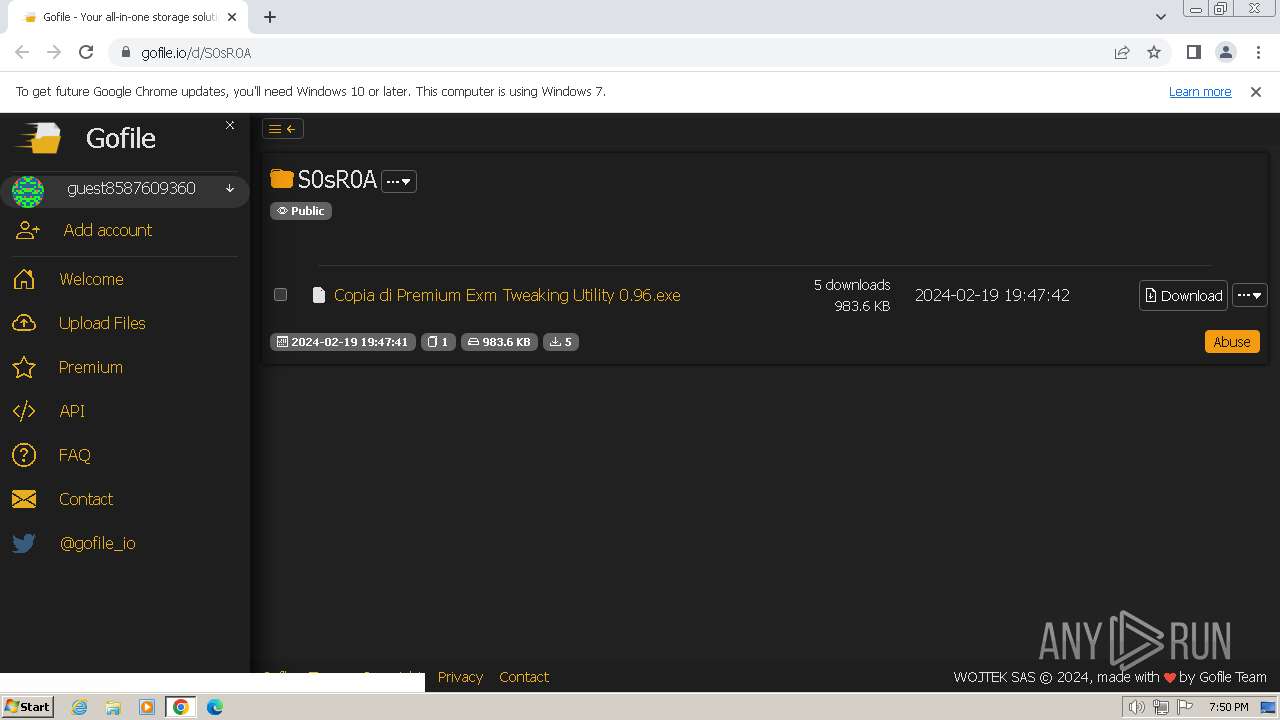
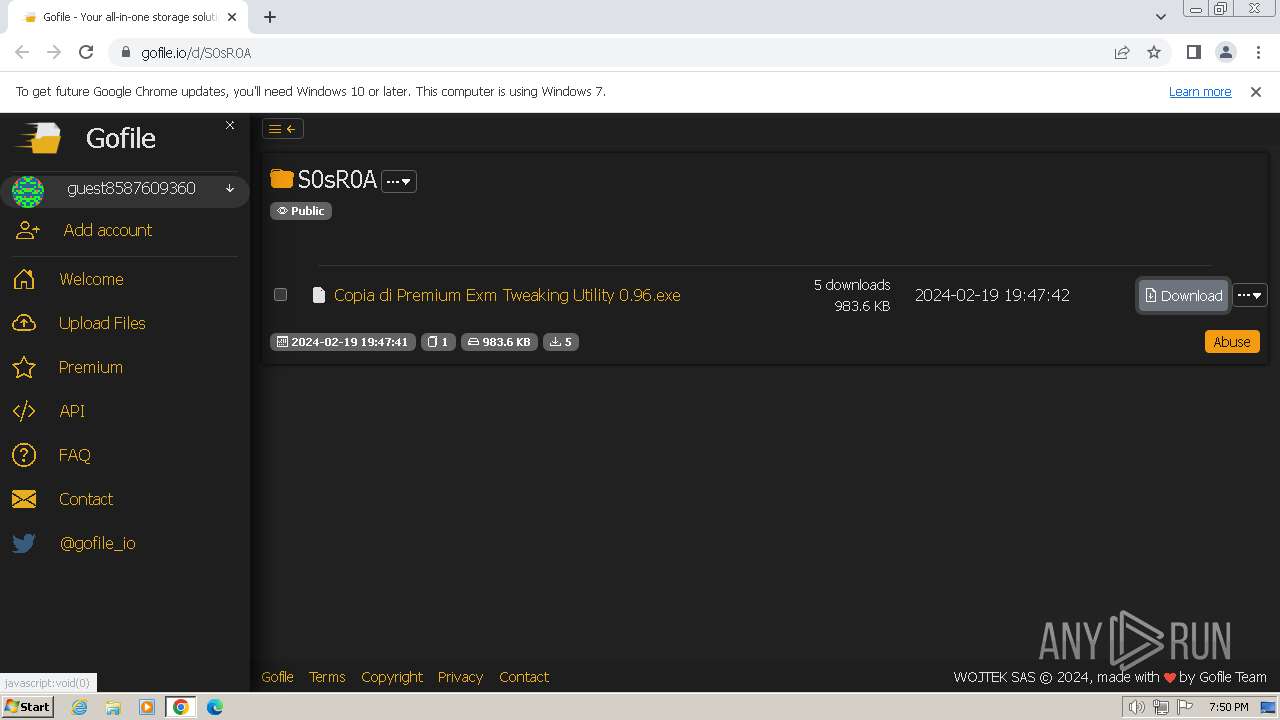
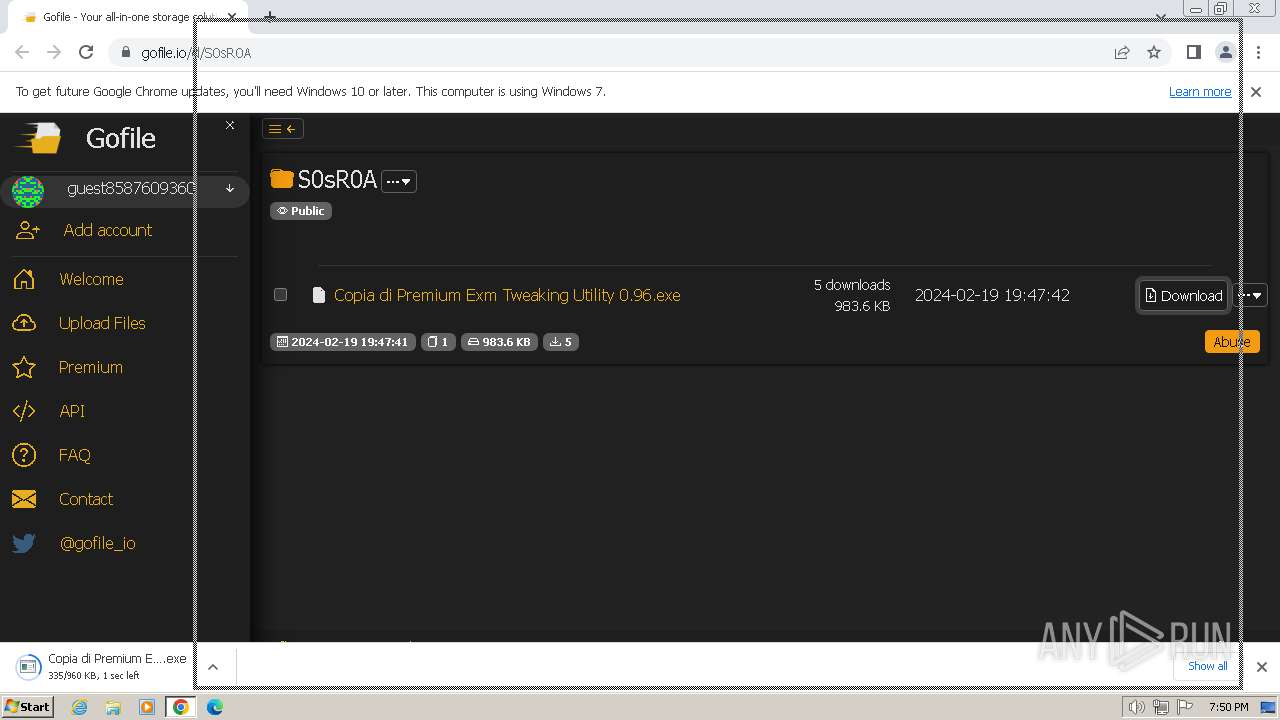
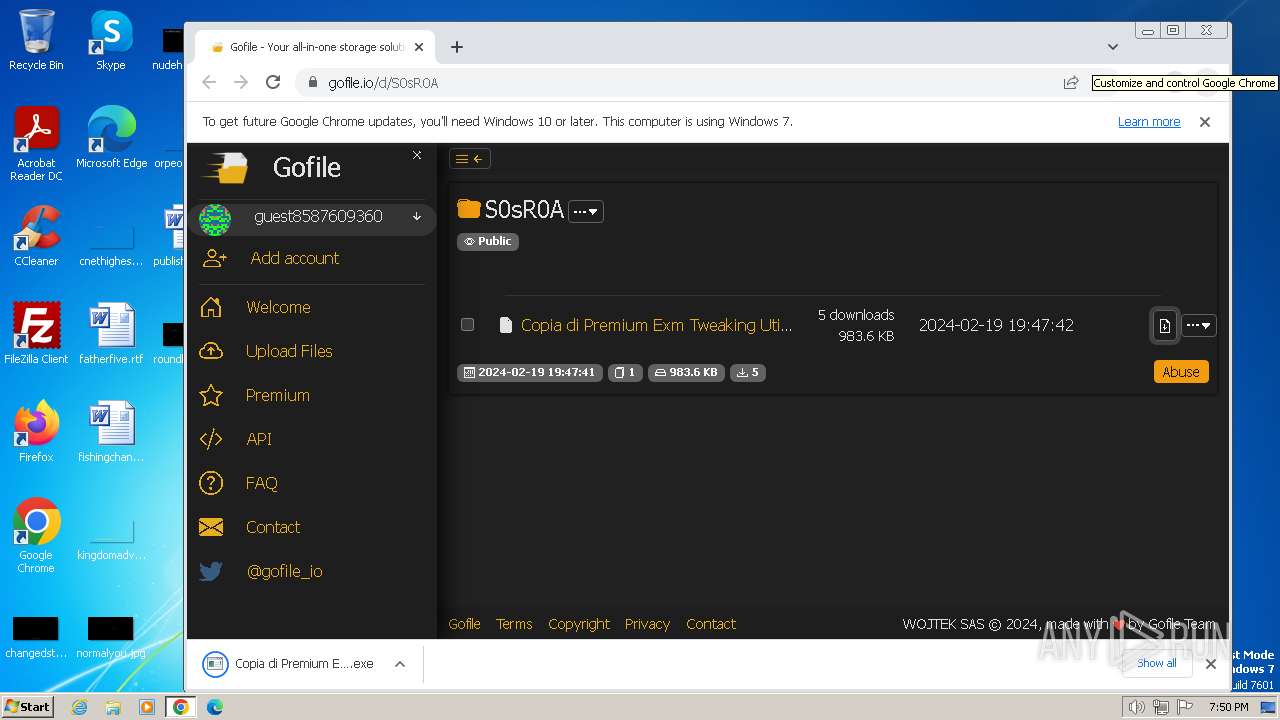
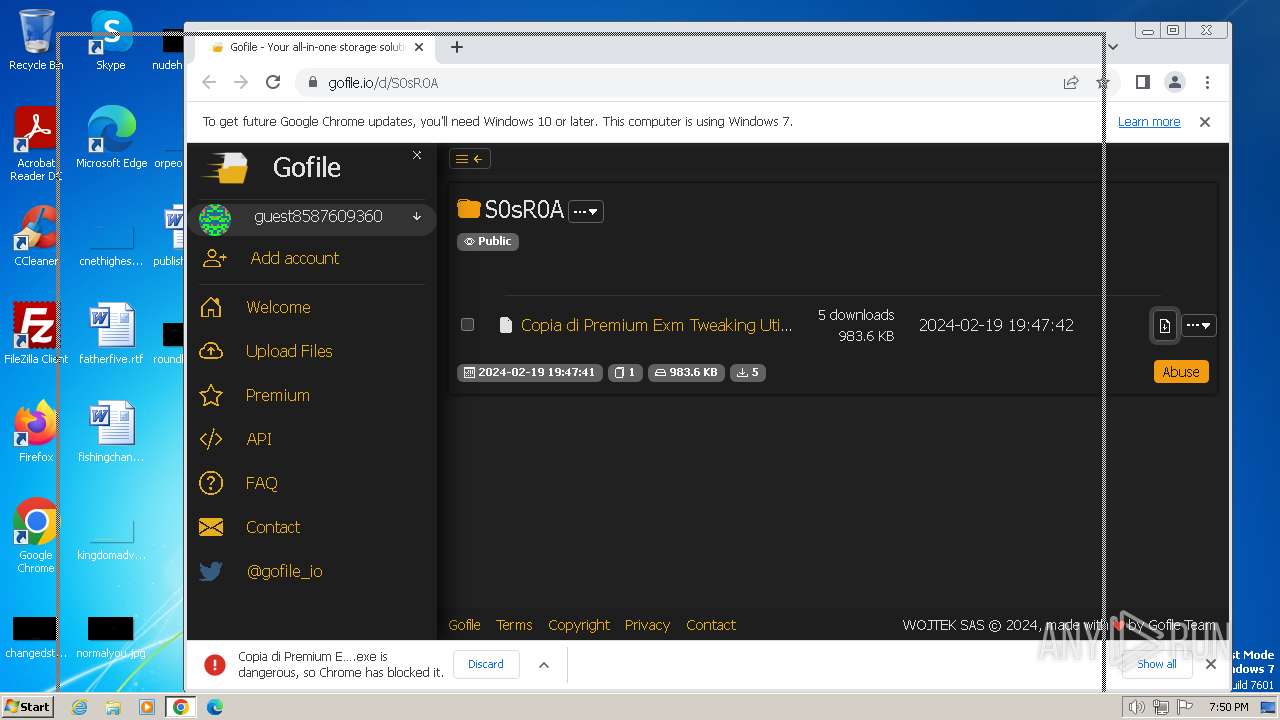
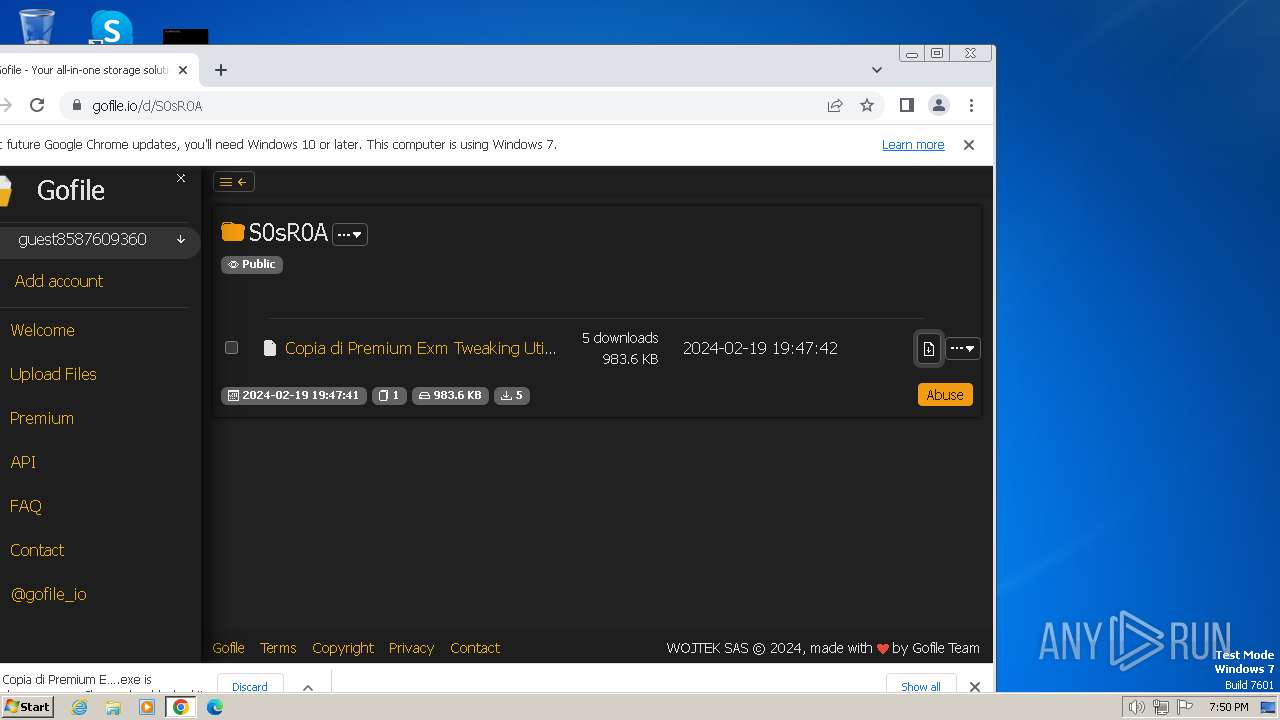
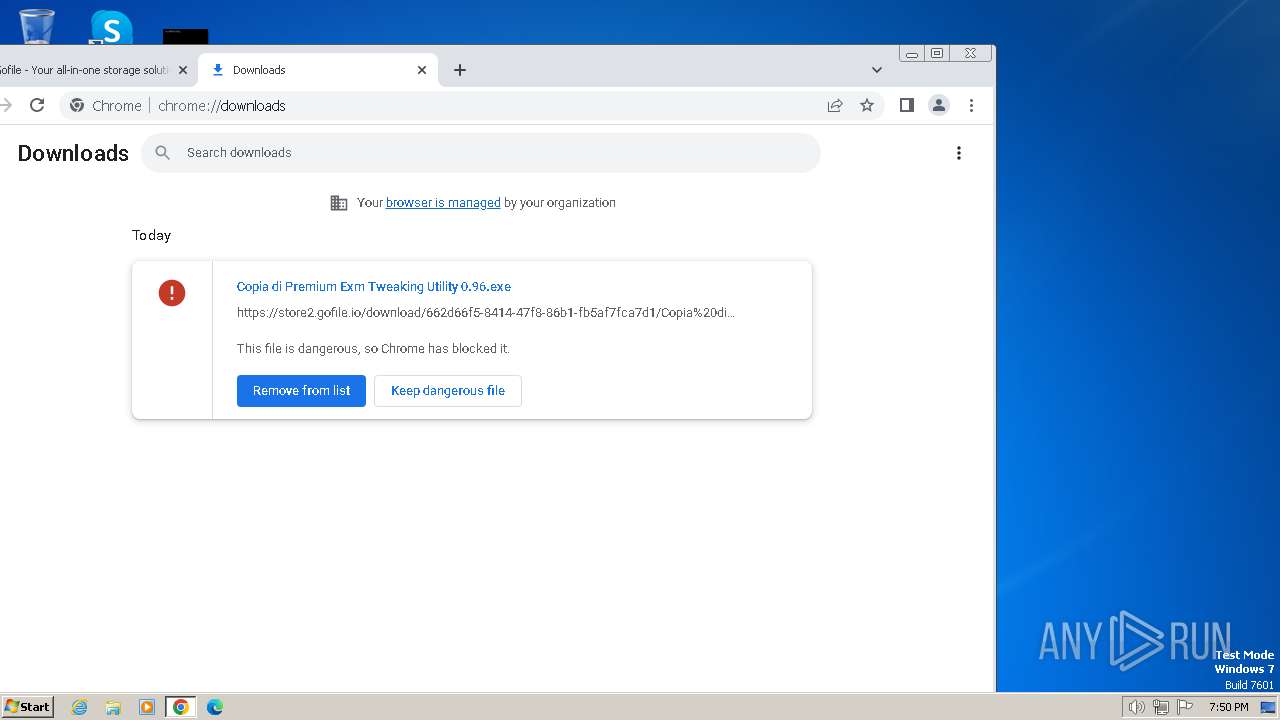
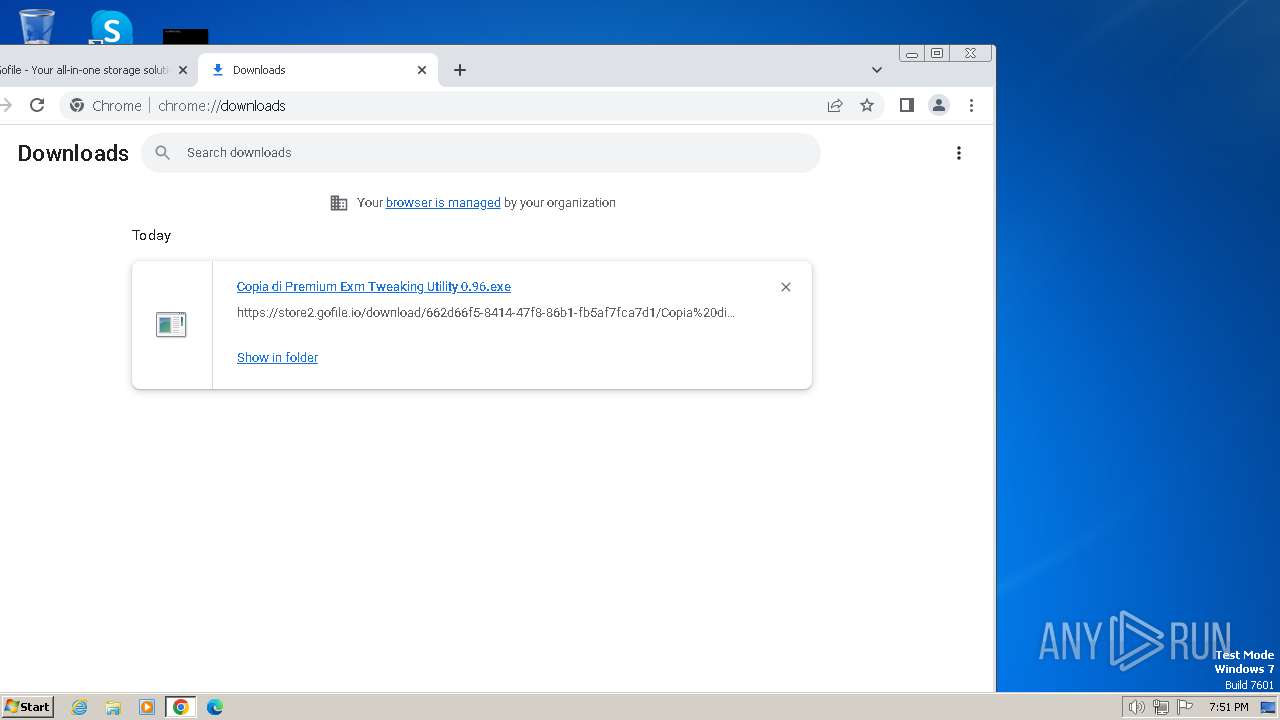
| URL: | https://gofile.io/d/S0sR0A |
| Full analysis: | https://app.any.run/tasks/380d72b5-e0e7-4d2e-9cd0-7bdfcc225e9e |
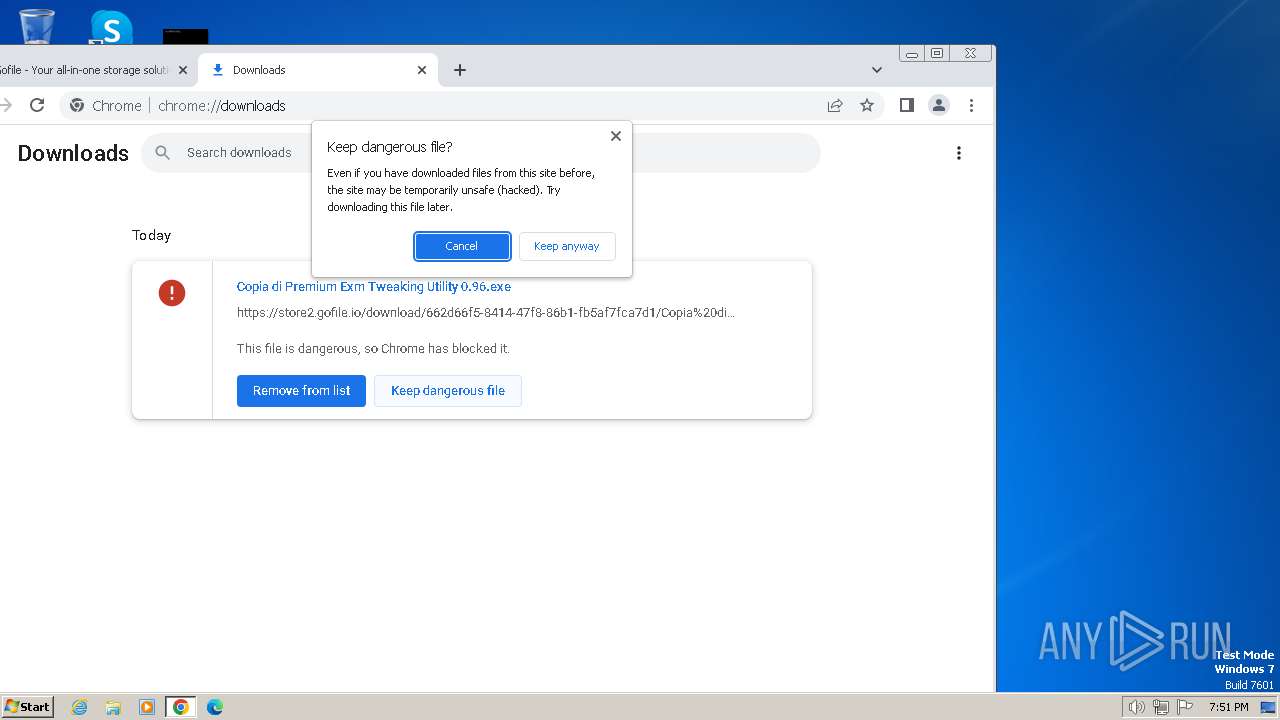
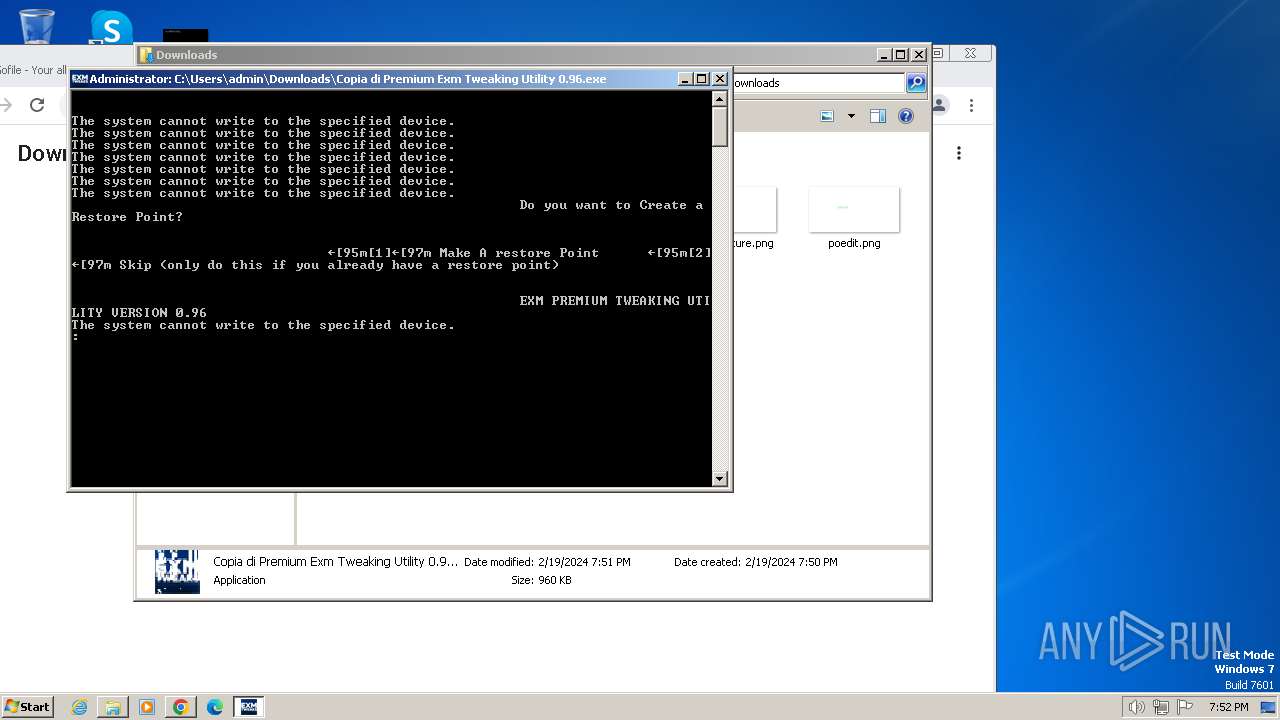
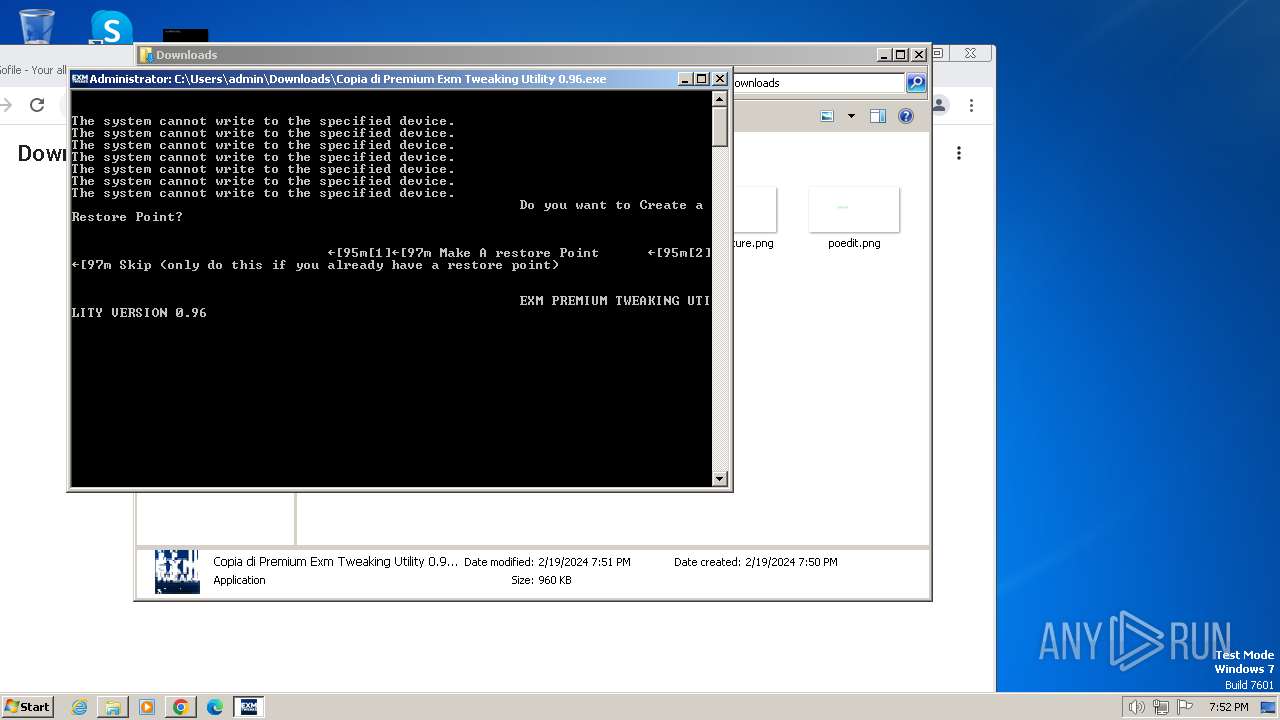
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2024, 19:50:38 |
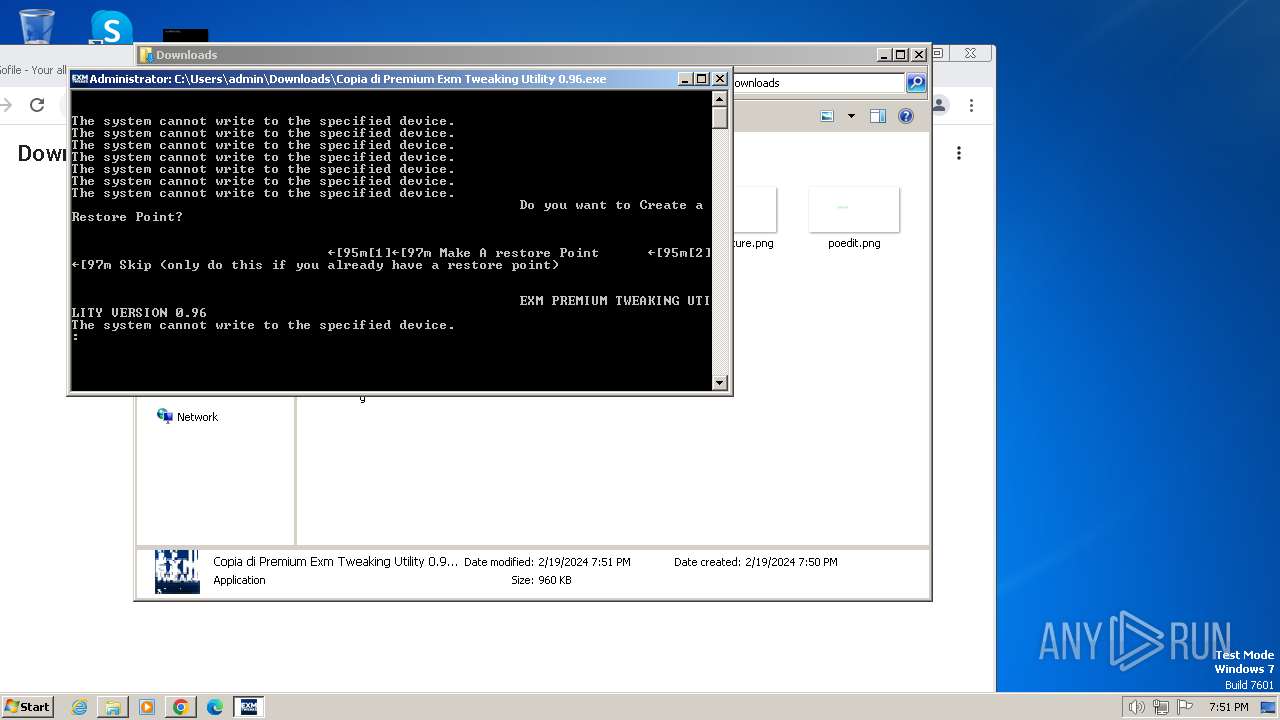
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E856AA37DF076281EB8491E3EA977750 |
| SHA1: | FA1E8AB2C292436A7BDE1E1652361E1D8B2D3D9E |
| SHA256: | 4491BD2456F06D963227DF84CE0F520444D604A0309ADA66DB5683BCA60F4666 |
| SSDEEP: | 3:N8rxL1NO:2Zm |
MALICIOUS
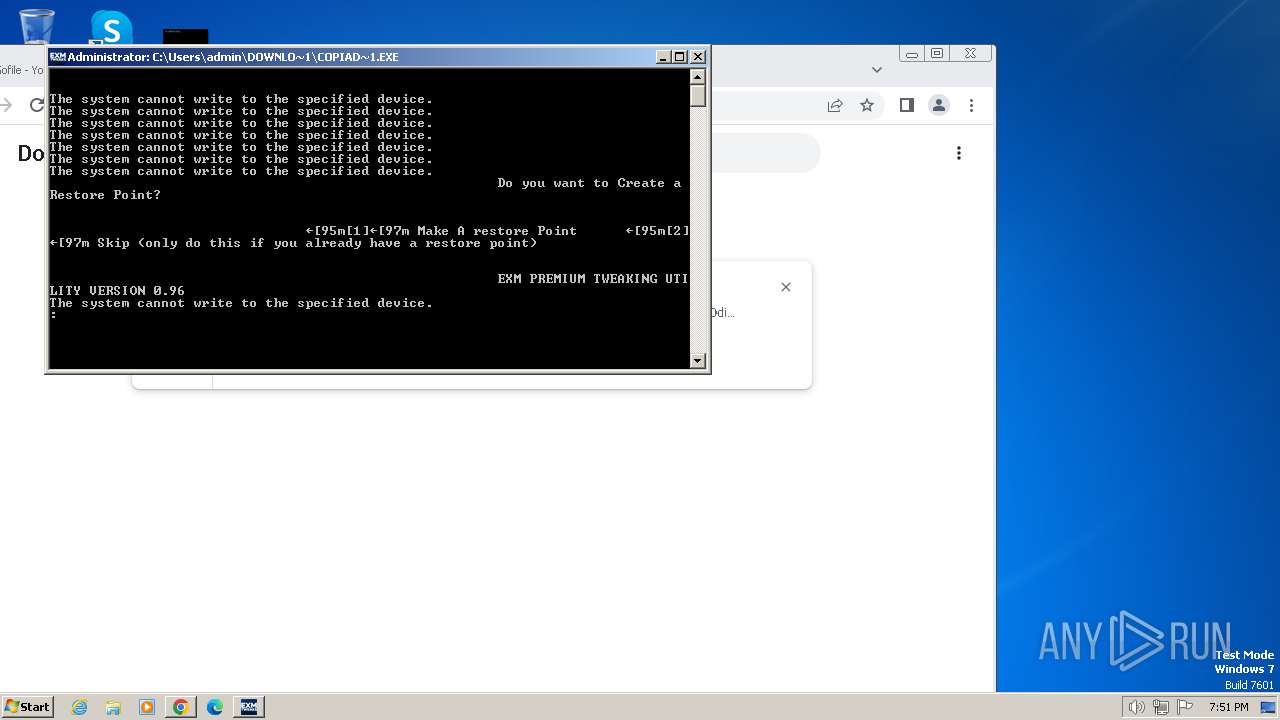
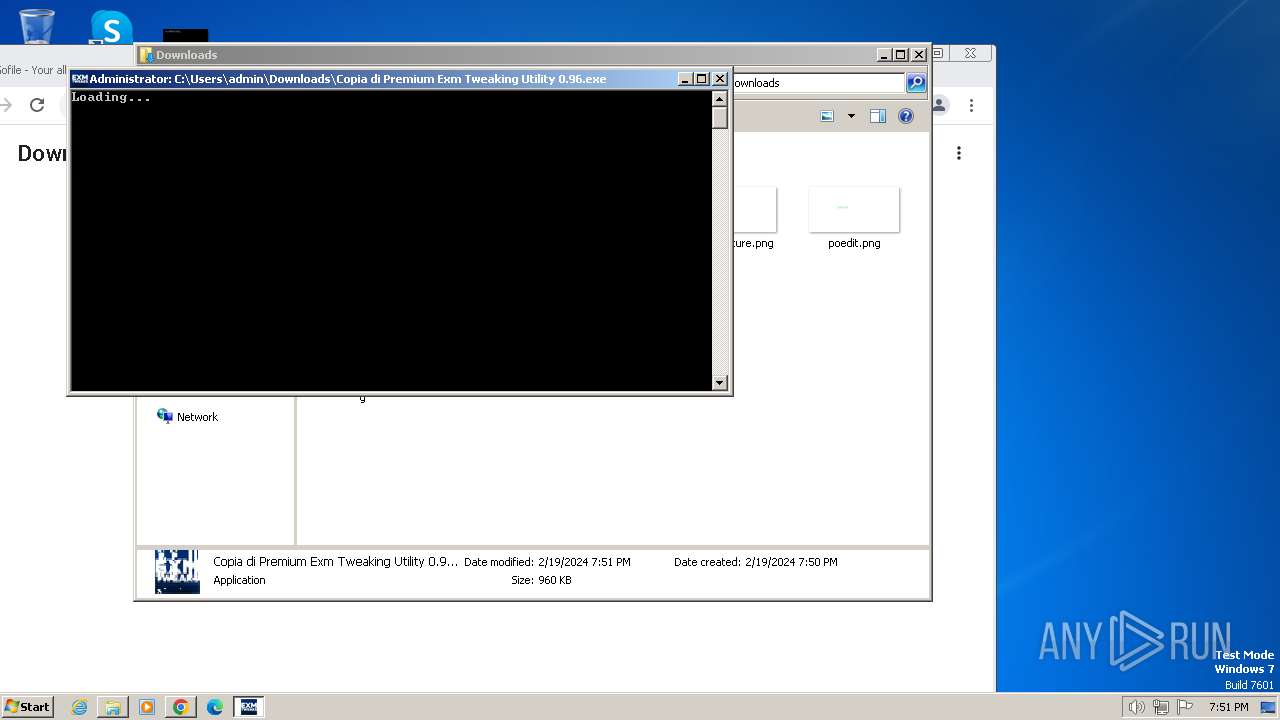
Changes powershell execution policy (Unrestricted)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 316)
SUSPICIOUS
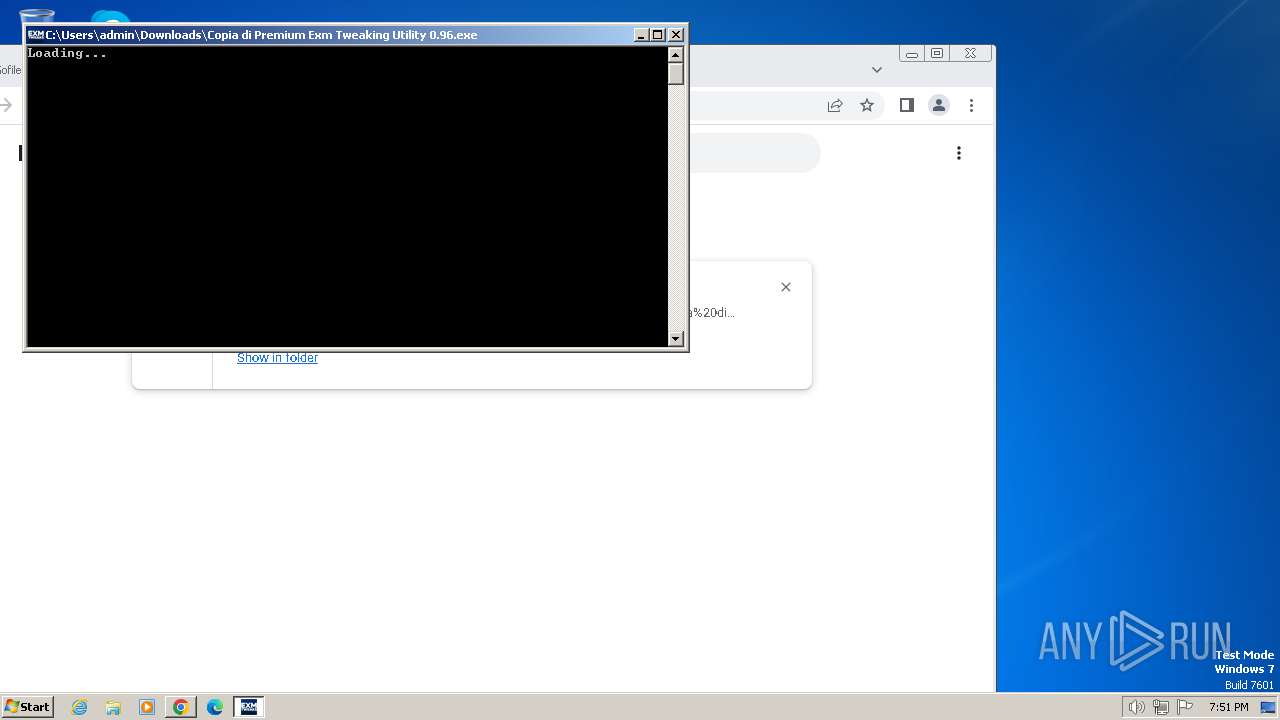
Starts CMD.EXE for commands execution
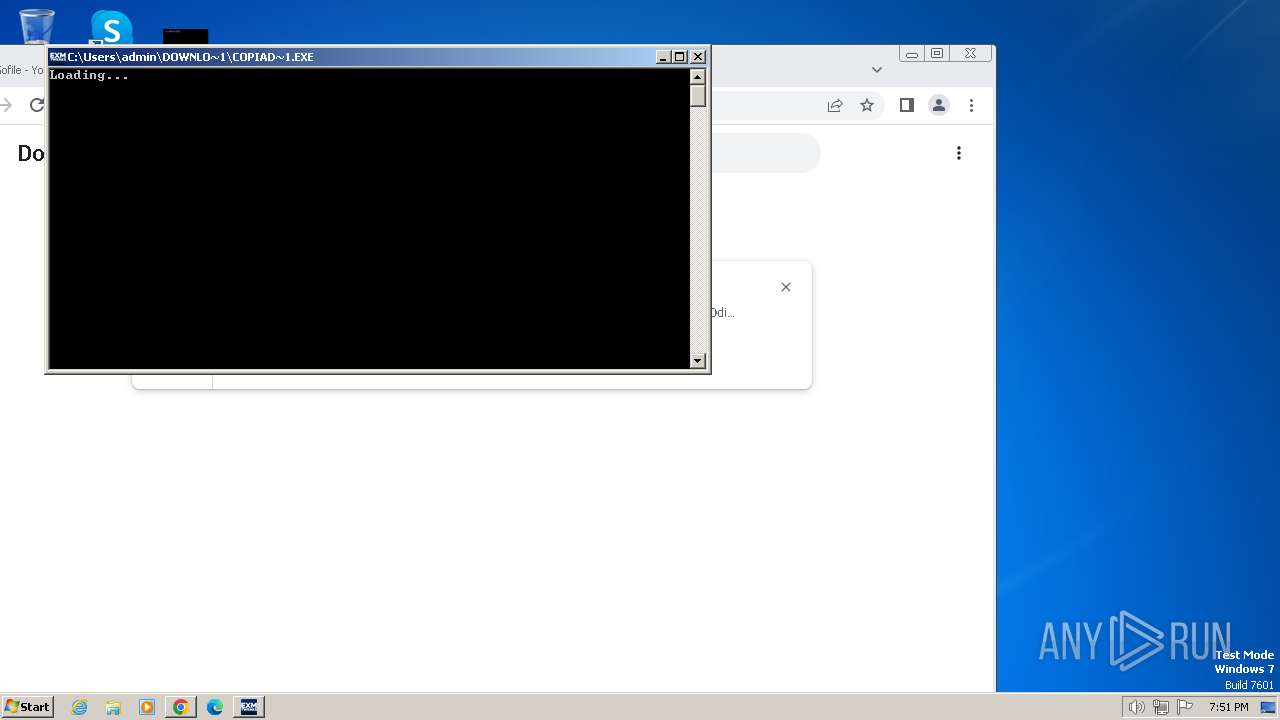
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 2748)
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 1196)
- cmd.exe (PID: 3548)
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 3800)
- cmd.exe (PID: 316)
Executing commands from a ".bat" file
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 2748)
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 1196)
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 3800)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2616)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 316)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2616)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 316)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2616)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 316)
Starts application with an unusual extension
- cmd.exe (PID: 2616)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 316)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2616)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 316)
The process hide an interactive prompt from the user
- cmd.exe (PID: 2616)
Reads the Internet Settings
- powershell.exe (PID: 3108)
- WMIC.exe (PID: 956)
- WMIC.exe (PID: 4072)
Application launched itself
- cmd.exe (PID: 3548)
- cmd.exe (PID: 316)
Uses WMIC.EXE to obtain user accounts information
- cmd.exe (PID: 1824)
- cmd.exe (PID: 1820)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1824)
- cmd.exe (PID: 1820)
INFO
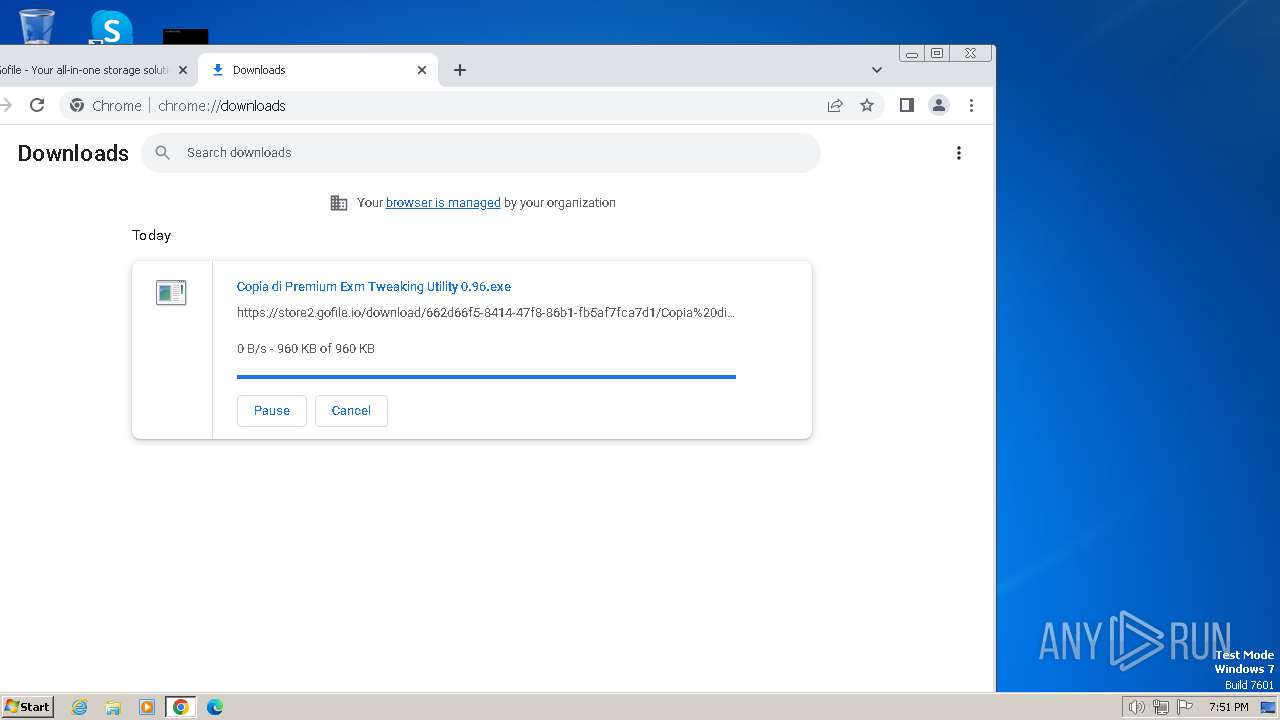
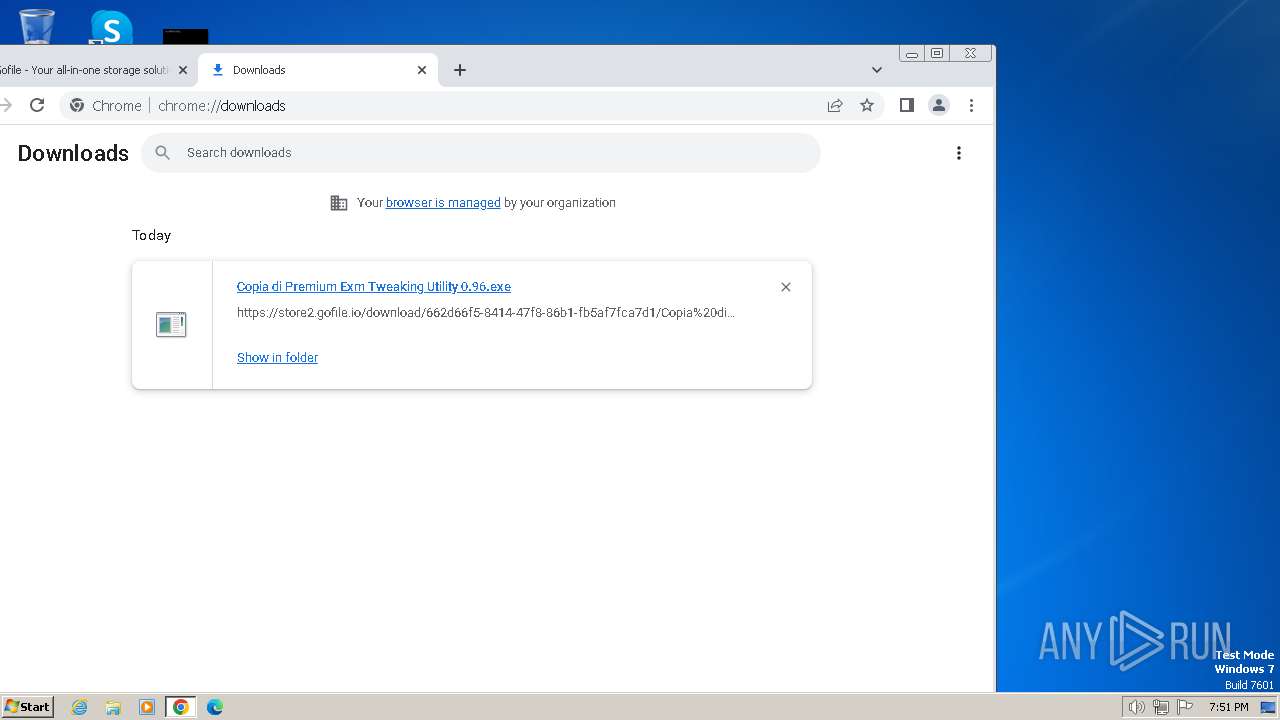
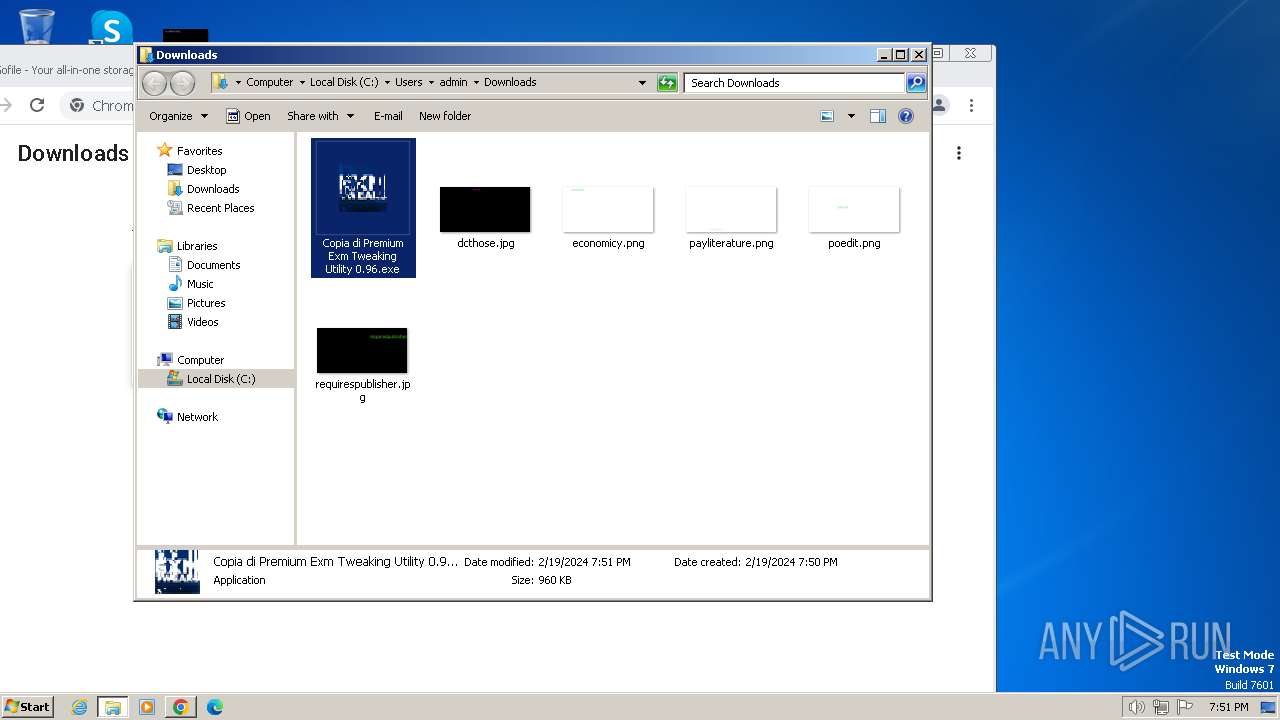
Executable content was dropped or overwritten
- chrome.exe (PID: 3672)
Checks supported languages
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 2748)
- chcp.com (PID: 3456)
- chcp.com (PID: 3236)
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 1196)
- chcp.com (PID: 1388)
- chcp.com (PID: 2940)
- chcp.com (PID: 3912)
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 3800)
- chcp.com (PID: 896)
- chcp.com (PID: 3192)
- chcp.com (PID: 548)
- chcp.com (PID: 3400)
- chcp.com (PID: 2612)
- wmpnscfg.exe (PID: 992)
- chcp.com (PID: 3380)
- chcp.com (PID: 3608)
- chcp.com (PID: 3296)
- chcp.com (PID: 2644)
- chcp.com (PID: 948)
- chcp.com (PID: 1496)
- chcp.com (PID: 1604)
Drops the executable file immediately after the start
- chrome.exe (PID: 3672)
The process uses the downloaded file
- chrome.exe (PID: 3672)
- chrome.exe (PID: 480)
- powershell.exe (PID: 3108)
Create files in a temporary directory
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 2748)
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 1196)
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 3800)
Application launched itself
- chrome.exe (PID: 3672)
The executable file from the user directory is run by the Powershell process
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 1196)
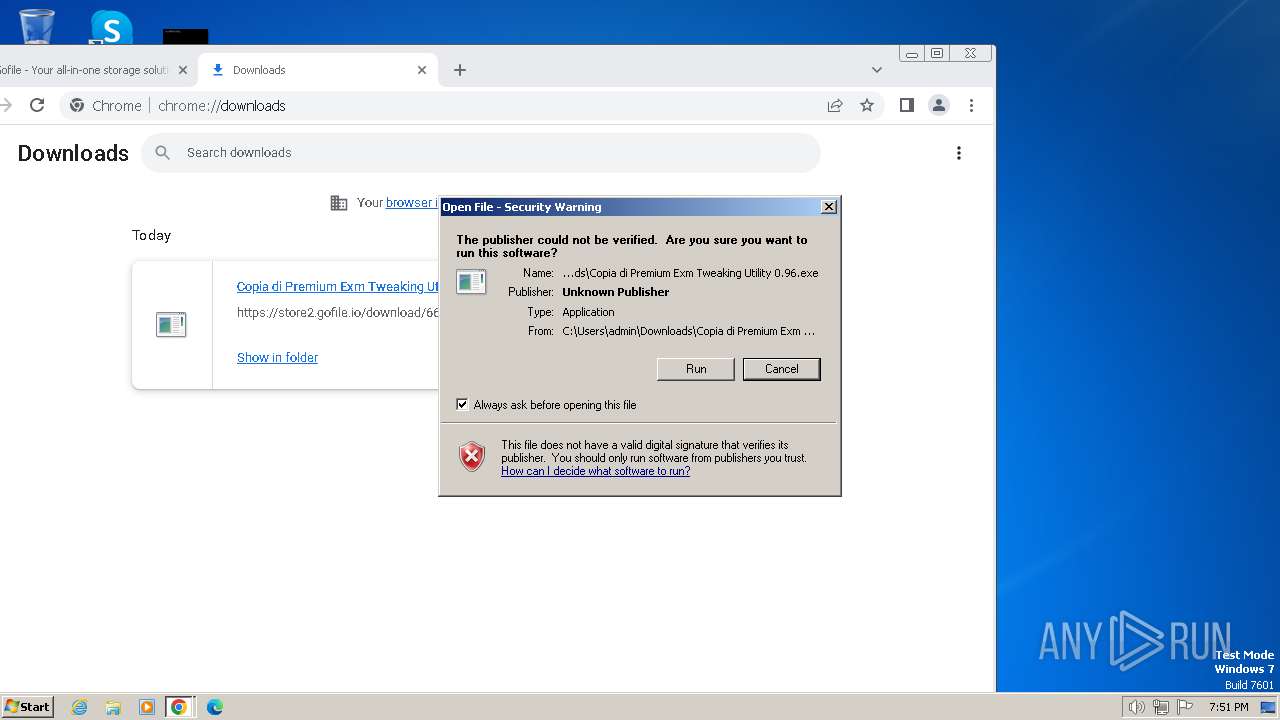
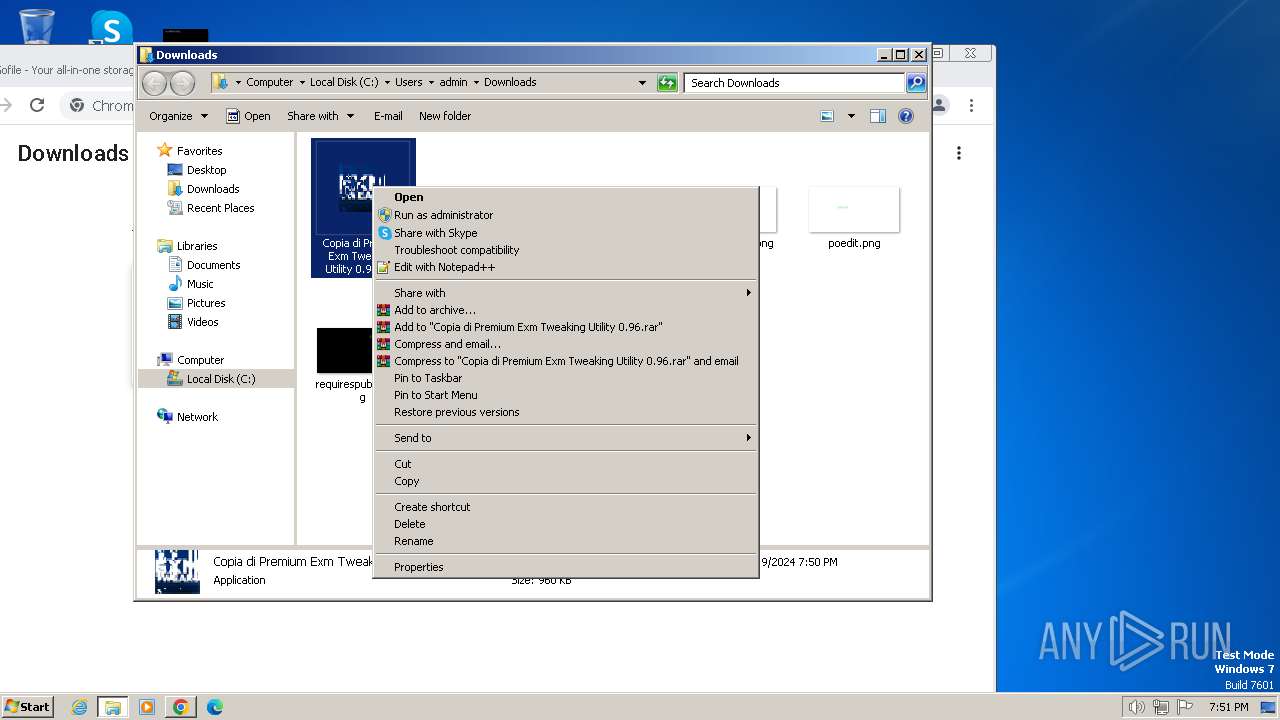
Manual execution by a user
- Copia di Premium Exm Tweaking Utility 0.96.exe (PID: 3800)
- wmpnscfg.exe (PID: 992)
Reads the computer name
- wmpnscfg.exe (PID: 992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
128
Monitored processes
80
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | powershell -ExecutionPolicy Unrestricted -NoProfile Enable-ComputerRestore -Drive 'C:\' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 316 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\8306.tmp\8307.tmp\8308.bat "C:\Users\admin\Downloads\Copia di Premium Exm Tweaking Utility 0.96.exe"" | C:\Windows\System32\cmd.exe | — | Copia di Premium Exm Tweaking Utility 0.96.