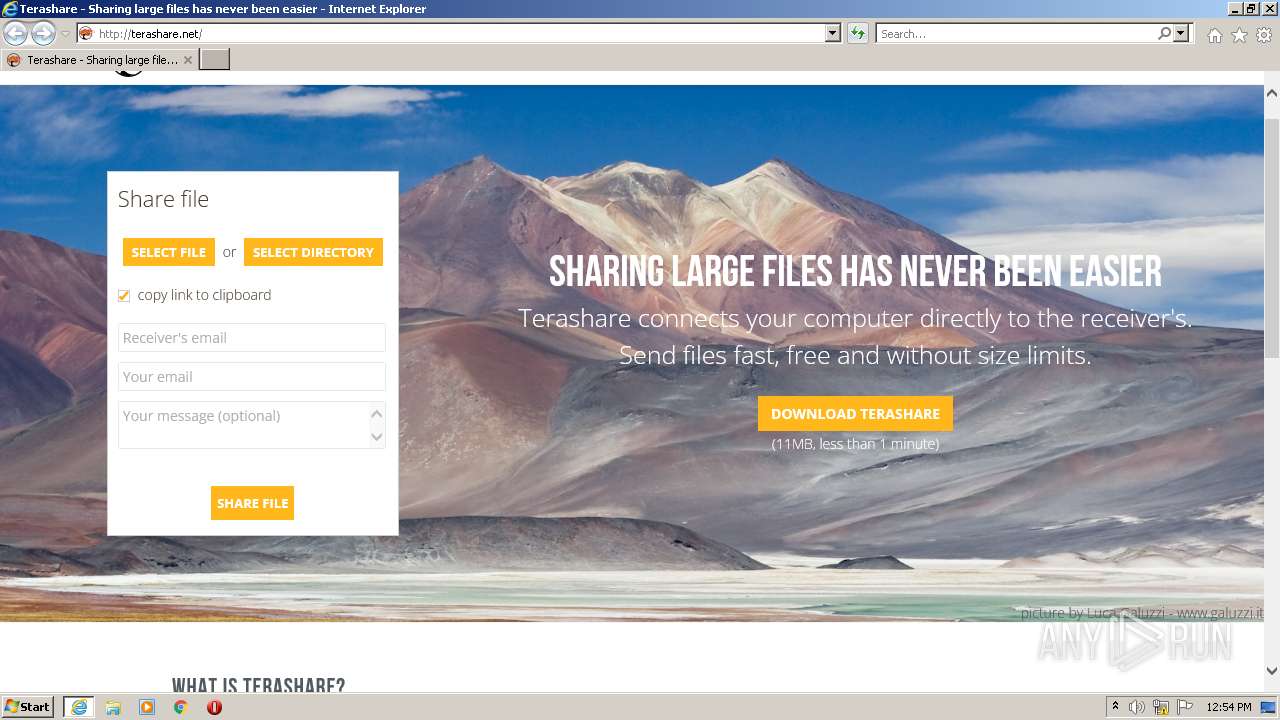
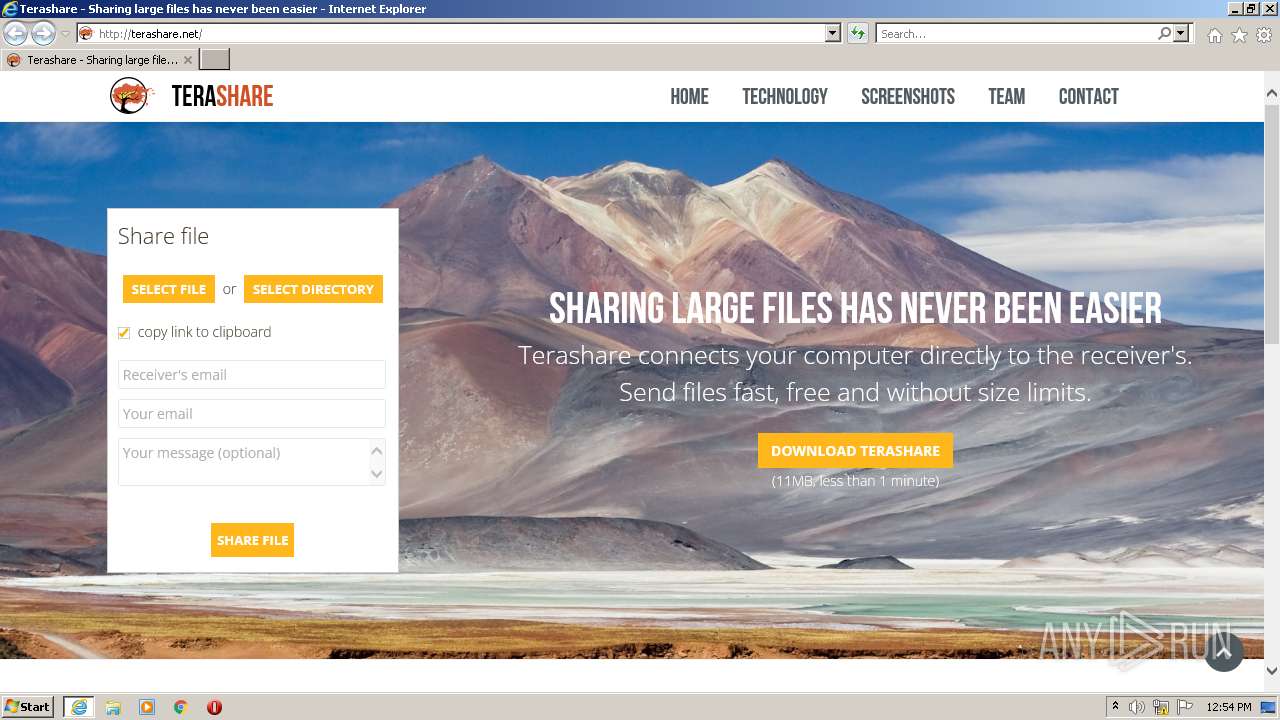
| URL: | https://www.bing.com/ck/a?!&&p=9917f24699d80e68JmltdHM9MTY2ODY0MzIwMCZpZ3VpZD0yODg0YmM3NC04Nzk4LTYzNzctMDcxNC1hYzlmODYyNzYyMjcmaW5zaWQ9NTE3OQ&ptn=3&hsh=3&fclid=2884bc74-8798-6377-0714-ac9f86276227&psq=terrashare&u=a1aHR0cDovL3RlcmFzaGFyZS5uZXQv&ntb=1 |
| Full analysis: | https://app.any.run/tasks/a9336056-9a7e-4a33-bdc5-150c13c7586c |
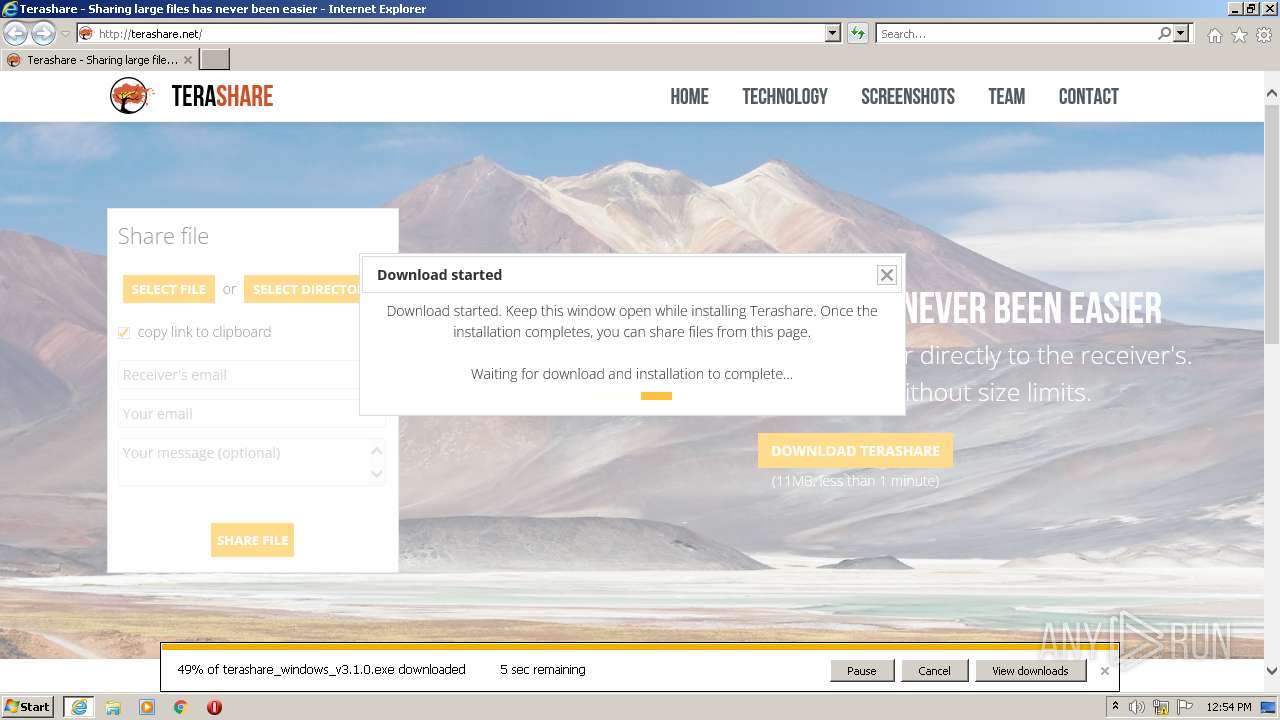
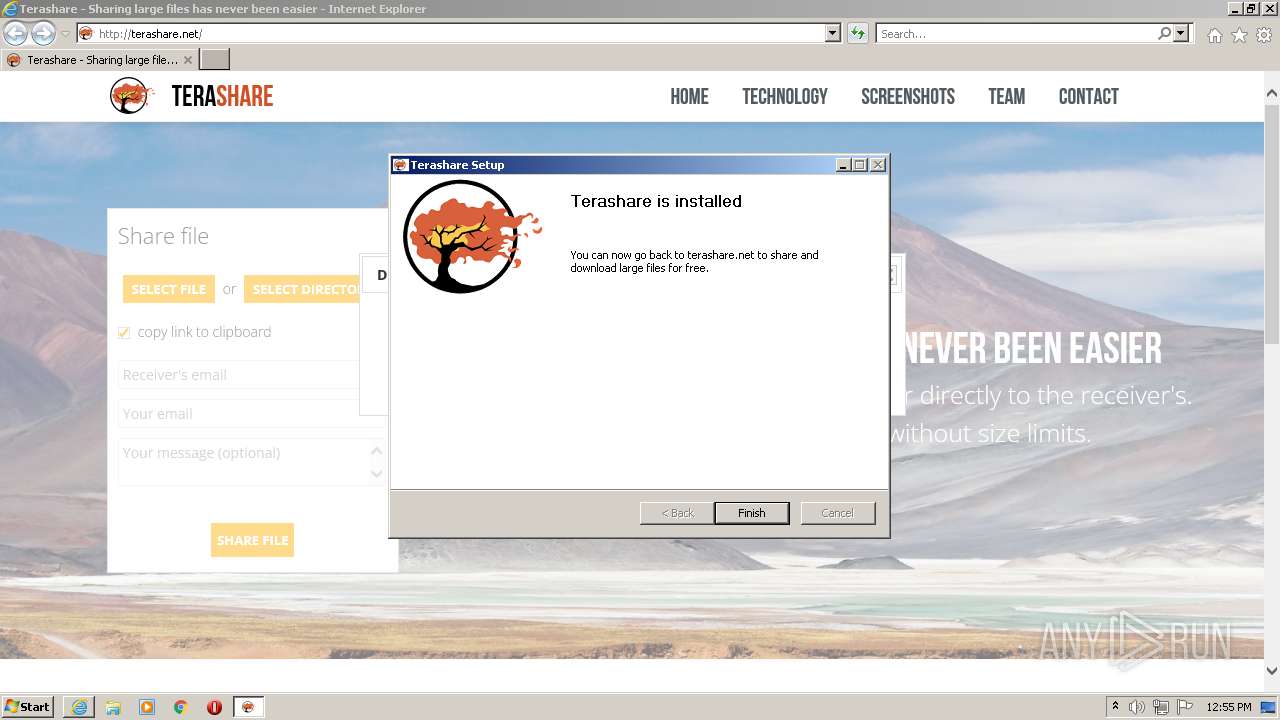
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2022, 12:53:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5476265FB1BD172E7F23F407DB88CCFE |
| SHA1: | F975E589995DA03A3815E4EBDB9A86F59101FC9C |
| SHA256: | 43FA24A933B0A43615E1BD89D25EC61114E87B46789CDA95371AEAD816FFE410 |
| SSDEEP: | 6:2OLsRR1dOBE3Xyydv2usOGJSGSBQuxD90z7:2LOBEjrIS9gX |
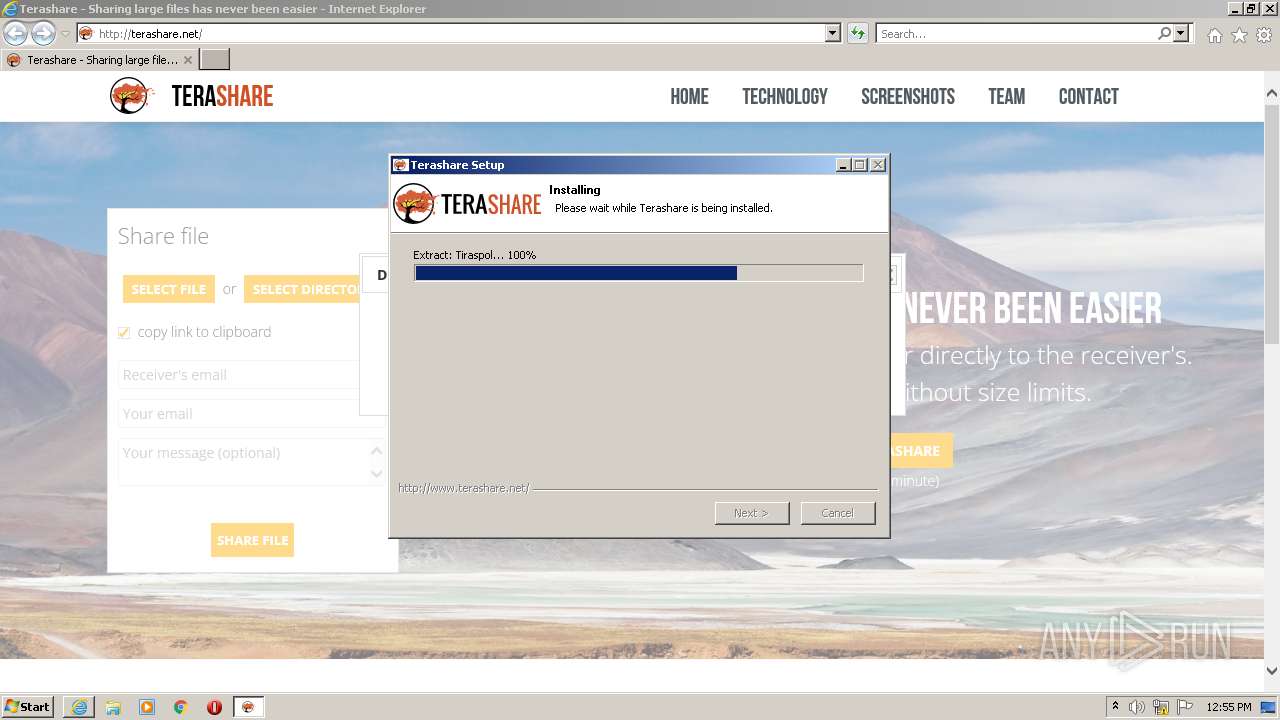
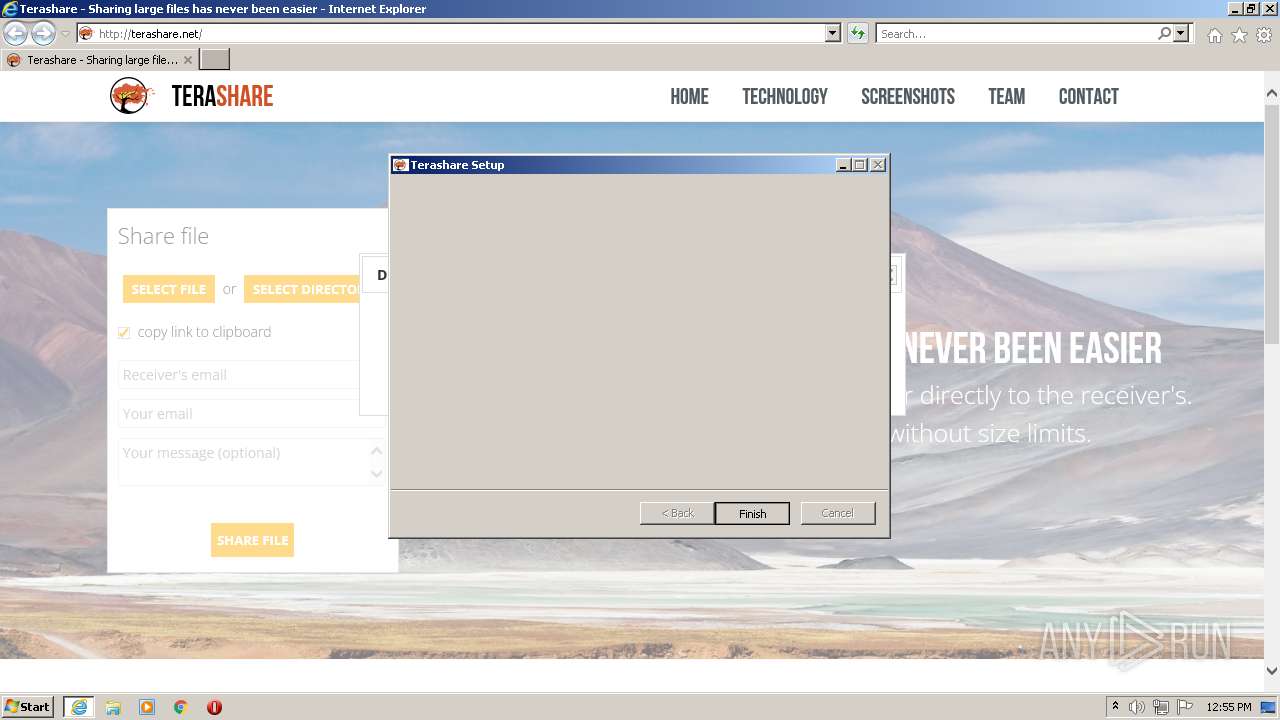
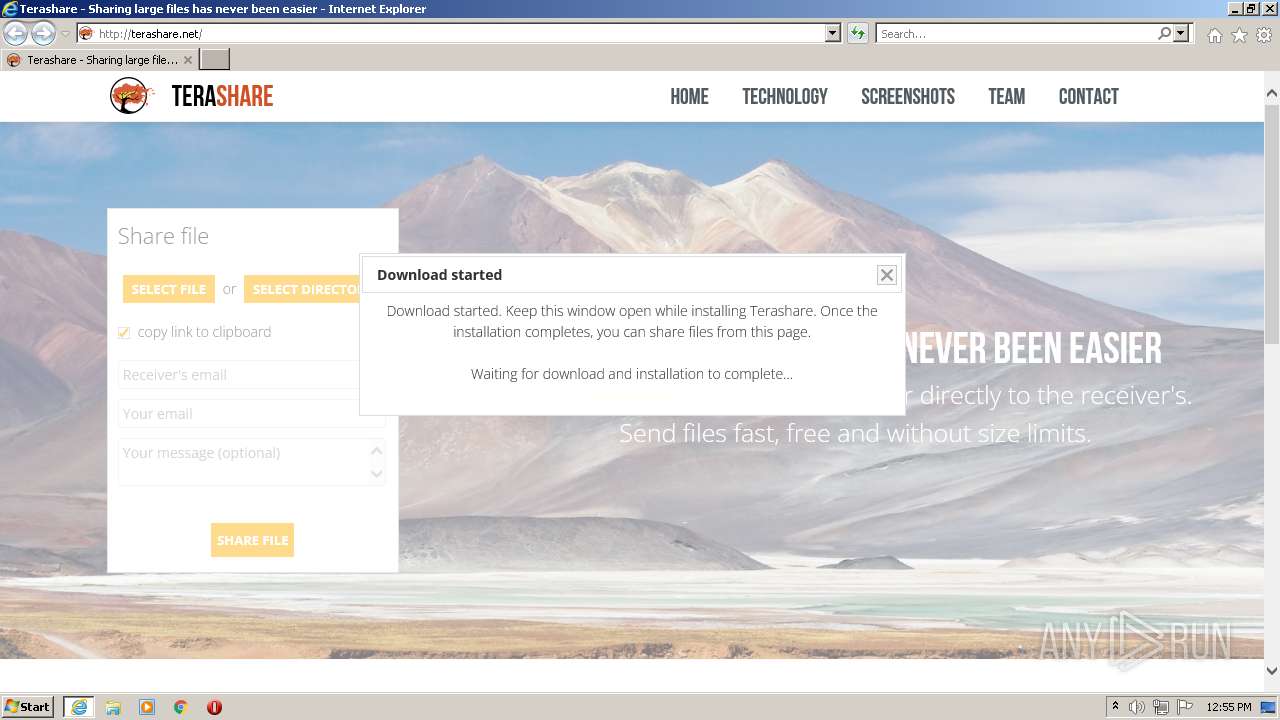
MALICIOUS
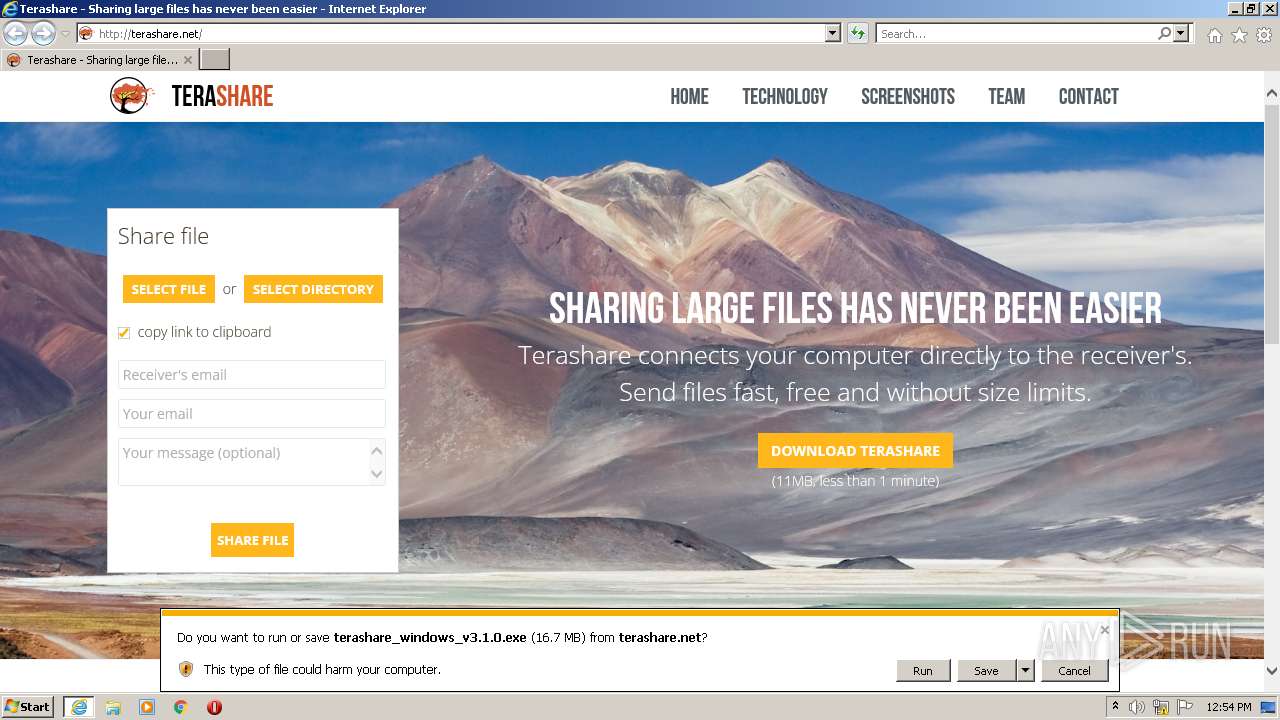
Application was dropped or rewritten from another process
- terashare_windows_v3.1.0.exe (PID: 3268)
- terashare.exe (PID: 968)
Drops the executable file immediately after the start
- terashare_windows_v3.1.0.exe (PID: 3268)
Loads dropped or rewritten executable
- terashare_windows_v3.1.0.exe (PID: 3268)
- terashare.exe (PID: 968)
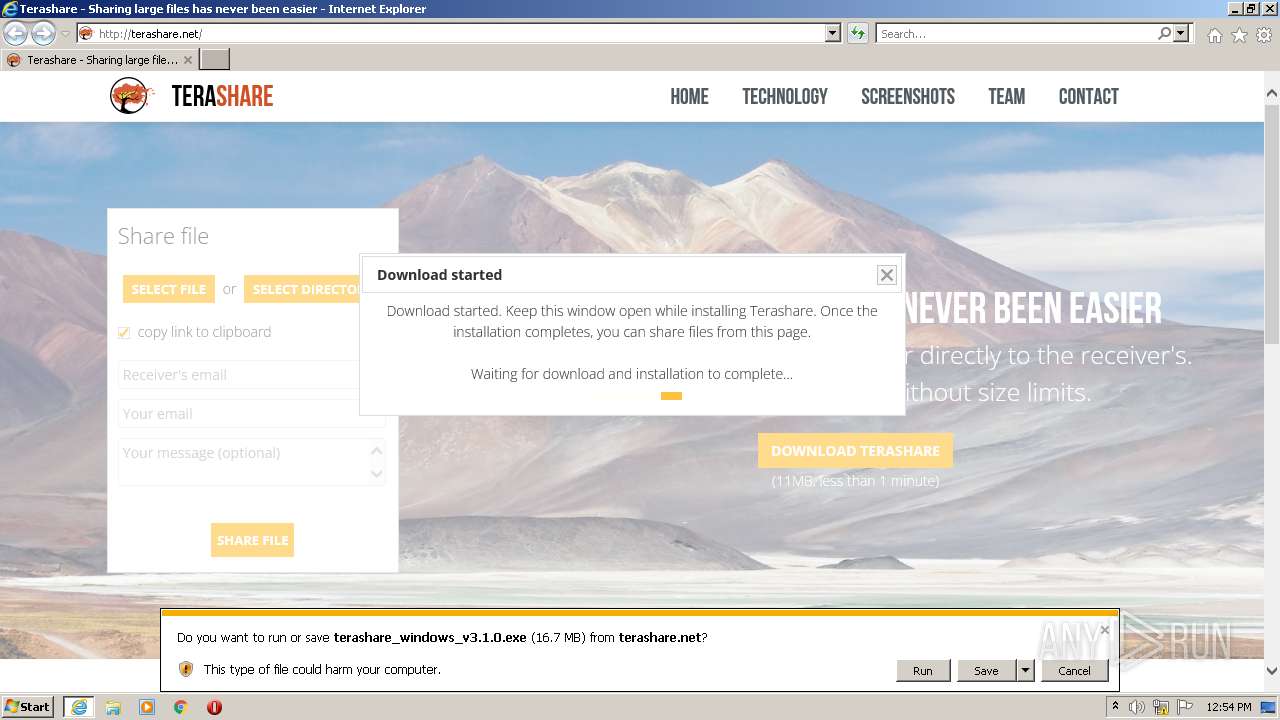
Changes the autorun value in the registry
- terashare_windows_v3.1.0.exe (PID: 3268)
SUSPICIOUS
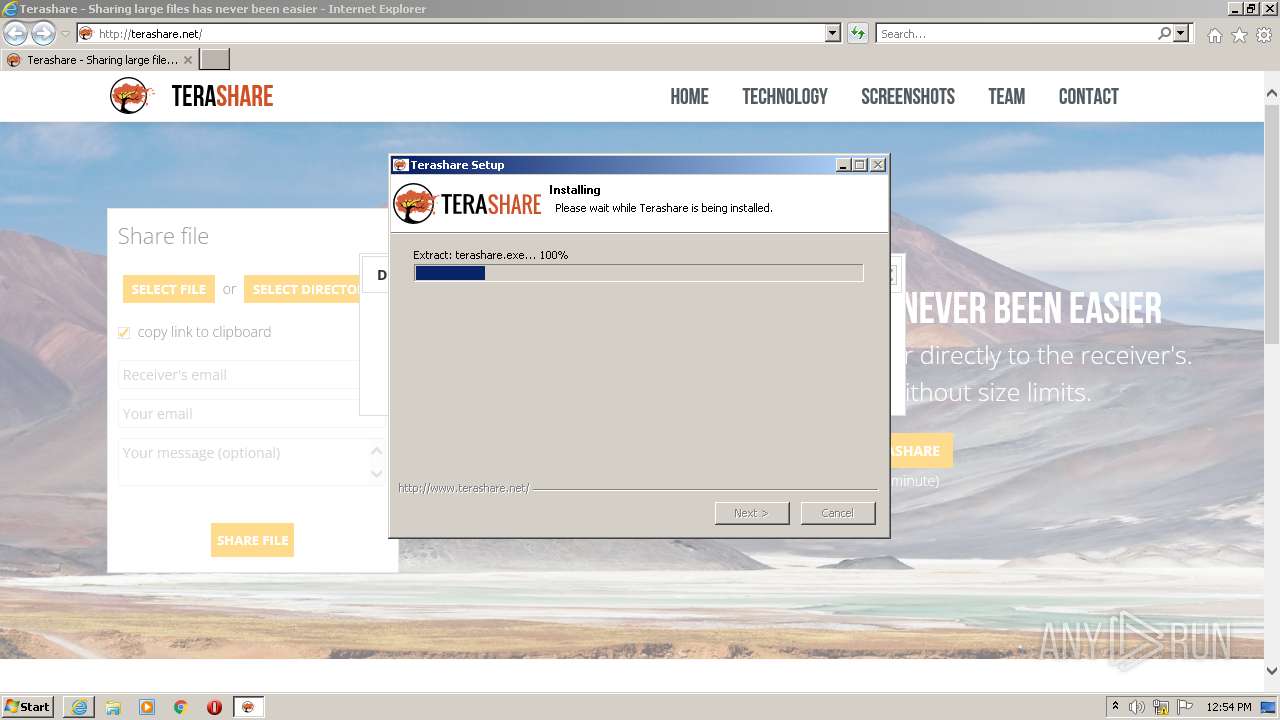
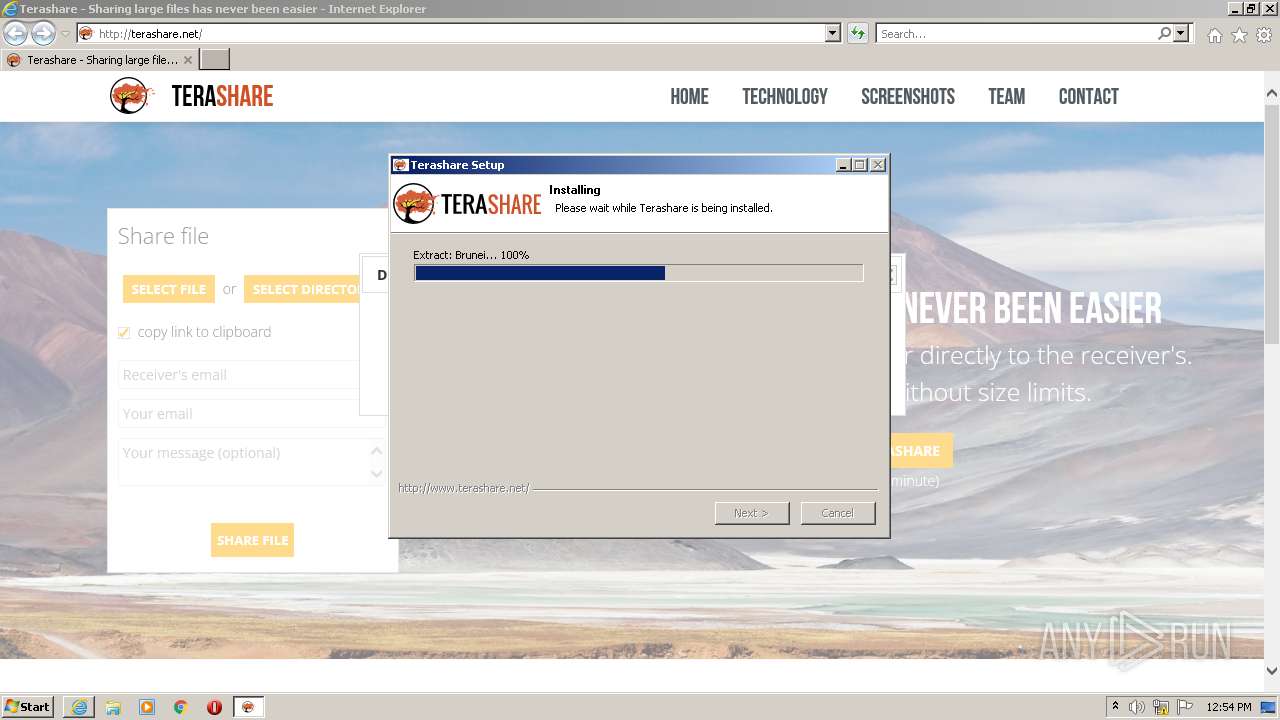
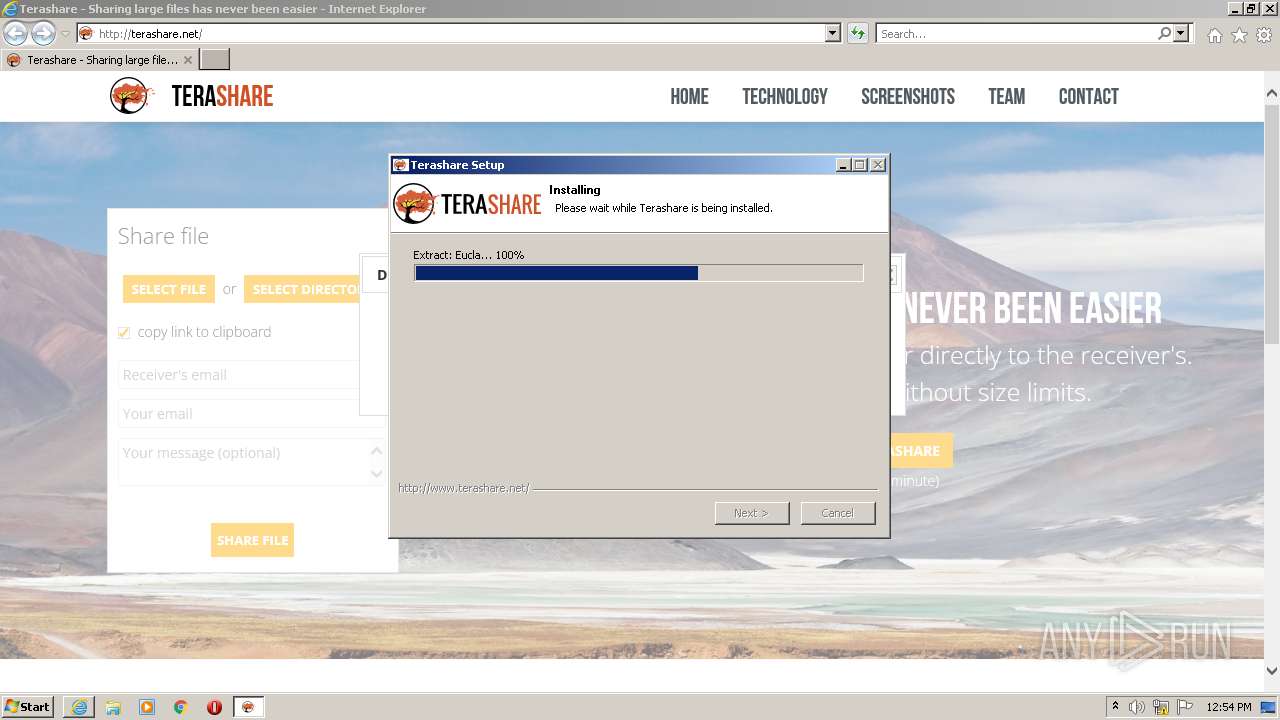
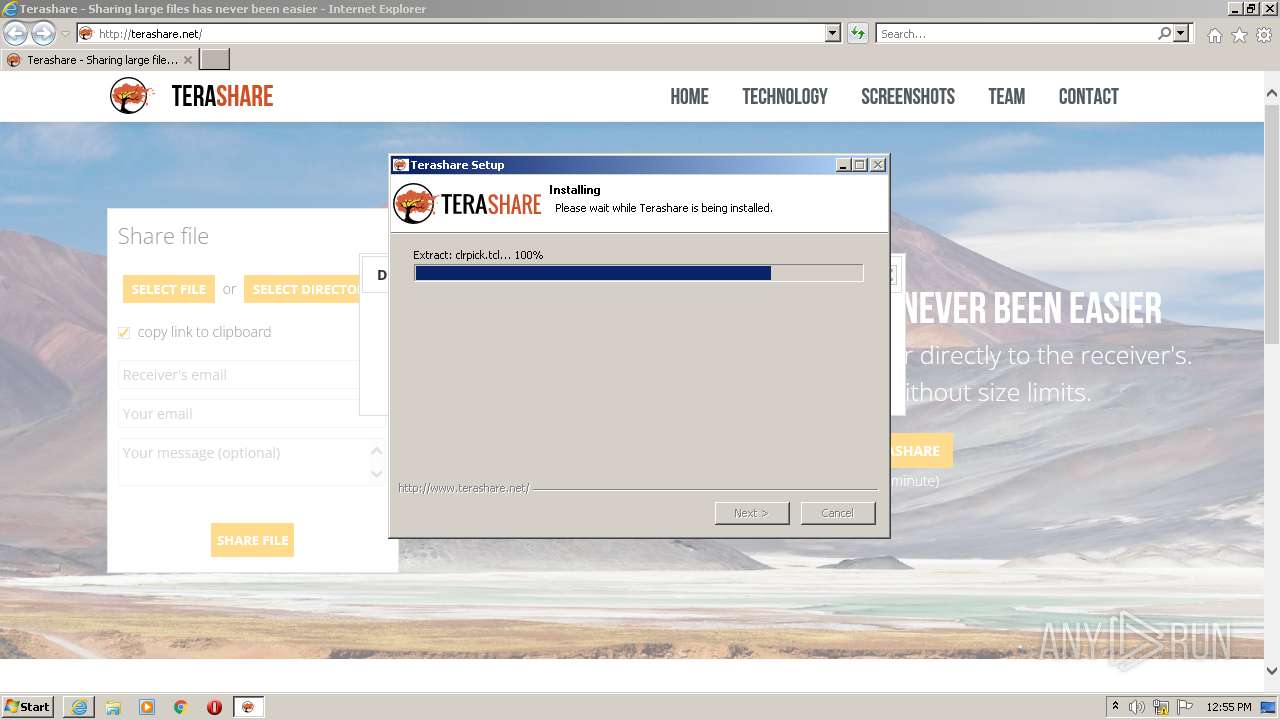
Executable content was dropped or overwritten
- terashare_windows_v3.1.0.exe (PID: 3268)
Drops a file with too old compile date
- terashare_windows_v3.1.0.exe (PID: 3268)
Reads Internet Settings
- terashare_windows_v3.1.0.exe (PID: 3268)
- terashare.exe (PID: 968)
Creates a software uninstall entry
- terashare_windows_v3.1.0.exe (PID: 3268)
Changes default file association
- terashare_windows_v3.1.0.exe (PID: 3268)
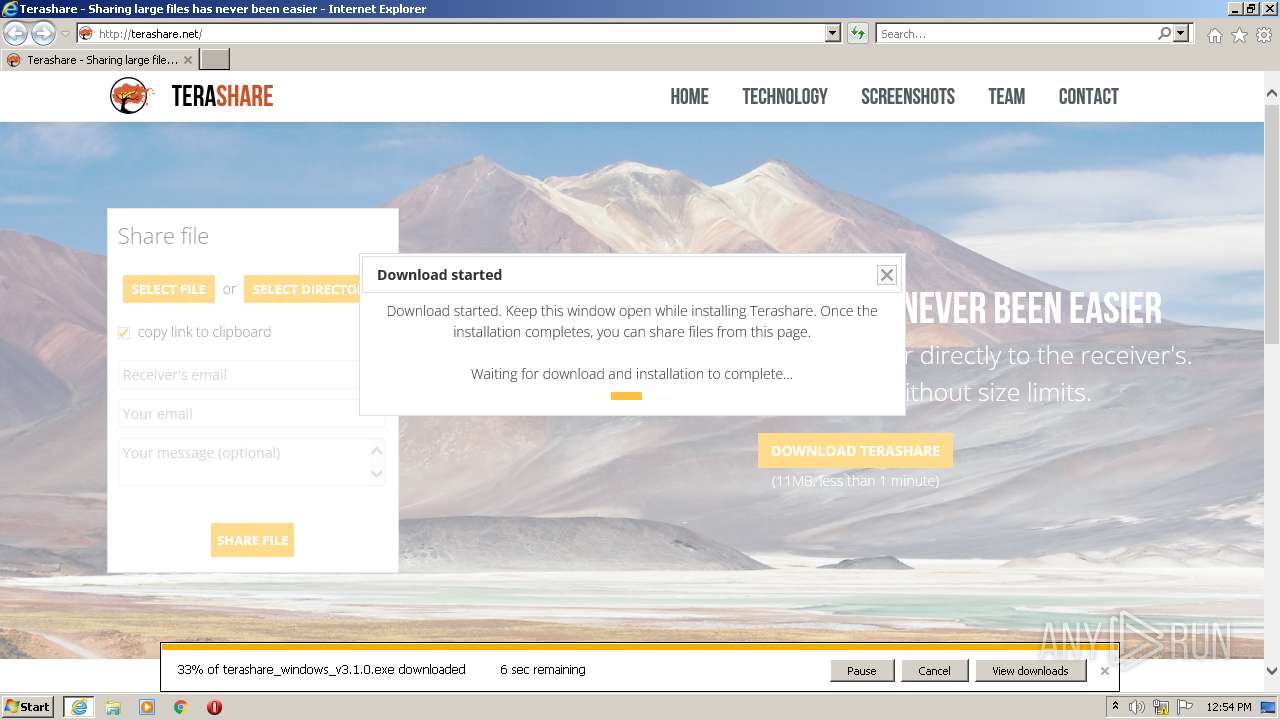
Loads Python modules
- terashare.exe (PID: 968)
INFO
Modifies the phishing filter of IE
- iexplore.exe (PID: 3708)
Drops the executable file immediately after the start
- iexplore.exe (PID: 3708)
- iexplore.exe (PID: 2432)
Application launched itself
- iexplore.exe (PID: 3708)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2432)
- iexplore.exe (PID: 3708)
Checks supported languages
- terashare_windows_v3.1.0.exe (PID: 3268)
- terashare.exe (PID: 968)
Reads the machine GUID from the registry
- terashare_windows_v3.1.0.exe (PID: 3268)
- terashare.exe (PID: 968)
Process checks LSA protection
- terashare_windows_v3.1.0.exe (PID: 3268)
- terashare.exe (PID: 968)
Reads Environment values
- terashare_windows_v3.1.0.exe (PID: 3268)
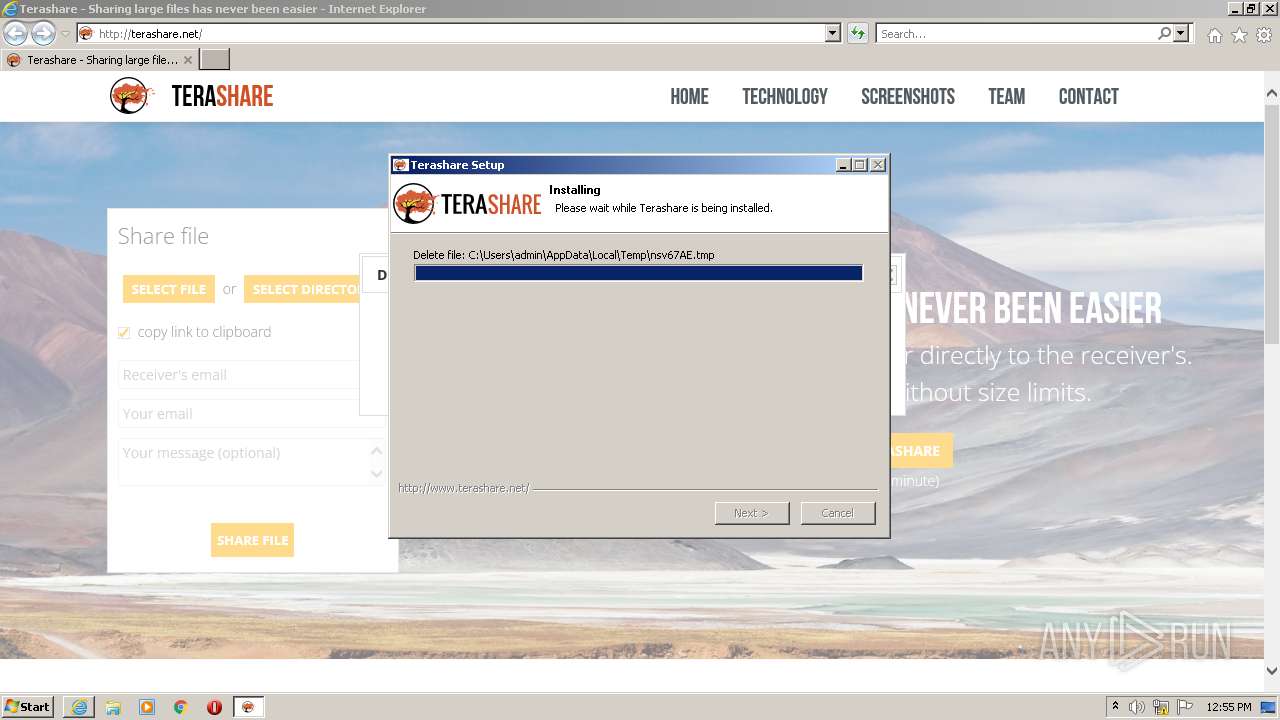
Creates a file in a temporary directory
- terashare_windows_v3.1.0.exe (PID: 3268)
- terashare.exe (PID: 968)
Drops a file that was compiled in debug mode
- terashare_windows_v3.1.0.exe (PID: 3268)
Dropped object may contain Bitcoin addresses
- terashare_windows_v3.1.0.exe (PID: 3268)
Reads the computer name
- terashare_windows_v3.1.0.exe (PID: 3268)
- terashare.exe (PID: 968)
Creates files in the user directory
- terashare.exe (PID: 968)
- terashare_windows_v3.1.0.exe (PID: 3268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Users\admin\AppData\Roaming\Terashare\terashare.exe" | C:\Users\admin\AppData\Roaming\Terashare\terashare.exe | terashare_windows_v3.1.0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3708 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3268 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\terashare_windows_v3.1.0.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\terashare_windows_v3.1.0.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3708 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.bing.com/ck/a?!&&p=9917f24699d80e68JmltdHM9MTY2ODY0MzIwMCZpZ3VpZD0yODg0YmM3NC04Nzk4LTYzNzctMDcxNC1hYzlmODYyNzYyMjcmaW5zaWQ9NTE3OQ&ptn=3&hsh=3&fclid=2884bc74-8798-6377-0714-ac9f86276227&psq=terrashare&u=a1aHR0cDovL3RlcmFzaGFyZS5uZXQv&ntb=1" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
15 898
Read events
15 729
Write events
166
Delete events
3
Modification events
| (PID) Process: | (3708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30997123 | |||
| (PID) Process: | (3708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30997123 | |||
| (PID) Process: | (3708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
53
Suspicious files
22
Text files
974
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:E42F10CF2B0752C2A424931DA8477CA7 | SHA256:F6745241B65638C874E5A8B902164CA09AFA6099F06FA2EAB8270FB30BE2160C | |||
| 2432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\a[1].htm | html | |
MD5:061B44BF5C288CB2022D39014FA8D933 | SHA256:92D9697176F986CA85B68AC6D7ABCE9726A4EBC528A90F552BFB0C66A38DEEED | |||
| 3708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:8685BA159996D66801EC6DA200E82641 | SHA256:C9E4A2E7DA1E6B0D676DACD73FD7EF4F6951C93BA9B5792B7E25BABE770F283E | |||
| 2432 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EQBIIZYK.txt | text | |
MD5:68C0BDB7FE5657A51E6B1C72F5EB3818 | SHA256:A12EE69B3517D47AAF80D3E1AA2578DABB430E2640561C9D6A04539F7CDEE56B | |||
| 2432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\3TGYM1Y3.htm | html | |
MD5:D3EF99A35B8F1396AD03806DB8B83C71 | SHA256:027FAEF6D43FD45B7C2D98DE79104AC39FFC21209E74E4F4C5A16543C6E5A439 | |||
| 3708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:CFFDF65FEA11C81B41FDEDA67640C5C4 | SHA256:7FDE3766729A641537E333F764E4153CD31C10B5D85DFEC019AFE1BE808AF93C | |||
| 3708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\imagestore\f7ruq93\imagestore.dat | binary | |
MD5:93082FD95FB158075FE31006EB87A214 | SHA256:FBE77FE43194303317C6BA4BA52868C706BB922FBCC2D8A27BC30F7FAF5489D6 | |||
| 3708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\reset[1].css | text | |
MD5:7EB823460F91FAC00E137BE59A5E1A13 | SHA256:40309581A71A88A4ADA93A85B2D971324DBA41086512700BD6984D091C3ED858 | |||
| 3708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
58
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
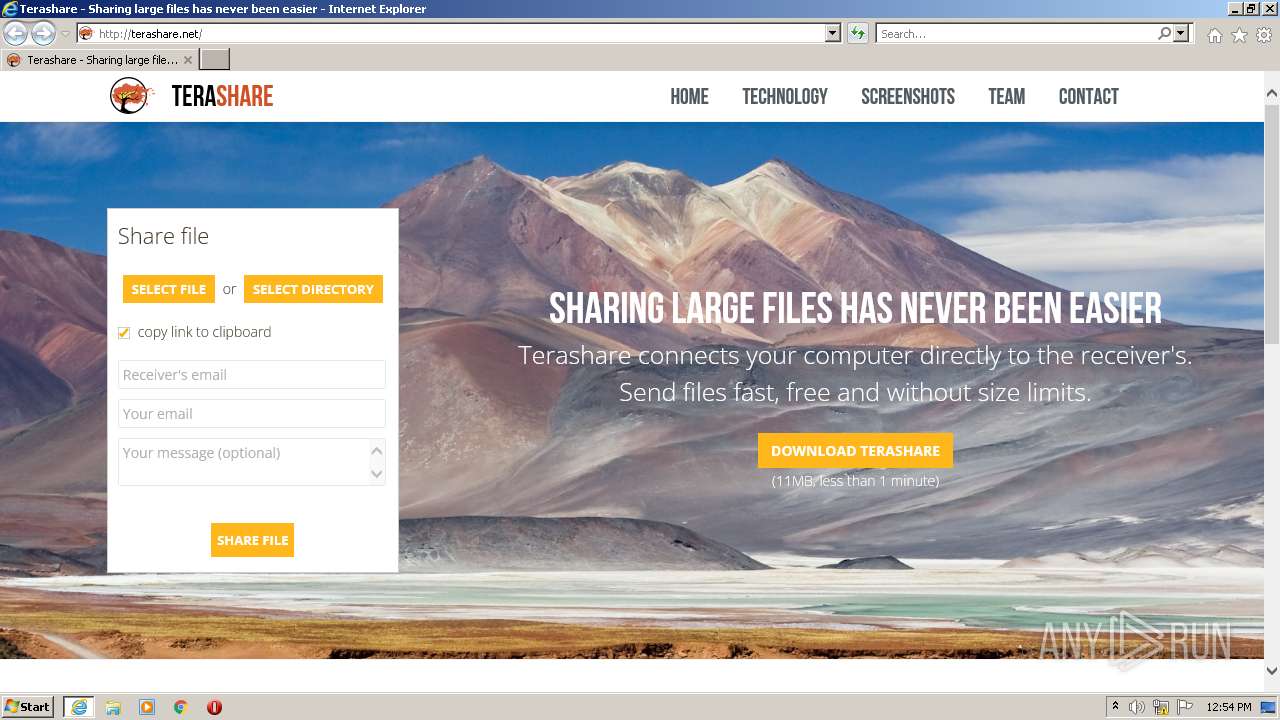
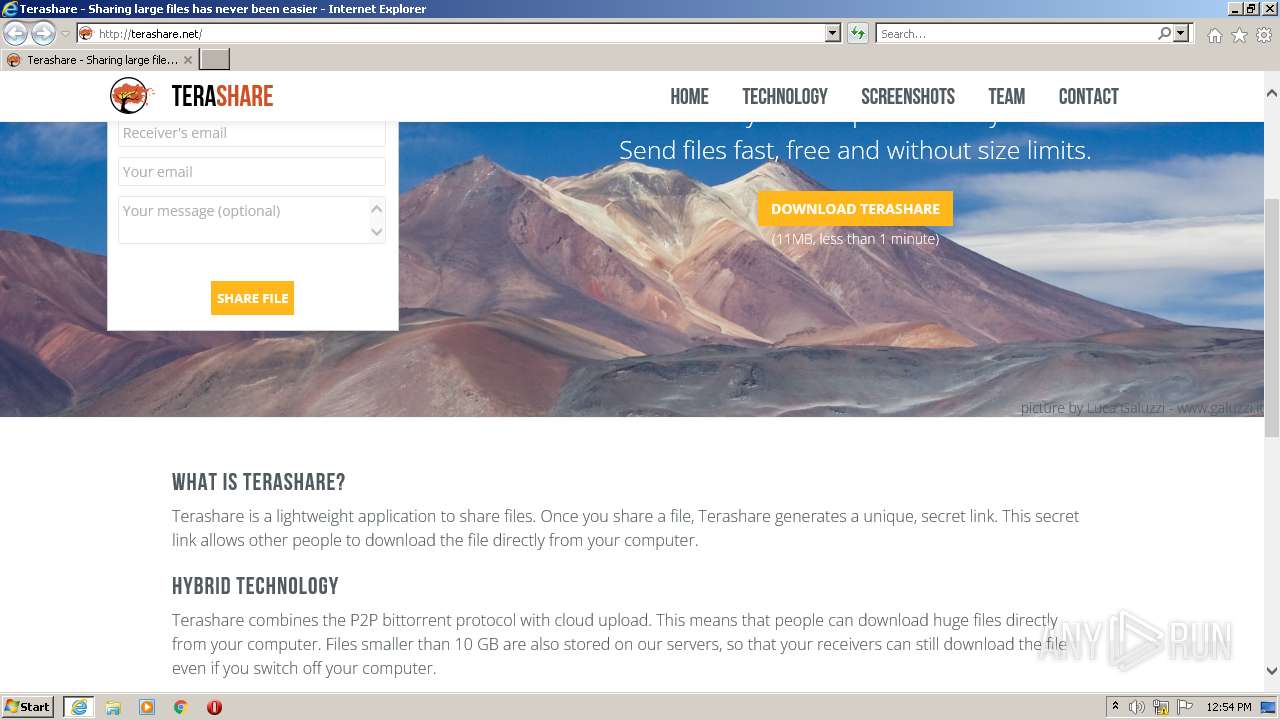
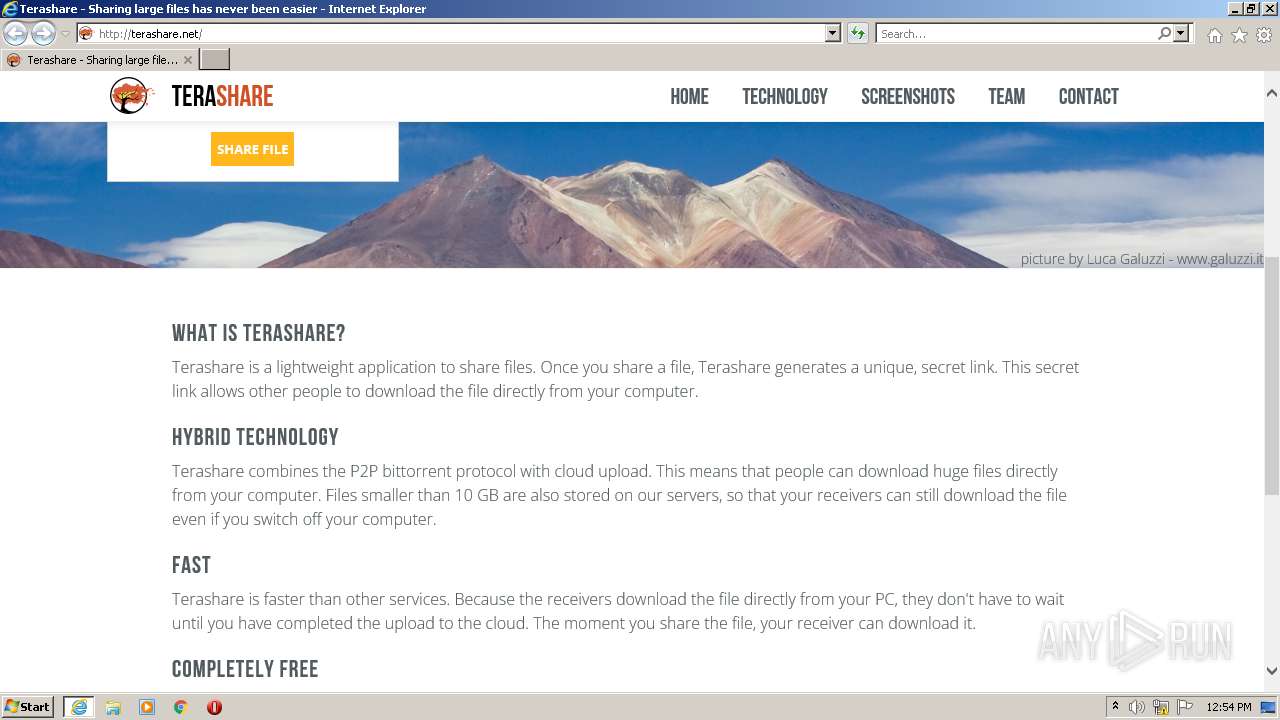
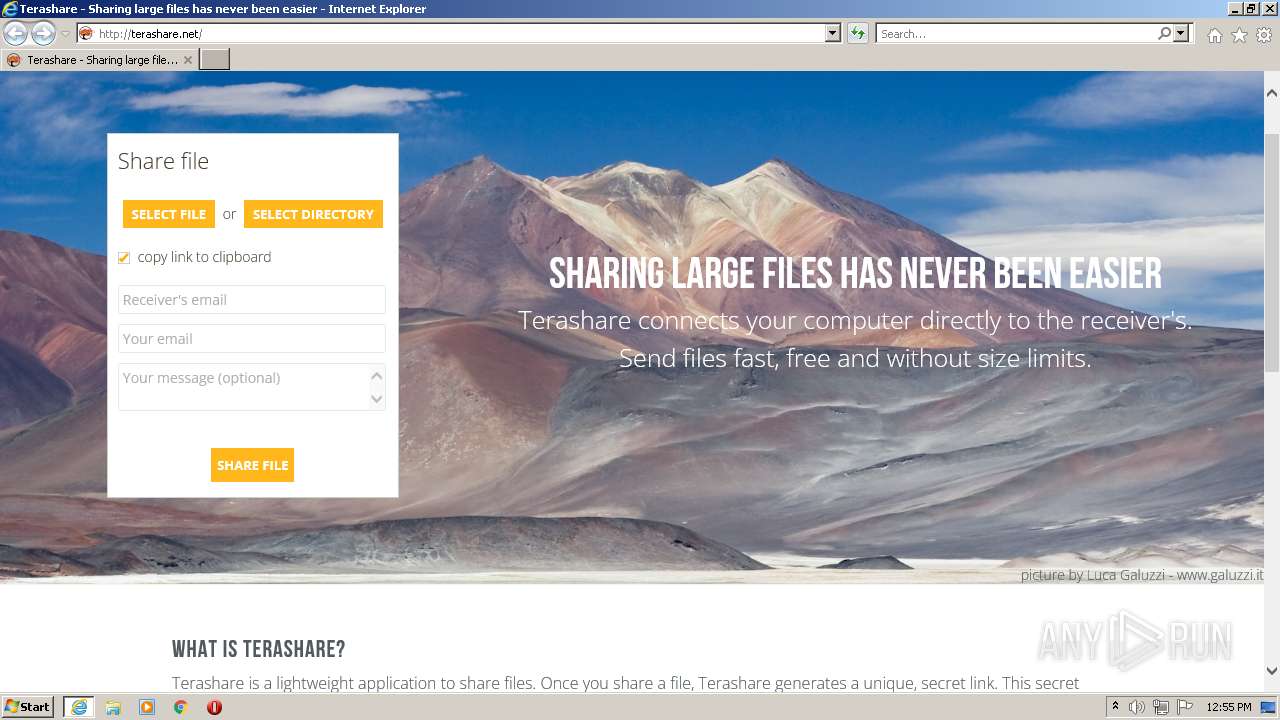
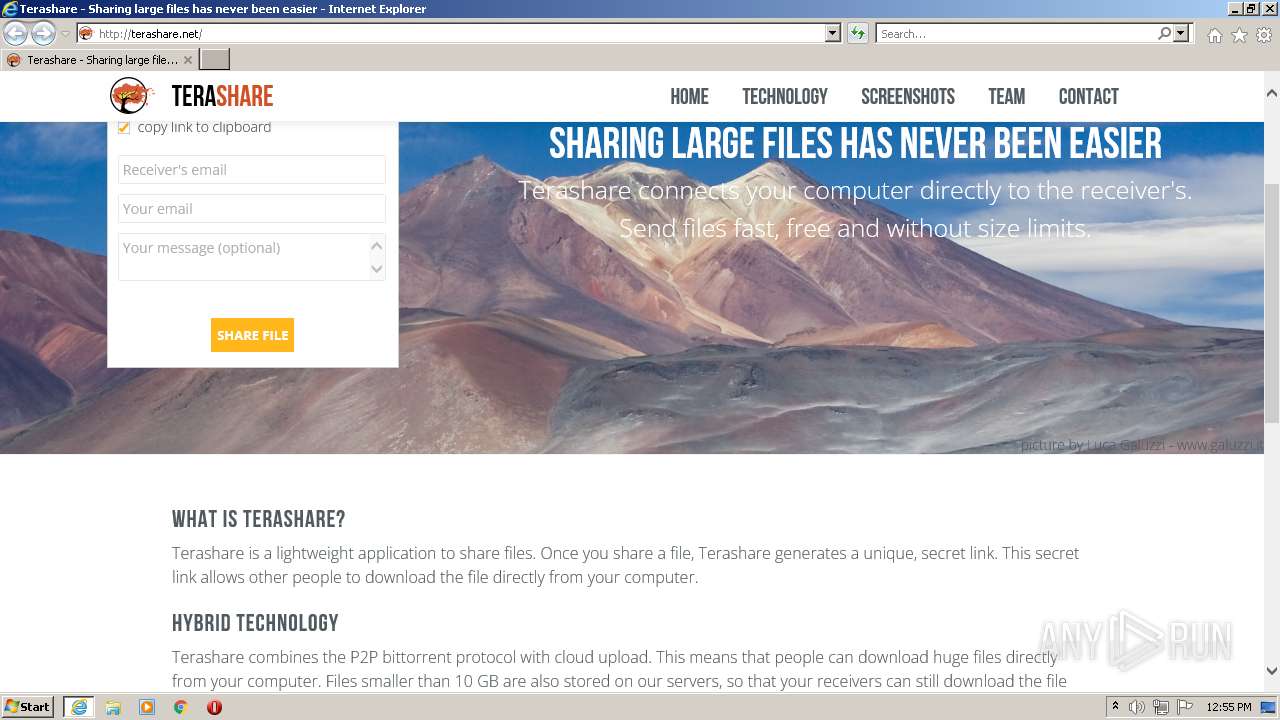
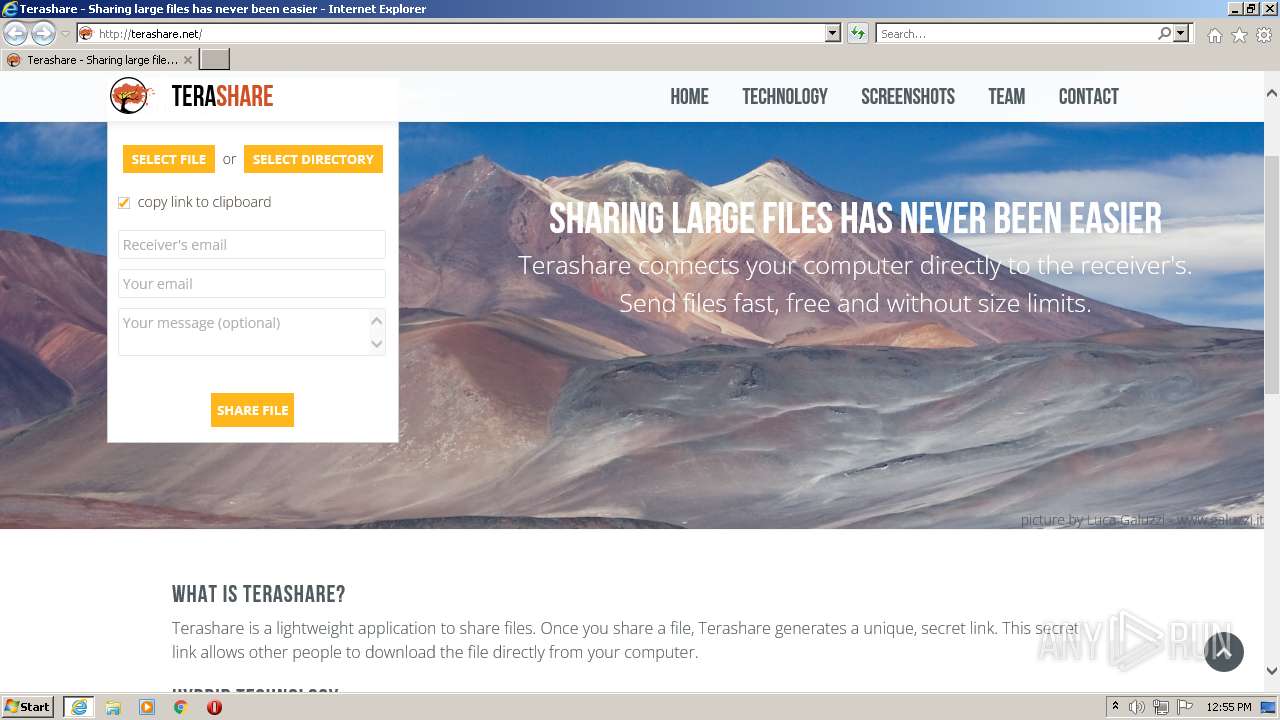
2432 | iexplore.exe | GET | 200 | 146.185.172.63:80 | http://terashare.net/static/css/skeleton.css?v=1 | NL | text | 9.61 Kb | suspicious |
2432 | iexplore.exe | GET | 200 | 146.185.172.63:80 | http://terashare.net/ | NL | html | 25.1 Kb | suspicious |
2432 | iexplore.exe | GET | — | 146.185.172.63:80 | http://terashare.net/static/css/style.css?v=1 | NL | — | — | suspicious |
2432 | iexplore.exe | GET | 200 | 146.185.172.63:80 | http://terashare.net/static/css/jquery-ui.min.css?v=1 | NL | text | 28.5 Kb | suspicious |
2432 | iexplore.exe | GET | 200 | 146.185.172.63:80 | http://terashare.net/static/css/font-awesome.css?v=1 | NL | text | 2.49 Kb | suspicious |
2432 | iexplore.exe | GET | — | 146.185.172.63:80 | http://terashare.net/static/js/external/jquery.form.js?v=1 | NL | — | — | suspicious |
2432 | iexplore.exe | GET | — | 146.185.172.63:80 | http://terashare.net/static/js/external/jquery-ui.min.js?v=1 | NL | — | — | suspicious |
2432 | iexplore.exe | GET | — | 146.185.172.63:80 | http://terashare.net/static/css/shortcodes.css?v=1 | NL | — | — | suspicious |
2432 | iexplore.exe | GET | 200 | 146.185.172.63:80 | http://terashare.net/static/js/external/jquery.min.js?v=1 | NL | text | 53.1 Kb | suspicious |
3708 | iexplore.exe | GET | 200 | 8.253.207.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c5ee03edacea2f03 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2432 | iexplore.exe | 13.107.22.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3708 | iexplore.exe | 13.107.22.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2432 | iexplore.exe | 151.101.2.217:443 | cdn.ravenjs.com | FASTLY | US | suspicious |
2432 | iexplore.exe | 104.18.20.226:80 | ocsp2.globalsign.com | CLOUDFLARENET | — | shared |
2432 | iexplore.exe | 142.250.181.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2432 | iexplore.exe | 142.250.186.35:80 | crl.pki.goog | GOOGLE | US | whitelisted |
3708 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2432 | iexplore.exe | 104.18.21.226:80 | ocsp2.globalsign.com | CLOUDFLARENET | — | shared |
2432 | iexplore.exe | 142.250.186.99:443 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3708 | iexplore.exe | 146.185.172.63:80 | terashare.net | DIGITALOCEAN-ASN | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
terashare.net |
| suspicious |
cdn.ravenjs.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2432 | iexplore.exe | Executable code was detected | ET SHELLCODE Common 0a0a0a0a Heap Spray String |