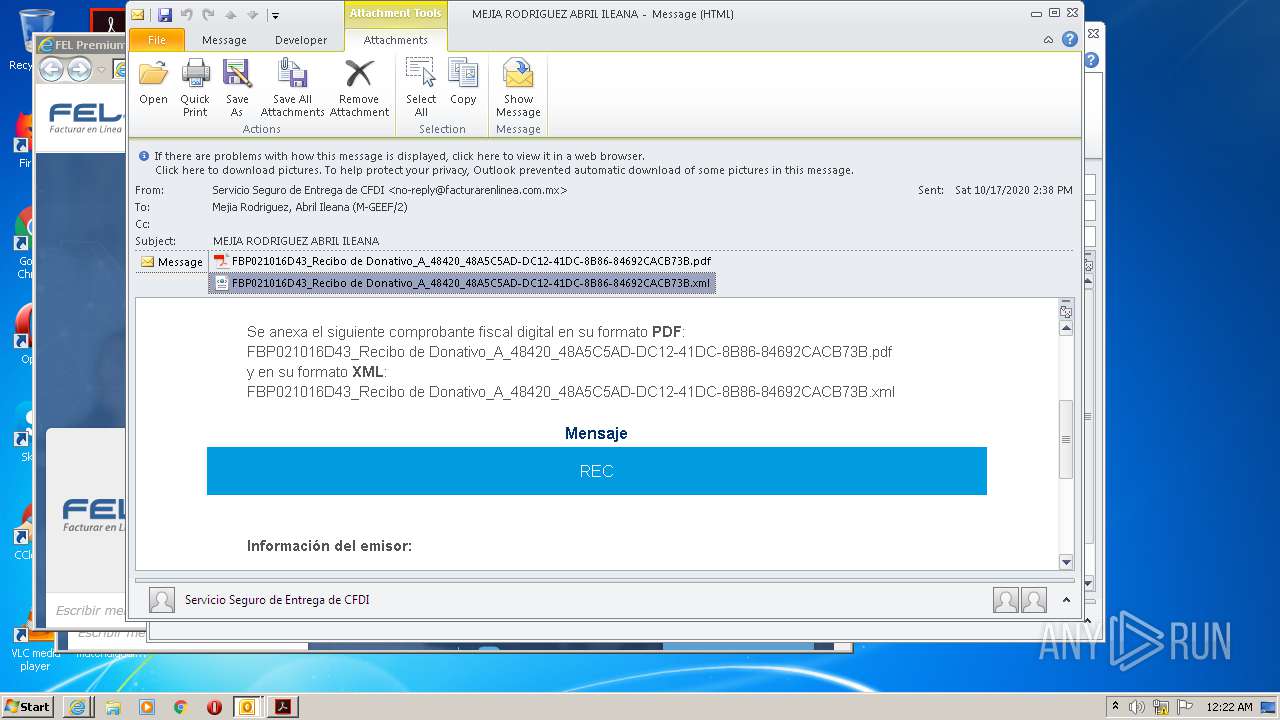
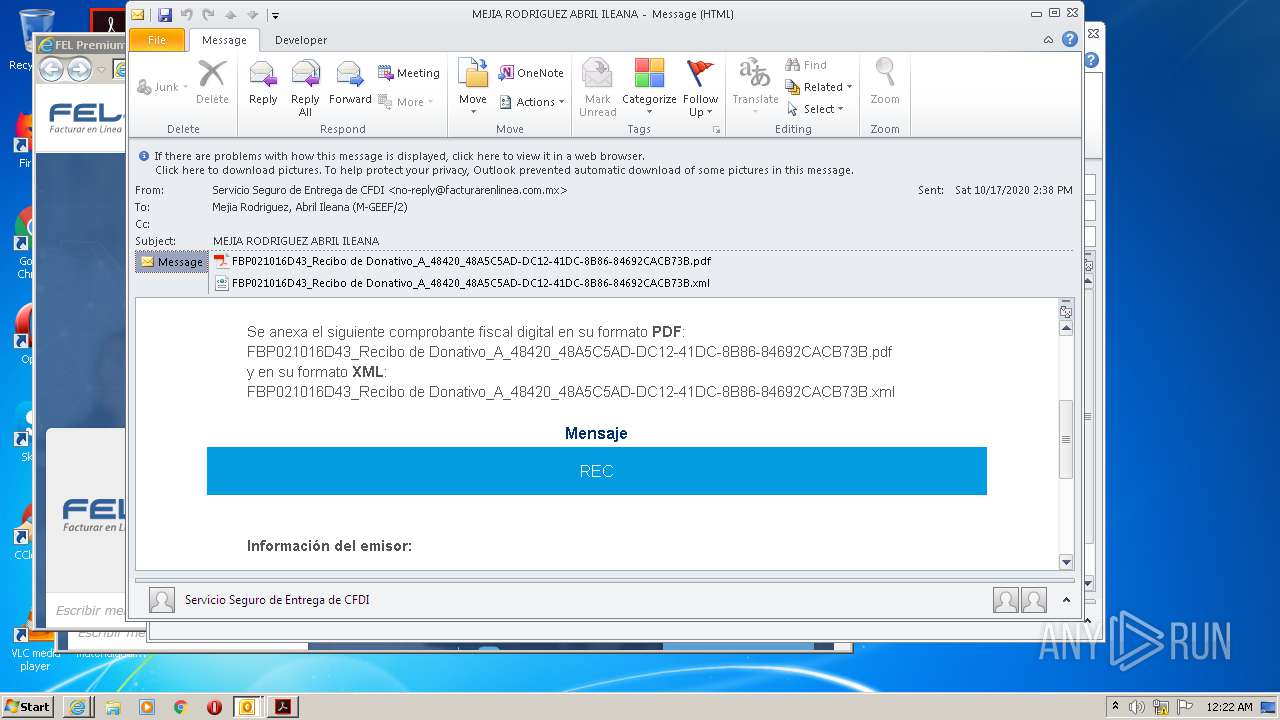
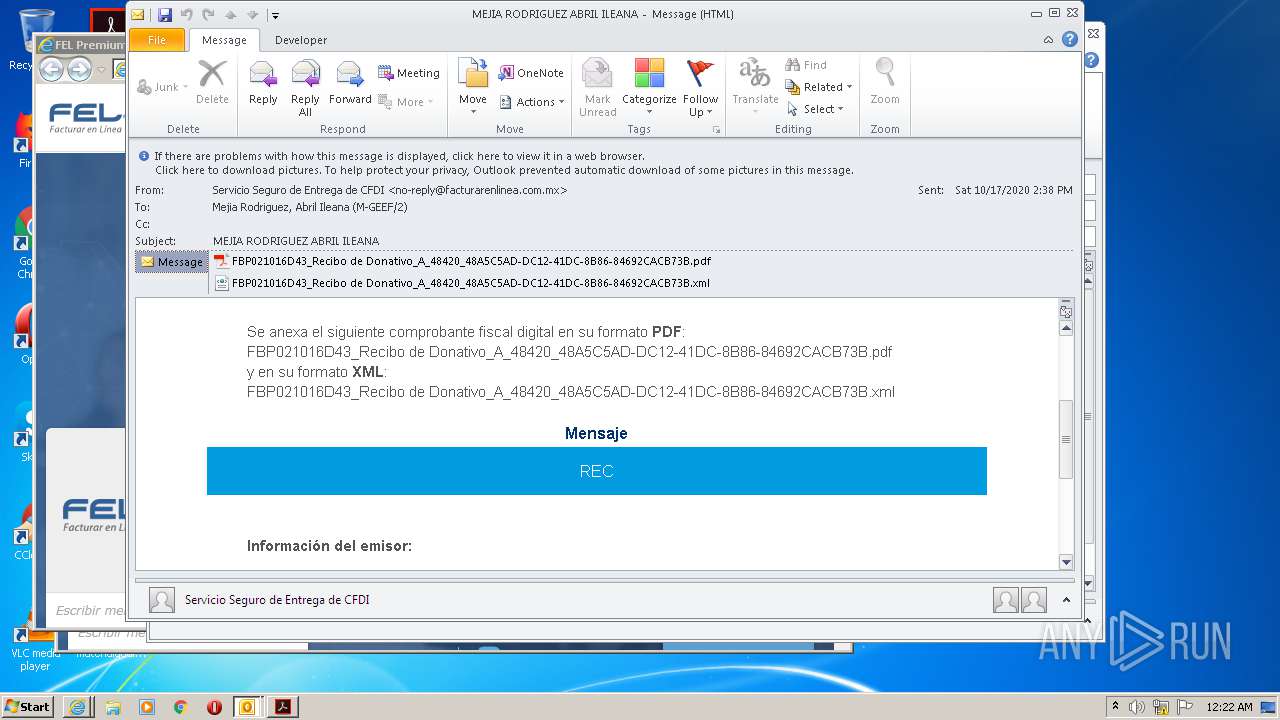
| File name: | MEJIA RODRIGUEZ ABRIL ILEANA.msg |
| Full analysis: | https://app.any.run/tasks/0ef7f20c-7371-4979-a732-5c1dcc540e04 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 23:21:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 8CAB8659CB10236E0B8FB417534B3D94 |
| SHA1: | 316778036534AB496ECF2B6DE8831E9E930278B5 |
| SHA256: | 44A93EFE25B300434A39F2BE94A8C1879A10B8D3DAB19496E59DAC7F400BB2B1 |
| SSDEEP: | 6144:sfGnYndrJlFOEk8e91AMxVbipEKuNP3VbipJKuNn:Cd1vOZ791AMVb2ETFVb2JT |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 1888)
SUSPICIOUS
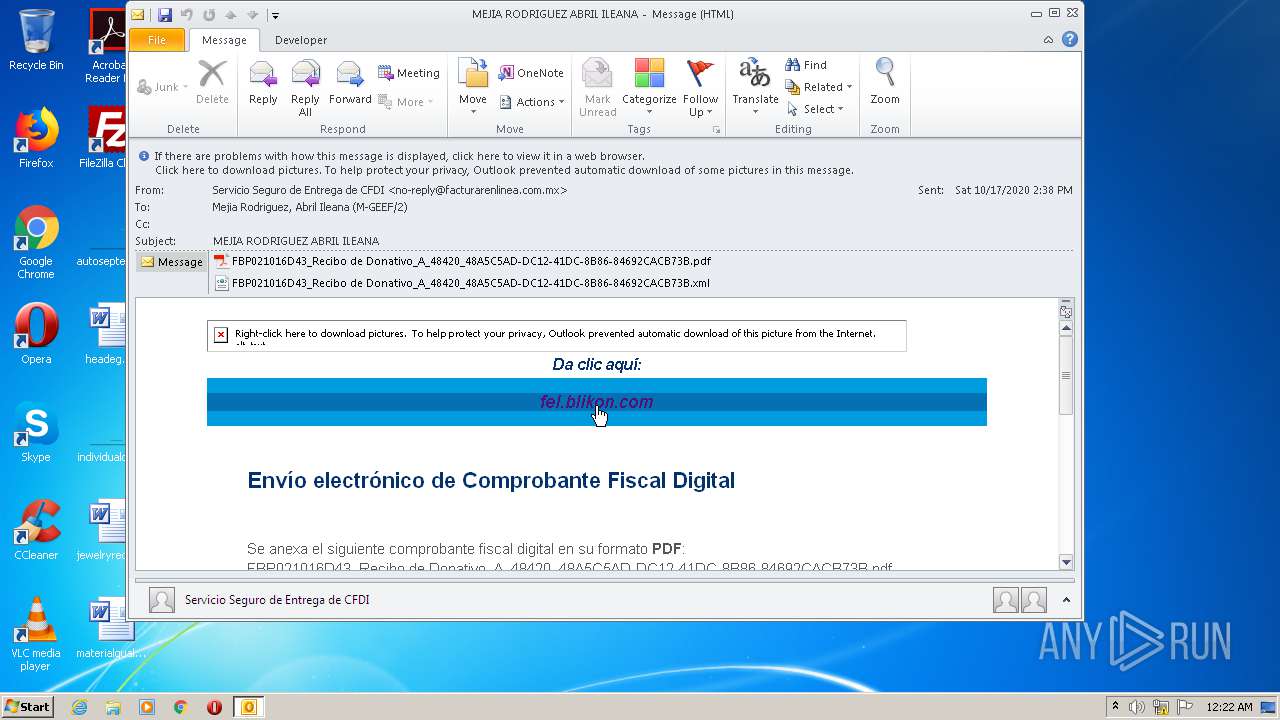
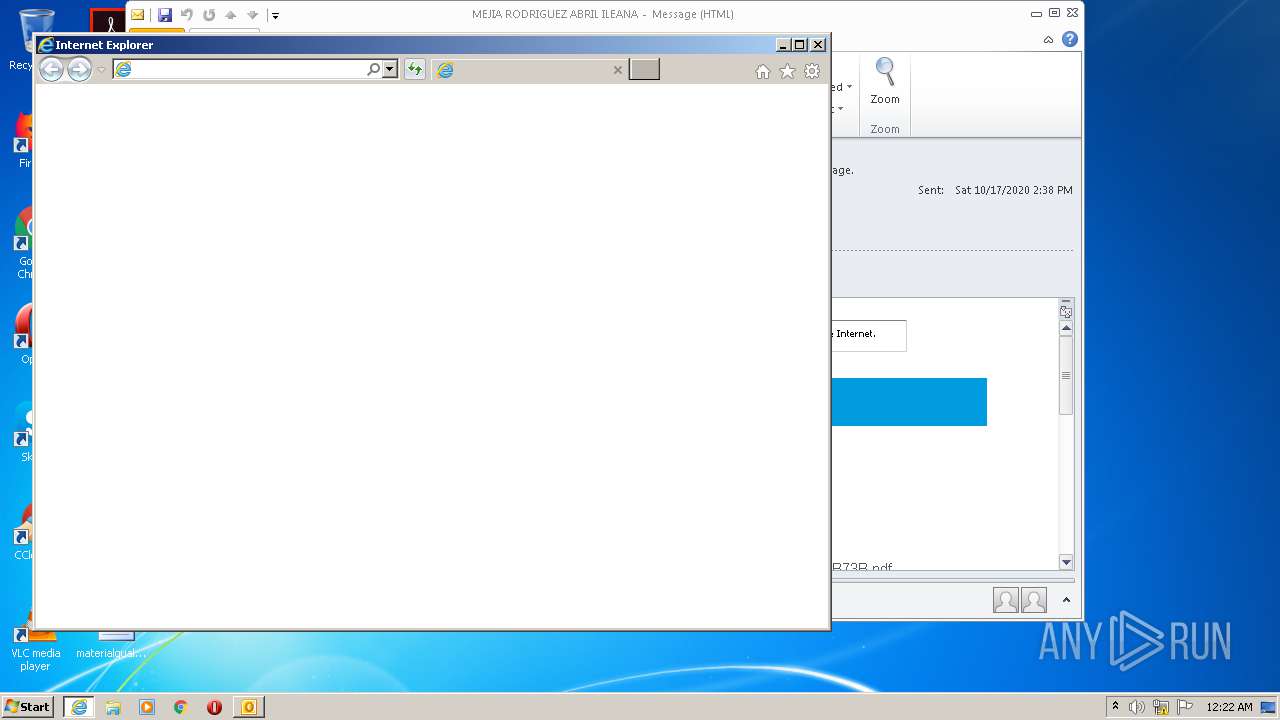
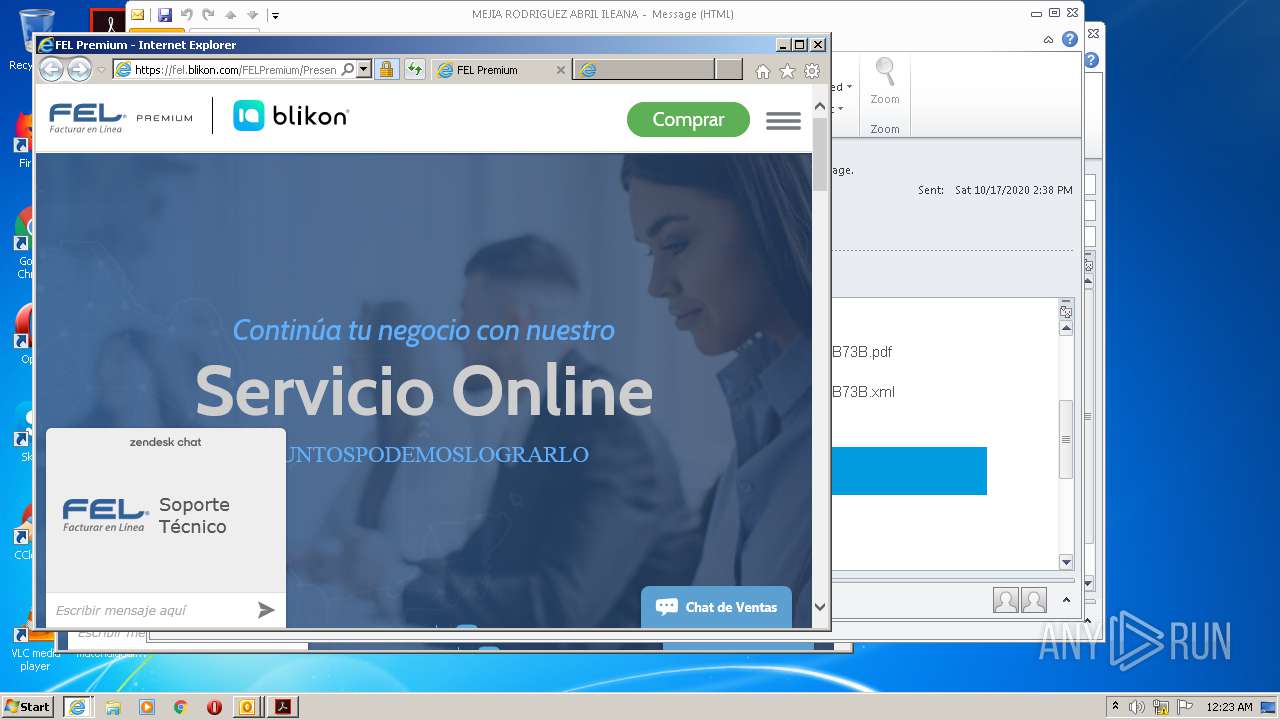
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1888)
Starts itself from another location
- OUTLOOK.EXE (PID: 1888)
INFO
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 1888)
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 3204)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 3124)
- AcroRd32.exe (PID: 1592)
- AcroRd32.exe (PID: 1304)
- iexplore.exe (PID: 2468)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1888)
- OUTLOOK.EXE (PID: 944)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1888)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 3124)
Application launched itself
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 3204)
- AcroRd32.exe (PID: 1592)
- RdrCEF.exe (PID: 2696)
Reads settings of System Certificates
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 3204)
- AcroRd32.exe (PID: 1592)
Changes internet zones settings
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 3204)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 3124)
Reads internet explorer settings
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 2468)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3204)
- iexplore.exe (PID: 2516)
Changes settings of System certificates
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 3204)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 1592)
Reads the hosts file
- RdrCEF.exe (PID: 2696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
48
Monitored processes
13
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
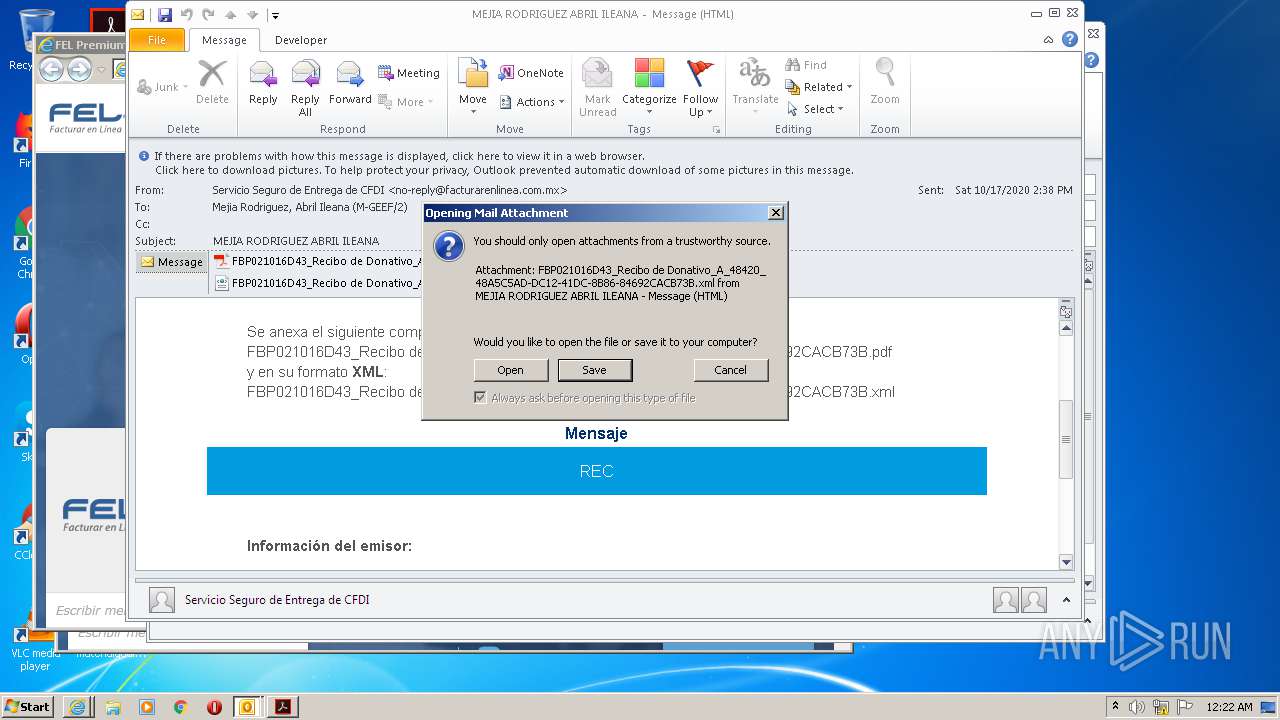
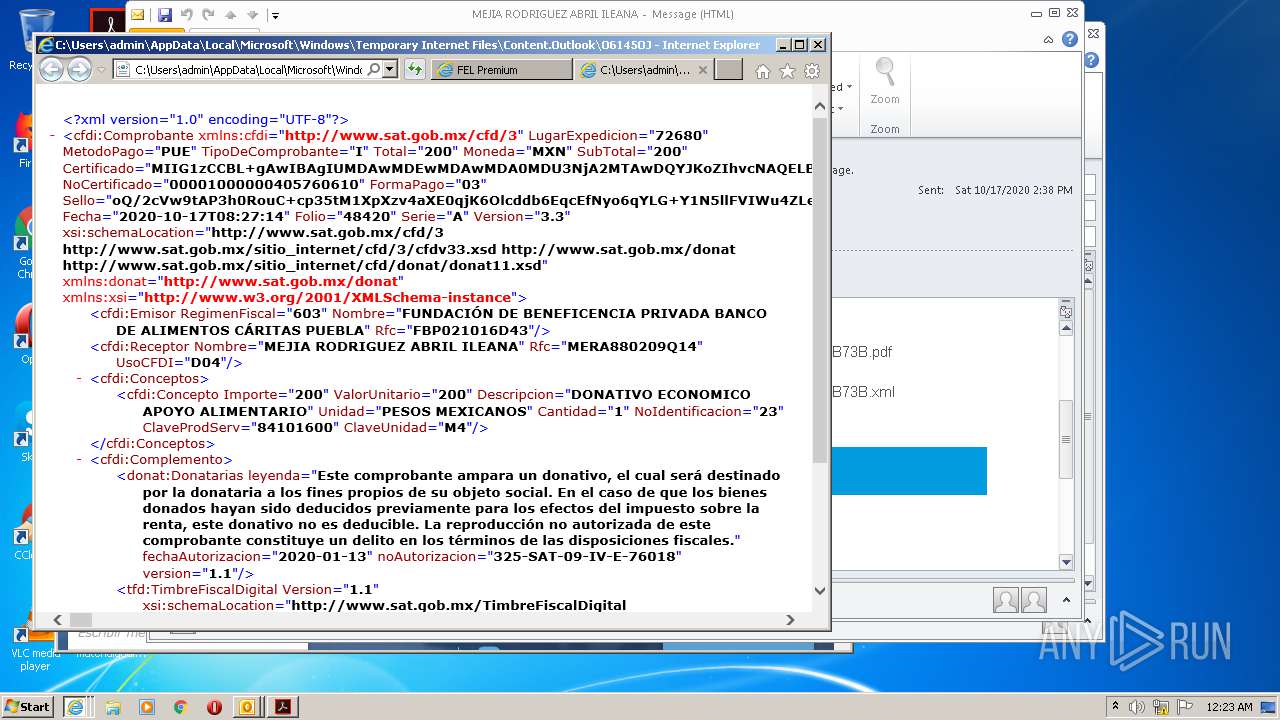
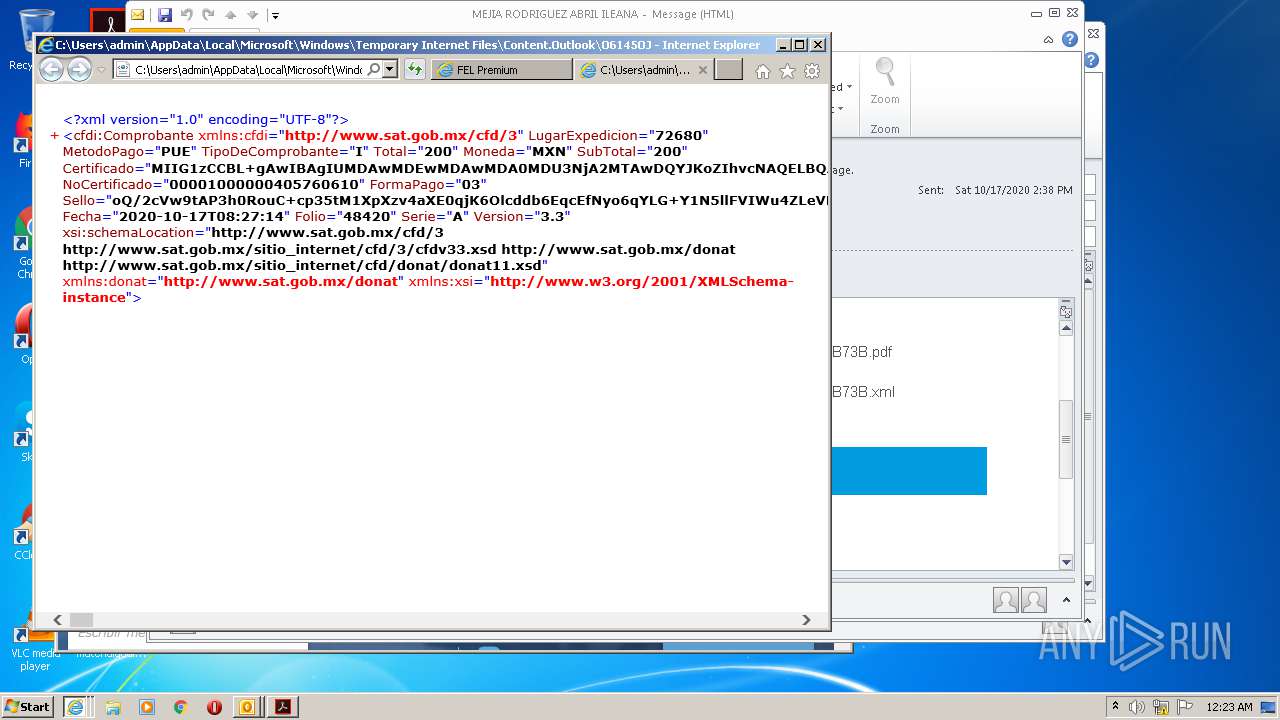
| 556 | "C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE" /verb open "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\O6145OJL\FBP021016D43_Recibo de Donativo_A_48420_48A5C5AD-DC12-41DC-8B86-84692CACB73B.xml" | C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: XML Editor Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3204 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
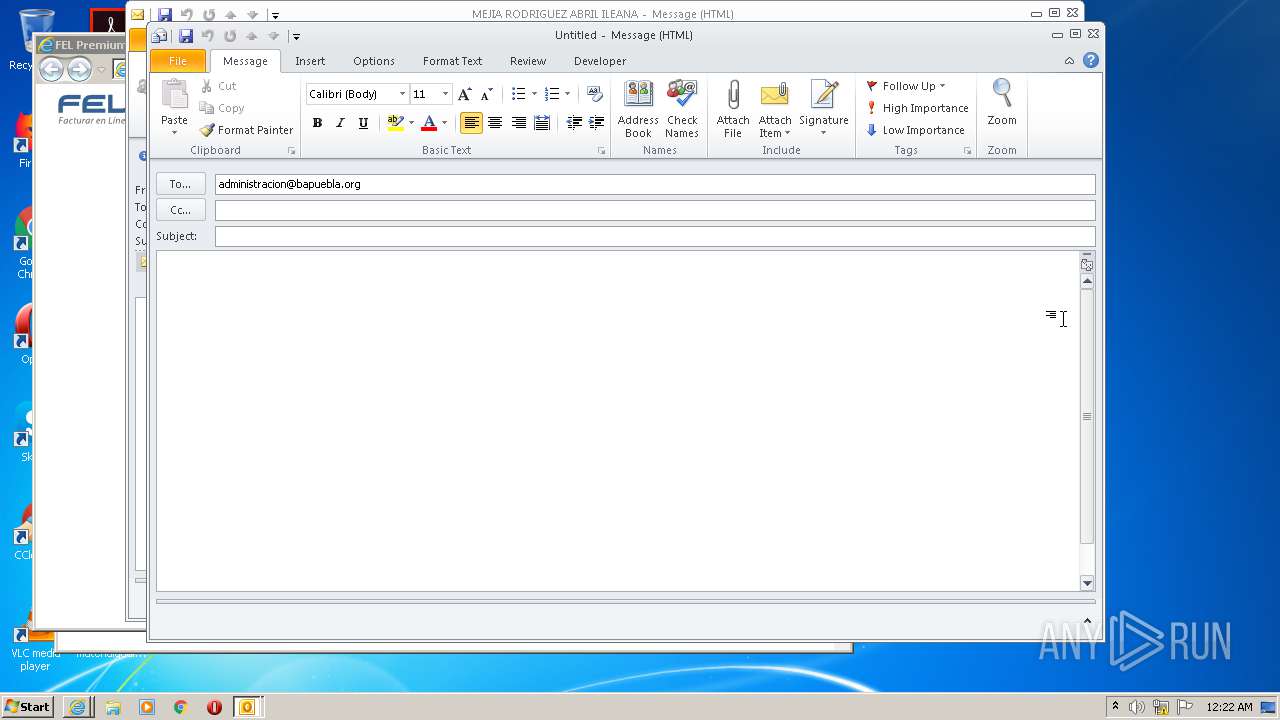
| 944 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:administracion@bapuebla.org" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
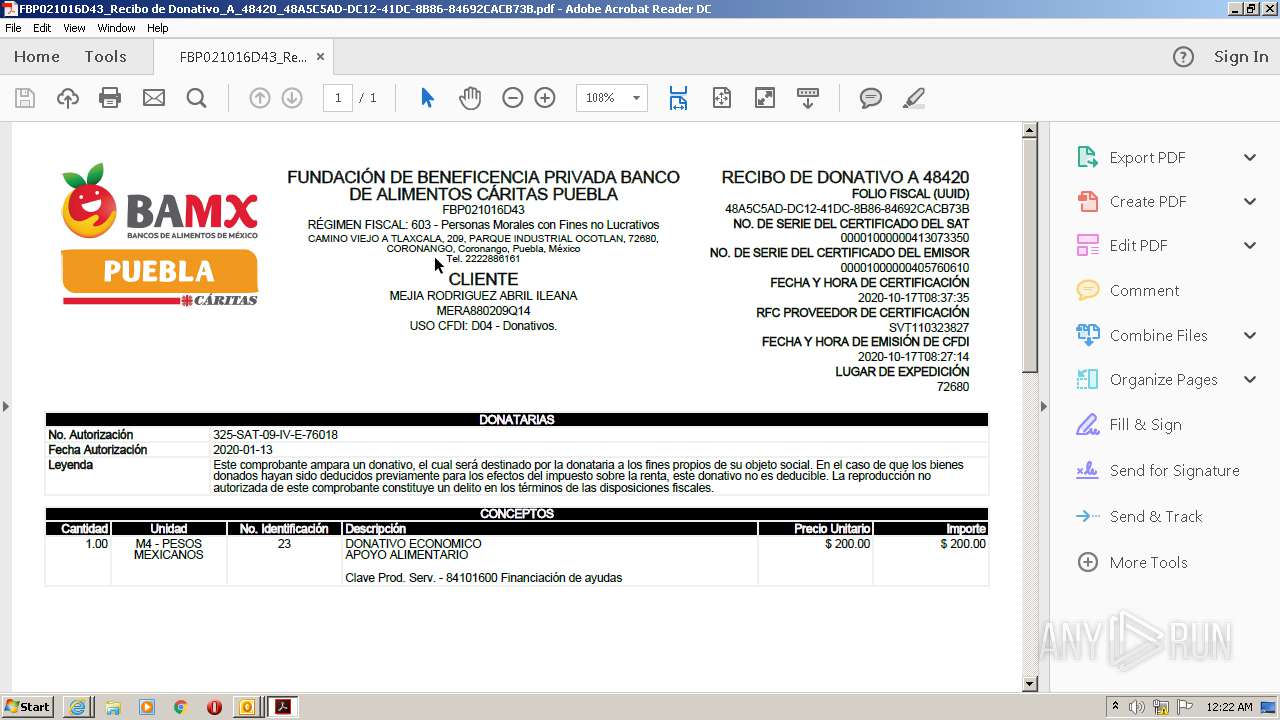
| 1304 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\O6145OJL\FBP021016D43_Recibo de Donativo_A_48420_48A5C5AD-DC12-41DC-8B86-84692CACB73B.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\O6145OJL\FBP021016D43_Recibo de Donativo_A_48420_48A5C5AD-DC12-41DC-8B86-84692CACB73B.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\MEJIA RODRIGUEZ ABRIL ILEANA.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2516 CREDAT:2888971 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Internet Explorer\iexplore.exe" https://u940138.ct.sendgrid.net/ls/click?upn=Cg2p-2FRTq2KqTebNJNRukqaum6ju7MEhDPrKSoNU32Ek-3DY8QV_NhGQB-2BOJq-2FdB4ecq4ungPiu6zF8IIcAmBDCYdzM0IJA2sNFmaPfuFz0FyGzQspXRrJrC54fUcIr94qFU5v2783pWTMKsvmfE0vAqaM6EEoJ6uf-2BuKQc31F9tnqKnYXnpFQ8ENfaDwrYaFLtDIoW1LkyAClxsCgtyeN5v5Snux69rb44muGk-2B3tpQmzArUc2uUAF687YuXM5psJcfmyXLiA-3D-3D | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2696.0.1256258825\1153884357" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2696 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
Total events
3 702
Read events
2 661
Write events
1 007
Delete events
34
Modification events
| (PID) Process: | (1888) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1888) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1888) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1888) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1888) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1888) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1888) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1888) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1888) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1888) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
146
Text files
209
Unknown types
108
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1888 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR4C53.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3124 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8768.tmp | — | |
MD5:— | SHA256:— | |||
| 3124 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8769.tmp | — | |
MD5:— | SHA256:— | |||
| 636 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B39C403EE7698F732743C79CB583A818_F94572BF13D20C8A2D58EA30B5AB031E | der | |
MD5:— | SHA256:— | |||
| 3124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 636 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8787.tmp | — | |
MD5:— | SHA256:— | |||
| 636 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8788.tmp | — | |
MD5:— | SHA256:— | |||
| 3124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
| 1888 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 636 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
88
TCP/UDP connections
128
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1888 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
636 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
636 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCAFQWPc8P68%2F | US | der | 1.74 Kb | whitelisted |
3124 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3124 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
3124 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
636 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEDwByosFVTbo7nA3ZppRxUI%3D | US | der | 471 b | whitelisted |
3124 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCAFQWPc8P68%2F | US | der | 1.74 Kb | whitelisted |
636 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEDwByosFVTbo7nA3ZppRxUI%3D | US | der | 471 b | whitelisted |
3124 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1888 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3124 | iexplore.exe | 167.89.115.54:443 | u940138.ct.sendgrid.net | SendGrid, Inc. | US | suspicious |
636 | iexplore.exe | 167.89.115.54:443 | u940138.ct.sendgrid.net | SendGrid, Inc. | US | suspicious |
3124 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
636 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
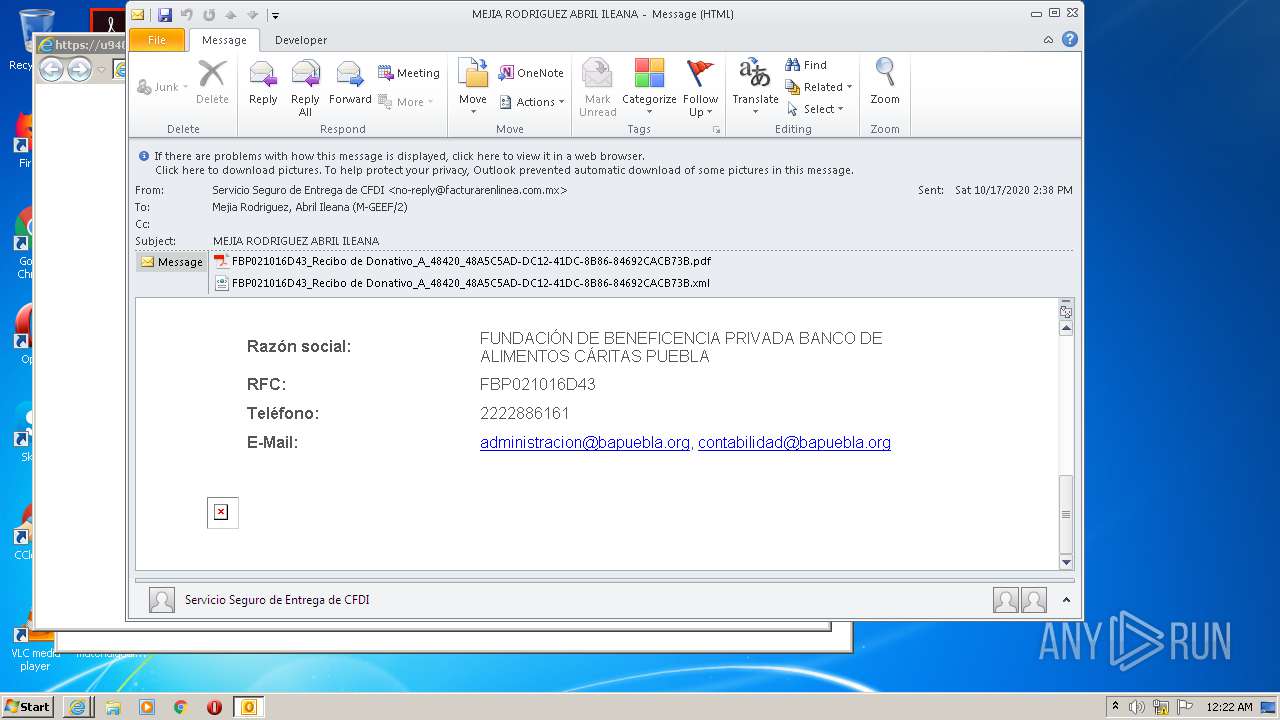
3124 | iexplore.exe | 201.175.24.180:443 | fel.blikon.com | Sixsigma Networks Mexico, S.A. de C.V. | MX | unknown |
2516 | iexplore.exe | 201.175.24.180:443 | fel.blikon.com | Sixsigma Networks Mexico, S.A. de C.V. | MX | unknown |
3204 | iexplore.exe | 201.175.24.180:443 | fel.blikon.com | Sixsigma Networks Mexico, S.A. de C.V. | MX | unknown |
2516 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3124 | iexplore.exe | 13.84.149.34:443 | www.facturarenlinea.com.mx | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
u940138.ct.sendgrid.net |
| suspicious |
ocsp.godaddy.com |
| whitelisted |
fel.blikon.com |
| unknown |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
unpkg.com |
| whitelisted |
www.facturarenlinea.com.mx |
| unknown |