| File name: | %A1%BE%C3%E2%B7%D1%D0͡%BF.exe |
| Full analysis: | https://app.any.run/tasks/c462a22f-5ffa-4252-9ed5-1131d3084ebc |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2019, 06:53:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5C7B75B53828D1EFE56126A7B0E8E005 |
| SHA1: | 6BD42BEA4229FFEAA18F28317410050802A7C904 |
| SHA256: | 444C59CB8B637414D51E188D5CD6DB3C84F55C6AD89FC8D85506B2BD67D8090D |
| SSDEEP: | 98304:T5J+E0SCxIk7zumFWAs/fyIgdElb3EIaFFpPVKh9uN8L4c7eBoLb+:lYE0SCI4rbECIwBbiL4c7N+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads internet explorer settings
- bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe (PID: 1252)
INFO
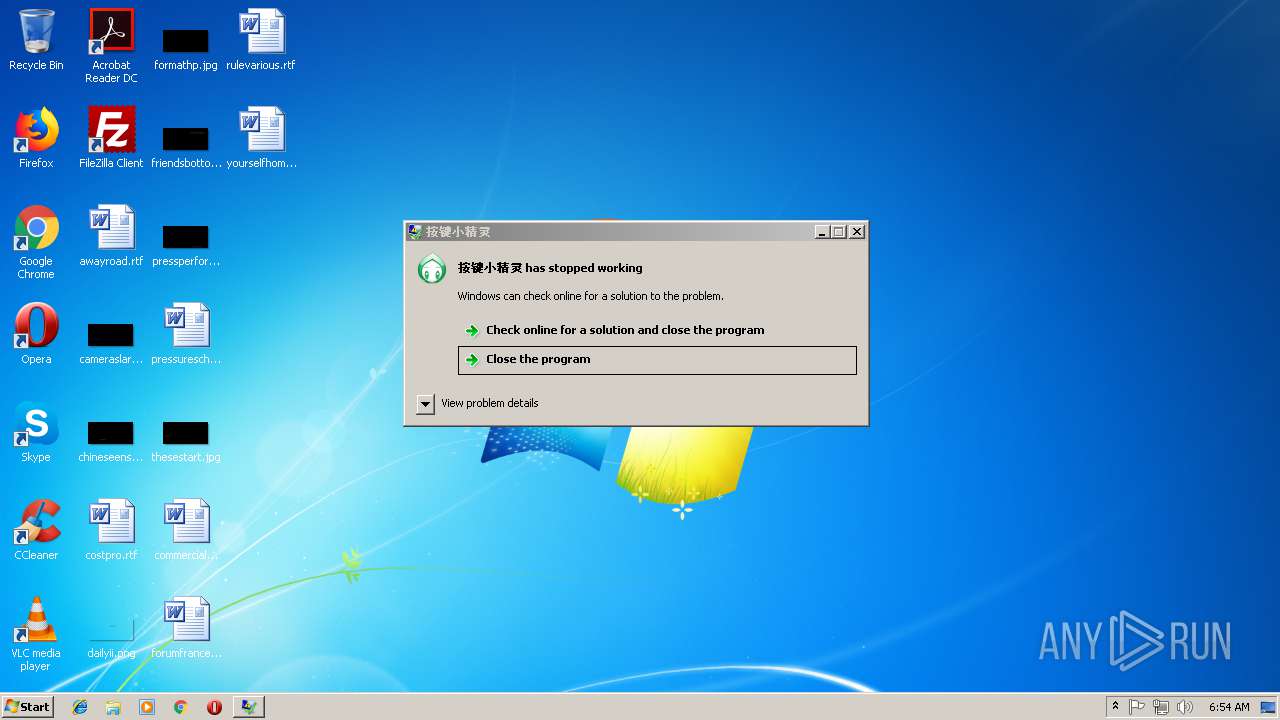
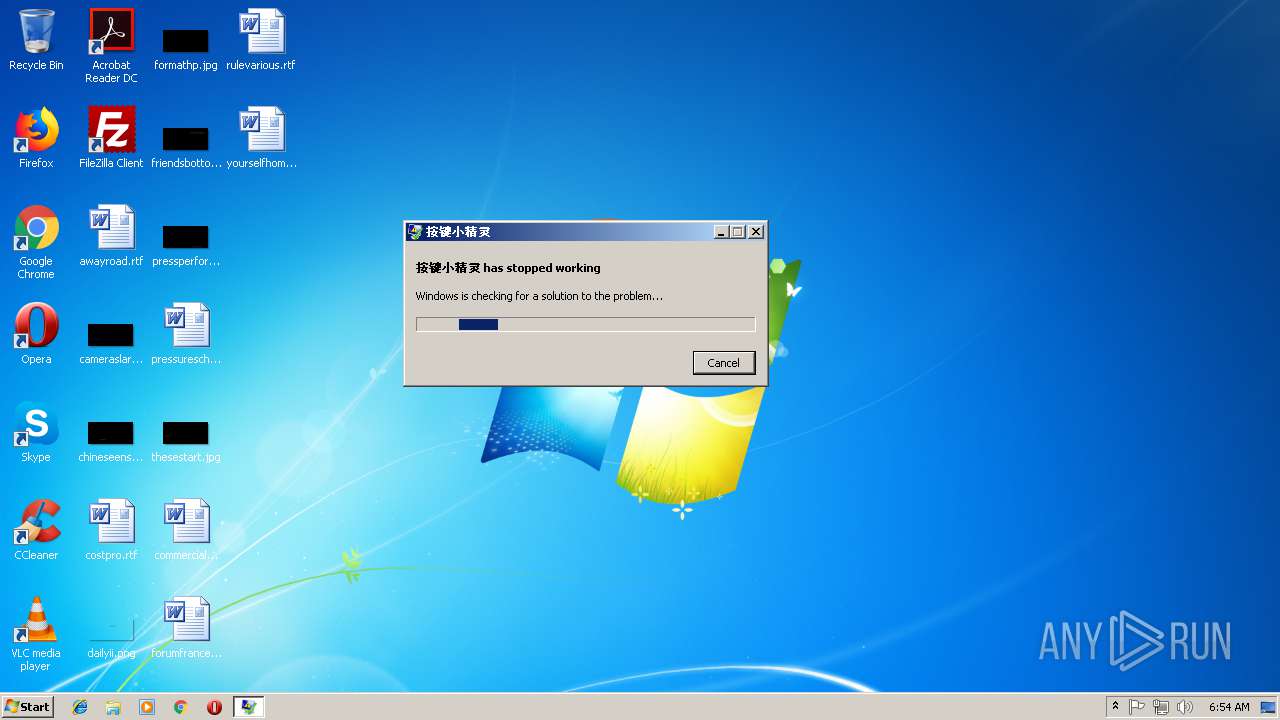
Application was crashed
- bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe (PID: 1252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:09:08 07:34:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 2342400 |
| InitializedDataSize: | 1075712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1610a7 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2014.0.5.17762 |
| ProductVersionNumber: | 2014.0.5.17762 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | 按键小精灵 (C) 2001 - 2017 |
| FileDescription: | 按键小精灵 |
| FileVersion: | 2014.0.5.17762 |
| InternalName: | MyMacro.exe |
| LegalCopyright: | Copyright (C) 2001 - 2017 |
| OriginalFileName: | MyMacro.exe |
| ProductName: | 按键小精灵 |
| ProductVersion: | 2014.0.5.17762 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Sep-2017 05:34:43 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| CompanyName: | 按键小精灵 (C) 2001 - 2017 |
| FileDescription: | 按键小精灵 |
| FileVersion: | 2014.0.5.17762 |
| InternalName: | MyMacro.exe |
| LegalCopyright: | Copyright (C) 2001 - 2017 |
| OriginalFilename: | MyMacro.exe |
| ProductName: | 按键小精灵 |
| ProductVersion: | 2014.0.5.17762 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 08-Sep-2017 05:34:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0023BD9A | 0x0023BE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61731 |
.rdata | 0x0023D000 | 0x0007C808 | 0x0007CA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16889 |
.data | 0x002BA000 | 0x00016284 | 0x0000C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.05743 |
.tls | 0x002D1000 | 0x00000002 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x002D2000 | 0x00039A5C | 0x00039C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.31609 |
.reloc | 0x0030C000 | 0x00043B80 | 0x00043C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.103 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05194 | 866 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.382 | 67624 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.73086 | 21640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 4.61991 | 16936 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 4.96807 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 5.0163 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 5.99663 | 256 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 6.489 | 1092 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.37819 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
10 | 5.21586 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
Total processes
42
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1252 | "C:\Users\admin\AppData\Local\Temp\bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe" | C:\Users\admin\AppData\Local\Temp\bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | explorer.exe | ||||||||||||
User: admin Company: 按键小精灵 (C) 2001 - 2017 Integrity Level: HIGH Description: 按键小精灵 Exit code: 3221225477 Version: 2014.0.5.17762 Modules
| |||||||||||||||
| 2516 | "C:\Windows\System32\PING.EXE" www.baidu.com -n 2 | C:\Windows\System32\PING.EXE | — | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2536 | "C:\Windows\System32\PING.EXE" www.baidu.com -n 2 | C:\Windows\System32\PING.EXE | — | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3188 | "C:\Users\admin\AppData\Local\Temp\bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe" | C:\Users\admin\AppData\Local\Temp\bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | — | explorer.exe | |||||||||||
User: admin Company: 按键小精灵 (C) 2001 - 2017 Integrity Level: MEDIUM Description: 按键小精灵 Exit code: 3221226540 Version: 2014.0.5.17762 Modules
| |||||||||||||||
| 4080 | "C:\Windows\System32\PING.EXE" www.baidu.com -n 2 | C:\Windows\System32\PING.EXE | — | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
162
Read events
142
Write events
20
Delete events
0
Modification events
| (PID) Process: | (1252) bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1252) bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1252) bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bd336e27-0d47-4b64-8256-dd9dfc09d8e3_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1252) bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bd336e27-0d47-4b64-8256-dd9dfc09d8e3_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1252) bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bd336e27-0d47-4b64-8256-dd9dfc09d8e3_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1252) bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bd336e27-0d47-4b64-8256-dd9dfc09d8e3_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1252) bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bd336e27-0d47-4b64-8256-dd9dfc09d8e3_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1252) bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bd336e27-0d47-4b64-8256-dd9dfc09d8e3_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1252) bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bd336e27-0d47-4b64-8256-dd9dfc09d8e3_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1252) bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bd336e27-0d47-4b64-8256-dd9dfc09d8e3_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | C:\Users\admin\AppData\Local\Temp\adcon\mm\tmpad.xml | — | |
MD5:— | SHA256:— | |||
| 1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | C:\Users\admin\AppData\Local\Temp\QMLog\20190228.log | text | |
MD5:— | SHA256:— | |||
| 1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | C:\Users\admin\AppData\Local\Temp\ad-mymacro9.xml | binary | |
MD5:B4494A1E6F7528BACA56904D6944C36C | SHA256:EC36E69C20842DDCC31EB91B44C084C606B4BBA604F5A4D1A43997586B89CD63 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
9
DNS requests
5
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | GET | — | 117.27.139.134:80 | http://down.vrbrothers.com/qmacro/up_mymacro/liveupdate8.dat | CN | — | — | malicious |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | GET | — | 117.27.139.134:80 | http://soft.anjian.com/Include/BuildPage/AnJianBindingInstallPC.html | CN | — | — | malicious |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | POST | — | 117.27.139.134:80 | http://soft.anjian.com/Include/BuildPage/ExitAdXJL.shtml | CN | — | — | malicious |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | GET | — | 117.27.139.134:80 | http://soft.anjian.com/V2014V2/Config/ad-mymacro.xml | CN | — | — | malicious |
2316 | WerFault.exe | GET | — | 40.67.186.102:80 | http://watson.microsoft.com/StageOne/bd336e27-0d47-4b64-8256-dd9dfc09d8e3_exe/2014_0_5_17762/59b22bf3/bd336e27-0d47-4b64-8256-dd9dfc09d8e3_exe/2014_0_5_17762/59b22bf3/c0000005/00053110.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | POST | — | 117.27.139.134:80 | http://soft.anjian.com/Interface/BindingPC/BindingUpdate.aspx | CN | — | — | malicious |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | POST | — | 117.27.139.134:80 | http://soft.anjian.com/Interface/BindingPC/BindingUsing.aspx | CN | — | — | malicious |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | POST | — | 117.27.139.134:80 | http://soft.anjian.com/Interface/GetIP.aspx | CN | — | — | malicious |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | GET | — | 103.235.46.191:80 | http://hm.baidu.com/h.js?82d5c049236934007371777578c30be1 | HK | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | 117.27.139.134:80 | soft.anjian.com | Fuzhou | CN | malicious |
2316 | WerFault.exe | 40.67.186.102:80 | watson.microsoft.com | Microsoft Corporation | US | whitelisted |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | 103.235.46.191:80 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
soft.anjian.com |
| malicious |
down.vrbrothers.com |
| malicious |
www.baidu.com |
| whitelisted |
watson.microsoft.com |
| whitelisted |
hm.baidu.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2316 | WerFault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | A Network Trojan was detected | ET MALWARE User-Agent (Mozilla/4.0 (compatible)) |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | A Network Trojan was detected | ET MALWARE User-Agent (Mozilla/4.0 (compatible)) |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | A Network Trojan was detected | ET MALWARE User-Agent (Mozilla/4.0 (compatible)) |
1252 | bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | A Network Trojan was detected | ET MALWARE User-Agent (Mozilla/4.0 (compatible)) |
Process | Message |
|---|---|
bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | g_szDataPath: C:\Users\admin\AppData\Roaming\MyMacro\RKey.dat
|
bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | g_hEventFlag: 278, g_hEvent_CodeInfo: 284
|
bd336e27-0d47-4b64-8256-dd9dfc09d8e3.exe | g_pCodeFlag: 2450000, g_pCodeInfo: 2460000
|