| File name: | curious.pdf |
| Full analysis: | https://app.any.run/tasks/2e437f6d-a5d1-4205-90d5-8b1395a6ac32 |
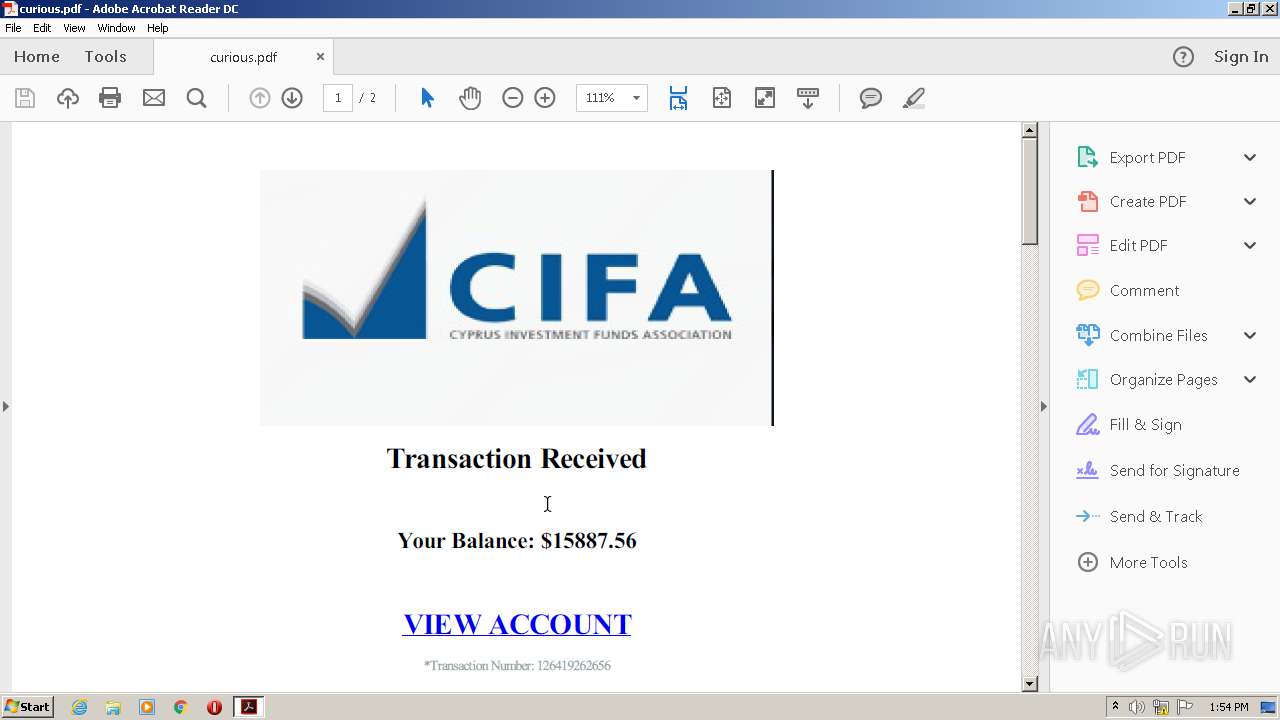
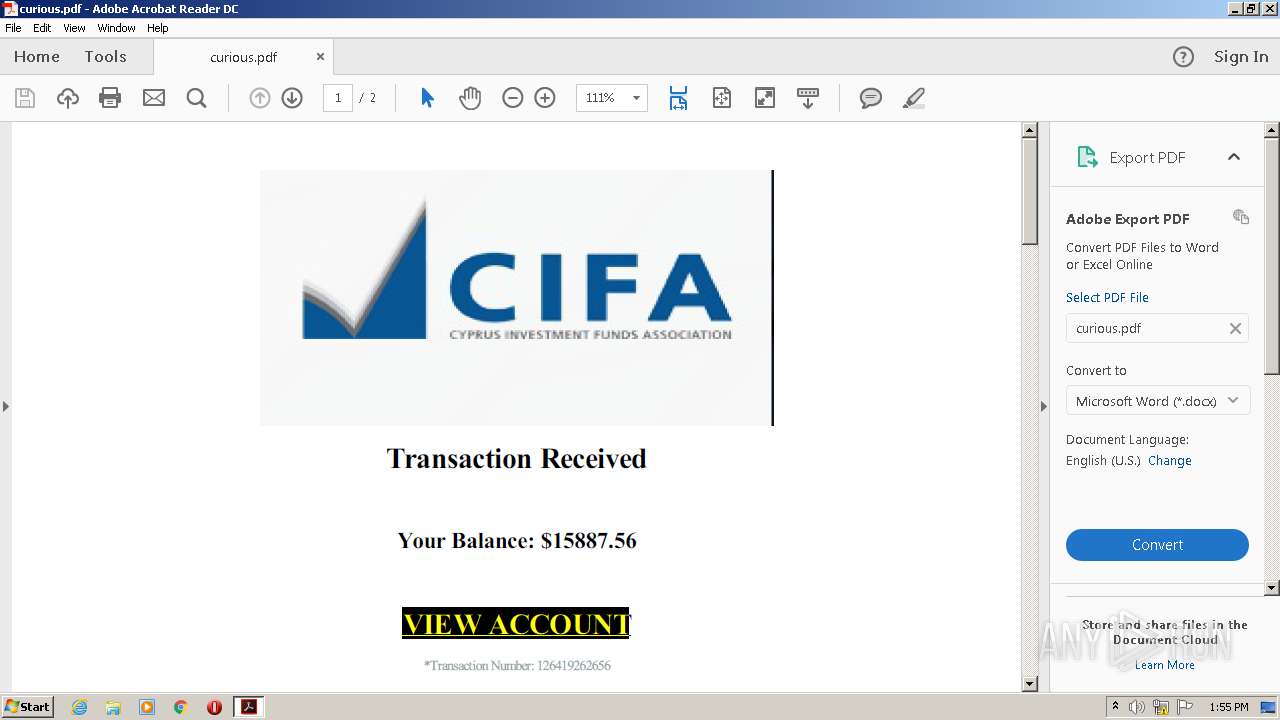
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 12:54:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.4 |
| MD5: | E93277CD22C3DEF305D960FABF986CF9 |
| SHA1: | 07C9DDE356D02AB6CBF716DFA0D7383D06C630E5 |
| SHA256: | 43BDADB5BE592C6F498B1BB742DF307633F8C5EA05AF66AD01619A9F4F4F73D9 |
| SSDEEP: | 768:4fEi9mbnpQwutHDpnWCkOYdxmBhCYIH0mmrPtX2+H2FgnDyFMc:4Z9MzOnTIrmjOUTxopac |
MALICIOUS
No malicious indicators.SUSPICIOUS
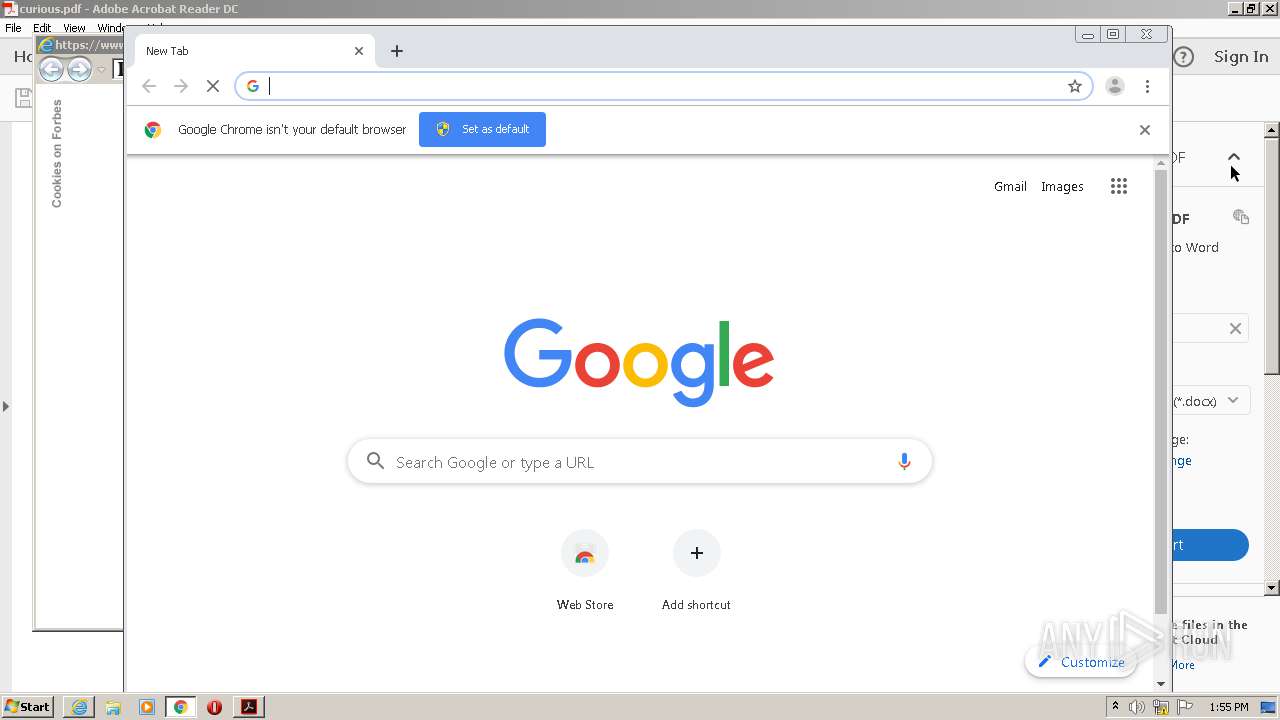
Starts Internet Explorer
- AcroRd32.exe (PID: 1388)
Creates files in the program directory
- AdobeARM.exe (PID: 612)
INFO
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 1388)
Reads the hosts file
- RdrCEF.exe (PID: 1760)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 2400)
Reads Internet Cache Settings
- AcroRd32.exe (PID: 1632)
- iexplore.exe (PID: 608)
- iexplore.exe (PID: 2732)
- AcroRd32.exe (PID: 1388)
Application launched itself
- AcroRd32.exe (PID: 1388)
- iexplore.exe (PID: 608)
- chrome.exe (PID: 2400)
- RdrCEF.exe (PID: 1760)
Reads settings of System Certificates
- iexplore.exe (PID: 2732)
- iexplore.exe (PID: 608)
- AcroRd32.exe (PID: 1388)
Reads internet explorer settings
- iexplore.exe (PID: 2732)
Creates files in the user directory
- iexplore.exe (PID: 2732)
- iexplore.exe (PID: 608)
Manual execution by user
- chrome.exe (PID: 2400)
Changes settings of System certificates
- iexplore.exe (PID: 608)
Adds / modifies Windows certificates
- iexplore.exe (PID: 608)
Changes internet zones settings
- iexplore.exe (PID: 608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.4 |
|---|---|
| Linearized: | No |
| Title: | - |
| Creator: | wkhtmltopdf 0.12.5 |
| Producer: | Qt 4.8.7 |
| CreateDate: | 2020:10:20 11:21:37+03:00 |
| PageCount: | 2 |
Total processes
72
Monitored processes
35
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,15909001087269536406,7142598368624363190,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15174522947992259675 --mojo-platform-channel-handle=3456 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,15909001087269536406,7142598368624363190,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4015838603985103866 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
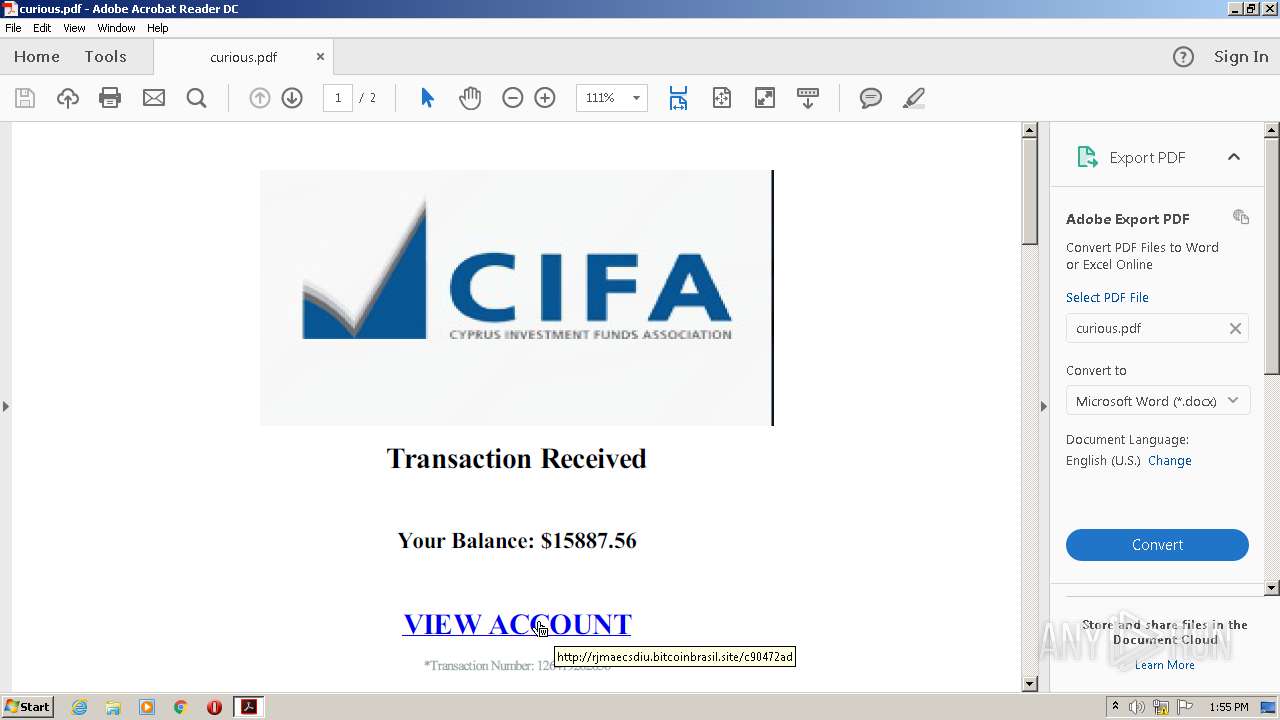
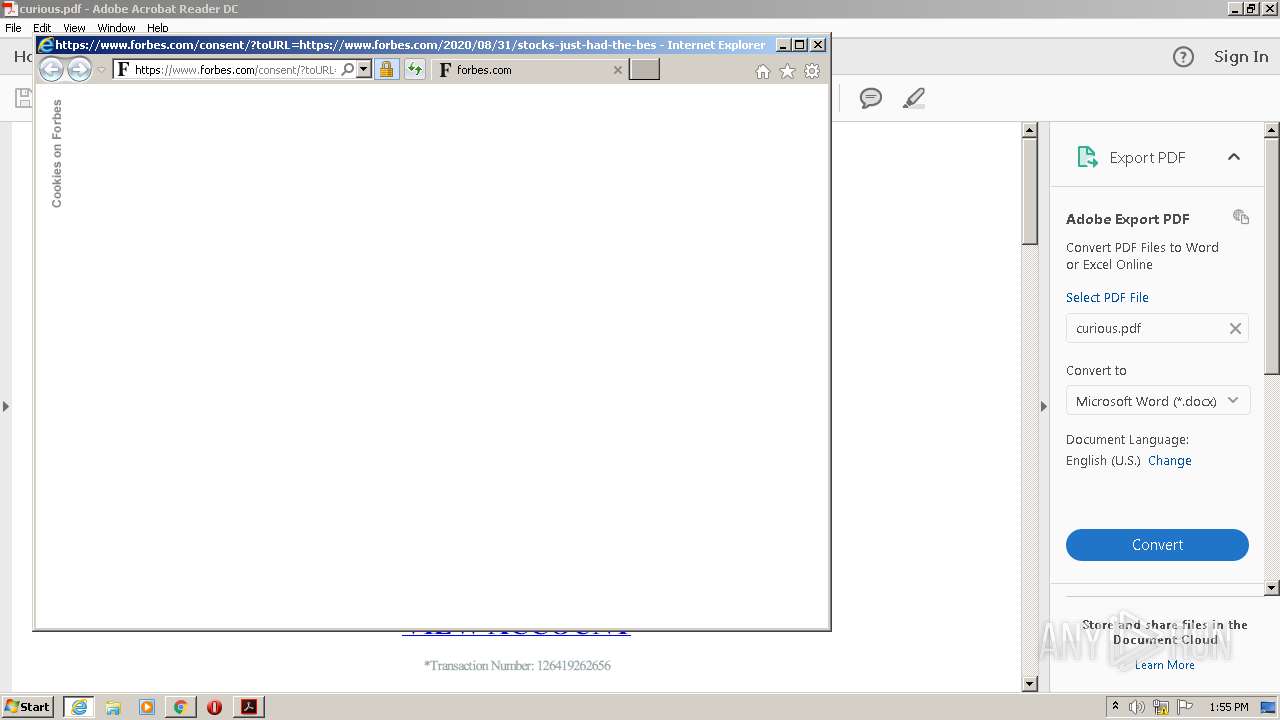
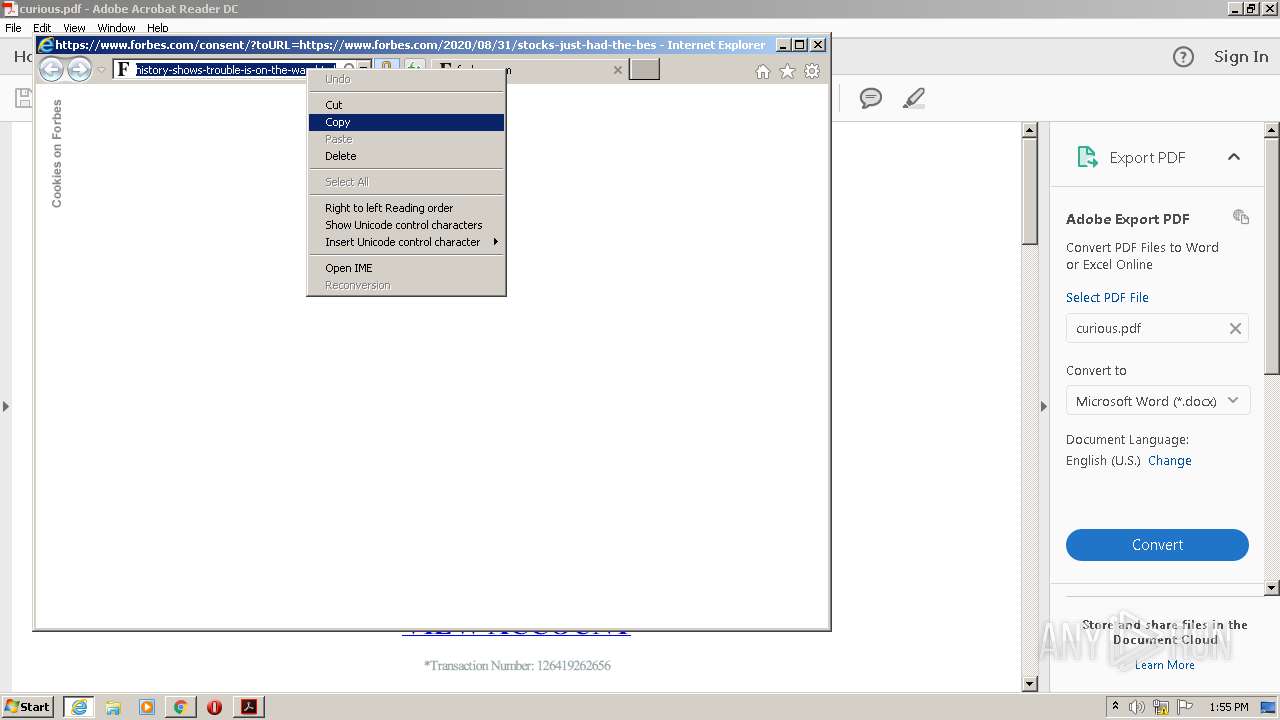
| 608 | "C:\Program Files\Internet Explorer\iexplore.exe" http://rjmaecsdiu.bitcoinbrasil.site/c90472ad | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 612 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2628 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Temp\curious.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\curious.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,15909001087269536406,7142598368624363190,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3301816313362600007 --mojo-platform-channel-handle=1060 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 614
Read events
1 397
Write events
211
Delete events
6
Modification events
| (PID) Process: | (1632) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (1632) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (1632) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (1388) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | AcroRd32.exe |
Value: 10001 | |||
| (PID) Process: | (1388) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000B479293CE0A6D601 | |||
| (PID) Process: | (608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1310757342 | |||
| (PID) Process: | (608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844640 | |||
| (PID) Process: | (608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
196
Text files
157
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1632 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 1632 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rglvtyj_15y8abp_19c.tmp | — | |
MD5:— | SHA256:— | |||
| 1632 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R17oxa97_15y8abo_19c.tmp | — | |
MD5:— | SHA256:— | |||
| 1632 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R19dzcl4_15y8abn_19c.tmp | — | |
MD5:— | SHA256:— | |||
| 1632 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rzi7rvt_15y8abm_19c.tmp | — | |
MD5:— | SHA256:— | |||
| 2732 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab814E.tmp | — | |
MD5:— | SHA256:— | |||
| 2732 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar814F.tmp | — | |
MD5:— | SHA256:— | |||
| 1388 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\Cab815D.tmp | — | |
MD5:— | SHA256:— | |||
| 1388 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\Tar815E.tmp | — | |
MD5:— | SHA256:— | |||
| 1632 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\UserCache.bin | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
181
DNS requests
133
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
