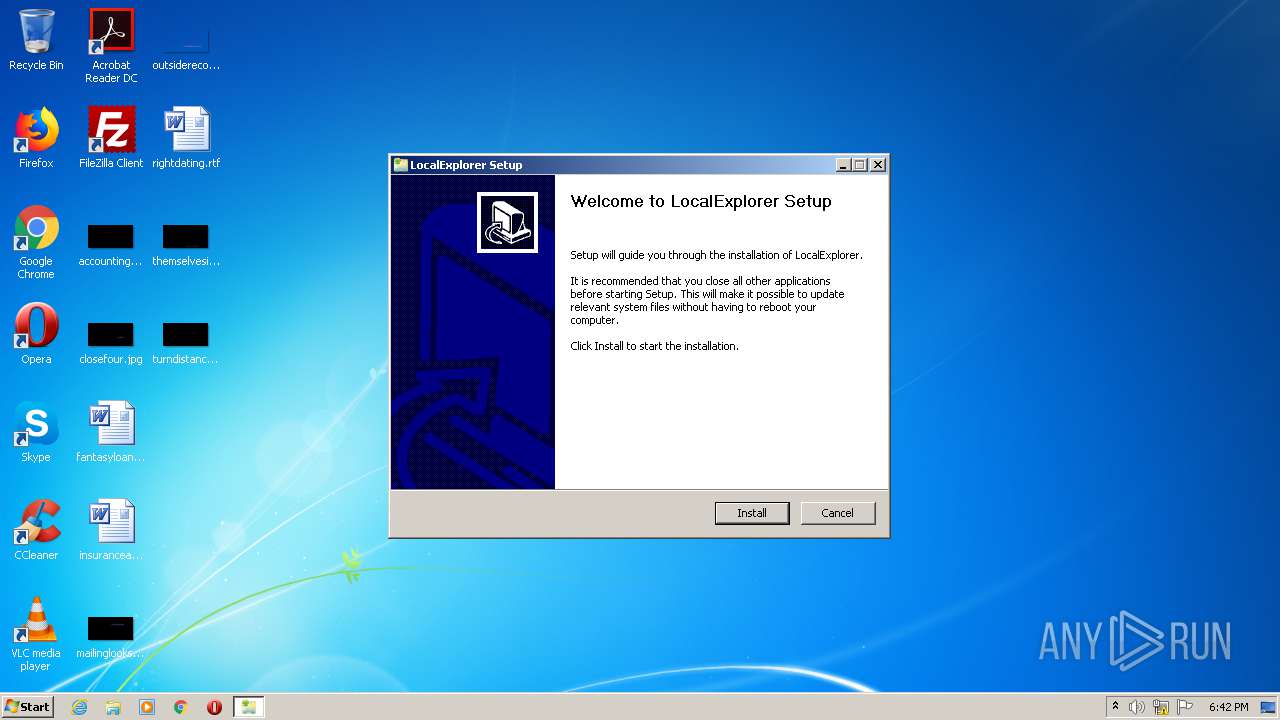
| download: | LocalExplorer-Setup.exe |
| Full analysis: | https://app.any.run/tasks/2776007c-a4ab-4f70-9920-643bab9aad3e |
| Verdict: | Malicious activity |
| Analysis date: | January 06, 2021, 18:42:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 8A5C2B0899D0EB53E02BC197819EB2C3 |
| SHA1: | 6B58FCE33F834DEE973E9D6B3454698D89731584 |
| SHA256: | 43839E66E9E89A2236F485EBC0B14DC472B96D8A003514FD0B336E452ADE9291 |
| SSDEEP: | 6144:F57TcfnCH0um5kTxqeVHt7mP2f3lP2fJTC9aP2fQ:2non5Me9t7G2f92fJToa2fQ |
MALICIOUS
Loads dropped or rewritten executable
- LocalExplorer-Setup.exe (PID: 3056)
Drops executable file immediately after starts
- LocalExplorer-Setup.exe (PID: 3056)
Uses Task Scheduler to run other applications
- LocalExplorer-Setup.exe (PID: 3056)
Loads the Task Scheduler COM API
- SCHTASKS.EXE (PID: 300)
- SCHTASKS.EXE (PID: 2948)
Uses Task Scheduler to autorun other applications
- LocalExplorer-Setup.exe (PID: 3056)
SUSPICIOUS
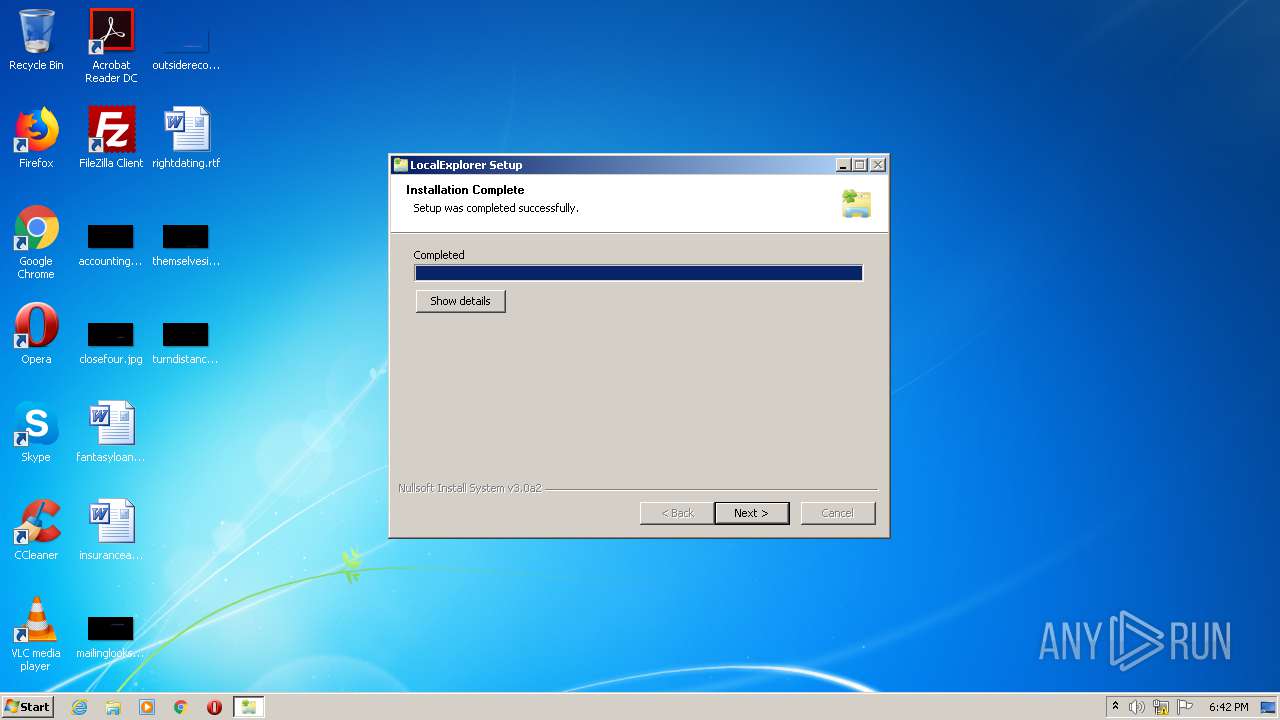
Executable content was dropped or overwritten
- LocalExplorer-Setup.exe (PID: 3056)
Drops a file with too old compile date
- LocalExplorer-Setup.exe (PID: 3056)
Uses TASKKILL.EXE to kill process
- LocalExplorer-Setup.exe (PID: 3056)
Creates a directory in Program Files
- LocalExplorer-Setup.exe (PID: 3056)
Creates files in the program directory
- LocalExplorer-Setup.exe (PID: 3056)
Changes default file association
- LocalExplorer-Setup.exe (PID: 3056)
Creates a software uninstall entry
- LocalExplorer-Setup.exe (PID: 3056)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 06:01:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30e4 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.3.0 |
| ProductVersionNumber: | 1.3.3.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | - |
| CompanyName: | VNProDev |
| FileDescription: | LocalExplorer Installer |
| FileVersion: | 1.3.3.0 |
| LegalCopyright: | © 2014 VNProDev |
| LegalTrademarks: | - |
| ProductName: | LocalExplorer |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-2013 05:01:41 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | VNProDev |
| FileDescription: | LocalExplorer Installer |
| FileVersion: | 1.3.3.0 |
| LegalCopyright: | © 2014 VNProDev |
| LegalTrademarks: | - |
| ProductName: | LocalExplorer |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-2013 05:01:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005DE2 | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50844 |
.rdata | 0x00007000 | 0x000012DA | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.10051 |
.data | 0x00009000 | 0x00025498 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.04207 |
.ndata | 0x0002F000 | 0x00012000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00041000 | 0x00008AA8 | 0x00008C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.70475 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25973 | 1013 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.61844 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.66016 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.79741 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.41973 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
45
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Windows\system32\SCHTASKS.EXE" /Delete /F /TN "LocalExplorer Update" | C:\Windows\system32\SCHTASKS.EXE | — | LocalExplorer-Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | "C:\Users\admin\AppData\Local\Temp\LocalExplorer-Setup.exe" | C:\Users\admin\AppData\Local\Temp\LocalExplorer-Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: VNProDev Integrity Level: MEDIUM Description: LocalExplorer Installer Exit code: 3221226540 Version: 1.3.3.0 Modules
| |||||||||||||||
| 2948 | "C:\Windows\system32\SCHTASKS.EXE" /Create /F /TN "LocalExplorer Update" /SC ONLOGON /RL HIGHEST /TR "\"C:\Program Files\LocalExplorer\LocalExplorer.exe\" /update" | C:\Windows\system32\SCHTASKS.EXE | — | LocalExplorer-Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3000 | "C:\Windows\system32\taskkill.exe" /F /IM LocalExplorer.exe | C:\Windows\system32\taskkill.exe | — | LocalExplorer-Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3056 | "C:\Users\admin\AppData\Local\Temp\LocalExplorer-Setup.exe" | C:\Users\admin\AppData\Local\Temp\LocalExplorer-Setup.exe | explorer.exe | ||||||||||||
User: admin Company: VNProDev Integrity Level: HIGH Description: LocalExplorer Installer Exit code: 0 Version: 1.3.3.0 Modules
| |||||||||||||||
Total events
378
Read events
348
Write events
30
Delete events
0
Modification events
| (PID) Process: | (3056) LocalExplorer-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3056) LocalExplorer-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3056) LocalExplorer-Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\localexplorer |
| Operation: | write | Name: | (default) |
Value: URL:localexplorer Protocol | |||
| (PID) Process: | (3056) LocalExplorer-Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\localexplorer |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3056) LocalExplorer-Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\localexplorer\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: "LocalExplorer.exe,1" | |||
| (PID) Process: | (3056) LocalExplorer-Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\localexplorer\shell\open\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\LocalExplorer\LocalExplorer.exe" "%1" | |||
| (PID) Process: | (3056) LocalExplorer-Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\localexplorerunicode |
| Operation: | write | Name: | (default) |
Value: URL:localexplorerunicode Protocol | |||
| (PID) Process: | (3056) LocalExplorer-Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\localexplorerunicode |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3056) LocalExplorer-Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\localexplorerunicode\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: "LocalExplorer.exe,1" | |||
| (PID) Process: | (3056) LocalExplorer-Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\localexplorerunicode\shell\open\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\LocalExplorer\LocalExplorer.exe" "%1" /unicode | |||
Executable files
6
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3056 | LocalExplorer-Setup.exe | C:\Users\admin\AppData\Local\Temp\nsx58AB.tmp | — | |
MD5:— | SHA256:— | |||
| 3056 | LocalExplorer-Setup.exe | C:\Program Files\LocalExplorer\update.json | text | |
MD5:96BD345D38EA90987A1D8C2F83FE6AAD | SHA256:5A2C4F7F293460D5C74461ED26D706EE71BAD0A552670644E65197CBBA44CB0B | |||
| 3056 | LocalExplorer-Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd41D6.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3056 | LocalExplorer-Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd41D6.tmp\System.dll | executable | |
MD5:960A5C48E25CF2BCA332E74E11D825C9 | SHA256:484F8E9F194ED9016274EF3672B2C52ED5F574FB71D3884EDF3C222B758A75A2 | |||
| 3056 | LocalExplorer-Setup.exe | C:\Program Files\LocalExplorer\Uninstall.exe | executable | |
MD5:3227FFF352FA3BB0500B9E63CD74E1DD | SHA256:15932CCD8D58DDB8773DB1BF5BBF6D34FEC685A84D2BF6B9AFD9B2082107BE60 | |||
| 3056 | LocalExplorer-Setup.exe | C:\Program Files\LocalExplorer\LocalExplorer.exe | executable | |
MD5:10ABB1B203C2A5CD0369B9DB6FC1F6B8 | SHA256:2B5395FD7E8C9F764A1406E5D0FE3D14C9528210AAEAA97CE5E8A9C4DB15EAC5 | |||
| 3056 | LocalExplorer-Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd41D6.tmp\inetc.dll | executable | |
MD5:D7A3FA6A6C738B4A3C40D5602AF20B08 | SHA256:67EFF17C53A78C8EC9A28F392B9BB93DF3E74F96F6ECD87A333A482C36546B3E | |||
| 3056 | LocalExplorer-Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd41D6.tmp\nsDialogs.dll | executable | |
MD5:8CED0B79F7B9033D0795AAB3BE6D627C | SHA256:495BDDC0BE6E18E981DB82FAB9D1DE55C7E269AB4EC3FF43035193BC017A307B | |||
| 3056 | LocalExplorer-Setup.exe | C:\Users\admin\AppData\Local\Temp\nsd41D6.tmp\nsisdt.dll | executable | |
MD5:DF4795DFABE3BC9278A73D496CC4B40D | SHA256:2261027077F23C8DBA6B72AF28862832AAA059740D0F5634B46CABB14326DD10 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3056 | LocalExplorer-Setup.exe | 172.217.214.113:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3056 | LocalExplorer-Setup.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3056 | LocalExplorer-Setup.exe | Misc activity | SUSPICIOUS [PTsecurity] HTTP header - Sometimes used by hostile installer |