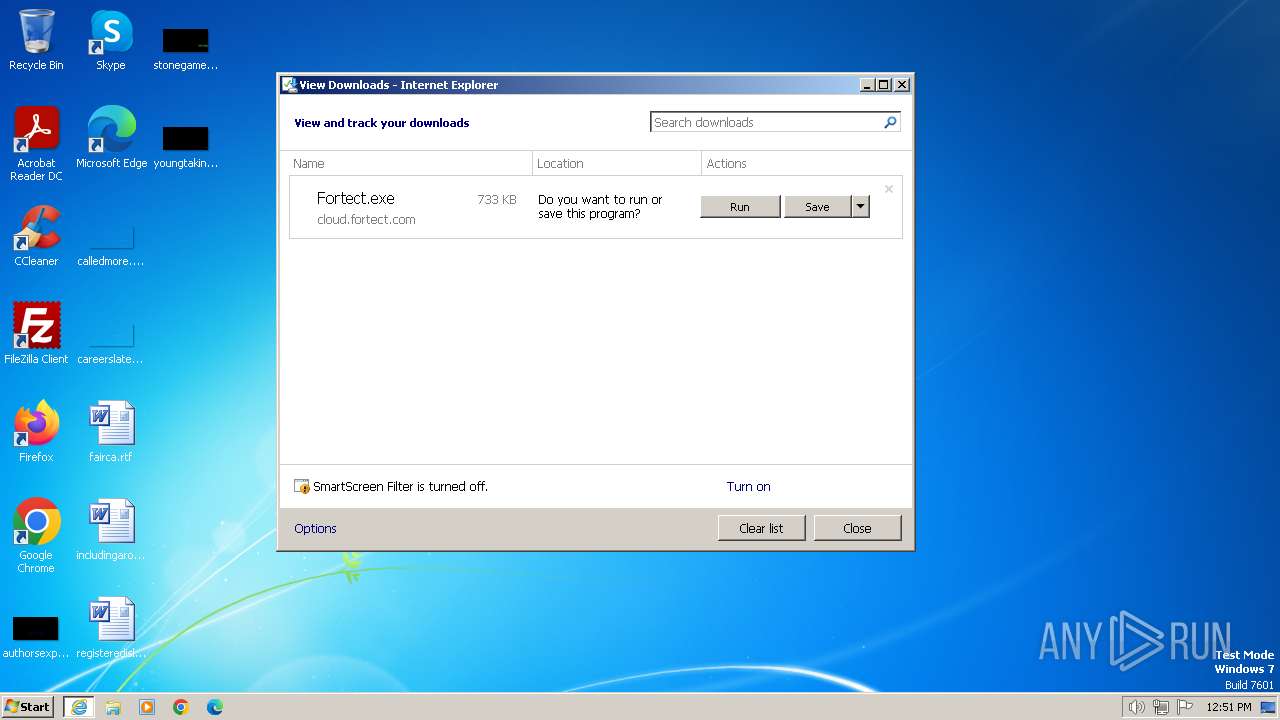
| URL: | https://cloud.fortect.com/app/installation/downloader/6200/Fortect.exe |
| Full analysis: | https://app.any.run/tasks/f982a6a7-cfe2-4aec-bf5b-4eb0ddce3976 |
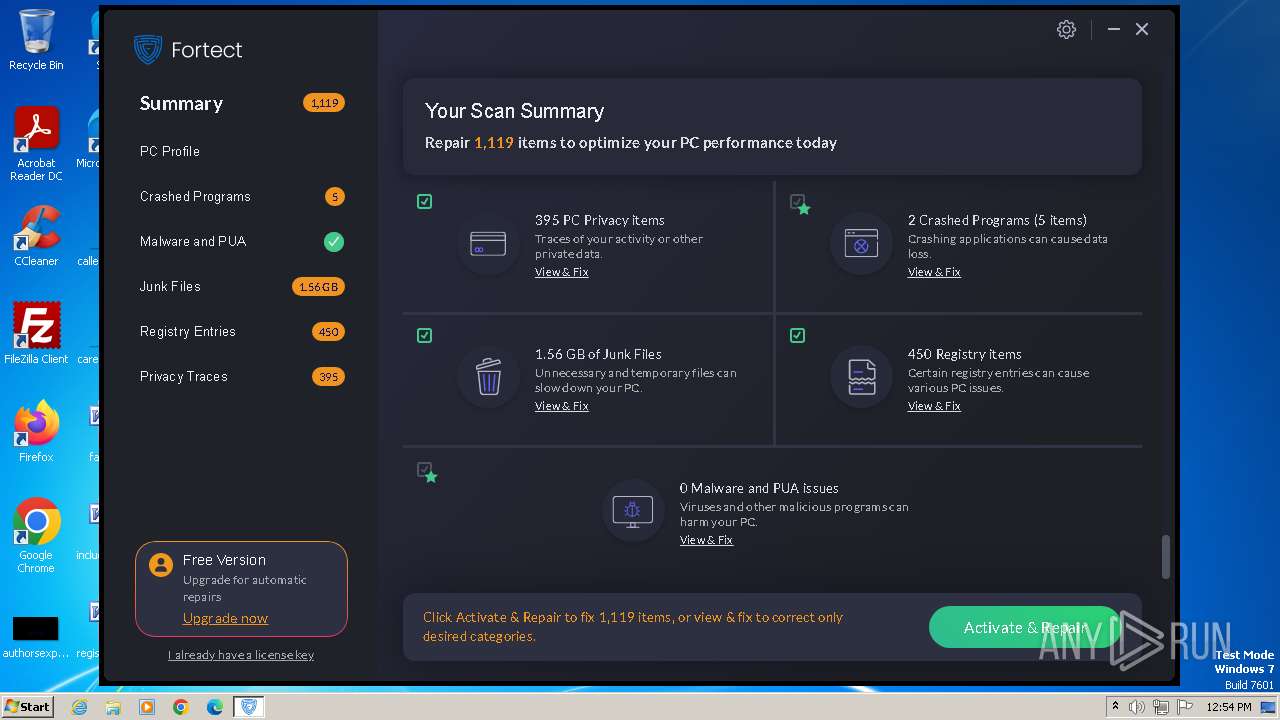
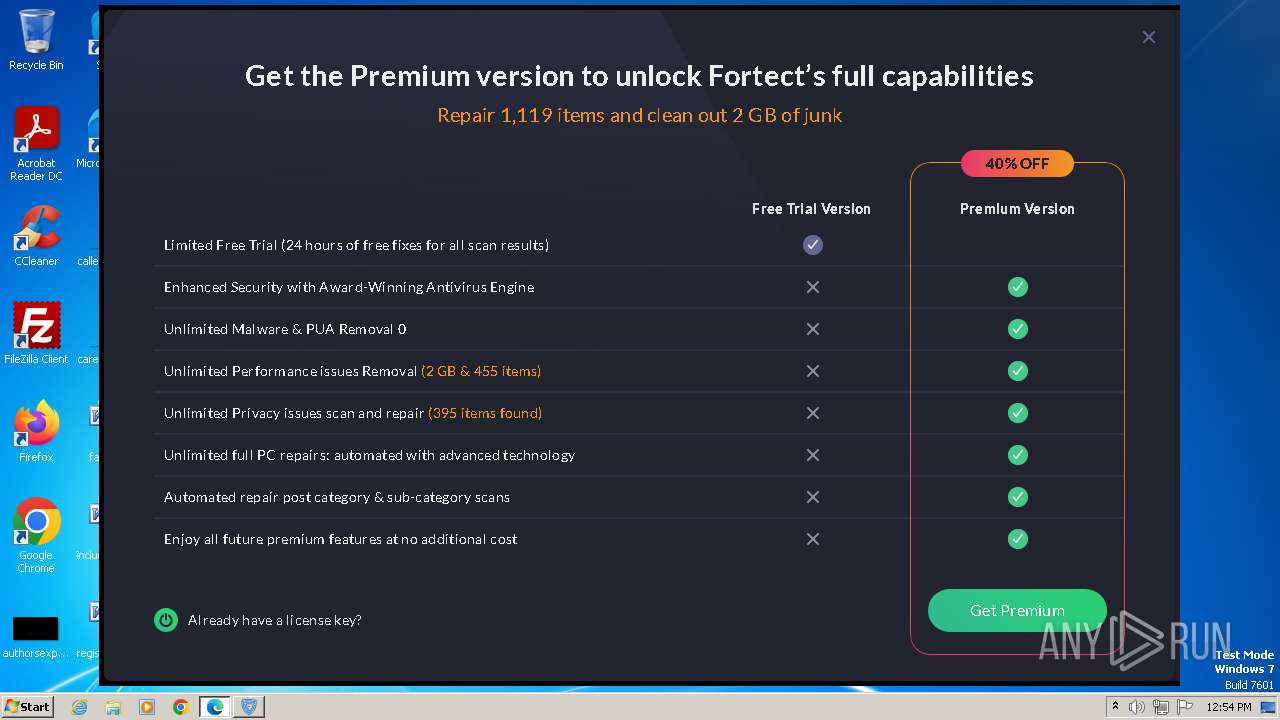
