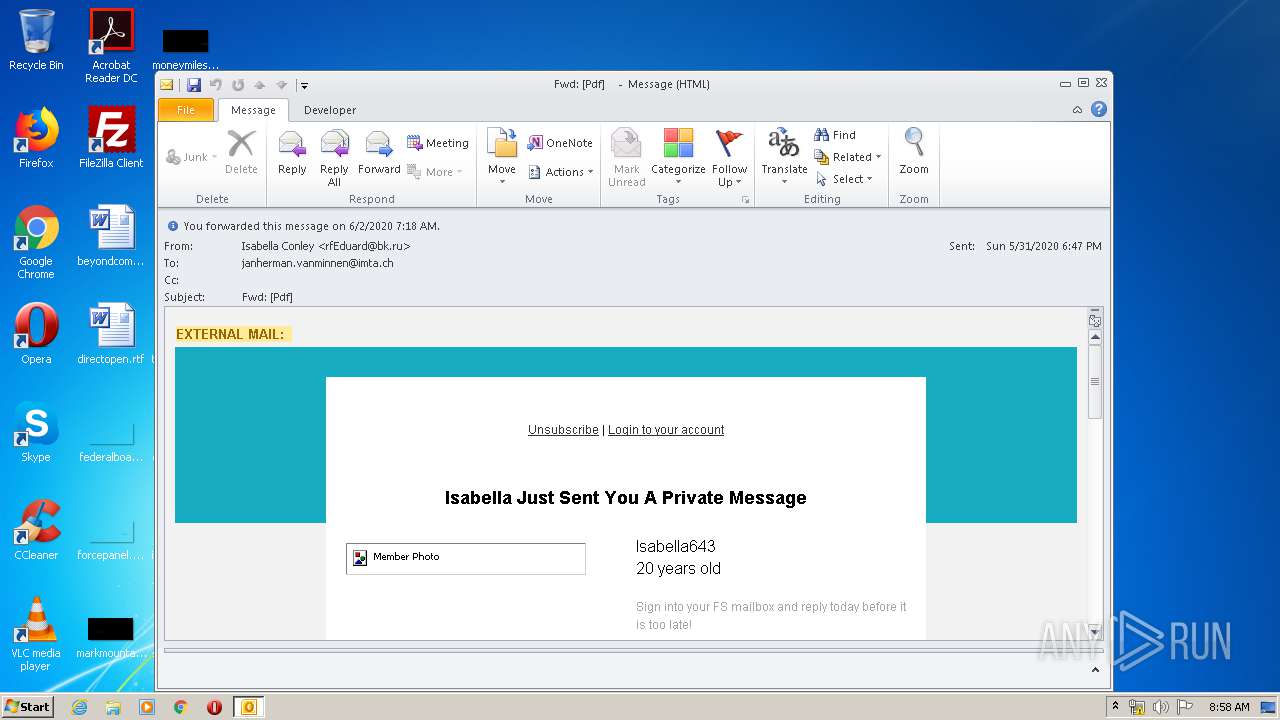
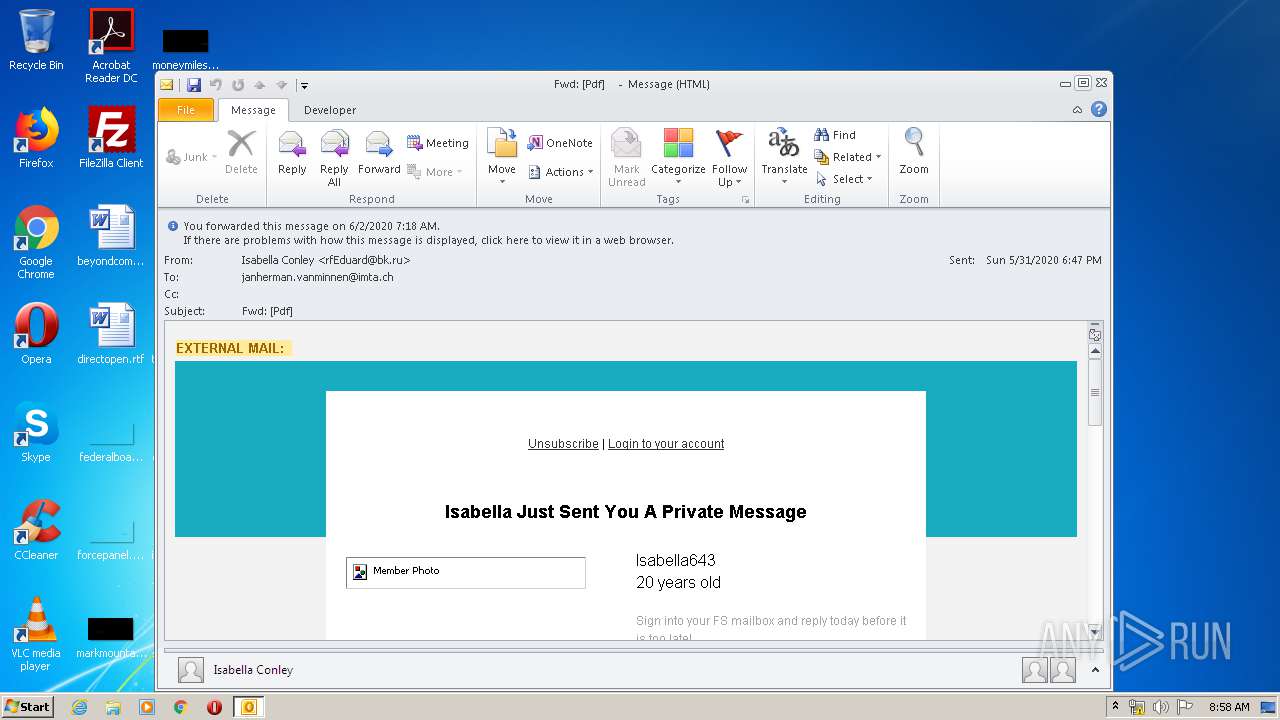
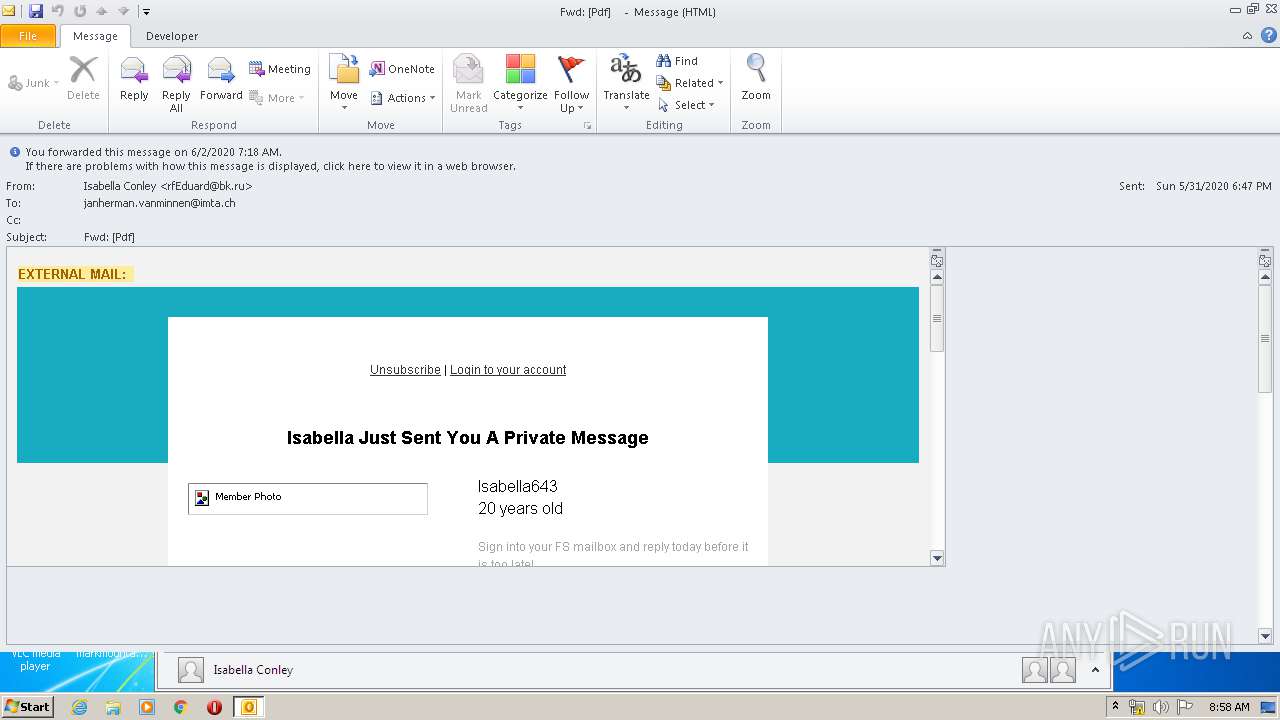
| File name: | Fwd Pdf .msg |
| Full analysis: | https://app.any.run/tasks/9b1ef2dc-7e6f-4bd8-98c1-4d0ce82756e9 |
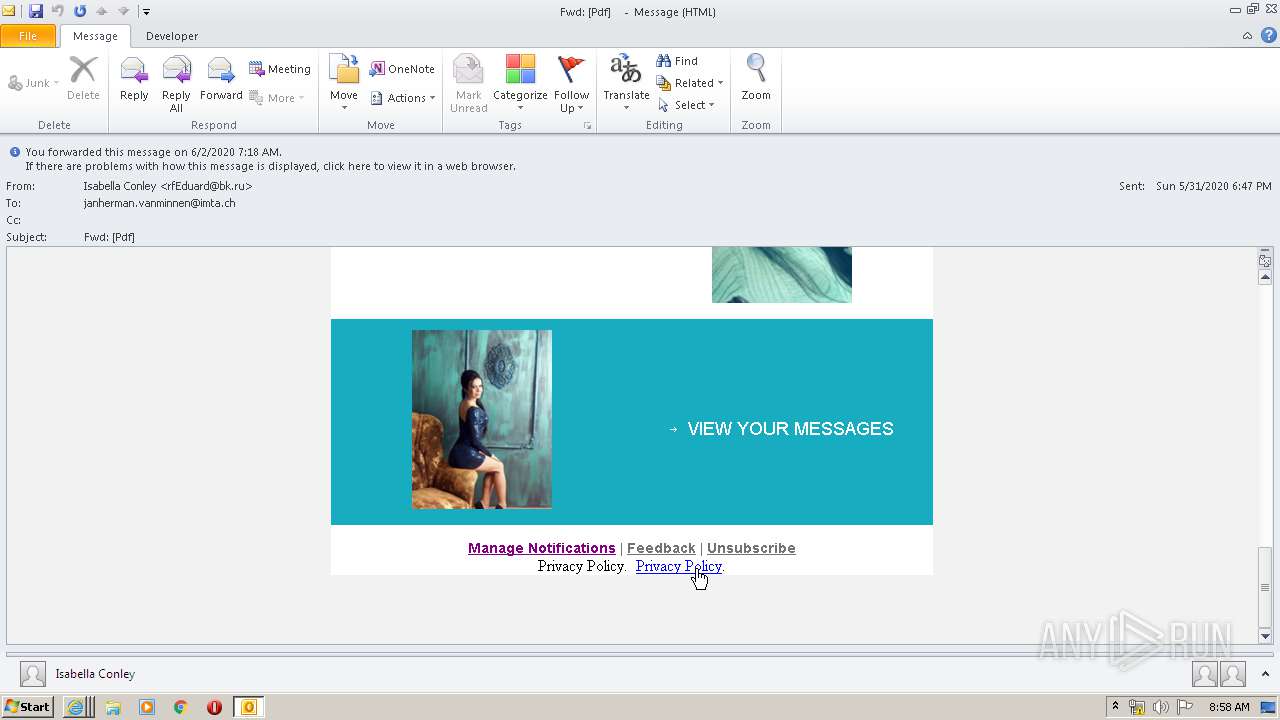
| Verdict: | Malicious activity |
| Analysis date: | June 02, 2020, 07:57:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | A8A1AF1CBA48BF163079339814836A2A |
| SHA1: | C3FDB4AB5CF6F6EF0EE8089838C69F8F485624E0 |
| SHA256: | 43B12A1515877A01369EC3CDDD7267E01AF6D4E5F0673A2664E403D39446F5DE |
| SSDEEP: | 768:qJGSsK0Bp4cOqzlcXVdjczeazUZPayxdyR76jPhFTYkpTulkGEI3n8QcHt/anyqA:KMrO0lQOJzU1dO76ooIRc4skIlyhpC |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2248)
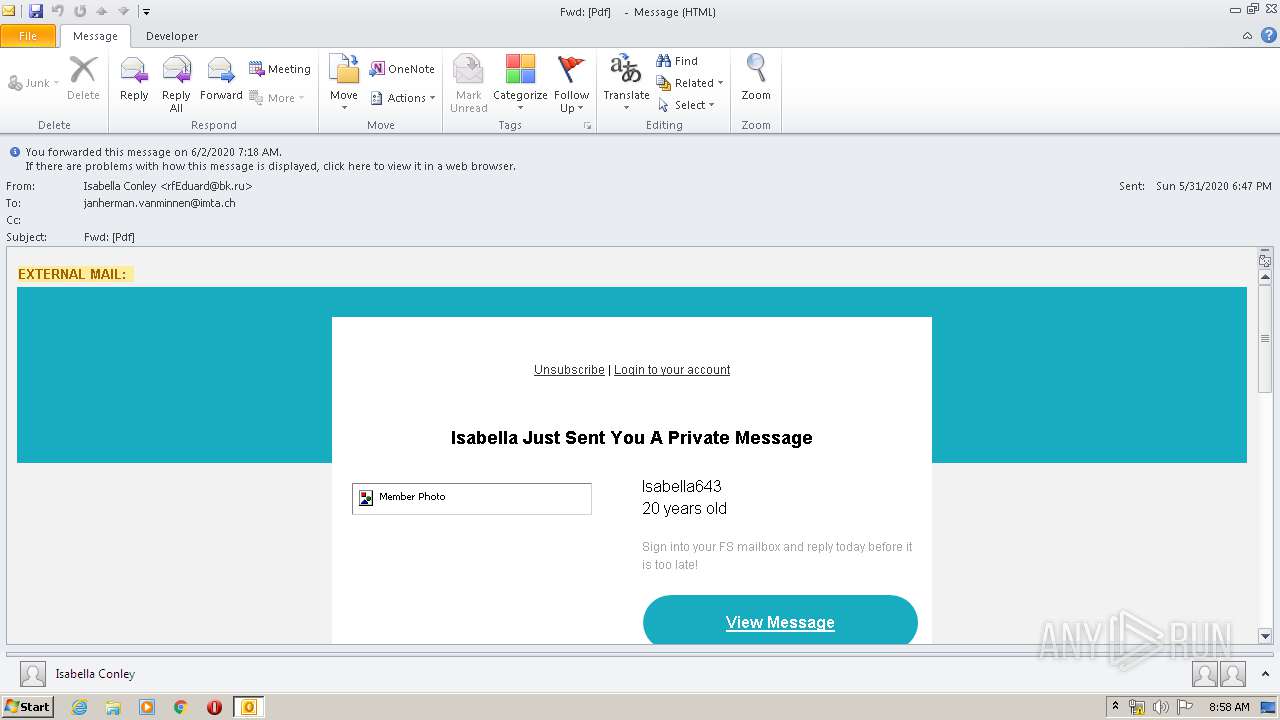
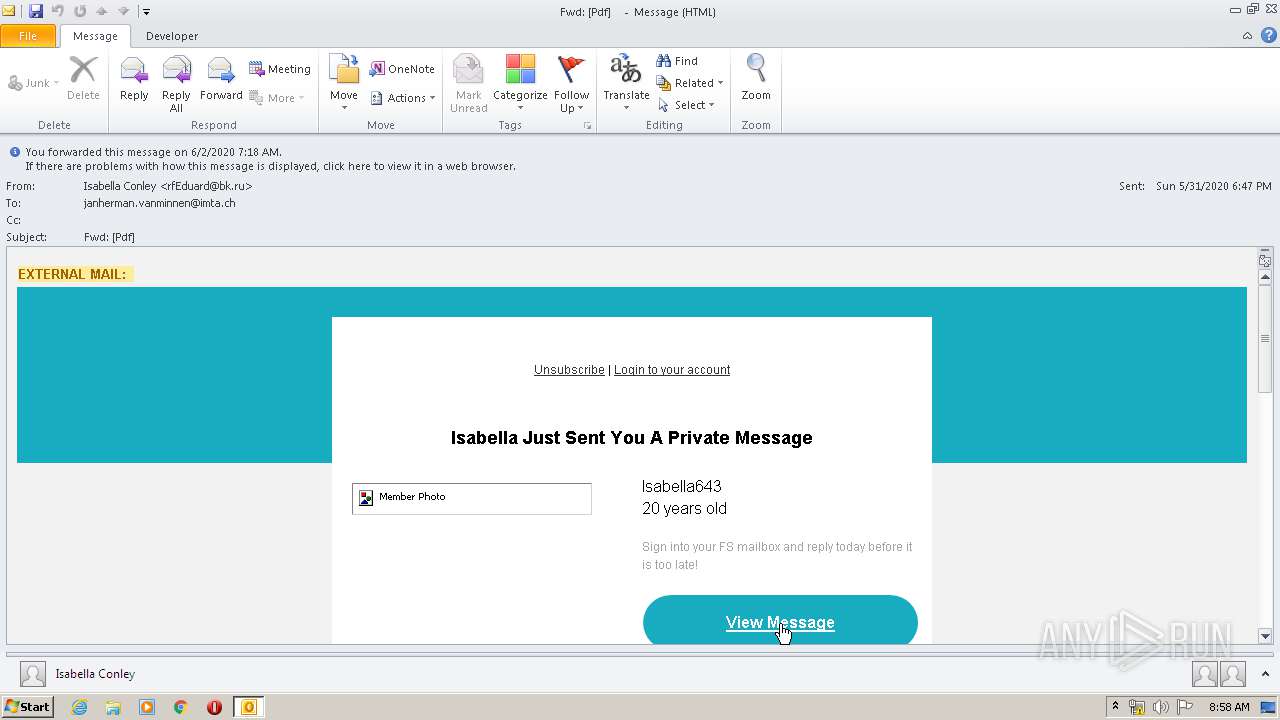
SUSPICIOUS
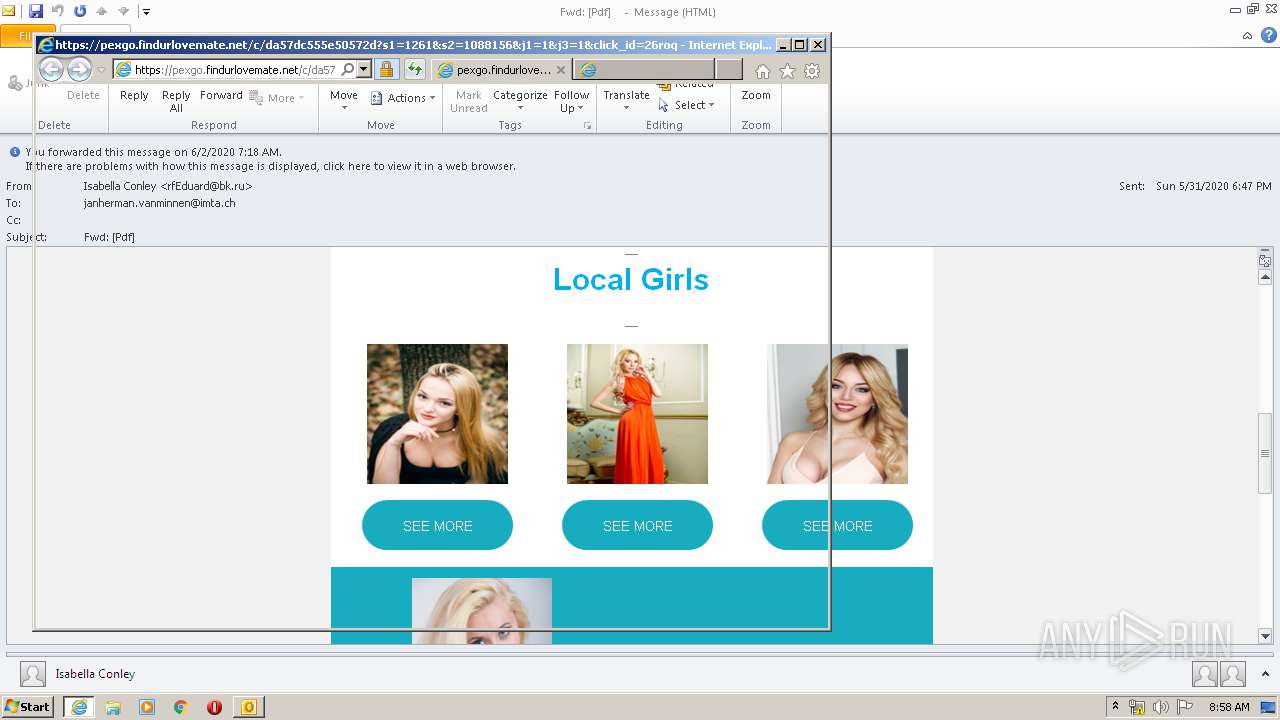
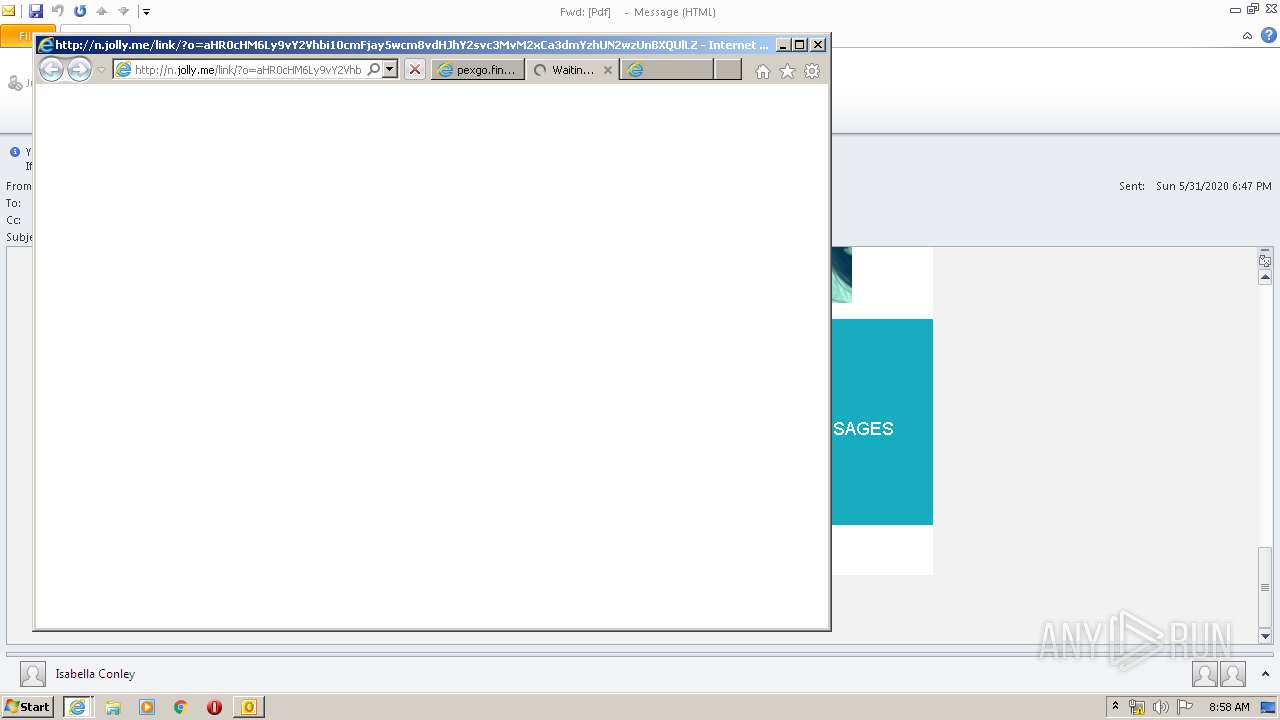
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2248)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2248)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1432)
- OUTLOOK.EXE (PID: 2248)
- iexplore.exe (PID: 3008)
- iexplore.exe (PID: 2216)
- iexplore.exe (PID: 3812)
- iexplore.exe (PID: 1880)
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 2248)
- iexplore.exe (PID: 3008)
- iexplore.exe (PID: 2216)
- iexplore.exe (PID: 1432)
- iexplore.exe (PID: 1880)
- iexplore.exe (PID: 3812)
Changes internet zones settings
- iexplore.exe (PID: 1432)
Creates files in the user directory
- iexplore.exe (PID: 2216)
- iexplore.exe (PID: 3008)
- iexplore.exe (PID: 1880)
- iexplore.exe (PID: 3812)
Application launched itself
- iexplore.exe (PID: 1432)
Reads internet explorer settings
- iexplore.exe (PID: 3008)
- iexplore.exe (PID: 3812)
- iexplore.exe (PID: 1880)
- iexplore.exe (PID: 2216)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2248)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1432)
Changes settings of System certificates
- iexplore.exe (PID: 1432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
43
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
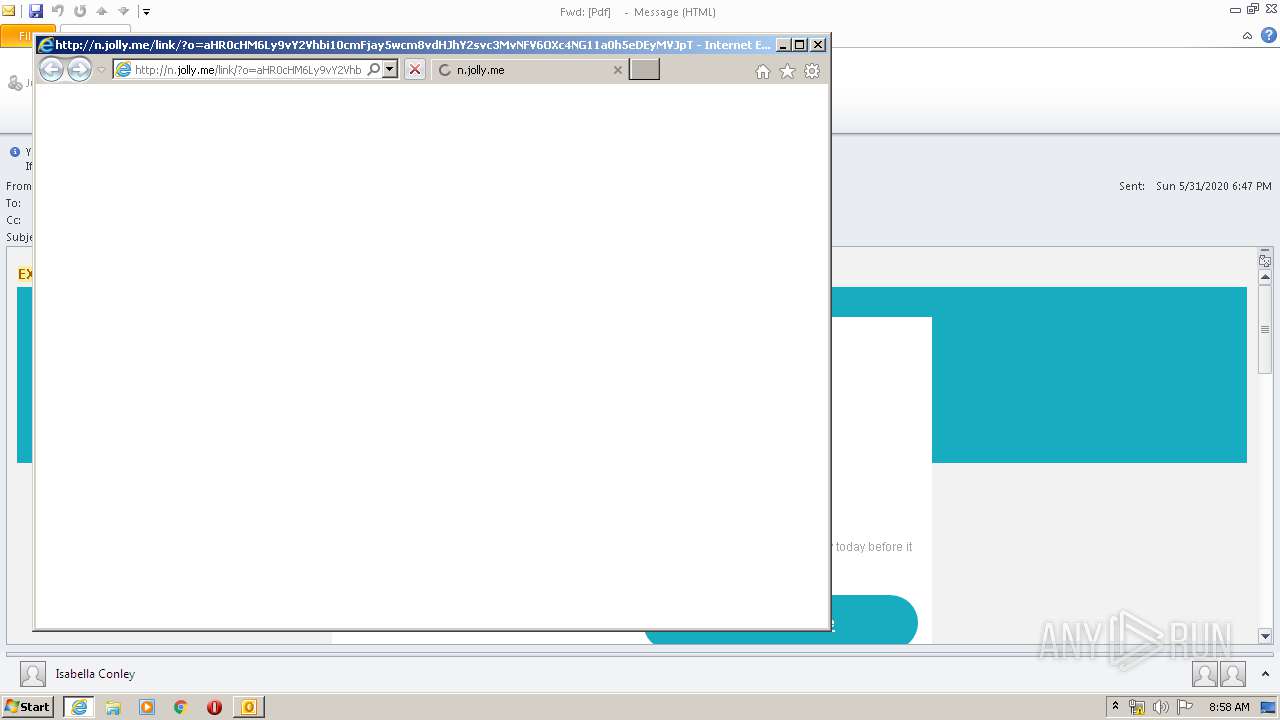
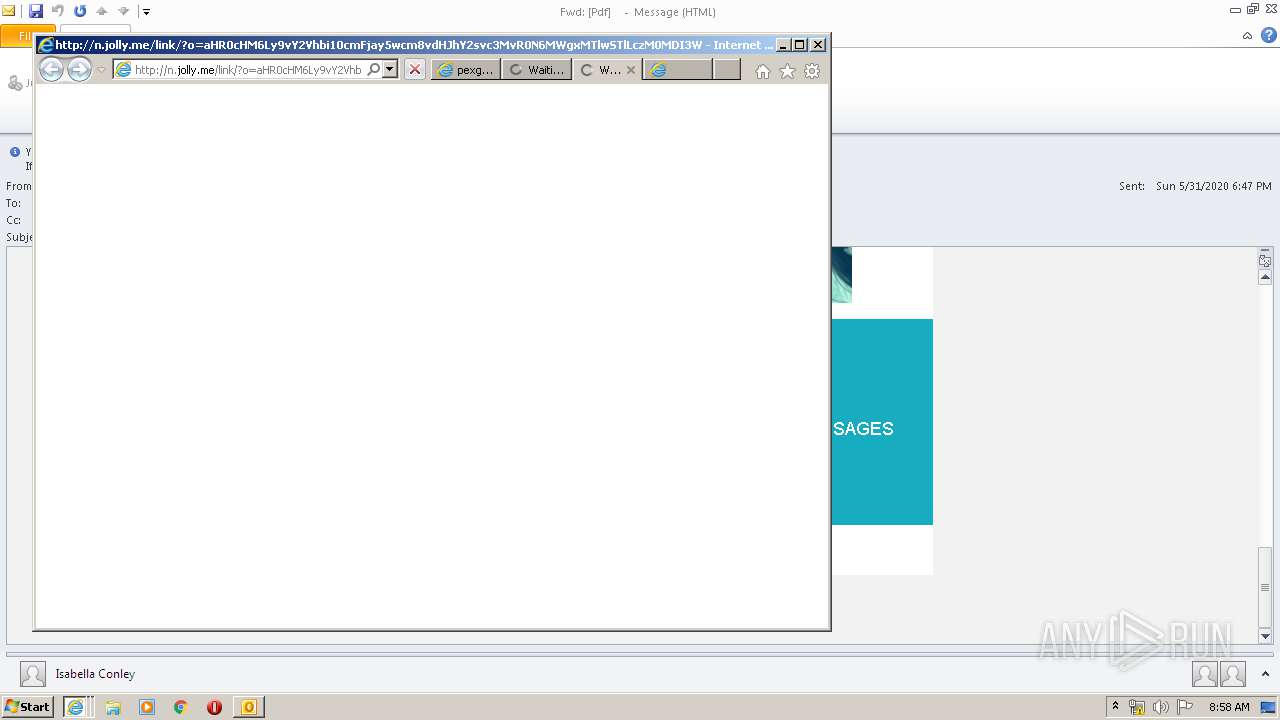
| 1432 | "C:\Program Files\Internet Explorer\iexplore.exe" http://n.jolly.me/link/?o=aHR0cHM6Ly9vY2Vhbi10cmFjay5wcm8vdHJhY2svc3MvNFV6OXc4NG11a0h5eDEyMVJpTzFJT05tMEpETGpxREM5YlExM2ZUZWxzUks4Zlc3NDE3Qk1GbGlwRDhHMksxOW1HczlwMzZNNWx5bnYxeEk3UG8ycFpOVW1nbTJxT2UwVUxxbHIyMDVMN1BVemkvP0lOX0RBVEU9U3VuLCAzMSBNYXkgMjAyMCAyMDo0NzowOA== | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1880 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1432 CREDAT:1512731 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1432 CREDAT:4003082 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Fwd Pdf .msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3008 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1432 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3812 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1432 CREDAT:1512716 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 331
Read events
2 801
Write events
2 564
Delete events
966
Modification events
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2248) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
63
Text files
76
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9889.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CabB856.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\TarB857.tmp | — | |
MD5:— | SHA256:— | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\7HCJA05E.txt | — | |
MD5:— | SHA256:— | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:96F7A6B8E3757A4BC912A5E4F76C5B21 | SHA256:3C0A8F6C770D6F7A736EF6DE2641BB469361C8B7D1555A25B382649ECF7F8ED9 | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C1B3CC7FF1466C71640A202F8258105B_D2FA6A9A7BEBCB8AF9497690C0557BDC | der | |
MD5:2D87FCCD422904F1DB9373AE92BD5E58 | SHA256:E8E91EBBB491C022D98B2FB87BF7C34DF2C0219127AD828F1C6A8ED1D16D06C4 | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:E024F99EBE4659E75D9F6AC67195B89D | SHA256:60CE37311CFF72A162991C0E3A0A4FA4CDDAADC25F92DEA0E76DA7B04DC74E27 | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\G15QJO8C.txt | text | |
MD5:C06D6AC5615780774570B968CDA9903E | SHA256:1DFFF4AD137DCEF898C3D372E963CC8DEA7010E64CDC70E7EB74F079A162FE77 | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:E7E6C33689E120616917AD6BDC39B10C | SHA256:FDBDA5D6489ED053159C9A4F02FD5F26037EC03B1FEDC0DD8EBB9710D38CC98F | |||
| 2248 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C1B3CC7FF1466C71640A202F8258105B_D2FA6A9A7BEBCB8AF9497690C0557BDC | binary | |
MD5:0F07373225DAB596F8B3639224CCDCE6 | SHA256:16C7DD562FACEE82F0ADA27E7AC1CAD3D1F565951E97318D5604AB4945BE8CD5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
96
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
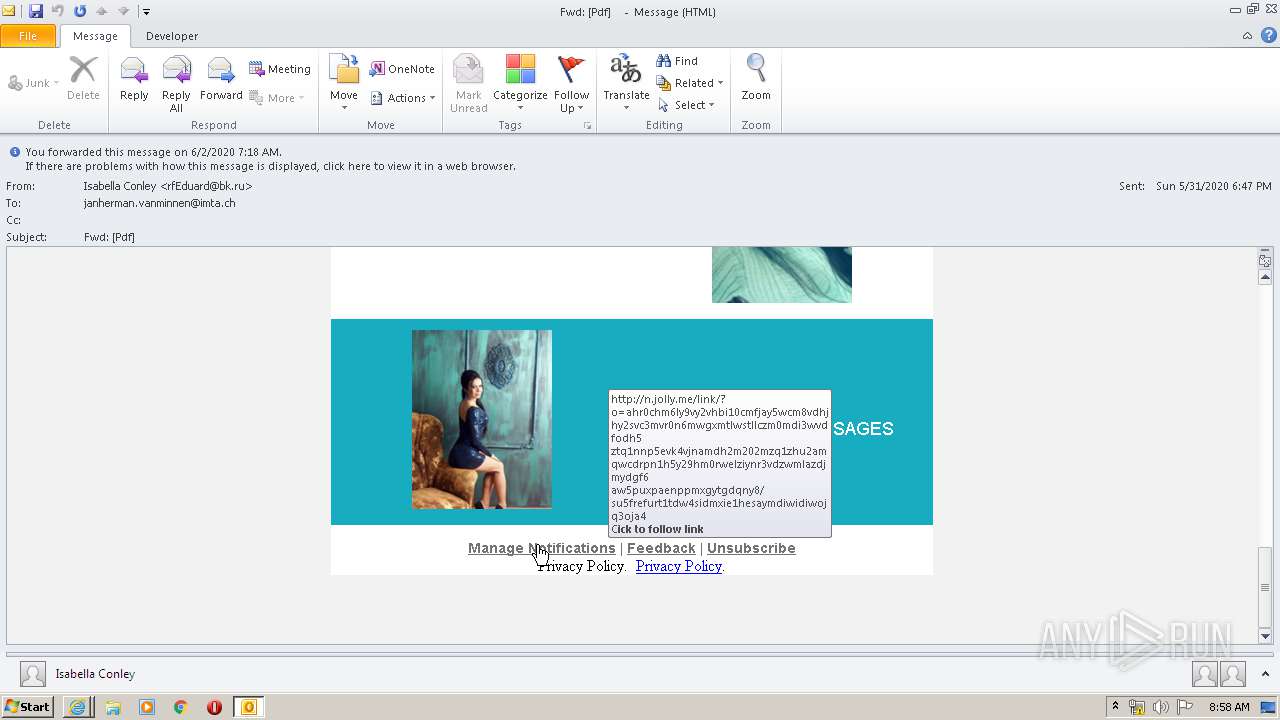
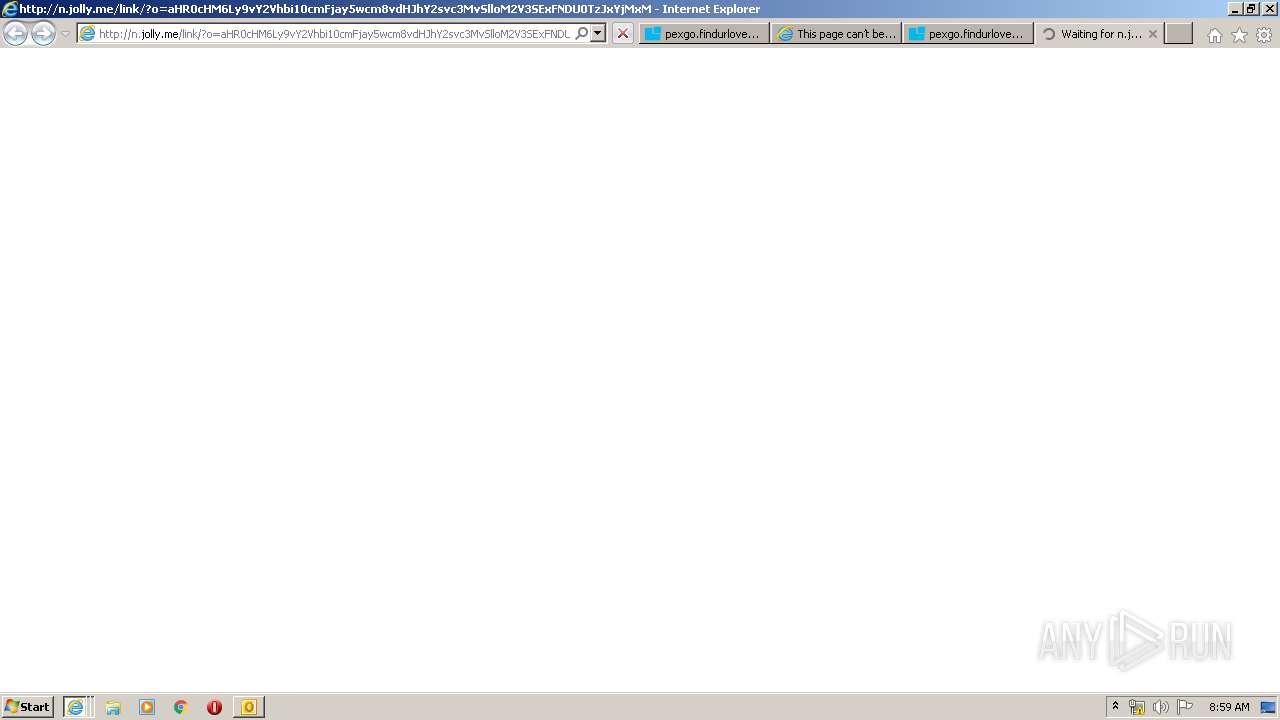
3008 | iexplore.exe | GET | 302 | 46.4.105.106:80 | http://n.mailfire.io/link/?o=aHR0cHM6Ly9vY2Vhbi10cmFjay5wcm8vdHJhY2svc3MvNFV6OXc4NG11a0h5eDEyMVJpTzFJT05tMEpETGpxREM5YlExM2ZUZWxzUks4Zlc3NDE3Qk1GbGlwRDhHMksxOW1HczlwMzZNNWx5bnYxeEk3UG8ycFpOVW1nbTJxT2UwVUxxbHIyMDVMN1BVemkvP0lOX0RBVEU9U3VuLCAzMSBNYXkgMjAyMCAyMDo0NzowOA== | DE | — | — | whitelisted |
3008 | iexplore.exe | GET | 200 | 72.247.178.9:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgM%2B845gUXRSHU4udGyttyQpcw%3D%3D | NL | der | 527 b | whitelisted |
3008 | iexplore.exe | GET | 302 | 46.4.81.189:80 | http://n.jolly.me/link/?o=aHR0cHM6Ly9vY2Vhbi10cmFjay5wcm8vdHJhY2svc3MvNFV6OXc4NG11a0h5eDEyMVJpTzFJT05tMEpETGpxREM5YlExM2ZUZWxzUks4Zlc3NDE3Qk1GbGlwRDhHMksxOW1HczlwMzZNNWx5bnYxeEk3UG8ycFpOVW1nbTJxT2UwVUxxbHIyMDVMN1BVemkvP0lOX0RBVEU9U3VuLCAzMSBNYXkgMjAyMCAyMDo0NzowOA== | DE | — | — | unknown |
3008 | iexplore.exe | GET | 200 | 72.247.178.41:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
3008 | iexplore.exe | GET | 200 | 72.247.178.41:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
2248 | OUTLOOK.EXE | GET | 200 | 72.21.91.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 5.23 Kb | whitelisted |
3008 | iexplore.exe | GET | 200 | 72.247.178.9:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgSy1Tp3UC9OmzkwOifAkOnH4g%3D%3D | NL | der | 527 b | whitelisted |
3008 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
3008 | iexplore.exe | GET | 200 | 72.247.178.9:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgM%2B845gUXRSHU4udGyttyQpcw%3D%3D | NL | der | 527 b | whitelisted |
3008 | iexplore.exe | GET | 200 | 72.247.178.9:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgTiTxdxW7te7bdyWj3rHcopsQ%3D%3D | NL | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
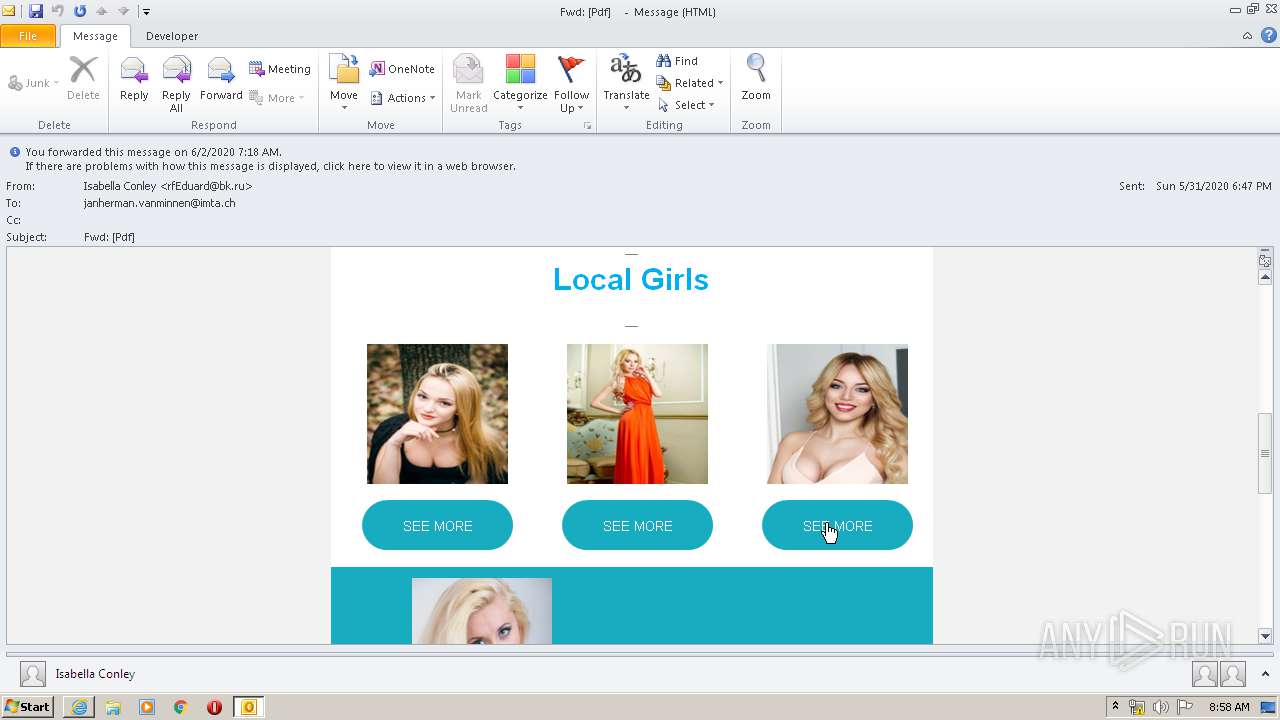
3008 | iexplore.exe | 34.243.169.105:443 | pexgo.findurlovemate.net | Amazon.com, Inc. | IE | suspicious |
3008 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3008 | iexplore.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1432 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3008 | iexplore.exe | 172.217.18.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2248 | OUTLOOK.EXE | 104.22.44.170:443 | image.prntscr.com | Cloudflare Inc | US | unknown |
2248 | OUTLOOK.EXE | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2248 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
image.prntscr.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.messenger.msn.com |
| whitelisted |
n.jolly.me |
| unknown |
n.mailfire.io |
| whitelisted |
ocean-track.pro |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
aglos.space |
| unknown |
pexgo.findurlovemate.net |
| suspicious |