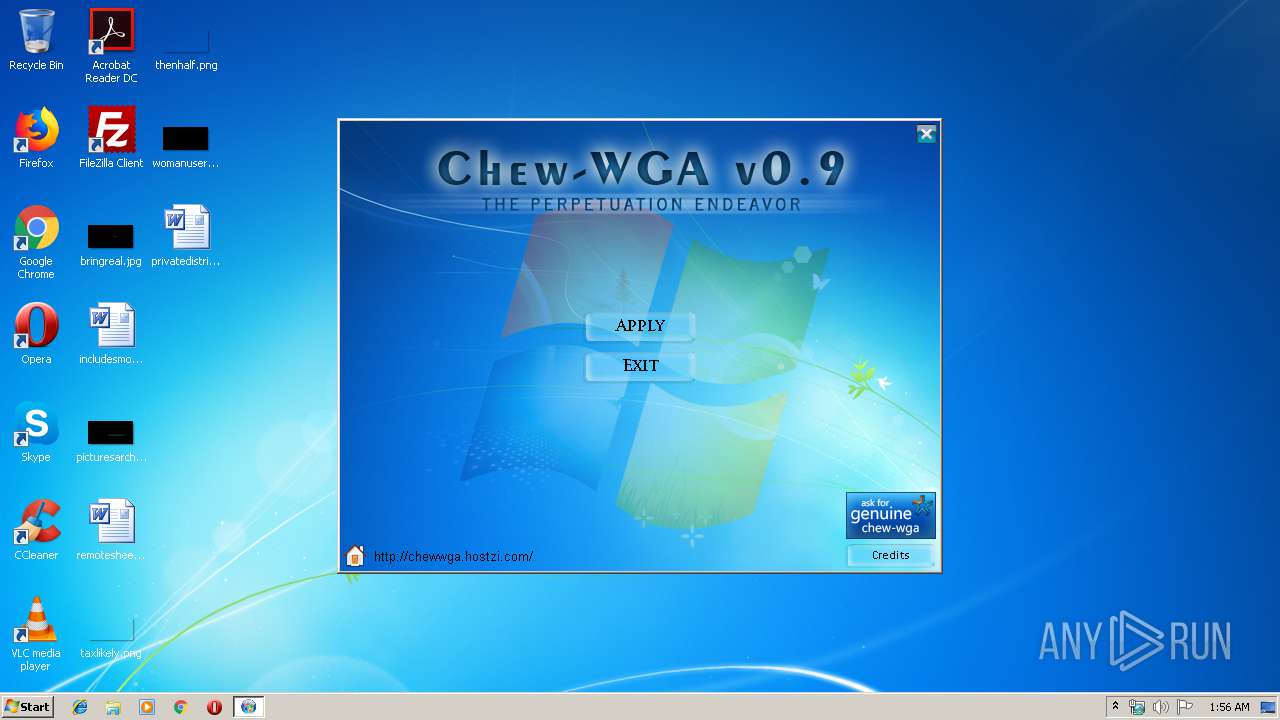
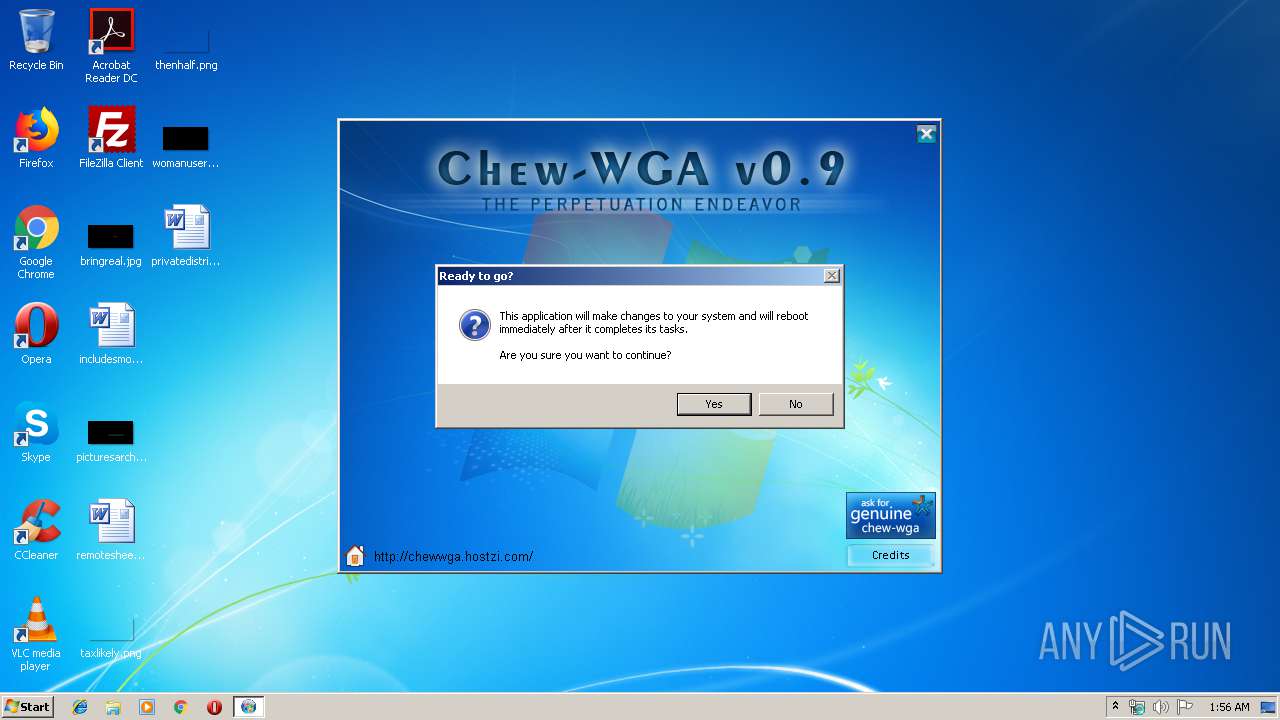
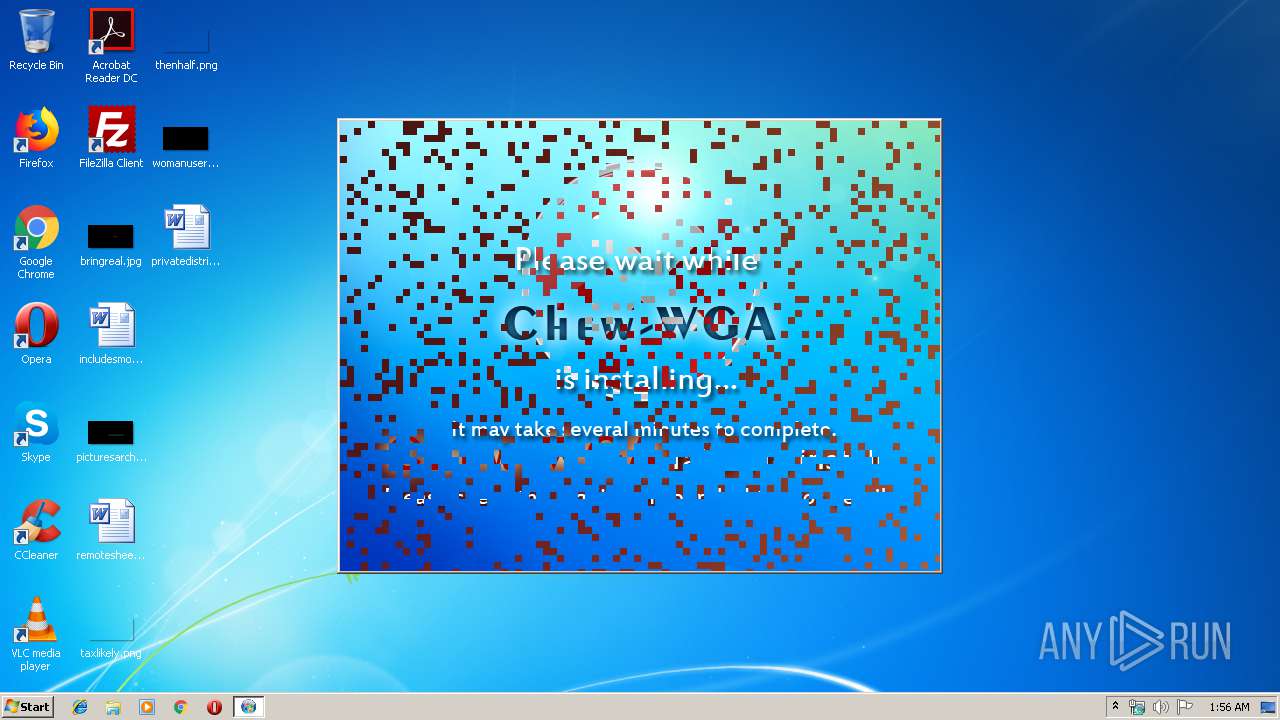
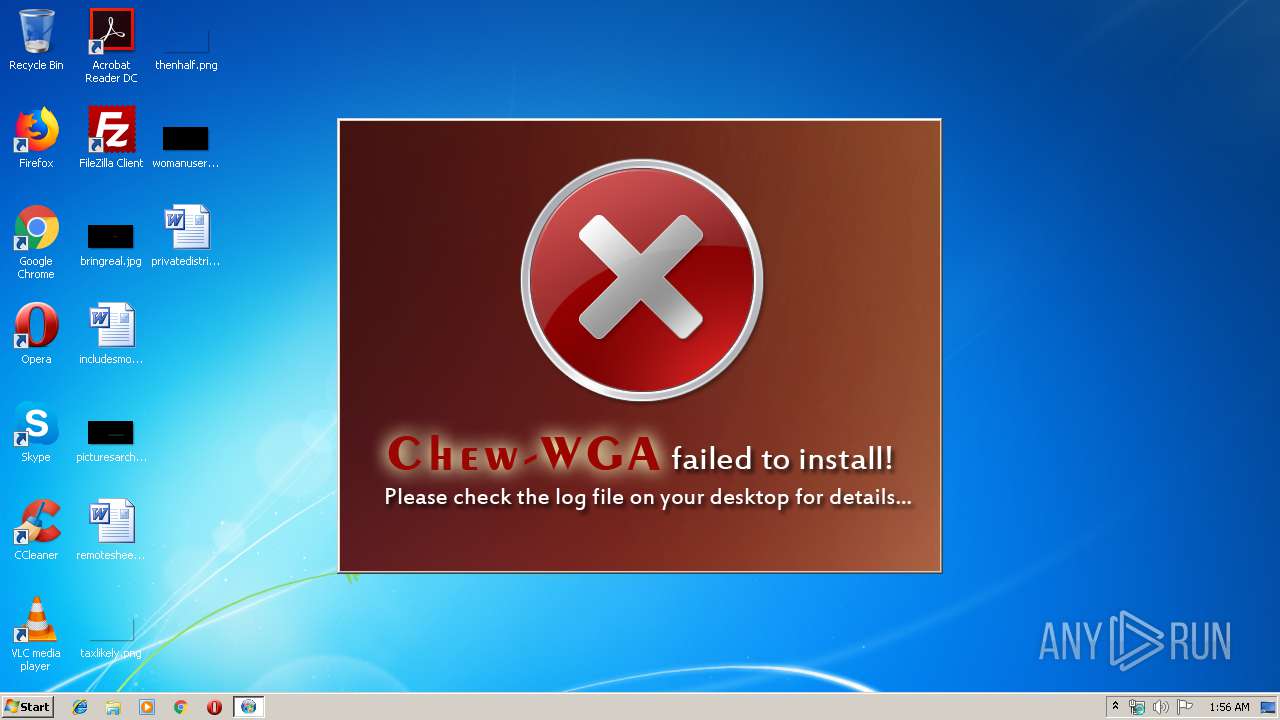
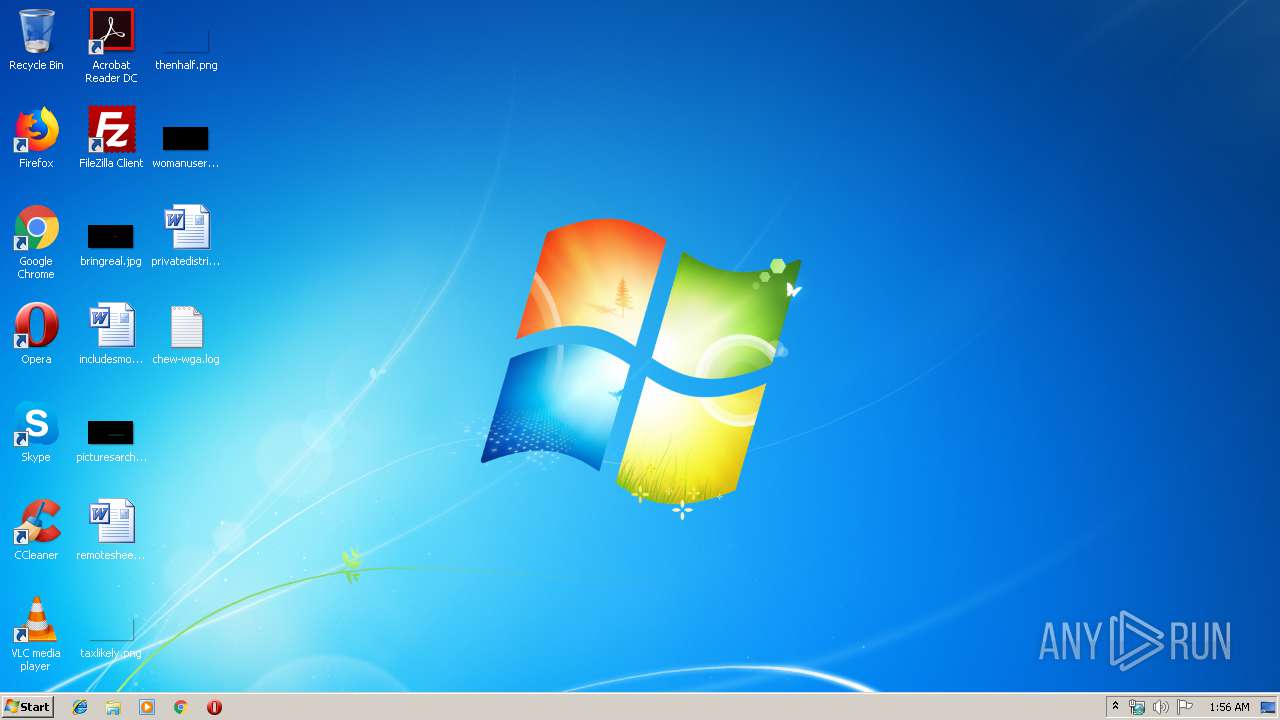
| File name: | Chew-WGA-v0.9.eXe |
| Full analysis: | https://app.any.run/tasks/9bfbd924-9a3a-4e2b-9661-4eab467d6a92 |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2020, 01:55:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 48EFA828B21F0FB0E63AE04735B505B3 |
| SHA1: | 5D5D91F2CEC4905A760A4E413E7FCA8180AA0F9E |
| SHA256: | 440AD7FC72E2835C3B043708BE099419089ACC9449DC01AC1DFA85D96CD12AC6 |
| SSDEEP: | 196608:9O1vl2I4a7SdzRDymXLa4mnb0DtUog3jCUE2nKNfMILF9UBDHLSwxT1aQhS:Wt2O7Sd1ymX+4mnOU9+UCZM6kzWu12 |
MALICIOUS
Application was dropped or rewritten from another process
- autorun.exe (PID: 2864)
- touch.exe (PID: 1792)
- banish.exe (PID: 3692)
- touch.exe (PID: 820)
- touch.exe (PID: 4068)
- hosts.exe (PID: 2832)
- touch.exe (PID: 1528)
- touch.exe (PID: 1748)
- banish.exe (PID: 1412)
- touch.exe (PID: 2632)
- touch.exe (PID: 1252)
- touch.exe (PID: 1772)
- touch.exe (PID: 3948)
- banish.exe (PID: 3248)
- touch.exe (PID: 1776)
- banish.exe (PID: 496)
- banish.exe (PID: 2752)
- touch.exe (PID: 592)
- touch.exe (PID: 3296)
- touch.exe (PID: 592)
- touch.exe (PID: 2204)
- touch.exe (PID: 2440)
- touch.exe (PID: 3504)
- touch.exe (PID: 3272)
- touch.exe (PID: 3768)
- touch.exe (PID: 3128)
- touch.exe (PID: 3652)
Modifies hosts file to block updates
- cmd.exe (PID: 2084)
Writes to the hosts file
- cmd.exe (PID: 2084)
Loads dropped or rewritten executable
- cmd.exe (PID: 3004)
- conhost.exe (PID: 1268)
- cmd.exe (PID: 3864)
- cmd.exe (PID: 3840)
- conhost.exe (PID: 3740)
- cmd.exe (PID: 3580)
- cmd.exe (PID: 2572)
- touch.exe (PID: 3296)
- conhost.exe (PID: 492)
- conhost.exe (PID: 2576)
- cmd.exe (PID: 3820)
- Chew-WGA-v0.9.eXe (PID: 2524)
- conhost.exe (PID: 320)
- windanr.exe (PID: 3472)
- cmd.exe (PID: 2028)
- find.exe (PID: 1012)
- banish.exe (PID: 2752)
- find.exe (PID: 2448)
- cmd.exe (PID: 2472)
- cmd.exe (PID: 1916)
- hosts.exe (PID: 2832)
- conhost.exe (PID: 3916)
- cmd.exe (PID: 3308)
- conhost.exe (PID: 3640)
- conhost.exe (PID: 436)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 2564)
- touch.exe (PID: 1776)
- conhost.exe (PID: 2876)
- conhost.exe (PID: 3832)
- cmd.exe (PID: 3876)
- AUDIODG.EXE (PID: 4044)
- touch.exe (PID: 3948)
- cmd.exe (PID: 1740)
- cmd.exe (PID: 2288)
- touch.exe (PID: 820)
- cmd.exe (PID: 932)
- conhost.exe (PID: 3676)
- cmd.exe (PID: 2644)
- touch.exe (PID: 2632)
- conhost.exe (PID: 3180)
- conhost.exe (PID: 2696)
- cmd.exe (PID: 2724)
- conhost.exe (PID: 1728)
- touch.exe (PID: 2204)
- cmd.exe (PID: 3536)
- touch.exe (PID: 1252)
- cmd.exe (PID: 3432)
- cmd.exe (PID: 3476)
- conhost.exe (PID: 2760)
- cmd.exe (PID: 2116)
- conhost.exe (PID: 3940)
- touch.exe (PID: 1528)
- cmd.exe (PID: 2476)
- touch.exe (PID: 1792)
- conhost.exe (PID: 3352)
- conhost.exe (PID: 2076)
- cmd.exe (PID: 4068)
- touch.exe (PID: 3504)
- conhost.exe (PID: 584)
- cmd.exe (PID: 3124)
- banish.exe (PID: 3692)
- touch.exe (PID: 4068)
- conhost.exe (PID: 3624)
- autorun.exe (PID: 2864)
- cmd.exe (PID: 2852)
- takeown.exe (PID: 1556)
- conhost.exe (PID: 2580)
- cmd.exe (PID: 4048)
- cmd.exe (PID: 1932)
- banish.exe (PID: 3248)
- conhost.exe (PID: 2760)
- conhost.exe (PID: 2884)
- conhost.exe (PID: 1800)
- conhost.exe (PID: 1796)
- conhost.exe (PID: 3684)
- takeown.exe (PID: 3148)
- takeown.exe (PID: 3188)
- cmd.exe (PID: 3340)
- cmd.exe (PID: 2696)
- cmd.exe (PID: 2484)
- cmd.exe (PID: 3744)
- touch.exe (PID: 592)
- cmd.exe (PID: 1744)
- takeown.exe (PID: 2856)
- conhost.exe (PID: 4052)
- touch.exe (PID: 592)
- banish.exe (PID: 1412)
- conhost.exe (PID: 3728)
- conhost.exe (PID: 3344)
- find.exe (PID: 2460)
- conhost.exe (PID: 2476)
- takeown.exe (PID: 3736)
- cmd.exe (PID: 2084)
- conhost.exe (PID: 1516)
- cmd.exe (PID: 3440)
- conhost.exe (PID: 2384)
- conhost.exe (PID: 3780)
- cmd.exe (PID: 3828)
- conhost.exe (PID: 736)
- cmd.exe (PID: 1992)
- conhost.exe (PID: 2948)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 3948)
- conhost.exe (PID: 616)
- cmd.exe (PID: 2352)
- takeown.exe (PID: 3132)
- conhost.exe (PID: 3508)
- touch.exe (PID: 1748)
- cmd.exe (PID: 1648)
- conhost.exe (PID: 3808)
- conhost.exe (PID: 3920)
- cmd.exe (PID: 1764)
- cmd.exe (PID: 3440)
- touch.exe (PID: 2440)
- cmd.exe (PID: 2724)
- conhost.exe (PID: 2436)
- touch.exe (PID: 1772)
- takeown.exe (PID: 2280)
- cmd.exe (PID: 716)
- cmd.exe (PID: 3708)
- conhost.exe (PID: 1812)
- cmd.exe (PID: 788)
- takeown.exe (PID: 3600)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 1504)
- conhost.exe (PID: 2304)
- touch.exe (PID: 3272)
- cmd.exe (PID: 1024)
- banish.exe (PID: 496)
- touch.exe (PID: 3768)
- touch.exe (PID: 3128)
- conhost.exe (PID: 272)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 3572)
- cmd.exe (PID: 1940)
- conhost.exe (PID: 2092)
- touch.exe (PID: 3652)
- cmd.exe (PID: 3868)
- conhost.exe (PID: 2296)
- conhost.exe (PID: 1724)
- takeown.exe (PID: 2060)
- conhost.exe (PID: 2500)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 3900)
- takeown.exe (PID: 3488)
- conhost.exe (PID: 460)
- cmd.exe (PID: 3560)
- conhost.exe (PID: 1504)
- cmd.exe (PID: 4028)
- conhost.exe (PID: 3780)
- cmd.exe (PID: 2532)
- cmd.exe (PID: 1448)
- conhost.exe (PID: 3756)
- conhost.exe (PID: 2948)
- DllHost.exe (PID: 3676)
SUSPICIOUS
Executable content was dropped or overwritten
- Chew-WGA-v0.9.eXe (PID: 2524)
