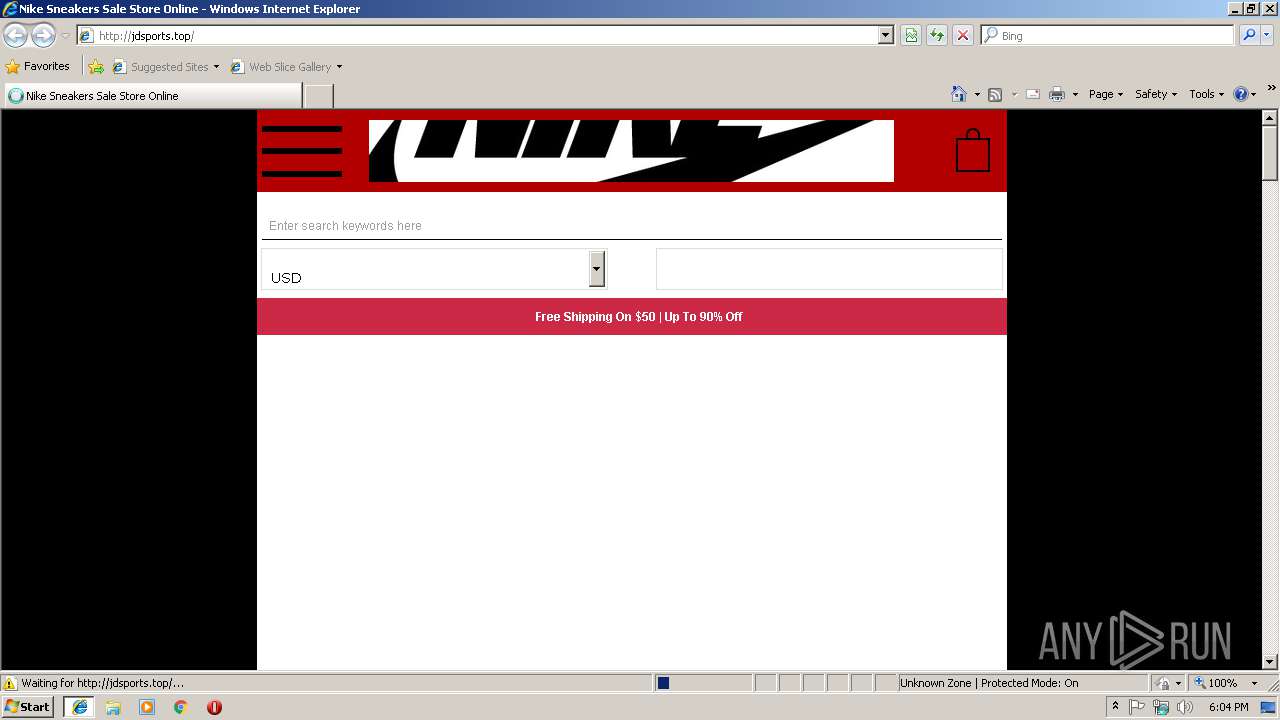
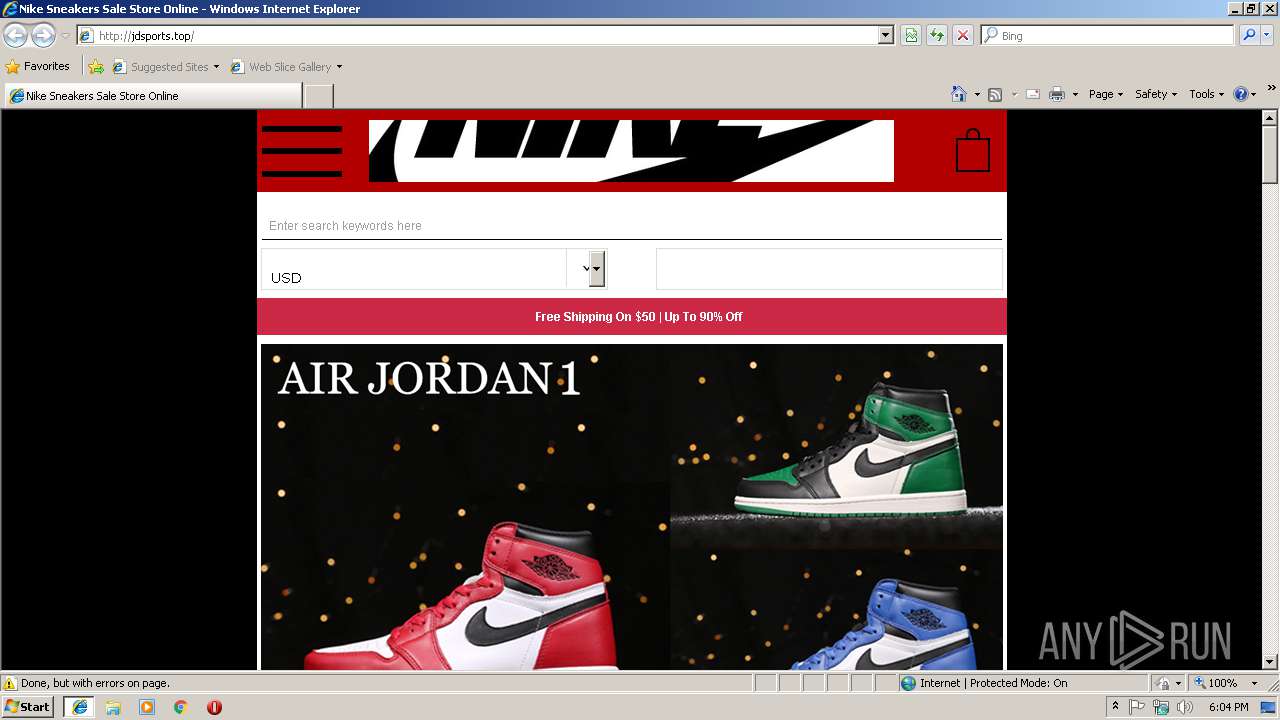
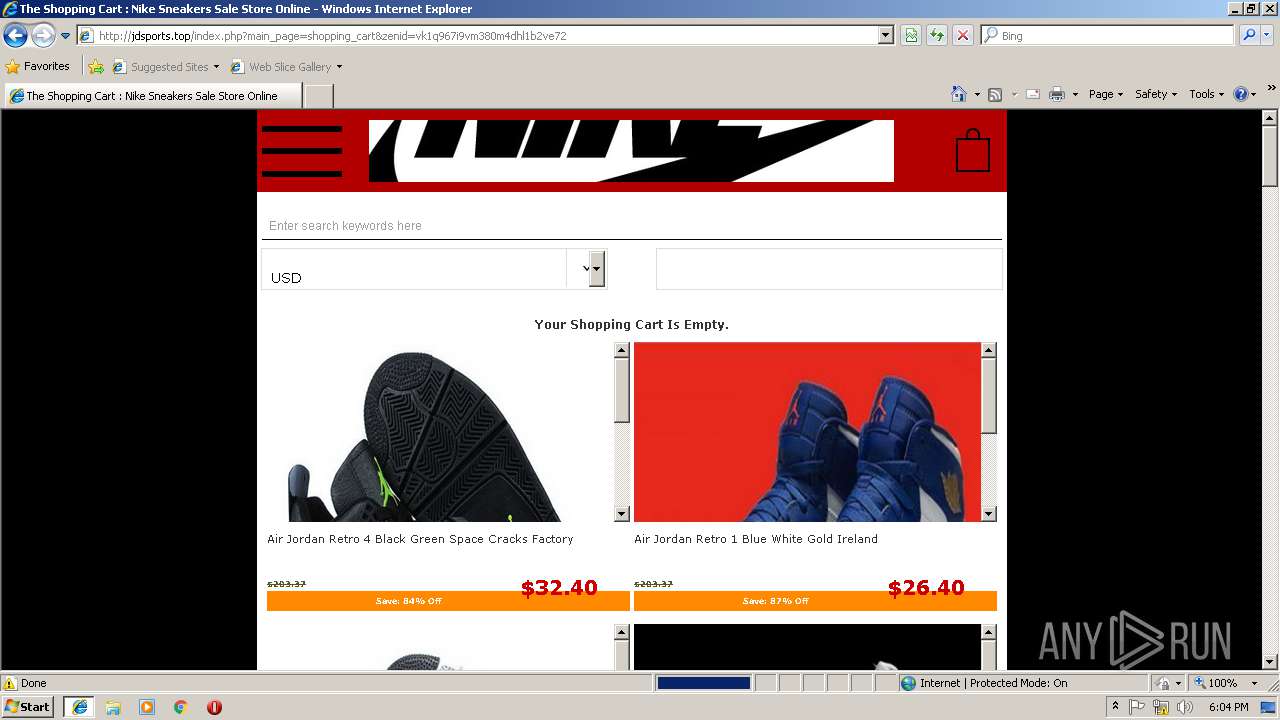
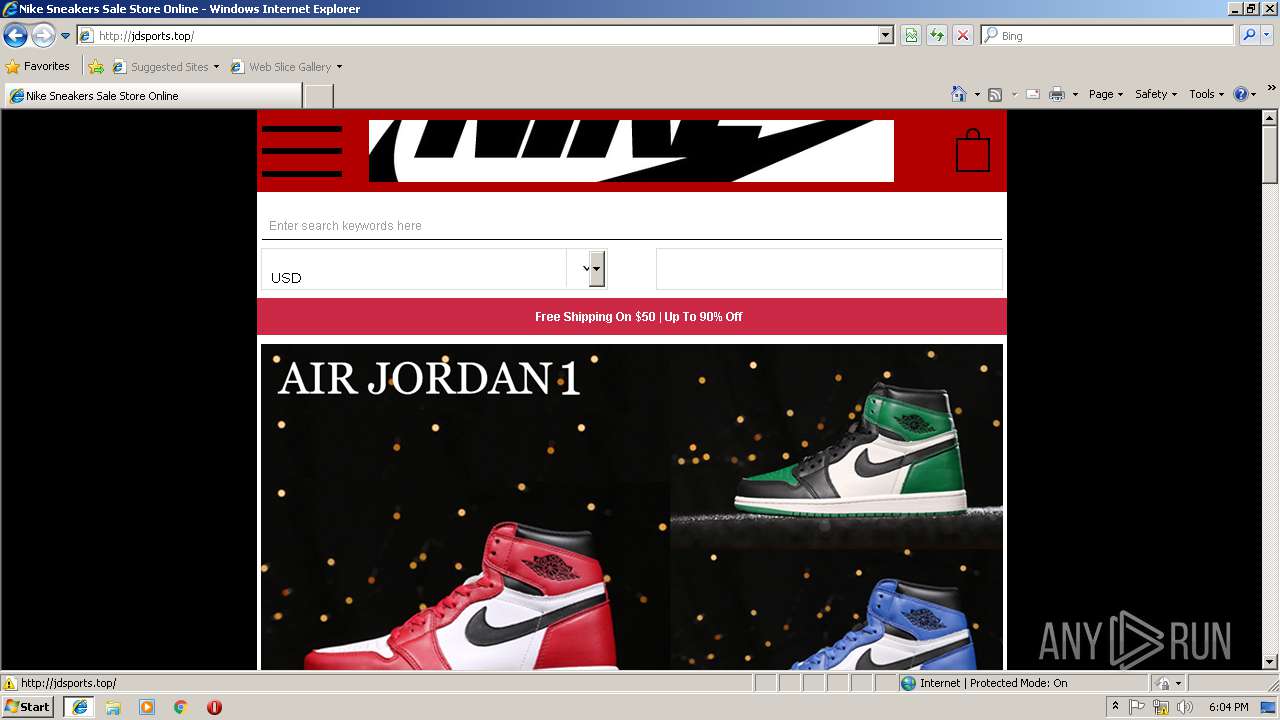
| URL: | http://jdsports.top/ |
| Full analysis: | https://app.any.run/tasks/9240710f-343b-40d2-9d30-15b8072f1364 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2019, 18:03:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 54E6BFEEB2462A08EAC8DB2E15424CCE |
| SHA1: | D2838E5B5818473E78296538CFA566FE2AADC487 |
| SHA256: | 44925C56A65C91CB7E136741169AD818188BA08BB9571277312A4CDBD5F2A682 |
| SSDEEP: | 3:N1KUgVMwQgn:CUov |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3244)
Creates files in the user directory
- iexplore.exe (PID: 3244)
Application launched itself
- iexplore.exe (PID: 2724)
Changes internet zones settings
- iexplore.exe (PID: 2724)
Reads settings of System Certificates
- iexplore.exe (PID: 3244)
Reads internet explorer settings
- iexplore.exe (PID: 3244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2724 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3244 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2724 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
398
Read events
336
Write events
59
Delete events
3
Modification events
| (PID) Process: | (2724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {18AF99B3-1502-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2724) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307010004000A001200030039004C02 | |||
Executable files
0
Suspicious files
0
Text files
82
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2724 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2724 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\jdsports_top[1].txt | — | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\stylesheet_select_popup[1].css | text | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\stylesheet[1].css | text | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\jdsports_top[1].htm | html | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\stylesheet_cart_header[1].css | text | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\stylesheet_css_buttons[1].css | text | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\stylesheet_categories_menu[1].css | text | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\stylesheet_znew[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
84
TCP/UDP connections
12
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3244 | iexplore.exe | GET | 200 | 104.233.213.89:80 | http://jdsports.top/includes/templates/N_Shoes_mobile/css/stylesheet_select_popup.css | US | text | 9.85 Kb | suspicious |
3244 | iexplore.exe | GET | 200 | 104.233.213.89:80 | http://jdsports.top/includes/templates/N_Shoes_mobile/css/stylesheet_cart_header.css | US | text | 571 b | suspicious |
3244 | iexplore.exe | GET | 200 | 104.233.213.89:80 | http://jdsports.top/includes/templates/N_Shoes_mobile/css/stylesheet_footer_menu.css | US | text | 833 b | suspicious |
3244 | iexplore.exe | GET | 200 | 104.233.213.89:80 | http://jdsports.top/includes/templates/N_Shoes_mobile/css/stylesheet_categories_menu.css | US | text | 1.08 Kb | suspicious |
3244 | iexplore.exe | GET | 200 | 104.233.213.89:80 | http://jdsports.top/includes/templates/N_Shoes_mobile/css/stylesheet_css_buttons.css | US | text | 1.22 Kb | suspicious |
3244 | iexplore.exe | GET | 200 | 104.233.213.89:80 | http://jdsports.top/includes/templates/N_Shoes_mobile/jscript/jscript_jquery-touchslider.js | US | text | 108 Kb | suspicious |
3244 | iexplore.exe | GET | 200 | 104.233.213.89:80 | http://jdsports.top/includes/templates/N_Shoes_mobile/jscript/jscript__jquery.min.js | US | html | 36.5 Kb | suspicious |
3244 | iexplore.exe | GET | 200 | 104.233.213.89:80 | http://jdsports.top/includes/templates/N_Shoes_mobile/css/stylesheet_productupdates.css | US | text | 24.9 Kb | suspicious |
3244 | iexplore.exe | GET | 200 | 104.233.213.89:80 | http://jdsports.top/includes/templates/N_Shoes_mobile/css/stylesheet.css | US | text | 10.2 Kb | suspicious |
3244 | iexplore.exe | GET | 200 | 104.233.213.89:80 | http://jdsports.top/includes/templates/N_Shoes_mobile/css/stylesheet_res.css | US | text | 602 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2724 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3244 | iexplore.exe | 104.233.213.89:80 | jdsports.top | PEG TECH INC | US | suspicious |
3244 | iexplore.exe | 157.240.1.23:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
3244 | iexplore.exe | 183.131.207.78:80 | ia.51.la | DaLi | CN | suspicious |
3244 | iexplore.exe | 220.243.212.50:443 | js.users.51.la | QUANTIL, INC | CN | unknown |
2724 | iexplore.exe | 104.233.213.89:80 | jdsports.top | PEG TECH INC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
jdsports.top |
| suspicious |
connect.facebook.net |
| whitelisted |
js.users.51.la |
| whitelisted |
ia.51.la |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3244 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3244 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |