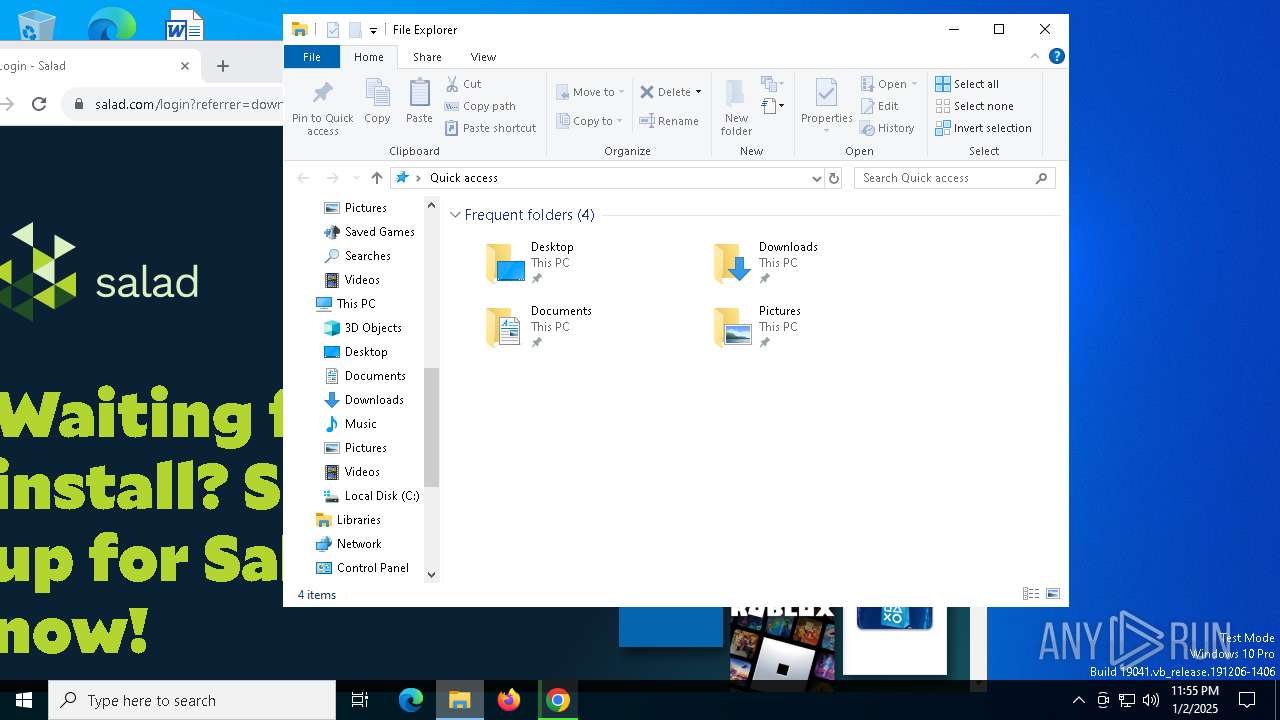
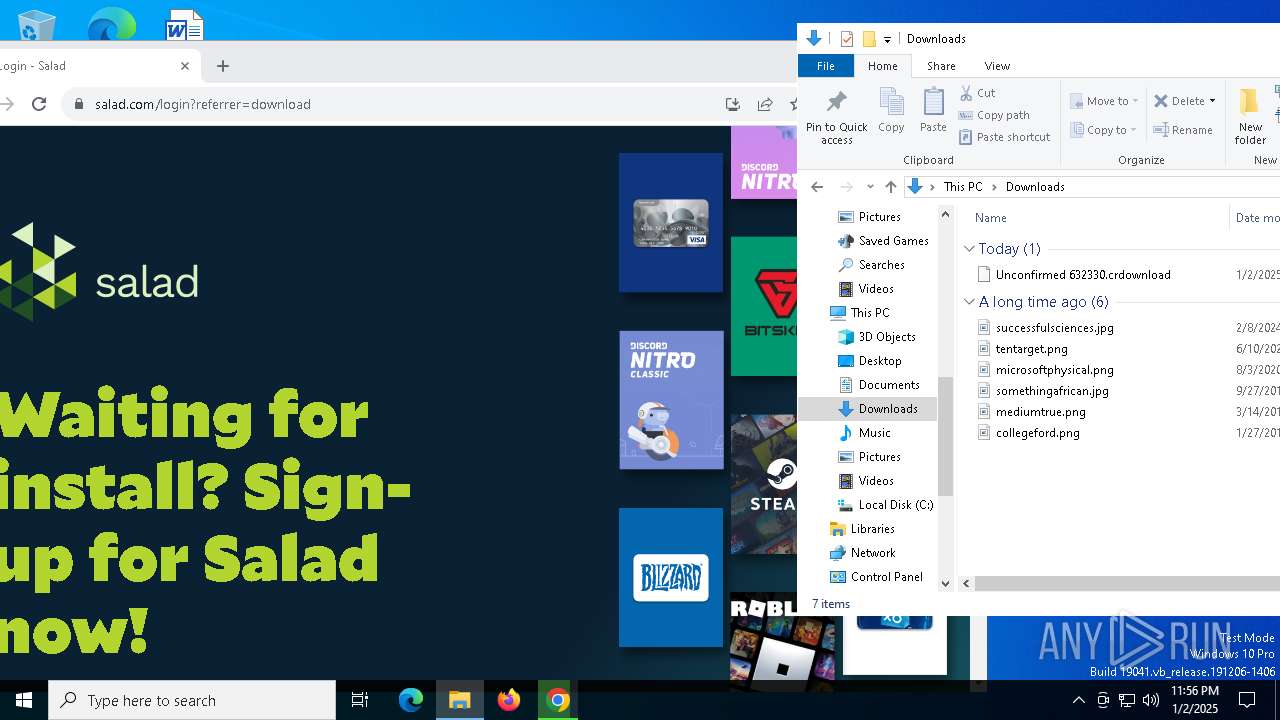
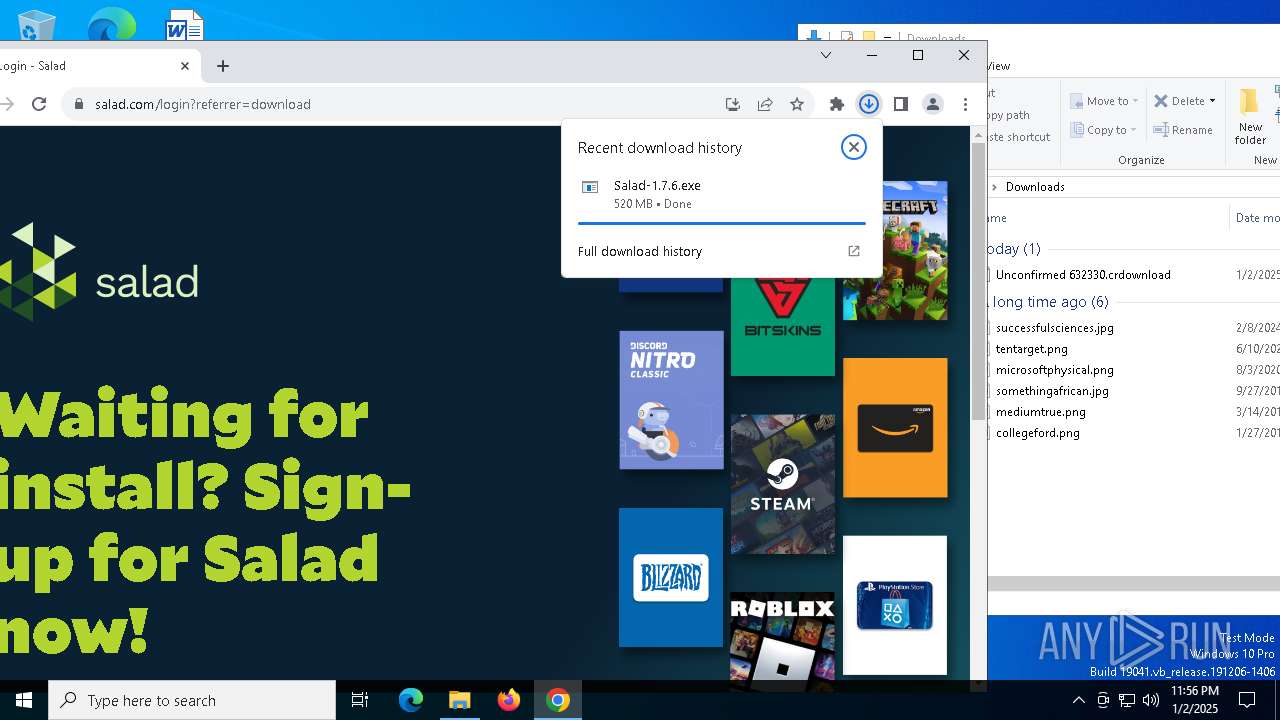
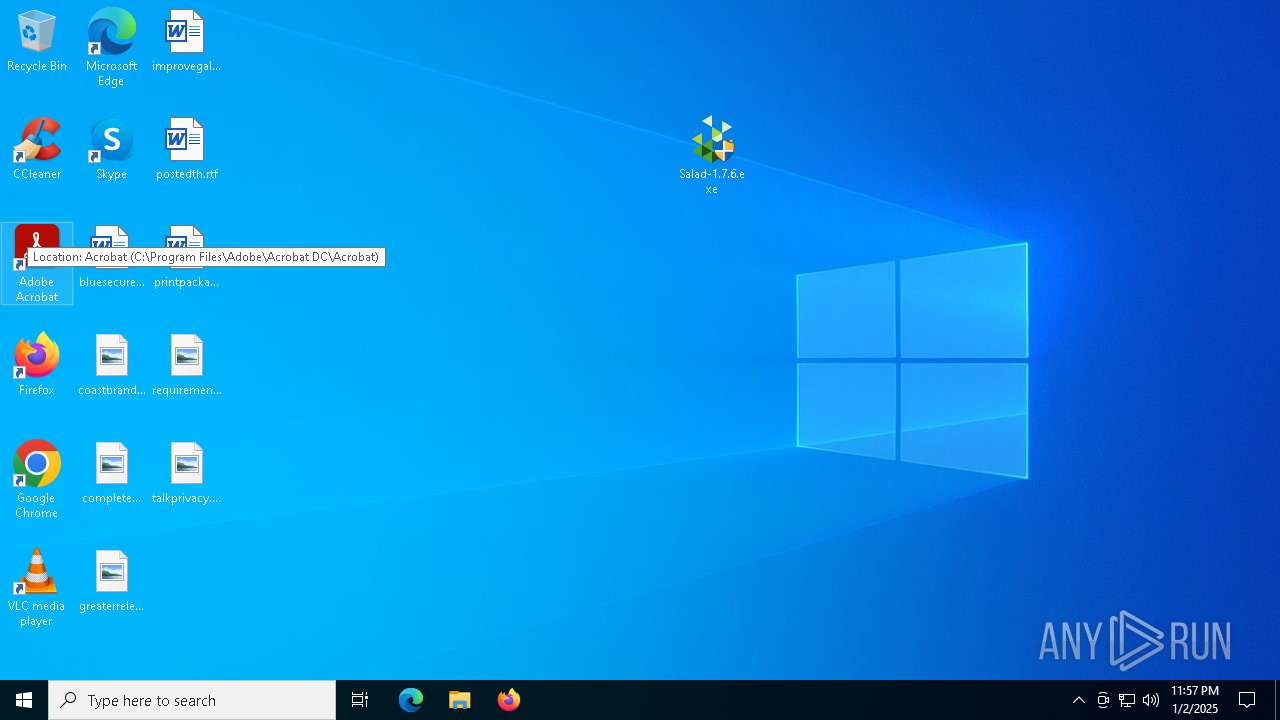
| URL: | https://salad.com/download |
| Full analysis: | https://app.any.run/tasks/95f26636-a0a4-4854-99ce-59aa44f10cd0 |
| Verdict: | Malicious activity |
| Analysis date: | January 02, 2025, 23:54:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
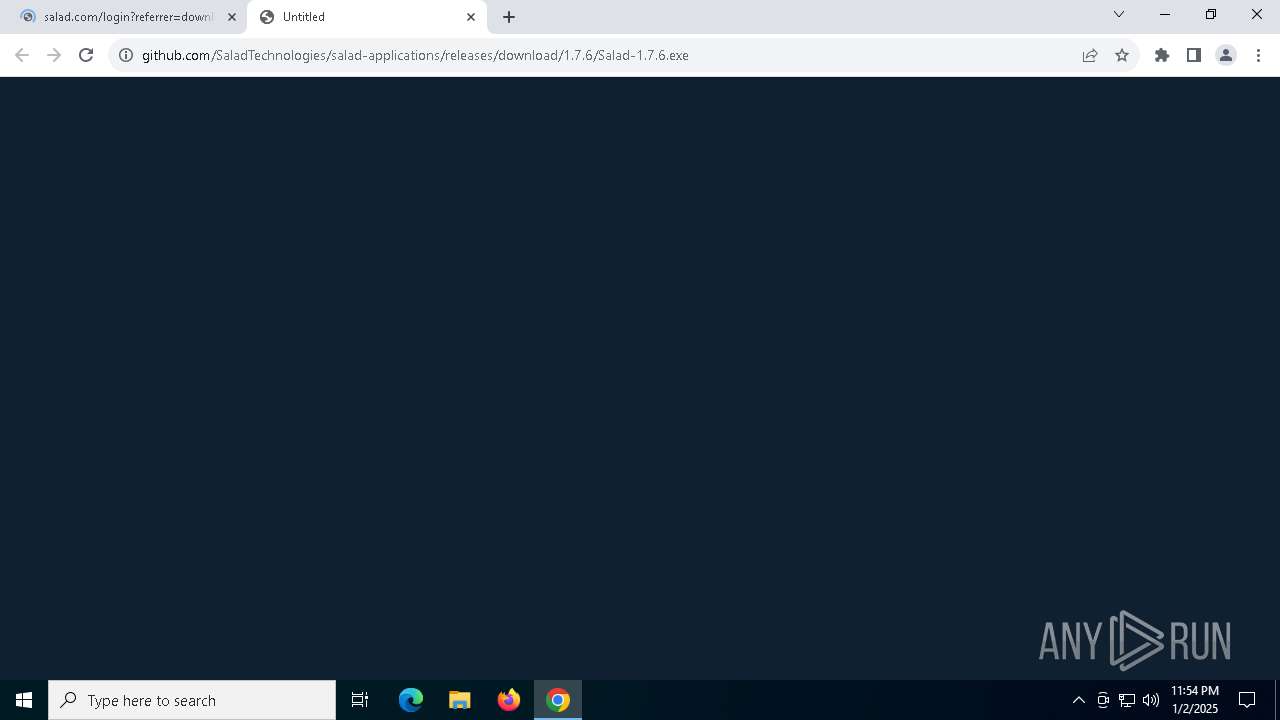
| MD5: | 821484A674EB718B19A51B6CB6352604 |
| SHA1: | 50638D7C1AAD69FF8A7C9E741B3201734330285D |
| SHA256: | 43A0BE0E303DCE7A9E7BF3ADFDC03A7C01F78ED2262819367501E3BB5578F9B6 |
| SSDEEP: | 3:N8JK9GKIBM:2k9GTBM |
MALICIOUS
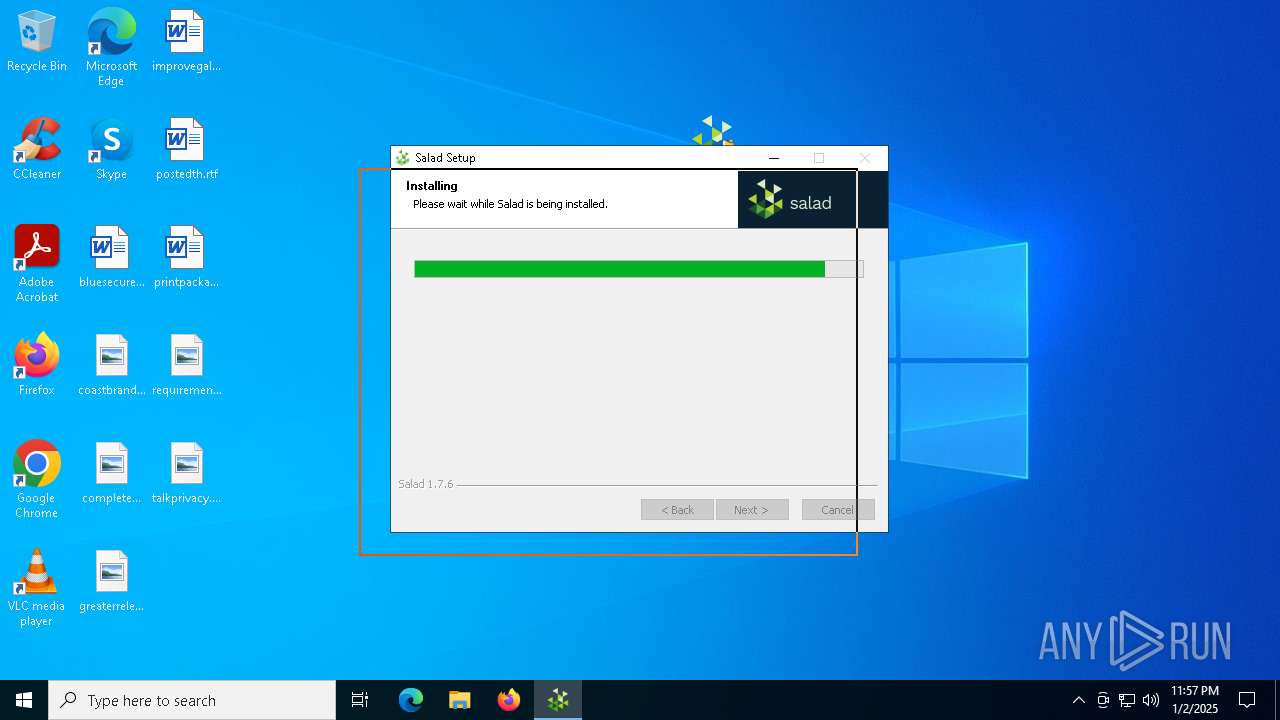
Run PowerShell with an invisible window
- powershell.exe (PID: 396)
- powershell.exe (PID: 2736)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7164)
- cmd.exe (PID: 2124)
Bypass execution policy to execute commands
- powershell.exe (PID: 396)
- powershell.exe (PID: 2736)
Changes powershell execution policy (Unrestricted)
- system-information-workload.exe (PID: 4704)
SUSPICIOUS
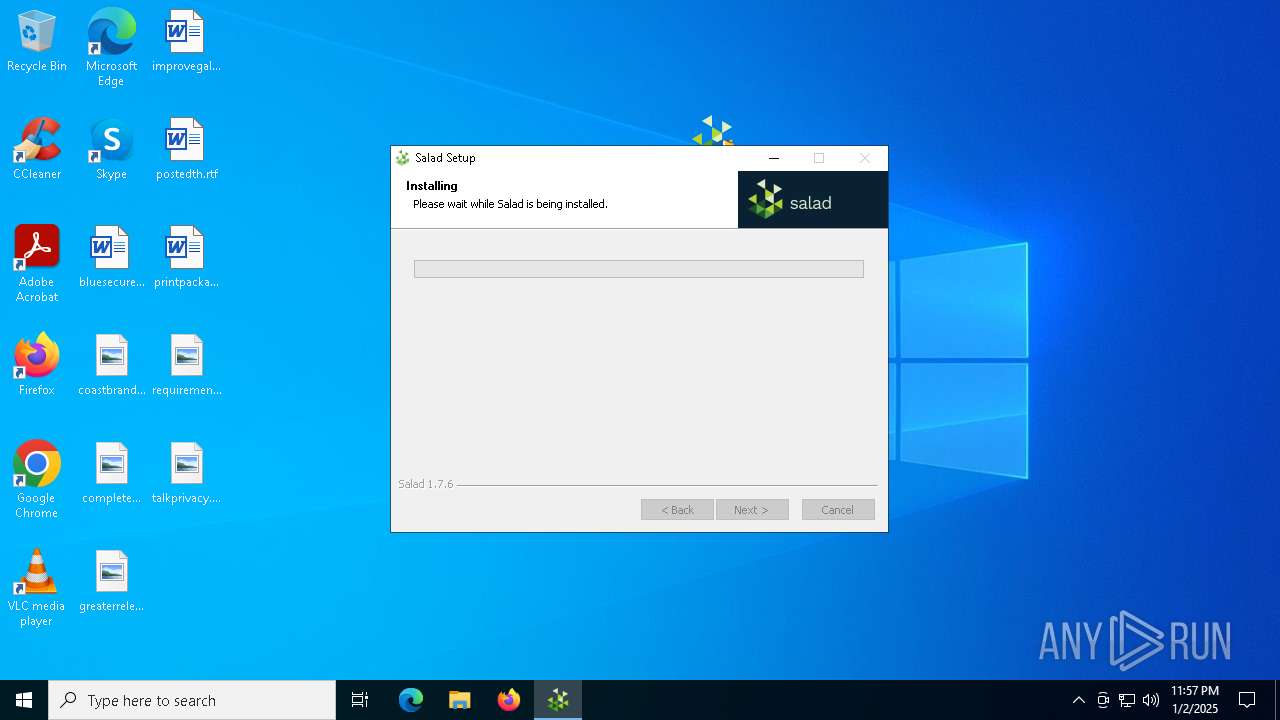
The process creates files with name similar to system file names
- Salad-1.7.6.exe (PID: 4704)
Executable content was dropped or overwritten
- Salad-1.7.6.exe (PID: 4704)
- Salad.Bowl.Service.exe (PID: 6492)
- Salad.Bowl.Service.exe (PID: 4648)
Malware-specific behavior (creating "System.dll" in Temp)
- Salad-1.7.6.exe (PID: 4704)
Uses TASKKILL.EXE to kill process
- Salad-1.7.6.exe (PID: 4704)
Drops 7-zip archiver for unpacking
- Salad-1.7.6.exe (PID: 4704)
Process drops legitimate windows executable
- Salad-1.7.6.exe (PID: 4704)
Reads security settings of Internet Explorer
- Salad-1.7.6.exe (PID: 4704)
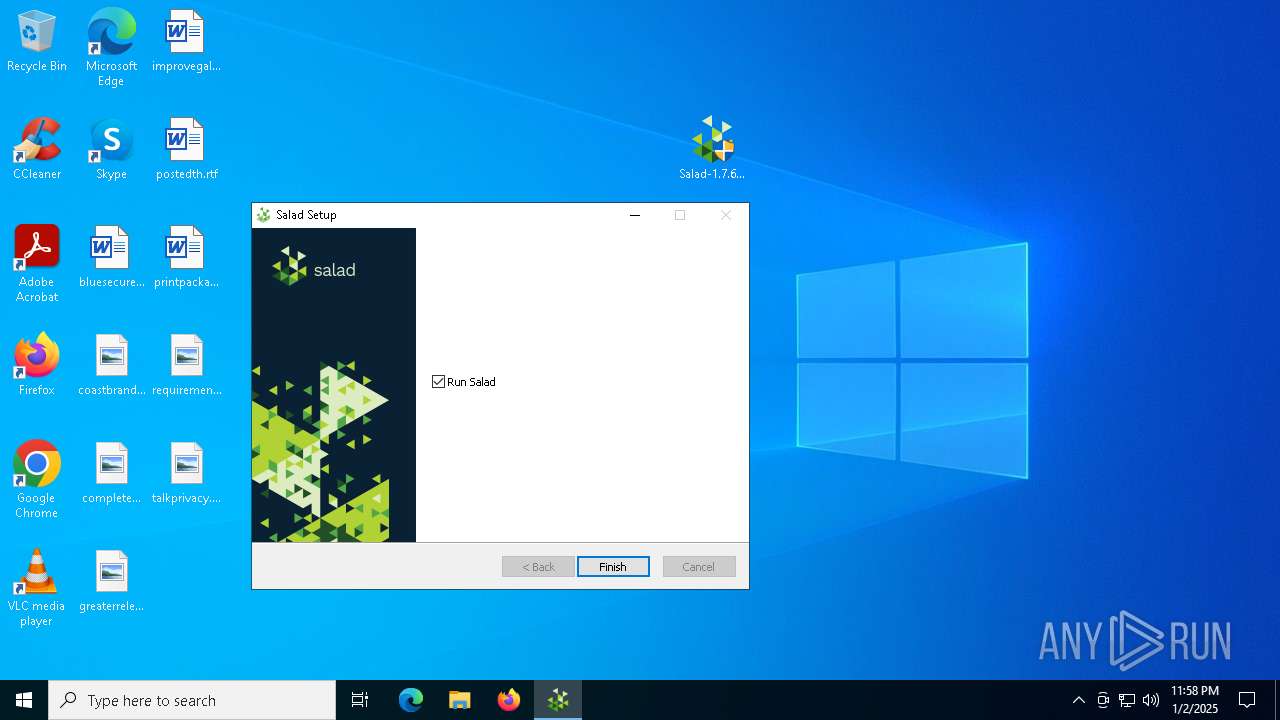
Creates a software uninstall entry
- Salad-1.7.6.exe (PID: 4704)
The process drops C-runtime libraries
- Salad-1.7.6.exe (PID: 4704)
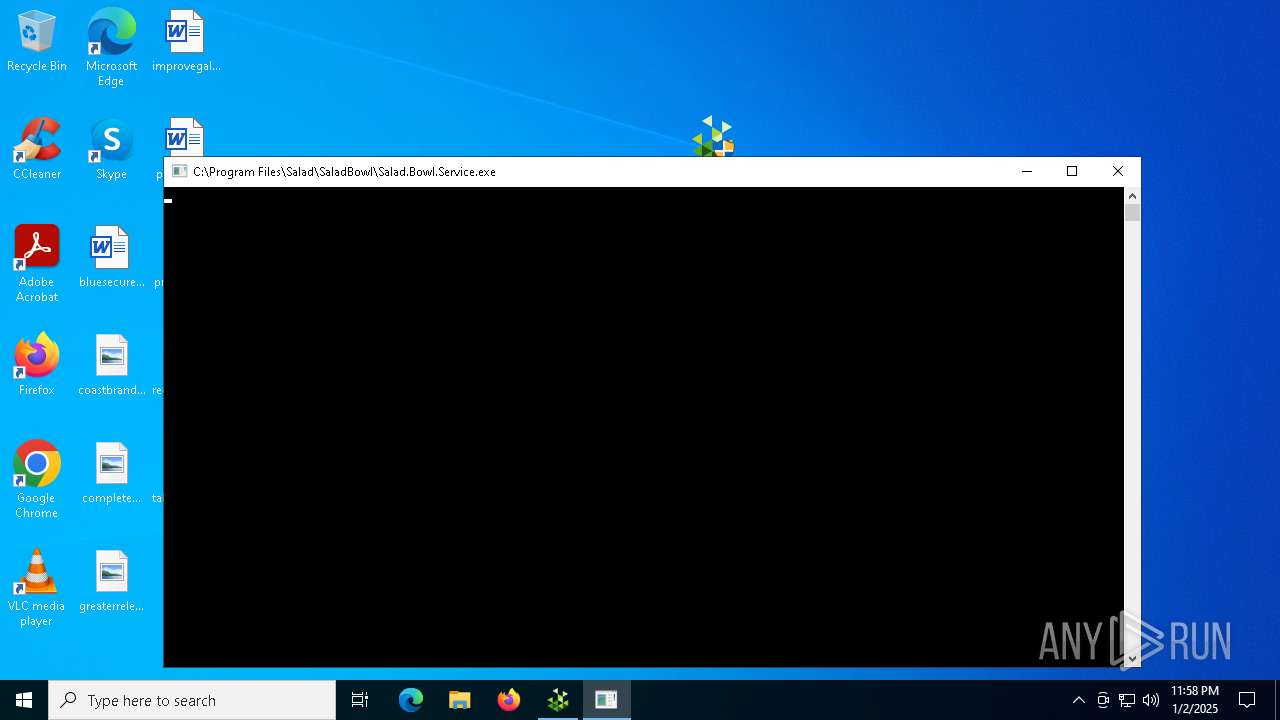
Executes as Windows Service
- Salad.Bootstrapper.exe (PID: 7020)
- WmiApSrv.exe (PID: 6680)
Checks Windows Trust Settings
- Salad.Bootstrapper.exe (PID: 7020)
- Salad.Bowl.Service.exe (PID: 6492)
Adds/modifies Windows certificates
- Salad.Bootstrapper.exe (PID: 7020)
- librespeed-cli.exe (PID: 2728)
The process checks if it is being run in the virtual environment
- Salad.Bowl.Service.exe (PID: 6492)
Application launched itself
- Salad.exe (PID: 2212)
Drops a system driver (possible attempt to evade defenses)
- Salad.Bowl.Service.exe (PID: 6492)
- Salad.Bowl.Service.exe (PID: 4648)
Starts CMD.EXE for commands execution
- Salad.exe (PID: 2212)
- system-information-workload.exe (PID: 4704)
- NETSTAT.EXE (PID: 3864)
The process hide an interactive prompt from the user
- cmd.exe (PID: 7164)
- cmd.exe (PID: 2124)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 7164)
- cmd.exe (PID: 2124)
- system-information-workload.exe (PID: 4704)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7164)
- cmd.exe (PID: 2124)
- system-information-workload.exe (PID: 4704)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7164)
- cmd.exe (PID: 2124)
- Salad.exe (PID: 2212)
- system-information-workload.exe (PID: 4704)
Starts application with an unusual extension
- cmd.exe (PID: 6404)
Executing commands from ".cmd" file
- system-information-workload.exe (PID: 4704)
Checks for Java to be installed
- java.exe (PID: 5836)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 1348)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 10036)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 1220)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 9776)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 2508)
INFO
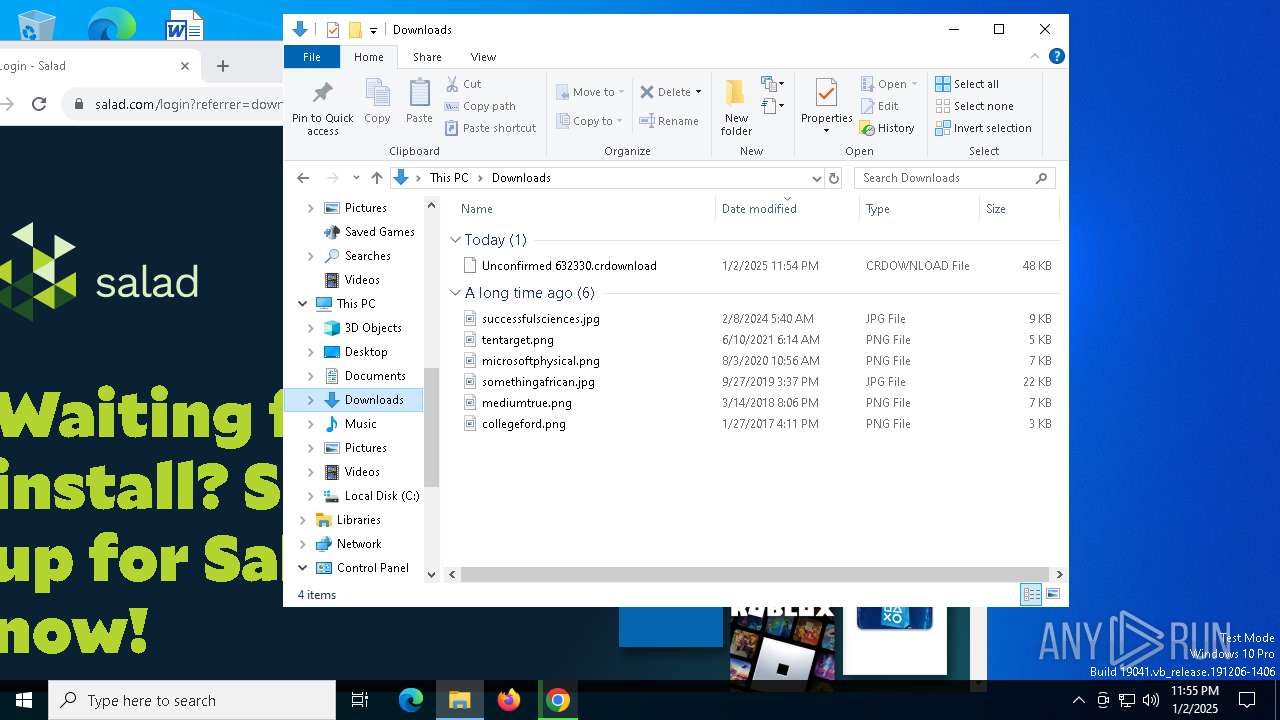
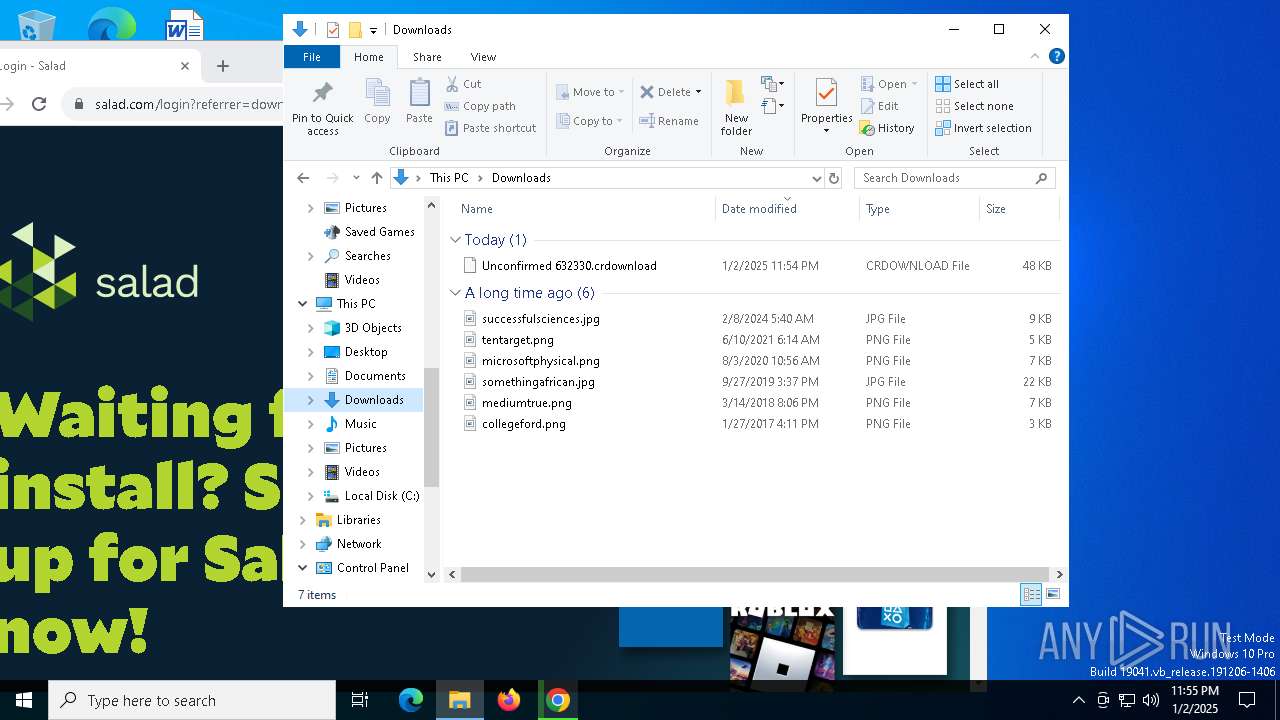
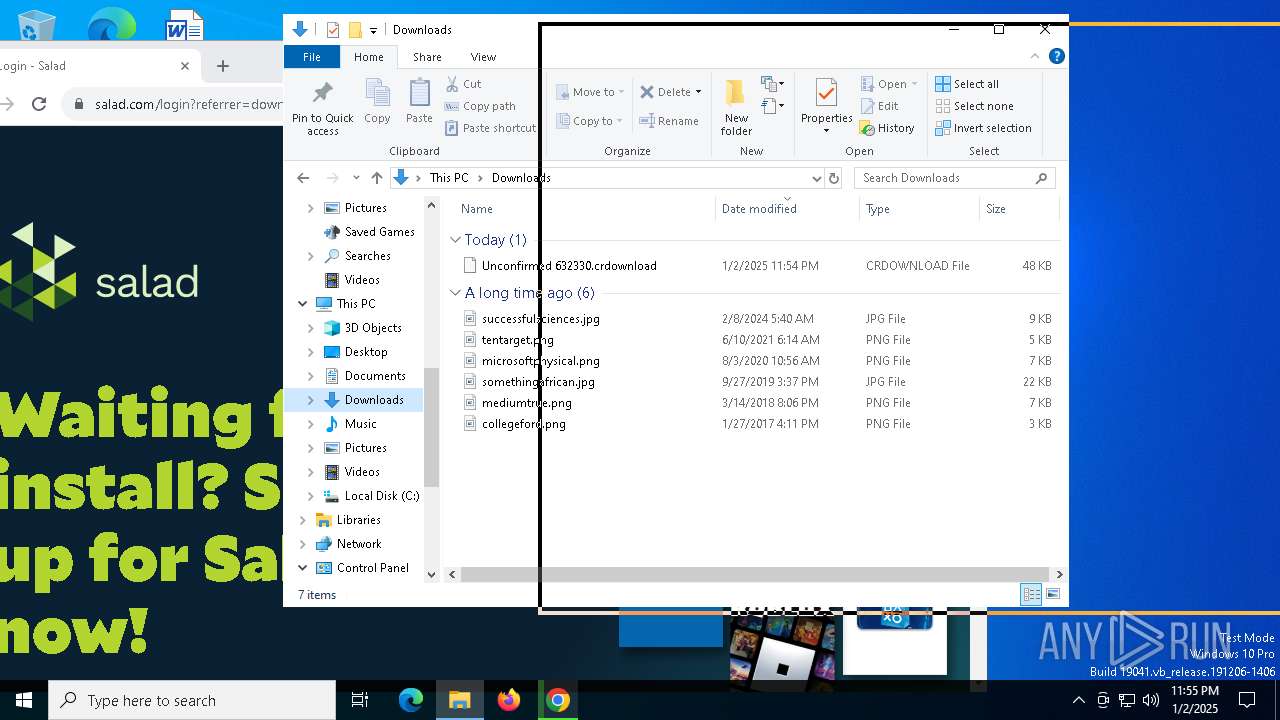
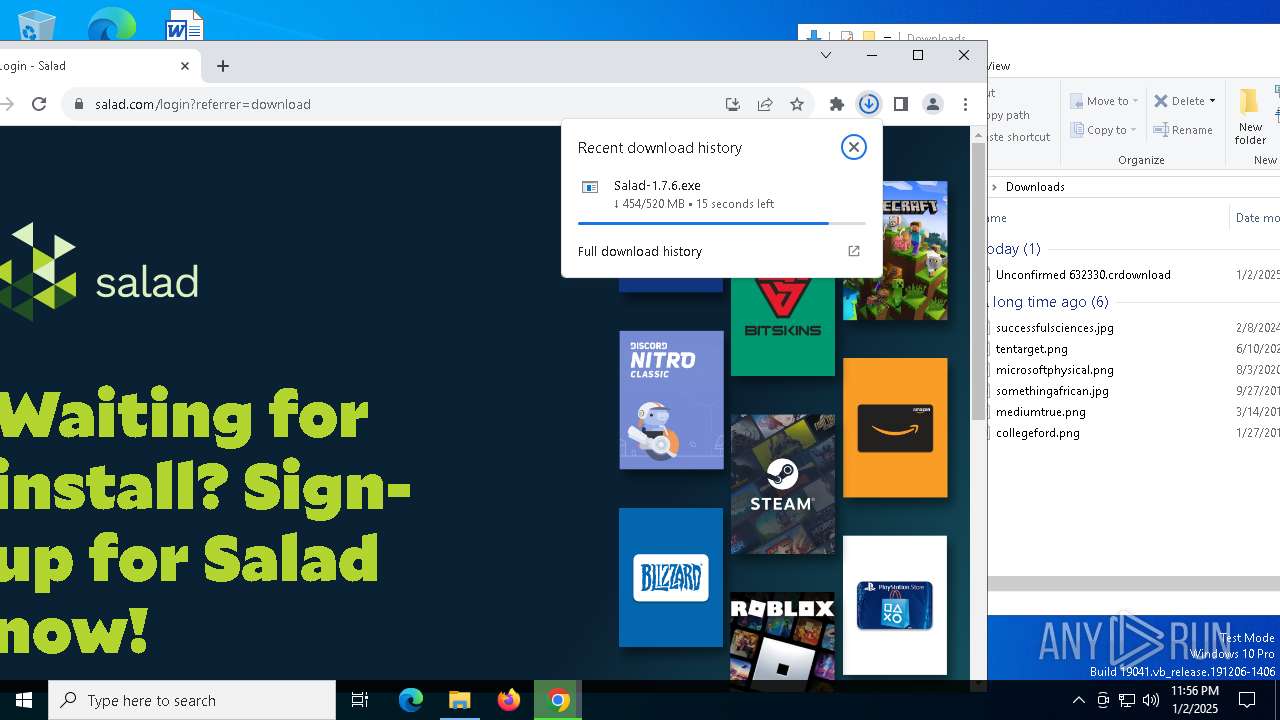
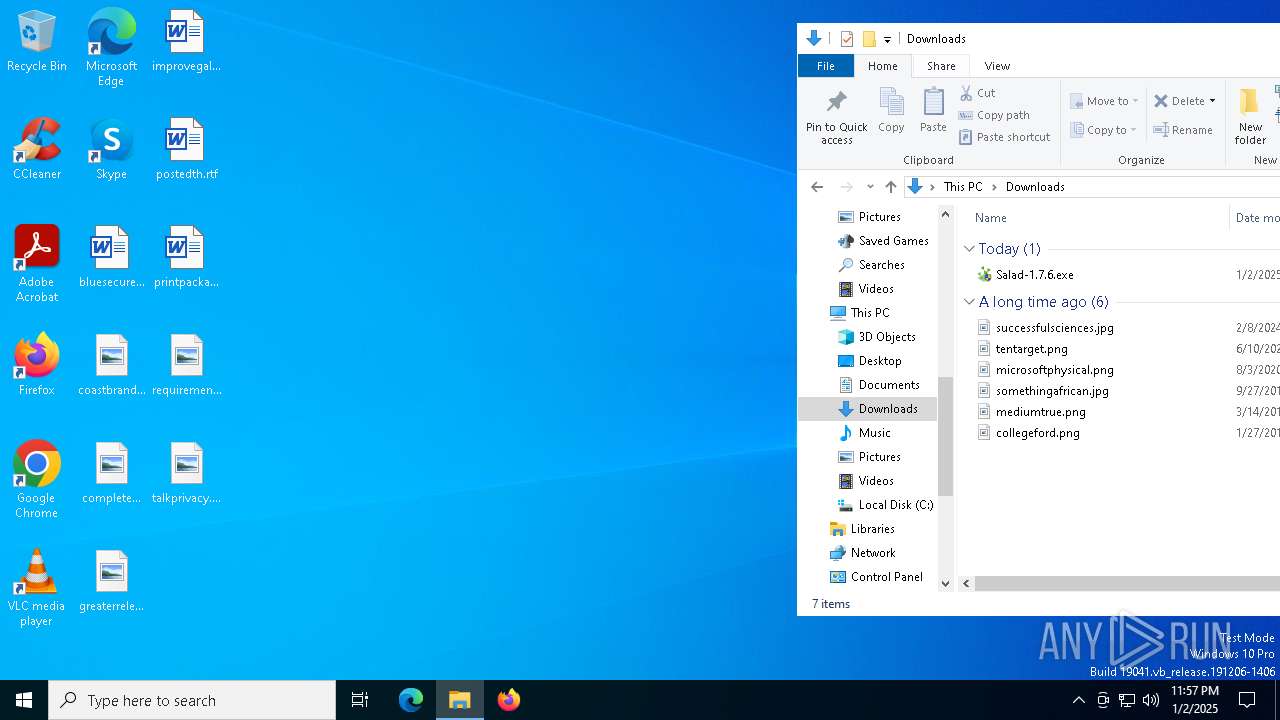
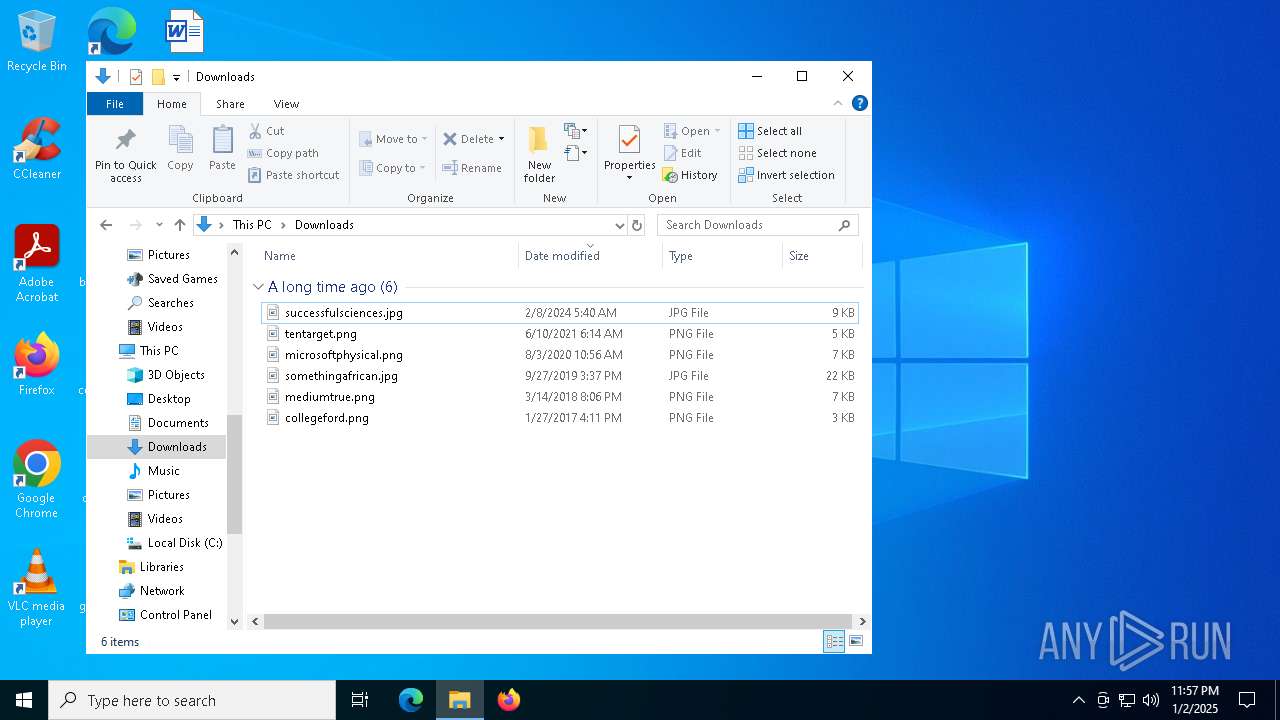
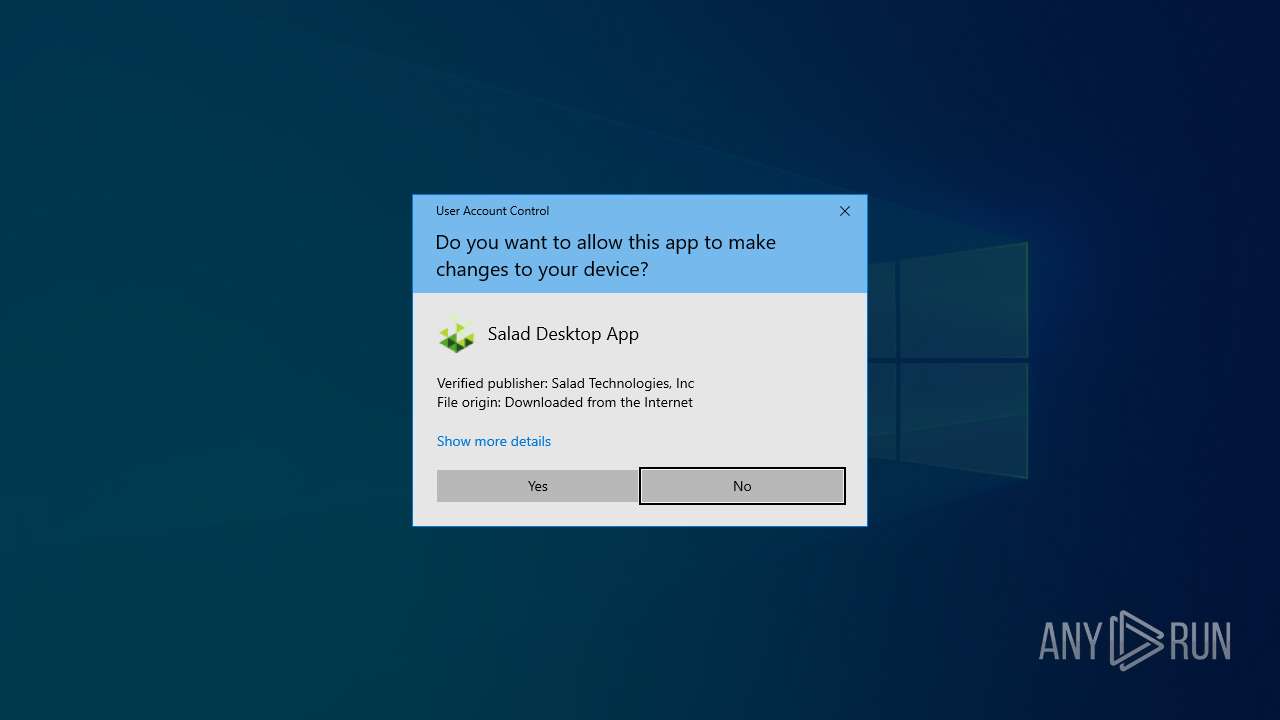
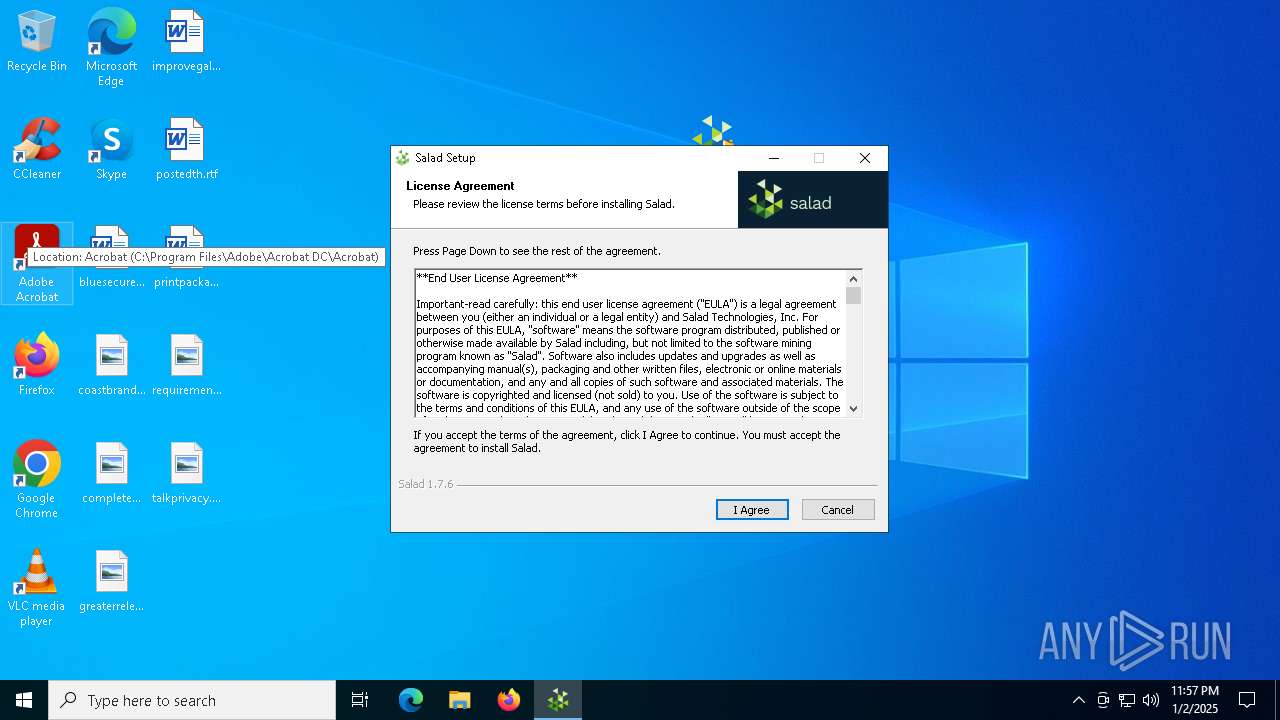
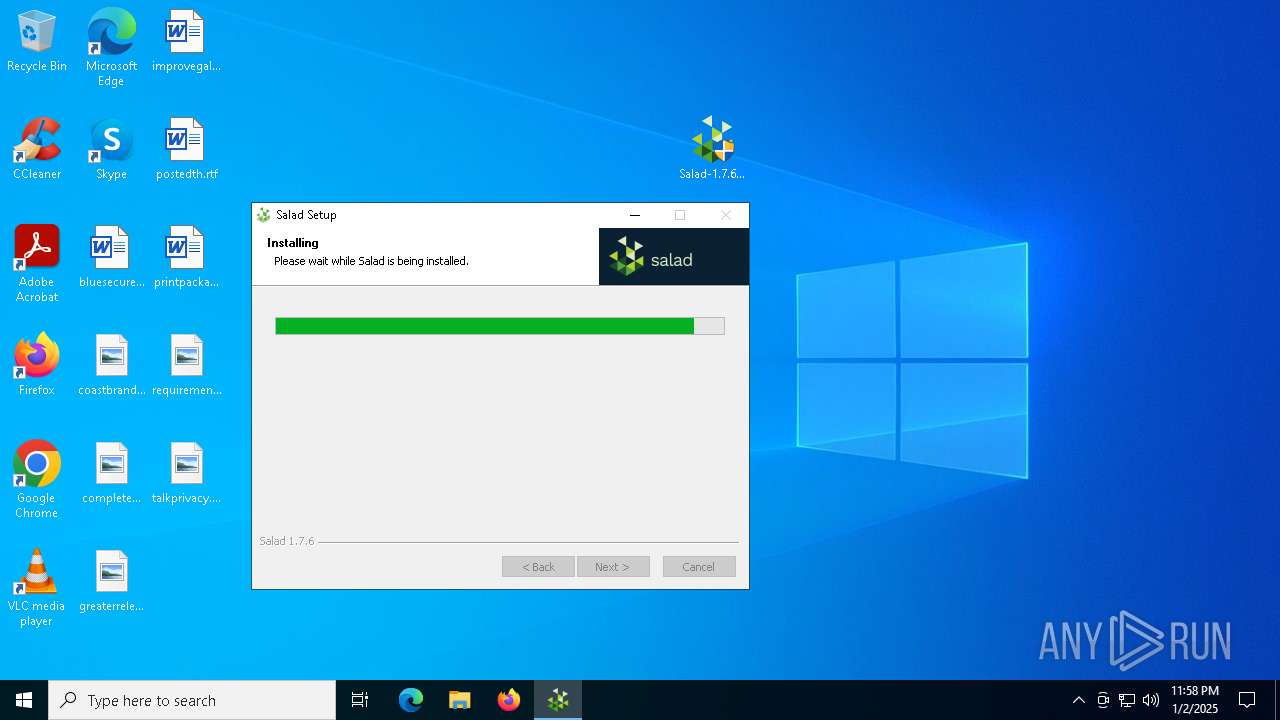
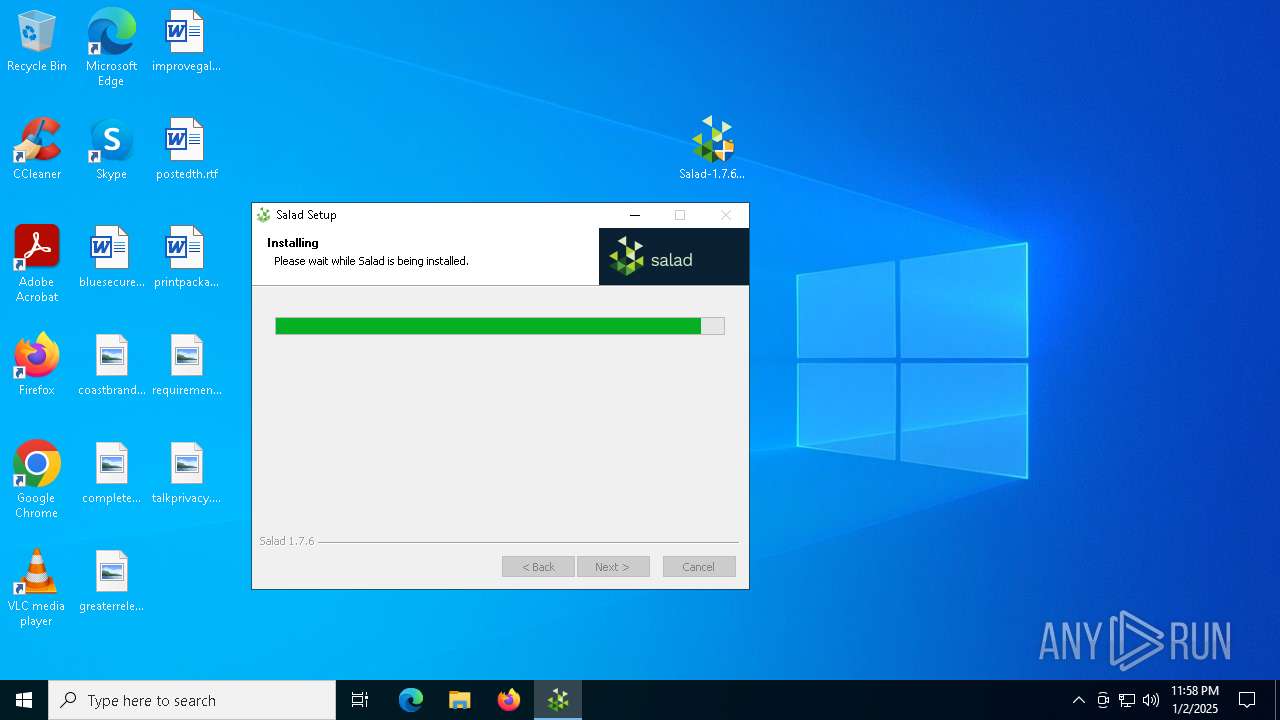
Manual execution by a user
- Salad-1.7.6.exe (PID: 5392)
- Salad-1.7.6.exe (PID: 4704)
- Salad.exe (PID: 2212)
Executable content was dropped or overwritten
- chrome.exe (PID: 3416)
The process uses the downloaded file
- chrome.exe (PID: 6900)
- Salad-1.7.6.exe (PID: 4704)
- powershell.exe (PID: 2928)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 1916)
- powershell.exe (PID: 6768)
- powershell.exe (PID: 4188)
- powershell.exe (PID: 6548)
- powershell.exe (PID: 7240)
- powershell.exe (PID: 7248)
- powershell.exe (PID: 6684)
- powershell.exe (PID: 448)
- powershell.exe (PID: 1592)
- powershell.exe (PID: 7232)
- powershell.exe (PID: 7272)
- powershell.exe (PID: 1200)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 6196)
- powershell.exe (PID: 5456)
- powershell.exe (PID: 5992)
- powershell.exe (PID: 2124)
- powershell.exe (PID: 1688)
- powershell.exe (PID: 3900)
- powershell.exe (PID: 4052)
- powershell.exe (PID: 7300)
- powershell.exe (PID: 2972)
- powershell.exe (PID: 6784)
Reads the computer name
- Salad-1.7.6.exe (PID: 4704)
- Salad.Bowl.Service.exe (PID: 4504)
- Salad.Bootstrapper.exe (PID: 7020)
- Salad.Bowl.Service.exe (PID: 6492)
- Salad.exe (PID: 2212)
- Salad.exe (PID: 6428)
- Salad.exe (PID: 6596)
- system-information-workload.exe (PID: 4704)
- librespeed-cli.exe (PID: 2728)
- PLUGScheduler.exe (PID: 2508)
- Salad.Bowl.Service.exe (PID: 4648)
Application launched itself
- chrome.exe (PID: 3416)
Checks supported languages
- Salad-1.7.6.exe (PID: 4704)
- Salad.Bowl.Service.exe (PID: 4504)
- Salad.Bootstrapper.exe (PID: 7020)
- Salad.Bowl.Service.exe (PID: 6492)
- Salad.exe (PID: 2212)
- Salad.exe (PID: 6596)
- Salad.exe (PID: 1620)
- Salad.exe (PID: 6428)
- system-information-workload.exe (PID: 4704)
- chcp.com (PID: 4144)
- librespeed-cli.exe (PID: 2728)
- java.exe (PID: 5836)
- Salad.exe (PID: 8088)
- PLUGScheduler.exe (PID: 2508)
- Salad.Bowl.Service.exe (PID: 4648)
The sample compiled with english language support
- Salad-1.7.6.exe (PID: 4704)
- Salad.Bowl.Service.exe (PID: 6492)
- Salad.Bowl.Service.exe (PID: 4648)
Create files in a temporary directory
- Salad-1.7.6.exe (PID: 4704)
- Salad.exe (PID: 2212)
Creates files in the program directory
- Salad-1.7.6.exe (PID: 4704)
- Salad.Bowl.Service.exe (PID: 4504)
- Salad.Bootstrapper.exe (PID: 7020)
- Salad.Bowl.Service.exe (PID: 6492)
- java.exe (PID: 5836)
Creates files or folders in the user directory
- Salad-1.7.6.exe (PID: 4704)
- Salad.exe (PID: 2212)
- Salad.exe (PID: 6596)
Process checks computer location settings
- Salad.Bootstrapper.exe (PID: 7020)
- Salad.Bowl.Service.exe (PID: 4504)
- Salad.Bowl.Service.exe (PID: 6492)
- Salad.exe (PID: 2212)
- Salad.exe (PID: 1620)
- Salad.exe (PID: 8088)
Reads the machine GUID from the registry
- Salad.Bootstrapper.exe (PID: 7020)
- Salad.Bowl.Service.exe (PID: 6492)
Reads the software policy settings
- Salad.Bootstrapper.exe (PID: 7020)
- Salad.Bowl.Service.exe (PID: 6492)
- librespeed-cli.exe (PID: 2728)
Reads CPU info
- Salad.Bowl.Service.exe (PID: 6492)
- system-information-workload.exe (PID: 4704)
Reads Environment values
- Salad.exe (PID: 2212)
- system-information-workload.exe (PID: 4704)
Reads the time zone
- Salad.Bowl.Service.exe (PID: 6492)
Reads product name
- Salad.exe (PID: 2212)
- system-information-workload.exe (PID: 4704)
Checks proxy server information
- Salad.exe (PID: 2212)
Changes the display of characters in the console
- cmd.exe (PID: 6404)
Prints a route via ROUTE.EXE
- ROUTE.EXE (PID: 6388)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7216)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
472
Monitored processes
214
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | taskkill /im "Salad.Bootstrapper.exe" /f | C:\Windows\SysWOW64\taskkill.exe | — | Salad-1.7.6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | PowerShell.exe -ExecutionPolicy Bypass -NoLogo -NoProfile -WindowStyle Hidden -Noninteractive -OutputFormat Text -Command "$PSVersionTable.PSVersion" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | system-information-workload.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | librespeed-cli.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | C:\WINDOWS\system32\cmd.exe /d /s /c "yarn --version" | C:\Windows\System32\cmd.exe | — | system-information-workload.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
230 015
Read events
229 915
Write events
60
Delete events
40
Modification events
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
45
Suspicious files
428
Text files
228
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF136082.TMP | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF136092.TMP | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF136092.TMP | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF136092.TMP | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1360a1.TMP | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
83
TCP/UDP connections
208
DNS requests
242
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6208 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kzib7c4bwrq3wgw34civndlcyq_9448/hfnkpimlhhgieaddgfemjhofmfblmnib_9448_all_adhp2cxdszrfvzcihsbdsklw4kba.crx3 | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kzib7c4bwrq3wgw34civndlcyq_9448/hfnkpimlhhgieaddgfemjhofmfblmnib_9448_all_adhp2cxdszrfvzcihsbdsklw4kba.crx3 | unknown | — | — | whitelisted |
6340 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kzib7c4bwrq3wgw34civndlcyq_9448/hfnkpimlhhgieaddgfemjhofmfblmnib_9448_all_adhp2cxdszrfvzcihsbdsklw4kba.crx3 | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kzib7c4bwrq3wgw34civndlcyq_9448/hfnkpimlhhgieaddgfemjhofmfblmnib_9448_all_adhp2cxdszrfvzcihsbdsklw4kba.crx3 | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kzib7c4bwrq3wgw34civndlcyq_9448/hfnkpimlhhgieaddgfemjhofmfblmnib_9448_all_adhp2cxdszrfvzcihsbdsklw4kba.crx3 | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kzib7c4bwrq3wgw34civndlcyq_9448/hfnkpimlhhgieaddgfemjhofmfblmnib_9448_all_adhp2cxdszrfvzcihsbdsklw4kba.crx3 | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kzib7c4bwrq3wgw34civndlcyq_9448/hfnkpimlhhgieaddgfemjhofmfblmnib_9448_all_adhp2cxdszrfvzcihsbdsklw4kba.crx3 | unknown | — | — | whitelisted |
6208 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cxmnq7ci5es7kes4fruun62via_2024.12.17.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2024.12.17.1202_all_adhesfd5wpyhstvspdj4hmgltslq.crx3 | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cxmnq7ci5es7kes4fruun62via_2024.12.17.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2024.12.17.1202_all_adhesfd5wpyhstvspdj4hmgltslq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4536 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4536 | svchost.exe | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
salad.com |
| unknown |
accounts.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
d1b3llzbo1rqxo.cloudfront.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6544 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6544 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6544 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6544 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6544 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6544 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6544 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6544 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6544 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6544 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |