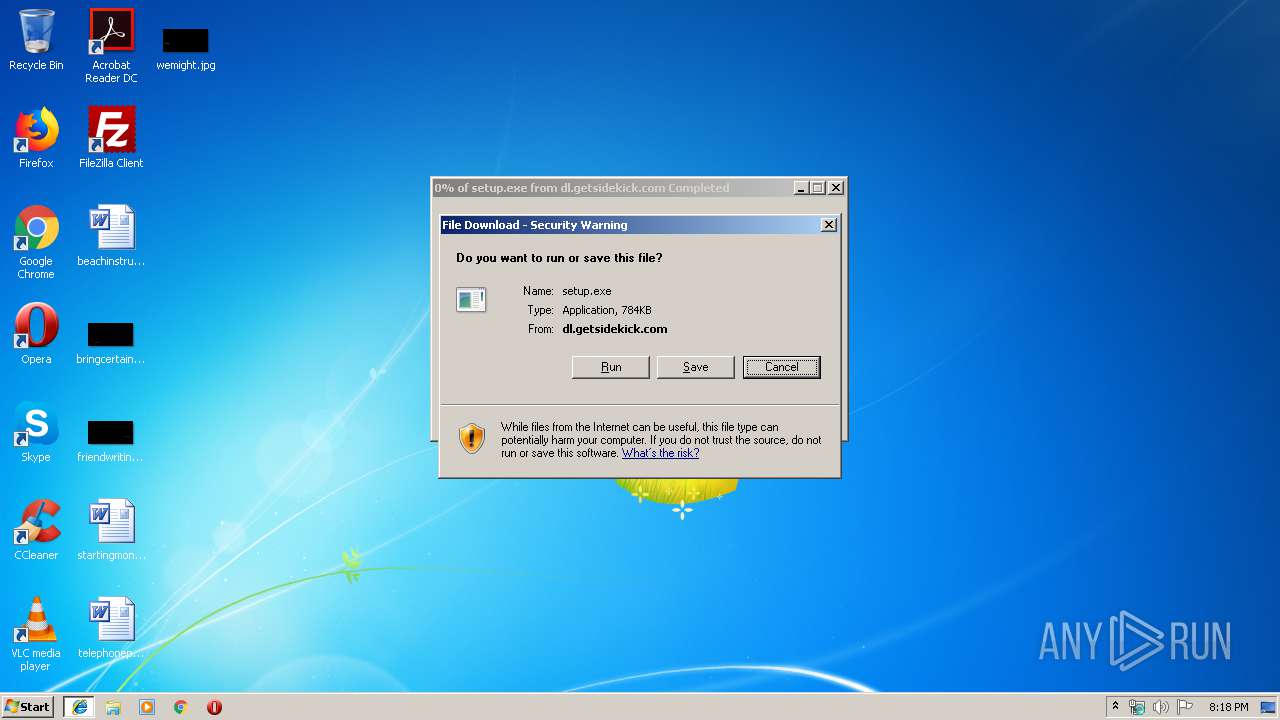
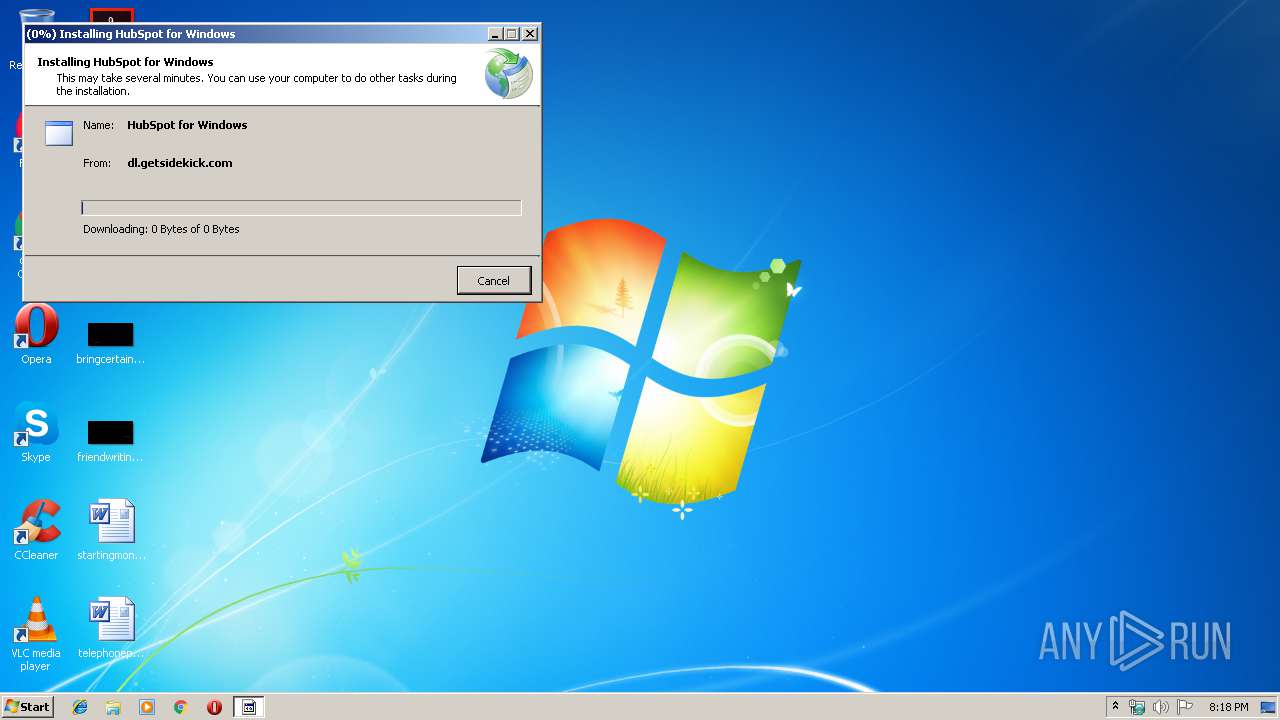
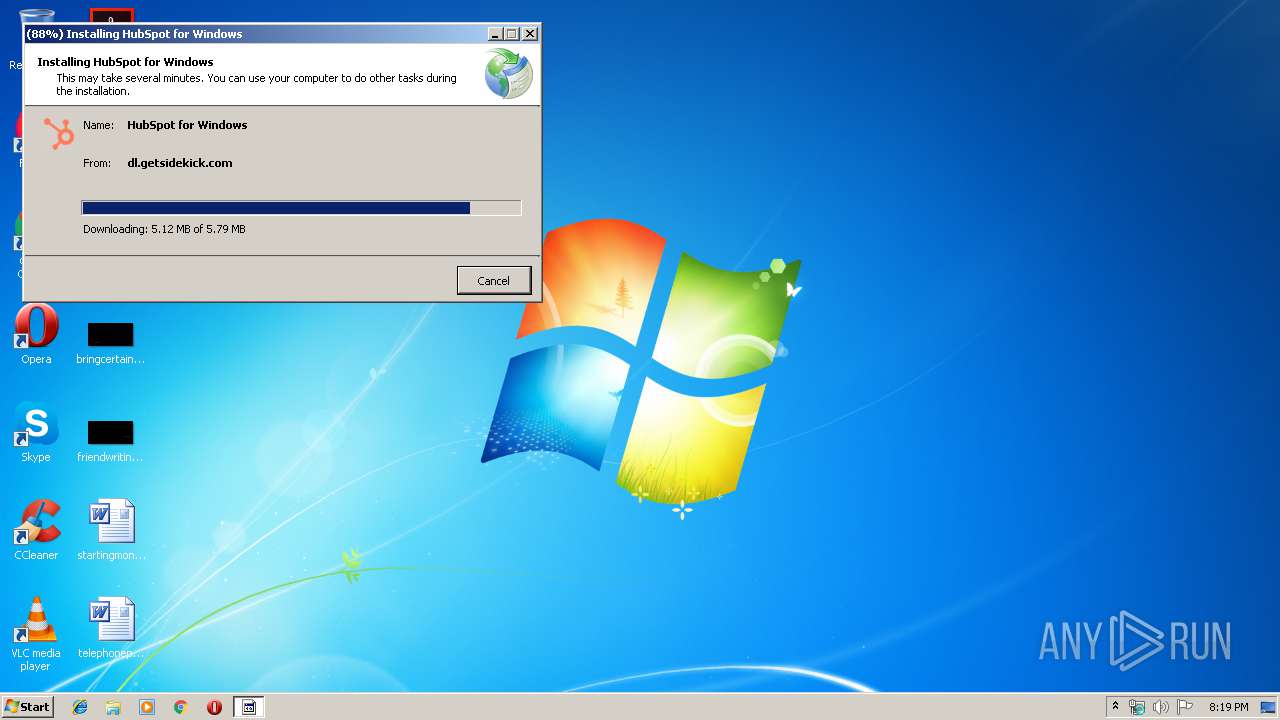
| URL: | https://dl.getsidekick.com/trayapp/setup.exe |
| Full analysis: | https://app.any.run/tasks/7c545654-7bf1-46eb-8413-728906fb8b23 |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2019, 19:18:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F5FF629024BC7984B100325F47E4C3C6 |
| SHA1: | 7AC236C6D9CF2511CA66C2FE7969CAE24A38ABFD |
| SHA256: | 43F9C9256E68DF98298D9B0D0A307CC5A22B035DC8DA8FB60F764BF6015418C8 |
| SSDEEP: | 3:N8RnRL2OMGIEcEVT4A:21RL2OMGcE94A |
MALICIOUS
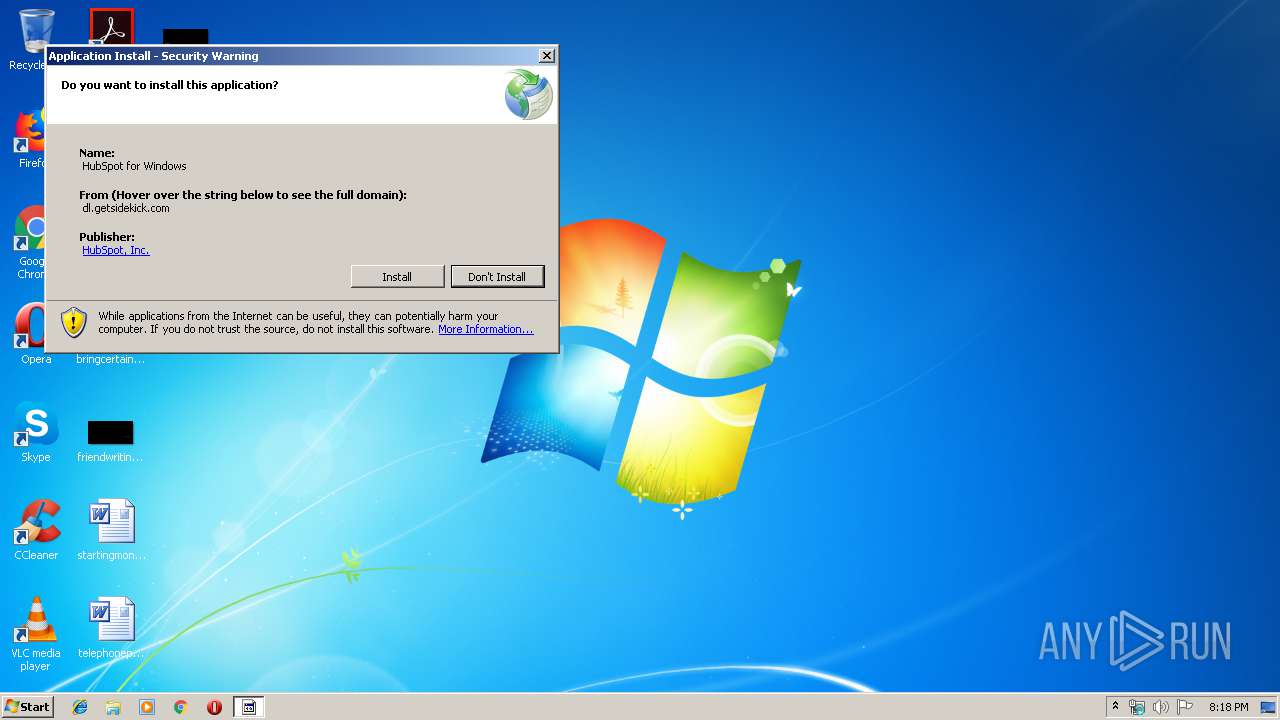
Loads dropped or rewritten executable
- dfsvc.exe (PID: 3956)
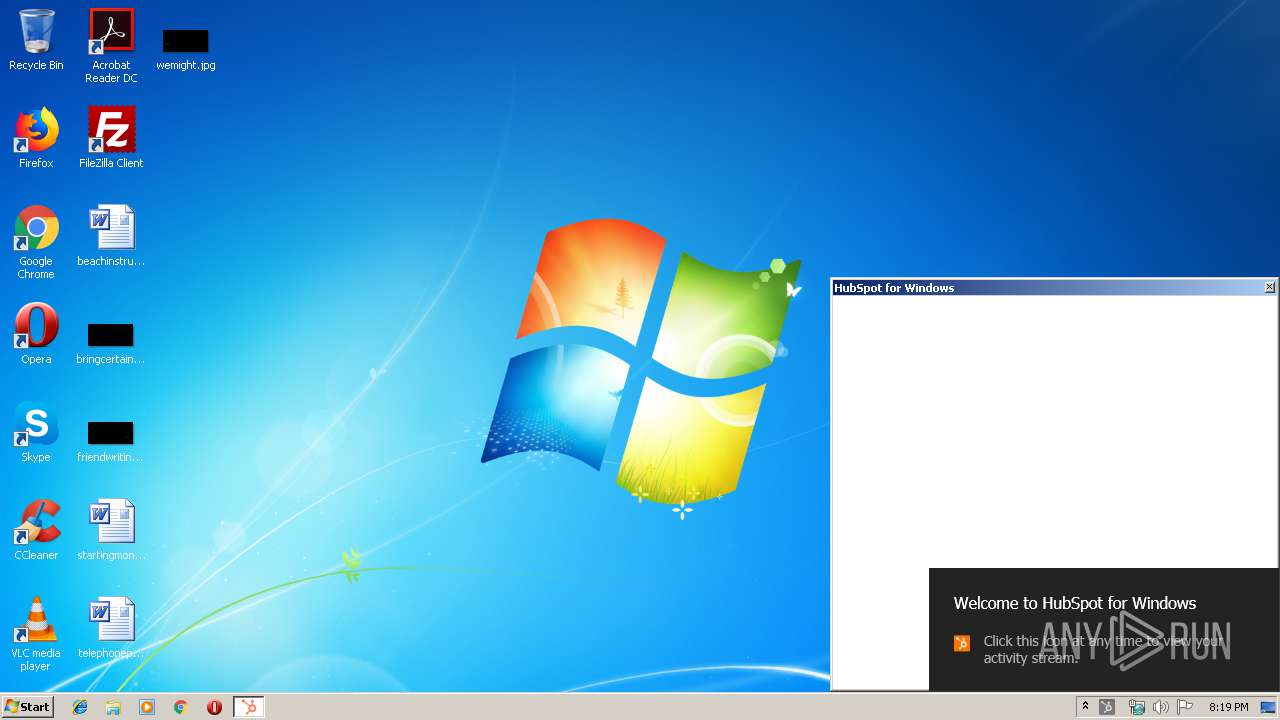
- SidekickTrayWPF.exe (PID: 3488)
Application was dropped or rewritten from another process
- SidekickTrayWPF.exe (PID: 3488)
- setup[1].exe (PID: 3116)
Changes settings of System certificates
- dfsvc.exe (PID: 3956)
Changes the autorun value in the registry
- SidekickTrayWPF.exe (PID: 3488)
SUSPICIOUS
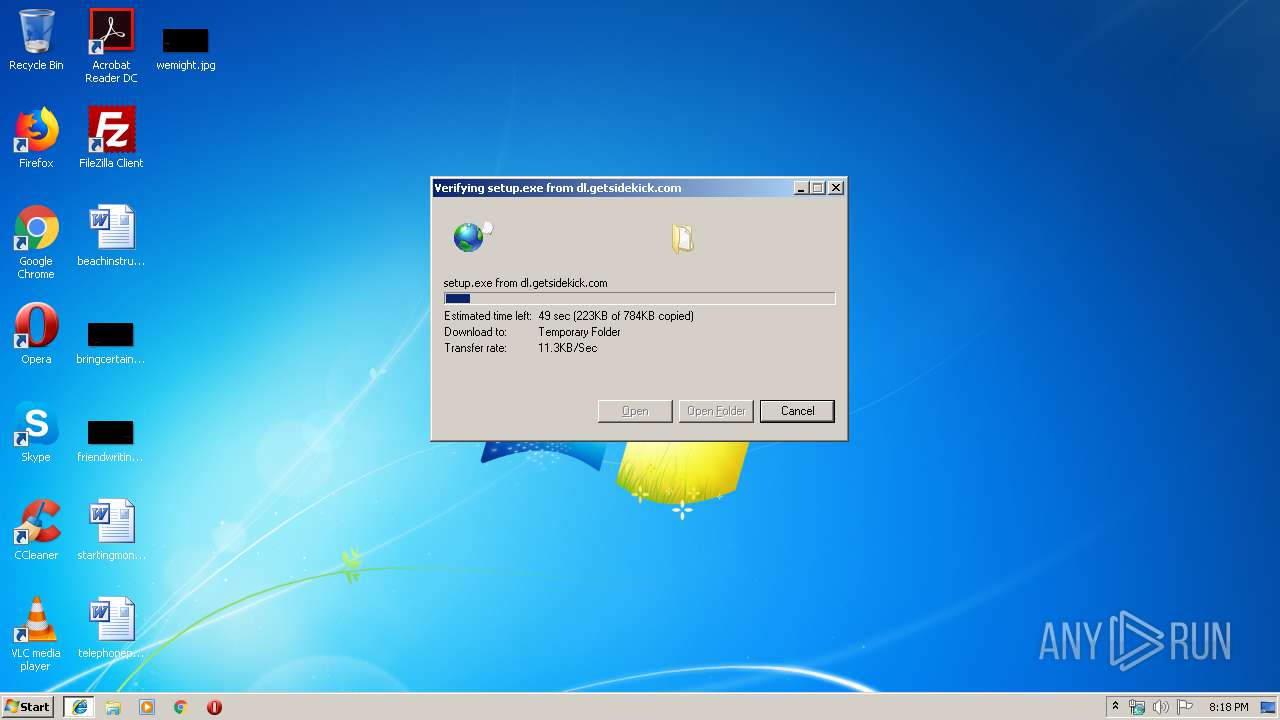
Executable content was dropped or overwritten
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 3404)
- dfsvc.exe (PID: 3956)
Reads Internet Cache Settings
- dfsvc.exe (PID: 3956)
- SidekickTrayWPF.exe (PID: 3488)
Creates files in the user directory
- setup[1].exe (PID: 3116)
- dfsvc.exe (PID: 3956)
- SidekickTrayWPF.exe (PID: 3488)
Reads Environment values
- dfsvc.exe (PID: 3956)
- SidekickTrayWPF.exe (PID: 3488)
Reads internet explorer settings
- dfsvc.exe (PID: 3956)
- SidekickTrayWPF.exe (PID: 3488)
Creates a software uninstall entry
- dfsvc.exe (PID: 3956)
Creates files in the program directory
- SidekickTrayWPF.exe (PID: 3488)
INFO
Application launched itself
- iexplore.exe (PID: 2932)
Changes internet zones settings
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 2288)
Reads settings of System Certificates
- iexplore.exe (PID: 3404)
- SidekickTrayWPF.exe (PID: 3488)
Creates files in the user directory
- iexplore.exe (PID: 3404)
Reads Internet Cache Settings
- iexplore.exe (PID: 3404)
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 2848)
Manual execution by user
- iexplore.exe (PID: 2288)
Reads internet explorer settings
- iexplore.exe (PID: 2848)
Dropped object may contain Bitcoin addresses
- SidekickTrayWPF.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2288 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2288 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Internet Explorer\iexplore.exe" https://dl.getsidekick.com/trayapp/setup.exe | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3116 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\setup[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\setup[1].exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Exit code: 0 Version: 15.0.27005.2 built by: D15REL Modules
| |||||||||||||||
| 3404 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2932 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
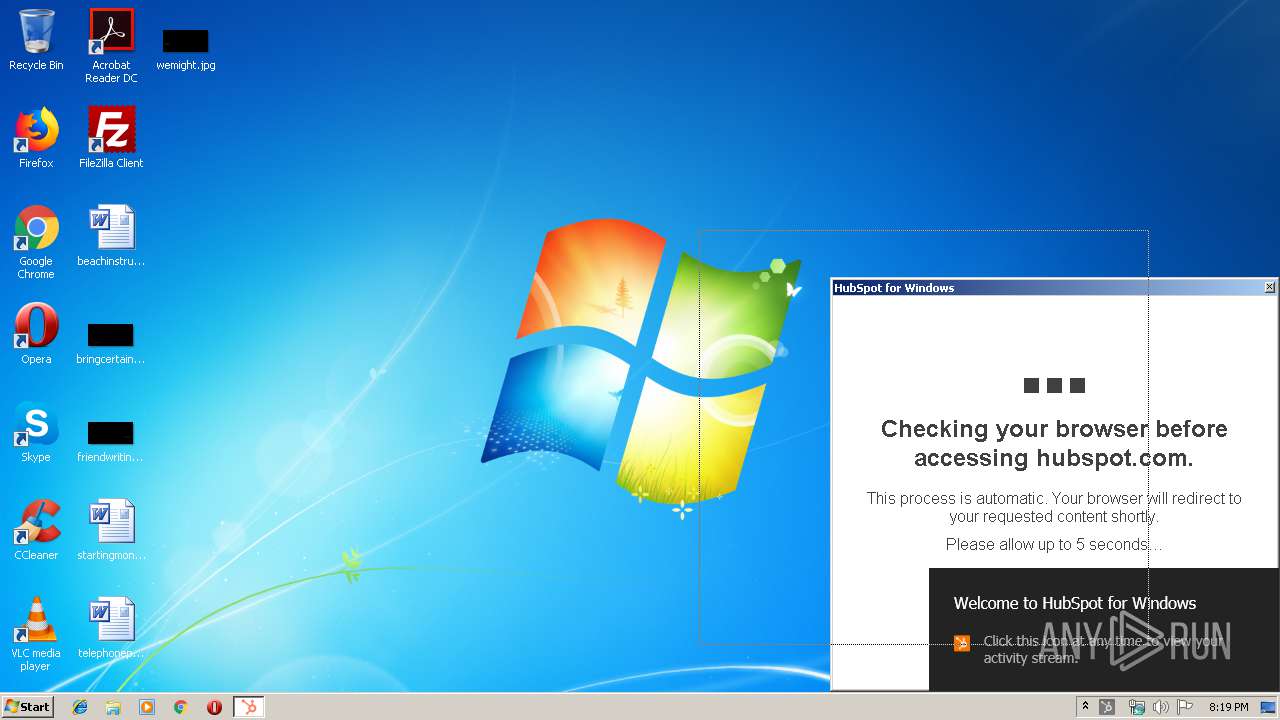
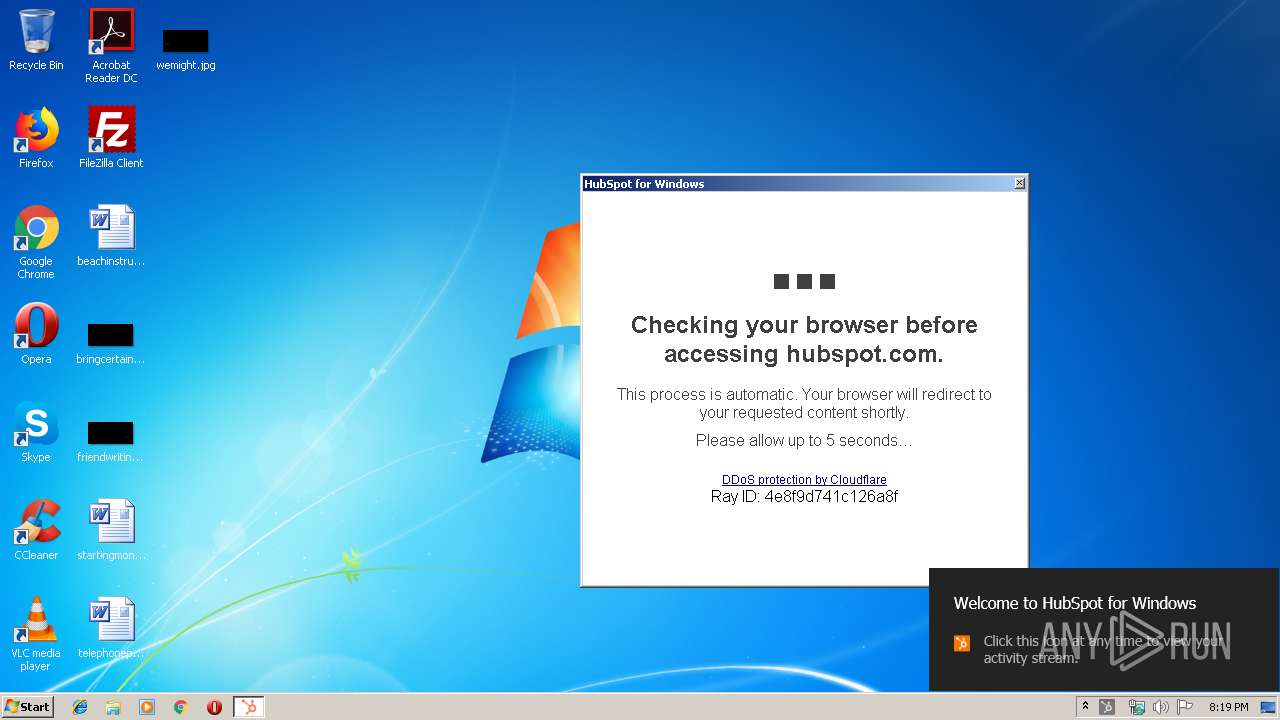
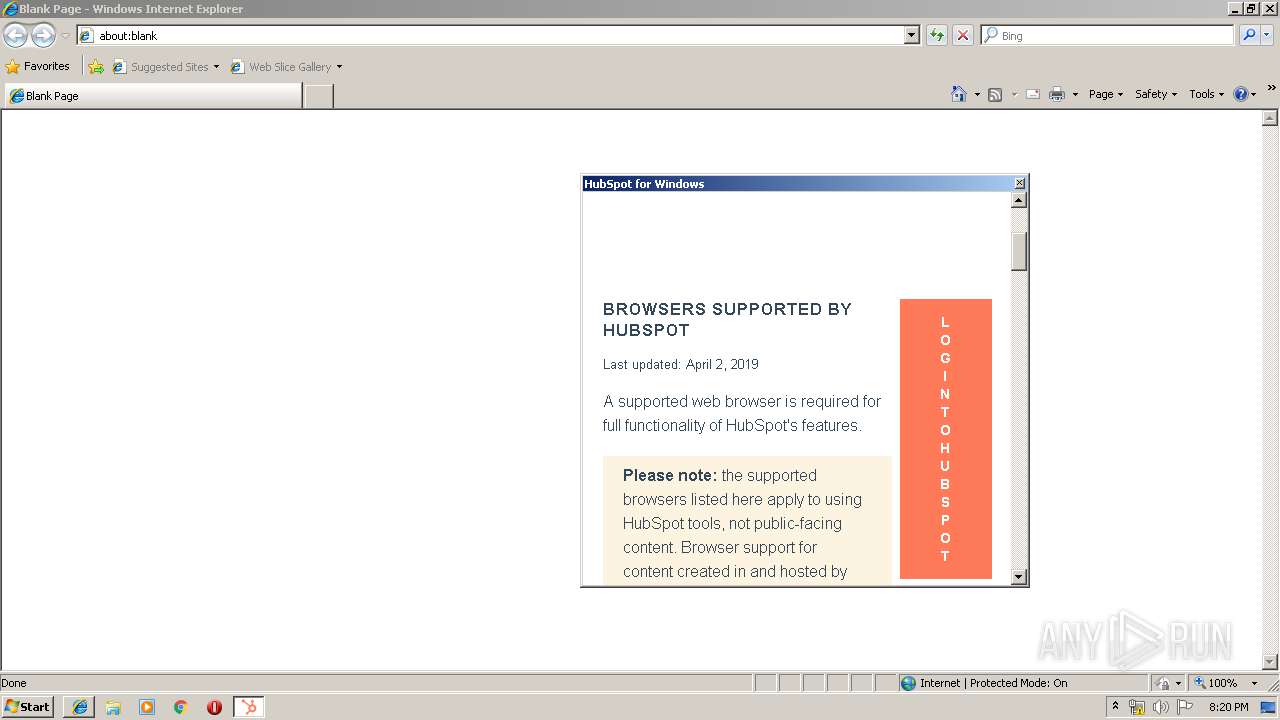
| 3488 | "C:\Users\admin\AppData\Local\Apps\2.0\WCGP2AN2.WQ8\VN3BJXBM.EZM\side..tion_55d9f4e27097afb7_0001.0000_0508a31f4403d499\SidekickTrayWPF.exe" | C:\Users\admin\AppData\Local\Apps\2.0\WCGP2AN2.WQ8\VN3BJXBM.EZM\side..tion_55d9f4e27097afb7_0001.0000_0508a31f4403d499\SidekickTrayWPF.exe | dfsvc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: HubSpot for Windows Exit code: 0 Version: 1.0.0.111 Modules
| |||||||||||||||
| 3956 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe | setup[1].exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
2 003
Read events
1 350
Write events
600
Delete events
53
Modification events
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {E71FE997-91FD-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307060002001200130012003300D601 | |||
Executable files
64
Suspicious files
36
Text files
162
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0082541F2D6649AE.TMP | — | |
MD5:— | SHA256:— | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\B1BB14DI\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\JV5H1XYI\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2932 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF90F3C1BDC59A6E83.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
68
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3956 | dfsvc.exe | GET | 200 | 104.18.10.39:80 | http://cacerts.digicert.com/DigiCertSHA2AssuredIDCodeSigningCA.crt | US | der | 1.30 Kb | whitelisted |
2932 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2288 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3404 | iexplore.exe | 104.16.51.78:443 | dl.getsidekick.com | Cloudflare Inc | US | shared |
2932 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3116 | setup[1].exe | 104.16.51.78:443 | dl.getsidekick.com | Cloudflare Inc | US | shared |
3956 | dfsvc.exe | 104.16.51.78:443 | dl.getsidekick.com | Cloudflare Inc | US | shared |
2288 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3488 | SidekickTrayWPF.exe | 104.17.9.210:443 | static.hsappstatic.net | Cloudflare Inc | US | shared |
3488 | SidekickTrayWPF.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
3488 | SidekickTrayWPF.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3488 | SidekickTrayWPF.exe | 216.58.205.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3488 | SidekickTrayWPF.exe | 172.217.21.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.getsidekick.com |
| unknown |
www.bing.com |
| whitelisted |
cacerts.digicert.com |
| whitelisted |
api.hubapi.com |
| whitelisted |
app.hubspot.com |
| whitelisted |
static.hsappstatic.net |
| whitelisted |
www.google.com |
| malicious |
www.googletagmanager.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|