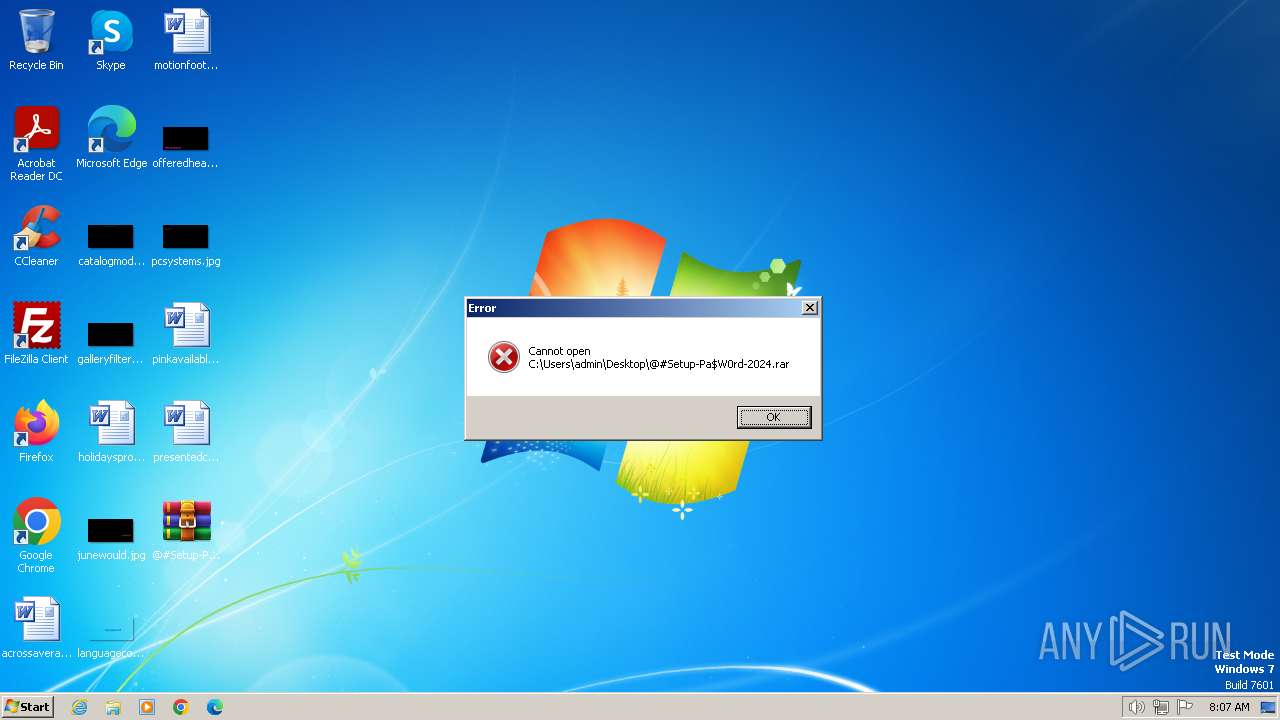
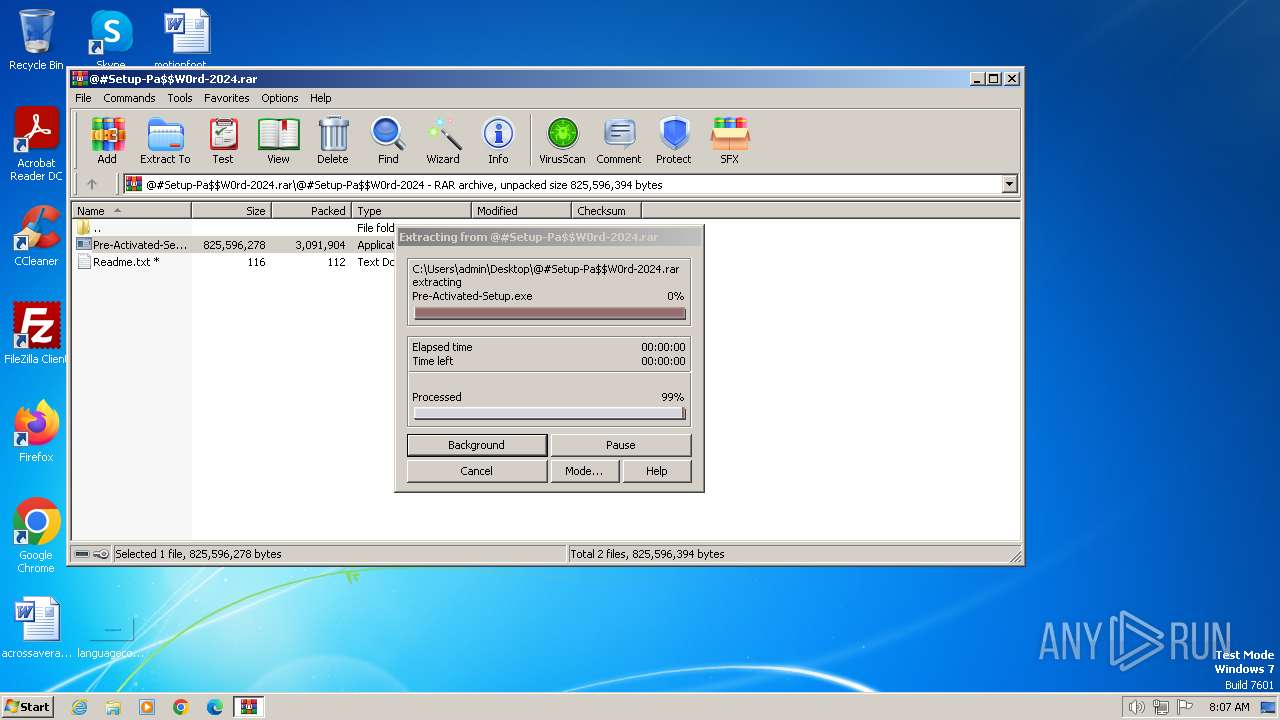
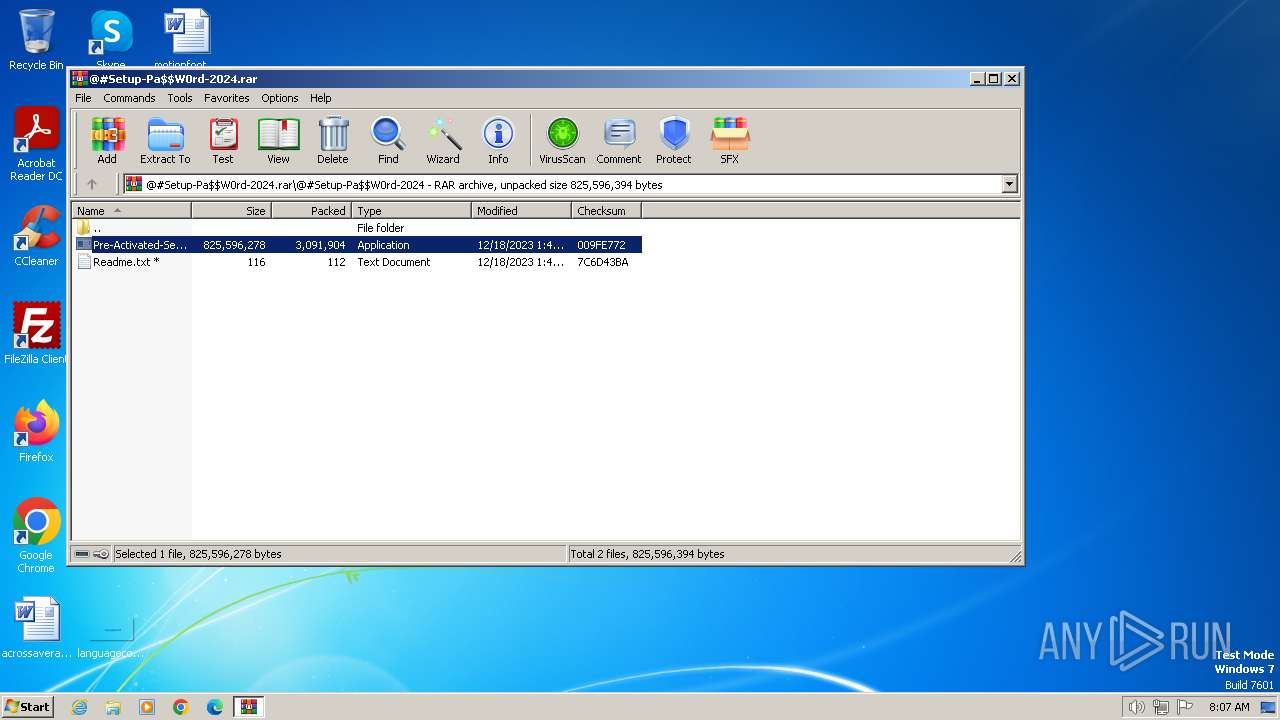
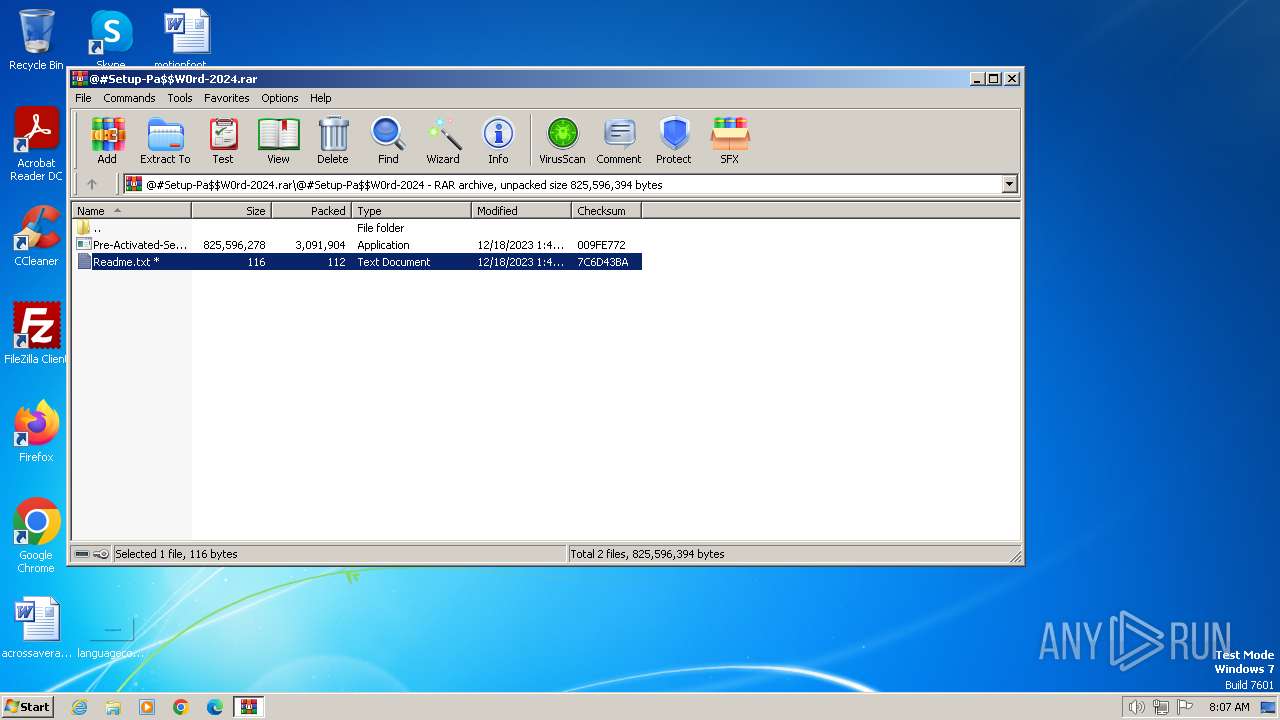
| File name: | @#Setup-Pa$W0rd-2024.rar |
| Full analysis: | https://app.any.run/tasks/cb4e7b42-648a-4183-a213-ba9f2620a6d2 |
| Verdict: | Malicious activity |
| Analysis date: | January 02, 2024, 08:07:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
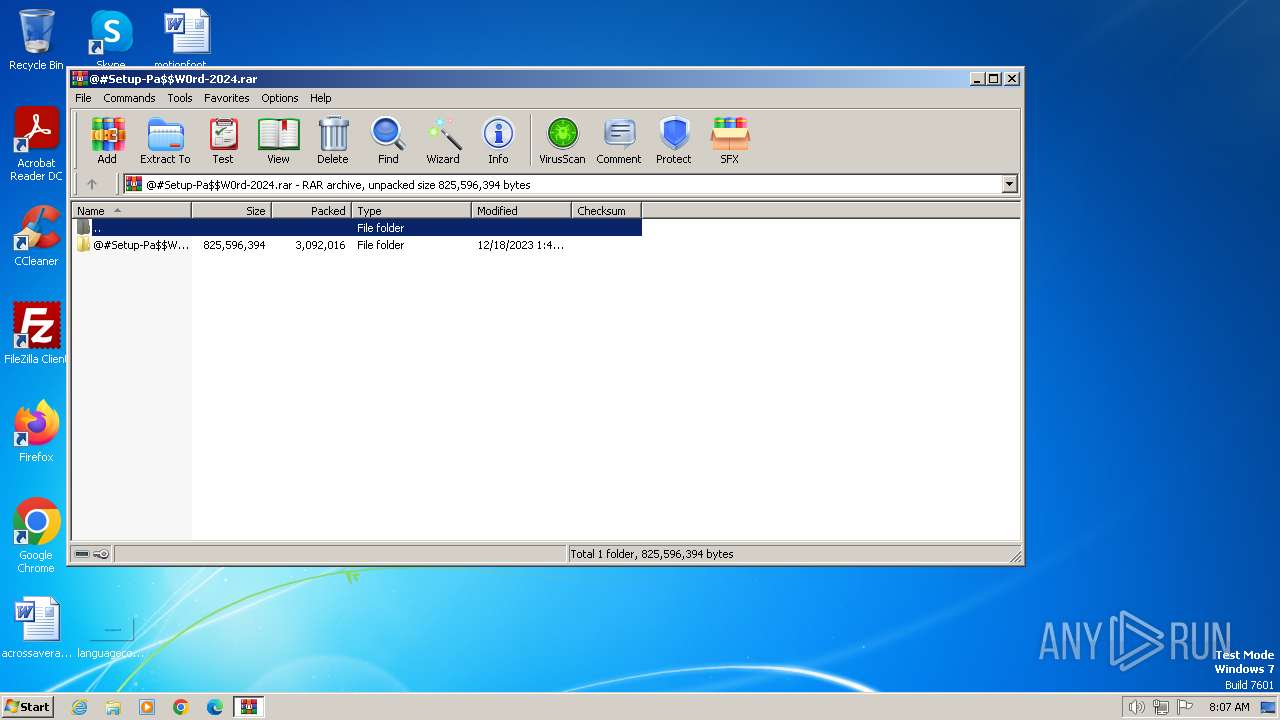
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F4A4061F55E6901FA6CC579949BD0896 |
| SHA1: | A65C360584136D9B1B634AEBA77A34C2F67B0315 |
| SHA256: | 445776C19EEAC7092E656AE16E733D7097922231872DA1EDB9BE65A2DB13C2E0 |
| SSDEEP: | 98304:HYbZuNpMroDr12w6HW9hcN1wOyVWBNzmwbAdUr5J5rNc6WNn3IWt2HboHzJ5c5+A:EGhkwJA |
MALICIOUS
No malicious indicators.SUSPICIOUS
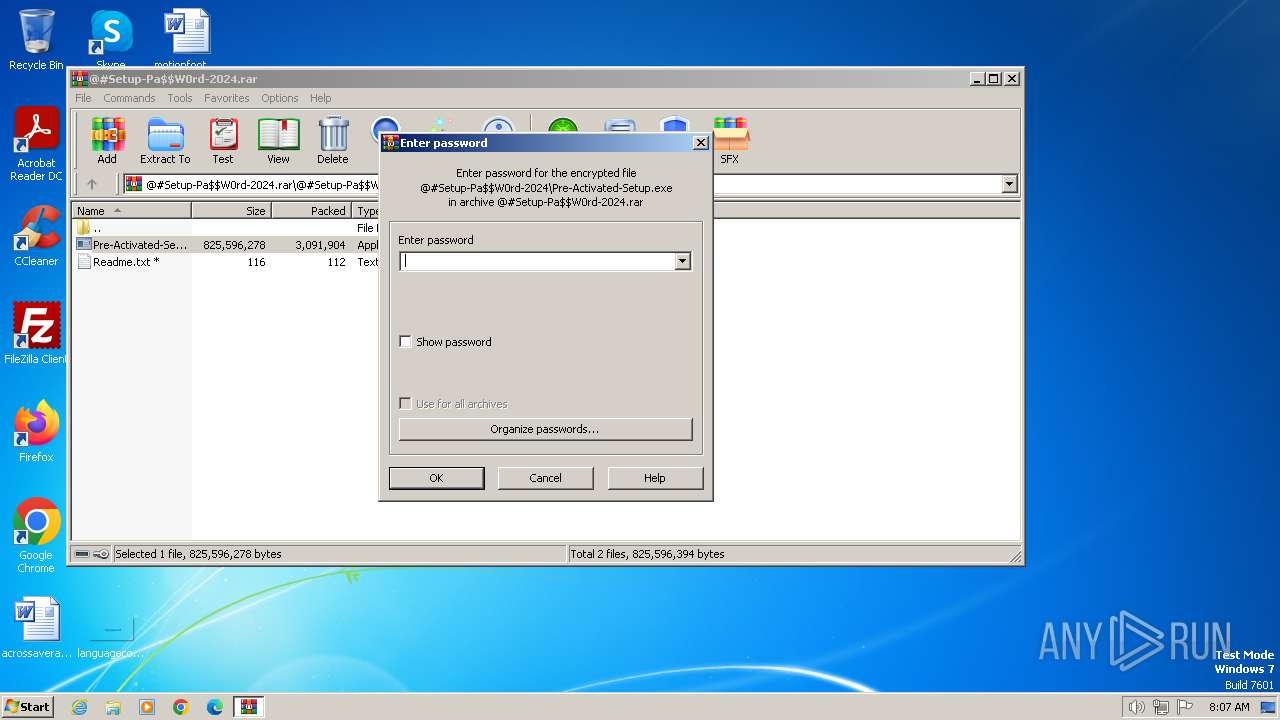
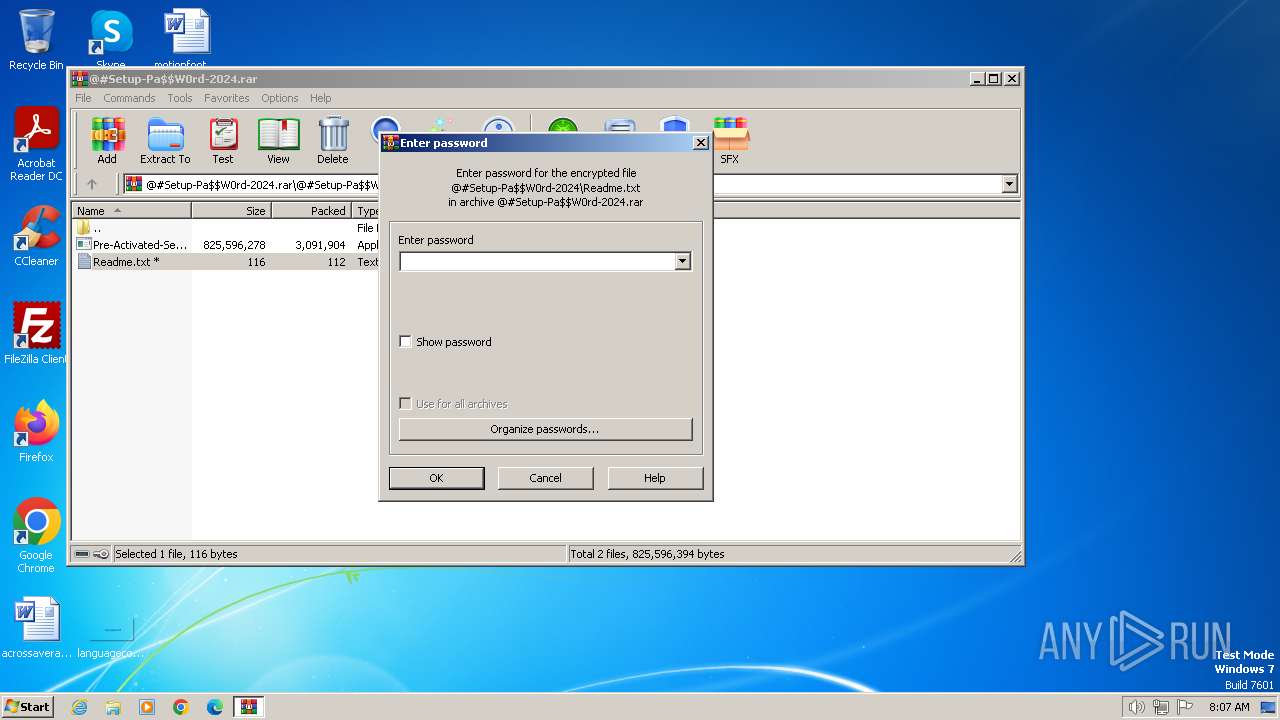
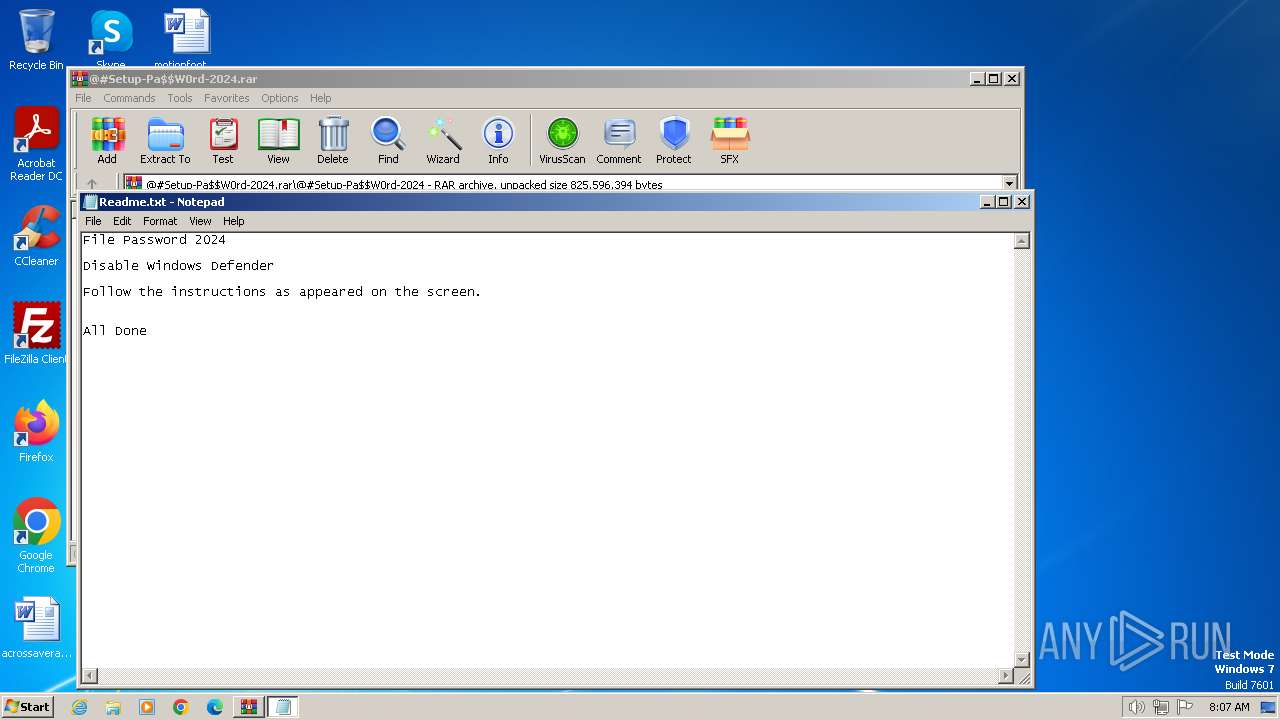
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 2080)
INFO
Reads the computer name
- Pre-Activated-Setup.exe (PID: 268)
Checks supported languages
- Pre-Activated-Setup.exe (PID: 268)
Manual execution by a user
- WinRAR.exe (PID: 2080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
37
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\@#Setup-Pa$W0rd-2024.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
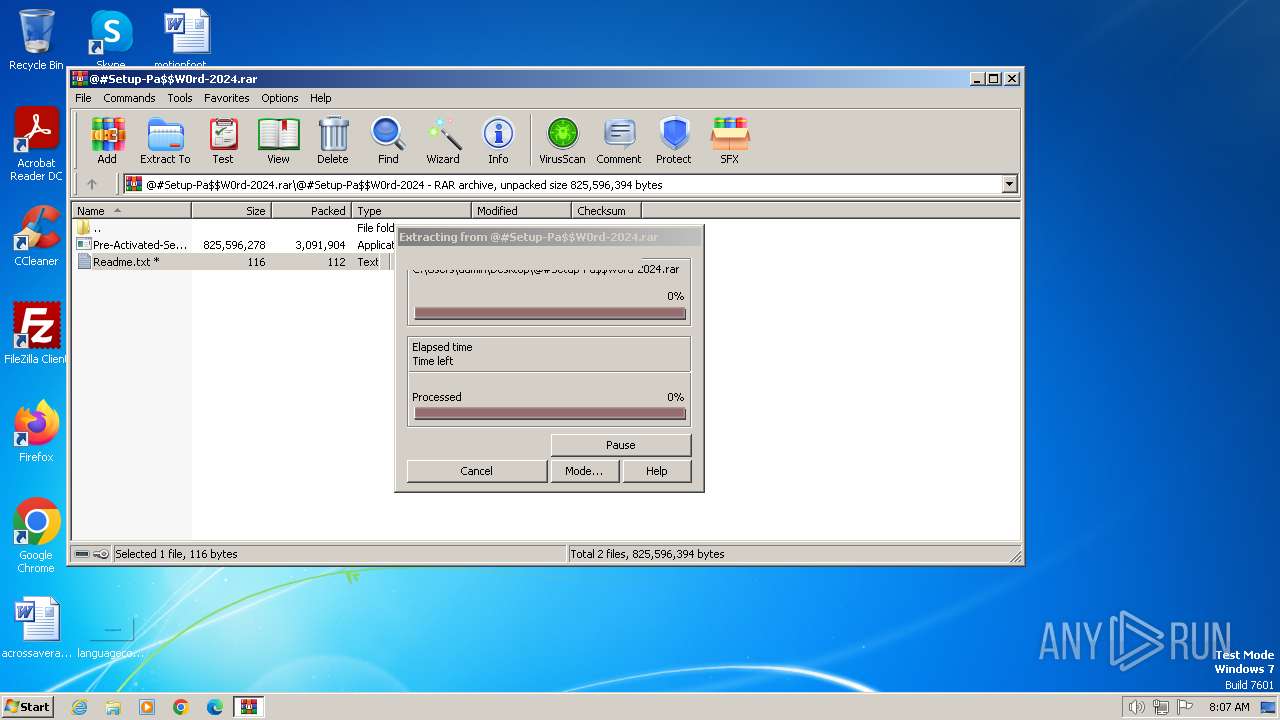
| 268 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2080.32878\@#Setup-Pa$W0rd-2024\Pre-Activated-Setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2080.32878\@#Setup-Pa$W0rd-2024\Pre-Activated-Setup.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1632 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIb2080.34280\Readme.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2080 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\@#Setup-Pa$W0rd-2024.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
1 963
Read events
1 935
Write events
28
Delete events
0
Modification events
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band56_0 |
Value: 38000000730100000402000000000000D4D0C8000000000000000000000000005C0104000000000039000000B40200000000000001000000 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band56_1 |
Value: 38000000730100000500000000000000D4D0C8000000000000000000000000008C010C0000000000160000002A0000000000000002000000 | |||
| (PID) Process: | (116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band56_2 |
Value: 38000000730100000400000000000000D4D0C800000000000000000000000000AC0107000000000016000000640000000000000003000000 | |||
| (PID) Process: | (2080) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2080 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2080.32878\@#Setup-Pa$W0rd-2024\Pre-Activated-Setup.exe | — | |
MD5:— | SHA256:— | |||
| 2080 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2080.32878\@#Setup-Pa$W0rd-2024\Readme.txt | text | |
MD5:AEAA412966CBE5D05A83D1AC60C5FC84 | SHA256:D5CDEE14FED046A1BD4AC755861CA2391A7604A8EF0056CE5A97F83E0F653910 | |||
| 2080 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2080.34280\Readme.txt | text | |
MD5:AEAA412966CBE5D05A83D1AC60C5FC84 | SHA256:D5CDEE14FED046A1BD4AC755861CA2391A7604A8EF0056CE5A97F83E0F653910 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
9
Threats
9
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
biznesroit.pw |
| unknown |
killredls.pw |
| unknown |
keewoolas.pw |
| unknown |
moskhoods.pw |
| unknown |
dayzilons.pw |
| unknown |
revivalsecularas.pw |
| unknown |
steycools.pw |
| unknown |
bloockflad.pw |
| unknown |
bookgames.pw |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |