| File name: | 444a3066eace07cf316d1df257bb1cd65fe714c1_win10x64_1903_c##windows#system32#tasks#microsoft#windows#softwareprotectionplatform#svcrestarttask(0)_files |
| Full analysis: | https://app.any.run/tasks/e5c39d4c-1b92-46e9-8207-bb7ee8aa4f12 |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2024, 09:47:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, Unicode text, UTF-16, little-endian text, with CRLF line terminators |
| MD5: | 43114B22390EEA761EAA204945ACB636 |
| SHA1: | 7CA7B506AD5BF6FC0EC44594730DA76D85970EE4 |
| SHA256: | 445DC66AA6E13095879442F1CB6824DBFC204D4D82D576A36EF050CAC7B27BEA |
| SSDEEP: | 96:OYMguQII4ip6h4aGdinipV9ll7UY5HAmzQ+:QA4R/xne7HO+ |
MALICIOUS
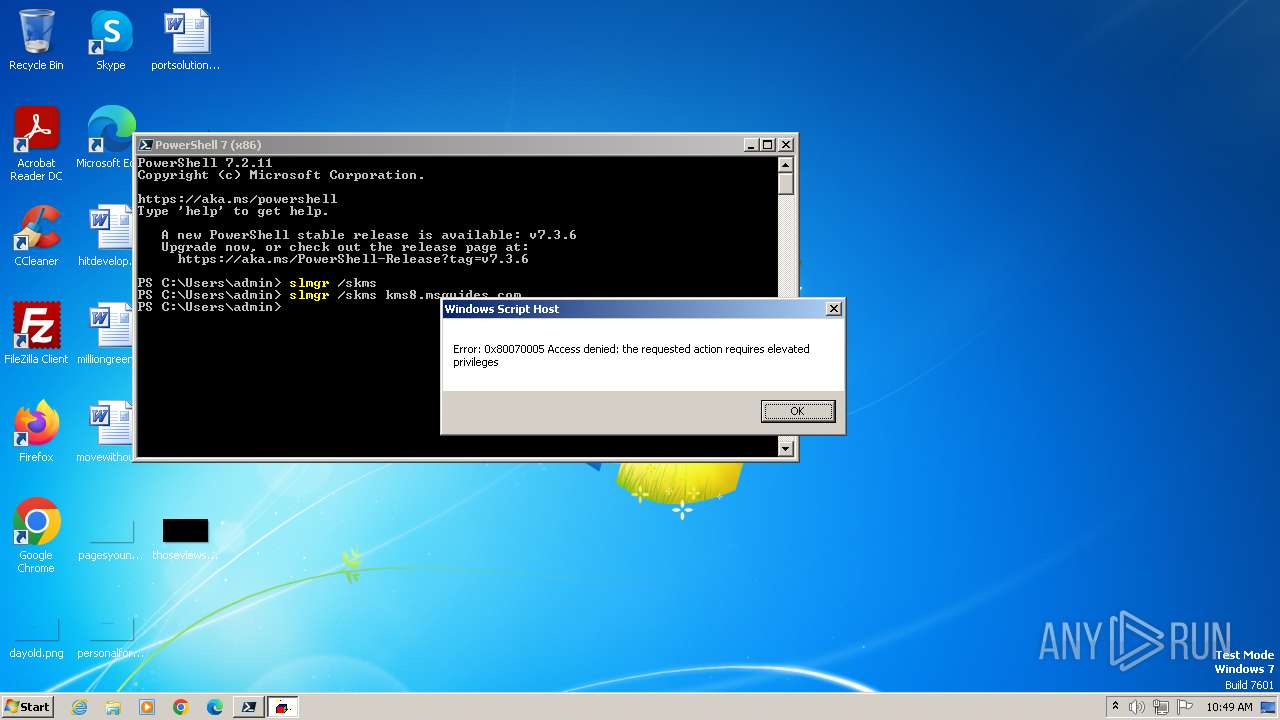
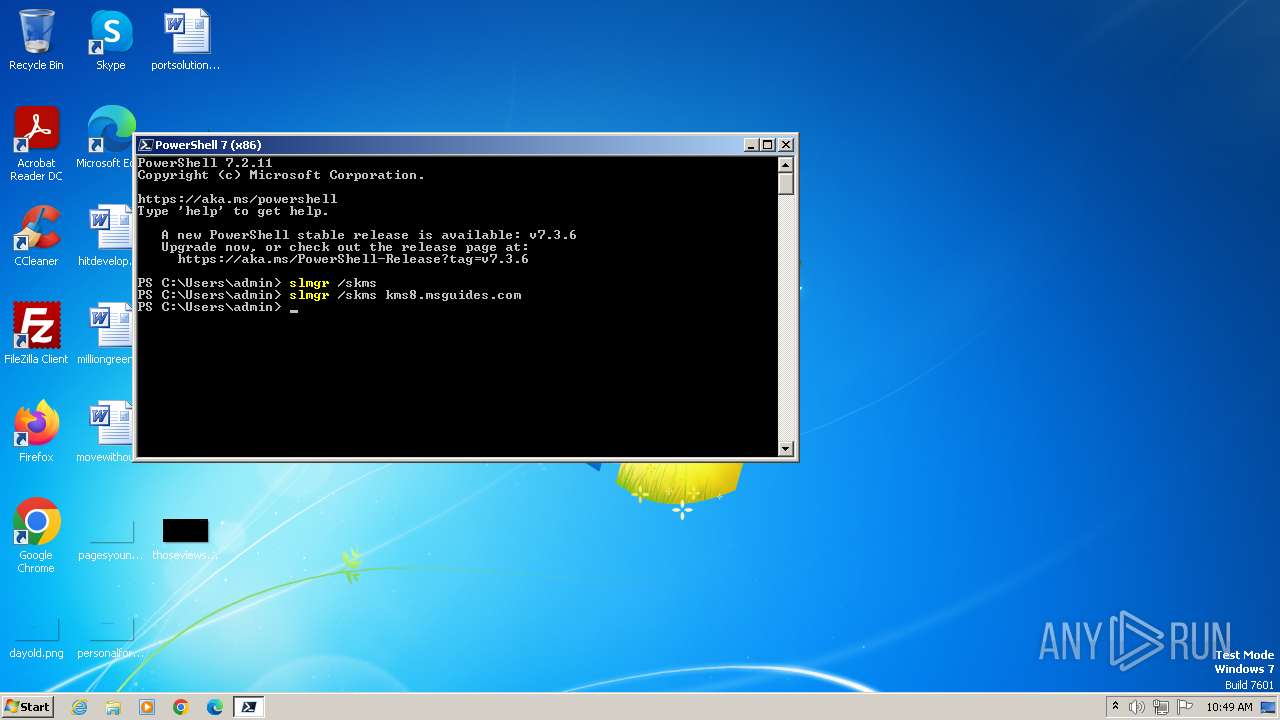
Opens a text file (SCRIPT)
- wscript.exe (PID: 2328)
- wscript.exe (PID: 1332)
- wscript.exe (PID: 848)
SUSPICIOUS
Reads the date of Windows installation
- pwsh.exe (PID: 1812)
- pwsh.exe (PID: 1480)
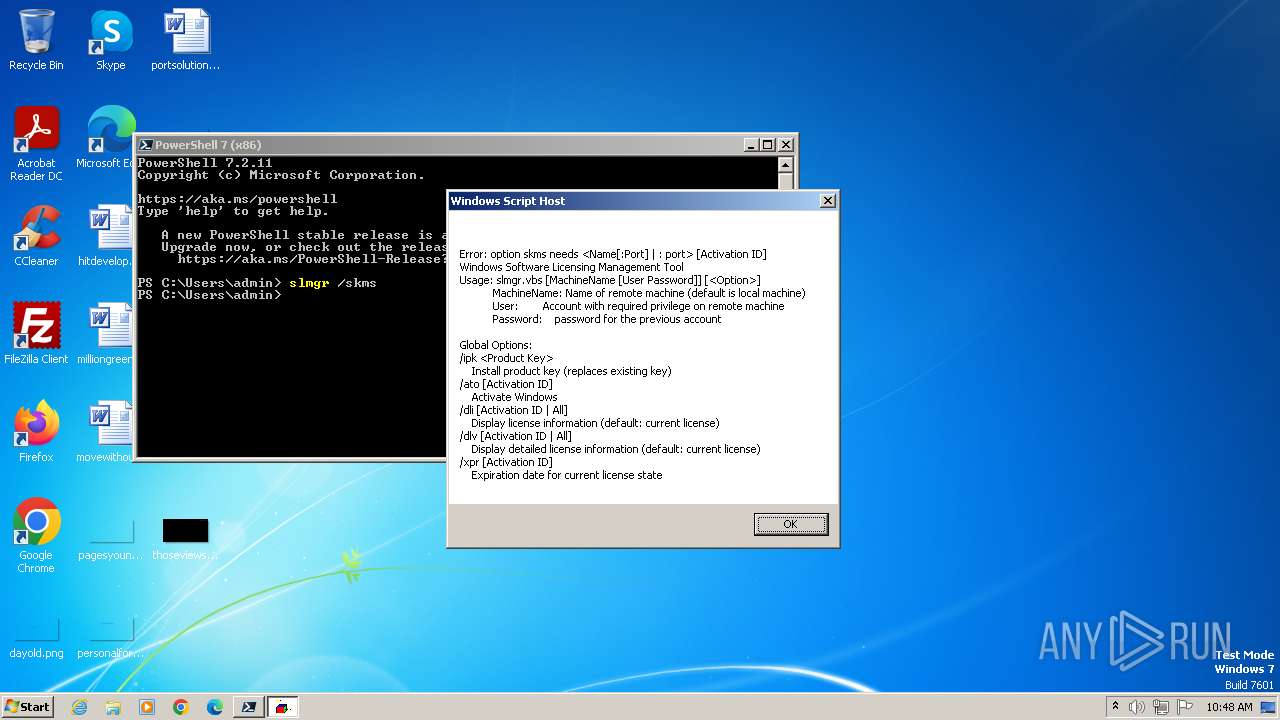
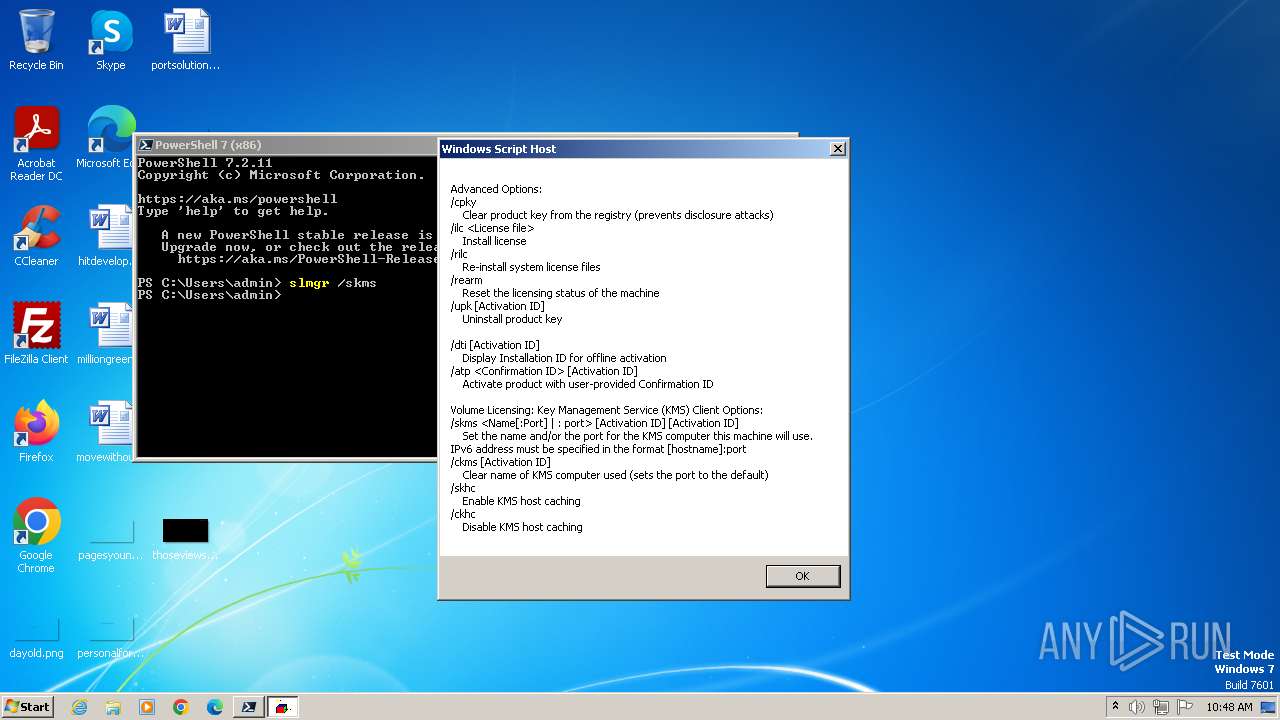
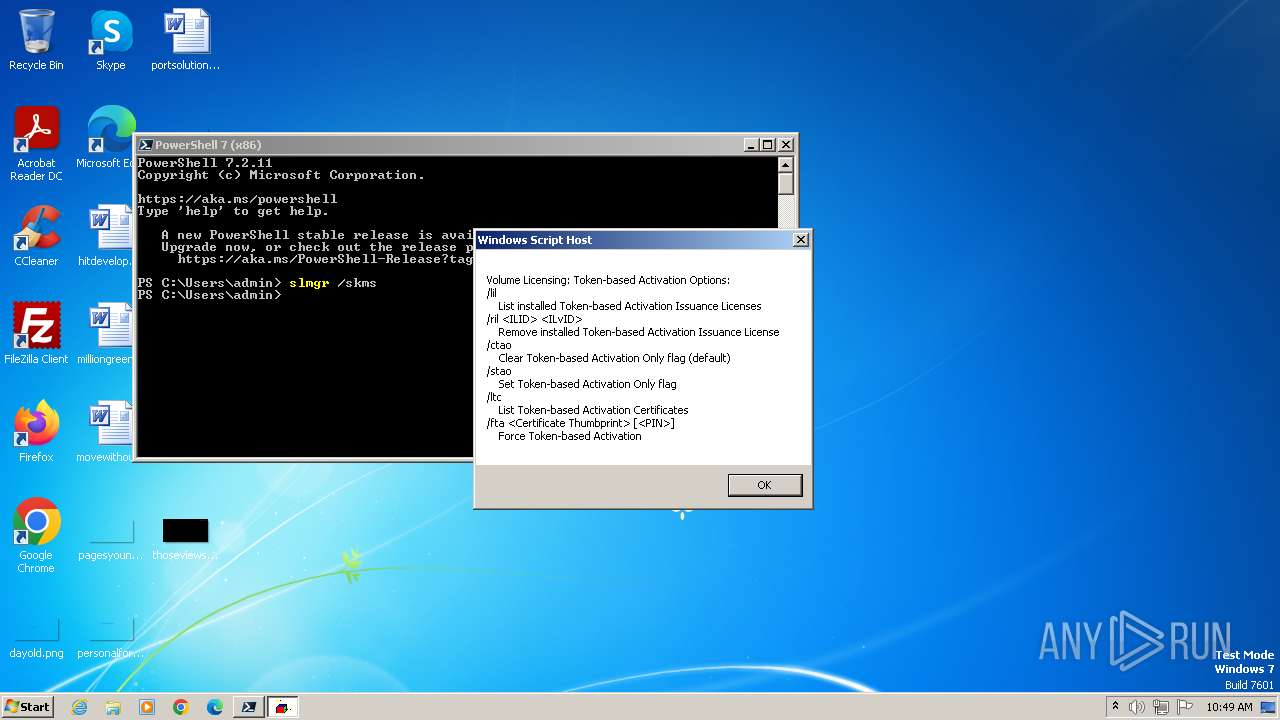
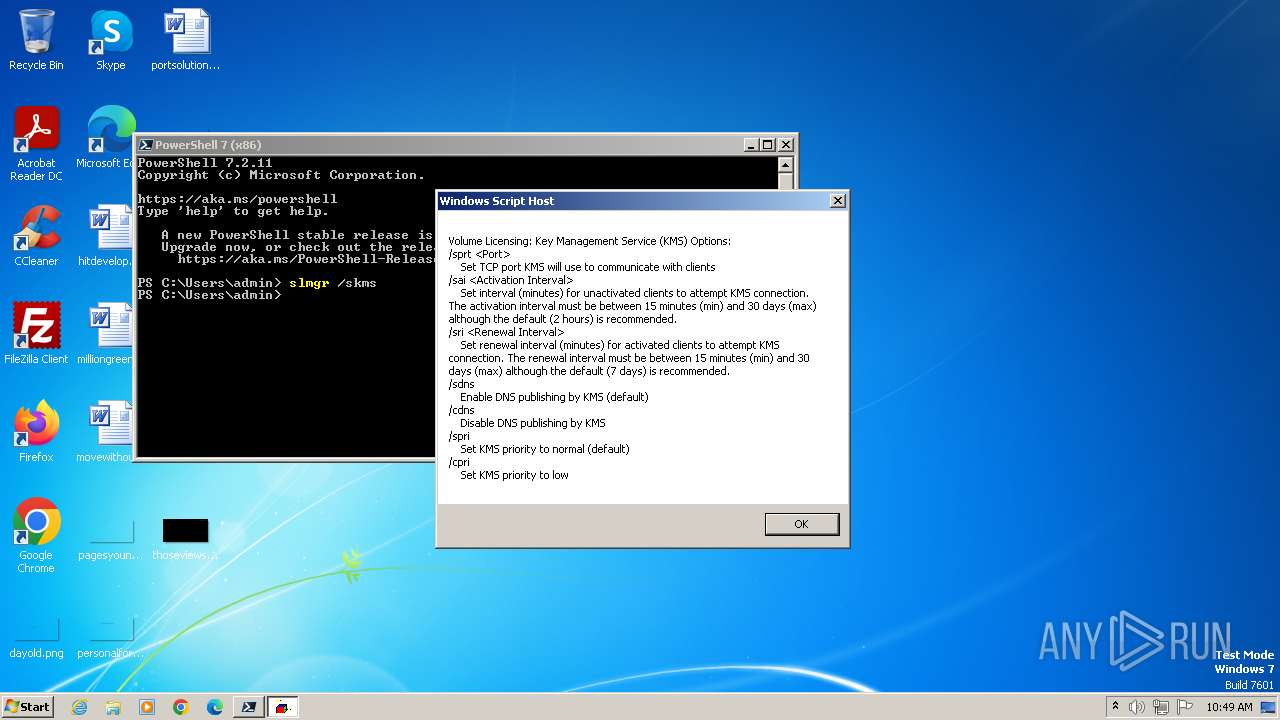
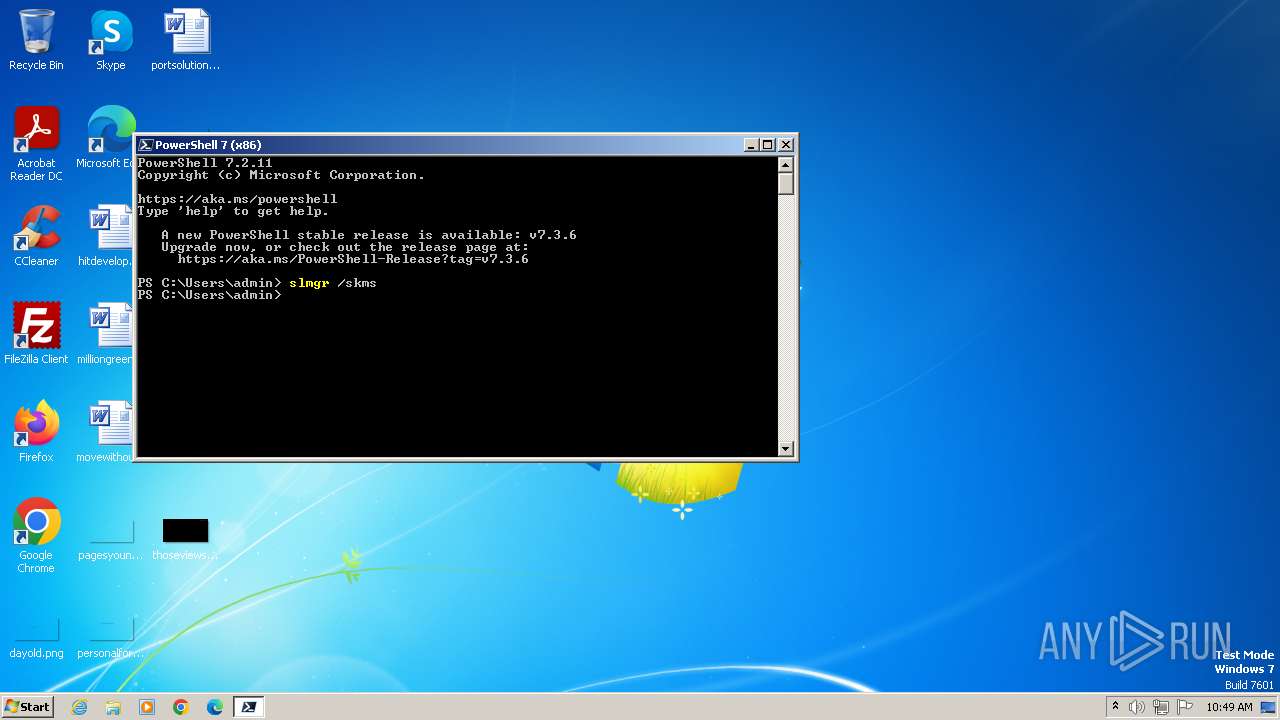
The process executes VB scripts
- pwsh.exe (PID: 1812)
- pwsh.exe (PID: 1480)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2328)
- wscript.exe (PID: 1332)
- wscript.exe (PID: 848)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 2328)
- wscript.exe (PID: 1332)
- wscript.exe (PID: 848)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 2328)
- wscript.exe (PID: 1332)
- wscript.exe (PID: 848)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 2328)
- wscript.exe (PID: 1332)
- wscript.exe (PID: 848)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2328)
- wscript.exe (PID: 1332)
- wscript.exe (PID: 848)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 1332)
- wscript.exe (PID: 848)
INFO
Application launched itself
- iexplore.exe (PID: 4024)
Reads the computer name
- wmpnscfg.exe (PID: 1948)
- pwsh.exe (PID: 1812)
- pwsh.exe (PID: 1480)
Checks supported languages
- wmpnscfg.exe (PID: 1948)
- pwsh.exe (PID: 1812)
- pwsh.exe (PID: 1480)
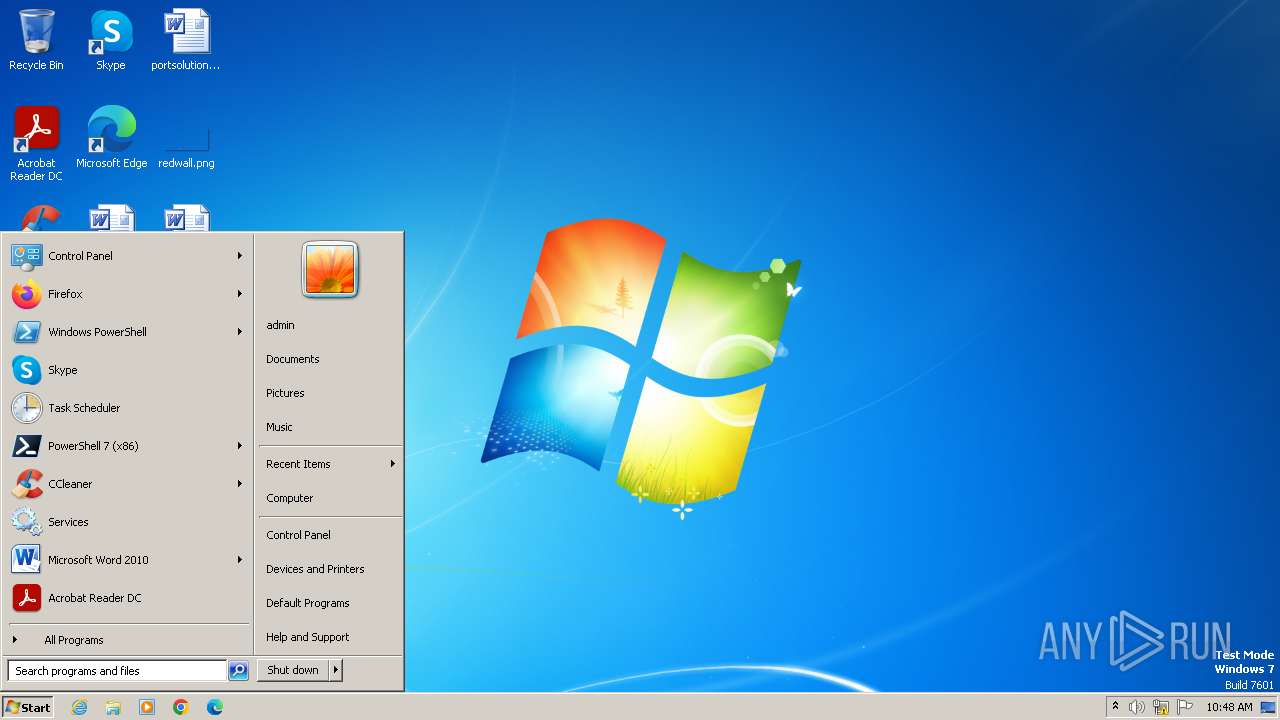
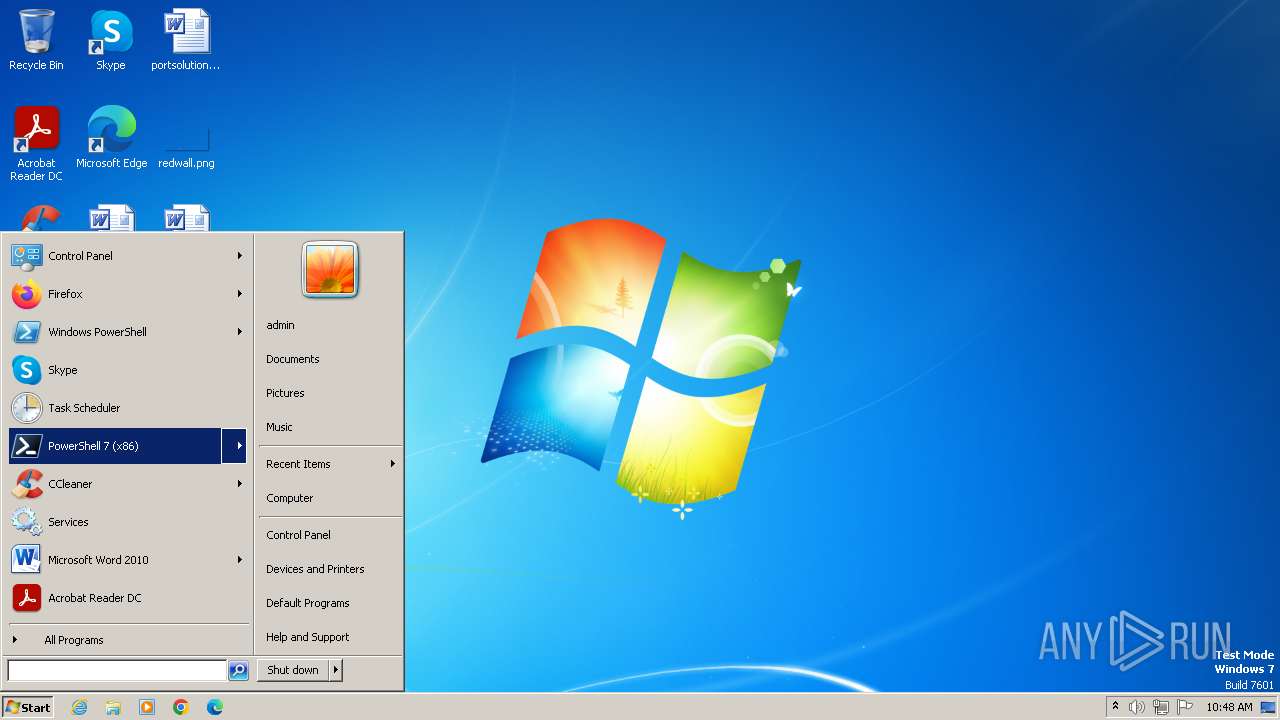
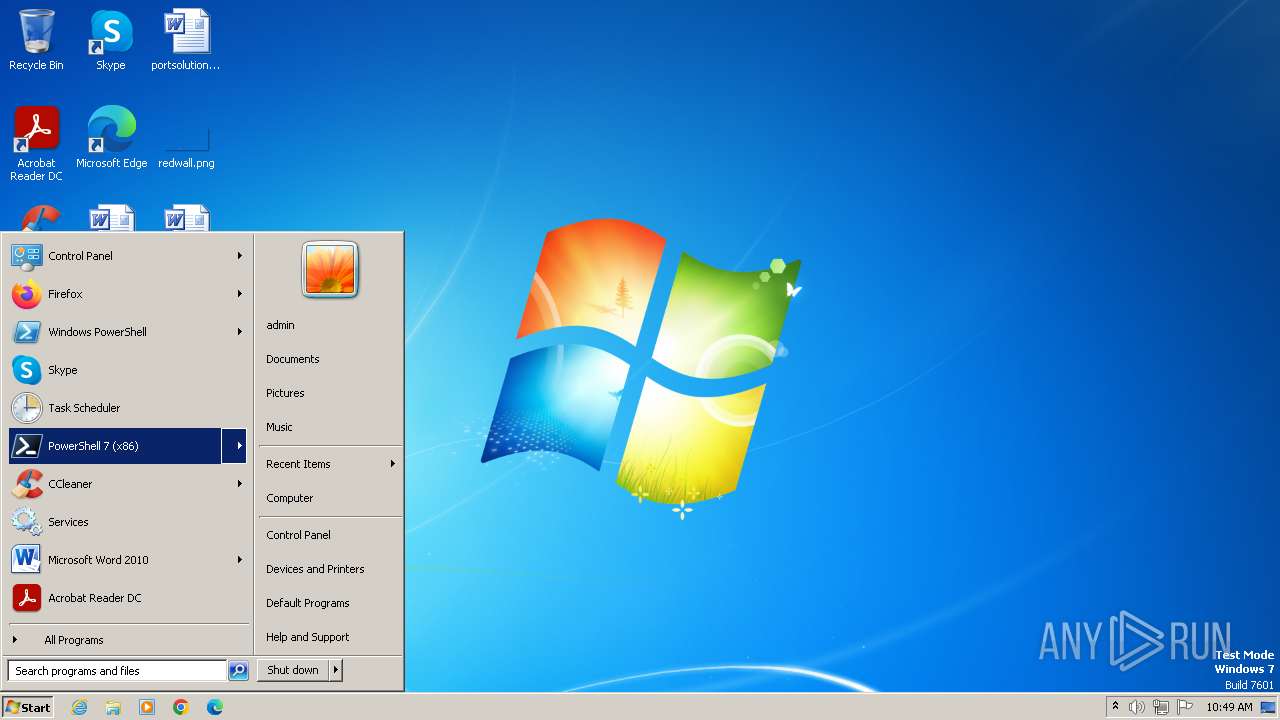
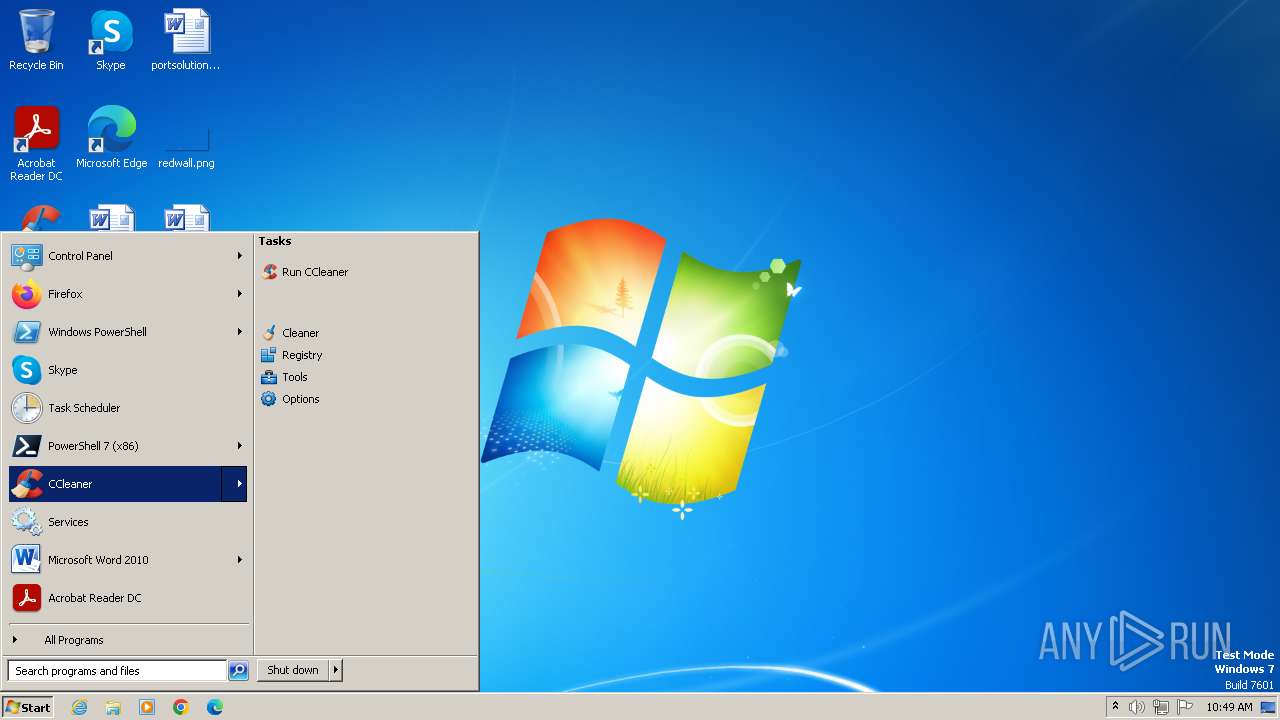
Manual execution by a user
- pwsh.exe (PID: 1812)
- wmpnscfg.exe (PID: 1948)
- pwsh.exe (PID: 1480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml | | | Generic XML (UTF-16 LE) (7.6) |
|---|---|---|
| .txt | | | Text - UTF-16 (LE) encoded (1.2) |
| .mp3 | | | MP3 audio (0.6) |
EXIF
XMP
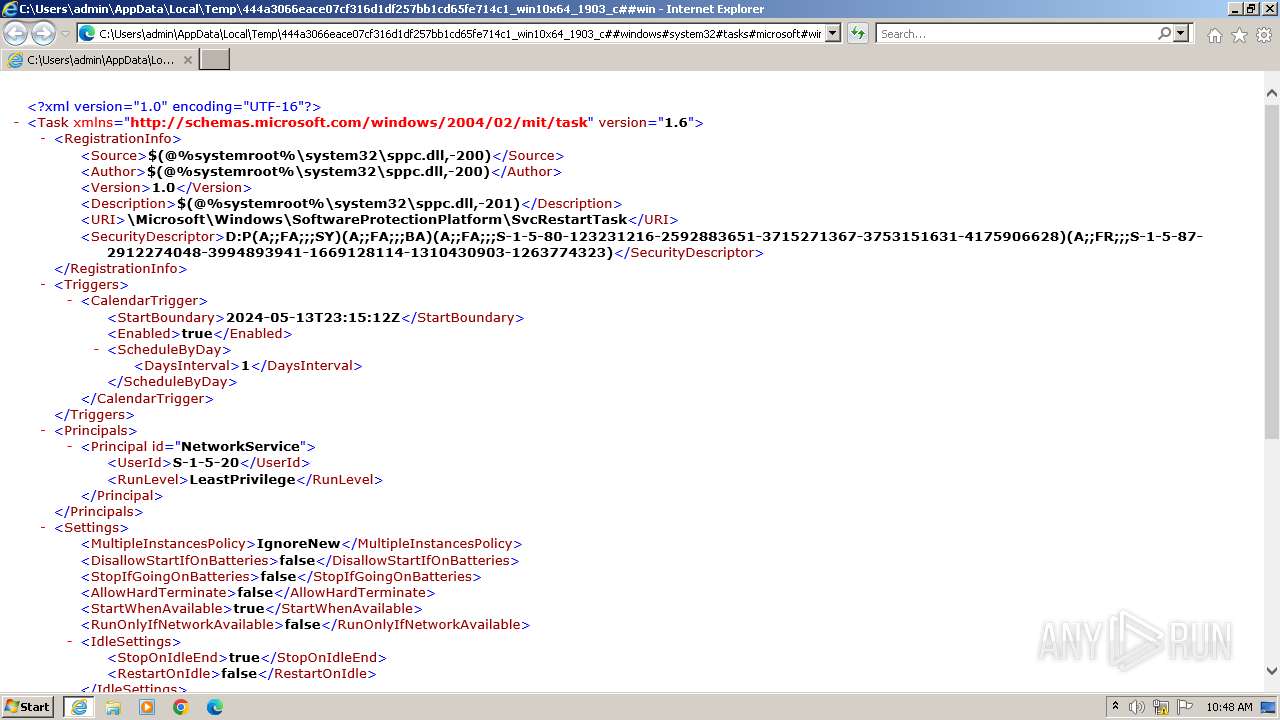
| TaskVersion: | 1.6 |
|---|---|
| TaskXmlns: | http://schemas.microsoft.com/windows/2004/02/mit/task |
| TaskRegistrationInfoSource: | $(@%systemroot%\system32\sppc.dll,-200) |
| TaskRegistrationInfoAuthor: | $(@%systemroot%\system32\sppc.dll,-200) |
| TaskRegistrationInfoVersion: | 1 |
| TaskRegistrationInfoDescription: | $(@%systemroot%\system32\sppc.dll,-201) |
| TaskRegistrationInfoUri: | \Microsoft\Windows\SoftwareProtectionPlatform\SvcRestartTask |
| TaskRegistrationInfoSecurityDescriptor: | D:P(A;;FA;;;SY)(A;;FA;;;BA)(A;;FA;;;S-1-5-80-123231216-2592883651-3715271367-3753151631-4175906628)(A;;FR;;;S-1-5-87-2912274048-3994893941-1669128114-1310430903-1263774323) |
| TaskTriggersCalendarTriggerStartBoundary: | 2024:05:13 23:15:12Z |
| TaskTriggersCalendarTriggerEnabled: | |
| TaskTriggersCalendarTriggerScheduleByDayDaysInterval: | 1 |
| TaskPrincipalsPrincipalId: | NetworkService |
| TaskPrincipalsPrincipalUserId: | S-1-5-20 |
| TaskPrincipalsPrincipalRunLevel: | LeastPrivilege |
| TaskSettingsMultipleInstancesPolicy: | IgnoreNew |
| TaskSettingsDisallowStartIfOnBatteries: | - |
| TaskSettingsStopIfGoingOnBatteries: | - |
| TaskSettingsAllowHardTerminate: | - |
| TaskSettingsStartWhenAvailable: | |
| TaskSettingsRunOnlyIfNetworkAvailable: | - |
| TaskSettingsIdleSettingsStopOnIdleEnd: | |
| TaskSettingsIdleSettingsRestartOnIdle: | - |
| TaskSettingsAllowStartOnDemand: | |
| TaskSettingsEnabled: | |
| TaskSettingsHidden: | |
| TaskSettingsRunOnlyIfIdle: | - |
| TaskSettingsDisallowStartOnRemoteAppSession: | - |
| TaskSettingsUseUnifiedSchedulingEngine: | |
| TaskSettingsWakeToRun: | - |
| TaskSettingsExecutionTimeLimit: | PT0S |
| TaskSettingsPriority: | 7 |
| TaskSettingsRestartOnFailureInterval: | PT1M |
| TaskSettingsRestartOnFailureCount: | 3 |
| TaskActionsContext: | NetworkService |
| TaskActionsComHandlerClassId: | {B1AEBB5D-EAD9-4476-B375-9C3ED9F32AFC} |
| TaskActionsComHandlerData: | timer |
Total processes
50
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4024 CREDAT:78849 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
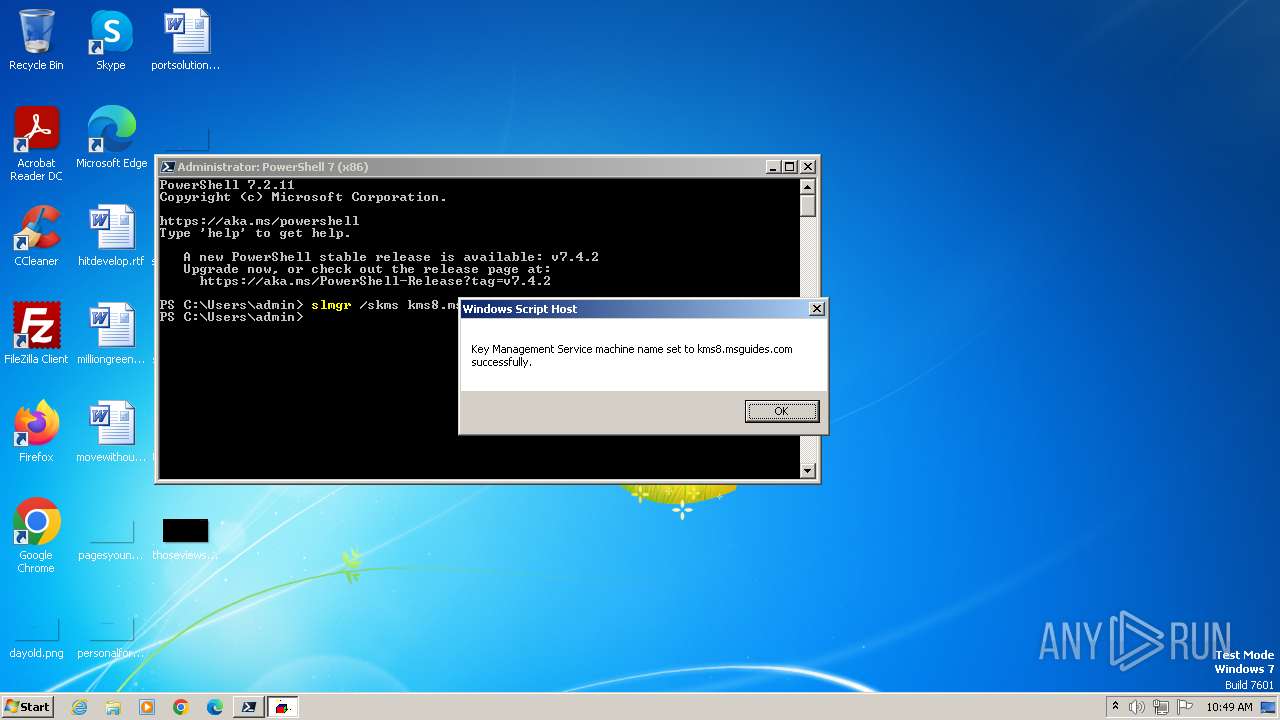
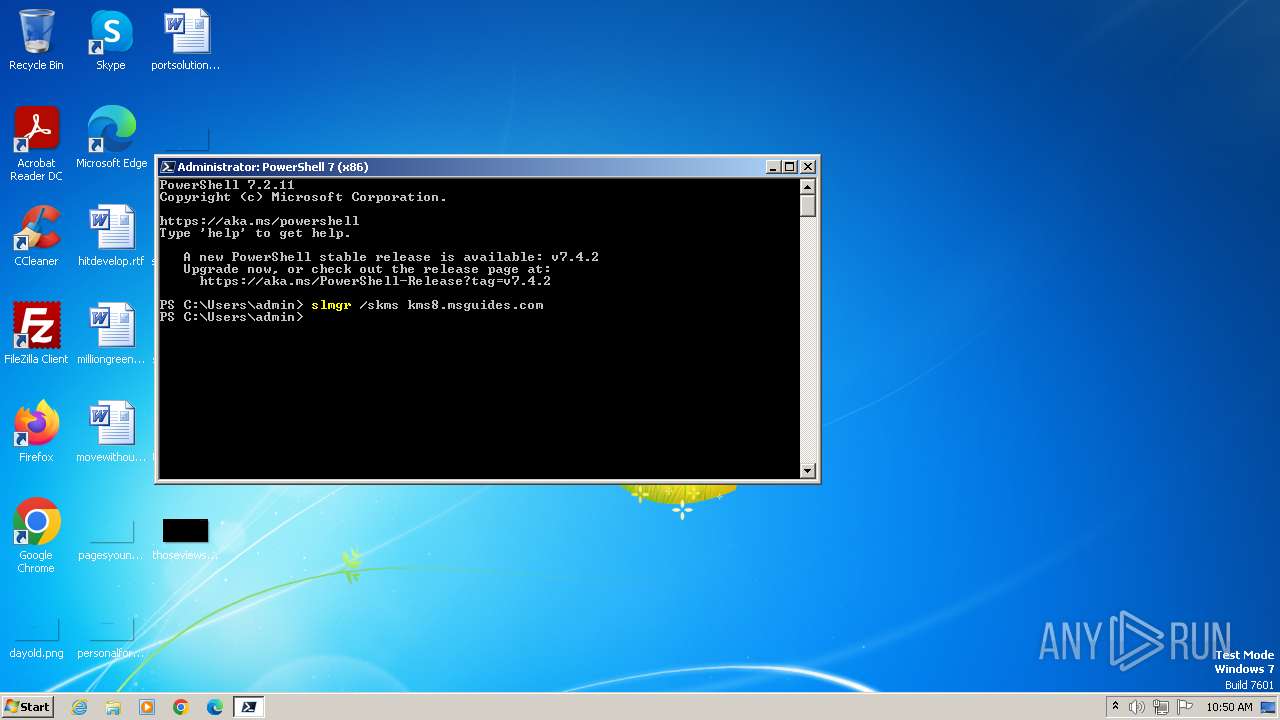
| 848 | "C:\Windows\System32\WScript.exe" "C:\Windows\system32\slmgr.vbs" /skms kms8.msguides.com | C:\Windows\System32\wscript.exe | — | pwsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1332 | "C:\Windows\System32\WScript.exe" "C:\Windows\system32\slmgr.vbs" /skms kms8.msguides.com | C:\Windows\System32\wscript.exe | — | pwsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 2147942405 Version: 5.8.7600.16385 Modules
| |||||||||||||||
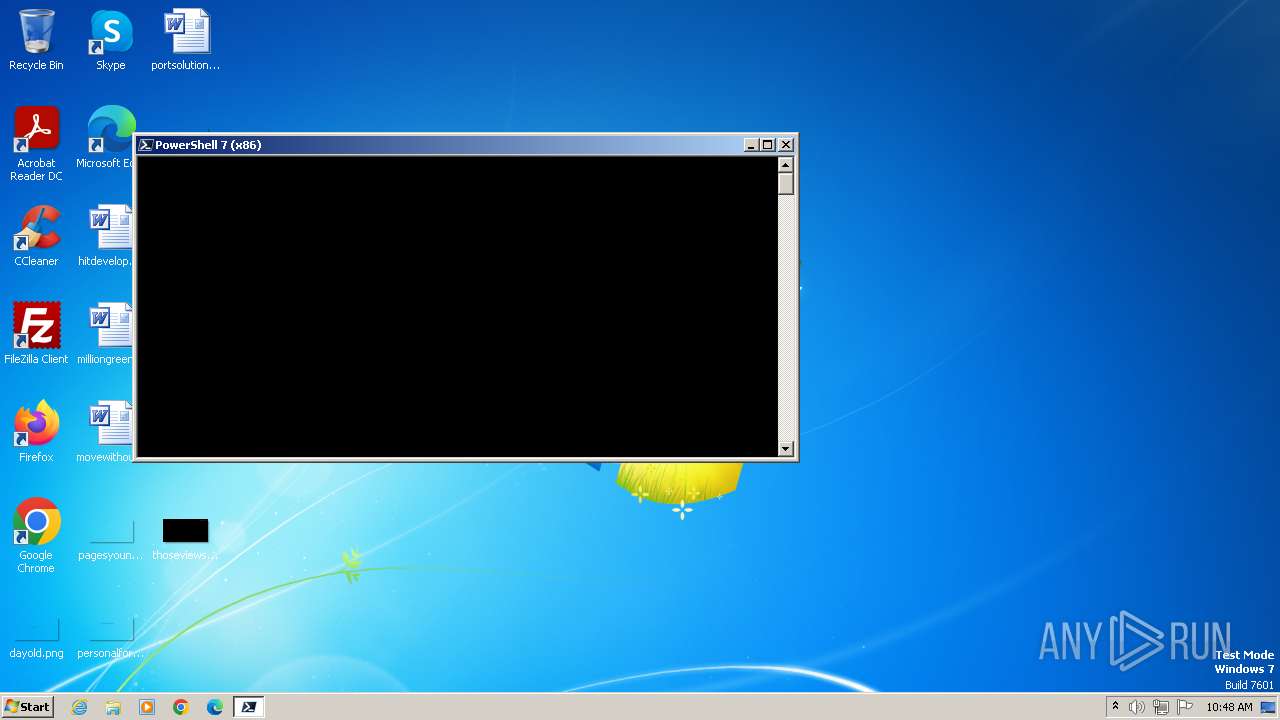
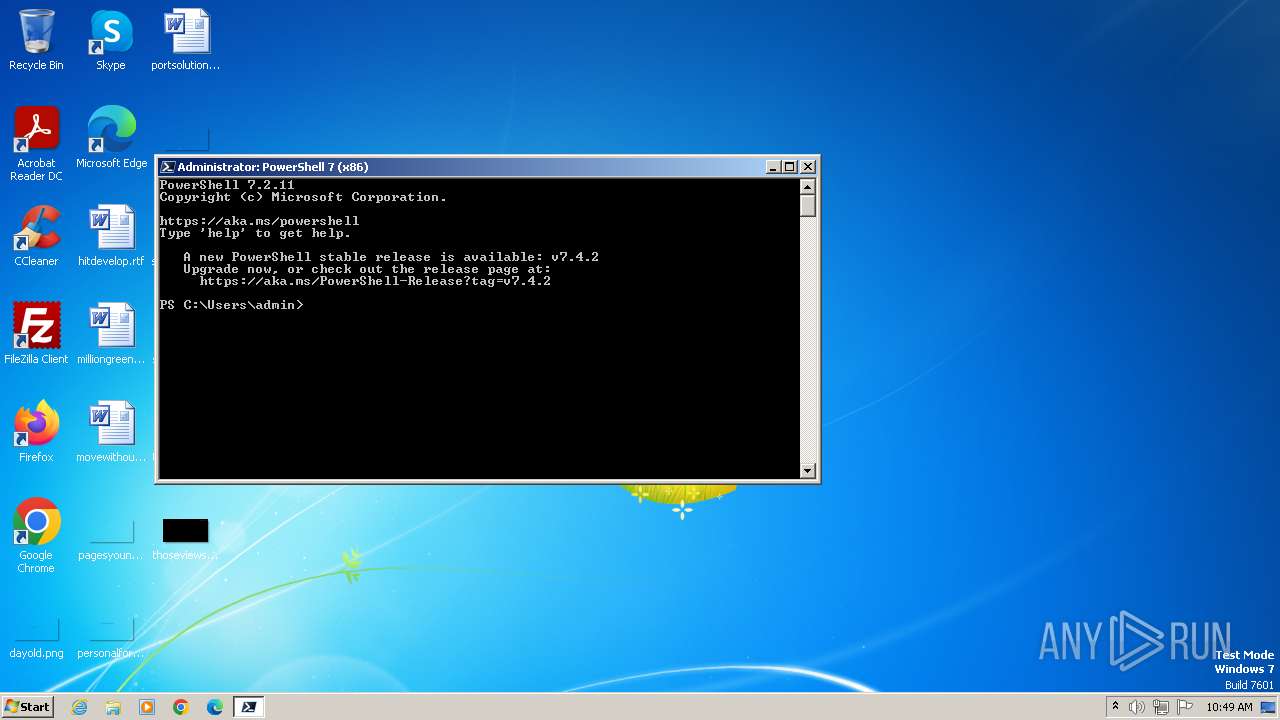
| 1480 | "C:\Program Files\PowerShell\7\pwsh.exe" -WorkingDirectory ~ | C:\Program Files\PowerShell\7\pwsh.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: pwsh Version: 7.2.11.500 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\PowerShell\7\pwsh.exe" -WorkingDirectory ~ | C:\Program Files\PowerShell\7\pwsh.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: pwsh Exit code: 3221225786 Version: 7.2.11.500 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | "C:\Windows\System32\WScript.exe" "C:\Windows\system32\slmgr.vbs" /skms | C:\Windows\System32\wscript.exe | — | pwsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3980 | "C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE" /verb open C:\Users\admin\AppData\Local\Temp\444a3066eace07cf316d1df257bb1cd65fe714c1_win10x64_1903_c##windows#system32#tasks#microsoft#windows#softwareprotectionplatform#svcrestarttask(0)_files.xml | C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: XML Editor Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 4024 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | MSOXMLED.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4064 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4024 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