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1016 --field-trial-handle=1108,i,4399882357578523065,9918136019549432450,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3600 --field-trial-handle=1108,i,4399882357578523065,9918136019549432450,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 548 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3780 --field-trial-handle=1108,i,4399882357578523065,9918136019549432450,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 896 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | wmic path Win32_UserAccount where name="admin" get sid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
17 337
Read events
17 202
Write events
122
Delete events
13
Modification events
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
3
Suspicious files
24
Text files
40
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f472.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\30993018-c809-4263-a745-a987729f01fa.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17f7cd.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF180450.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
25
DNS requests
27
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 6.01 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 10.0 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 10.8 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 9.98 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 20.9 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 30.1 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 14.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 172 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 333 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3672 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3228 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
3228 | chrome.exe | 151.80.29.83:443 | gofile.io | OVH SAS | FR | unknown |
3228 | chrome.exe | 51.38.43.18:443 | gofile.io | OVH SAS | FR | unknown |
3228 | chrome.exe | 51.75.242.210:443 | s.gofile.io | OVH SAS | FR | unknown |
3228 | chrome.exe | 142.250.74.202:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 31.14.70.243:443 | store2.gofile.io | MOJI SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
gofile.io |
| whitelisted |
api.gofile.io |
| unknown |
s.gofile.io |
| unknown |
content-autofill.googleapis.com |
| whitelisted |
store2.gofile.io |
| unknown |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3228 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
3228 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
3228 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
3228 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
3228 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
3228 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
3228 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
3228 | chrome.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
3228 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
3228 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |