| File name: | اختراق.bat |
| Full analysis: | https://app.any.run/tasks/d8512a78-66f3-4d48-b007-70b666593d25 |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 15:01:47 |
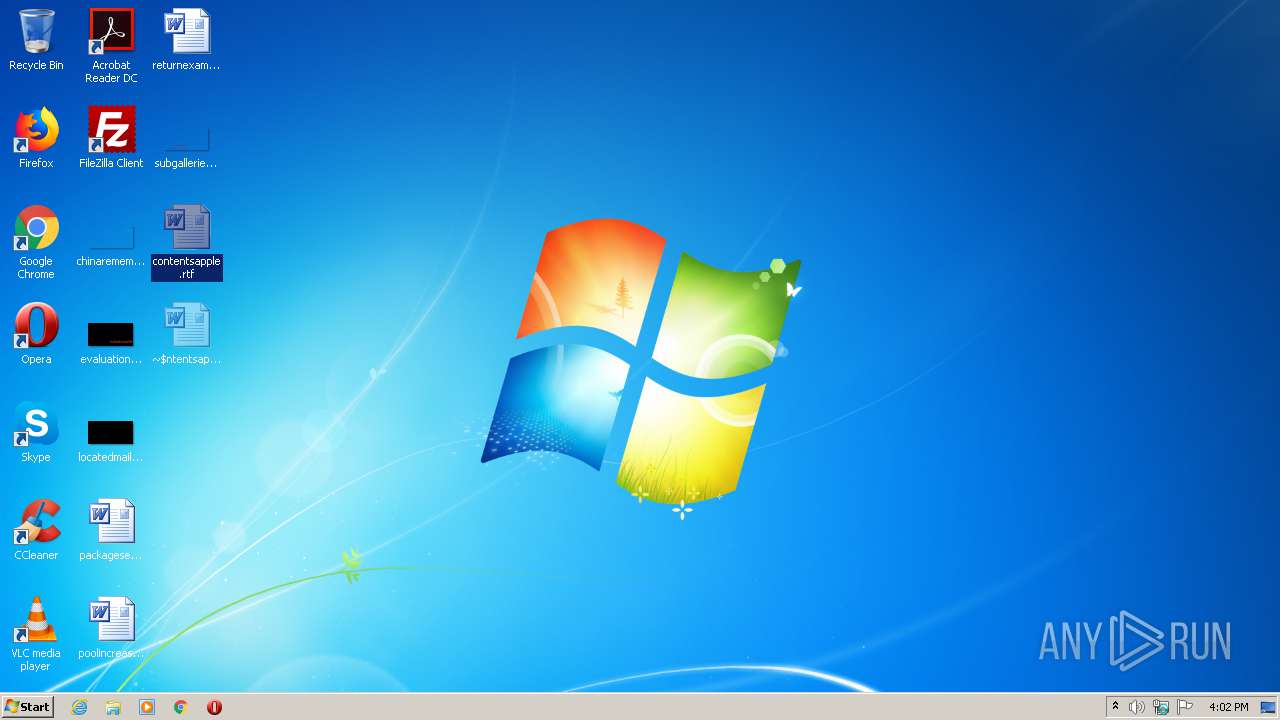
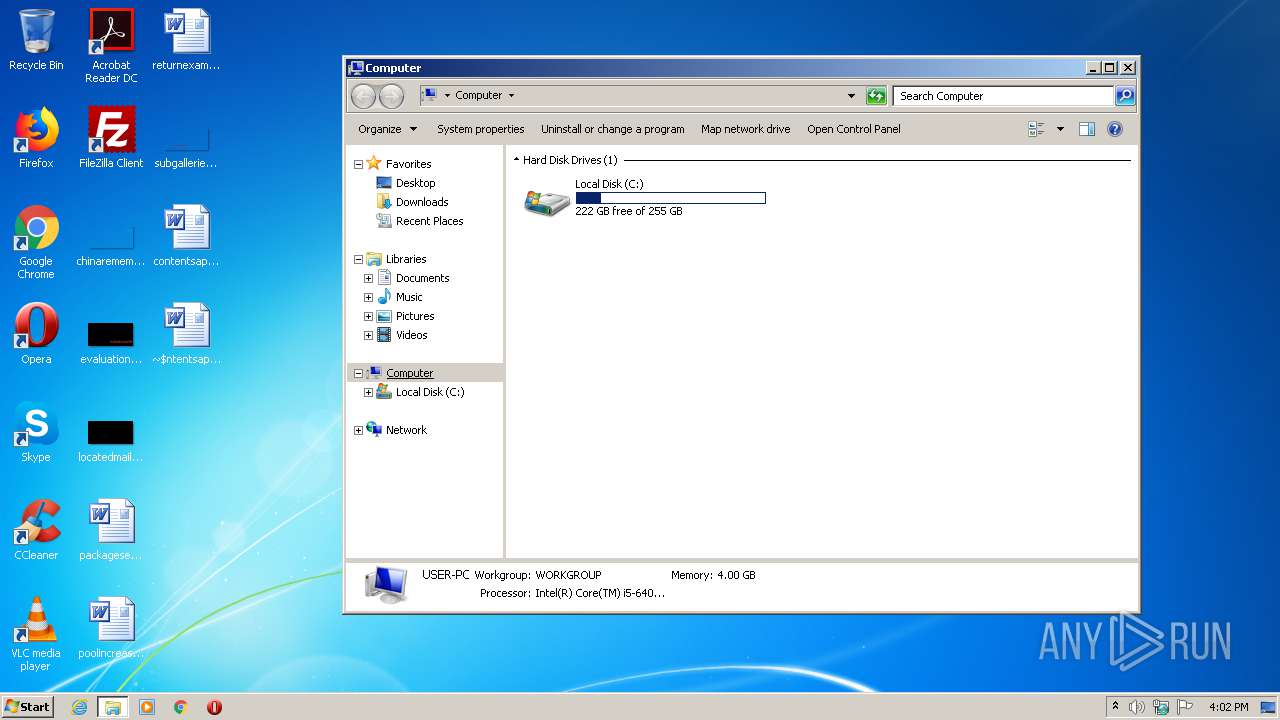
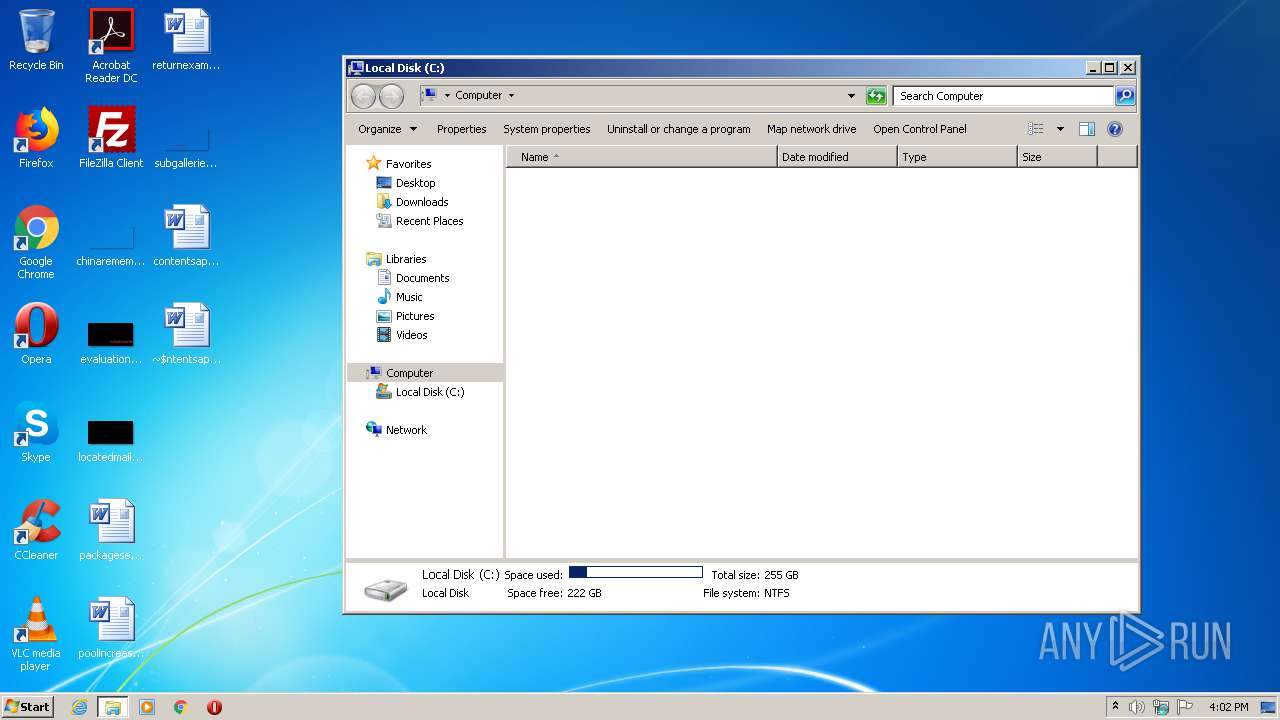
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | BB19C7CF94436DFFF52AE63D944AC7C0 |
| SHA1: | F71AFF9F8DEC1D9FBB90BC5A2F099F9888198DDB |
| SHA256: | 4375005BFC42ED7F7EA35854254C48610BE81112A5FC680A6B4CAF8DED9C007A |
| SSDEEP: | 3:wq3vK0F4o4vK0Fa1Yo4vK0FWo4vK0F8KxmYo4vK0FonoxSvn:fvK0uK0bK0gK07pK08vn |
MALICIOUS
No malicious indicators.SUSPICIOUS
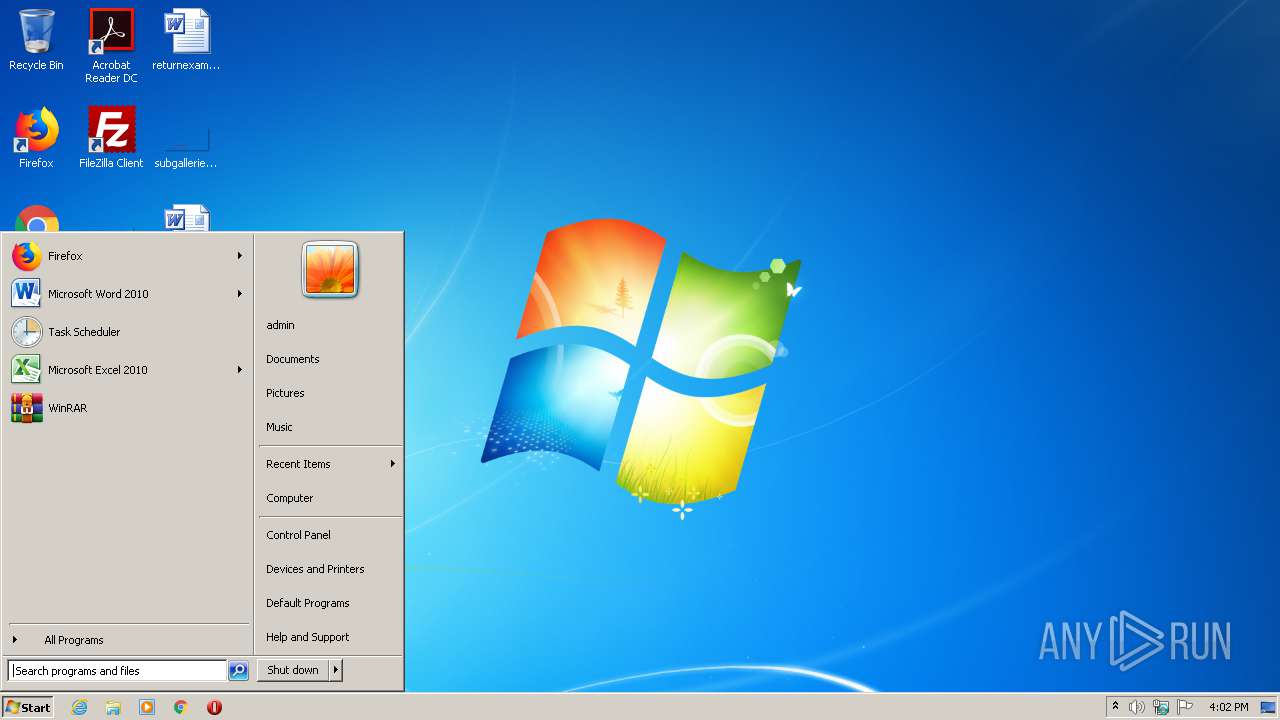
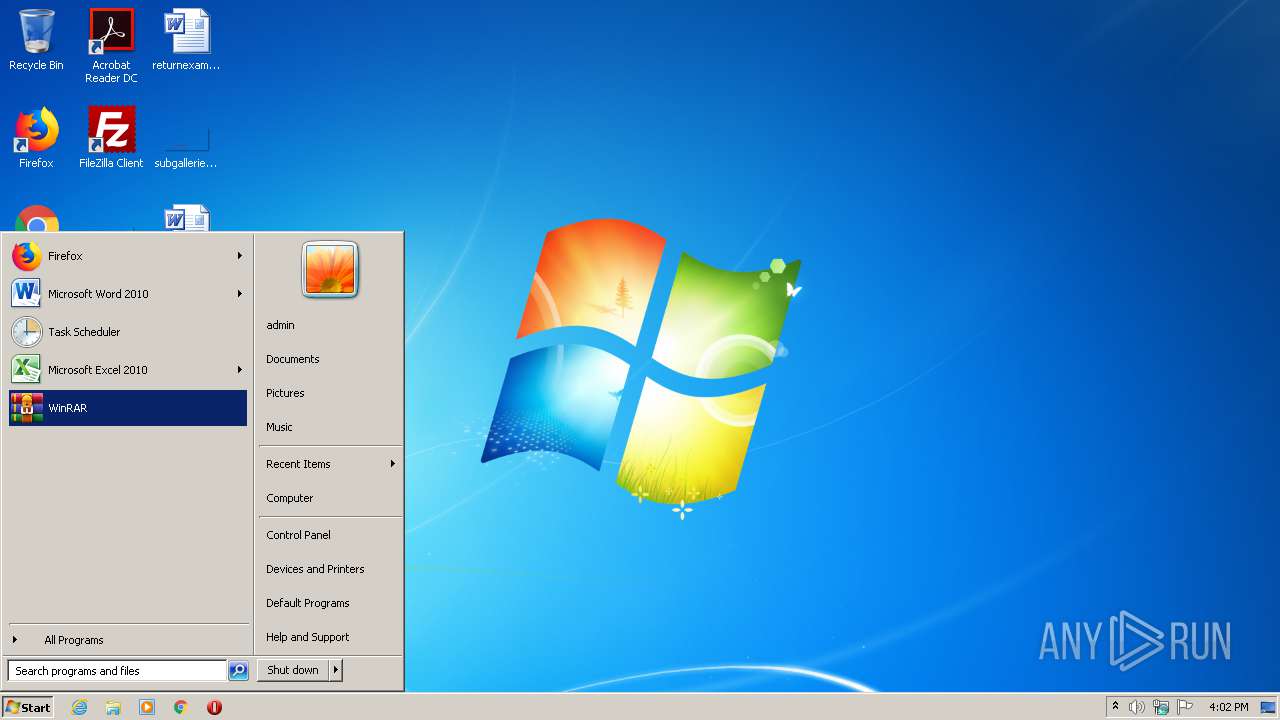
Starts application with an unusual extension
- cmd.exe (PID: 2976)
INFO
Manual execution by user
- WINWORD.EXE (PID: 3704)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3704)
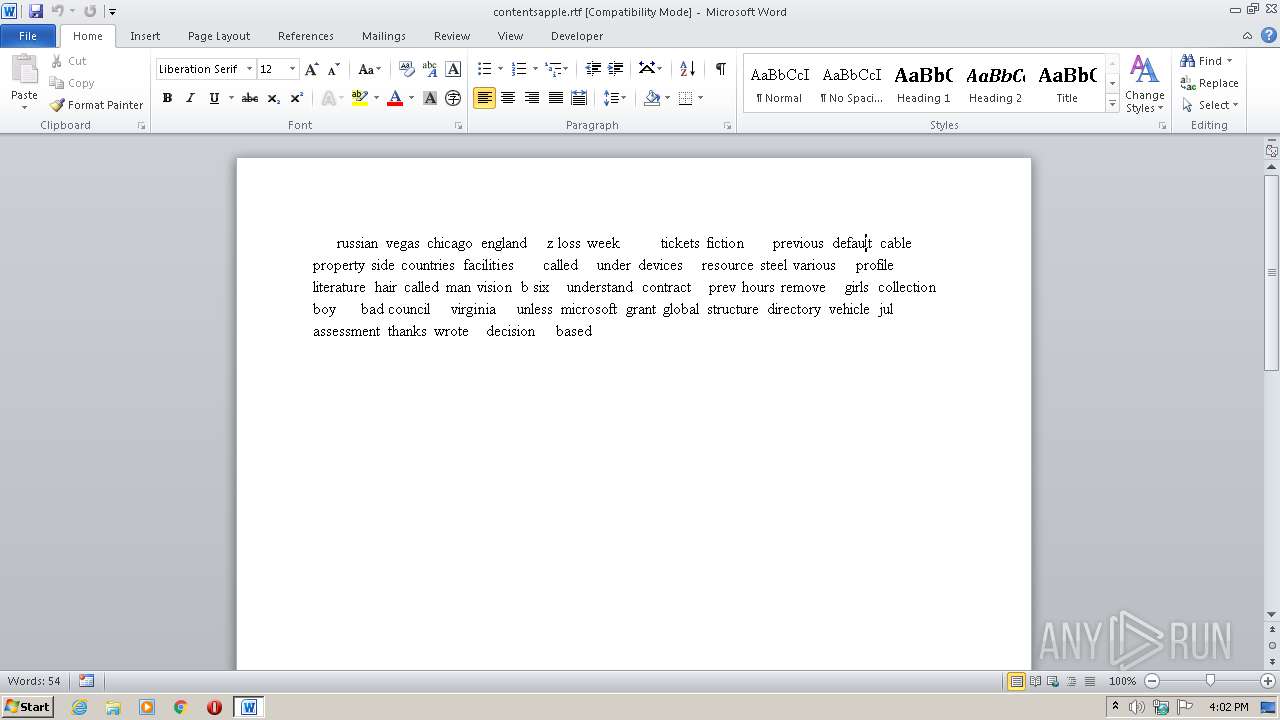
Creates files in the user directory
- WINWORD.EXE (PID: 3704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
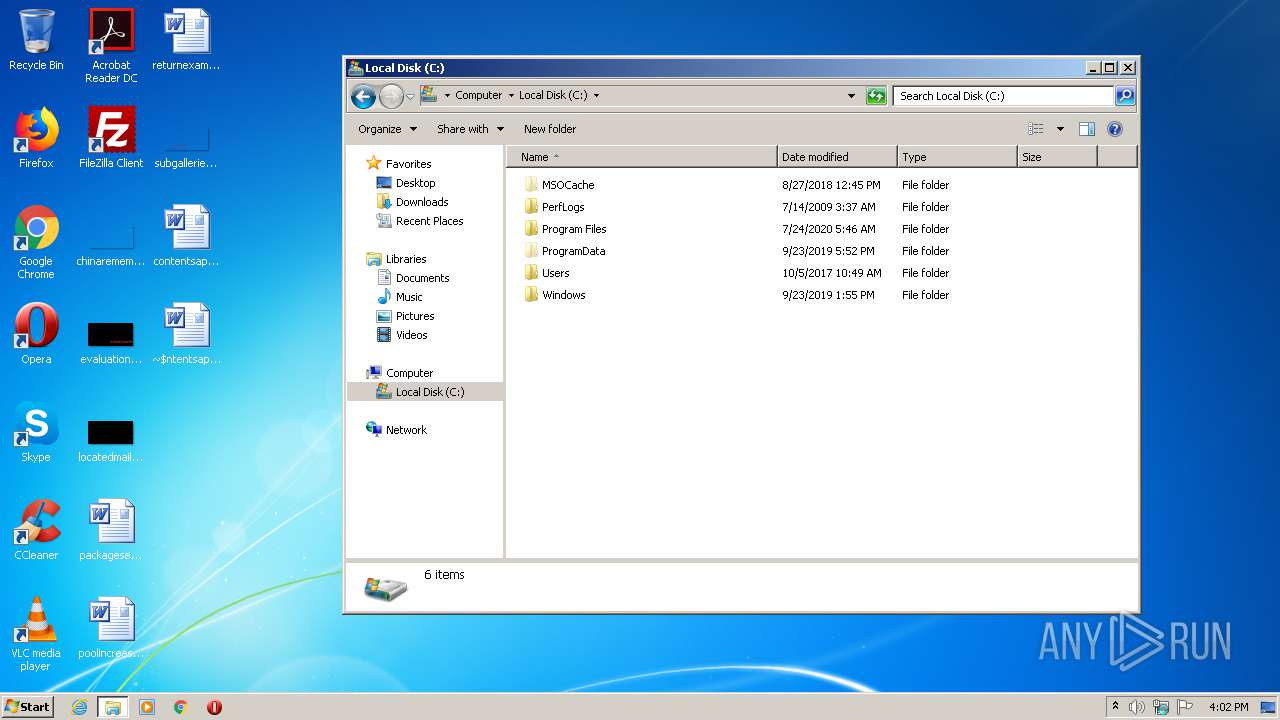
| 884 | FORMAT /Q E:/Y | C:\Windows\system32\format.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Disk Format Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1808 | FORMAT /Q D:/Y | C:\Windows\system32\format.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Disk Format Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | FORMAT /Q C:/Y | C:\Windows\system32\format.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Disk Format Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | cmd /c ""C:\Users\admin\AppData\Local\Temp\اختراق.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2984 | FORMAT /Q F:/Y | C:\Windows\system32\format.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Disk Format Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3704 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\contentsapple.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3892 | FORMAT /Q G:/Y | C:\Windows\system32\format.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Disk Format Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 088
Read events
785
Write events
162
Delete events
141
Modification events
| (PID) Process: | (3704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | q7< |
Value: 71373C00780E0000010000000000000000000000 | |||
| (PID) Process: | (3704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3704) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1BC1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{16F35A7E-0AFD-43A5-81E6-F11AB7144103}.tmp | — | |
MD5:— | SHA256:— | |||
| 3704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{7DD36DB8-CF0D-4CA5-A5E4-963F231DE5DC}.tmp | — | |
MD5:— | SHA256:— | |||
| 3704 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{D8A07801-6F78-4186-8AB2-50C09B7D9A3A}.tmp | — | |
MD5:— | SHA256:— | |||
| 3704 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3704 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\contentsapple.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3704 | WINWORD.EXE | C:\Users\admin\Desktop\~$ntentsapple.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3704 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report