27 210
Read events
26 890
Write events
267
Delete events
53
Modification events
| (PID) Process: | (3980) MSOXMLED.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3980) MSOXMLED.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3980) MSOXMLED.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4024) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4024) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (4024) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31106531 | |||
| (PID) Process: | (4024) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4024) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31106531 | |||
| (PID) Process: | (4024) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4024) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
0
Suspicious files
27
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1812 | pwsh.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qzt3dahv.rtb.psm1 | — | |
MD5:— | SHA256:— | |||
| 4024 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 4024 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2E52D3A37A3C033D.TMP | binary | |
MD5:7FF1DE871AD49586542019AD94DF50E5 | SHA256:AA986F7014B1FB8D2DBEBF14194CF41F04A4F4A564DD22F8D2D9CB2217737C9D | |||
| 4024 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1812 | pwsh.exe | C:\Users\admin\AppData\Local\Microsoft\PowerShell\7.2.11\update1_v7.4.2_2024-04-12 | — | |
MD5:— | SHA256:— | |||
| 4024 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 4024 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{0EE6F99D-11D7-11EF-9E36-12A9866C77DE}.dat | binary | |
MD5:CB8B1AD58E77AF3DB12F70570D4A0BD0 | SHA256:7066D5FACCA8B76F6C3D963C73656F02DE5E24788891F566F22BDC8EC2240C08 | |||
| 4024 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4E50FE3FB3921D94.TMP | binary | |
MD5:DA4CBC3A7D82C7200C16B74A7EBFA45D | SHA256:1019B2F1B8F3F642C66E5A31895A35ED1163944F1E21EE1976E97E266C422DF8 | |||
| 4024 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF6BF1B3E94D32D13.TMP | binary | |
MD5:21929A21BE99759F88E47D2FCBE41F3E | SHA256:CA97061469667110C2FA5A6E8693DE131E0625E38EA96088EF8C60CE62F3B848 | |||
| 4024 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD8CB6CE4344F8B7F.TMP | gmc | |
MD5:205C7F25DBD573683A2BF334A44BCFEF | SHA256:DF74CCB84570BFE22A7CE02FDC17B1D8F4D7293901AA4A01B05A76D865478284 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
17
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4024 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c1a4deebb02290fd | unknown | — | — | unknown |
4024 | iexplore.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?210b99e4fbc8d7fd | unknown | — | — | unknown |
4024 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
— | — | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f33259cc05673396 | unknown | — | — | unknown |
4024 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4024 | iexplore.exe | 184.86.251.19:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4024 | iexplore.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
4024 | iexplore.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
4024 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1812 | pwsh.exe | 23.201.217.150:443 | aka.ms | Akamai International B.V. | US | unknown |
1812 | pwsh.exe | 52.239.160.36:443 | pscoretestdata.blob.core.windows.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4024 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
aka.ms |
| whitelisted |
pscoretestdata.blob.core.windows.net |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
dc.services.visualstudio.com |
| whitelisted |
Threats
Process | Message |
|---|---|
pwsh.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 1812. Message ID: [0x2509].
|
pwsh.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 1480. Message ID: [0x2509].
|