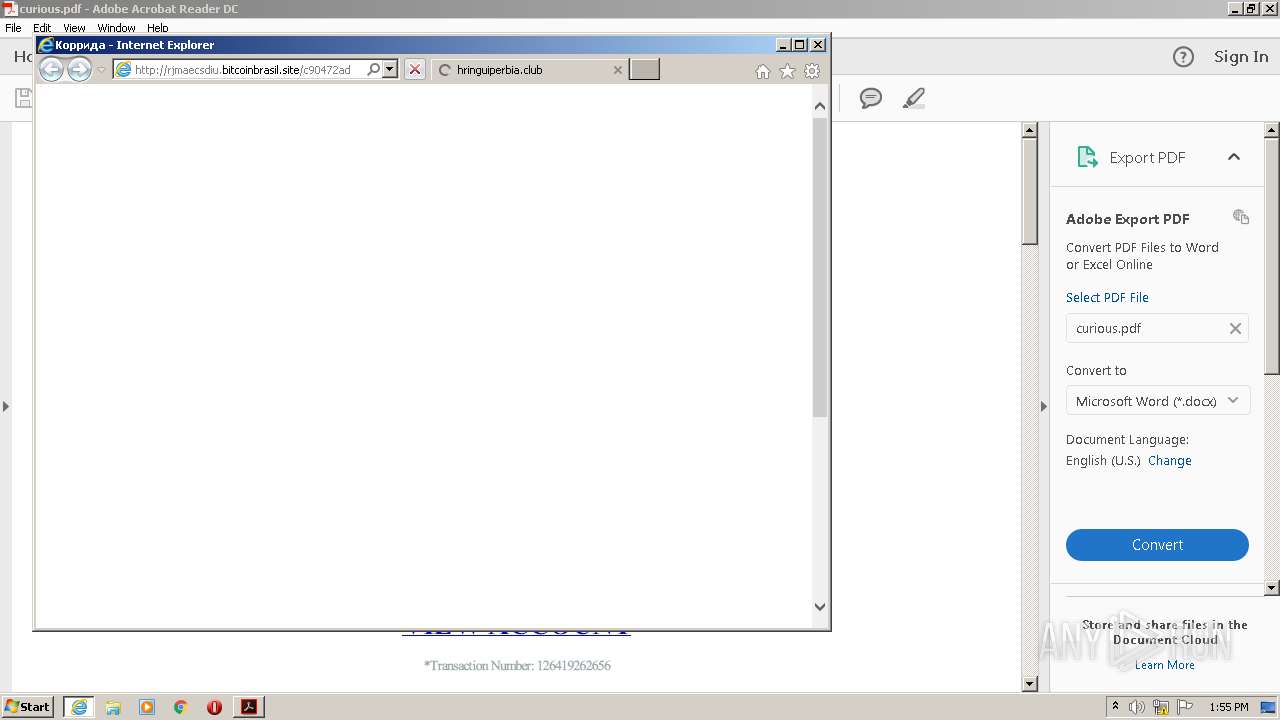
608 | iexplore.exe | GET | 404 | 199.188.206.22:80 | http://rjmaecsdiu.bitcoinbrasil.site/favicon.ico | US | — | — | malicious |
1388 | AcroRd32.exe | GET | 304 | 2.16.107.49:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
1388 | AcroRd32.exe | GET | 304 | 2.16.107.49:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
1388 | AcroRd32.exe | GET | 304 | 2.16.107.49:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2732 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2732 | iexplore.exe | GET | 200 | 199.188.206.22:80 | http://rjmaecsdiu.bitcoinbrasil.site/c90472ad | US | html | 2.85 Kb | malicious |
2732 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
2732 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
2732 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
2732 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2732 | iexplore.exe | 199.188.206.22:80 | rjmaecsdiu.bitcoinbrasil.site | Namecheap, Inc. | US | malicious |
2732 | iexplore.exe | 104.28.15.35:443 | hringuiperbia.club | Cloudflare Inc | US | unknown |
— | — | 199.188.206.22:80 | rjmaecsdiu.bitcoinbrasil.site | Namecheap, Inc. | US | malicious |
1388 | AcroRd32.exe | 2.21.36.203:443 | armmf.adobe.com | GTT Communications Inc. | FR | suspicious |
2732 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1388 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
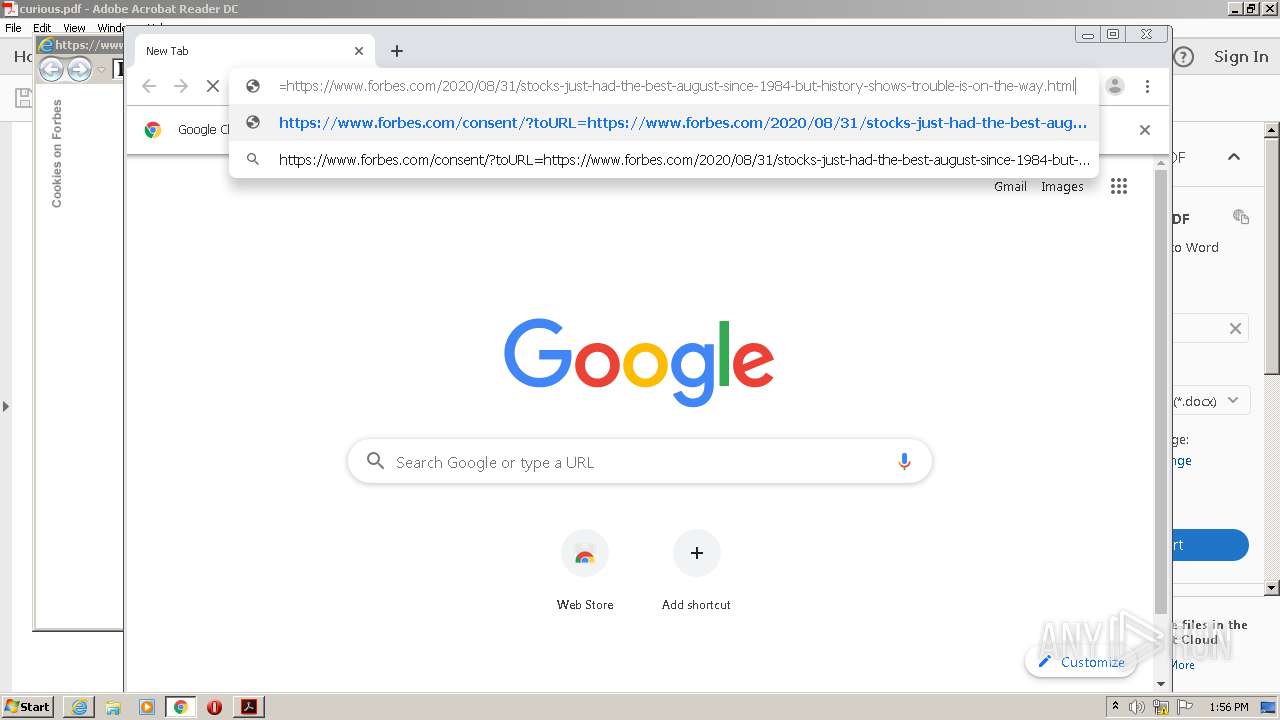
2732 | iexplore.exe | 151.101.2.49:443 | www.forbes.com | Fastly | US | malicious |
2732 | iexplore.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
2732 | iexplore.exe | 99.86.2.84:443 | consent.truste.com | AT&T Services, Inc. | US | malicious |
2732 | iexplore.exe | 192.124.249.23:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rjmaecsdiu.bitcoinbrasil.site |
| malicious |
hringuiperbia.club |
| suspicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.forbes.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
consent.truste.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |