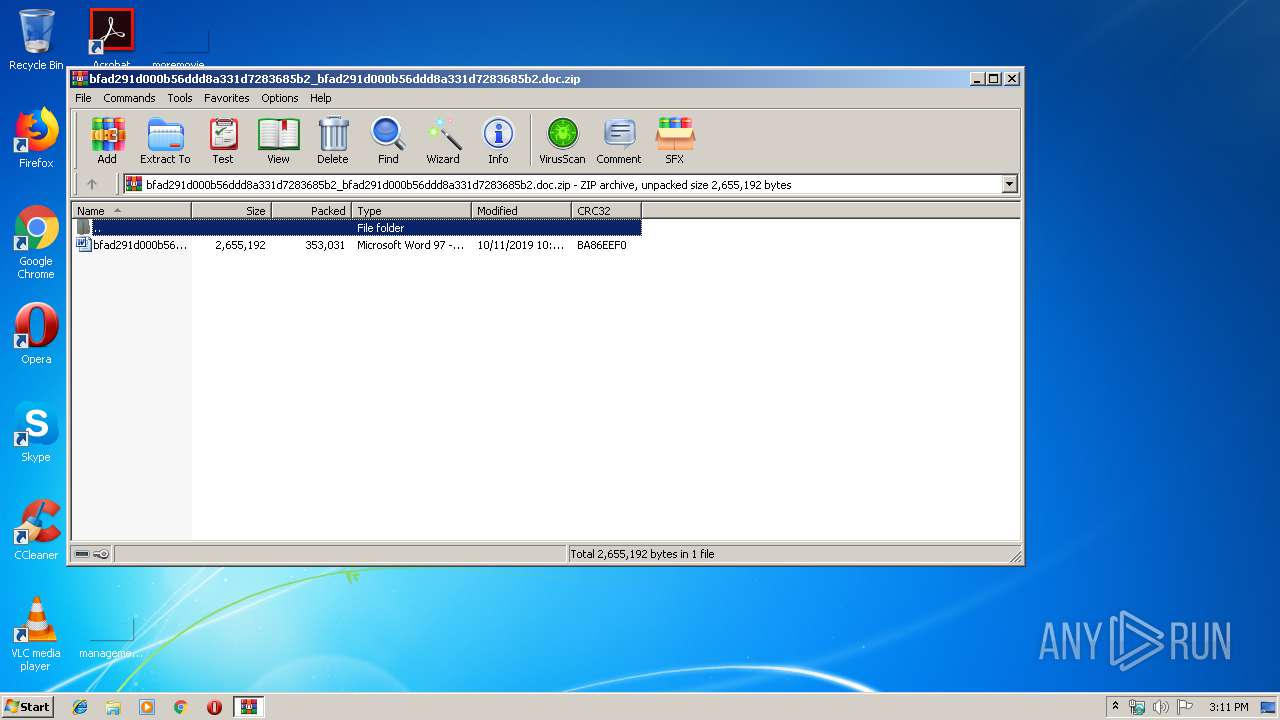
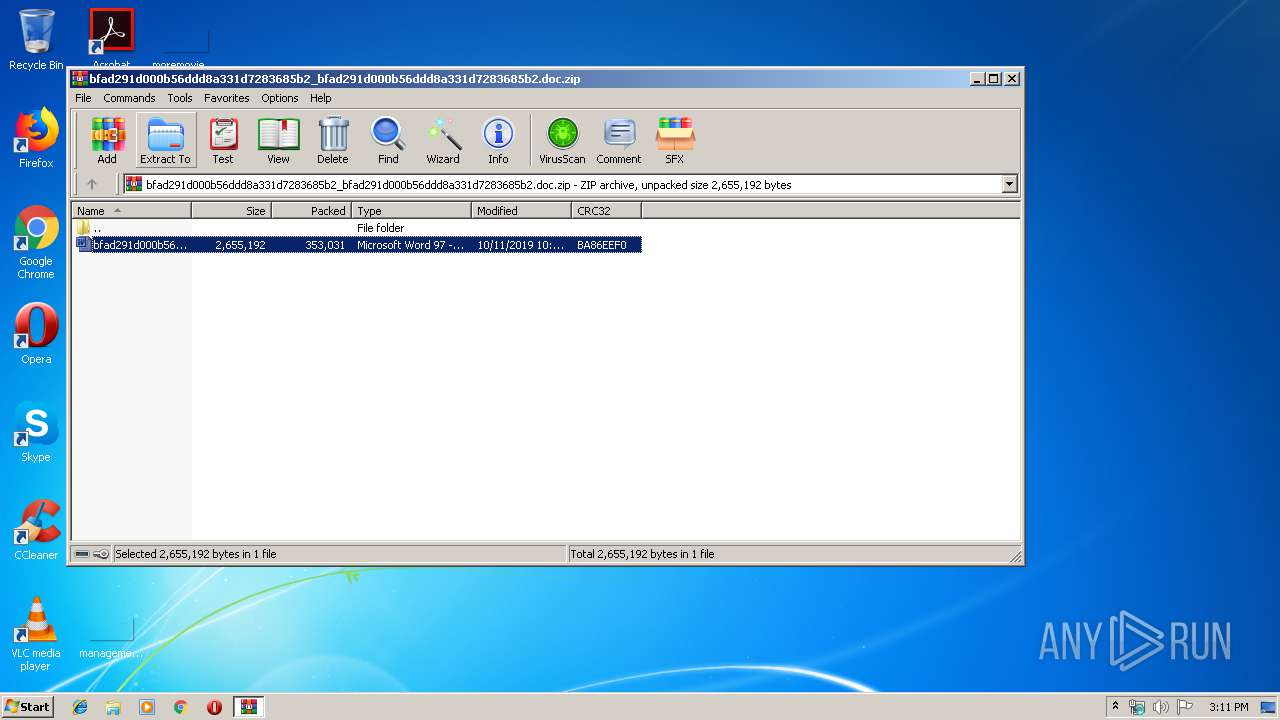
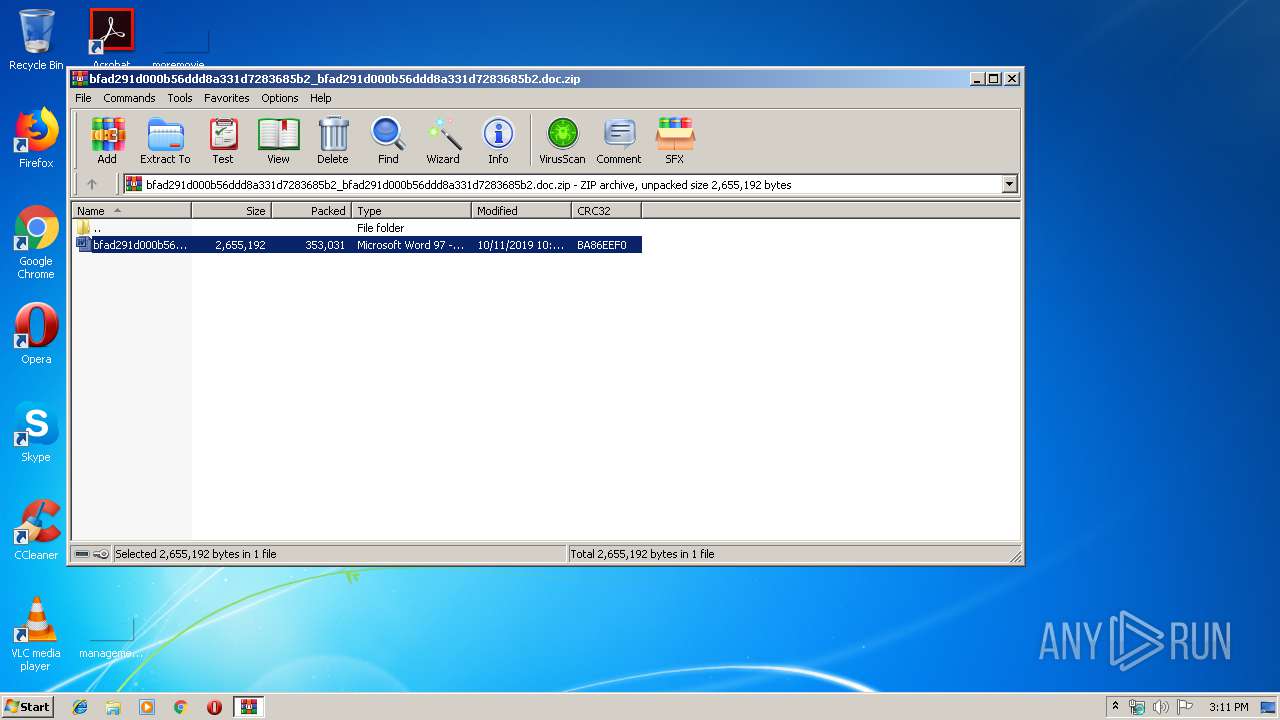
| File name: | bfad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc.zip |
| Full analysis: | https://app.any.run/tasks/512b8f84-3bca-4cb4-8cbd-601365f3cd13 |
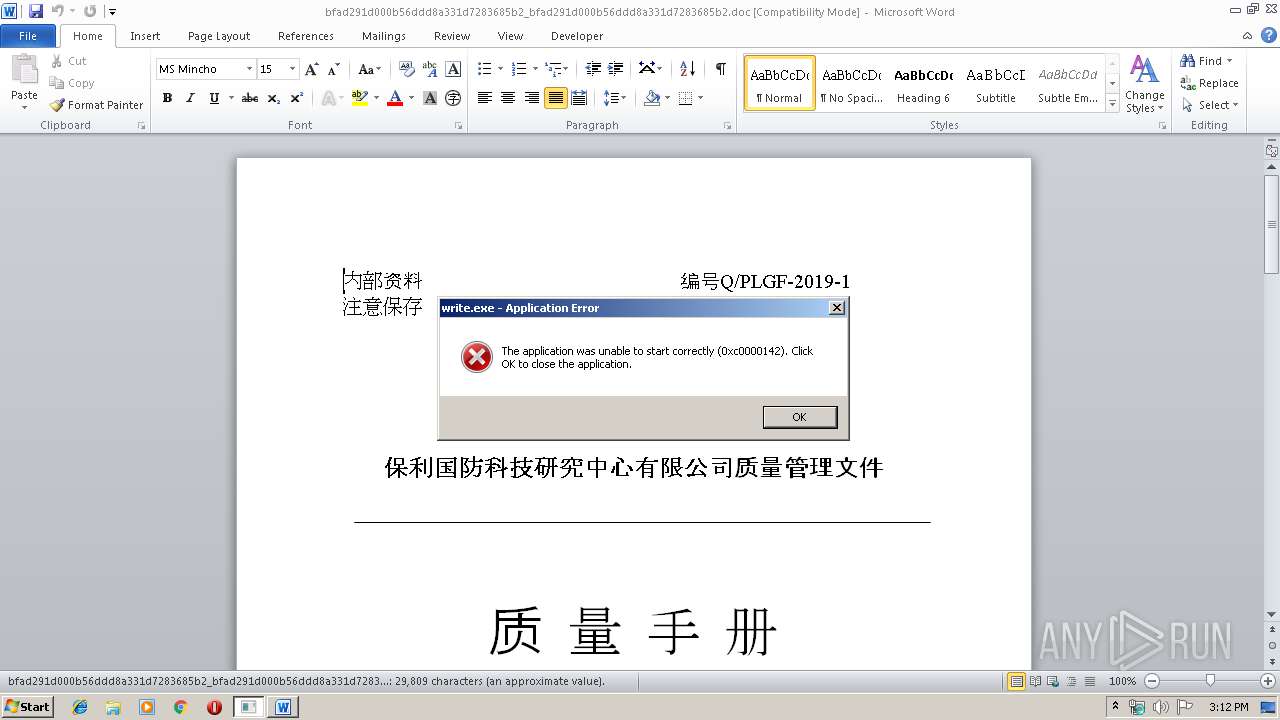
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 14:11:18 |
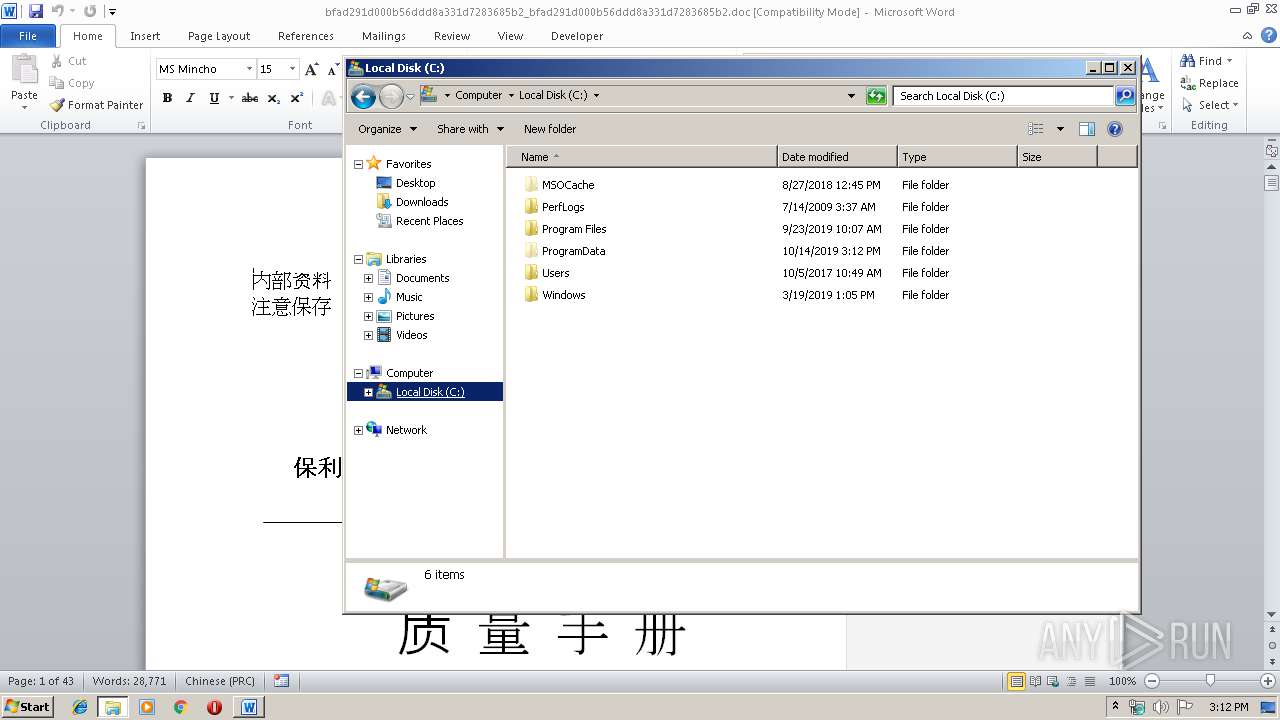
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1E815A32A3FD0DB3EC6022601779672D |
| SHA1: | CFF1E5F39CA619D41536B16CFAD0A8F37BC282C5 |
| SHA256: | 44055D730B636EEE349C8558C795D154AADBD502B63FDFFDE7105A0279931312 |
| SSDEEP: | 6144:/QfCHHgIwbApfb9sBZ/yoq2+2SUT4Ps0NGodaRIPrkyxkRtQJHOg0etF42f+:opwSHyoqR9XDGoairkyxkDQJOg0e7422 |
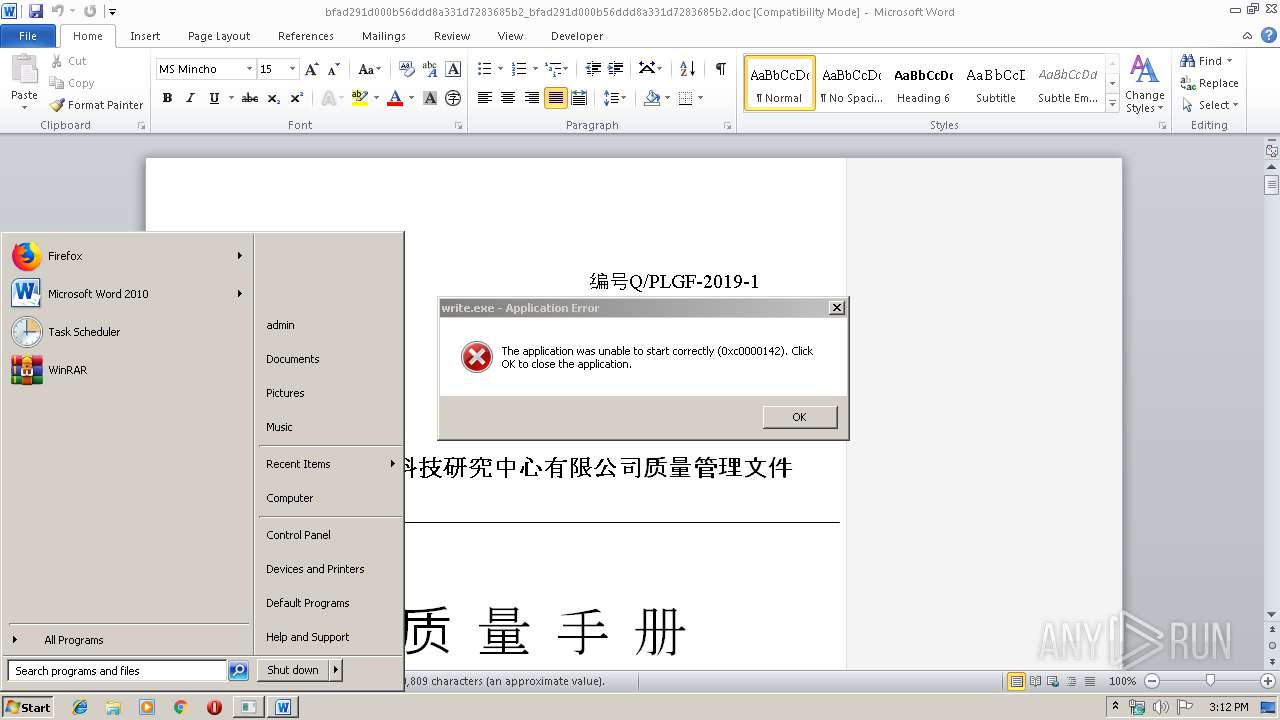
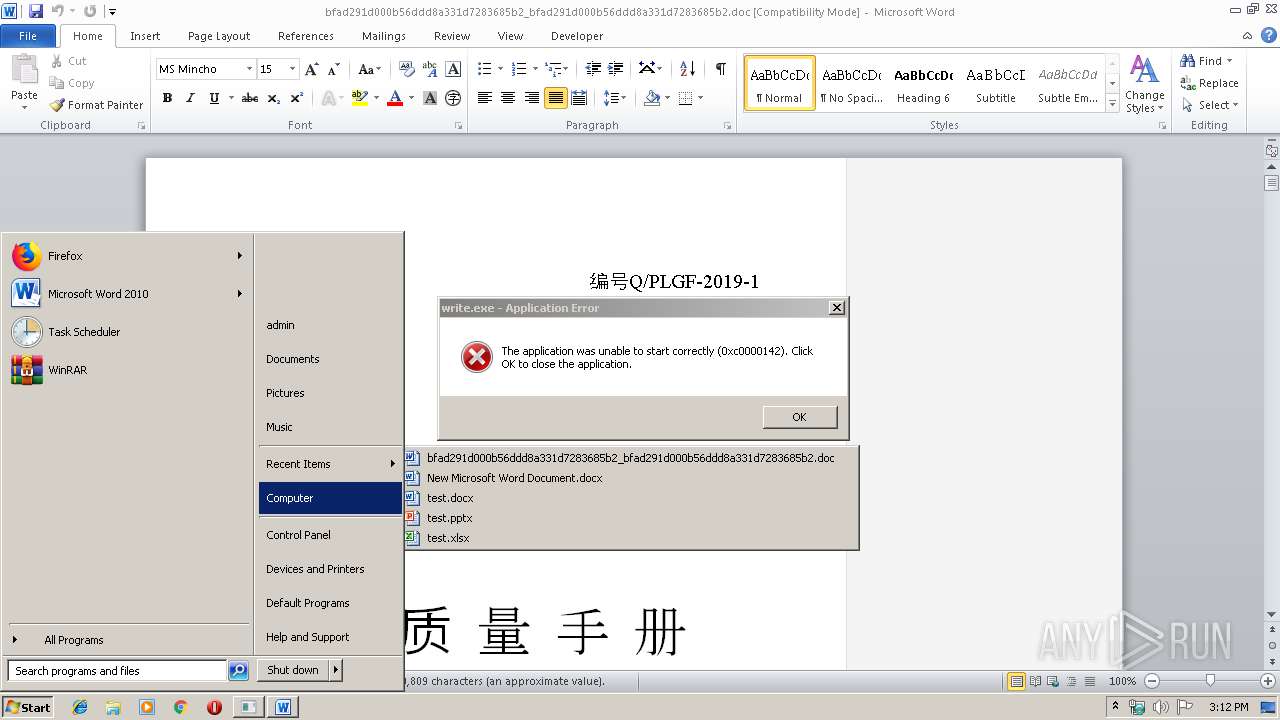
MALICIOUS
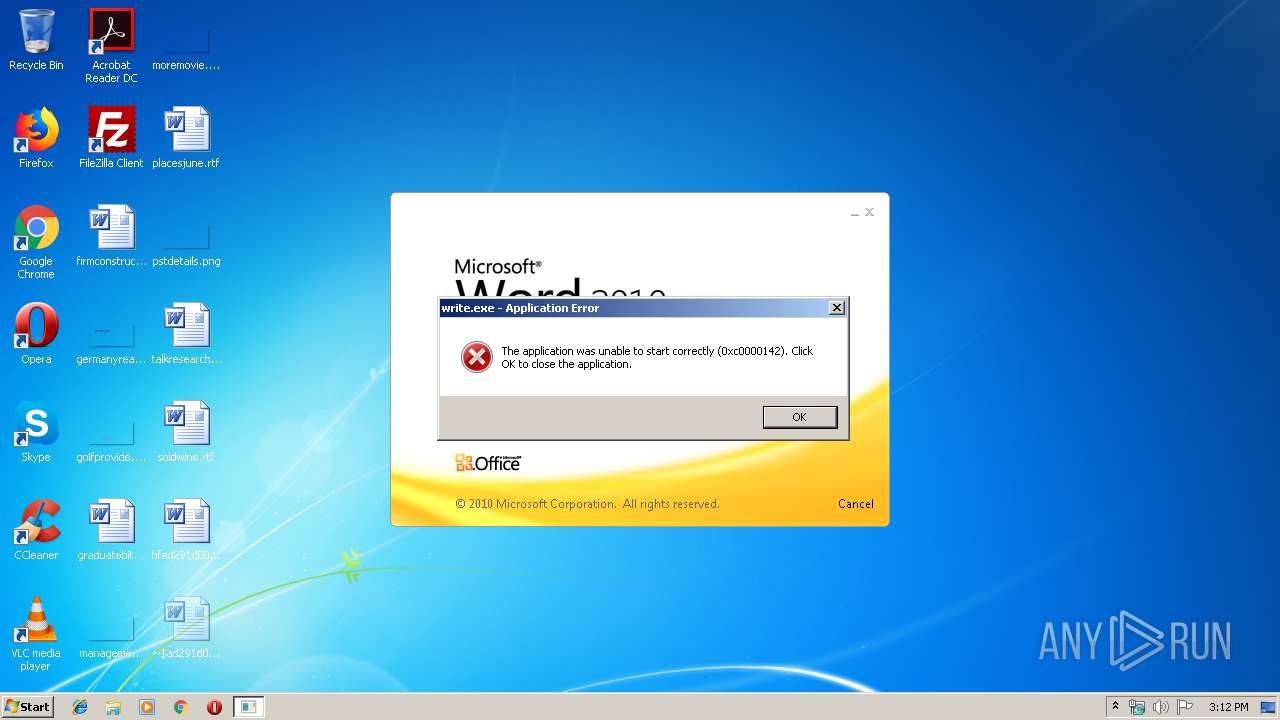
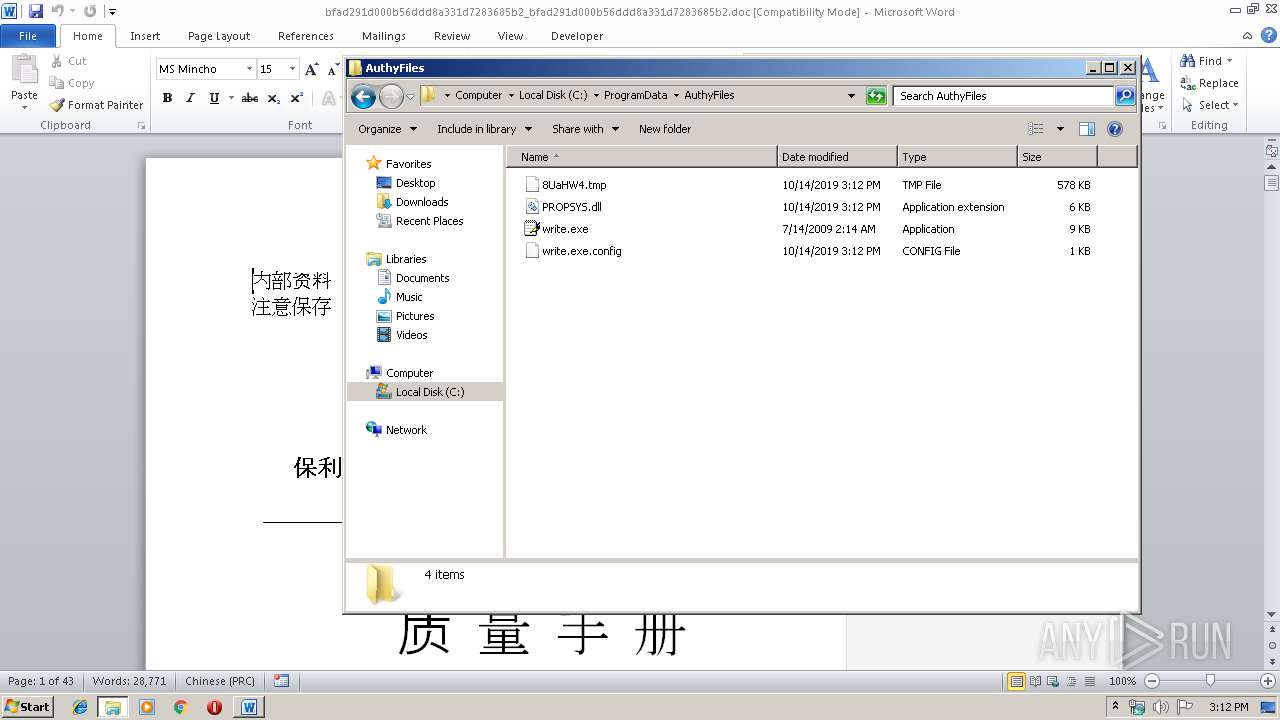
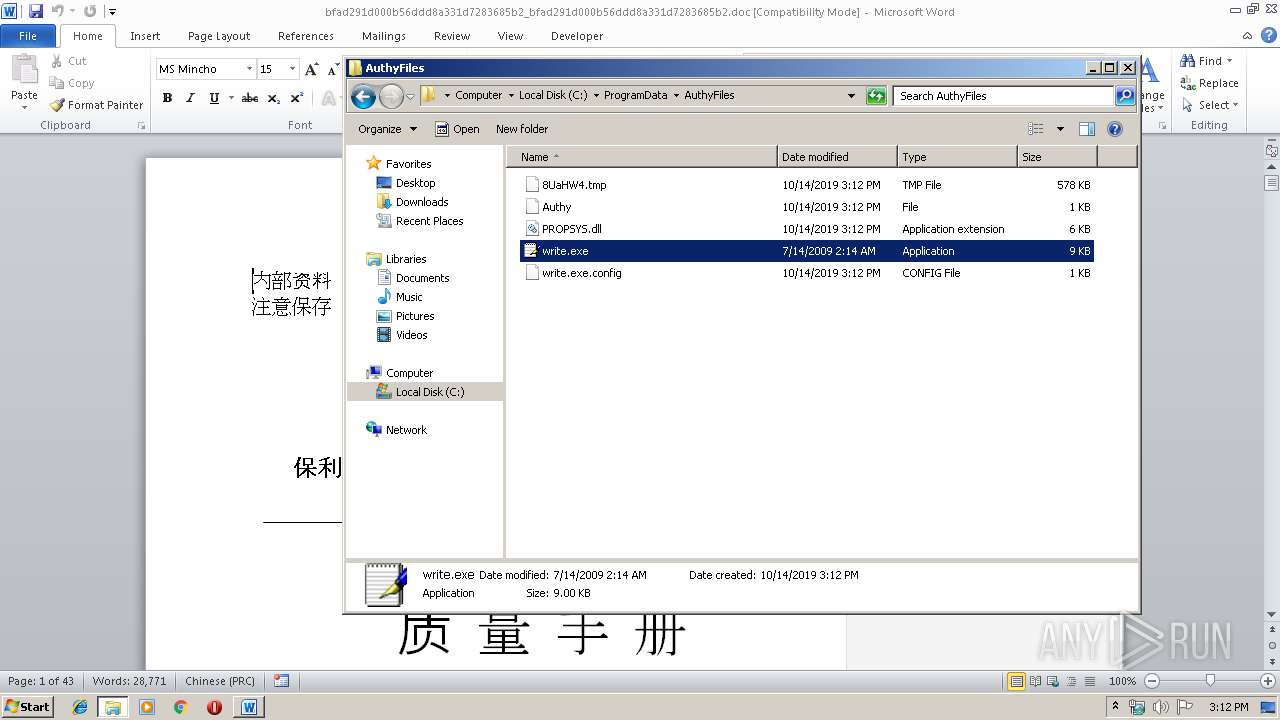
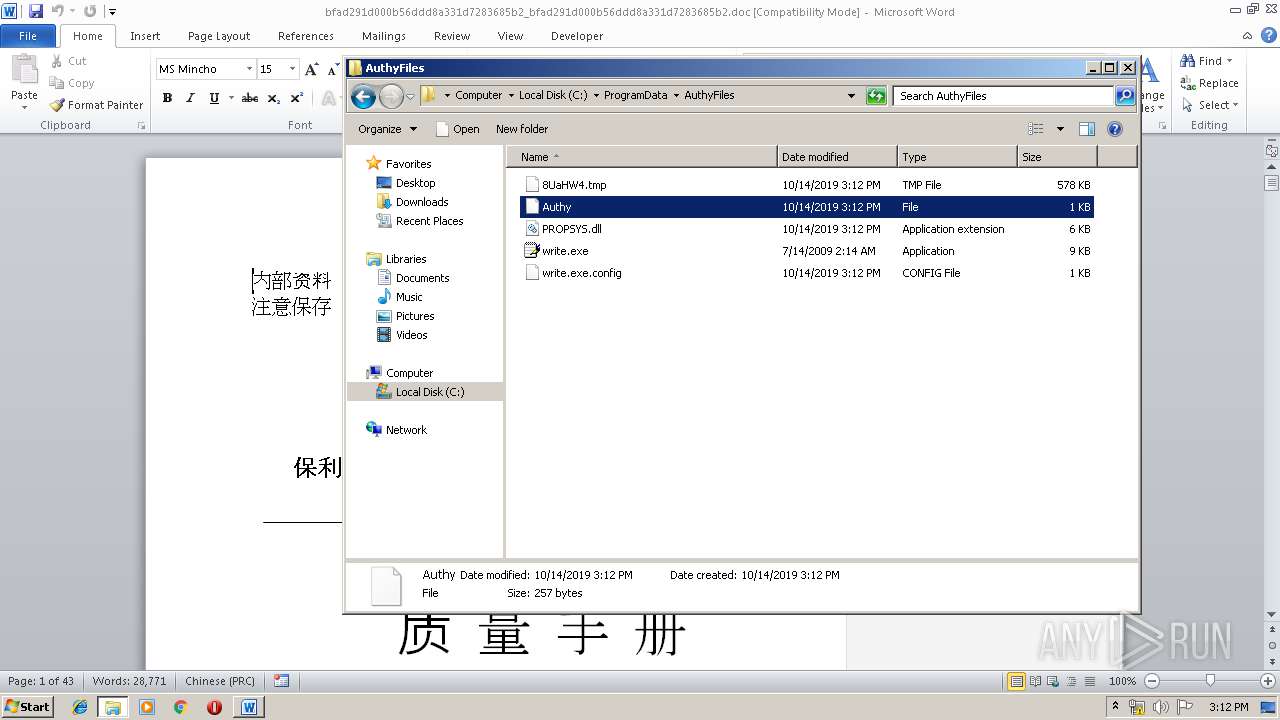
Application was dropped or rewritten from another process
- write.exe (PID: 2732)
- write.exe (PID: 2416)
Changes the autorun value in the registry
- EQNEDT32.EXE (PID: 2332)
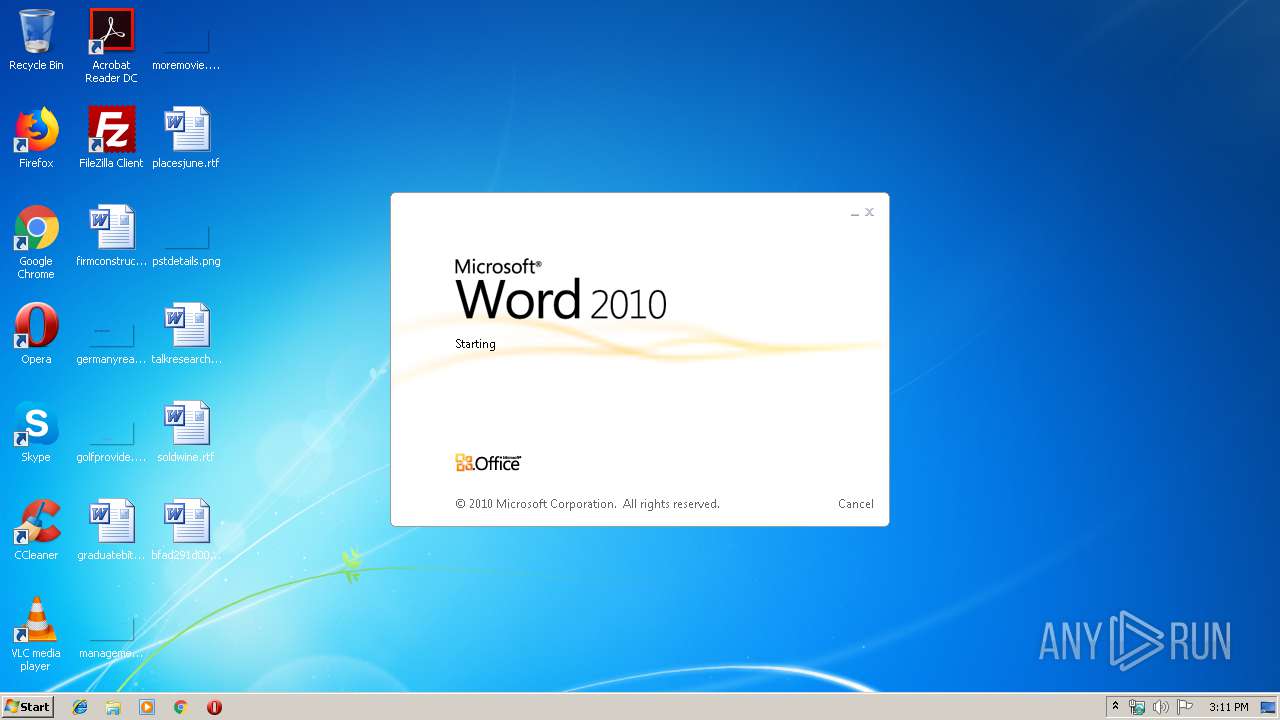
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2332)
Loads dropped or rewritten executable
- write.exe (PID: 2416)
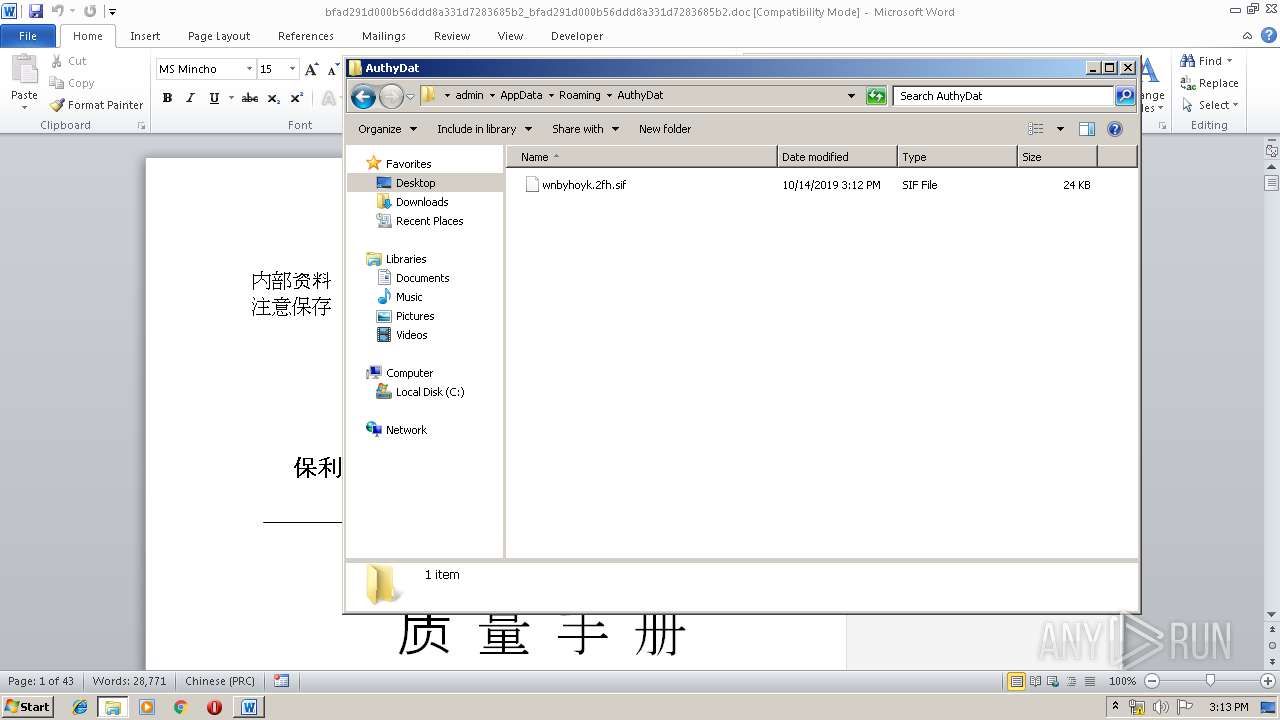
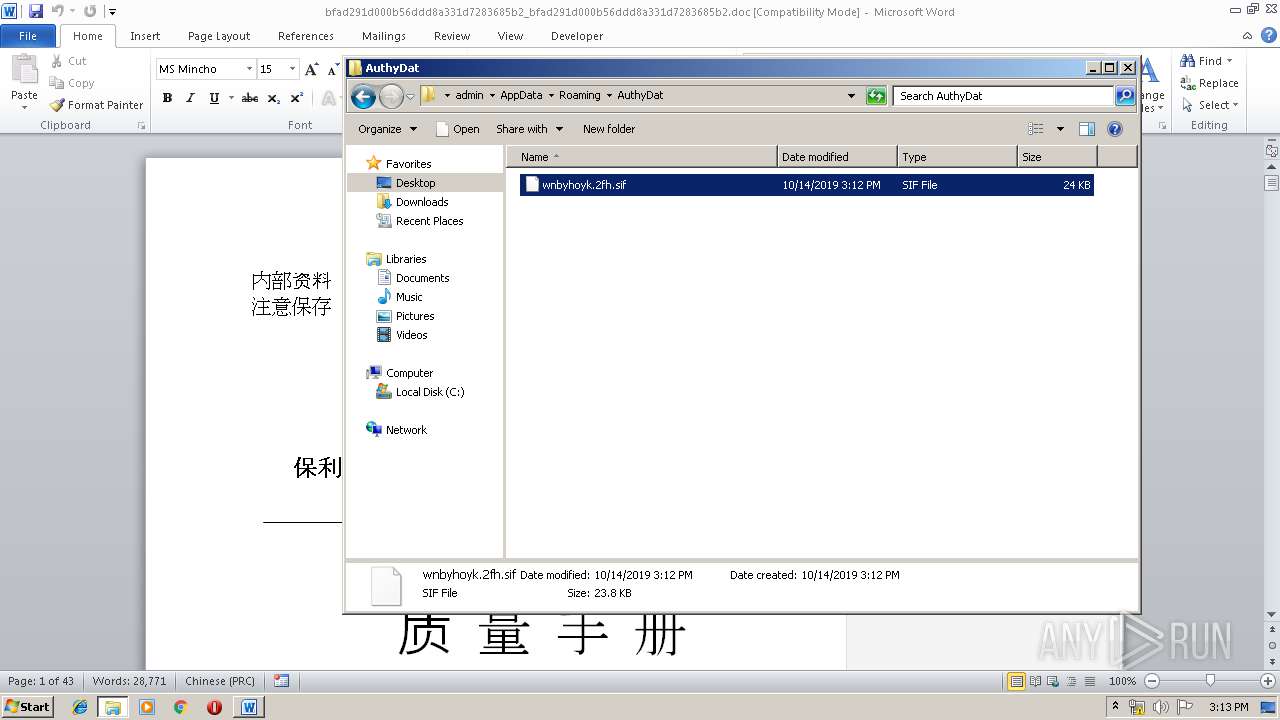
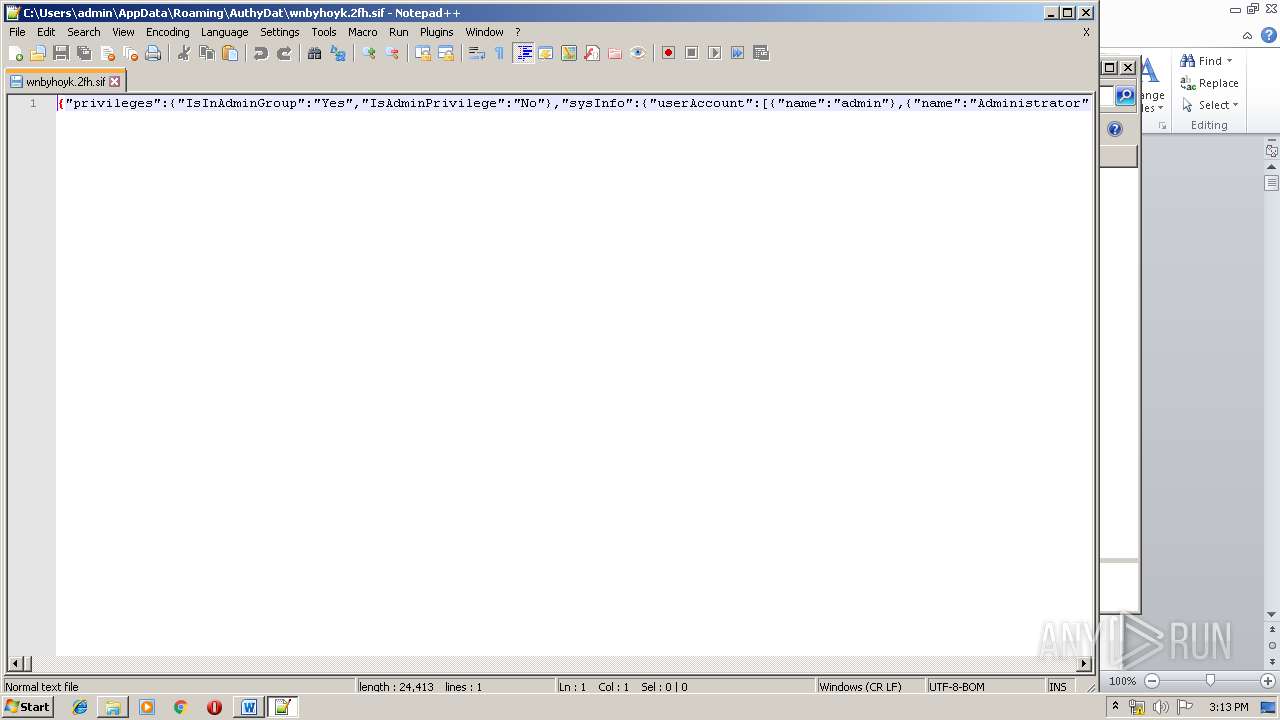
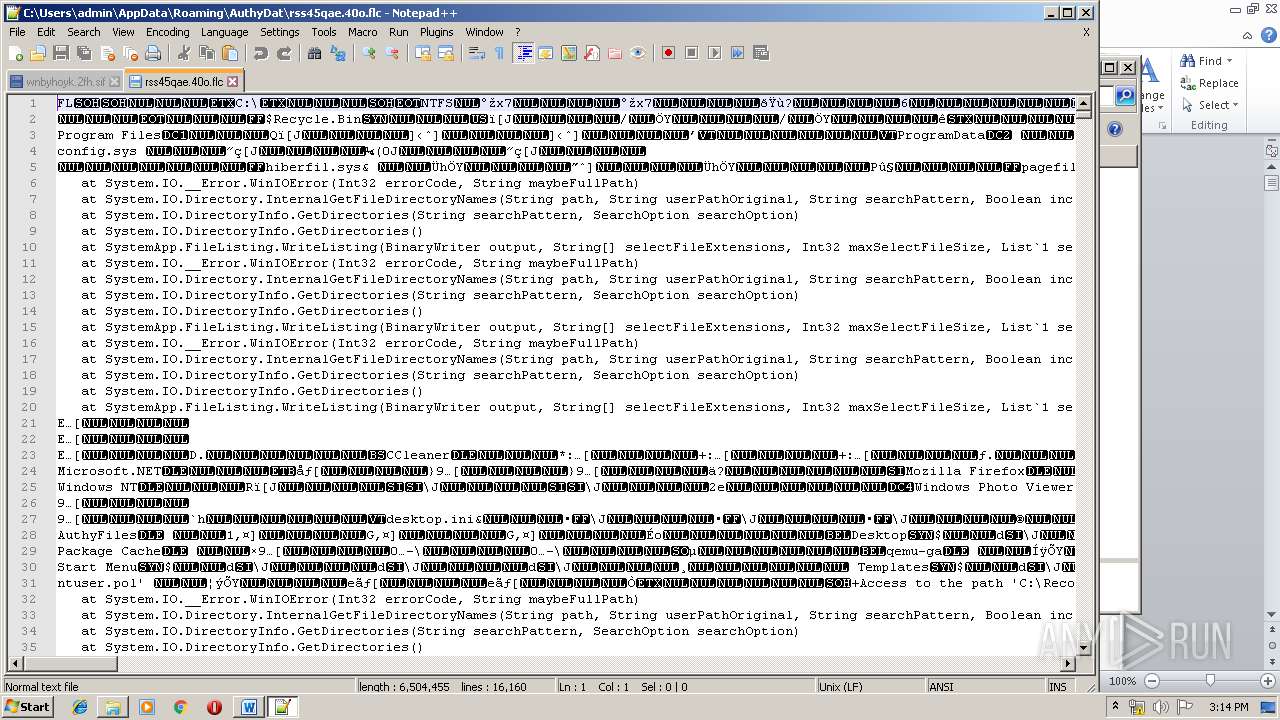
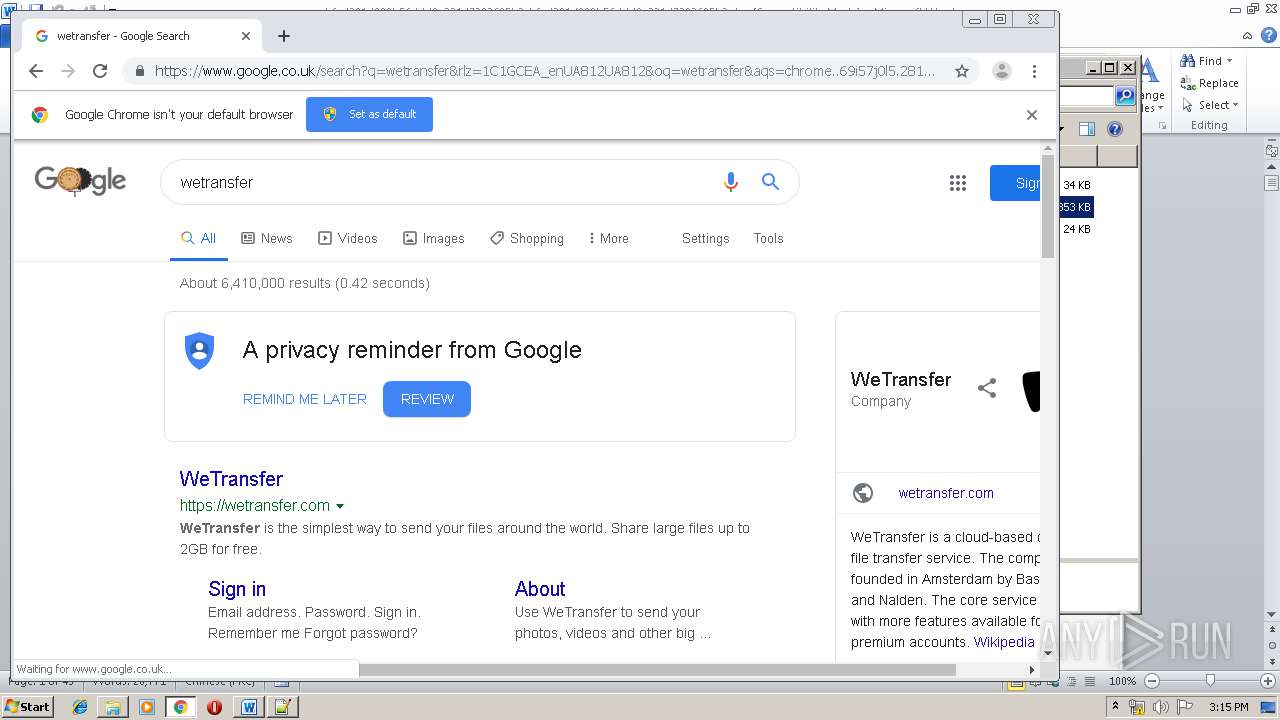
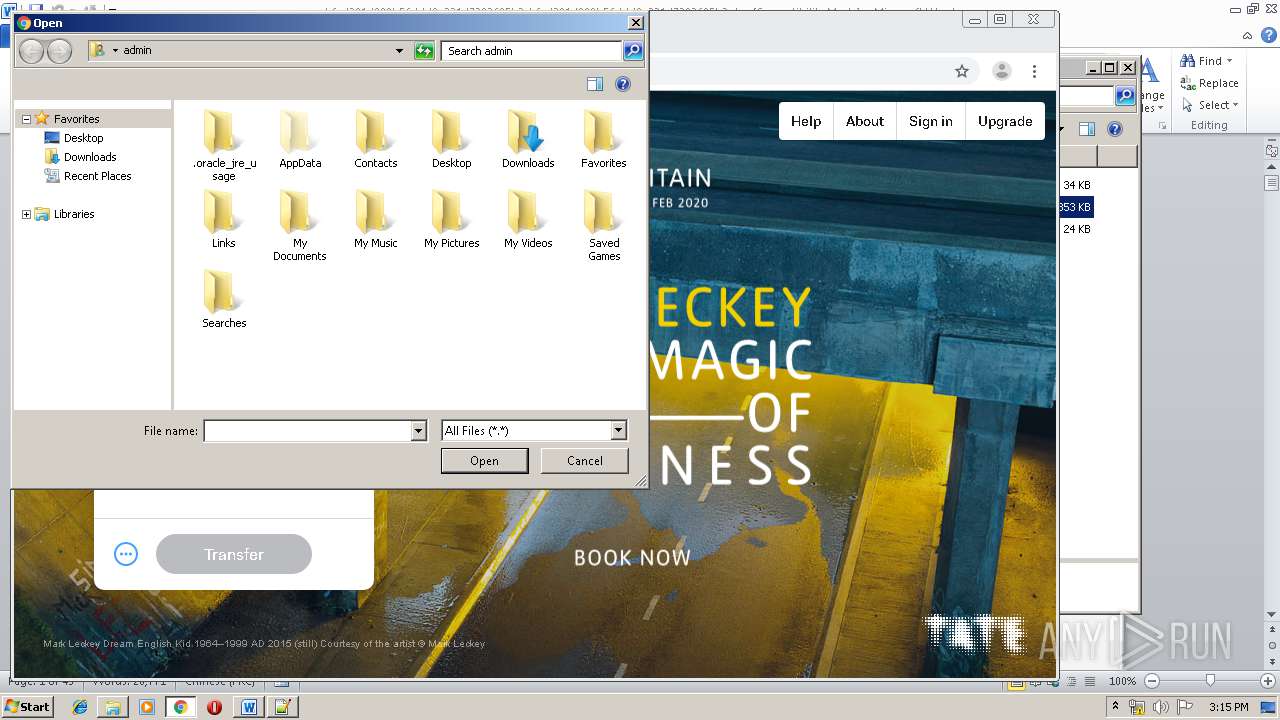
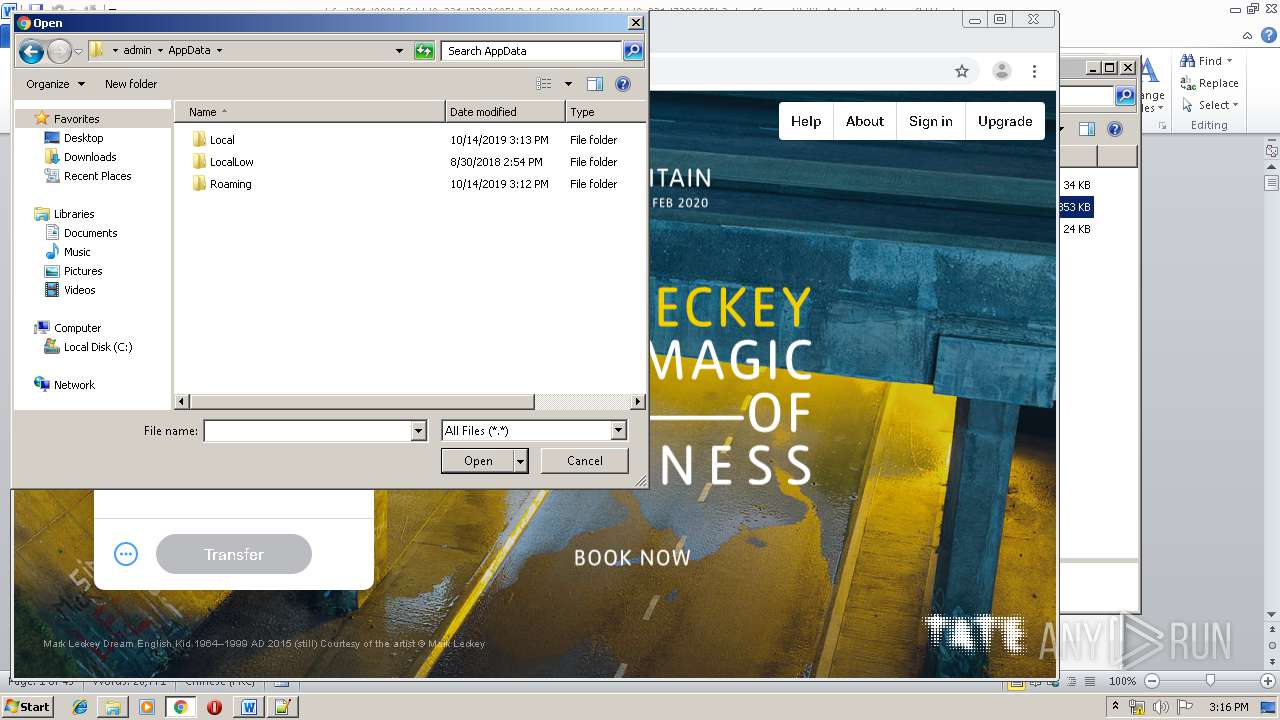
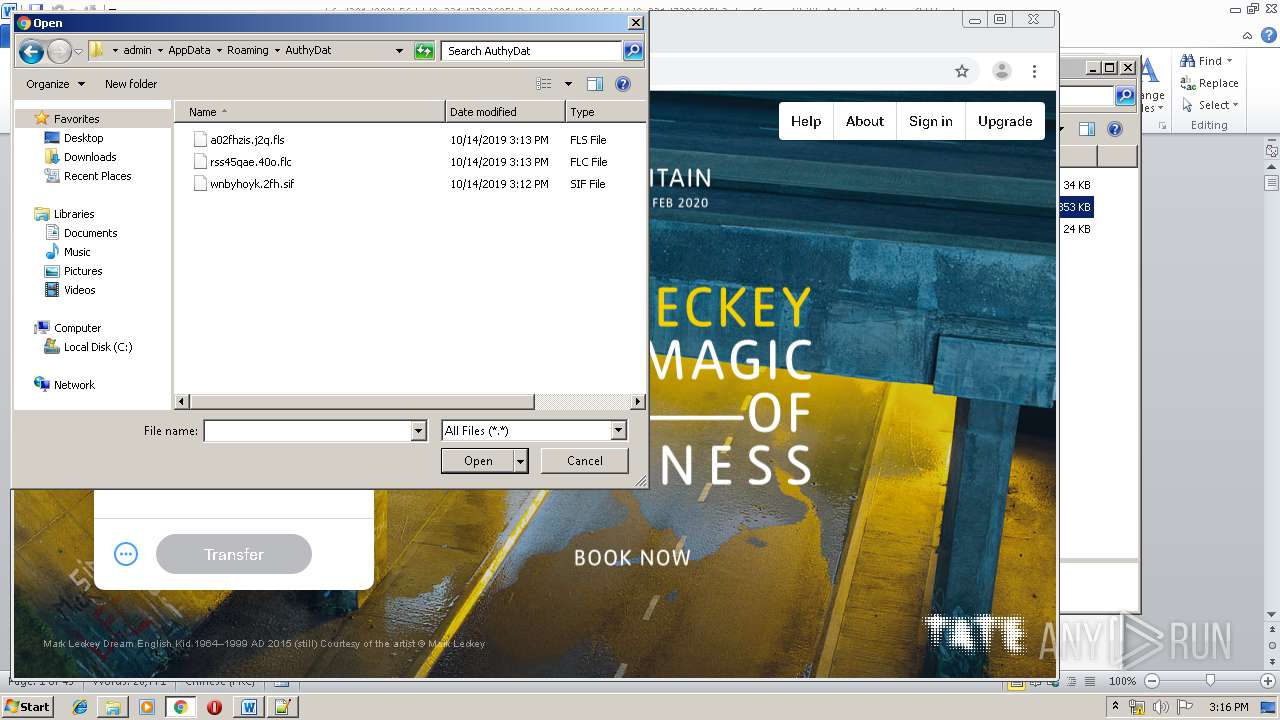
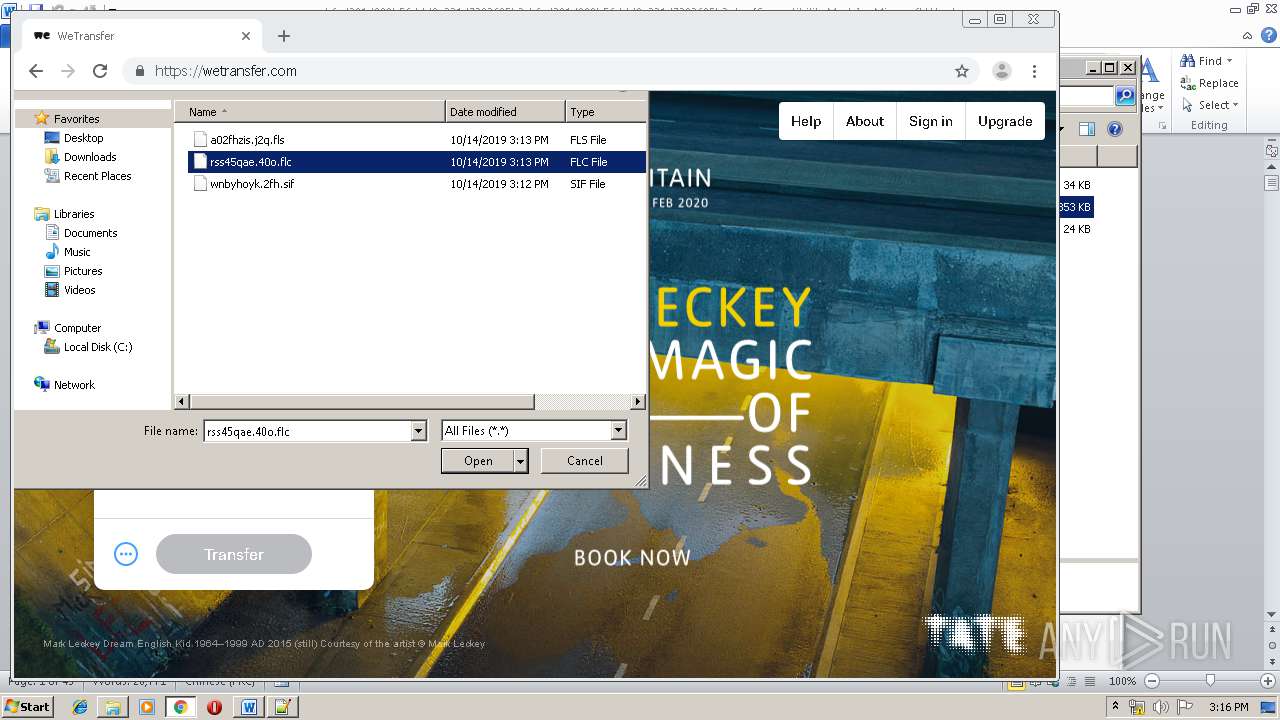
Actions looks like stealing of personal data
- write.exe (PID: 2416)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 2332)
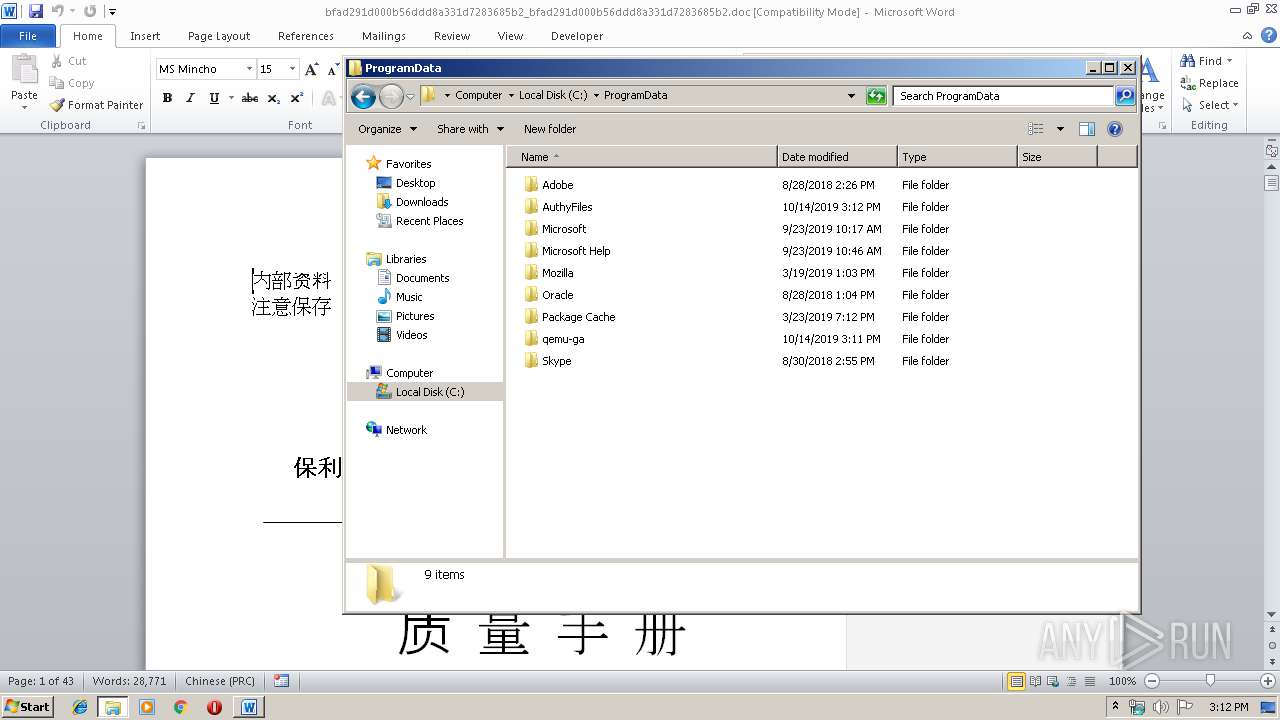
Creates files in the program directory
- EQNEDT32.EXE (PID: 2332)
- write.exe (PID: 2416)
Reads internet explorer settings
- EQNEDT32.EXE (PID: 2332)
Creates files in the user directory
- notepad++.exe (PID: 3300)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 2332)
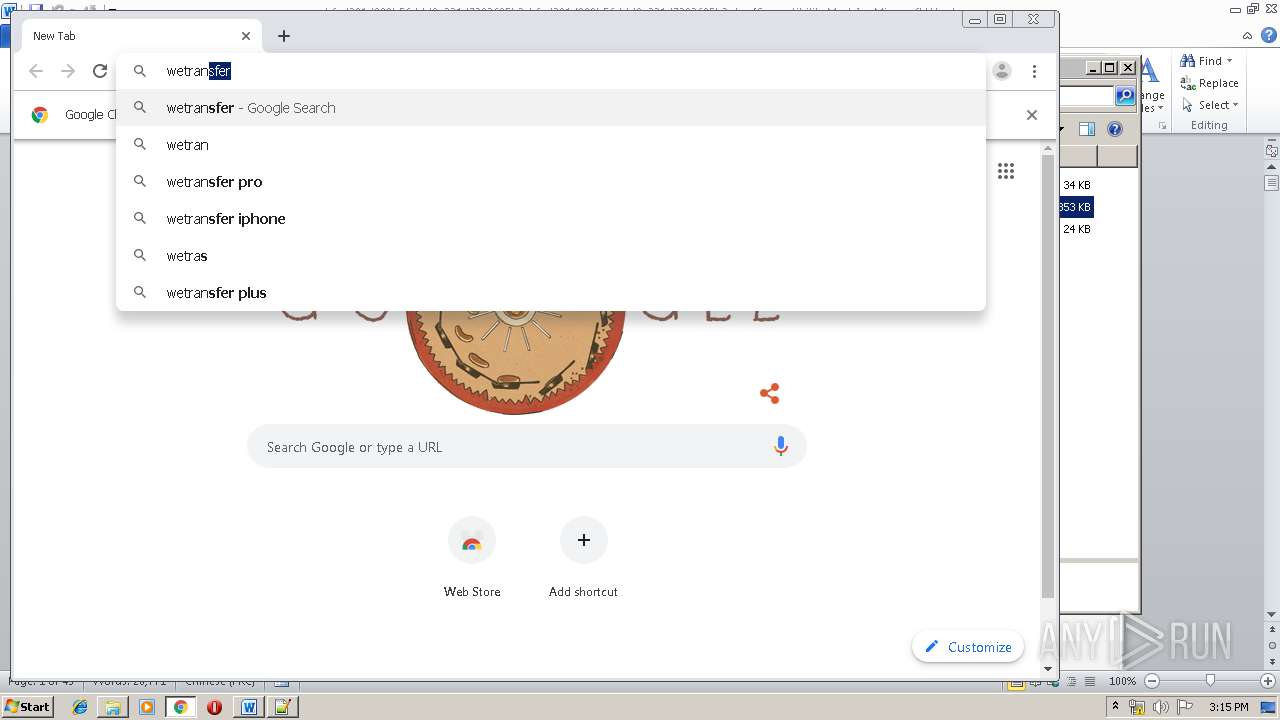
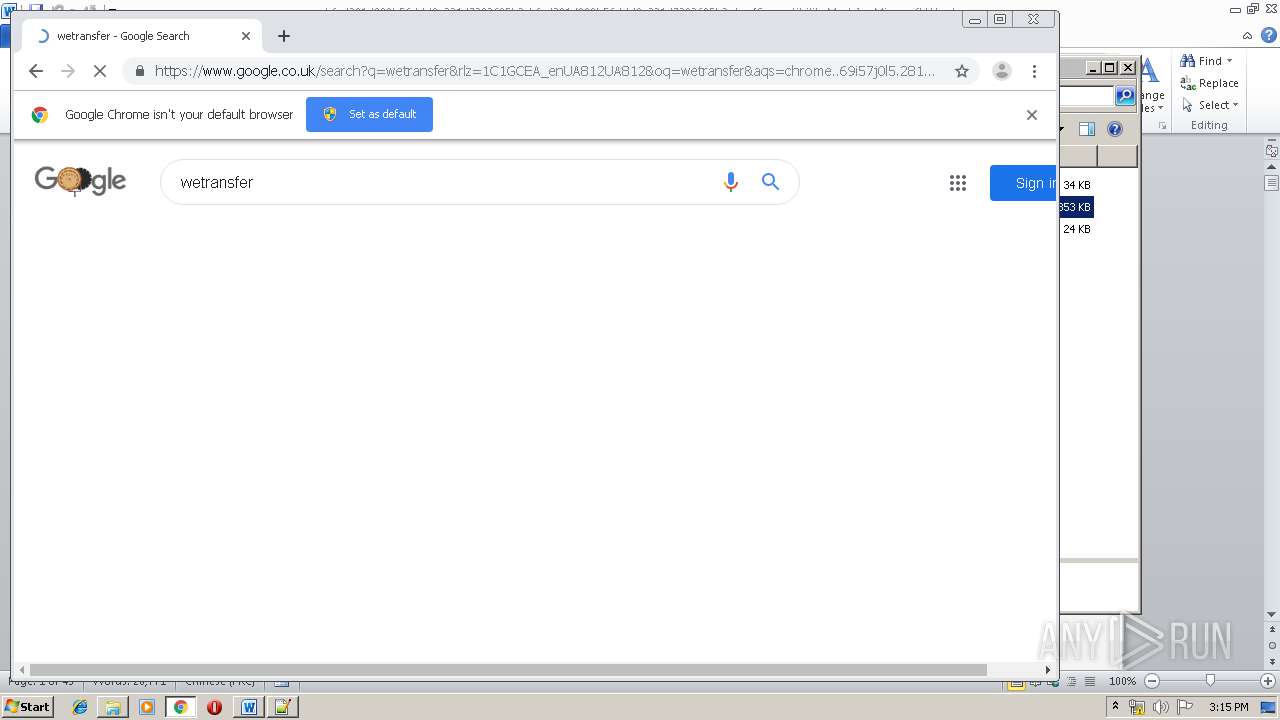
Modifies files in Chrome extension folder
- chrome.exe (PID: 3272)
INFO
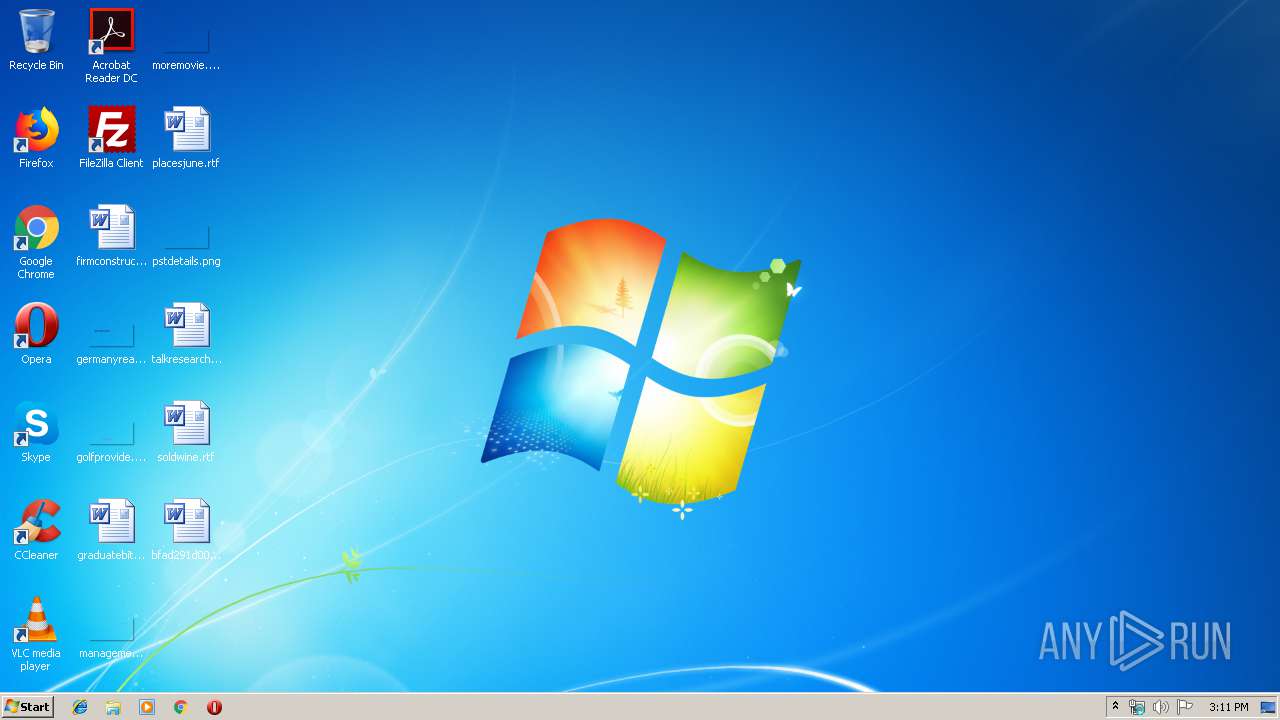
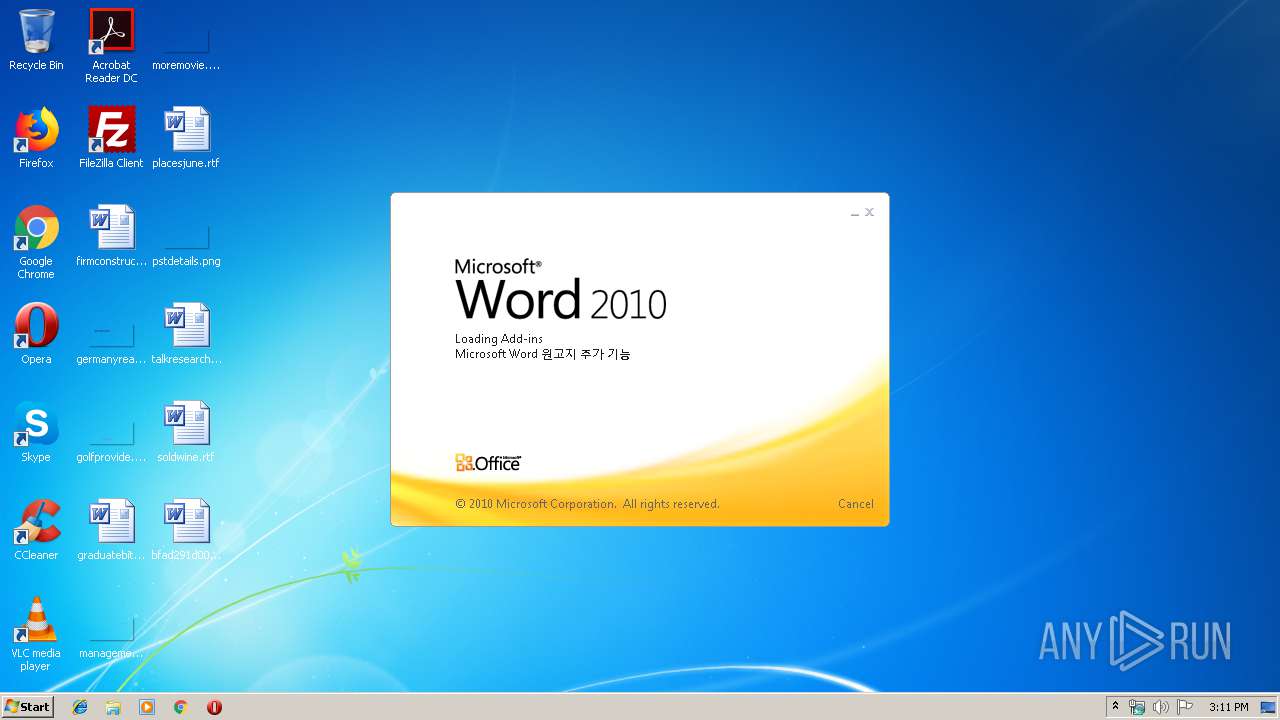
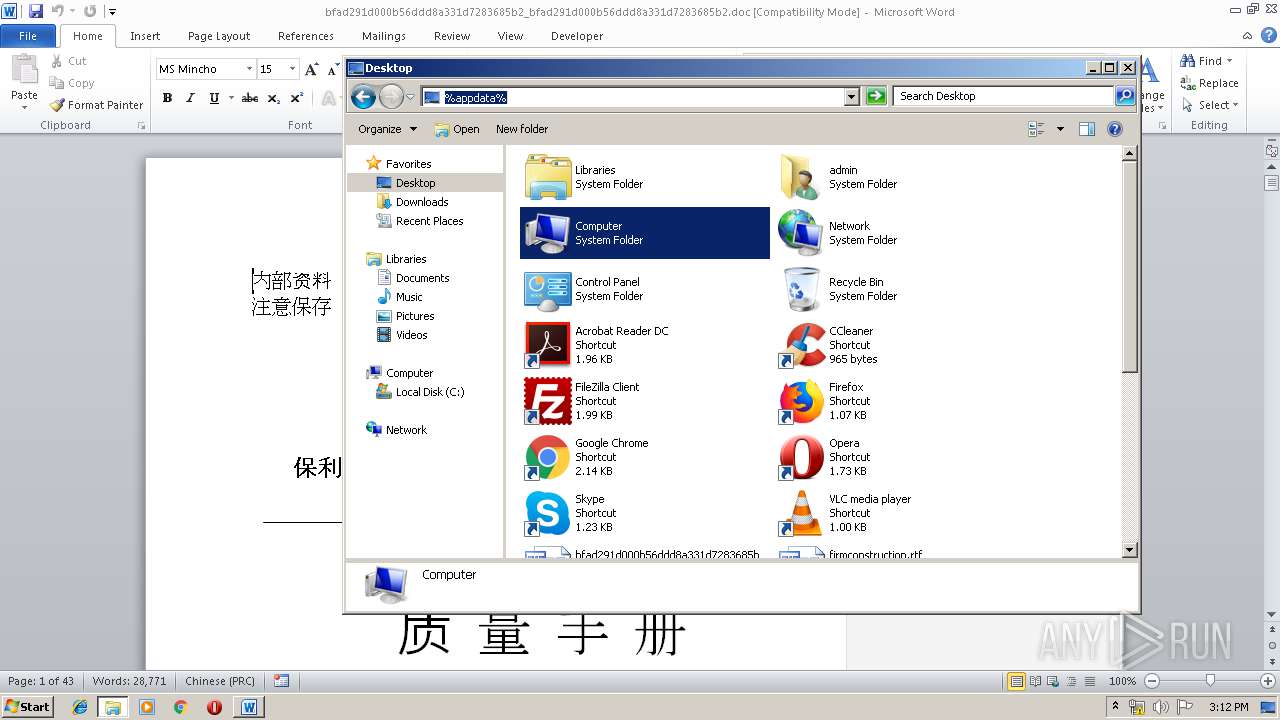
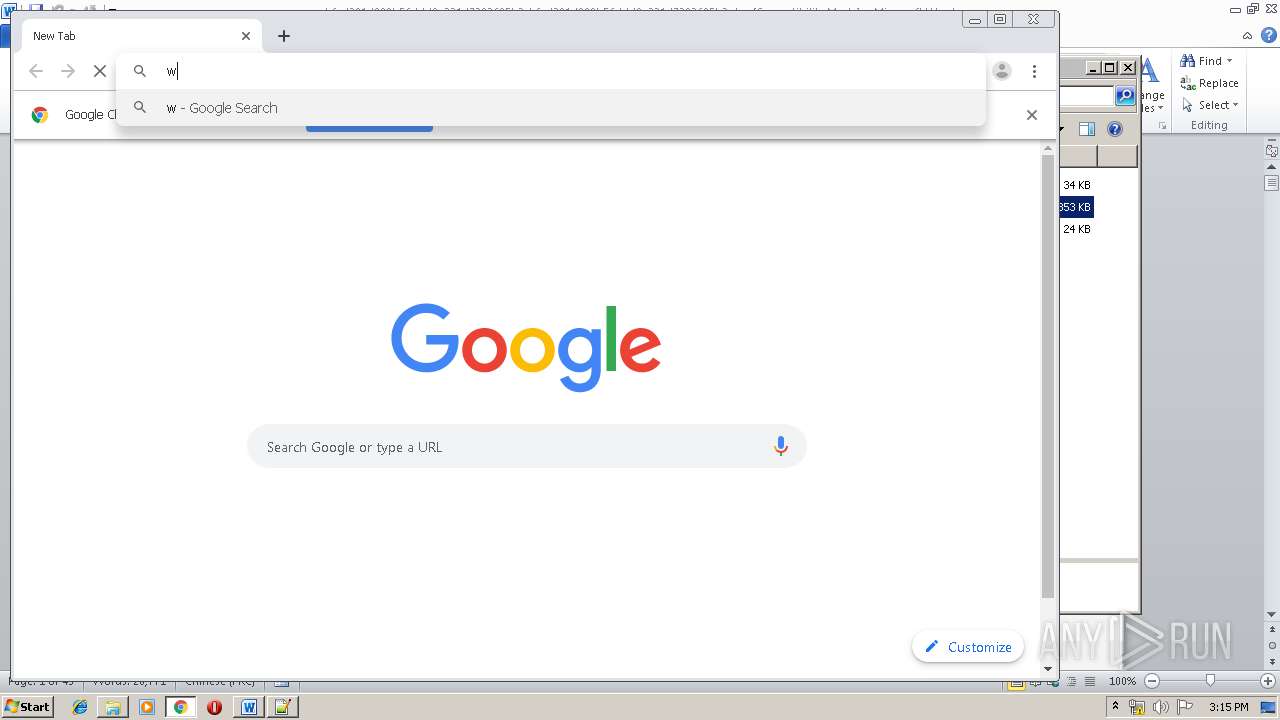
Manual execution by user
- WINWORD.EXE (PID: 1732)
- write.exe (PID: 2416)
- notepad++.exe (PID: 3304)
- notepad++.exe (PID: 3300)
- chrome.exe (PID: 3272)
Creates files in the user directory
- WINWORD.EXE (PID: 1732)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1732)
Application launched itself
- chrome.exe (PID: 3272)
Reads settings of System Certificates
- chrome.exe (PID: 4068)
Reads the hosts file
- chrome.exe (PID: 3272)
- chrome.exe (PID: 4068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:11 11:44:21 |
| ZipCRC: | 0xba86eef0 |
| ZipCompressedSize: | 353031 |
| ZipUncompressedSize: | 2655192 |
| ZipFileName: | bfad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc |
Total processes
90
Monitored processes
44
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,10698680909303847912,3515566358870455655,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11045043548491383794 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,10698680909303847912,3515566358870455655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18296094881051696651 --mojo-platform-channel-handle=4924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,10698680909303847912,3515566358870455655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10088610091693978854 --mojo-platform-channel-handle=4504 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,10698680909303847912,3515566358870455655,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5151739281561183169 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,10698680909303847912,3515566358870455655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13579950638840023235 --mojo-platform-channel-handle=4432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,10698680909303847912,3515566358870455655,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7026859481875395040 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,10698680909303847912,3515566358870455655,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10429816861100354618 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,10698680909303847912,3515566358870455655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18087812662244755696 --mojo-platform-channel-handle=3640 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\bfad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,10698680909303847912,3515566358870455655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16894539523446304366 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 791
Read events
2 439
Write events
1 208
Delete events
144
Modification events
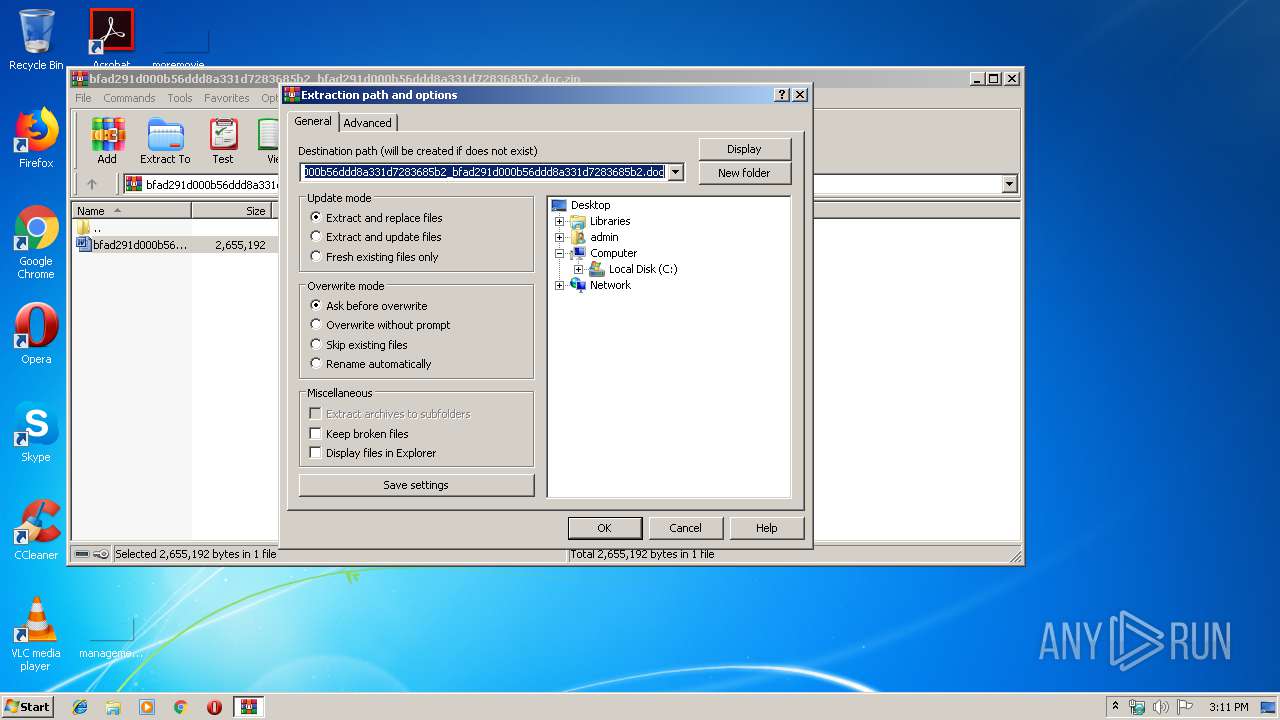
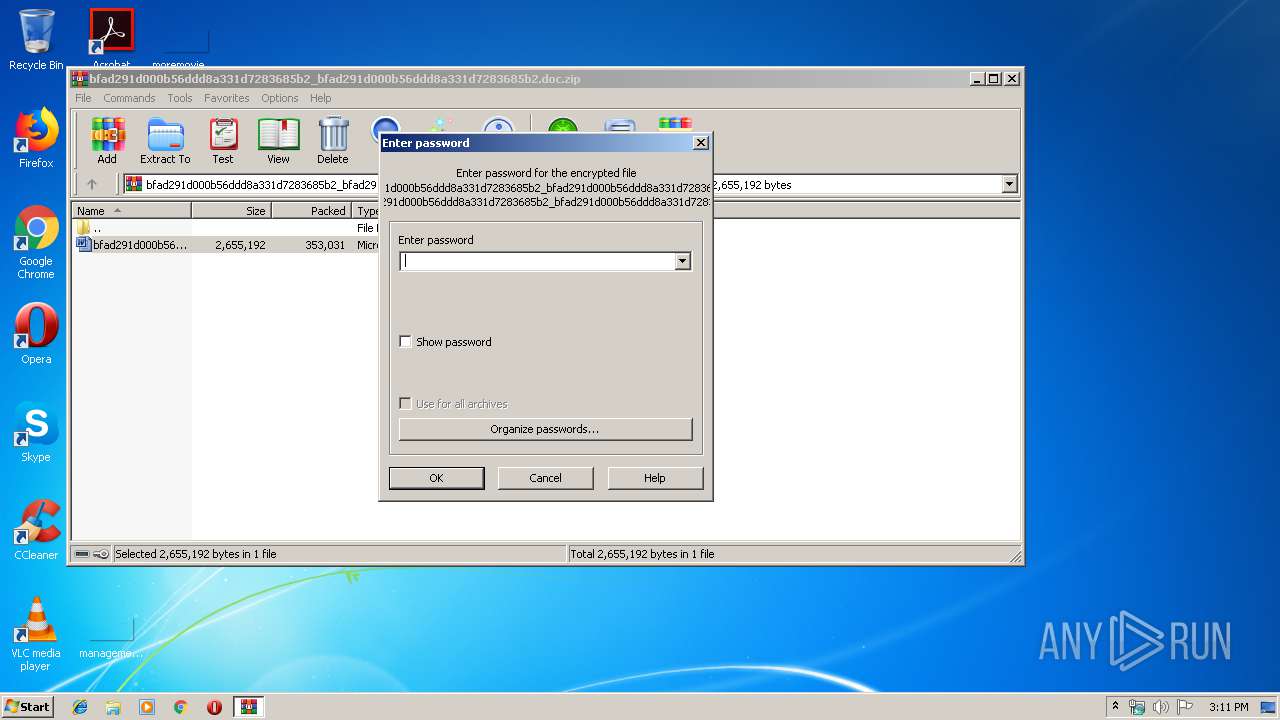
| (PID) Process: | (2420) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2420) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2420) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2420) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\bfad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc.zip | |||
| (PID) Process: | (2420) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2420) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2420) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2420) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2420) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2420) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
71
Text files
271
Unknown types
17
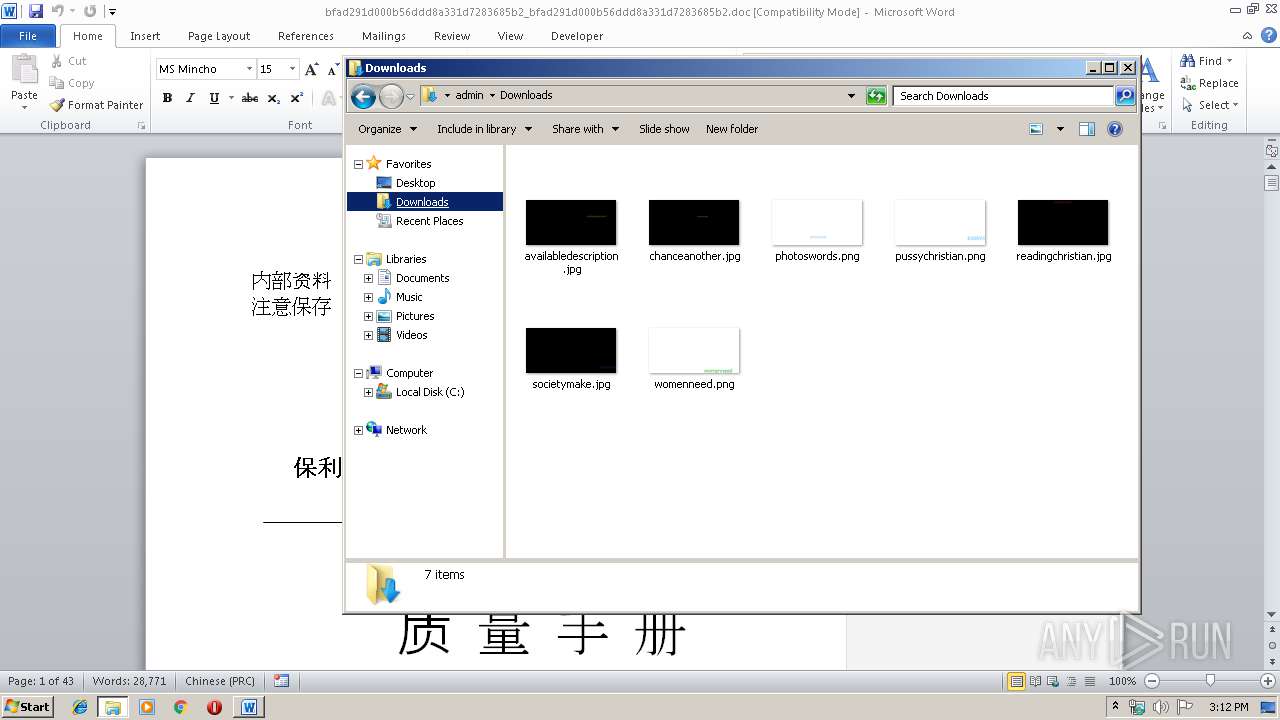
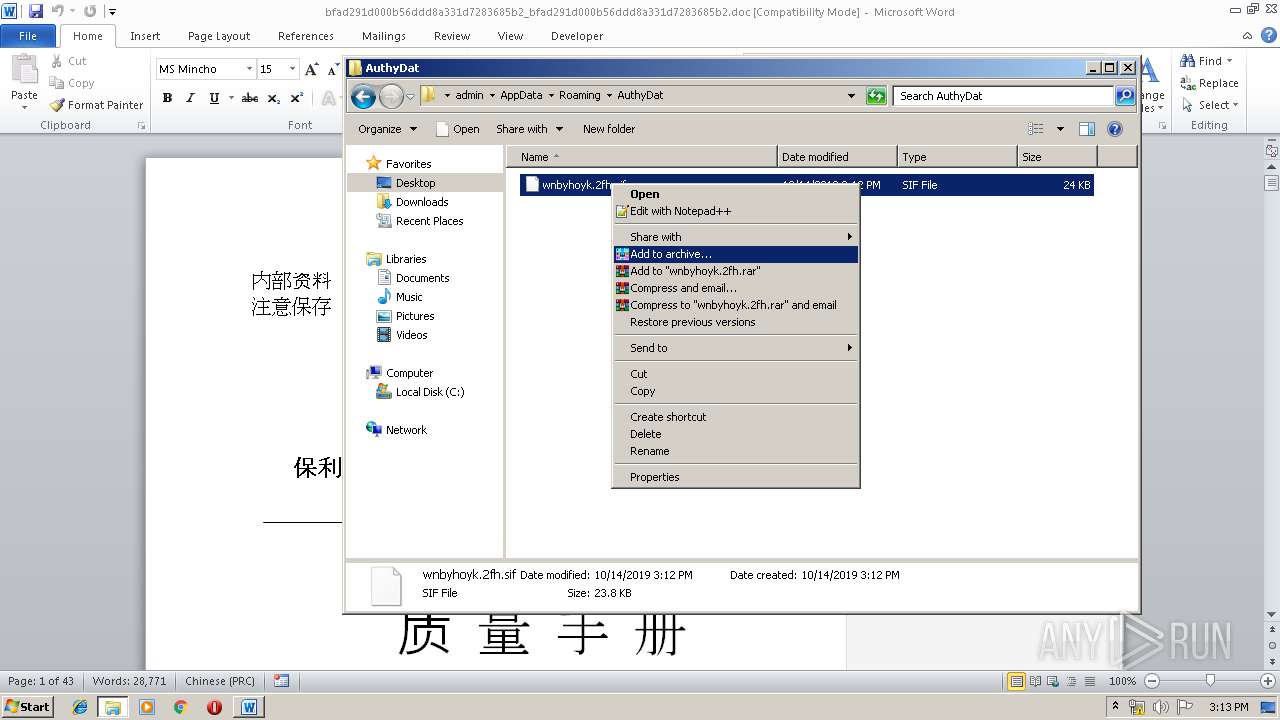
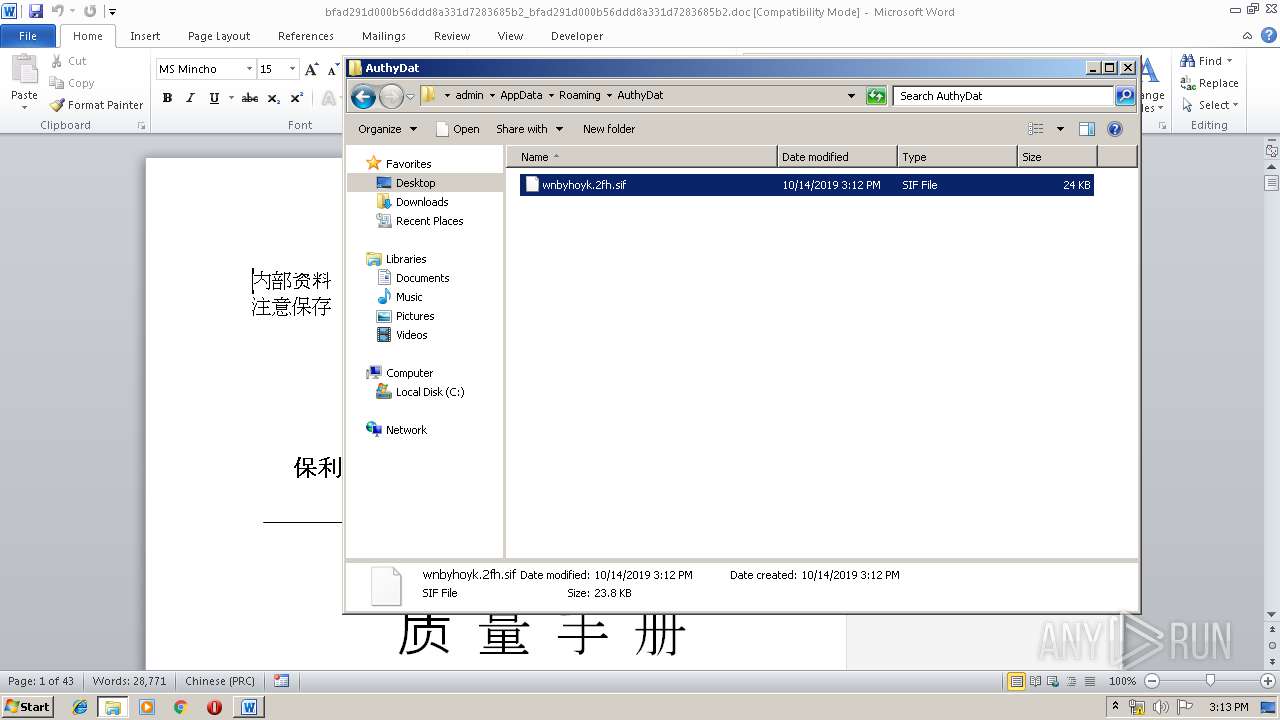
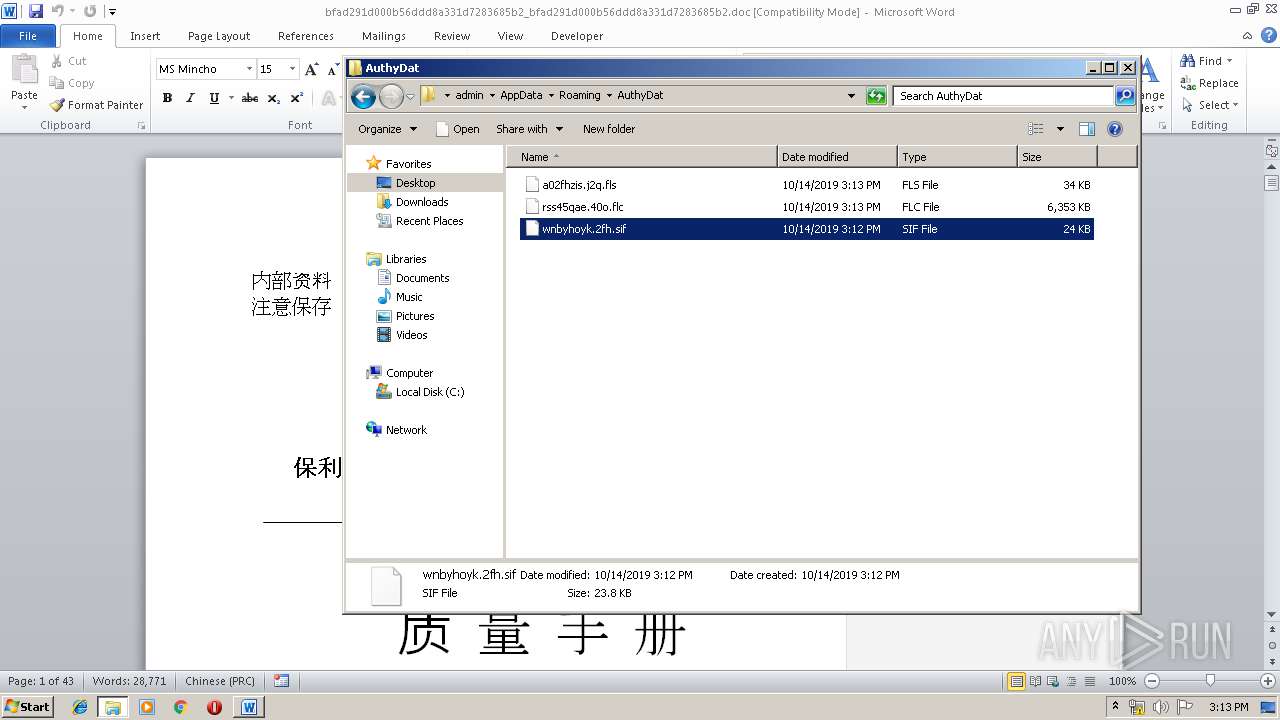
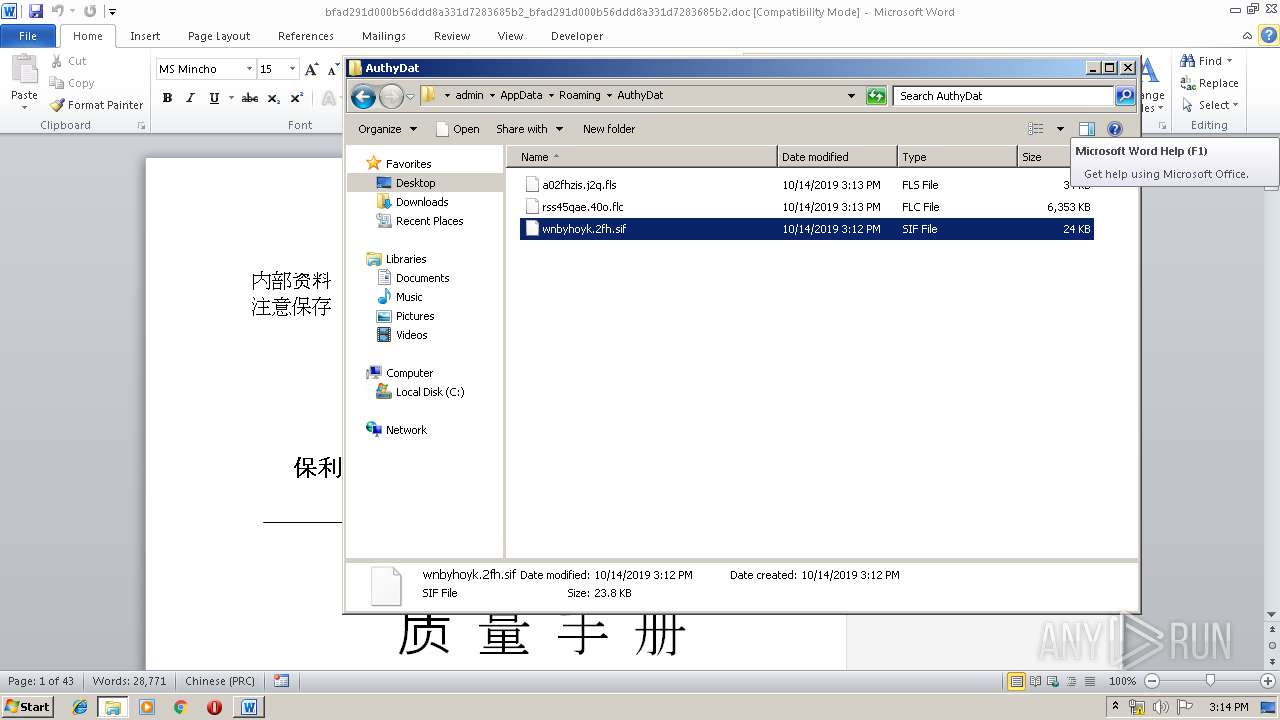
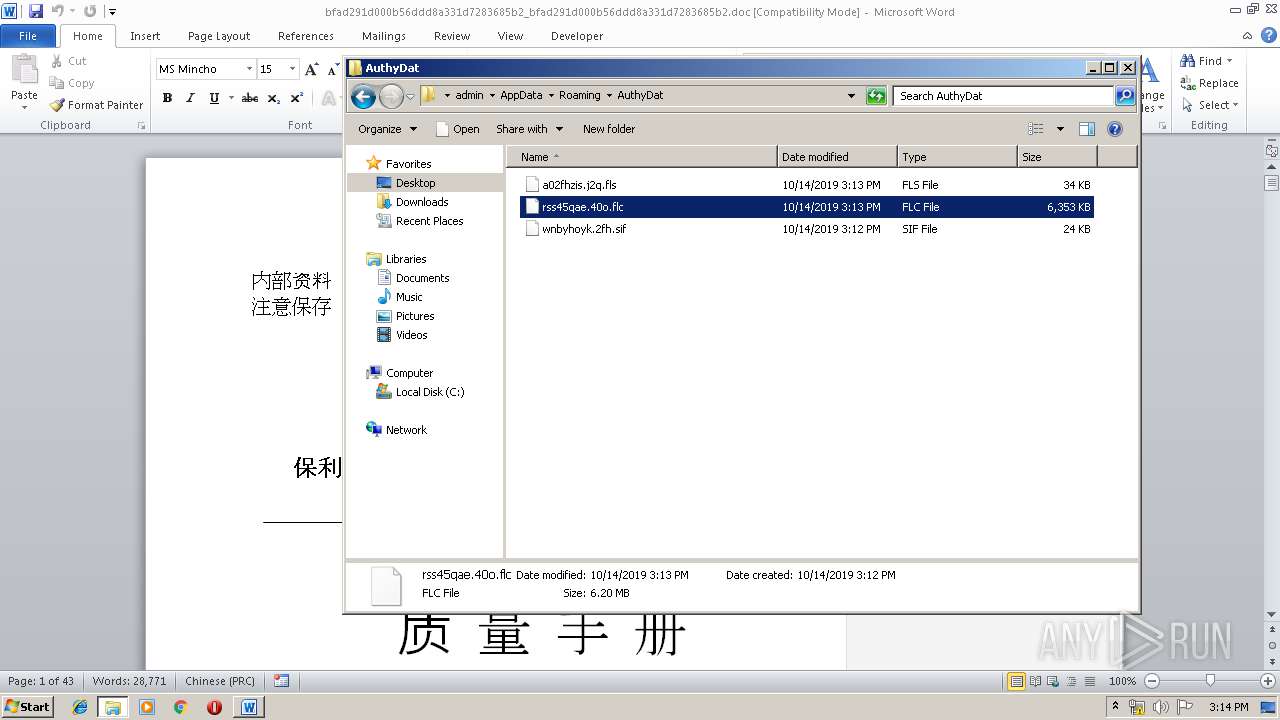
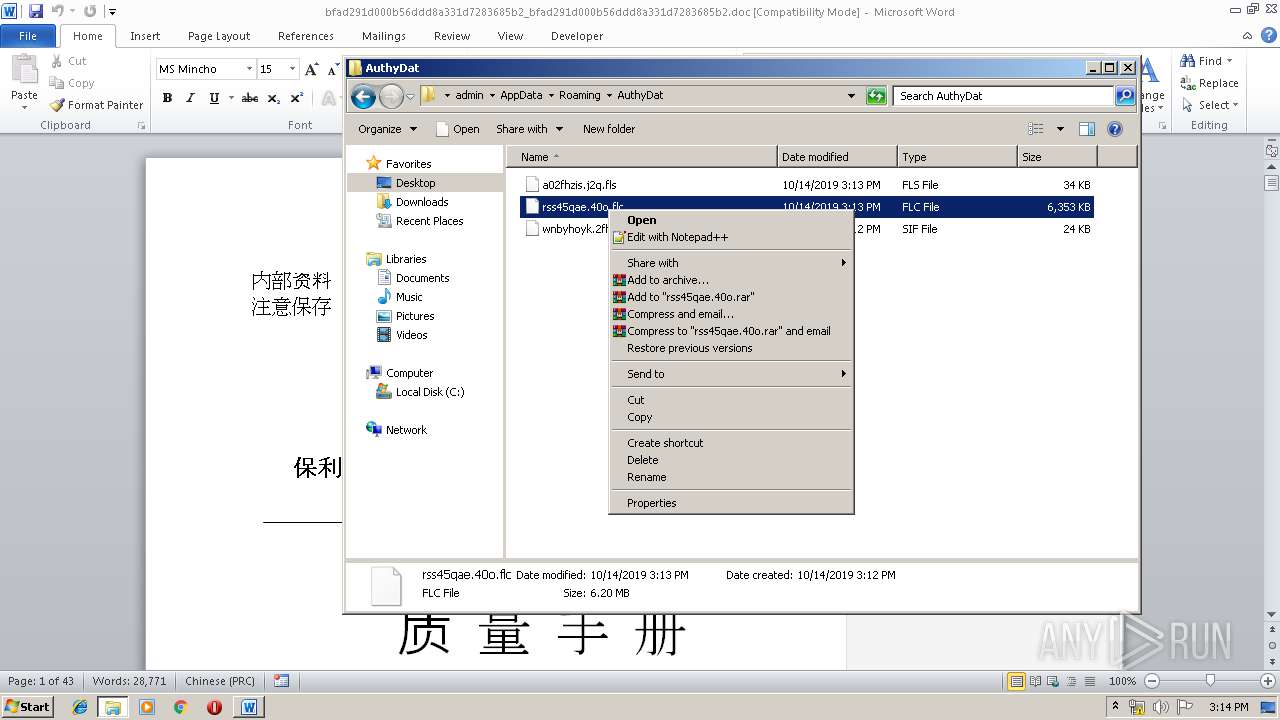
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFB14.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2416 | write.exe | C:\Users\admin\AppData\Local\Temp\tmp5BA2.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | write.exe | C:\Users\admin\AppData\Local\Temp\tmp6875.tmp | — | |
MD5:— | SHA256:— | |||
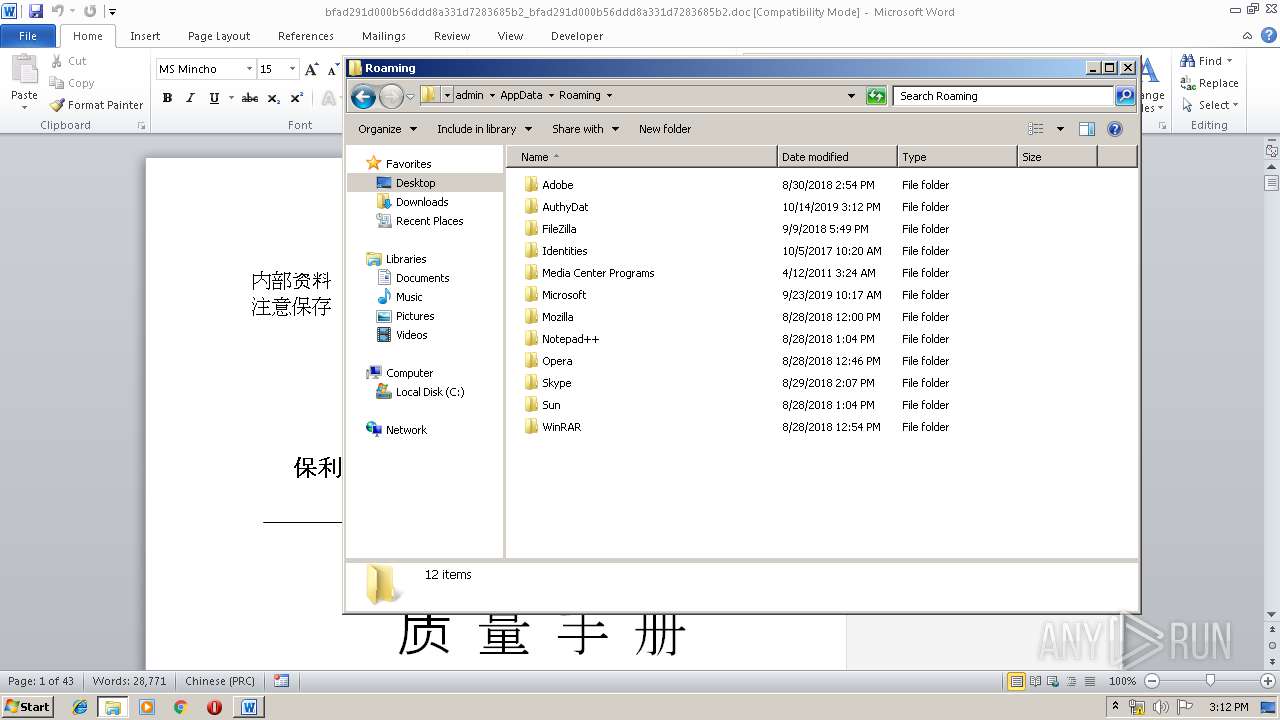
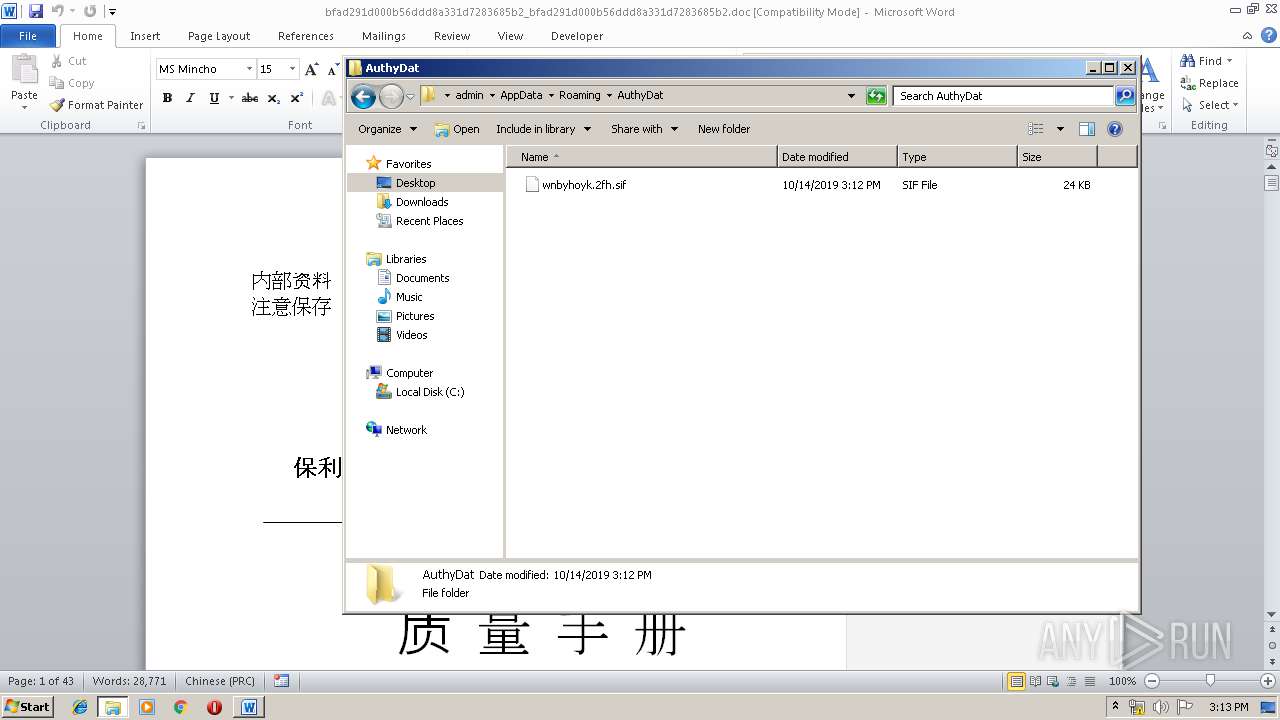
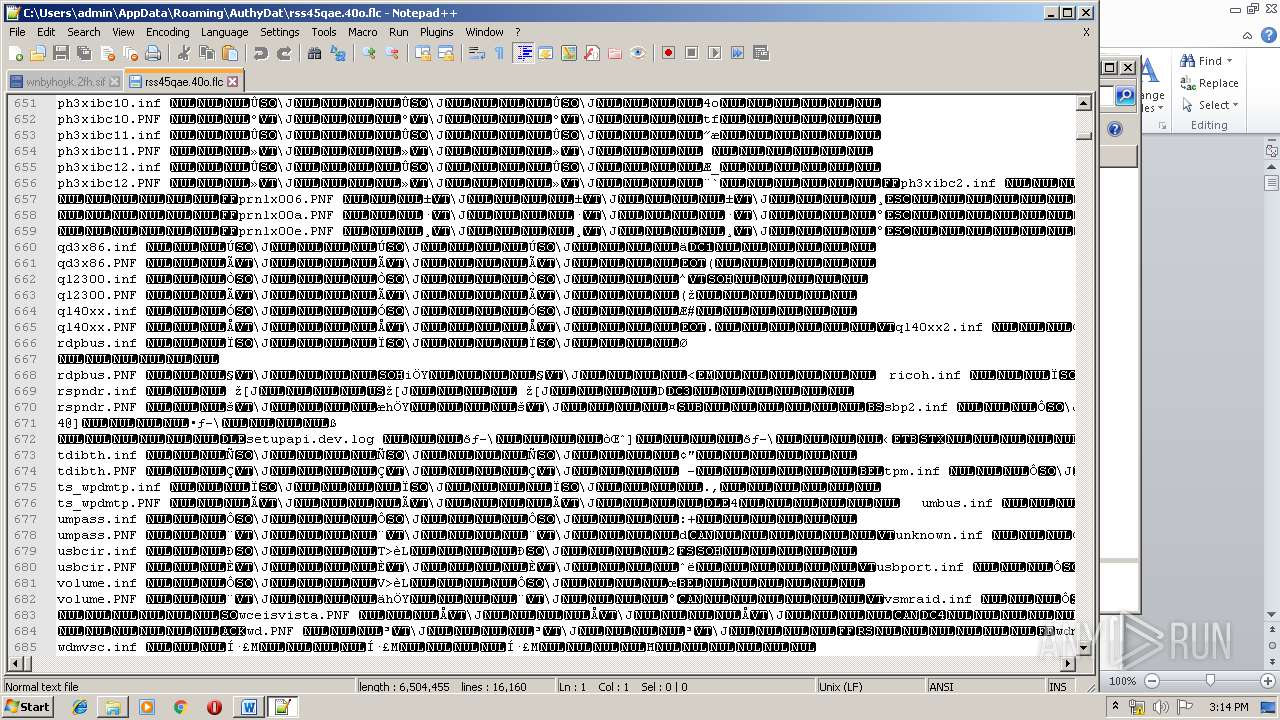
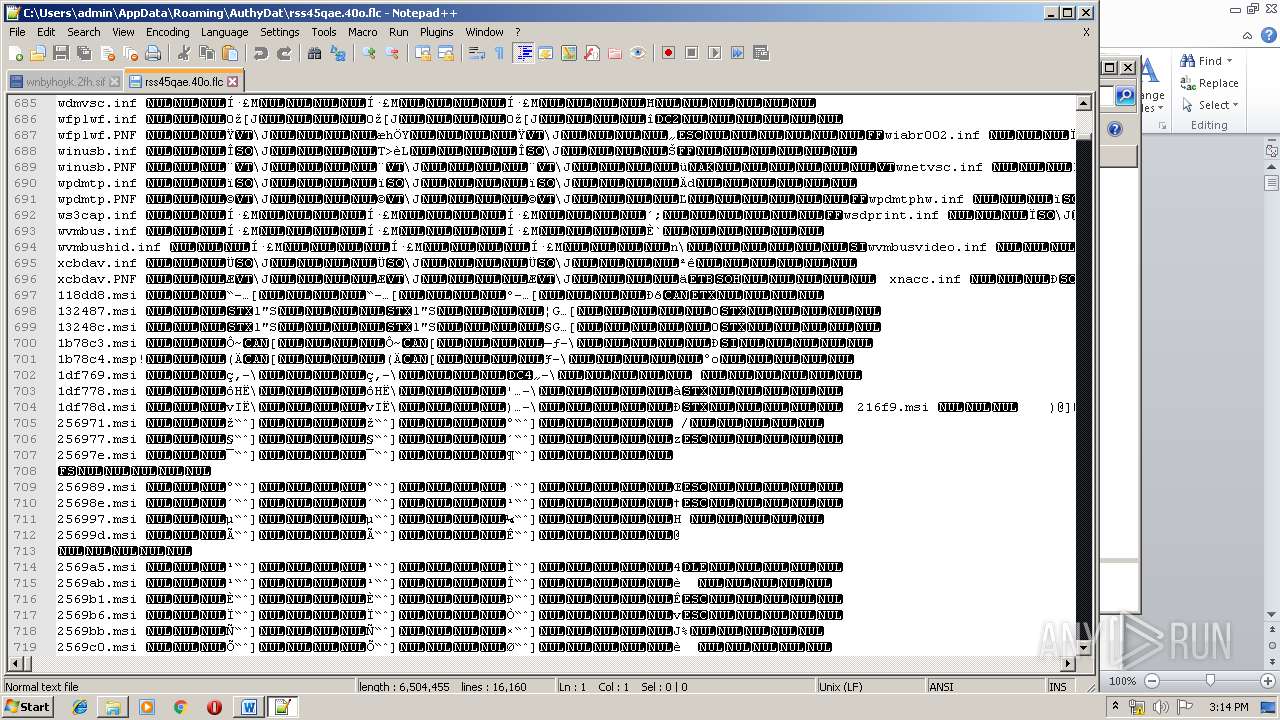
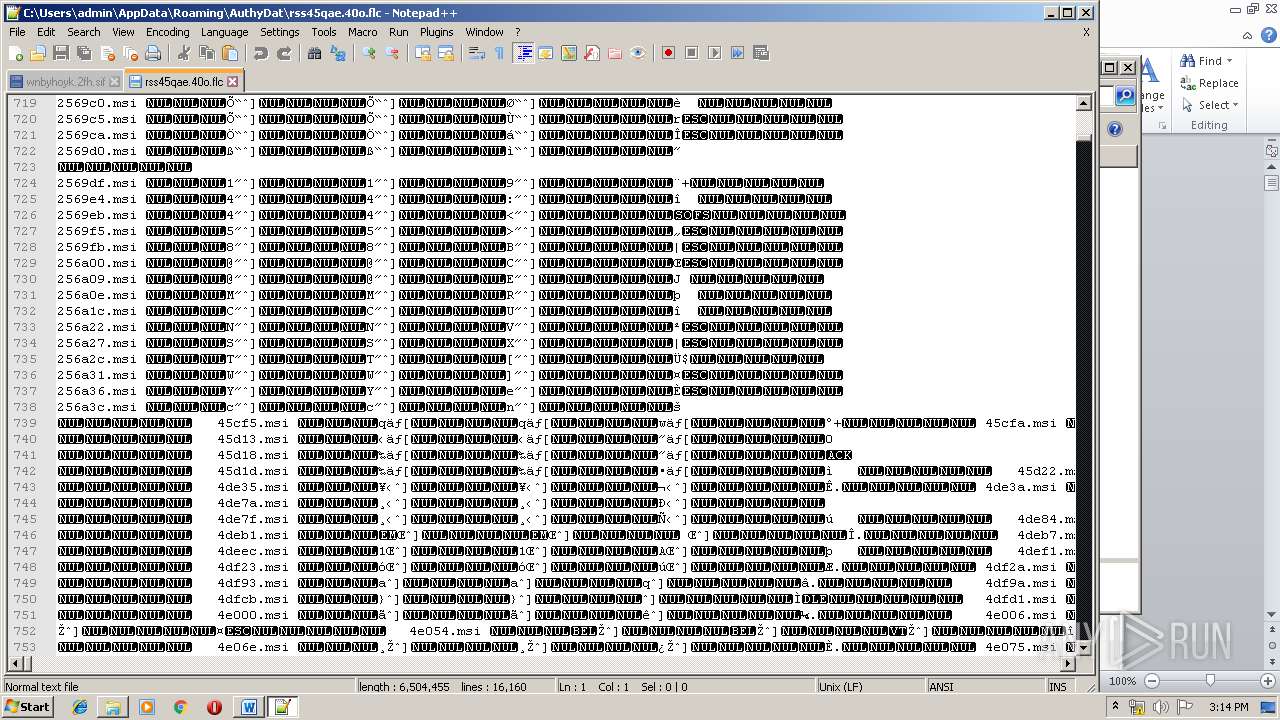
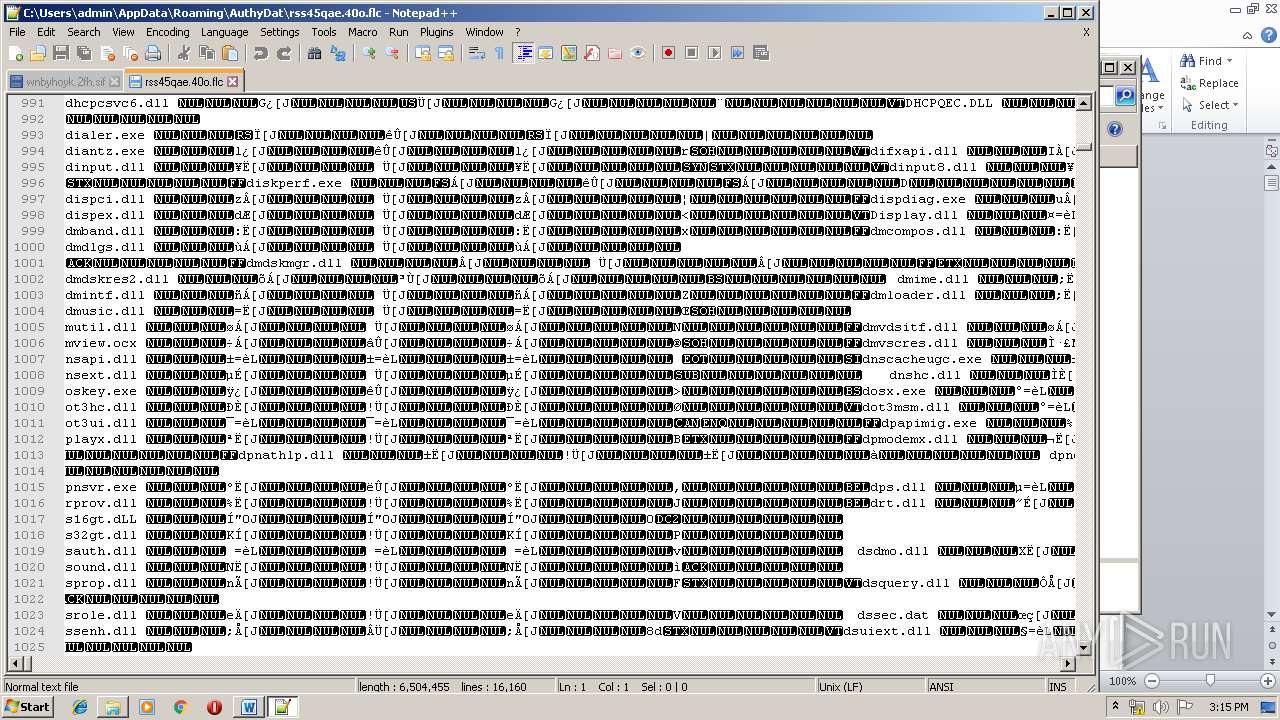
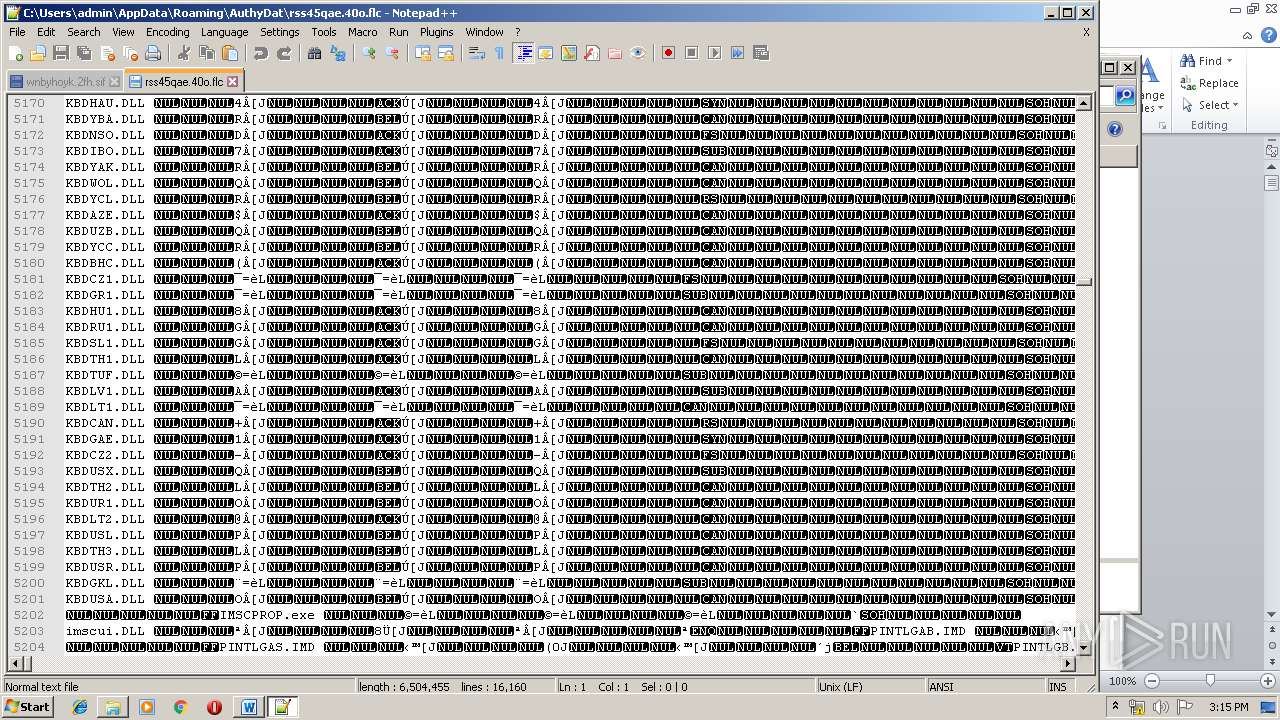
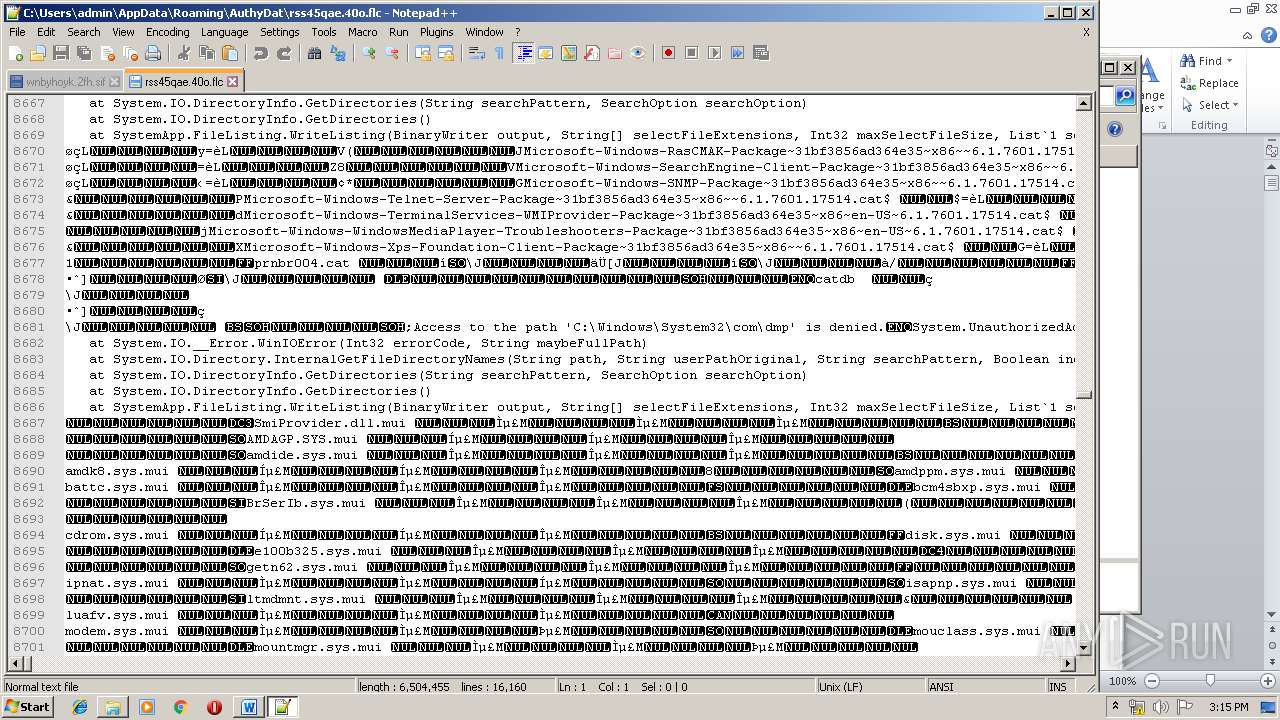
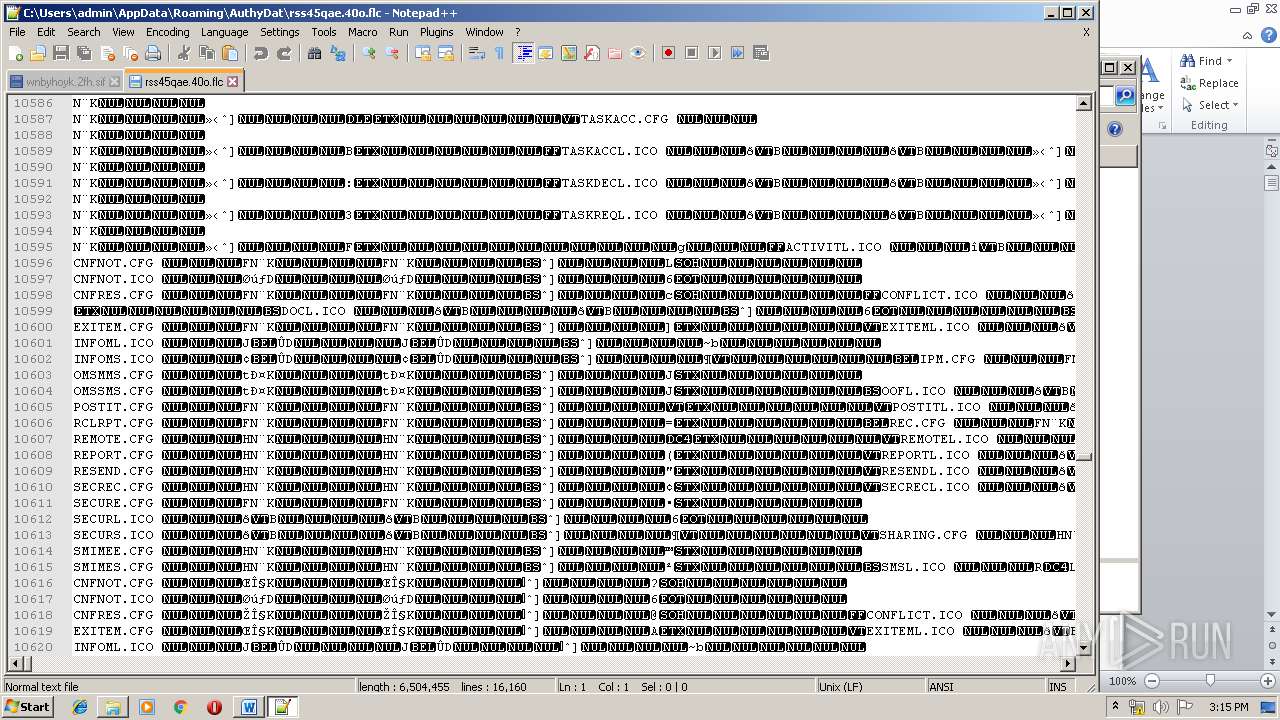
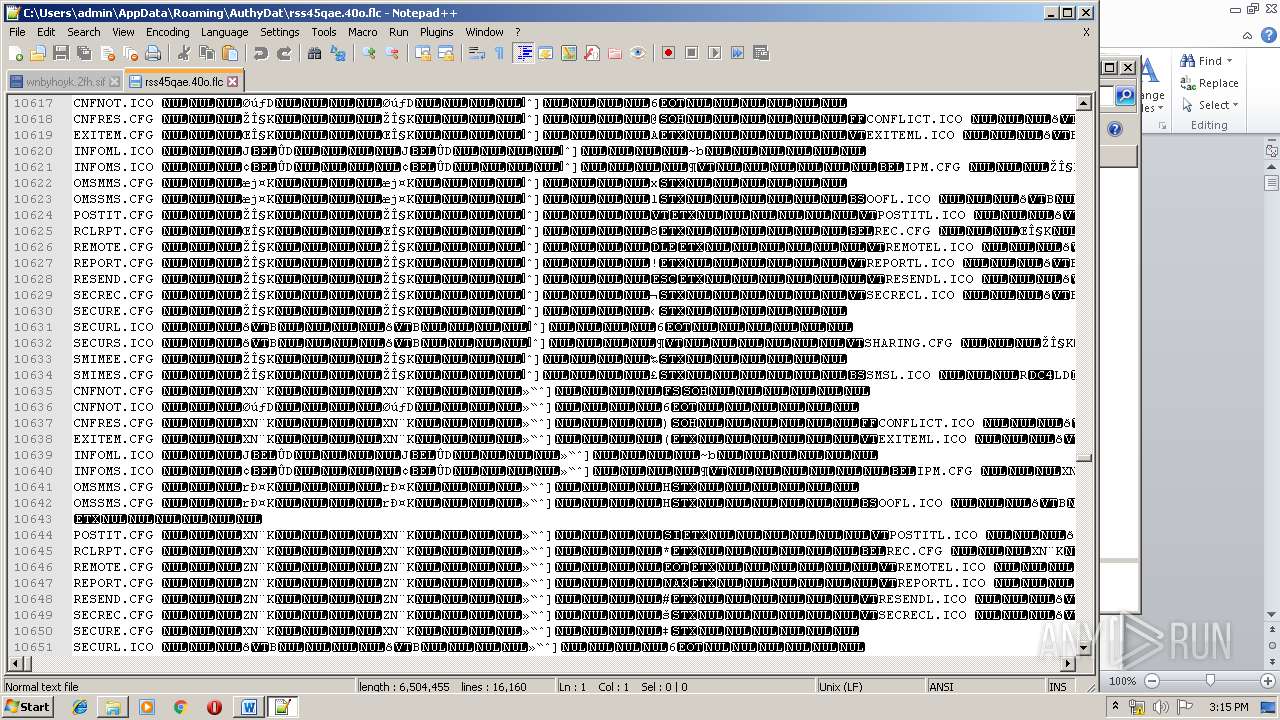
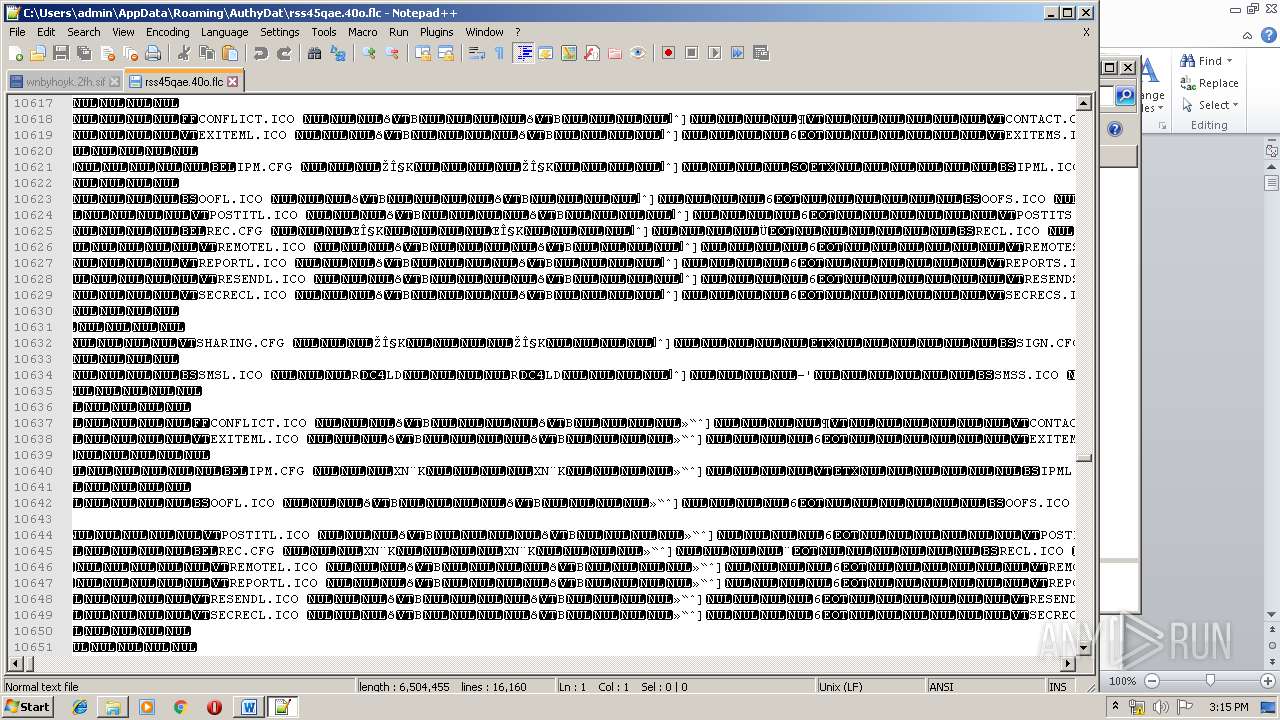
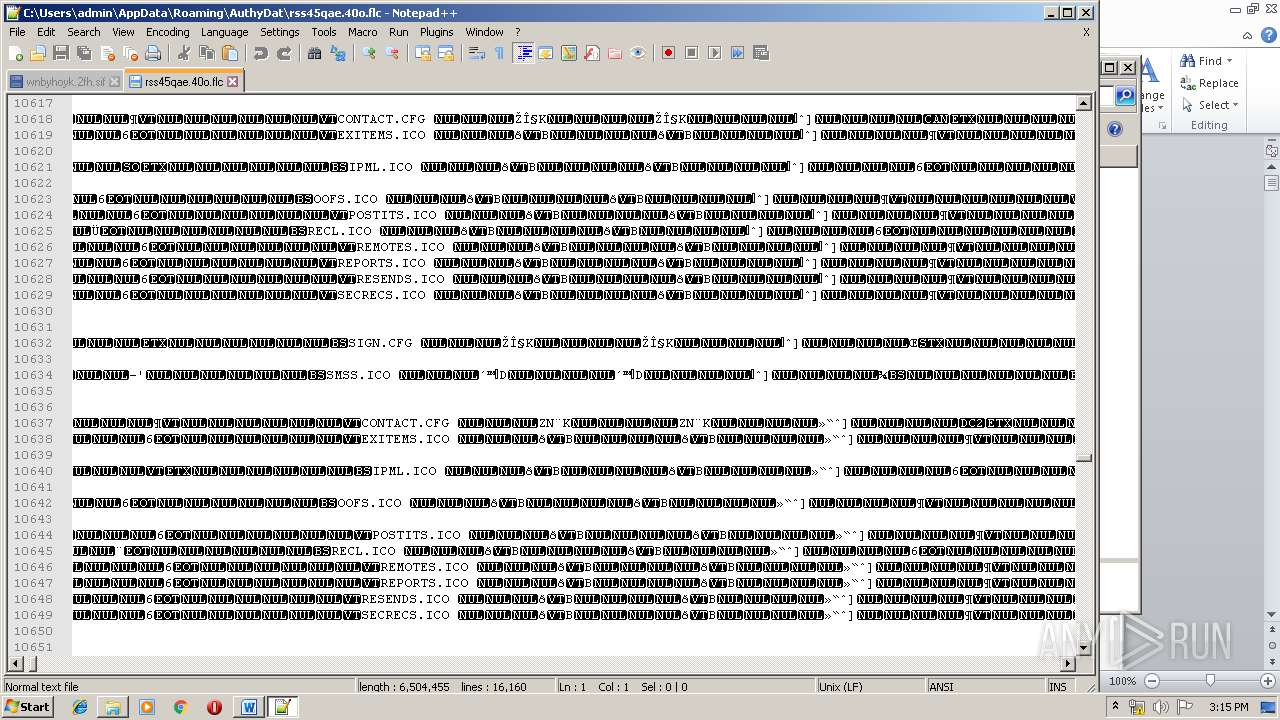
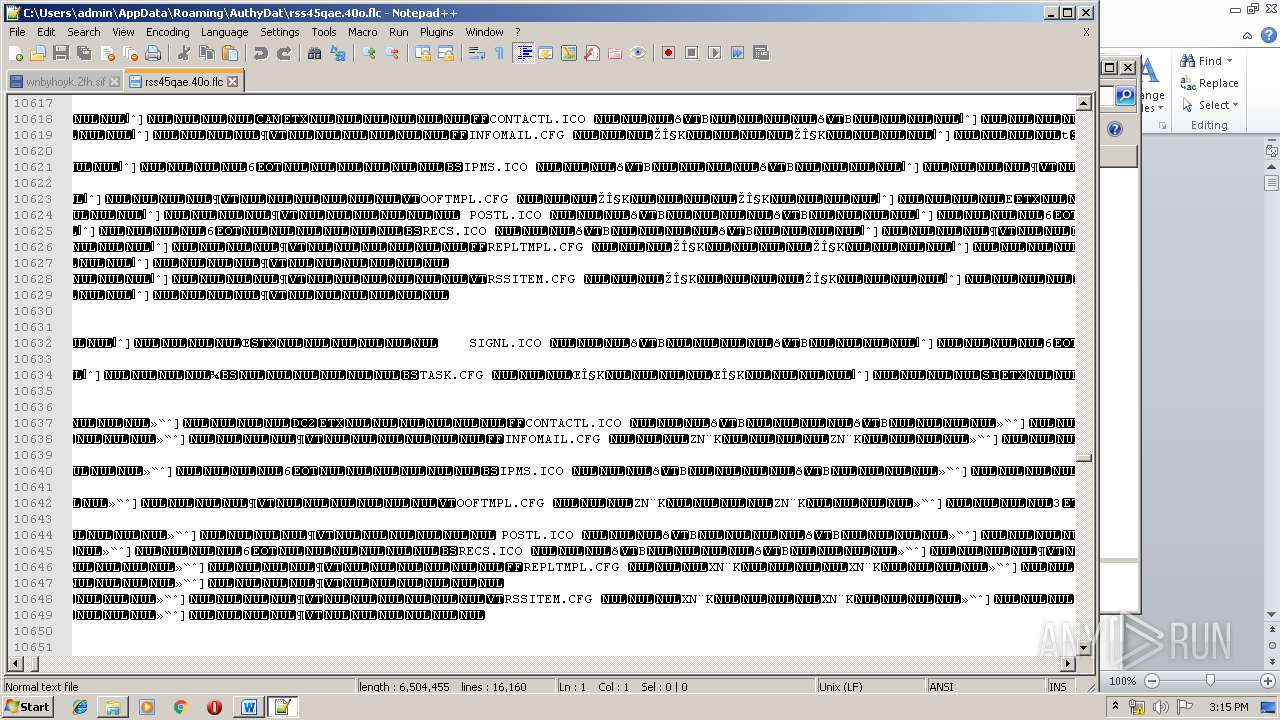
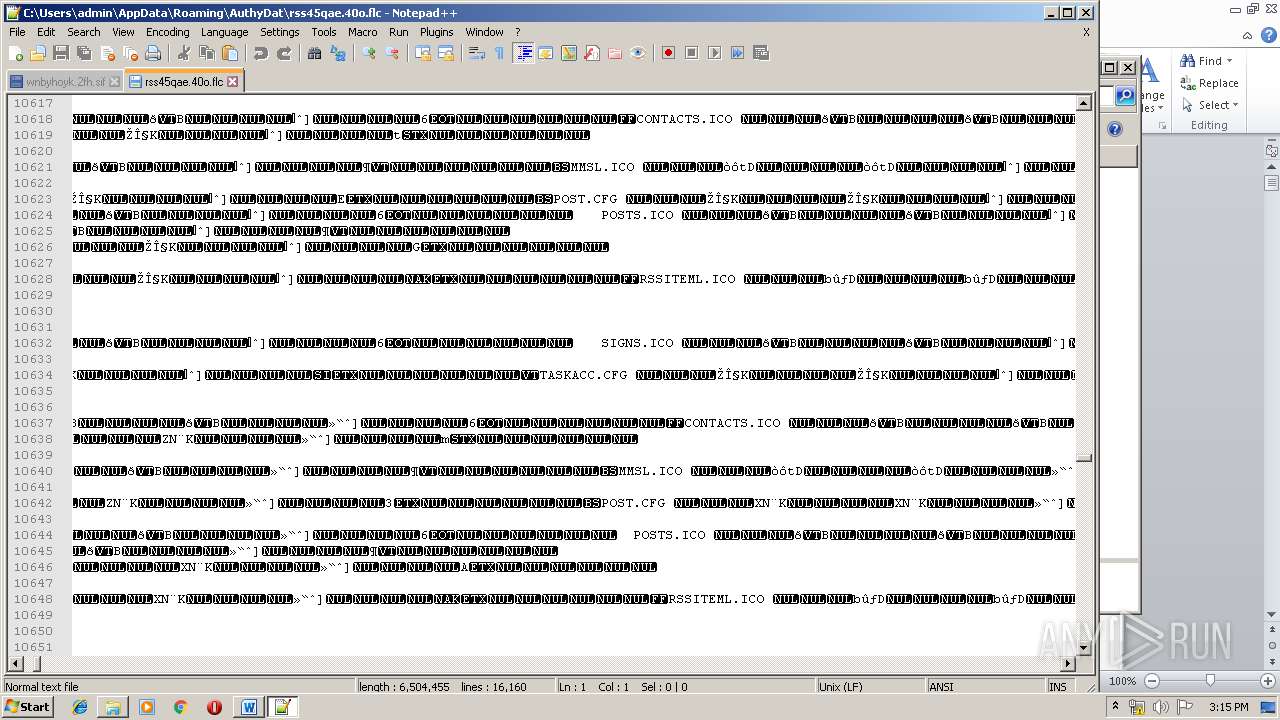
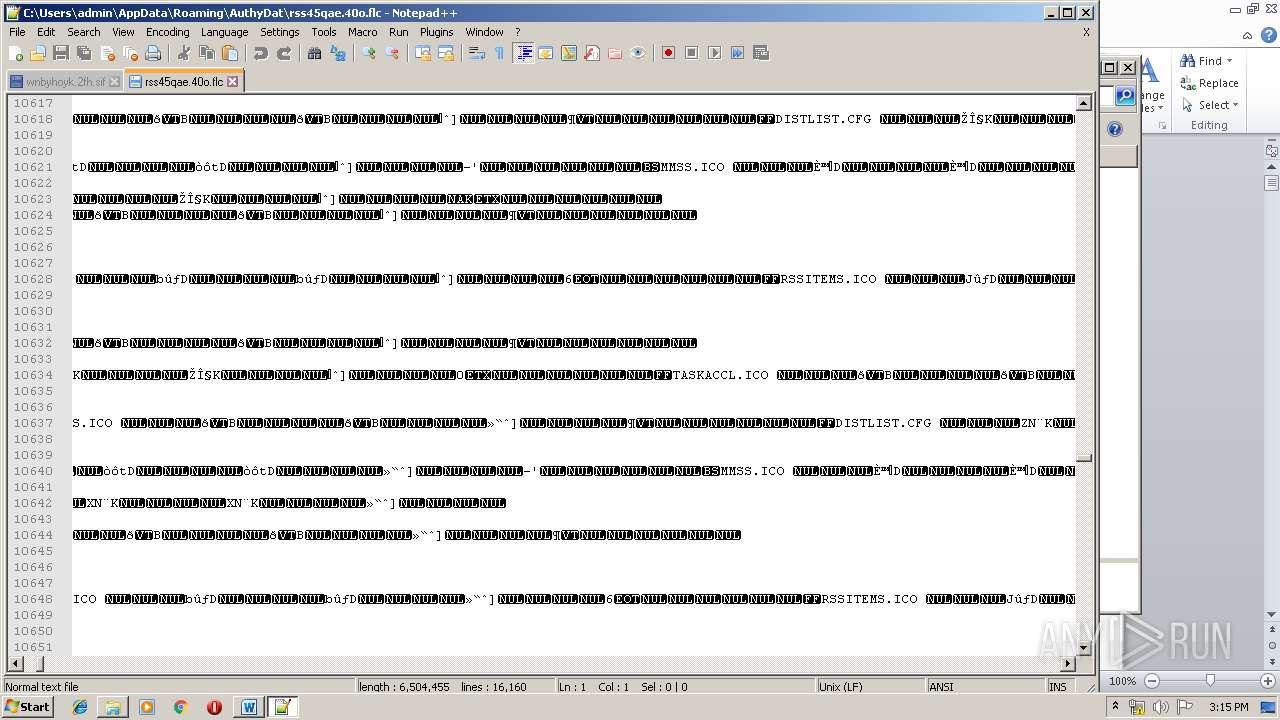
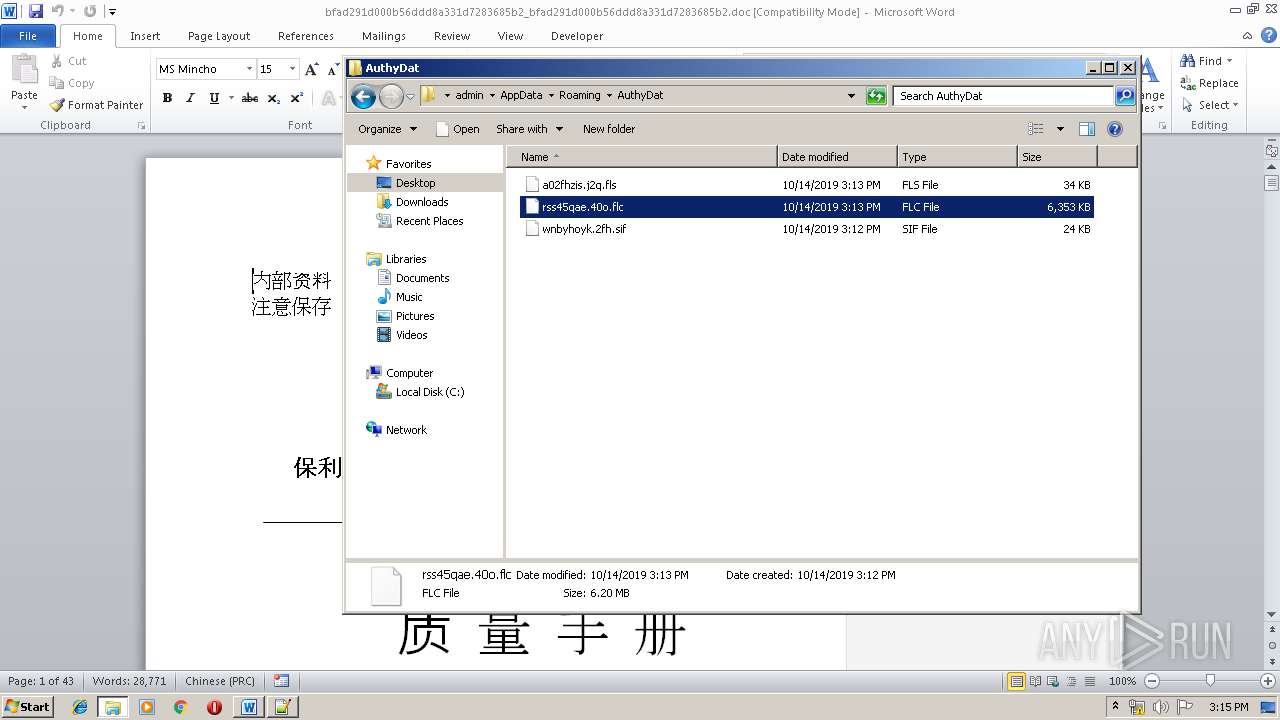
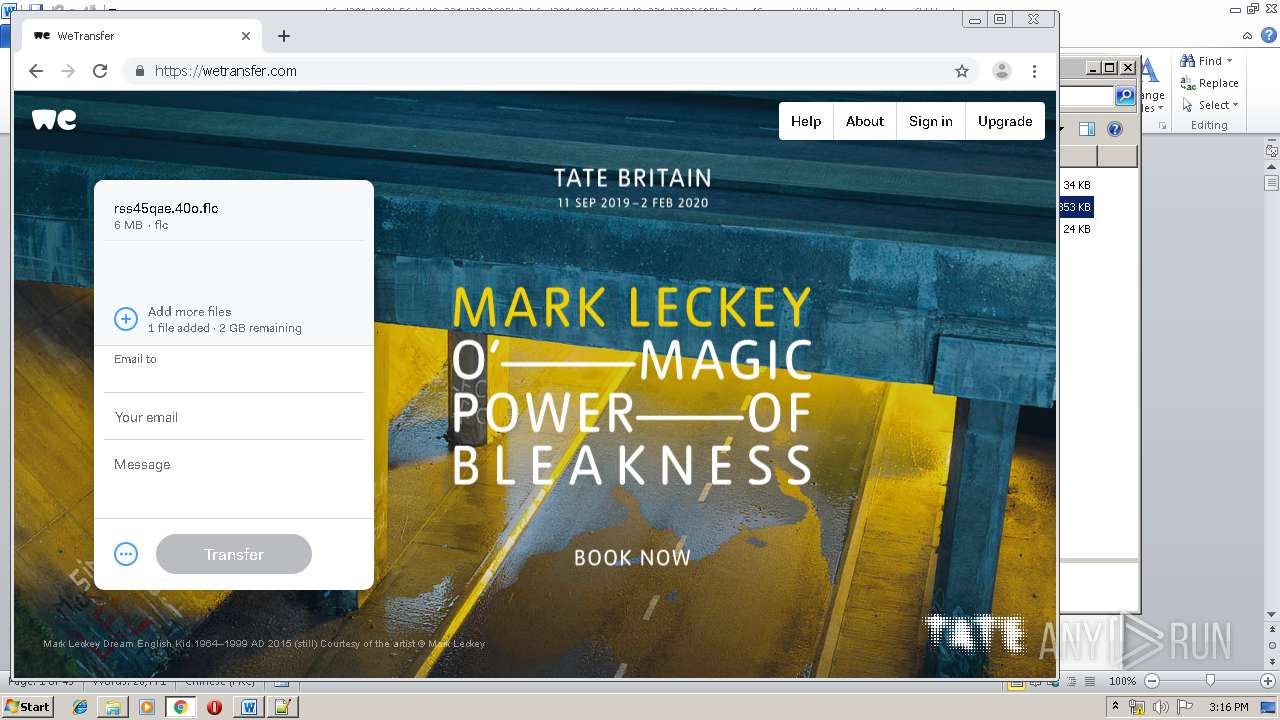
| 2416 | write.exe | C:\Users\admin\AppData\Roaming\AuthyDat\rss45qae.40o.flc | — | |
MD5:— | SHA256:— | |||
| 2416 | write.exe | C:\Users\admin\AppData\Local\Temp\tmpC7E6.tmp | — | |
MD5:— | SHA256:— | |||
| 2332 | EQNEDT32.EXE | C:\ProgramData\AuthyFiles\PROPSYS.dll | executable | |
MD5:— | SHA256:— | |||
| 2332 | EQNEDT32.EXE | C:\ProgramData\AuthyFiles\8UaHW4.tmp | binary | |
MD5:— | SHA256:— | |||
| 3300 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:— | SHA256:— | |||
| 2420 | WinRAR.exe | C:\Users\admin\Desktop\bfad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc | text | |
MD5:— | SHA256:— | |||
| 2416 | write.exe | C:\ProgramData\AuthyFiles\Authy | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
86
DNS requests
66
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.72.151:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgMpeSsuddjFyk25ZqSQ83ahjg%3D%3D | unknown | der | 527 b | whitelisted |
— | — | GET | 200 | 95.101.72.176:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
4068 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
4068 | chrome.exe | GET | 200 | 74.125.4.169:80 | http://r4---sn-aigzrne7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.92.25.20&mm=28&mn=sn-aigzrne7&ms=nvh&mt=1571062399&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
4068 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
4068 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
4068 | chrome.exe | GET | 200 | 52.222.149.36:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
4068 | chrome.exe | GET | 200 | 74.125.4.216:80 | http://r2---sn-aigzrney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.92.25.20&mm=28&mn=sn-aigzrney&ms=nvh&mt=1571062399&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2416 | write.exe | 178.62.190.33:443 | trans-can.net | Digital Ocean, Inc. | NL | unknown |
4068 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2296 | gup.exe | 2.57.89.199:443 | notepad-plus-plus.org | — | — | suspicious |
4068 | chrome.exe | 216.58.207.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
4068 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4068 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
4068 | chrome.exe | 172.217.16.142:443 | ogs.google.com | Google Inc. | US | whitelisted |
4068 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
4068 | chrome.exe | 172.217.22.99:443 | www.google.co.uk | Google Inc. | US | whitelisted |
4068 | chrome.exe | 52.222.149.113:80 | x.ss2.us | Amazon.com, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
trans-can.net |
| malicious |
notepad-plus-plus.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|