- autorun.exe (PID: 2864)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 3708)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 788)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 1448)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2084)
- hosts.exe (PID: 2832)
- banish.exe (PID: 3692)
- autorun.exe (PID: 2864)
- banish.exe (PID: 1412)
- banish.exe (PID: 2752)
- banish.exe (PID: 3248)
- banish.exe (PID: 496)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 1992)
- cmd.exe (PID: 3004)
- cmd.exe (PID: 2696)
- cmd.exe (PID: 3580)
- cmd.exe (PID: 1764)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 2484)
- cmd.exe (PID: 1932)
- cmd.exe (PID: 3440)
- cmd.exe (PID: 3476)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 1504)
INFO
Reads the hosts file
- cmd.exe (PID: 3432)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 716)
- cmd.exe (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:06:23 19:57:07+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 192512 |
| InitializedDataSize: | 458752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x173a6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.9.0.0 |
| ProductVersionNumber: | 0.9.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | Created with AutoPlay Media Studio (www.indigorose.com) |
| CompanyName: | Anemeros Software |
| FileDescription: | The Perpetuation Endeavor |
| FileVersion: | 0.9.0.0 |
| InternalName: | ams60_launch |
| LegalCopyright: | Copyright (c) 2009 - Anemeros Software |
| LegalTrademarks: | Chew-WGA |
| OriginalFileName: | cw.exe |
| ProductName: | Chew-WGA v0.9 |
| ProductVersion: | 0.9.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Jun-2009 17:57:07 |
| Detected languages: |
|
| Comments: | Created with AutoPlay Media Studio (www.indigorose.com) |
| CompanyName: | Anemeros Software |
| FileDescription: | The Perpetuation Endeavor |
| FileVersion: | 0.9.0.0 |
| InternalName: | ams60_launch |
| LegalCopyright: | Copyright (c) 2009 - Anemeros Software |
| LegalTrademarks: | Chew-WGA |
| OriginalFilename: | cw.exe |
| ProductName: | Chew-WGA v0.9 |
| ProductVersion: | 0.9.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Jun-2009 17:57:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E906 | 0x0002F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.60114 |
.rdata | 0x00030000 | 0x0000842E | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.57824 |
.data | 0x00039000 | 0x00009D08 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.67512 |
.rsrc | 0x00043000 | 0x000609FC | 0x00061000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.60247 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02016 | 901 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.77242 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.67191 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.61132 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.54801 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.5135 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.44696 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.26041 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.02695 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
10 | 2.74274 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
WINSPOOL.DRV |
comdlg32.dll |
Total processes
207
Monitored processes
173
Malicious processes
37
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 320 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 436 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 460 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 496 | banish.exe "C:\Windows\System32\winver.exe" | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Scripts\banish.exe | — | cmd.exe | |||||||||||
User: admin Company: Anemeros Integrity Level: HIGH Exit code: 1 Version: 1. 0. 0. 0 Modules
| |||||||||||||||
| 584 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | touch.exe /h /q /c /m /a /r C:\Windows\System32\user32.dll t1.txt | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Scripts\touch.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 592 | touch.exe /h /q /c /m /a /r C:\Windows\Sysnative\user32.dll t2a.txt | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Scripts\touch.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 616 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
560
Read events
540
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3472) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3472) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3472) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3472) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3472) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3472) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3472) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3472) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3472) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (3472) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
33
Suspicious files
15
Text files
197
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | Chew-WGA-v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Audio\Shekere.ogg | ogg | |
MD5:2B1395C376D645D076CE7E2171EF9C7F | SHA256:F8D1022DEE83BF00C33AD160F4085464CA5818CA186C909030FDA3F6D9C71A79 | |||
| 2524 | Chew-WGA-v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Audio\Click1.ogg | ogg | |
MD5:93270C4FA492E4E4EDEE872A2B961DDE | SHA256:25D49CBBD65D48AD462455F1143F73EE997DF8F747E7D2213DAAB18E321C028B | |||
| 2524 | Chew-WGA-v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Icons\mainicon.ico | image | |
MD5:31ACA1A1047EFBC8D2A6E22101B2227B | SHA256:A9EAAFA2C8E36BB80F58D5930694676D76DAB647B8F709F3142649BB8018FBFA | |||
| 2524 | Chew-WGA-v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\Home2.Btn | compressed | |
MD5:1C85362B0780DFB2F580E567AD57643A | SHA256:70919D158D55BA3A9C38BBE91C79BC69452E67FE7862AA00FE77DF56A7DDE4E7 | |||
| 2524 | Chew-WGA-v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\Baslat.Btn | compressed | |
MD5:DB33064E86D7E634CB842DD2918A3E05 | SHA256:05FFCFCA2AAD8509C6A16FFBCC727F290449956E9884495D86045A129331B0A4 | |||
| 2524 | Chew-WGA-v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\Cik-2.Btn | compressed | |
MD5:2553A95A1D503C6C445DF761BF668E00 | SHA256:8311159D24F50560BAB4491918D0684E66AB80ECABC158118B9AE4063B2473AA | |||
| 2524 | Chew-WGA-v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\Sol-4.Btn | compressed | |
MD5:AAD23F06616570B7DCD713B320217179 | SHA256:4C7218EE657EA5301FB87A0F9AB282E9002B0C2B2EAED4AF3DD9E7CCA2E72613 | |||
| 2524 | Chew-WGA-v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Images\done-install.jpg | image | |
MD5:B6479C2EC0E8353D8BA175D6D783612B | SHA256:457B13621CC0B8C07B048CAD8761DF175C3FEBC8B8E457789FDD88FEEDE20A83 | |||
| 2524 | Chew-WGA-v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\Cik11.Btn | compressed | |
MD5:EB199B1CB2087CADF5DD4D7B06DB4F62 | SHA256:B99136B165304979E84E98930EA5FEE03508B8967ACF6B82844B96863D916B15 | |||
| 2524 | Chew-WGA-v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Images\credits-screen.jpg | image | |
MD5:176DCAD7034126C2C5A9C96DE952DAC7 | SHA256:6B3396A302DDFDE39EFE8230C6B6EB30585DDF013CD56592780ED74DE1774B1D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report