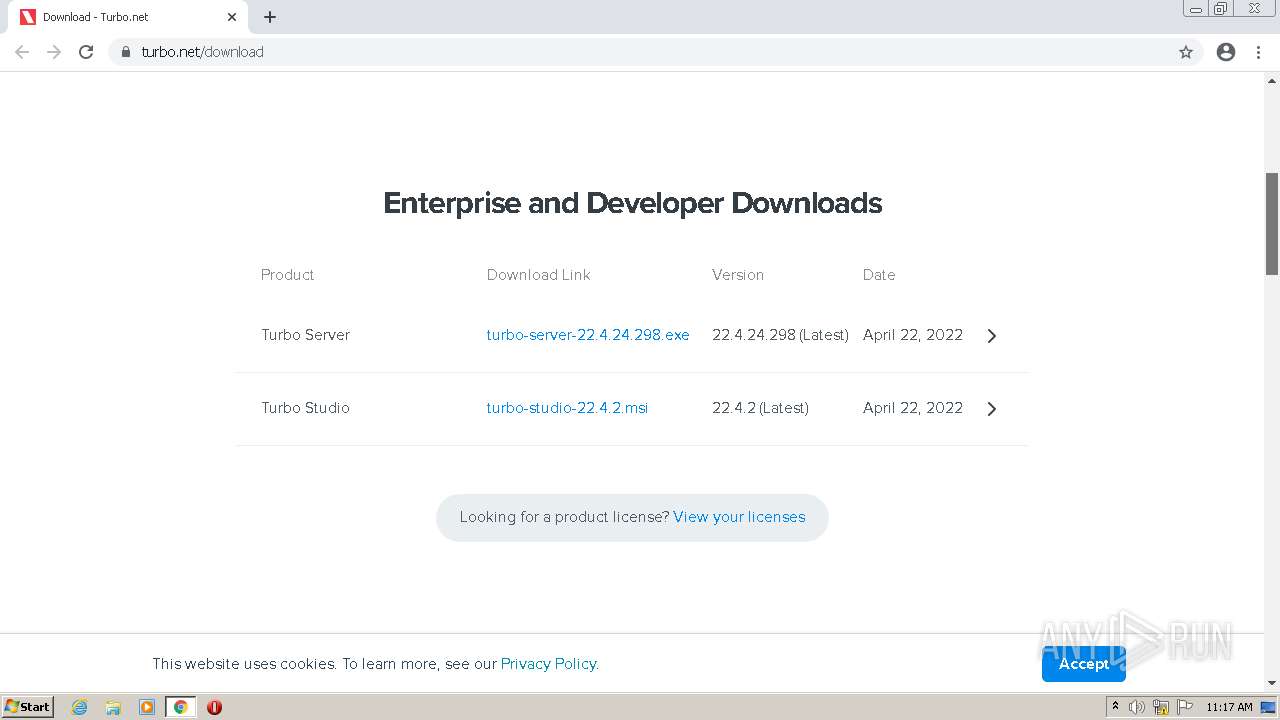
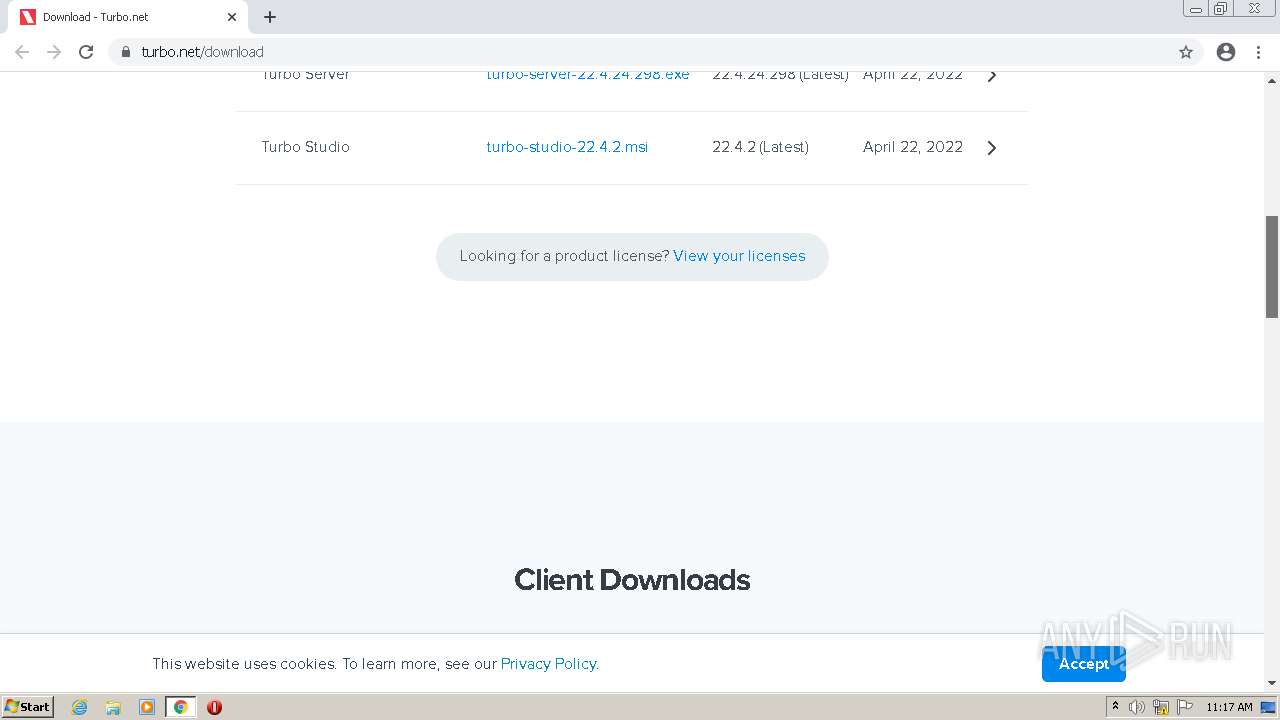
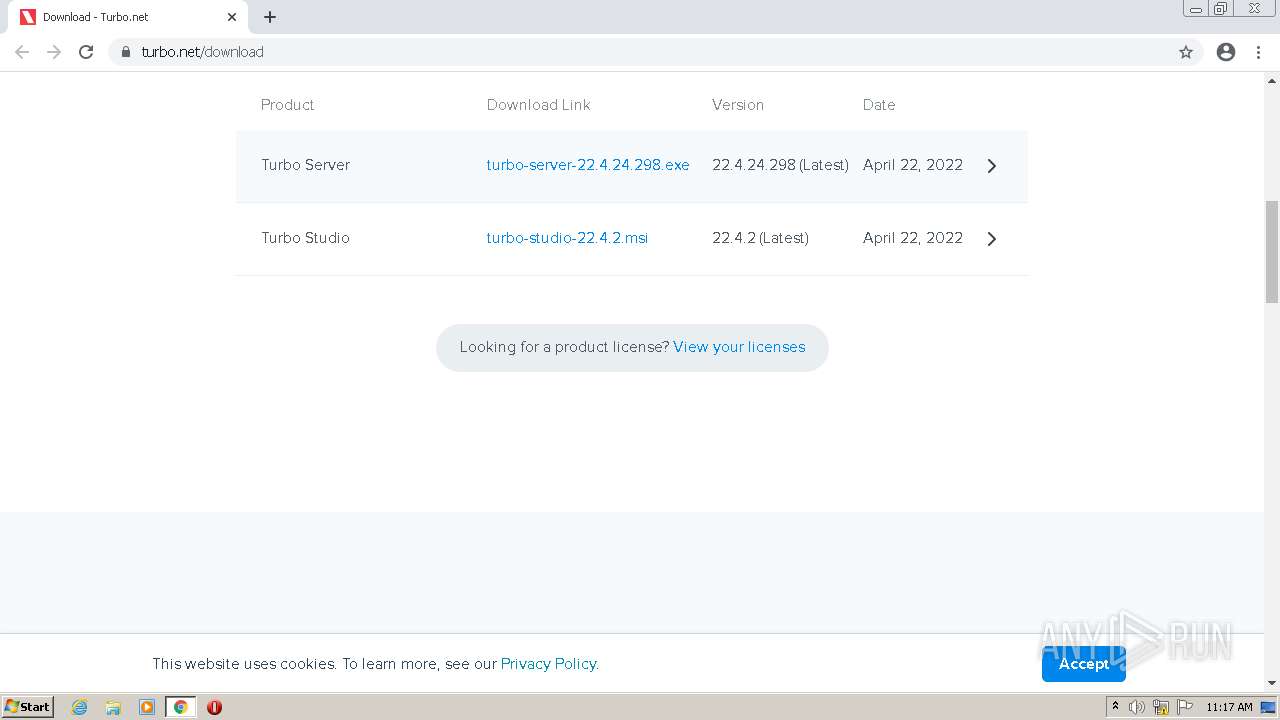
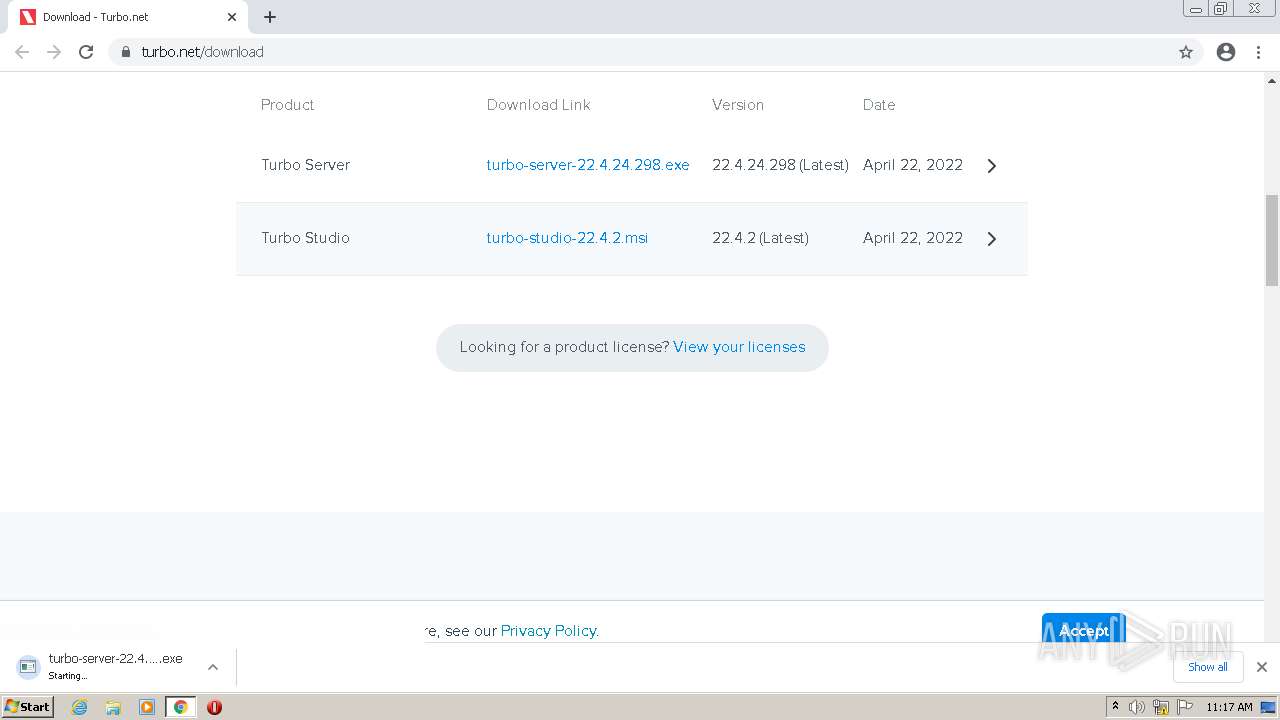
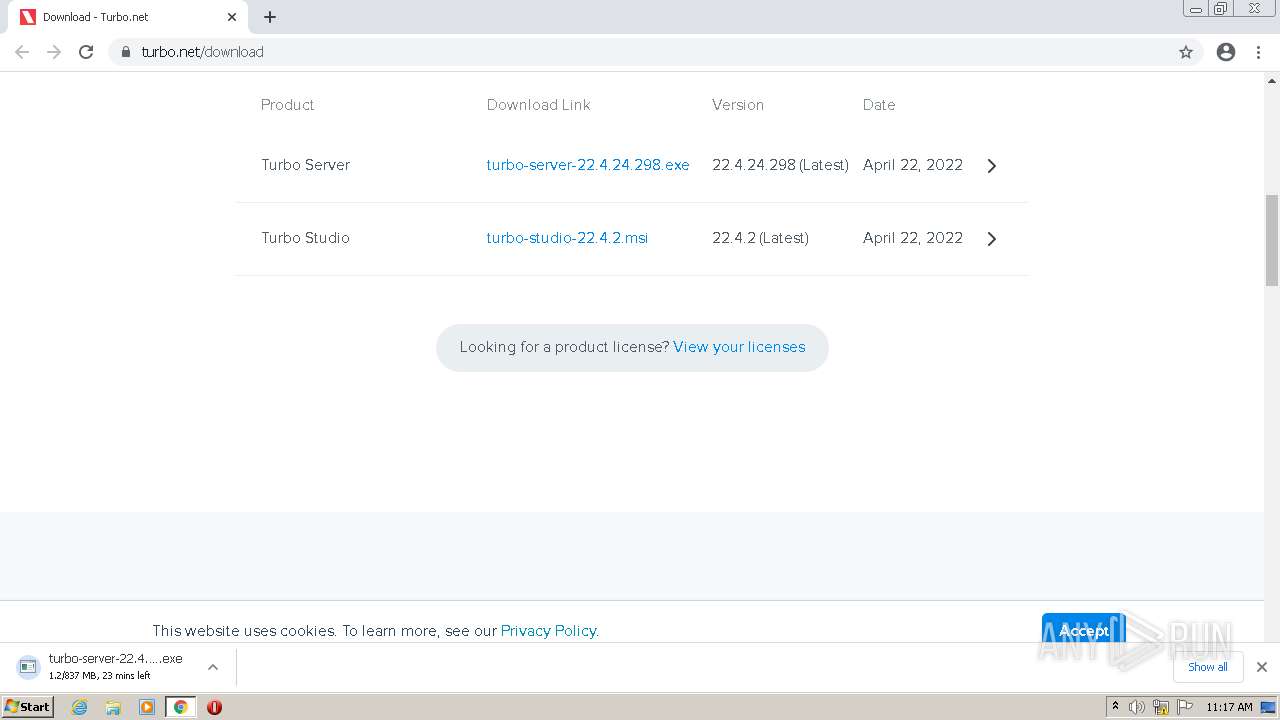
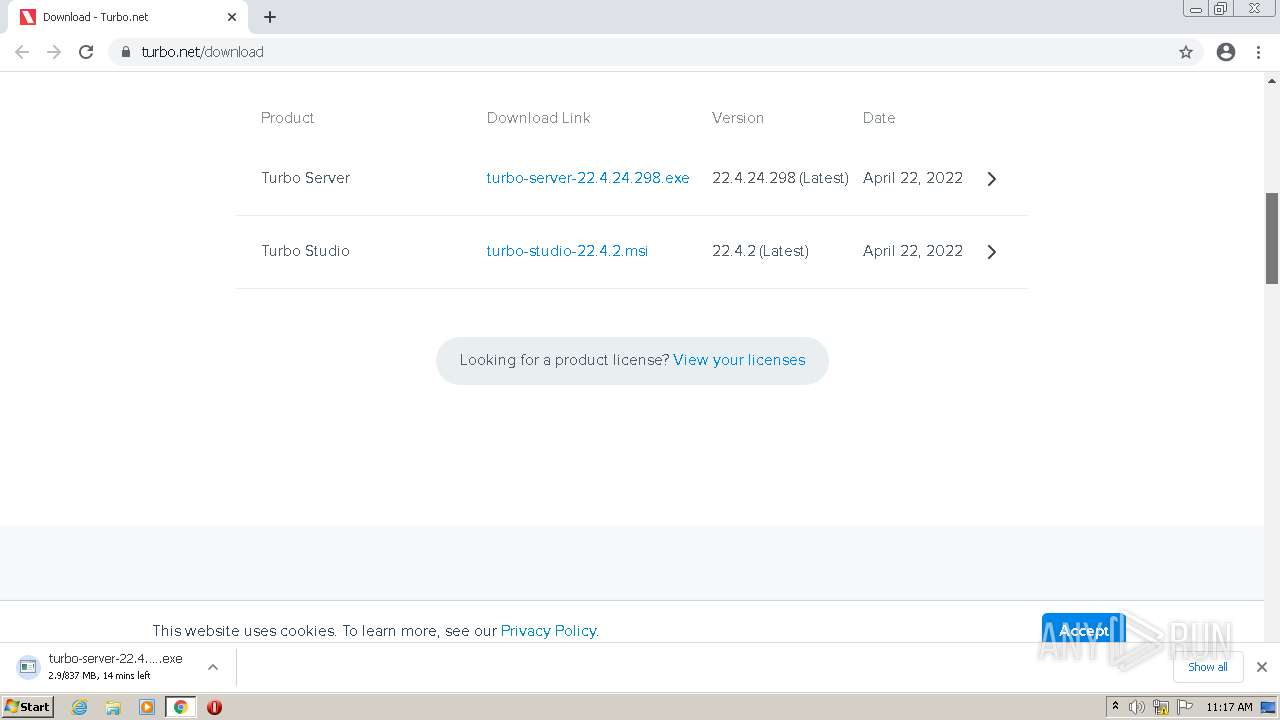
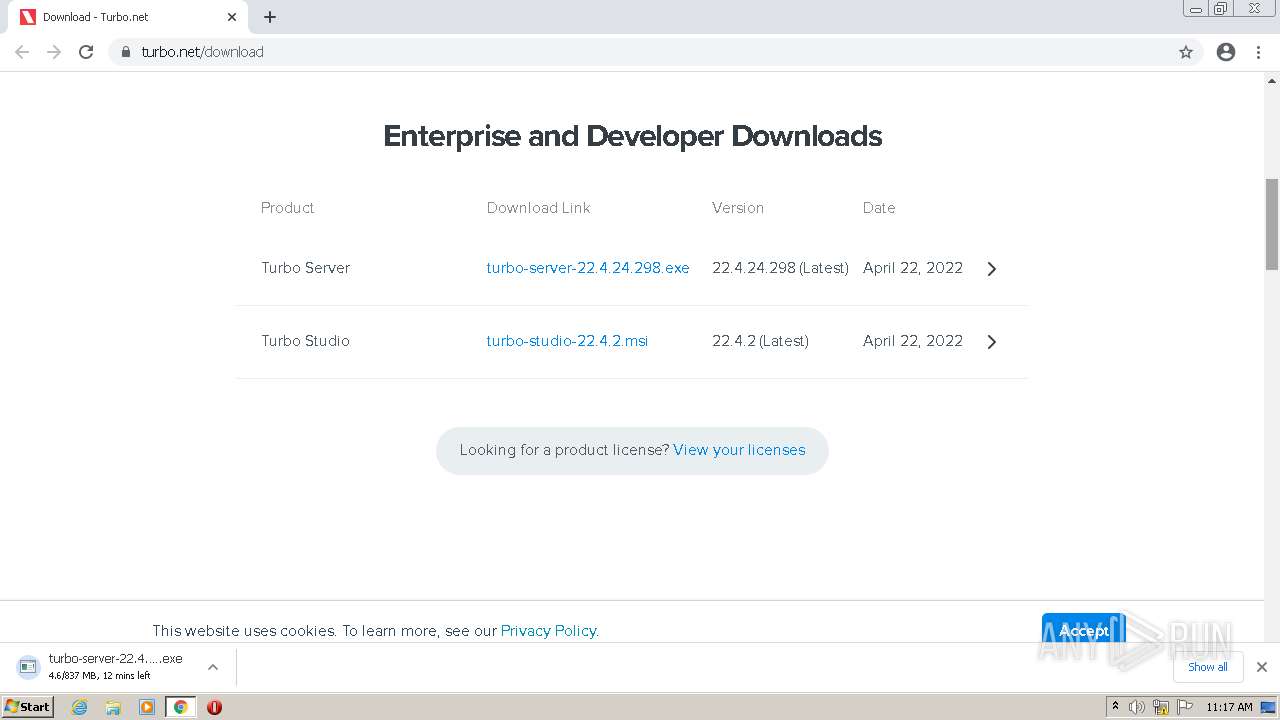
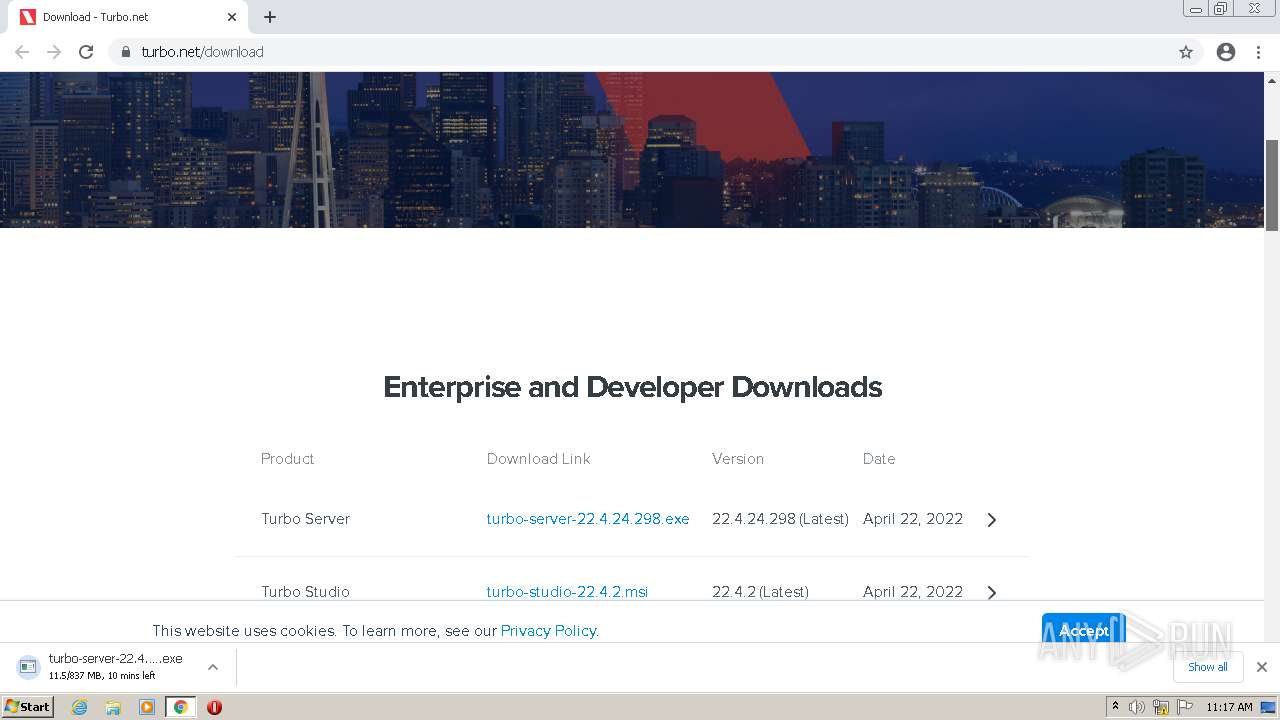
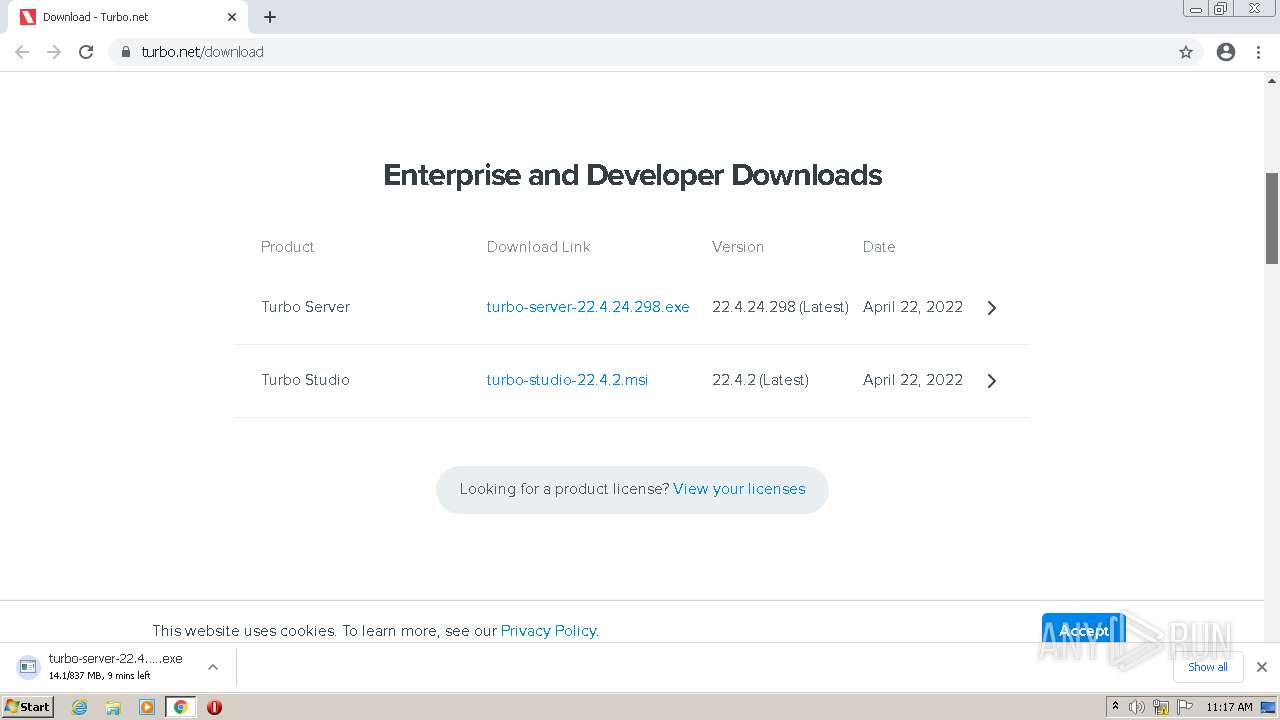
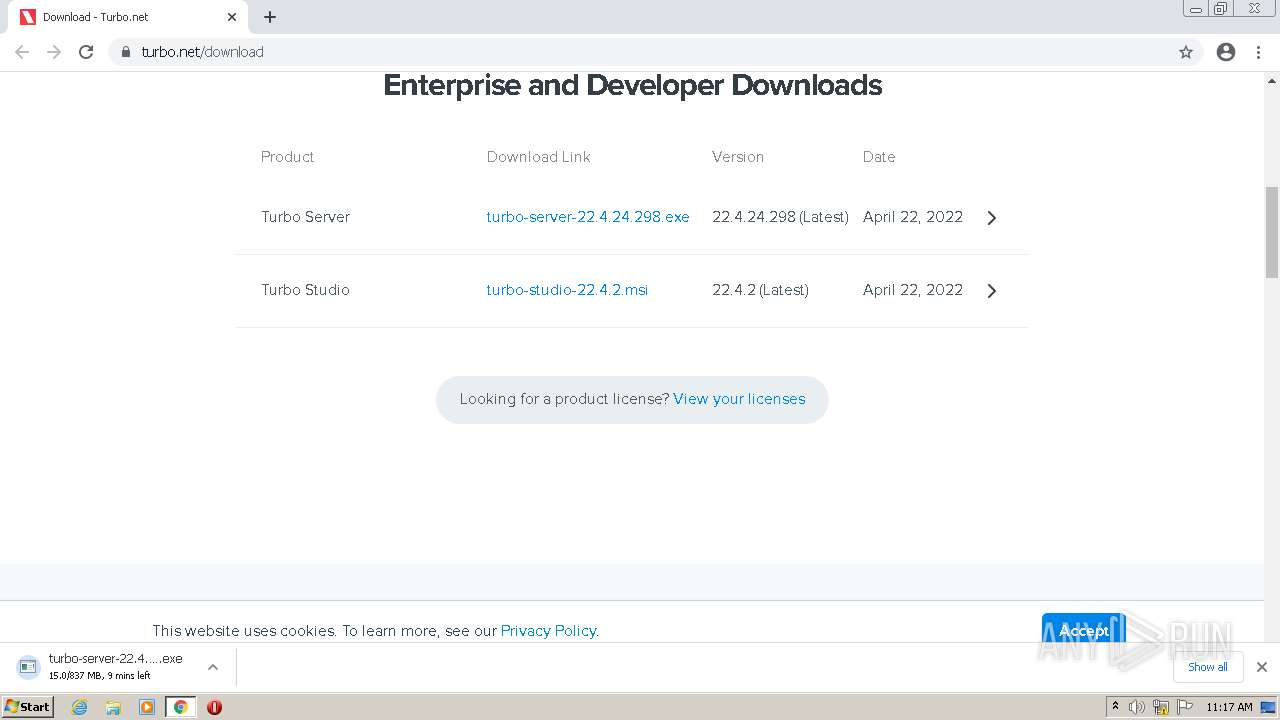
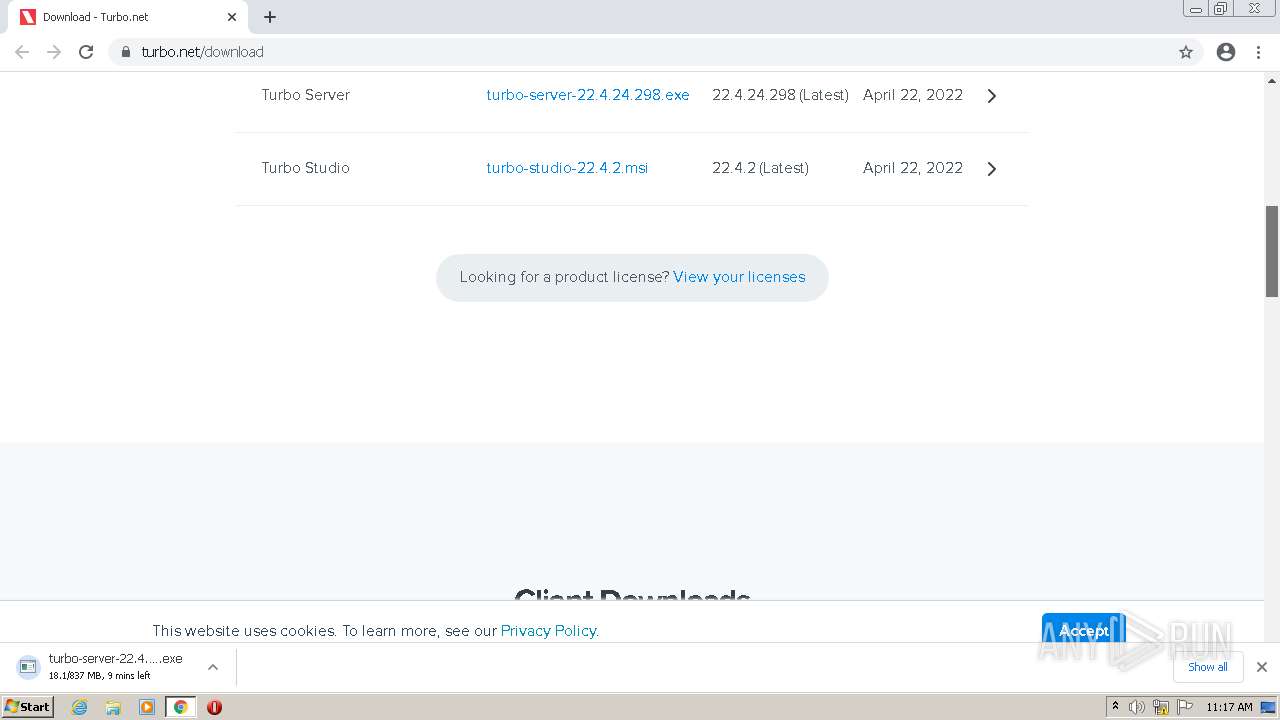
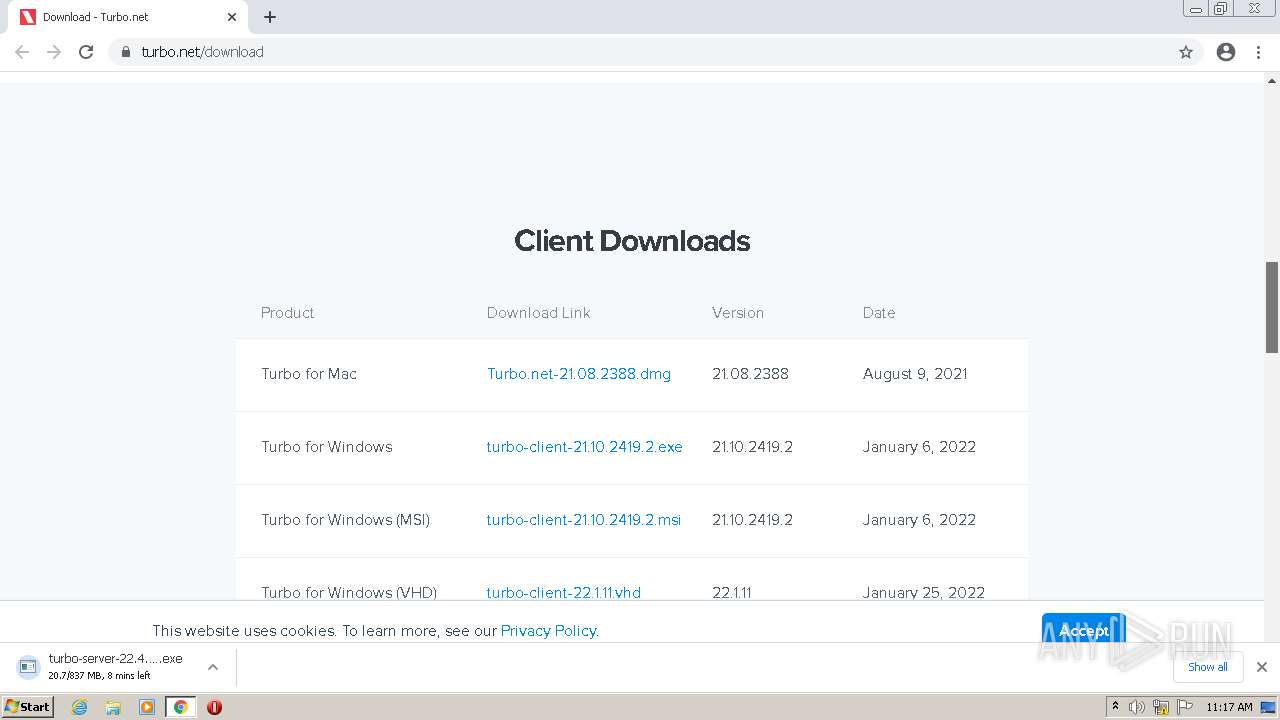
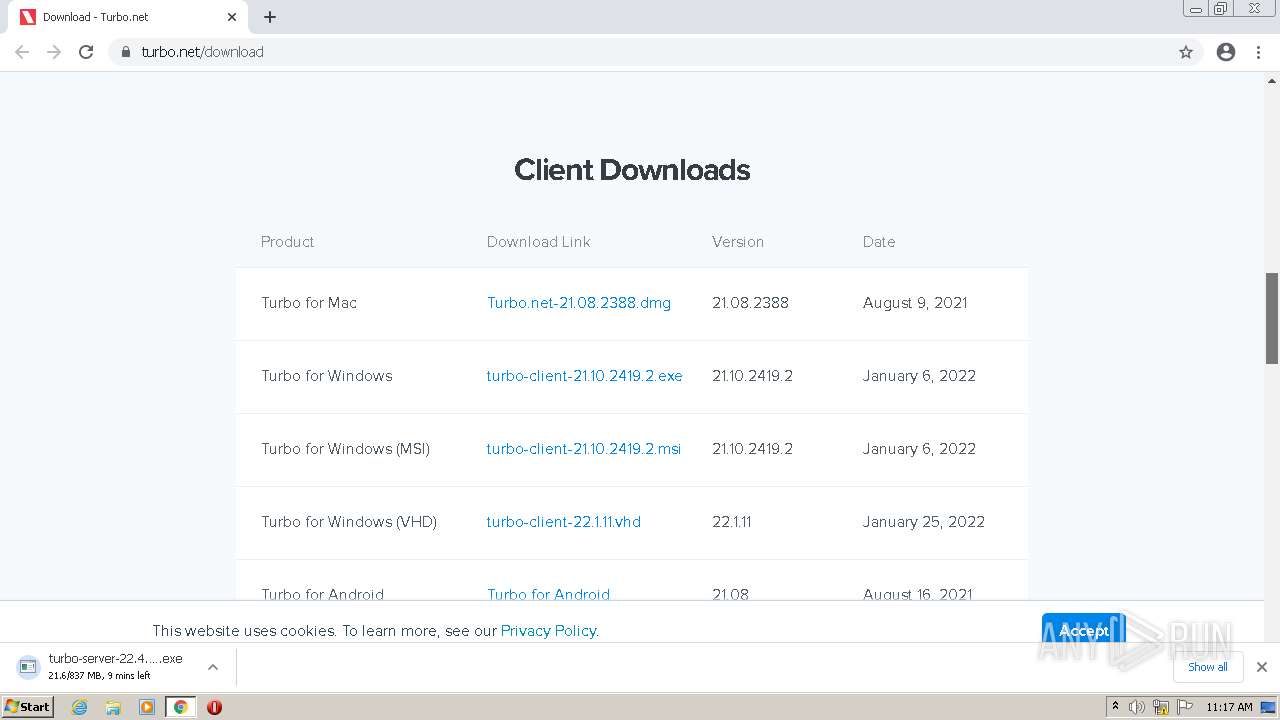
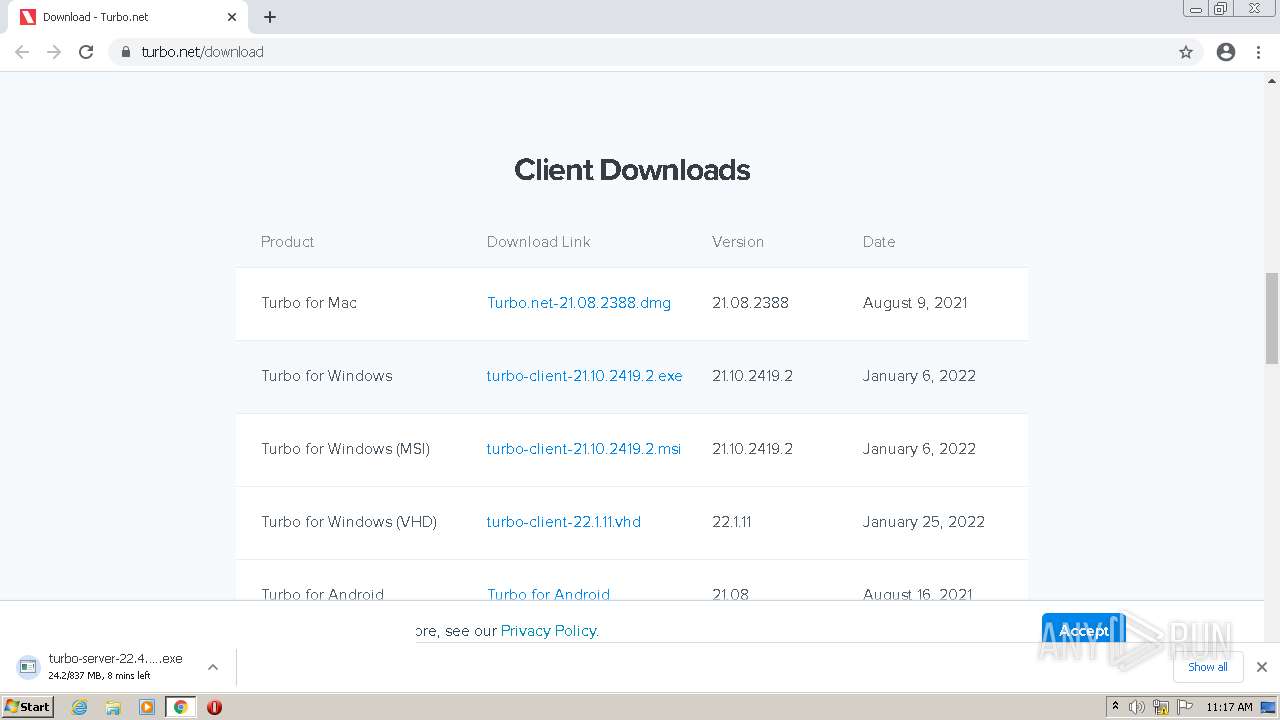
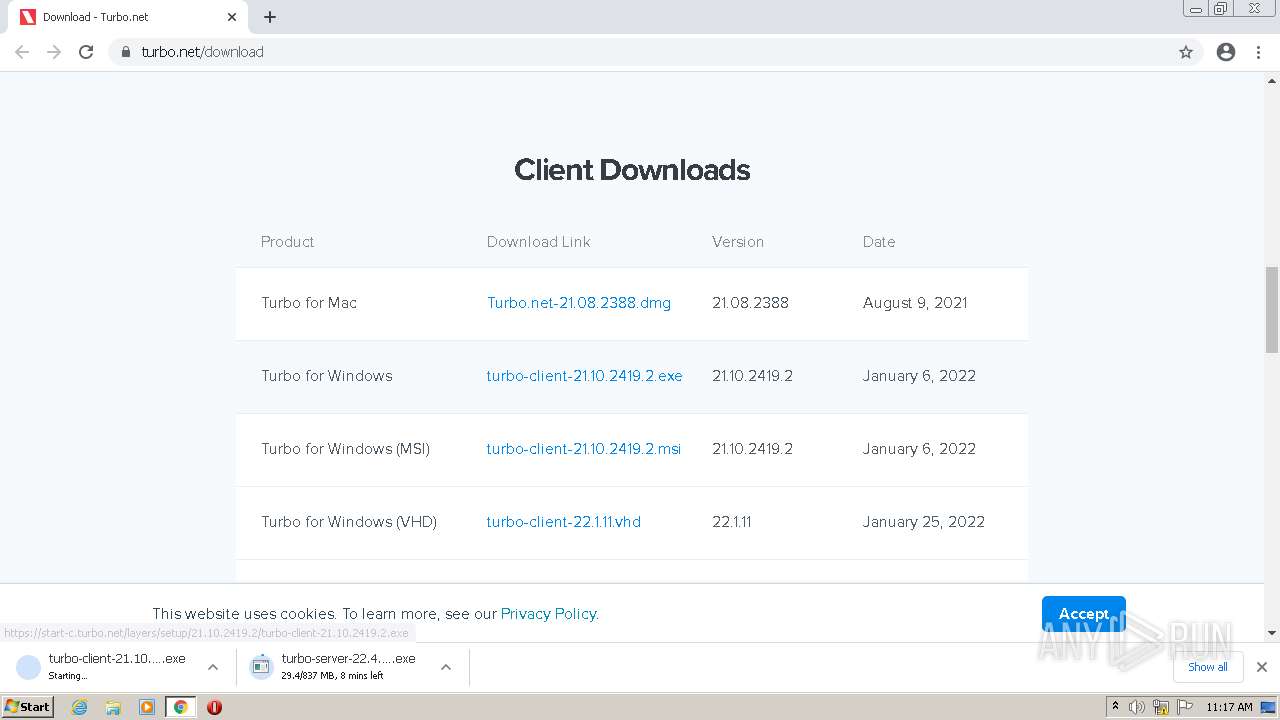
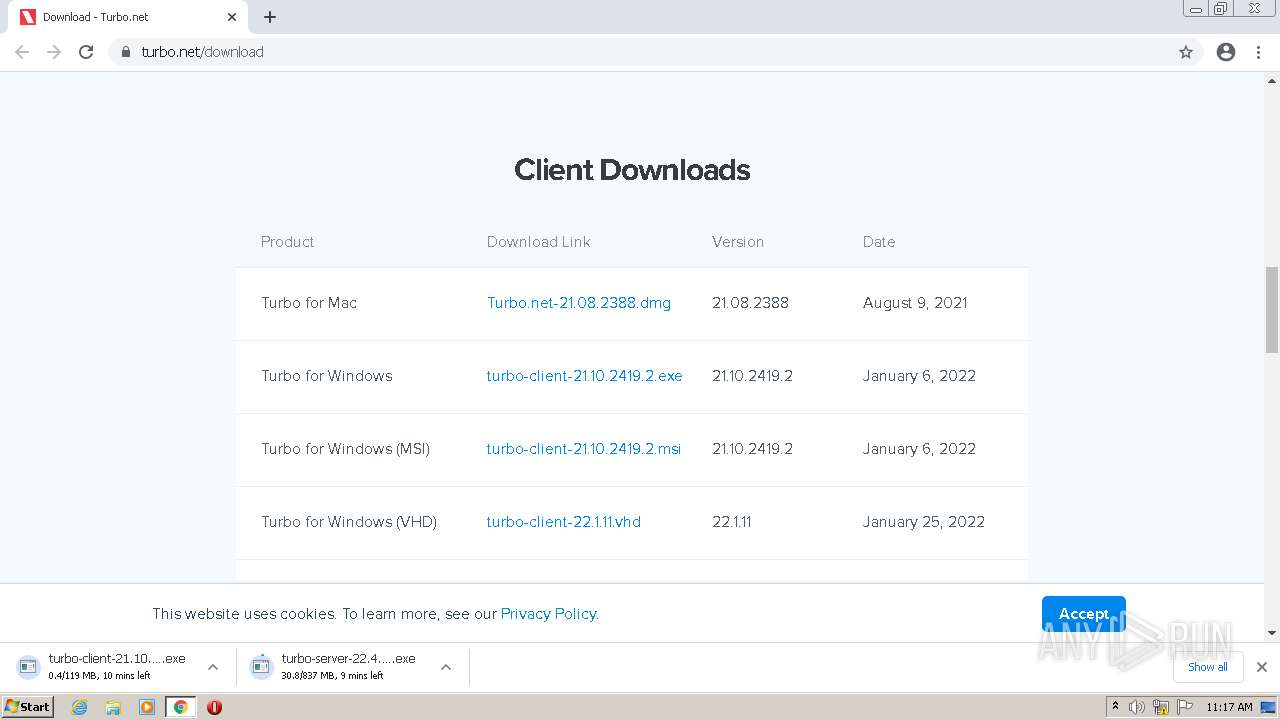
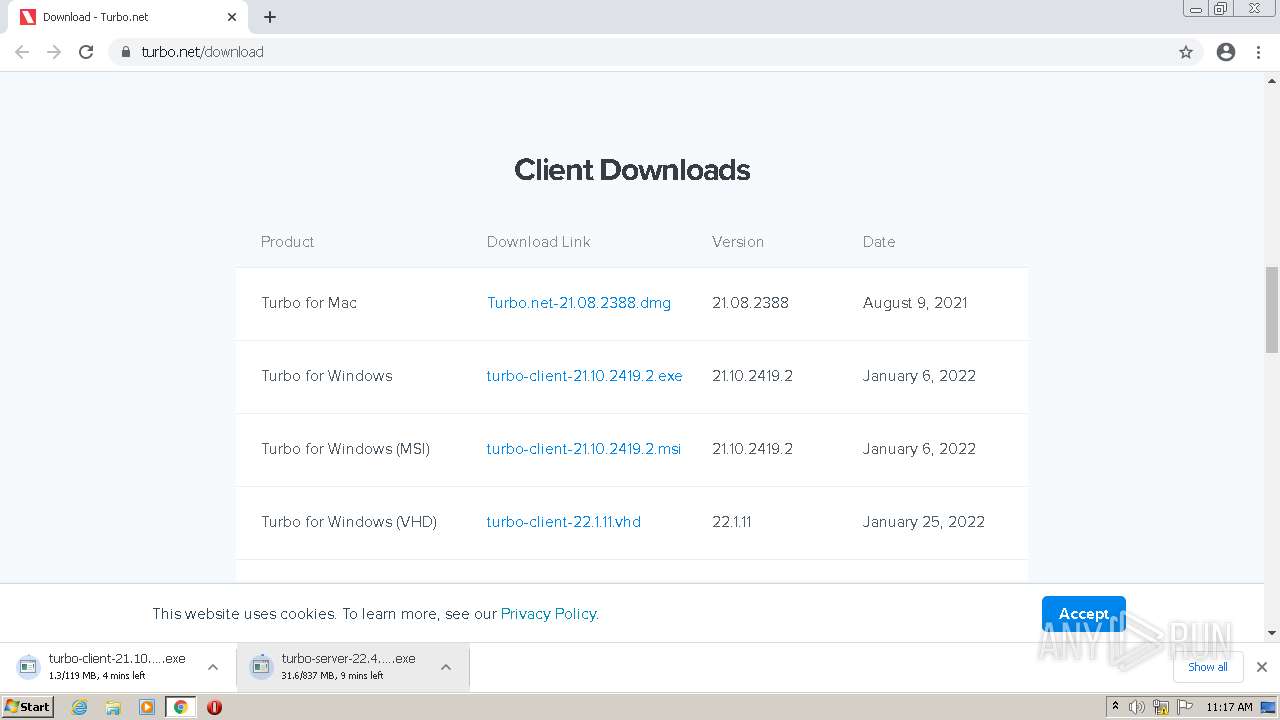
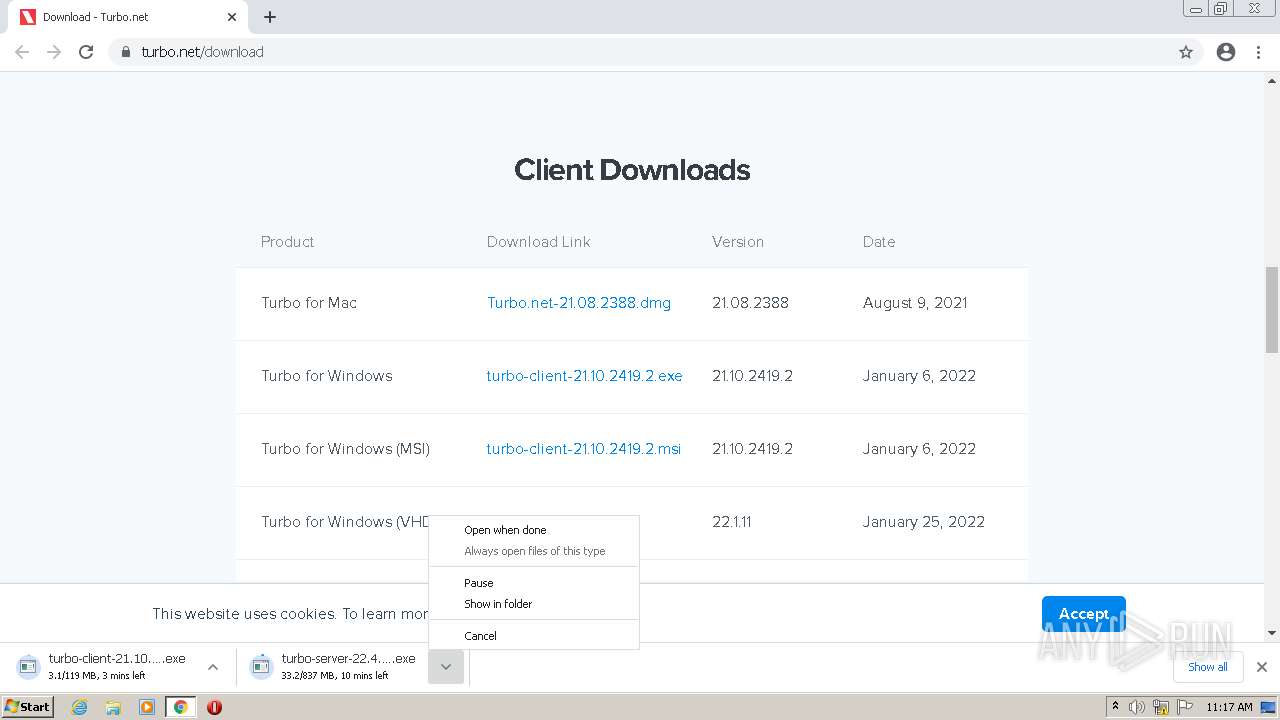
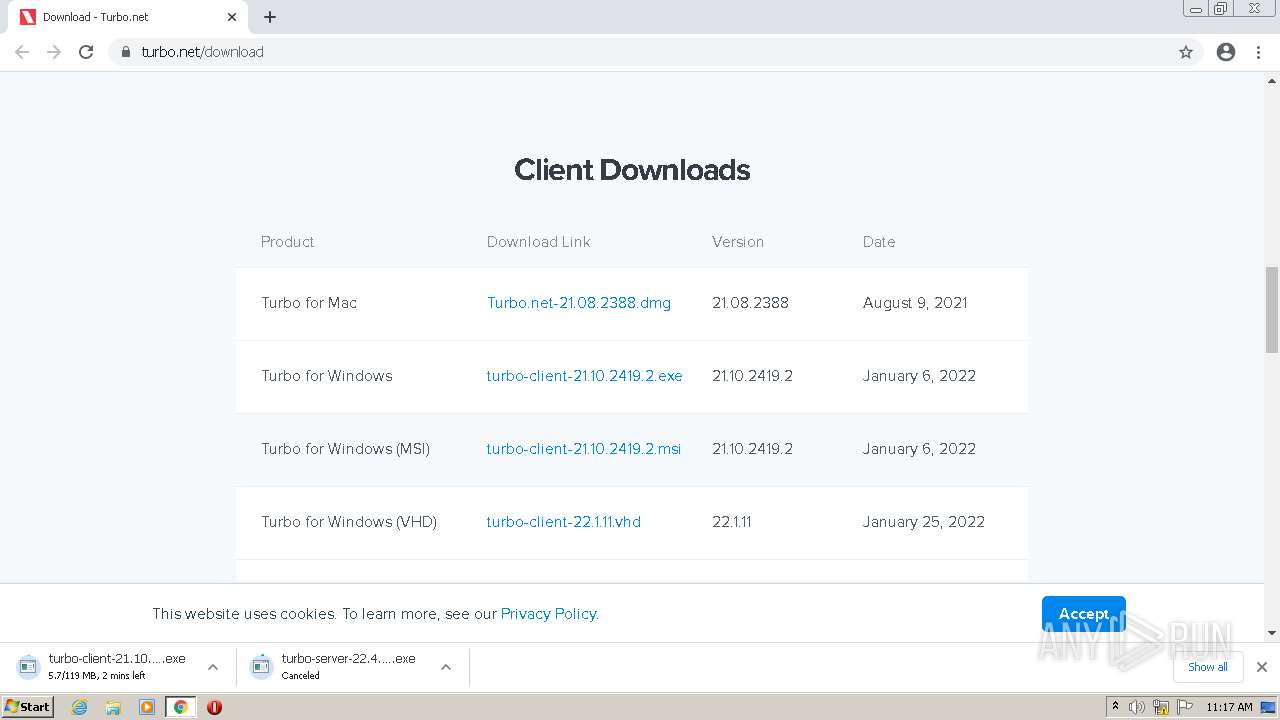
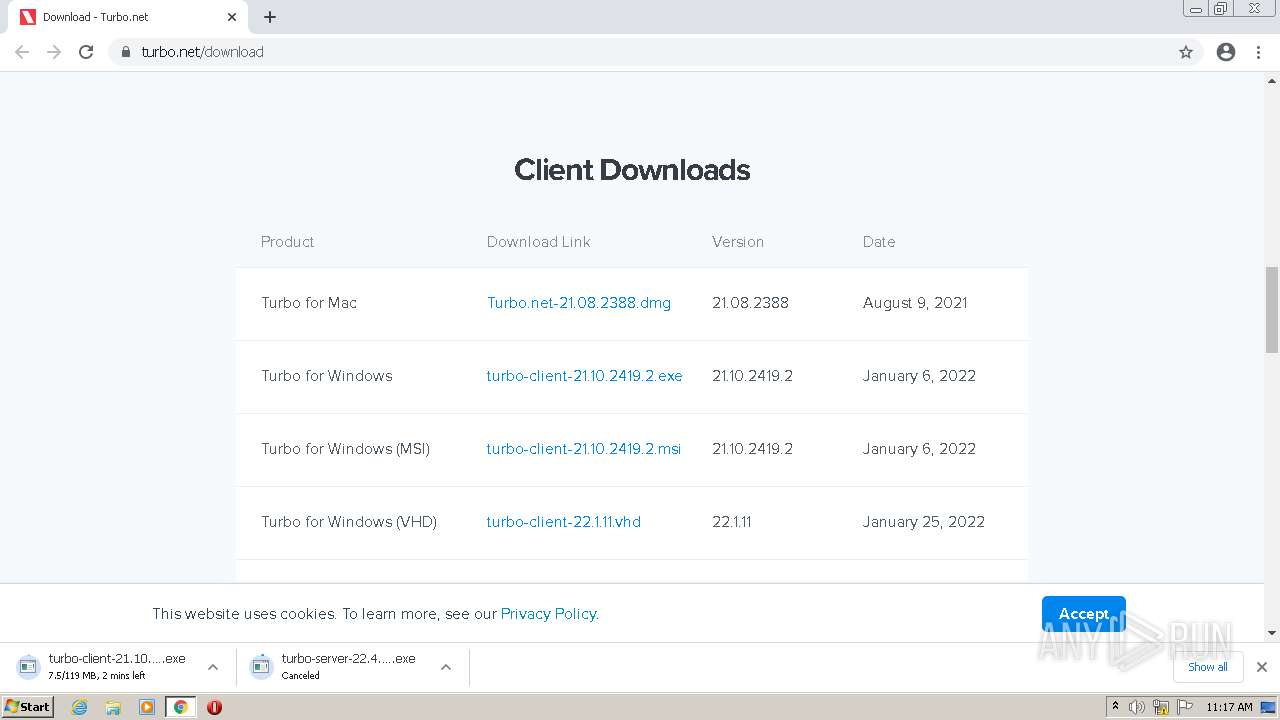
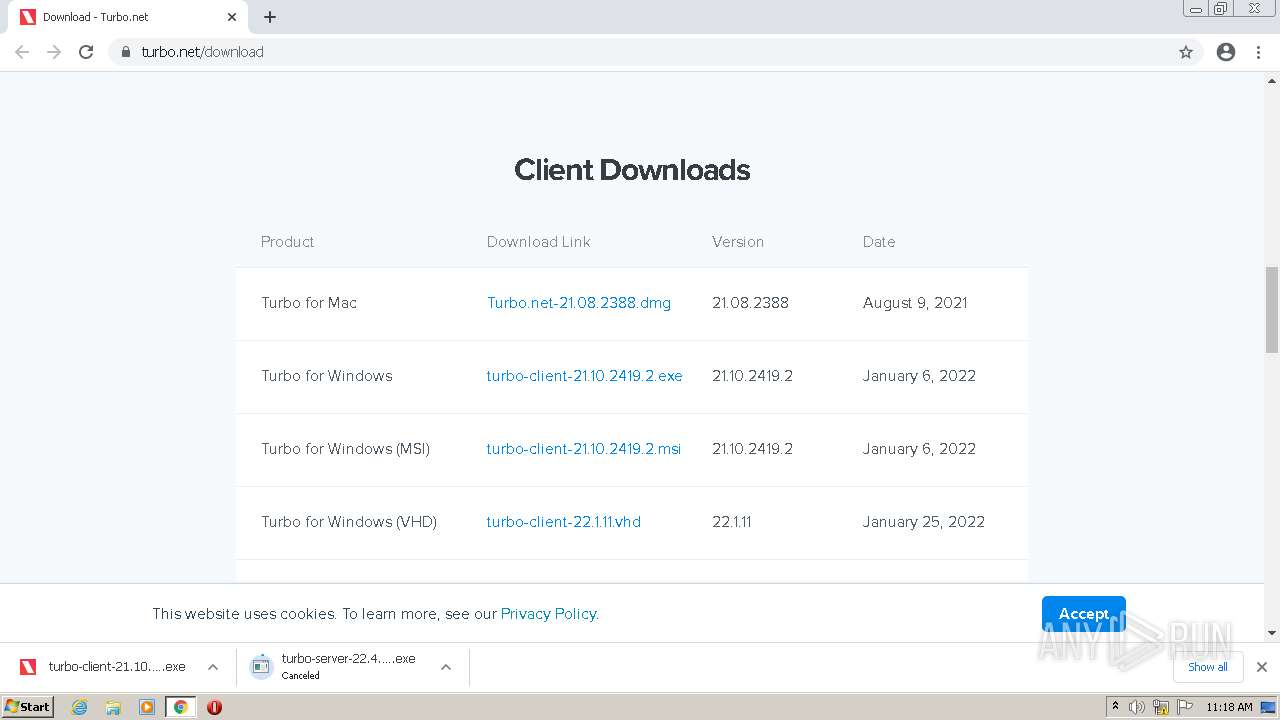
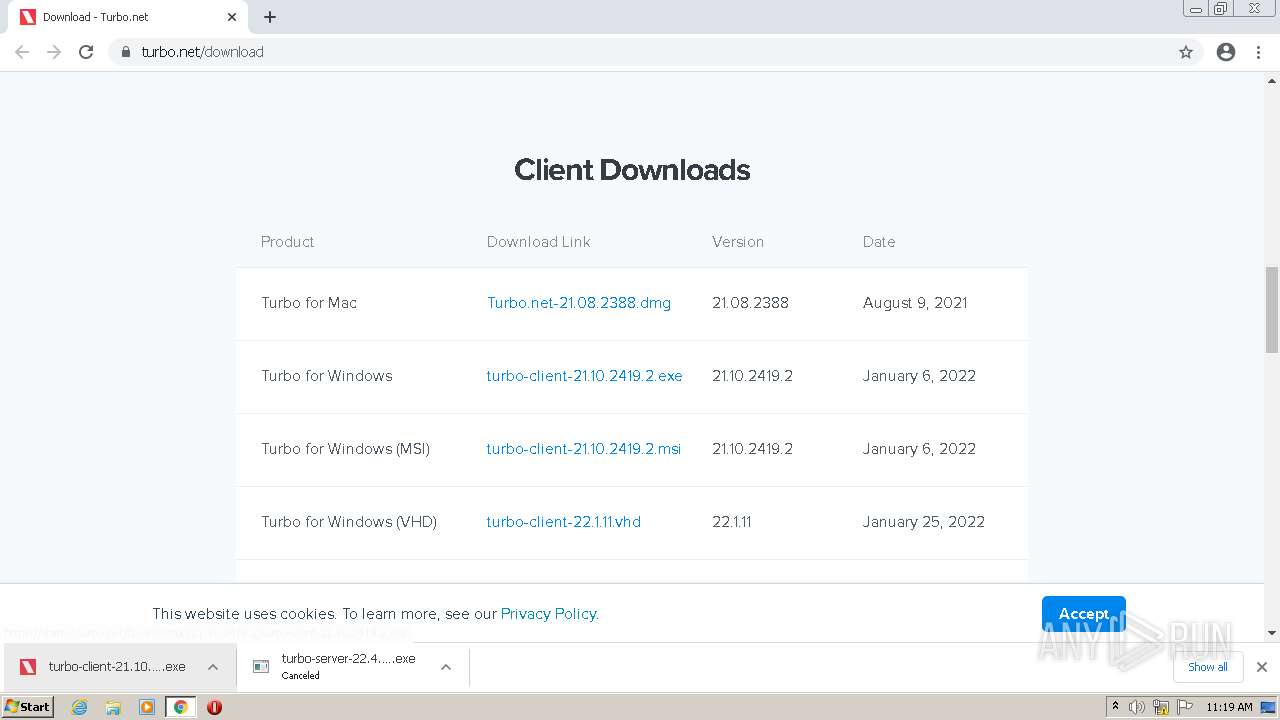
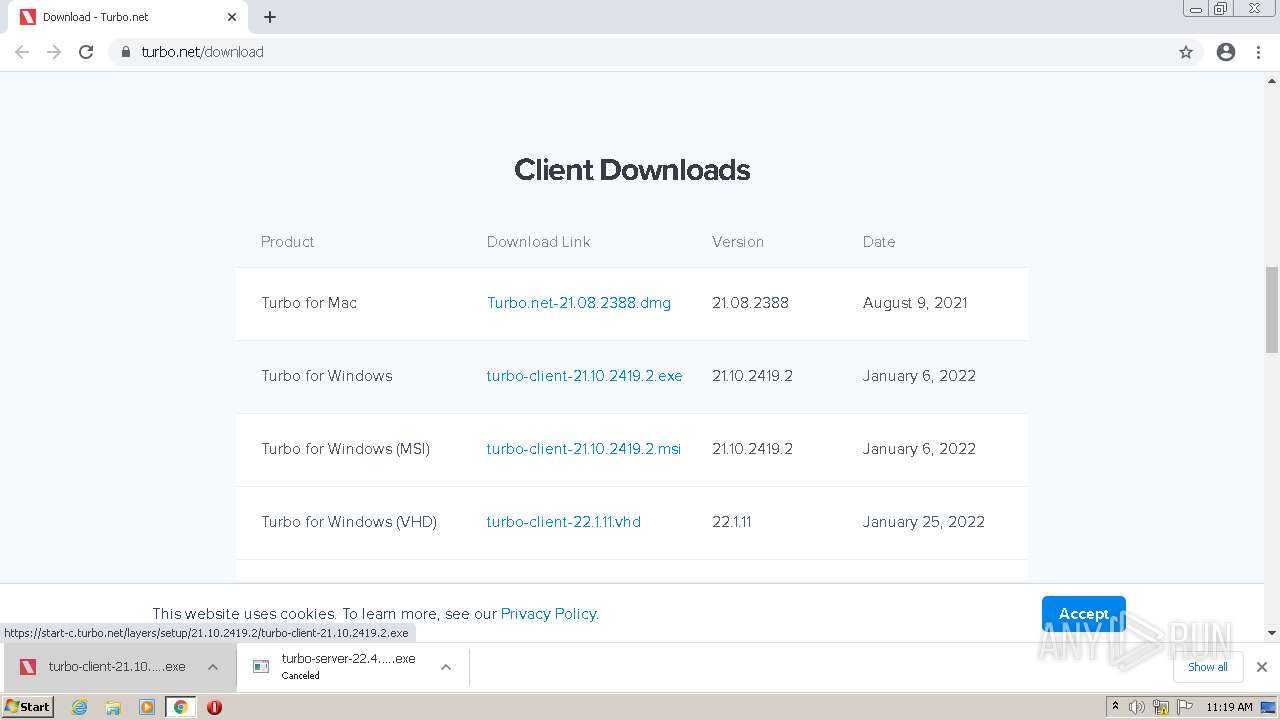
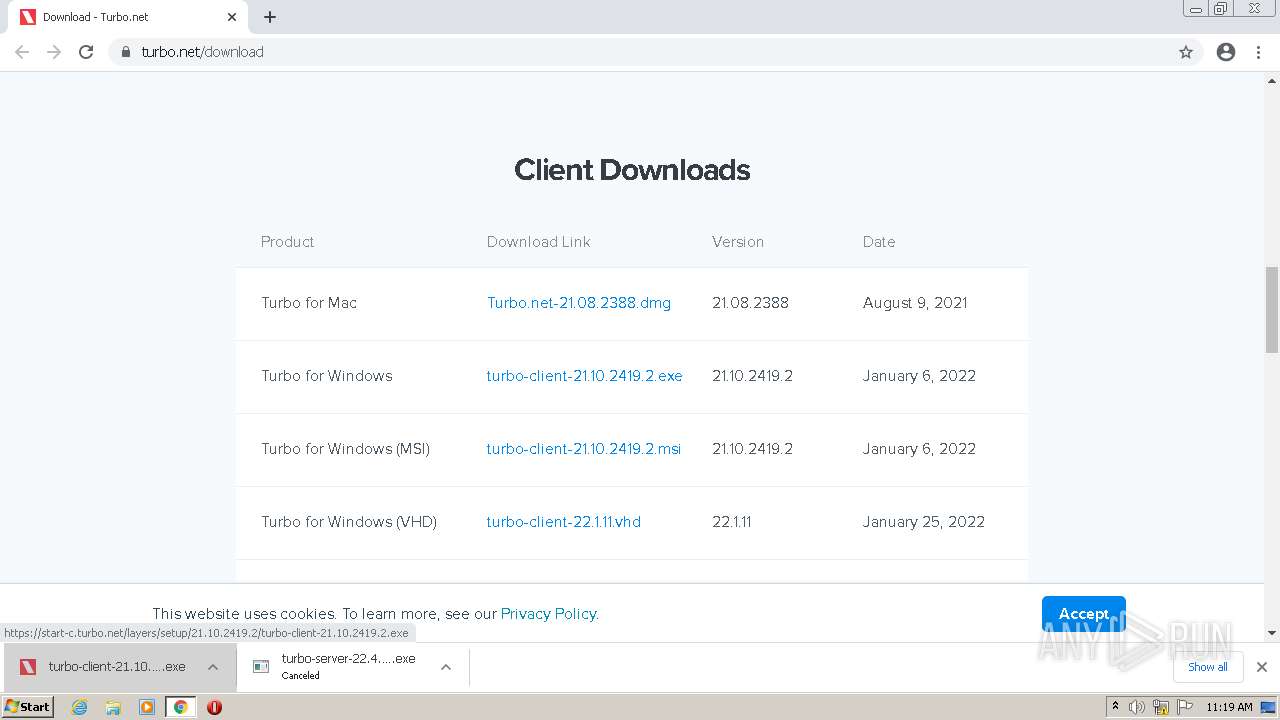
| URL: | https://turbo.net/download |
| Full analysis: | https://app.any.run/tasks/05af2966-a61c-4080-9ae2-7f8de6d9fe34 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2022, 10:16:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 63F14005490B67E8B9FDB12C31E2D1A4 |
| SHA1: | 7E6E711993C08EBA1EDEFCC958799AF70932AA30 |
| SHA256: | 4415B419D983D9BBDC8B225FF0BA8A4A75D5A84A76DF6EFCD871241AADF08898 |
| SSDEEP: | 3:N8Yk8M:2Y3M |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 1036)
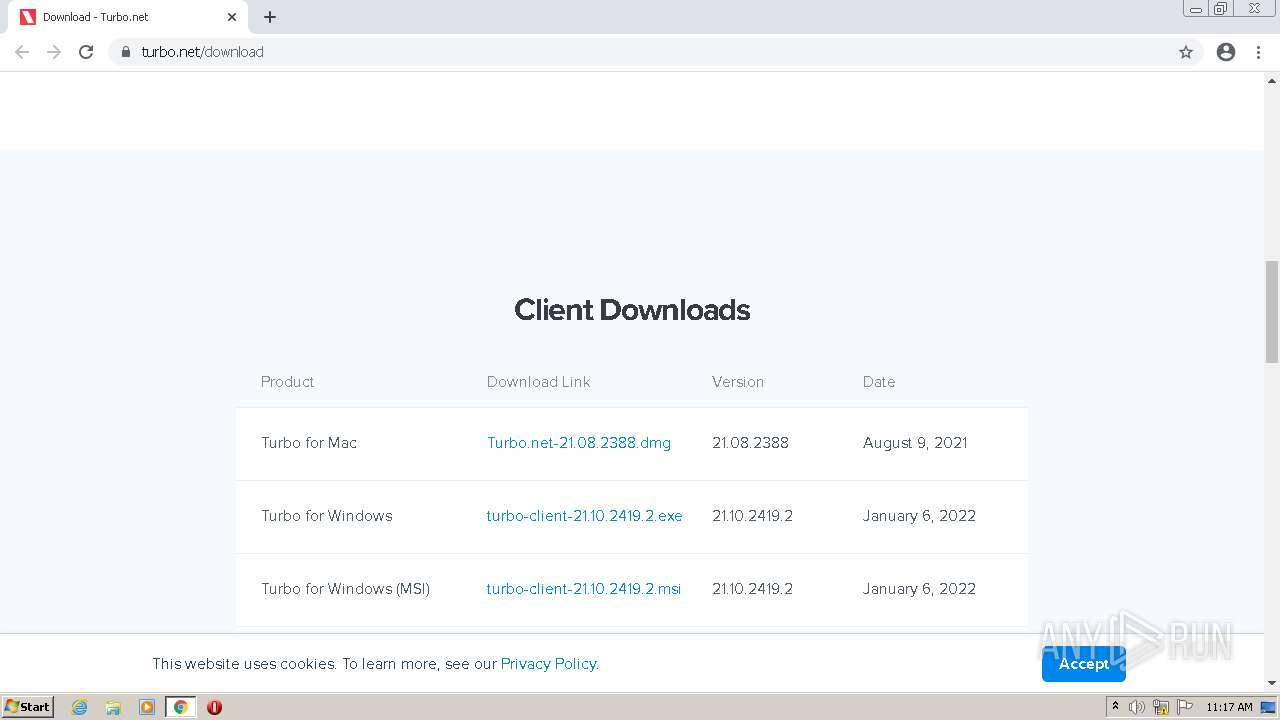
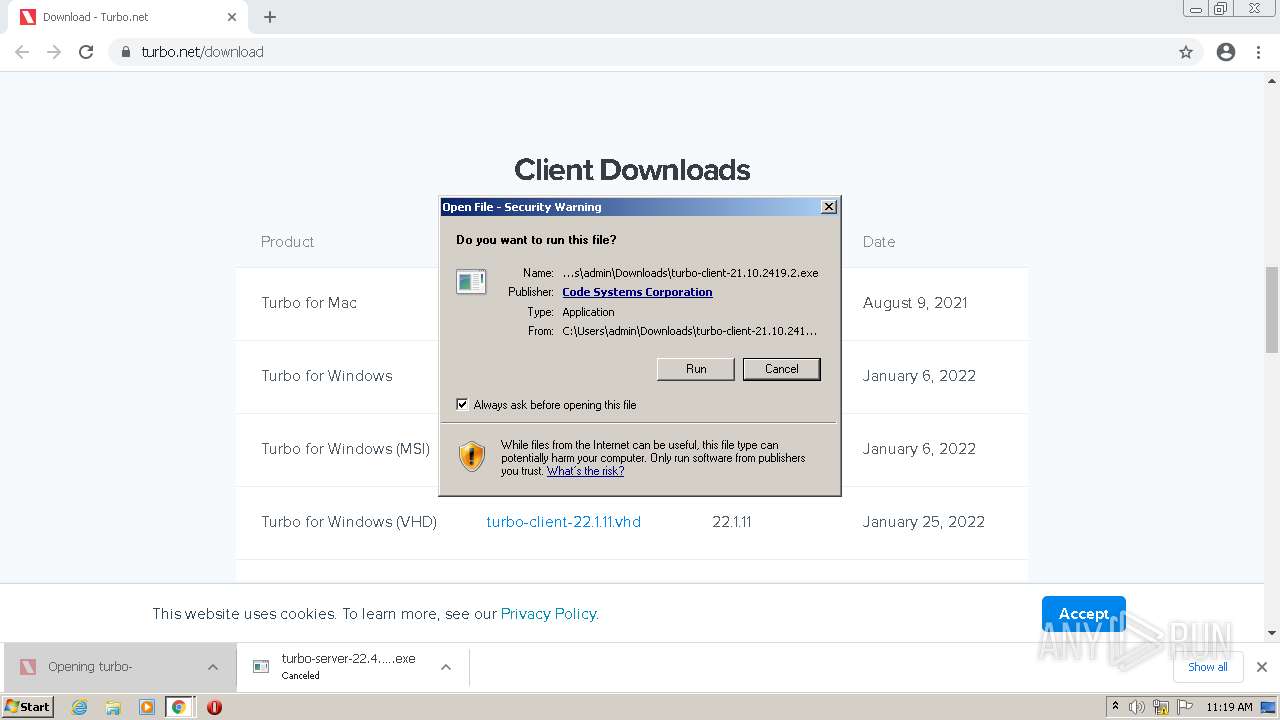
- turbo-client-21.10.2419.2.exe (PID: 1588)
Writes to a start menu file
- turbo-client-21.10.2419.2.exe (PID: 1588)
Application was dropped or rewritten from another process
- Turbo-Sandbox.exe (PID: 1968)
Registers / Runs the DLL via REGSVR32.EXE
- turbo-client-21.10.2419.2.exe (PID: 1588)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 584)
- Turbo-Sandbox.exe (PID: 1968)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1036)
Executable content was dropped or overwritten
- chrome.exe (PID: 1036)
- turbo-client-21.10.2419.2.exe (PID: 1588)
Drops a file with a compile date too recent
- chrome.exe (PID: 1036)
- turbo-client-21.10.2419.2.exe (PID: 1588)
Checks supported languages
- turbo-client-21.10.2419.2.exe (PID: 1588)
- Turbo-Sandbox.exe (PID: 1968)
Changes default file association
- turbo-client-21.10.2419.2.exe (PID: 1588)
Writes to a desktop.ini file (may be used to cloak folders)
- turbo-client-21.10.2419.2.exe (PID: 1588)
Reads the computer name
- turbo-client-21.10.2419.2.exe (PID: 1588)
- Turbo-Sandbox.exe (PID: 1968)
Creates files in the user directory
- turbo-client-21.10.2419.2.exe (PID: 1588)
Reads Environment values
- Turbo-Sandbox.exe (PID: 1968)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 584)
Creates a software uninstall entry
- Turbo-Sandbox.exe (PID: 1968)
INFO
Reads the computer name
- chrome.exe (PID: 1036)
- chrome.exe (PID: 856)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 2748)
- WISPTIS.EXE (PID: 2840)
Checks supported languages
- chrome.exe (PID: 3772)
- chrome.exe (PID: 1036)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 1044)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 856)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2784)
- chrome.exe (PID: 1592)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 2116)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 2364)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 1332)
- regsvr32.exe (PID: 584)
- WISPTIS.EXE (PID: 2840)
Application launched itself
- chrome.exe (PID: 1036)
Reads the hosts file
- chrome.exe (PID: 1036)
- chrome.exe (PID: 856)
Reads settings of System Certificates
- chrome.exe (PID: 856)
- chrome.exe (PID: 1036)
- Turbo-Sandbox.exe (PID: 1968)
Reads the date of Windows installation
- chrome.exe (PID: 2744)
Checks Windows Trust Settings
- chrome.exe (PID: 1036)
- Turbo-Sandbox.exe (PID: 1968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
30
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | regsvr32.exe /s /n /i:user "C:\Users\admin\AppData\Local\Turbo\21.10.2419.2\Turbo-Plugin.dll" | C:\Windows\system32\regsvr32.exe | — | turbo-client-21.10.2419.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,6646554092276951349,17140558677072463358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1244 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://turbo.net/download" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6646554092276951349,17140558677072463358,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2368 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,6646554092276951349,17140558677072463358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,6646554092276951349,17140558677072463358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3040 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
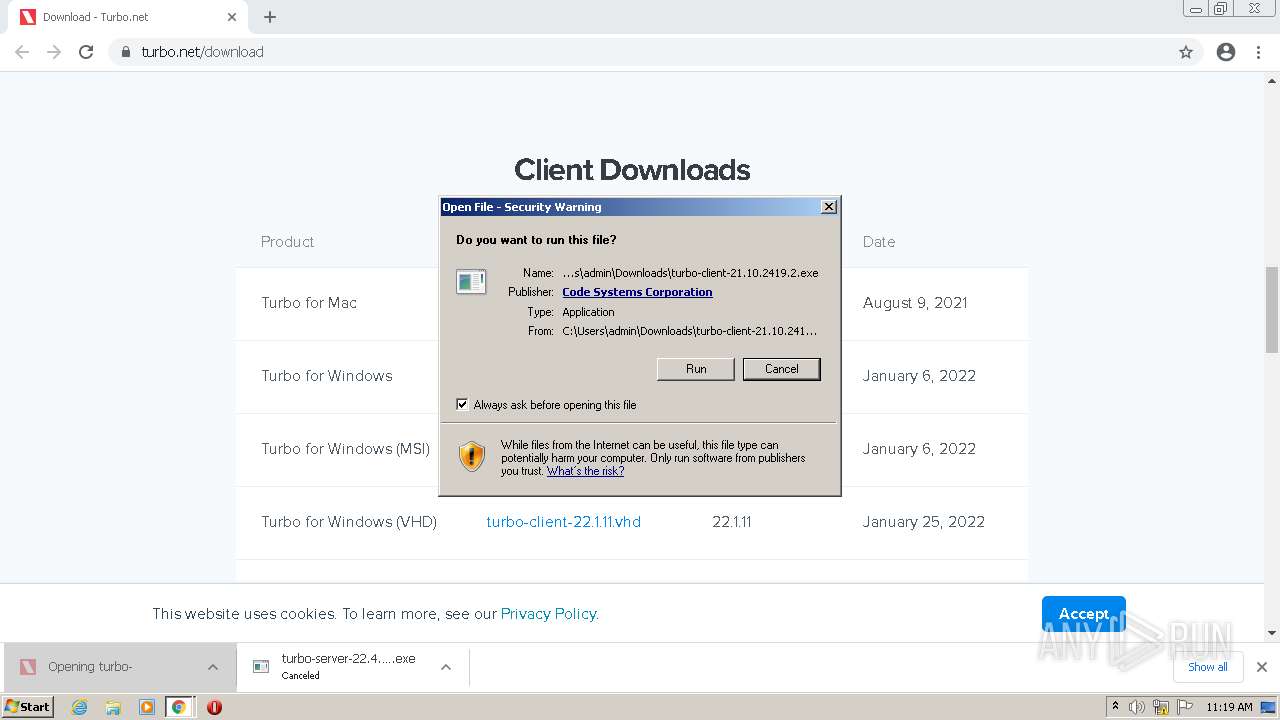
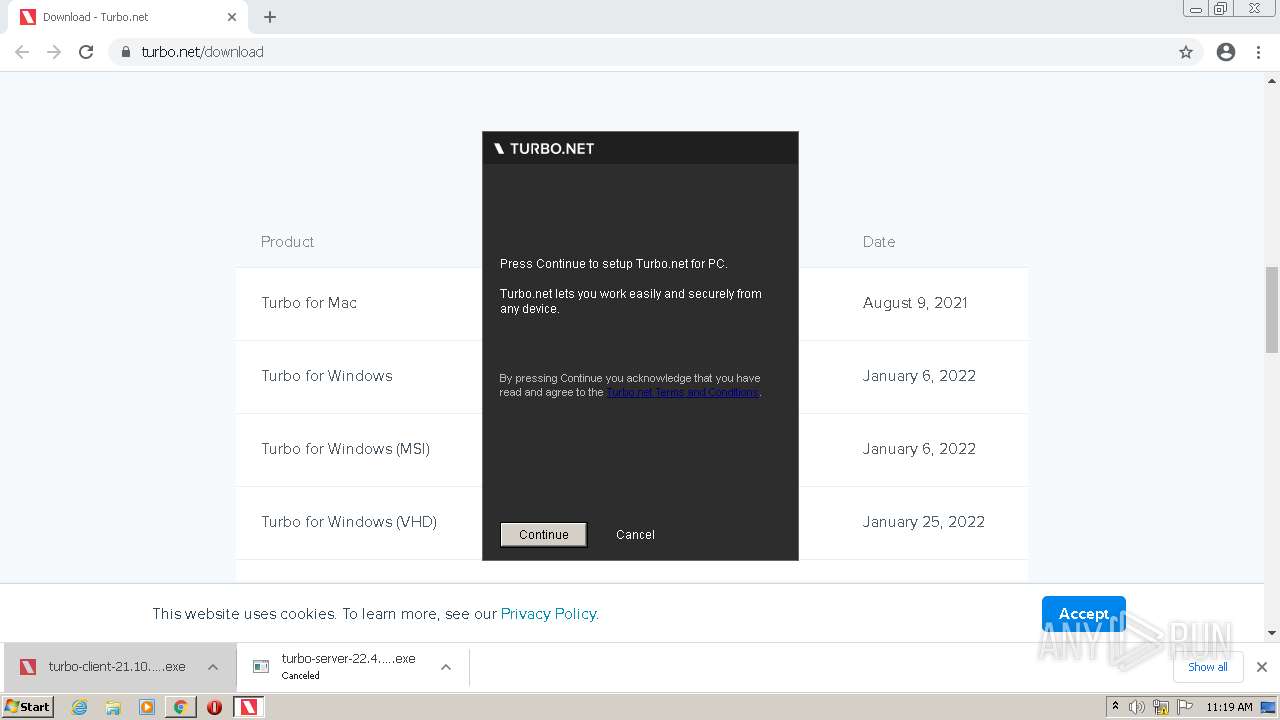
| 1588 | "C:\Users\admin\Downloads\turbo-client-21.10.2419.2.exe" | C:\Users\admin\Downloads\turbo-client-21.10.2419.2.exe | chrome.exe | ||||||||||||
User: admin Company: Code Systems Corporation Integrity Level: MEDIUM Description: Turbo.net for PC 21.10 Exit code: 0 Version: 21.10.2419.2 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,6646554092276951349,17140558677072463358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,6646554092276951349,17140558677072463358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
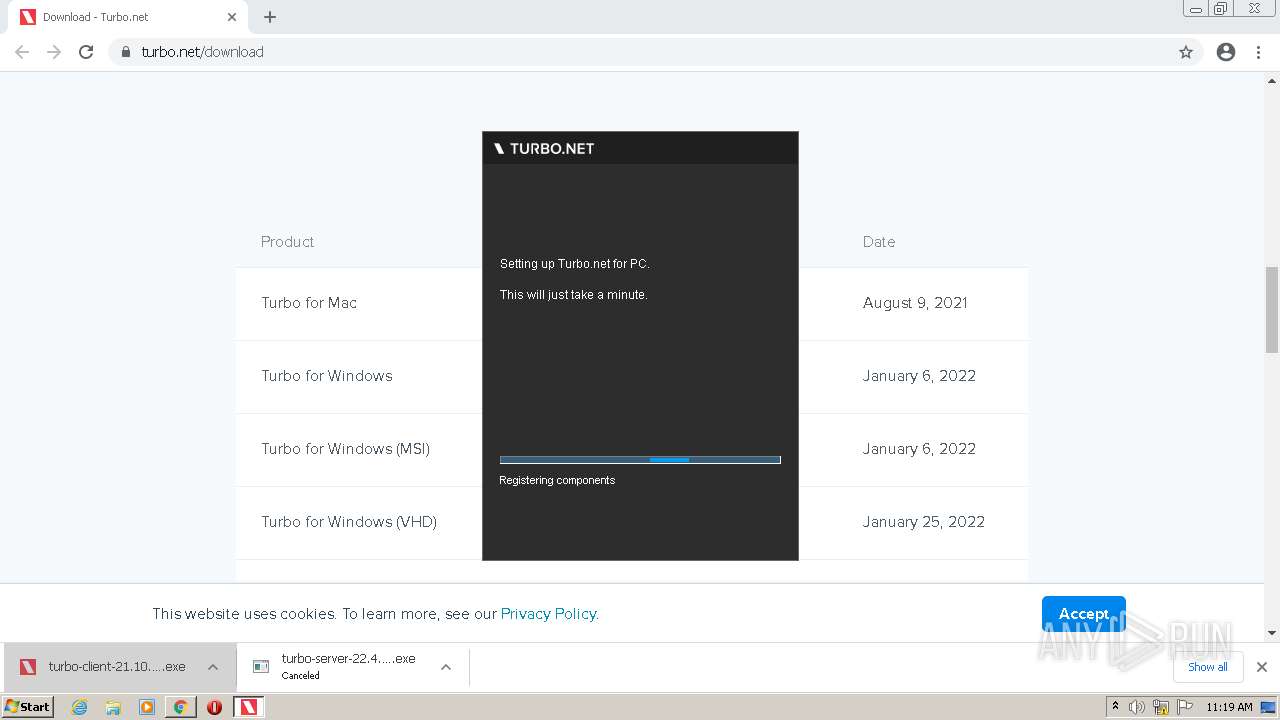
| 1968 | "C:\Users\admin\AppData\Local\Turbo\21.10.2419.2\Turbo-Sandbox.exe" --first-run | C:\Users\admin\AppData\Local\Turbo\21.10.2419.2\Turbo-Sandbox.exe | turbo-client-21.10.2419.2.exe | ||||||||||||
User: admin Company: Code Systems Corporation Integrity Level: MEDIUM Description: Turbo.net Sandbox Manager Exit code: 0 Version: 21.10.2419.2 Modules
| |||||||||||||||
Total events
25 083
Read events
24 777
Write events
301
Delete events
5
Modification events
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
87
Suspicious files
63
Text files
193
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62667505-40C.pma | — | |
MD5:— | SHA256:— | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf9561.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3c331f72-22bb-4854-971a-73f9eed7473d.tmp | text | |
MD5:A48E0A98198B1EC9EAFE6840A5816540 | SHA256:BB90481E15E01C8E65DFEED93383521B43E64A890DB6B62870355930FF90DBF3 | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFf967a.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:A48E0A98198B1EC9EAFE6840A5816540 | SHA256:BB90481E15E01C8E65DFEED93383521B43E64A890DB6B62870355930FF90DBF3 | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 3772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFf9561.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
96
DNS requests
61
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
— | — | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 574 b | whitelisted |
— | — | GET | 206 | 74.125.110.138:80 | http://r5---sn-5goeen7y.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=157.97.120.10&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1650881540&mv=m&mvi=5&pl=24&rmhost=r1---sn-5goeen7y.gvt1.com&shardbypass=sd | US | binary | 9.49 Kb | whitelisted |
— | — | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 574 b | whitelisted |
— | — | GET | 206 | 74.125.110.138:80 | http://r5---sn-5goeen7y.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=157.97.120.10&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1650881540&mv=m&mvi=5&pl=24&rmhost=r1---sn-5goeen7y.gvt1.com&shardbypass=sd | US | binary | 9.49 Kb | whitelisted |
— | — | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 574 b | whitelisted |
— | — | GET | 206 | 74.125.110.138:80 | http://r5---sn-5goeen7y.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=157.97.120.10&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1650881540&mv=m&mvi=5&pl=24&rmhost=r1---sn-5goeen7y.gvt1.com&shardbypass=sd | US | binary | 20.7 Kb | whitelisted |
— | — | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 574 b | whitelisted |
— | — | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 574 b | whitelisted |
— | — | GET | 206 | 74.125.110.138:80 | http://r5---sn-5goeen7y.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=157.97.120.10&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1650881540&mv=m&mvi=5&pl=24&rmhost=r1---sn-5goeen7y.gvt1.com&shardbypass=sd | US | binary | 88.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
856 | chrome.exe | 142.250.186.45:443 | accounts.google.com | Google Inc. | US | suspicious |
856 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 3.248.8.137:443 | turbo.net | — | US | malicious |
856 | chrome.exe | 142.250.186.132:443 | www.google.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 64.38.175.52:443 | app.turbo.net | Isomedia, Inc. | US | unknown |
856 | chrome.exe | 104.16.124.175:443 | unpkg.com | Cloudflare Inc | US | shared |
856 | chrome.exe | 151.101.2.217:443 | client-registry.mutinycdn.com | Fastly | US | suspicious |
856 | chrome.exe | 142.250.181.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 13.224.98.99:443 | d3e54v103j8qbb.cloudfront.net | — | US | unknown |
856 | chrome.exe | 172.66.42.216:443 | assets.calendly.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
turbo.net |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
assets-global.website-files.com |
| shared |
ajax.googleapis.com |
| whitelisted |
app.turbo.net |
| unknown |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
turbo-client-21.10.2419.2.exe | Unable to find install dir pattern: C:\Program Files\Turbo\* |
turbo-client-21.10.2419.2.exe | Unable to find install dir pattern: C:\Program Files\Spoon\* |
turbo-client-21.10.2419.2.exe | Unable to find install dir pattern: C:\Users\admin\AppData\Local\Turbo\* |
turbo-client-21.10.2419.2.exe | Unable to find install dir pattern: C:\Users\admin\AppData\Local\Spoon\* |
turbo-client-21.10.2419.2.exe | Unable to find install dir pattern: C:\Program Files\Turbo\* |
turbo-client-21.10.2419.2.exe | Unable to find install dir pattern: C:\Program Files\Spoon\* |
turbo-client-21.10.2419.2.exe | 04/25/22 11:19:18 - Copying web plugin: C:\Users\admin\AppData\Local\Turbo\21.10.2419.2\Turbo-Plugin.dll
|
turbo-client-21.10.2419.2.exe | 04/25/22 11:19:18 - Copying web plugin: C:\Users\admin\AppData\Local\Turbo\21.10.2419.2\Turbo-Plugin-x64.dll
|
turbo-client-21.10.2419.2.exe | 04/25/22 11:19:18 - Copying IE extension x86: C:\Users\admin\AppData\Local\Turbo\21.10.2419.2\Turbo-IEBrowserHelper.dll
|
turbo-client-21.10.2419.2.exe | 04/25/22 11:19:18 - Copying IE extension x64: C:\Users\admin\AppData\Local\Turbo\21.10.2419.2\Turbo-IEBrowserHelper-x64.dll
|