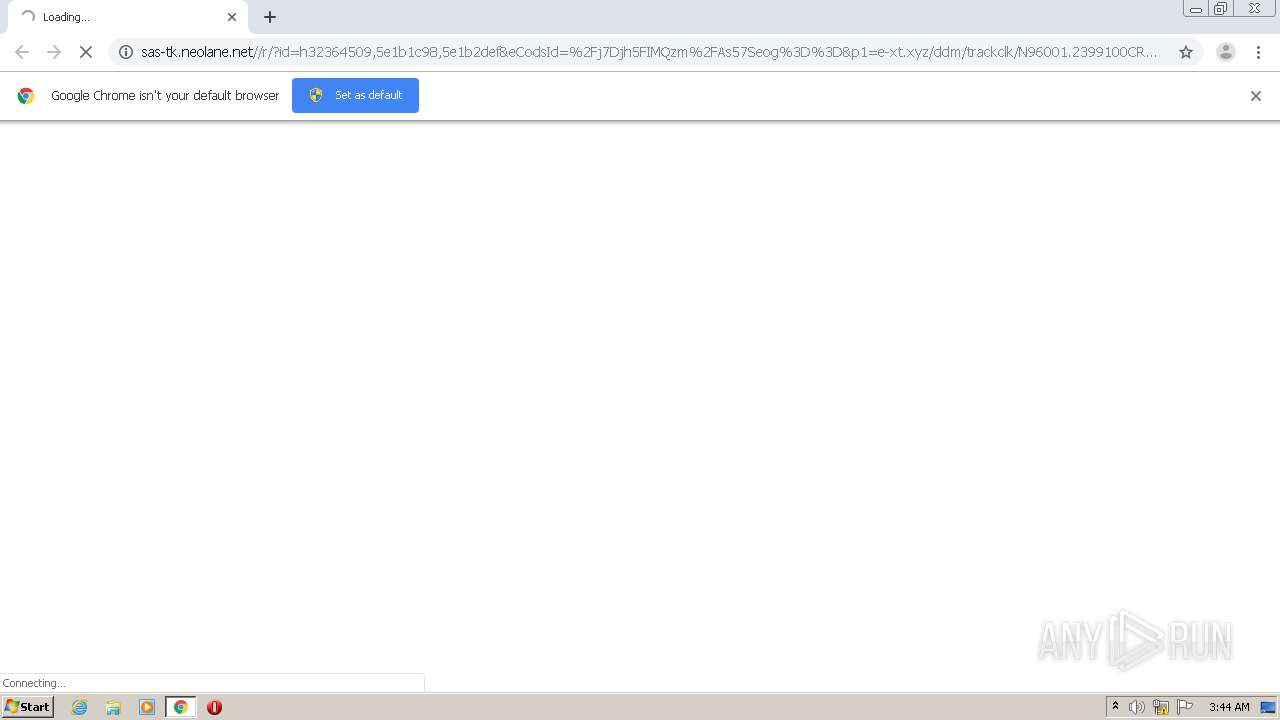
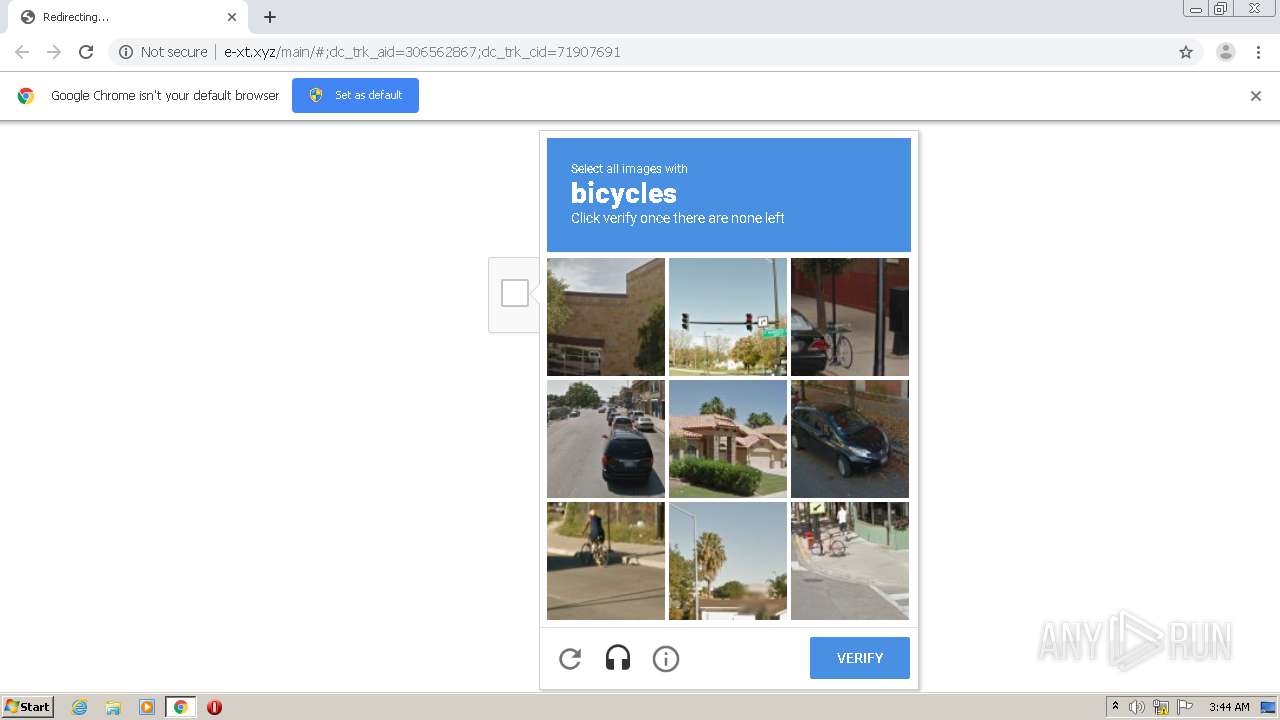
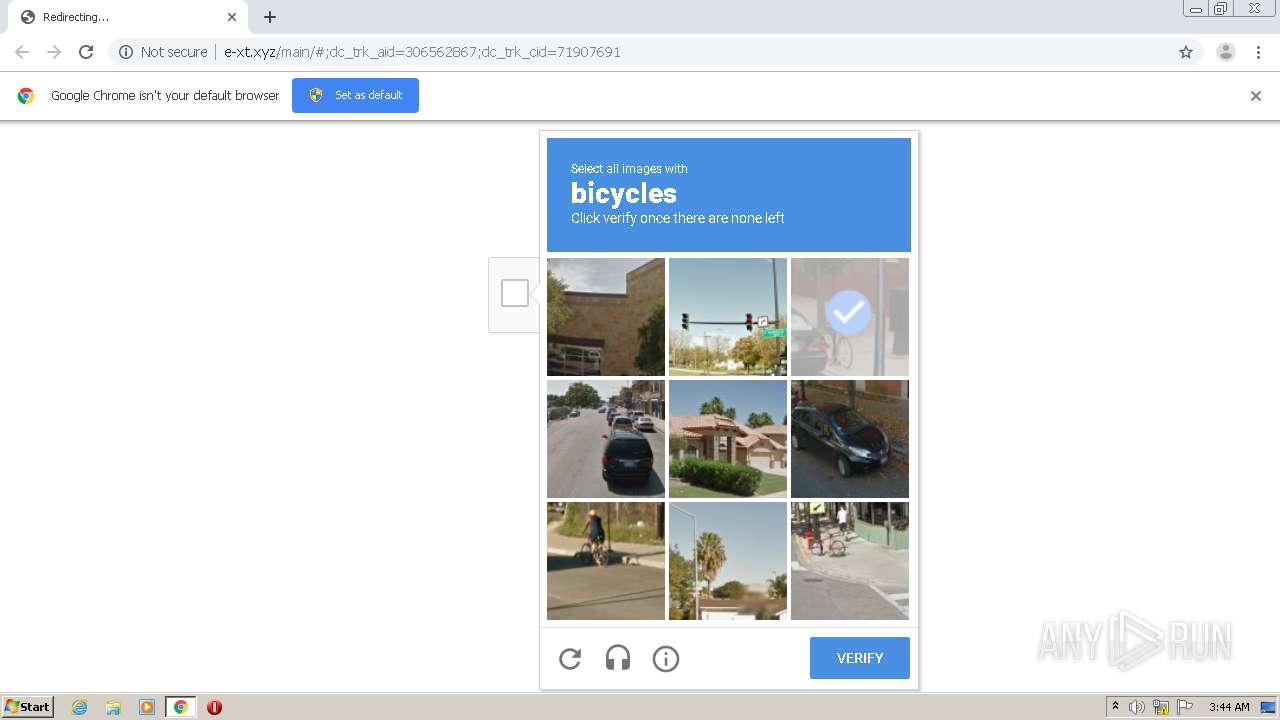
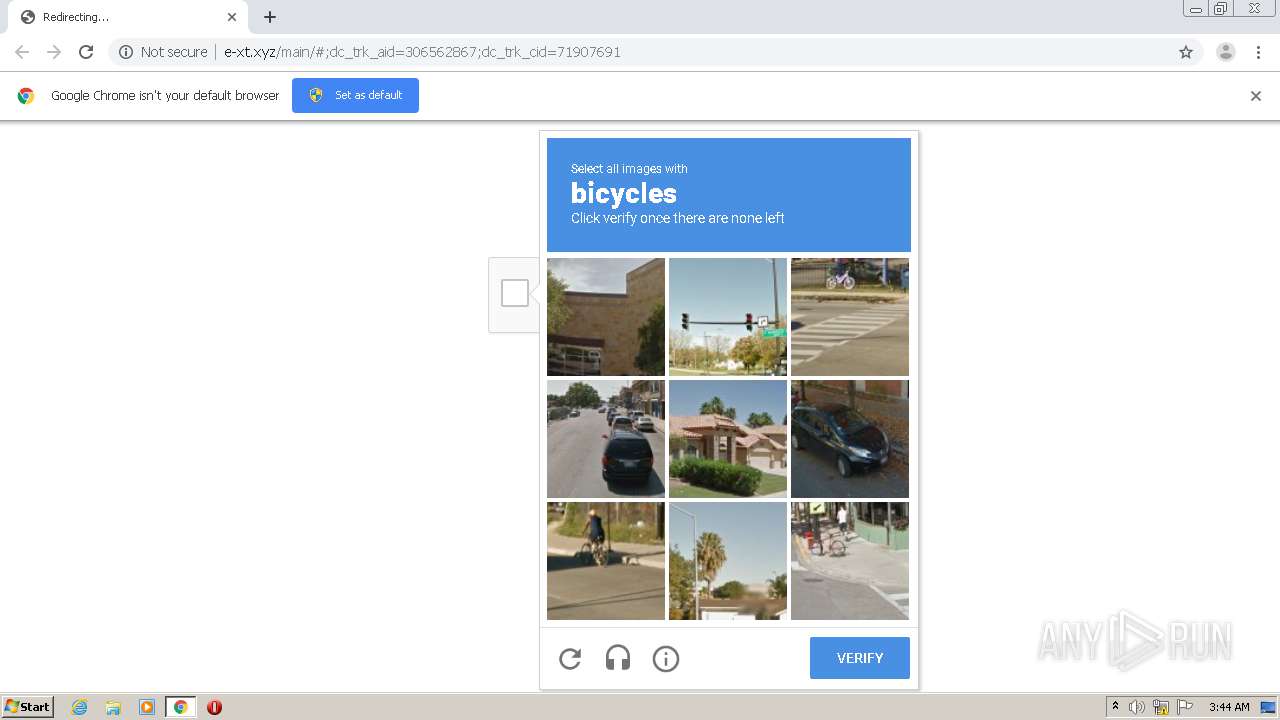
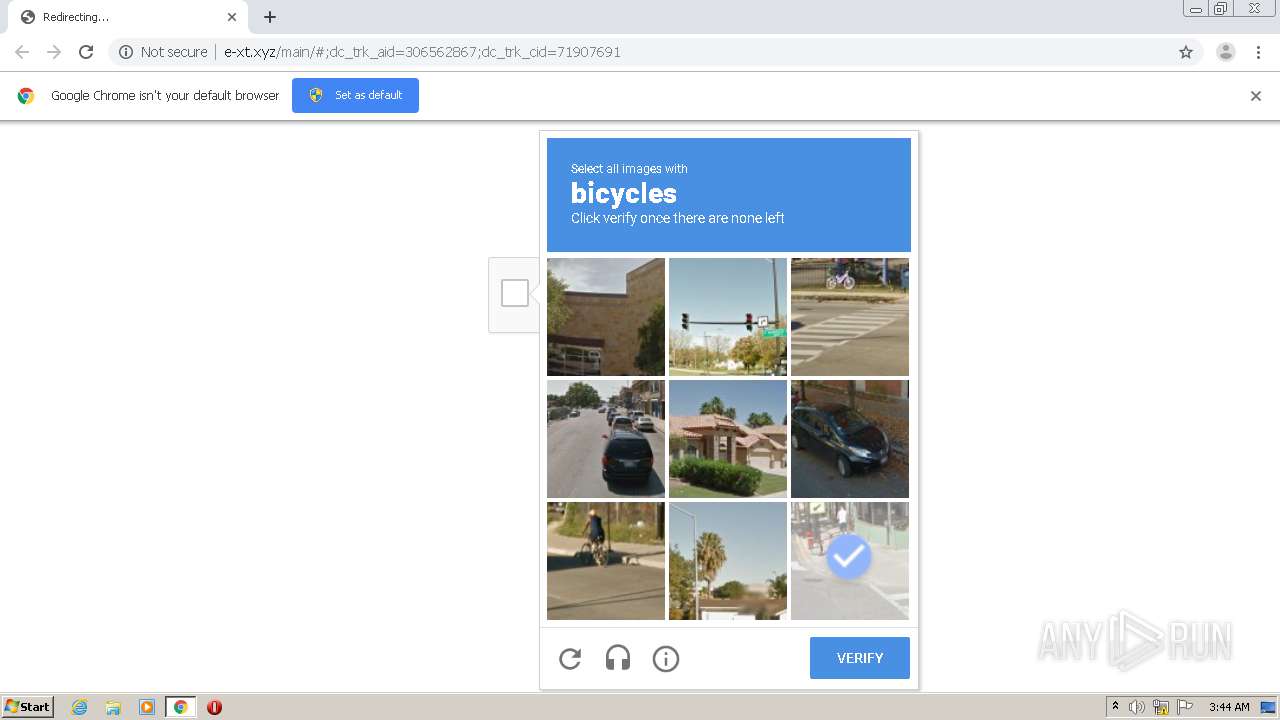
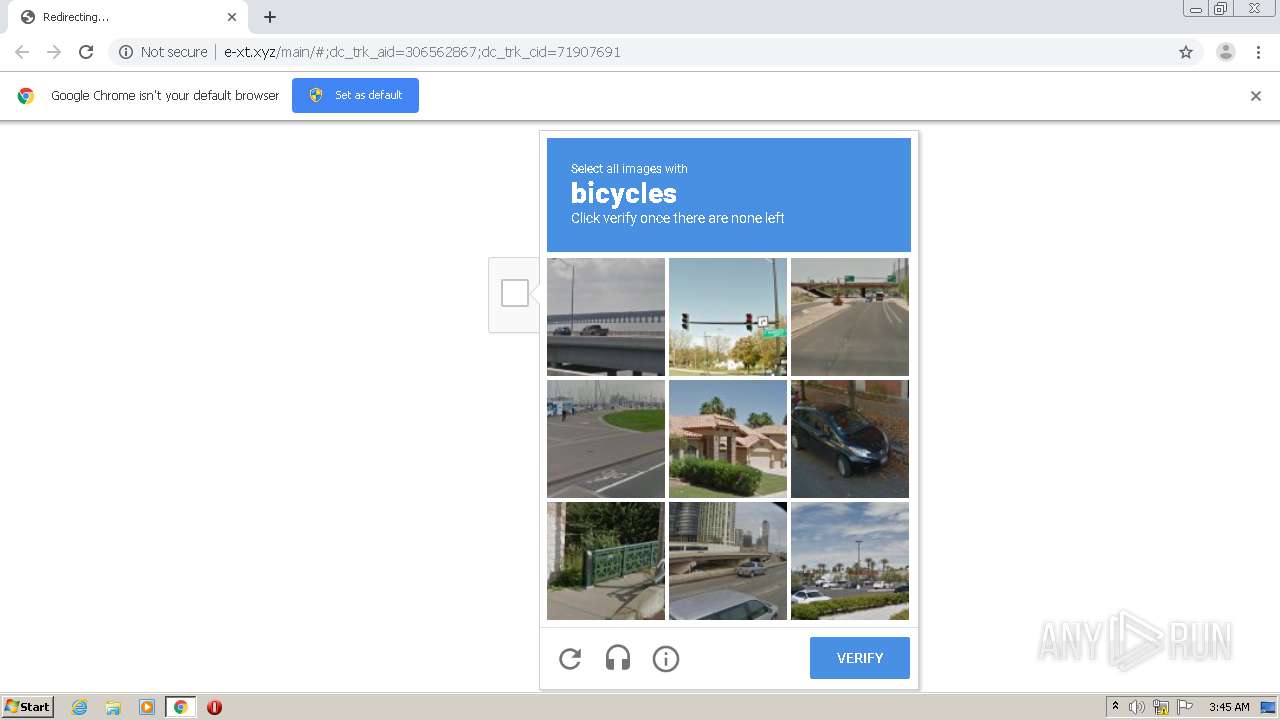
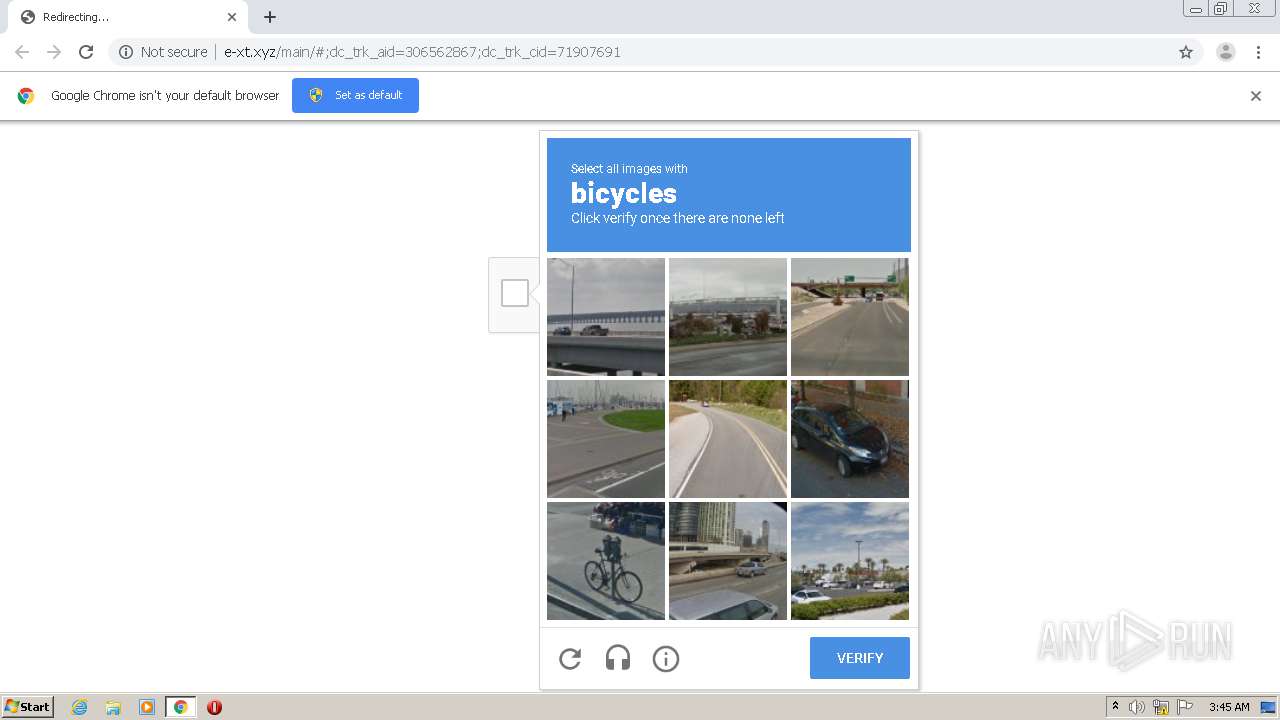
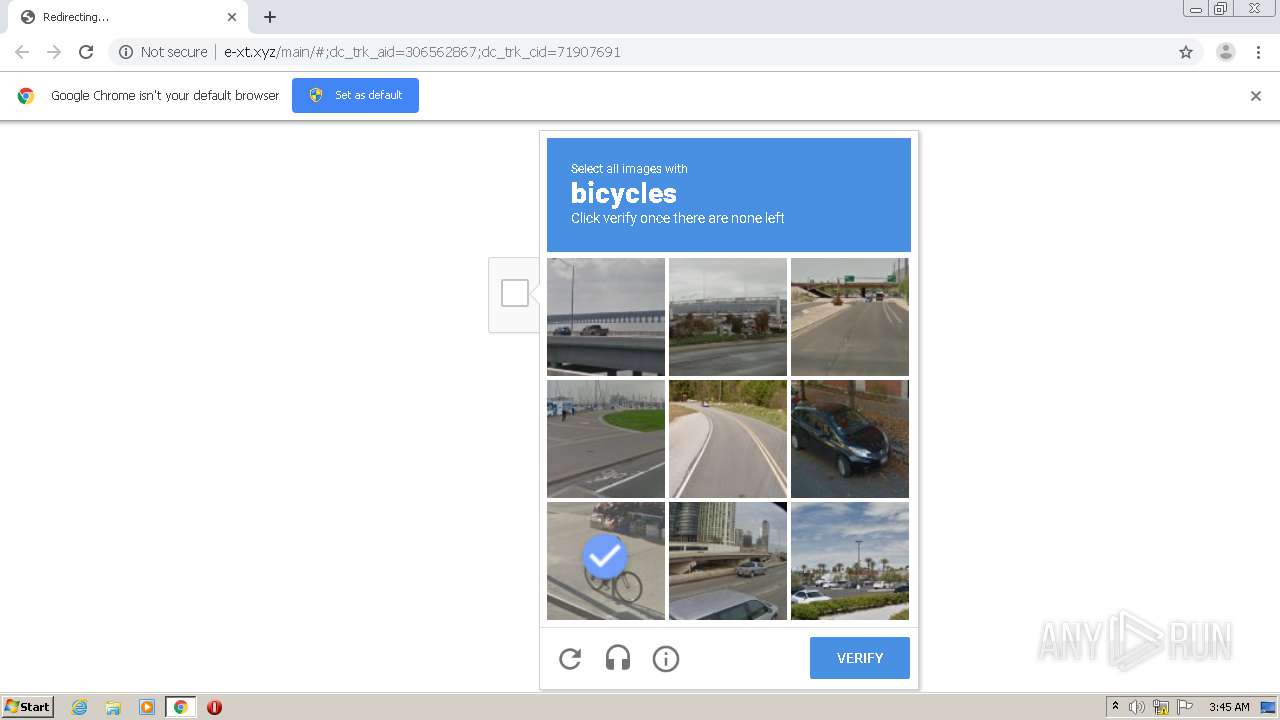
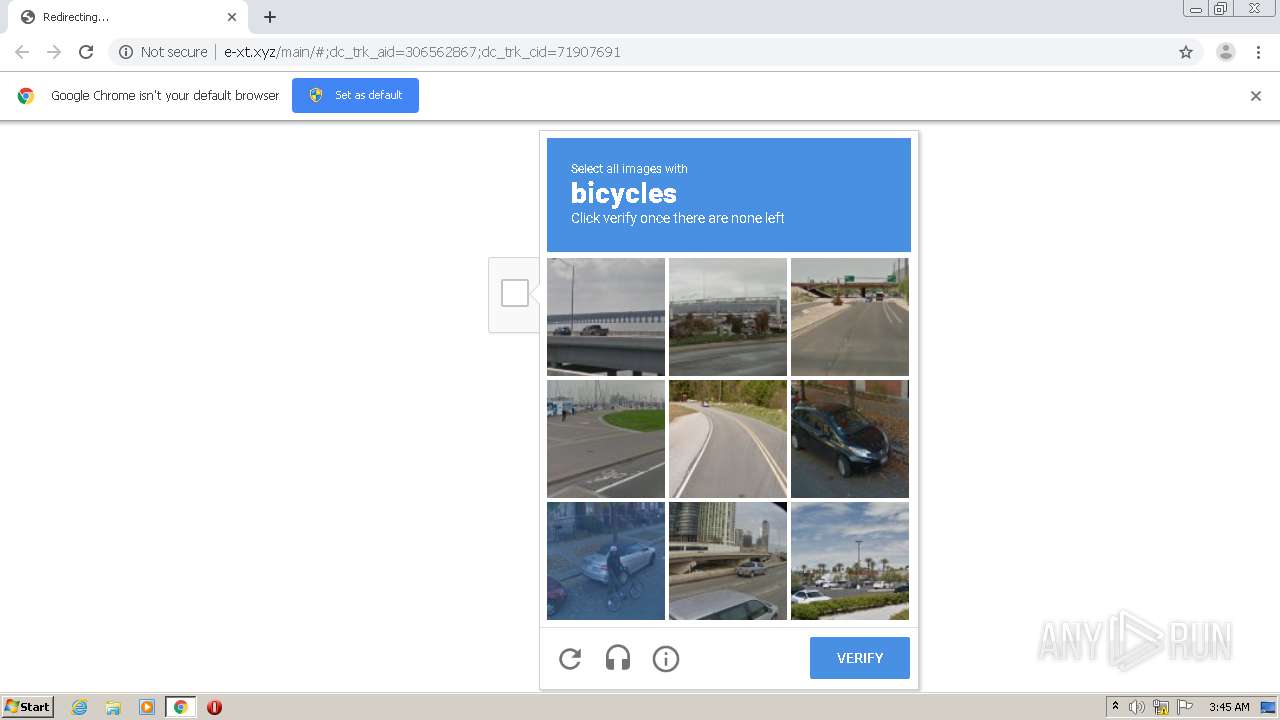
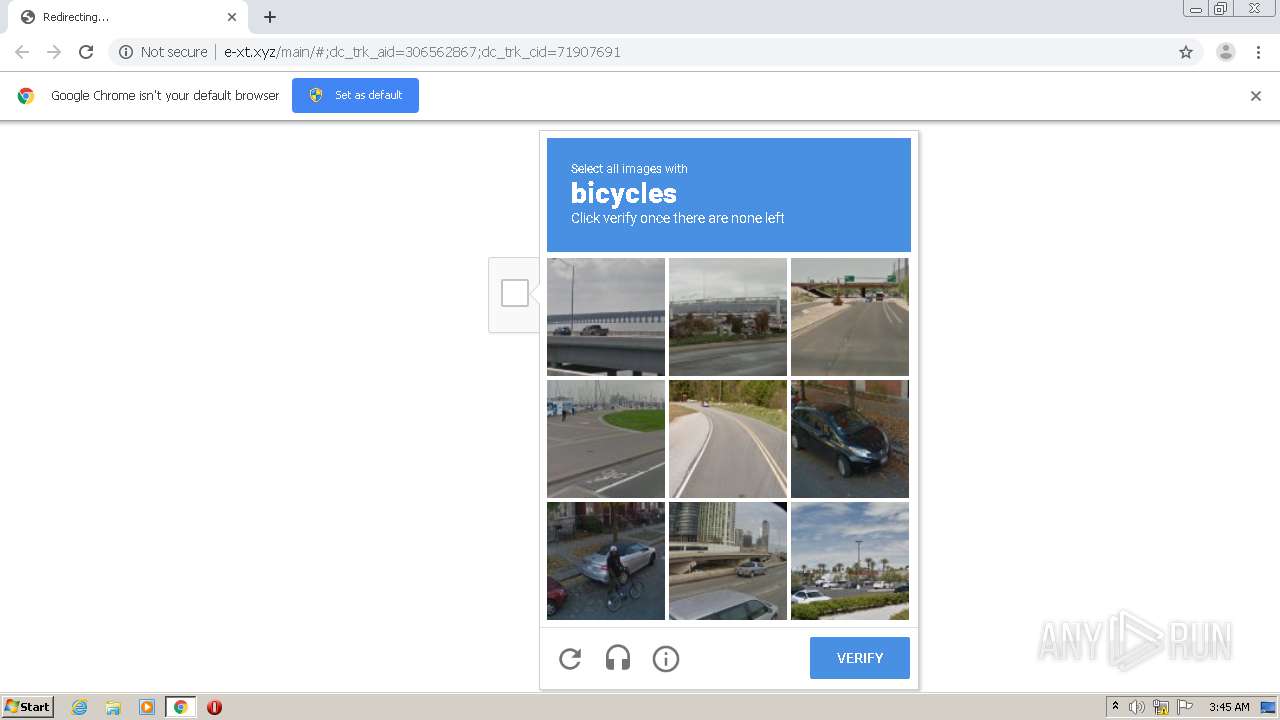
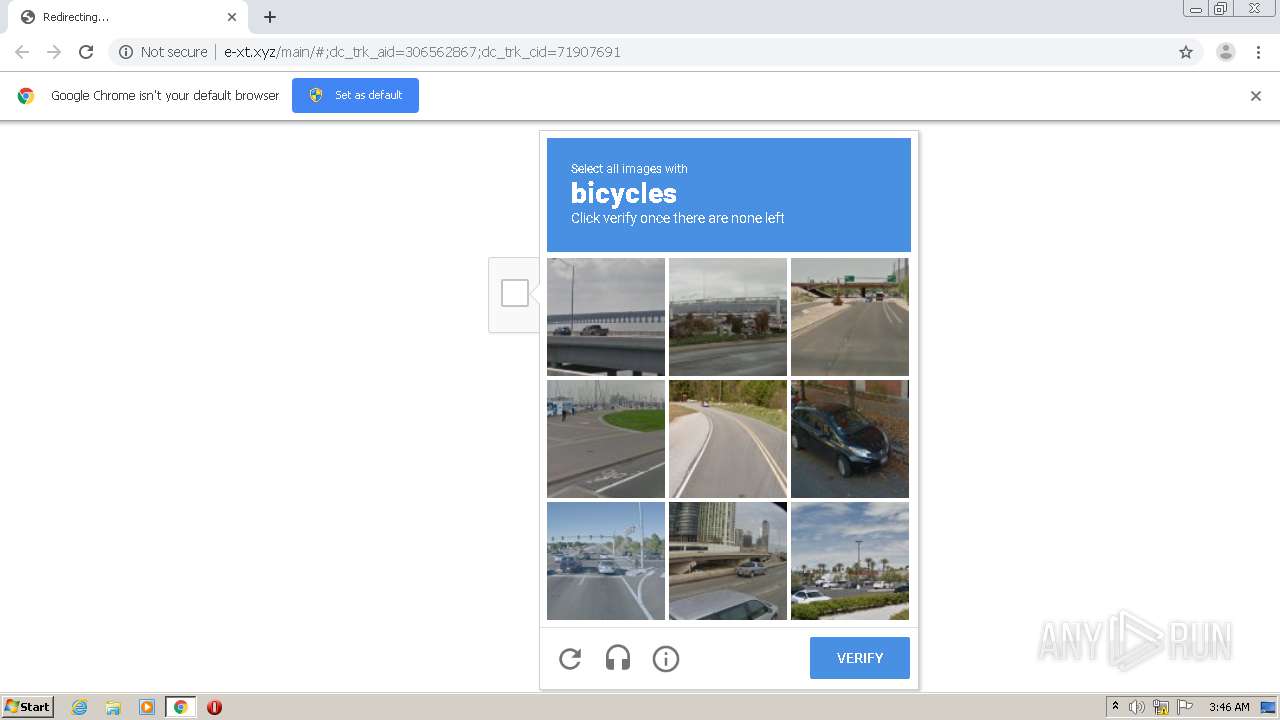
| URL: | http://sas-tk.neolane.net//r/?id=h32364509,5e1b1c98,5e1b2def&eCodsId=%2Fj7Djh5FIMQzm%2FAs57Seog%3D%3D&p1=e-xt.xyz/ddm/trackclk/N96001.2399100CRM/B9941585.134363607?e=ZGFuLmxvZ2FuQDUzLmNvbQ==%23;dc_trk_aid=306562867;dc_trk_cid=71907691?&p2=%40tSg2yOhjbBb8RYqSwHfJuQ%3D%3D |
| Full analysis: | https://app.any.run/tasks/087b802b-1b6b-4071-93b8-aea7bfe87ed5 |
| Verdict: | Malicious activity |
| Analysis date: | December 22, 2020, 03:44:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E7A2792122D16015E8562040E5C98817 |
| SHA1: | 1863F5A321ED40D57B19B222D4EF2DD661CCCD7E |
| SHA256: | 443171767877F0EB4C3A27F1645CDE5ED997788A4EC75707E1EB1A5B5BD63A97 |
| SSDEEP: | 6:CWWgdq90J+K6hQxNWD6yZPtyD4SUUYFuTdimRT5LSm:pJkm83hQxNWD6yZPtyDLO7mRT5em |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2664)
Reads the hosts file
- chrome.exe (PID: 2004)
- chrome.exe (PID: 2664)
Reads settings of System Certificates
- chrome.exe (PID: 2004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,9217523051800373883,4723678714015753490,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15168927322153986924 --mojo-platform-channel-handle=3652 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,9217523051800373883,4723678714015753490,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14492693368054629736 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,9217523051800373883,4723678714015753490,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12218922186219062853 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2088 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9217523051800373883,4723678714015753490,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15118212461851152855 --mojo-platform-channel-handle=1296 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9217523051800373883,4723678714015753490,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18432894538086994302 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,9217523051800373883,4723678714015753490,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13974457658390261250 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,9217523051800373883,4723678714015753490,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7170937588114023344 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2572 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://sas-tk.neolane.net//r/?id=h32364509,5e1b1c98,5e1b2def&eCodsId=%2Fj7Djh5FIMQzm%2FAs57Seog%3D%3D&p1=e-xt.xyz/ddm/trackclk/N96001.2399100CRM/B9941585.134363607?e=ZGFuLmxvZ2FuQDUzLmNvbQ==%23;dc_trk_aid=306562867;dc_trk_cid=71907691?&p2=%40tSg2yOhjbBb8RYqSwHfJuQ%3D%3D" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x71aea9d0,0x71aea9e0,0x71aea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
584
Read events
529
Write events
52
Delete events
3
Modification events
| (PID) Process: | (2436) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2664-13253082256454375 |
Value: 259 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2664) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
19
Text files
73
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FE16B91-A68.pma | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9b561f6e-c38d-4e44-900b-0eec3a38579b.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1505a7.TMP | text | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15076c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
22
DNS requests
12
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
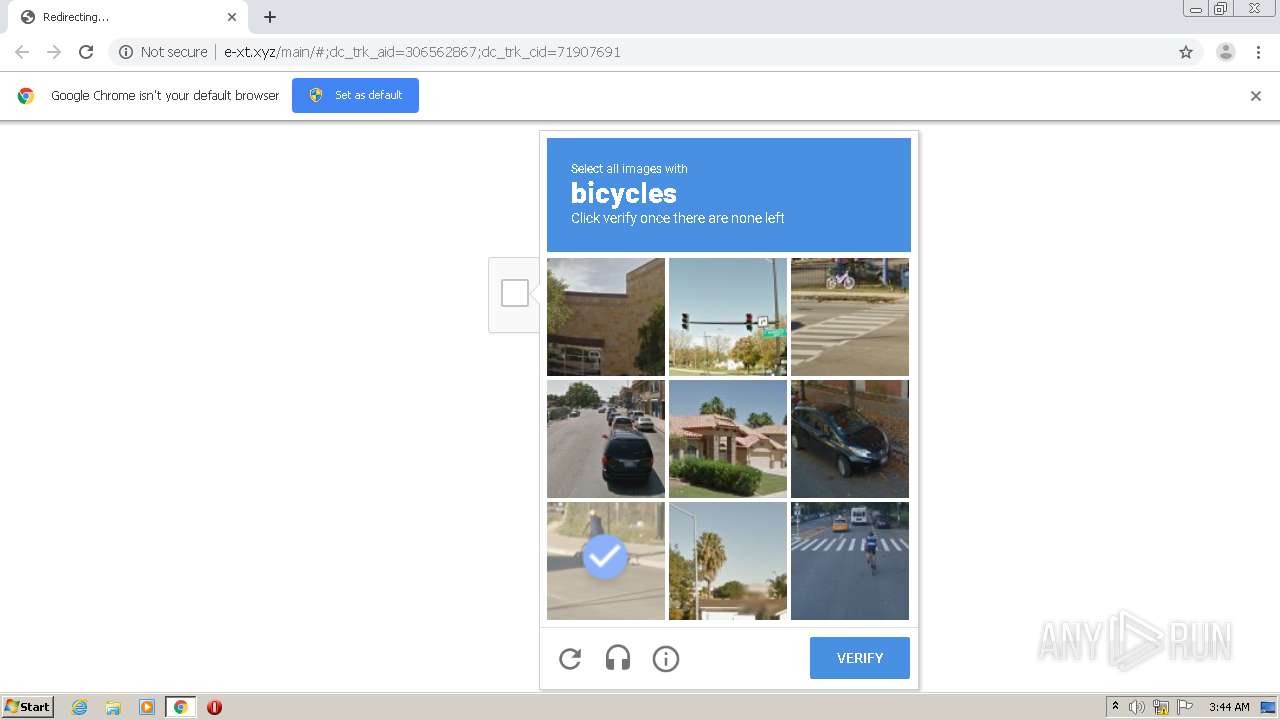
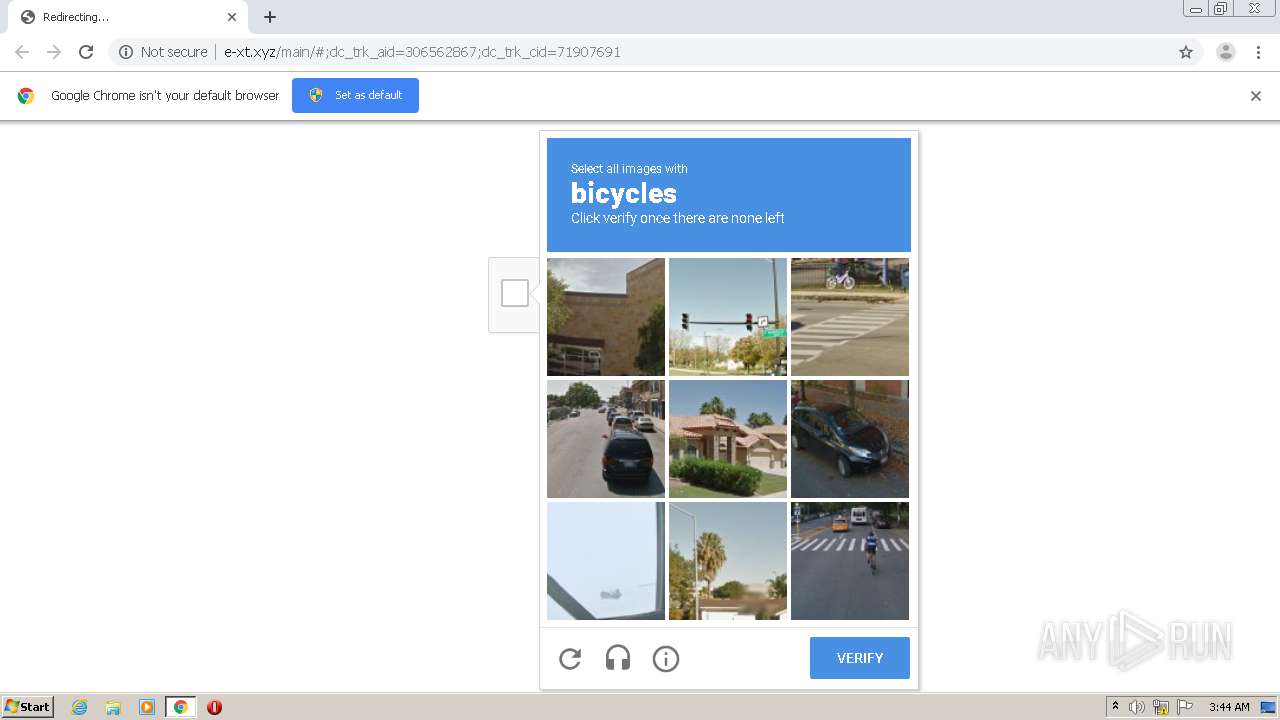
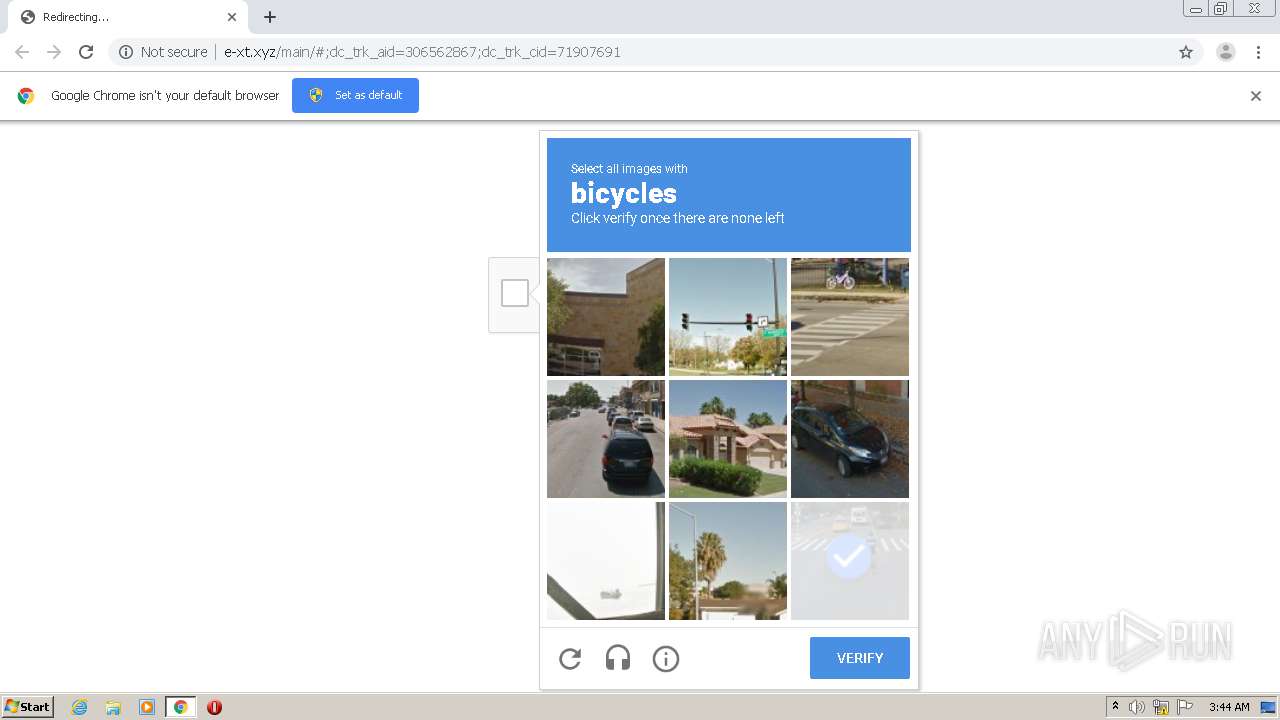
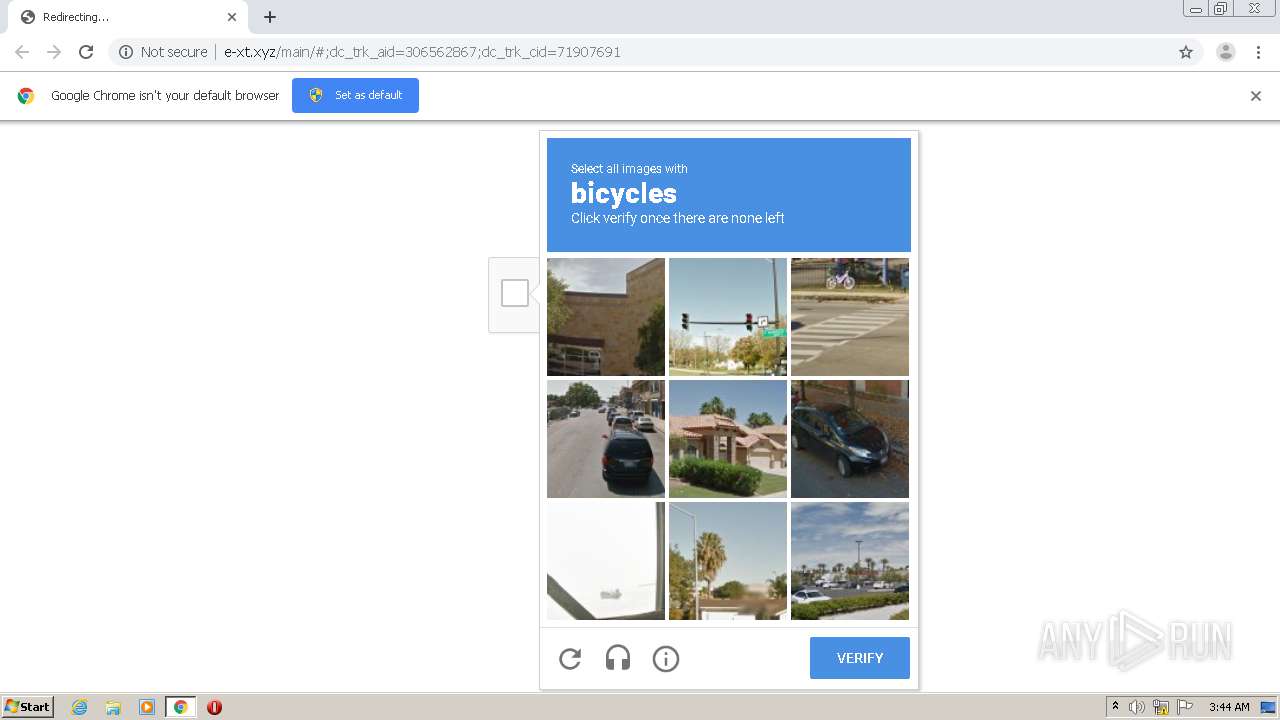
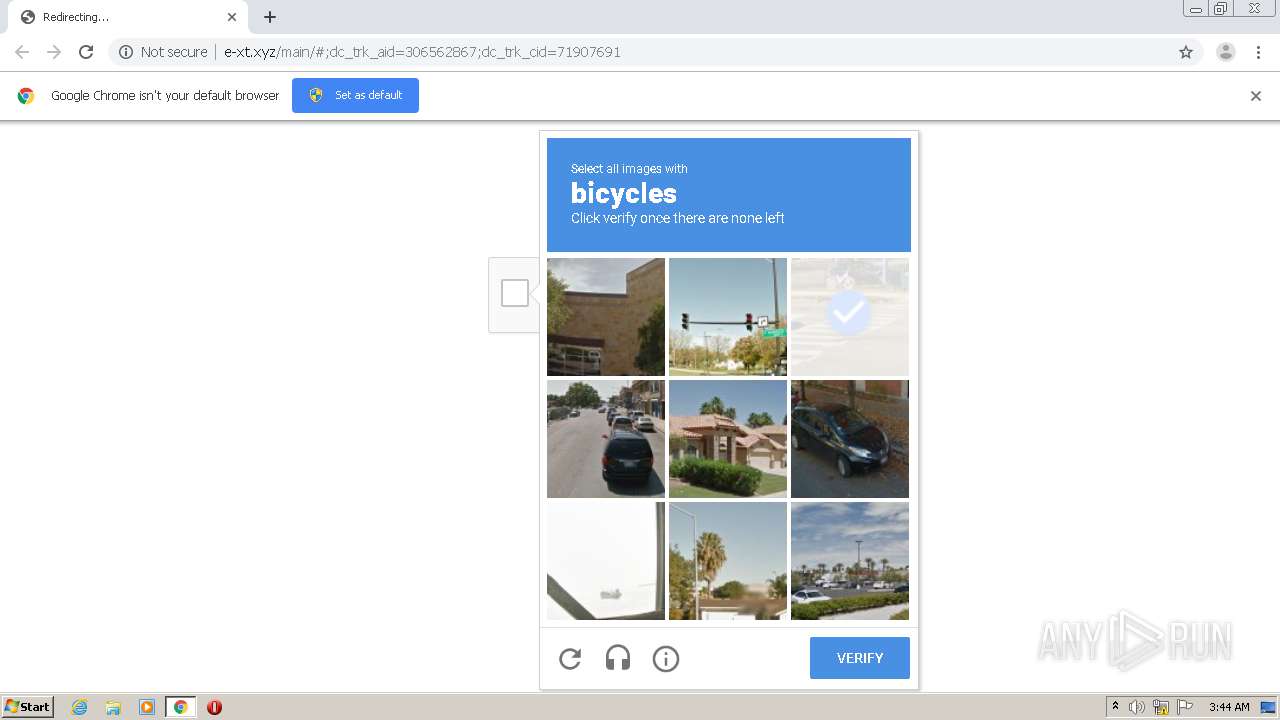
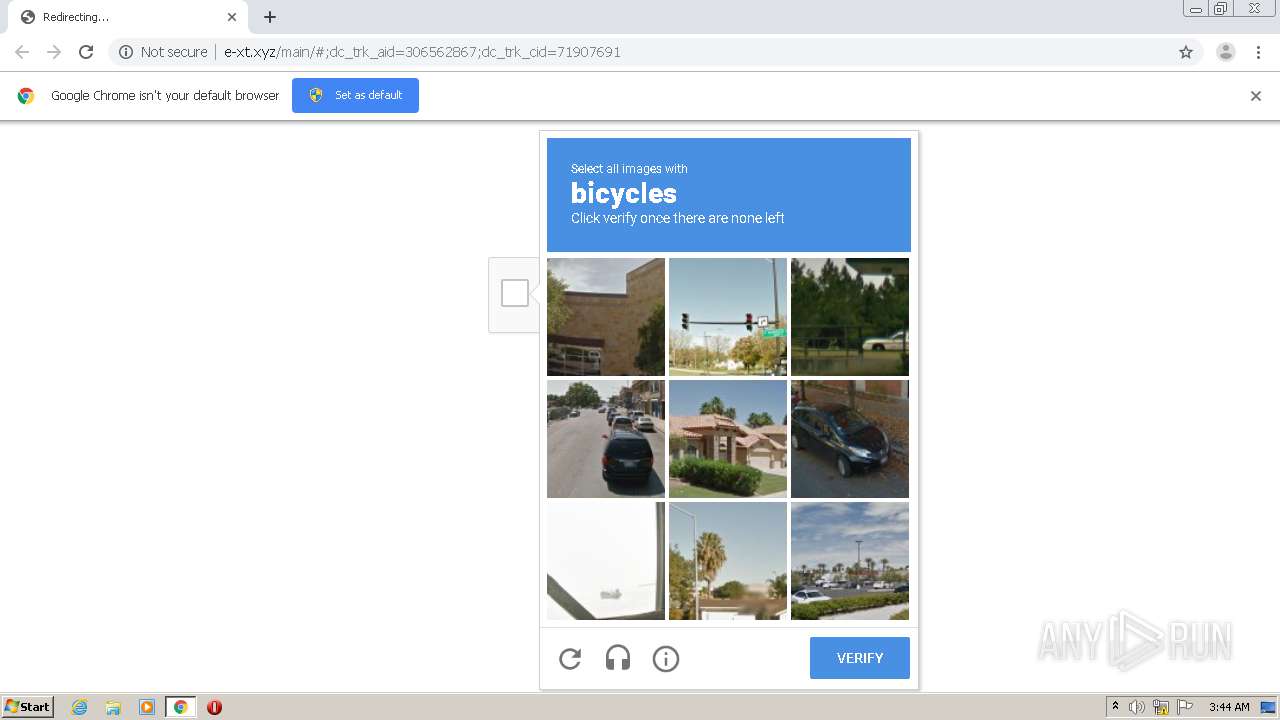
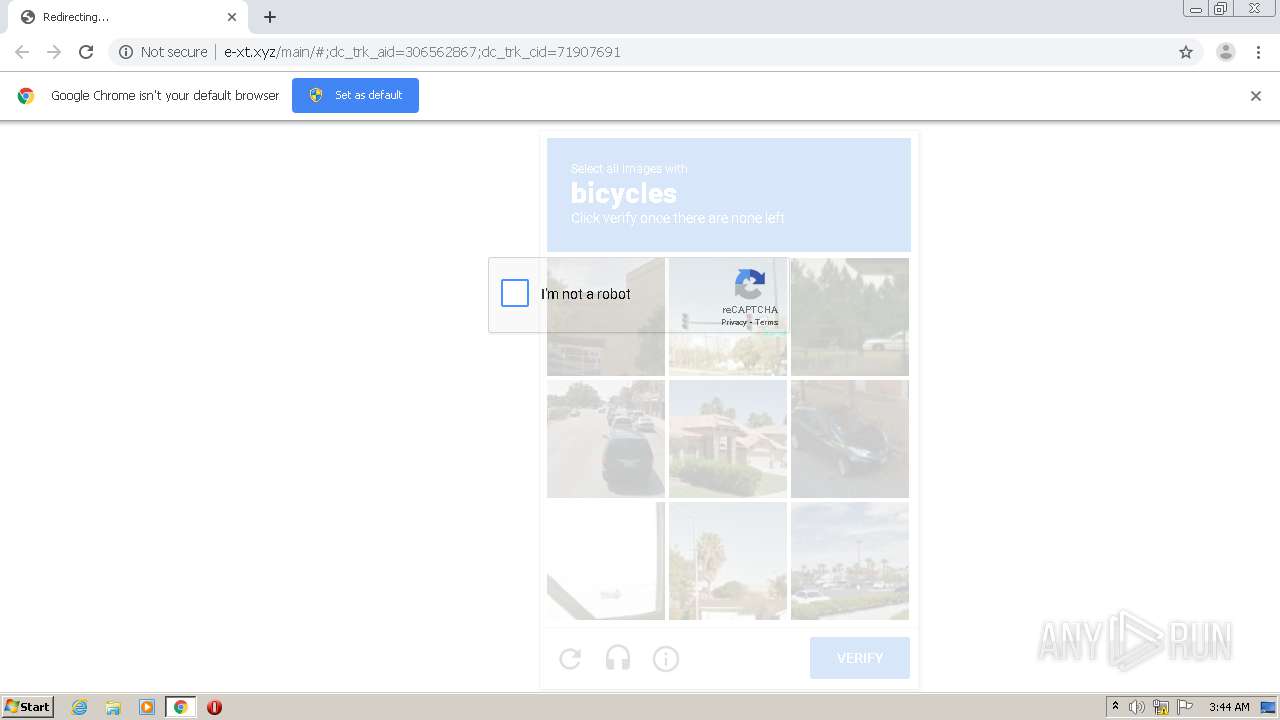
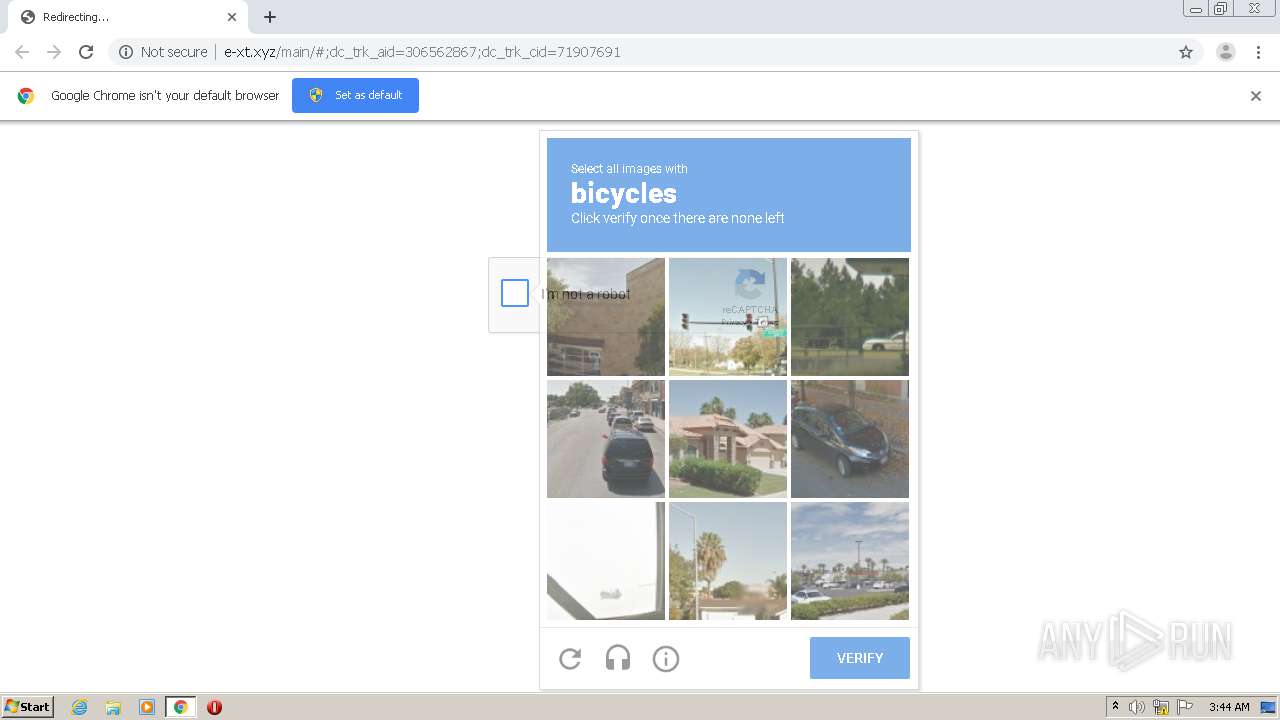
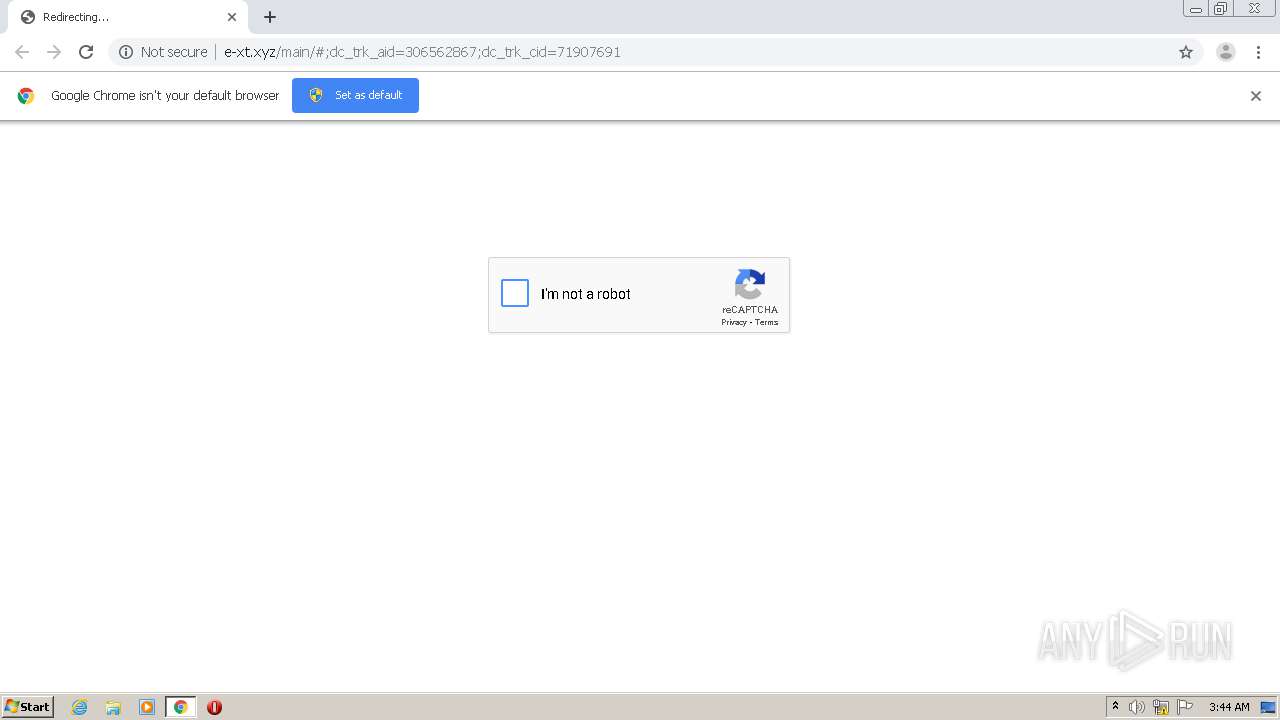
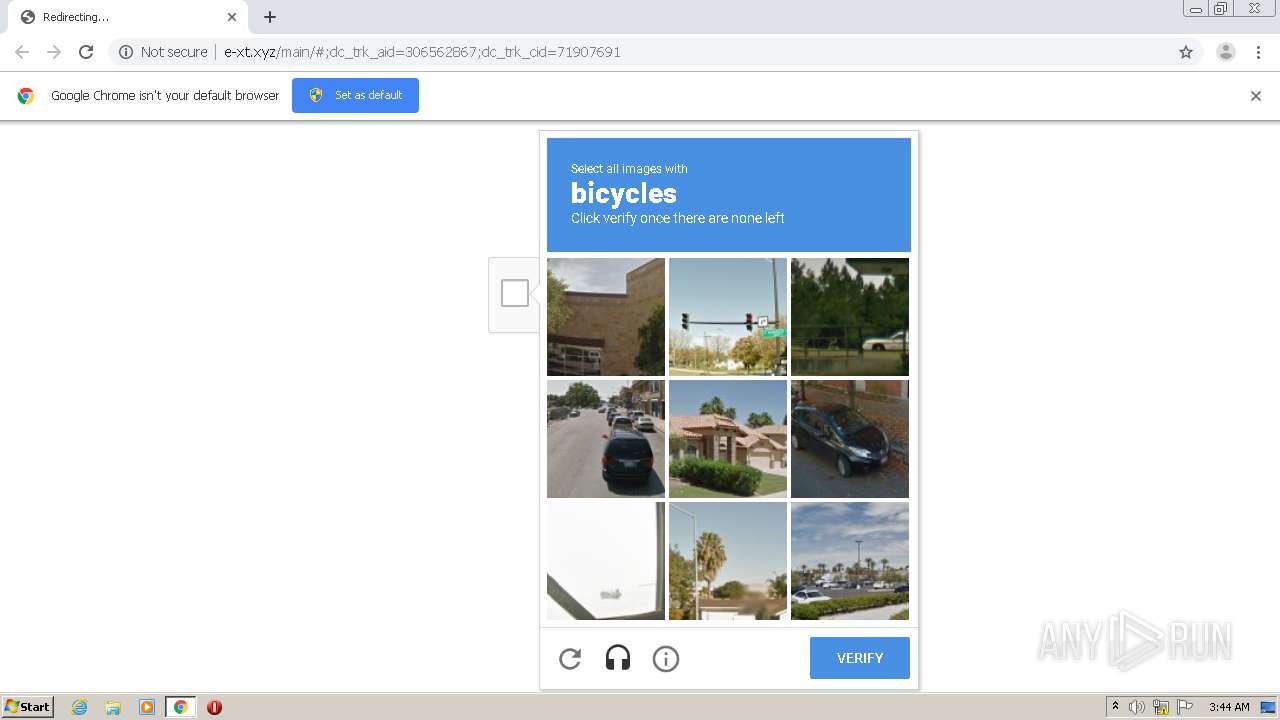
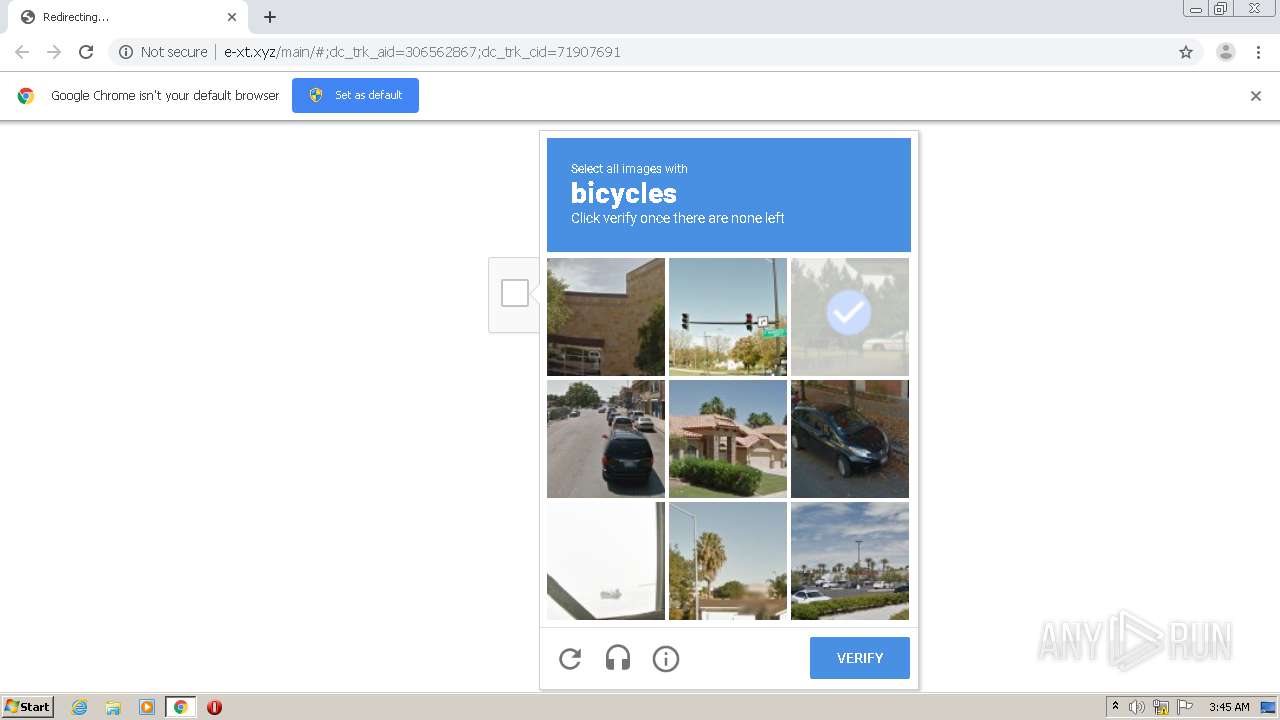
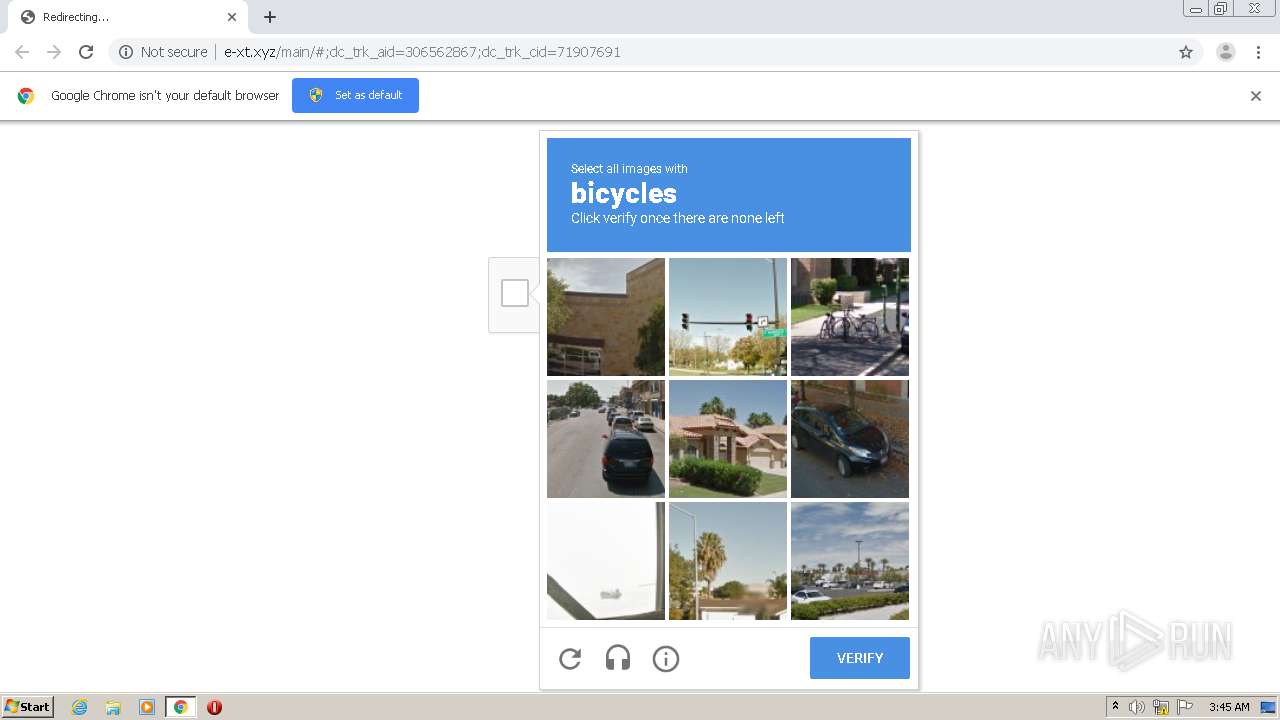
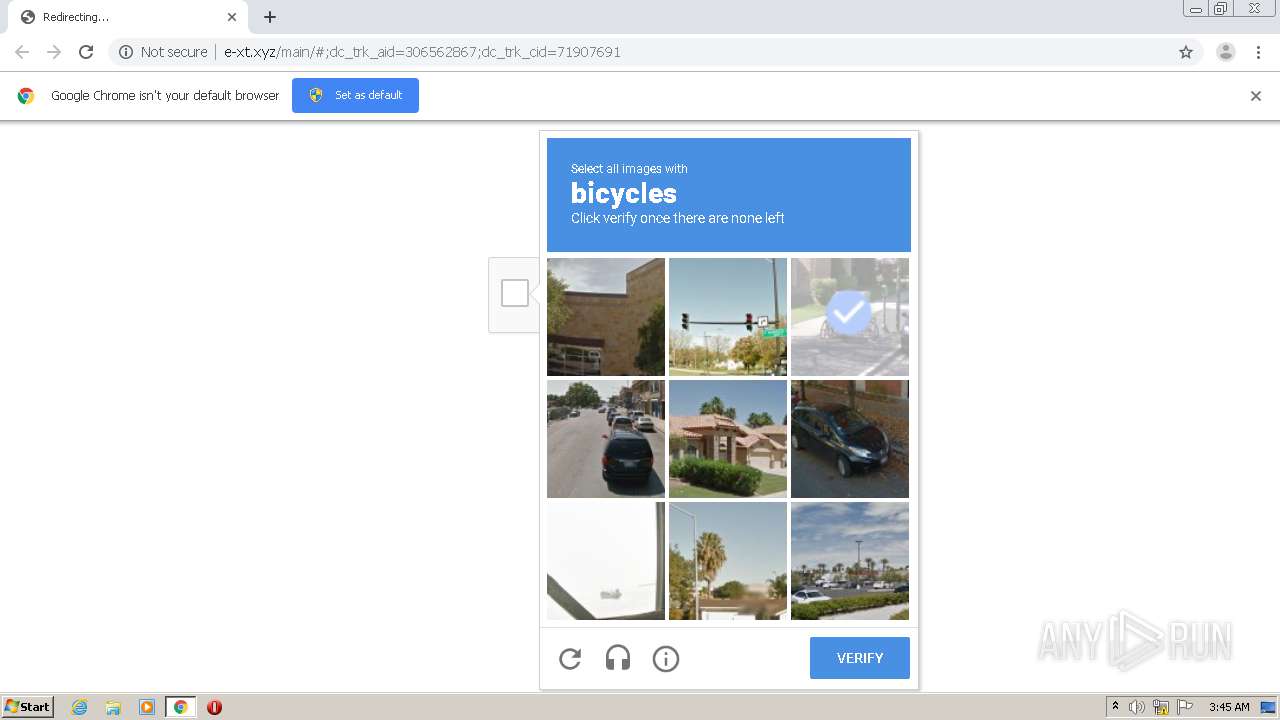
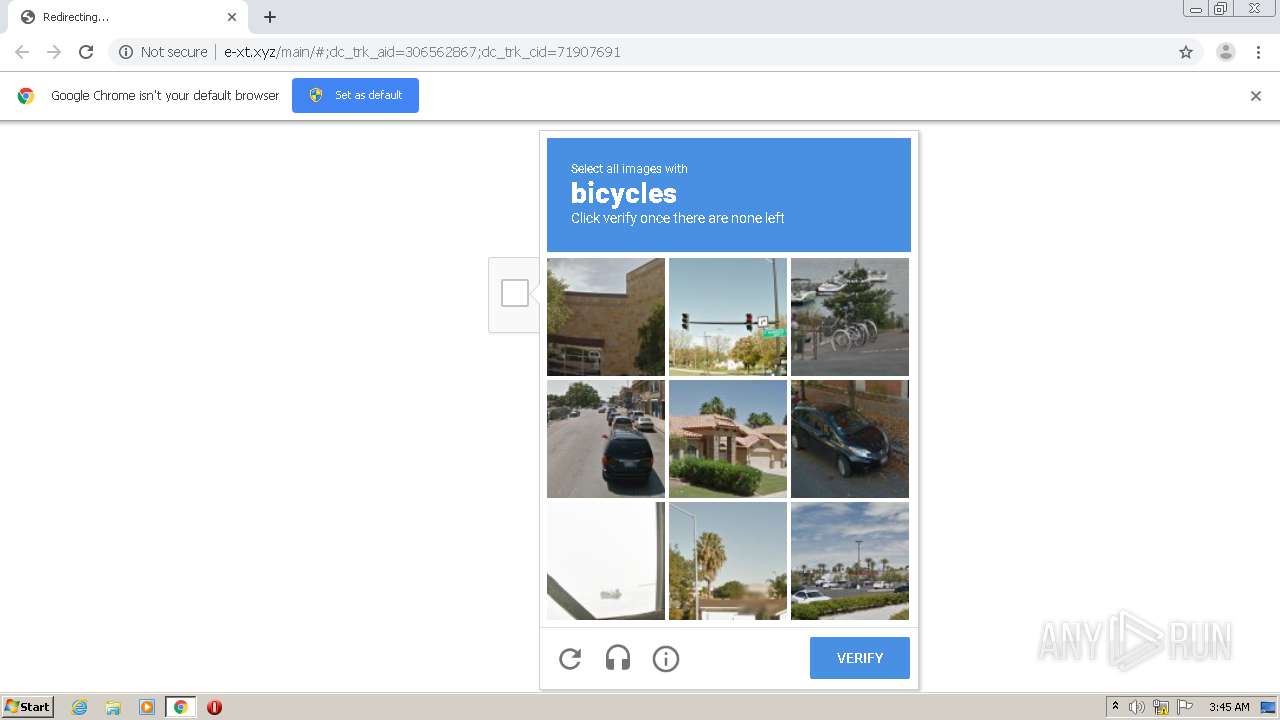
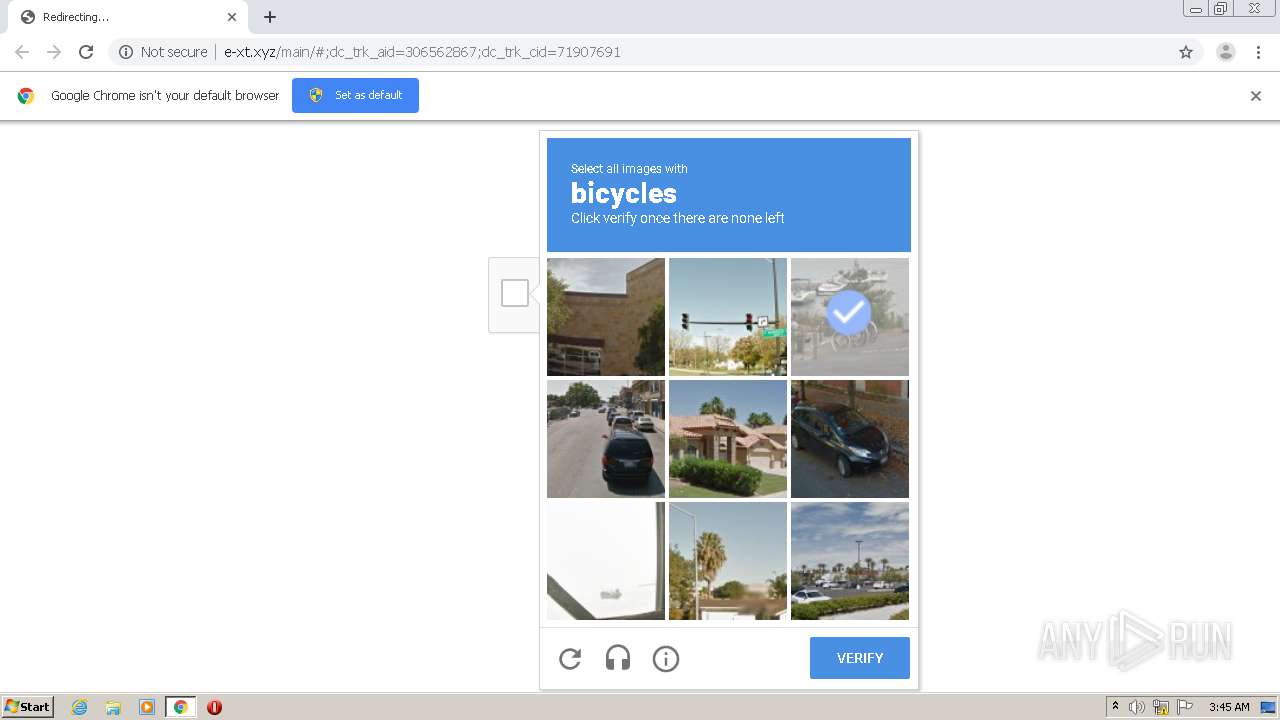
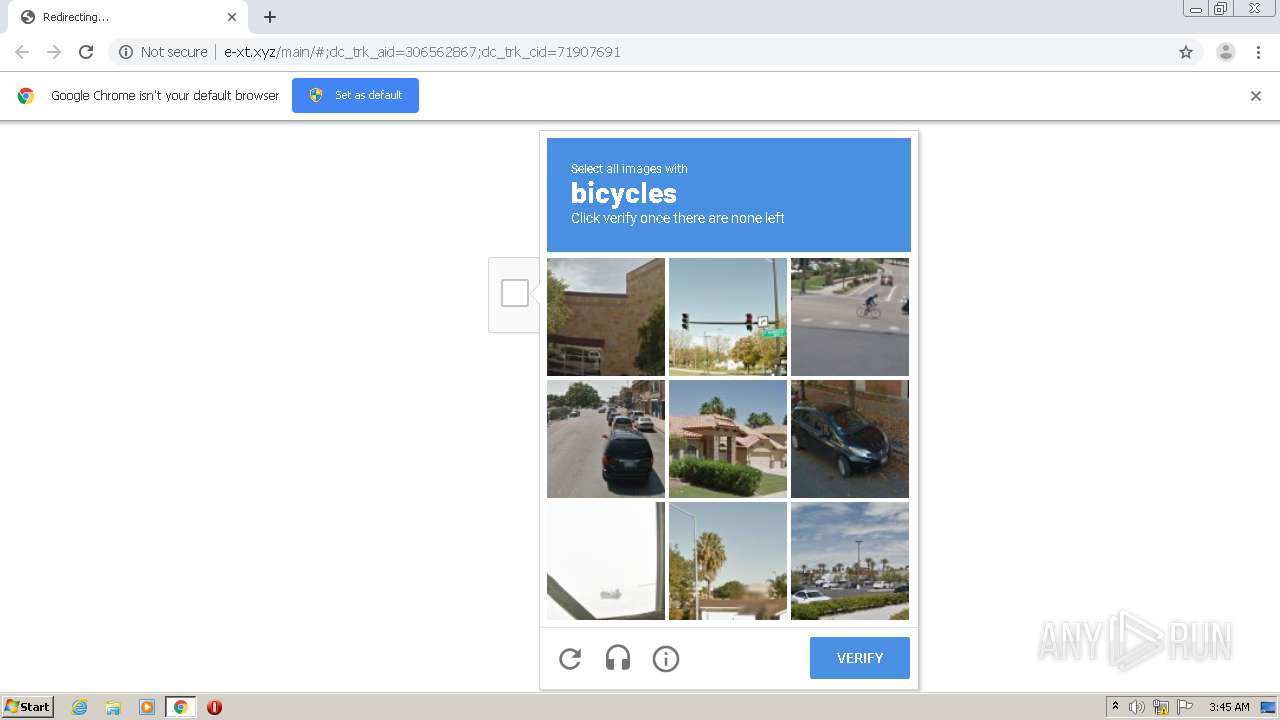
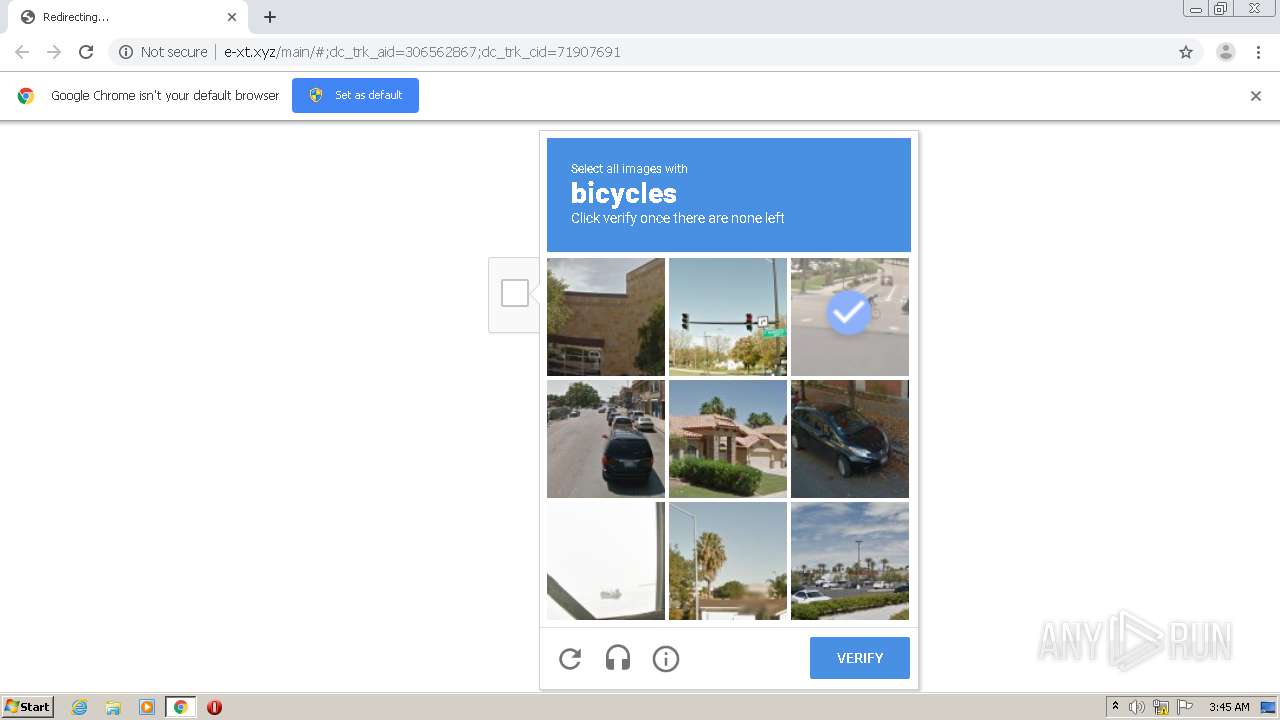
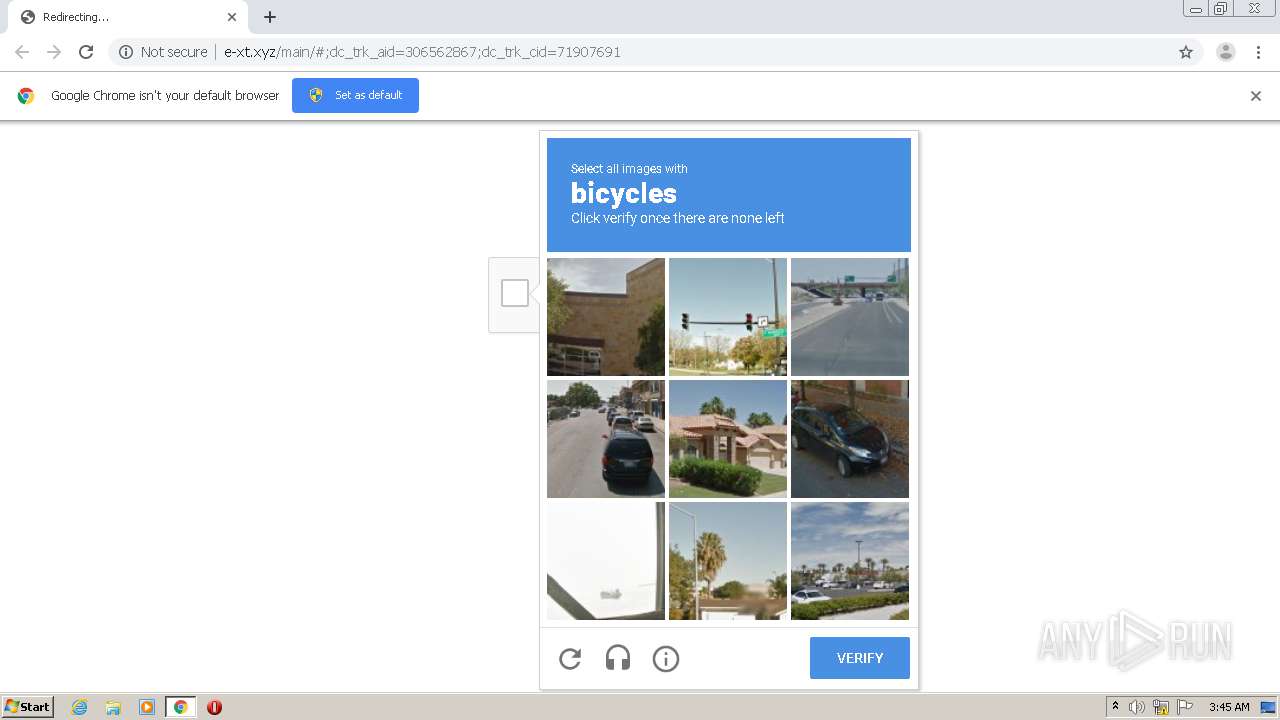
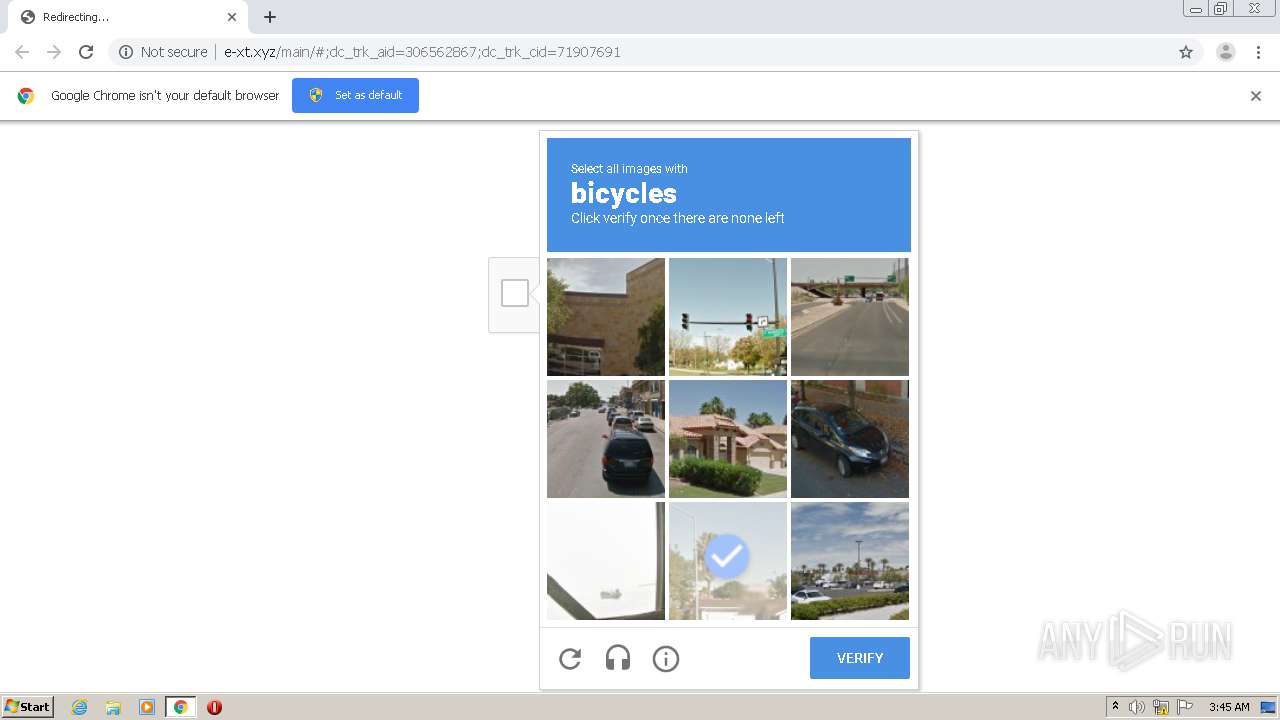
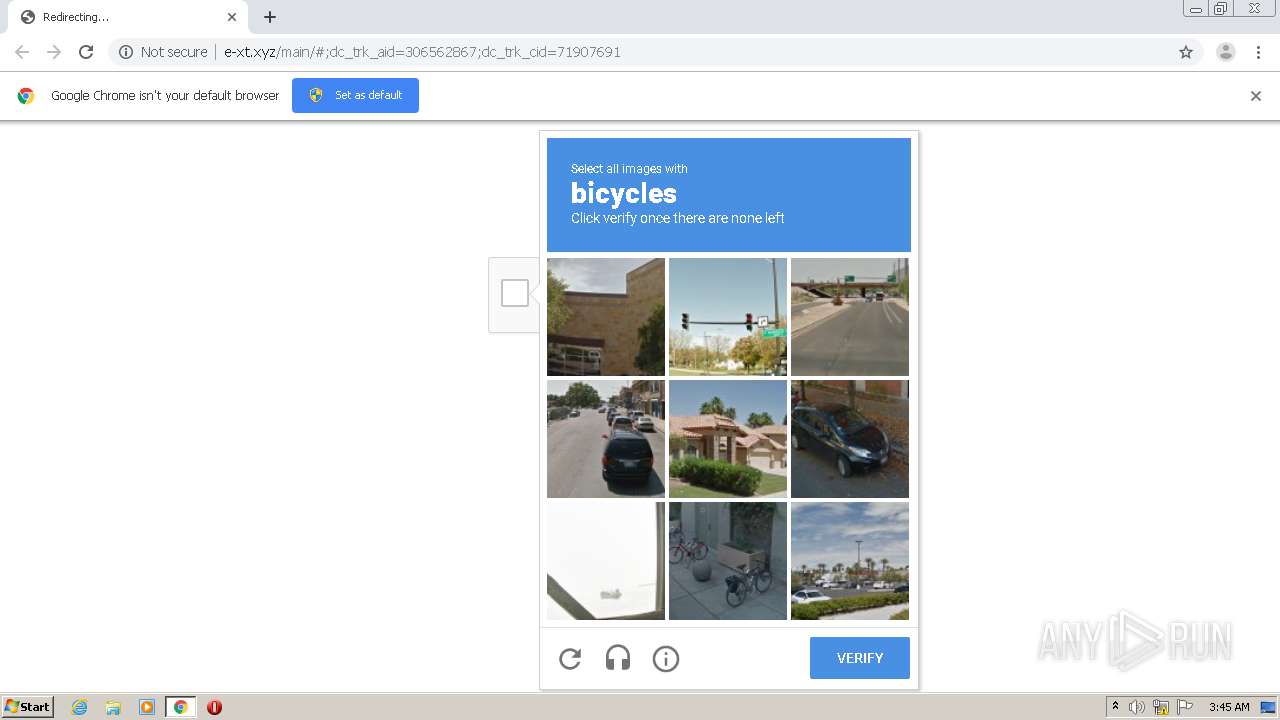
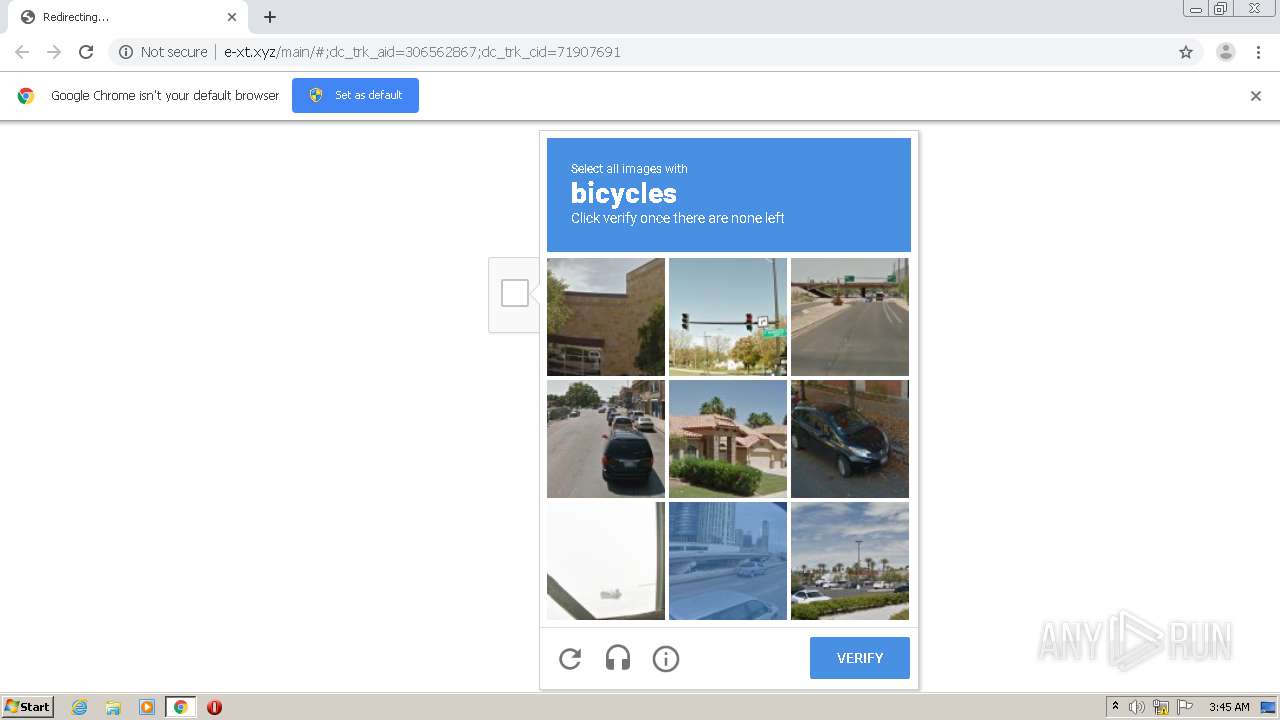
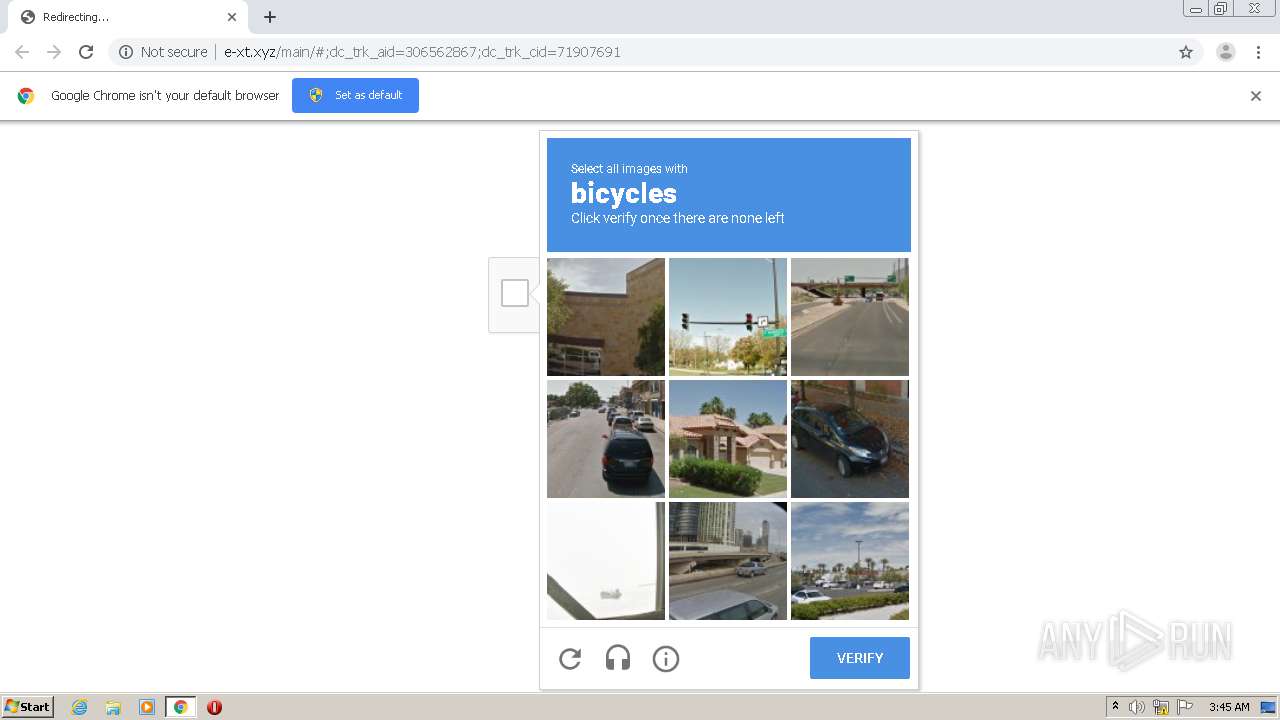
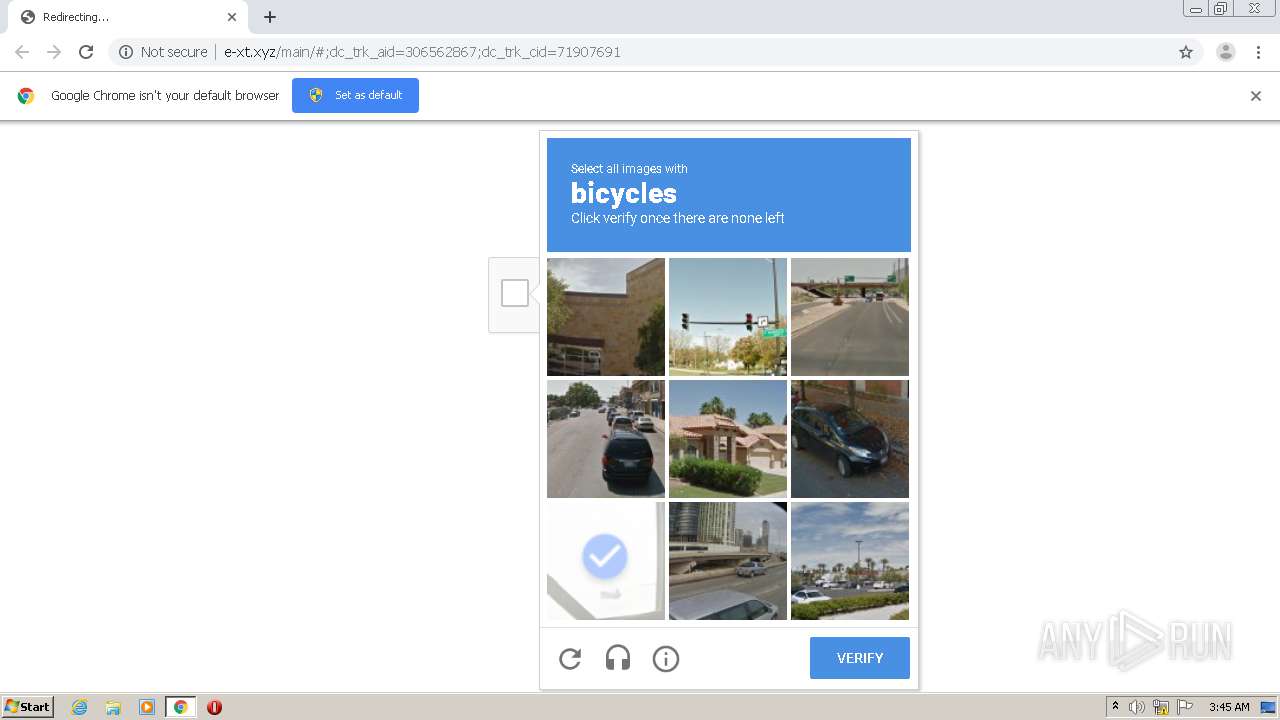
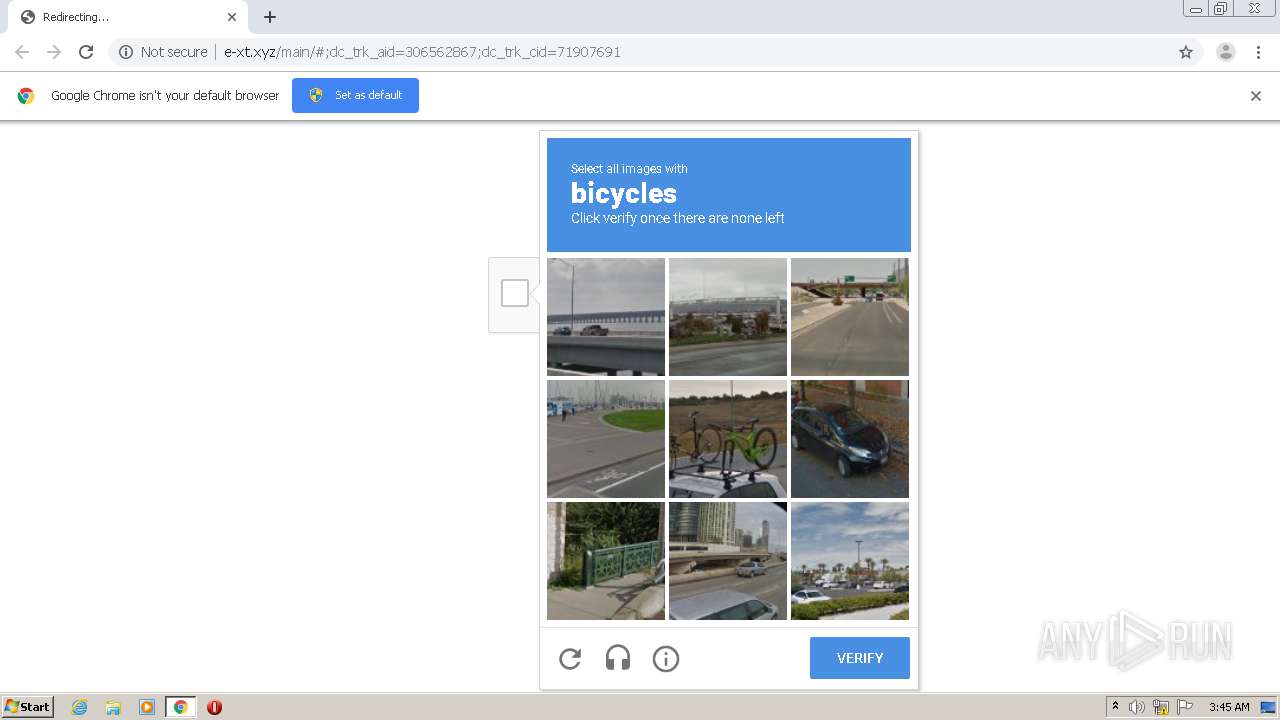
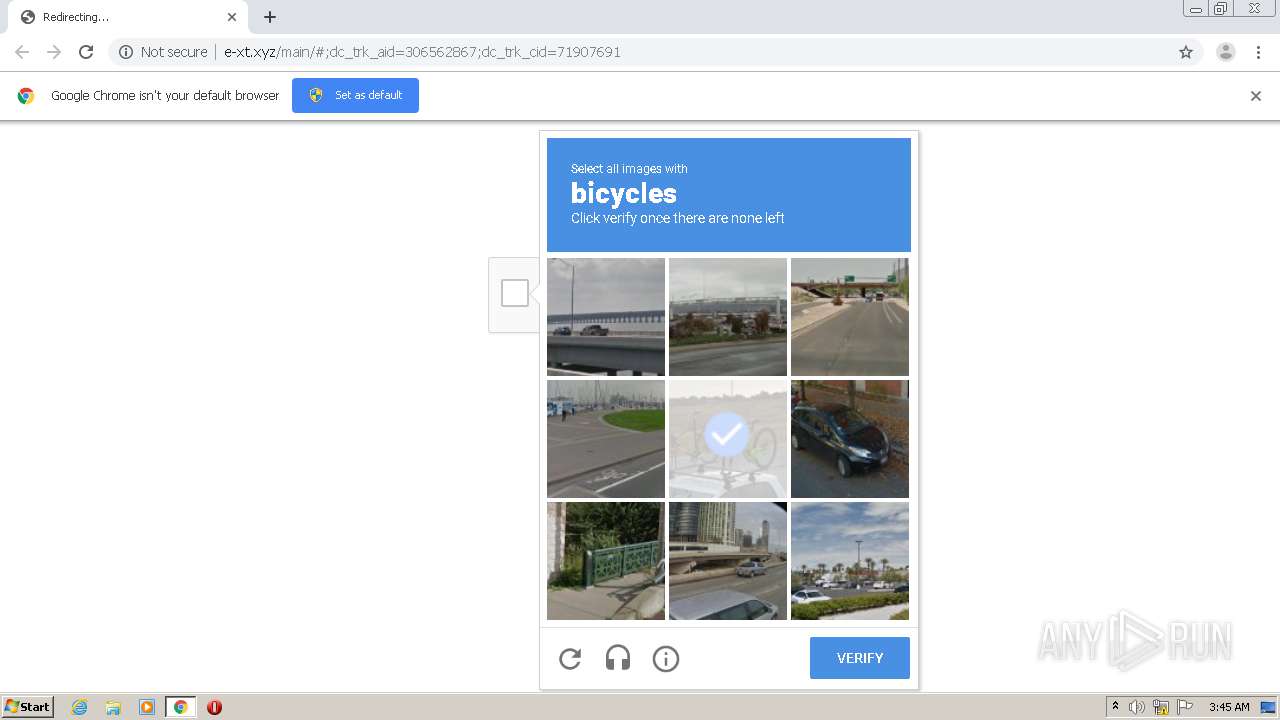
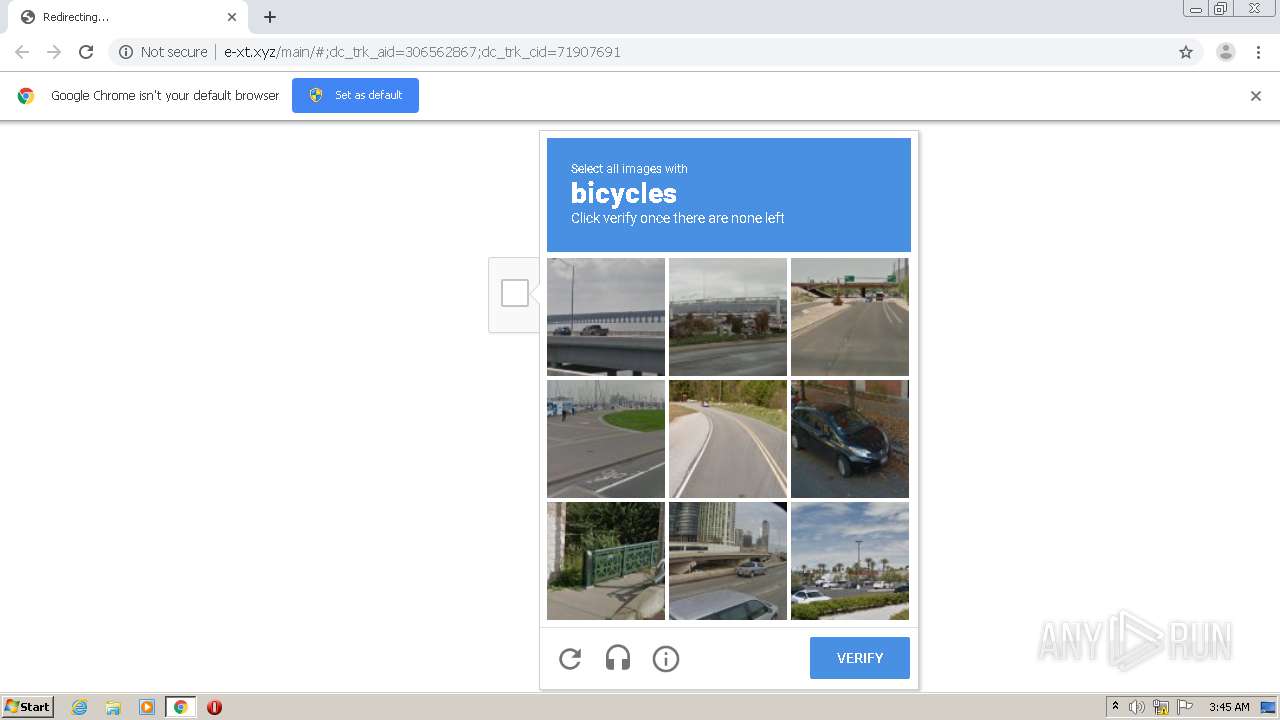
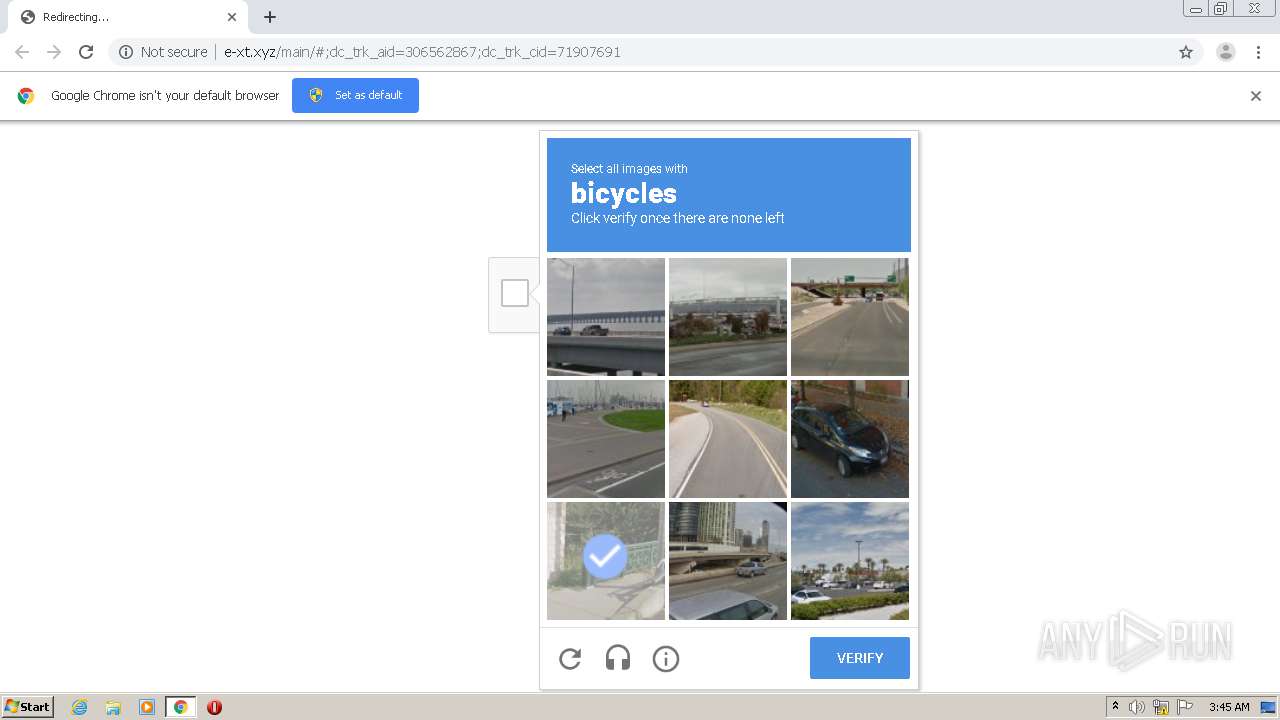
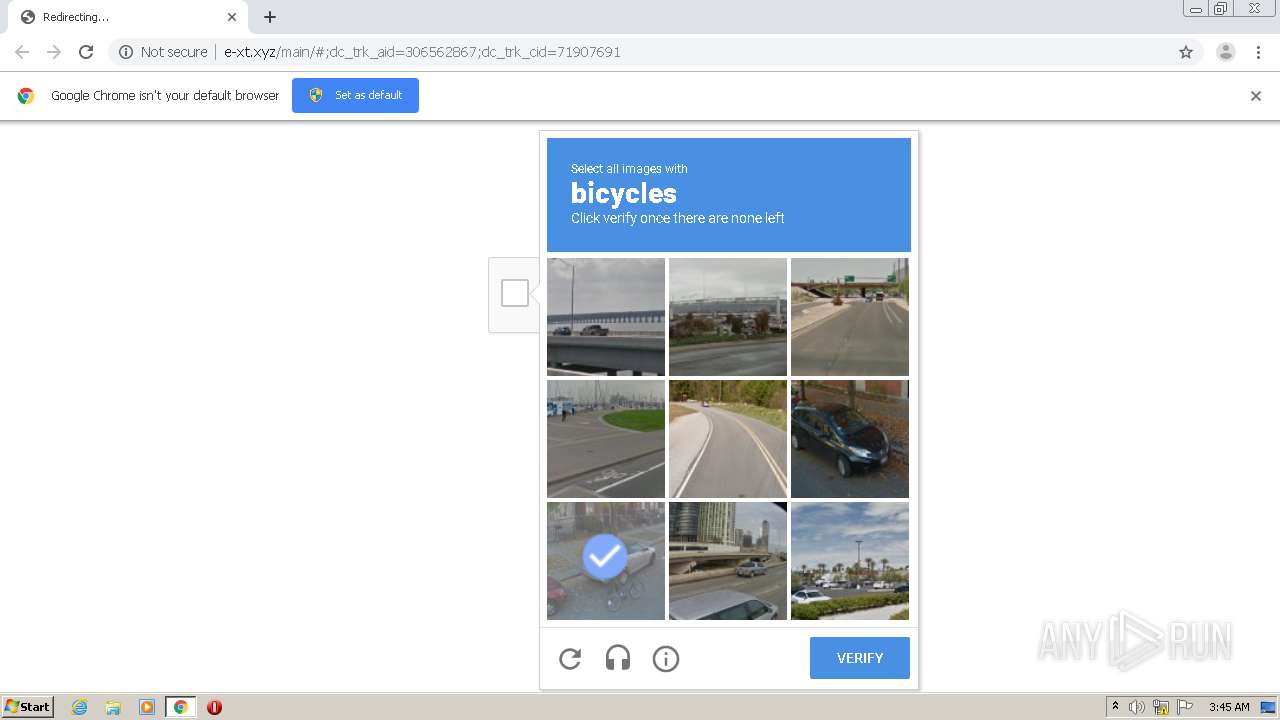
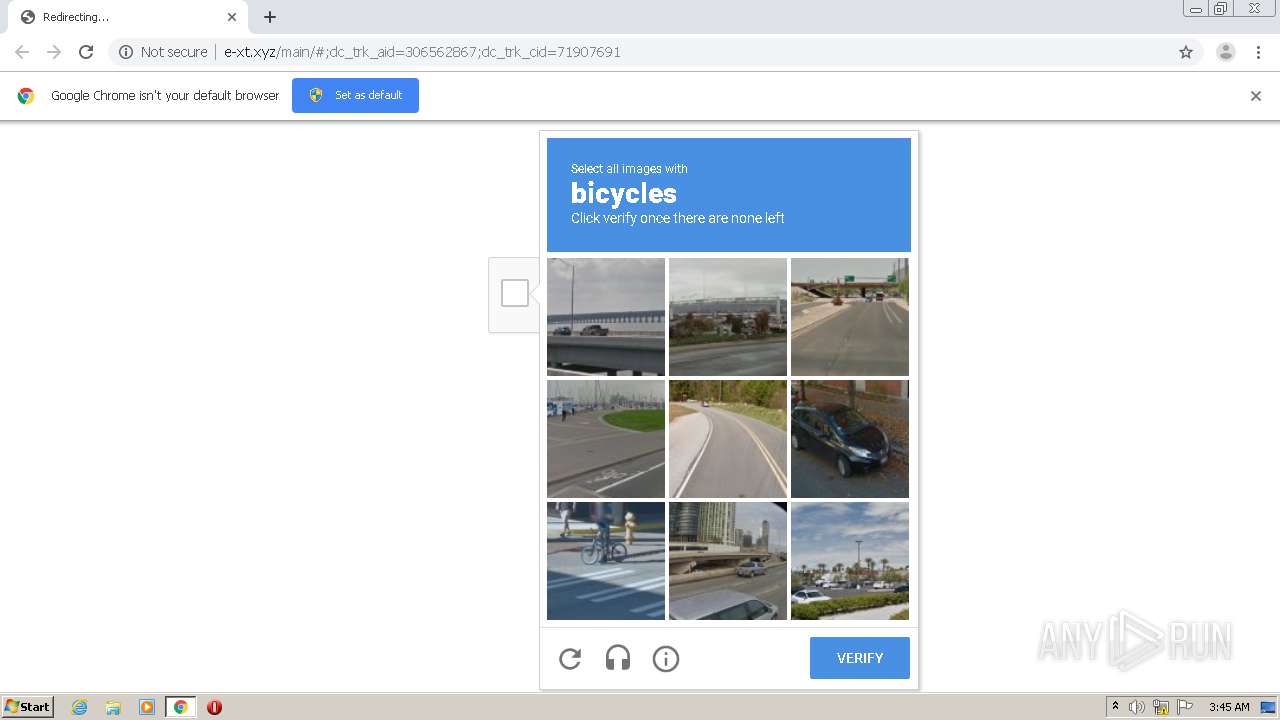
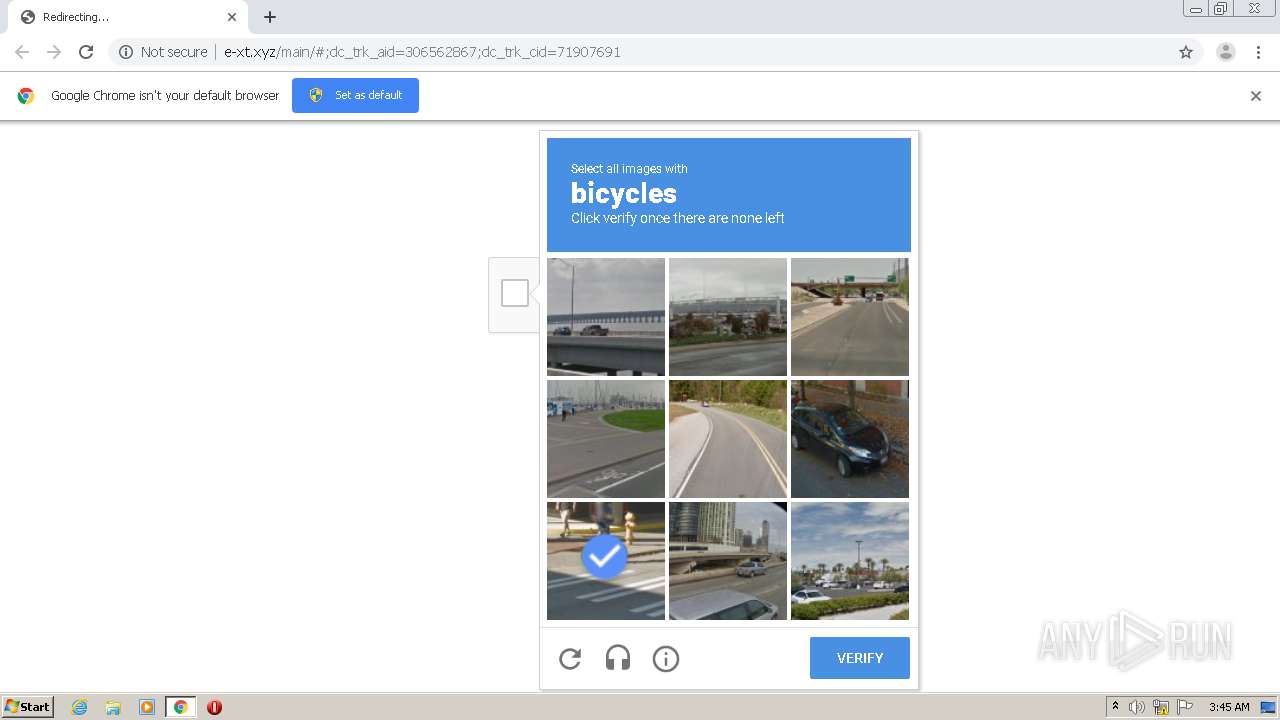
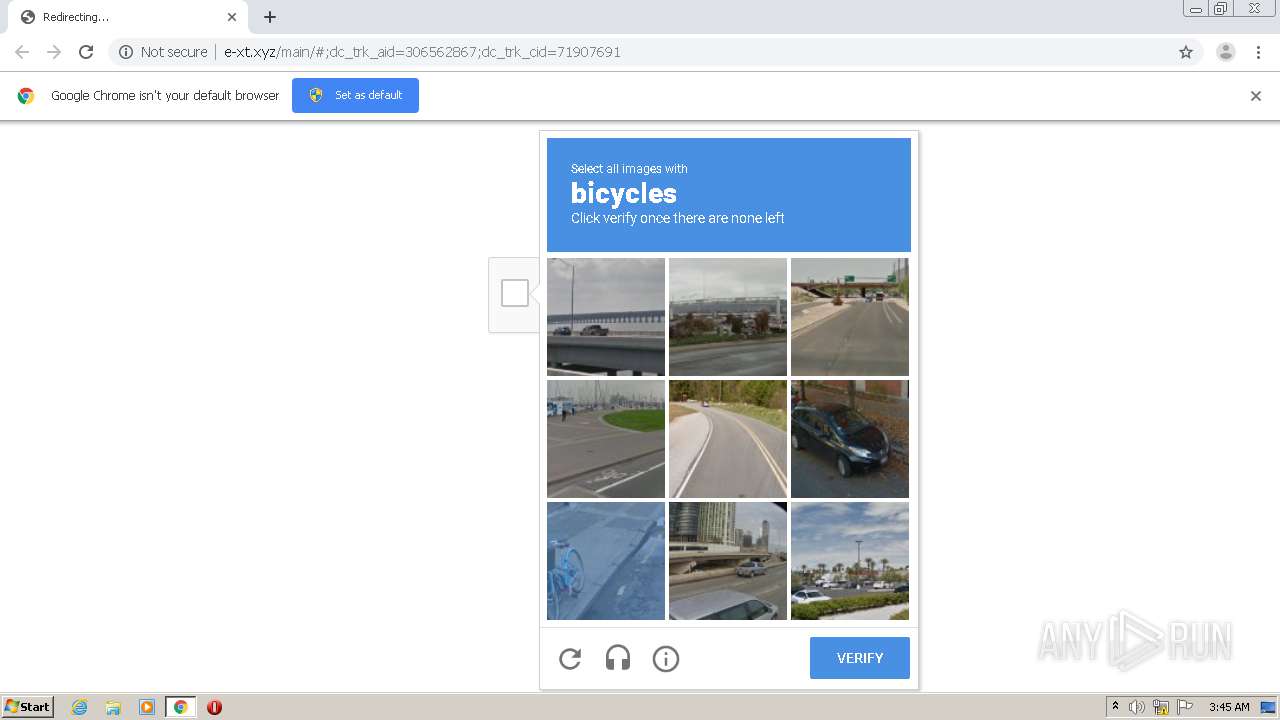
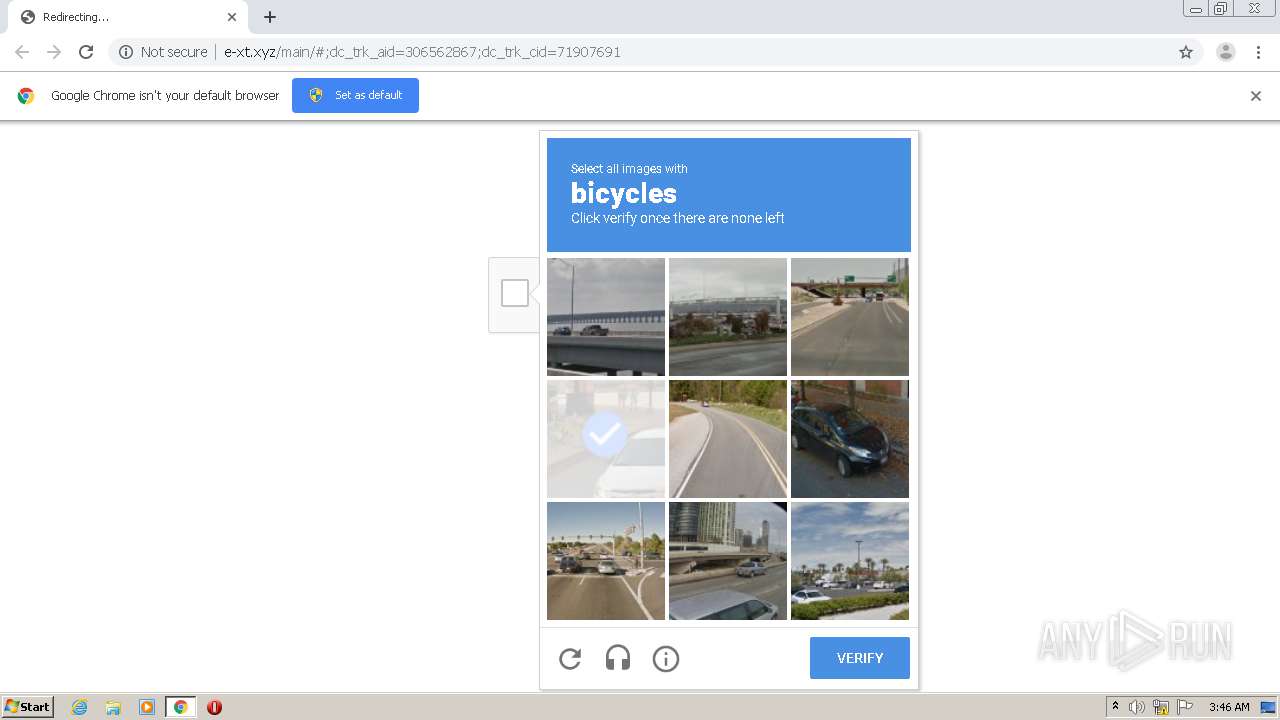
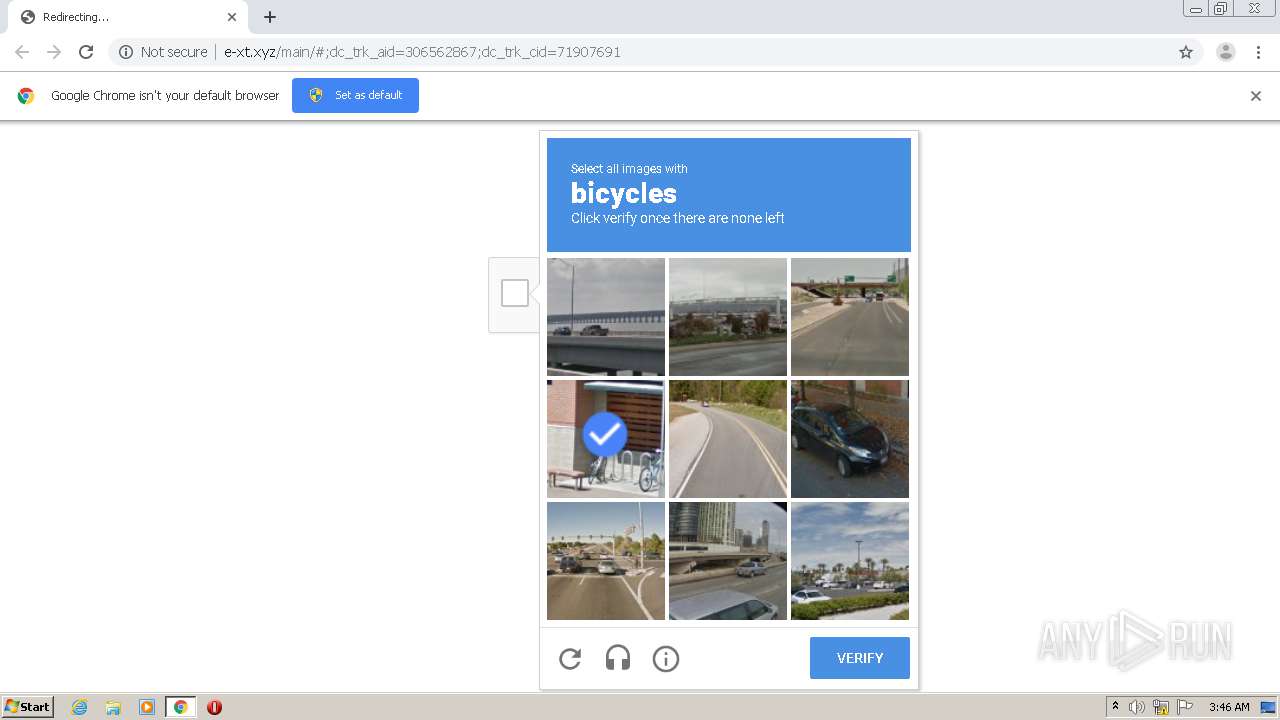
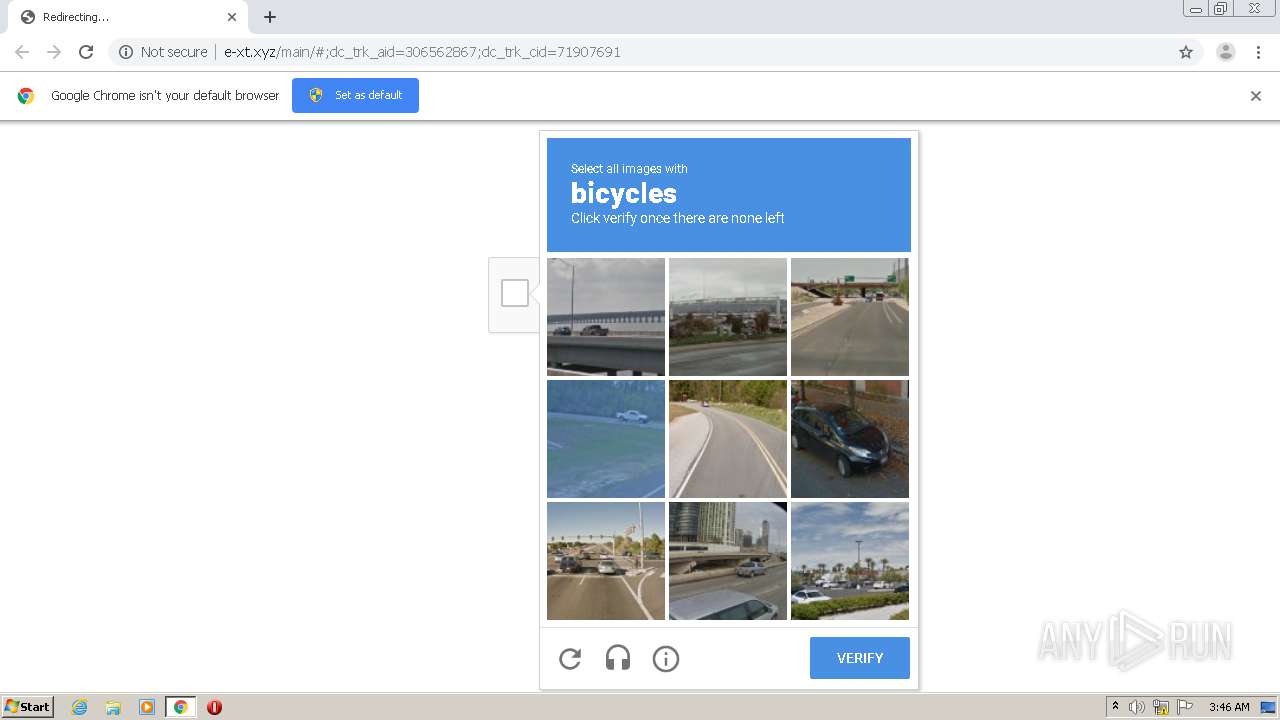
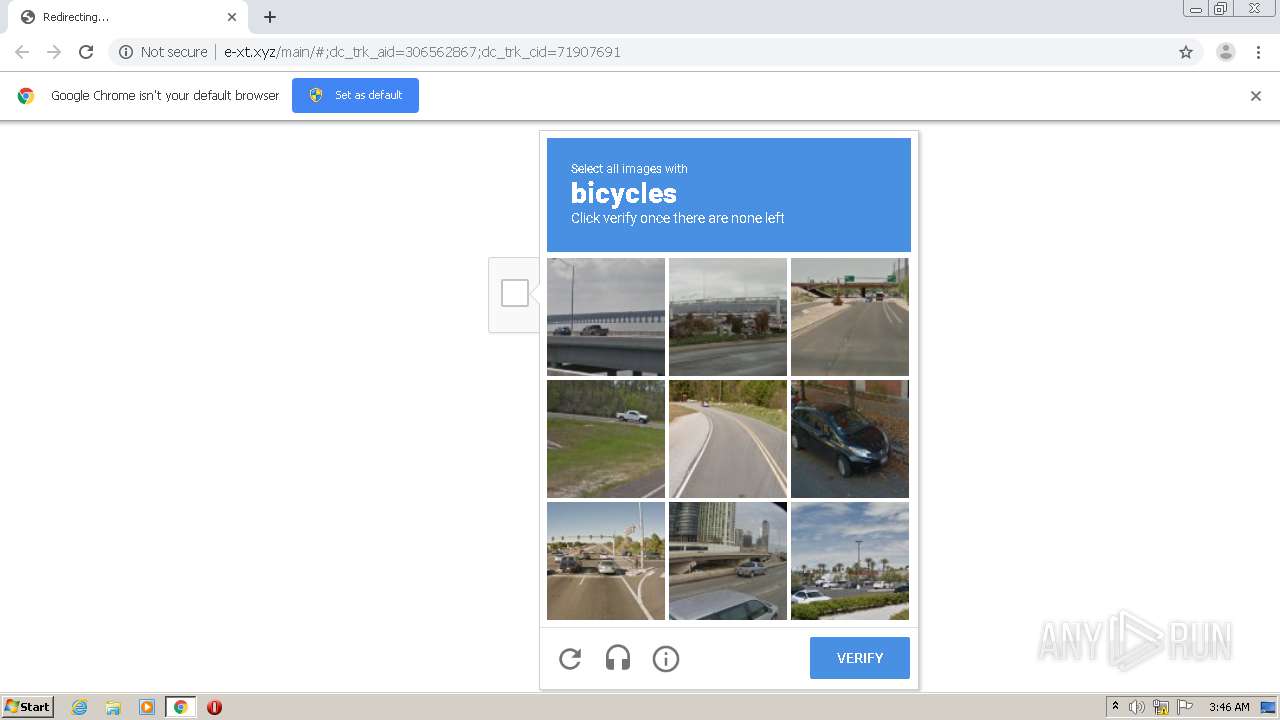
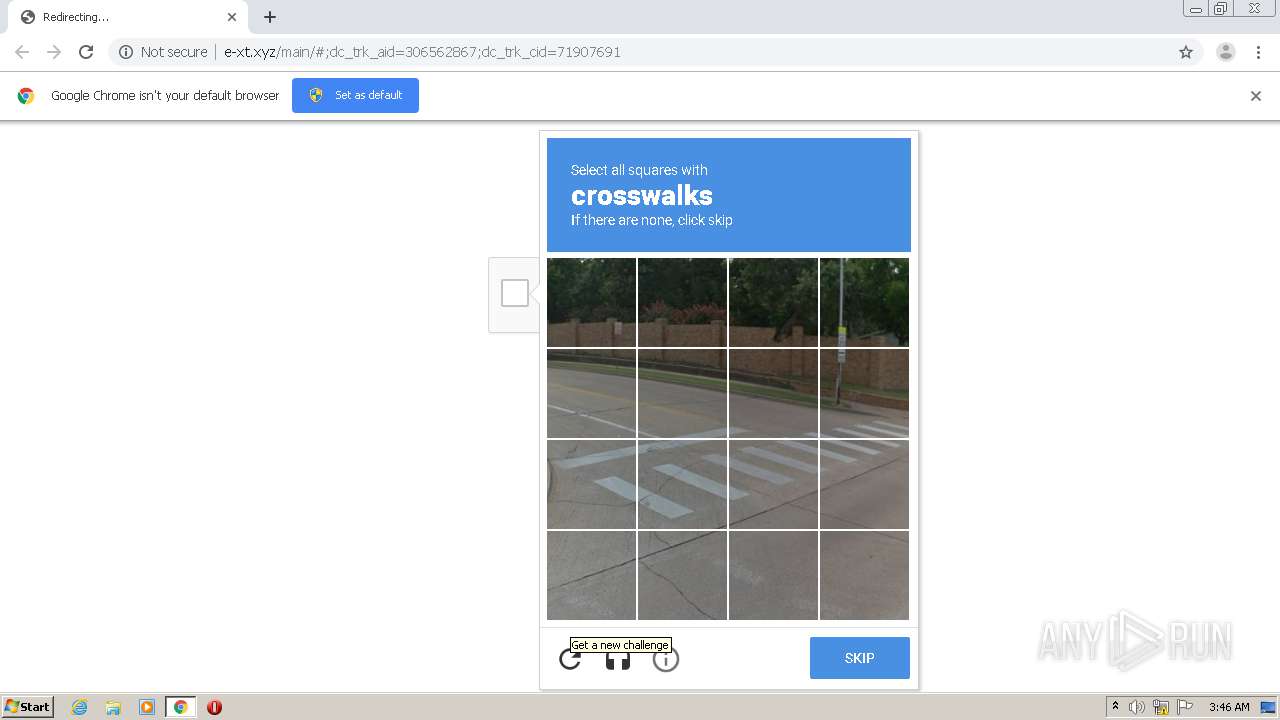
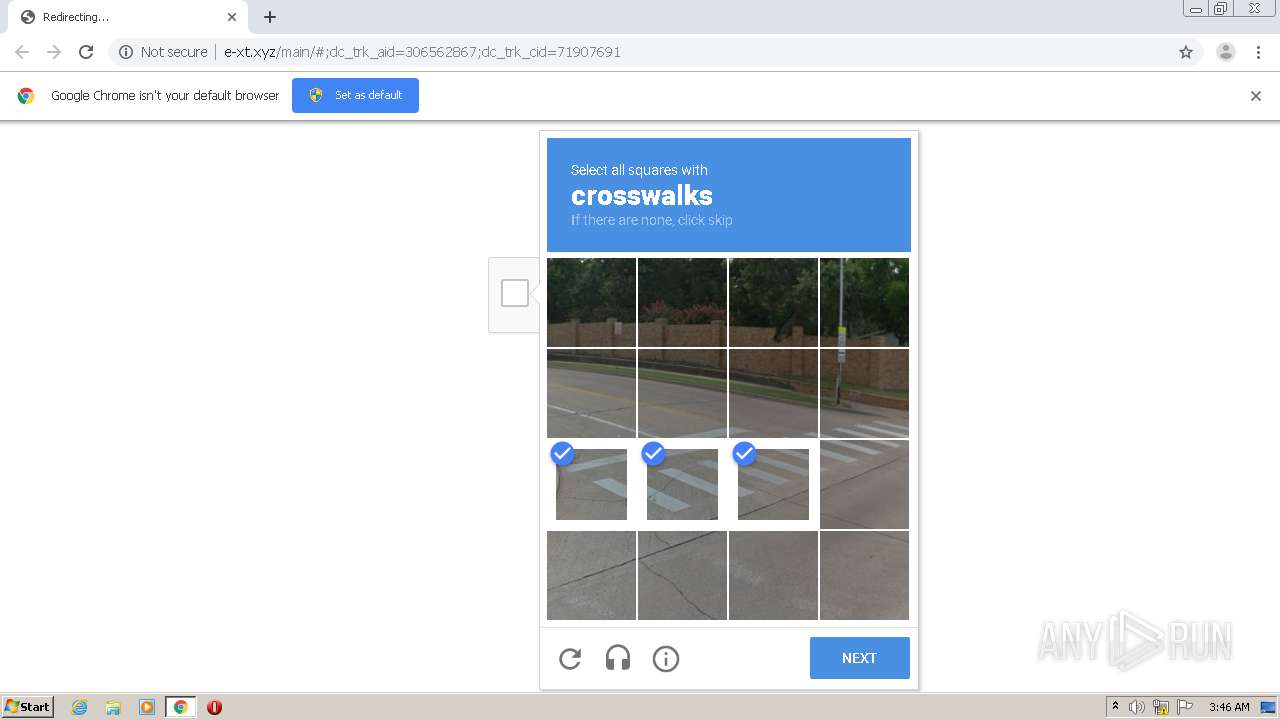
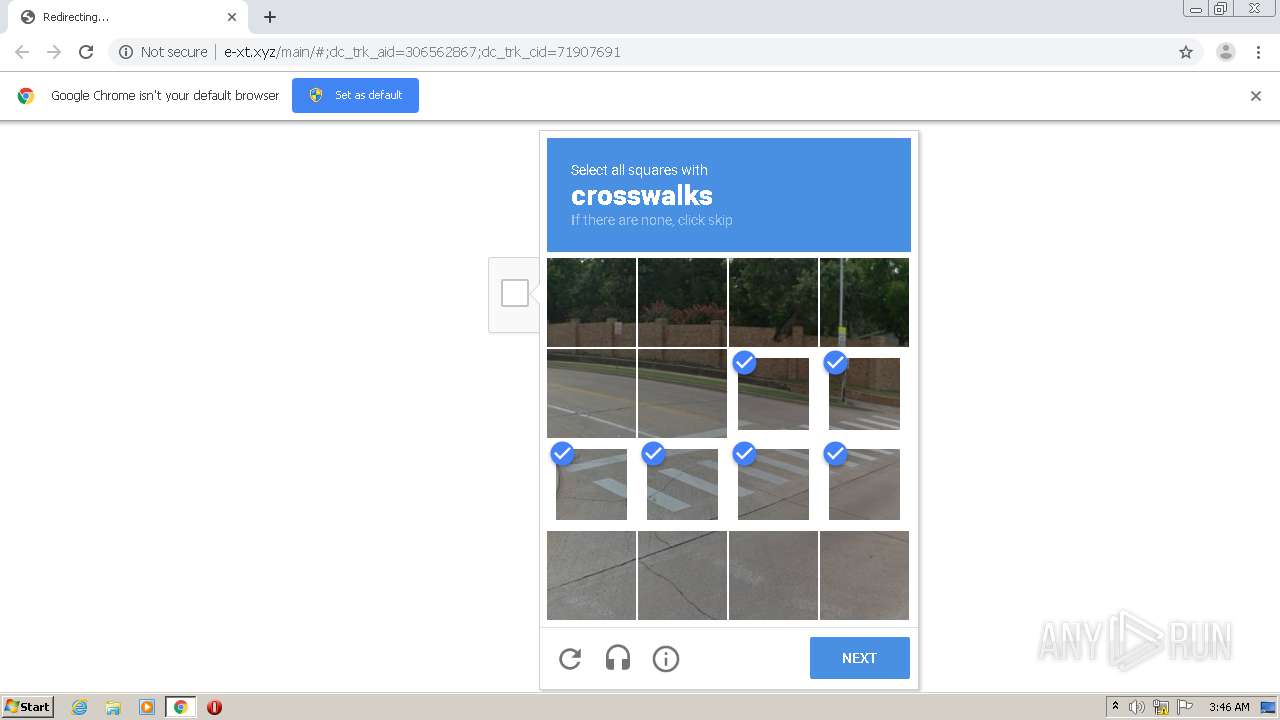
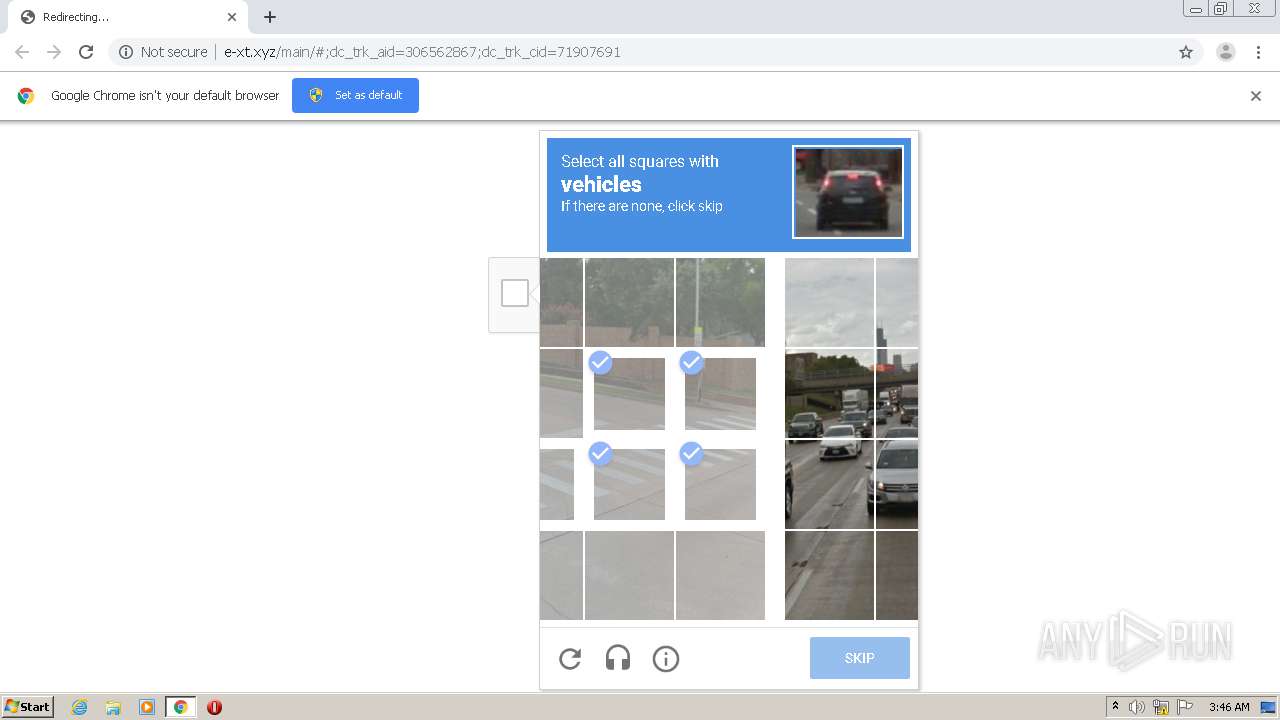
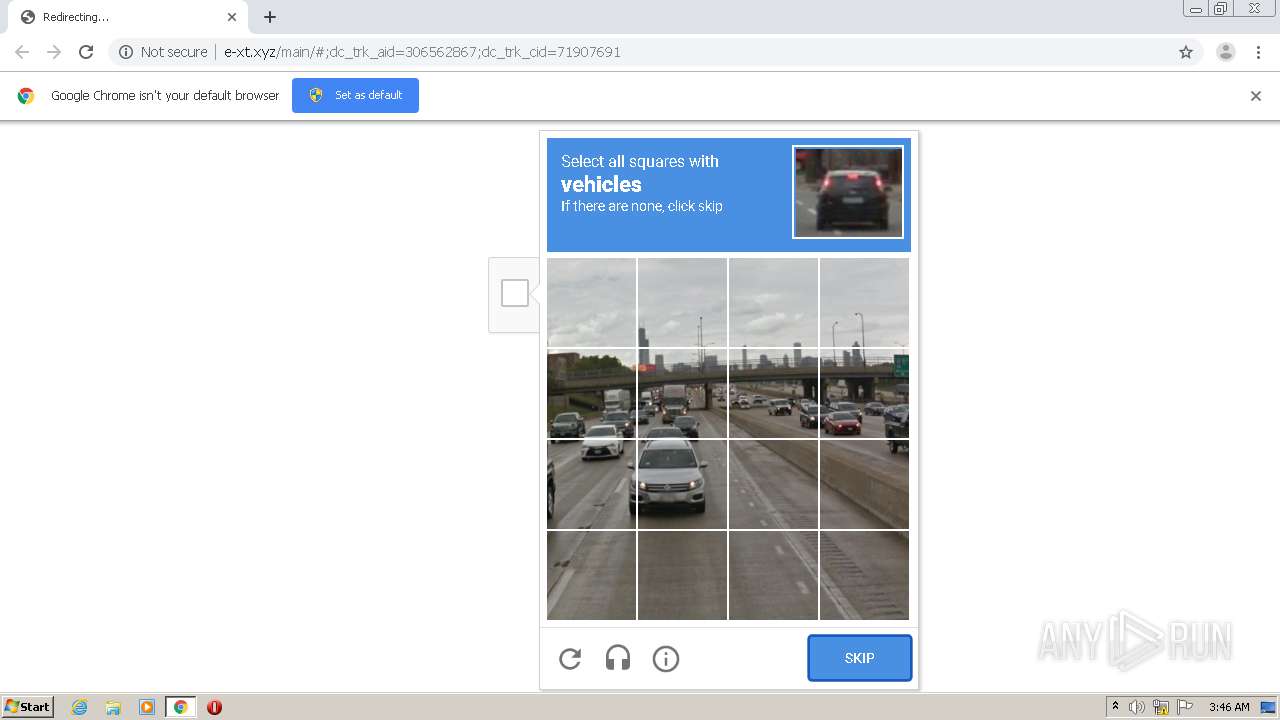
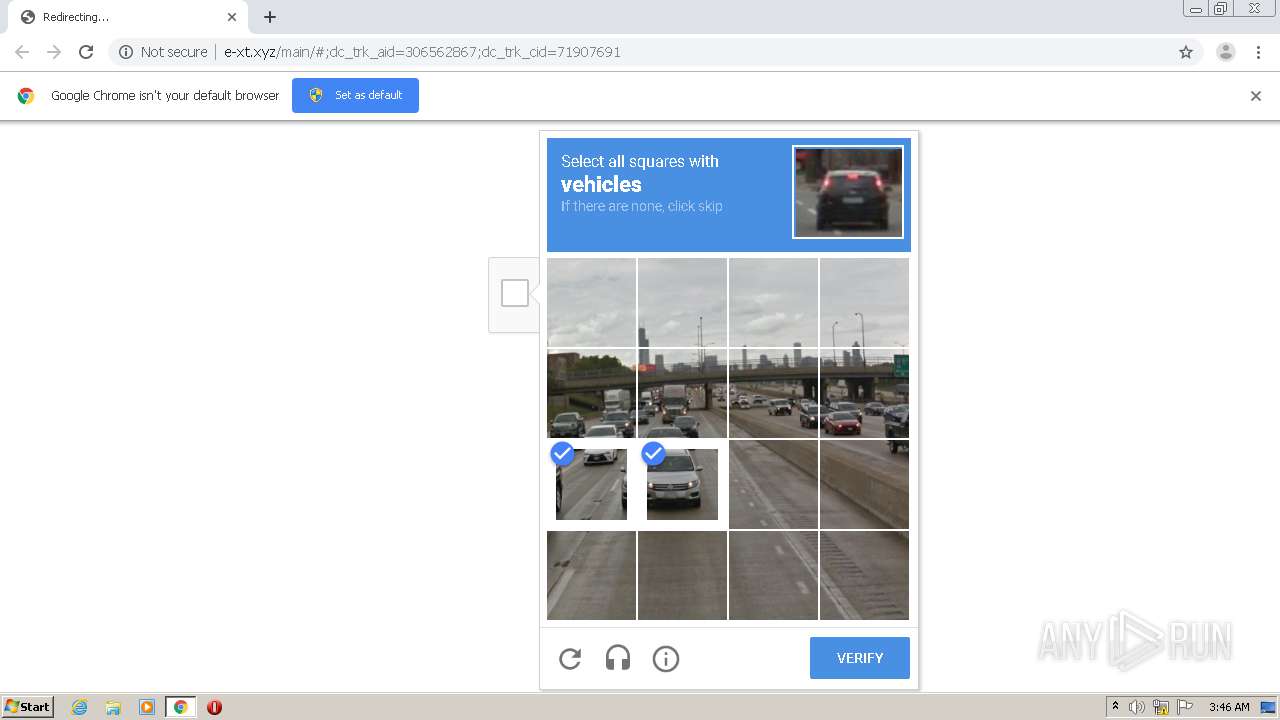
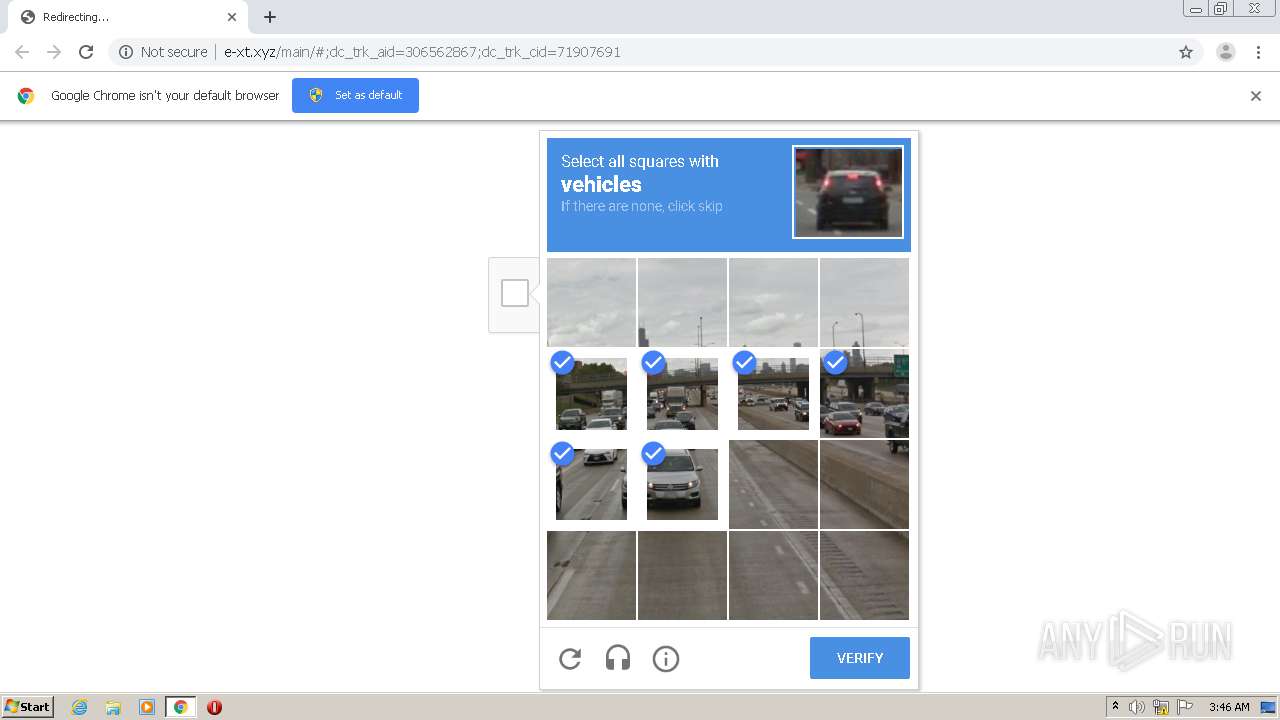
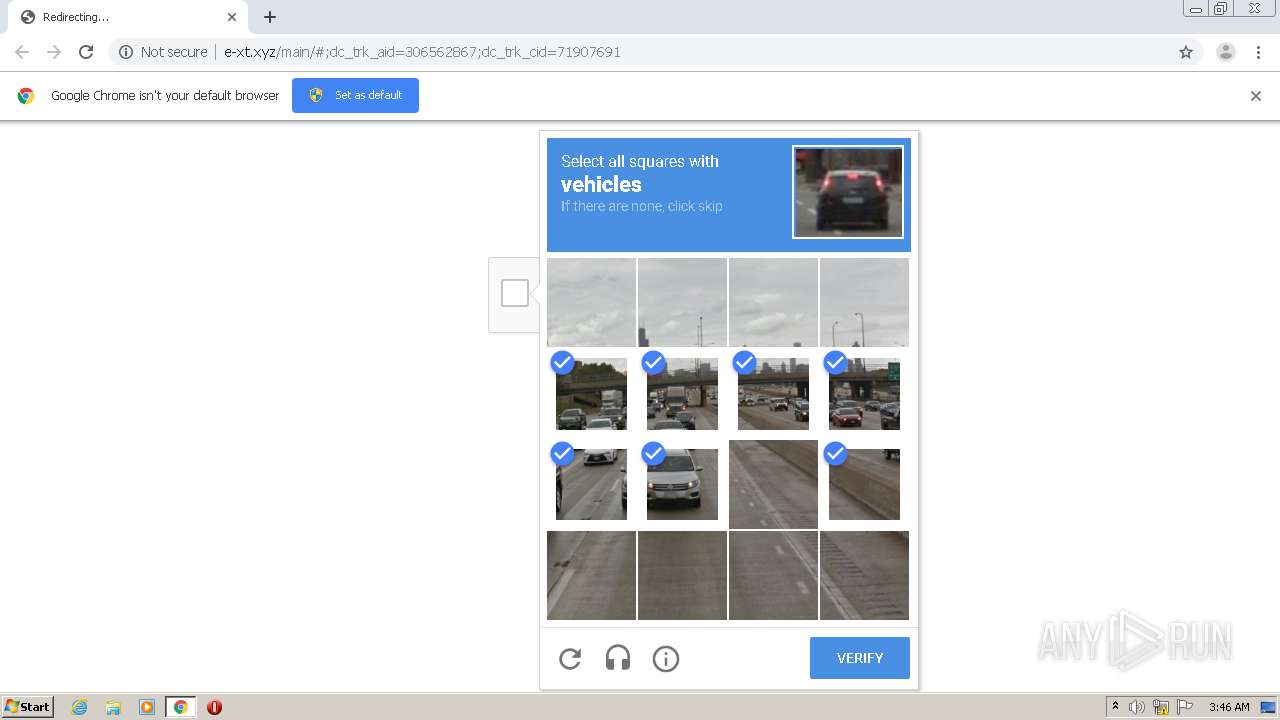
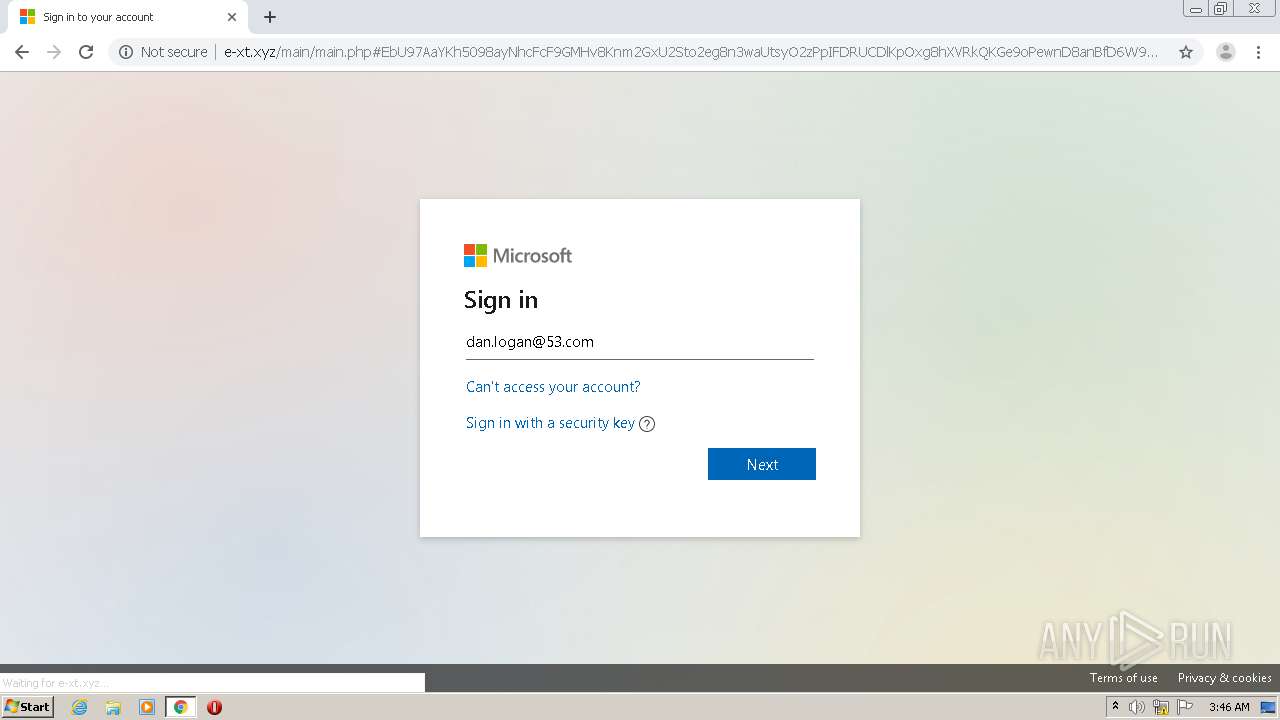
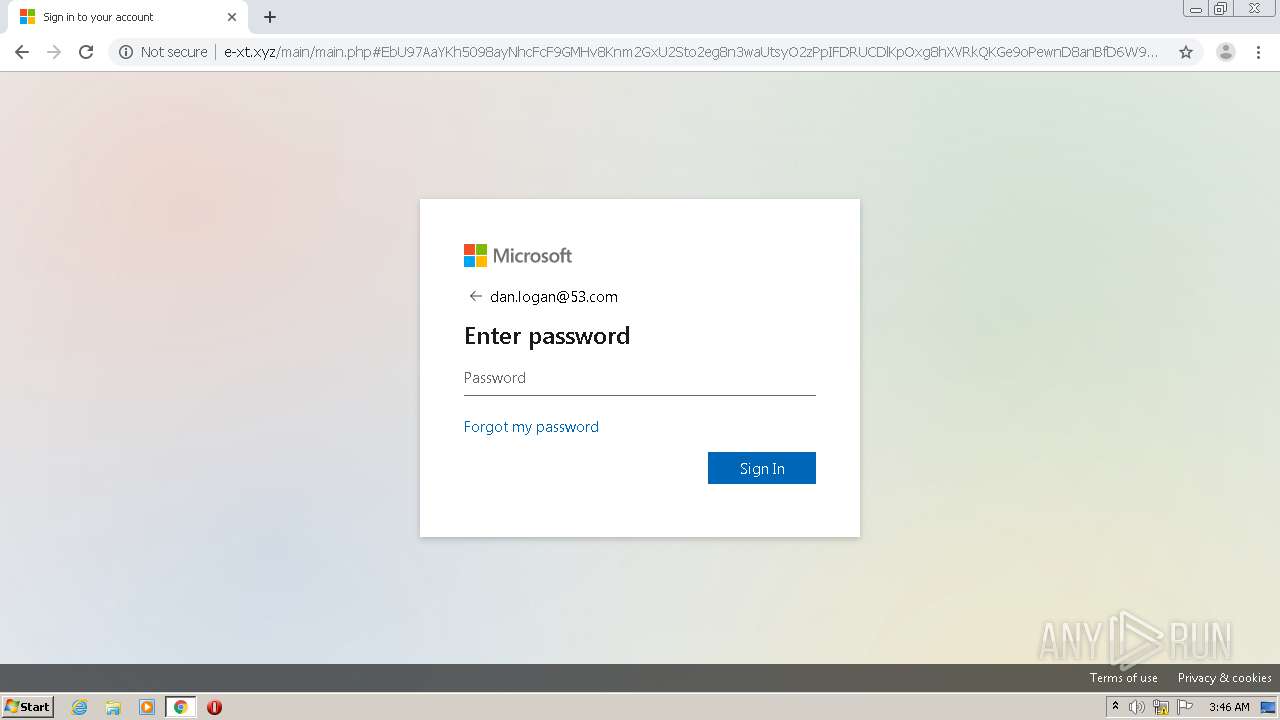
2004 | chrome.exe | GET | 200 | 198.84.123.130:80 | http://e-xt.xyz/mx/mbg.jpg | US | image | 368 Kb | suspicious |
2004 | chrome.exe | GET | 200 | 198.84.123.130:80 | http://e-xt.xyz/main/ | US | html | 2.96 Kb | suspicious |
2004 | chrome.exe | GET | 200 | 198.84.123.130:80 | http://e-xt.xyz/mx/style.css | US | text | 18.2 Kb | suspicious |
2004 | chrome.exe | GET | 200 | 198.84.123.130:80 | http://e-xt.xyz/favicon.ico | US | html | 135 b | suspicious |
2004 | chrome.exe | GET | 200 | 198.84.123.130:80 | http://e-xt.xyz/mx/favicon.ico | US | image | 16.7 Kb | suspicious |
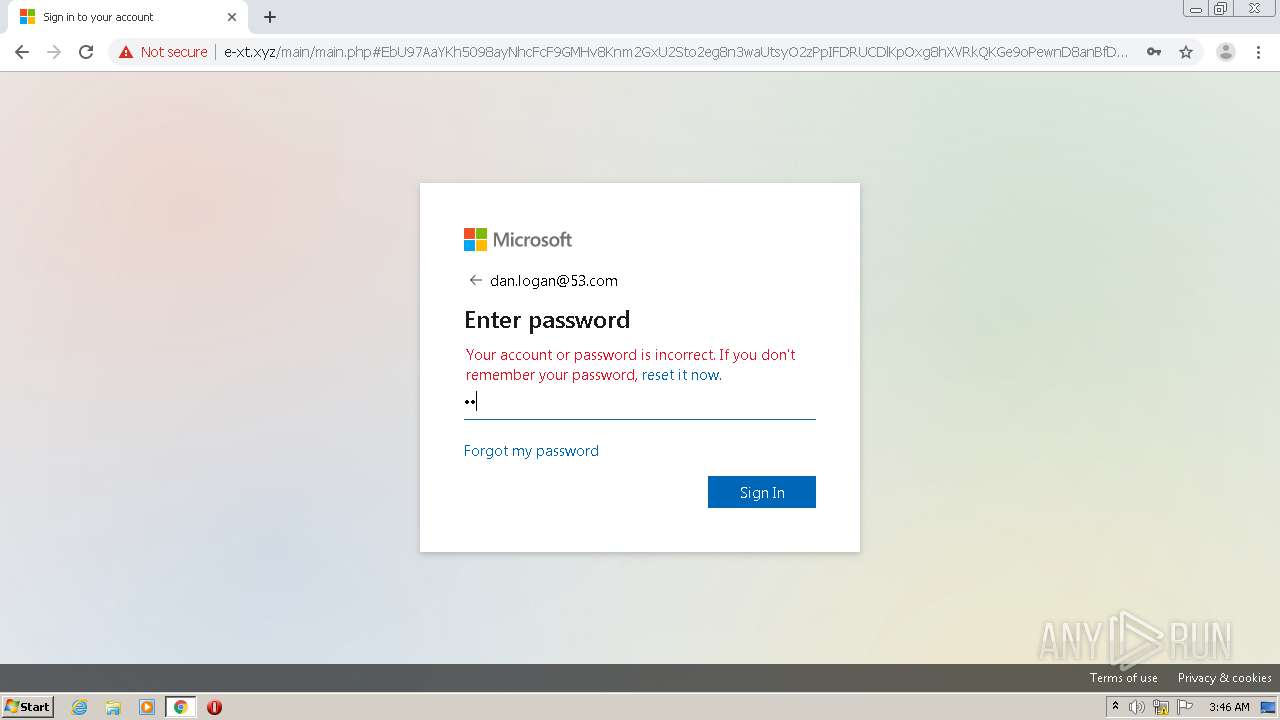
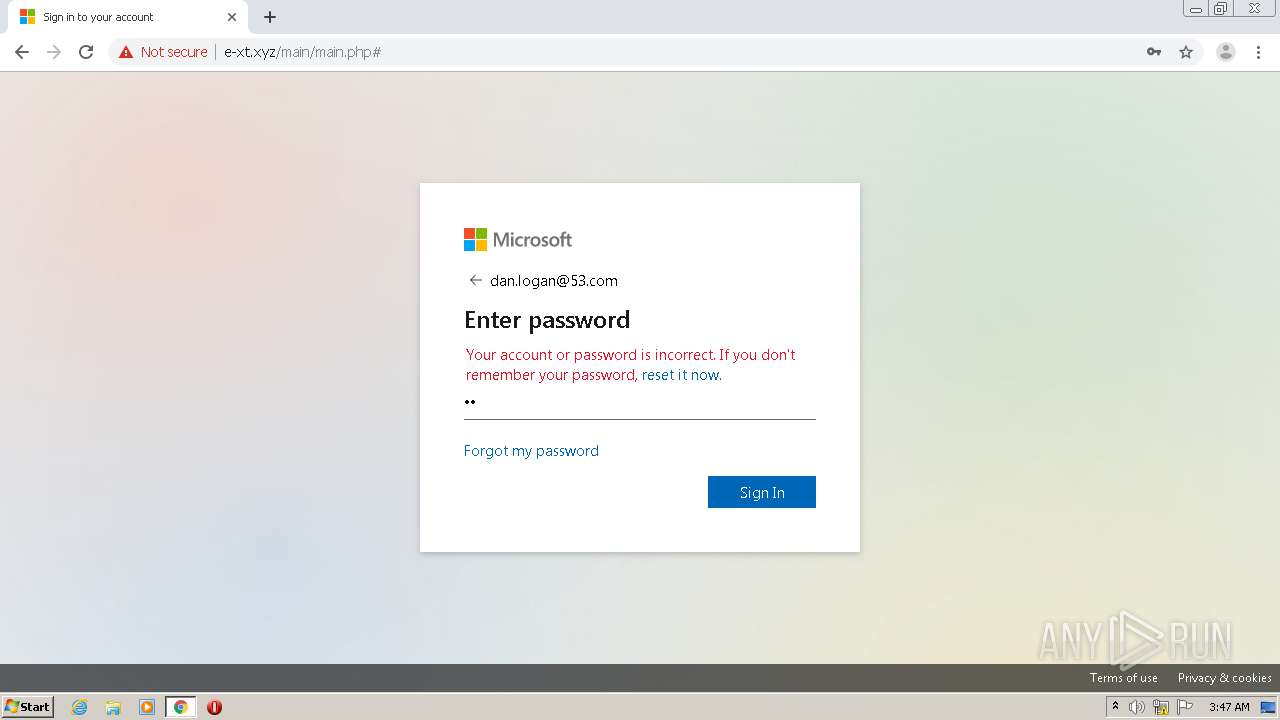
2004 | chrome.exe | POST | 200 | 198.84.123.130:80 | http://e-xt.xyz/main/main.php | US | html | 6.00 Kb | suspicious |
2004 | chrome.exe | POST | 200 | 198.84.123.130:80 | http://e-xt.xyz/etc/login.php | US | image | 16.7 Kb | suspicious |
2004 | chrome.exe | GET | 302 | 198.84.123.130:80 | http://e-xt.xyz/index.php?e=ZGFuLmxvZ2FuQDUzLmNvbQ==&eCodsId=%2Fj7Djh5FIMQzm%2FAs57Seog%3D%3D | US | html | 135 b | suspicious |
2004 | chrome.exe | GET | 200 | 198.84.123.130:80 | http://e-xt.xyz/ddm/trackclk/N96001.2399100CRM/B9941585.134363607?e=ZGFuLmxvZ2FuQDUzLmNvbQ==&eCodsId=%2Fj7Djh5FIMQzm%2FAs57Seog%3D%3D | US | html | 135 b | suspicious |
2004 | chrome.exe | GET | 200 | 198.84.123.130:80 | http://e-xt.xyz/mx/logo.svg | US | image | 1.40 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2004 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2004 | chrome.exe | 13.224.194.48:80 | sas-tk.neolane.net | — | US | whitelisted |
2004 | chrome.exe | 198.84.123.130:80 | e-xt.xyz | Hostwinds LLC. | US | suspicious |
2004 | chrome.exe | 209.197.3.15:443 | stackpath.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2004 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
2004 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2004 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
2004 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2004 | chrome.exe | 13.107.246.13:443 | aadcdn.msauth.net | Microsoft Corporation | US | suspicious |
2004 | chrome.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sas-tk.neolane.net |
| whitelisted |
accounts.google.com |
| shared |
e-xt.xyz |
| suspicious |
www.google.com |
| malicious |
stackpath.bootstrapcdn.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
aadcdn.msauth.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2004 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2004 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2004 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2004 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2004 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2004 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2004 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2004 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2004 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2004 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1 ETPRO signatures available at the full report