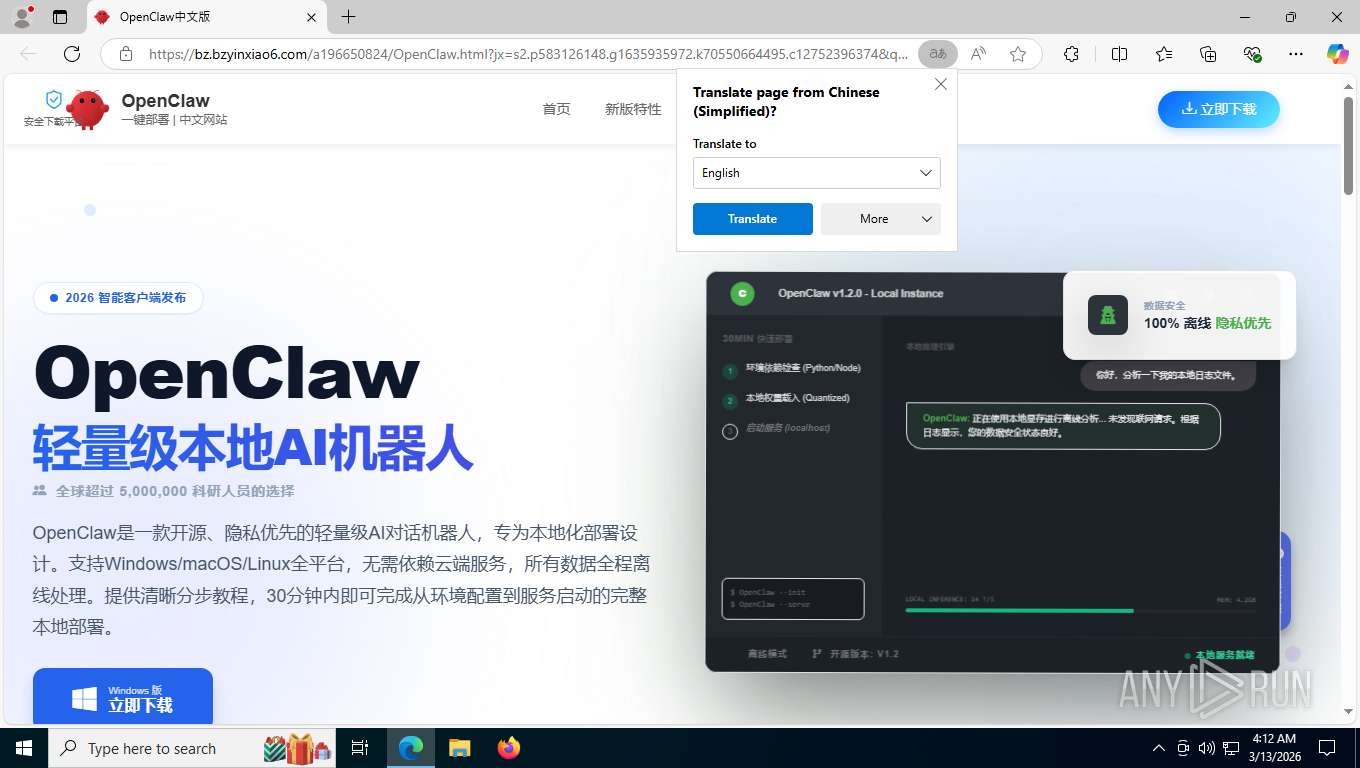
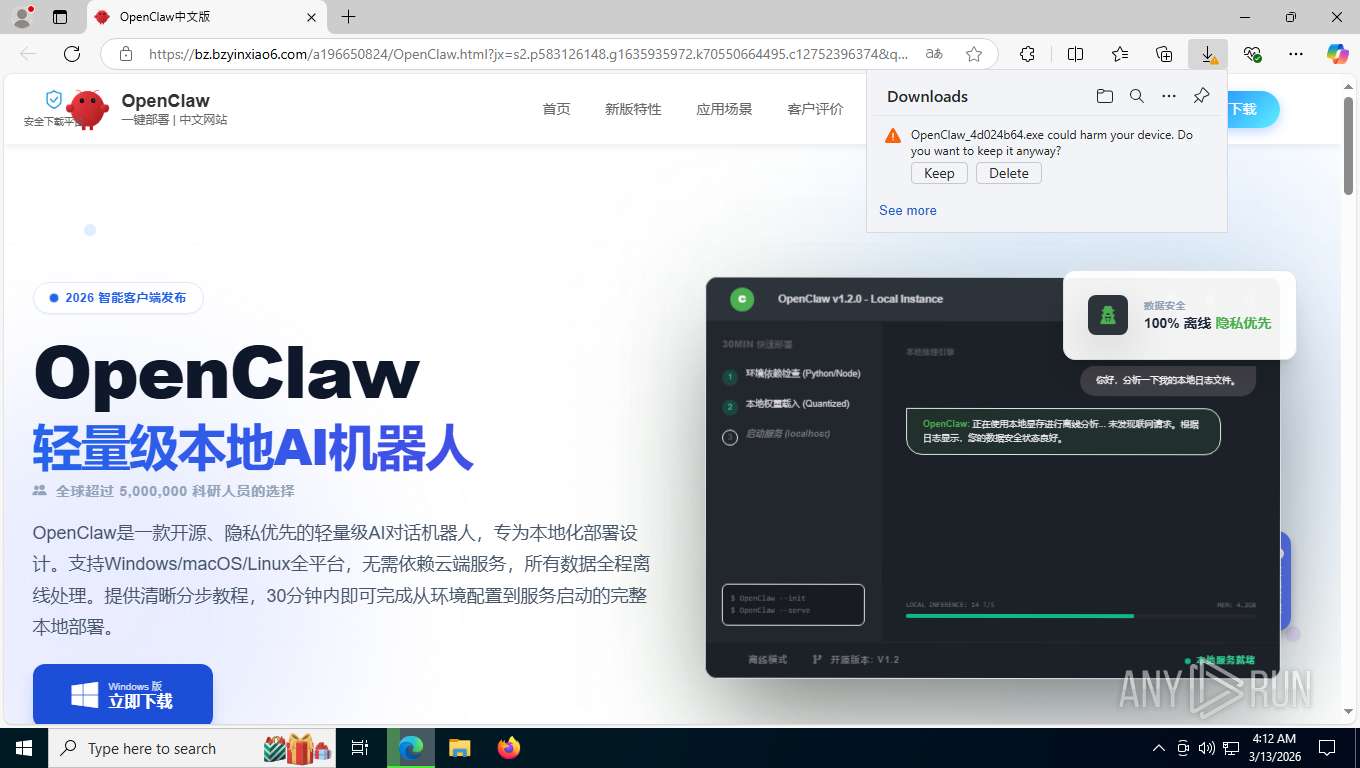
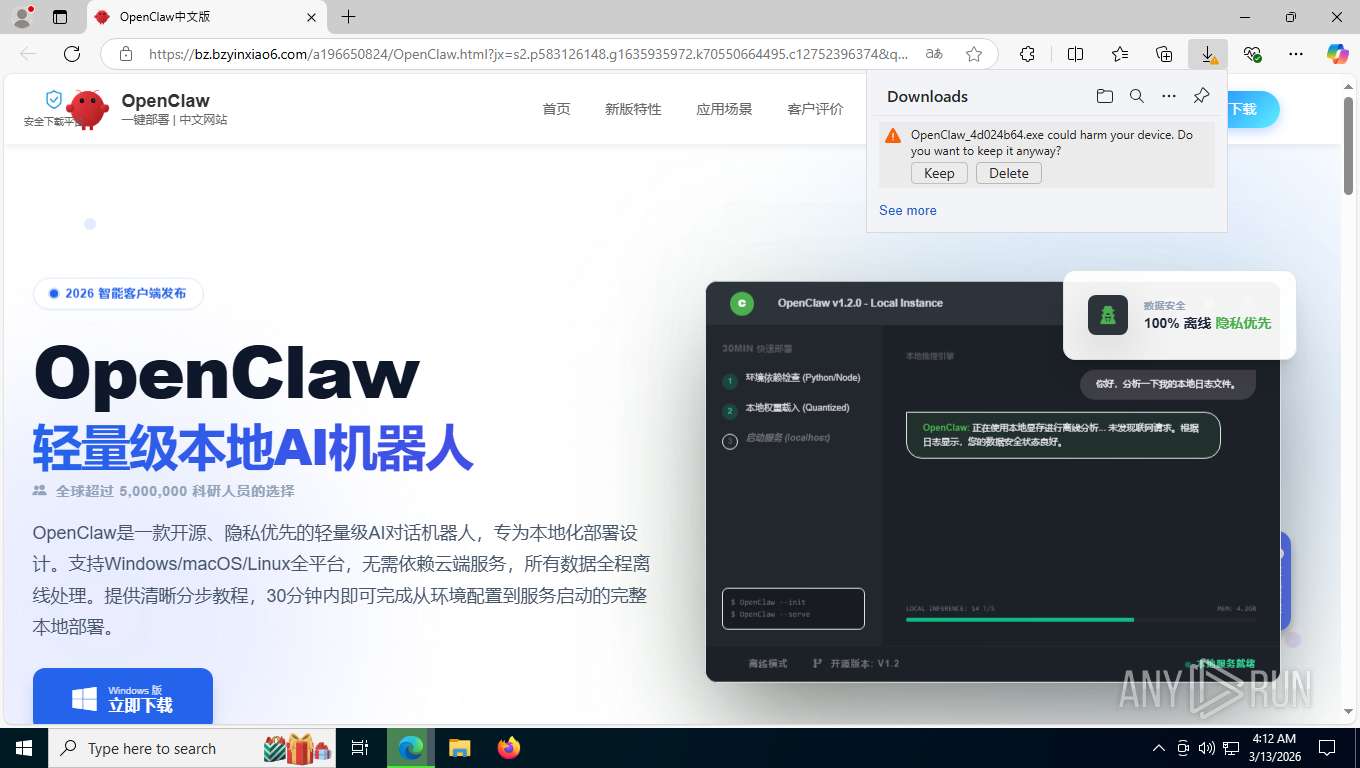
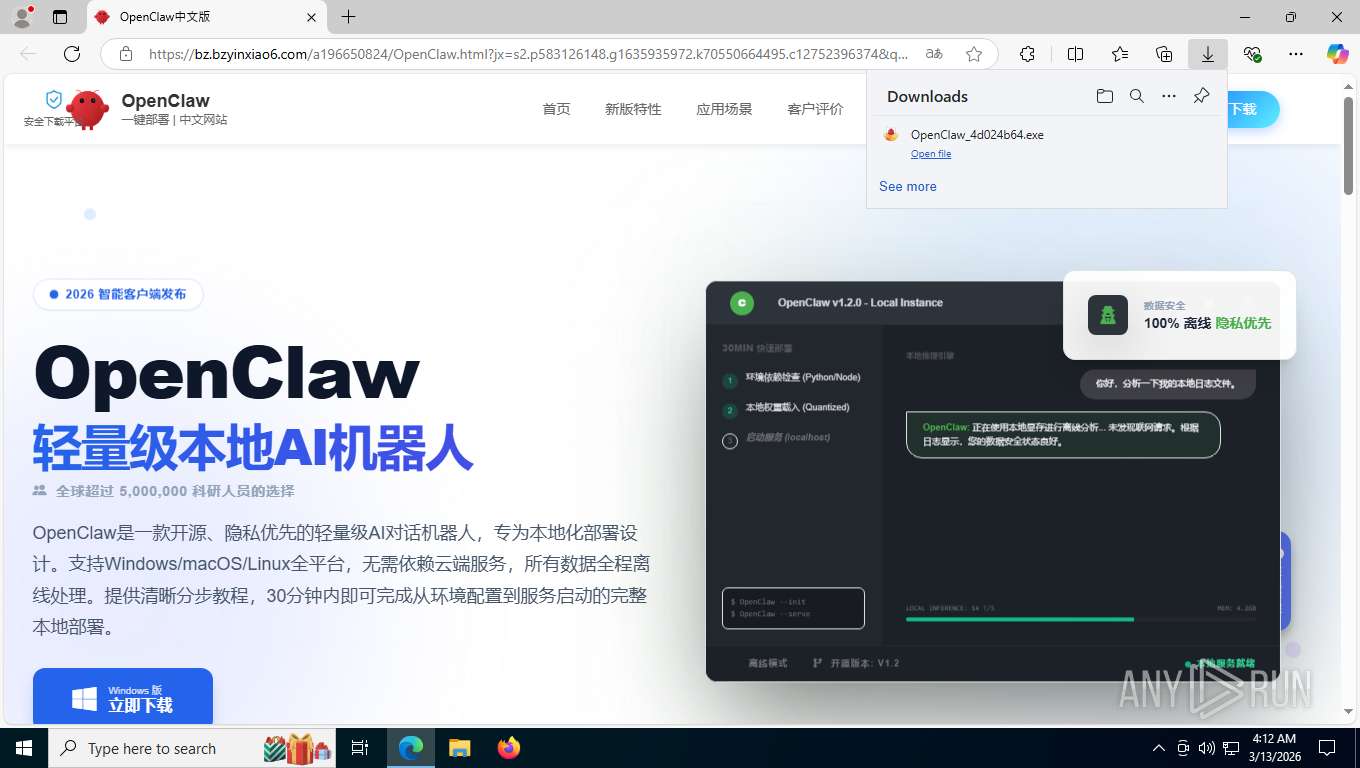
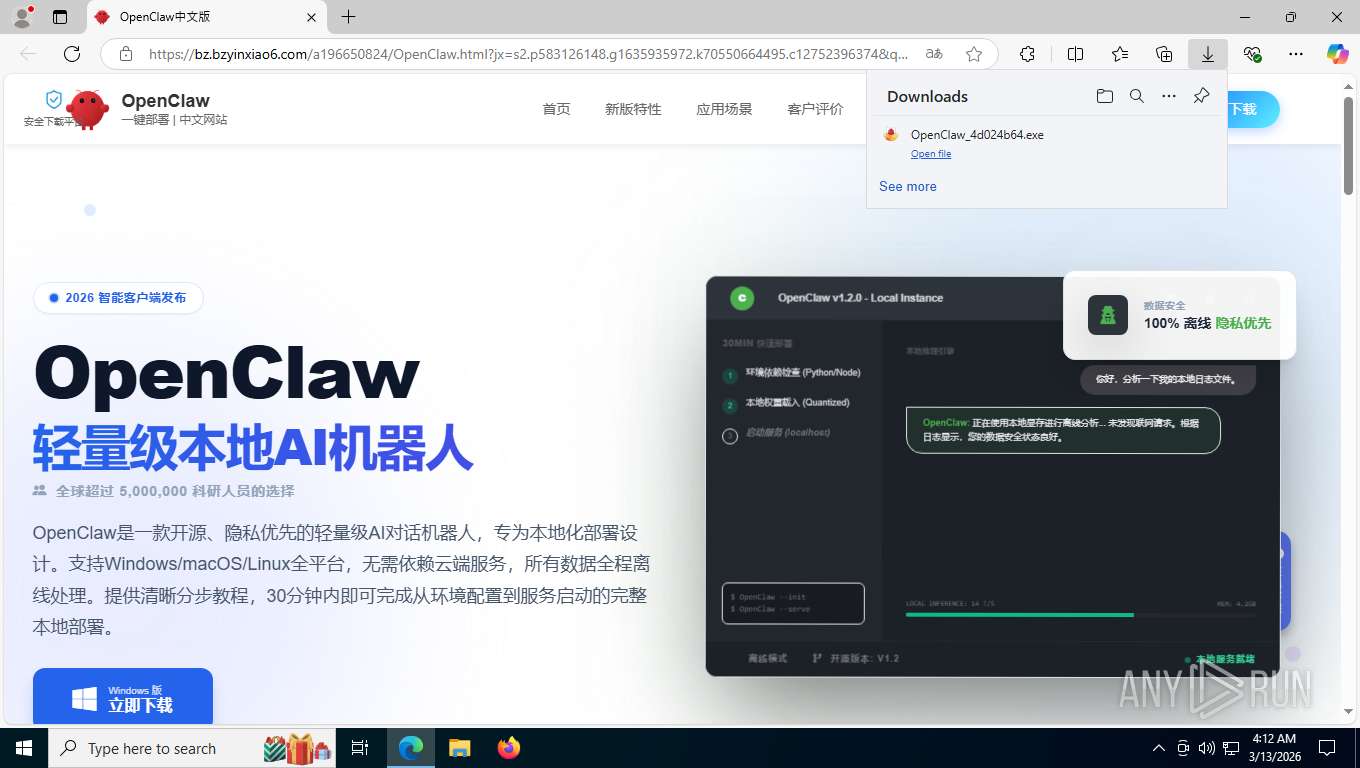
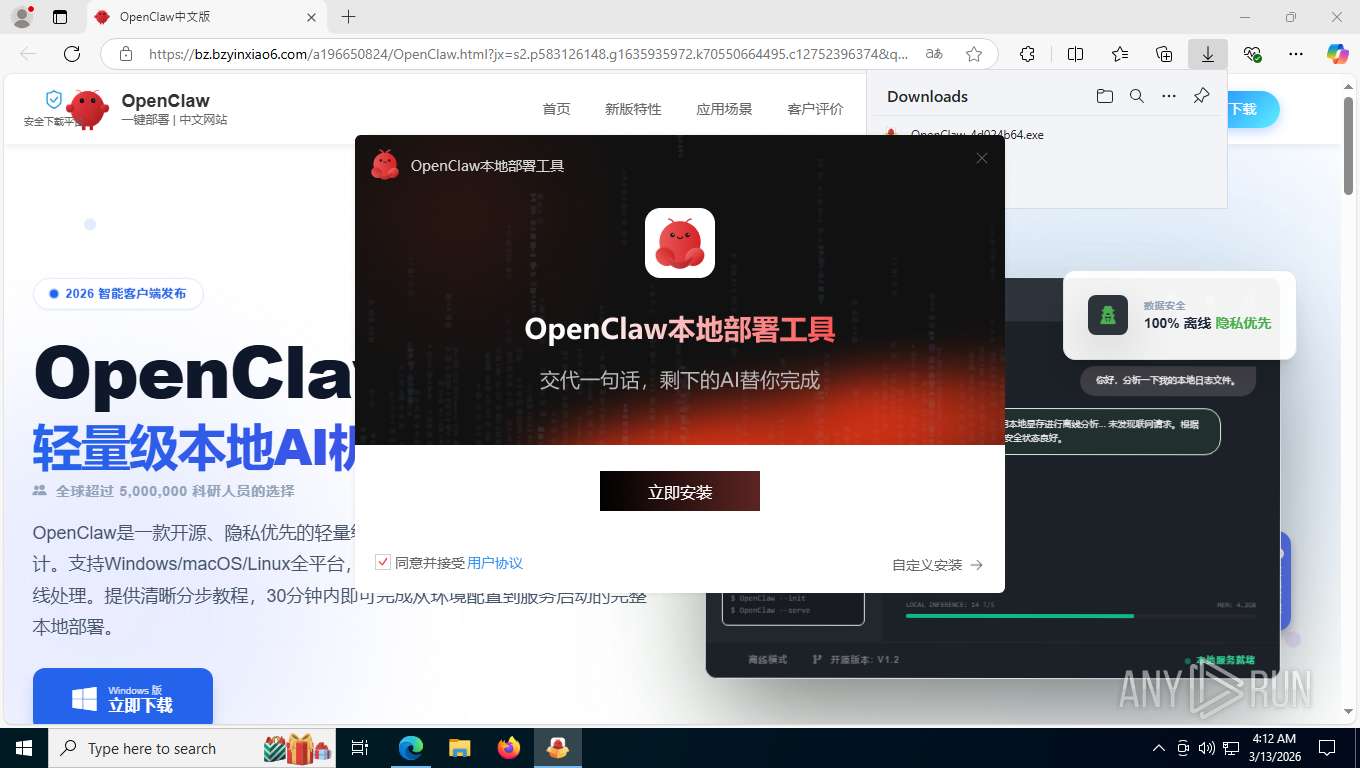
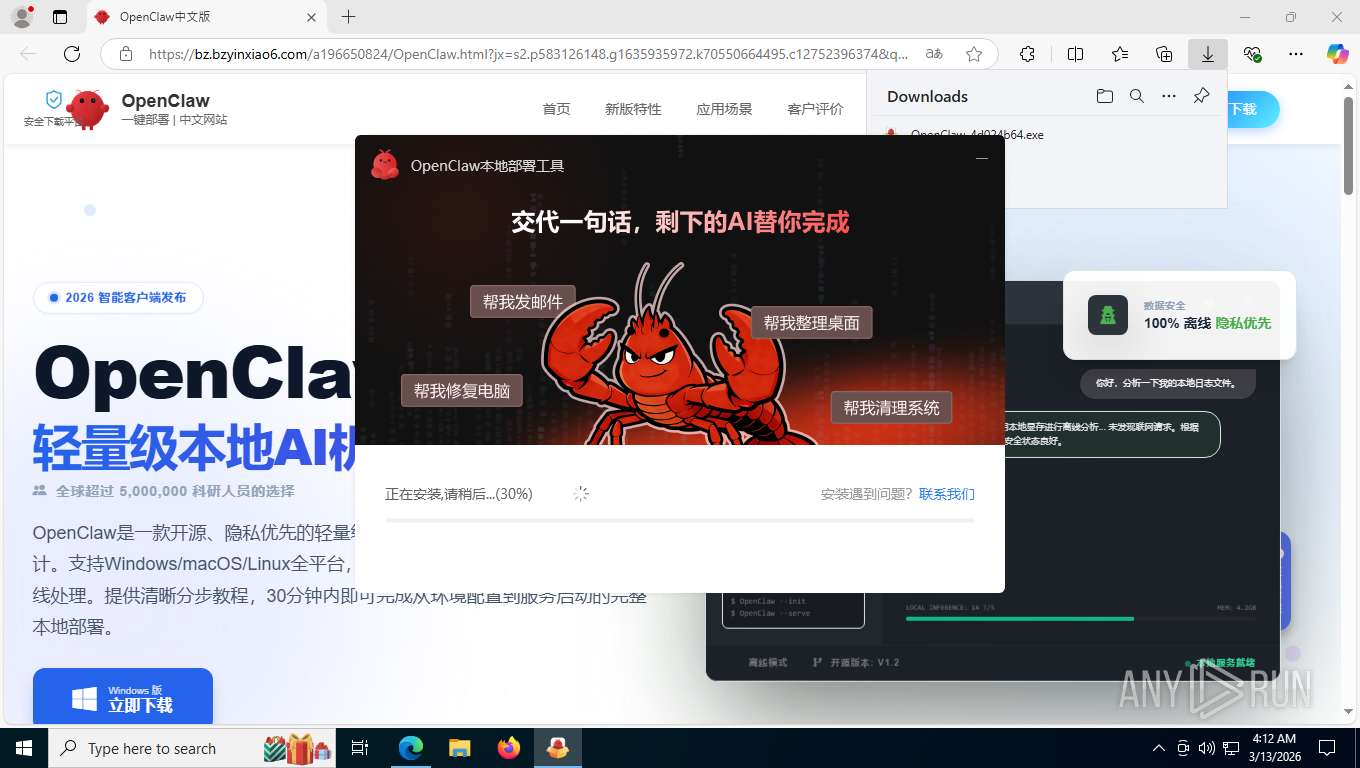
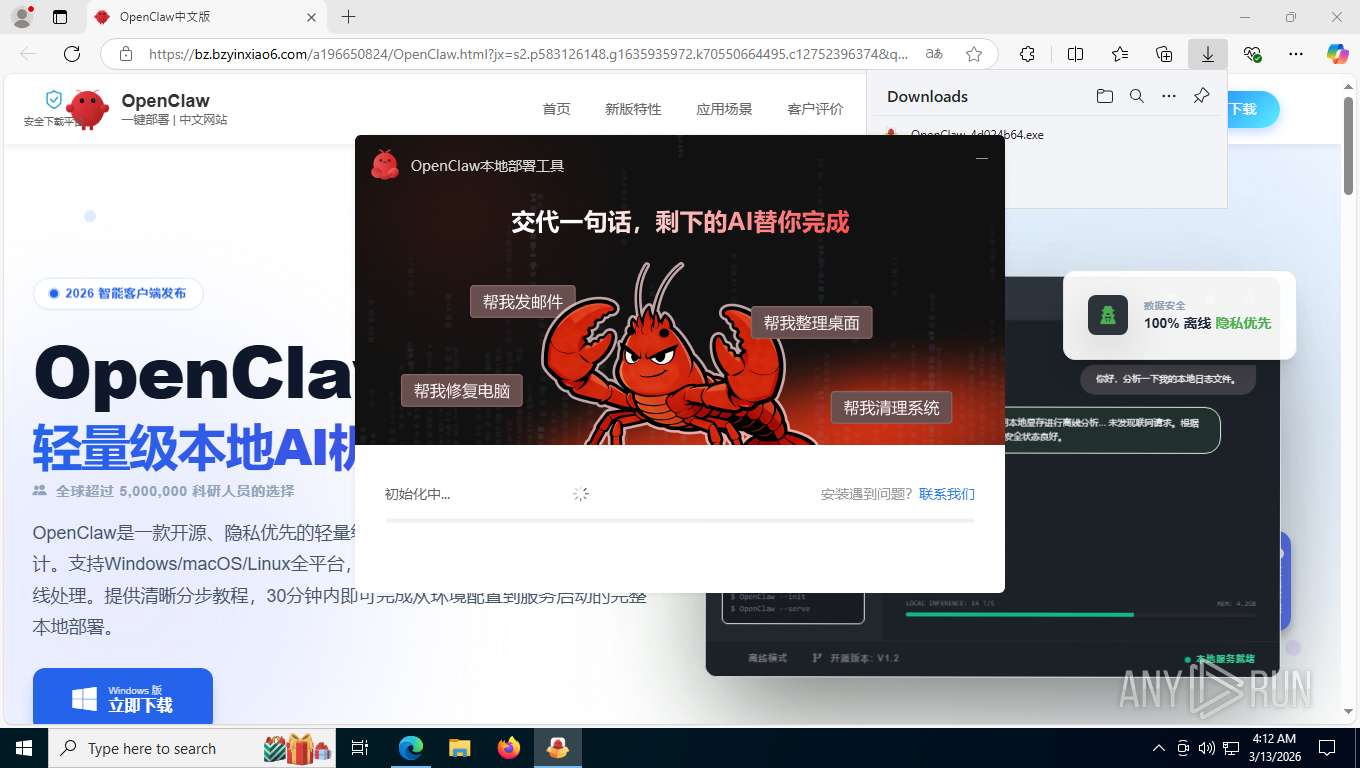
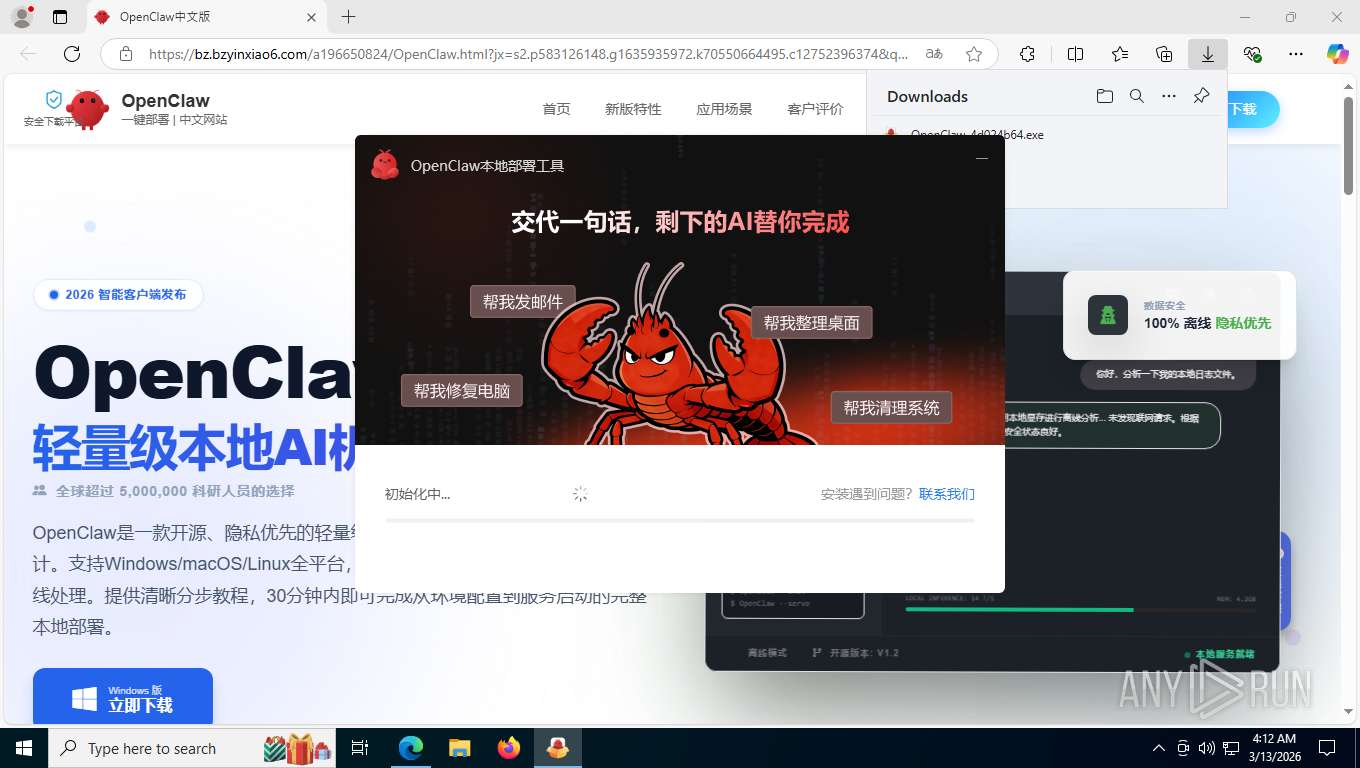
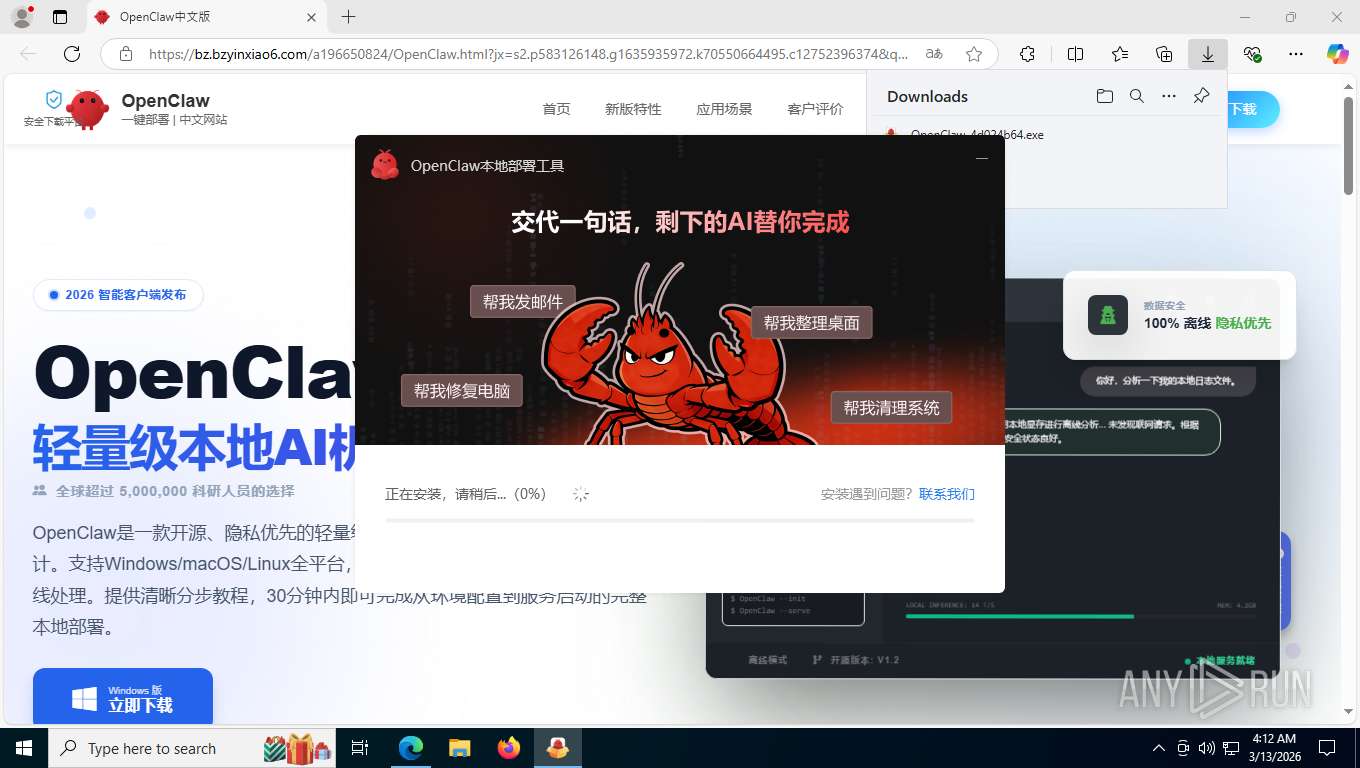
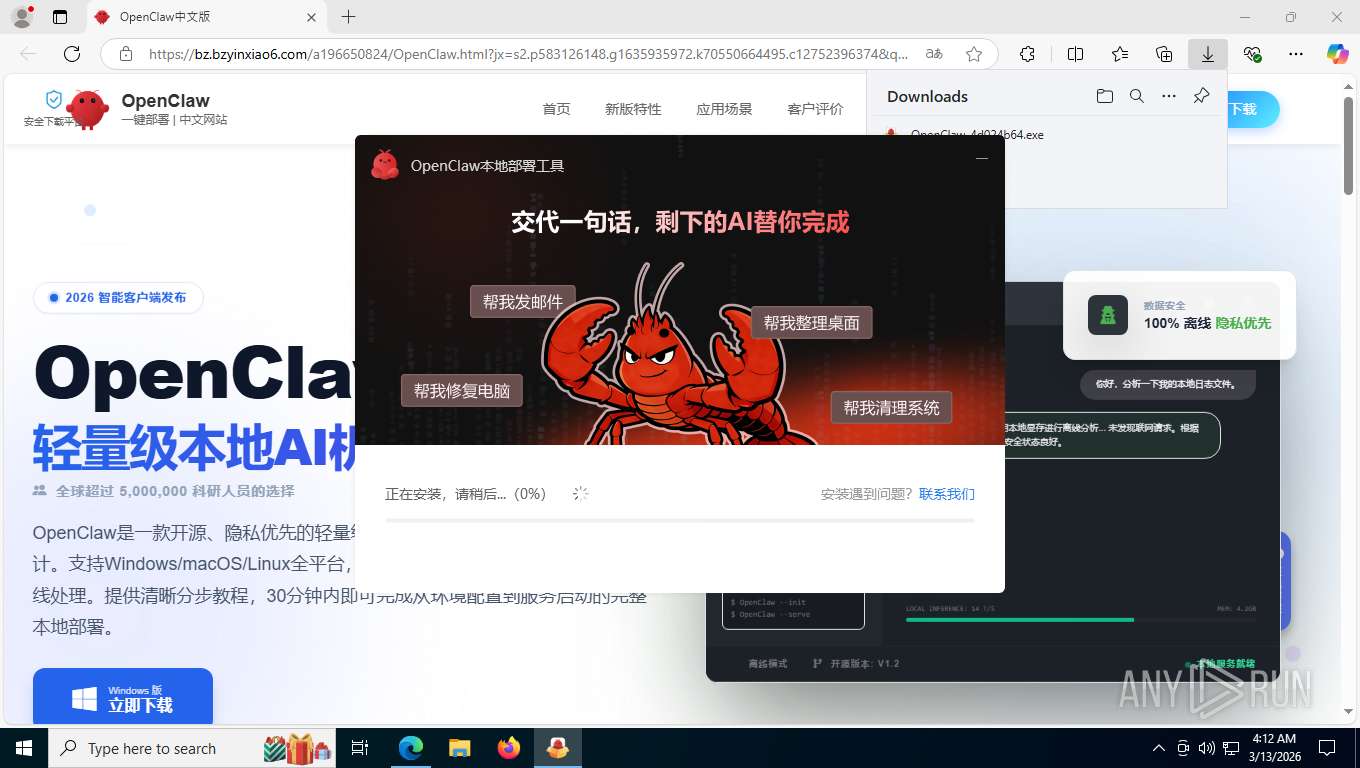
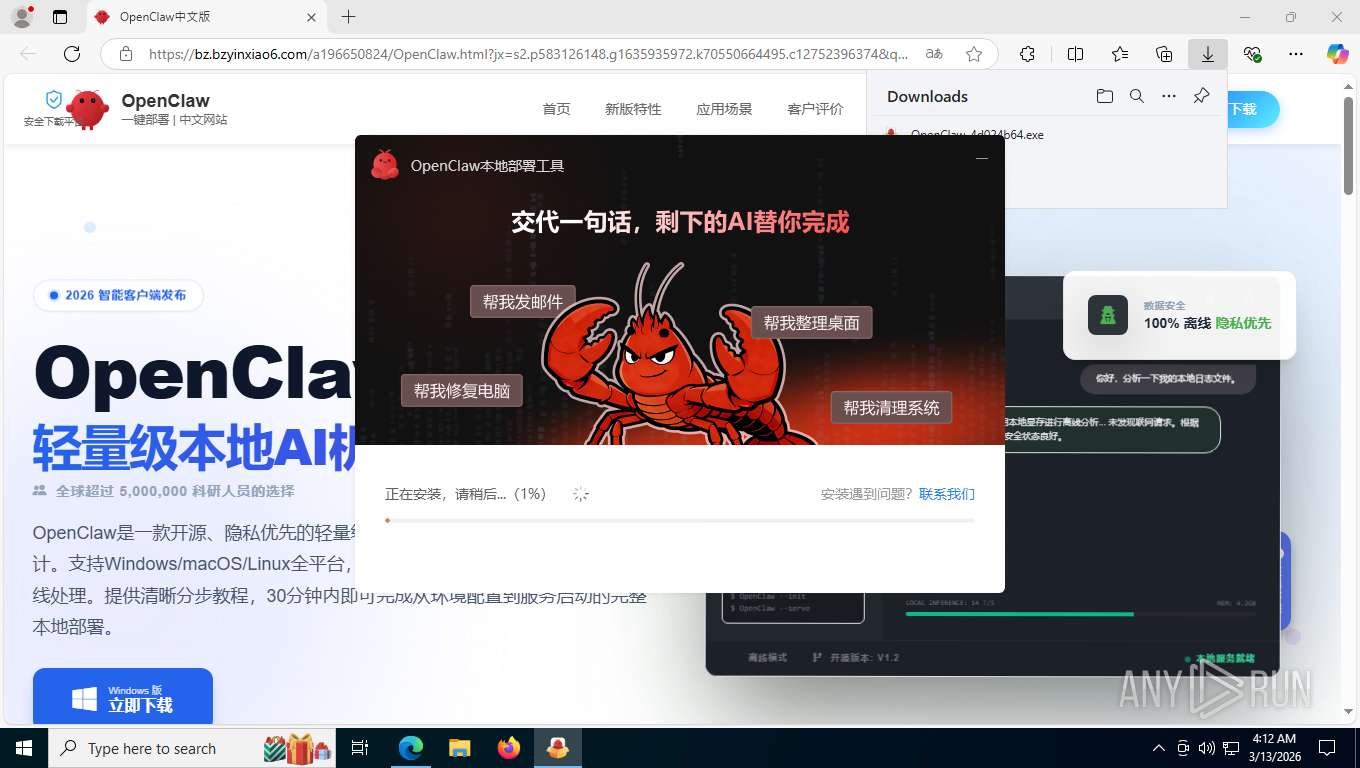
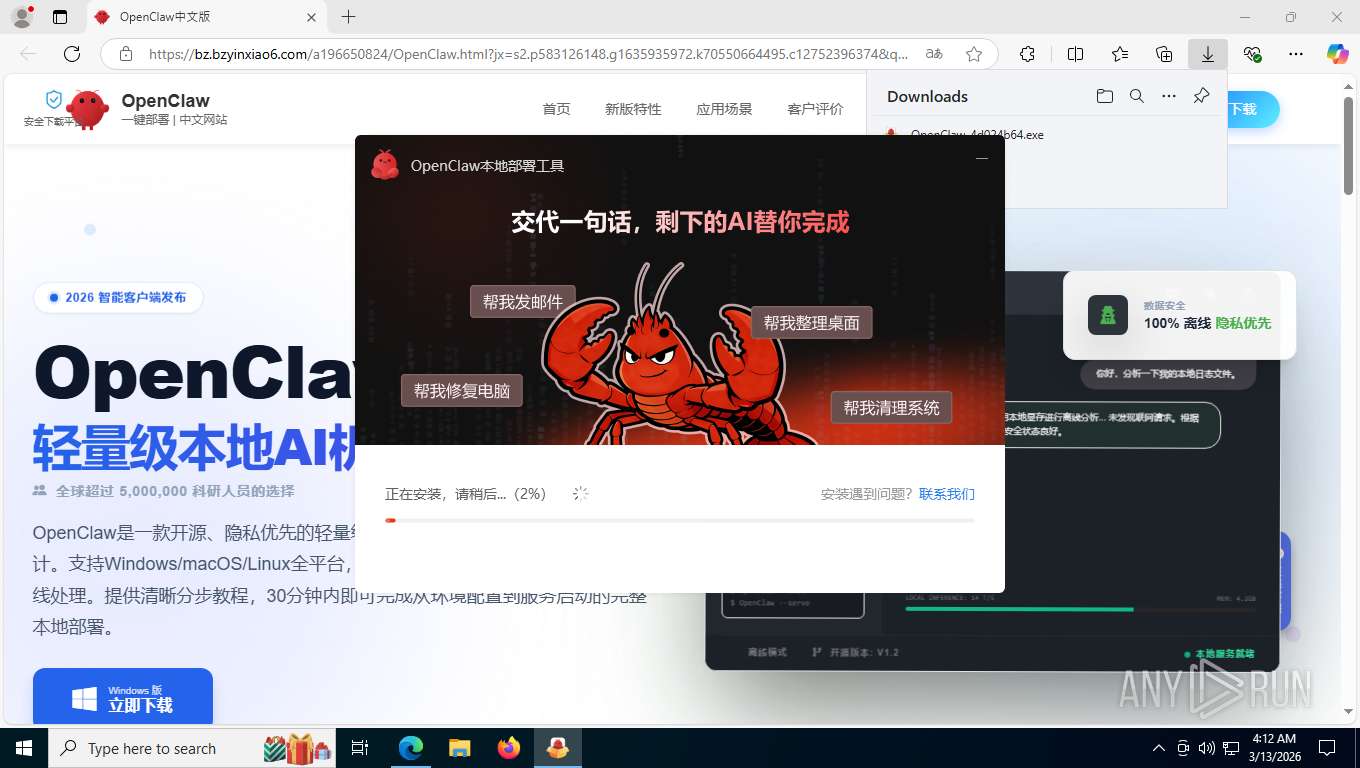
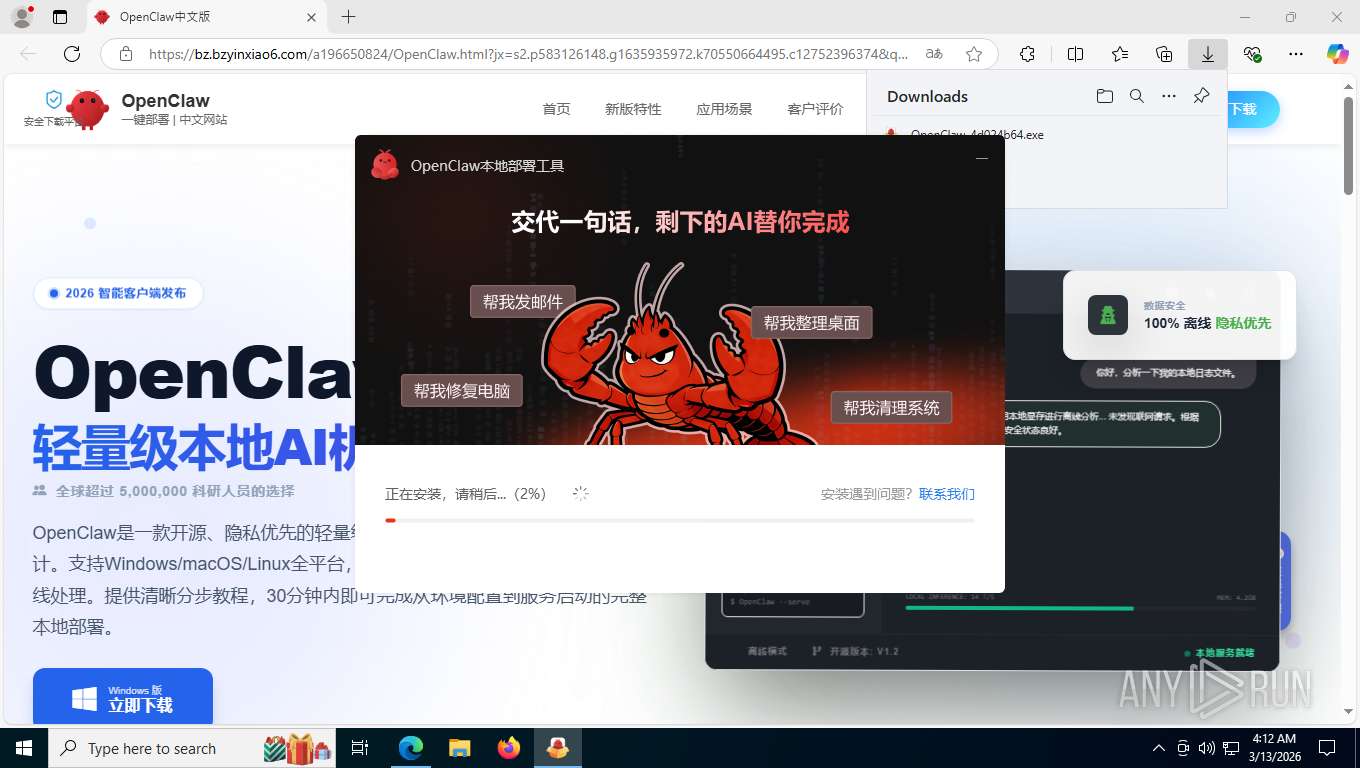
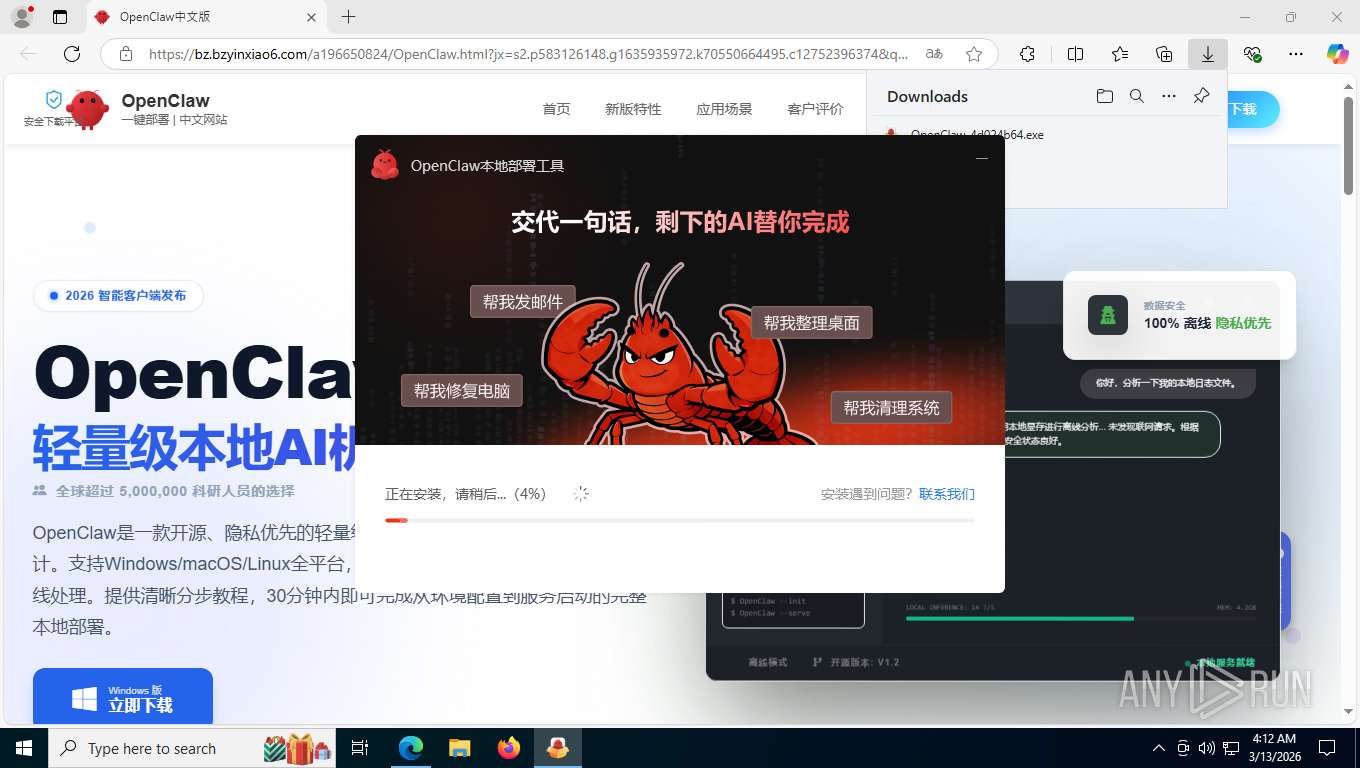
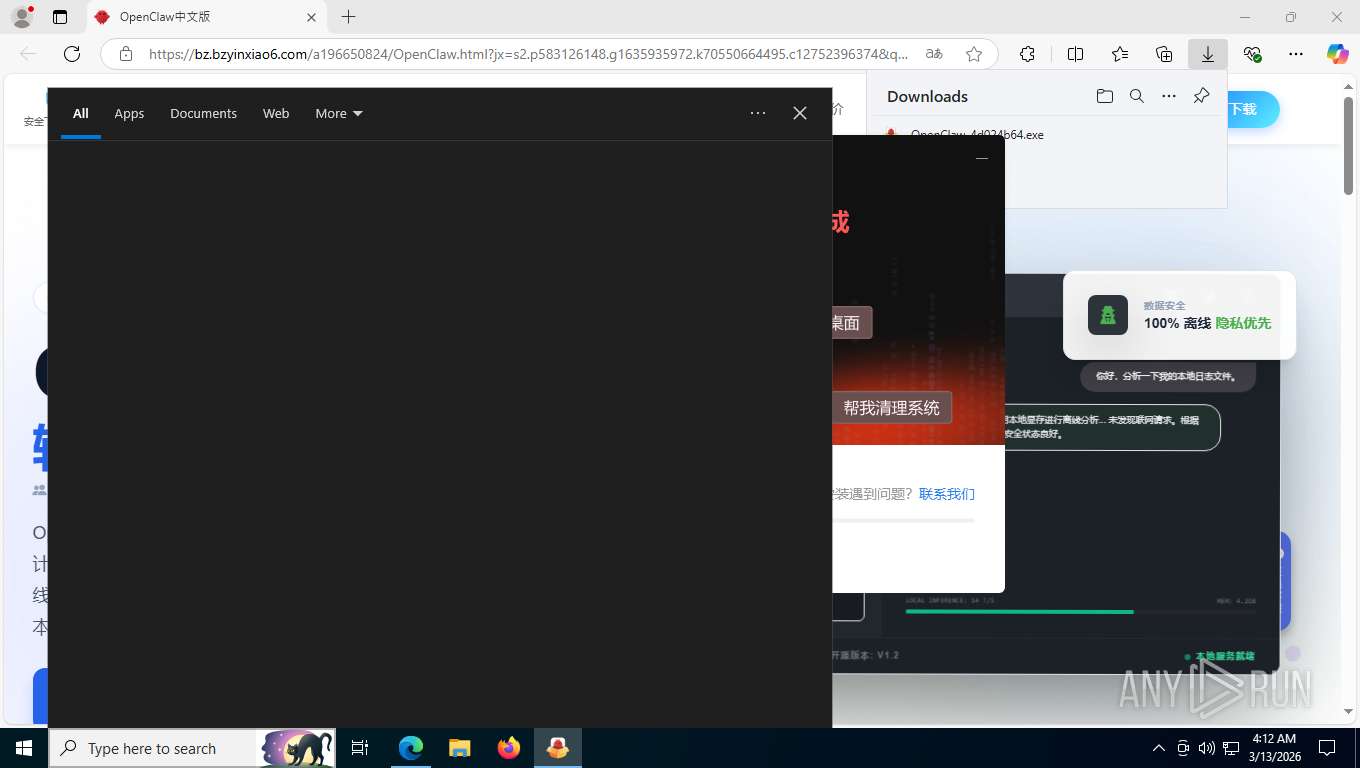
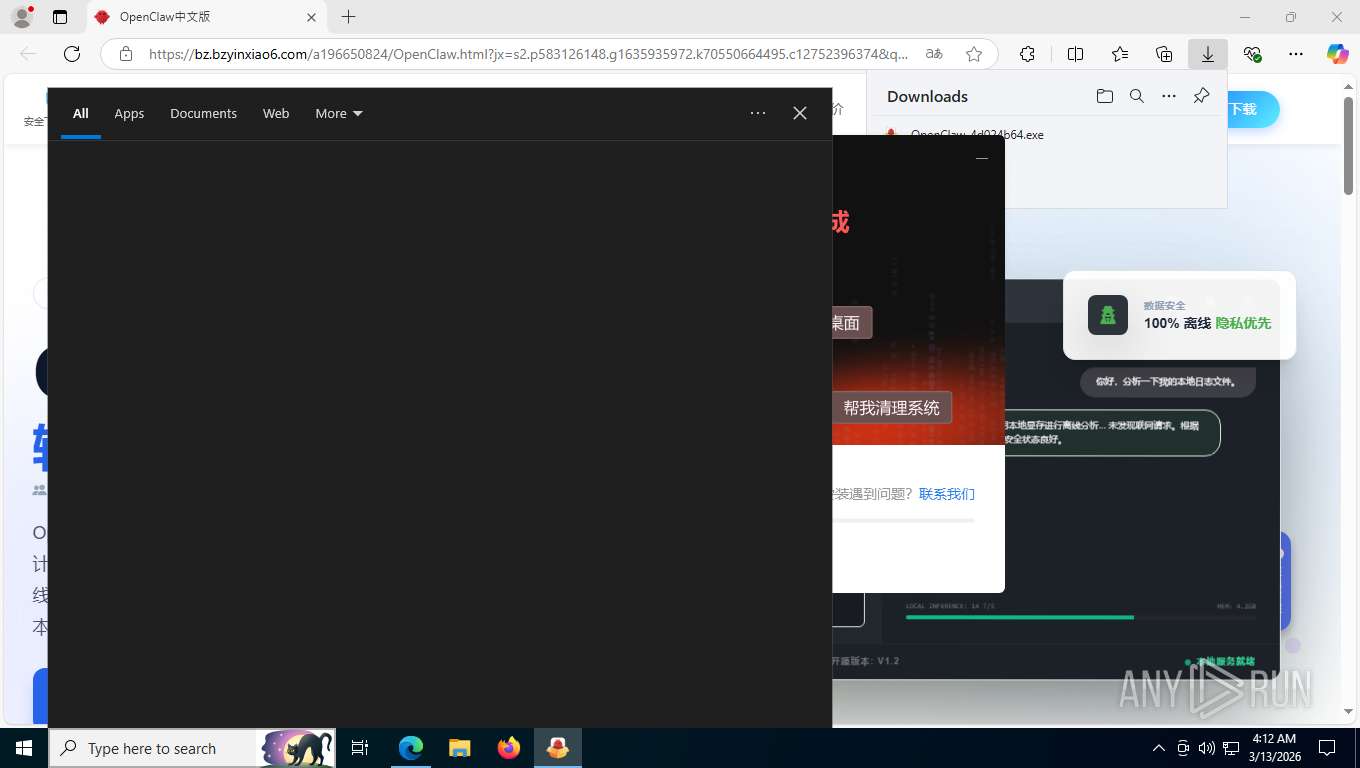
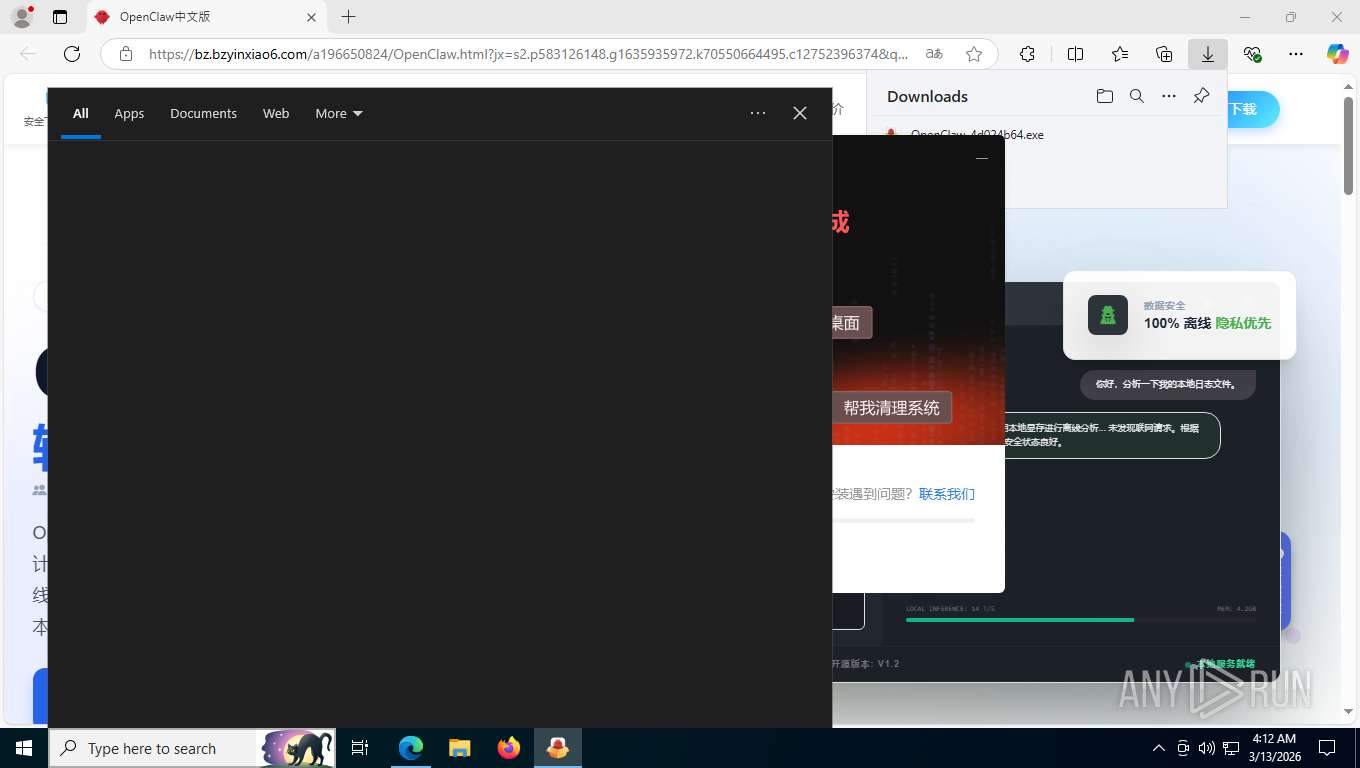
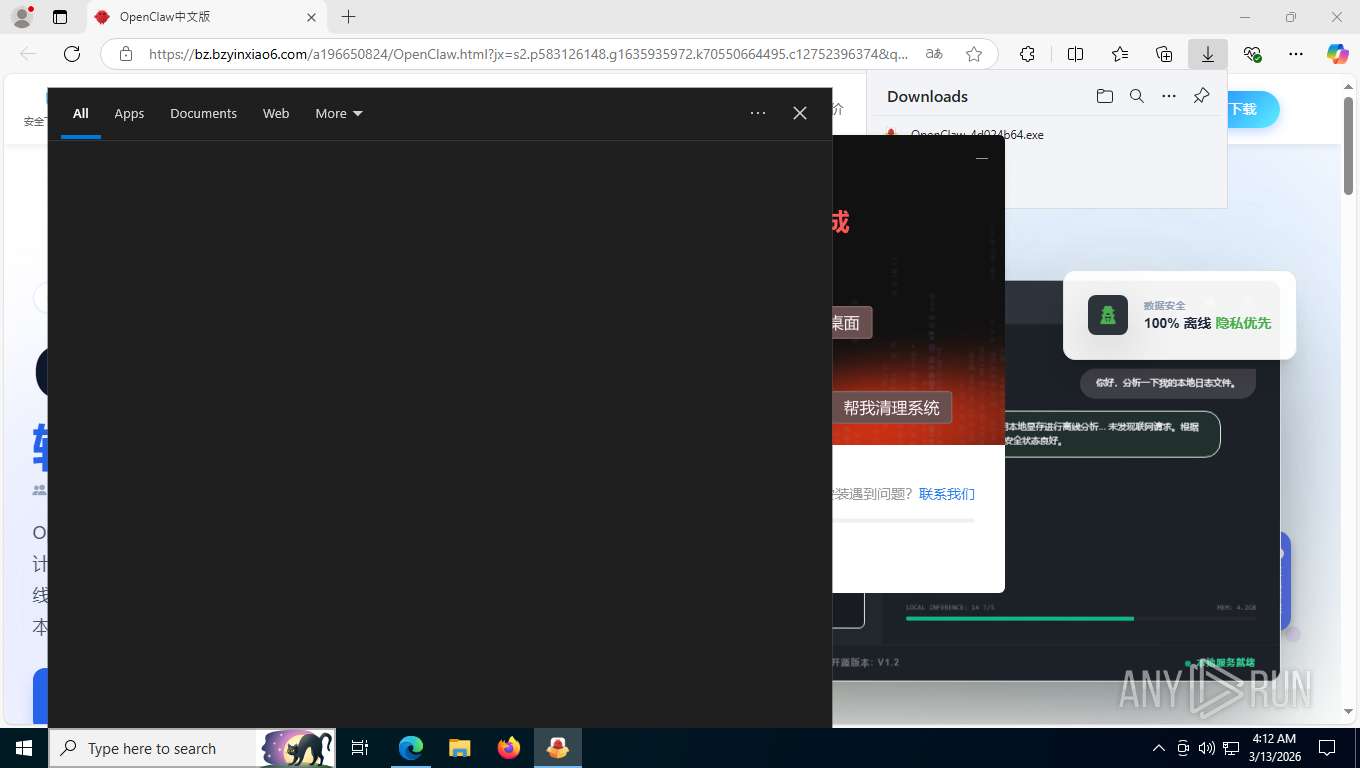
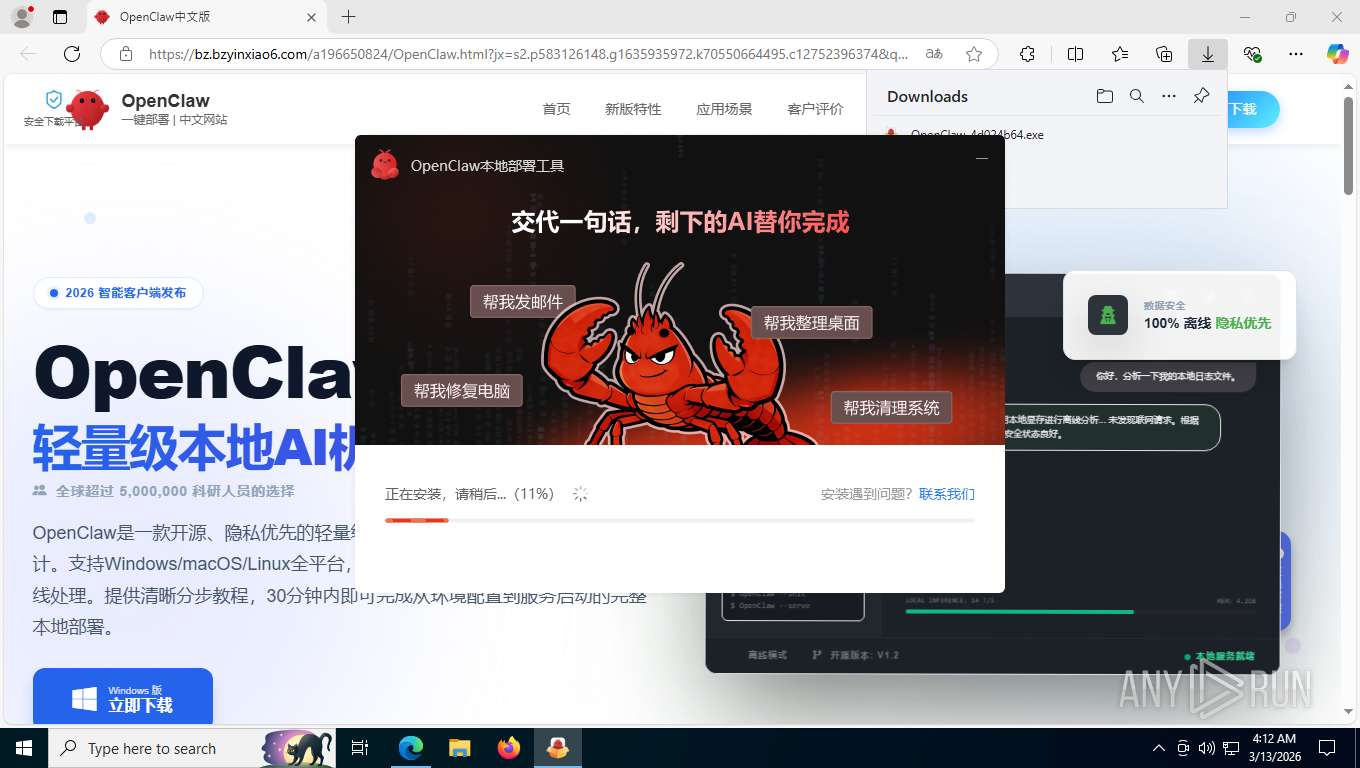
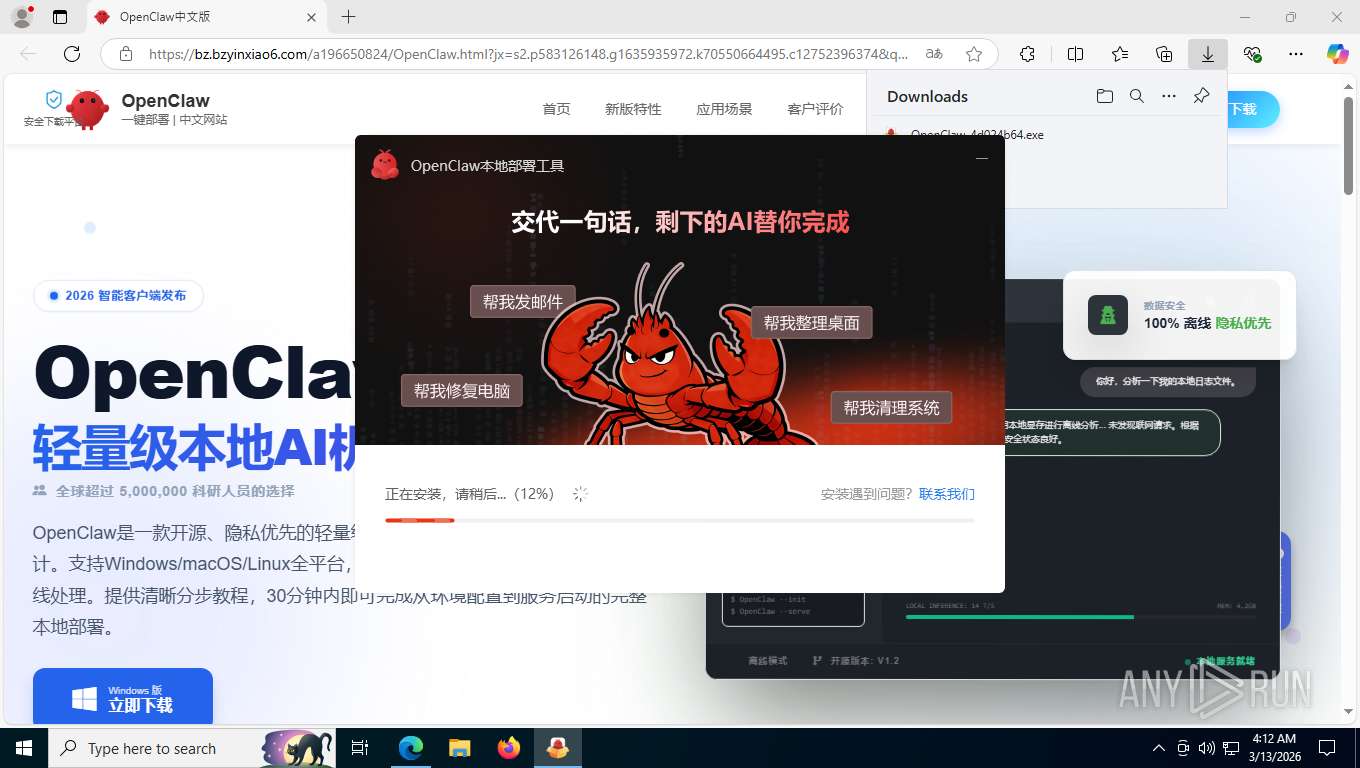
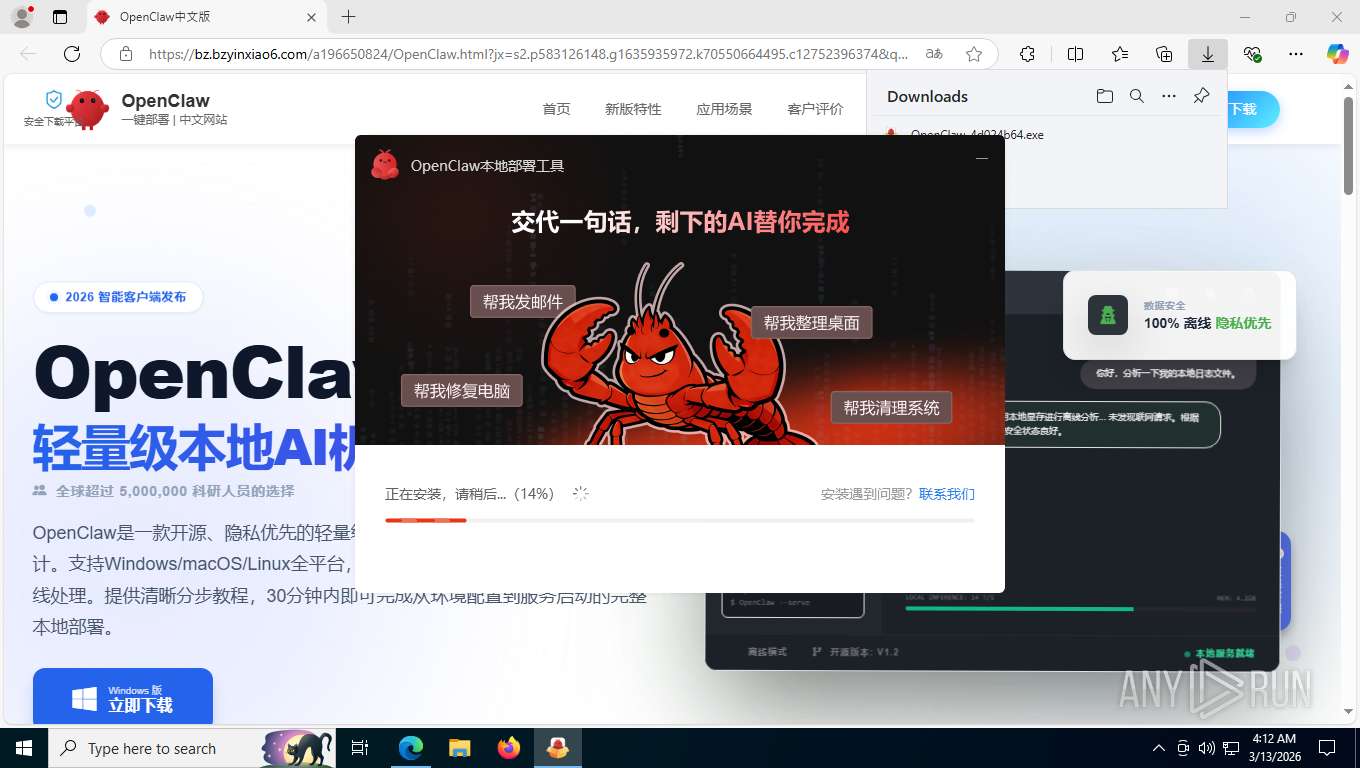
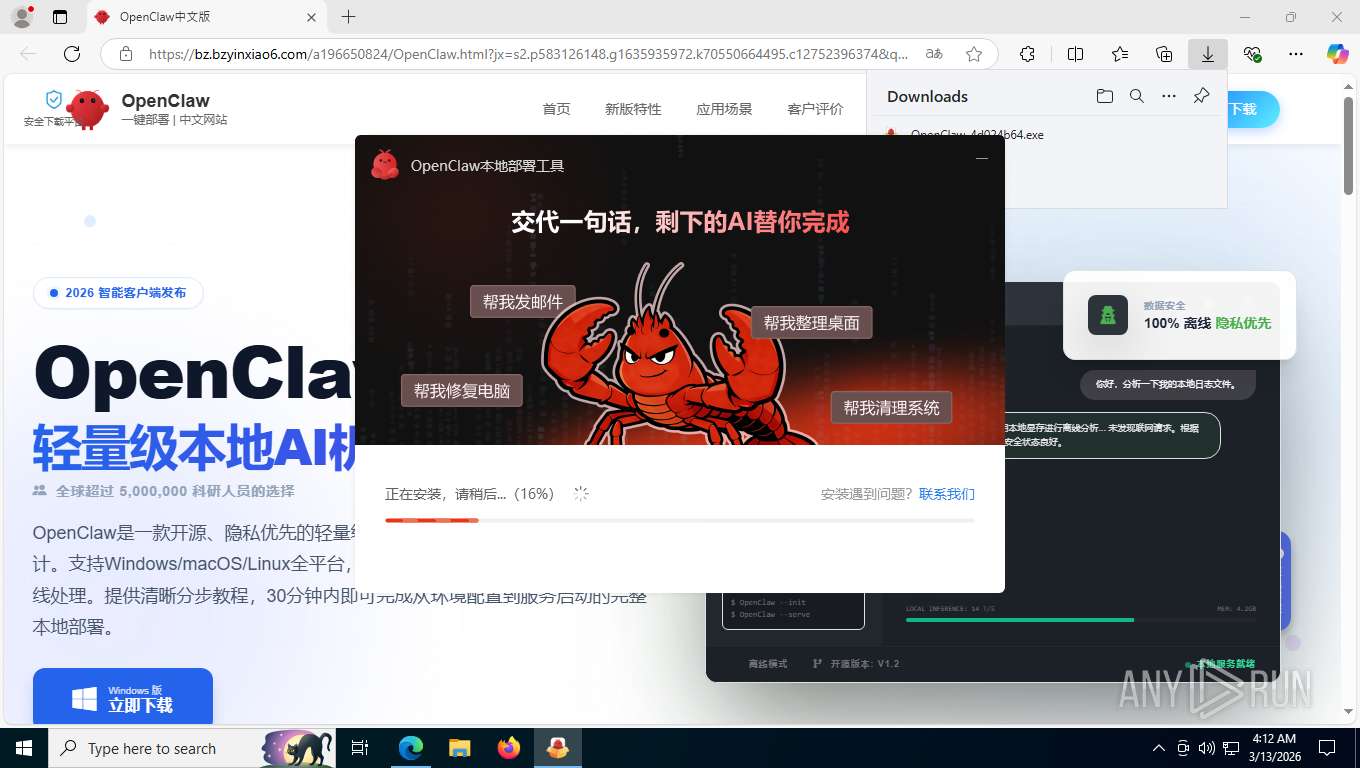
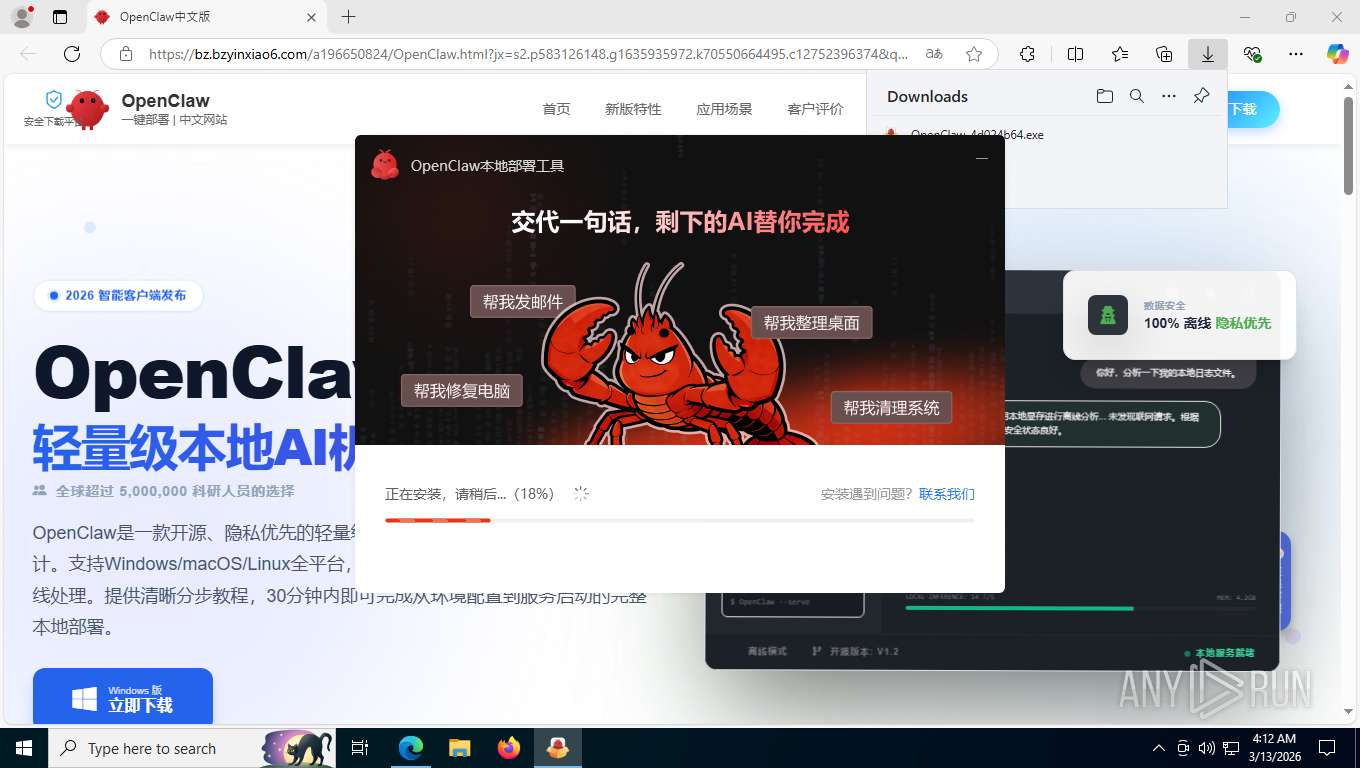
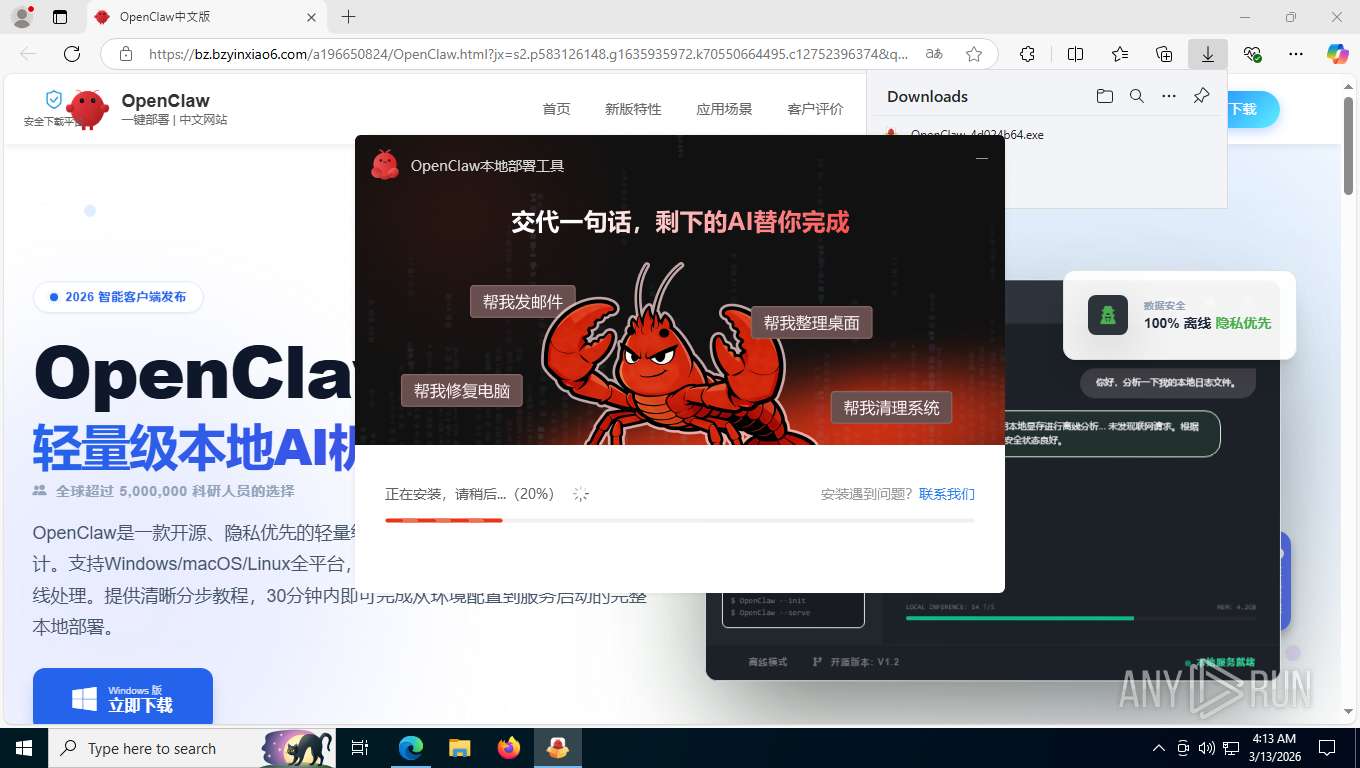
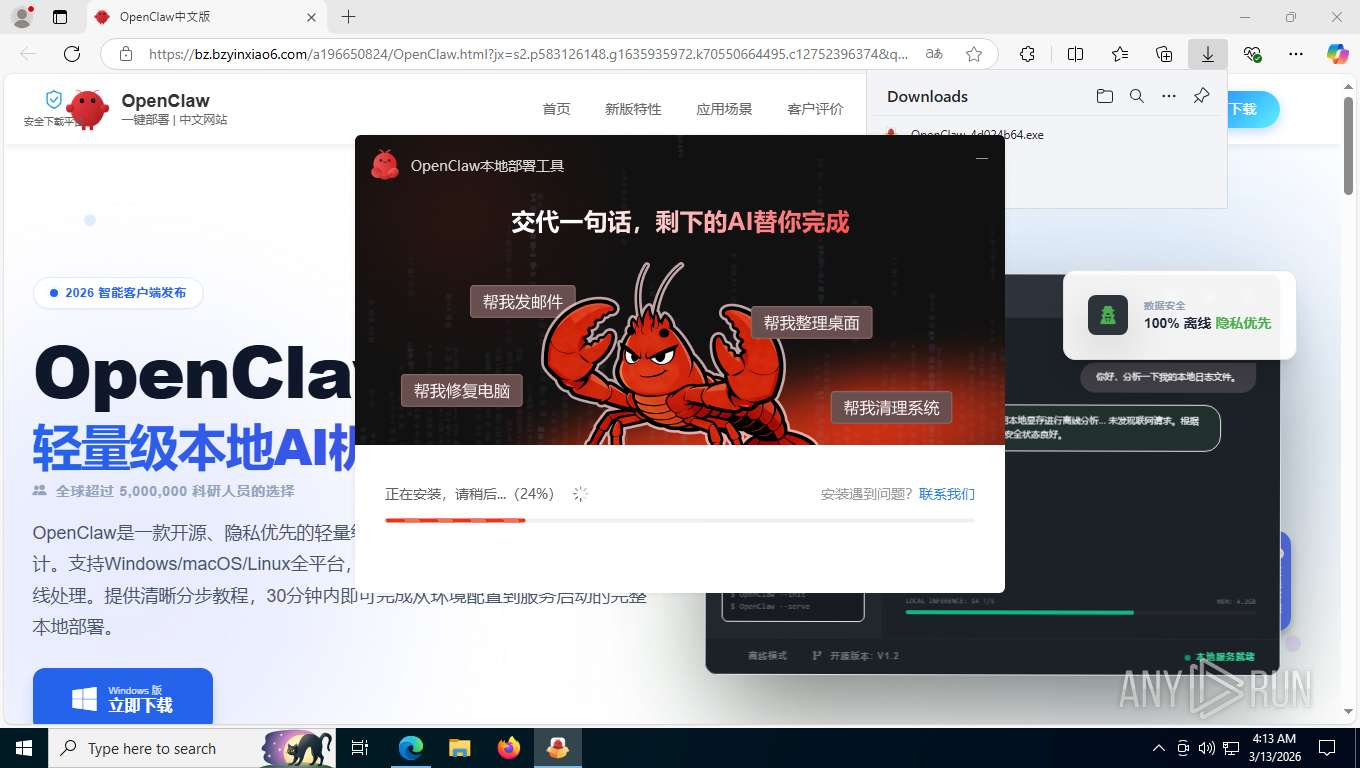
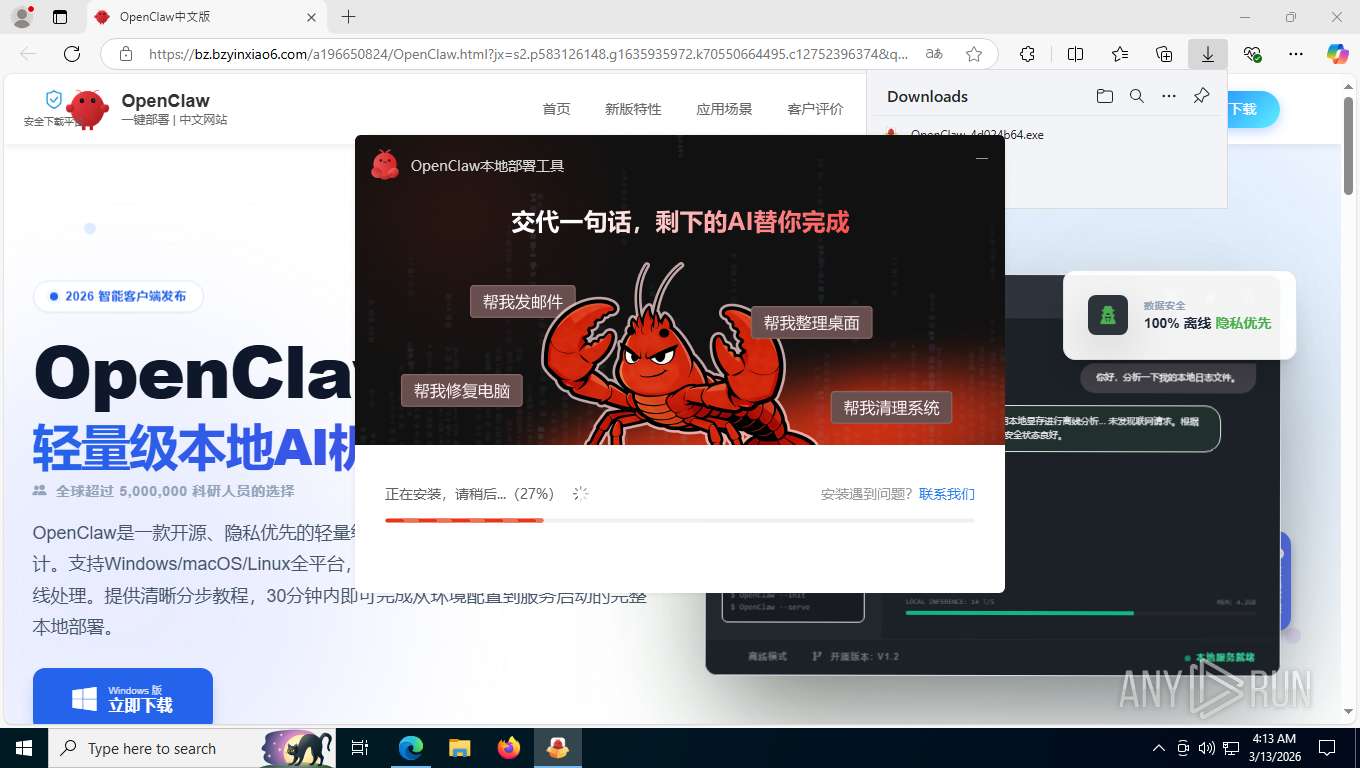
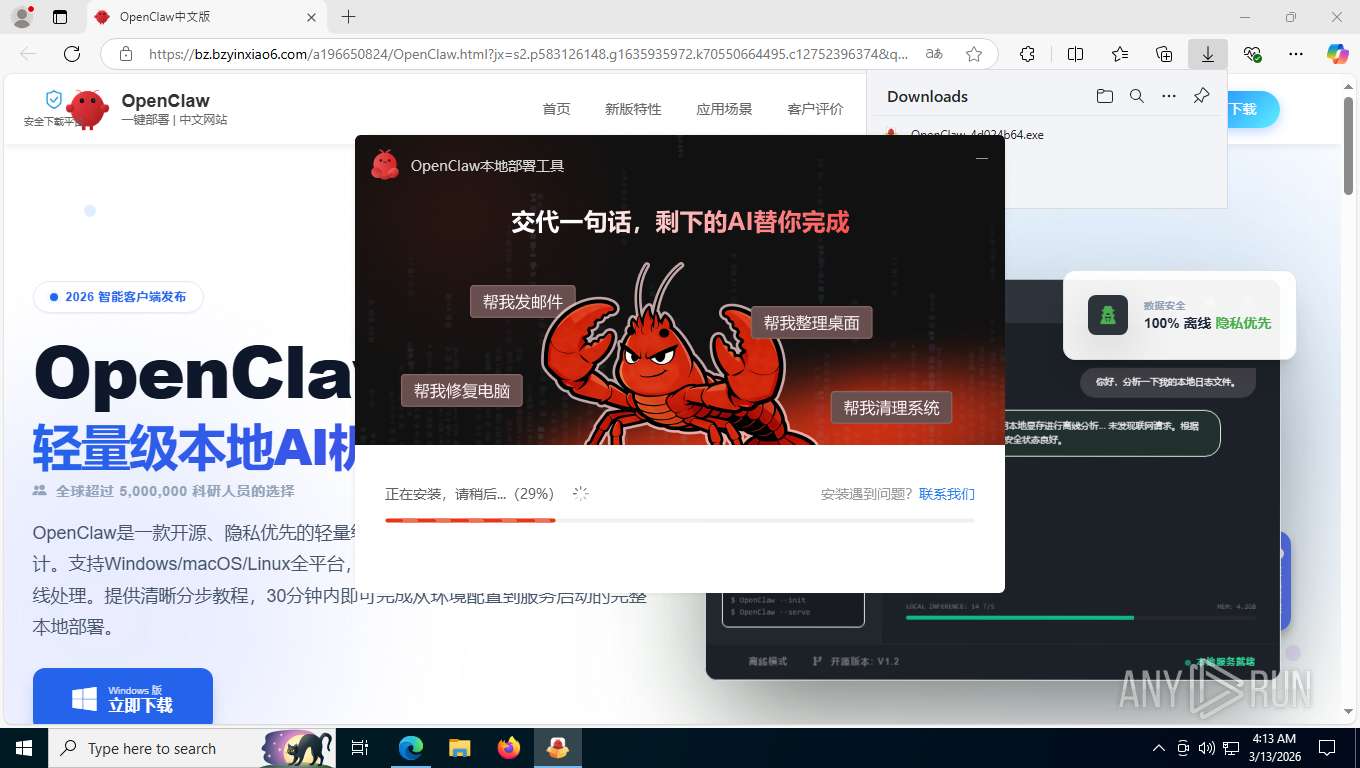
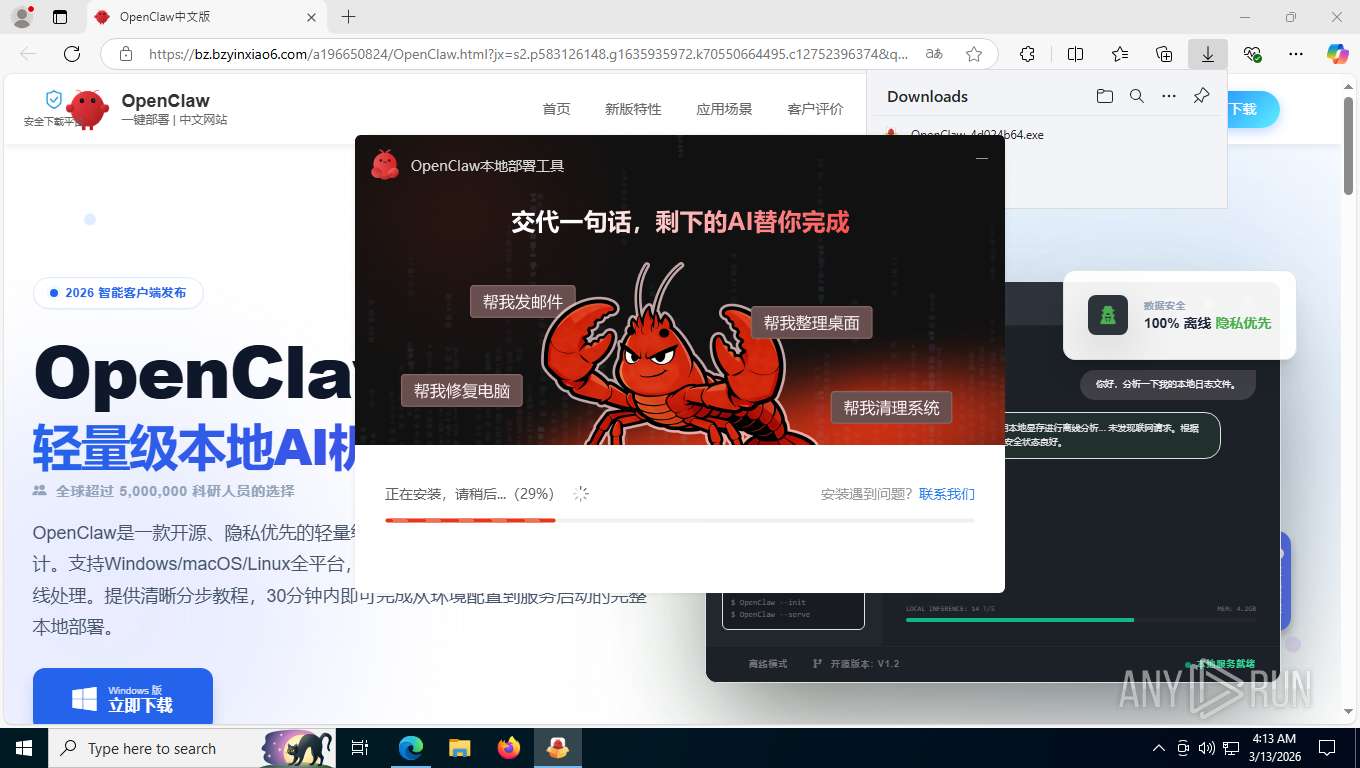
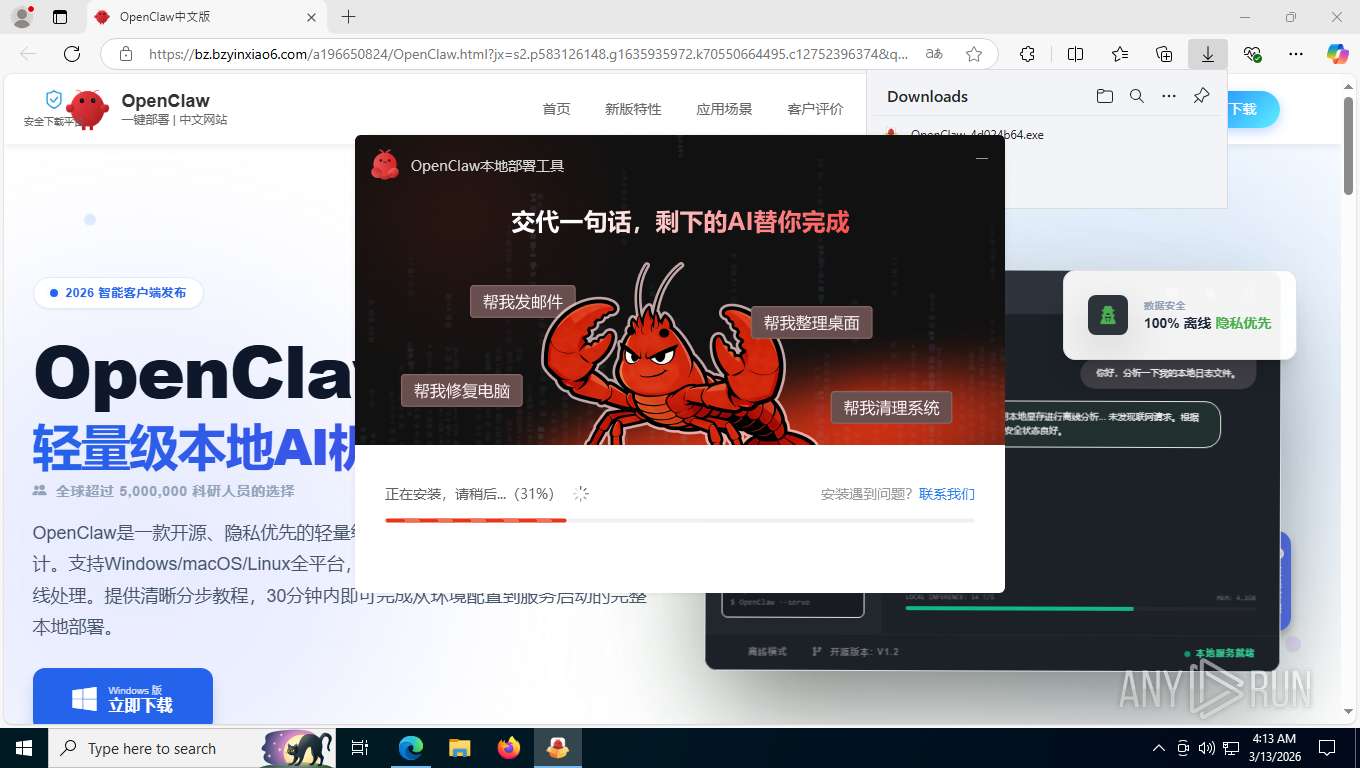
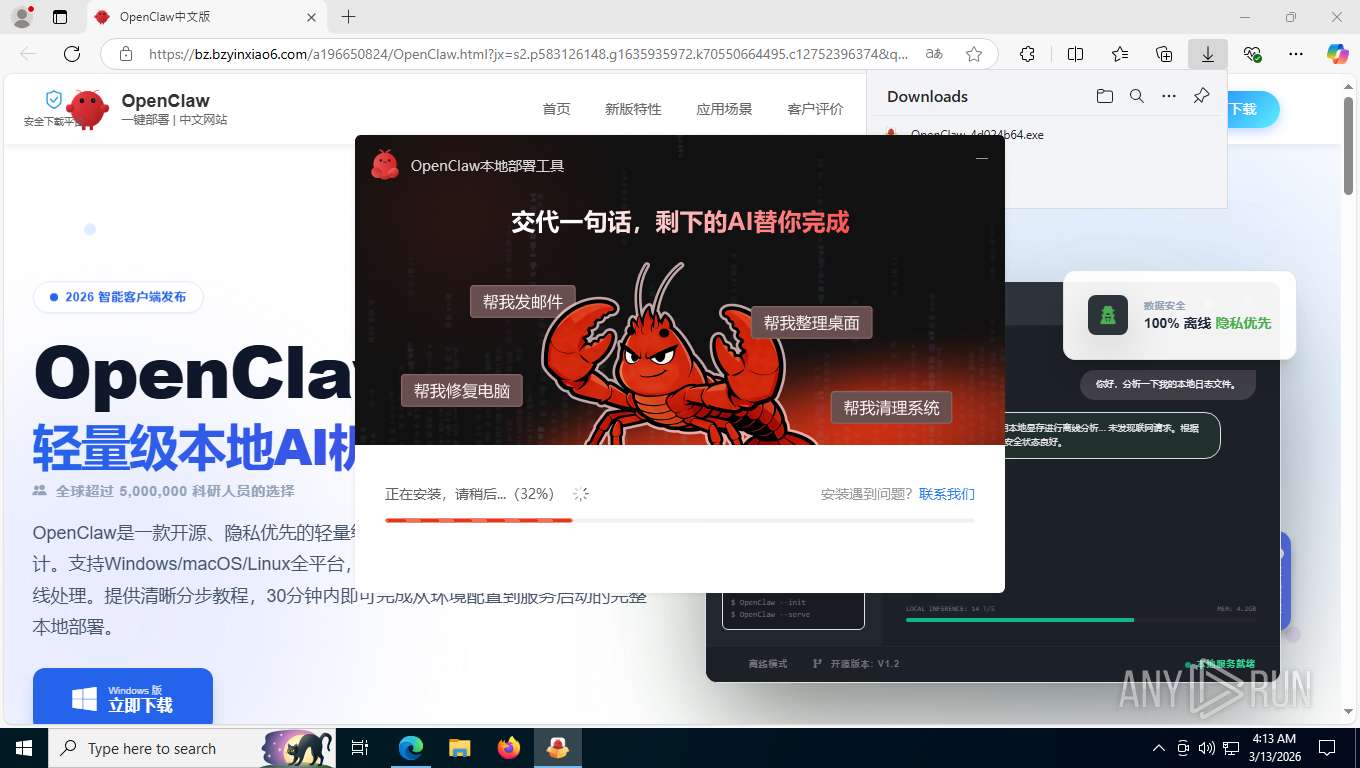
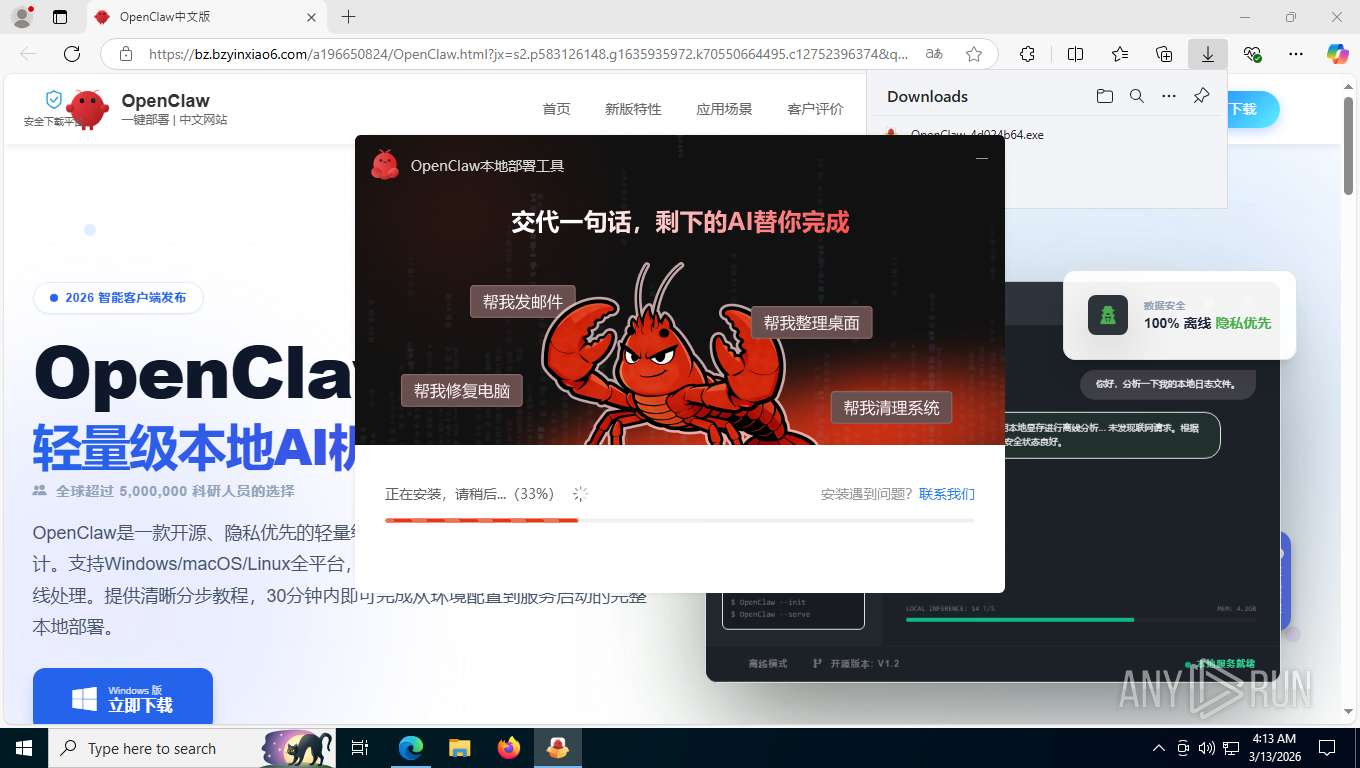
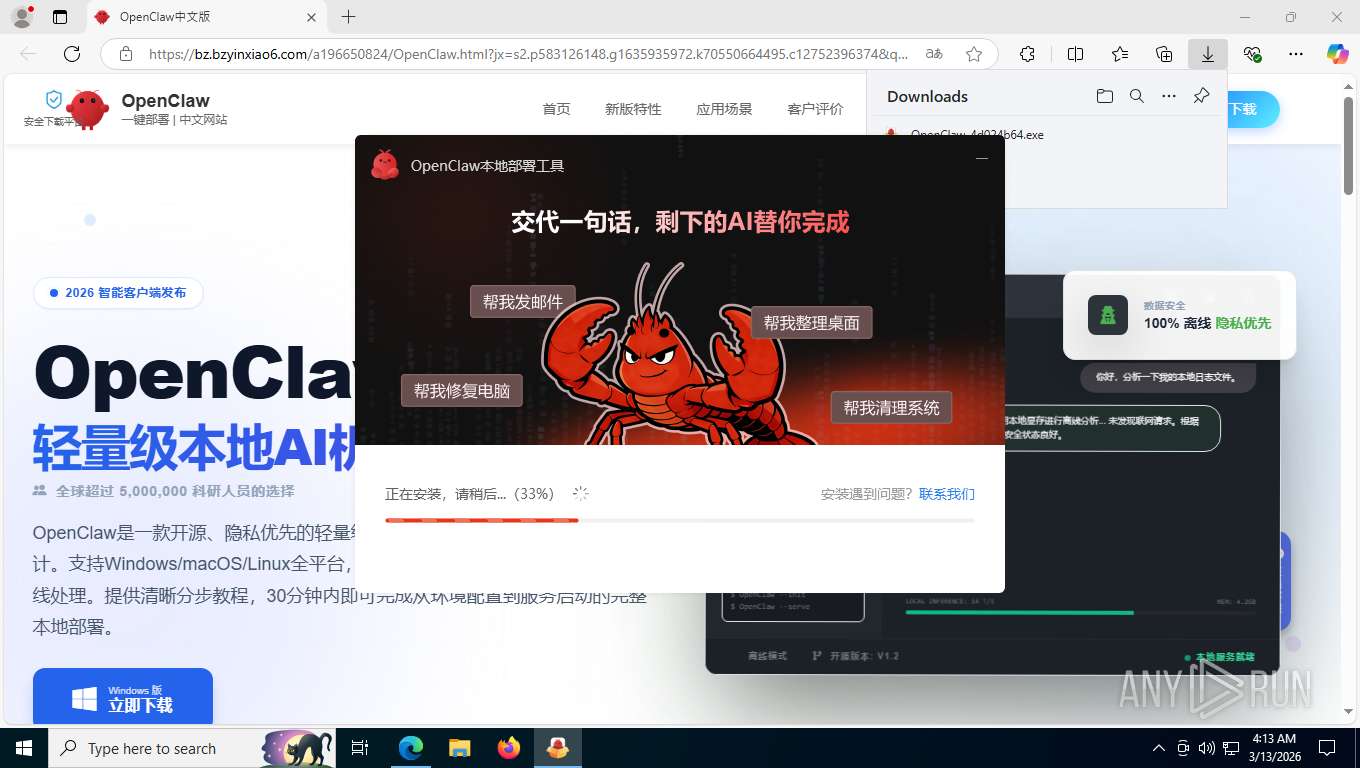
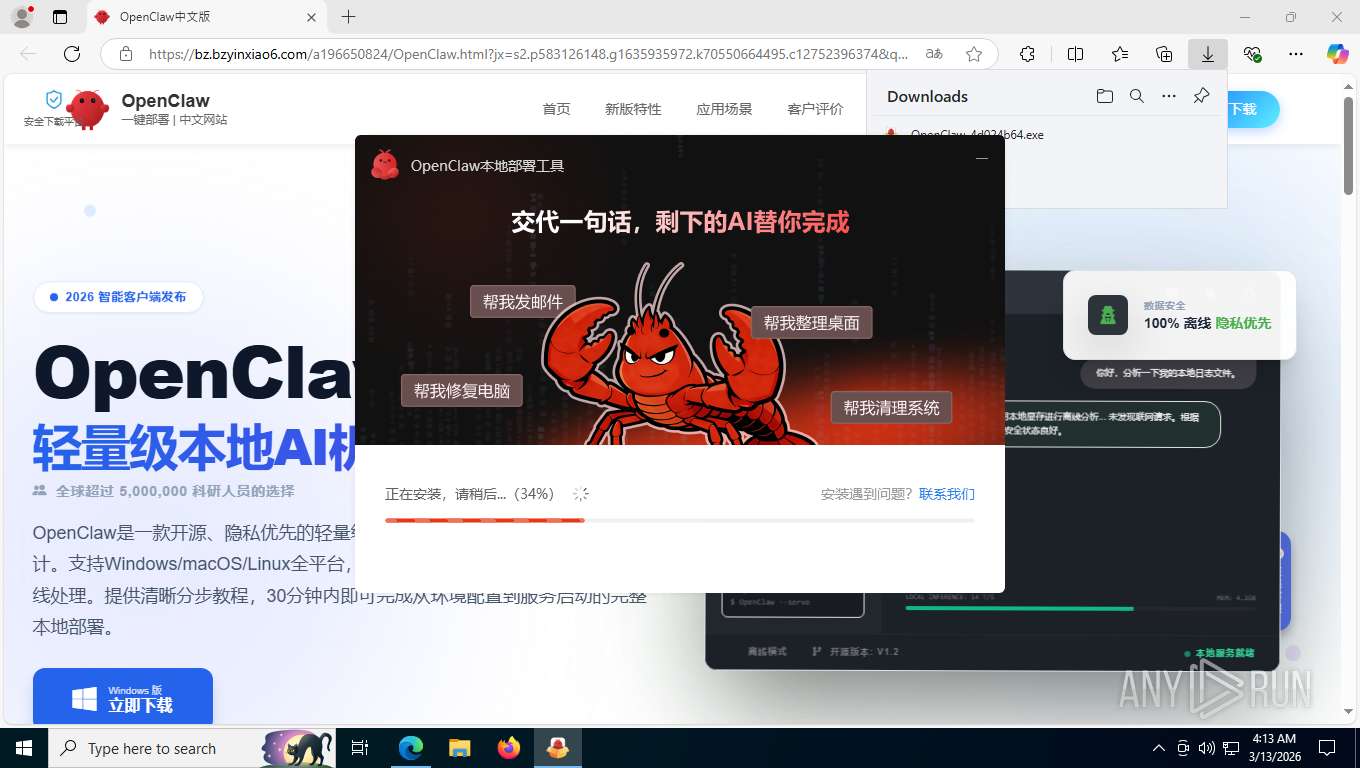
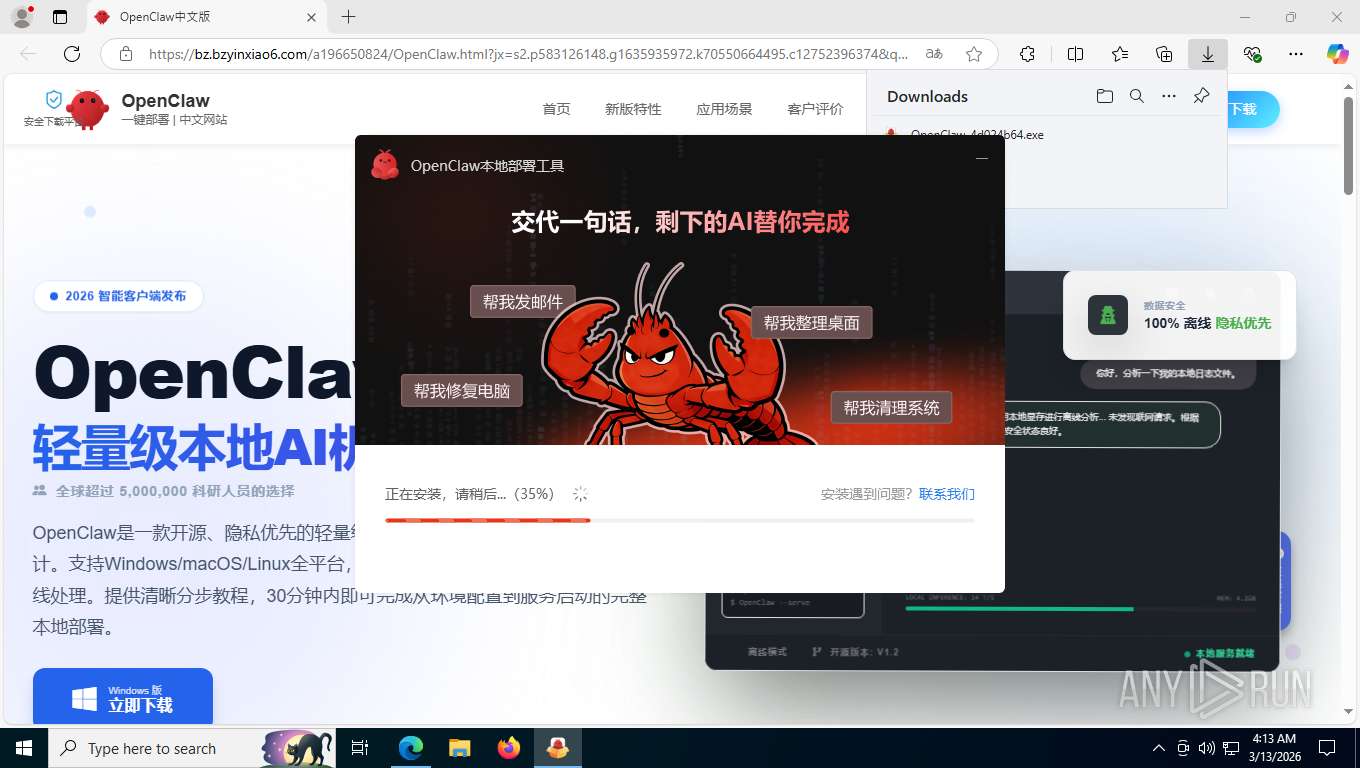
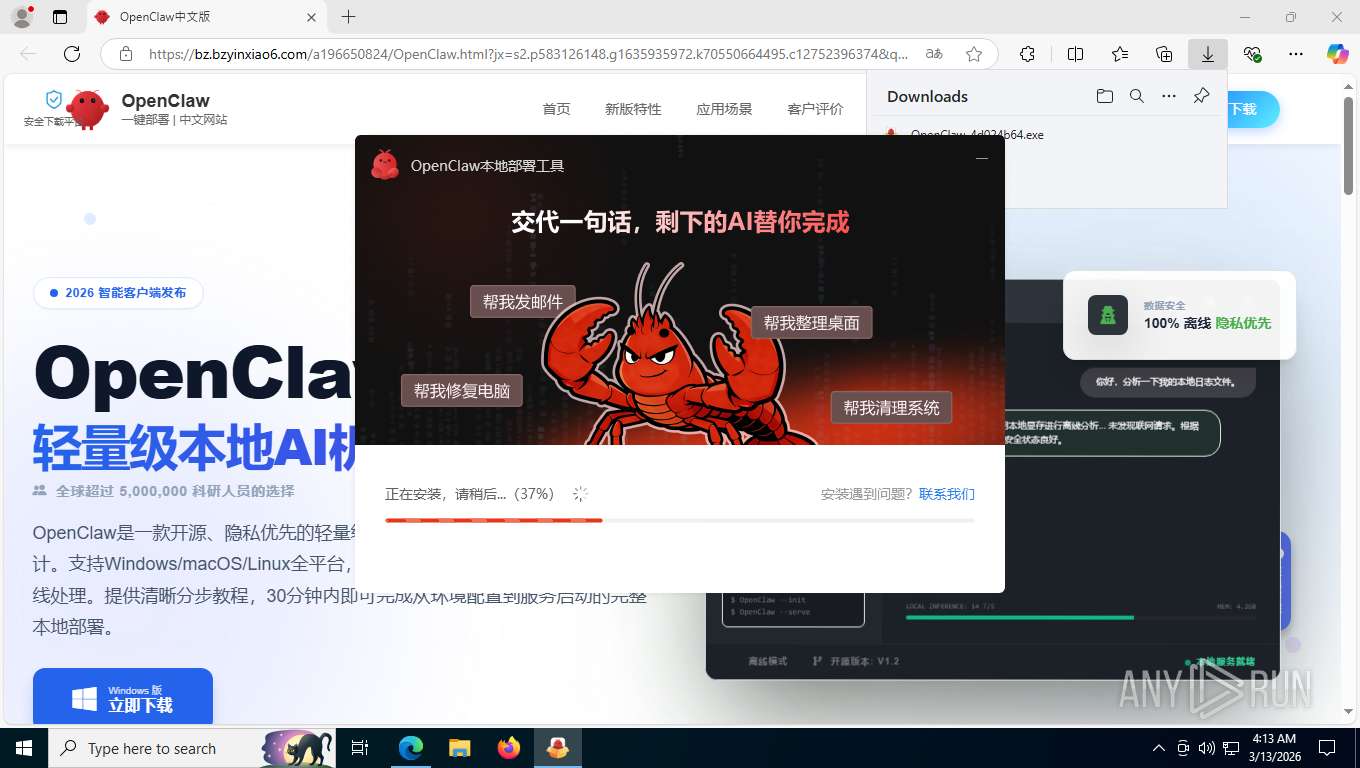
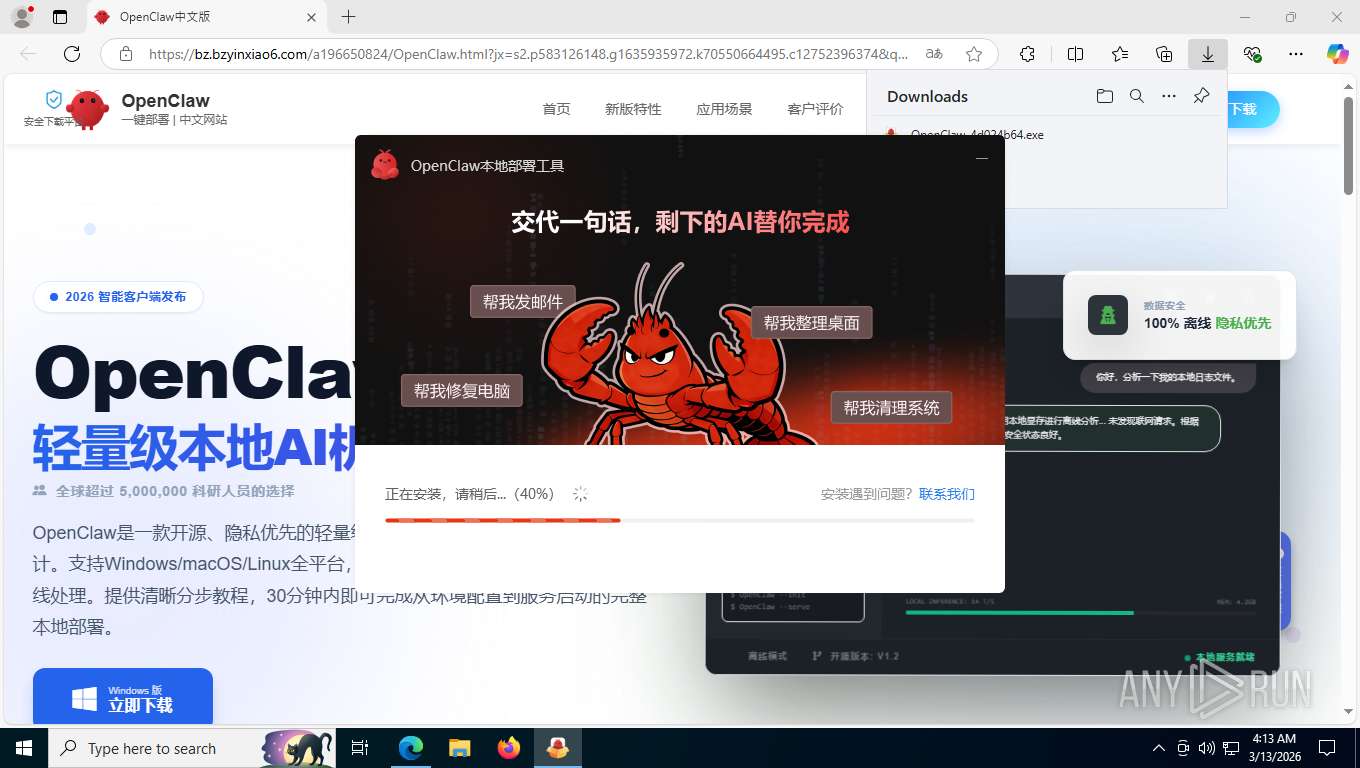
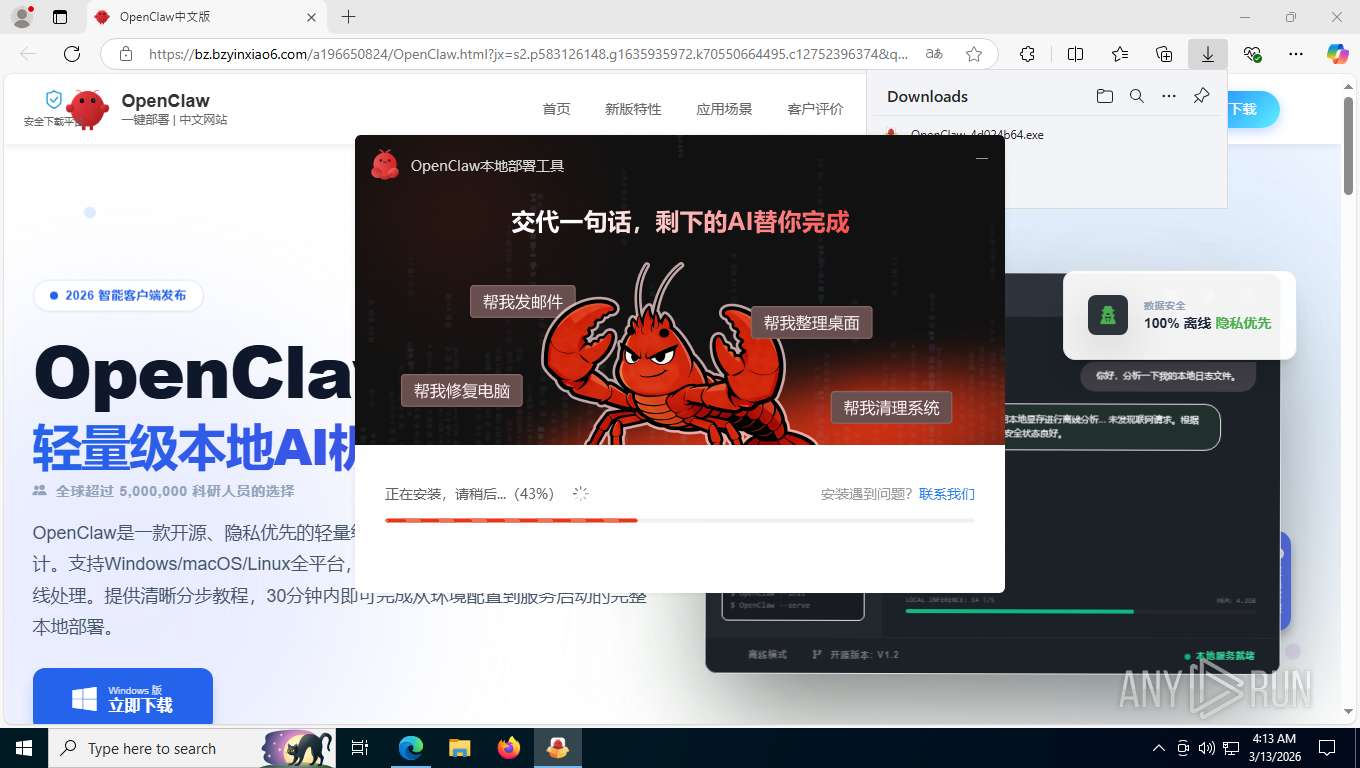
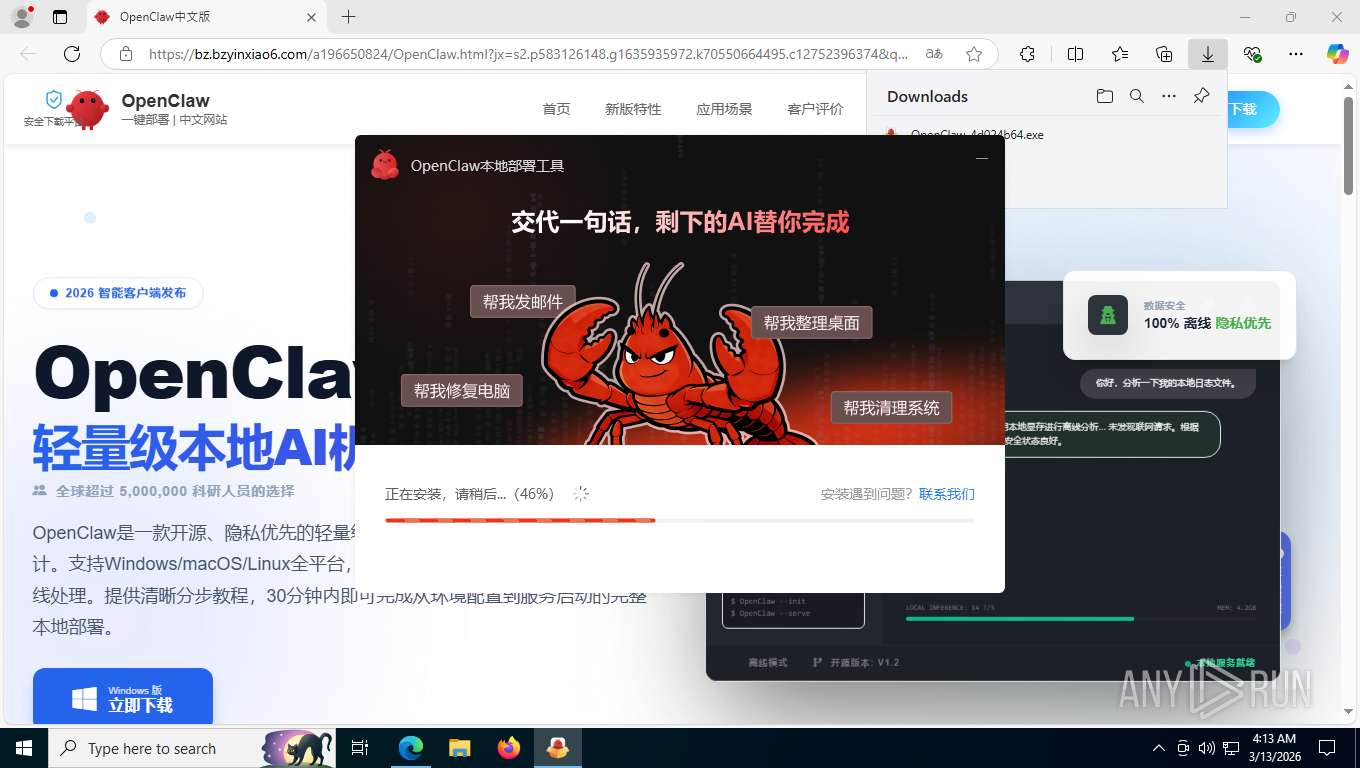
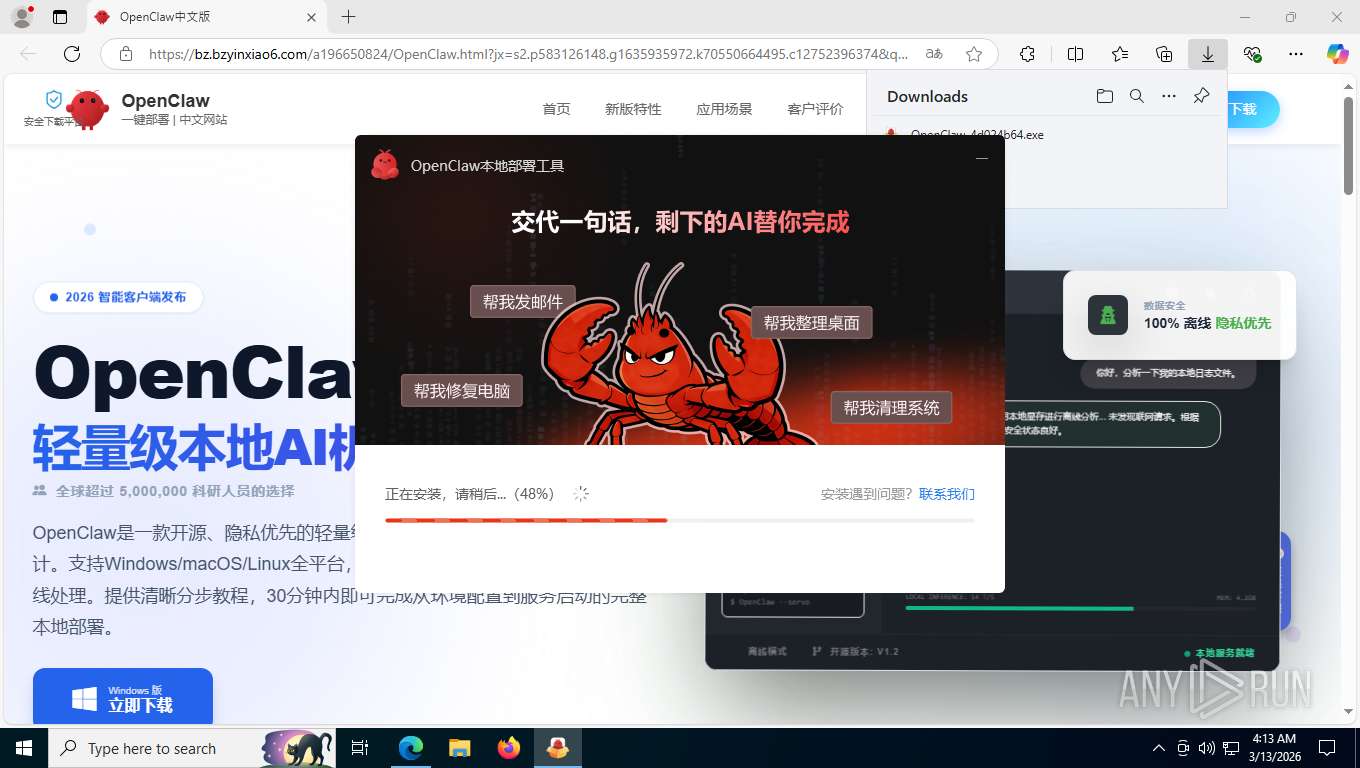
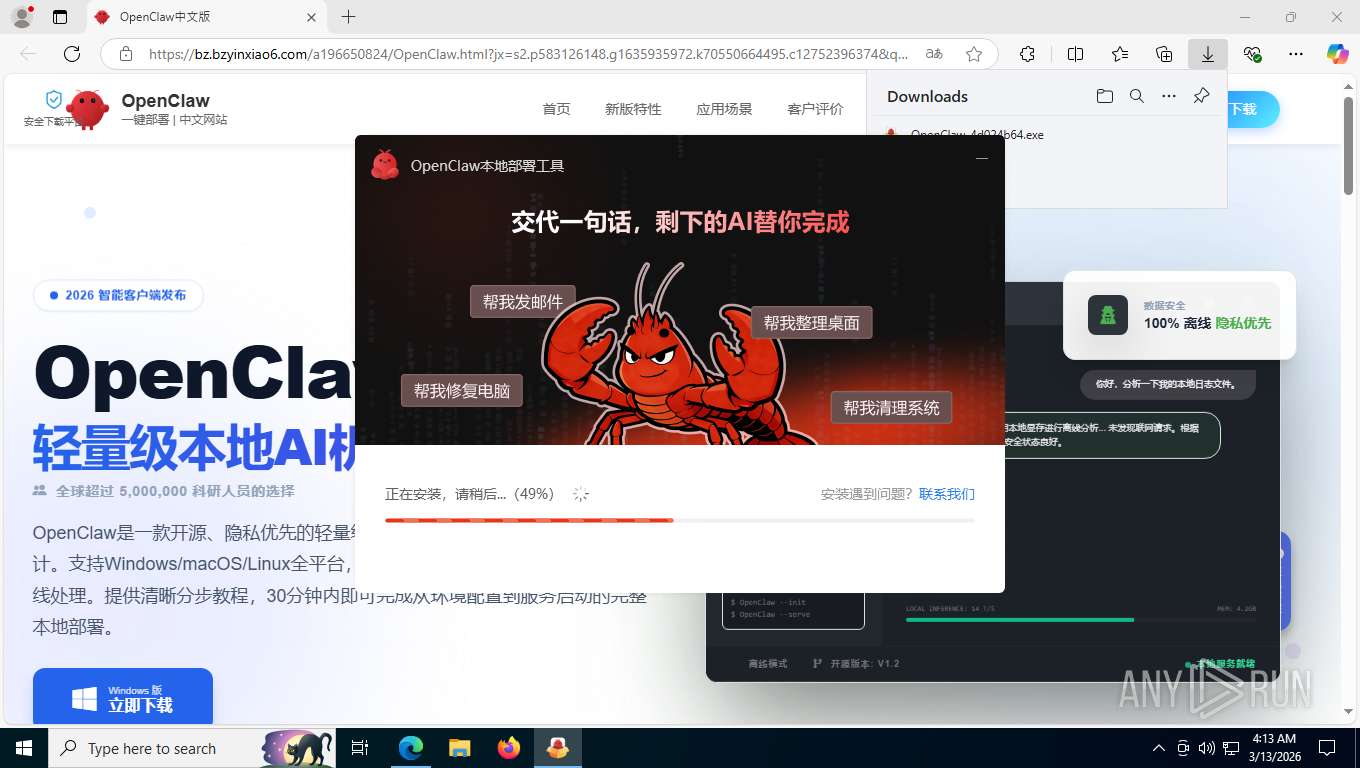
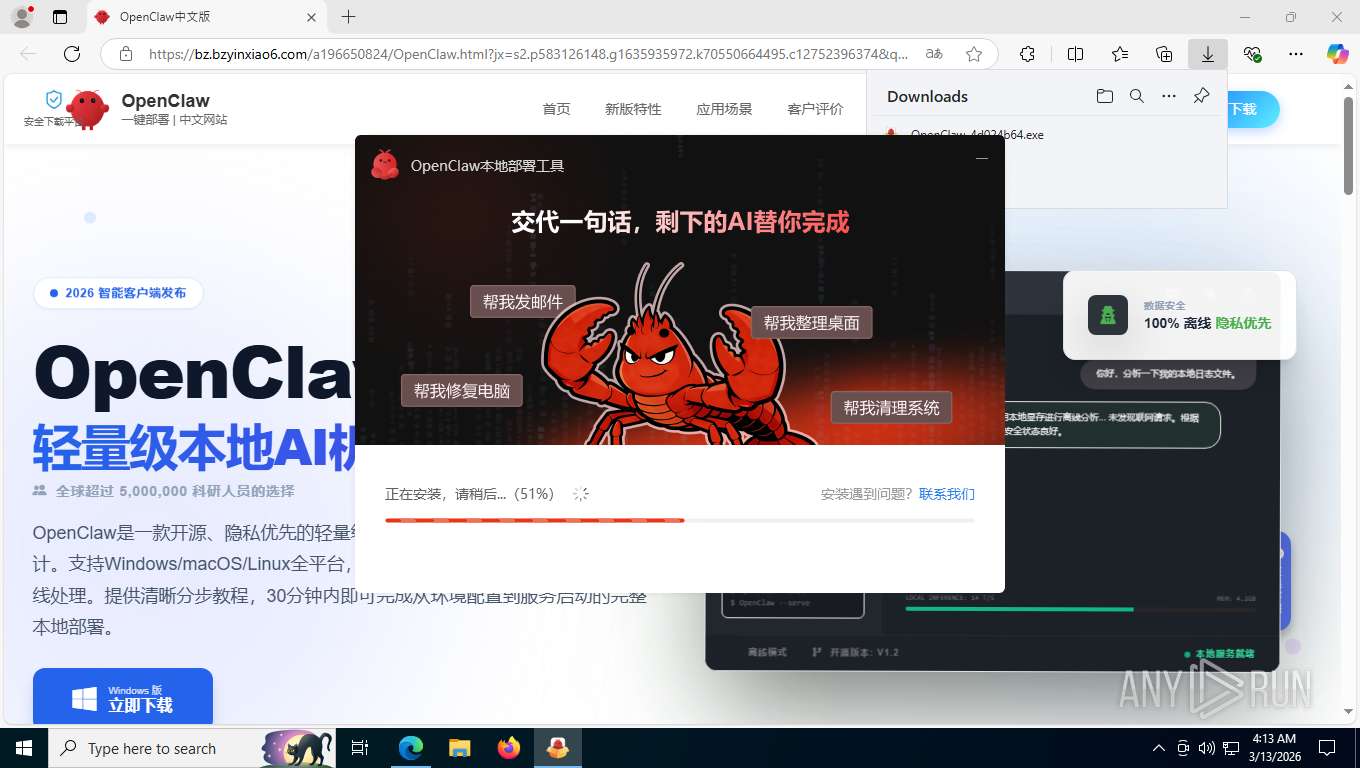
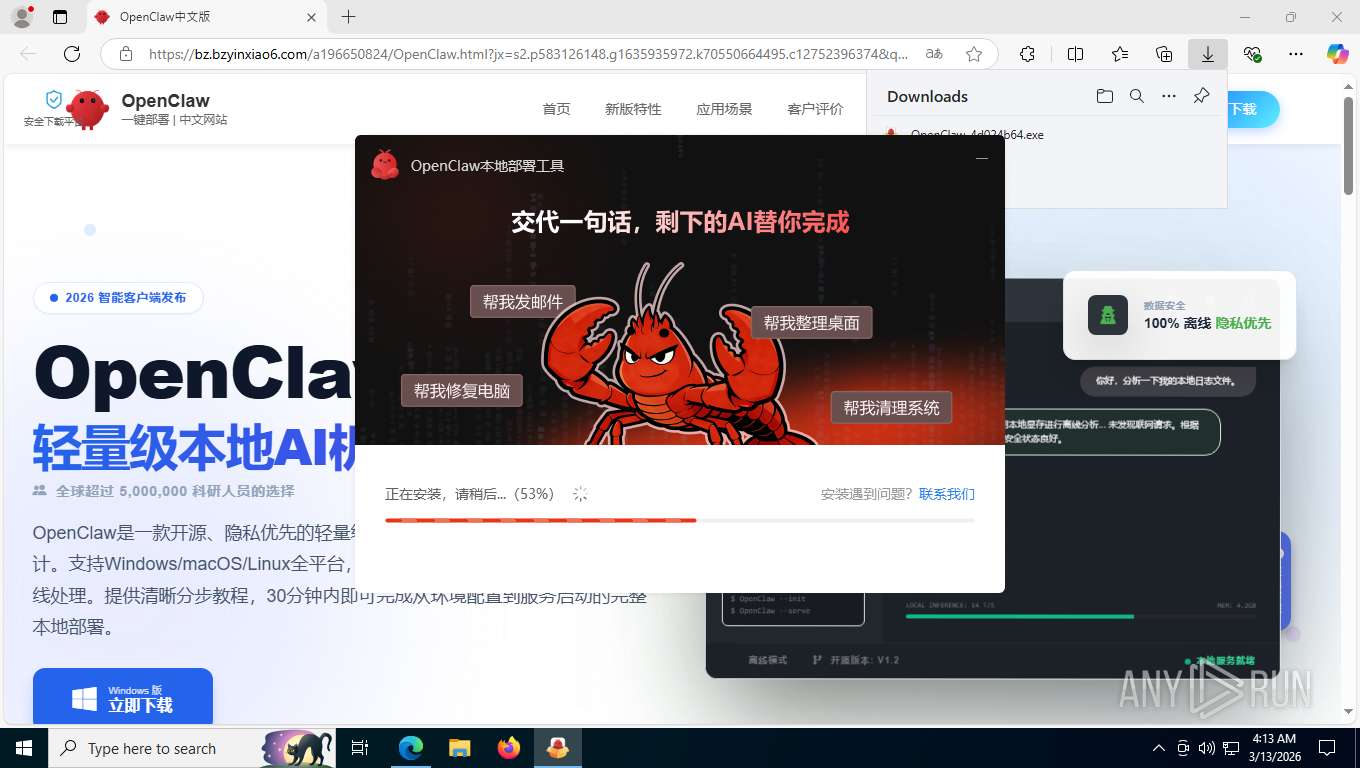
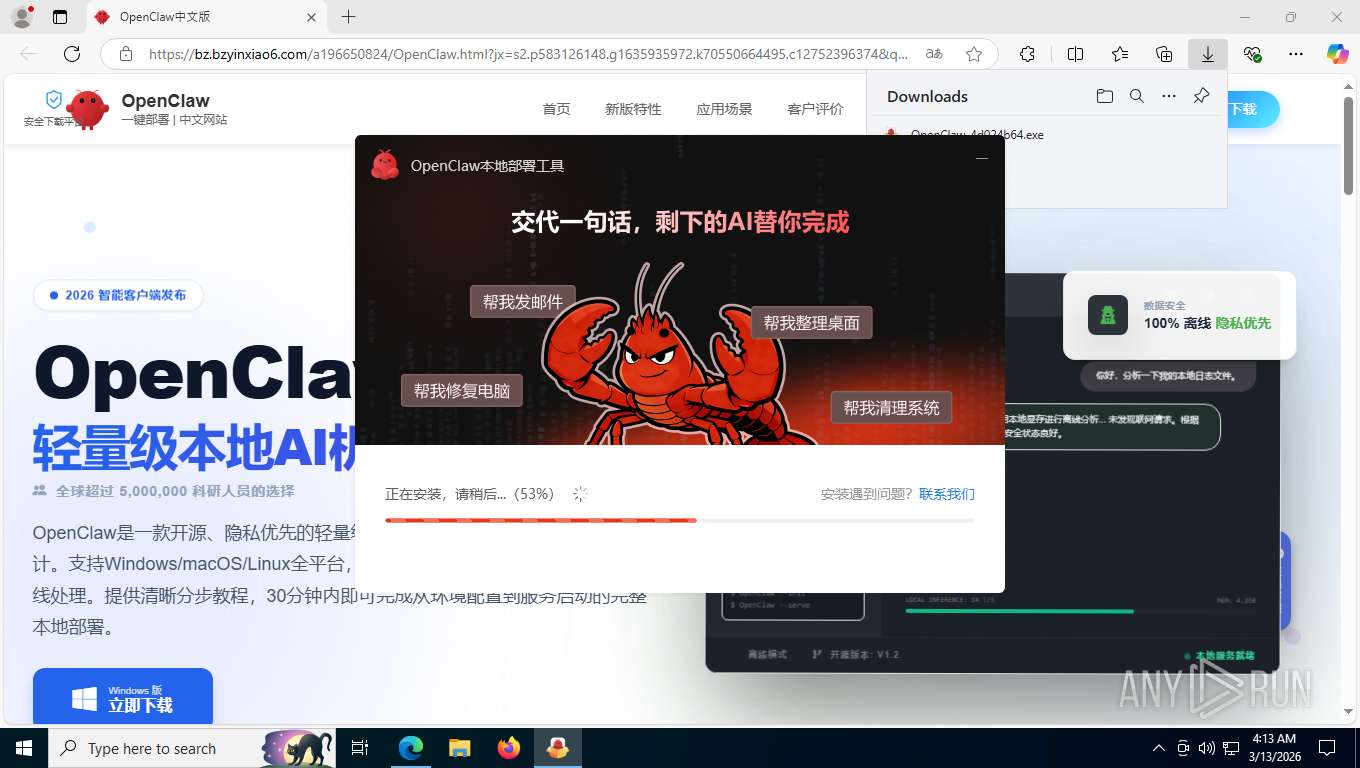
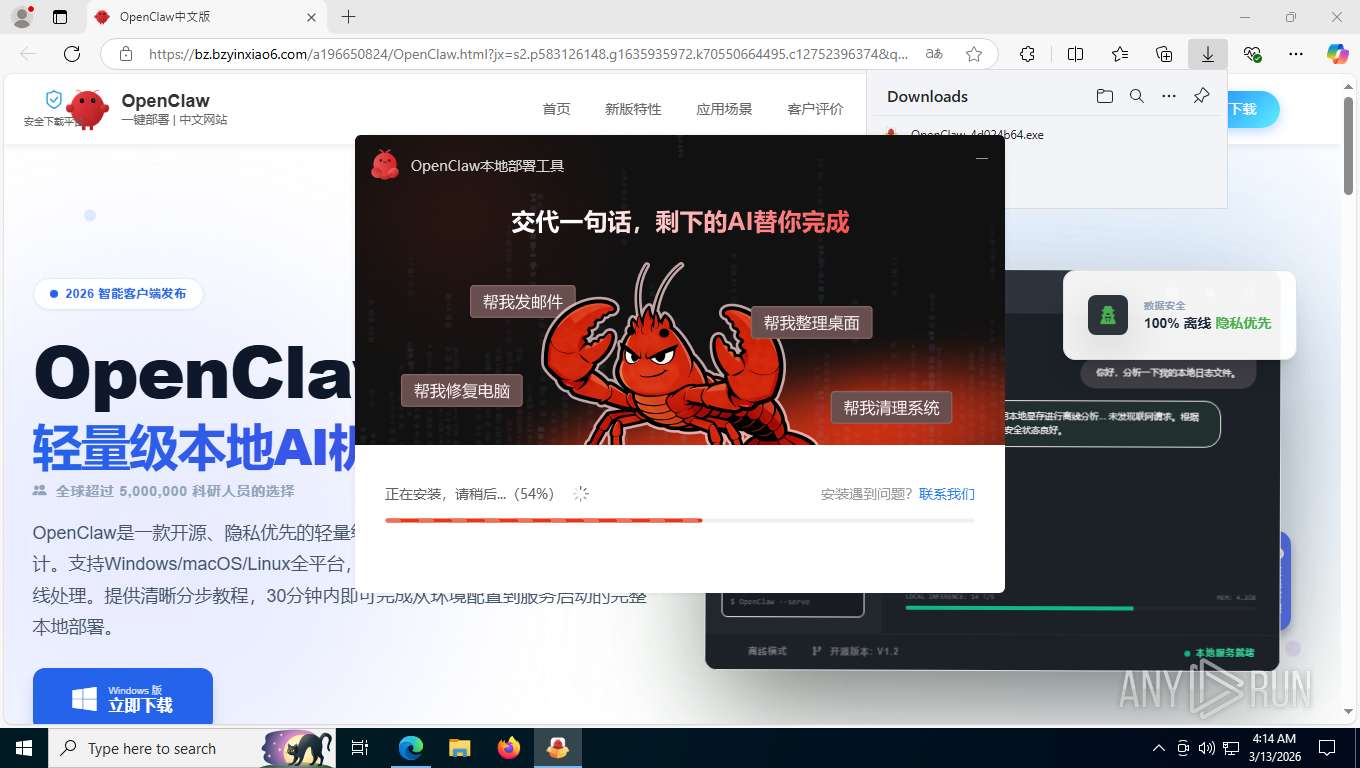
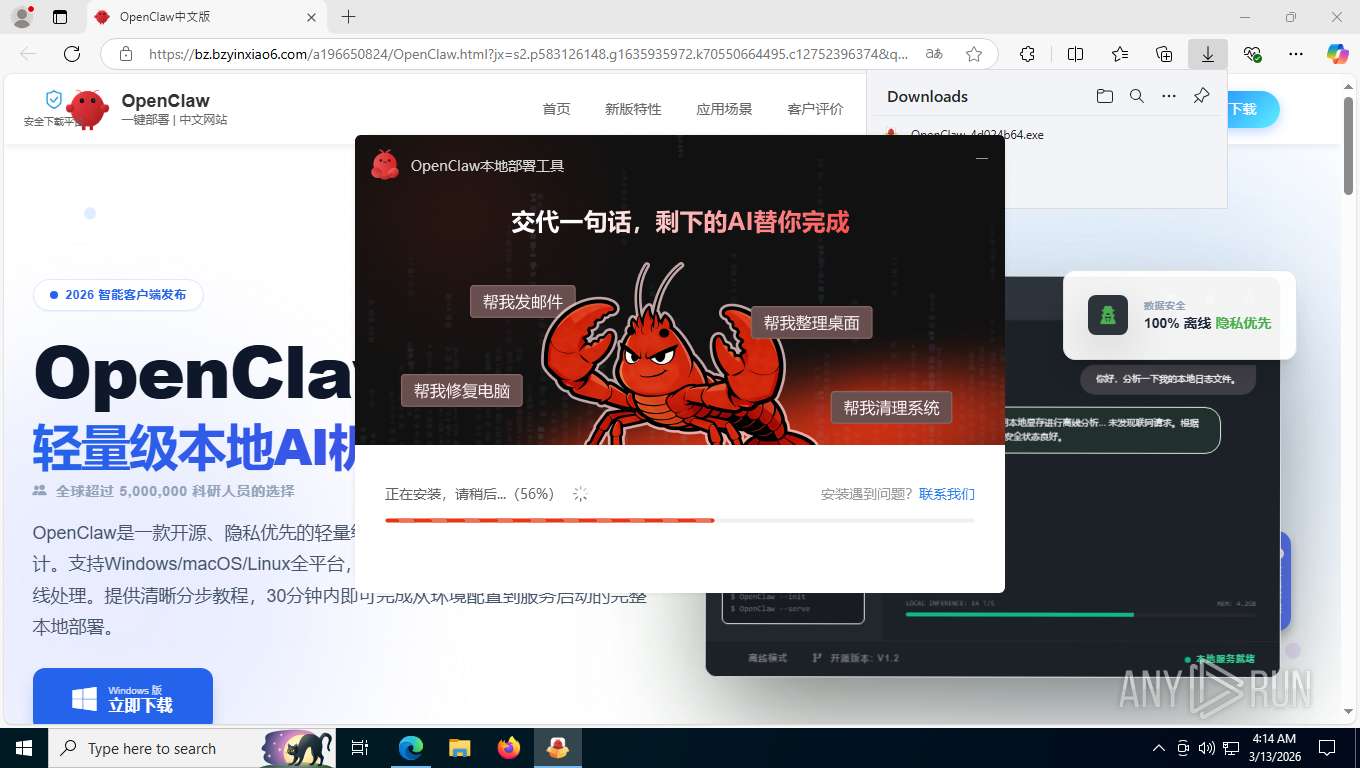
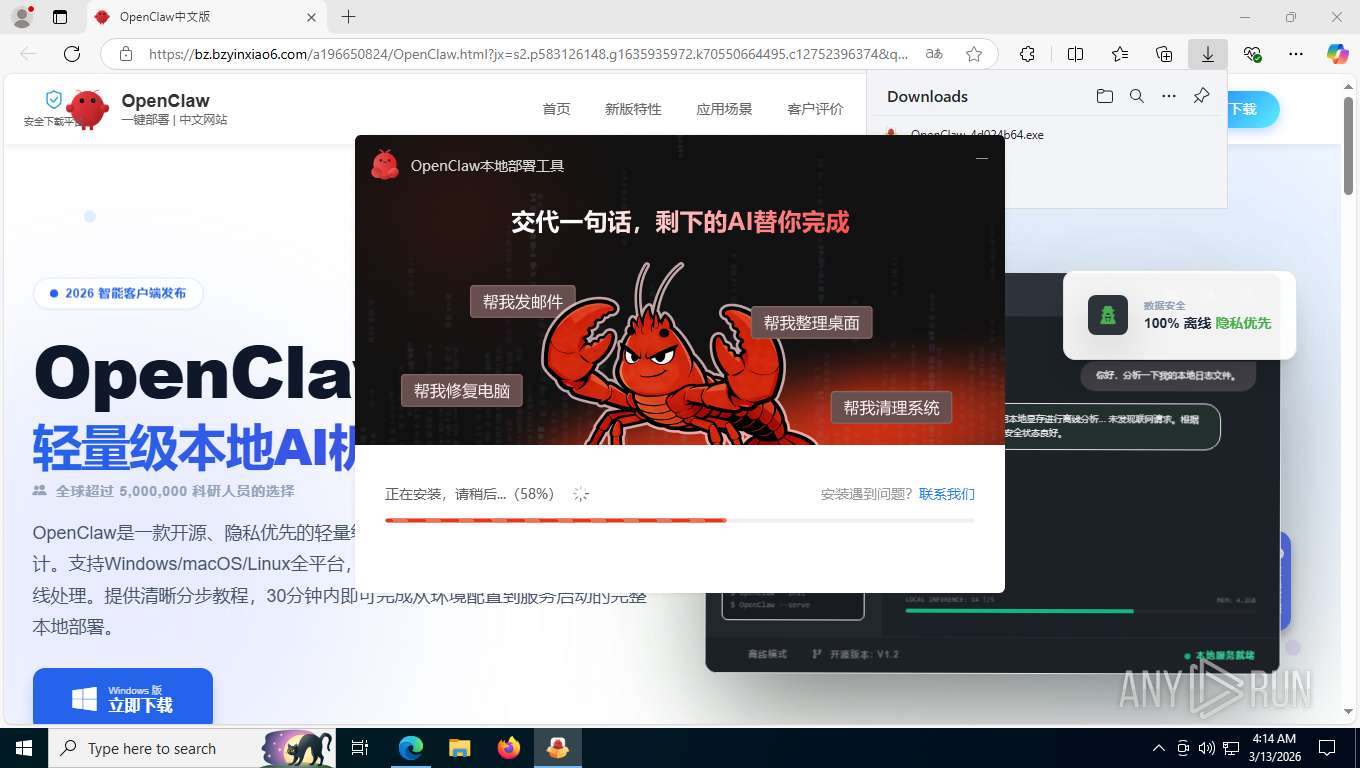
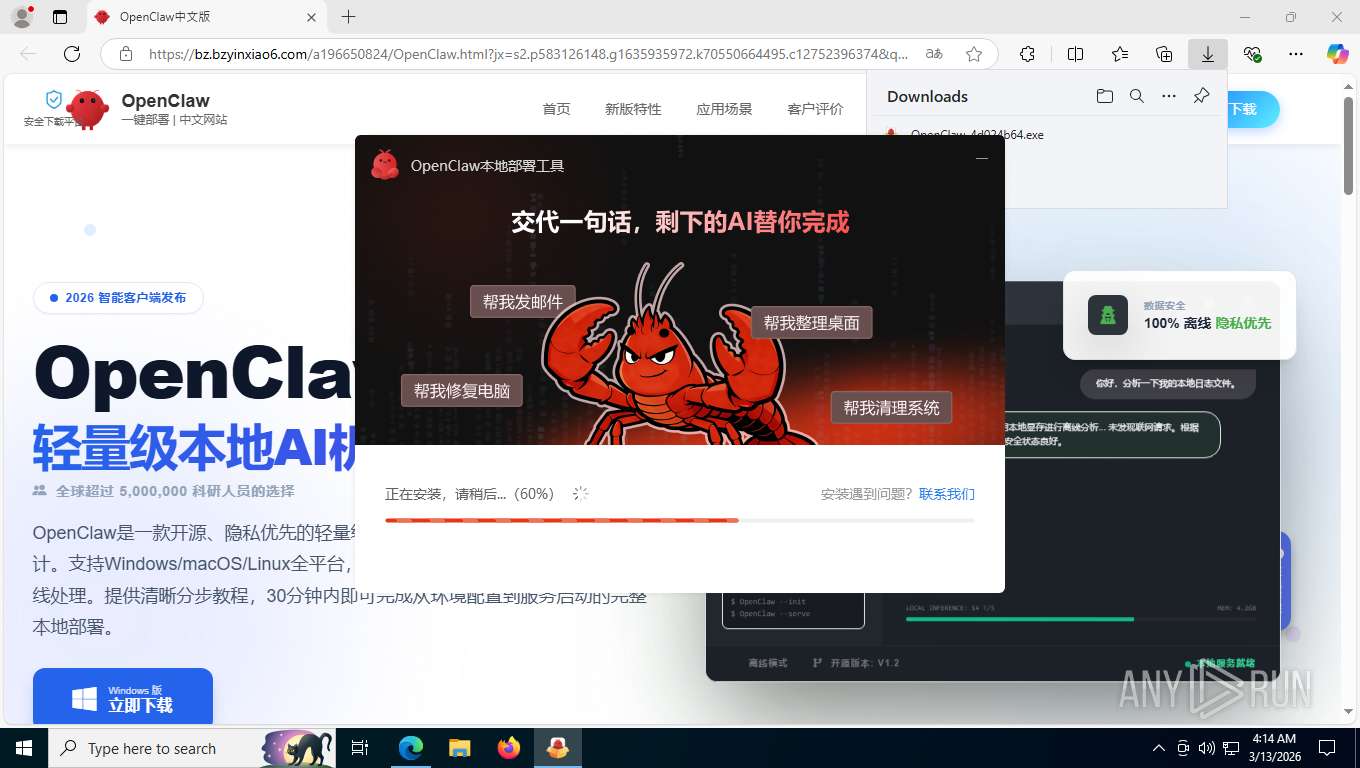
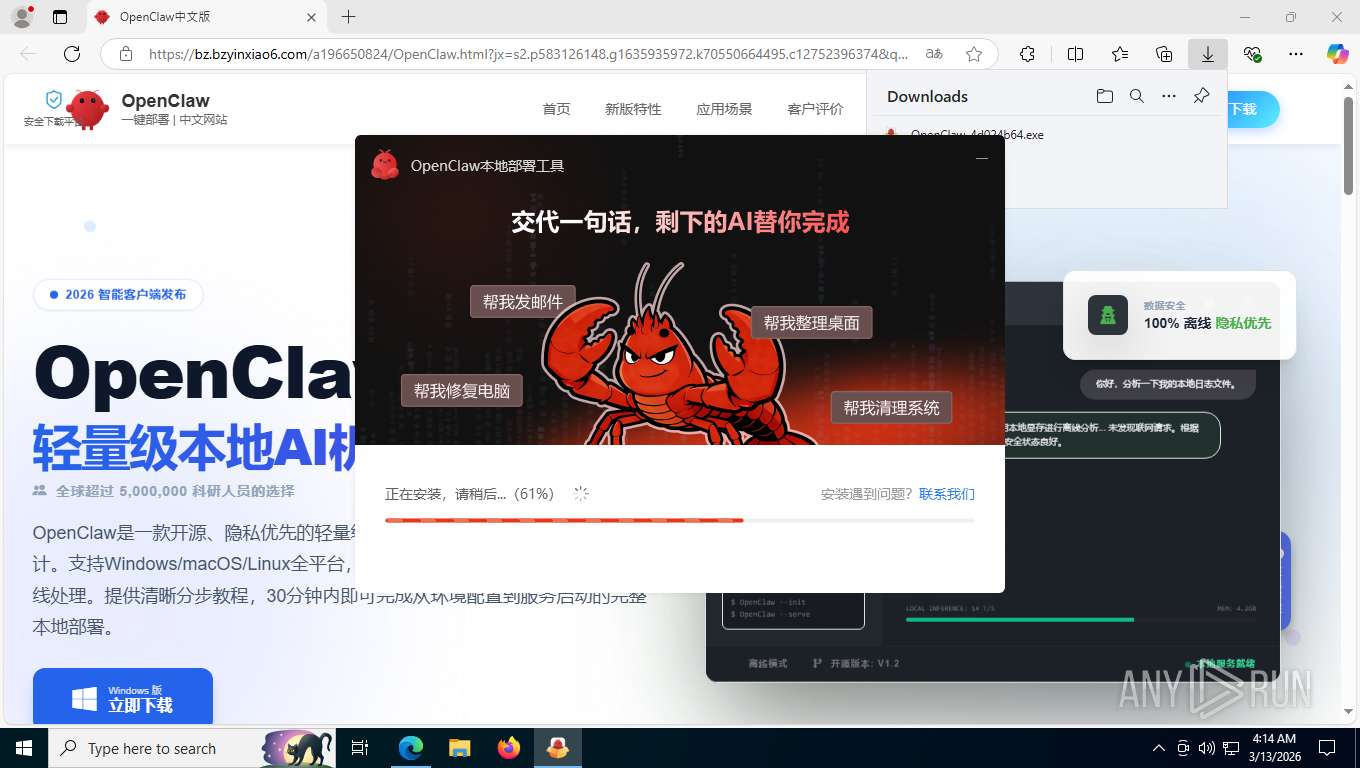
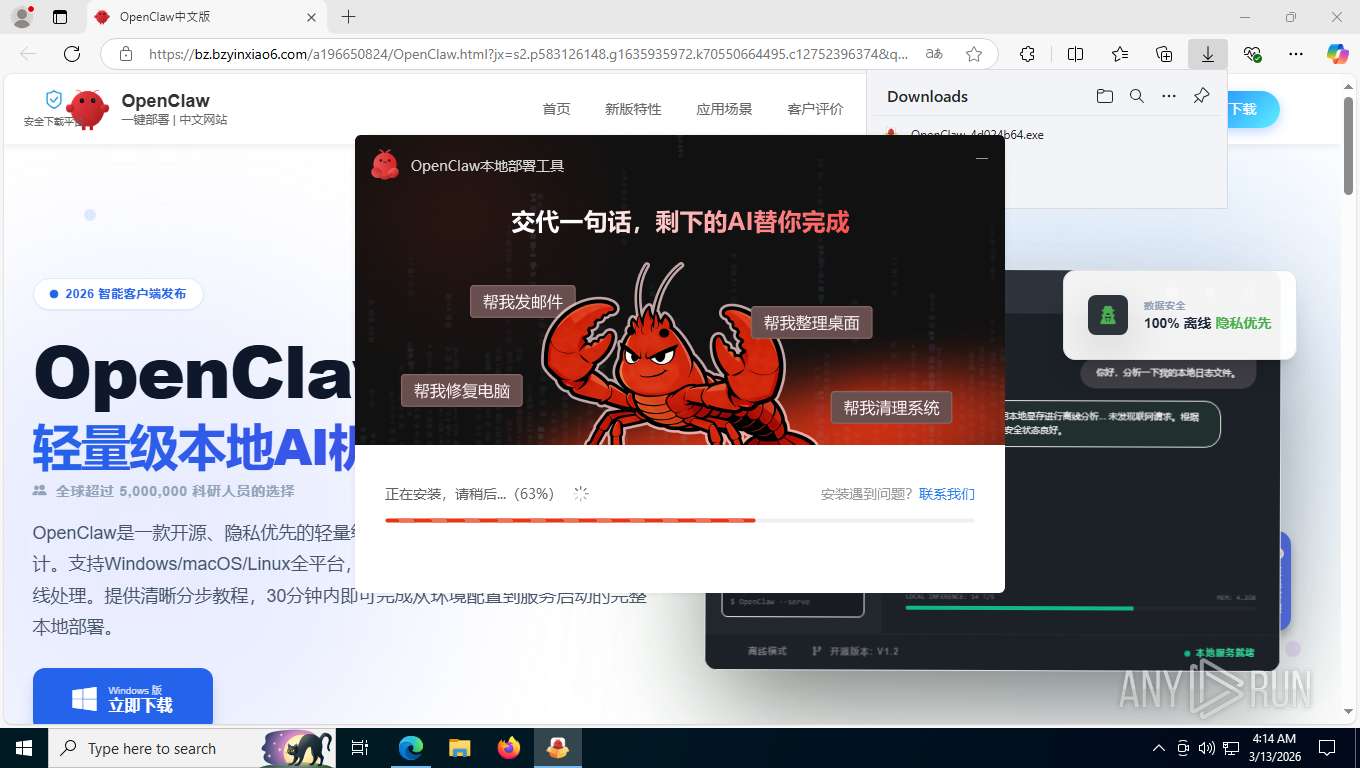
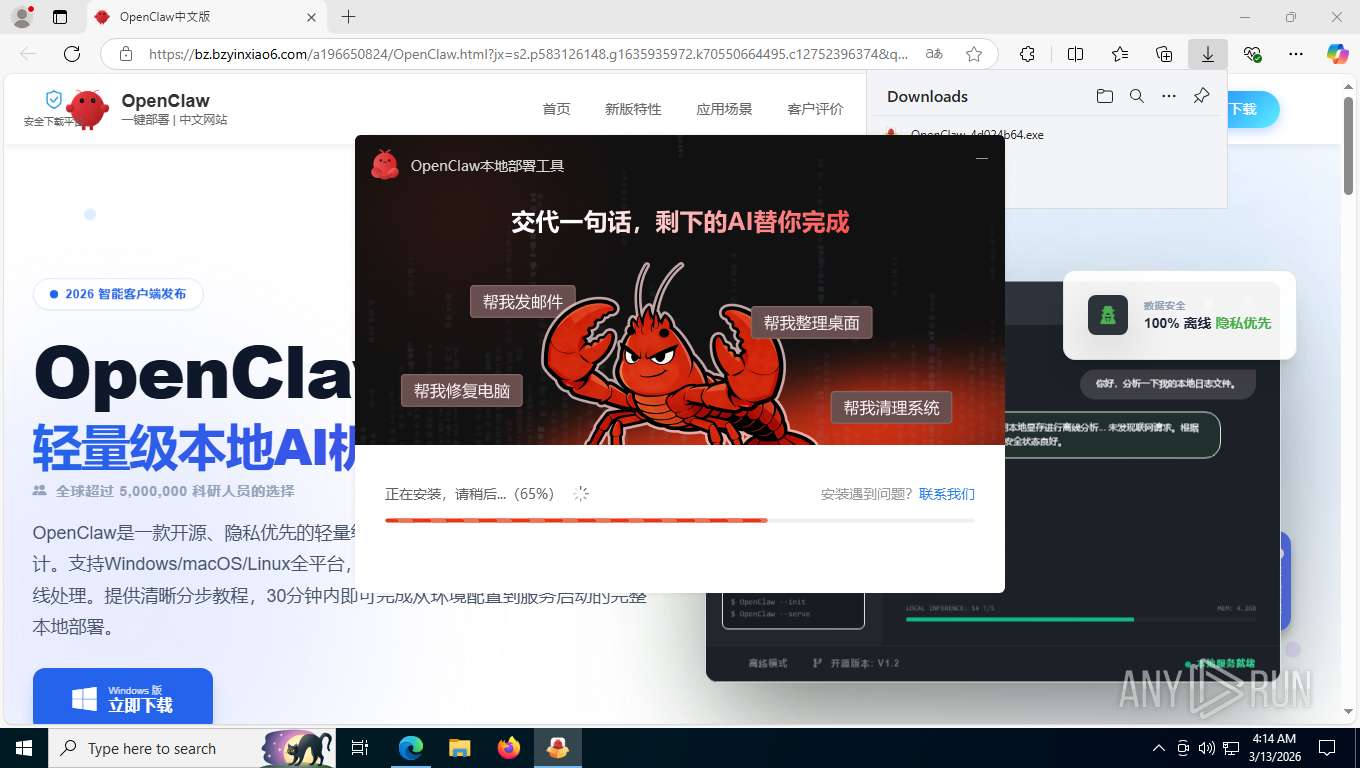
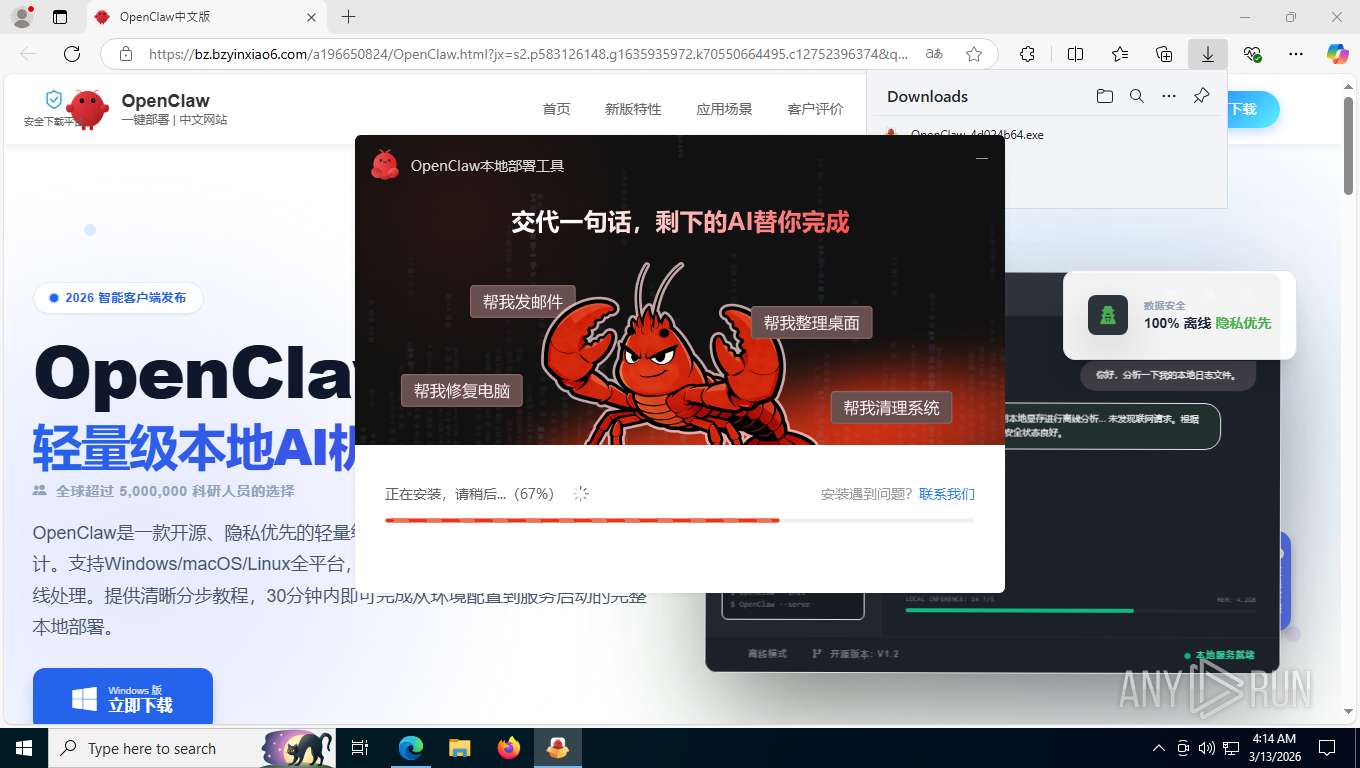
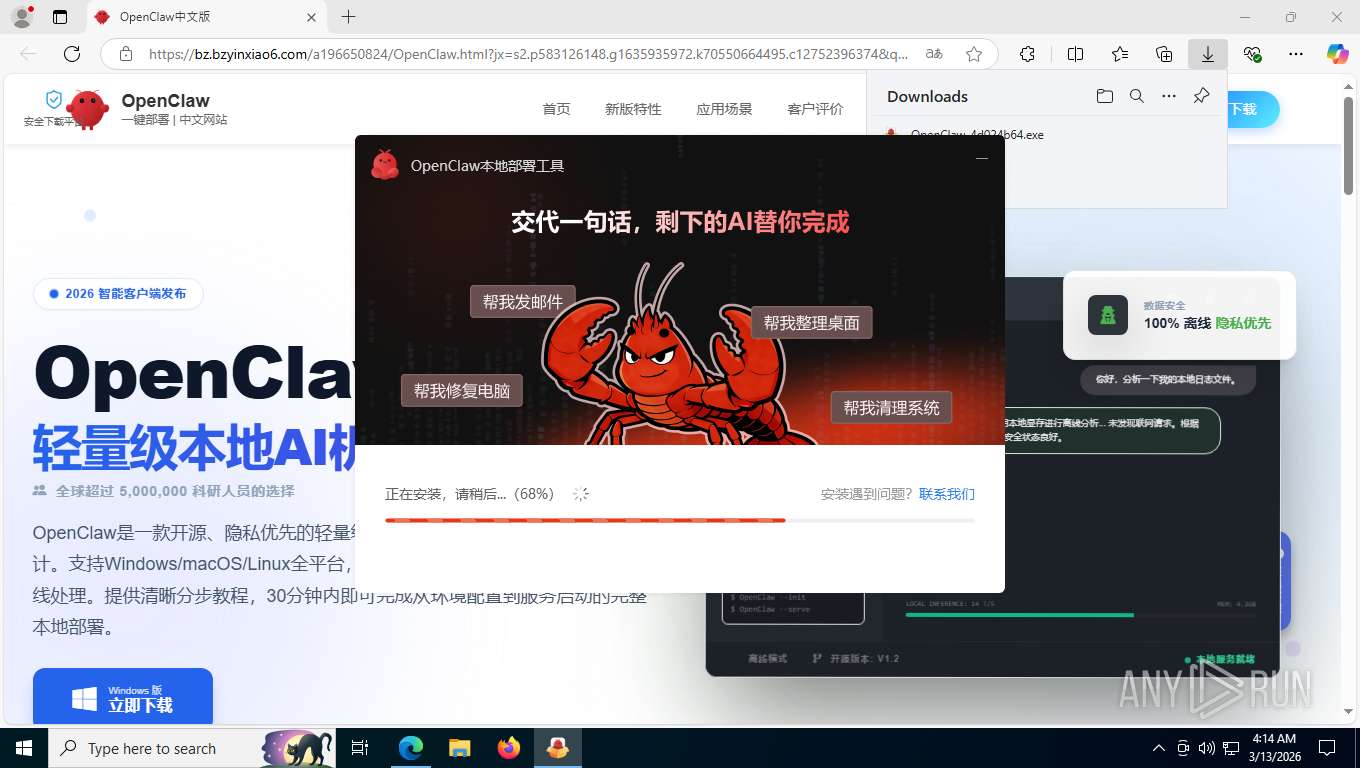
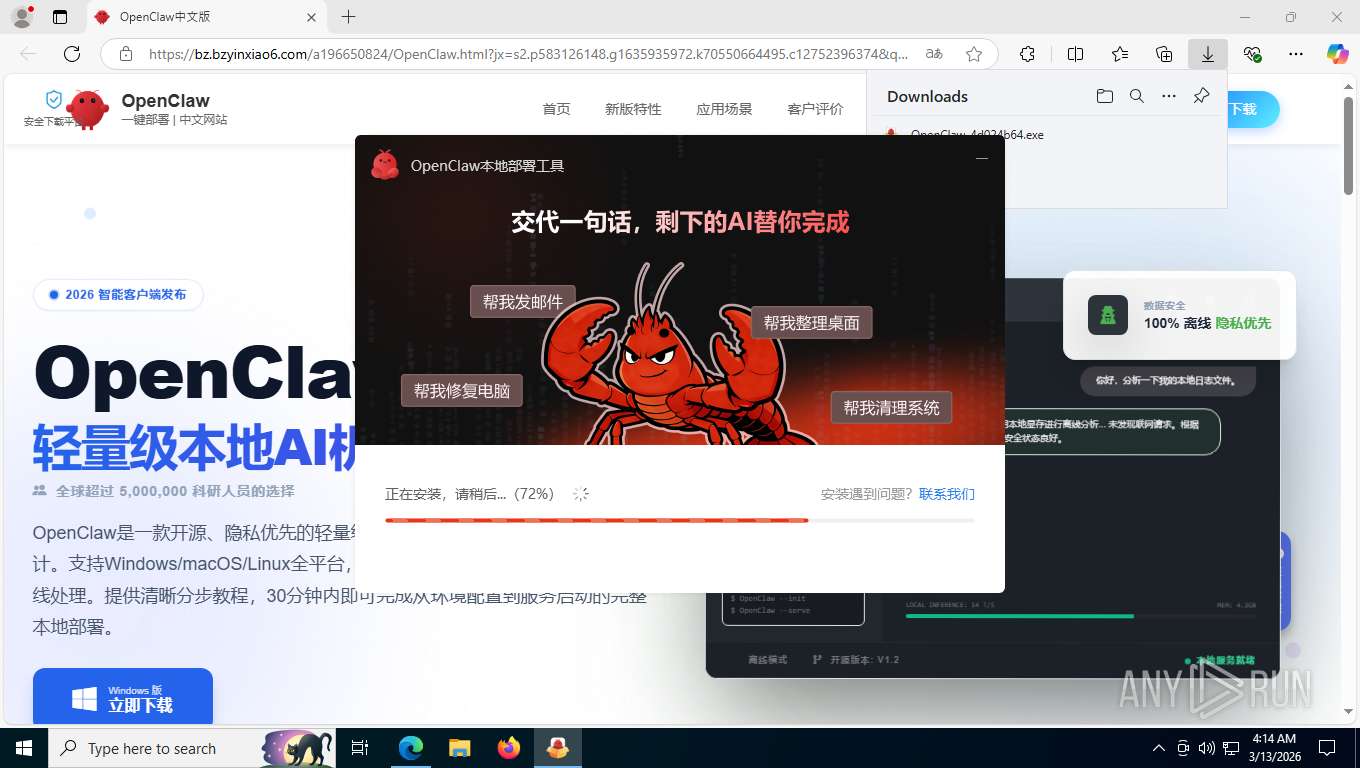
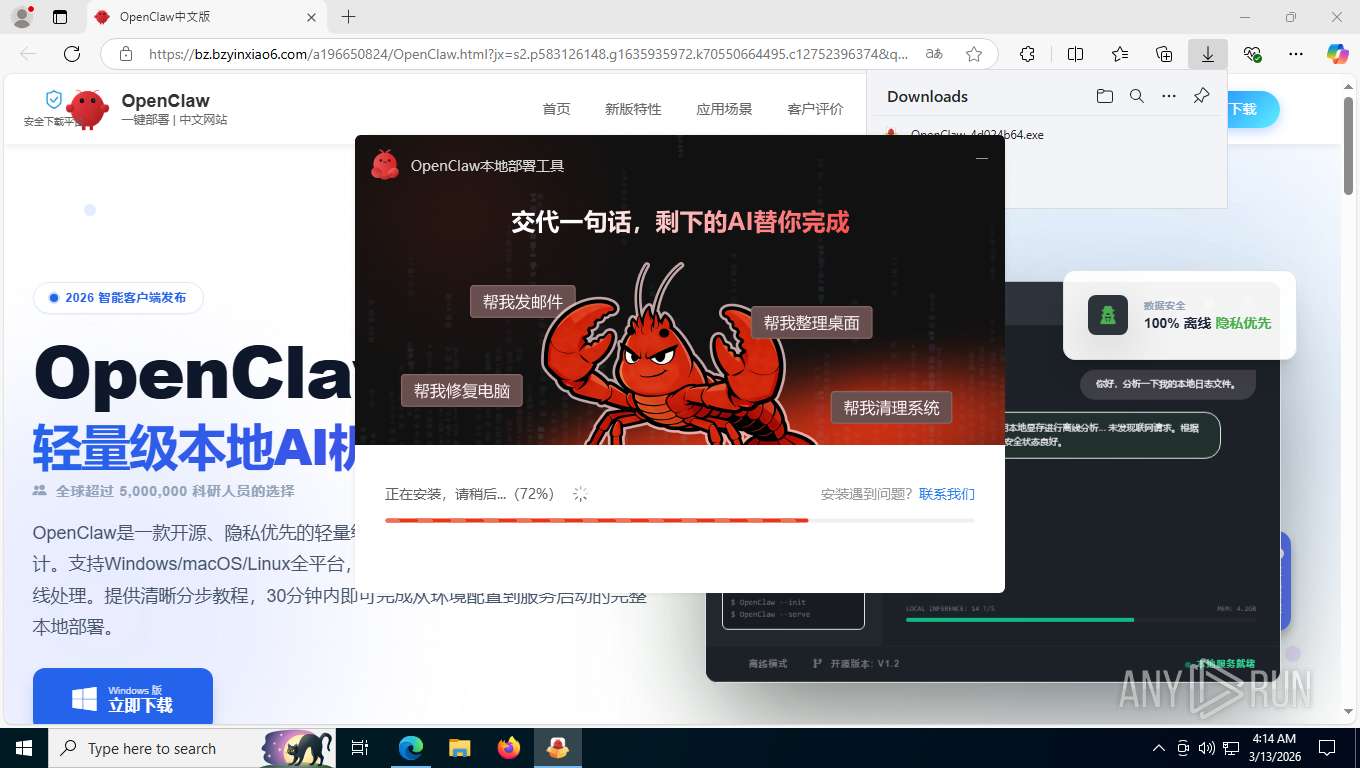
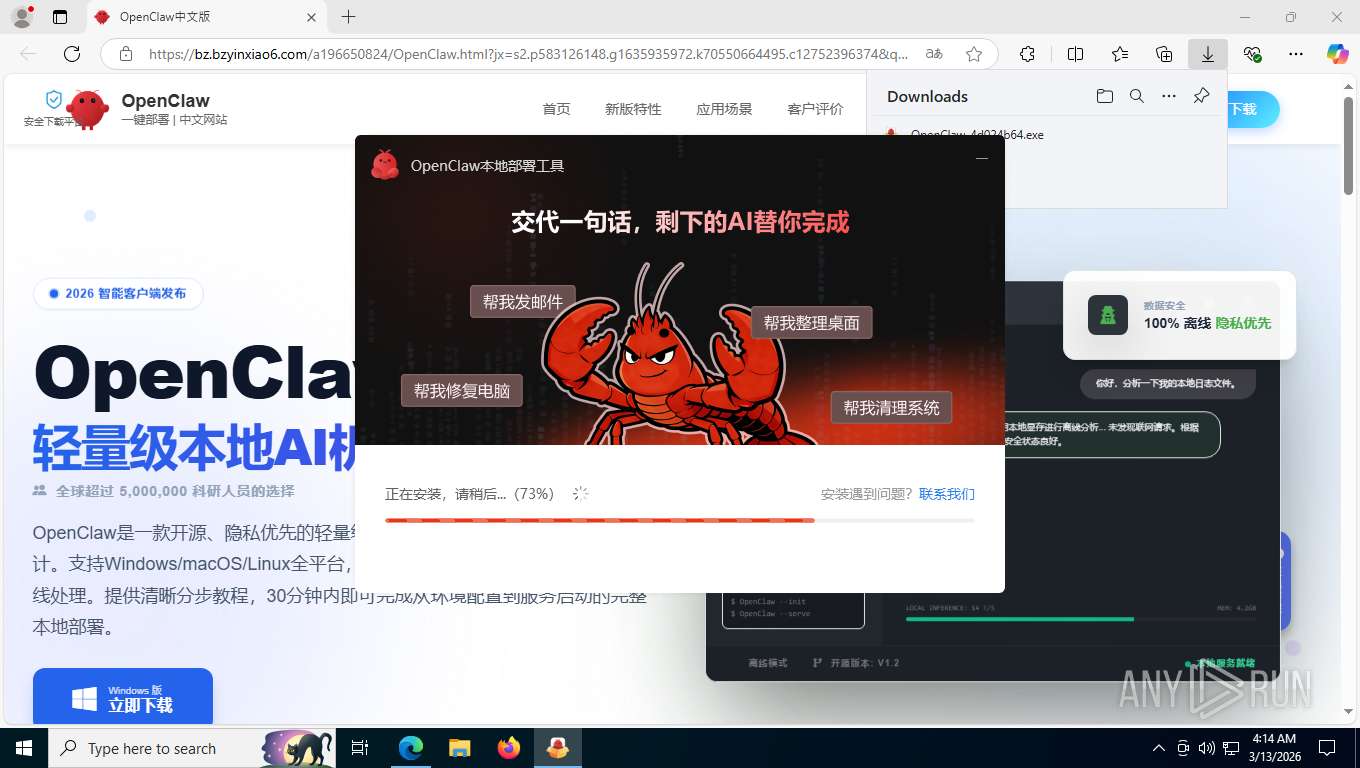
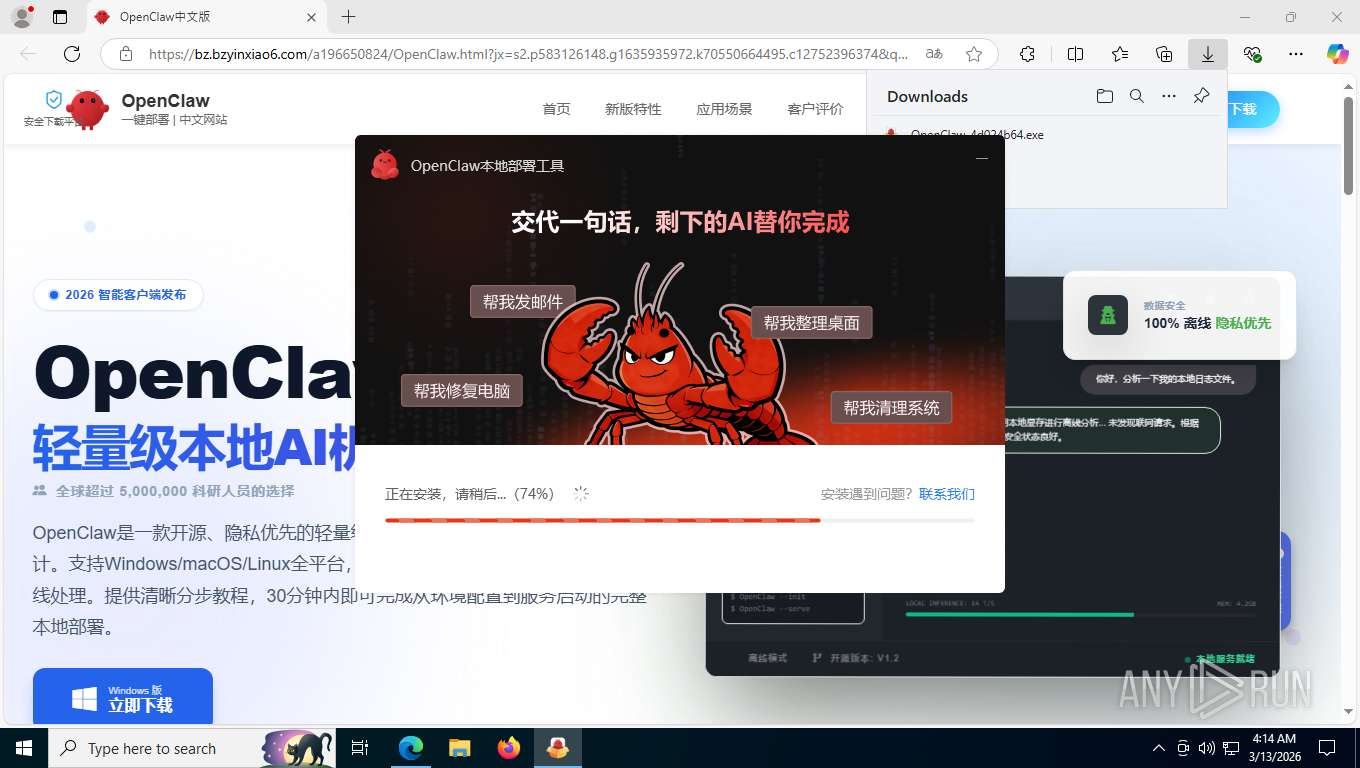
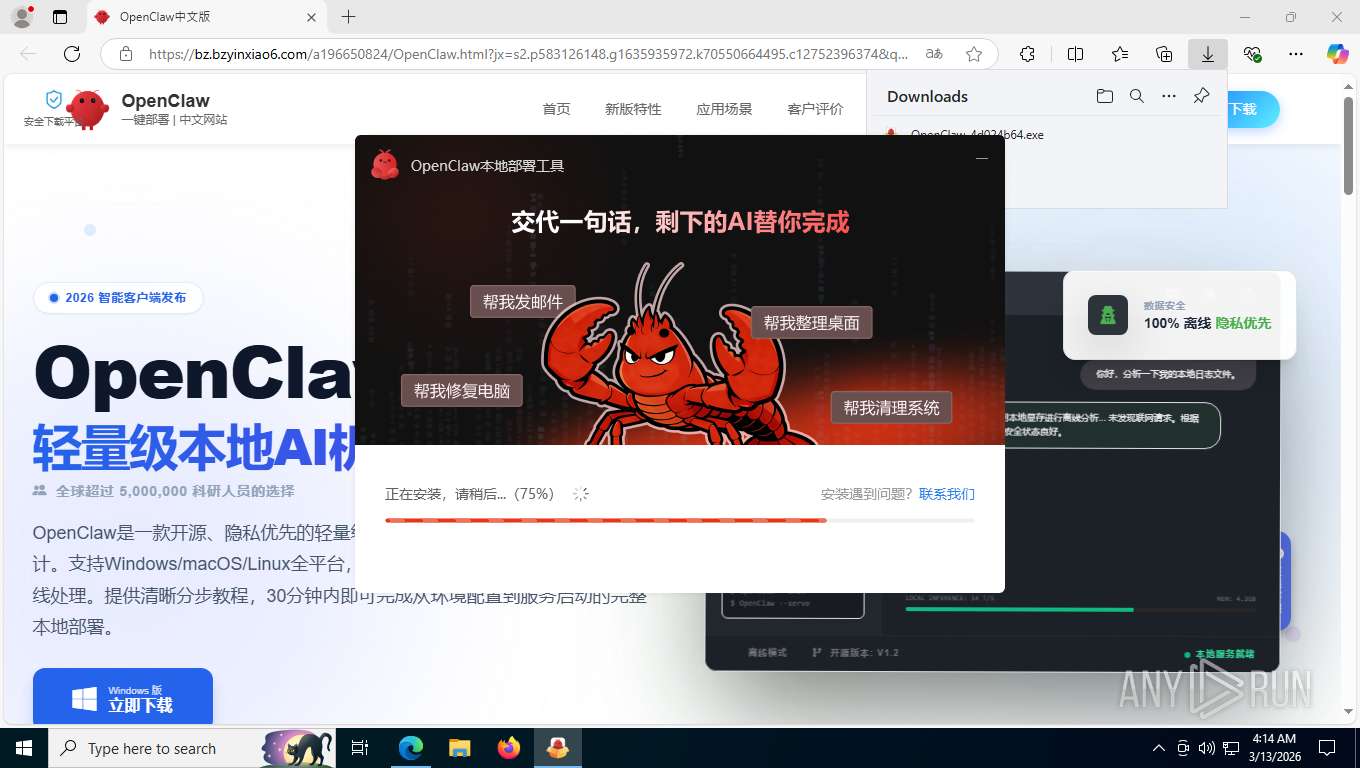
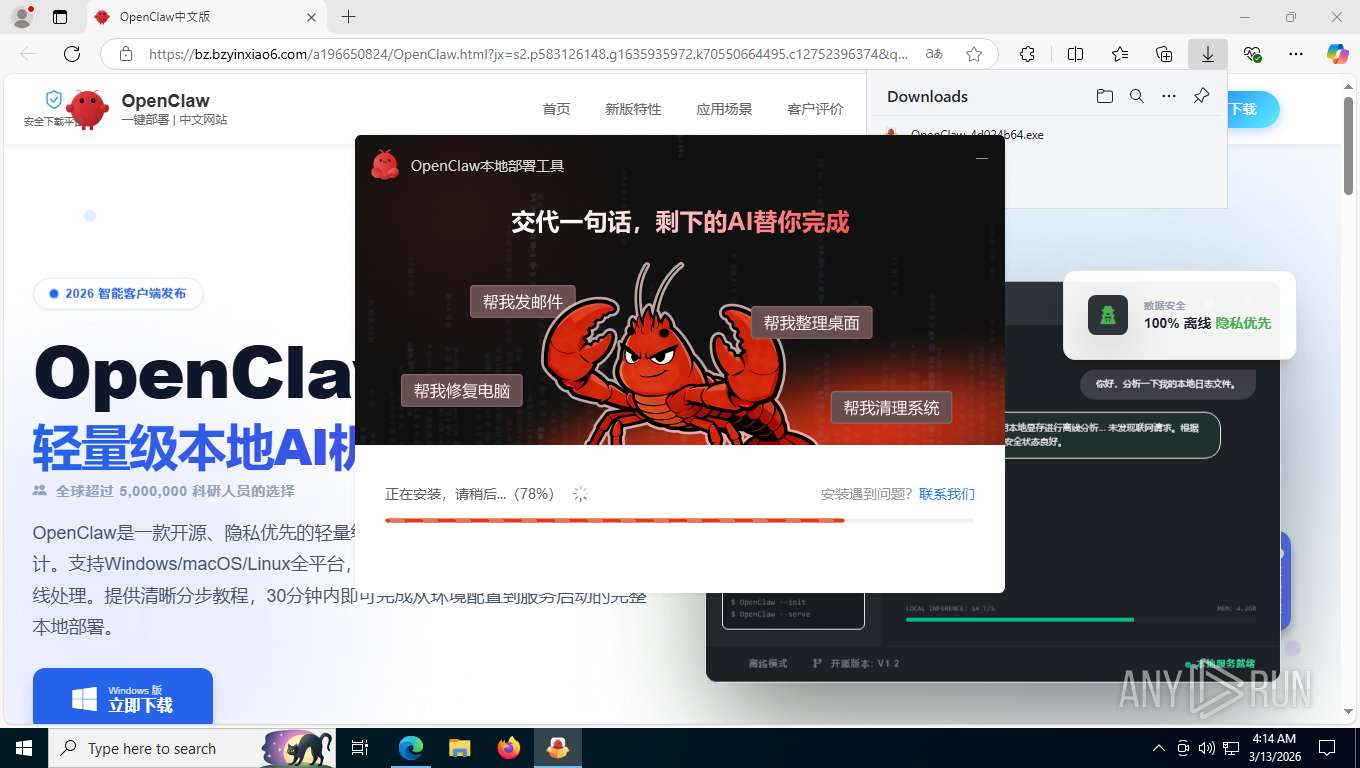
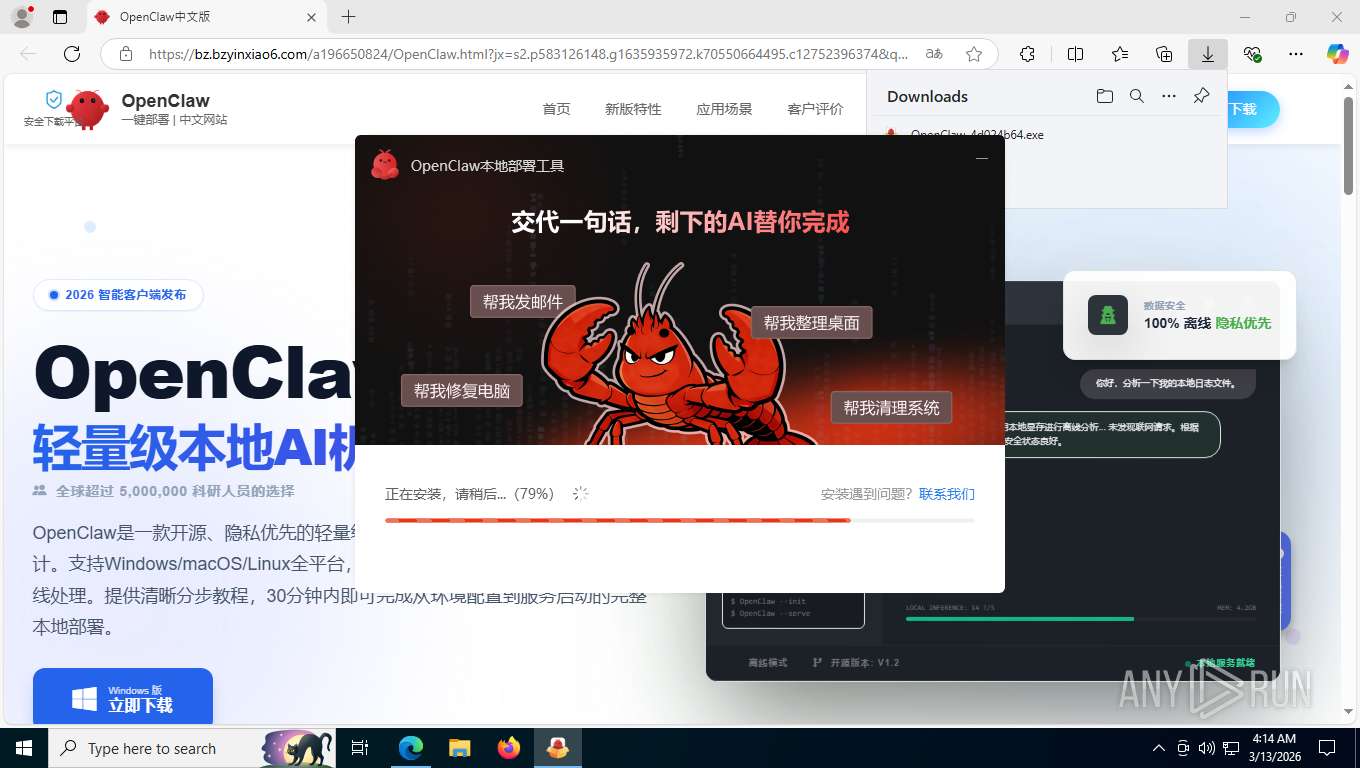
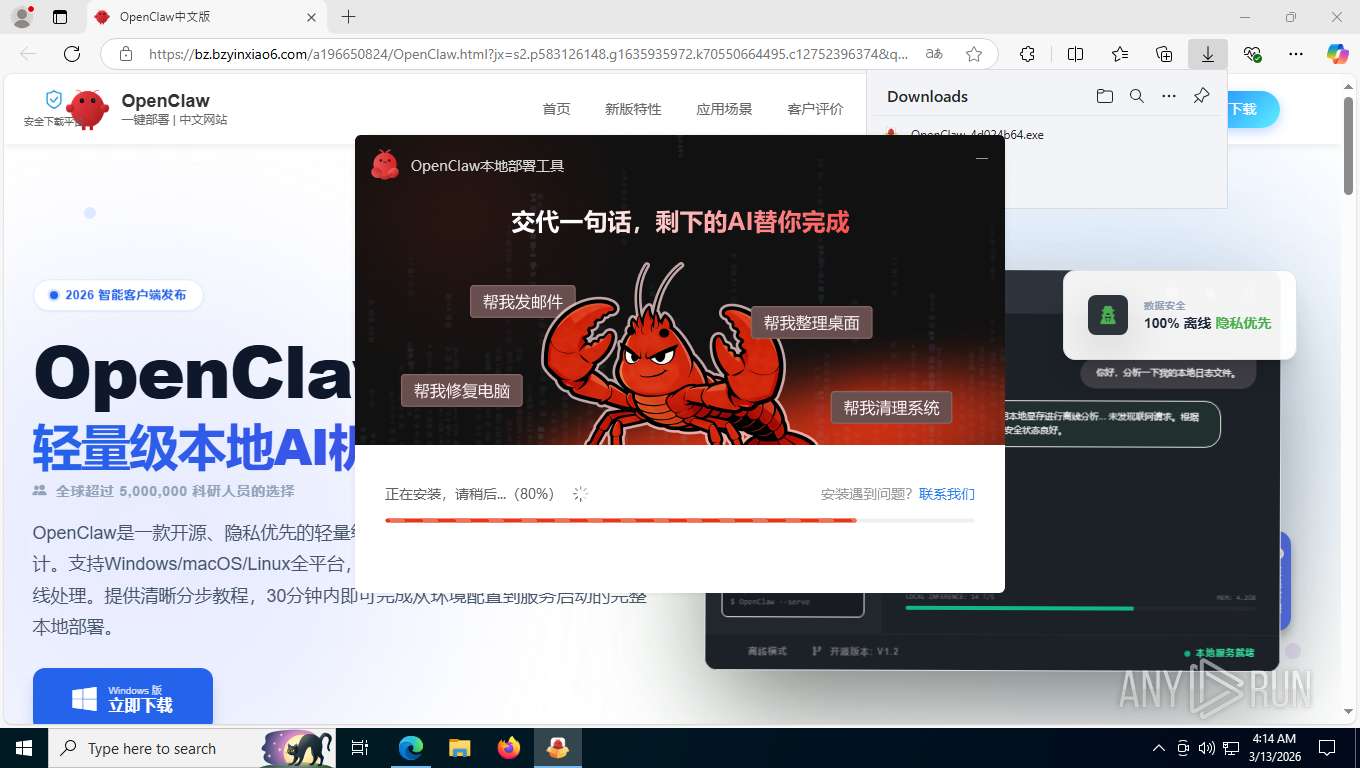
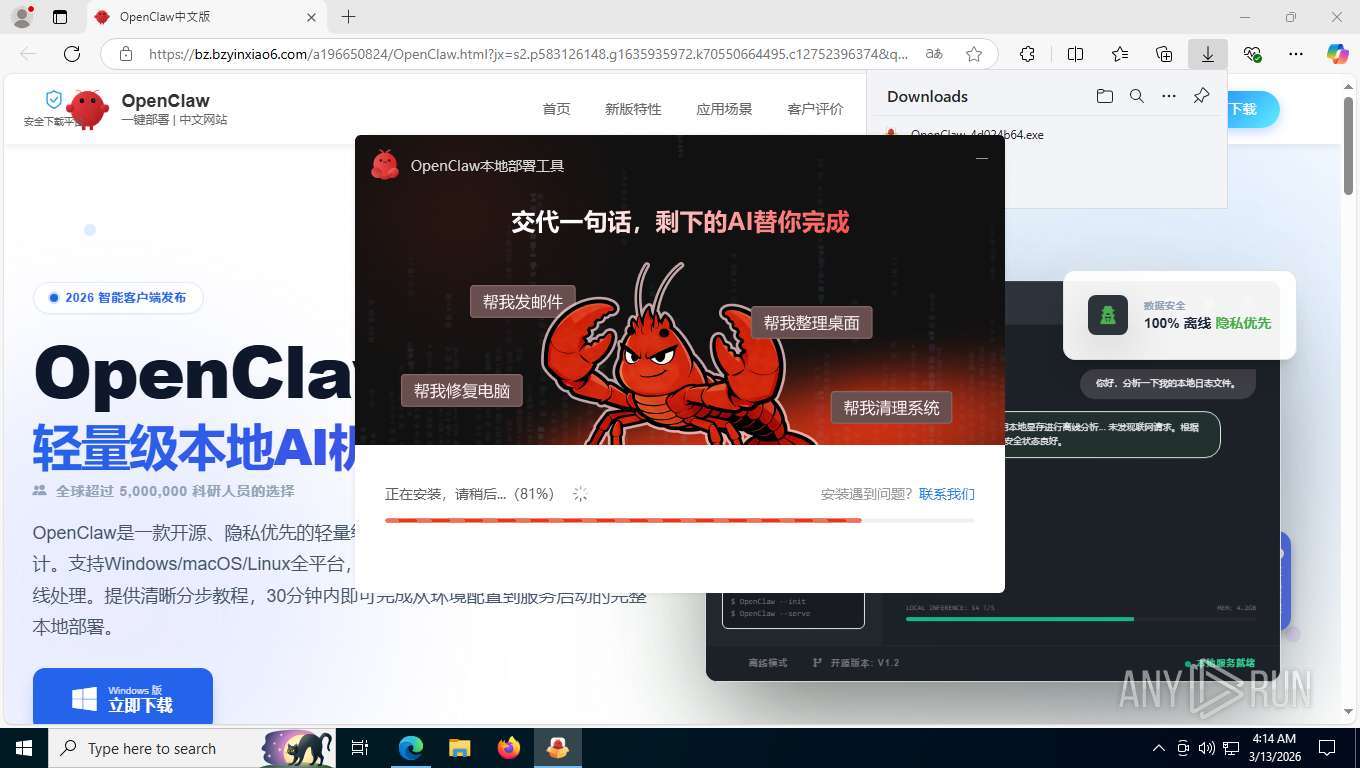
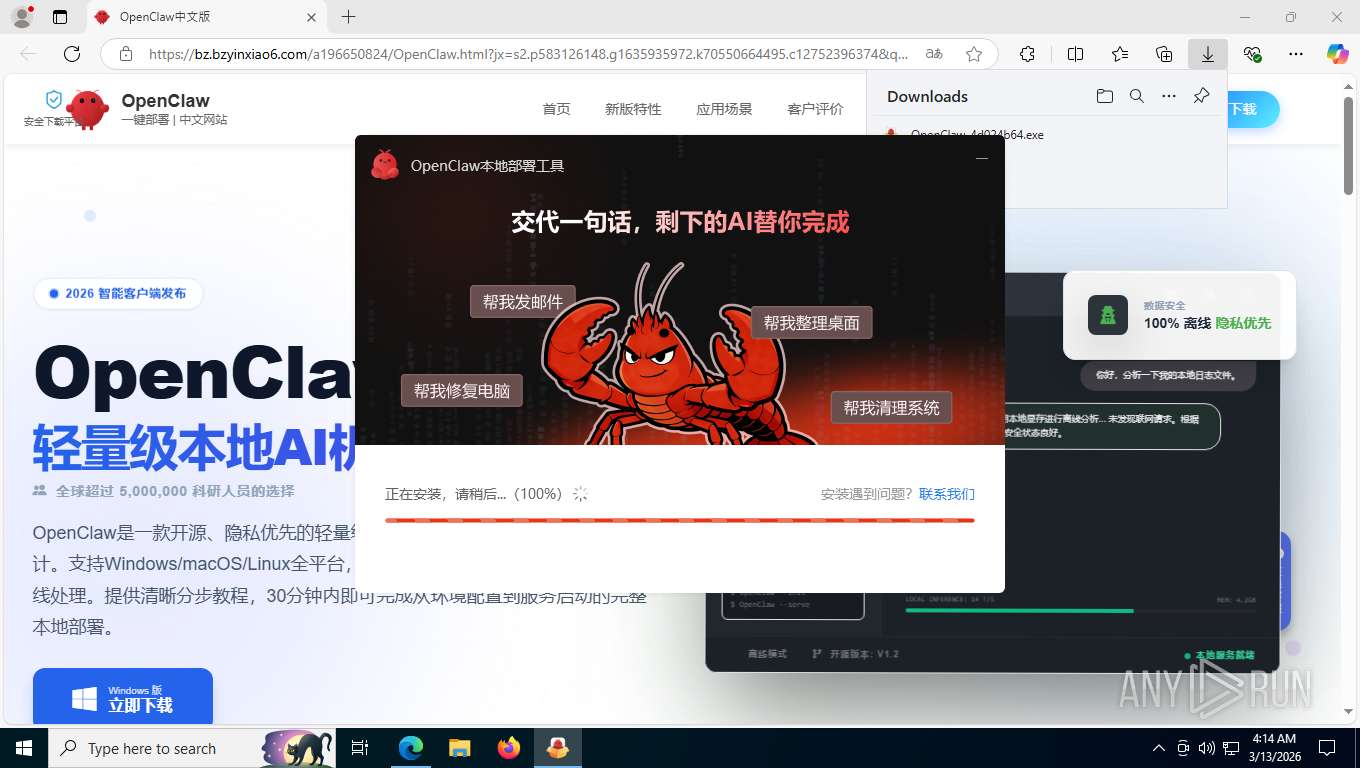
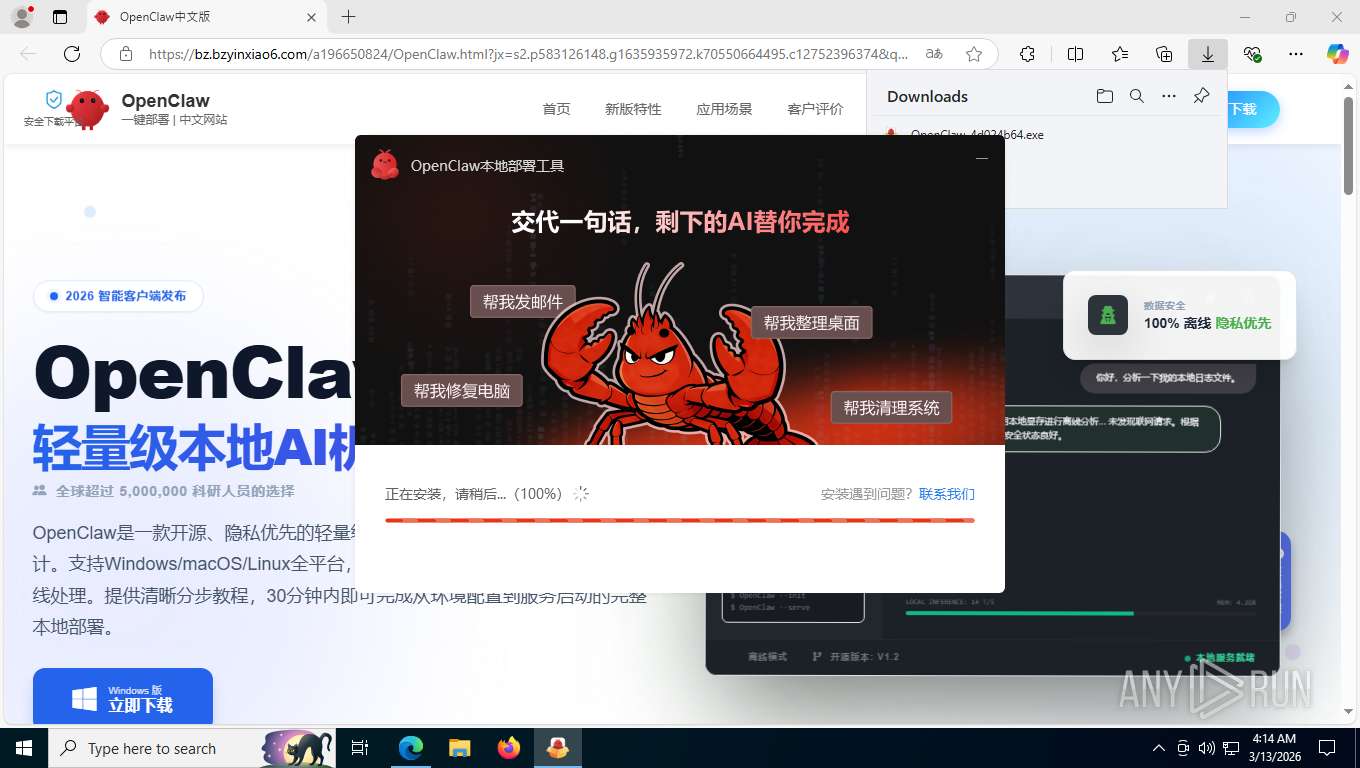
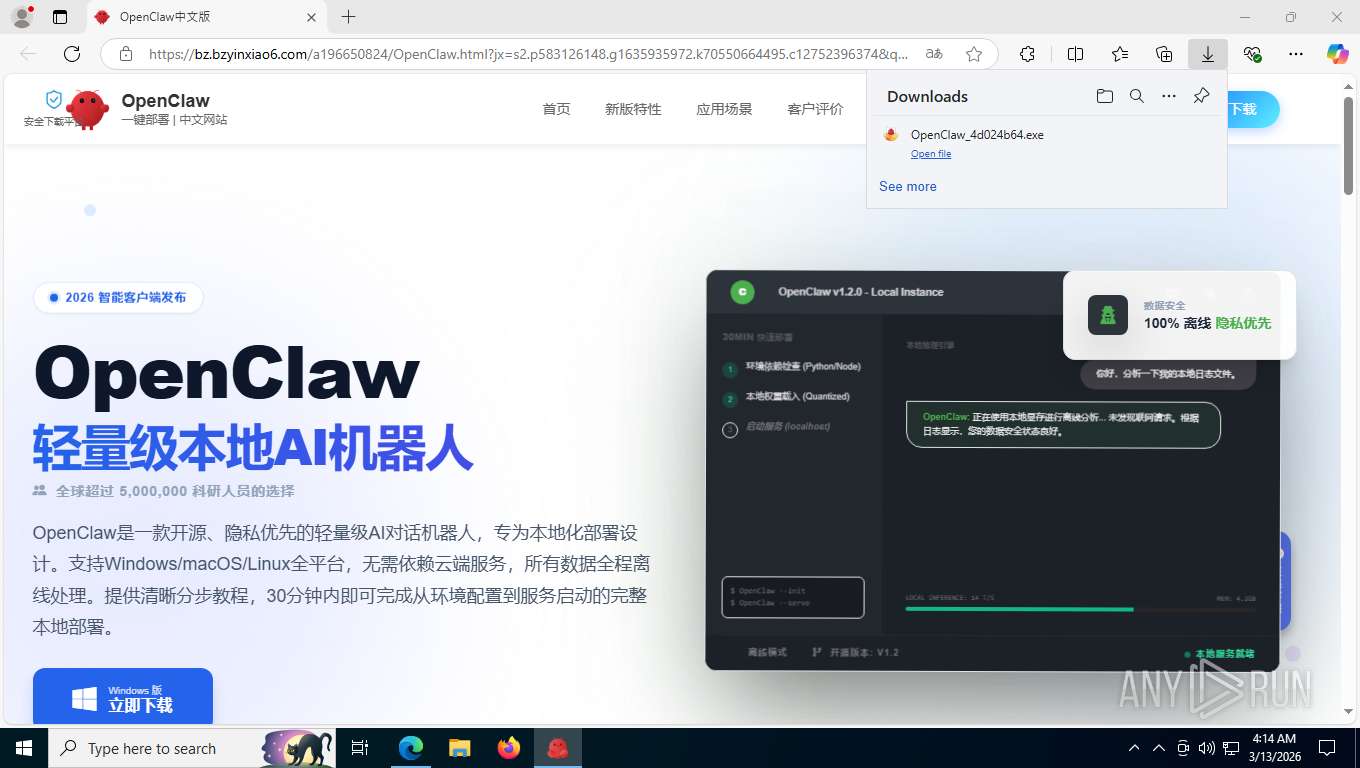
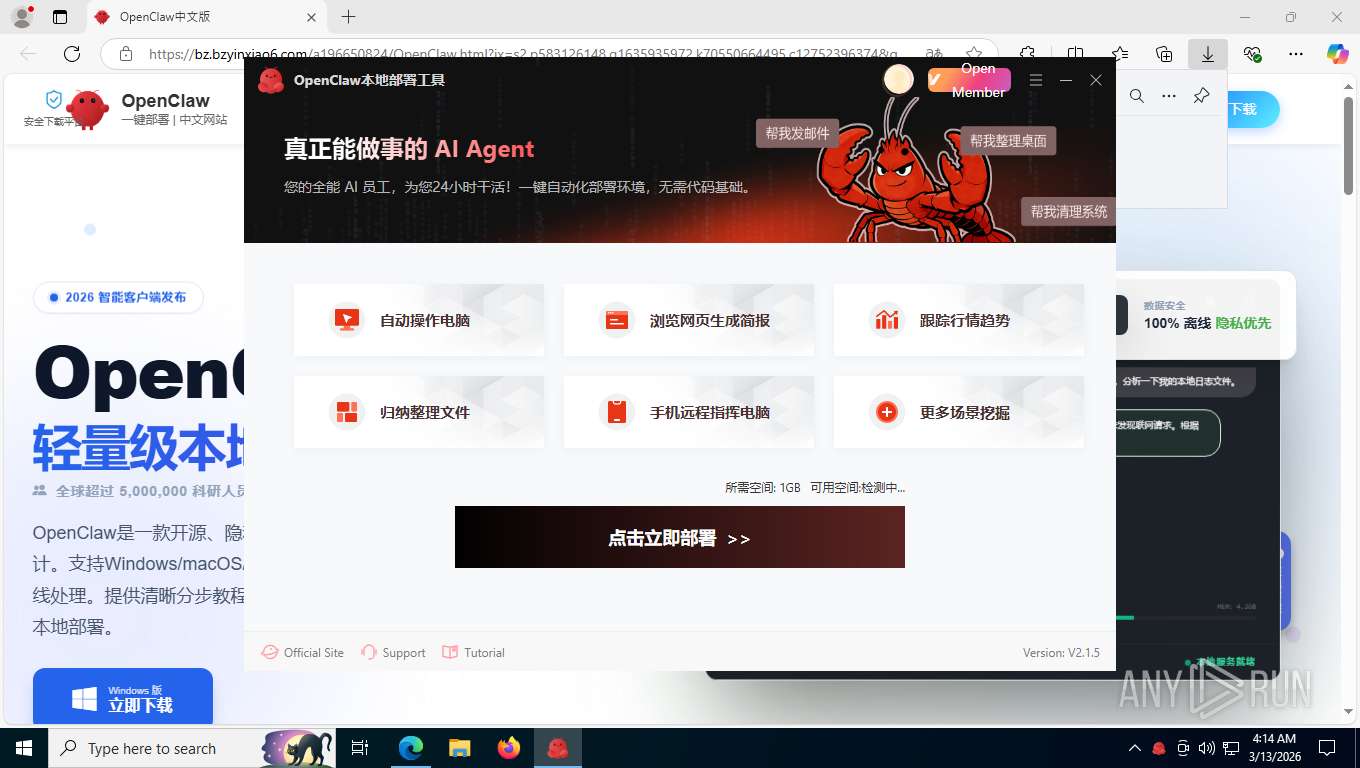
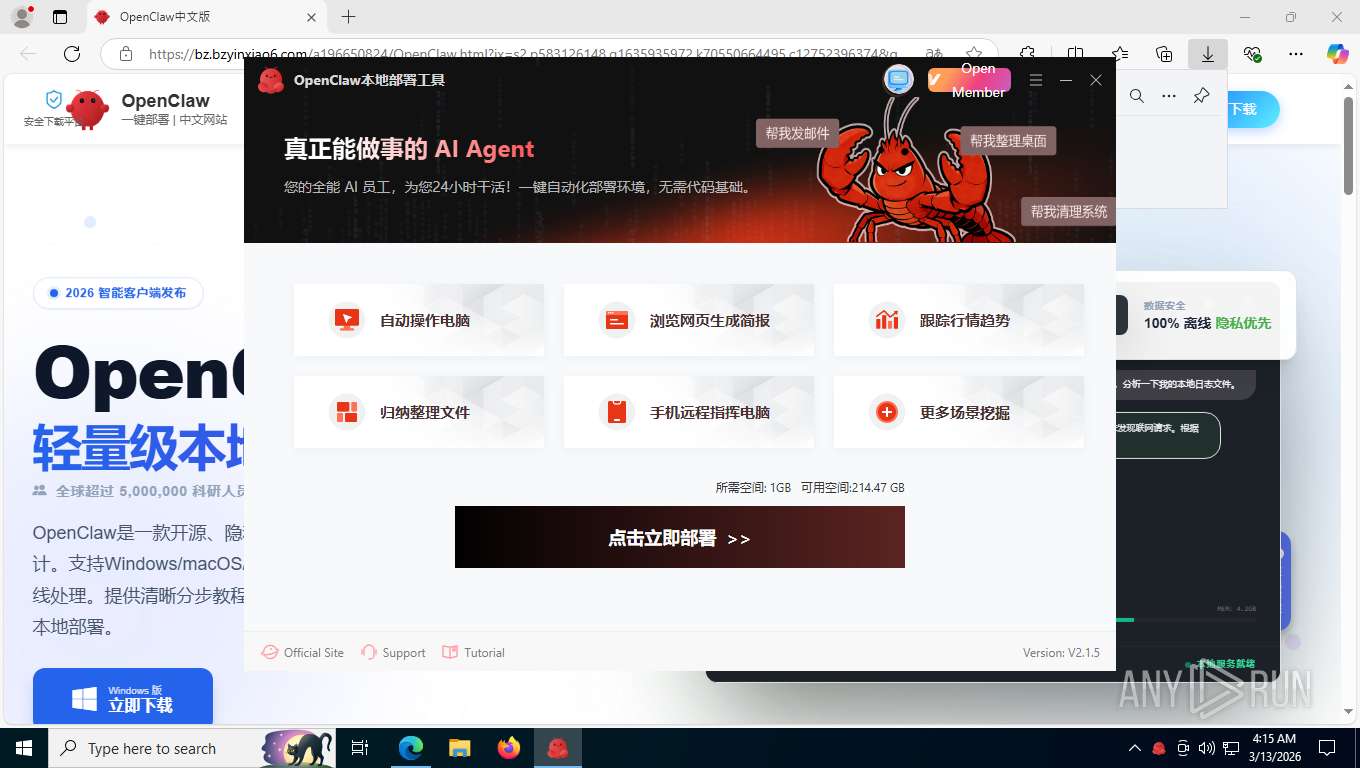
| URL: | https://bz.bzyinxiao6.com/a196650824/OpenClaw.html?jx=s2.p583126148.g1635935972.k70550664495.c12752396374&qhclickid=bd84253d7c5b6084 |
| Full analysis: | https://app.any.run/tasks/94642c69-5ce4-47a5-9cd0-eecbcbc46f0a |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | March 13, 2026, 08:11:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EC0FC3D2CE12B751AD444A06FA7A531D |
| SHA1: | 99A30FE8A95C0C179273CCF2C5C17080FC122CF2 |
| SHA256: | 4396D9BCFD44618C166E83CD21FB85C81D3D91384F9799FF2D4A52C85220748E |
| SSDEEP: | 3:N8V0uTOFqSJLNGEaWXL2wfJNmQA5PDXjX30NeMGOAYHFAFZdRn:2V0uTIqeDnoPDT6rHiVRn |
MALICIOUS
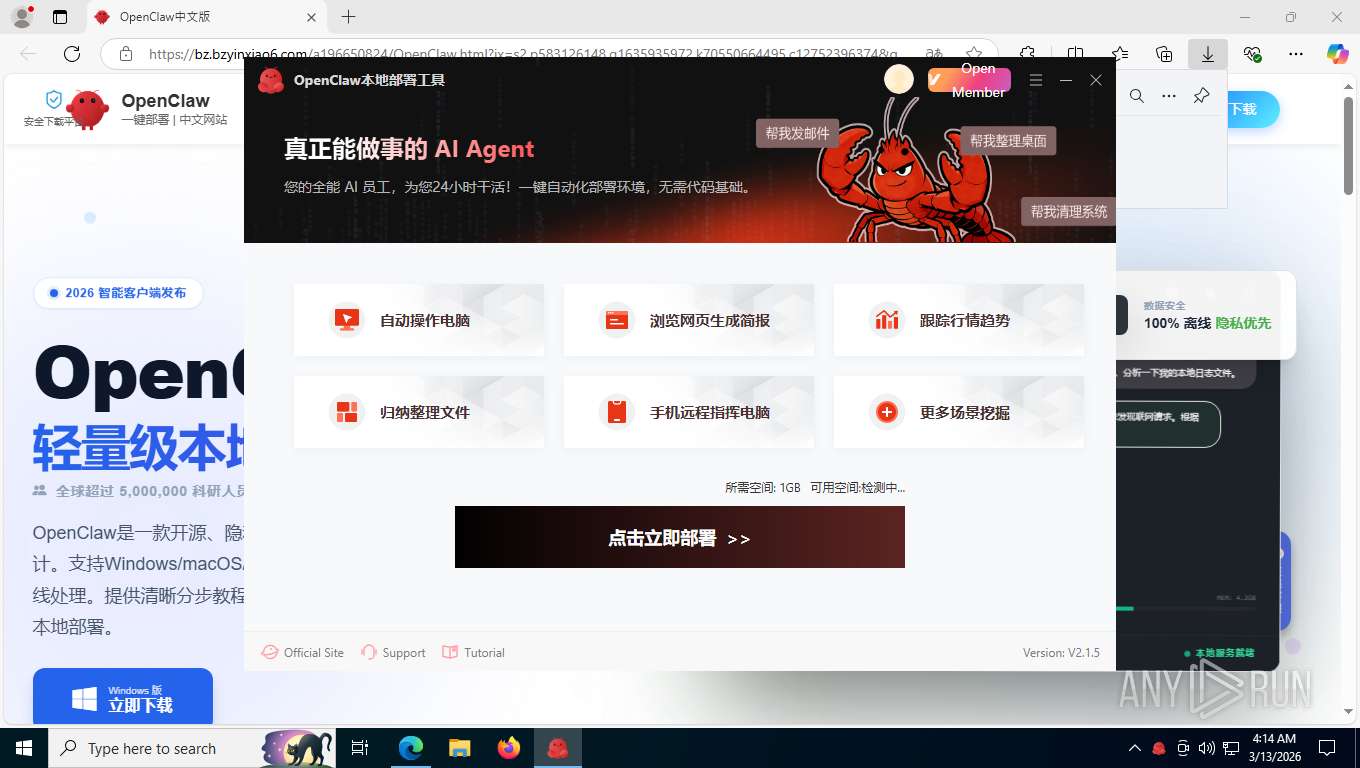
Changes the autorun value in the registry
- OpenClaw_4d024b64.exe (PID: 6300)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- OpenClaw_4d024b64.exe (PID: 6300)
The process creates files with name similar to system file names
- OpenClaw_4d024b64.exe (PID: 6300)
Executable content was dropped or overwritten
- OpenClaw_4d024b64.exe (PID: 6300)
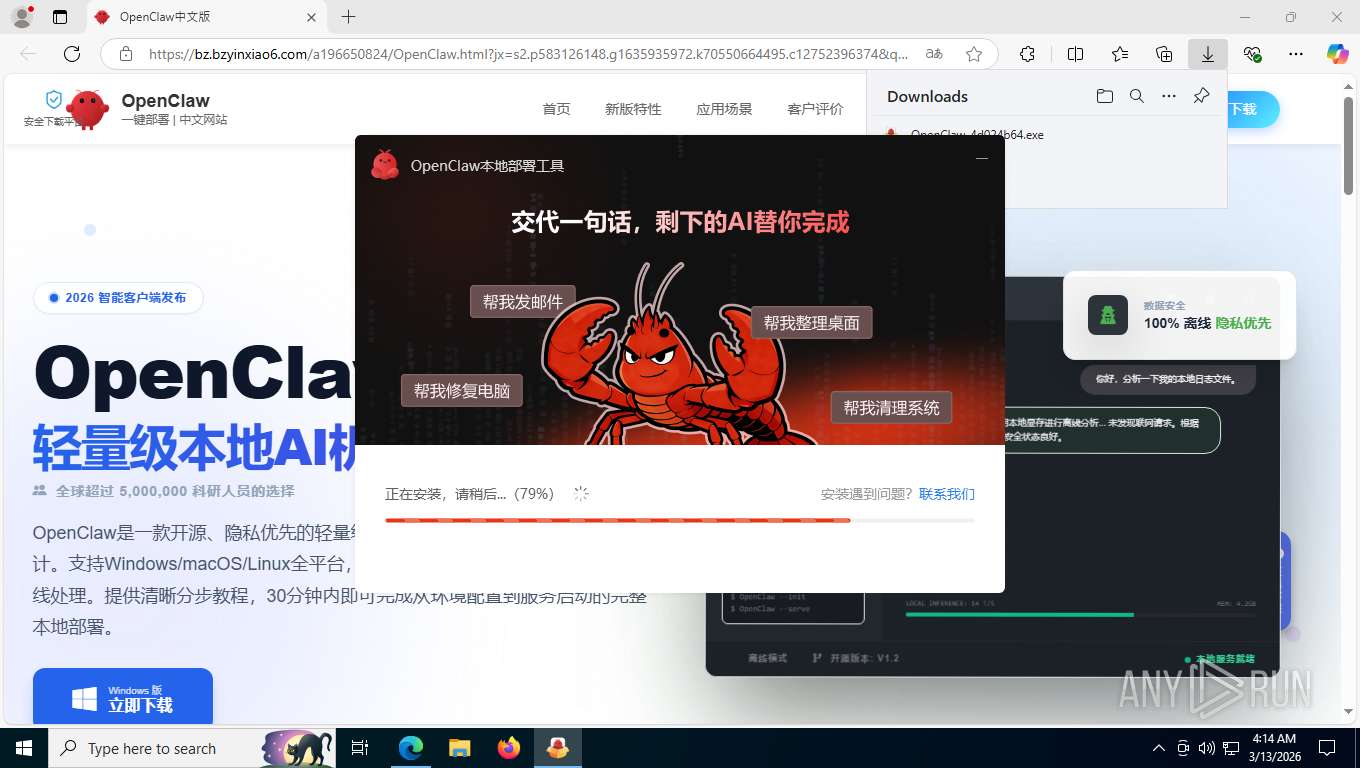
Uses NETSH.EXE to add a firewall rule or allowed programs
- OpenClaw_4d024b64.exe (PID: 6300)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- OpenClaw_4d024b64.exe (PID: 6300)
Application launched itself
- DeOpenClaw.exe (PID: 5528)
Starts CMD.EXE with AutoRun commands disabled
- cmd.exe (PID: 1692)
- cmd.exe (PID: 4484)
- cmd.exe (PID: 4936)
Starts CMD.EXE with special quote handling
- cmd.exe (PID: 1692)
- cmd.exe (PID: 4936)
- cmd.exe (PID: 4484)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1692)
- cmd.exe (PID: 4484)
- cmd.exe (PID: 4936)
- DeOpenClaw.exe (PID: 5528)
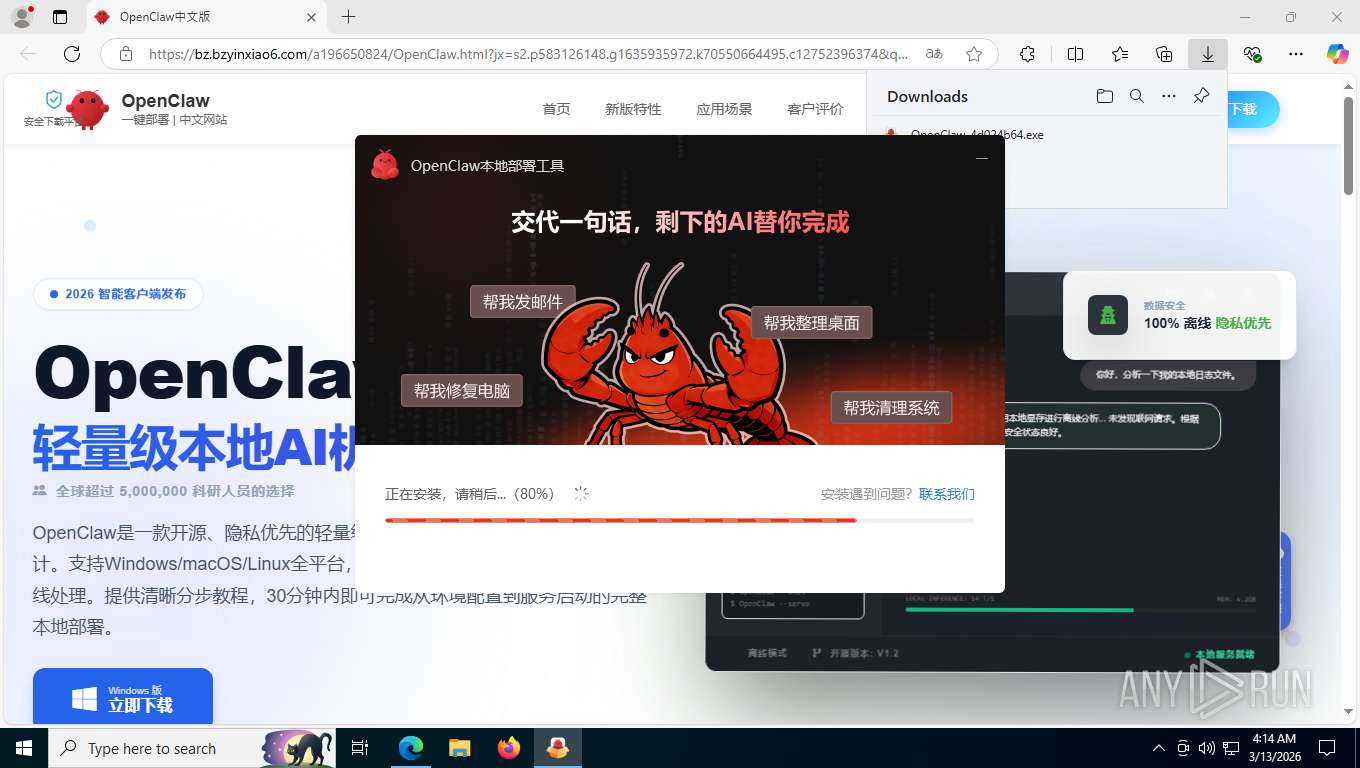
Uses WMIC.EXE to obtain data on the base board management (motherboard or system board)
- cmd.exe (PID: 1692)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 4484)
- cmd.exe (PID: 4936)
Starts POWERSHELL.EXE for commands execution
- DeOpenClaw.exe (PID: 5528)
INFO
Checks supported languages
- identity_helper.exe (PID: 8636)
- OpenClaw_4d024b64.exe (PID: 6300)
- DeOpenClaw.exe (PID: 7368)
- DeOpenClaw.exe (PID: 4352)
- DeOpenClaw.exe (PID: 7320)
- DeOpenClaw.exe (PID: 5528)
Application launched itself
- msedge.exe (PID: 7832)
Reads the computer name
- identity_helper.exe (PID: 8636)
- OpenClaw_4d024b64.exe (PID: 6300)
- DeOpenClaw.exe (PID: 7368)
- DeOpenClaw.exe (PID: 4352)
- DeOpenClaw.exe (PID: 5528)
Reads Environment values
- identity_helper.exe (PID: 8636)
- DeOpenClaw.exe (PID: 5528)
- DeOpenClaw.exe (PID: 7320)
Launching a file from the Downloads directory
- msedge.exe (PID: 7832)
Executable content was dropped or overwritten
- msedge.exe (PID: 7832)
- msedge.exe (PID: 1612)
The sample compiled with chinese language support
- msedge.exe (PID: 1612)
- msedge.exe (PID: 7832)
- OpenClaw_4d024b64.exe (PID: 6300)
Create files in a temporary directory
- OpenClaw_4d024b64.exe (PID: 6300)
- DeOpenClaw.exe (PID: 5528)
Creates files in the program directory
- OpenClaw_4d024b64.exe (PID: 6300)
Reads the machine GUID from the registry
- OpenClaw_4d024b64.exe (PID: 6300)
- DeOpenClaw.exe (PID: 5528)
There is functionality for taking screenshot (YARA)
- OpenClaw_4d024b64.exe (PID: 6300)
Creates files or folders in the user directory
- OpenClaw_4d024b64.exe (PID: 6300)
- DeOpenClaw.exe (PID: 5528)
- DeOpenClaw.exe (PID: 4352)
The sample compiled with english language support
- OpenClaw_4d024b64.exe (PID: 6300)
Reads security settings of Internet Explorer
- OpenClaw_4d024b64.exe (PID: 6300)
- WMIC.exe (PID: 3560)
- WMIC.exe (PID: 6808)
- WMIC.exe (PID: 1172)
Process checks computer location settings
- OpenClaw_4d024b64.exe (PID: 6300)
- DeOpenClaw.exe (PID: 7320)
- DeOpenClaw.exe (PID: 5528)
Launching a file from a Registry key
- OpenClaw_4d024b64.exe (PID: 6300)
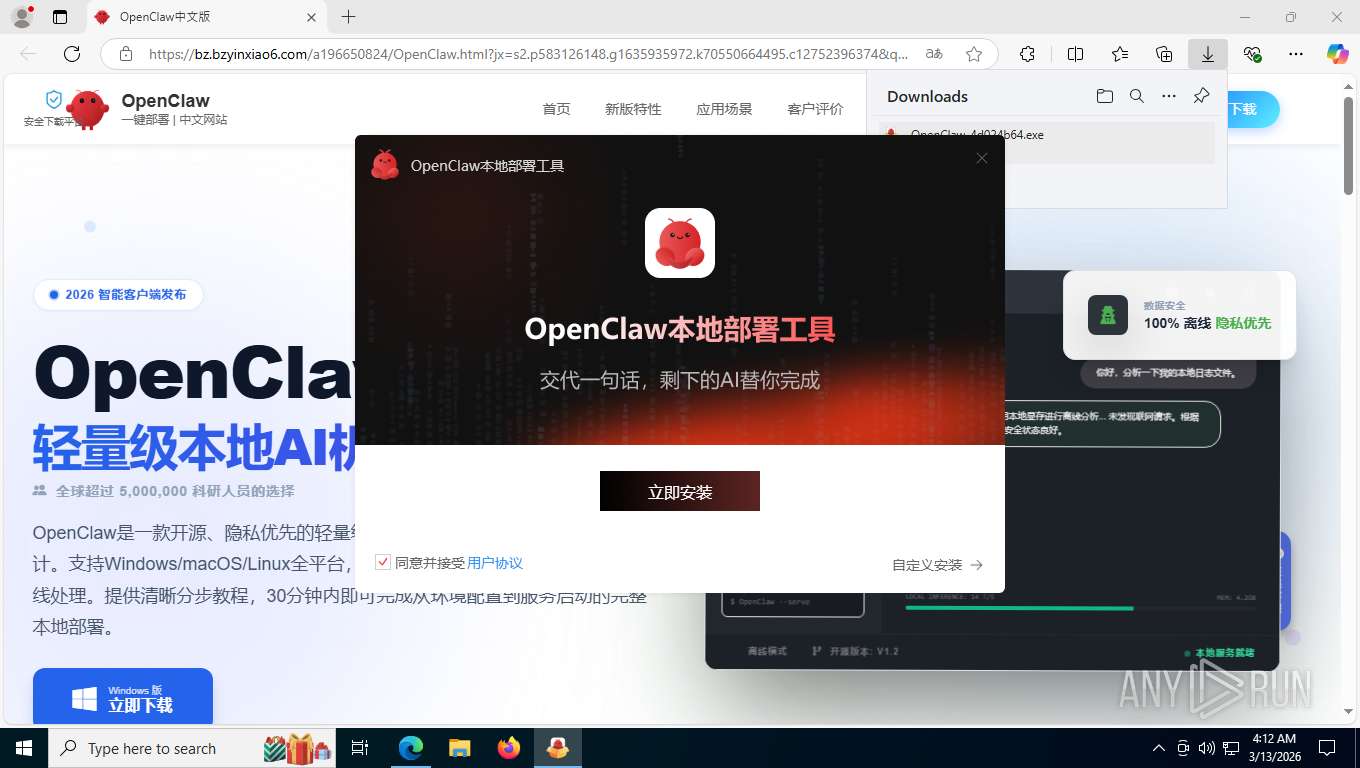
Creates a software uninstall entry
- OpenClaw_4d024b64.exe (PID: 6300)
Reads product name
- DeOpenClaw.exe (PID: 5528)
- DeOpenClaw.exe (PID: 7320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
210
Monitored processes
56
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3836,i,6846211685380865685,7713426814548110931,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6468 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6012,i,6846211685380865685,7713426814548110931,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6836 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1172 | wmic os get osarchitecture | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2276,i,6846211685380865685,7713426814548110931,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2476 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1692 | C:\WINDOWS\system32\cmd.exe /d /s /c "wmic baseboard get Manufacturer" | C:\Windows\System32\cmd.exe | — | DeOpenClaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1916 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7192,i,6846211685380865685,7713426814548110931,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6468 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2248 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3592,i,6846211685380865685,7713426814548110931,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2280 | where powershell | C:\Windows\System32\where.exe | — | DeOpenClaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Where - Lists location of files Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2424 | "C:\Windows\System32\netsh.exe" advfirewall firewall add rule name="DeOpenClaw" description="DeOpenClaw" dir=in action=allow protocol=TCP program="C:\ProgramData\DeOpenClaw\download\minithunderplatform.exe" enable=yes | C:\Windows\SysWOW64\netsh.exe | — | OpenClaw_4d024b64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2572 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4332,i,6846211685380865685,7713426814548110931,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6868 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
12 845
Read events
12 811
Write events
16
Delete events
18
Modification events
| (PID) Process: | (6300) OpenClaw_4d024b64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DeOpenClaw |
| Operation: | write | Name: | DisplayName |
Value: OpenClaw本地部署工具 | |||
| (PID) Process: | (6300) OpenClaw_4d024b64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DeOpenClaw |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Roaming\daesoft\DeOpenClaw\ | |||
| (PID) Process: | (6300) OpenClaw_4d024b64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DeOpenClaw |
| Operation: | write | Name: | UninstallString |
Value: C:\Users\admin\AppData\Roaming\daesoft\DeOpenClaw\uninstx.exe | |||
| (PID) Process: | (6300) OpenClaw_4d024b64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DeOpenClaw |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Roaming\daesoft\DeOpenClaw\DeOpenClaw.exe | |||
| (PID) Process: | (6300) OpenClaw_4d024b64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DeOpenClaw |
| Operation: | write | Name: | DisplayVersion |
Value: 2.1.5.0 | |||
| (PID) Process: | (6300) OpenClaw_4d024b64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DeOpenClaw |
| Operation: | write | Name: | Publisher |
Value: 惠州大鹅软件有限公司 | |||
| (PID) Process: | (6300) OpenClaw_4d024b64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DeOpenClaw |
| Operation: | write | Name: | URLInfoAbout |
Value: https://www.daetool.com/openclaw | |||
| (PID) Process: | (6300) OpenClaw_4d024b64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DeOpenClaw |
| Operation: | write | Name: | URLUpdateInfo |
Value: https://www.daetool.com/openclaw | |||
| (PID) Process: | (6300) OpenClaw_4d024b64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DeOpenClaw |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (6300) OpenClaw_4d024b64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DeOpenClaw |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
Executable files
29
Suspicious files
139
Text files
324
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e5409.TMP | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e5429.TMP | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e5429.TMP | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e5429.TMP | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e5438.TMP | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7832 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e5438.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
268
TCP/UDP connections
121
DNS requests
87
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1612 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 295 b | whitelisted |
1612 | msedge.exe | GET | 200 | 180.163.146.41:443 | https://res.daetool.com/wm-static-resource/Sem/919_sem/logo.png | unknown | image | 729 Kb | unknown |
1612 | msedge.exe | GET | 200 | 180.163.146.39:443 | https://bz.bzyinxiao6.com/static/common/js/jquery-3.5.1.min.js | unknown | text | 87.3 Kb | unknown |
356 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
8776 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1612 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:G0EmJIv68ifCg_Vfl5QeNDf_Dz9ttInv4CVV1642kCA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1612 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
1612 | msedge.exe | GET | 200 | 13.107.246.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | unknown | binary | 82 b | whitelisted |
1612 | msedge.exe | GET | 200 | 52.123.243.218:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | unknown | text | 4.55 Kb | whitelisted |
1612 | msedge.exe | GET | 200 | 180.163.146.39:443 | https://bz.bzyinxiao6.com/a196650824/OpenClaw.html?jx=s2.p583126148.g1635935972.k70550664495.c12752396374&qhclickid=bd84253d7c5b6084 | unknown | html | 82.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8776 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7236 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.204.153:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
1612 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1612 | msedge.exe | 52.123.243.218:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1612 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
bz.bzyinxiao6.com |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
res.daetool.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8776 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1612 | msedge.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
1612 | msedge.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
Process | Message |
|---|---|
OpenClaw_4d024b64.exe | SMessageLoop::Run - exiting,code = 0 SOUI::SMessageLoop::Run e:\soui.2903_static\soui\src\core\smsgloop.cpp:49
|
OpenClaw_4d024b64.exe | FindChildByName2 Failed, no window of class [tabctrl] with name of [tab_installing] was found within [-1] levels SOUI::SWindow::FindChildByName2 e:\soui.2903_mt\soui\include\core\swnd.h:526
|
OpenClaw_4d024b64.exe | FindChildByName2 Failed, no window of class [tabctrl] with name of [tab_installing] was found within [-1] levels SOUI::SWindow::FindChildByName2 e:\soui.2903_mt\soui\include\core\swnd.h:526
|
OpenClaw_4d024b64.exe | FindChildByName2 Failed, no window of class [tabctrl] with name of [tab_installing] was found within [-1] levels SOUI::SWindow::FindChildByName2 e:\soui.2903_mt\soui\include\core\swnd.h:526
|
OpenClaw_4d024b64.exe | FindChildByName2 Failed, no window of class [tabctrl] with name of [tab_installing] was found within [-1] levels SOUI::SWindow::FindChildByName2 e:\soui.2903_mt\soui\include\core\swnd.h:526
|
OpenClaw_4d024b64.exe | FindChildByName2 Failed, no window of class [tabctrl] with name of [tab_installing] was found within [-1] levels SOUI::SWindow::FindChildByName2 e:\soui.2903_mt\soui\include\core\swnd.h:526
|
OpenClaw_4d024b64.exe | FindChildByName2 Failed, no window of class [tabctrl] with name of [tab_installing] was found within [-1] levels SOUI::SWindow::FindChildByName2 e:\soui.2903_mt\soui\include\core\swnd.h:526
|
OpenClaw_4d024b64.exe | FindChildByName2 Failed, no window of class [tabctrl] with name of [tab_installing] was found within [-1] levels SOUI::SWindow::FindChildByName2 e:\soui.2903_mt\soui\include\core\swnd.h:526
|
OpenClaw_4d024b64.exe | FindChildByName2 Failed, no window of class [tabctrl] with name of [tab_installing] was found within [-1] levels SOUI::SWindow::FindChildByName2 e:\soui.2903_mt\soui\include\core\swnd.h:526
|
OpenClaw_4d024b64.exe | FindChildByName2 Failed, no window of class [tabctrl] with name of [tab_installing] was found within [-1] levels SOUI::SWindow::FindChildByName2 e:\soui.2903_mt\soui\include\core\swnd.h:526
|