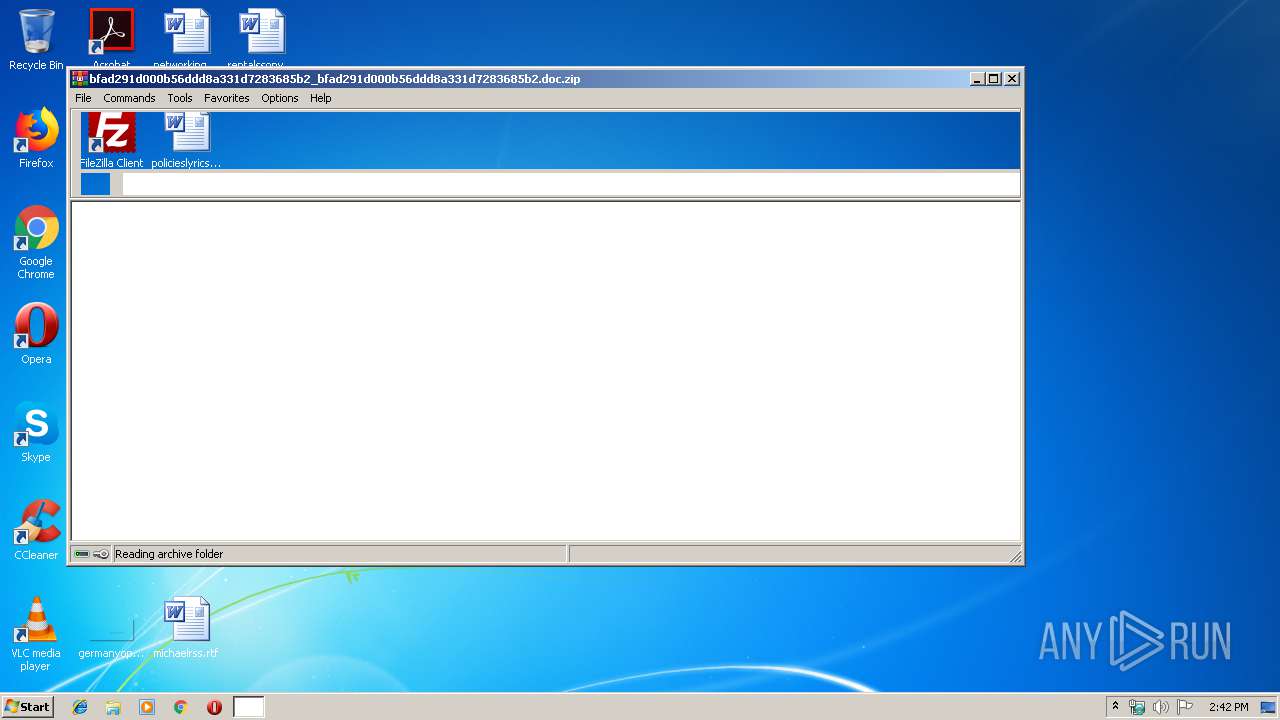
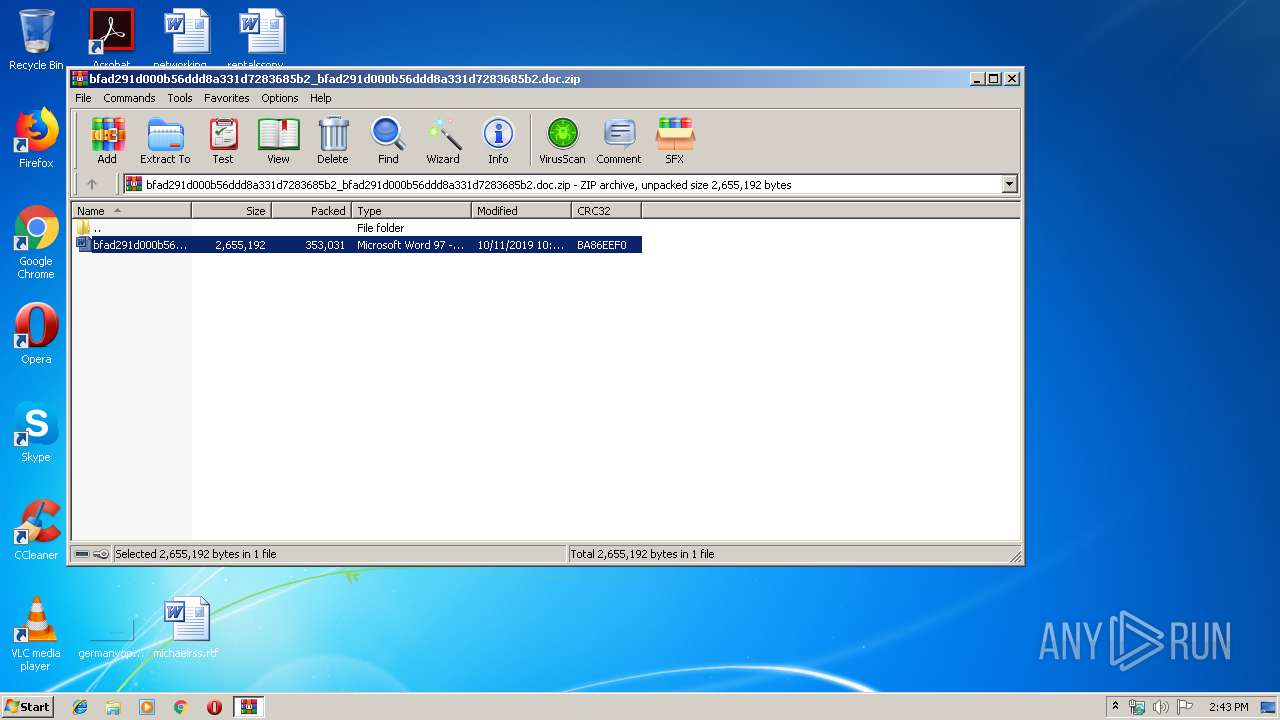
| File name: | bfad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc.zip |
| Full analysis: | https://app.any.run/tasks/20a6fb3b-8be9-481d-9953-0e0dc1ce5dd6 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 13:42:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1E815A32A3FD0DB3EC6022601779672D |
| SHA1: | CFF1E5F39CA619D41536B16CFAD0A8F37BC282C5 |
| SHA256: | 44055D730B636EEE349C8558C795D154AADBD502B63FDFFDE7105A0279931312 |
| SSDEEP: | 6144:/QfCHHgIwbApfb9sBZ/yoq2+2SUT4Ps0NGodaRIPrkyxkRtQJHOg0etF42f+:opwSHyoqR9XDGoairkyxkDQJOg0e7422 |
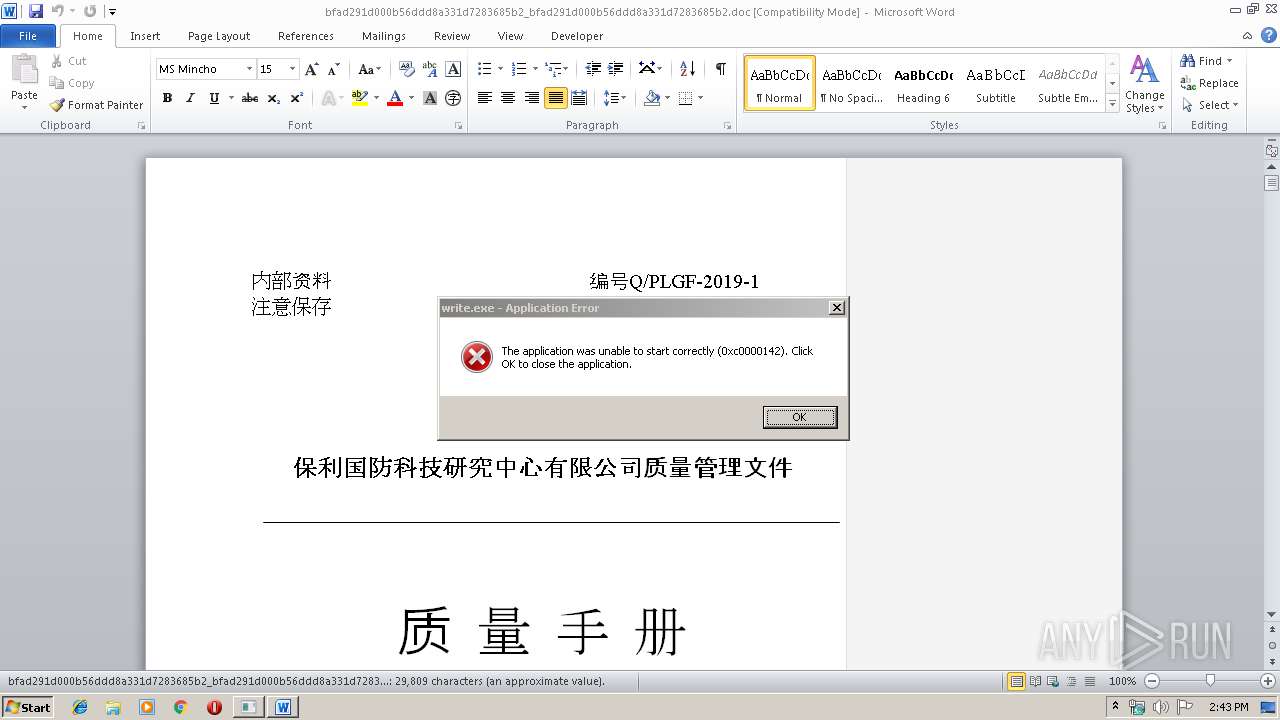
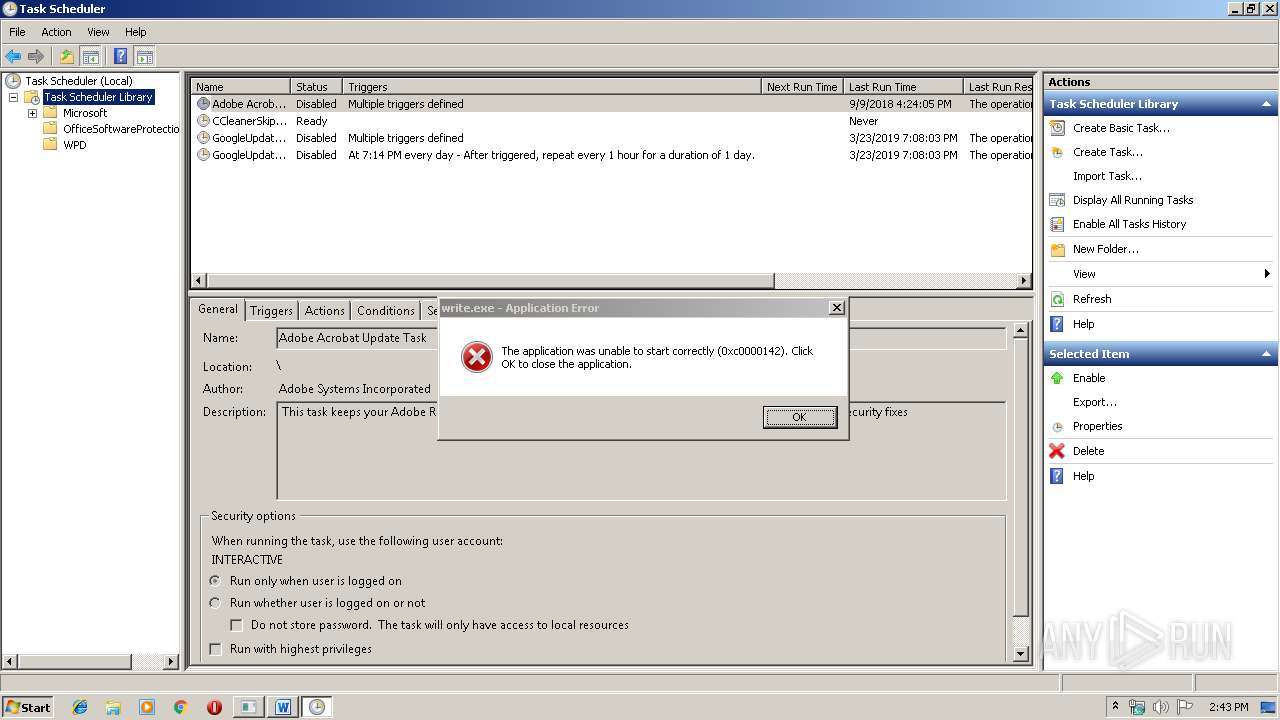
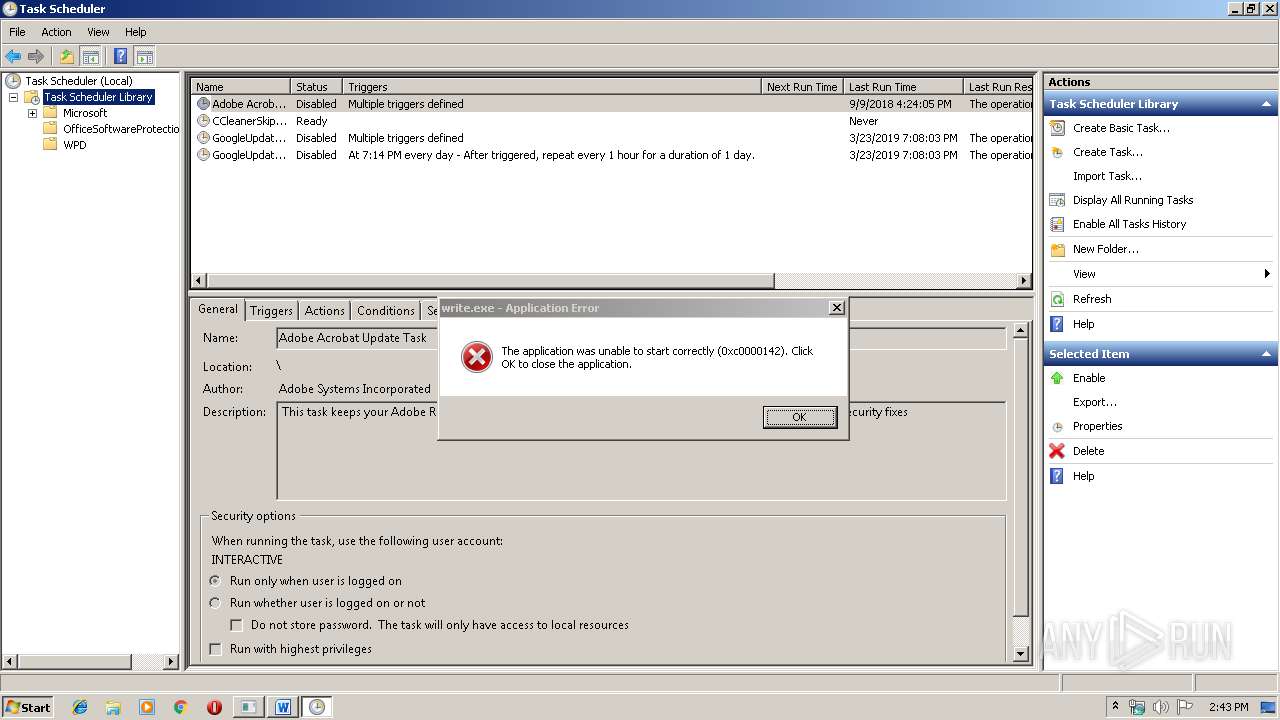
MALICIOUS
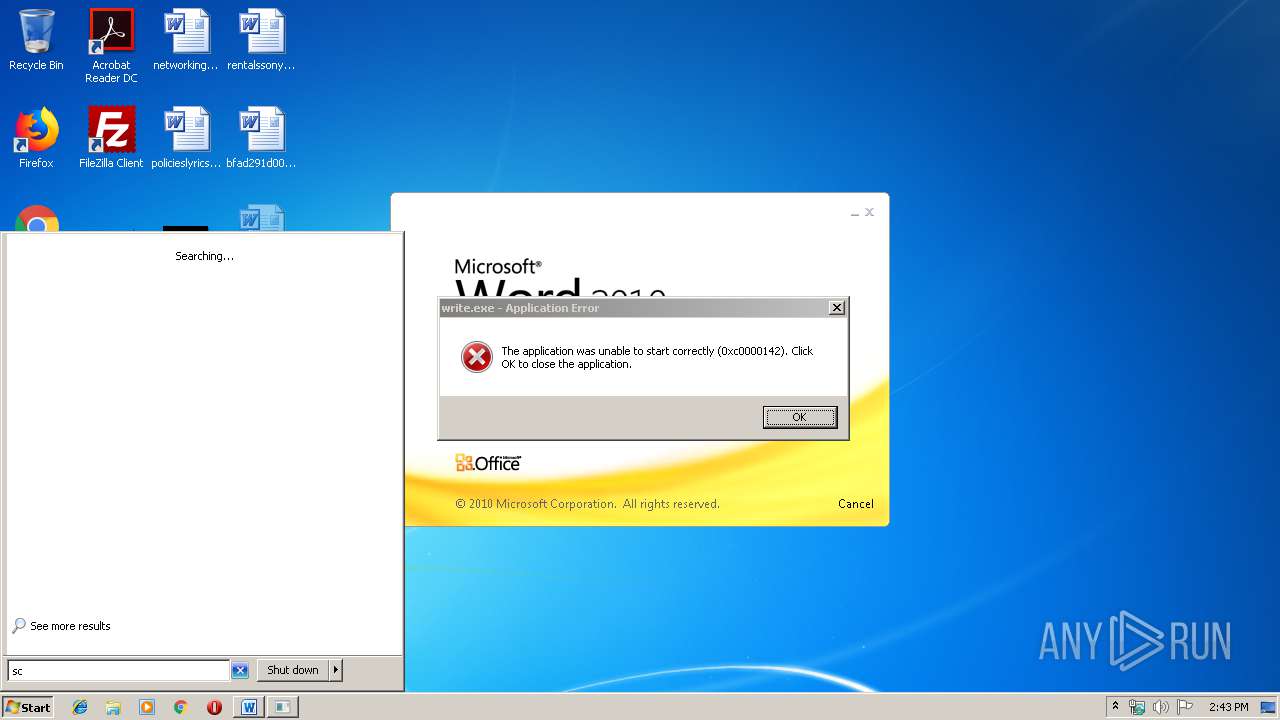
Application was dropped or rewritten from another process
- write.exe (PID: 3944)
- write.exe (PID: 3416)
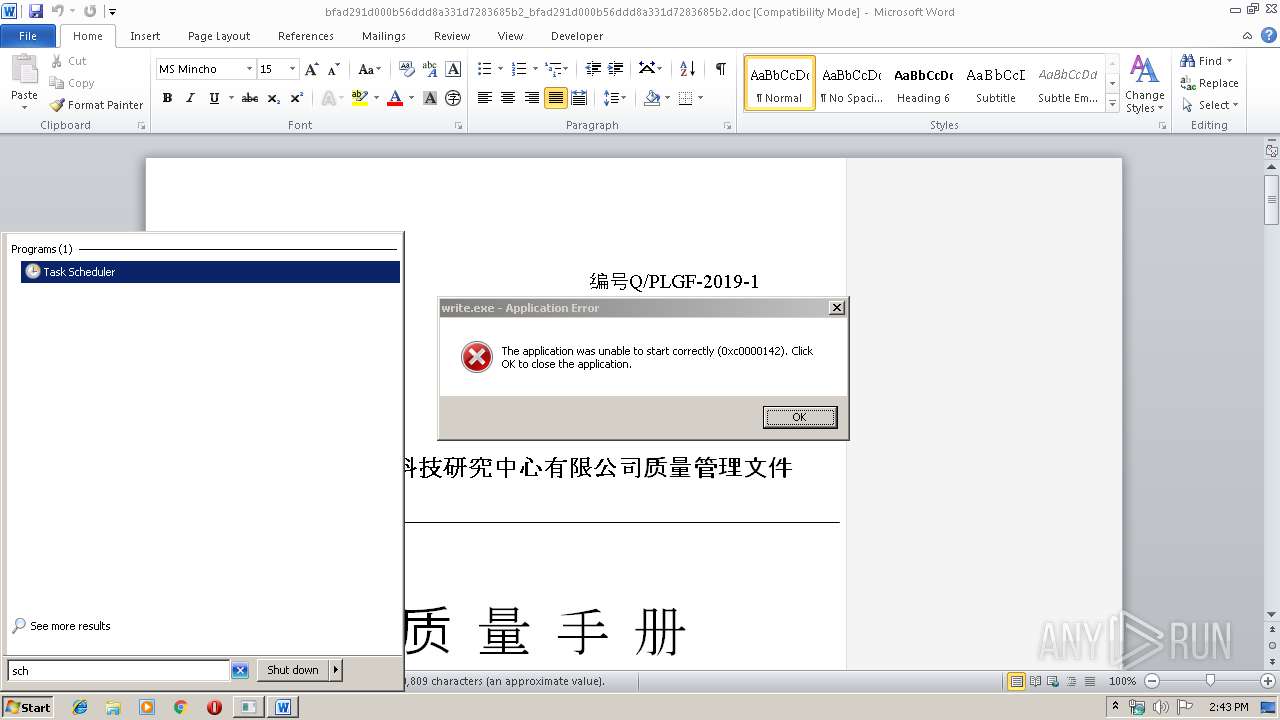
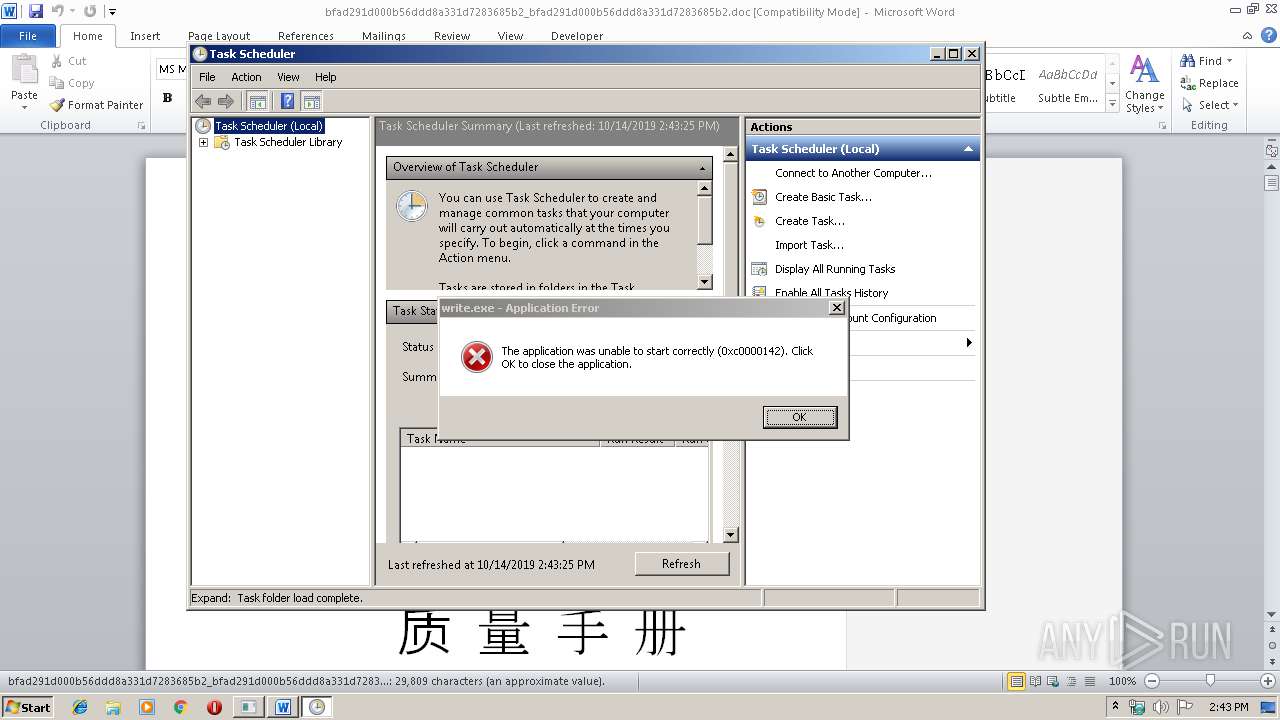
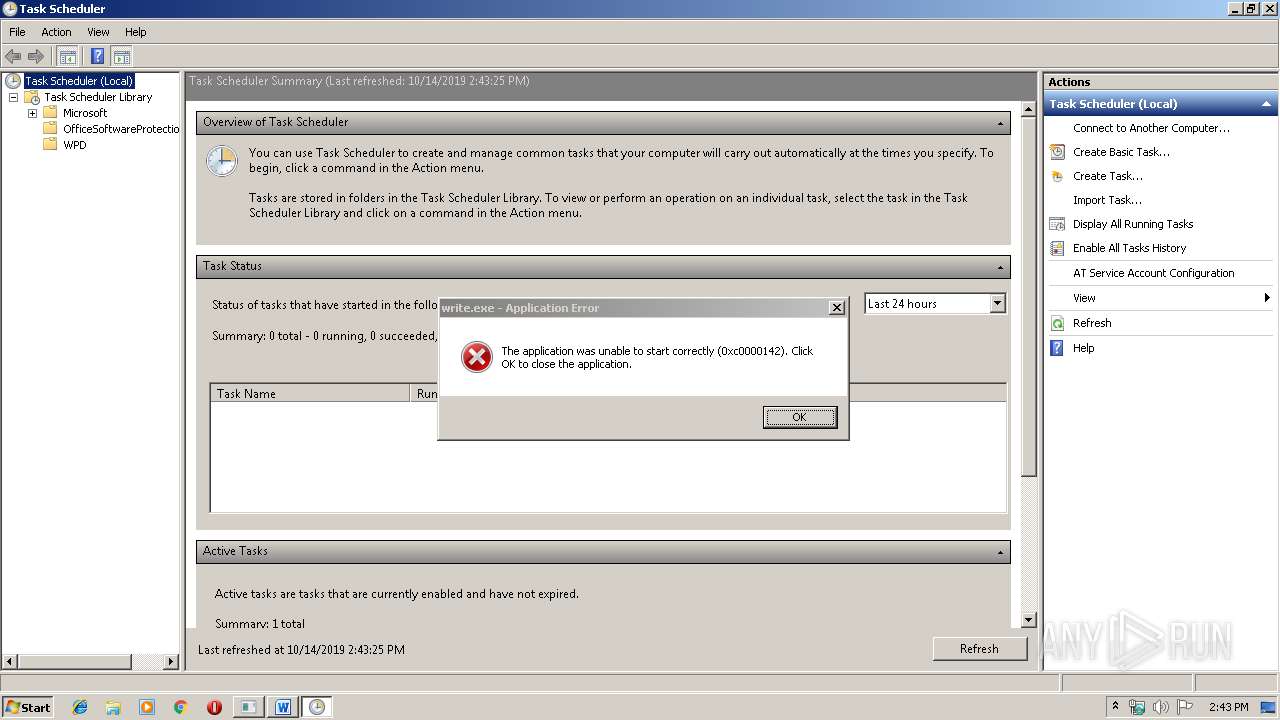
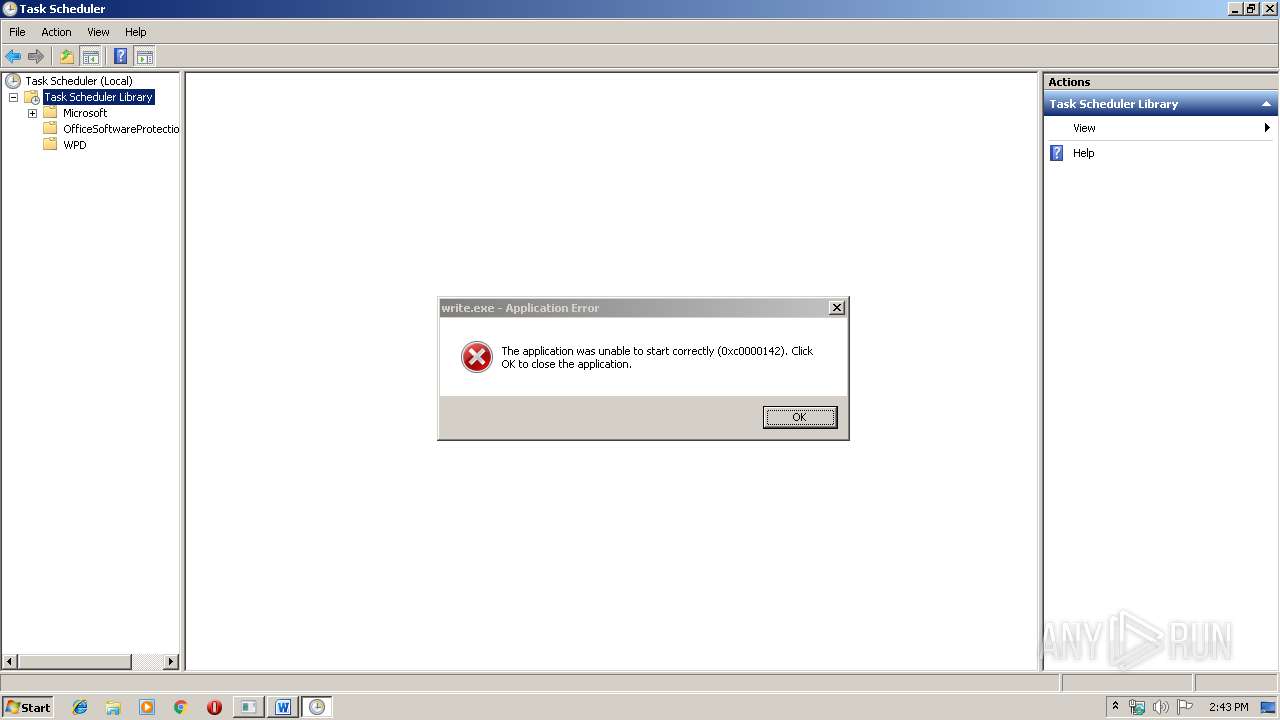
Loads the Task Scheduler COM API
- mmc.exe (PID: 3856)
Changes the autorun value in the registry
- EQNEDT32.EXE (PID: 2612)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2612)
Loads dropped or rewritten executable
- write.exe (PID: 3416)
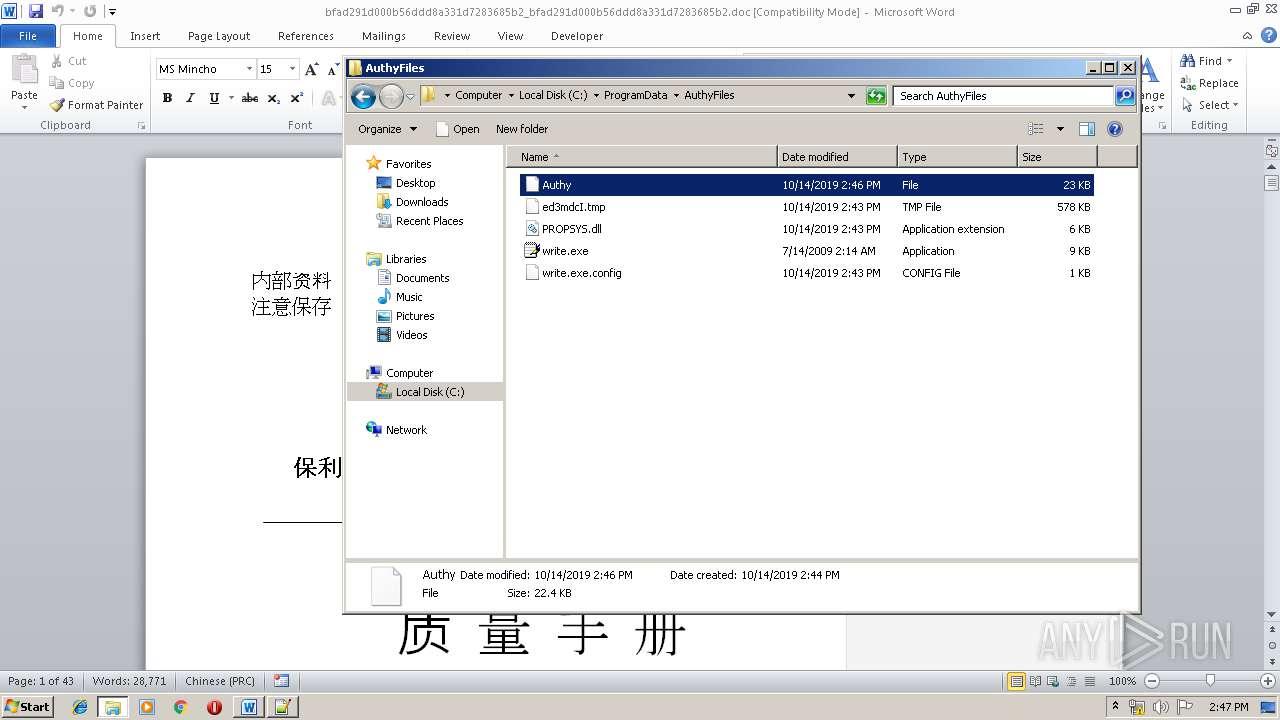
Actions looks like stealing of personal data
- write.exe (PID: 3416)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 2612)
Reads internet explorer settings
- EQNEDT32.EXE (PID: 2612)
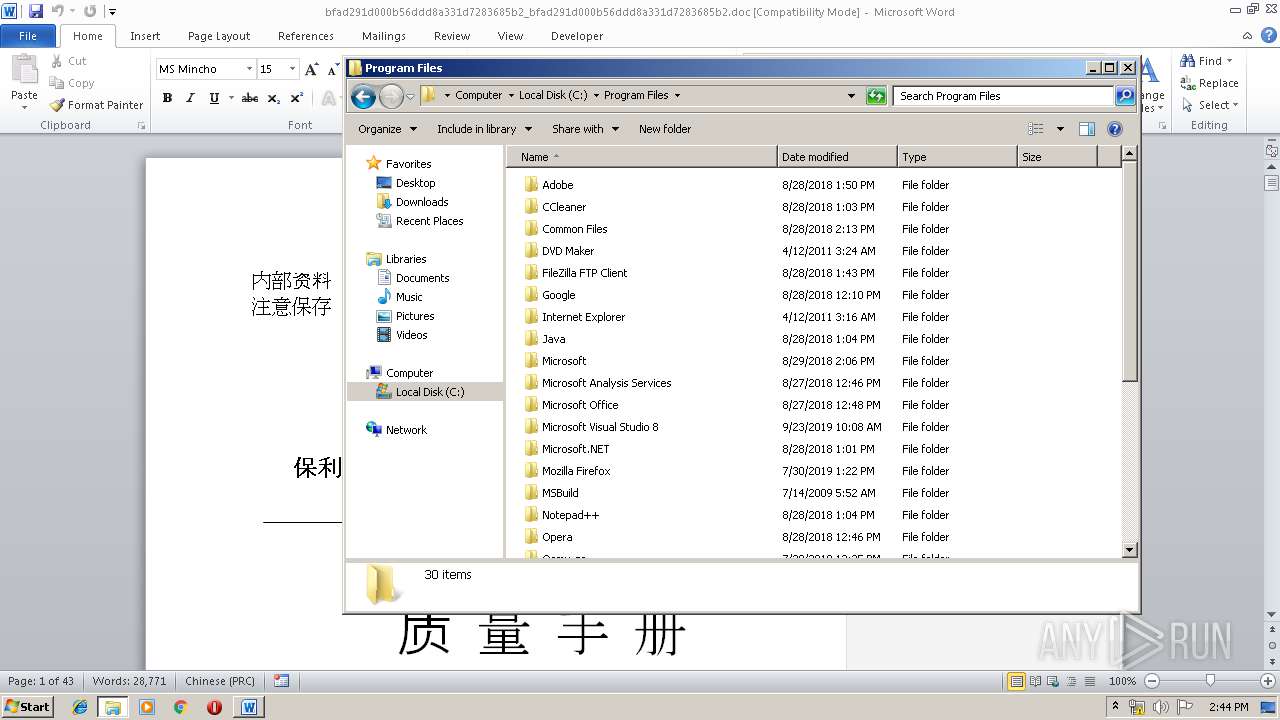
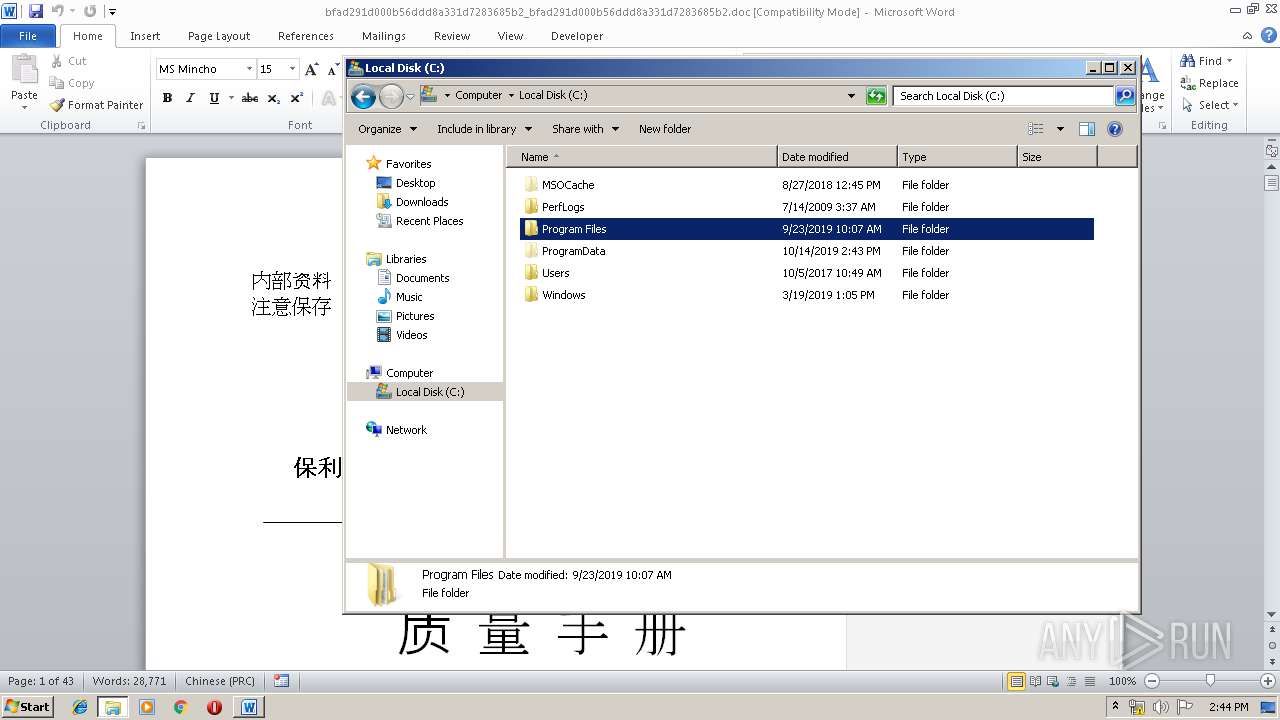
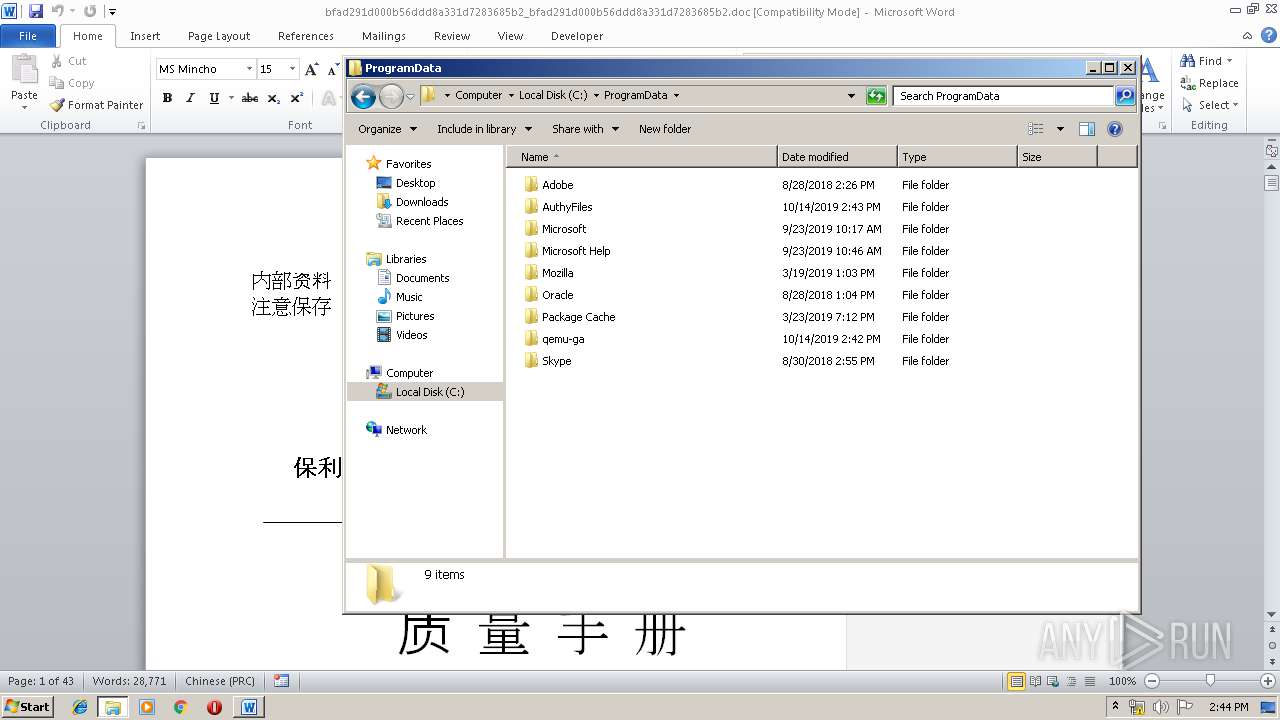
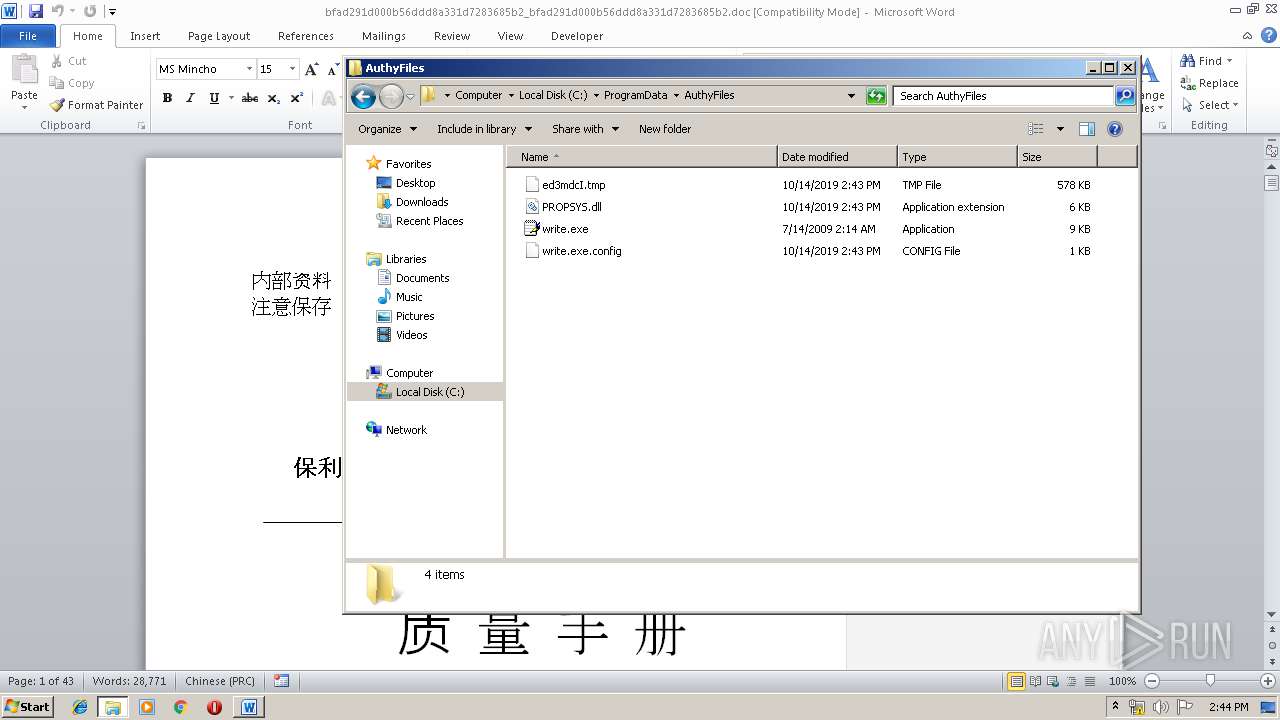
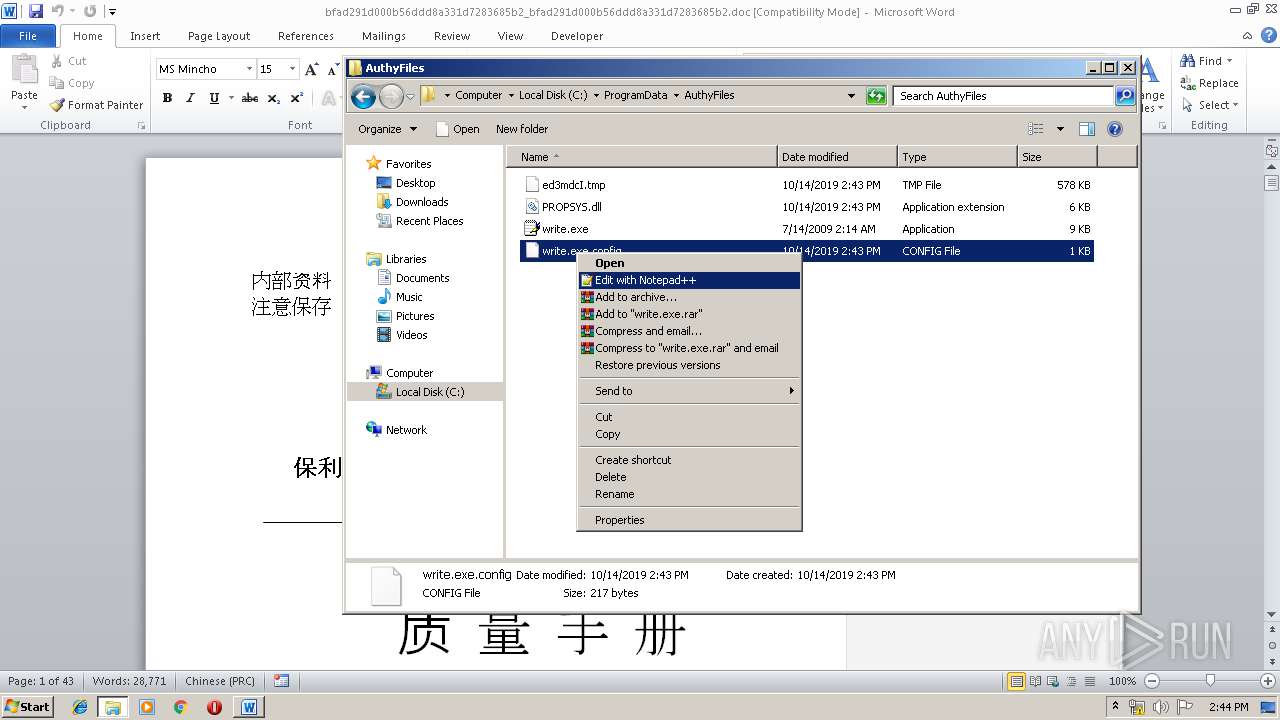
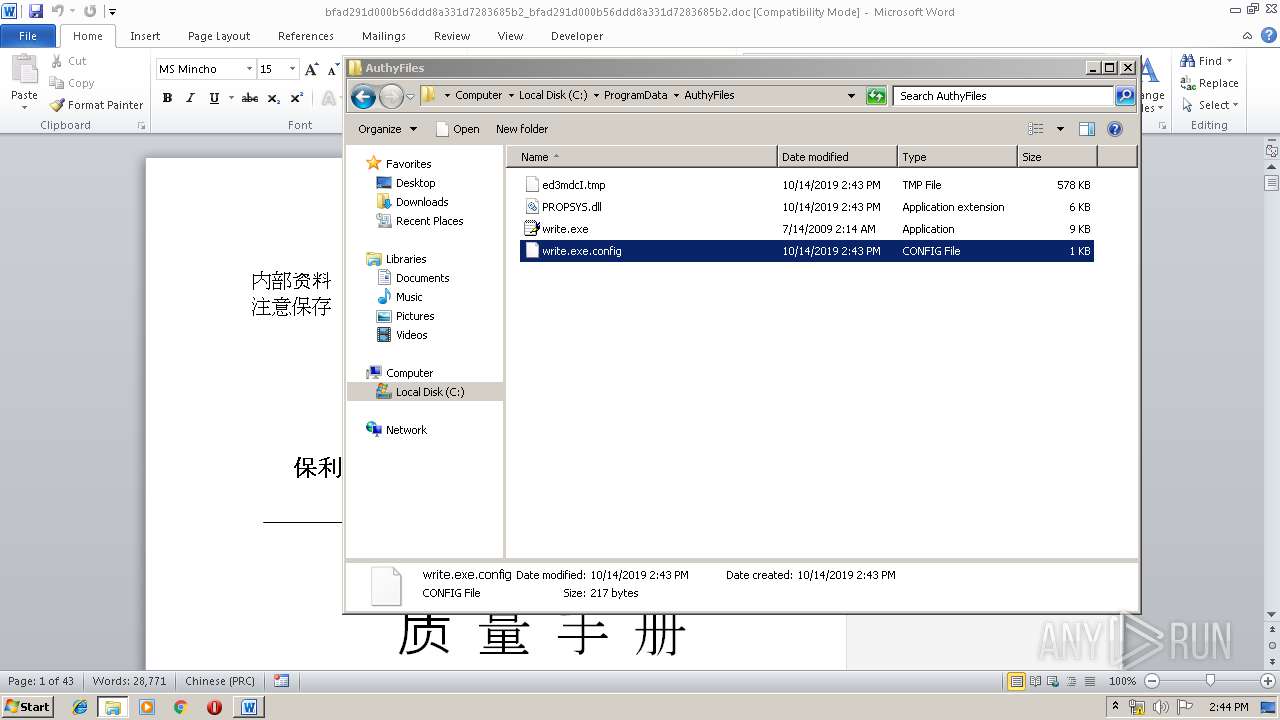
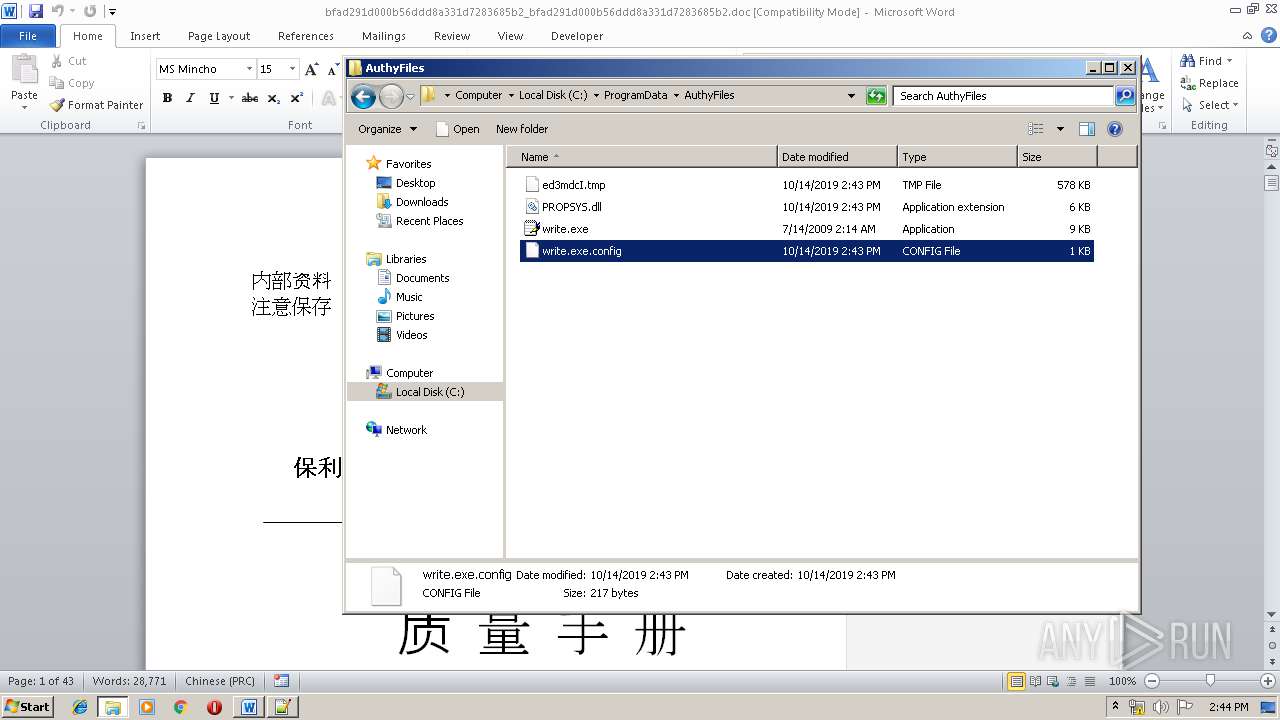
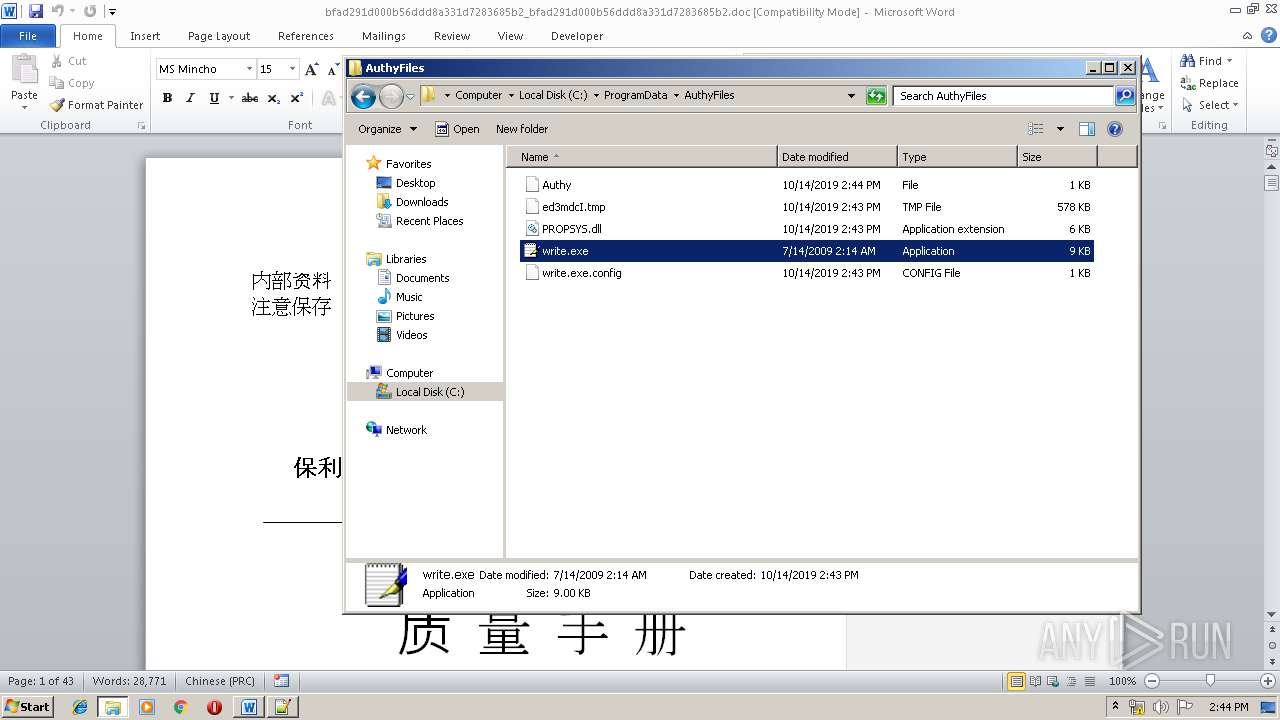
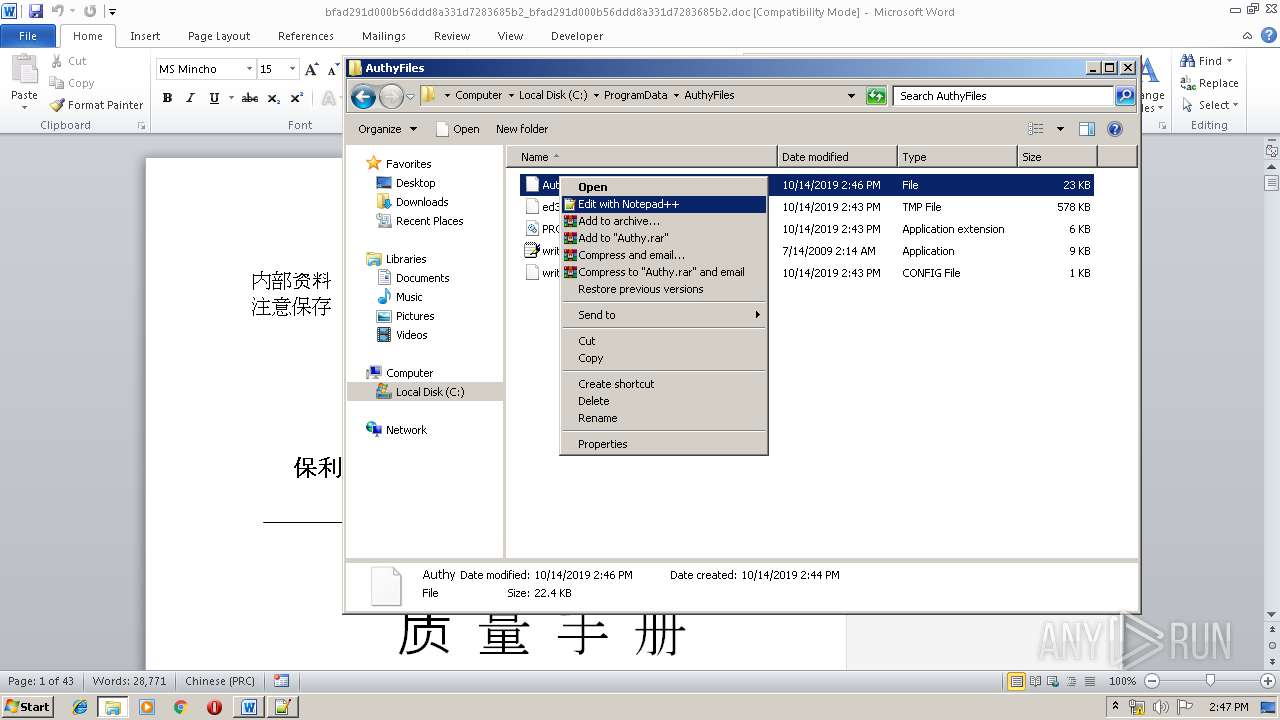
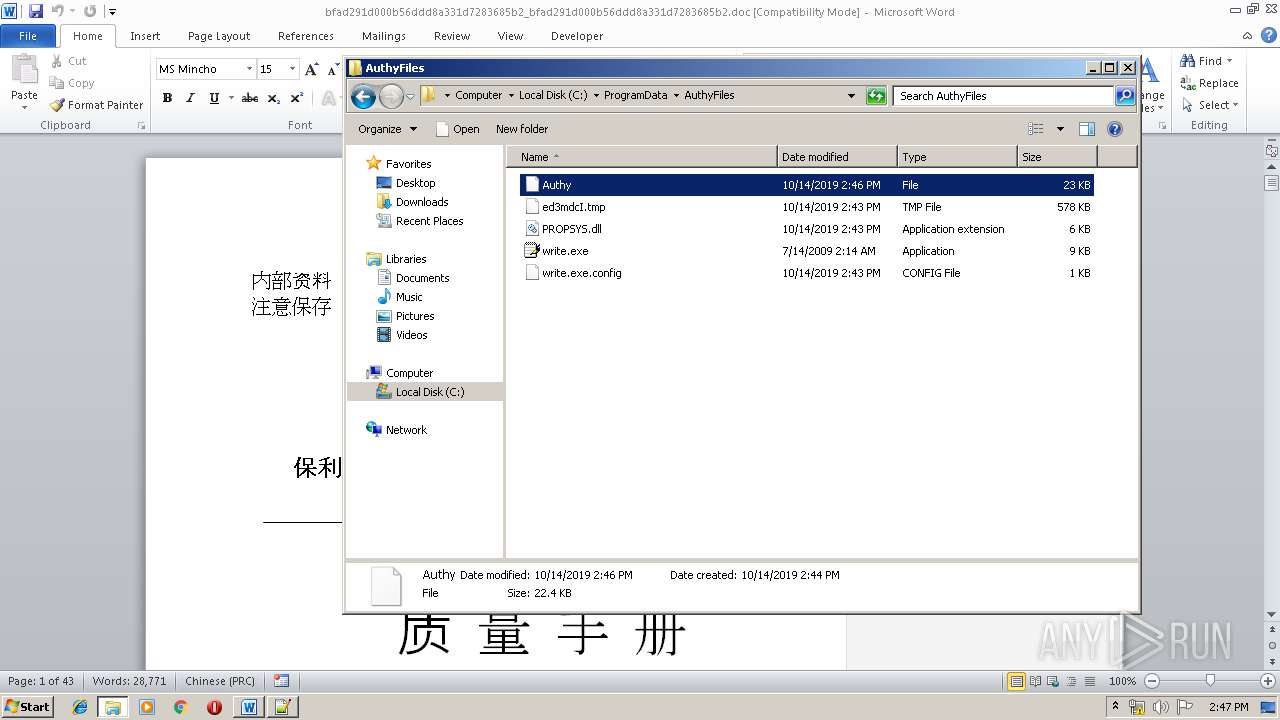
Creates files in the program directory
- EQNEDT32.EXE (PID: 2612)
- write.exe (PID: 3416)
Creates files in the user directory
- notepad++.exe (PID: 3840)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 2612)
INFO
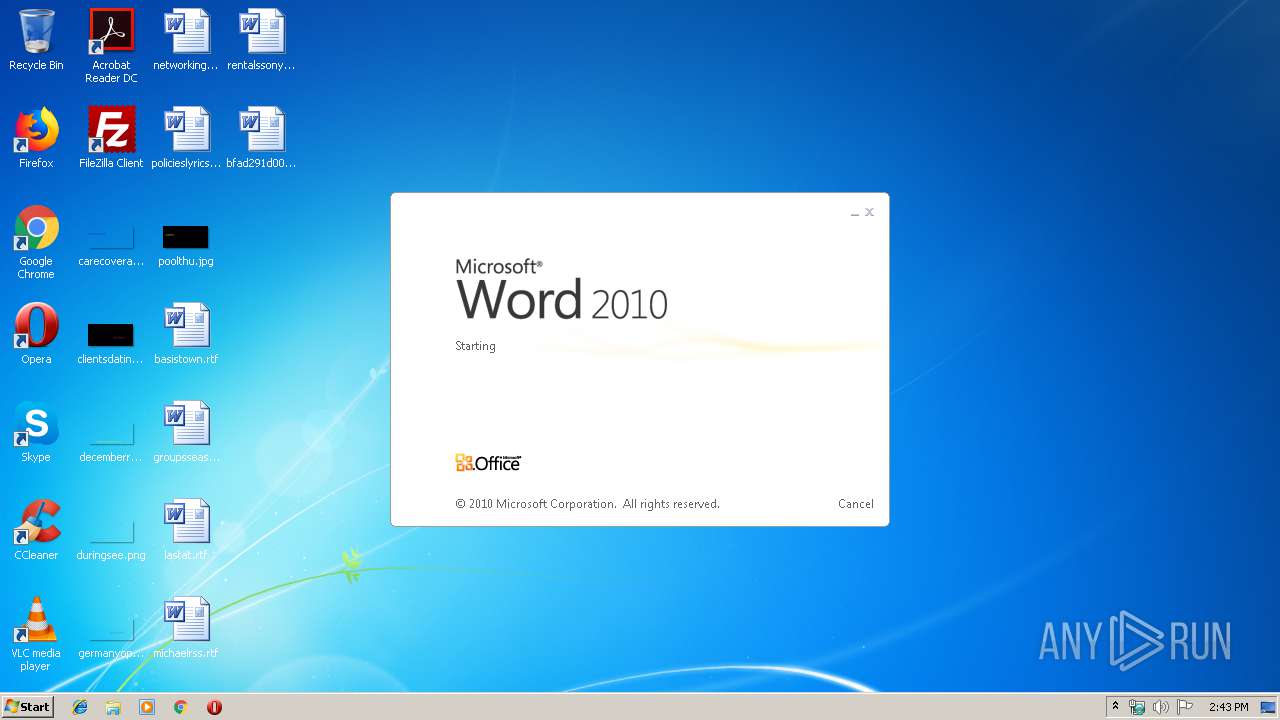
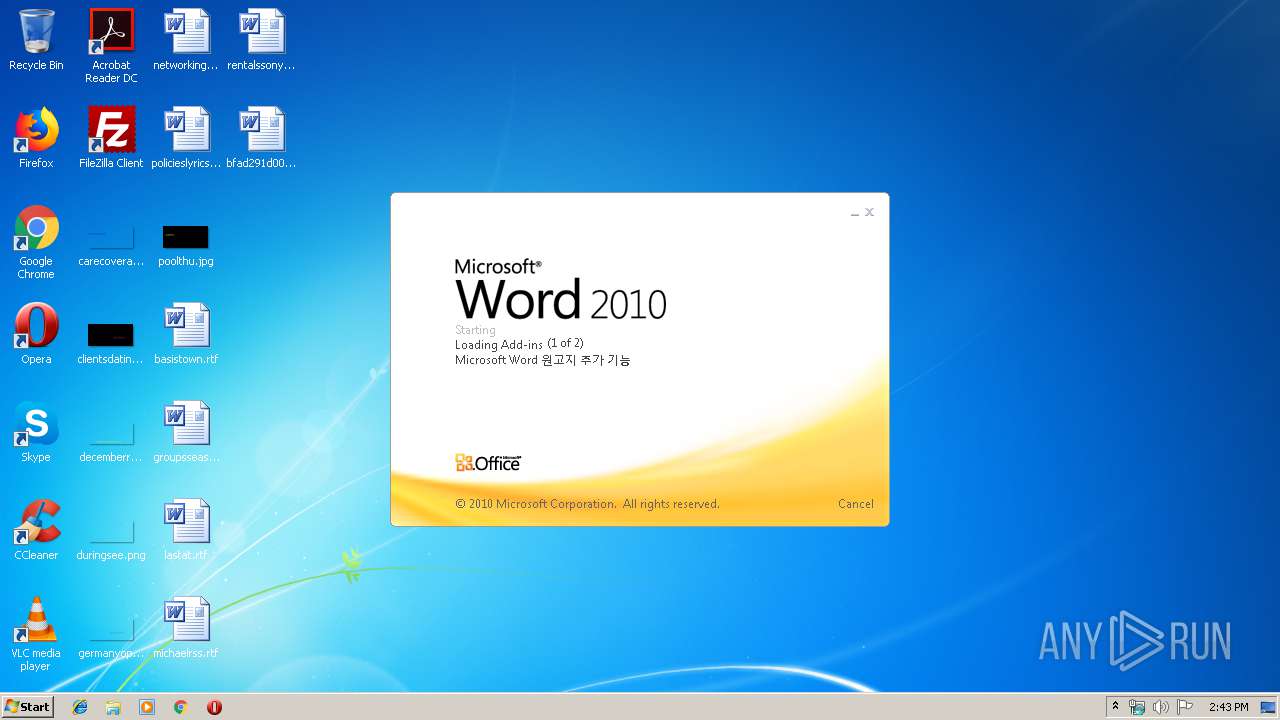
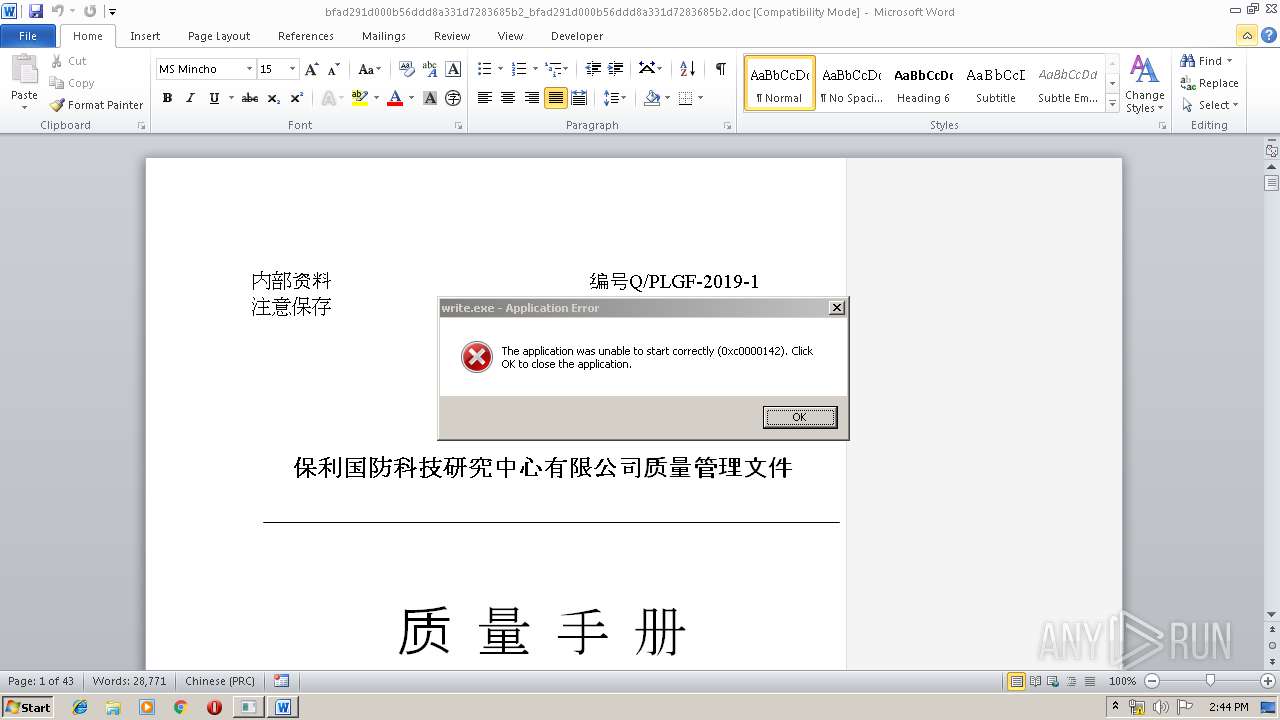
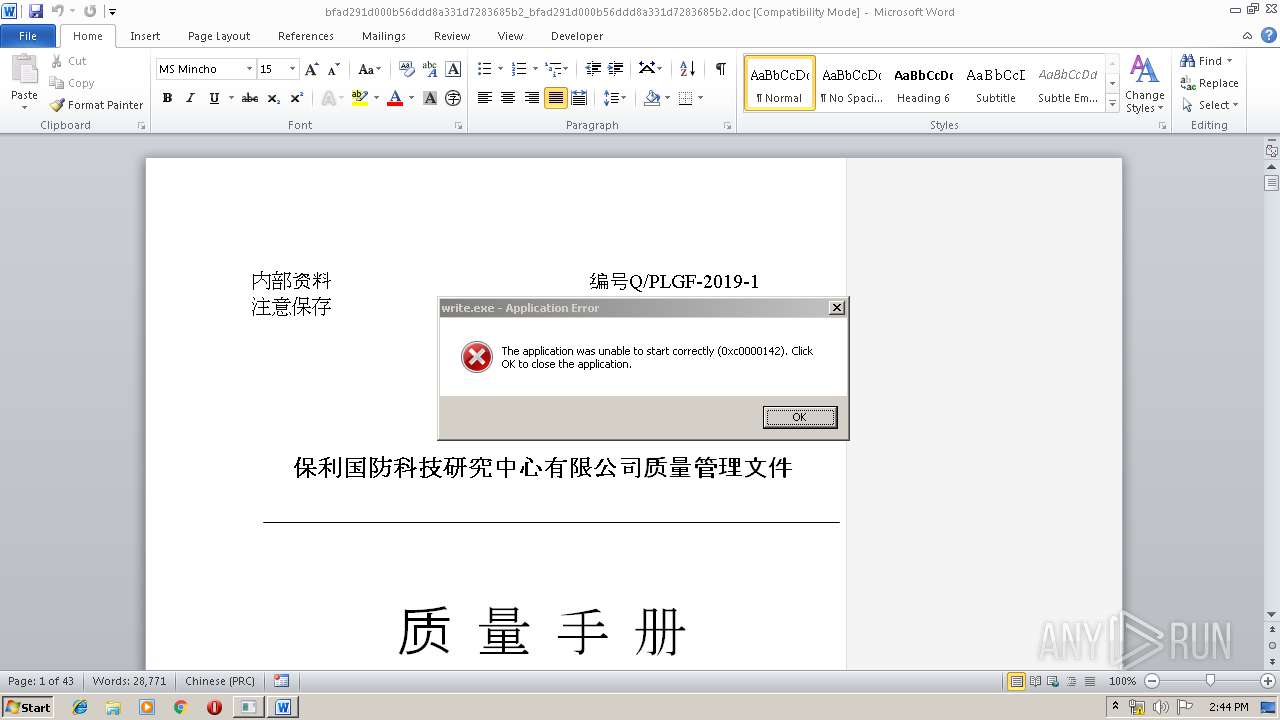
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1556)
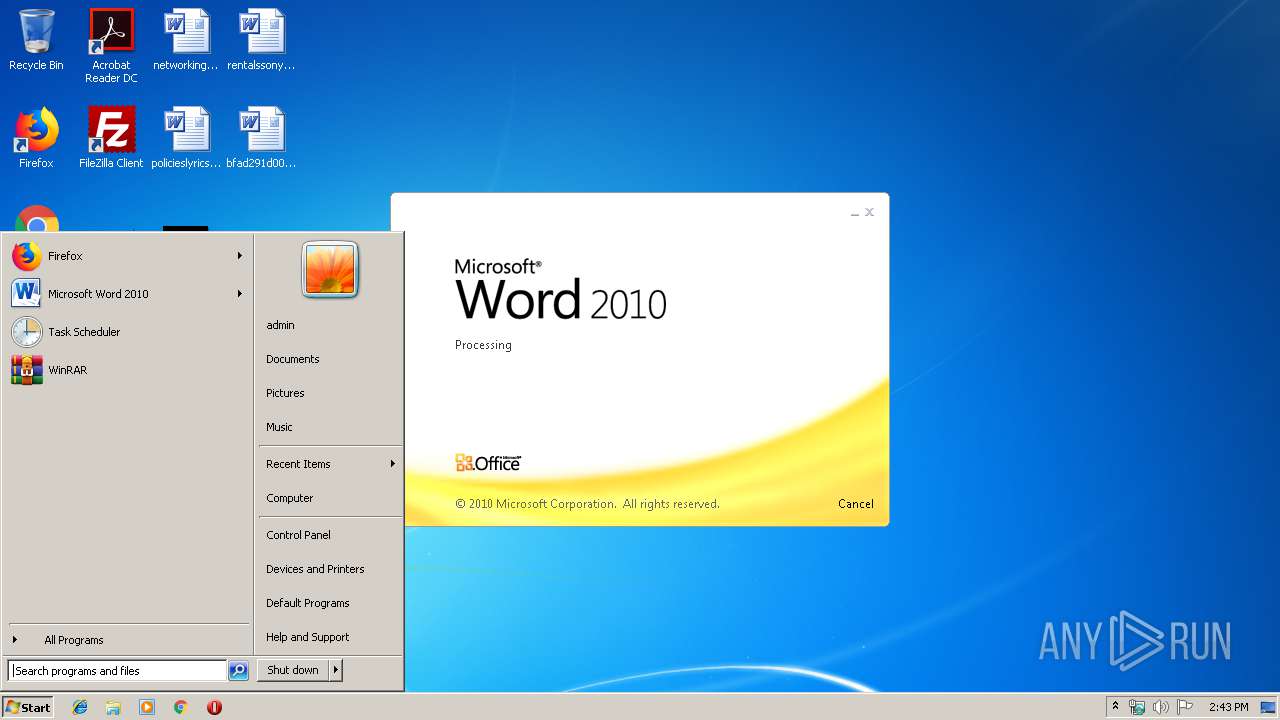
Manual execution by user
- WINWORD.EXE (PID: 1556)
- notepad++.exe (PID: 3840)
- mmc.exe (PID: 2548)
- write.exe (PID: 3416)
- mmc.exe (PID: 3856)
- notepad++.exe (PID: 3968)
Creates files in the user directory
- WINWORD.EXE (PID: 1556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
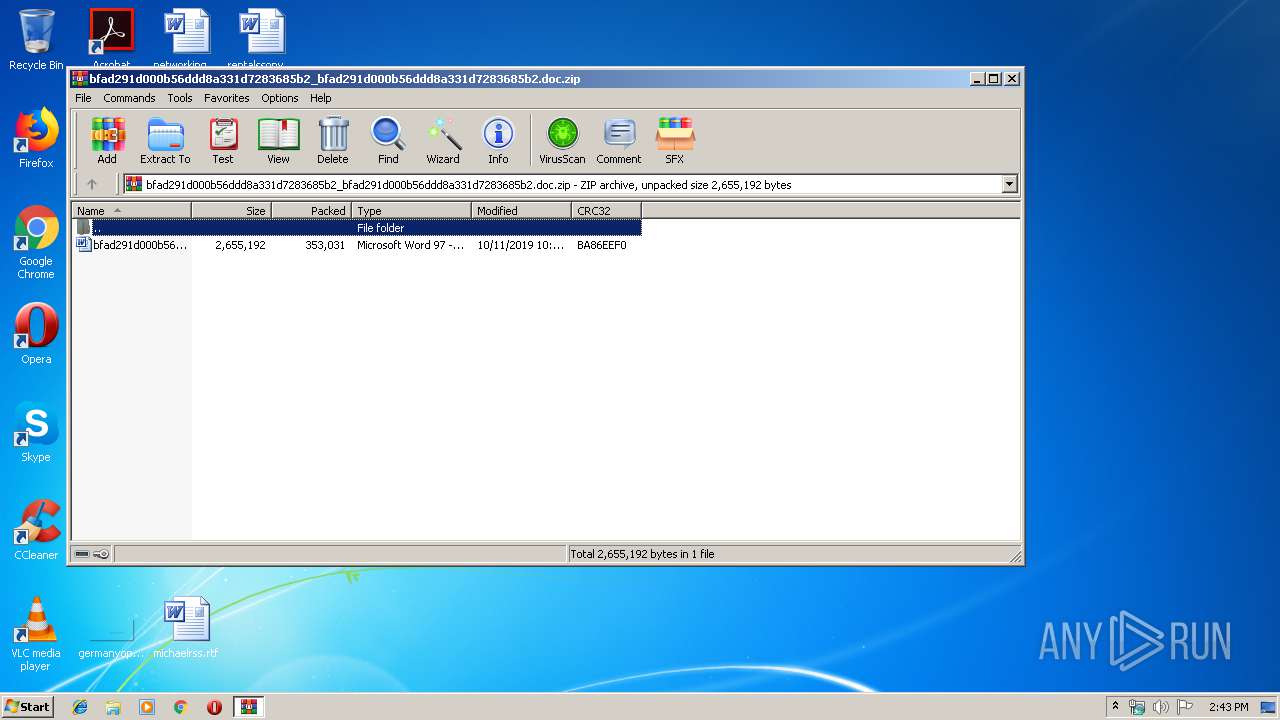
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:11 11:44:21 |
| ZipCRC: | 0xba86eef0 |
| ZipCompressedSize: | 353031 |
| ZipUncompressedSize: | 2655192 |
| ZipFileName: | bfad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc |
Total processes
56
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1556 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\bfad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\bfad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 4294967295 Version: 4.1 Modules
| |||||||||||||||
| 2548 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3416 | "C:\ProgramData\AuthyFiles\write.exe" | C:\ProgramData\AuthyFiles\write.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Write Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
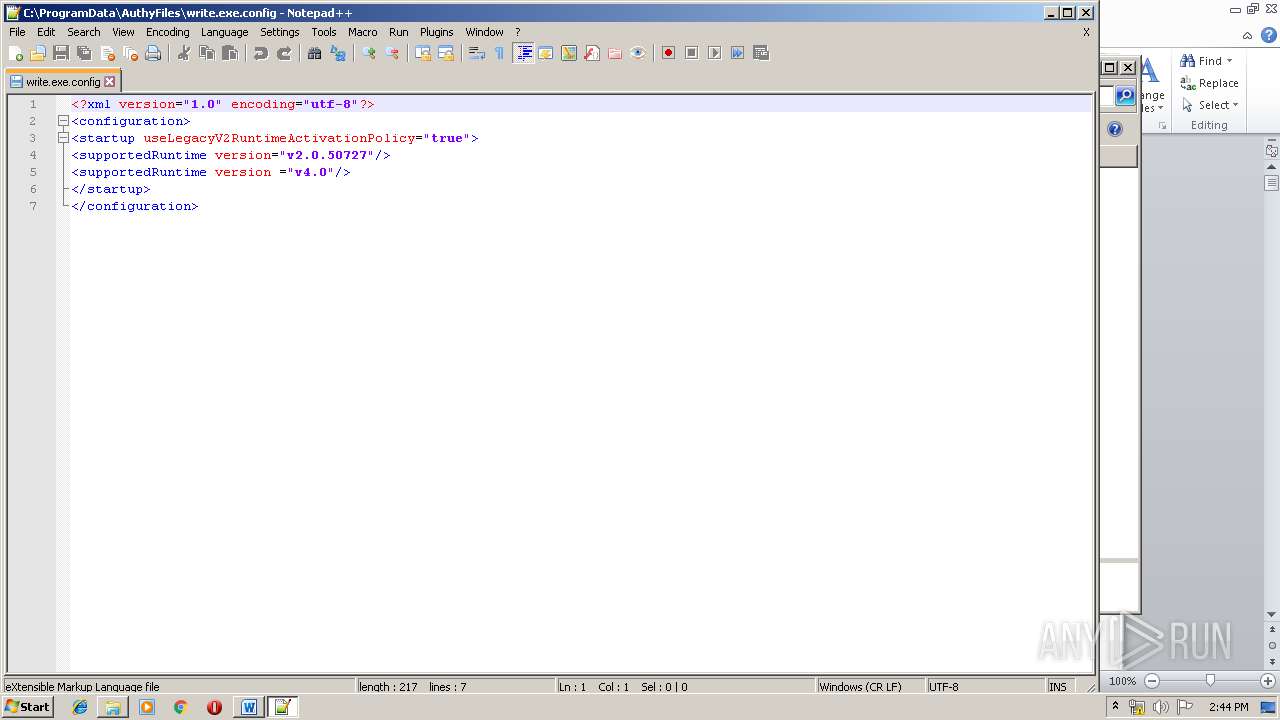
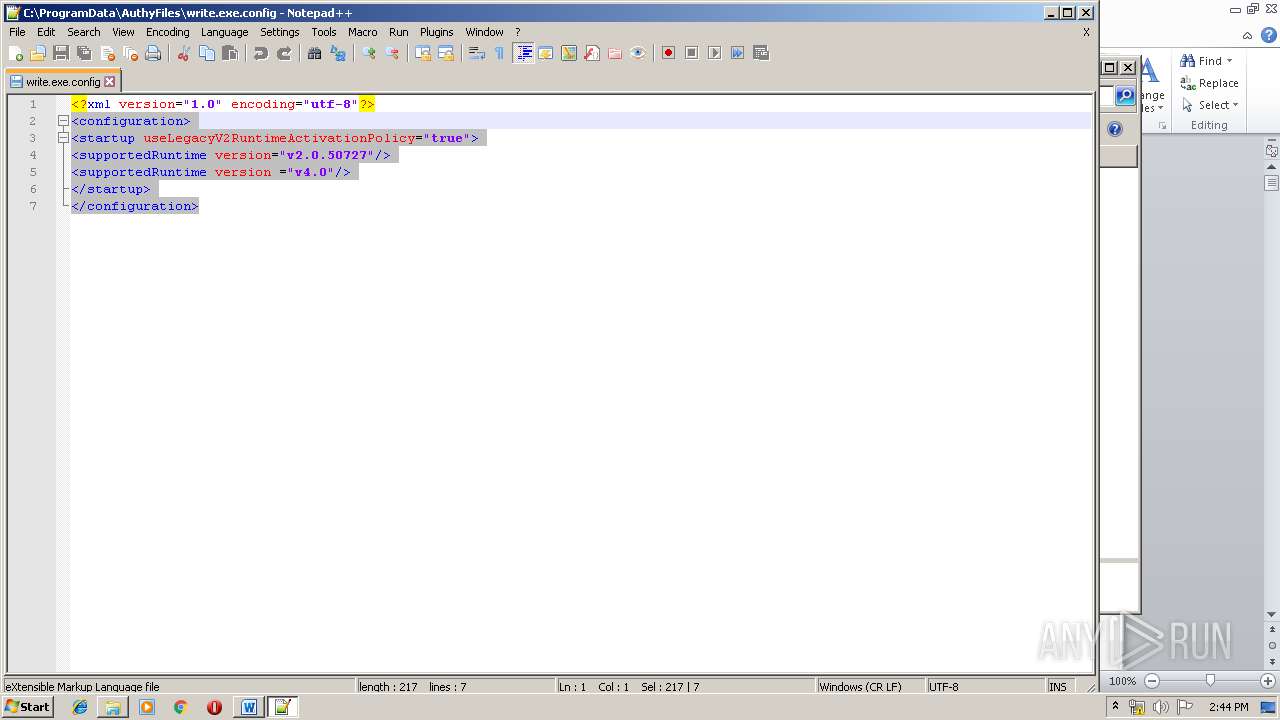
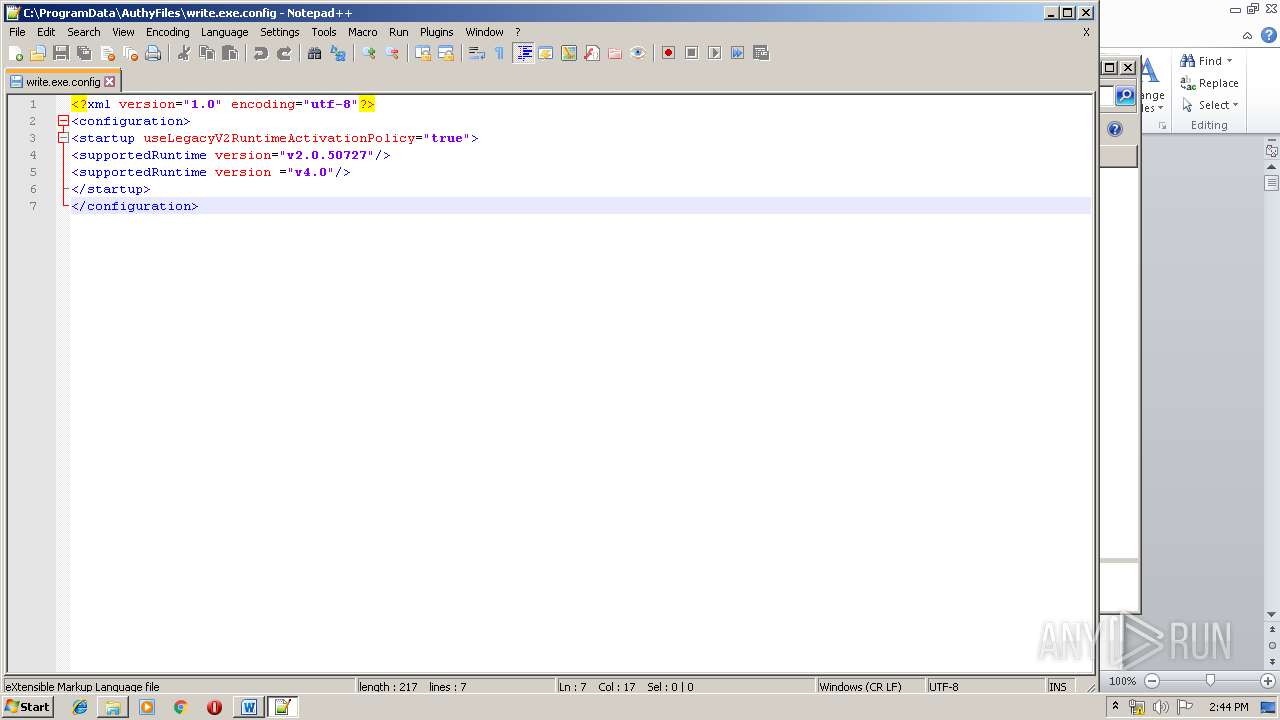
| 3840 | "C:\Program Files\Notepad++\notepad++.exe" "C:\ProgramData\AuthyFiles\write.exe.config" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 3856 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3944 | "C:\ProgramData\AuthyFiles\write.exe" | C:\ProgramData\AuthyFiles\write.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Write Exit code: 3221225794 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
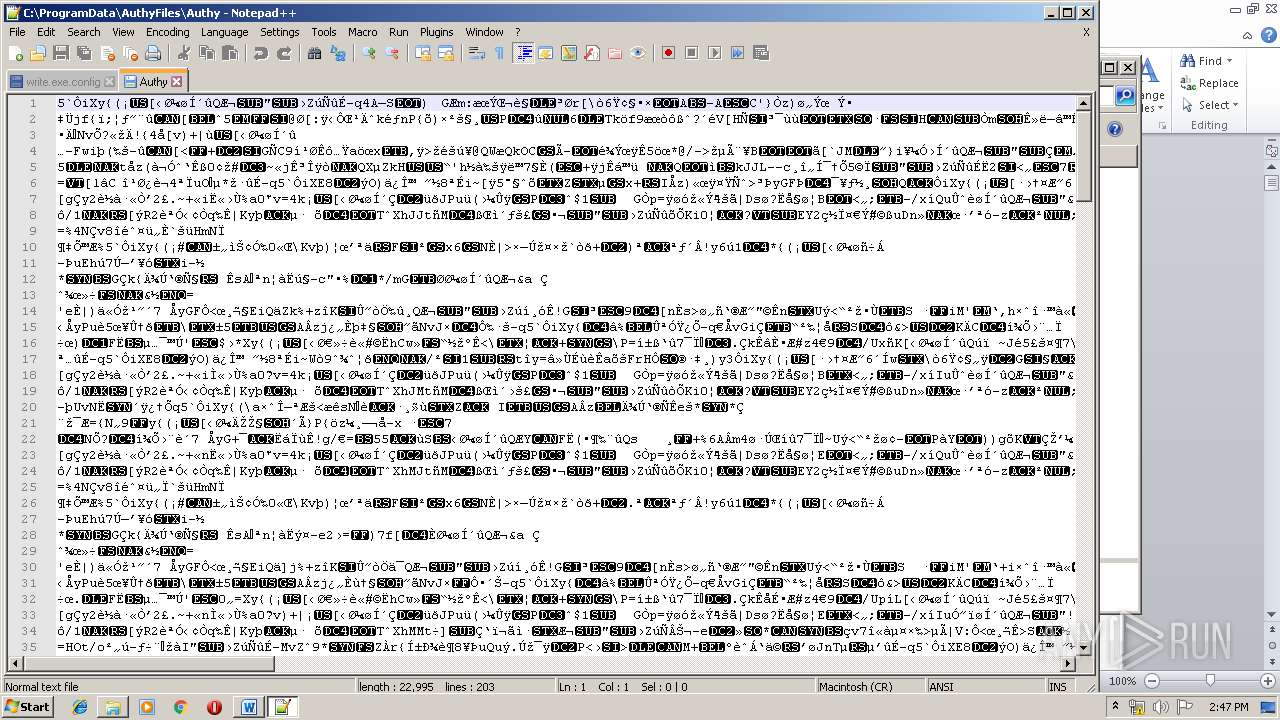
| 3968 | "C:\Program Files\Notepad++\notepad++.exe" "C:\ProgramData\AuthyFiles\Authy" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
Total events
2 592
Read events
1 447
Write events
998
Delete events
147
Modification events
| (PID) Process: | (1584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1584) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\bfad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc.zip | |||
| (PID) Process: | (1584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
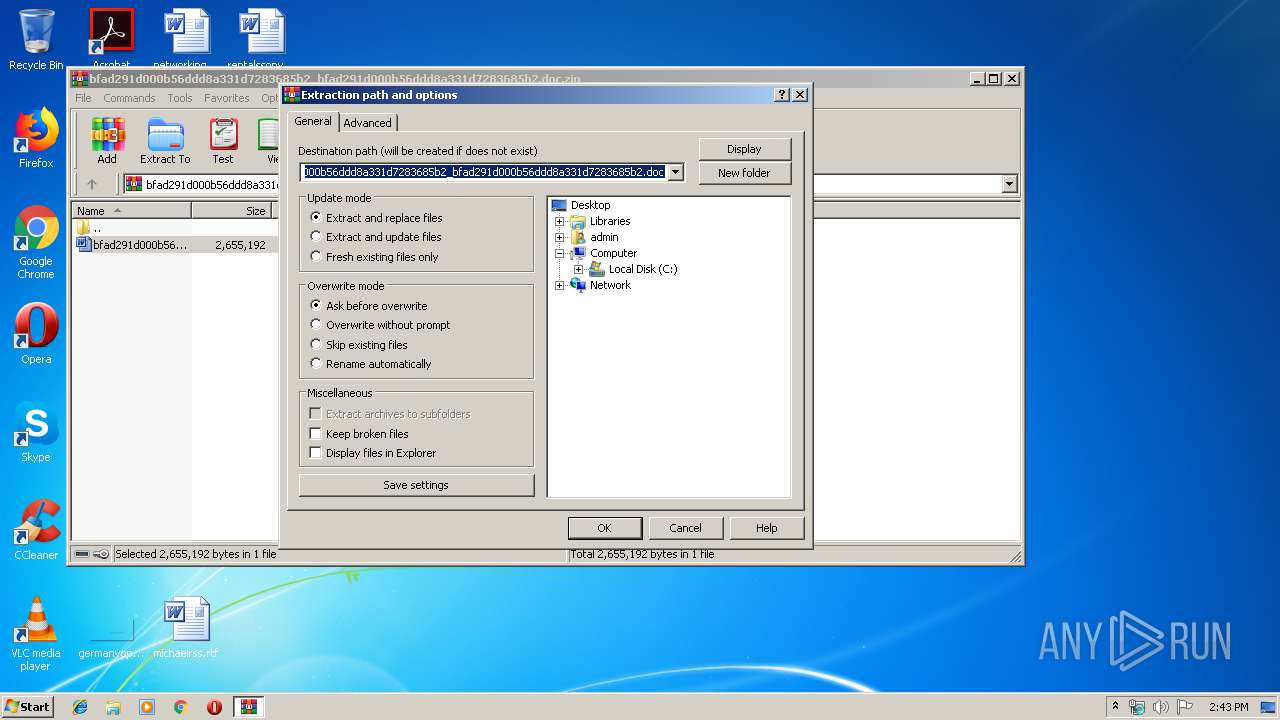
| (PID) Process: | (1584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
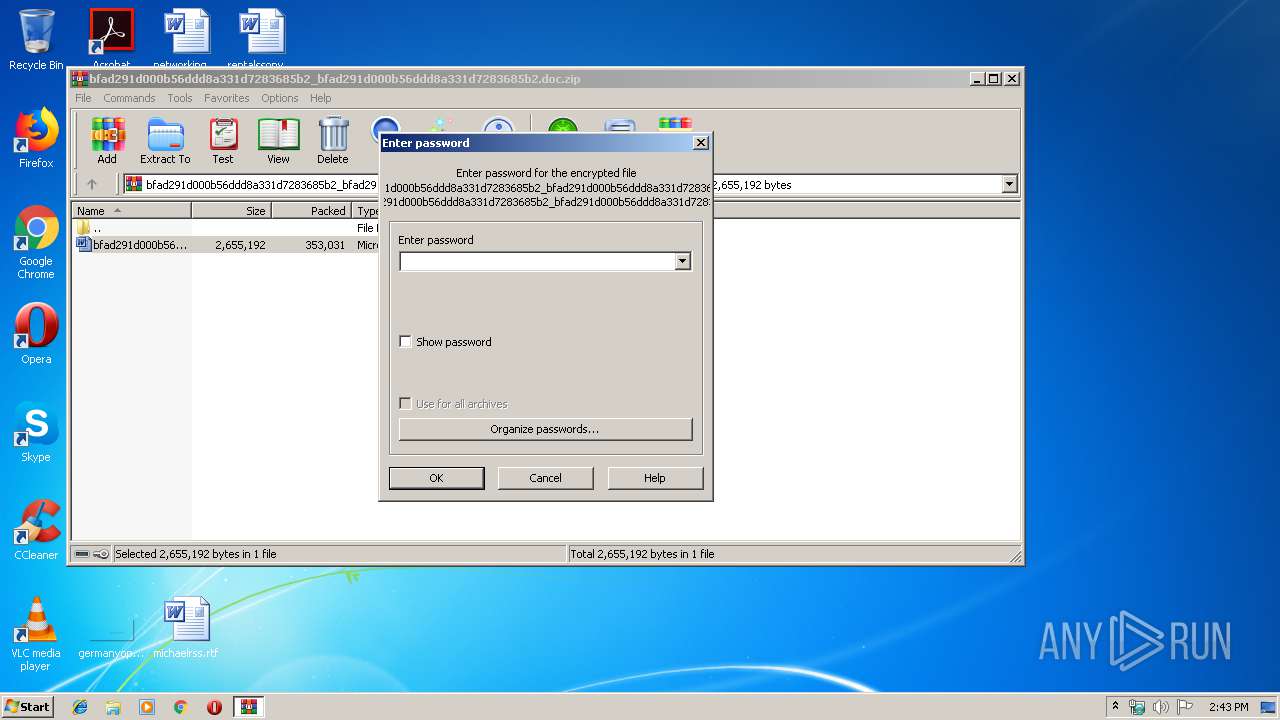
| (PID) Process: | (1584) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
4
Text files
12
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1556 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2B5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3416 | write.exe | C:\Users\admin\AppData\Local\Temp\tmp802D.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | write.exe | C:\Users\admin\AppData\Local\Temp\tmp8C82.tmp | — | |
MD5:— | SHA256:— | |||
| 3416 | write.exe | C:\Users\admin\AppData\Roaming\AuthyDat\tm4a2dlv.jjm.flc | — | |
MD5:— | SHA256:— | |||
| 3416 | write.exe | C:\Users\admin\AppData\Local\Temp\tmpBC78.tmp | — | |
MD5:— | SHA256:— | |||
| 2612 | EQNEDT32.EXE | C:\ProgramData\AuthyFiles\PROPSYS.dll | executable | |
MD5:— | SHA256:— | |||
| 1556 | WINWORD.EXE | C:\Users\admin\Desktop\~$ad291d000b56ddd8a331d7283685b2_bfad291d000b56ddd8a331d7283685b2.doc | pgc | |
MD5:— | SHA256:— | |||
| 1556 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\1.a | text | |
MD5:— | SHA256:— | |||
| 2612 | EQNEDT32.EXE | C:\ProgramData\AuthyFiles\ed3mdcI.tmp | binary | |
MD5:— | SHA256:— | |||
| 1556 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.72.151:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgMpeSsuddjFyk25ZqSQ83ahjg%3D%3D | unknown | der | 527 b | whitelisted |
— | — | GET | 200 | 95.101.72.151:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2420 | gup.exe | 2.57.89.199:443 | notepad-plus-plus.org | — | — | suspicious |
3416 | write.exe | 178.62.190.33:443 | trans-can.net | Digital Ocean, Inc. | NL | unknown |
— | — | 95.101.72.151:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
trans-can.net |
| malicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
Threats
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabl |
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|