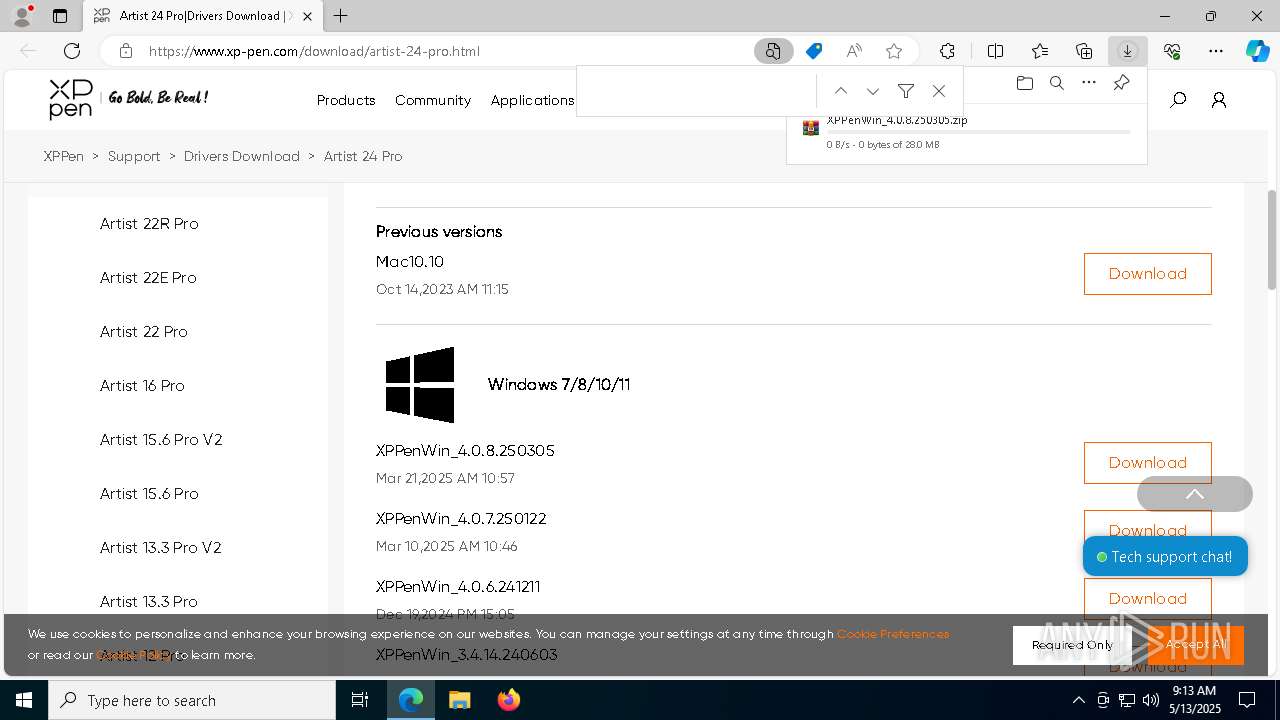
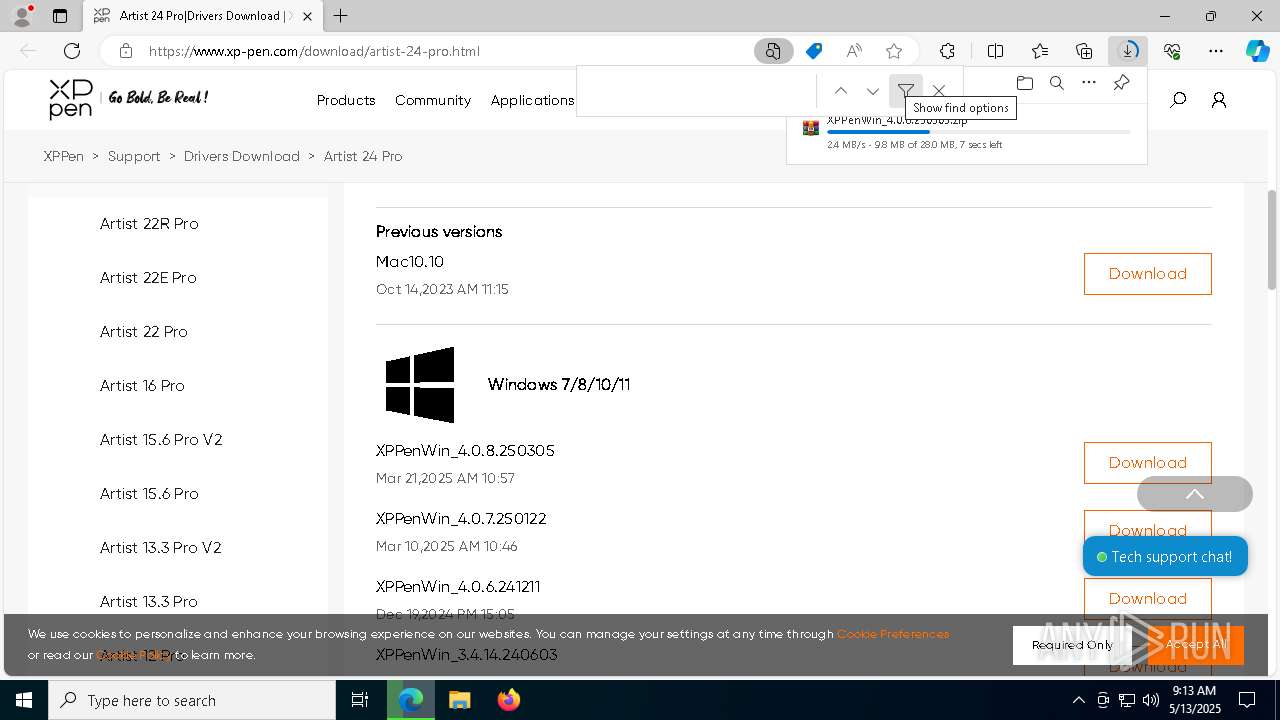
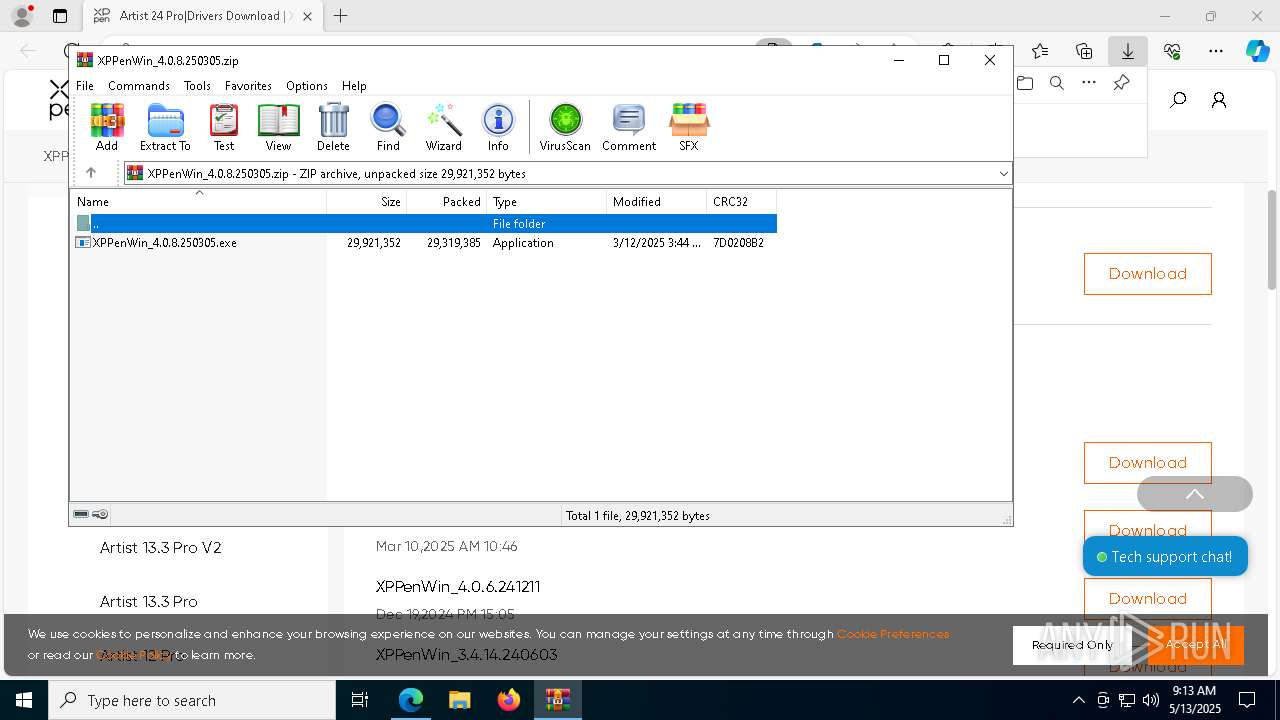
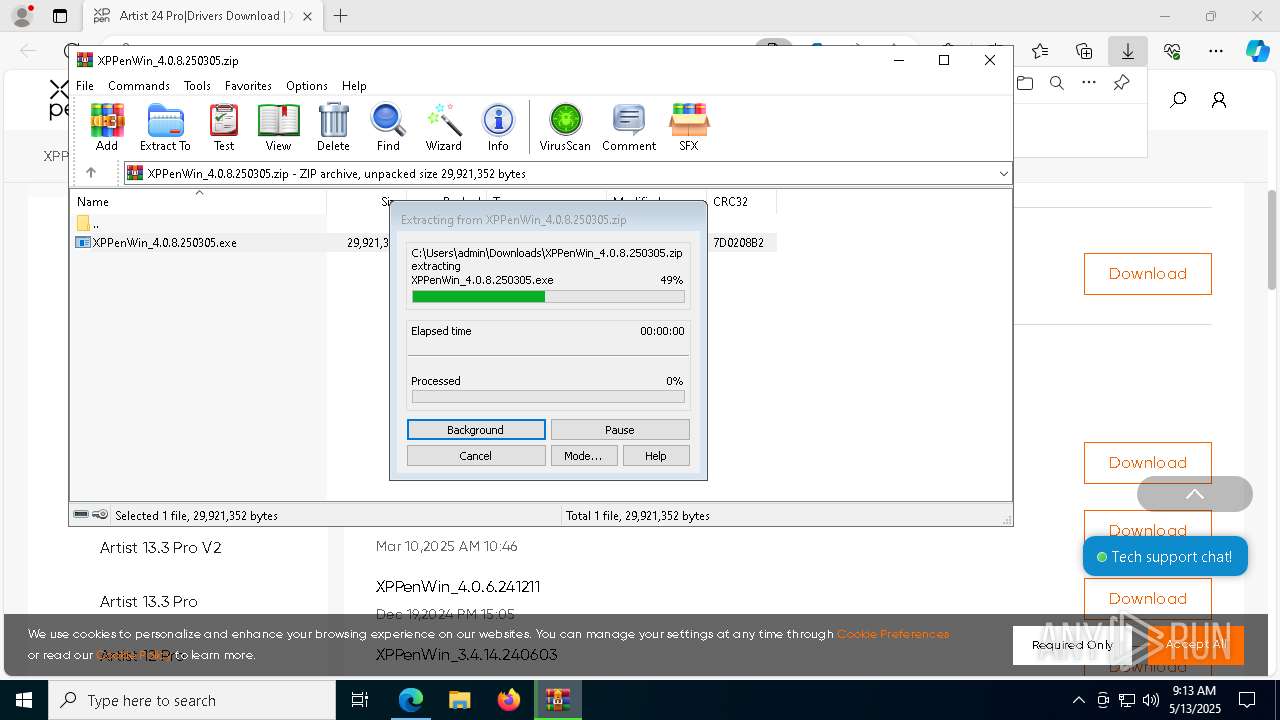
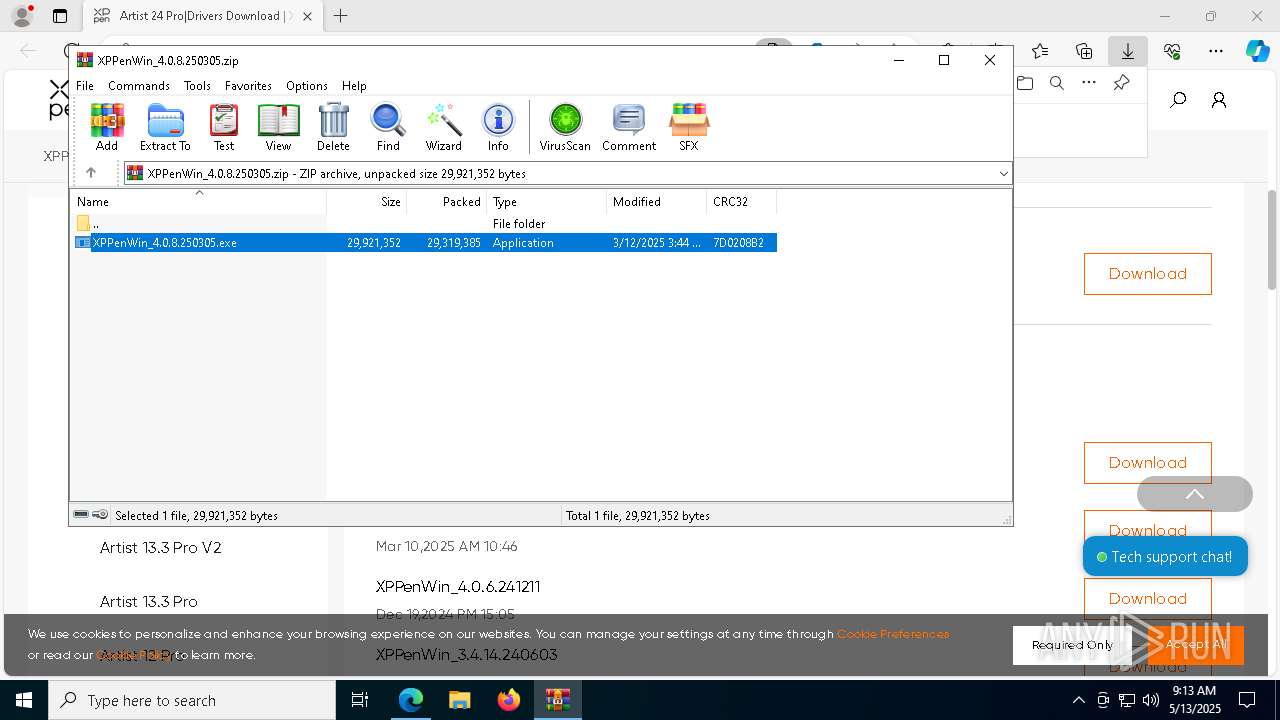
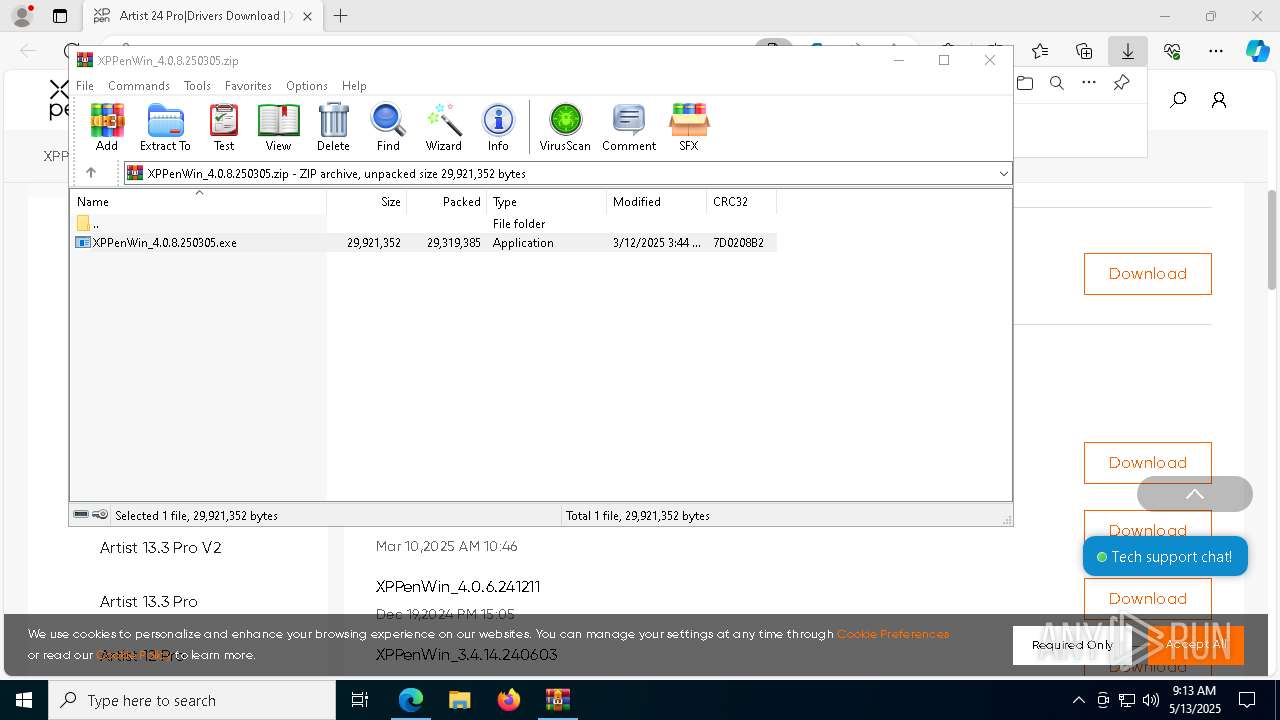
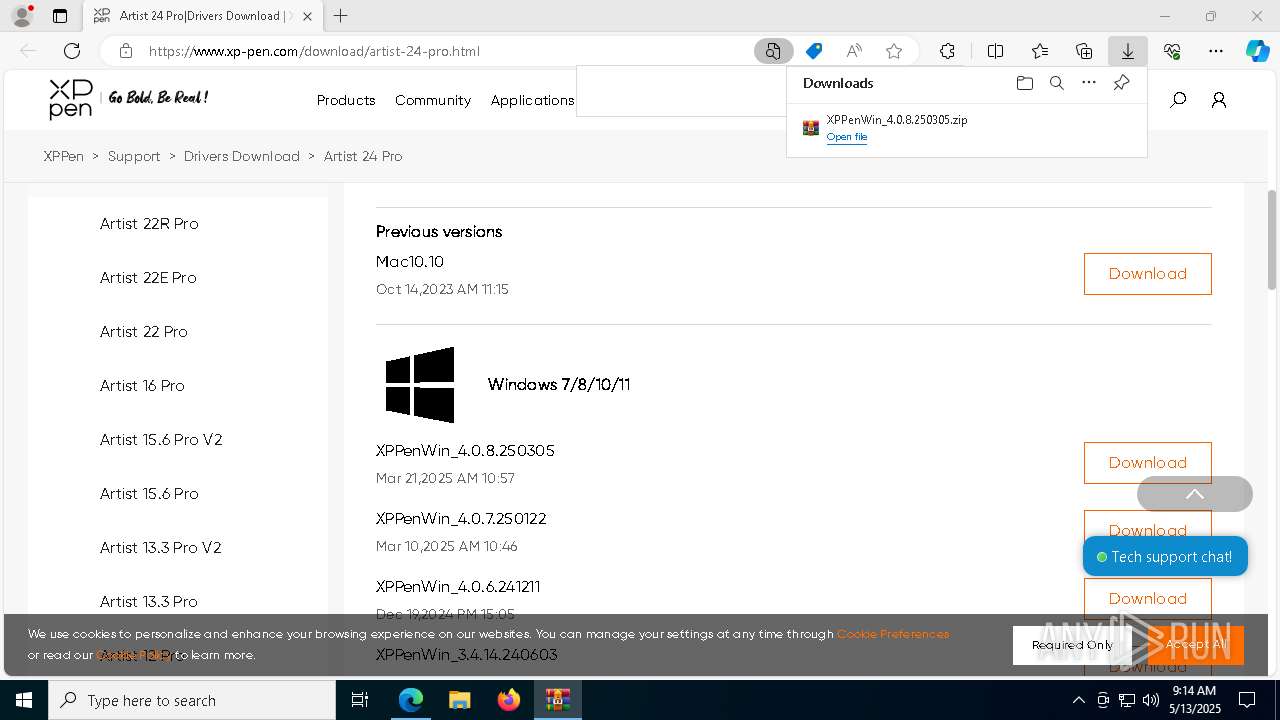
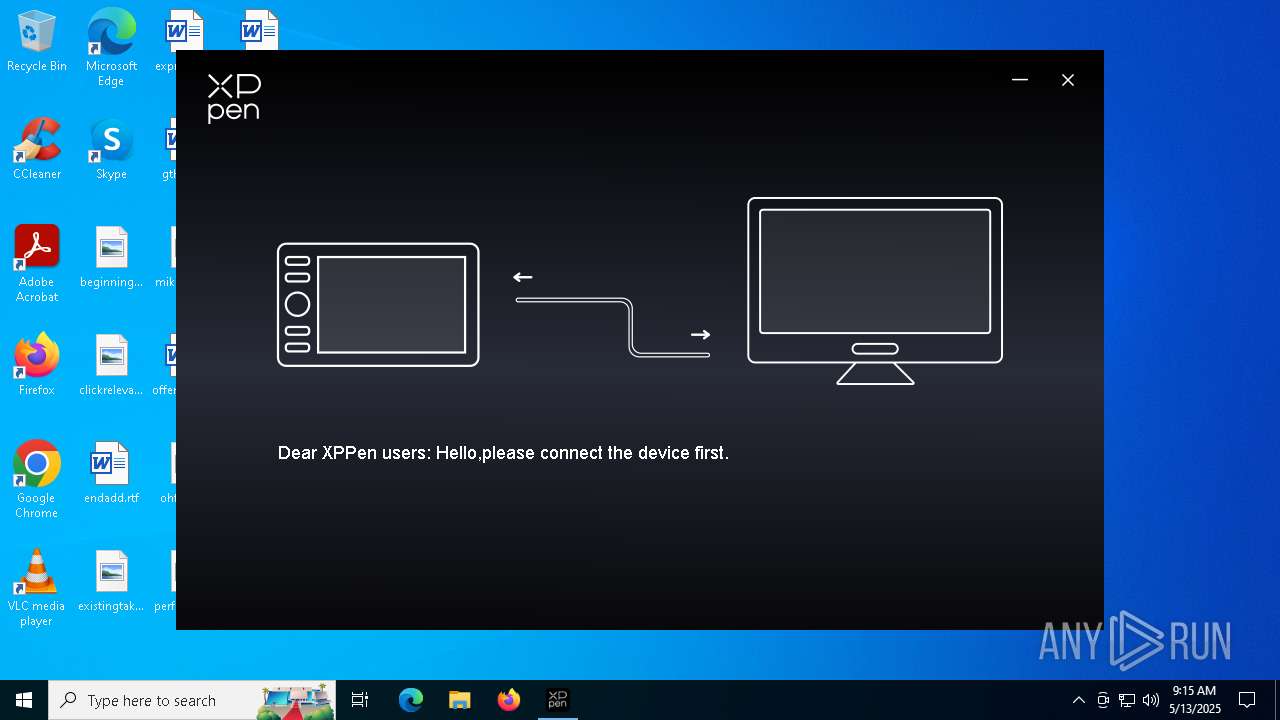
| URL: | https://www.xp-pen.com/download/artist-24-pro.html |
| Full analysis: | https://app.any.run/tasks/b18fbbcd-a024-4f4a-8699-5427241f2fc7 |
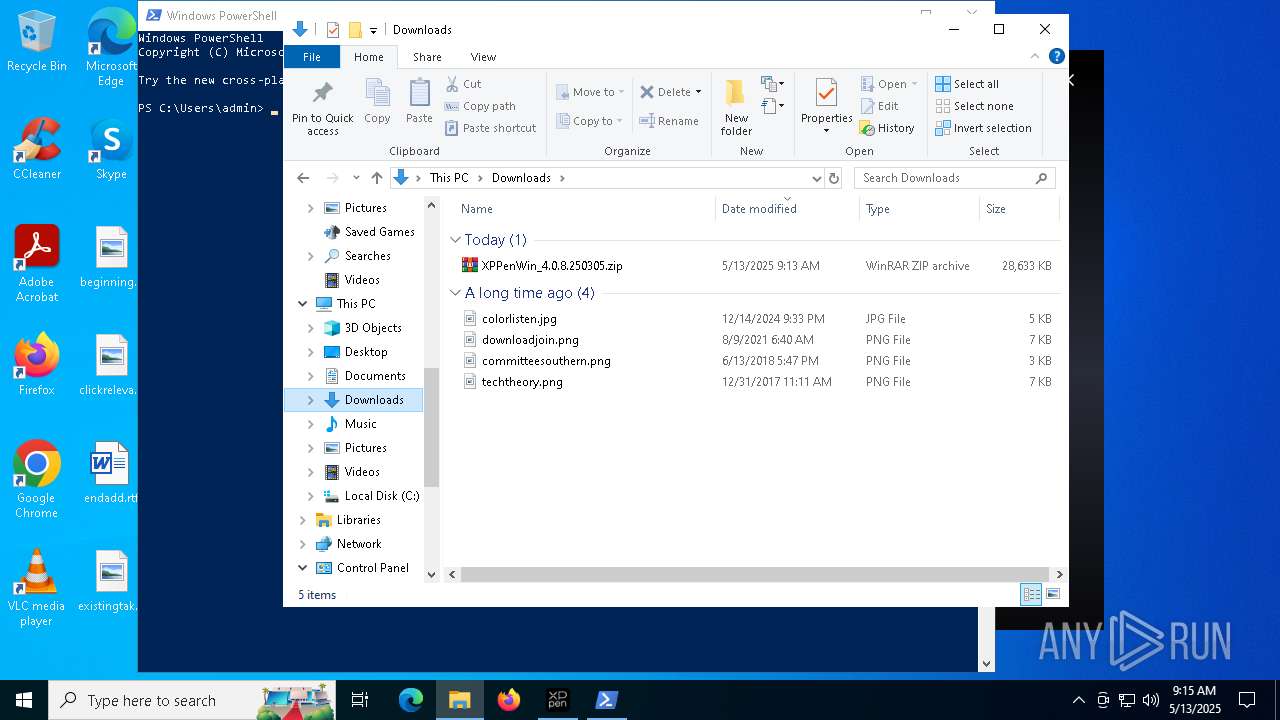
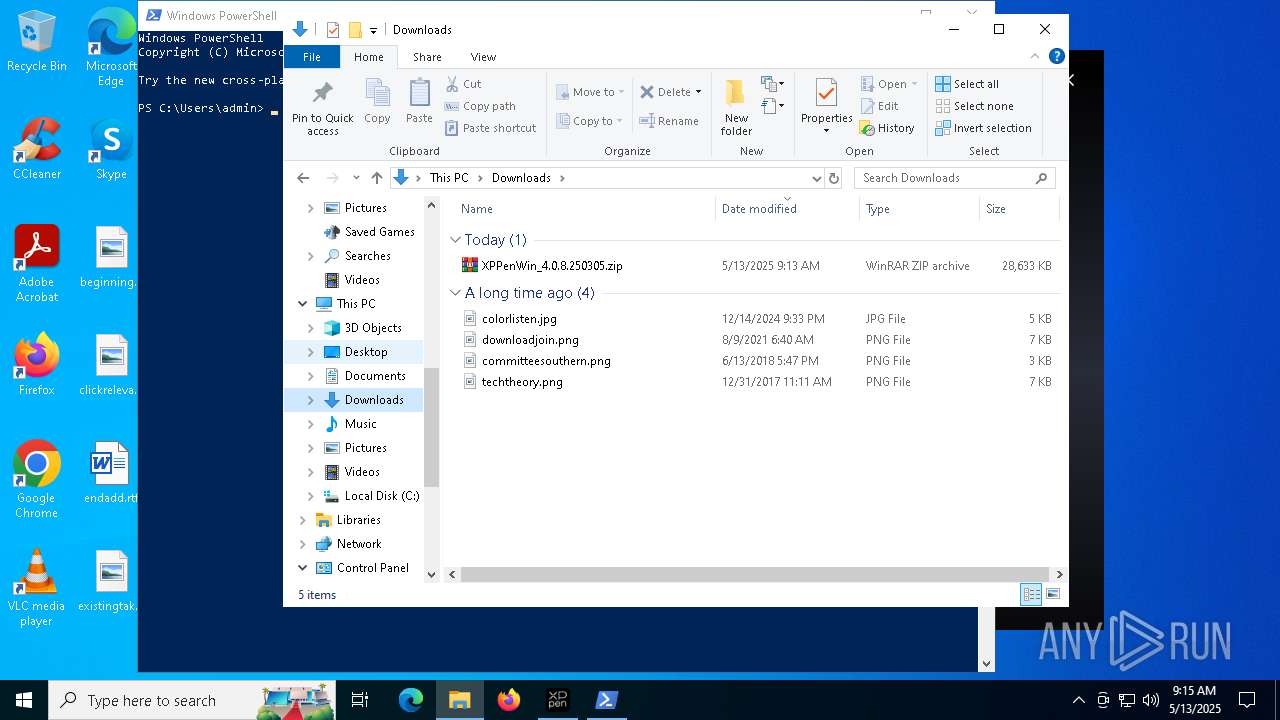
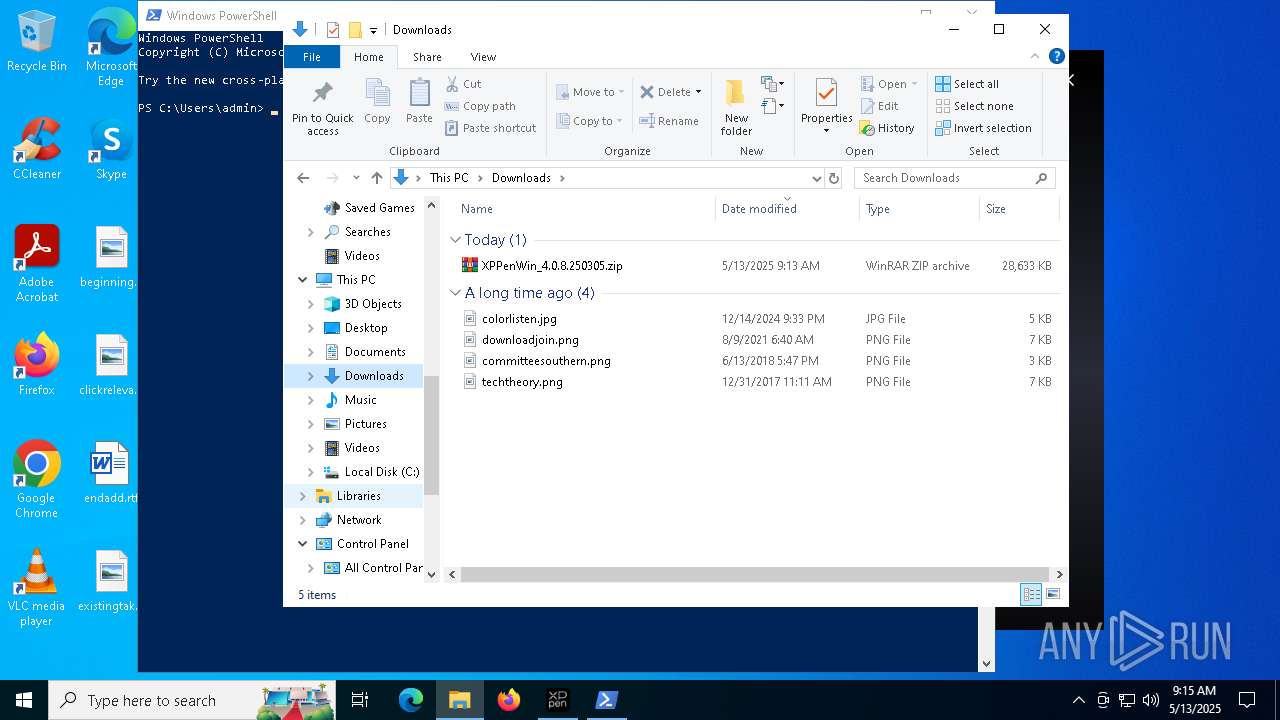
| Verdict: | Malicious activity |
| Analysis date: | May 13, 2025, 09:12:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
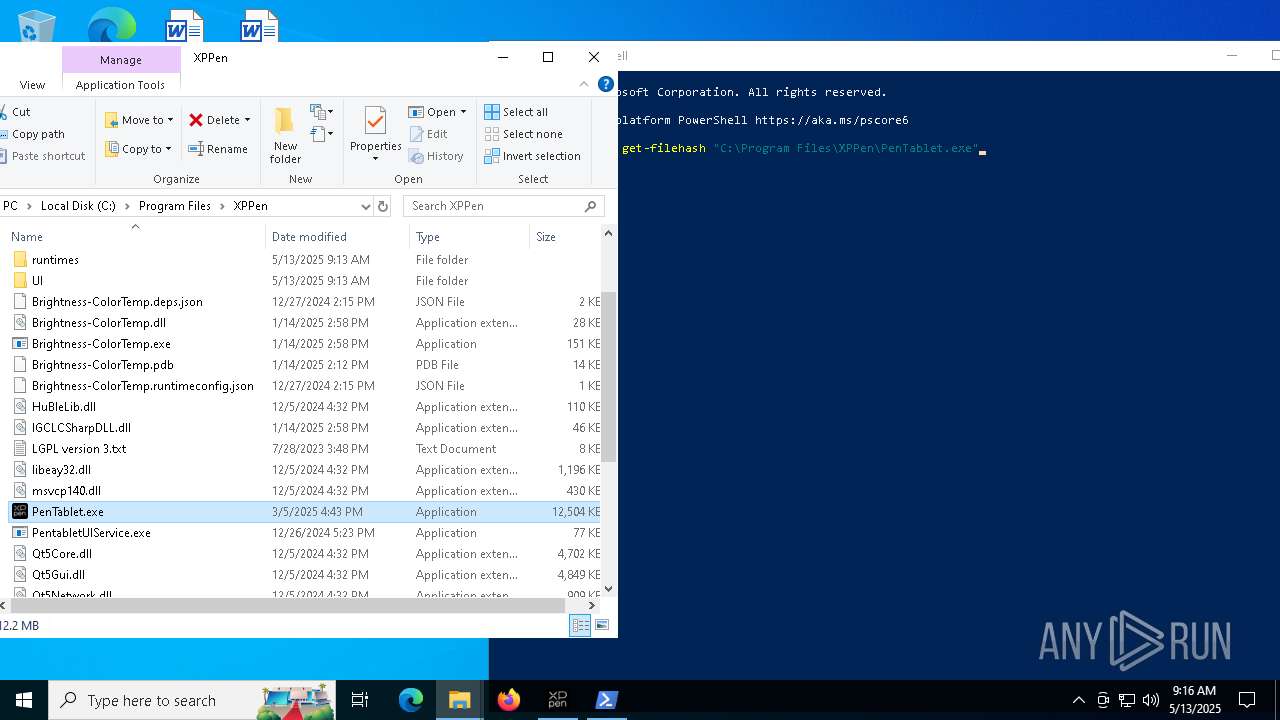
| MD5: | A1EADEB01115F56FF070332DC41C780D |
| SHA1: | 339FC67ADF1D338AEFD6364EF85EA7DF4AEA6500 |
| SHA256: | 445F488A5553C5DF8C5EE8B532853E27C166662900A1006C5FB2416B2799871F |
| SSDEEP: | 3:N8DSL4SIaKL+RXYRtDIJ:2OL8B+8tDIJ |
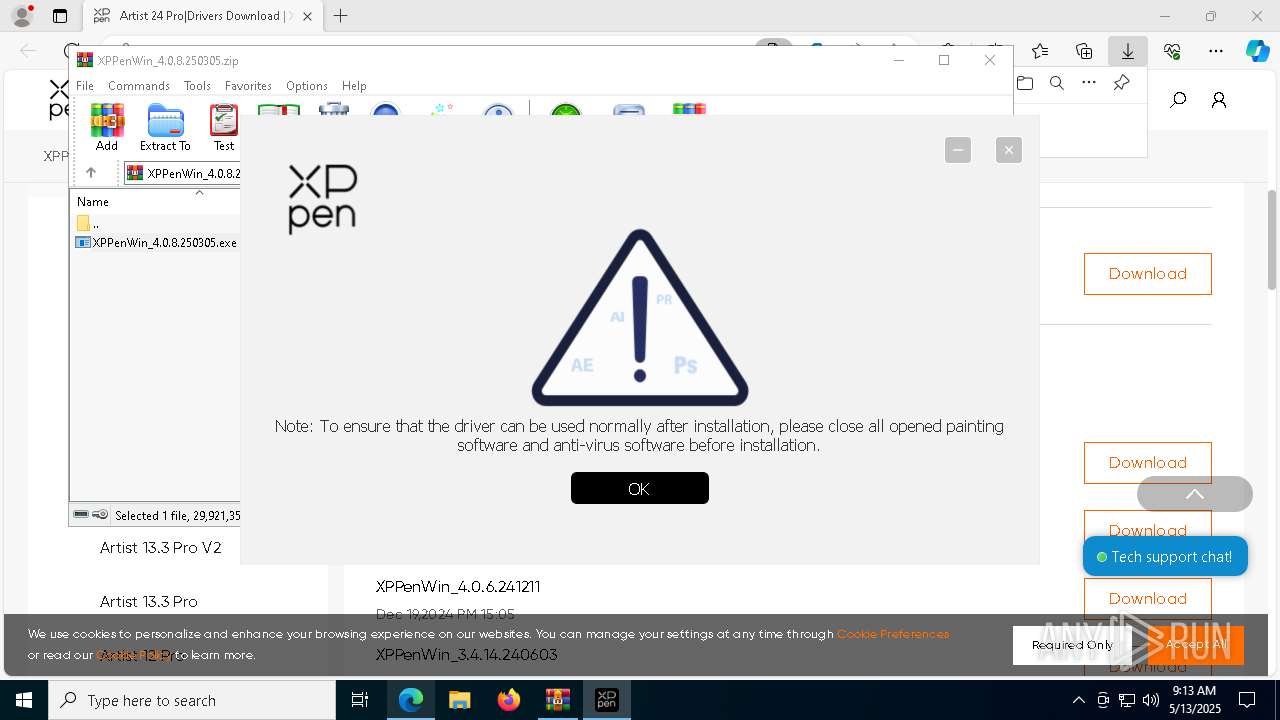
MALICIOUS
Executing a file with an untrusted certificate
- Listdlls.exe (PID: 4152)
- Listdlls64.exe (PID: 4652)
- dpinst.exe (PID: 6700)
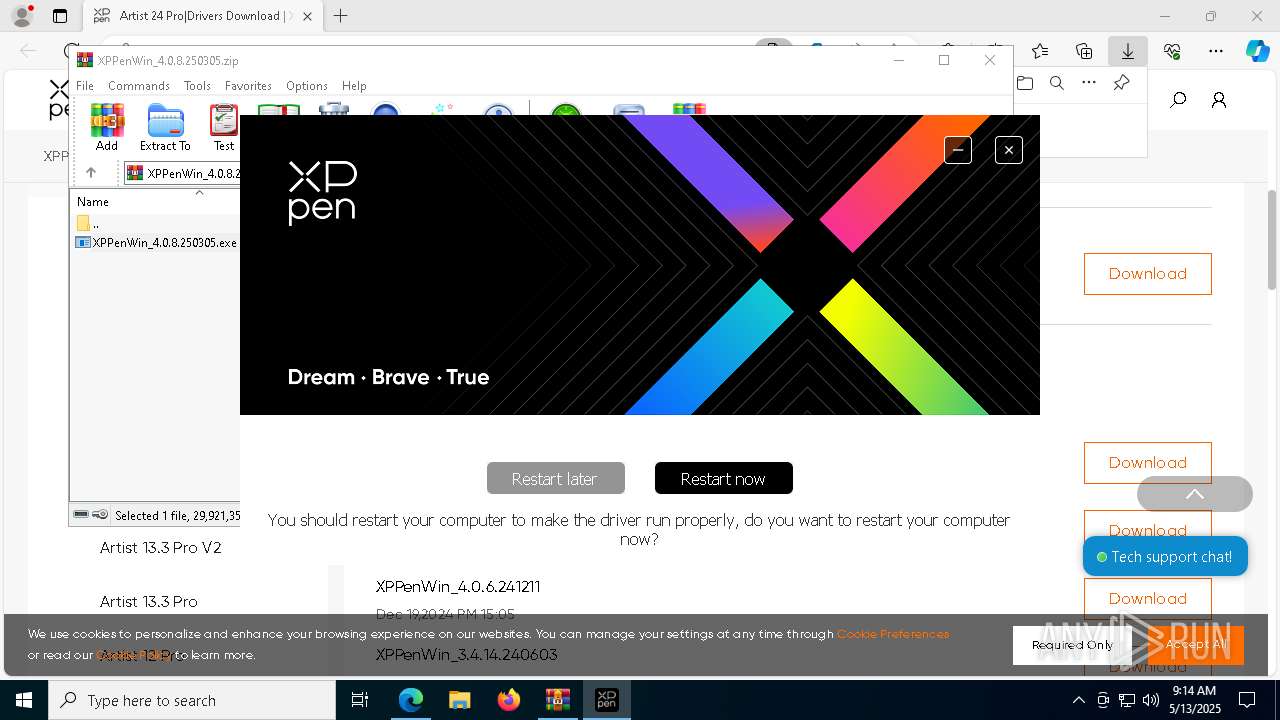
Changes the autorun value in the registry
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4728)
- XPPenWin_4.0.8.250305.tmp (PID: 5576)
- devcon.exe (PID: 1600)
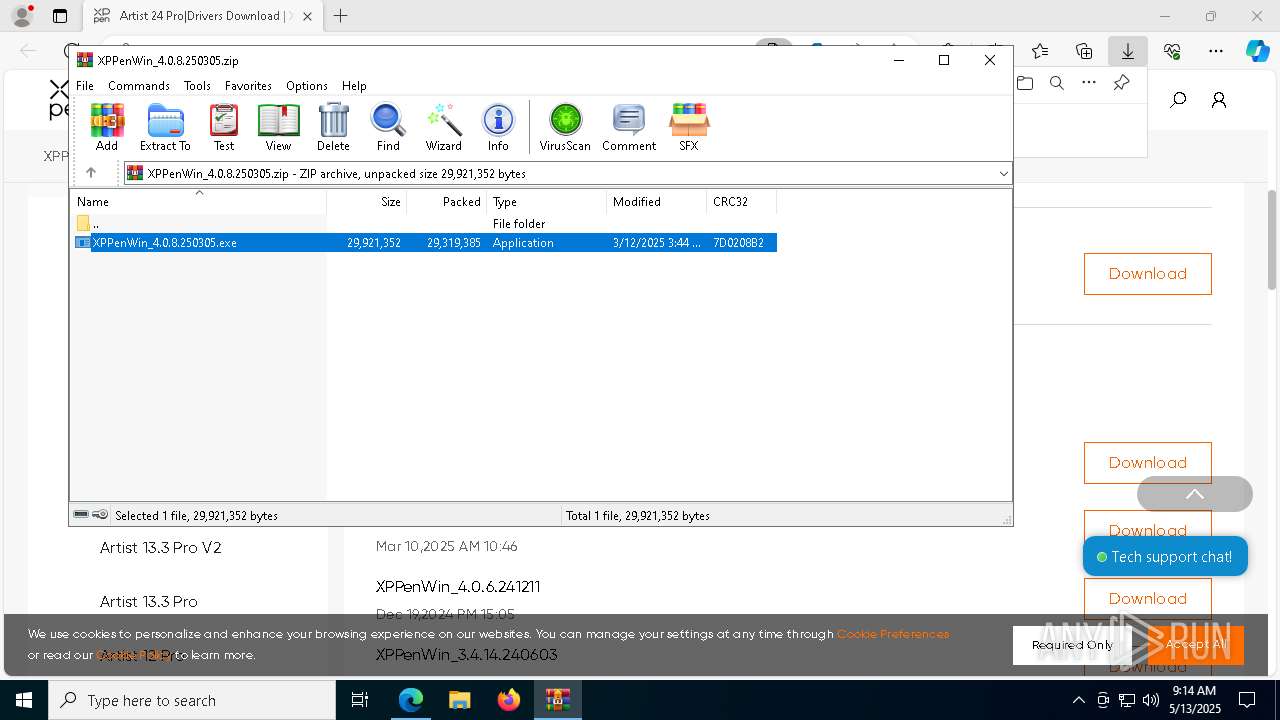
Executable content was dropped or overwritten
- XPPenWin_4.0.8.250305.exe (PID: 1300)
- XPPenWin_4.0.8.250305.exe (PID: 7832)
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
- Listdlls.exe (PID: 4152)
- devcon.exe (PID: 1600)
- drvinst.exe (PID: 8184)
- drvinst.exe (PID: 5020)
- dpinst.exe (PID: 6700)
- drvinst.exe (PID: 8132)
- drvinst.exe (PID: 1132)
Reads the Windows owner or organization settings
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
Starts CMD.EXE for commands execution
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
- cmd.exe (PID: 5936)
Executing commands from a ".bat" file
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
The executable file from the user directory is run by the CMD process
- Listdlls.exe (PID: 4152)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 5936)
Application launched itself
- cmd.exe (PID: 5936)
Process drops legitimate windows executable
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
- devcon.exe (PID: 1600)
- drvinst.exe (PID: 8184)
- dpinst.exe (PID: 6700)
- drvinst.exe (PID: 8132)
- drvinst.exe (PID: 1132)
Drops a system driver (possible attempt to evade defenses)
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
- devcon.exe (PID: 1600)
- drvinst.exe (PID: 8184)
- drvinst.exe (PID: 8132)
- dpinst.exe (PID: 6700)
- drvinst.exe (PID: 1132)
- drvinst.exe (PID: 5020)
Creates files in the driver directory
- drvinst.exe (PID: 8184)
- drvinst.exe (PID: 5020)
- drvinst.exe (PID: 8132)
- drvinst.exe (PID: 1132)
Creates or modifies Windows services
- drvinst.exe (PID: 5020)
- drvinst.exe (PID: 1132)
The process drops C-runtime libraries
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
There is functionality for taking screenshot (YARA)
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 2192)
INFO
Application launched itself
- msedge.exe (PID: 7084)
Reads Environment values
- identity_helper.exe (PID: 7832)
Checks supported languages
- identity_helper.exe (PID: 7832)
- XPPenWin_4.0.8.250305.exe (PID: 1300)
- XPPenWin_4.0.8.250305.tmp (PID: 5576)
- XPPenWin_4.0.8.250305.exe (PID: 7832)
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
- Listdlls.exe (PID: 4152)
- Listdlls64.exe (PID: 4652)
- devcon.exe (PID: 1600)
- drvinst.exe (PID: 8184)
- drvinst.exe (PID: 5020)
- drvinst.exe (PID: 8132)
- dpinst.exe (PID: 6700)
- drvinst.exe (PID: 1132)
Reads the computer name
- identity_helper.exe (PID: 7832)
- XPPenWin_4.0.8.250305.tmp (PID: 5576)
- XPPenWin_4.0.8.250305.exe (PID: 7832)
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
- Listdlls64.exe (PID: 4652)
- devcon.exe (PID: 1600)
- drvinst.exe (PID: 8184)
- drvinst.exe (PID: 5020)
- dpinst.exe (PID: 6700)
- drvinst.exe (PID: 1132)
- drvinst.exe (PID: 8132)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4728)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7084)
Create files in a temporary directory
- XPPenWin_4.0.8.250305.exe (PID: 1300)
- XPPenWin_4.0.8.250305.exe (PID: 7832)
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
- Listdlls.exe (PID: 4152)
- devcon.exe (PID: 1600)
- dpinst.exe (PID: 6700)
Process checks computer location settings
- XPPenWin_4.0.8.250305.tmp (PID: 5576)
The sample compiled with english language support
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
- Listdlls.exe (PID: 4152)
- devcon.exe (PID: 1600)
- drvinst.exe (PID: 8184)
- drvinst.exe (PID: 5020)
- dpinst.exe (PID: 6700)
- drvinst.exe (PID: 8132)
- drvinst.exe (PID: 1132)
The sample compiled with russian language support
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
Compiled with Borland Delphi (YARA)
- XPPenWin_4.0.8.250305.exe (PID: 1300)
- XPPenWin_4.0.8.250305.tmp (PID: 5576)
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
- XPPenWin_4.0.8.250305.exe (PID: 7832)
Detects InnoSetup installer (YARA)
- XPPenWin_4.0.8.250305.exe (PID: 1300)
- XPPenWin_4.0.8.250305.tmp (PID: 5576)
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
- XPPenWin_4.0.8.250305.exe (PID: 7832)
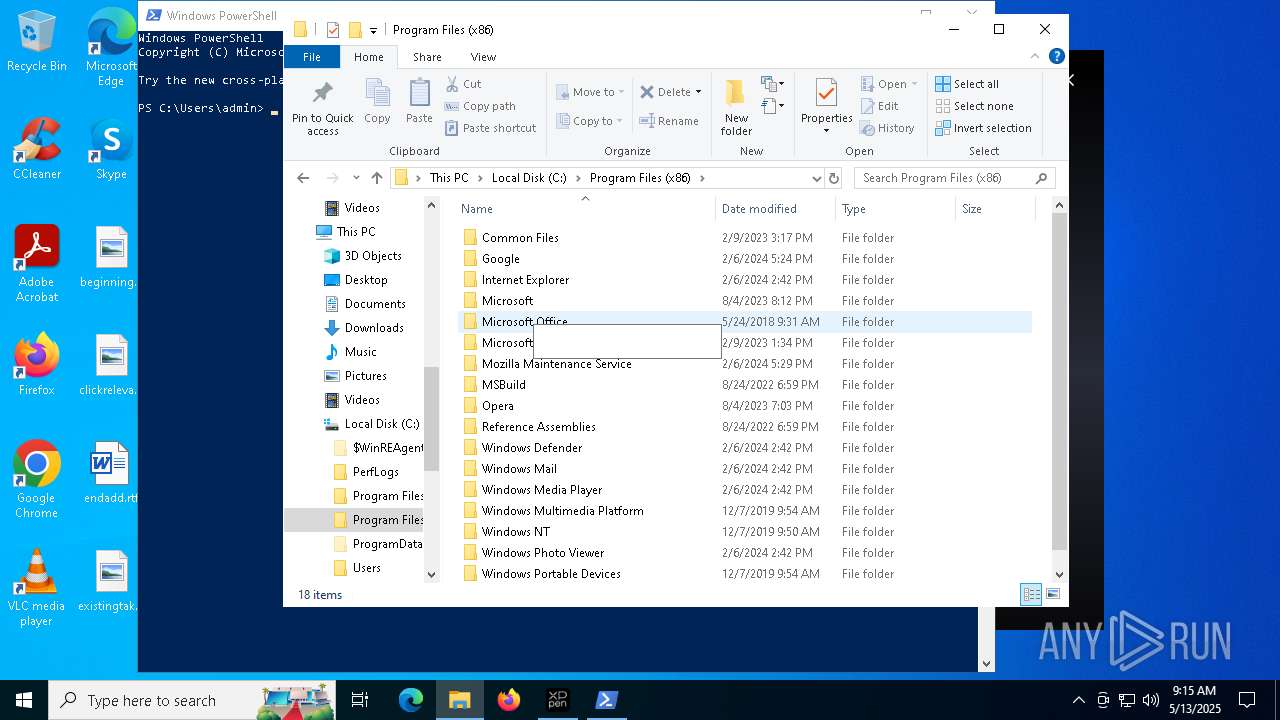
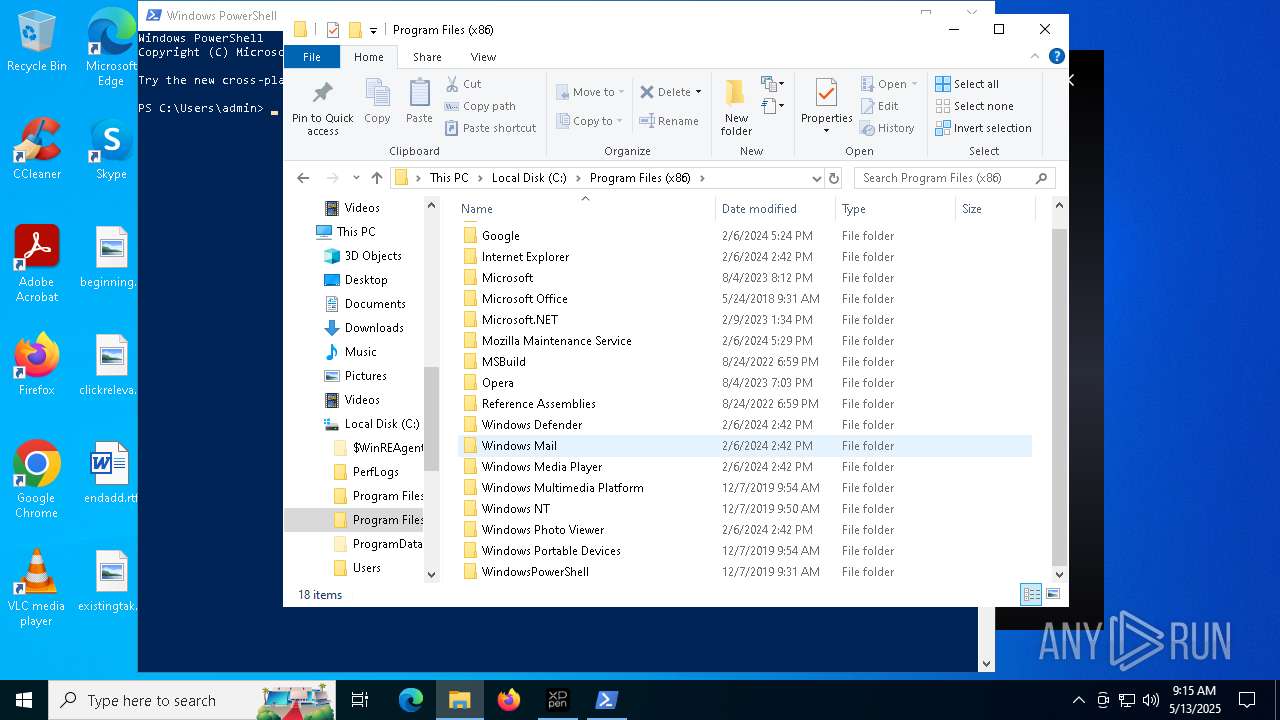
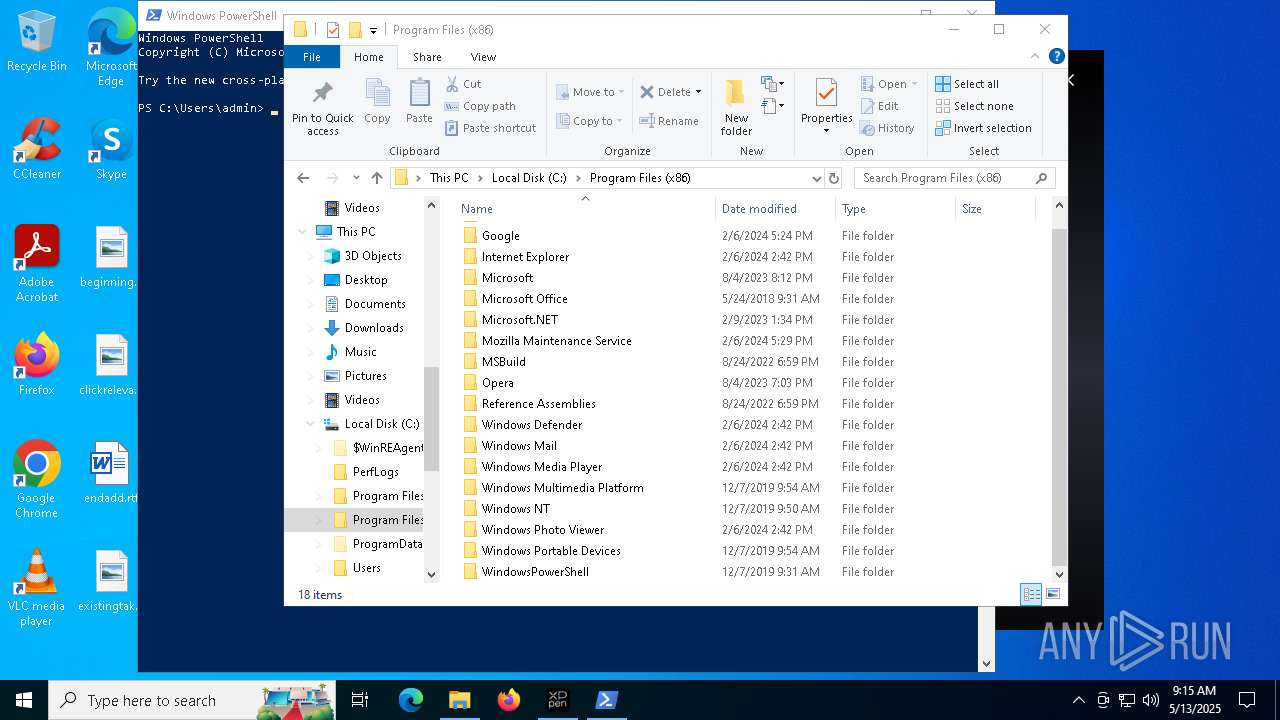
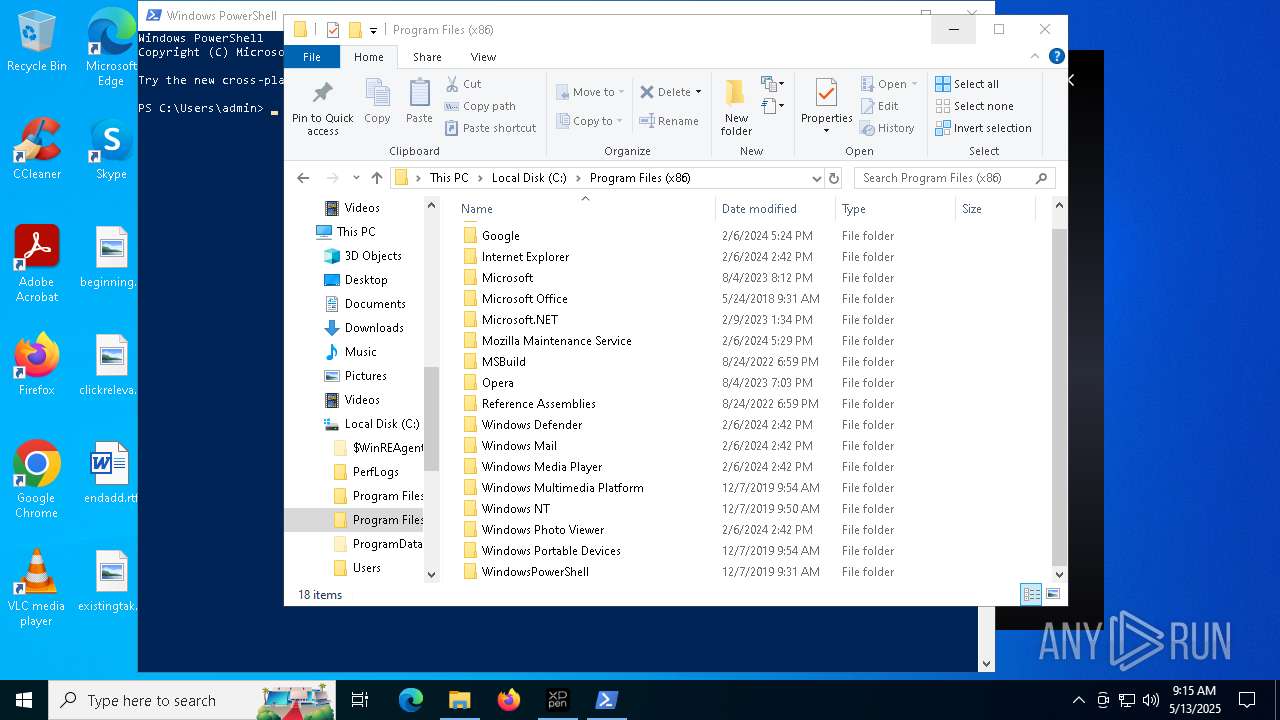
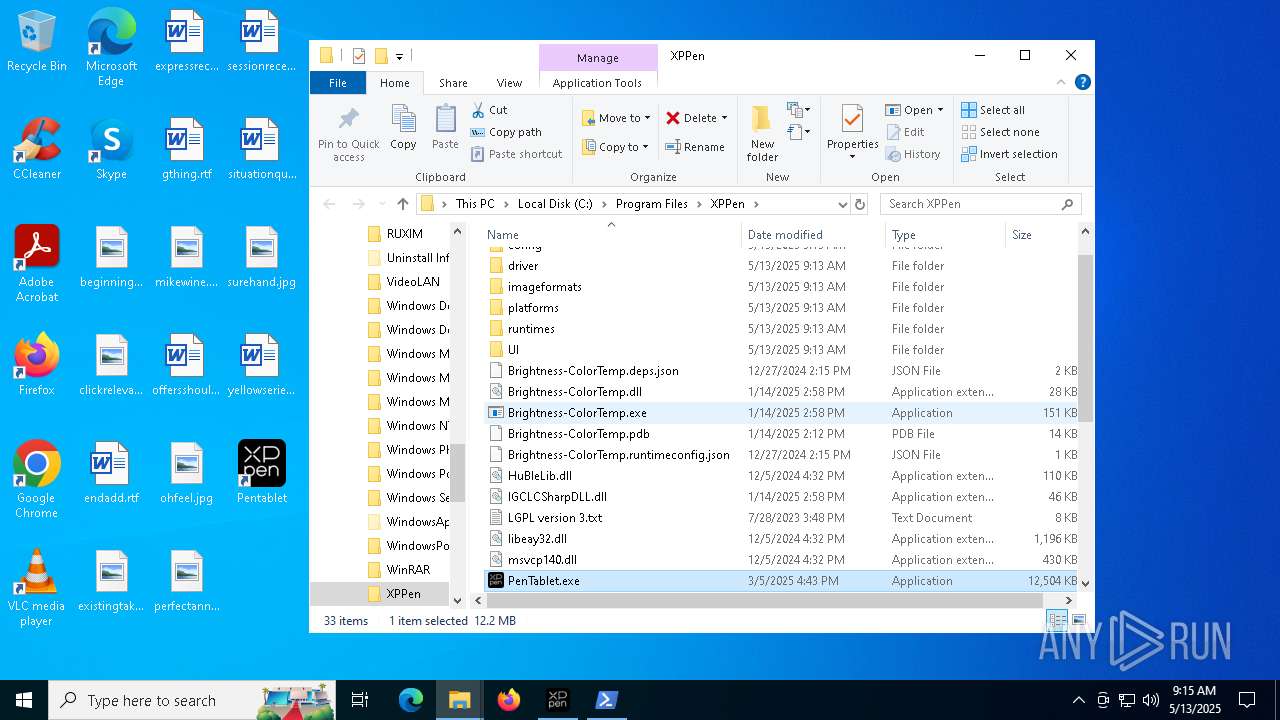
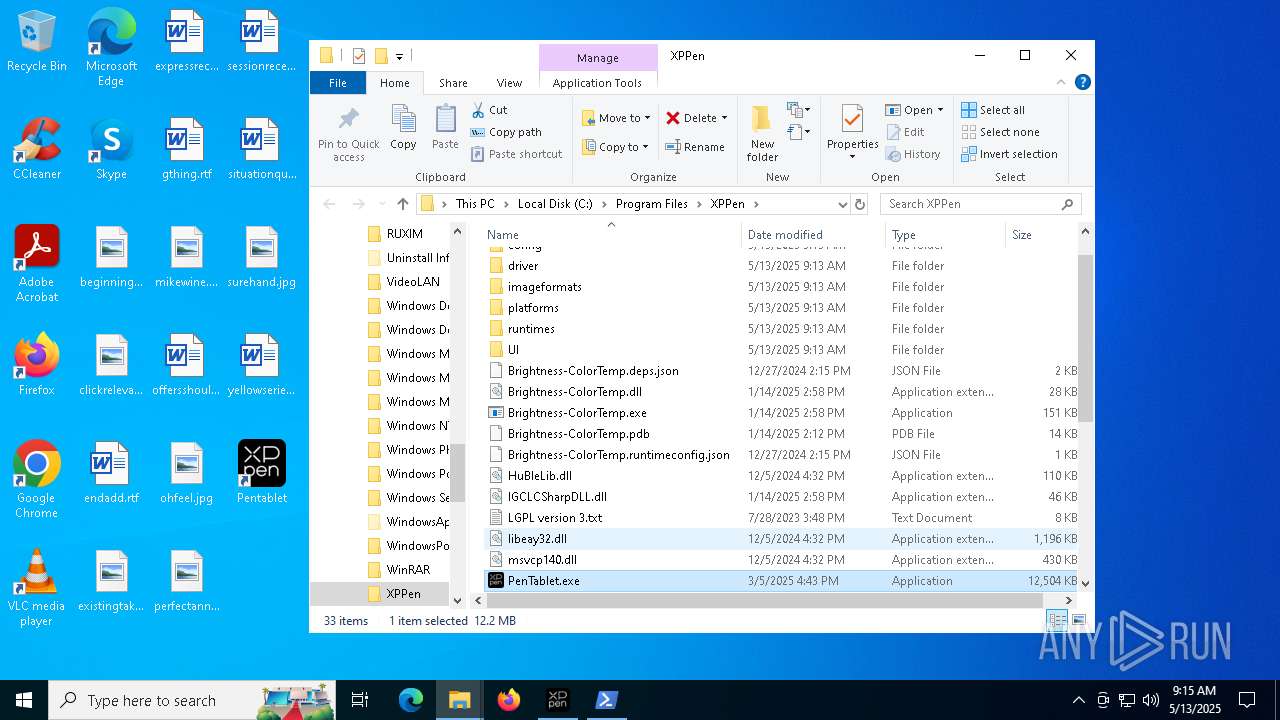
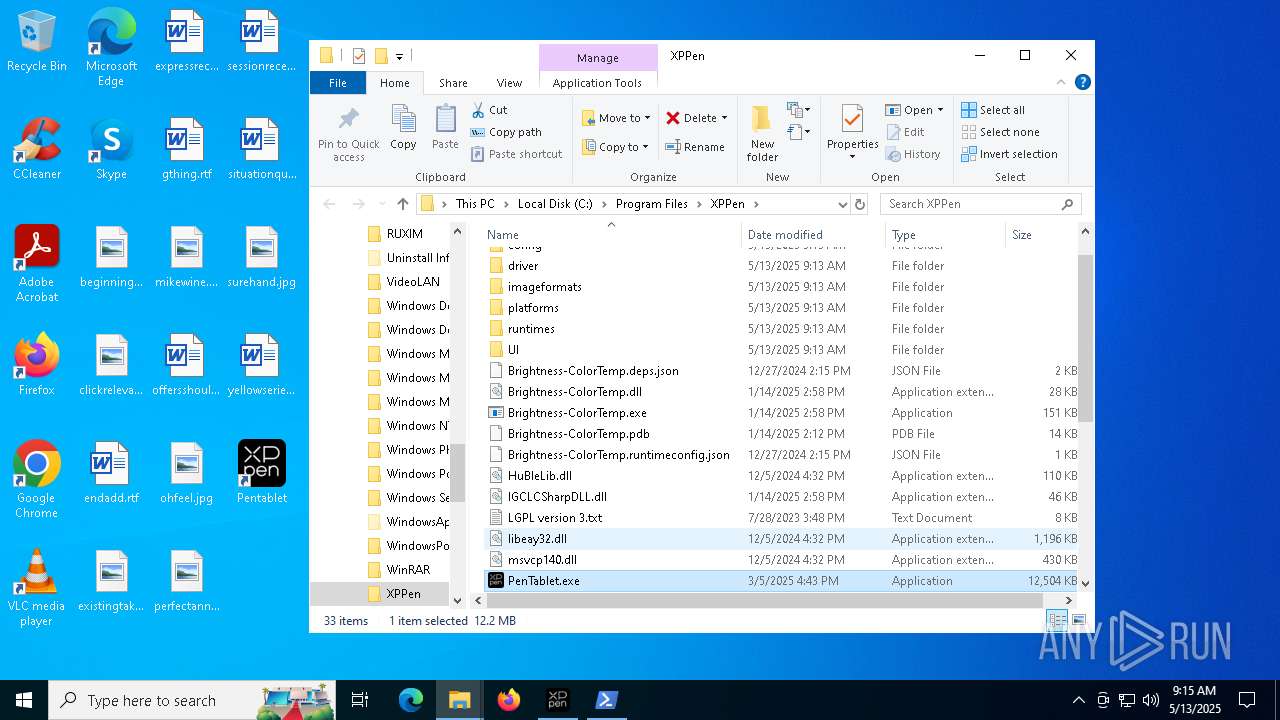
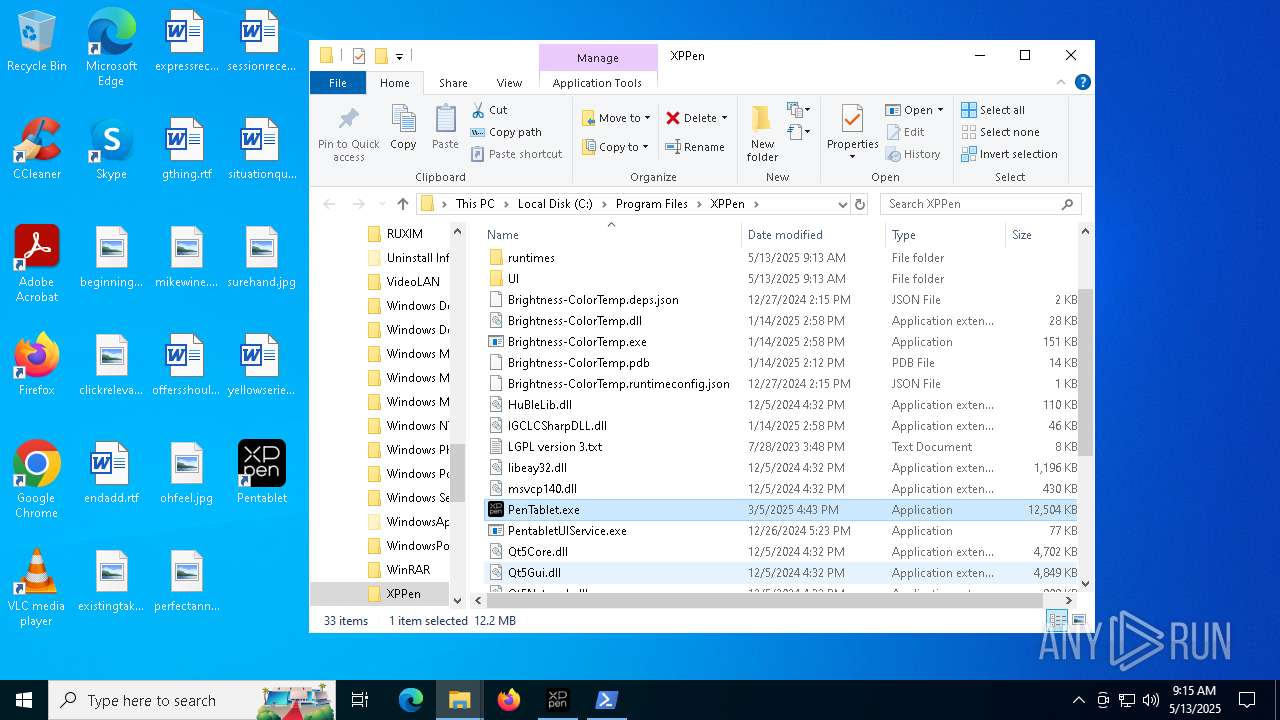
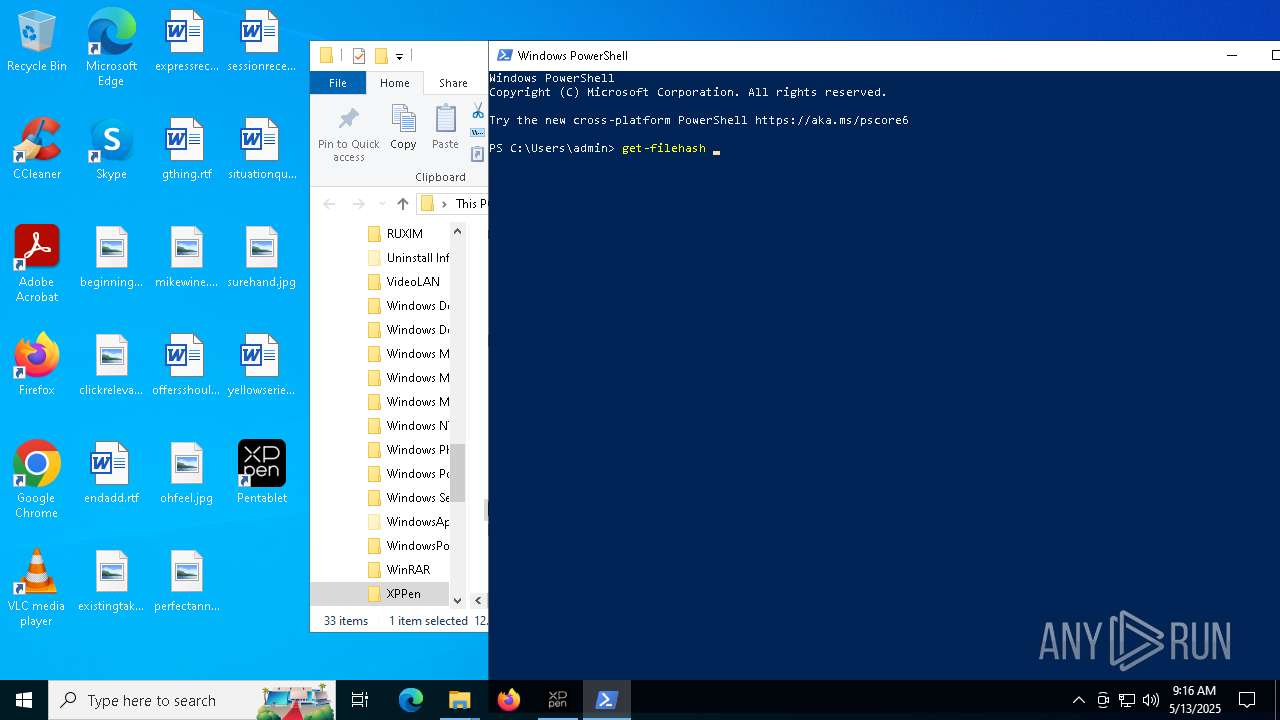
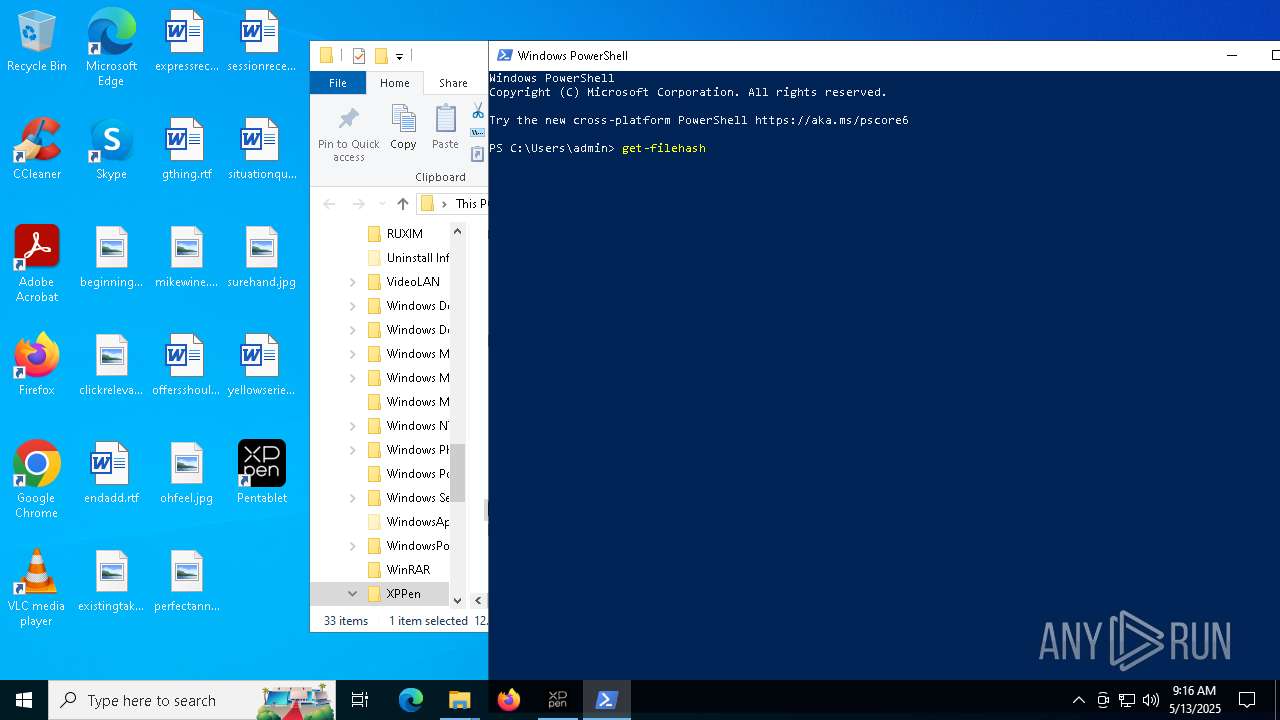
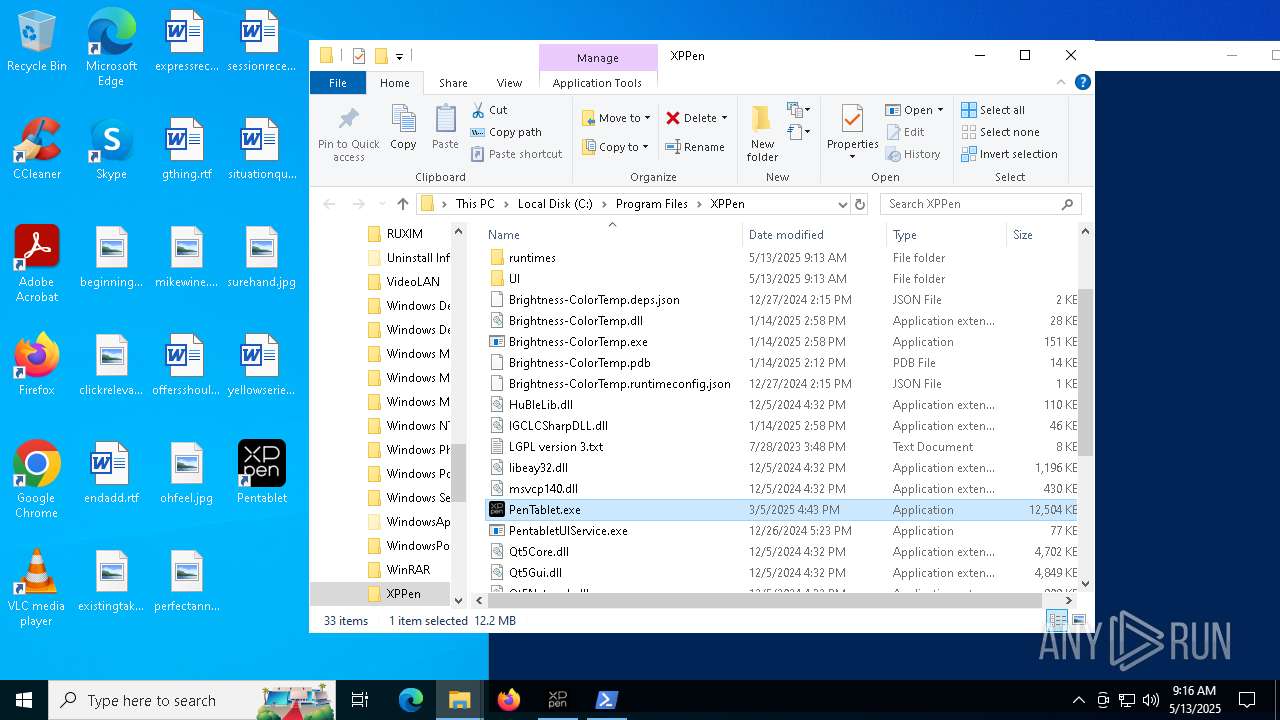
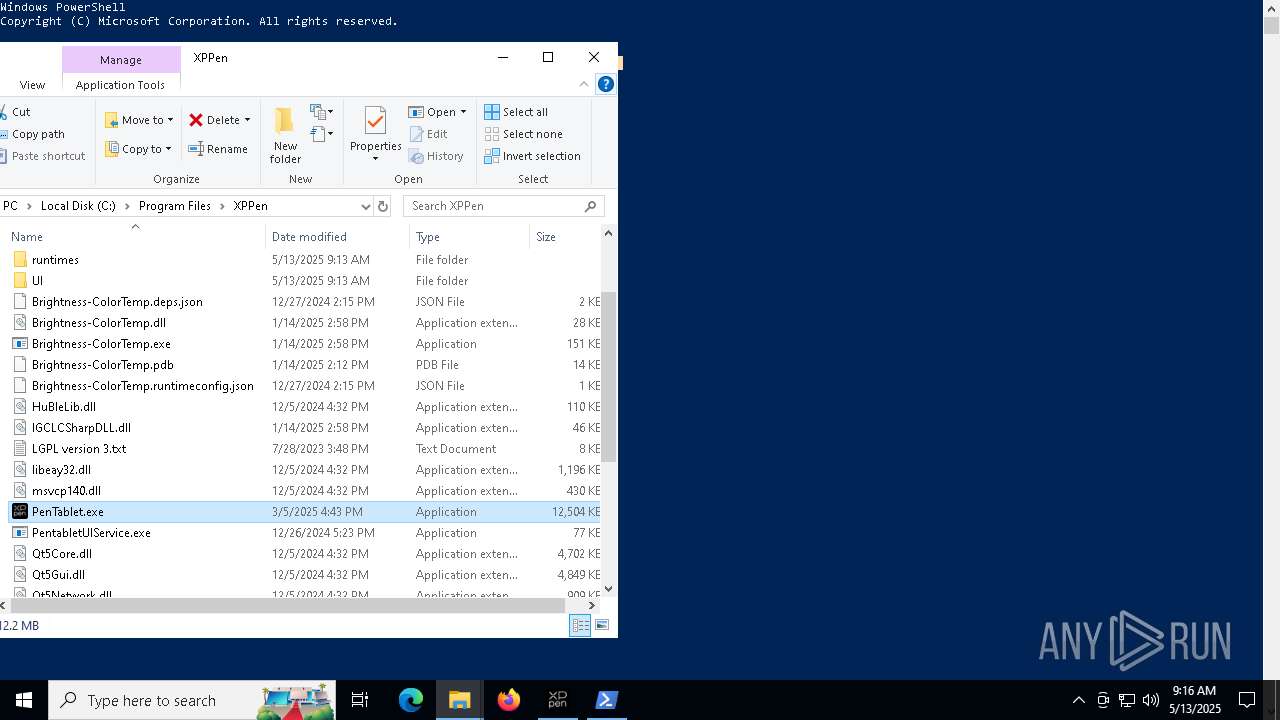
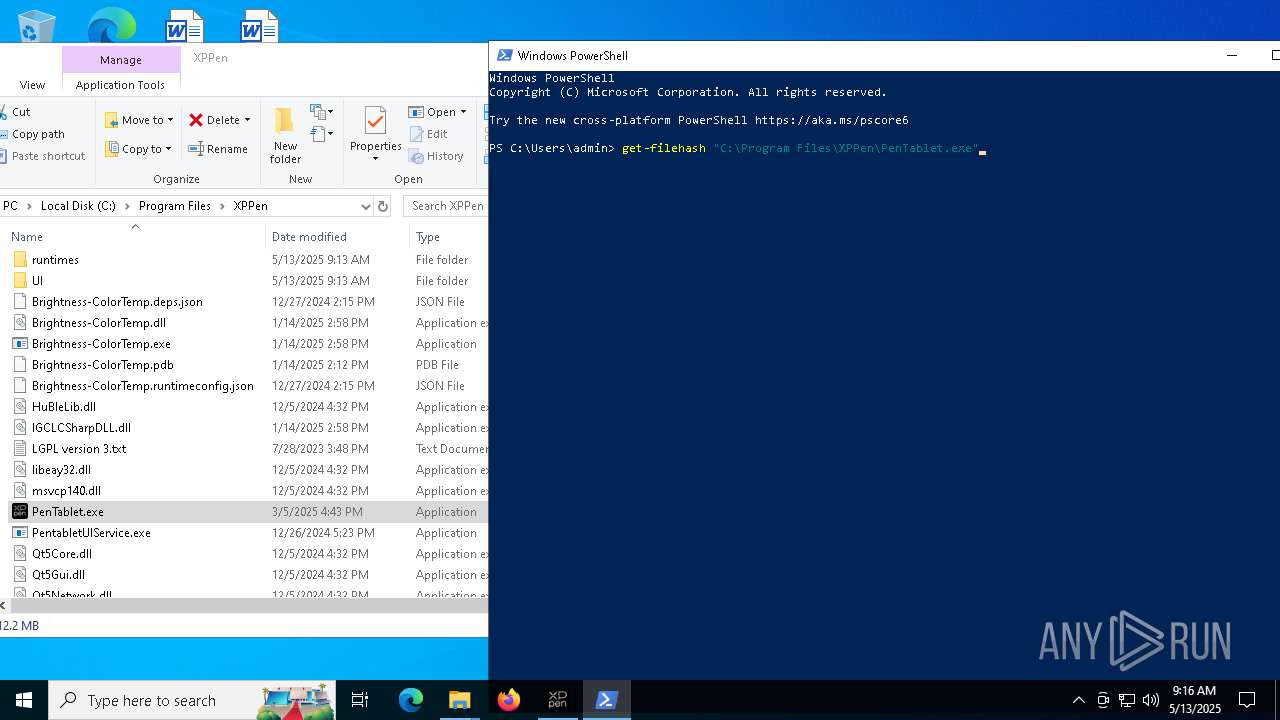
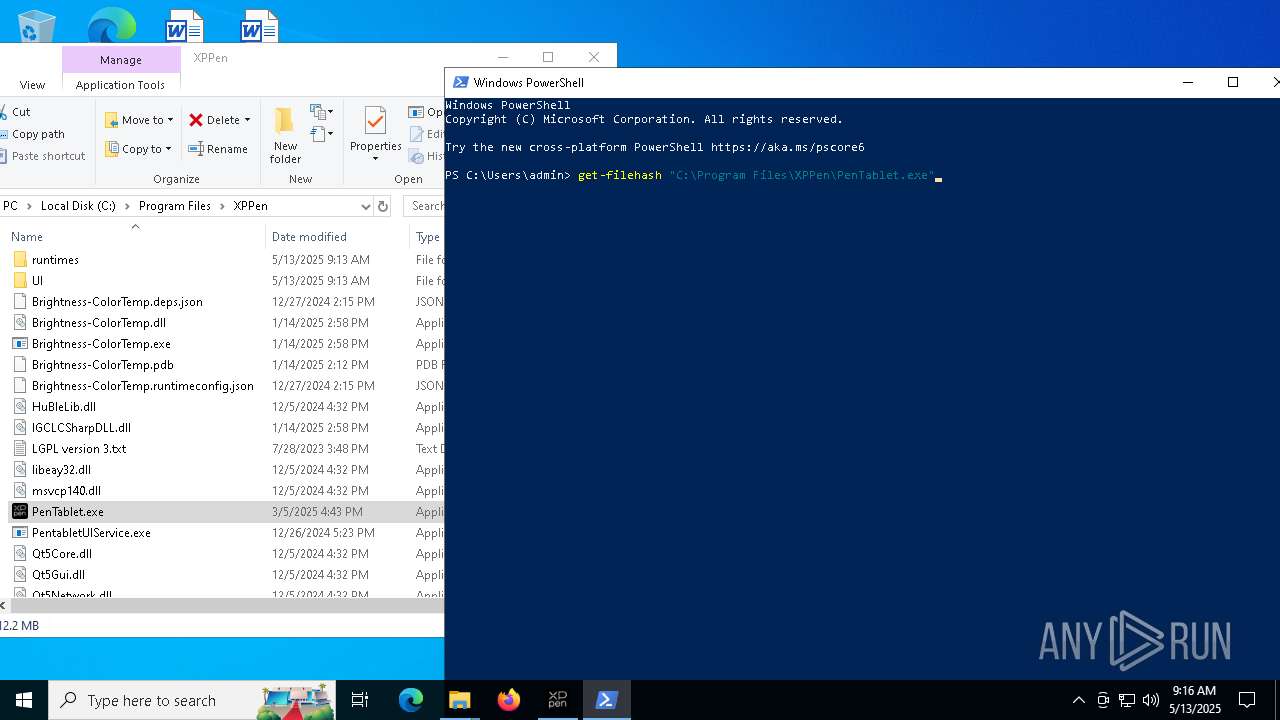
Creates files in the program directory
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
The sample compiled with chinese language support
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
The sample compiled with arabic language support
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
Reads the software policy settings
- devcon.exe (PID: 1600)
- drvinst.exe (PID: 8184)
- slui.exe (PID: 3888)
- drvinst.exe (PID: 8132)
Reads the machine GUID from the registry
- devcon.exe (PID: 1600)
- drvinst.exe (PID: 8184)
- drvinst.exe (PID: 8132)
Creates files or folders in the user directory
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
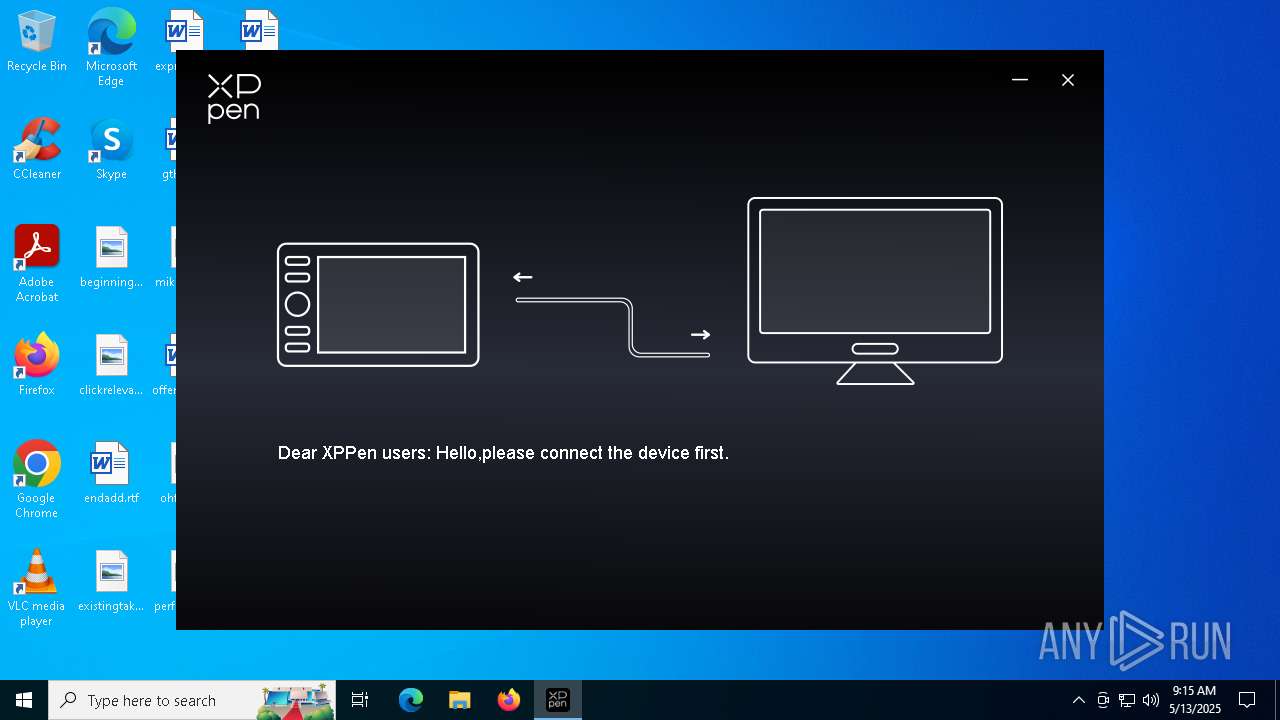
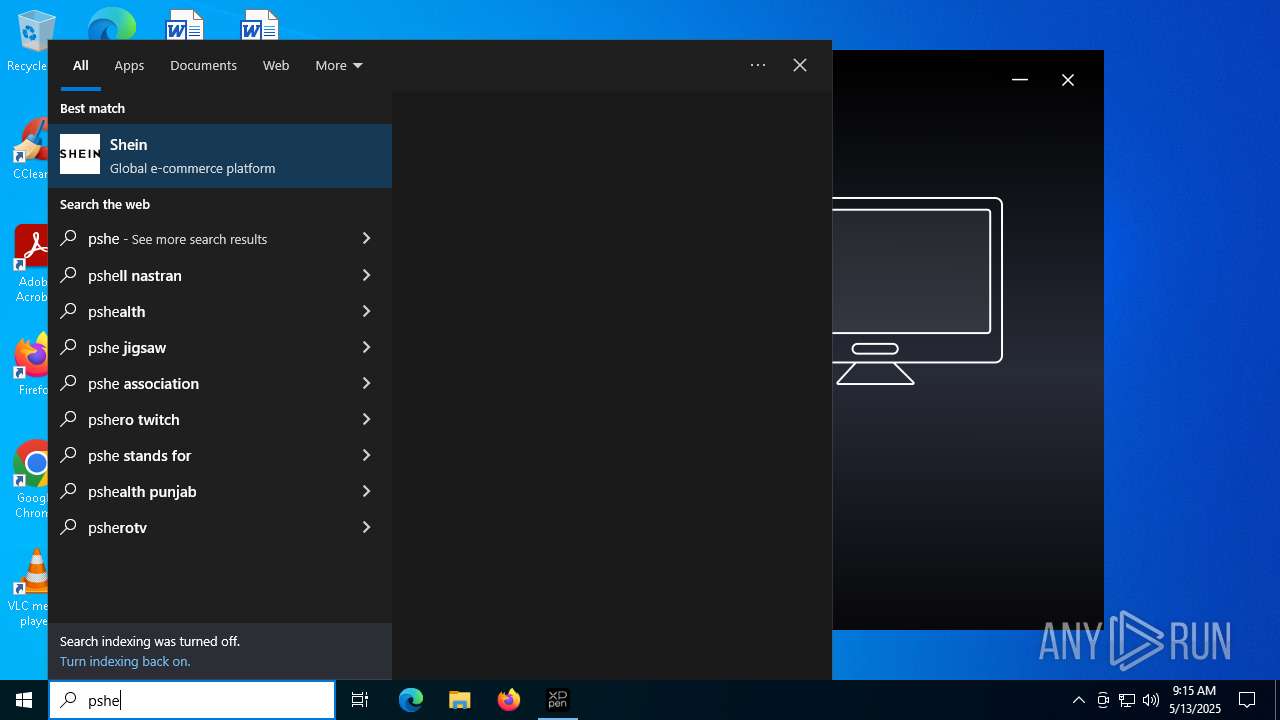
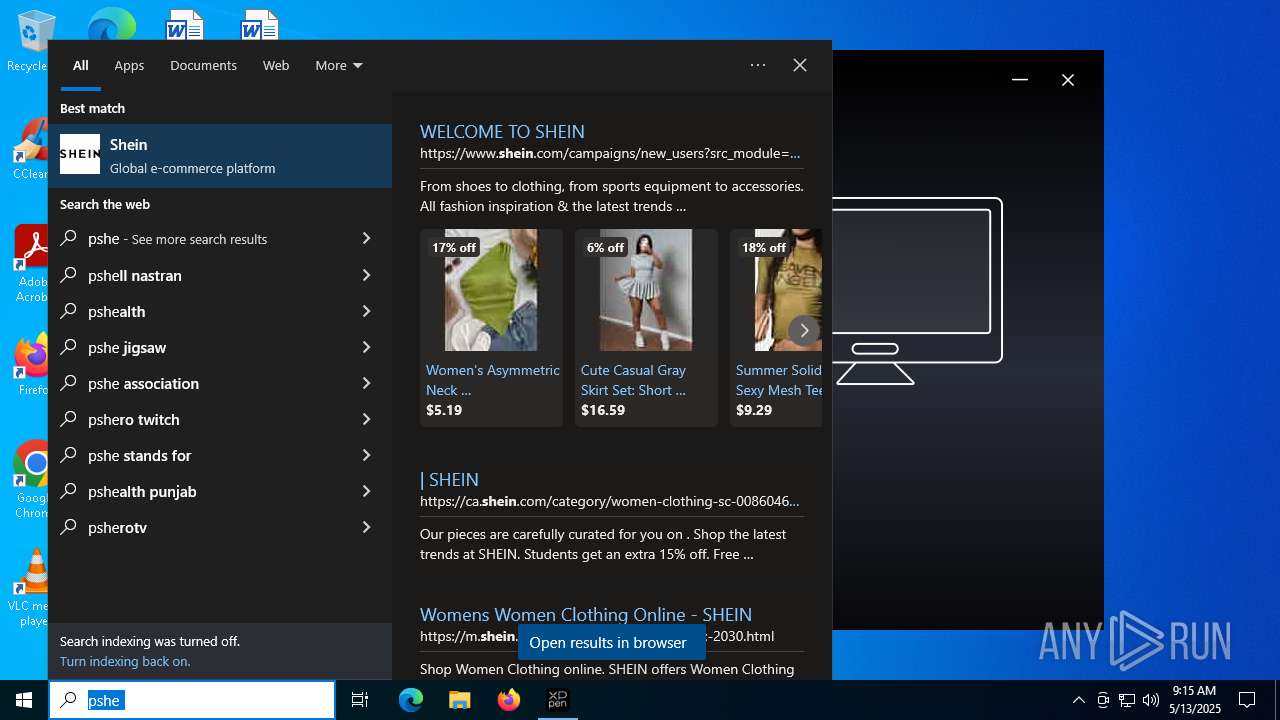
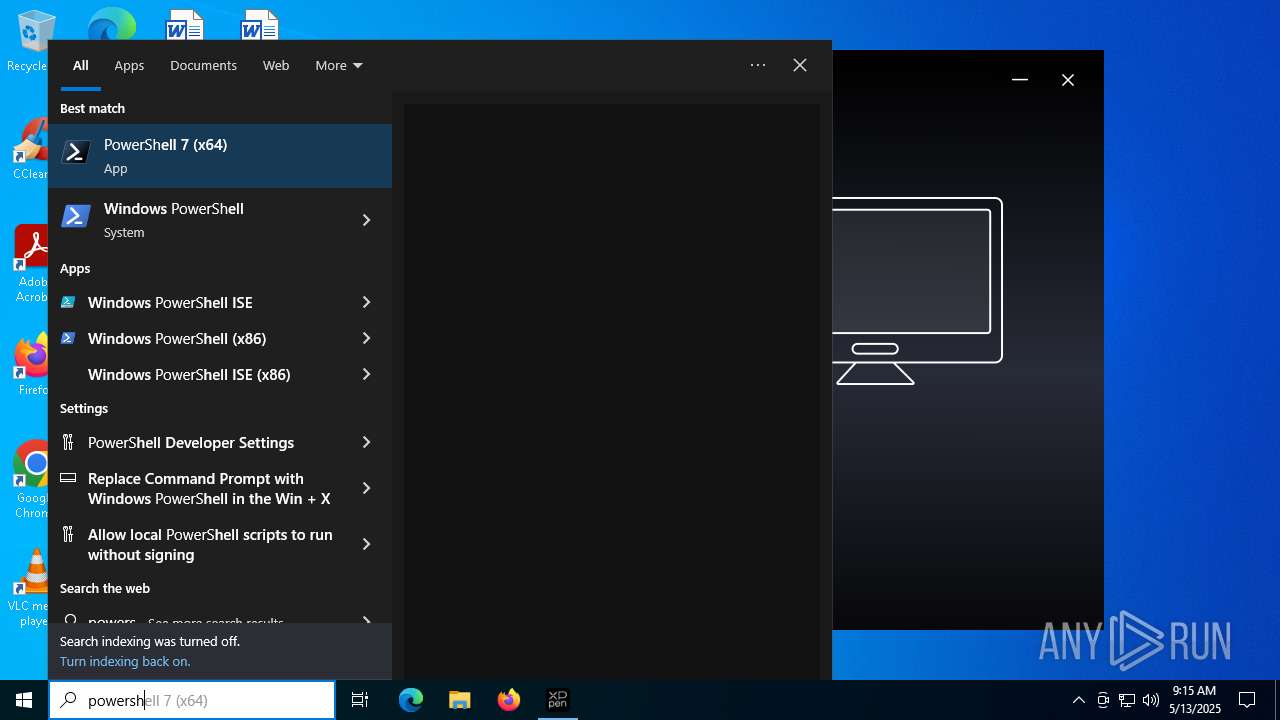
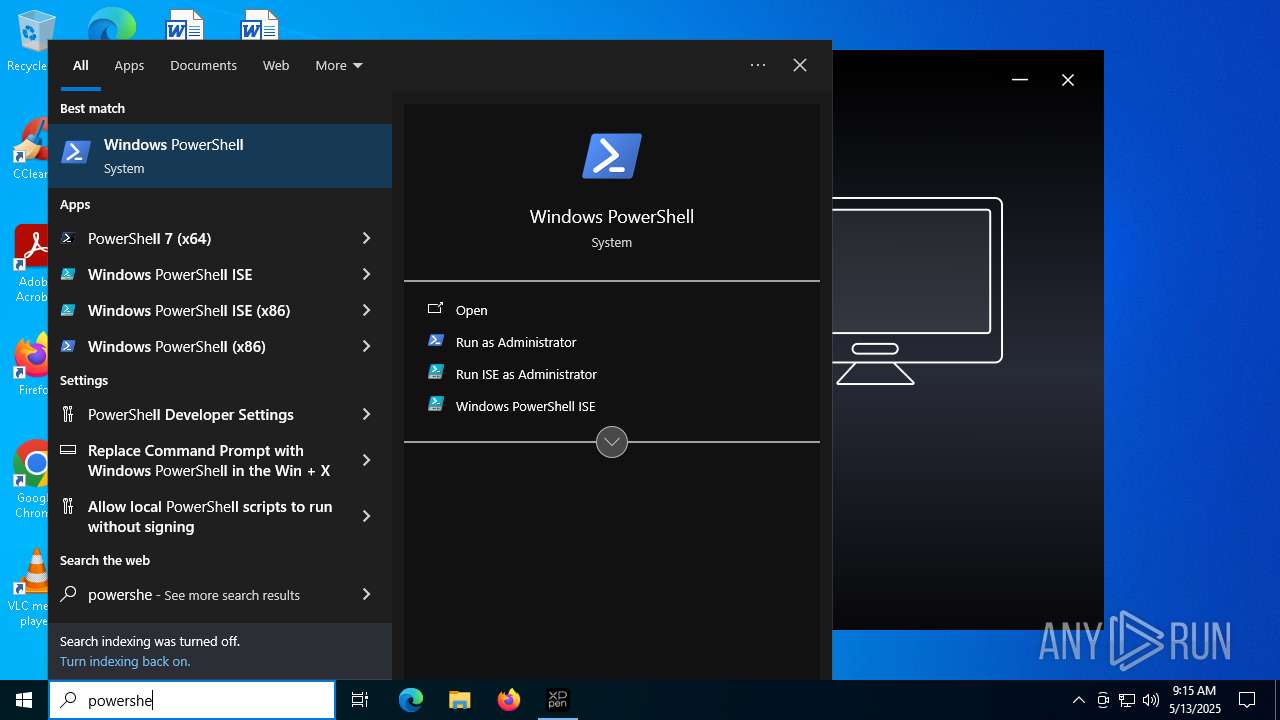
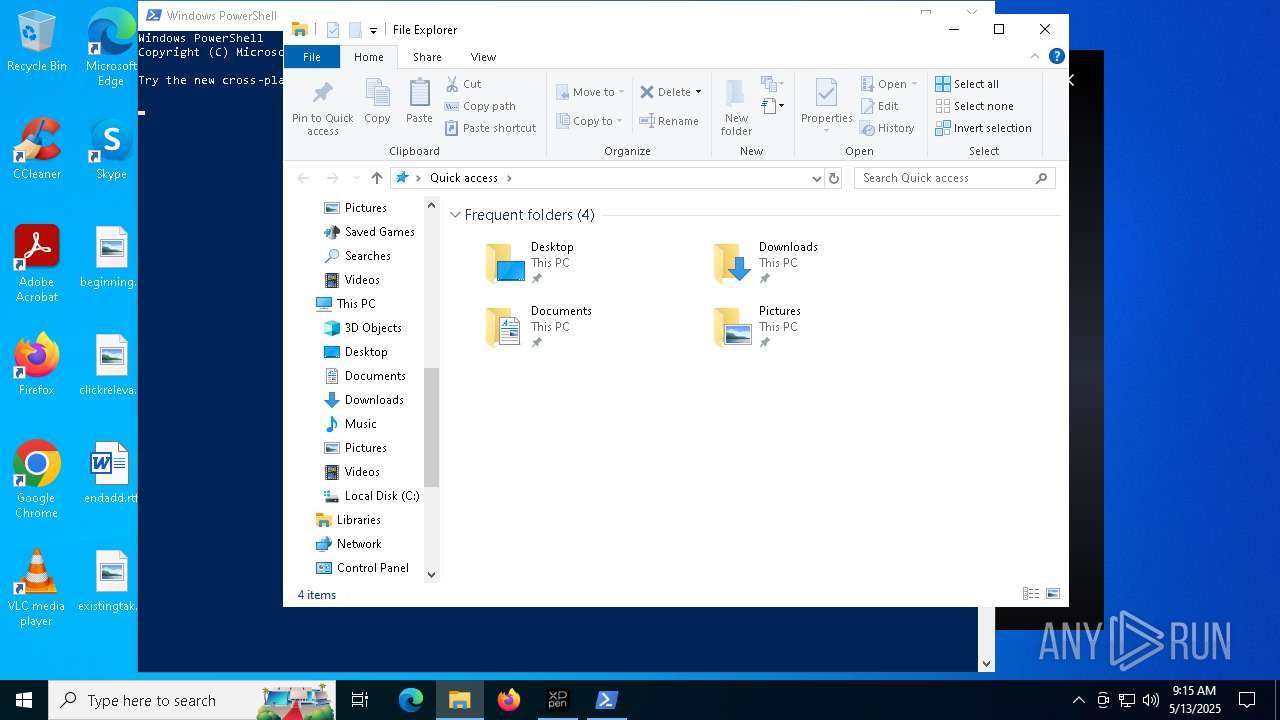
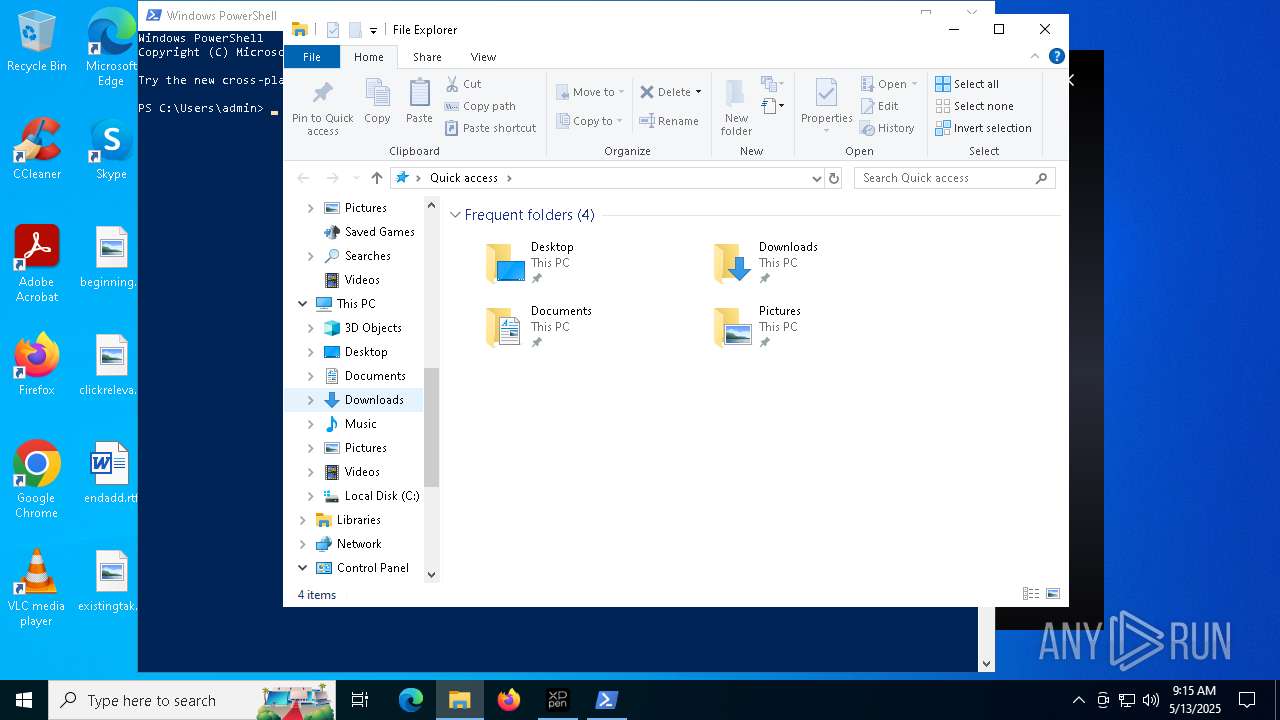
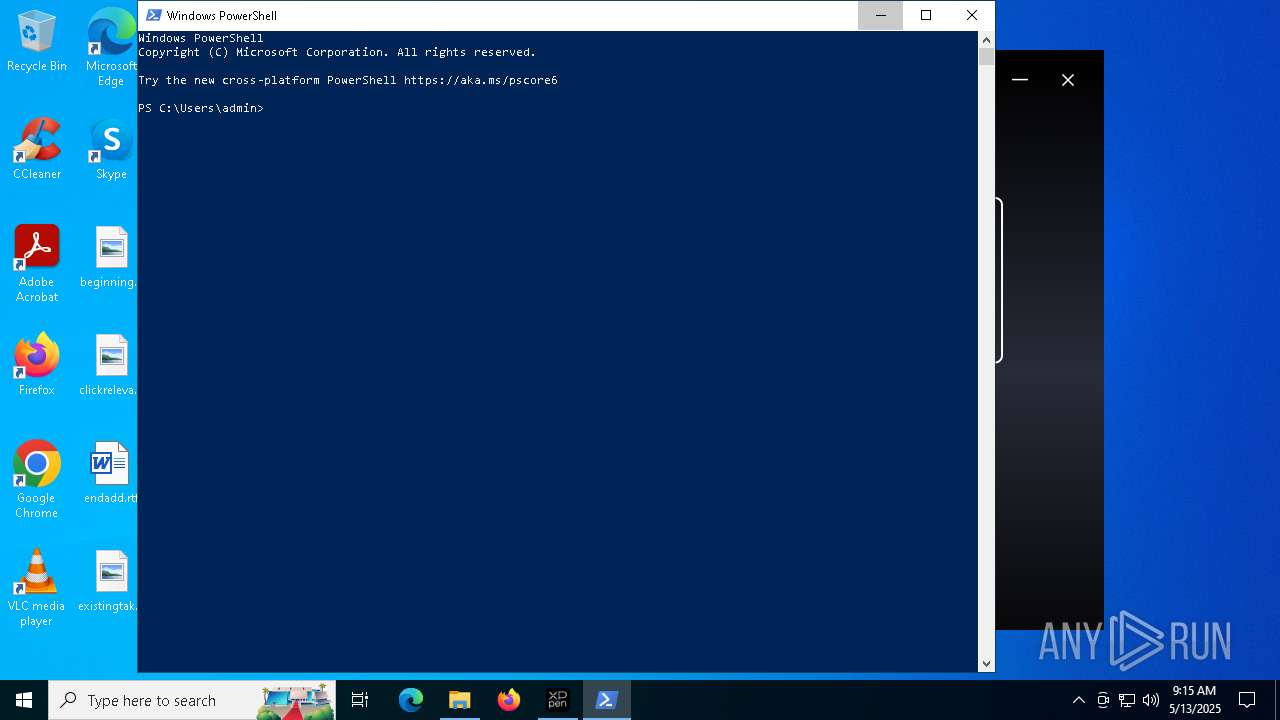
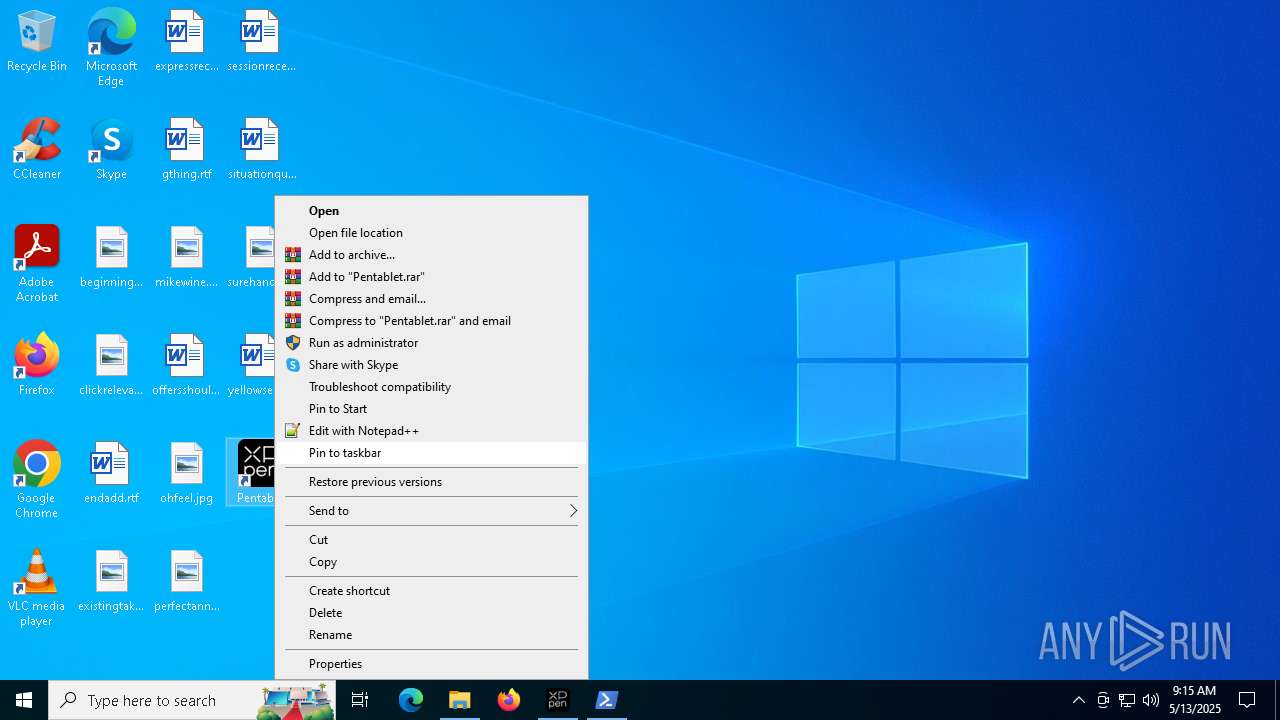
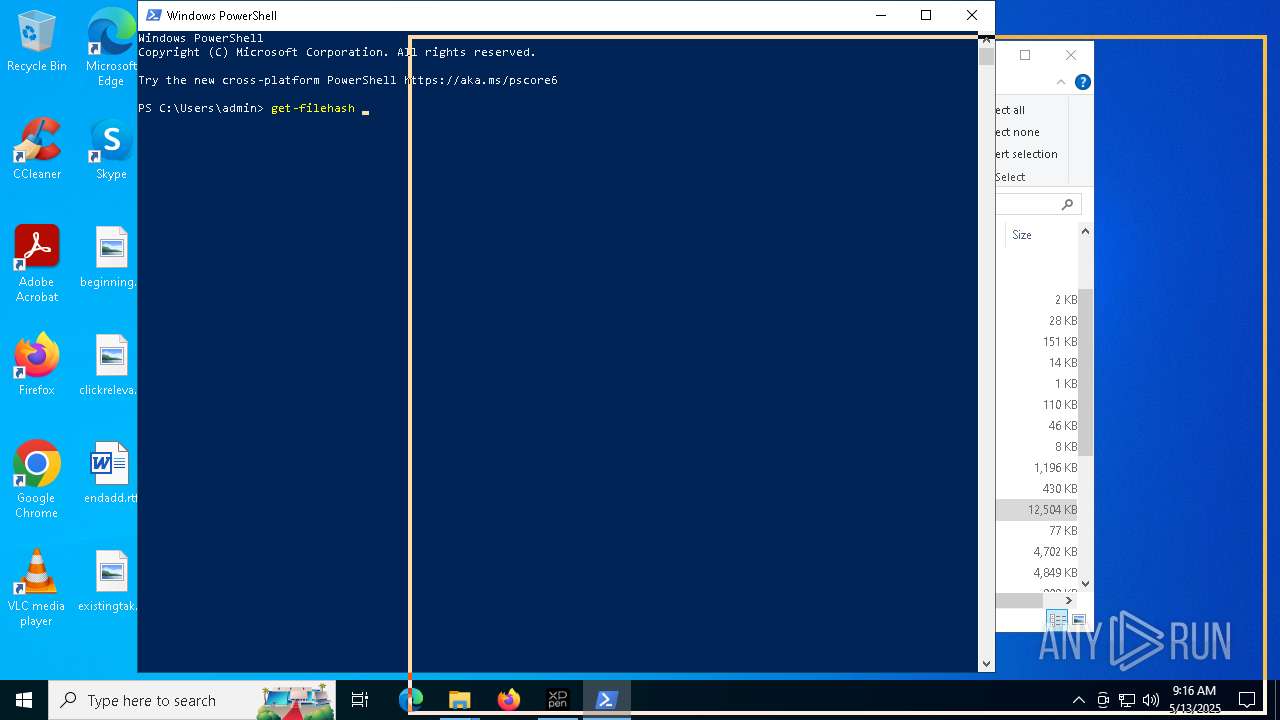
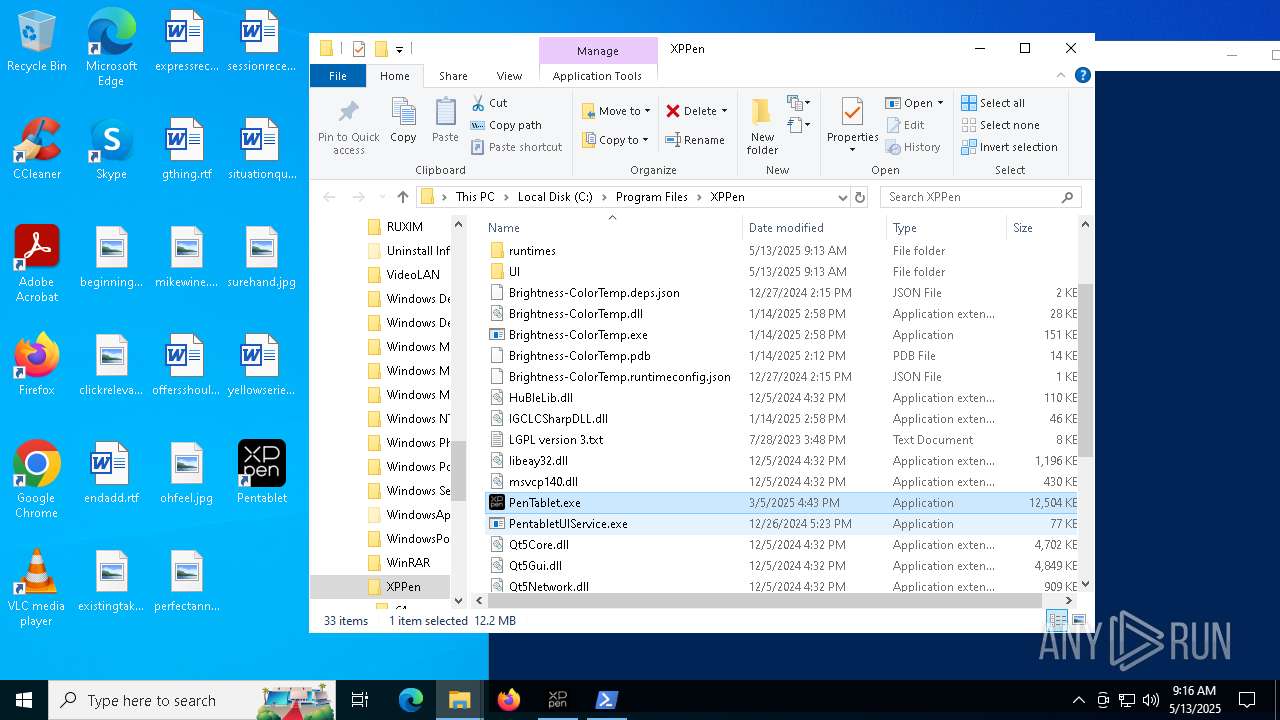
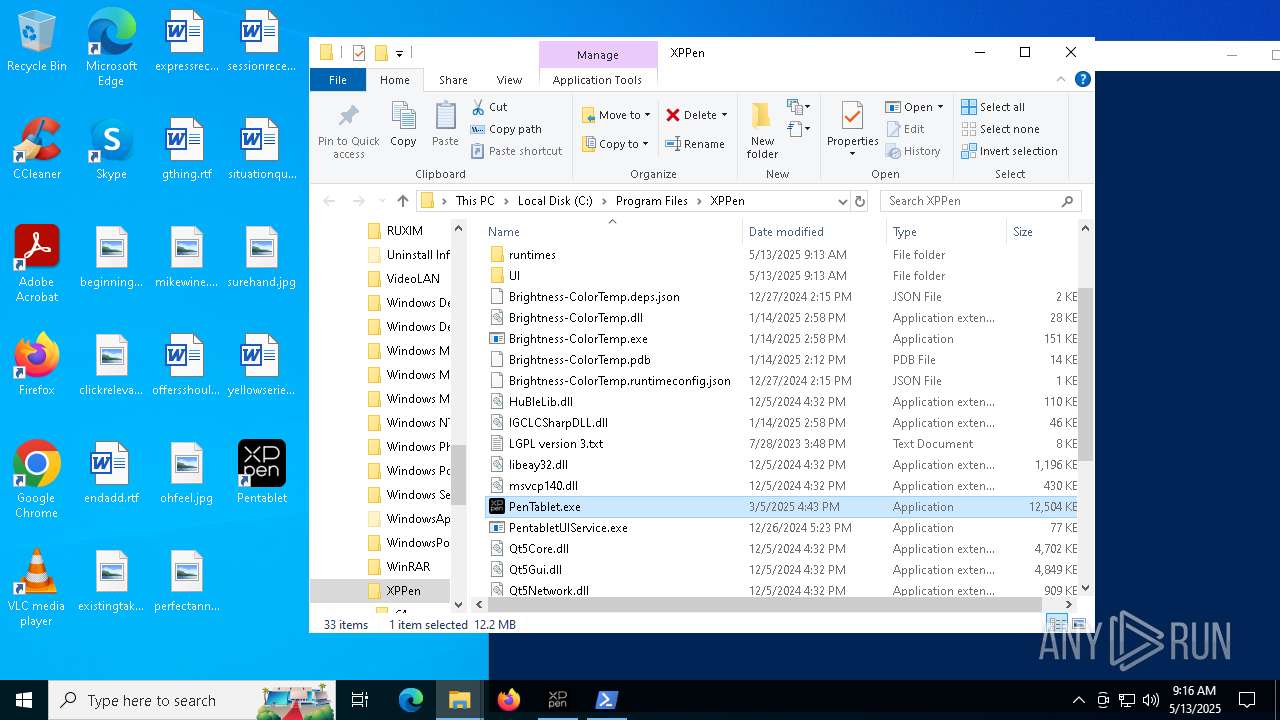
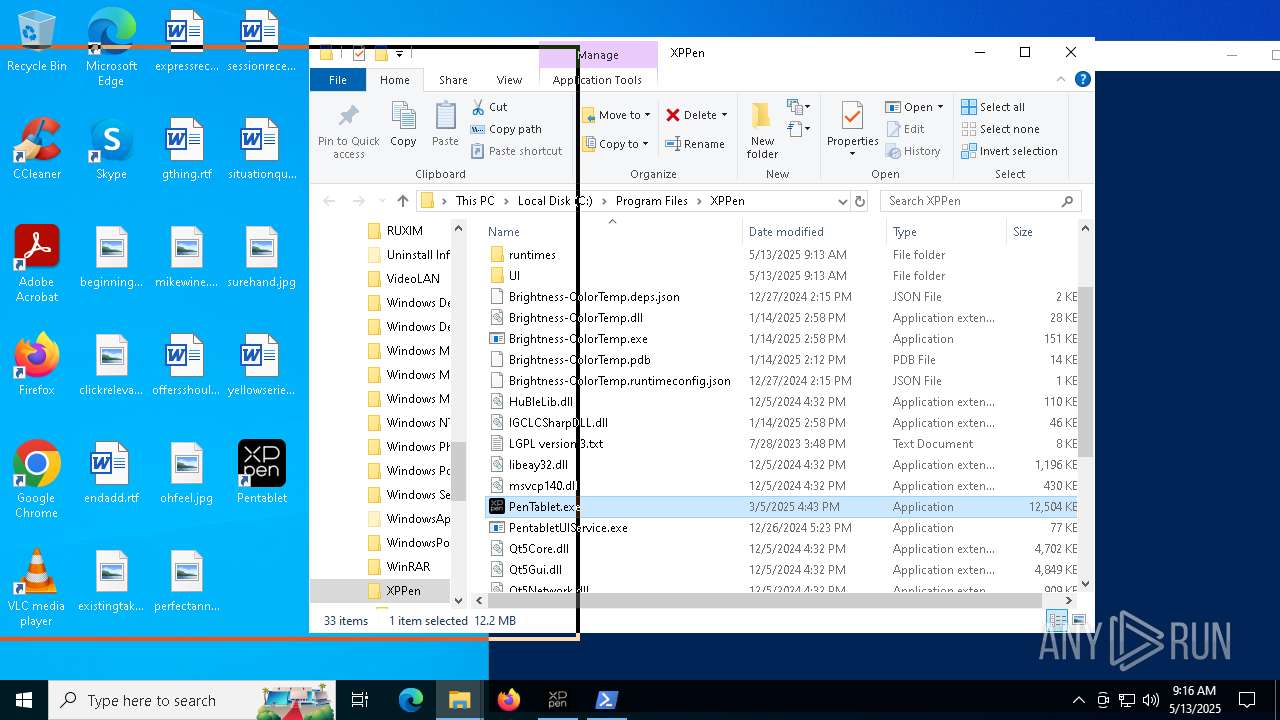
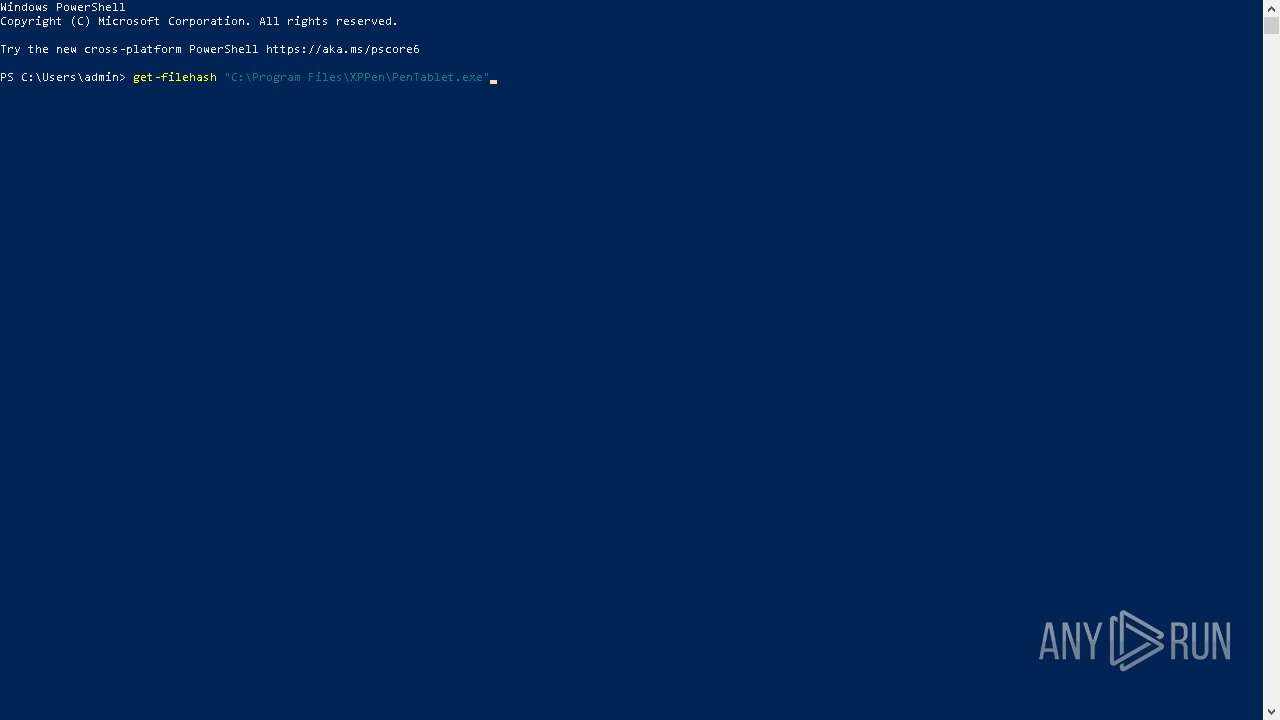
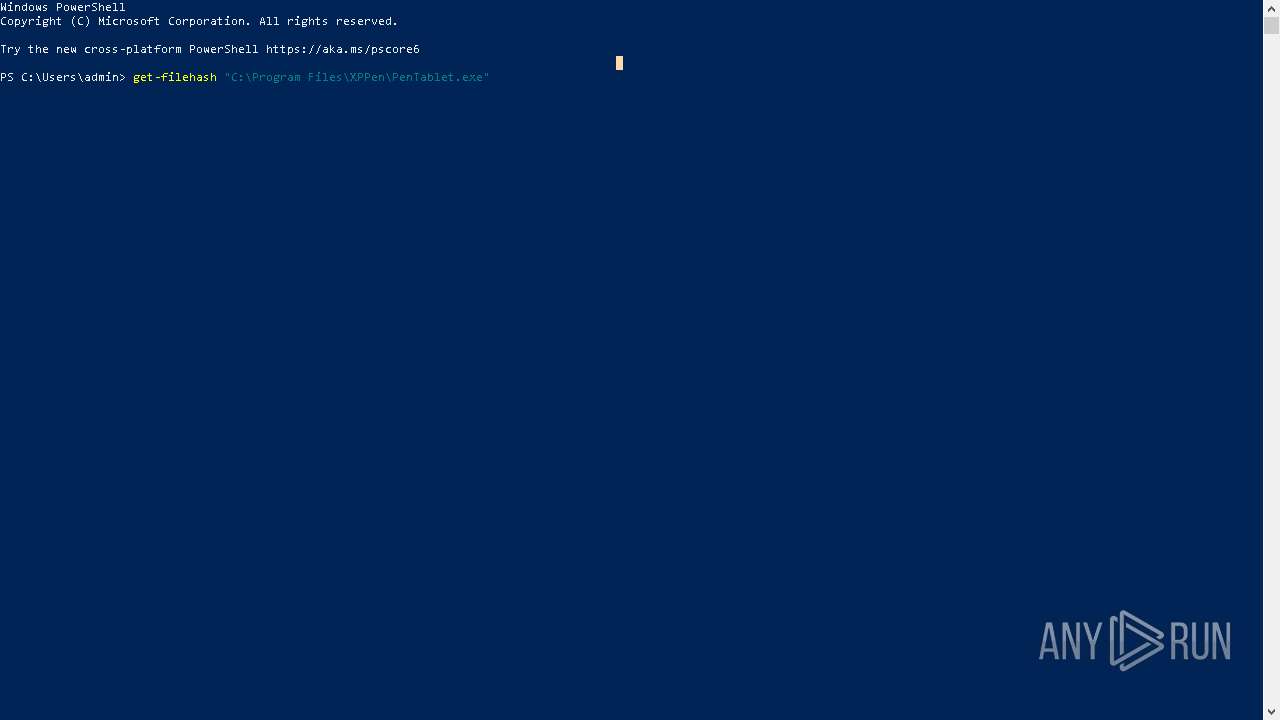
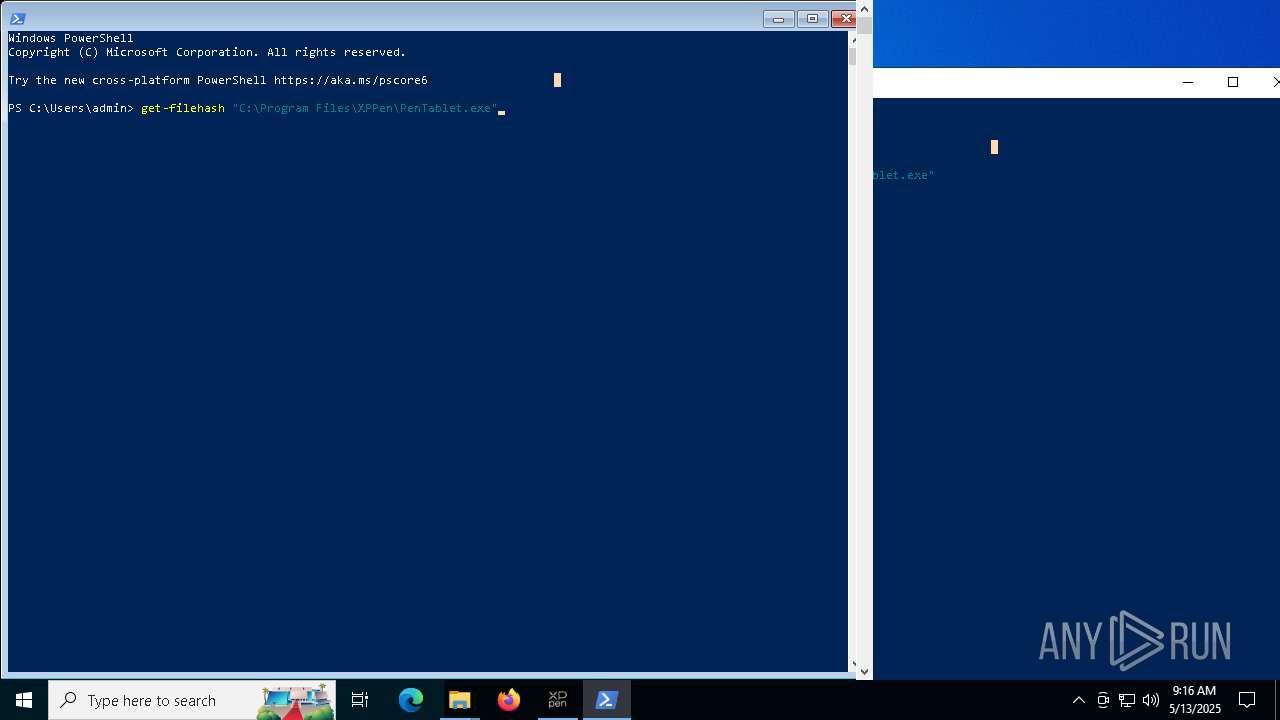
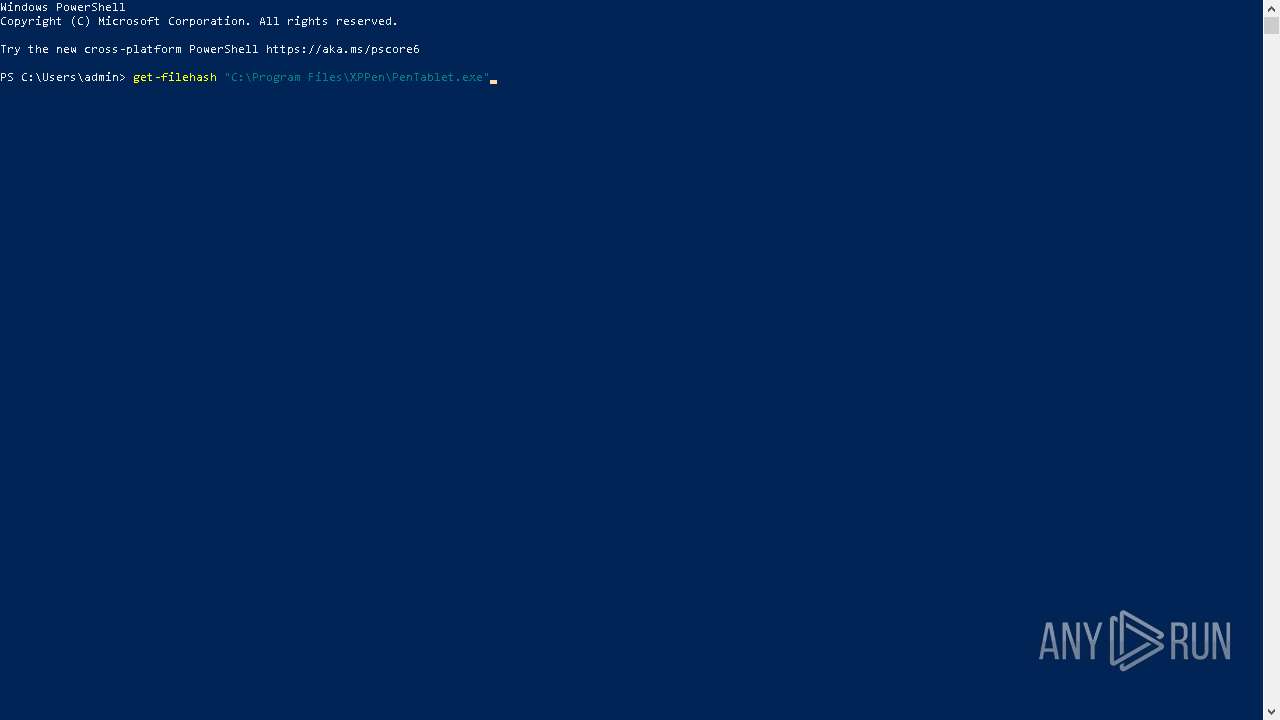
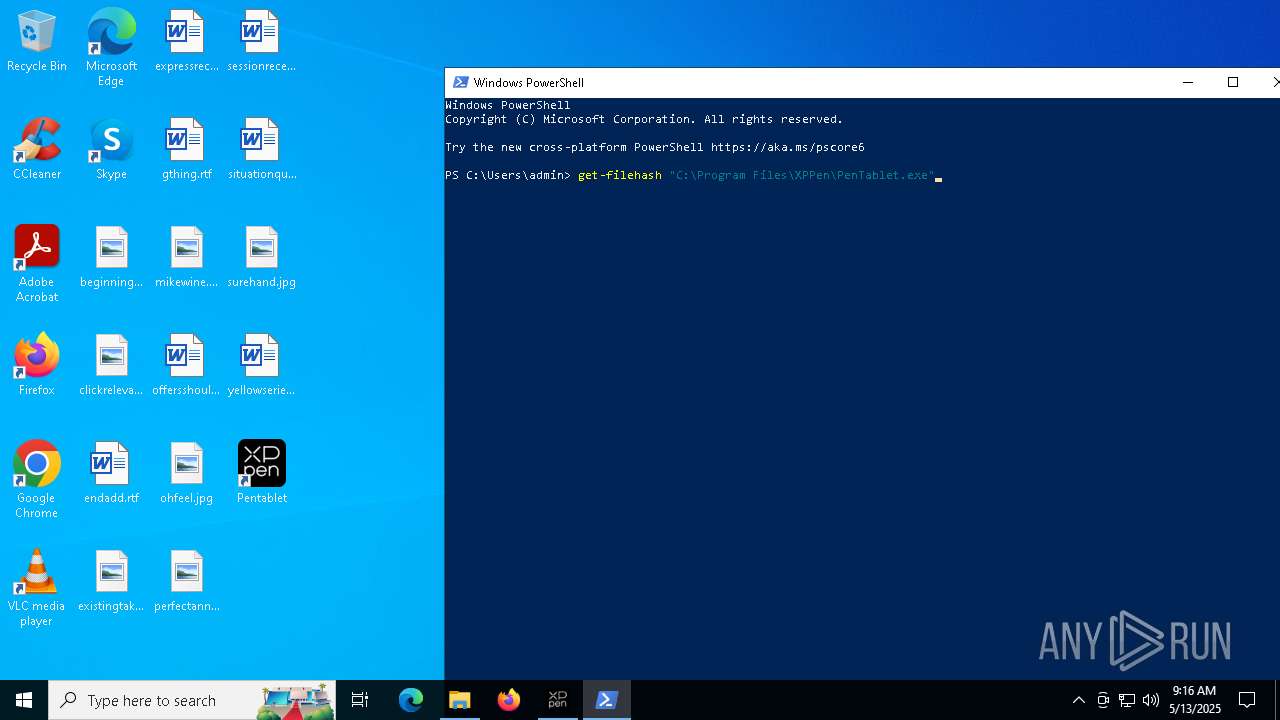
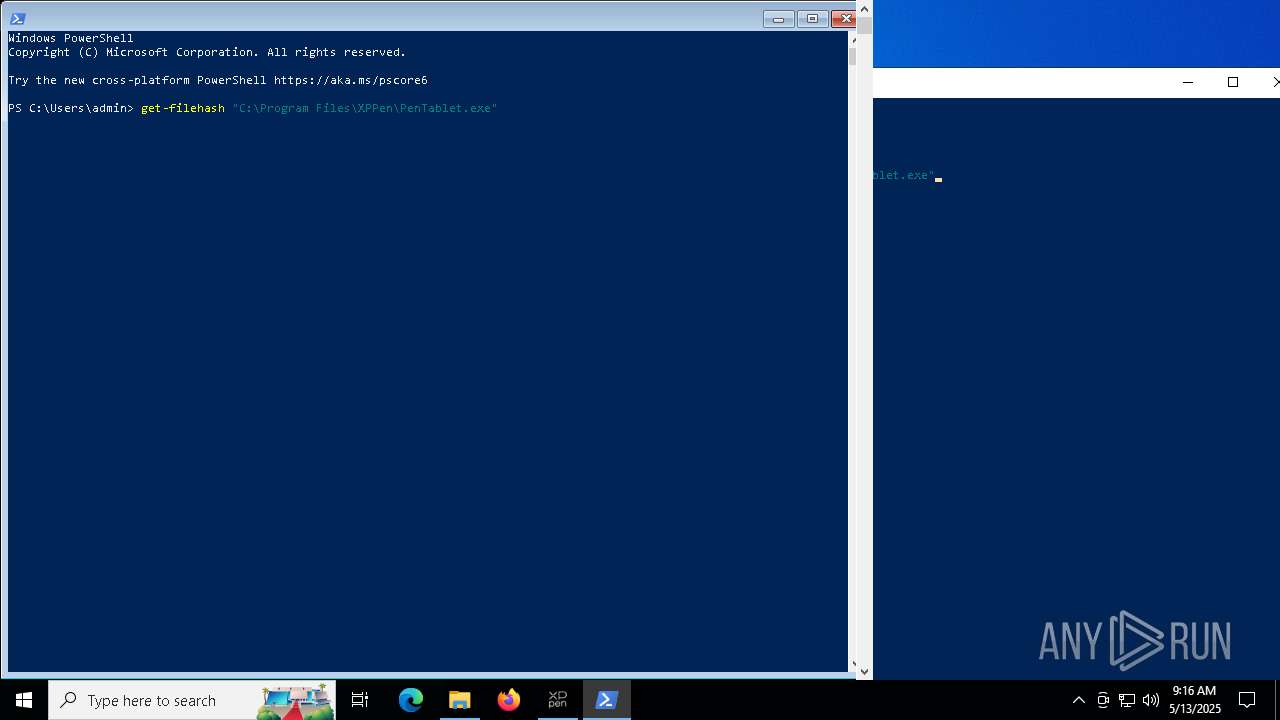
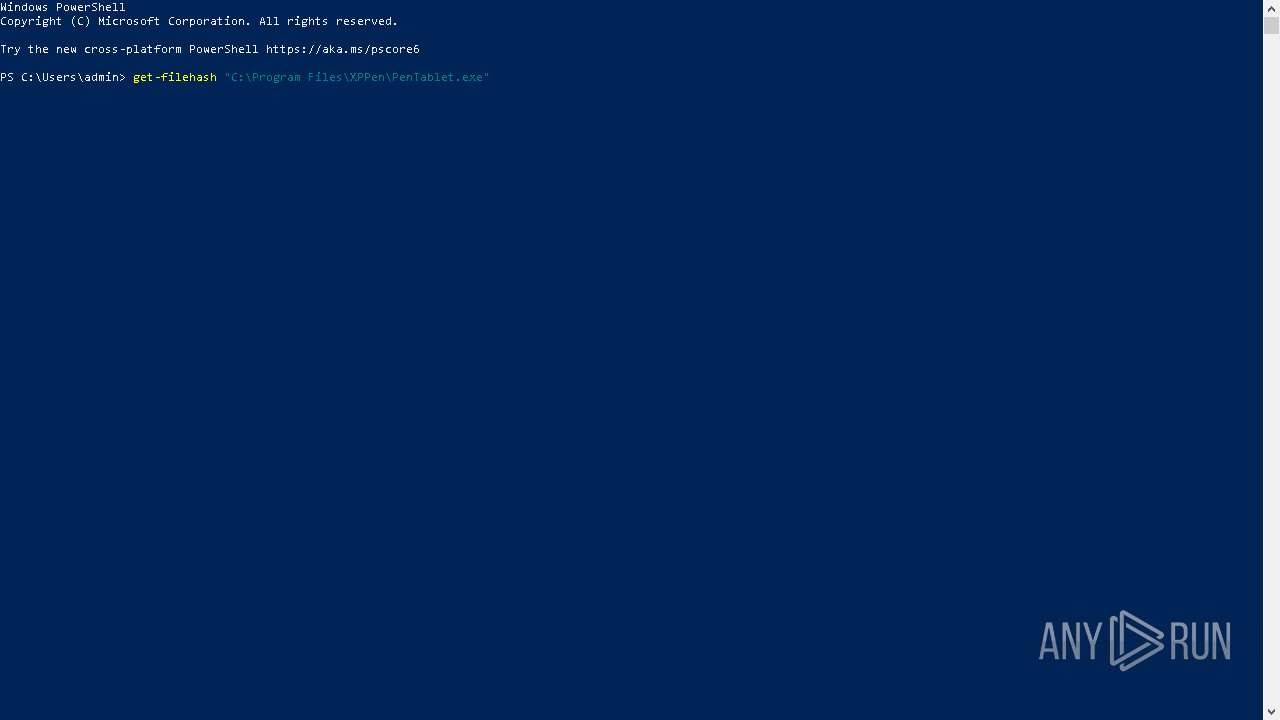
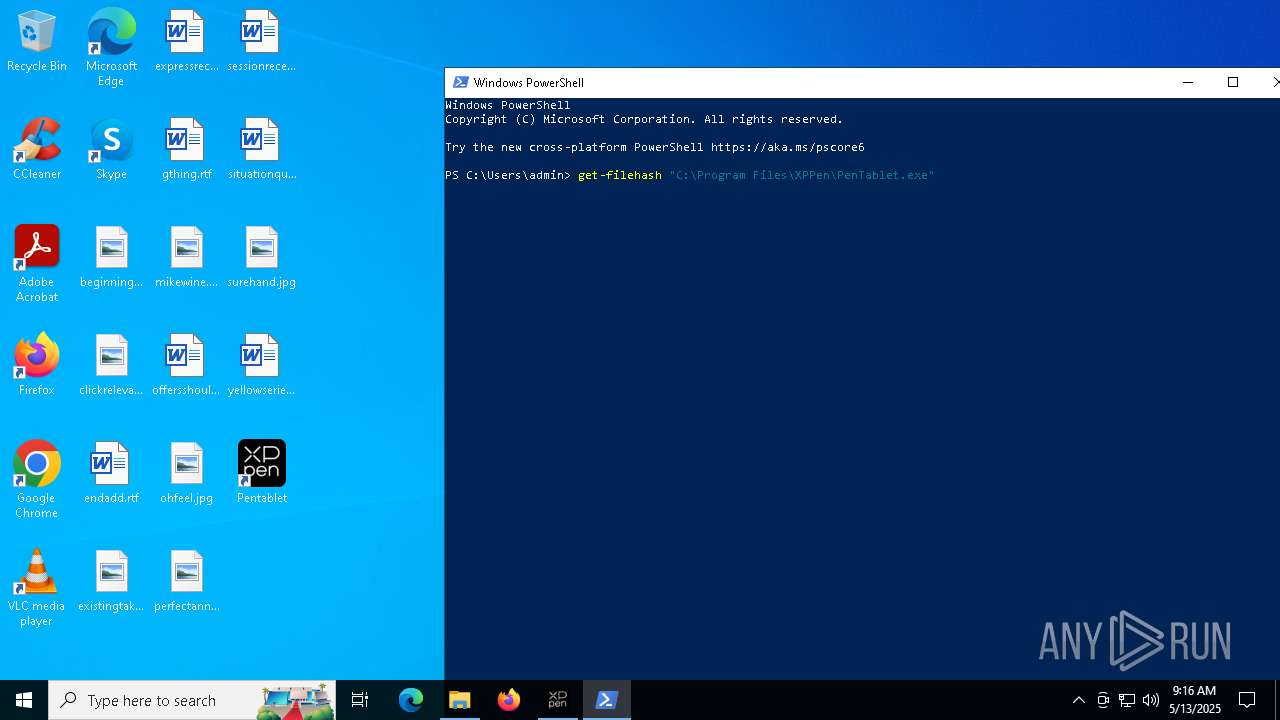
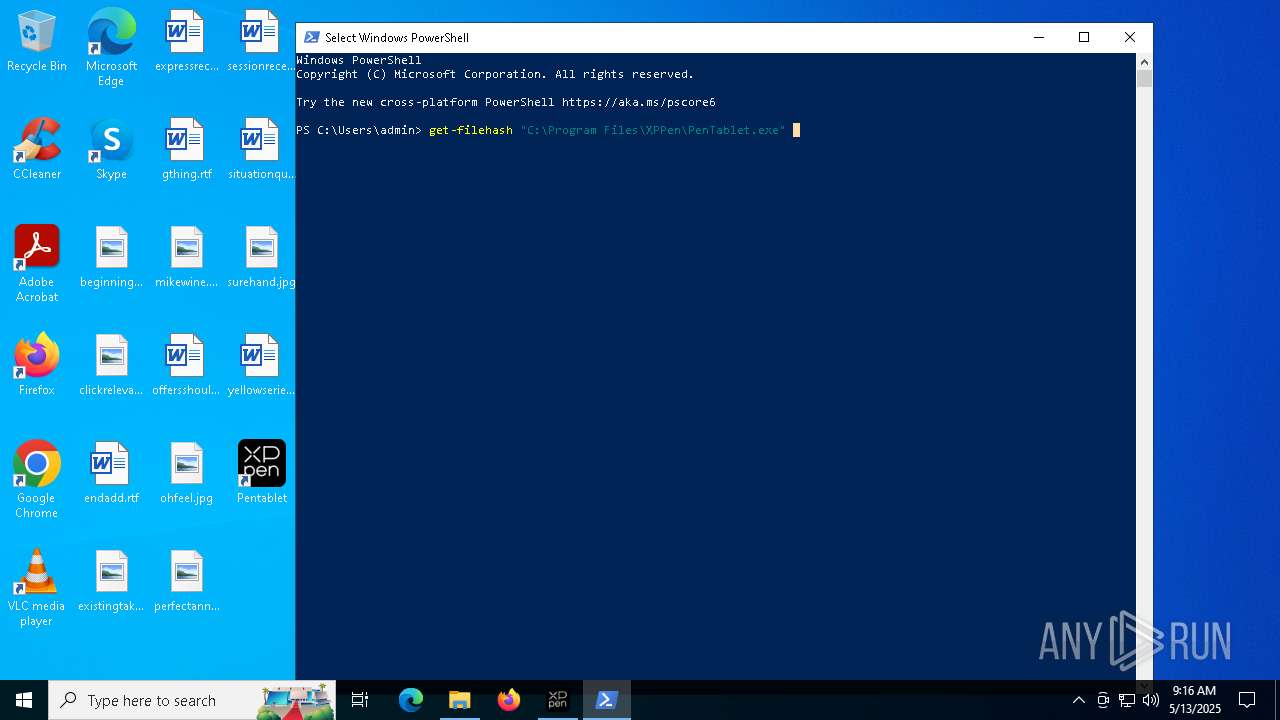
Manual execution by a user
- PenTablet.exe (PID: 6632)
- PenTablet.exe (PID: 3408)
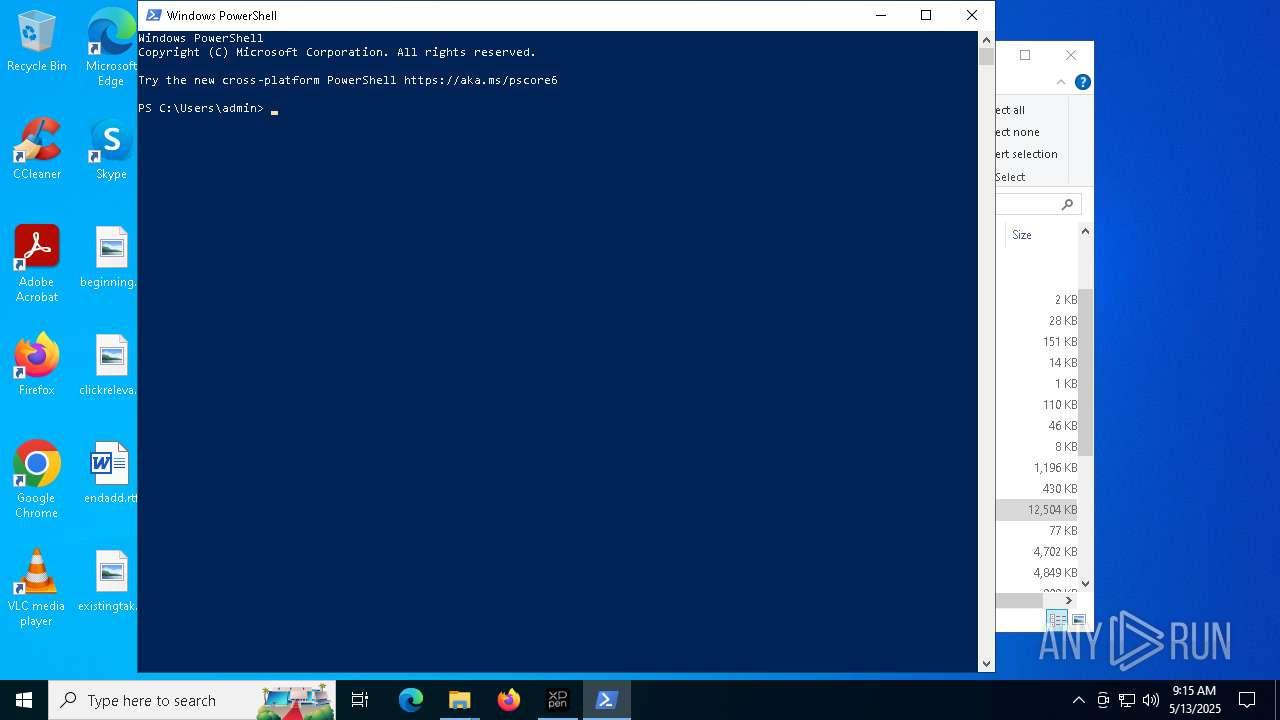
- powershell.exe (PID: 7128)
Creates a software uninstall entry
- XPPenWin_4.0.8.250305.tmp (PID: 5772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
410
Monitored processes
128
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\WINDOWS\system32\cmd.exe" /C ""C:\Users\admin\AppData\Local\Temp\is-92D5H.tmp\PSCC.bat"" | C:\Windows\System32\cmd.exe | — | XPPenWin_4.0.8.250305.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | find "pid:" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo Error opening svchost.exe(2892): " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | find "pid:" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5132 --field-trial-handle=2328,i,4158936590764937492,10912124168098488831,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6824 --field-trial-handle=2328,i,4158936590764937492,10912124168098488831,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | find "pid:" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7496 --field-trial-handle=2328,i,4158936590764937492,10912124168098488831,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo Error opening smss.exe(412): " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | DrvInst.exe "2" "211" "HID\PENTABLET&COL01\1&2D595CA7&0&0000" "C:\WINDOWS\INF\oem6.inf" "oem6.inf:ed86ca113d4f58de:hanvonugeemfilter:14.27.40.873:hid\pentablet&col01," "45f95b4db" "0000000000000208" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 981
Read events
23 832
Write events
130
Delete events
19
Modification events
| (PID) Process: | (7084) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7084) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7084) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7084) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7084) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5C59C31E97932F00 | |||
| (PID) Process: | (7084) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EAA2CC1E97932F00 | |||
| (PID) Process: | (7084) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9678FD19-B89F-48BB-B9D7-D174EEA54D87} | |||
| (PID) Process: | (7084) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A051A14F-5E76-4559-A738-8C0D1A8BDB54} | |||
| (PID) Process: | (7084) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {20A97853-5F36-48DE-A4CE-0DDCCC3D5969} | |||
| (PID) Process: | (7084) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A889A9EA-C020-4EBC-ACC7-D16E23543976} | |||
Executable files
149
Suspicious files
470
Text files
124
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b930.TMP | — | |
MD5:— | SHA256:— | |||
| 7084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b911.TMP | — | |
MD5:— | SHA256:— | |||
| 7084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b940.TMP | — | |
MD5:— | SHA256:— | |||
| 7084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b940.TMP | — | |
MD5:— | SHA256:— | |||
| 7084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b95f.TMP | — | |
MD5:— | SHA256:— | |||
| 7084 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
153
DNS requests
142
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.15:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6752 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6752 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1020 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747705073&P2=404&P3=2&P4=VUTlvvqmSUokk9azN1kLYgAOLHhn75Ag7MwgE1r3P2hdznuP7Za7z9j9cixLVsBWCggsItjXjhxr81Cq9oe5nQ%3d%3d | unknown | — | — | whitelisted |
1020 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747705073&P2=404&P3=2&P4=VUTlvvqmSUokk9azN1kLYgAOLHhn75Ag7MwgE1r3P2hdznuP7Za7z9j9cixLVsBWCggsItjXjhxr81Cq9oe5nQ%3d%3d | unknown | — | — | whitelisted |
1020 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747705073&P2=404&P3=2&P4=VUTlvvqmSUokk9azN1kLYgAOLHhn75Ag7MwgE1r3P2hdznuP7Za7z9j9cixLVsBWCggsItjXjhxr81Cq9oe5nQ%3d%3d | unknown | — | — | whitelisted |
1020 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747705073&P2=404&P3=2&P4=VUTlvvqmSUokk9azN1kLYgAOLHhn75Ag7MwgE1r3P2hdznuP7Za7z9j9cixLVsBWCggsItjXjhxr81Cq9oe5nQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.15:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7244 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7084 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7244 | msedge.exe | 150.171.29.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
www.xp-pen.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7244 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7244 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7244 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7244 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7244 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7244 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |