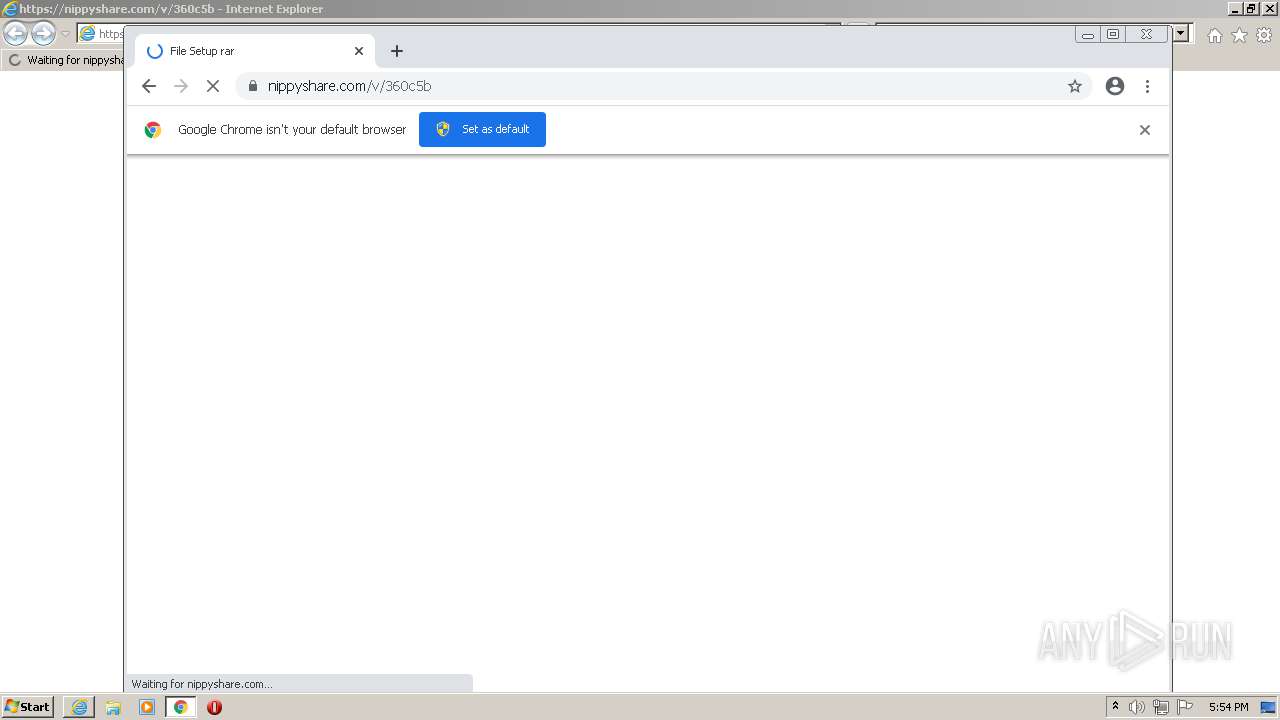
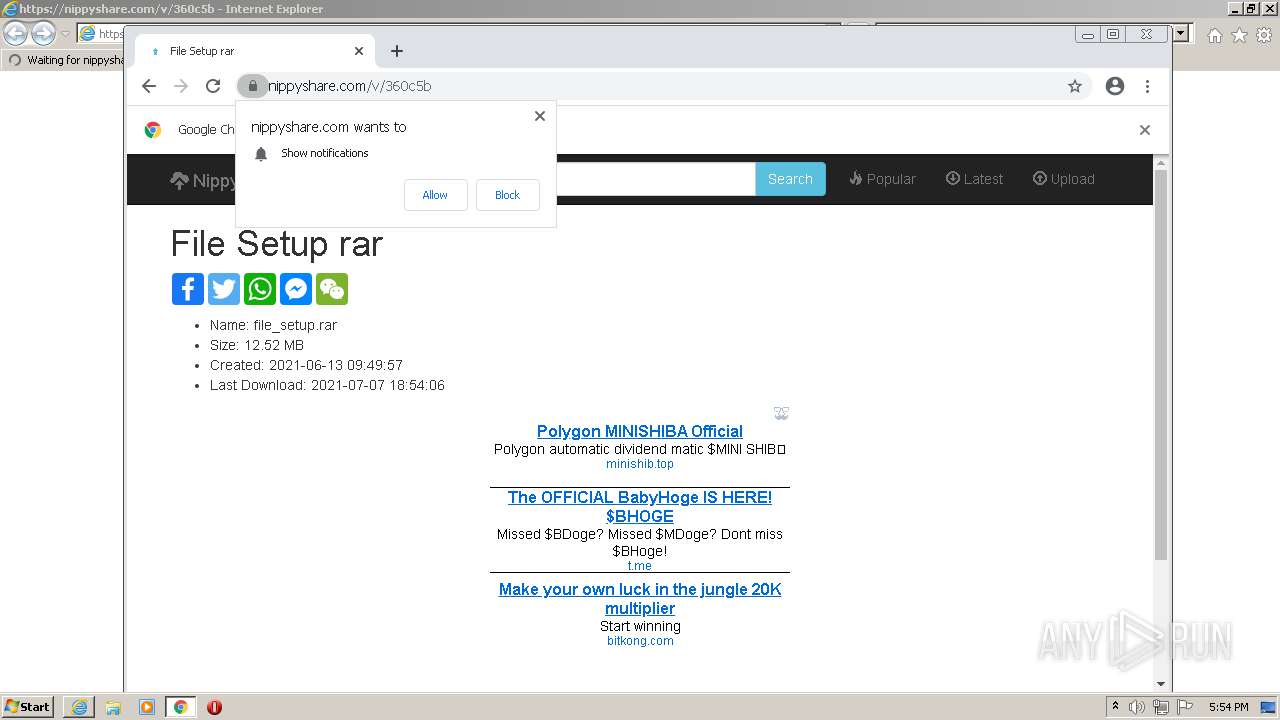
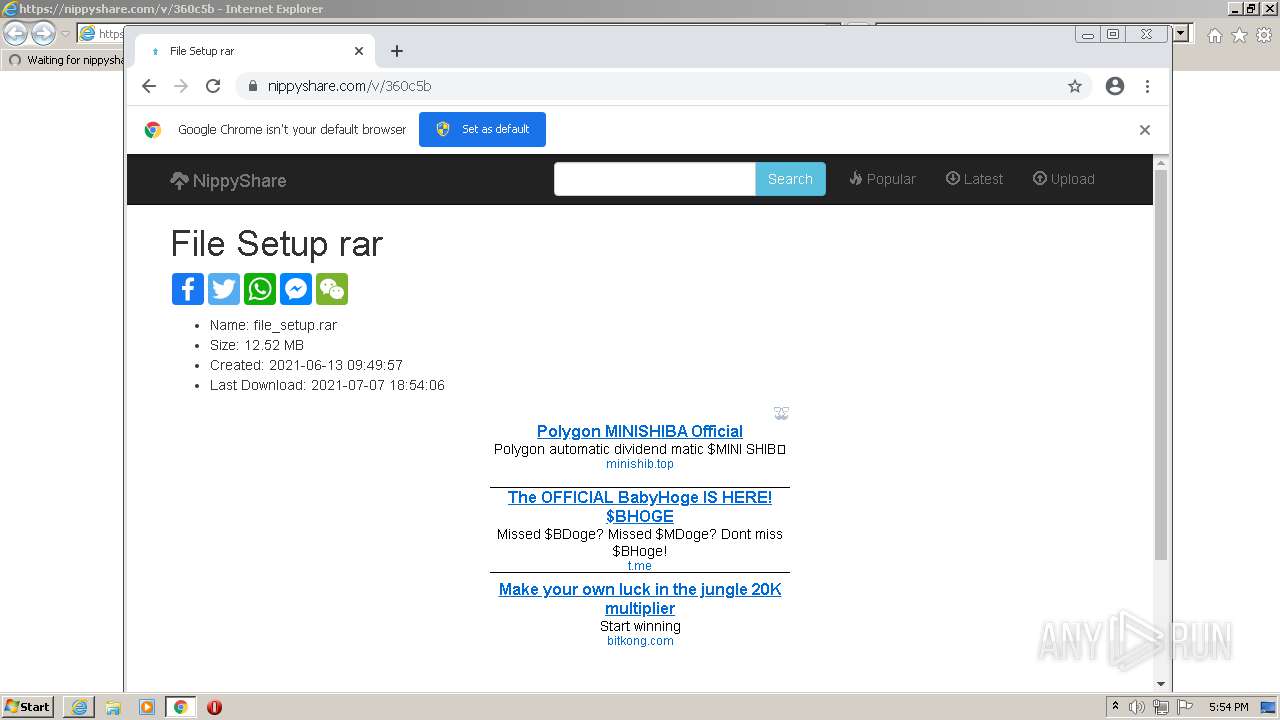
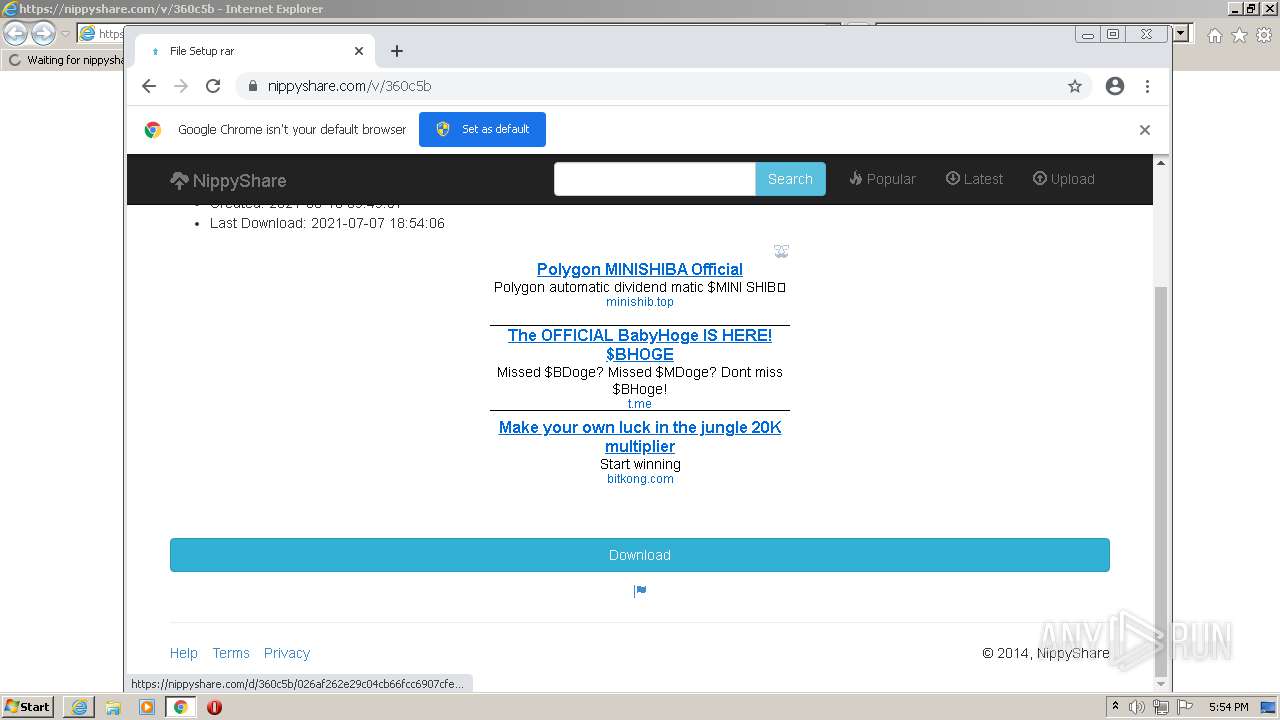
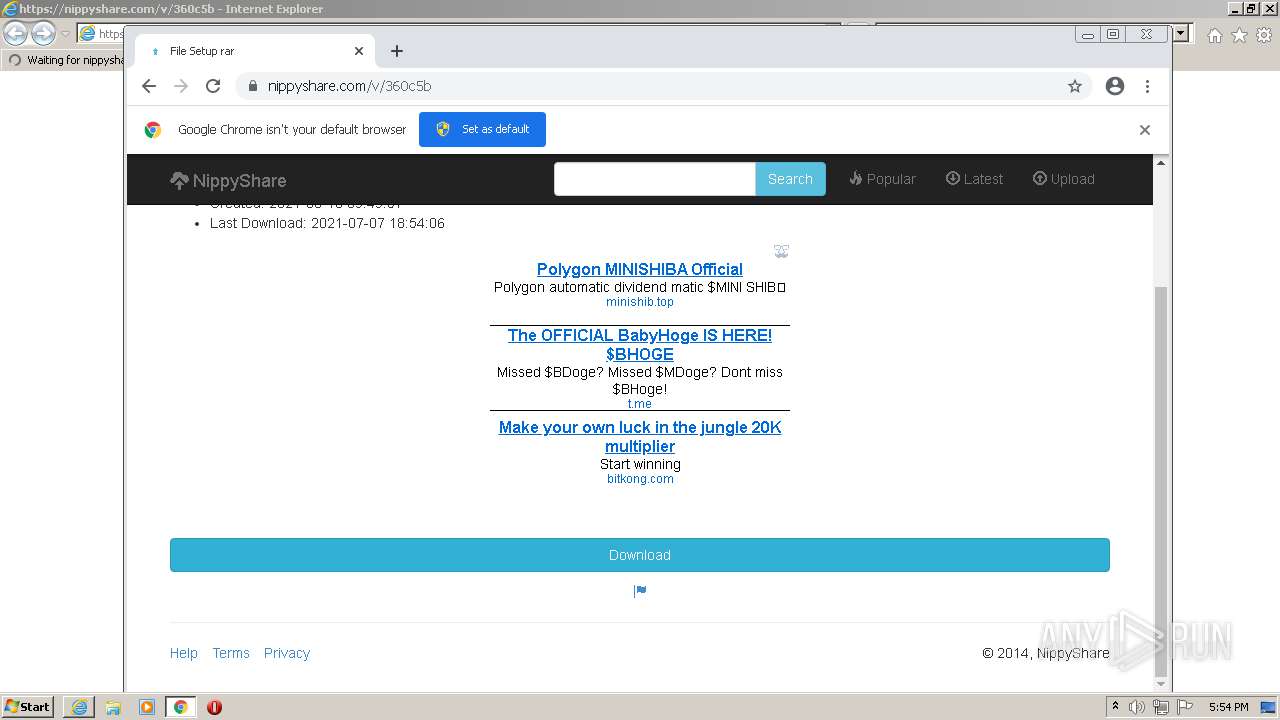
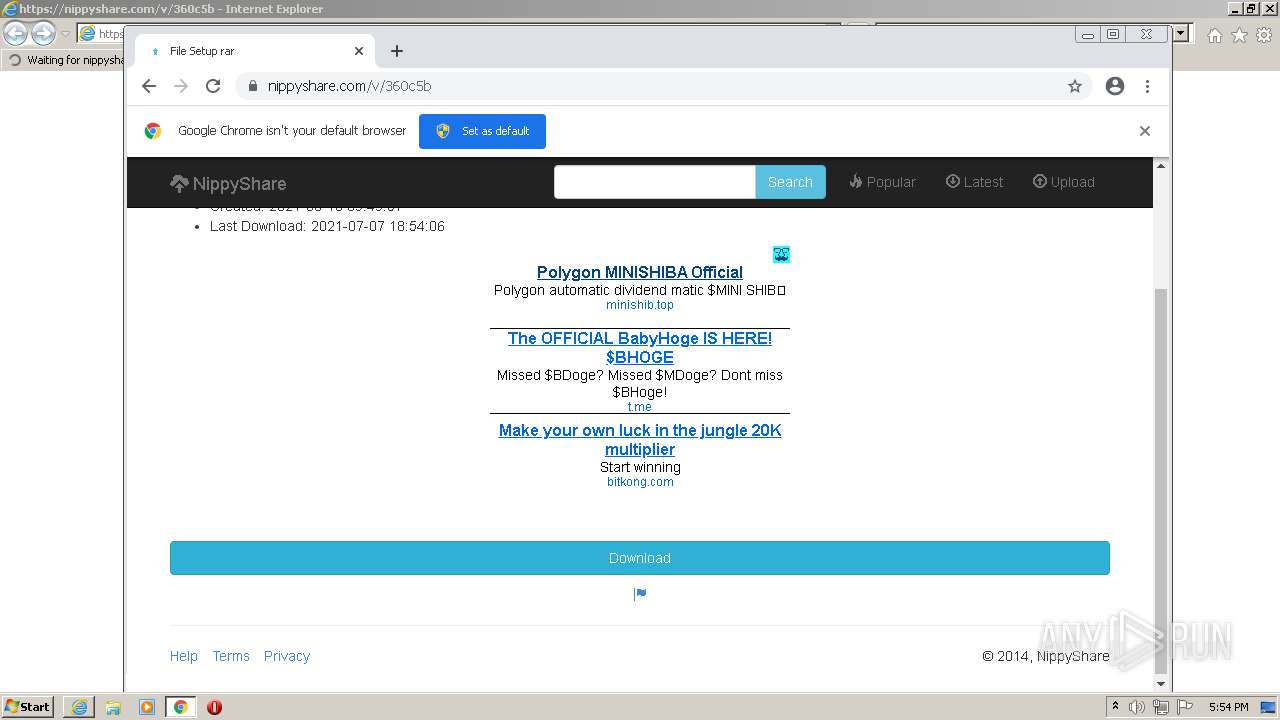
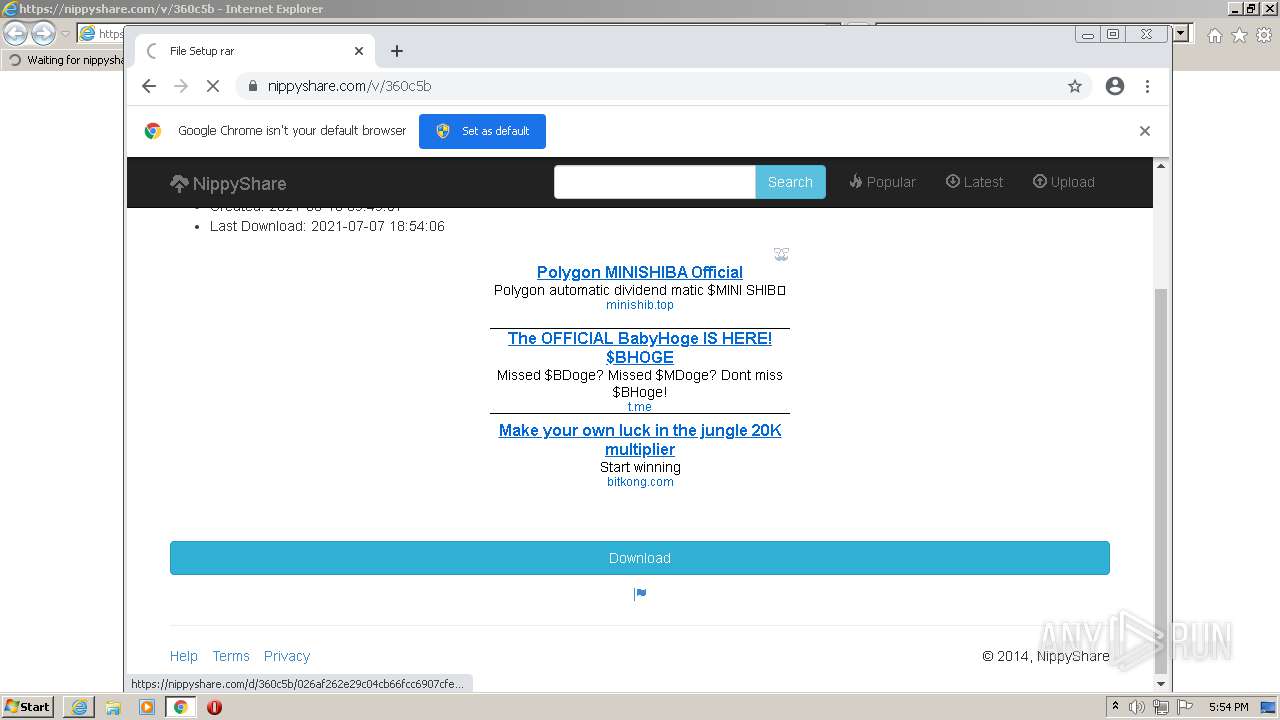
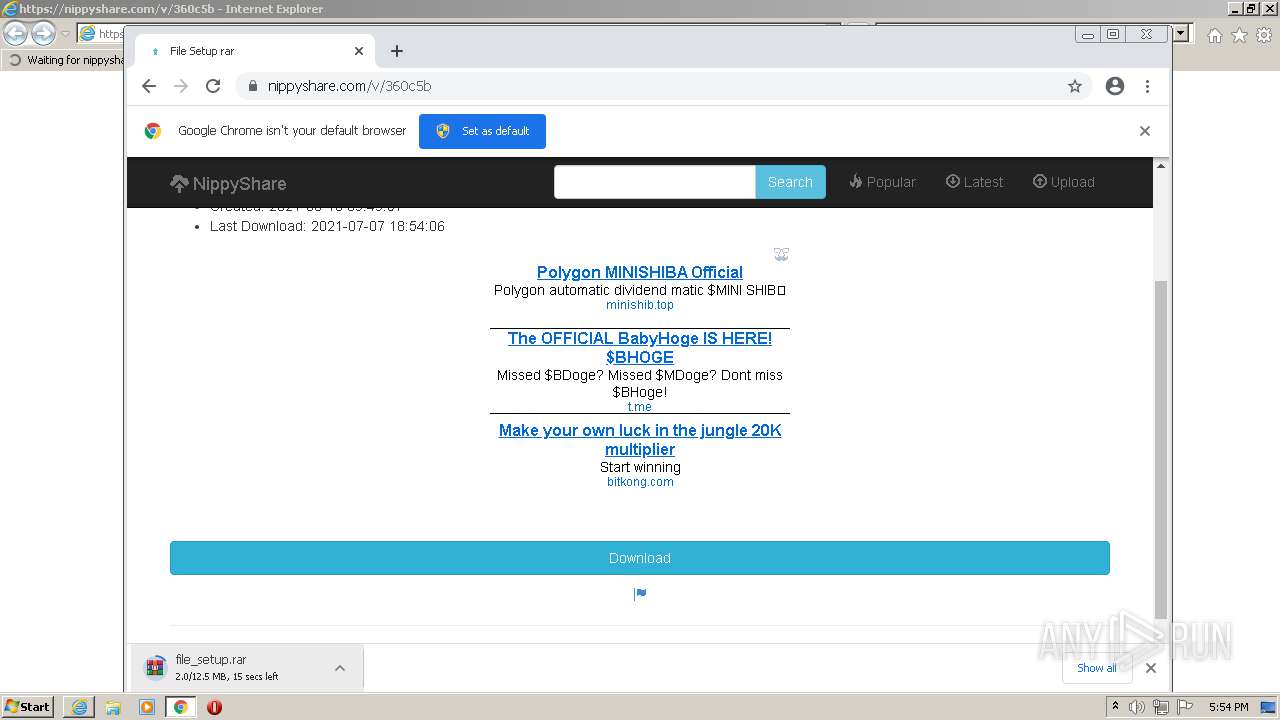
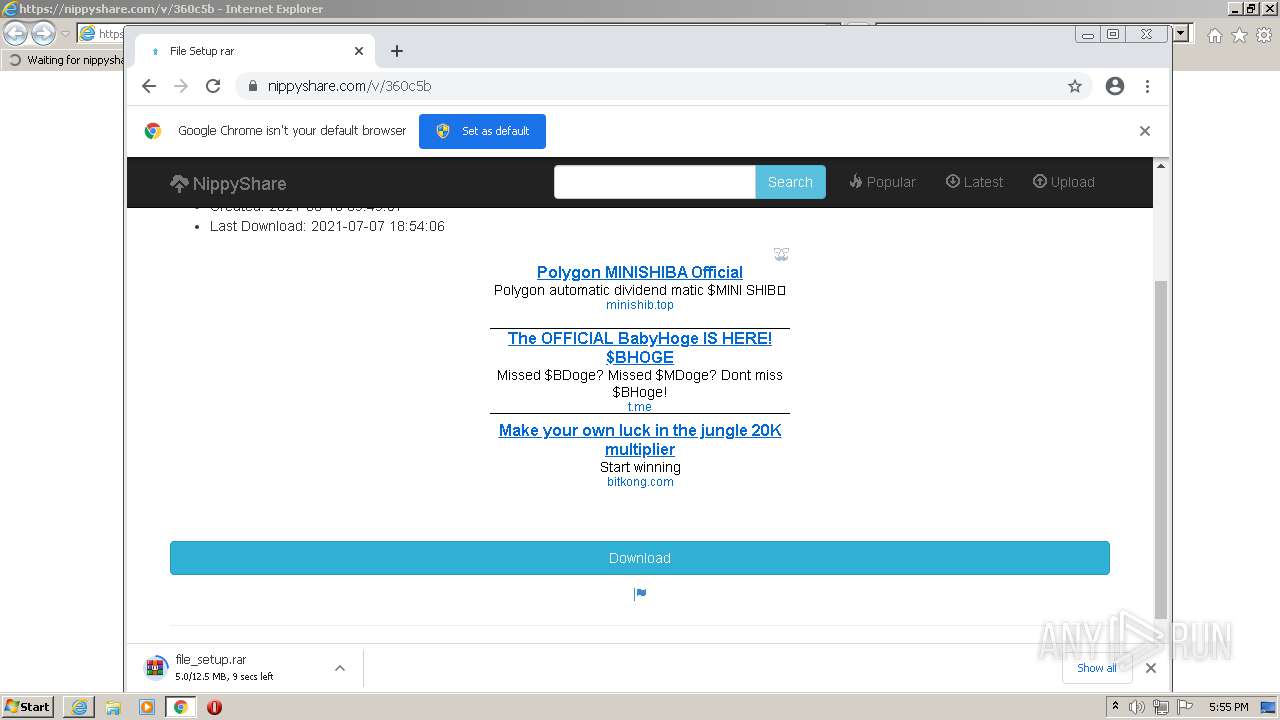
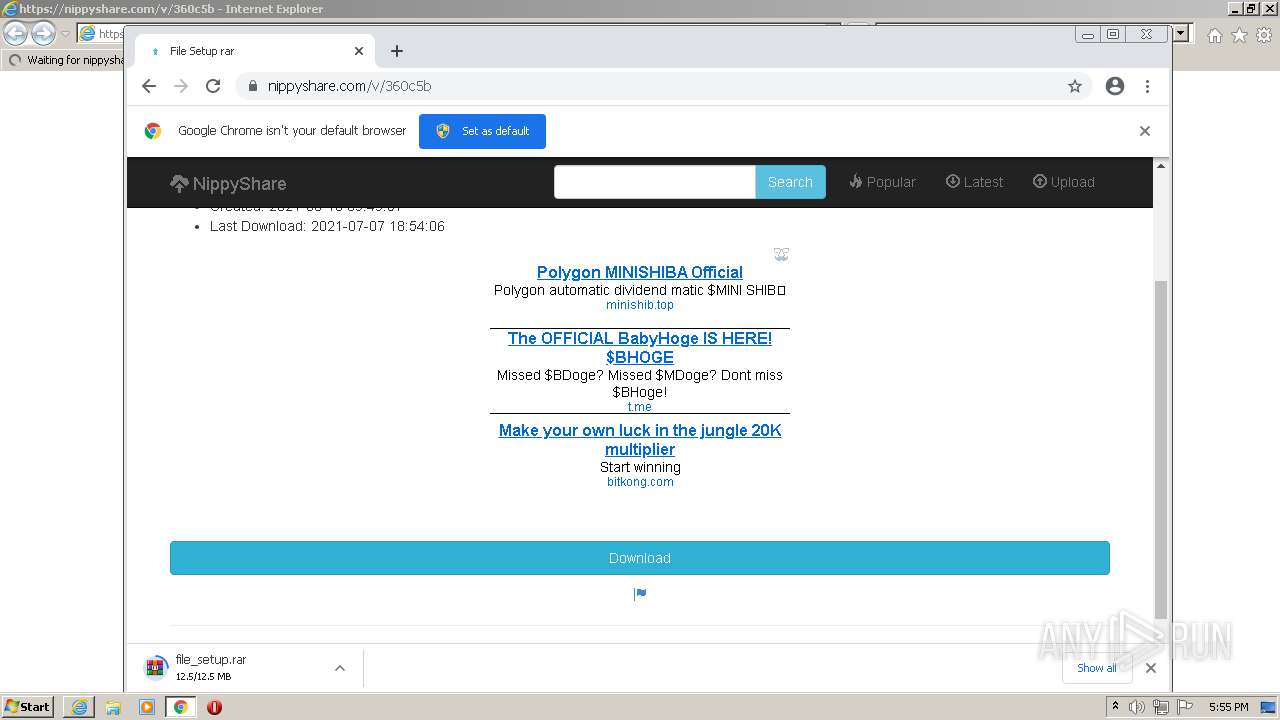
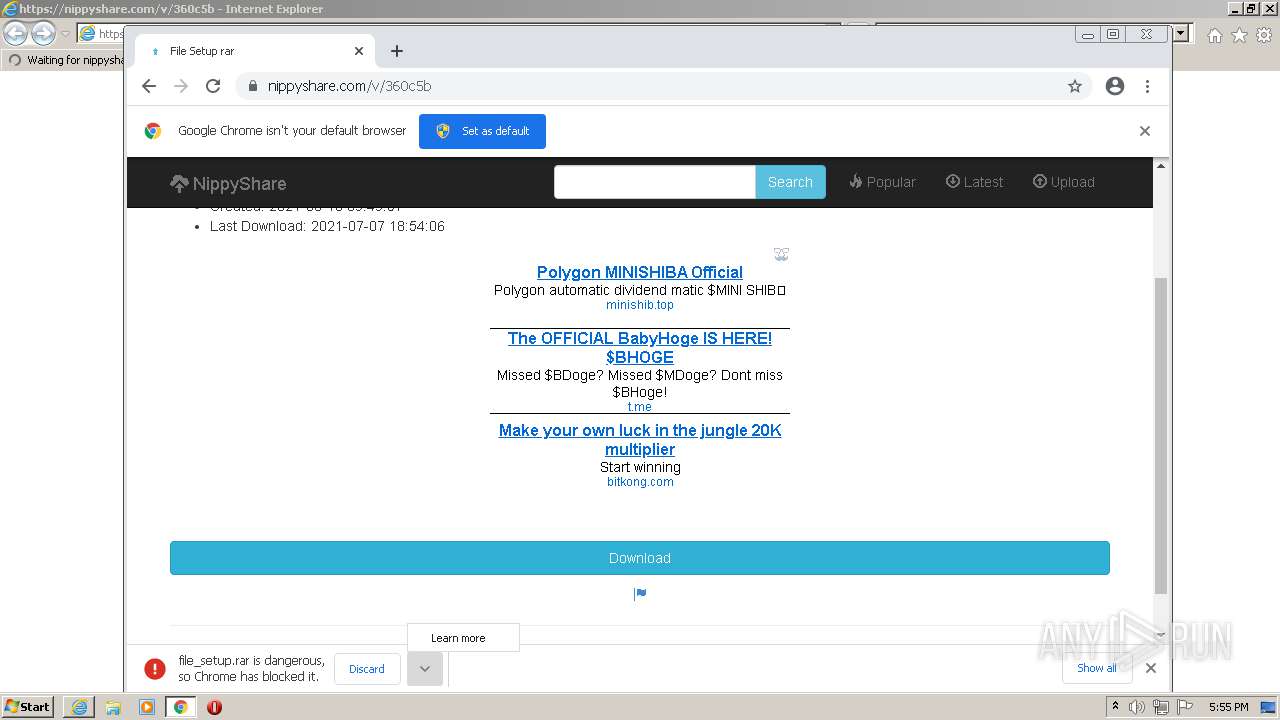
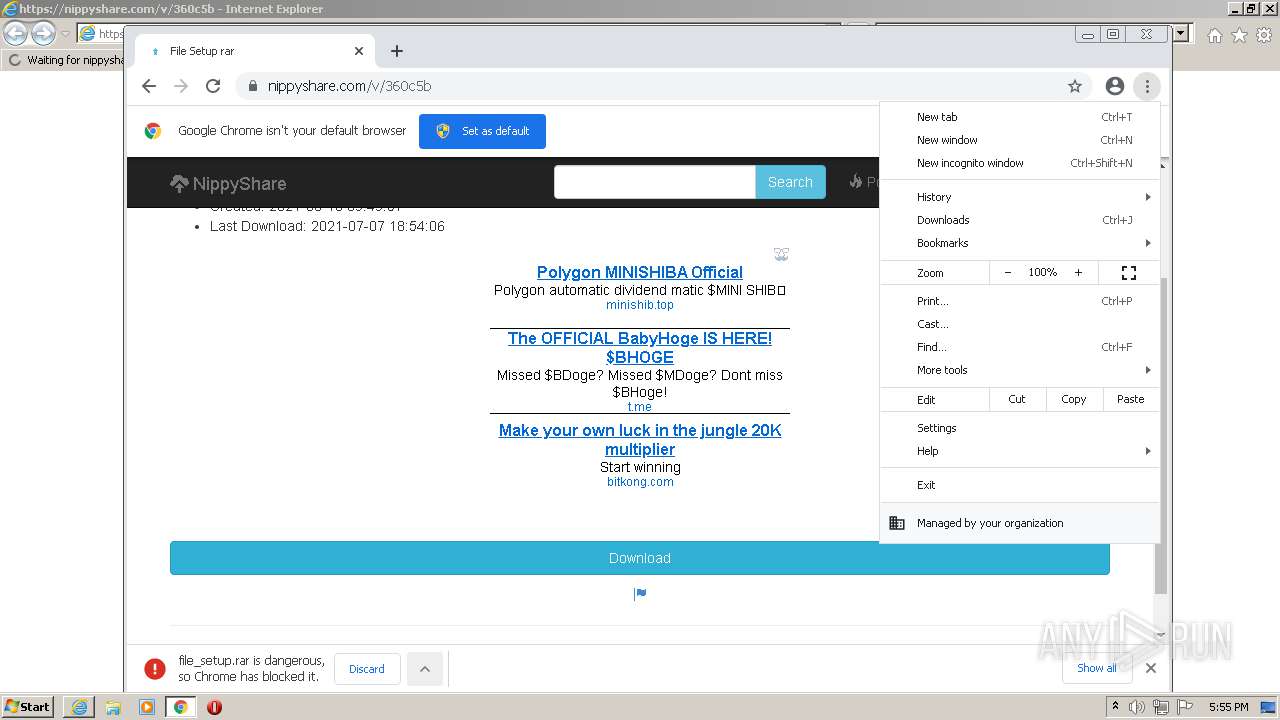
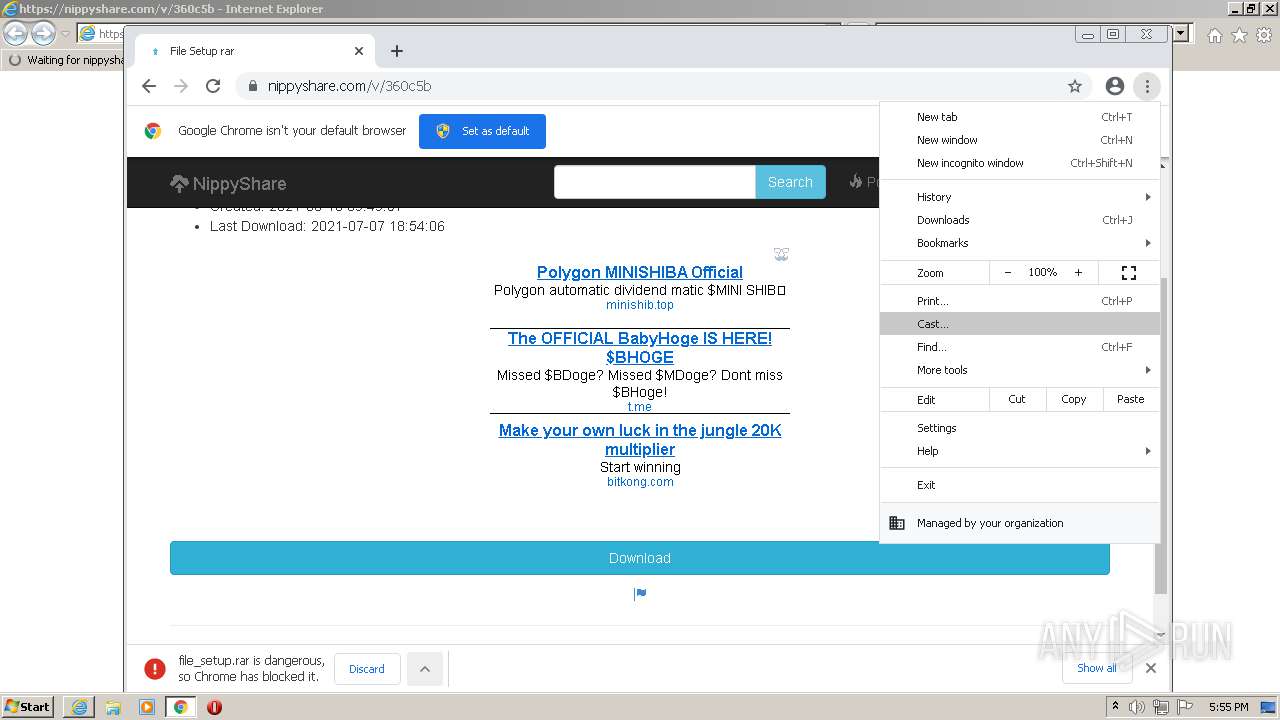
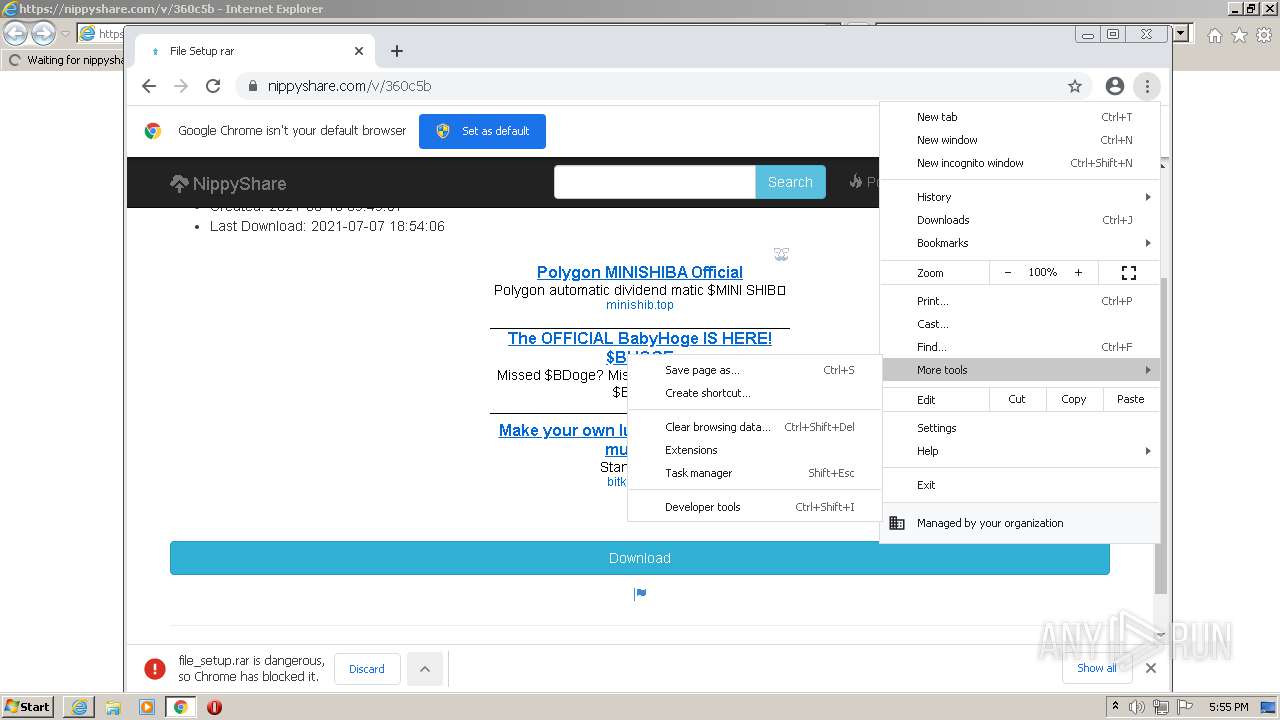
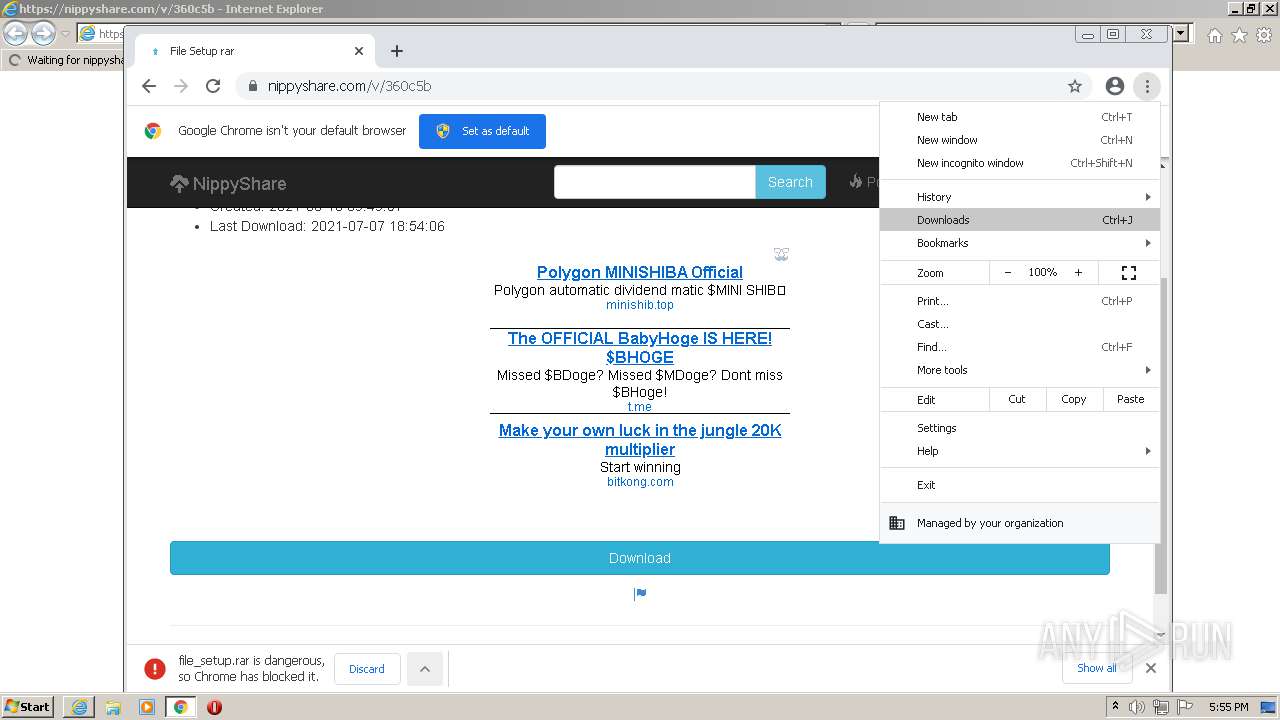
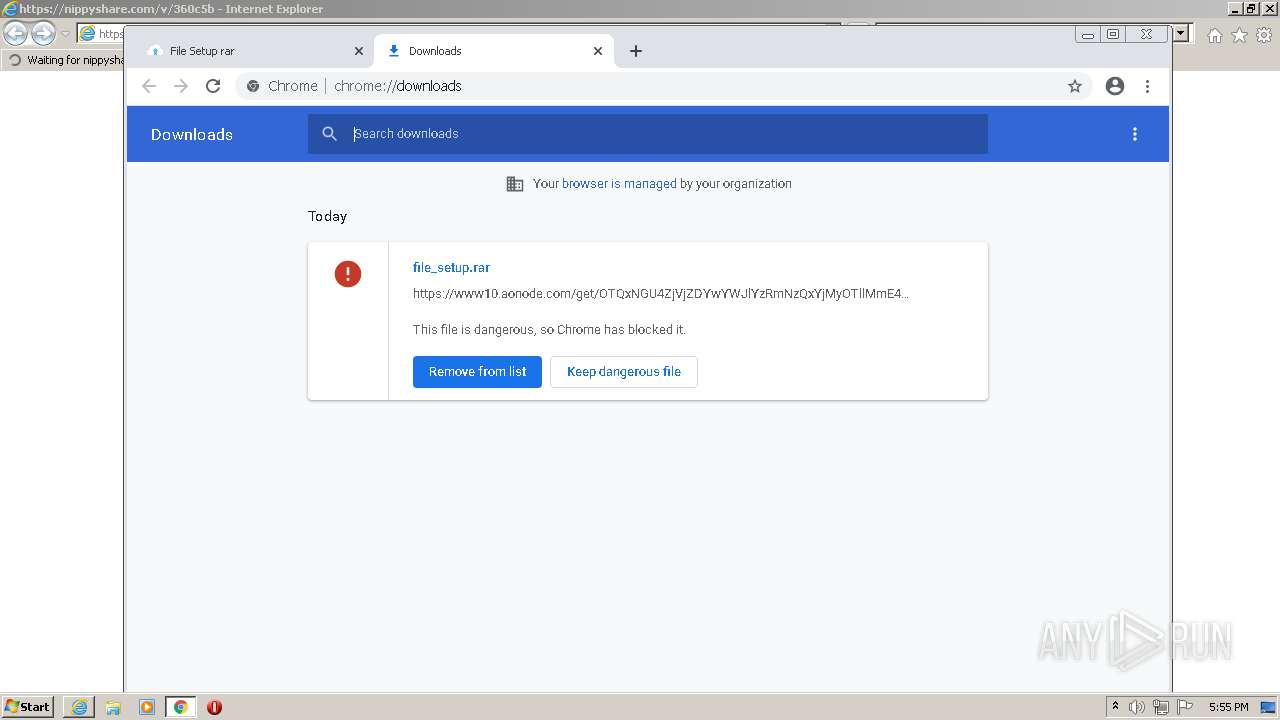
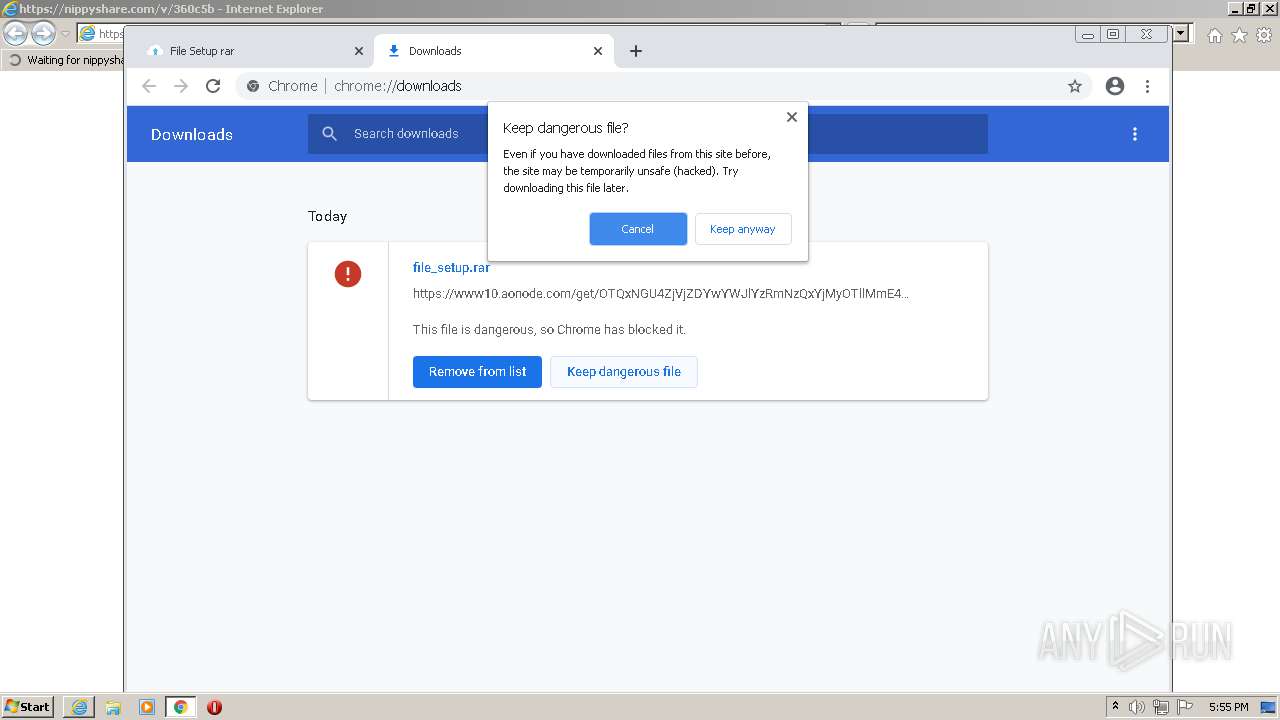
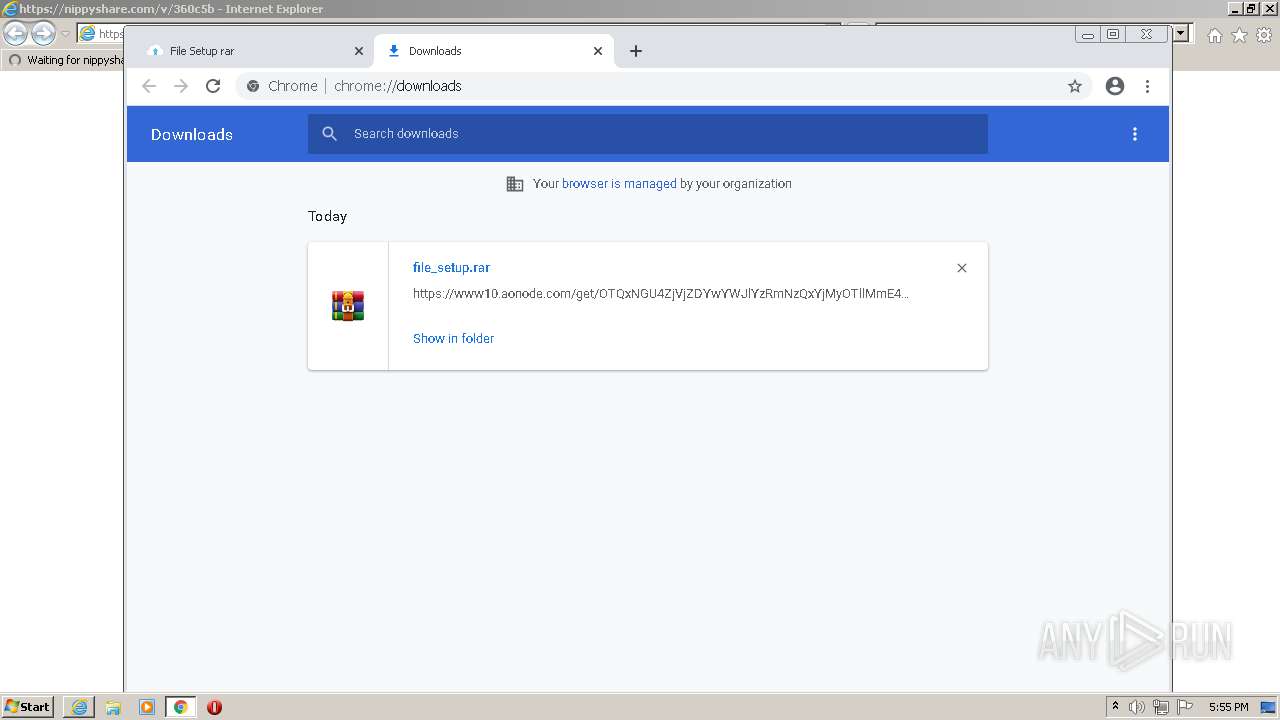
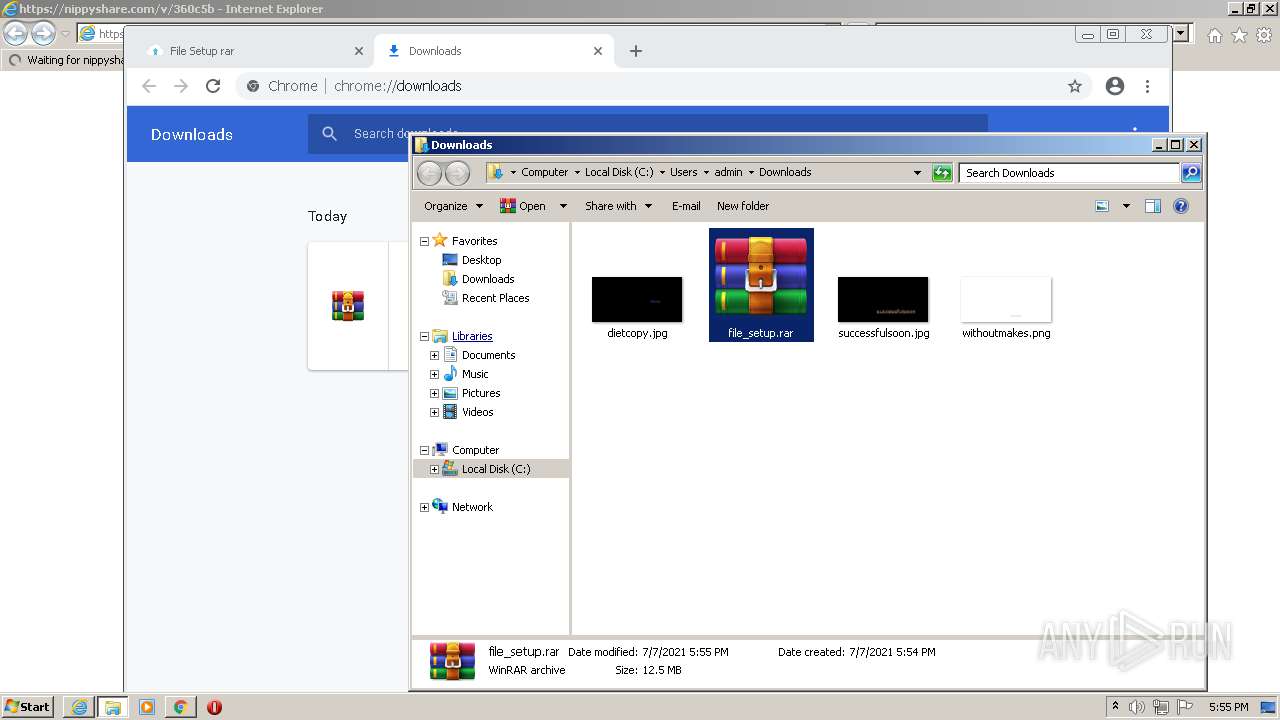
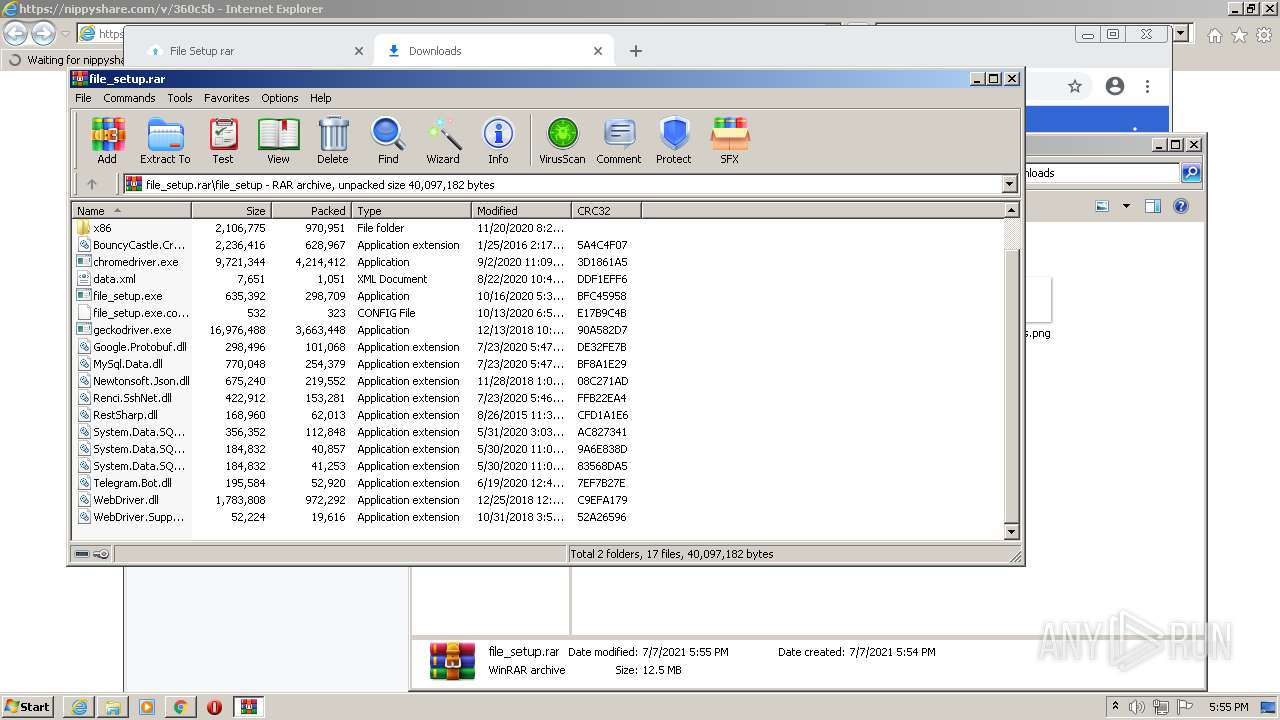
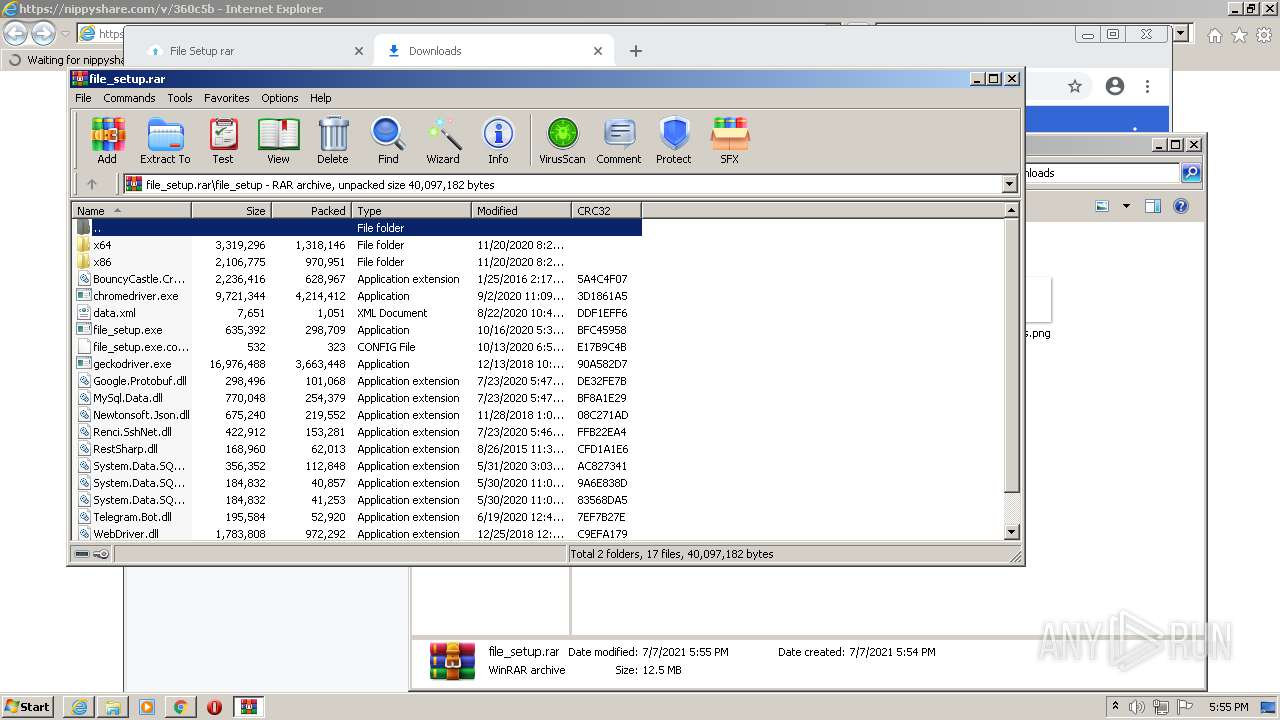
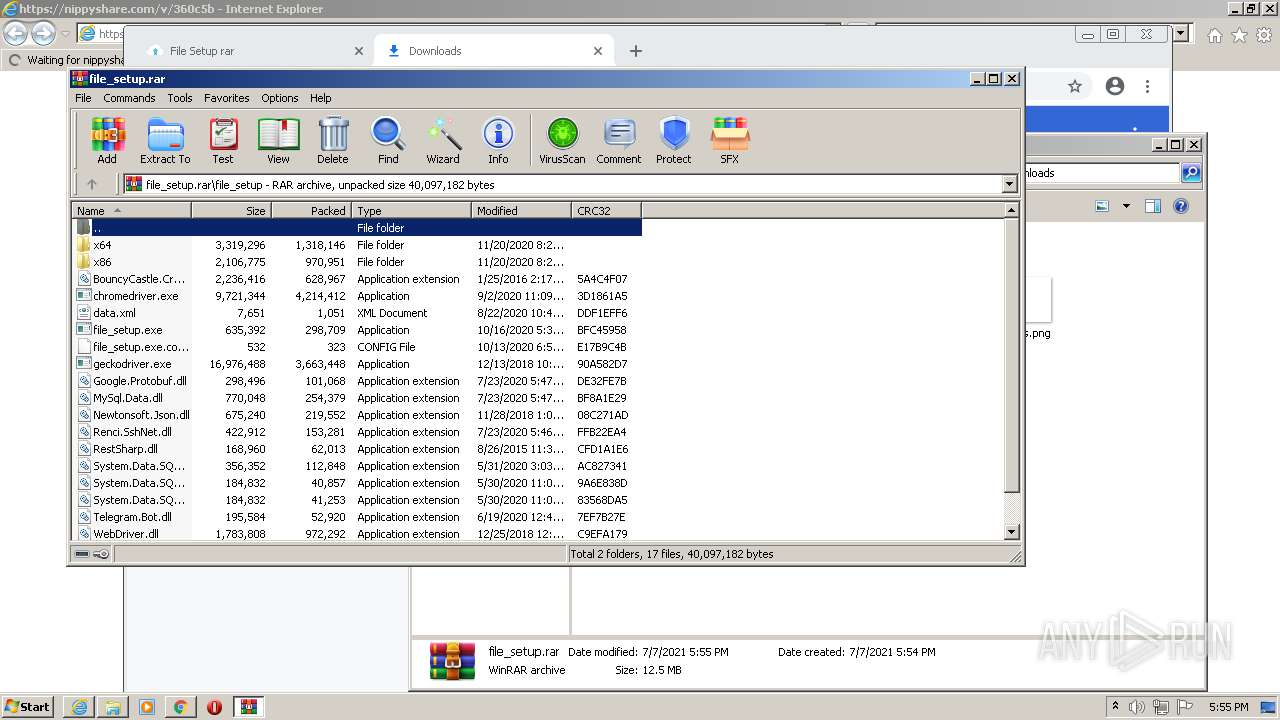
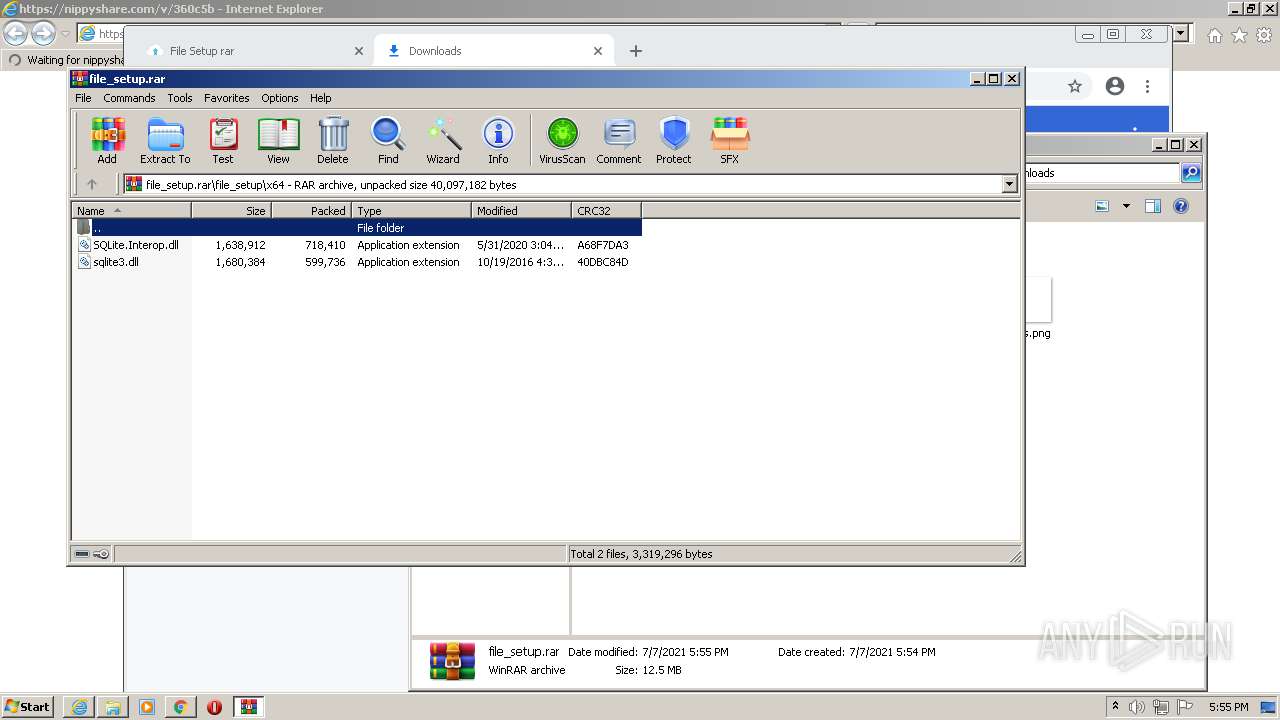
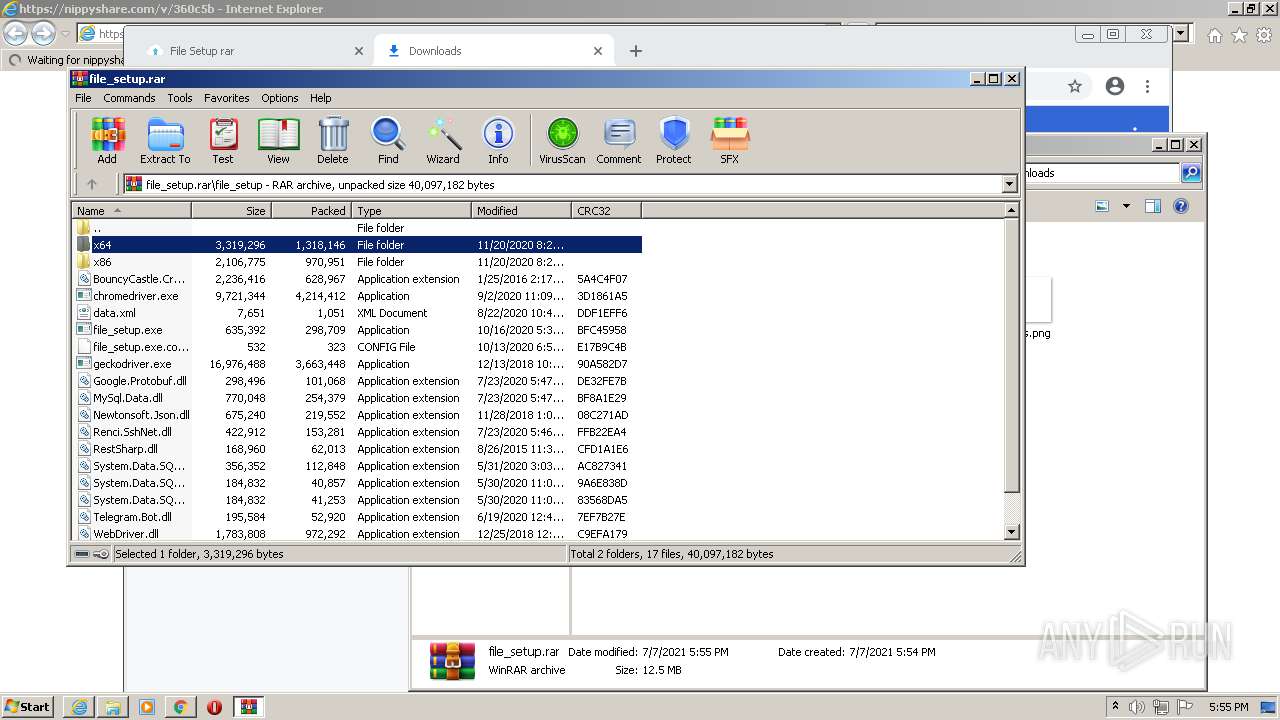
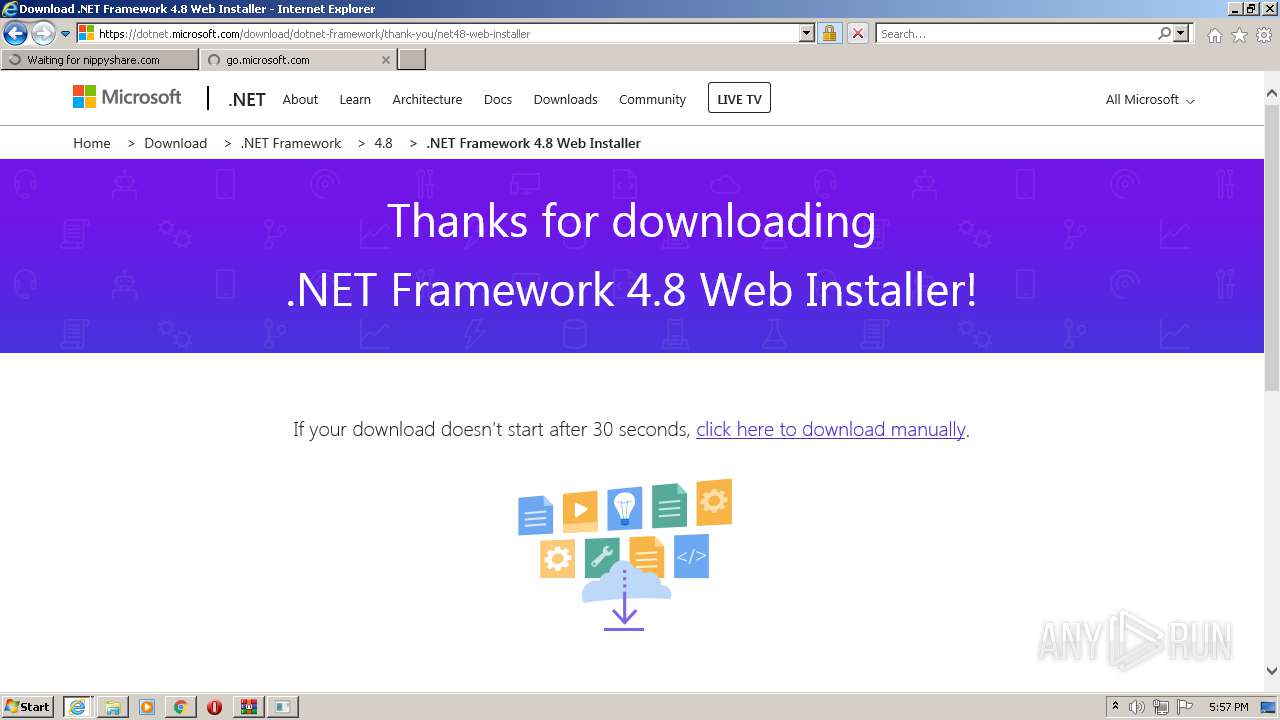
| URL: | https://nippyshare.com/v/360c5b |
| Full analysis: | https://app.any.run/tasks/4445e7ef-3bca-4e52-9212-d2e6435d0955 |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2021, 16:53:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B2CBCD8206ACC4E32F1FD5BA3027AE8D |
| SHA1: | 7401E2962F1FA4AC47F4D61137394819F527F480 |
| SHA256: | 44A3BF3534C6E8F6E837FAA62298BD08E99A7EB0C0D709E667A91A0E35531CA2 |
| SSDEEP: | 3:N8ChGKjKWTB:26Gjy |
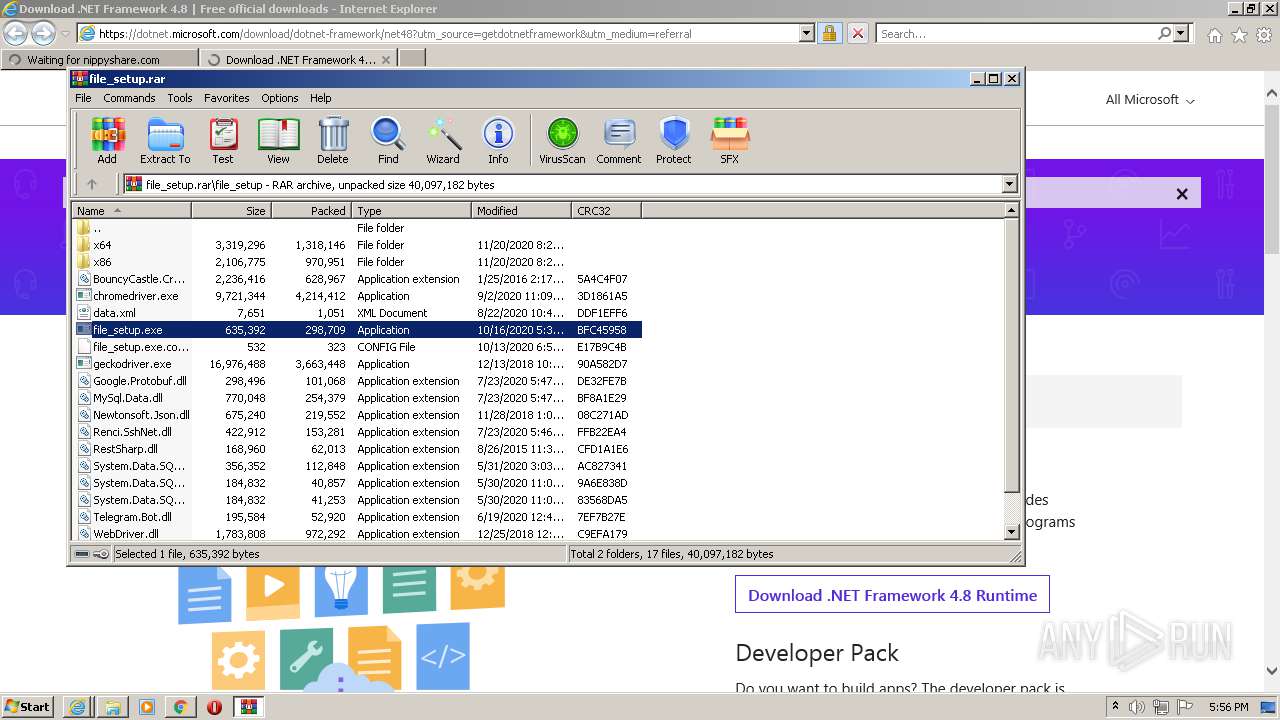
MALICIOUS
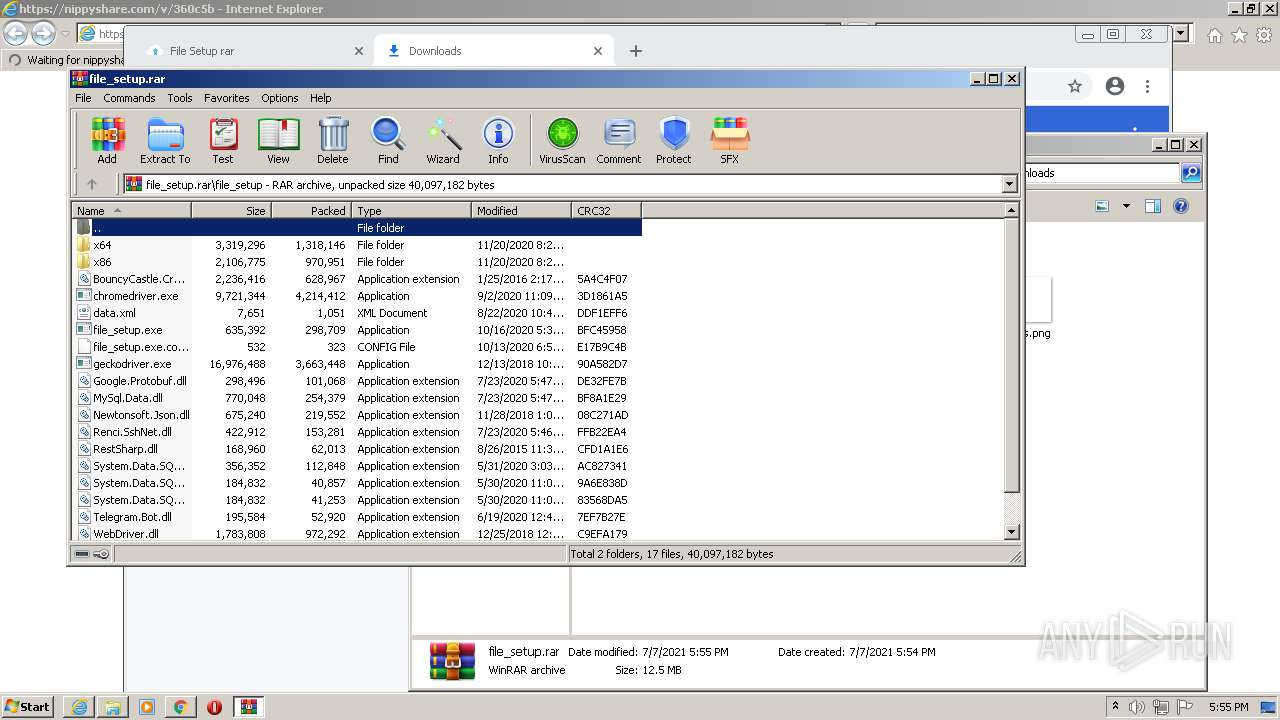
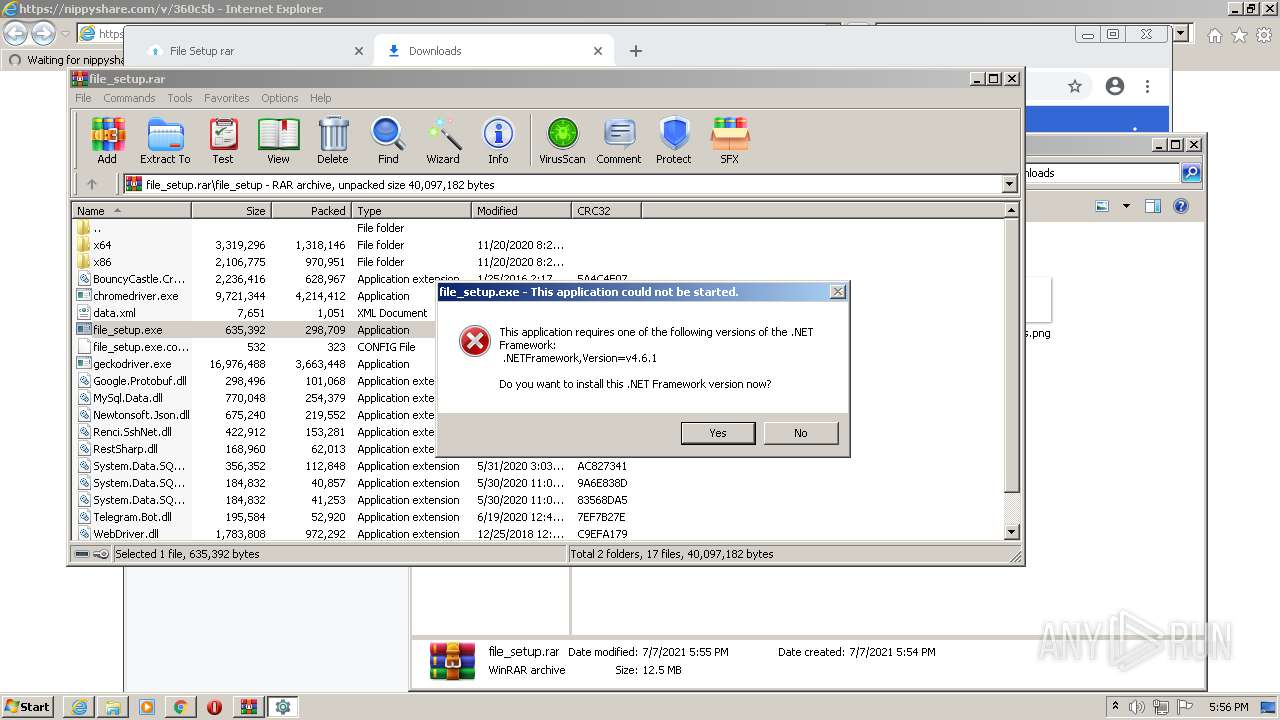
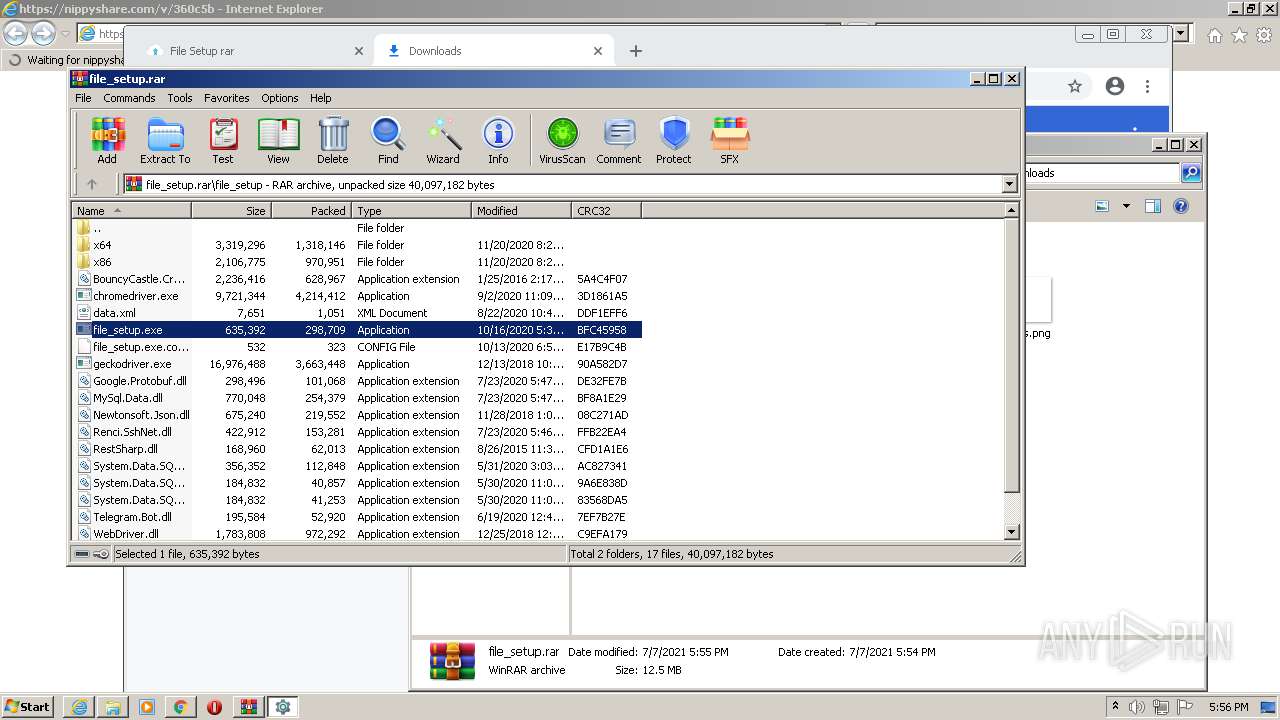
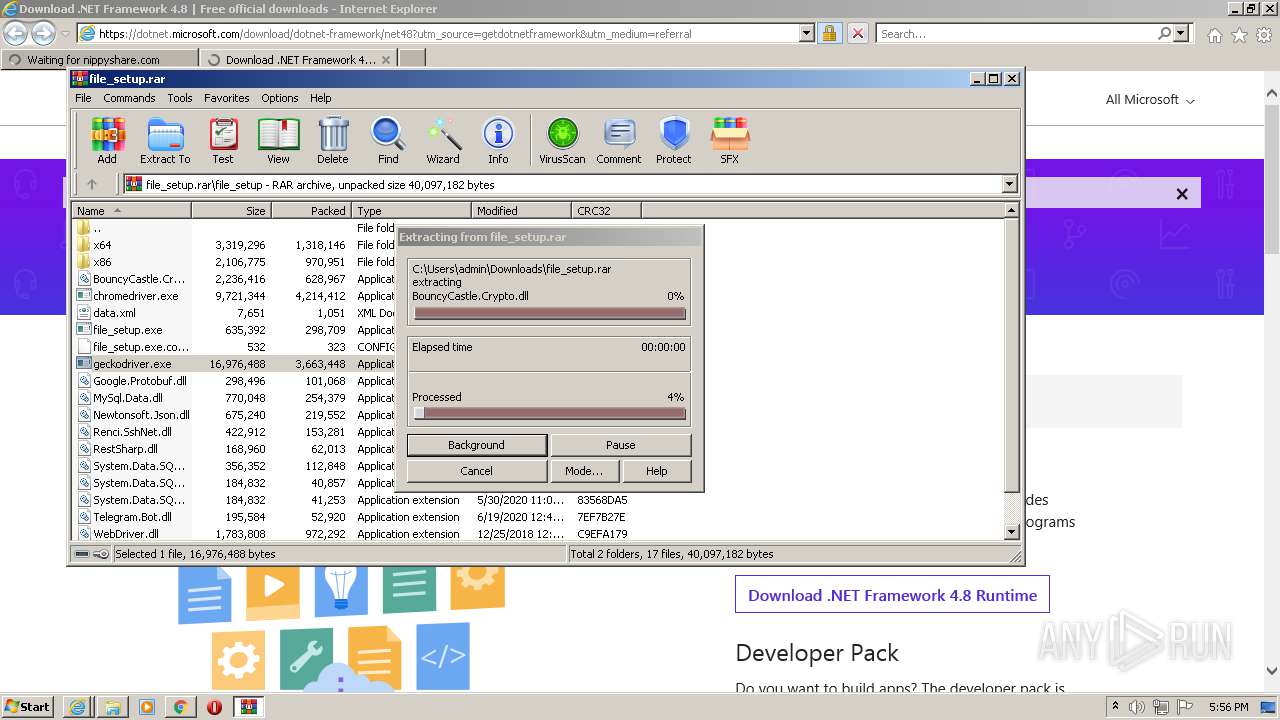
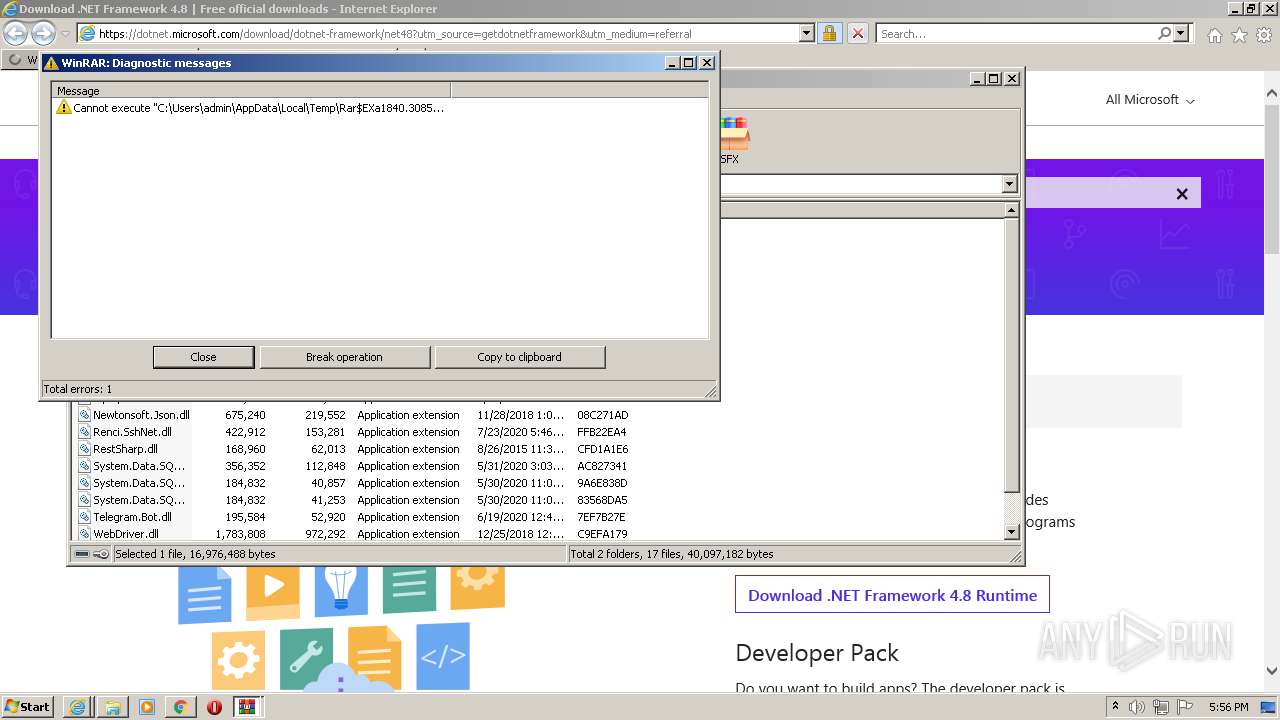
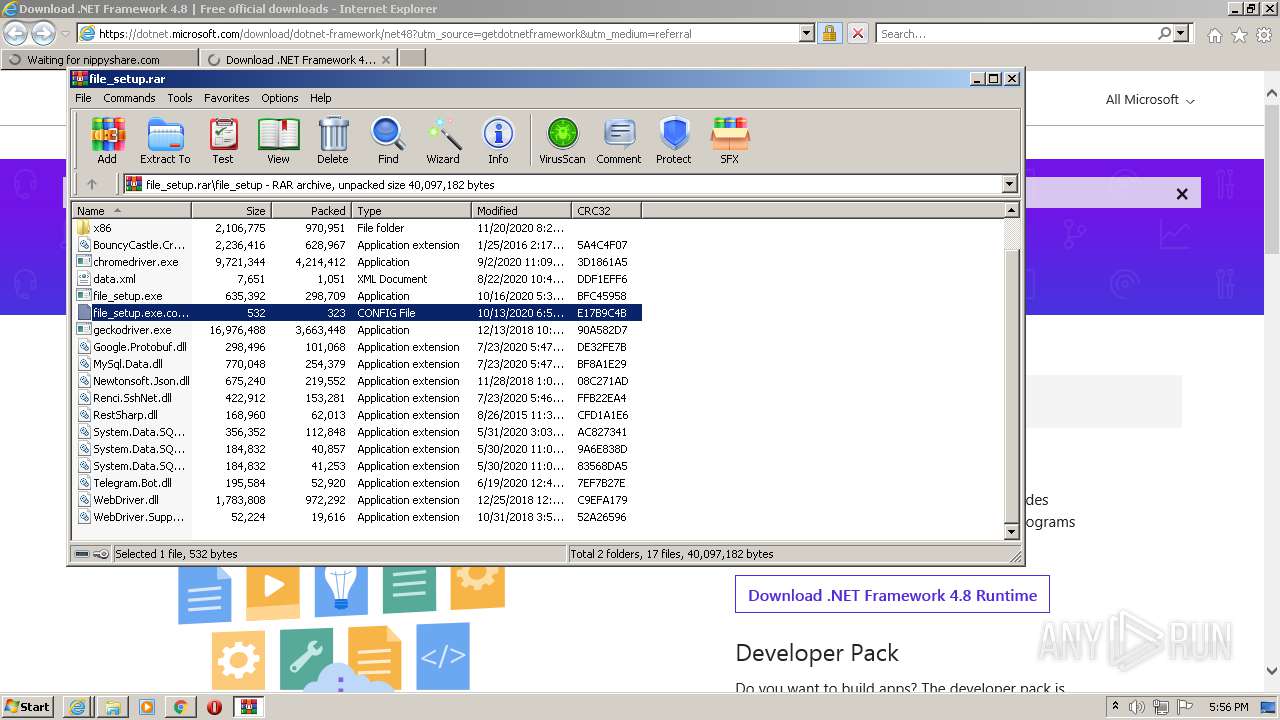
Application was dropped or rewritten from another process
- file_setup.exe (PID: 3692)
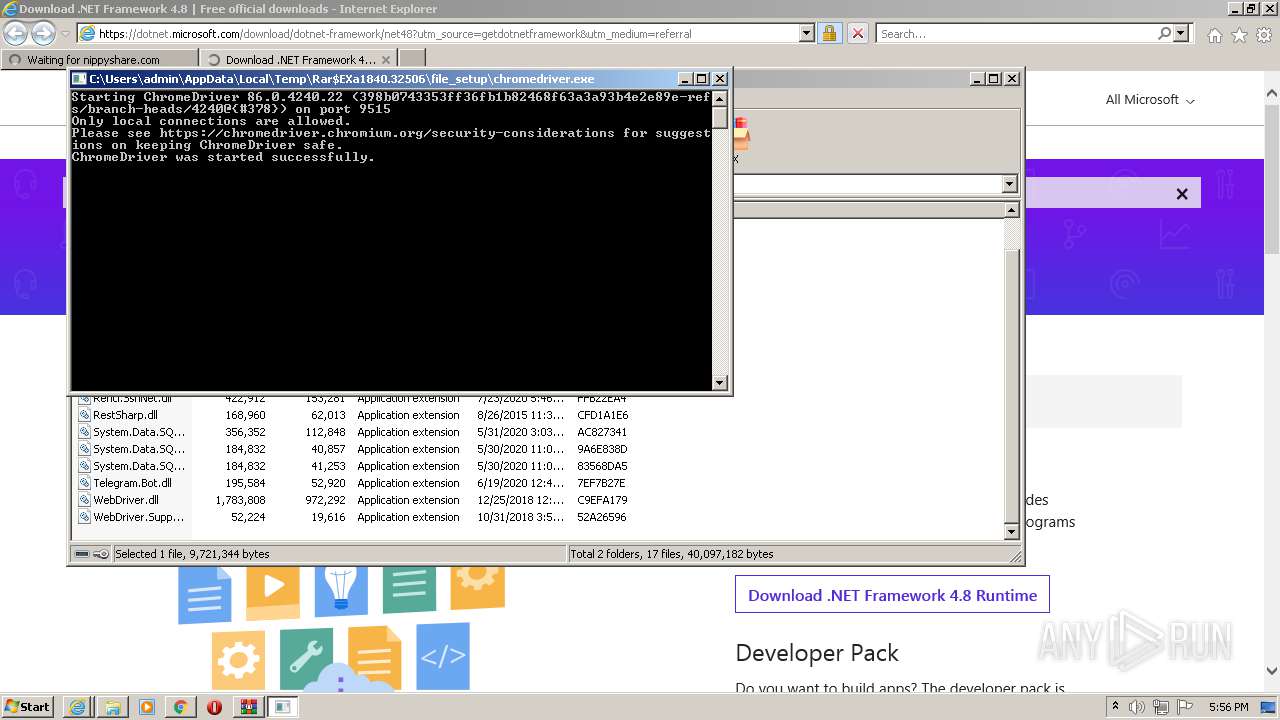
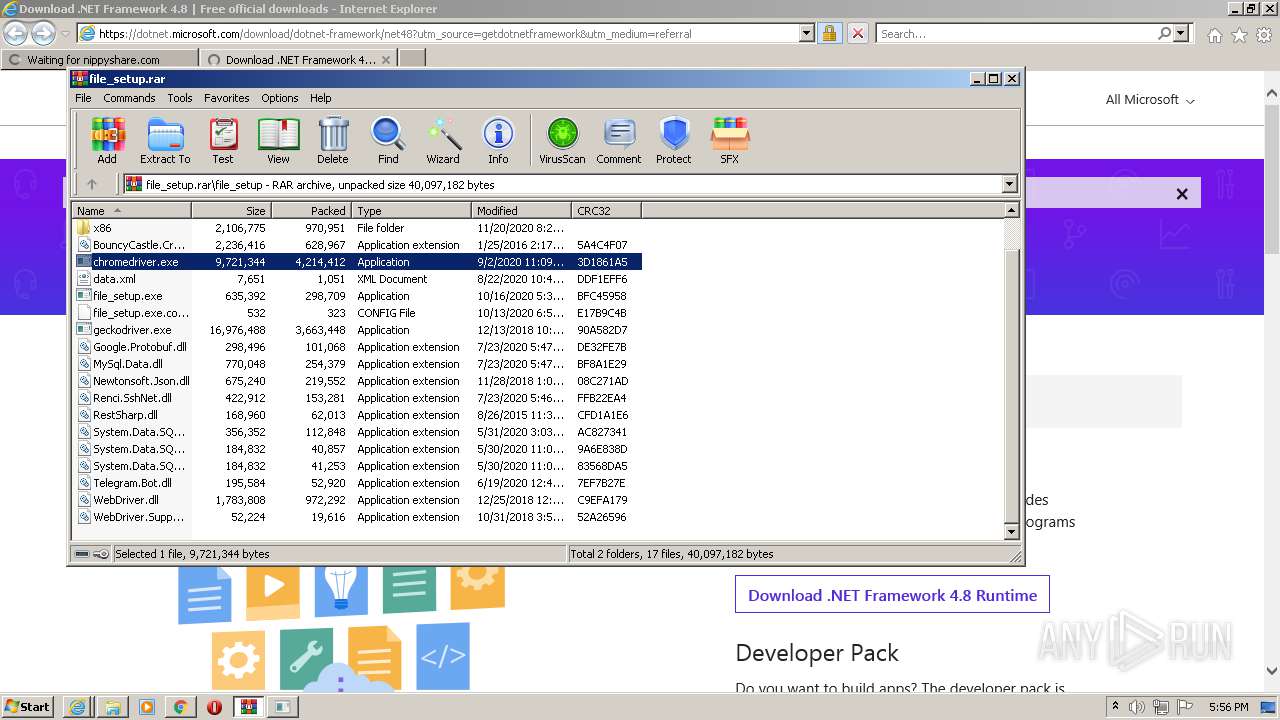
- chromedriver.exe (PID: 1820)
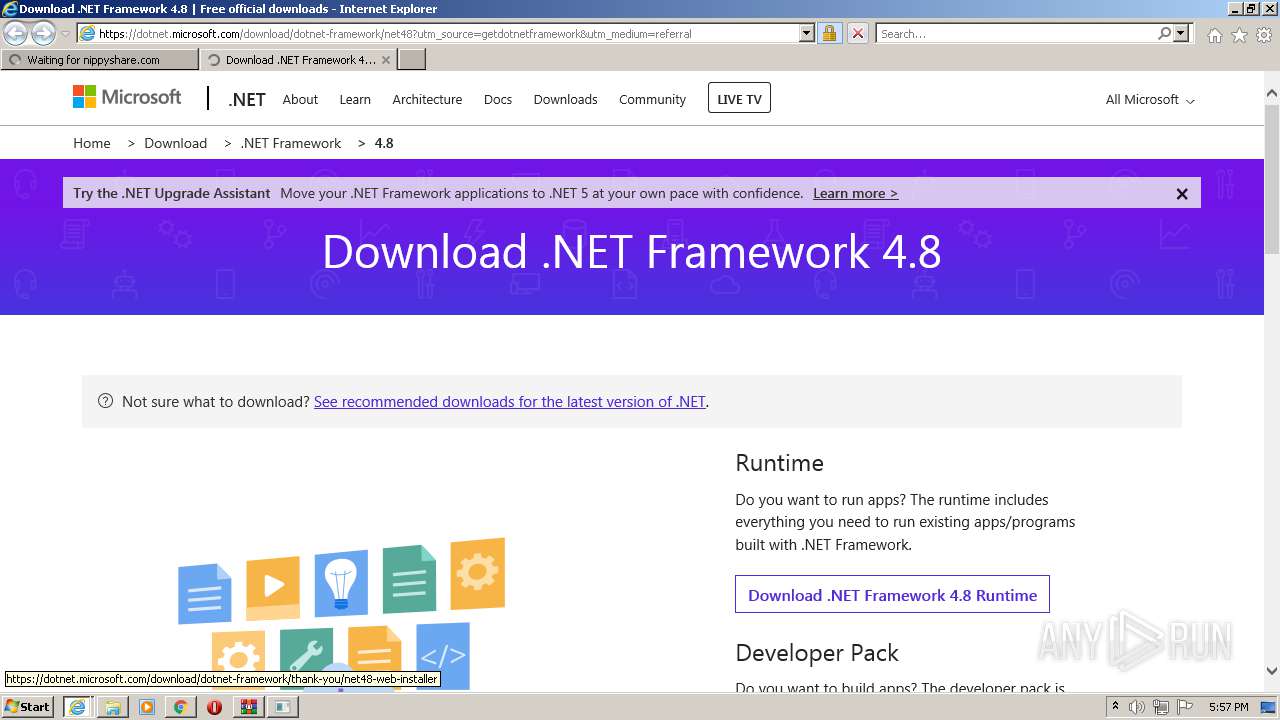
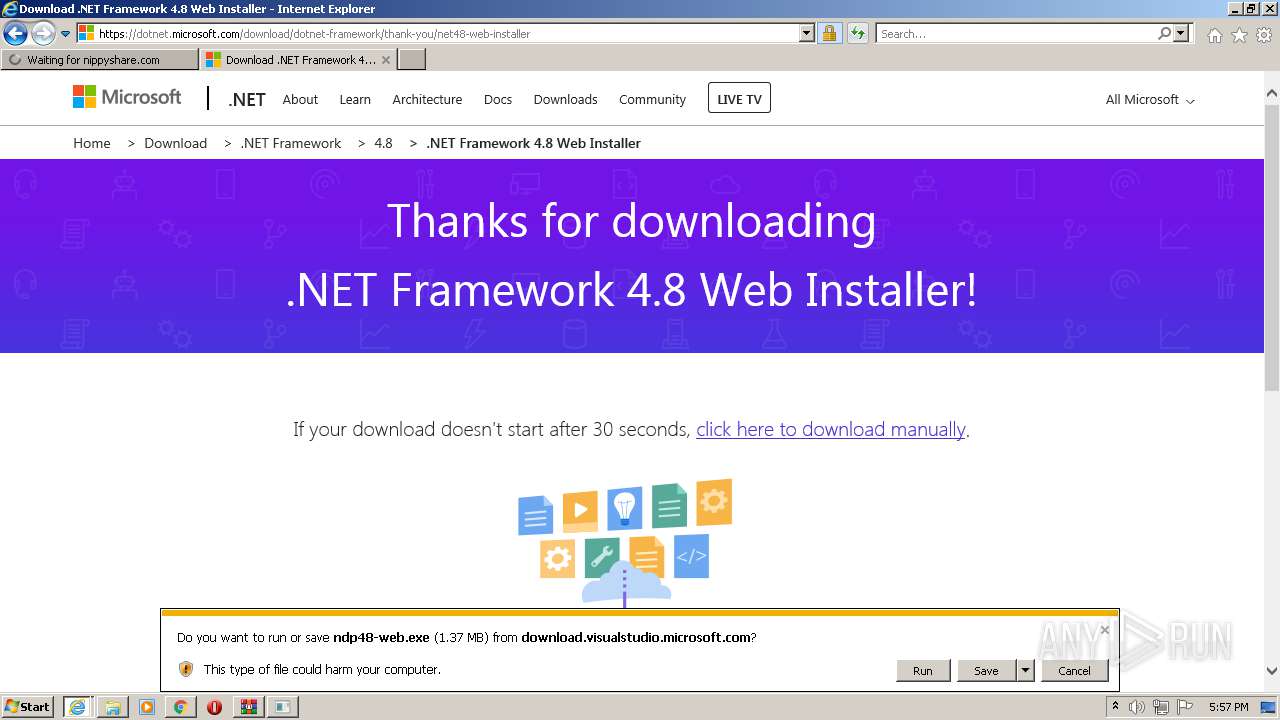
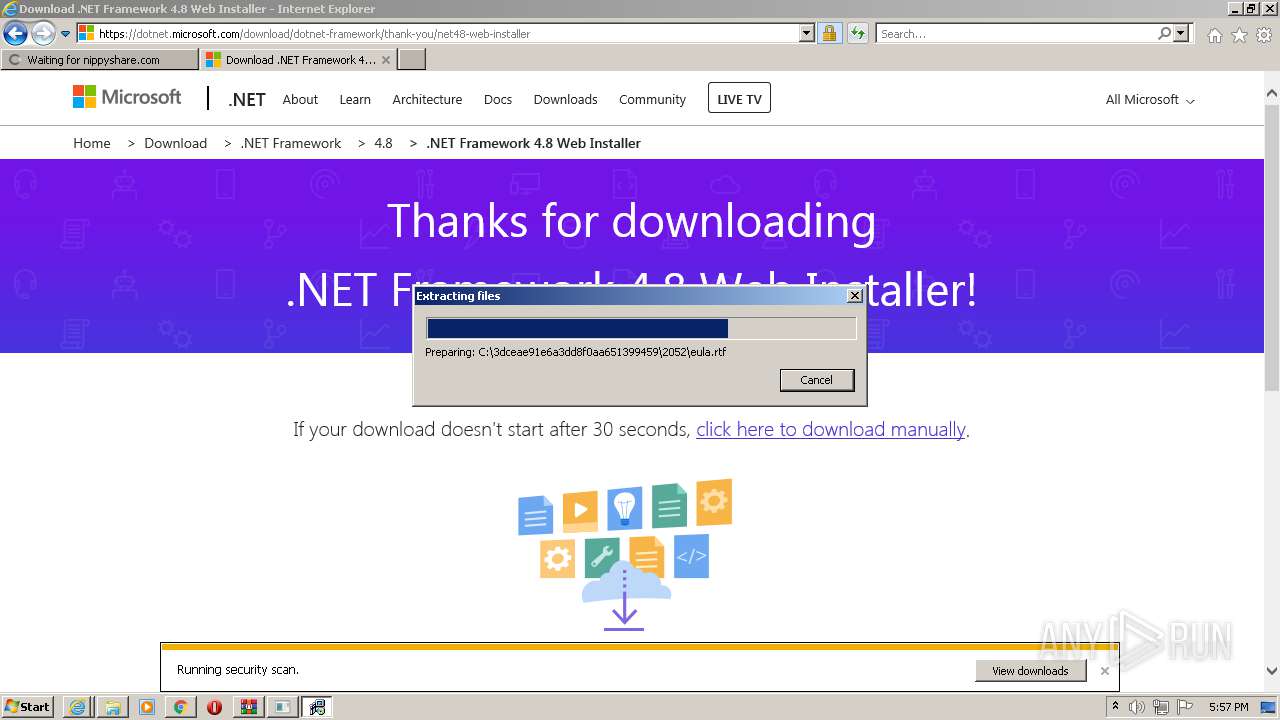
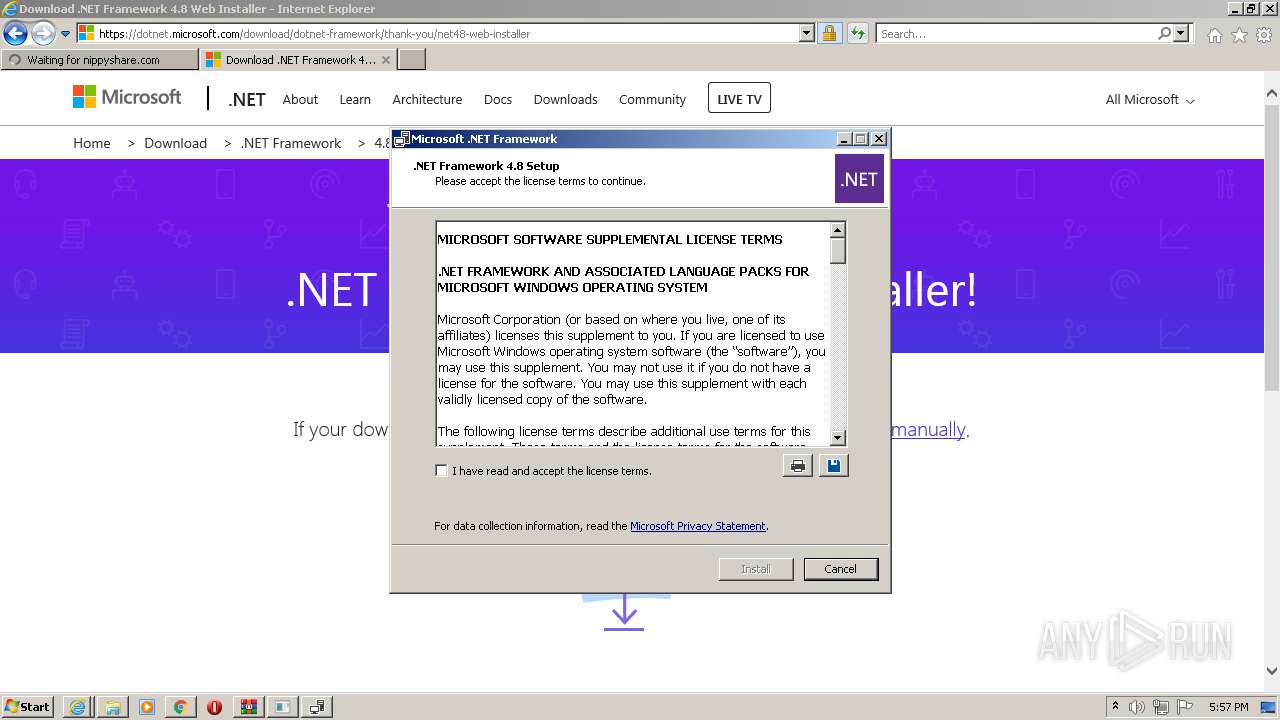
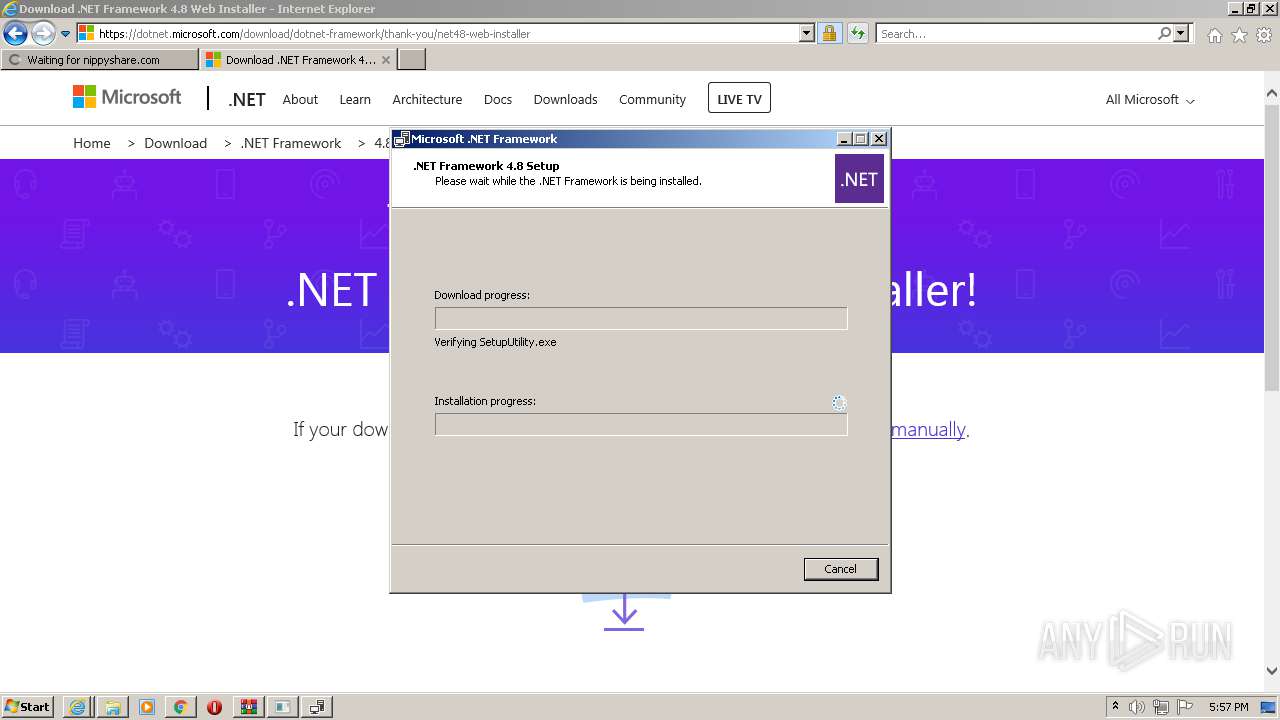
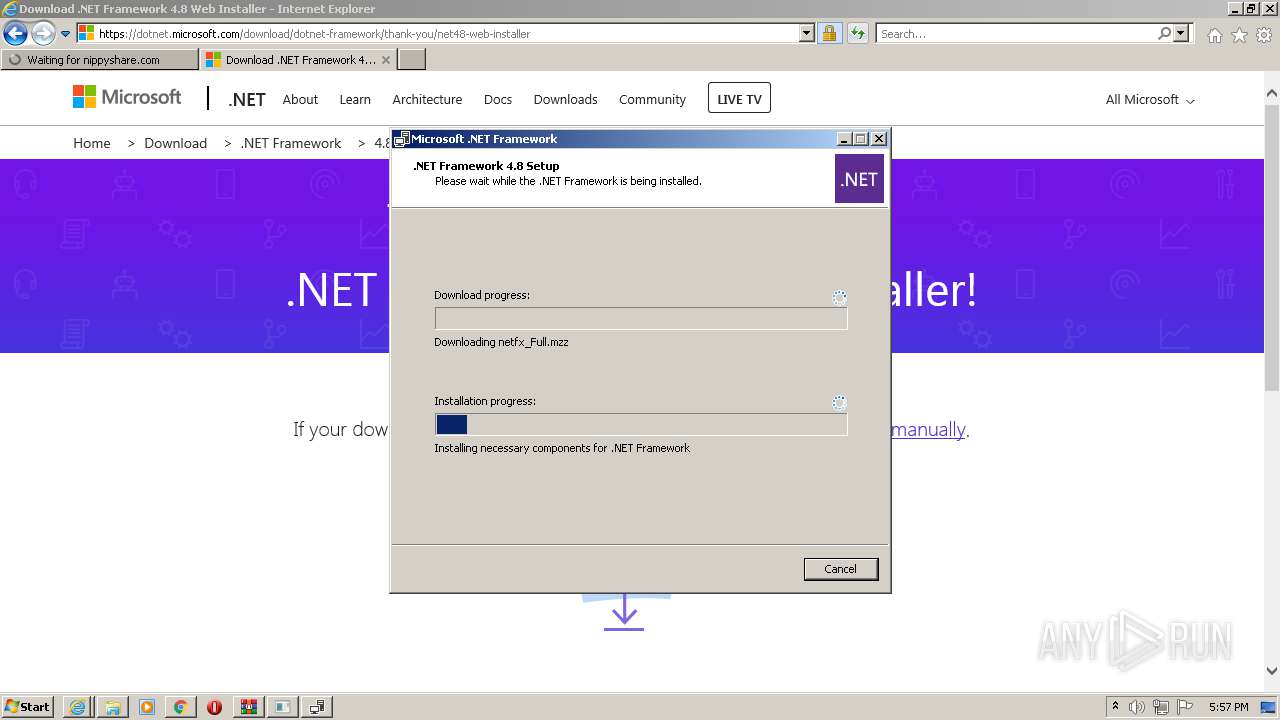
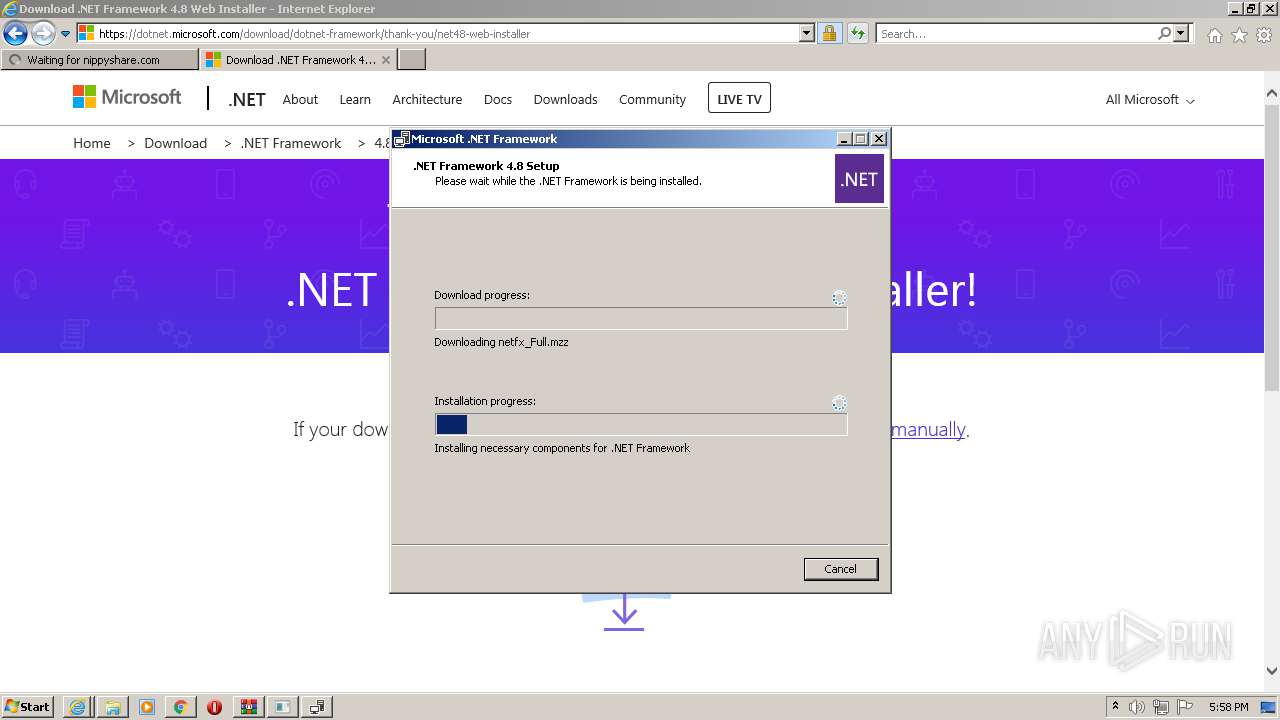
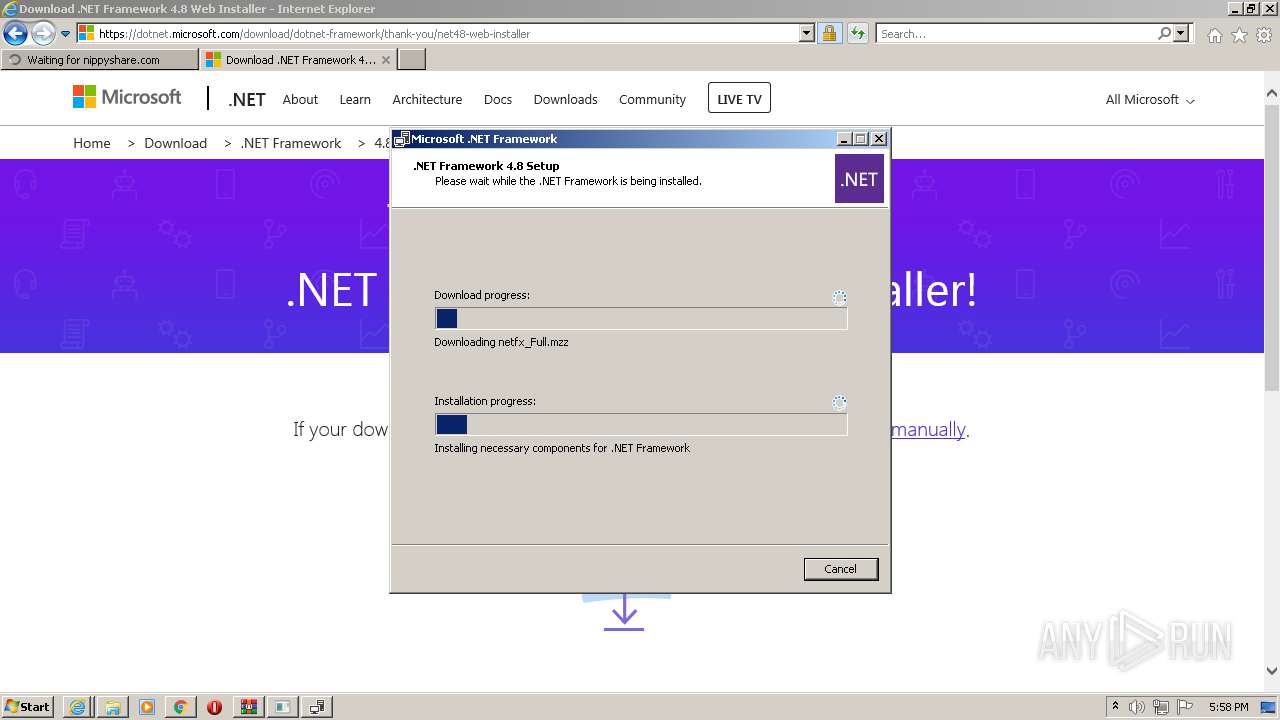
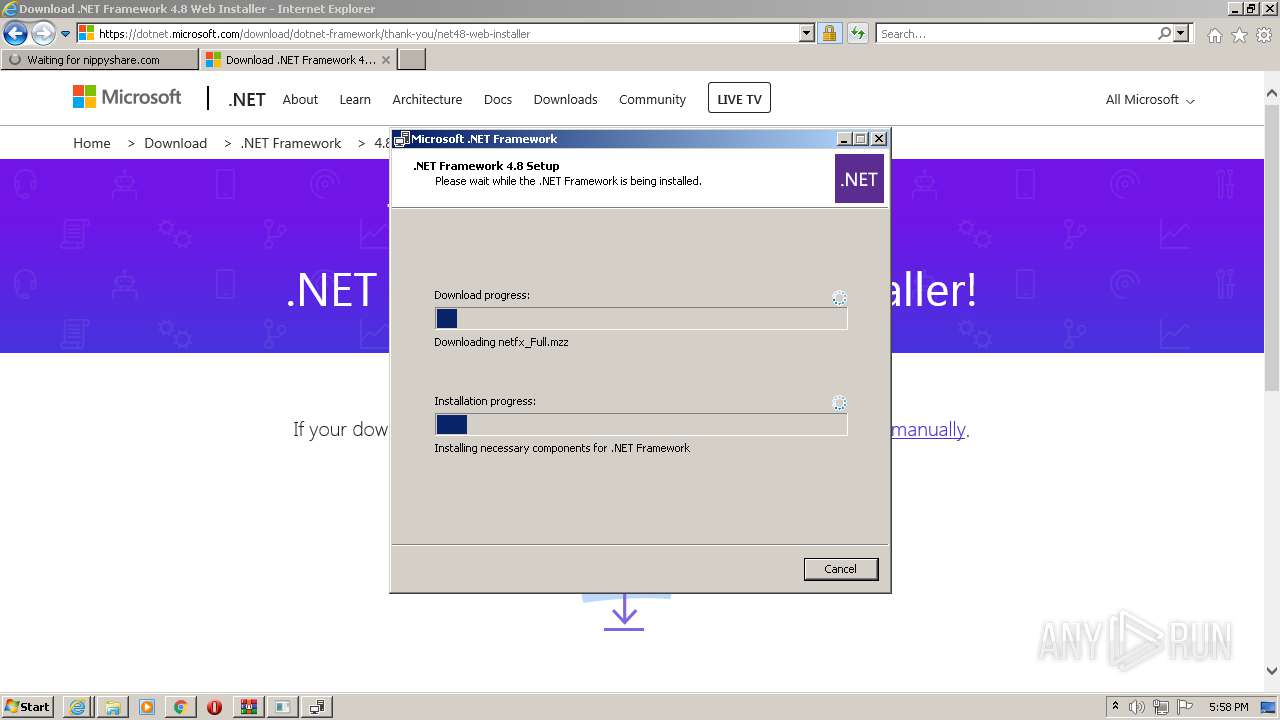
- ndp48-web.exe (PID: 1420)
- ndp48-web.exe (PID: 3504)
- Setup.exe (PID: 1152)
- SetupUtility.exe (PID: 2844)
- SetupUtility.exe (PID: 3720)
Actions looks like stealing of personal data
- ndp48-web.exe (PID: 3504)
Loads dropped or rewritten executable
- Setup.exe (PID: 1152)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 3924)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3852)
Checks supported languages
- file_setup.exe (PID: 3692)
- WinRAR.exe (PID: 1840)
- chromedriver.exe (PID: 1820)
- ndp48-web.exe (PID: 3504)
- Setup.exe (PID: 1152)
- SetupUtility.exe (PID: 3720)
- SetupUtility.exe (PID: 2844)
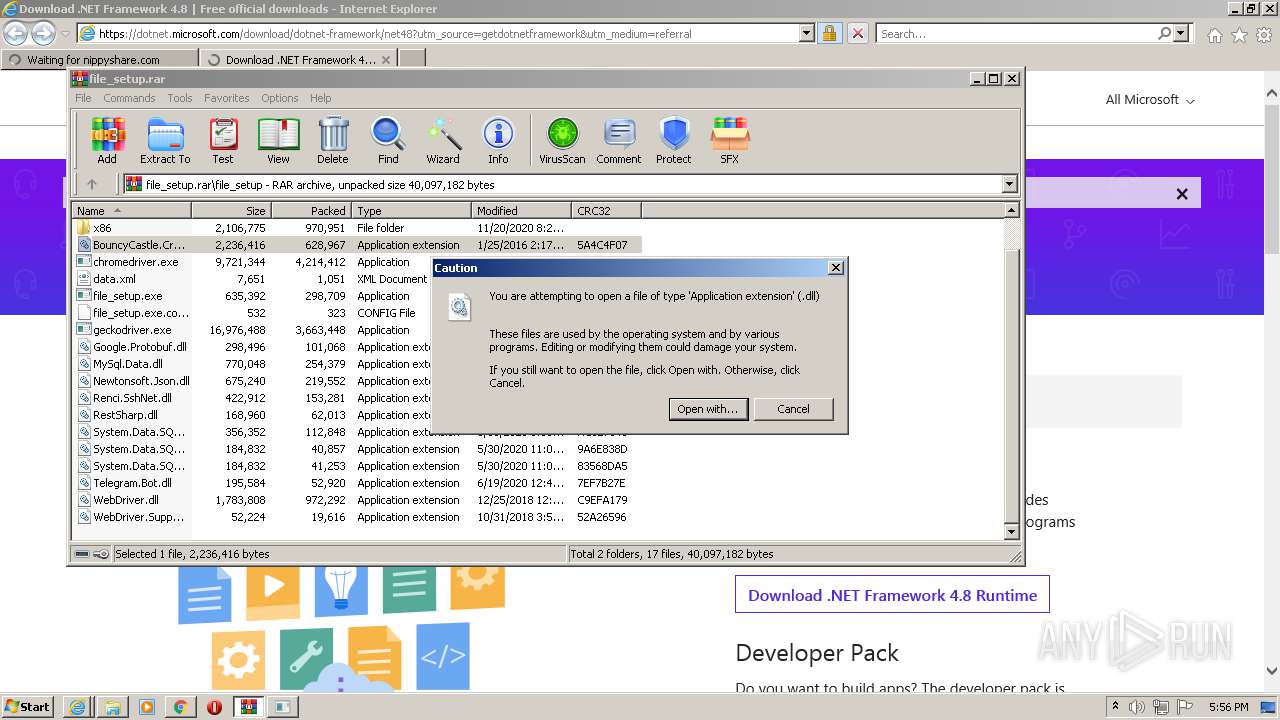
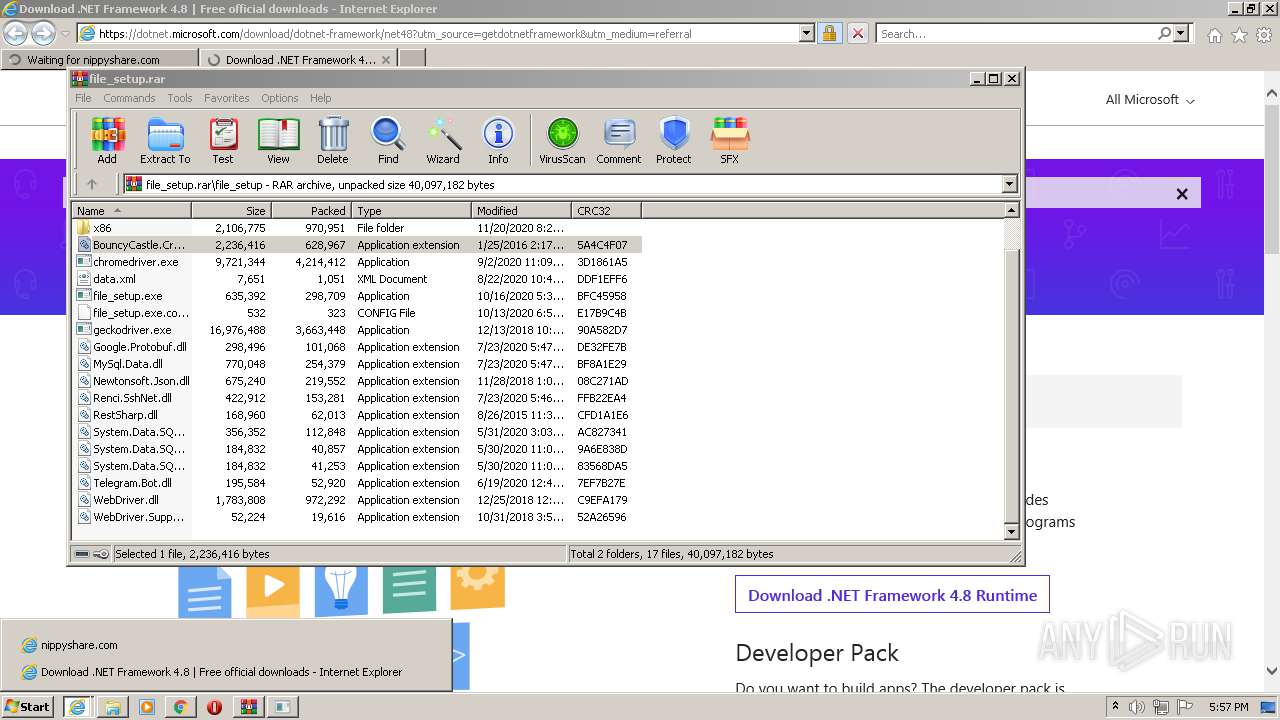
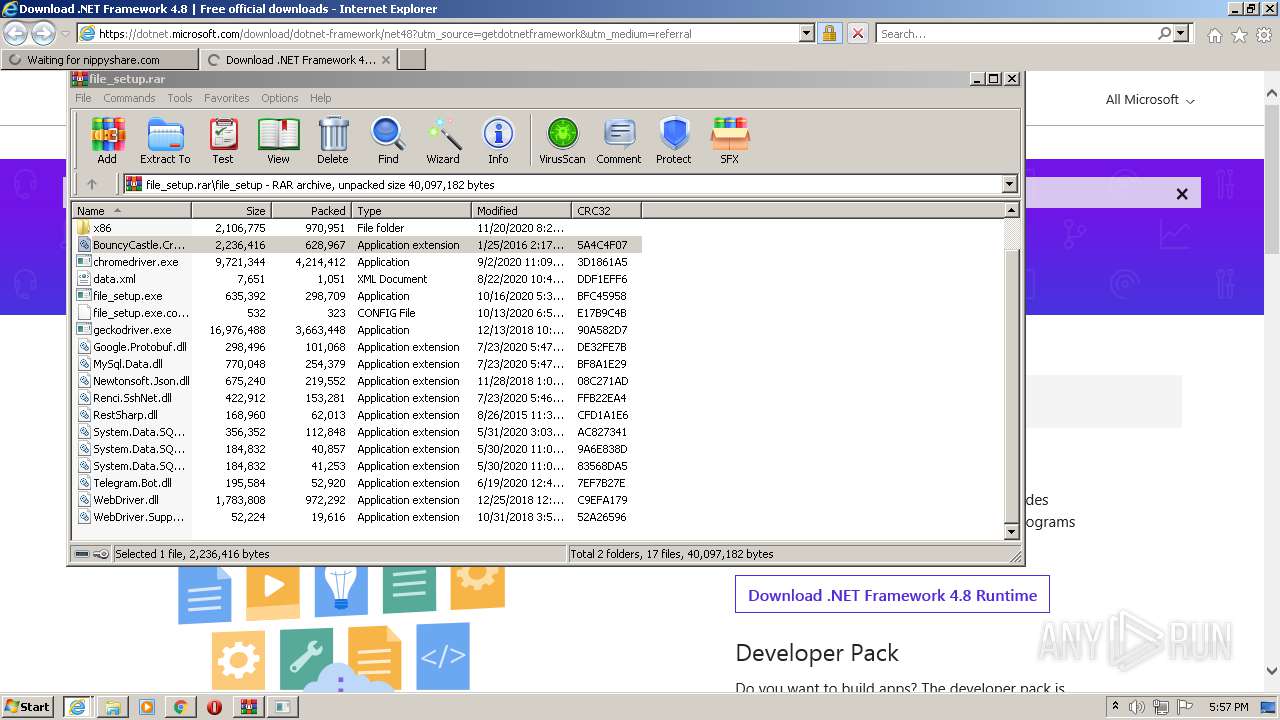
Drops a file with too old compile date
- WinRAR.exe (PID: 1840)
Reads the computer name
- WinRAR.exe (PID: 1840)
- chromedriver.exe (PID: 1820)
- ndp48-web.exe (PID: 3504)
- Setup.exe (PID: 1152)
- SetupUtility.exe (PID: 2844)
- SetupUtility.exe (PID: 3720)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1840)
- iexplore.exe (PID: 3304)
- iexplore.exe (PID: 3924)
- ndp48-web.exe (PID: 3504)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1840)
- iexplore.exe (PID: 3924)
- iexplore.exe (PID: 3304)
- ndp48-web.exe (PID: 3504)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 1840)
Reads CPU info
- Setup.exe (PID: 1152)
Reads Environment values
- Setup.exe (PID: 1152)
INFO
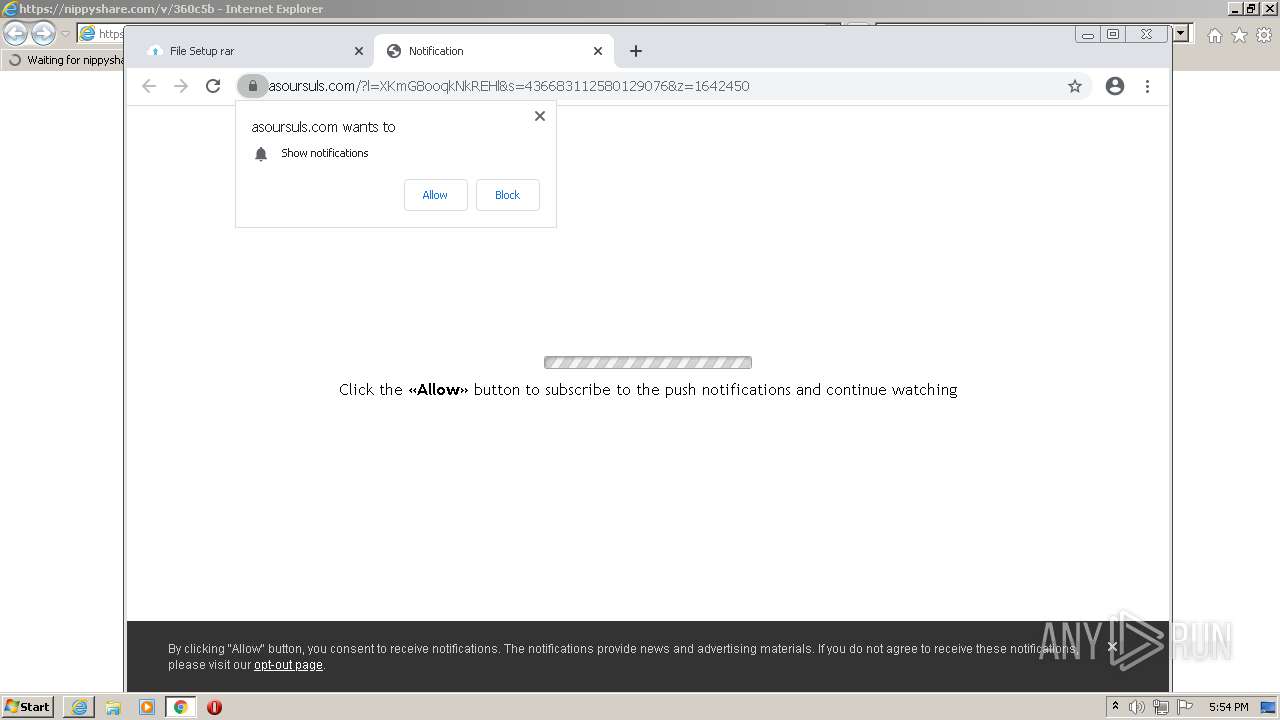
Changes internet zones settings
- iexplore.exe (PID: 3304)
Checks Windows Trust Settings
- iexplore.exe (PID: 3304)
- iexplore.exe (PID: 3924)
- Setup.exe (PID: 1152)
Manual execution by user
- chrome.exe (PID: 3852)
- WinRAR.exe (PID: 1840)
Checks supported languages
- chrome.exe (PID: 3256)
- iexplore.exe (PID: 3304)
- iexplore.exe (PID: 2988)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 3316)
- chrome.exe (PID: 3772)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 1844)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 1412)
- chrome.exe (PID: 2304)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 940)
- chrome.exe (PID: 952)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 2876)
- iexplore.exe (PID: 3924)
- rundll32.exe (PID: 2672)
- chrome.exe (PID: 3788)
- rundll32.exe (PID: 2792)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 3772)
- chrome.exe (PID: 528)
Reads the computer name
- iexplore.exe (PID: 3304)
- iexplore.exe (PID: 2988)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 1412)
- chrome.exe (PID: 940)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 952)
- iexplore.exe (PID: 3924)
- rundll32.exe (PID: 2672)
Application launched itself
- iexplore.exe (PID: 3304)
- chrome.exe (PID: 3852)
Reads settings of System Certificates
- iexplore.exe (PID: 3304)
- chrome.exe (PID: 1024)
- iexplore.exe (PID: 3924)
- Setup.exe (PID: 1152)
Reads internet explorer settings
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 3924)
Reads the hosts file
- chrome.exe (PID: 3852)
- chrome.exe (PID: 1024)
Reads the date of Windows installation
- chrome.exe (PID: 940)
Creates files in the user directory
- iexplore.exe (PID: 3304)
- iexplore.exe (PID: 3924)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3304)
Changes settings of System certificates
- iexplore.exe (PID: 3304)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3304)
- SetupUtility.exe (PID: 3720)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
46
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,3945337611082595214,108785302142048750,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2440 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,3945337611082595214,108785302142048750,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2176 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1028,3945337611082595214,108785302142048750,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=960 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1028,3945337611082595214,108785302142048750,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1252 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1152 | C:\3dceae91e6a3dd8f0aa651399459\\Setup.exe /x86 /x64 /web | C:\3dceae91e6a3dd8f0aa651399459\Setup.exe | ndp48-web.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,3945337611082595214,108785302142048750,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2148 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1420 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ndp48-web.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ndp48-web.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4.8 Setup Exit code: 3221226540 Version: 4.8.04115.00 Modules
| |||||||||||||||
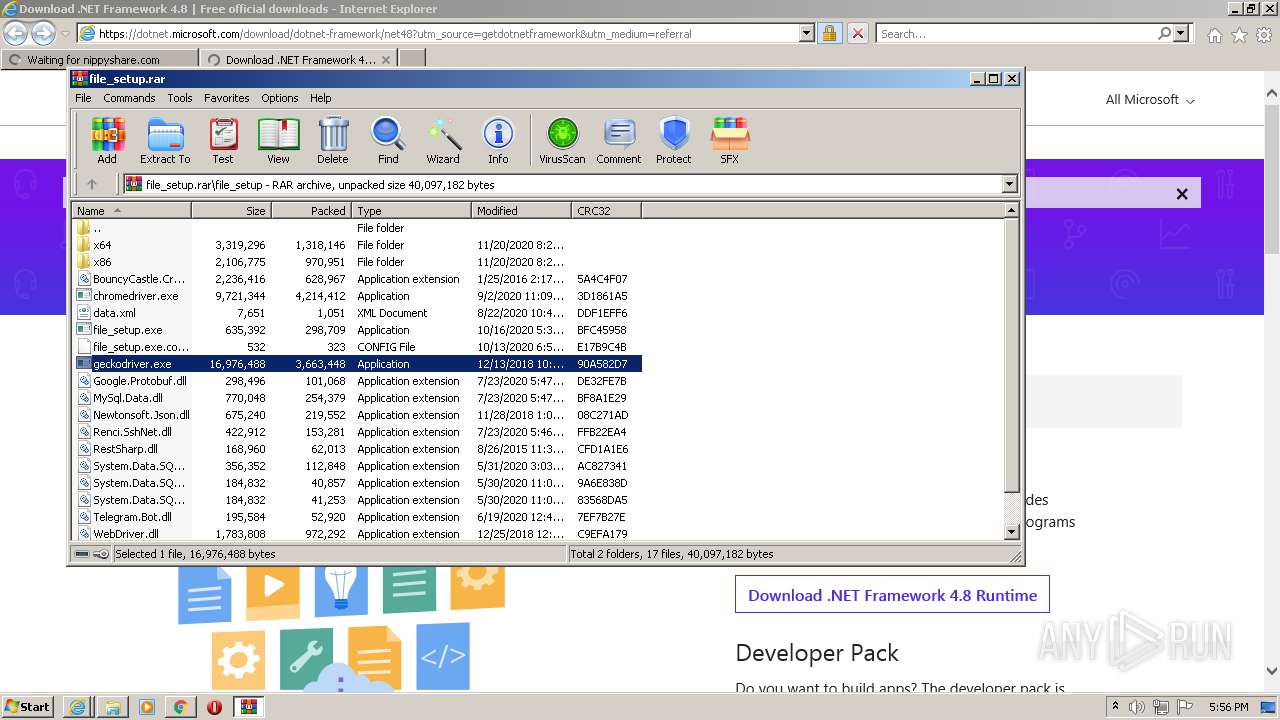
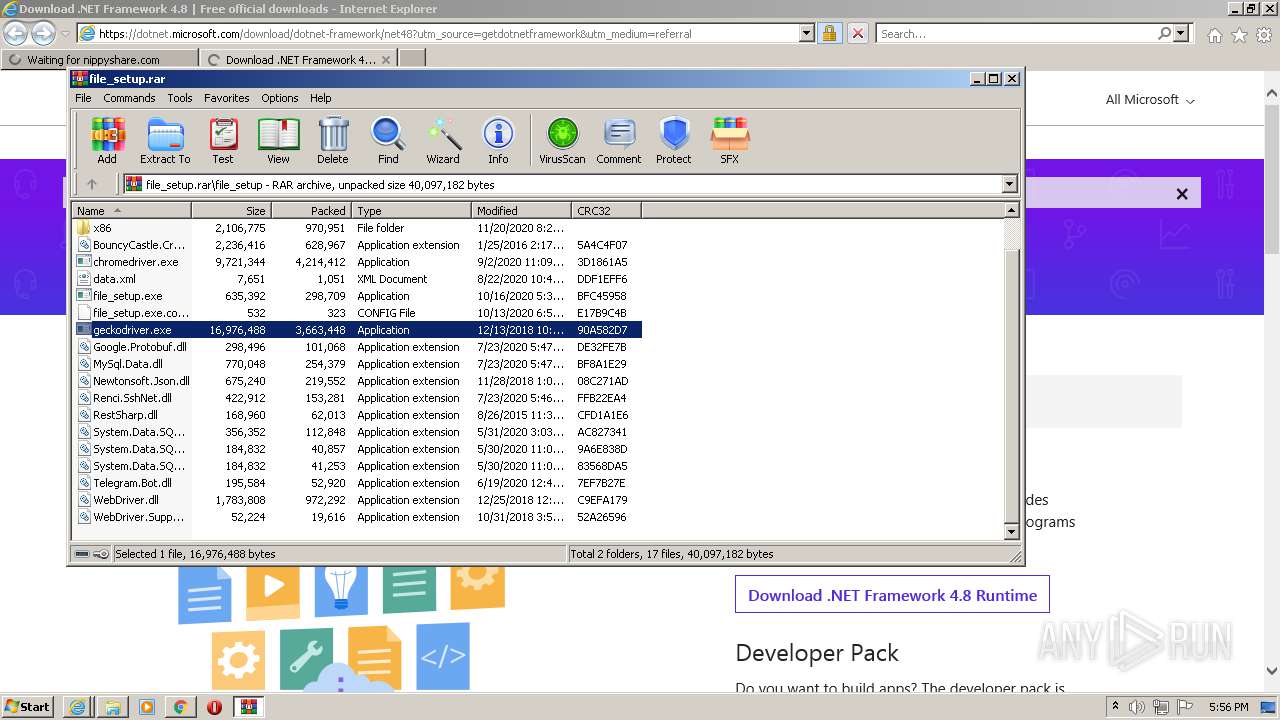
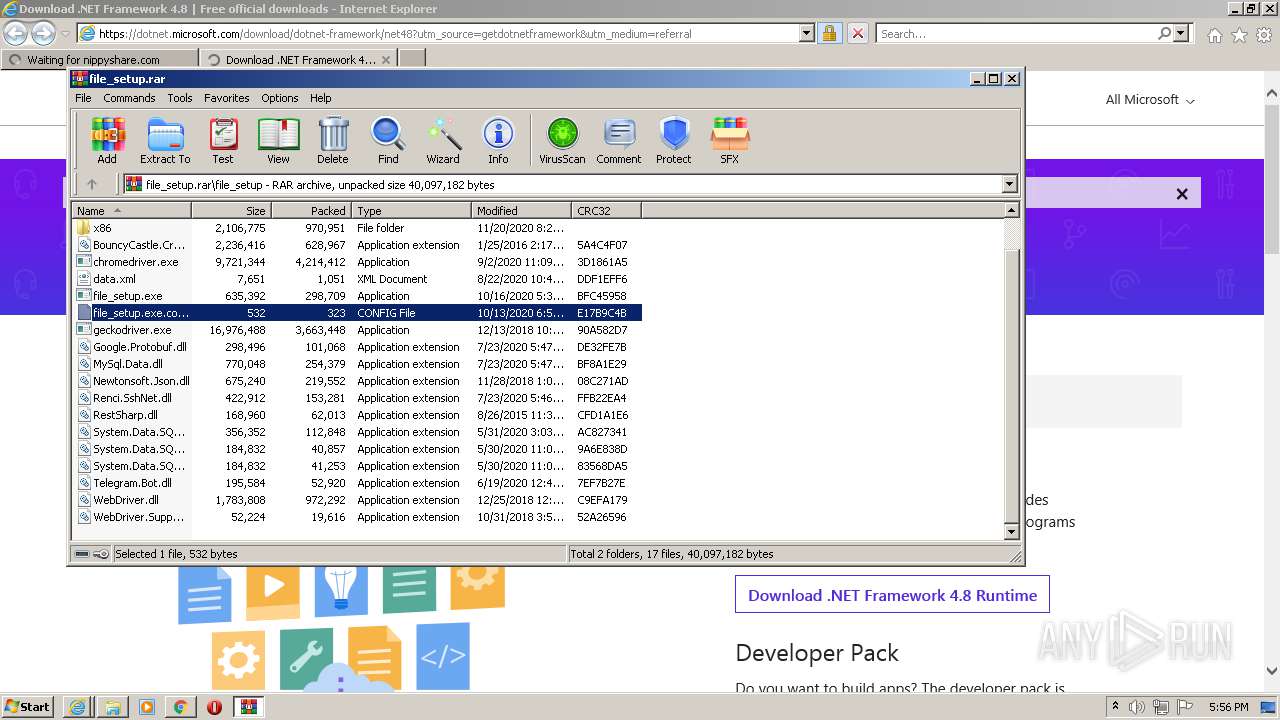
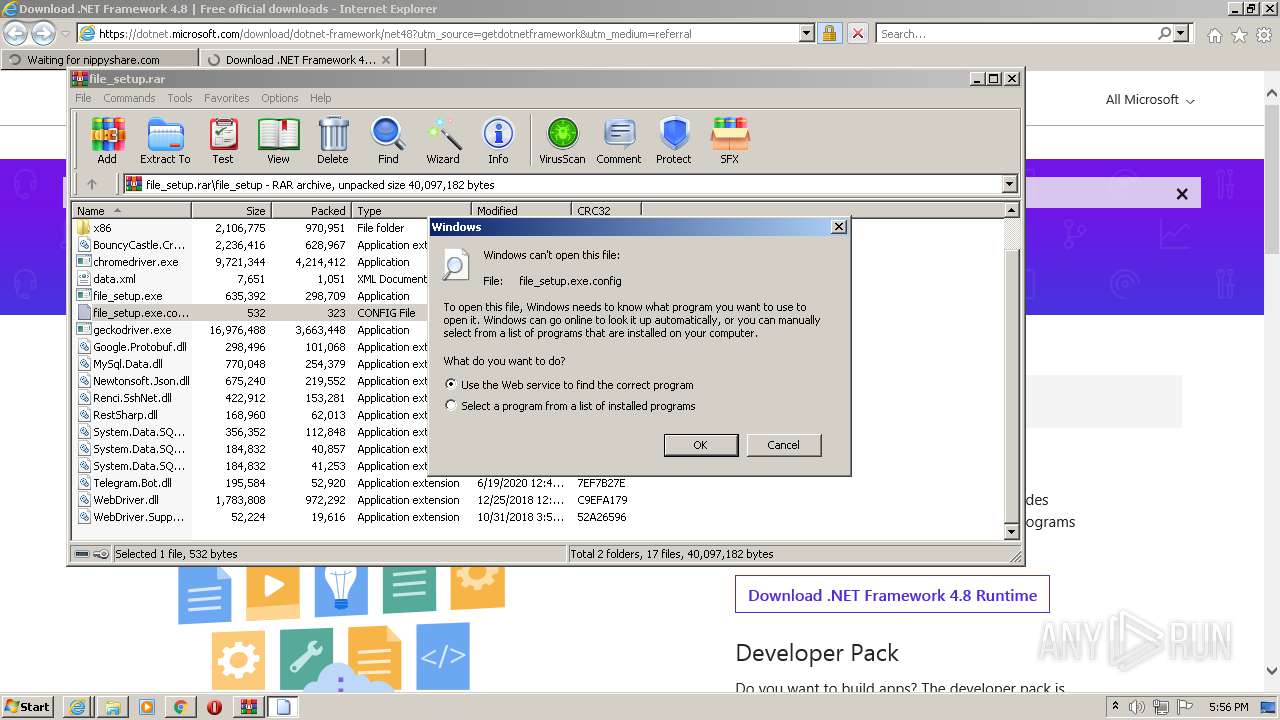
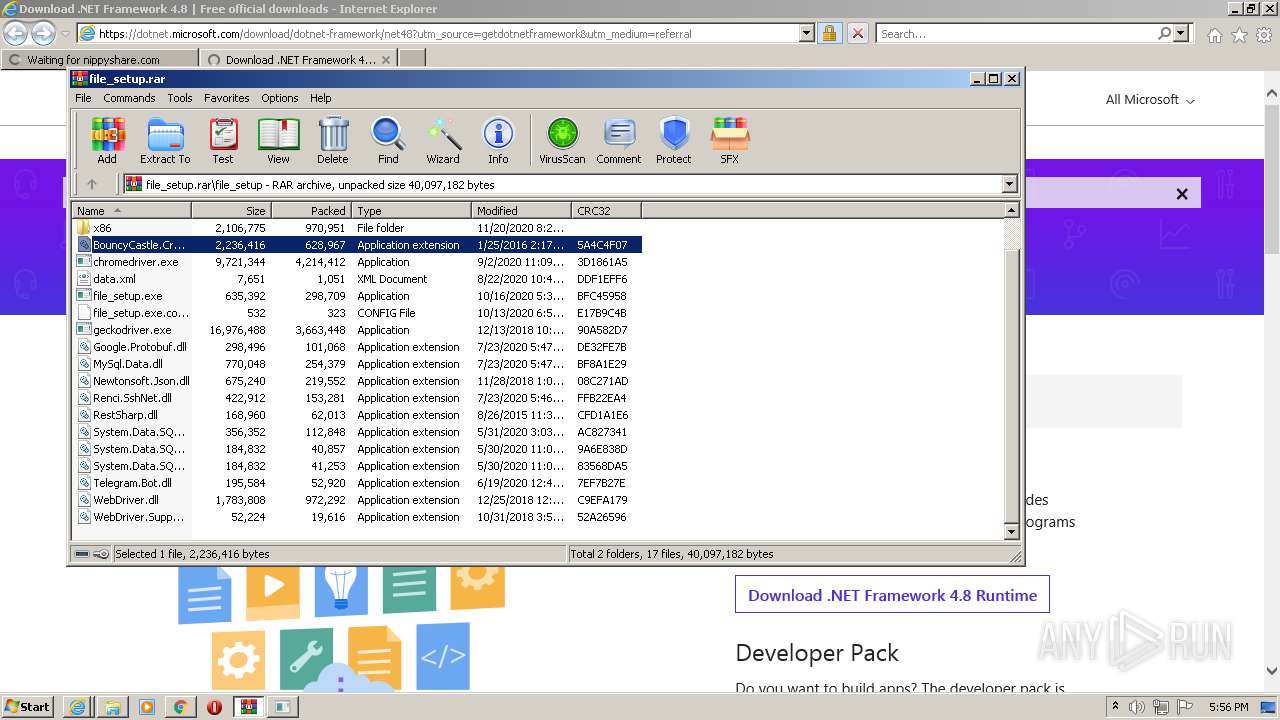
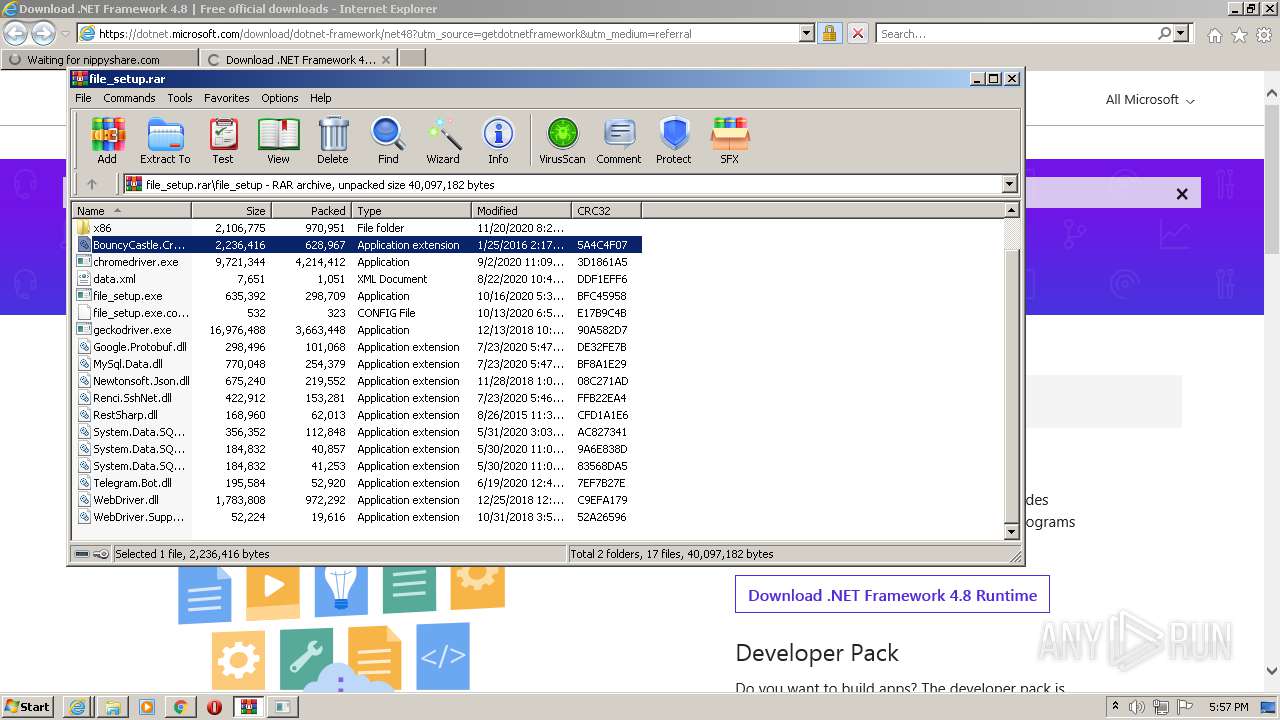
| 1820 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1840.32506\file_setup\chromedriver.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1840.32506\file_setup\chromedriver.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
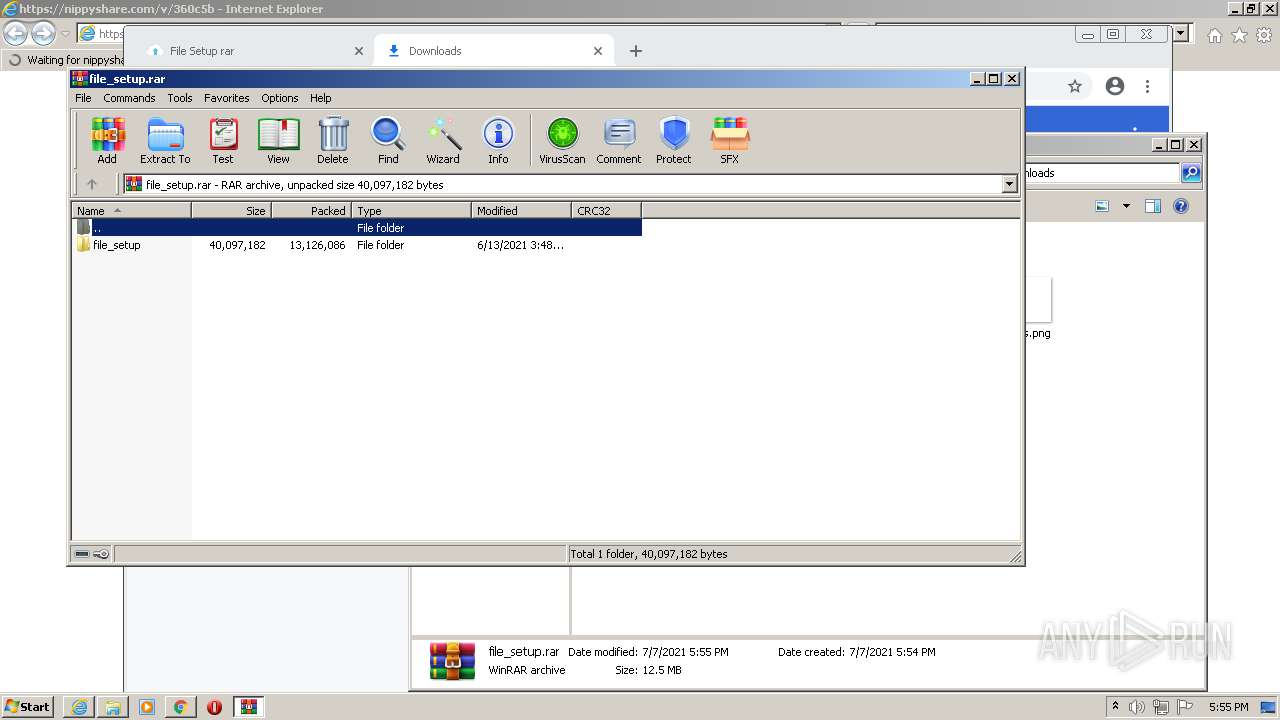
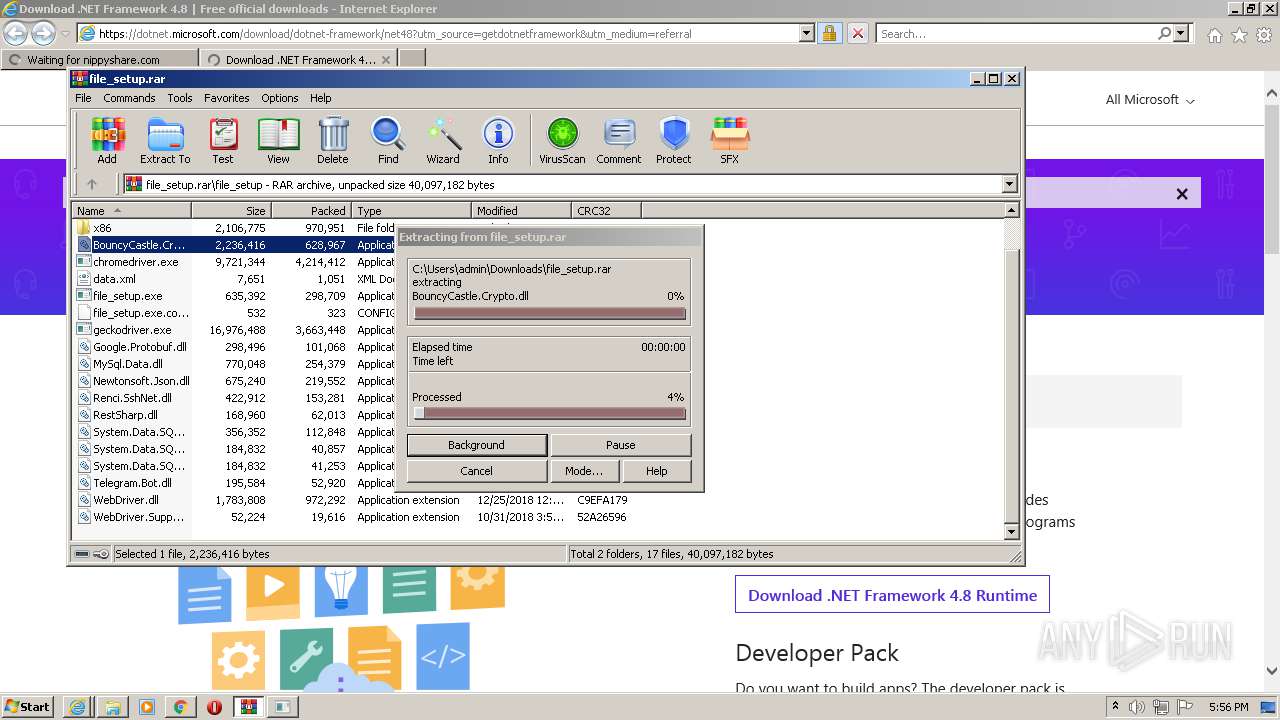
| 1840 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\file_setup.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3945337611082595214,108785302142048750,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3608 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
36 246
Read events
35 829
Write events
406
Delete events
11
Modification events
| (PID) Process: | (3304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30896976 | |||
| (PID) Process: | (3304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30896976 | |||
| (PID) Process: | (3304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3304) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
90
Suspicious files
130
Text files
379
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60E5DC48-F0C.pma | — | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
| 3304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ad58d6dd-5666-4669-822b-b72ee05c309a.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF19fcd5.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
112
DNS requests
67
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3304 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 178 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 358 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 43.6 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 7.10 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 21.1 Kb | whitelisted |
3924 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
3924 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | binary | 365 Kb | whitelisted |
3924 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2988 | iexplore.exe | 185.66.91.78:443 | nippyshare.com | — | — | suspicious |
3304 | iexplore.exe | 2.16.186.42:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3304 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1024 | chrome.exe | 142.250.186.132:443 | www.google.com | Google Inc. | US | whitelisted |
1024 | chrome.exe | 142.250.181.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
1024 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1024 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1024 | chrome.exe | 142.250.74.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1024 | chrome.exe | 142.250.186.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nippyshare.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2988 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |