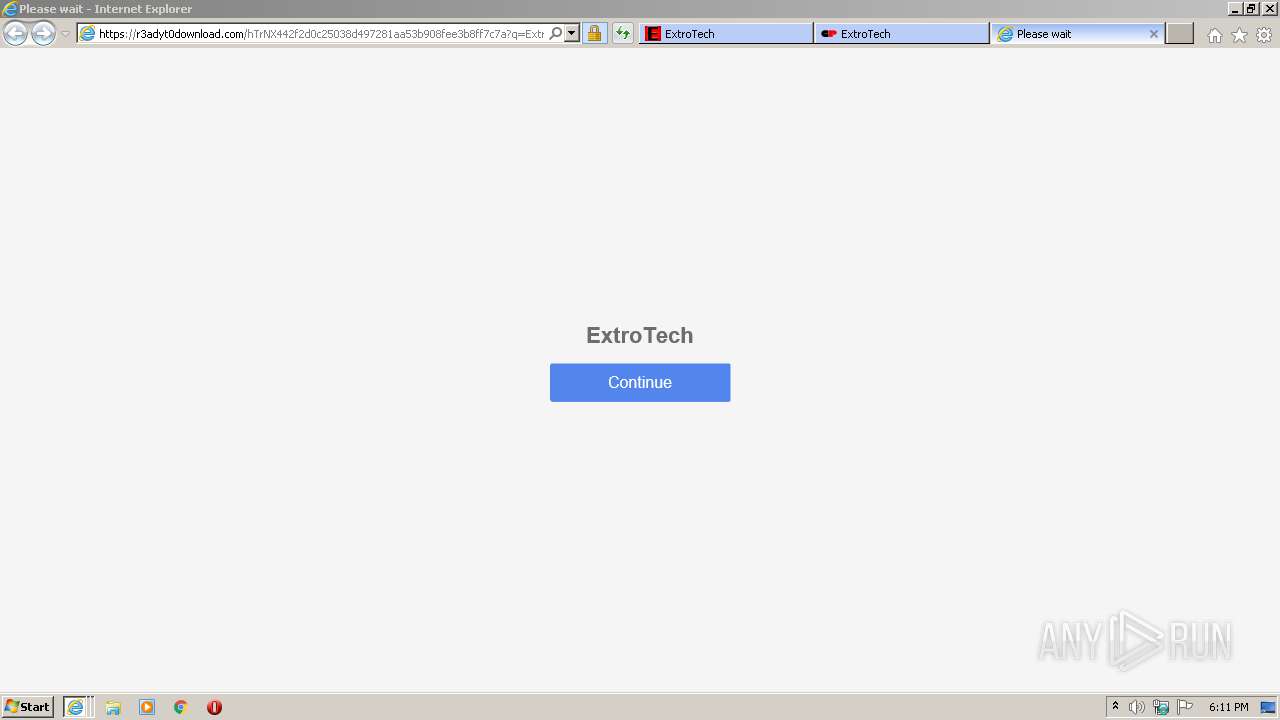
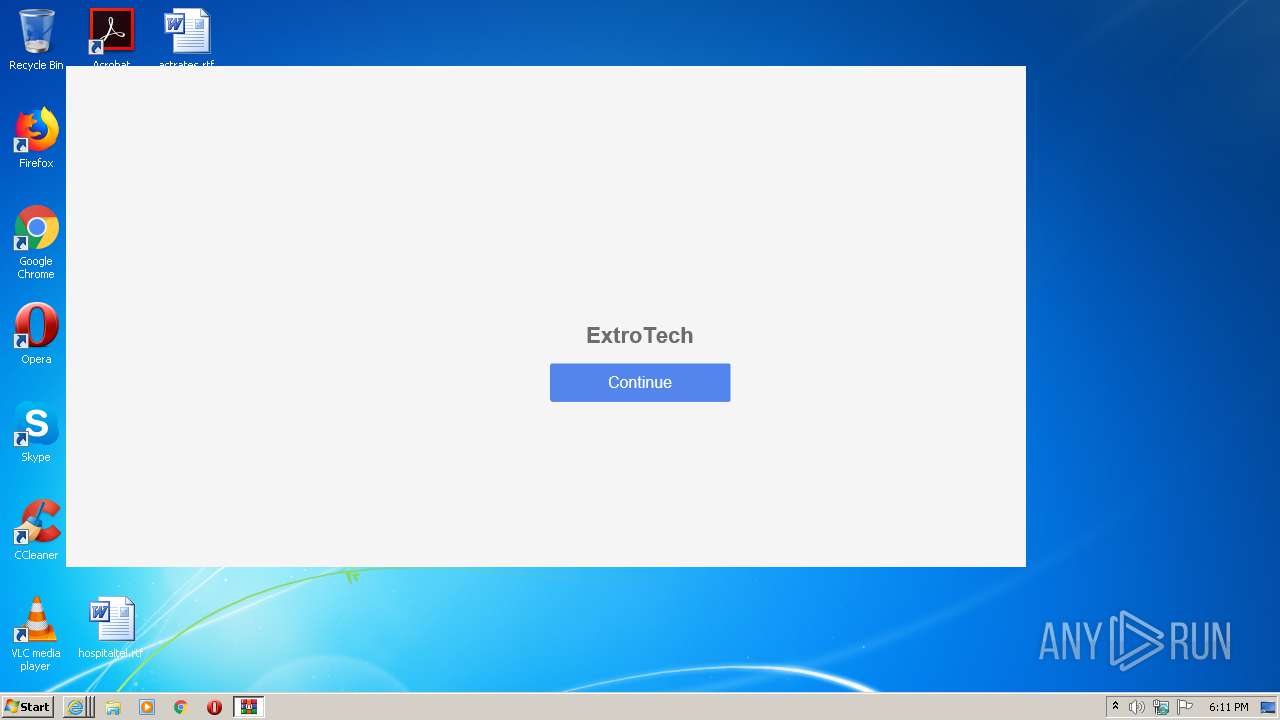
| URL: | https://extrotech.blogspot.com |
| Full analysis: | https://app.any.run/tasks/386fd552-45b6-4bdc-b530-24aa51404625 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2021, 17:10:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6EDAEB01BC51BCF5BA2922ABB0B14D34 |
| SHA1: | 0E1F4B7FD6AF641B1DB0414C8740D422EAA8ADE0 |
| SHA256: | 44383C32647F3726A1D8F6F9287FE0C3587A4A074DBDD87F4DD87FC4E102FC0C |
| SSDEEP: | 3:N8zRAEzKn:2iqKn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 2500)
Reads settings of System Certificates
- iexplore.exe (PID: 2500)
- iexplore.exe (PID: 3784)
Changes settings of System certificates
- iexplore.exe (PID: 2500)
Reads internet explorer settings
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 3100)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2500)
Application launched itself
- iexplore.exe (PID: 2500)
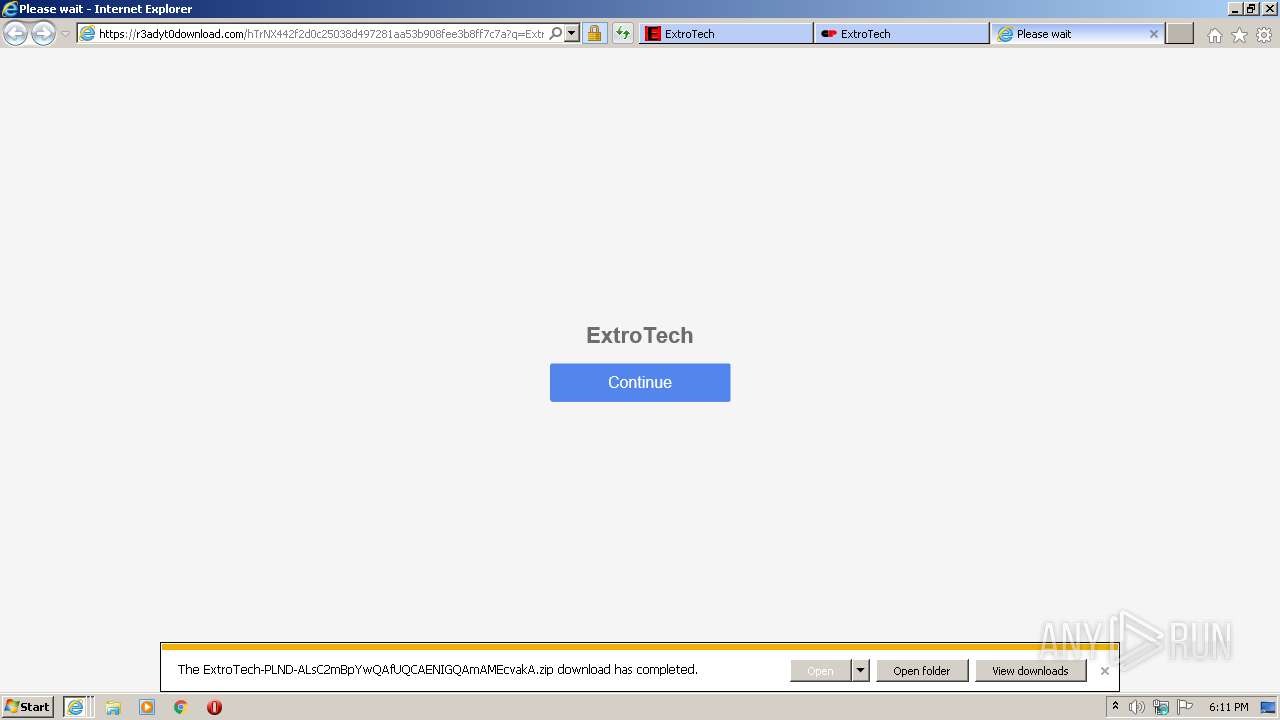
Creates files in the user directory
- iexplore.exe (PID: 3100)
- iexplore.exe (PID: 3784)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2332 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2500 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://extrotech.blogspot.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3100 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2500 CREDAT:2888971 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
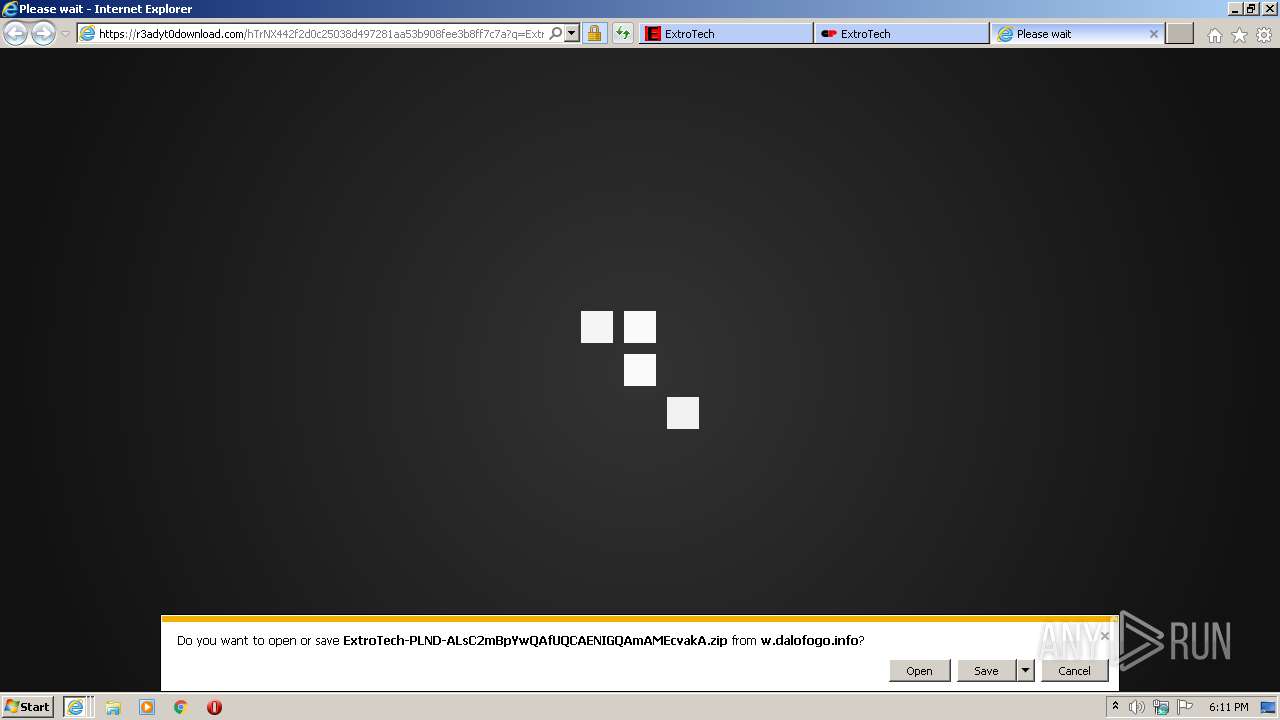
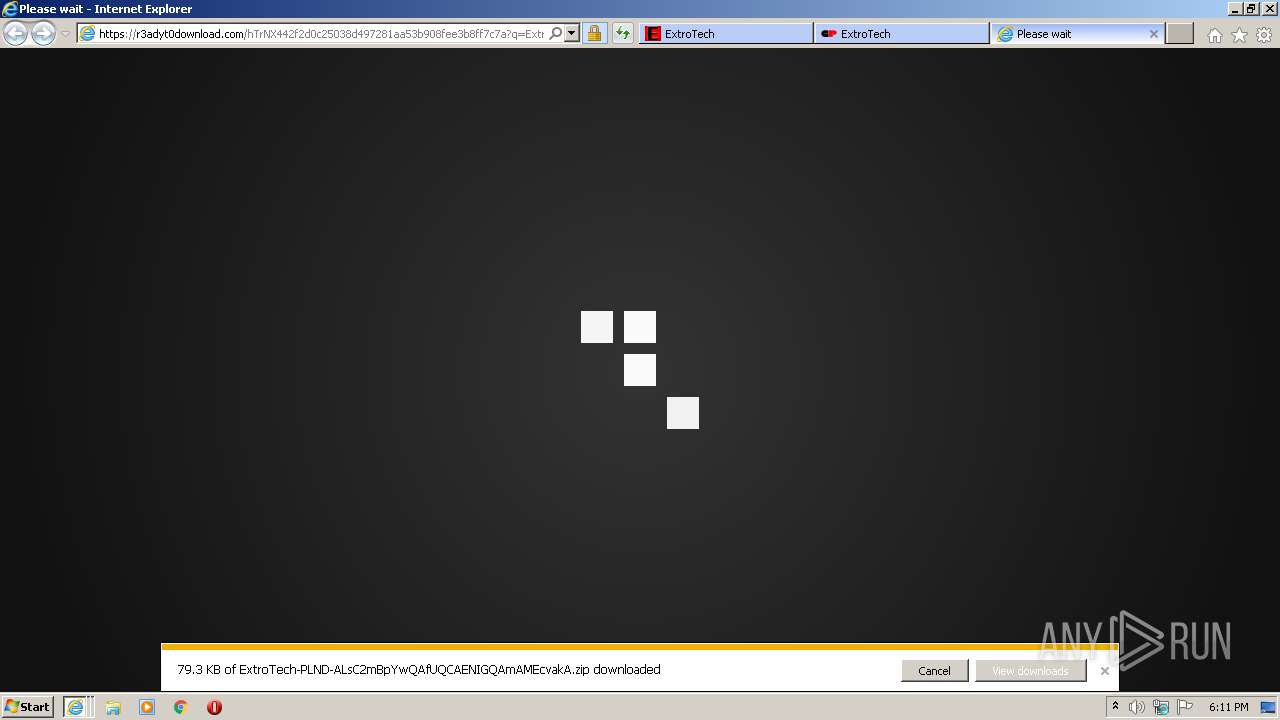
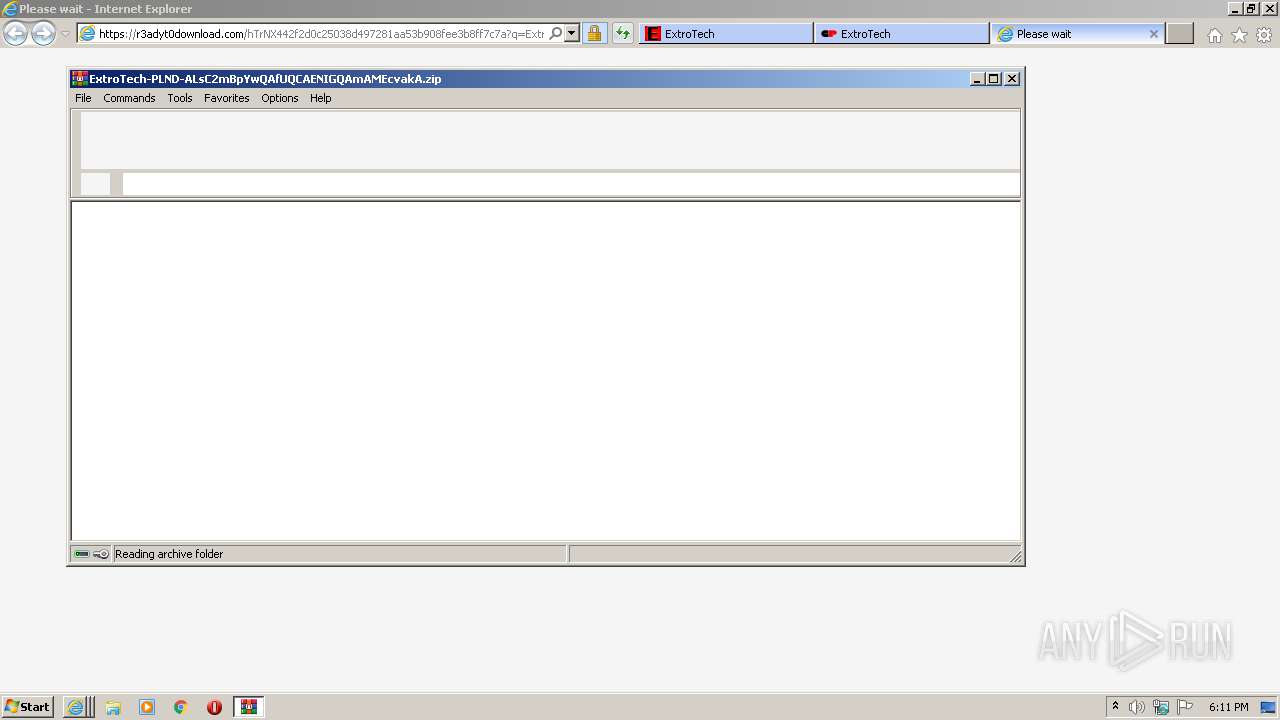
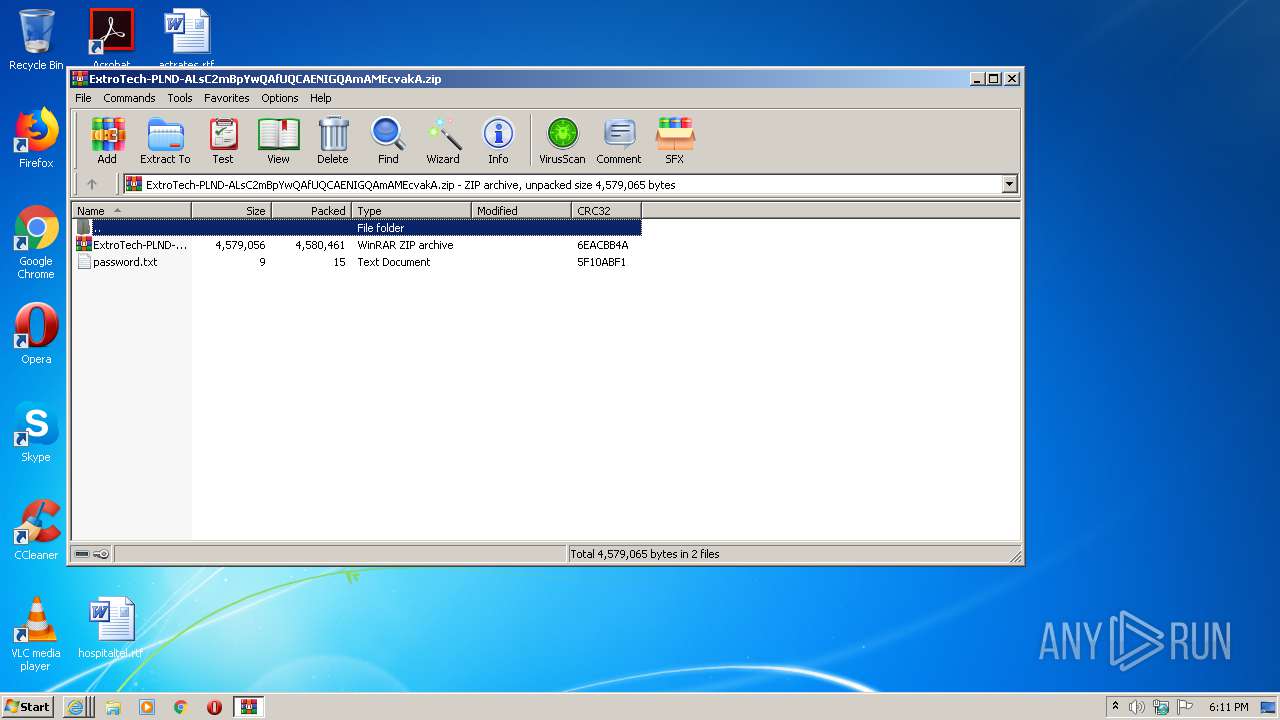
| 3216 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ExtroTech-PLND-ALsC2mBpYwQAfUQCAENIGQAmAMEcvakA.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3784 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2500 CREDAT:3347725 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 743
Read events
1 581
Write events
158
Delete events
4
Modification events
| (PID) Process: | (2500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2535296772 | |||
| (PID) Process: | (2500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30895168 | |||
| (PID) Process: | (2500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
119
Text files
78
Unknown types
60
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab1D3B.tmp | — | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar1D3C.tmp | — | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F2DDCD2B5F37625B82E81F4976CEE400_730E85E276148AD0B8D51532584D5522 | binary | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F2DDCD2B5F37625B82E81F4976CEE400_730E85E276148AD0B8D51532584D5522 | der | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\fortnite logo 2[1].PNG | image | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2CFA.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
129
DNS requests
53
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2332 | iexplore.exe | GET | 200 | 172.217.20.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCTDvaZSXoOygoAAAAA3JeE | US | der | 472 b | whitelisted |
2332 | iexplore.exe | GET | 200 | 172.217.20.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCED43httujs%2BXCgAAAADcj5E%3D | US | der | 471 b | whitelisted |
3784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAtIgyHhzCAgf0Woj6GgeOA%3D | US | der | 471 b | whitelisted |
3784 | iexplore.exe | GET | 200 | 2.22.118.168:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | GB | der | 1.16 Kb | whitelisted |
2332 | iexplore.exe | GET | 200 | 172.217.20.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCTDvaZSXoOygoAAAAA3JeE | US | der | 472 b | whitelisted |
3784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3784 | iexplore.exe | GET | 200 | 2.22.118.168:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | GB | der | 1.16 Kb | whitelisted |
2332 | iexplore.exe | GET | 200 | 172.217.20.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDAj6AZuIBzdAoAAAAA3JuZ | US | der | 472 b | whitelisted |
3784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2332 | iexplore.exe | GET | 200 | 172.217.20.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCED43httujs%2BXCgAAAADcj5E%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
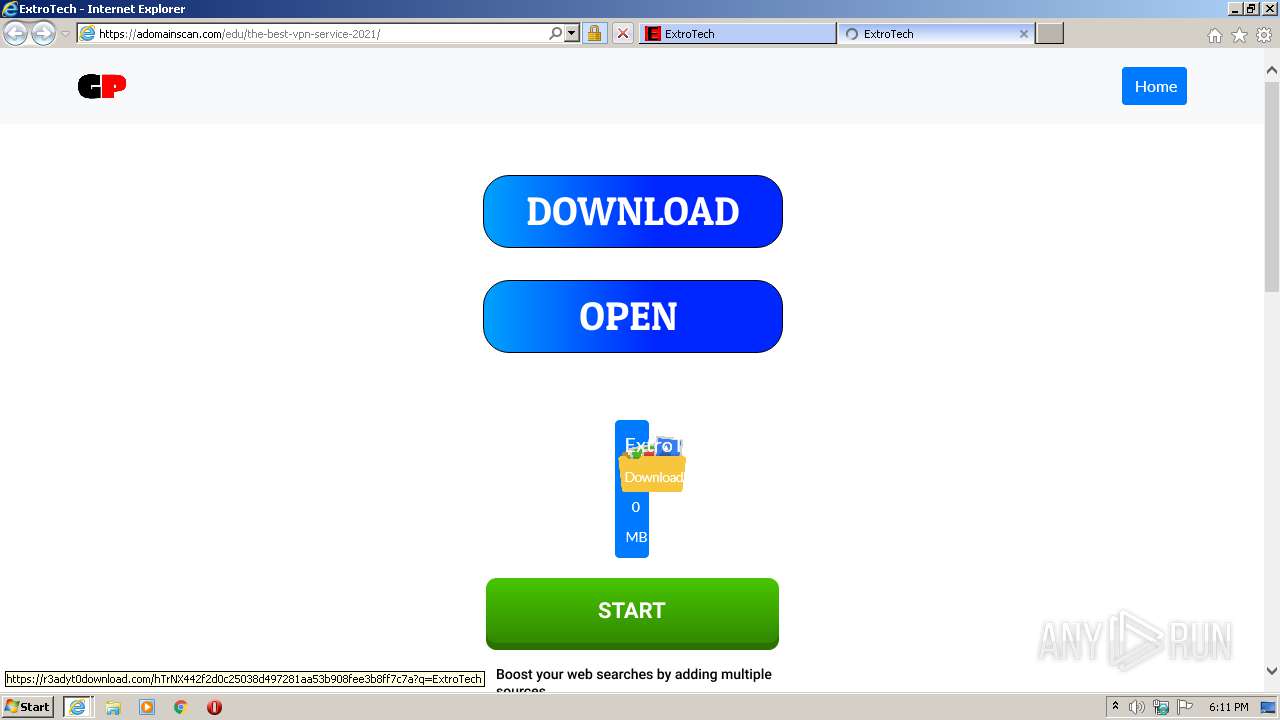
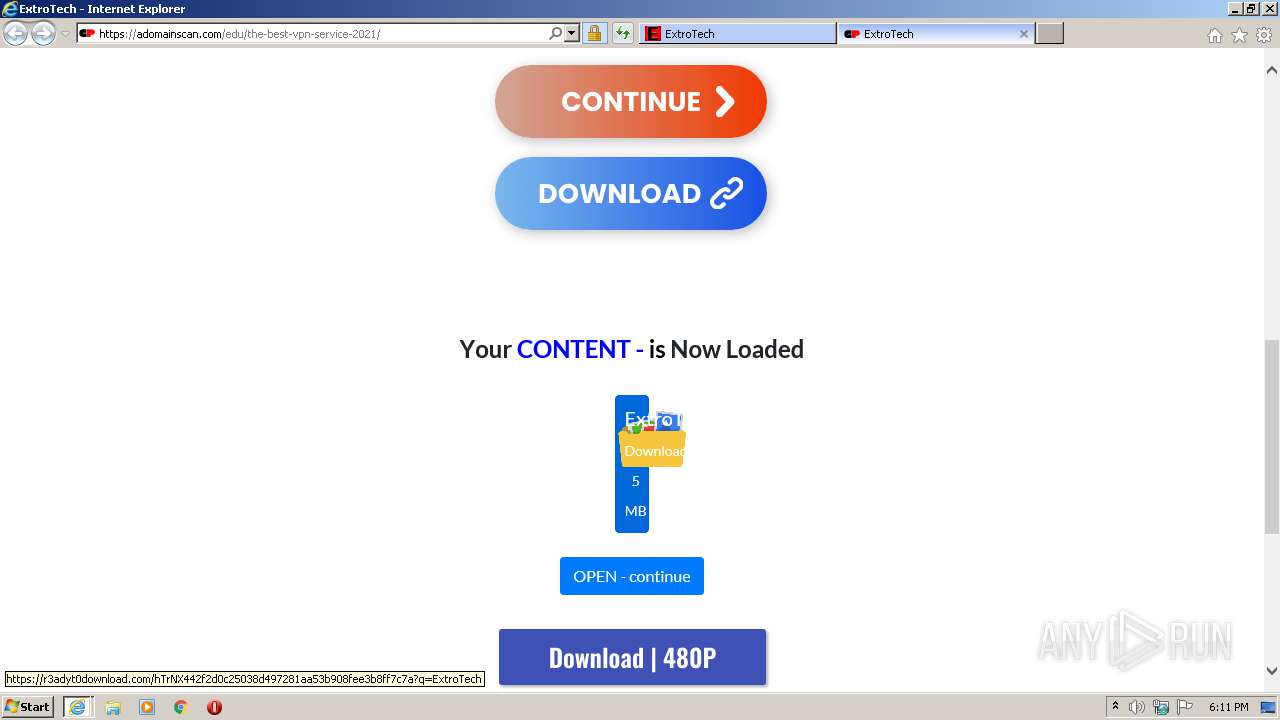
3784 | iexplore.exe | 172.67.181.141:443 | adomainscan.com | — | US | unknown |
3784 | iexplore.exe | 142.250.74.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3784 | iexplore.exe | 142.250.74.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3784 | iexplore.exe | 37.59.184.171:443 | joyhaftsyears.com | OVH SAS | FR | unknown |
3784 | iexplore.exe | 139.45.197.242:443 | upgulpinon.com | — | US | suspicious |
2332 | iexplore.exe | 172.217.23.65:443 | extrotech.blogspot.com | Google Inc. | US | whitelisted |
2332 | iexplore.exe | 216.58.207.137:443 | www.blogger.com | Google Inc. | US | unknown |
2332 | iexplore.exe | 172.217.20.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2332 | iexplore.exe | 142.251.36.225:443 | 3.bp.blogspot.com | Google Inc. | US | whitelisted |
2332 | iexplore.exe | 172.217.23.41:443 | resources.blogblog.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
extrotech.blogspot.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.blogger.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
3.bp.blogspot.com |
| whitelisted |
resources.blogblog.com |
| whitelisted |
1.bp.blogspot.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
bit.ly |
| shared |