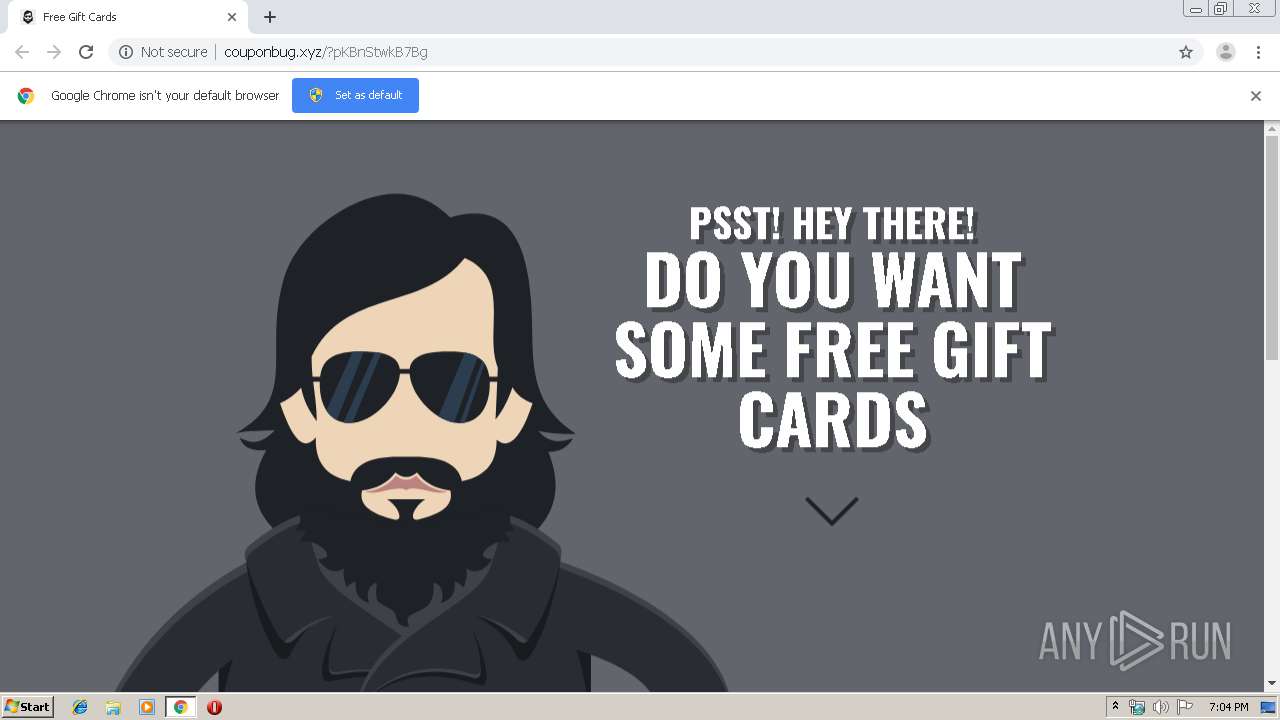
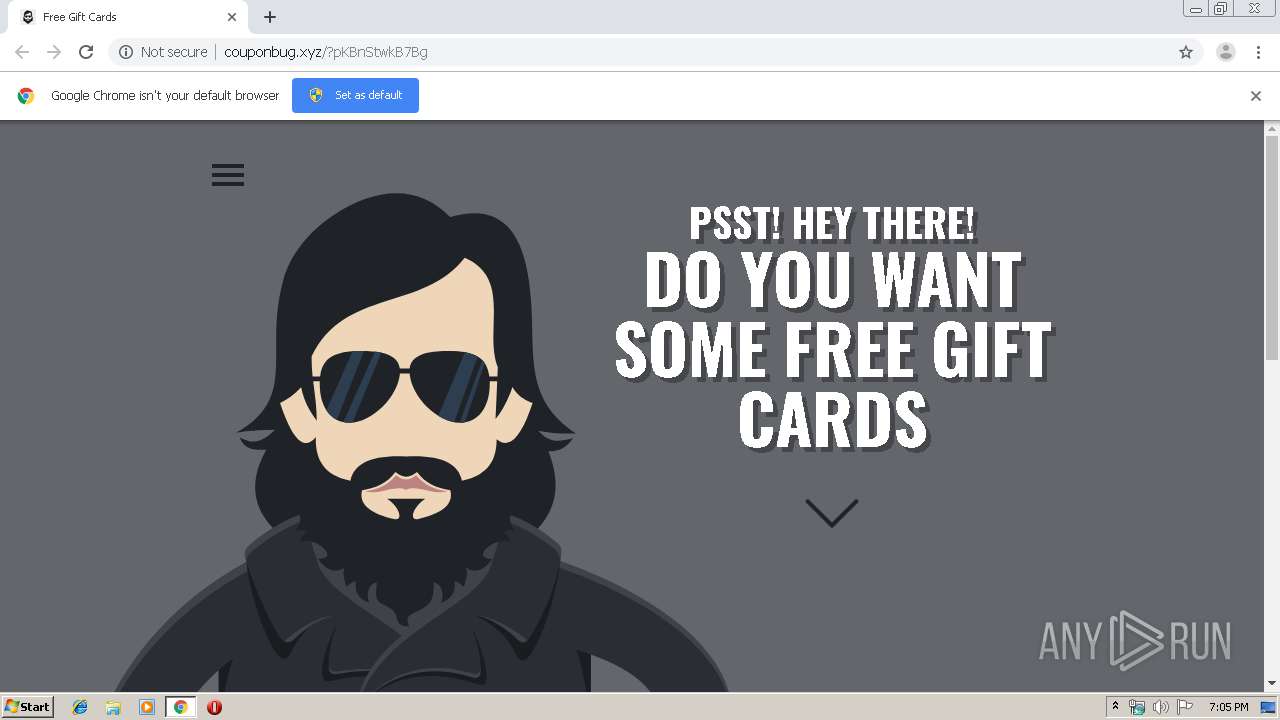
| URL: | http://couponbug.xyz/?pKBnStwkB7Bg |
| Full analysis: | https://app.any.run/tasks/97569def-47c5-4a0f-a524-f146970f06a0 |
| Verdict: | Suspicious activity |
| Analysis date: | October 01, 2019, 18:03:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8564A228CC4FDCF985B2C0A3567BB61C |
| SHA1: | 138DD970A44E6D78DE67B09C26539D3B36E176E4 |
| SHA256: | 439ACF8064207ECF15FA19622655A8259E1EE3265D101083448D44B5B7F0B291 |
| SSDEEP: | 3:N1KdKQeefjxL:CIQTxL |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2356)
INFO
Reads the hosts file
- chrome.exe (PID: 2356)
- chrome.exe (PID: 1880)
Application launched itself
- chrome.exe (PID: 2356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13882282357020559152,5378298326926916686,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=369711902875935513 --mojo-platform-channel-handle=3648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13882282357020559152,5378298326926916686,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10395304702139114640 --mojo-platform-channel-handle=3444 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13882282357020559152,5378298326926916686,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3896840599526546592 --mojo-platform-channel-handle=1600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13882282357020559152,5378298326926916686,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3093036335833588450 --mojo-platform-channel-handle=3496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,13882282357020559152,5378298326926916686,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18117414098863284834 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://couponbug.xyz/?pKBnStwkB7Bg" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13882282357020559152,5378298326926916686,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18258005397436707853 --mojo-platform-channel-handle=3428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13882282357020559152,5378298326926916686,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16566805018900534509 --mojo-platform-channel-handle=3280 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13882282357020559152,5378298326926916686,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13207665177448187046 --mojo-platform-channel-handle=3460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13882282357020559152,5378298326926916686,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6417210102435379944 --mojo-platform-channel-handle=3448 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
604
Read events
520
Write events
79
Delete events
5
Modification events
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2356-13214426654616125 |
Value: 259 | |||
| (PID) Process: | (2356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2356) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2356) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
14
Text files
138
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\47df0409-131d-42c7-9b1a-3e07885609fa.tmp | — | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF100f44.TMP | text | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF100f82.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
24
DNS requests
13
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1880 | chrome.exe | GET | 200 | 104.31.90.193:80 | http://couponbug.xyz/?pKBnStwkB7Bg | US | html | 26.6 Kb | suspicious |
1880 | chrome.exe | GET | 200 | 104.31.90.193:80 | http://couponbug.xyz/plugins.js | US | text | 14.2 Kb | suspicious |
1880 | chrome.exe | GET | 200 | 104.31.90.193:80 | http://couponbug.xyz/css.css?family=Oswald:700 | US | text | 162 b | suspicious |
1880 | chrome.exe | GET | 200 | 198.27.69.19:80 | http://s4.histats.com/stats/e.php?4273030&@Ab&@R85496&@w | CA | text | 51 b | whitelisted |
1880 | chrome.exe | GET | 200 | 46.105.201.240:80 | http://s10.histats.com/js15_as.js | FR | html | 4.42 Kb | whitelisted |
1880 | chrome.exe | GET | 200 | 198.27.69.19:80 | http://s4.histats.com/stats/0.php?4273030&@f16&@g1&@h1&@i1&@j1569953057372&@k0&@l1&@mFree%20Gift%20Cards&@n0&@o1000&@q0&@r0&@s0&@ten-US&@u1280&@b1:151753363&@b3:1569953057&@b4:js15_as.js&@b5:60&@a-_0.2.1&@vhttp%3A%2F%2Fcouponbug.xyz%2F%3FpKBnStwkB7Bg&@w | CA | text | 51 b | whitelisted |
1880 | chrome.exe | GET | 200 | 104.31.90.193:80 | http://couponbug.xyz/assets/js/h.js | US | text | 268 b | suspicious |
1880 | chrome.exe | GET | 200 | 104.31.90.193:80 | http://couponbug.xyz/css_9v3lNV.css?family=Open+Sans:400,600 | US | text | 209 b | suspicious |
1880 | chrome.exe | GET | 200 | 104.31.90.193:80 | http://couponbug.xyz/jquery.min.js | US | text | 32.5 Kb | suspicious |
1880 | chrome.exe | GET | 200 | 185.180.12.140:80 | http://r1---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.107.227&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1569952785&mv=u&mvi=0&pl=24&shardbypass=yes | AT | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1880 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 151.101.112.193:443 | i.imgur.com | Fastly | US | malicious |
1880 | chrome.exe | 198.27.69.19:80 | s4.histats.com | OVH SAS | CA | suspicious |
1880 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.22.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.22.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 151.101.2.109:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
1880 | chrome.exe | 46.105.201.240:80 | s10.histats.com | OVH SAS | FR | suspicious |
1880 | chrome.exe | 151.101.66.109:443 | cdn.jsdelivr.net | Fastly | US | unknown |
1880 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
couponbug.xyz |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdn.jsdelivr.net |
| whitelisted |
s10.histats.com |
| whitelisted |
s4.histats.com |
| whitelisted |
i.imgur.com |
| malicious |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1880 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1880 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1880 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1880 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1880 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1880 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1880 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1880 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |