| File name: | DeviceDiagnostics.jnlp |
| Full analysis: | https://app.any.run/tasks/8f4f3d7a-bc79-43e0-84bb-08daab9bb68c |
| Verdict: | Malicious activity |
| Analysis date: | October 31, 2019, 18:46:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text, with CRLF line terminators |
| MD5: | 77D24E43FC69663246FD6E5CCD209CCD |
| SHA1: | E1EFB6319FCBE638A6E2659061CC532ECE727900 |
| SHA256: | 438265DAAD92C3F18C8FC6F72B1161237475451DD6D363D3C925A7C89F7D9CAA |
| SSDEEP: | 12:TMHdfsOUEufSEd4A6btTyNkZkANqe40SrNaIfH4VHELPfdXYUMdBUBdjpfTz:2dUt/f/d4ueZvAmM3XudSTz |
MALICIOUS
Starts Visual C# compiler
- sdiagnhost.exe (PID: 3456)
SUSPICIOUS
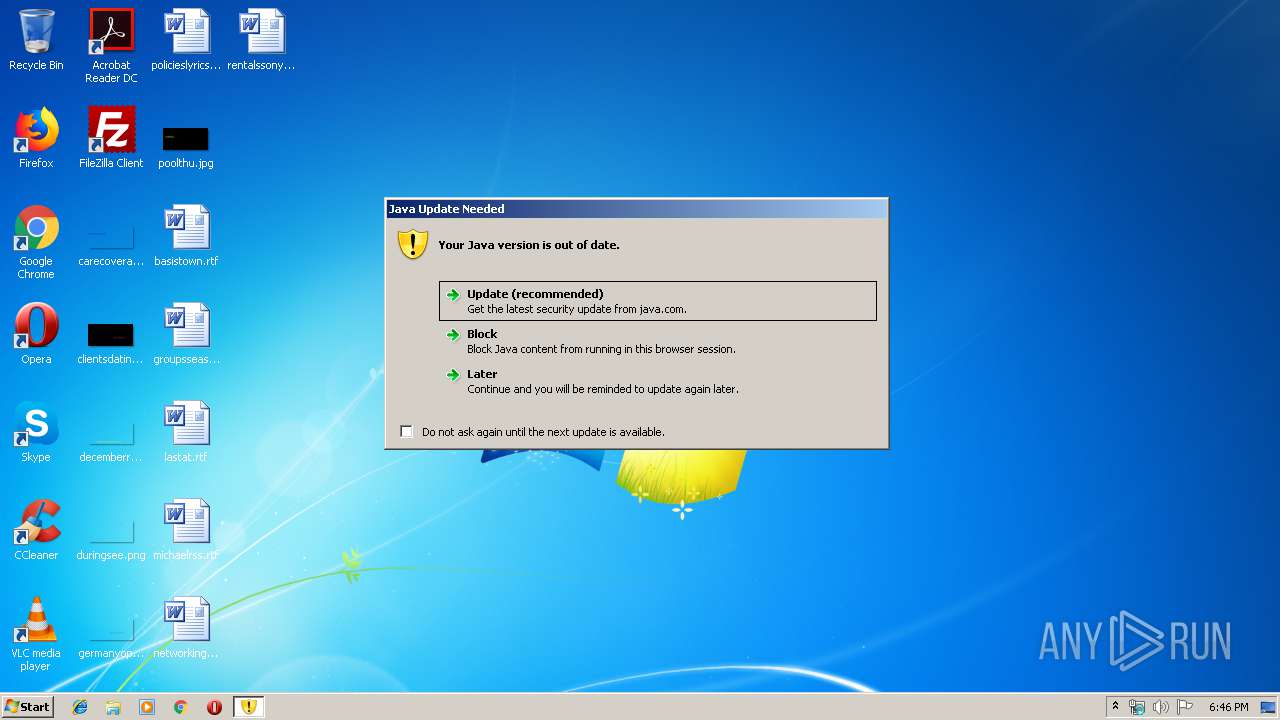
Executes JAVA applets
- javaws.exe (PID: 1608)
Check for Java to be installed
- javaws.exe (PID: 1608)
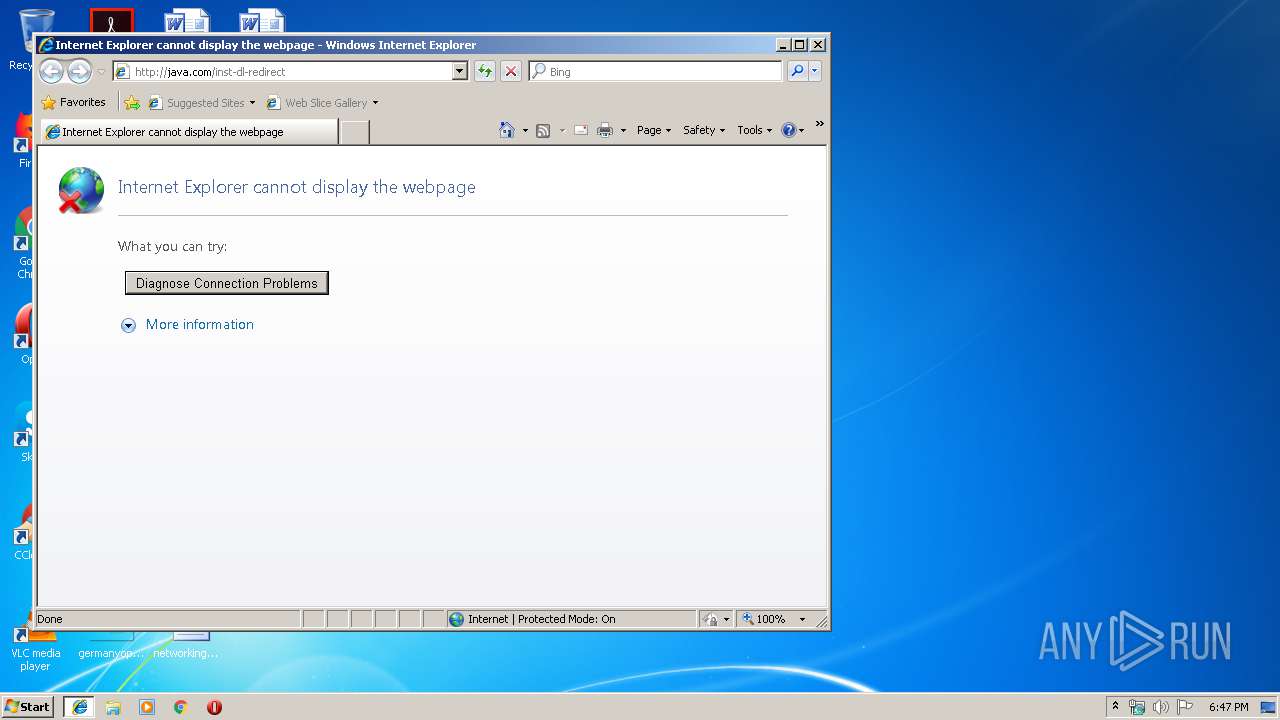
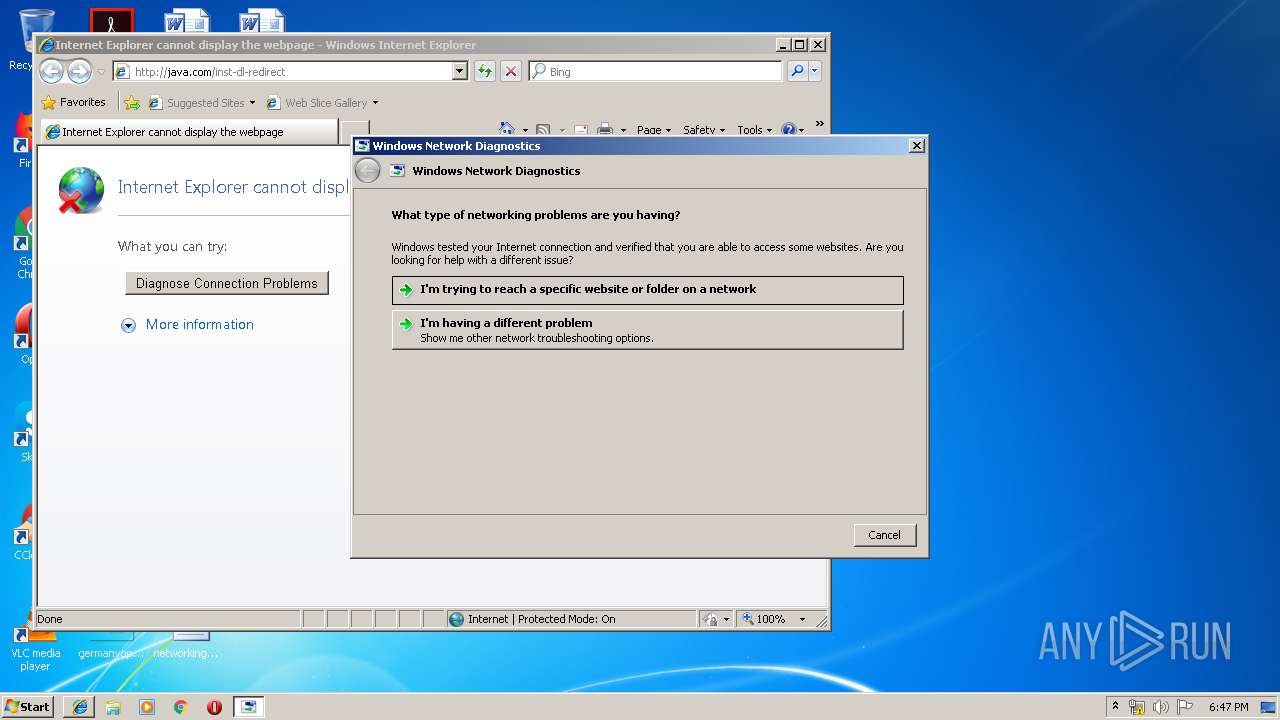
Starts Internet Explorer
- javaws.exe (PID: 1608)
Executed via COM
- sdiagnhost.exe (PID: 2924)
- sdiagnhost.exe (PID: 3456)
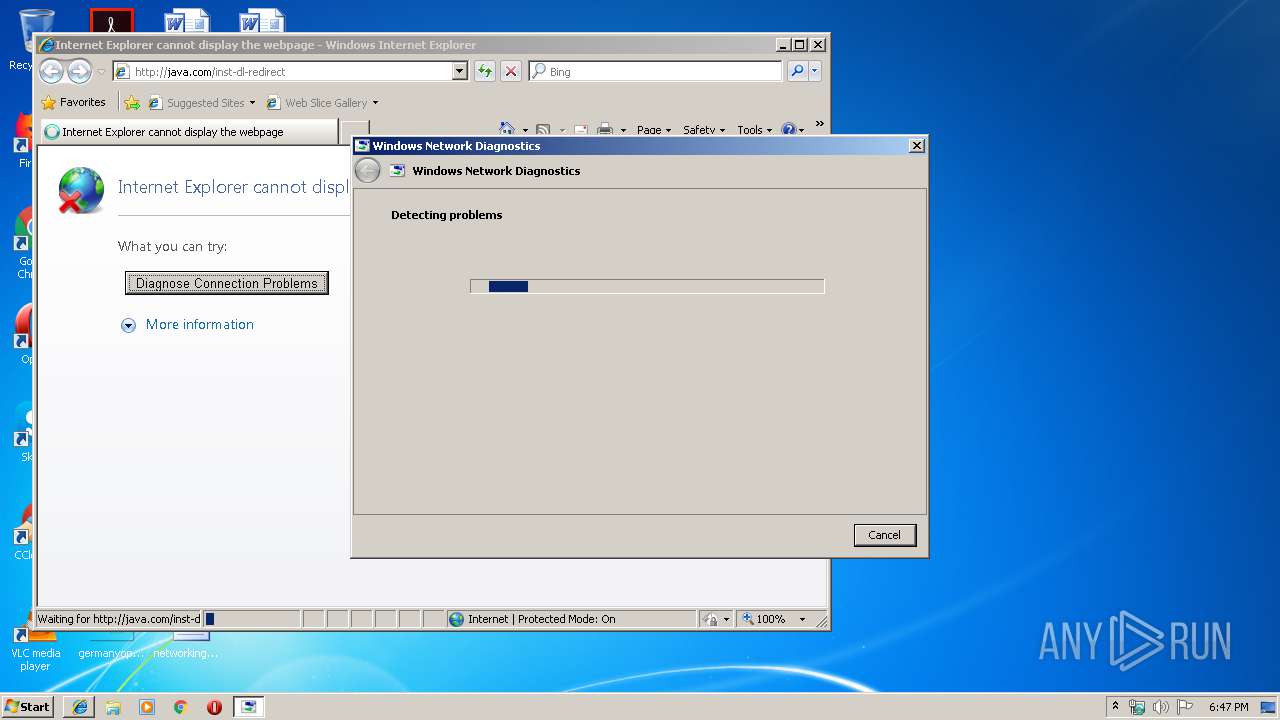
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 2924)
- sdiagnhost.exe (PID: 3456)
Executable content was dropped or overwritten
- msdt.exe (PID: 2456)
- msdt.exe (PID: 2524)
INFO
Manual execution by user
- msdt.exe (PID: 2456)
Reads internet explorer settings
- iexplore.exe (PID: 408)
Reads Internet Cache Settings
- iexplore.exe (PID: 408)
Changes internet zones settings
- iexplore.exe (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jnlp | | | Java Web Start application descriptor (88.3) |
|---|---|---|
| .xml | | | Generic XML (ASCII) (11.6) |
EXIF
XMP
| JnlpSpec: | 1.6+ |
|---|---|
| JnlpCodebase: | https://vocollect.blob.core.windows.net:443/devicediagnostics |
| JnlpHref: | DeviceDiagnostics.jnlp |
| JnlpInformationTitle: | Device Diagnostics |
| JnlpInformationVendor: | Vocollect, Inc. |
| JnlpInformationDescription: | Vocollect Device Diagnostics Troubleshooting Tool |
| JnlpInformationIconHref: | vocollect_icon.gif |
| JnlpInformationShortcutOnline: | |
| JnlpInformationShortcutDesktop: | - |
| JnlpInformationShortcutMenuSubmenu: | Device Diagnostics |
| JnlpInformationOffline-allowed: | - |
| JnlpUpdateCheck: | timeout |
| JnlpUpdatePolicy: | always |
| JnlpSecurityAll-permissions: | - |
| JnlpResourcesJ2seVersion: | 1.6+ |
| JnlpResourcesJarHref: | DeviceDiagnostics.jar |
| JnlpApplication-descMain-class: | com.vocollect.devicediagnostics.DeviceDiagnostics |
Total processes
53
Monitored processes
18
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3252 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 564 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\system32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Java\jre1.8.0_92\bin\javaws.exe" "C:\Users\admin\AppData\Local\Temp\DeviceDiagnostics.jnlp" | C:\Program Files\Java\jre1.8.0_92\bin\javaws.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Start Launcher Exit code: 1 Version: 11.92.2.14 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.92.2" "1572547610" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1932 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\system32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.suppression.11.92.2" "false" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
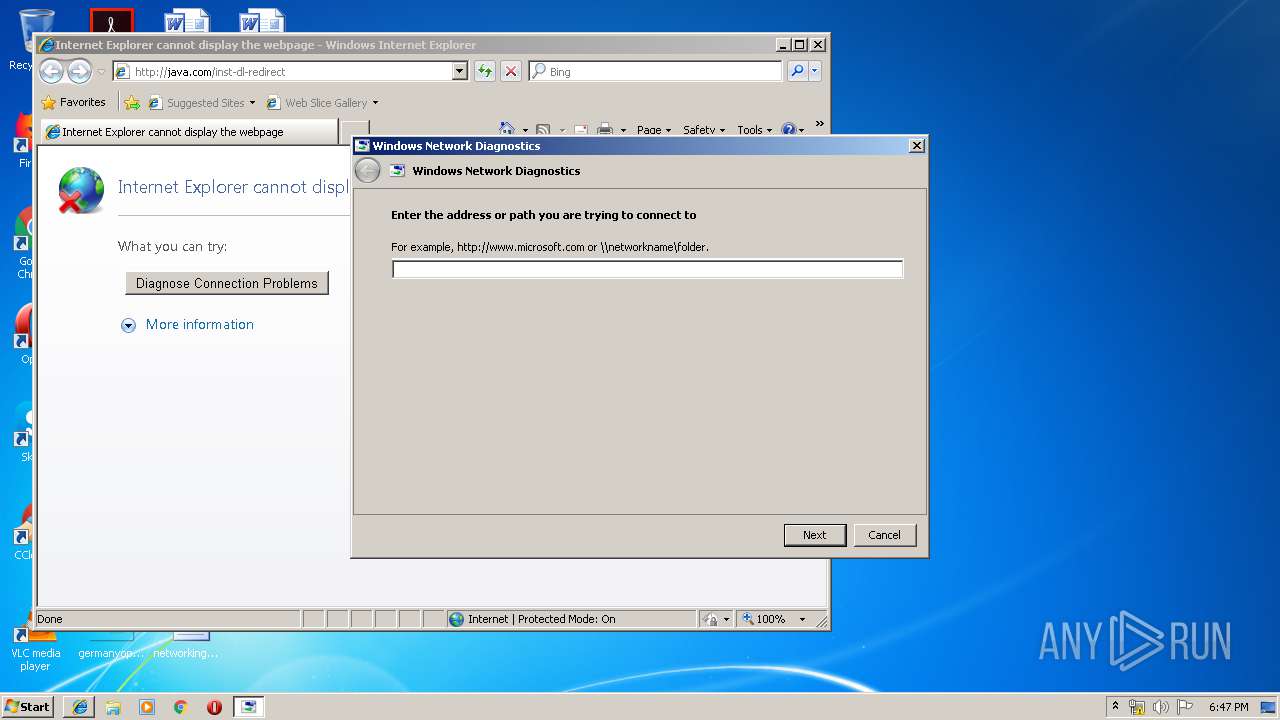
| 2456 | "C:\Windows\System32\msdt.exe" -skip TRUE -path C:\Windows\diagnostics\system\networking -ep NetworkDiagnosticsPNI | C:\Windows\System32\msdt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2520 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES7083.tmp" "c:\Users\admin\AppData\Local\Temp\CSC7082.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2524 | -modal 262474 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF2BC8.tmp -ep NetworkDiagnosticsWeb | C:\Windows\system32\msdt.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\a0kucn6z.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
Total events
614
Read events
491
Write events
117
Delete events
6
Modification events
| (PID) Process: | (1812) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1812) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1572547610847 | |||
| (PID) Process: | (1812) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.roaming.profile |
Value: false | |||
| (PID) Process: | (1812) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.version |
Value: 8 | |||
| (PID) Process: | (1812) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expiration.decision.11.92.2 |
Value: update | |||
| (PID) Process: | (1812) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expired.version |
Value: 11.92.2 | |||
| (PID) Process: | (1812) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.browser.path |
Value: C:\Program Files\Internet Explorer\iexplore.exe | |||
| (PID) Process: | (1812) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expiration.decision.timestamp.11.92.2 |
Value: 1572547610 | |||
| (PID) Process: | (3968) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3968) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1535457890299 | |||
Executable files
4
Suspicious files
11
Text files
72
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JavaDeployReg.log | — | |
MD5:— | SHA256:— | |||
| 3968 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3968 | javaw.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\deployment.properties | text | |
MD5:— | SHA256:— | |||
| 2284 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2284 | javaw.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\deployment.properties | text | |
MD5:— | SHA256:— | |||
| 1812 | javaw.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\deployment.properties | text | |
MD5:— | SHA256:— | |||
| 2284 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JavaDeployReg.log | text | |
MD5:— | SHA256:— | |||
| 1812 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JavaDeployReg.log | text | |
MD5:— | SHA256:— | |||
| 1812 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
12
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3252 | iexplore.exe | GET | — | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | — | — | whitelisted |
1000 | svchost.exe | GET | 200 | 23.210.249.93:80 | http://www.microsoft.com/ | NL | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3252 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
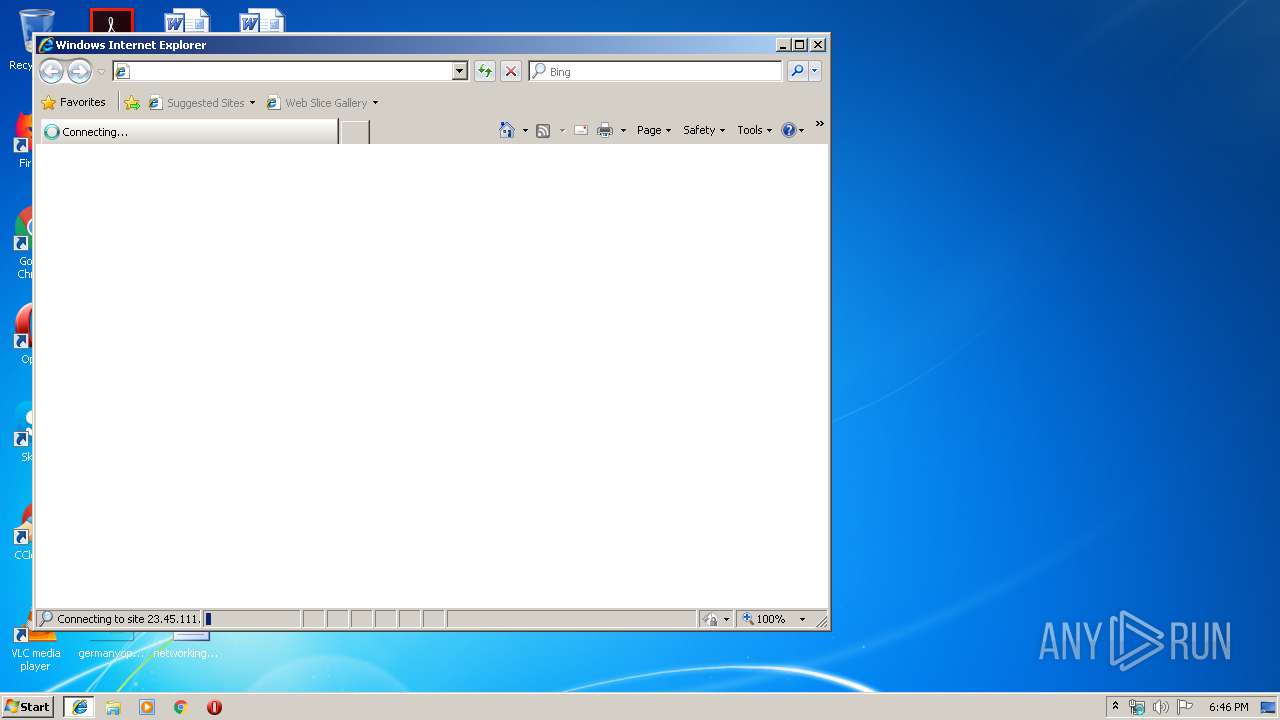
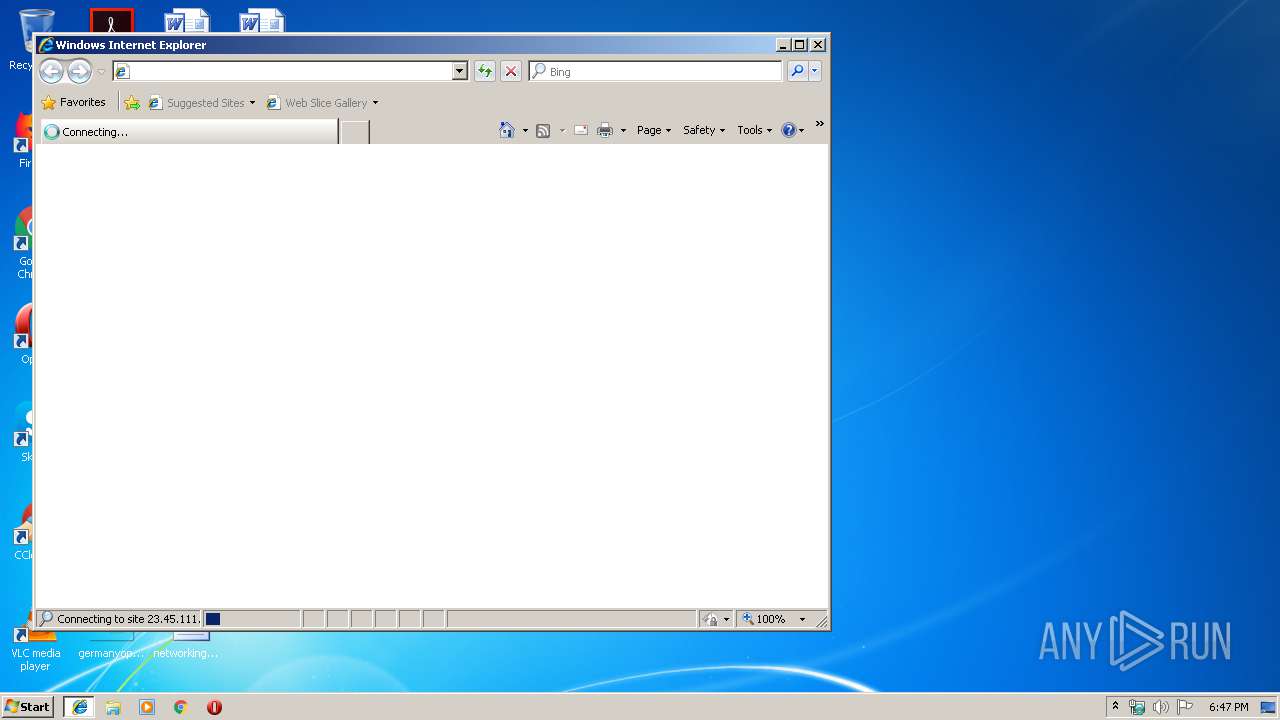
408 | iexplore.exe | 23.45.111.85:80 | java.com | Akamai International B.V. | NL | malicious |
3252 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1000 | svchost.exe | 23.45.111.85:80 | java.com | Akamai International B.V. | NL | malicious |
1000 | svchost.exe | 23.45.111.85:443 | java.com | Akamai International B.V. | NL | malicious |
408 | iexplore.exe | 23.45.111.85:443 | java.com | Akamai International B.V. | NL | malicious |
1000 | svchost.exe | 23.210.249.93:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
java.com |
| whitelisted |
www.java.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|