| Verdict: | Malicious activity |
| Analysis date: | April 07, 2024, 11:51:38 |
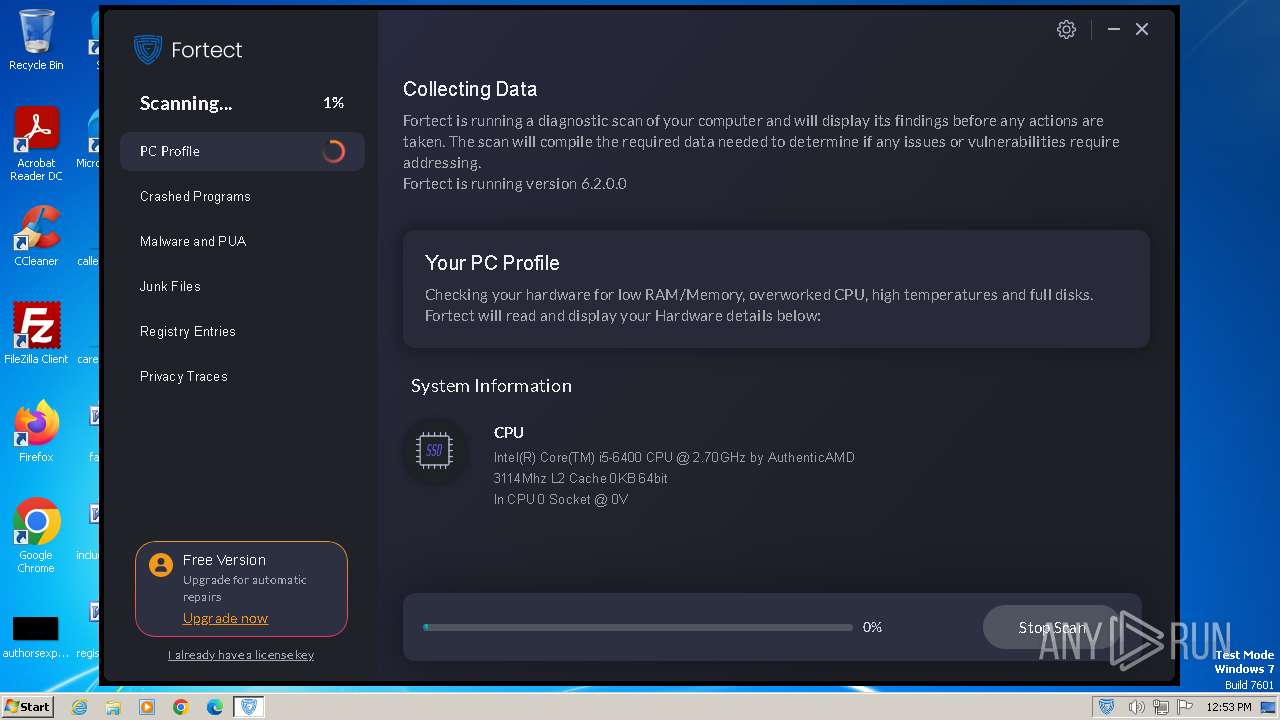
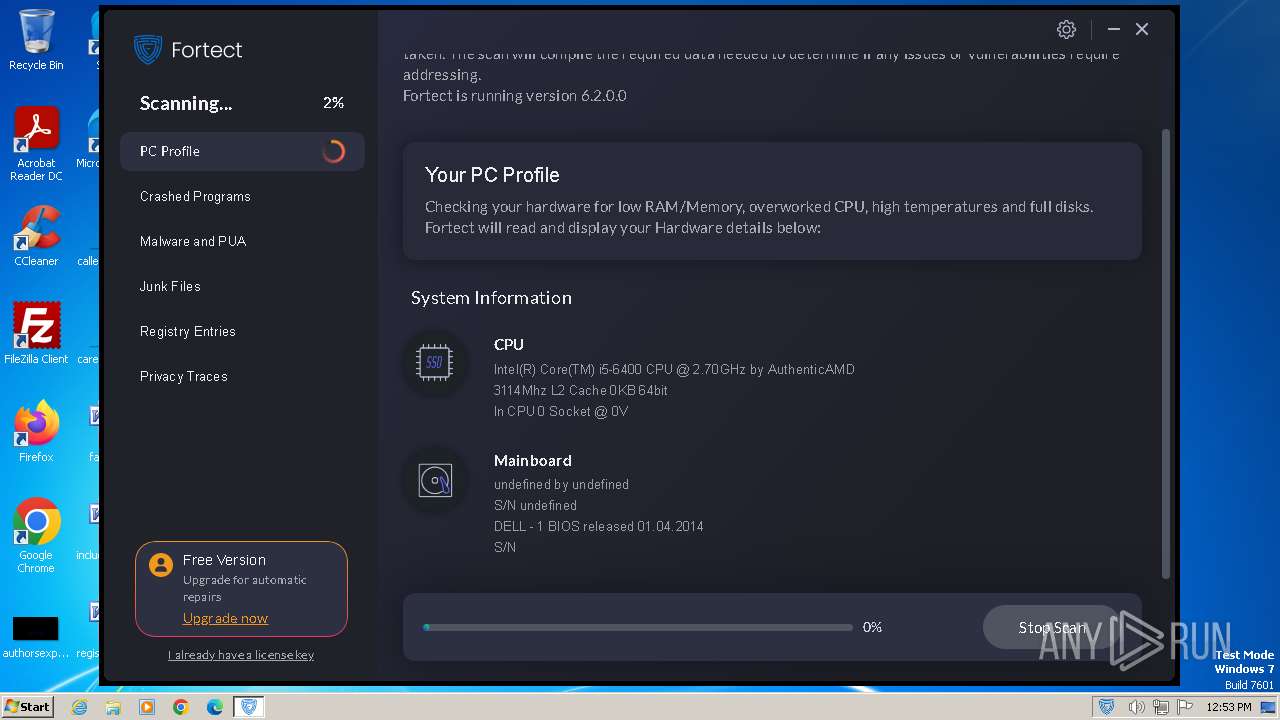
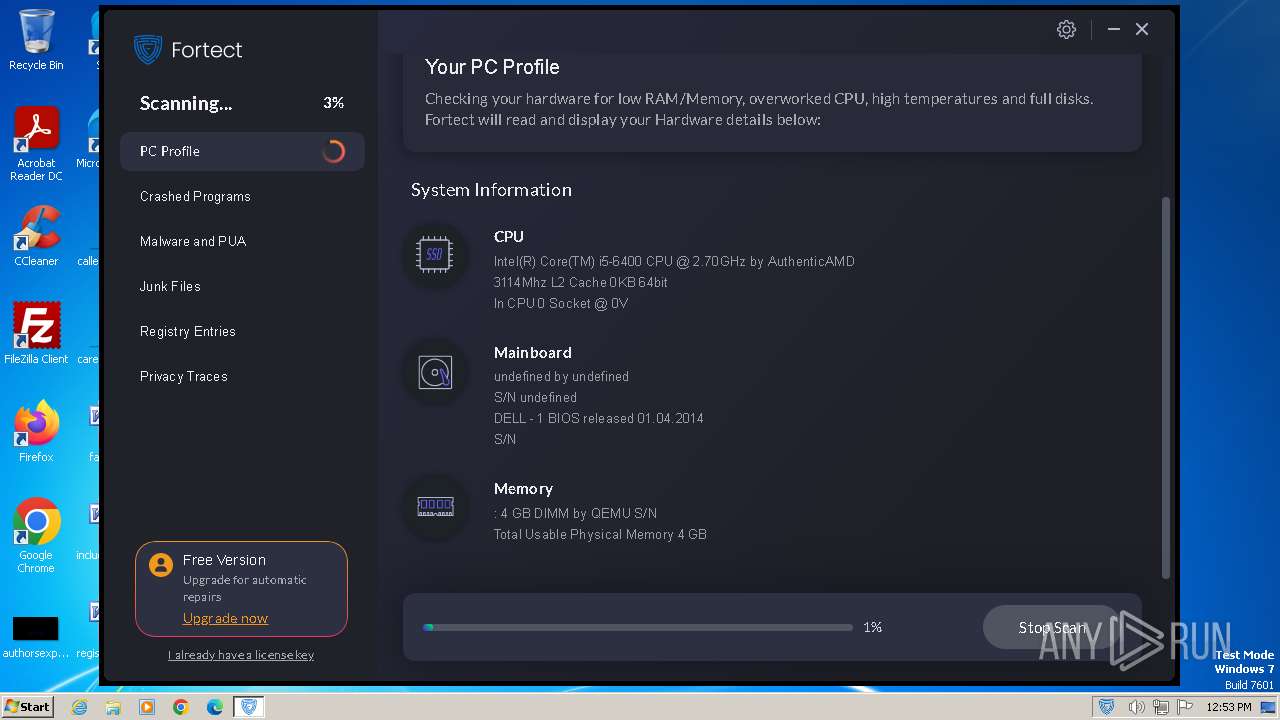
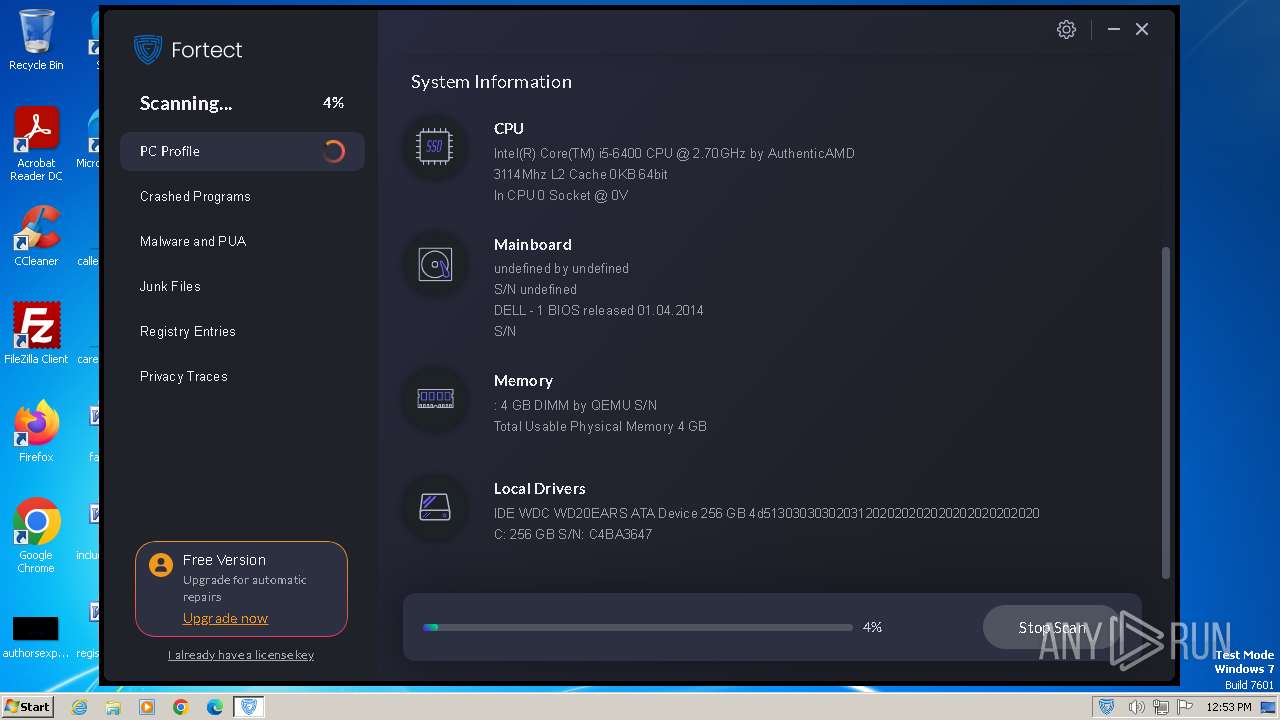
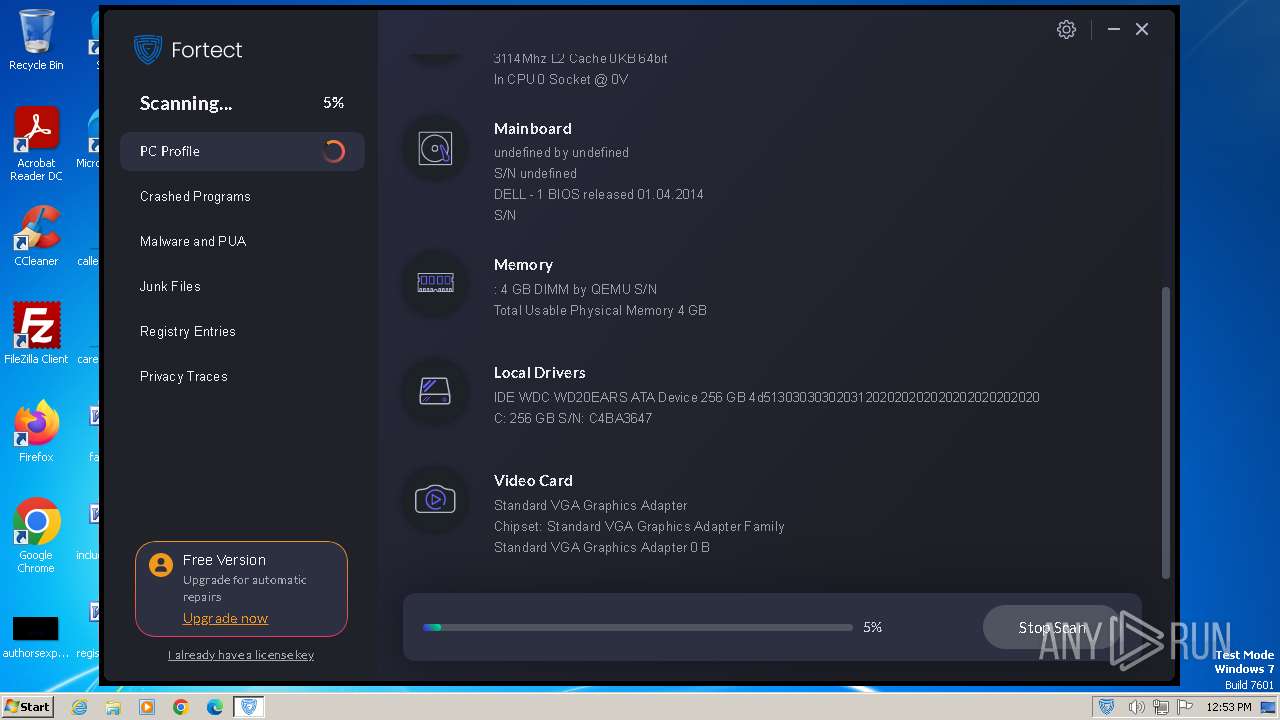
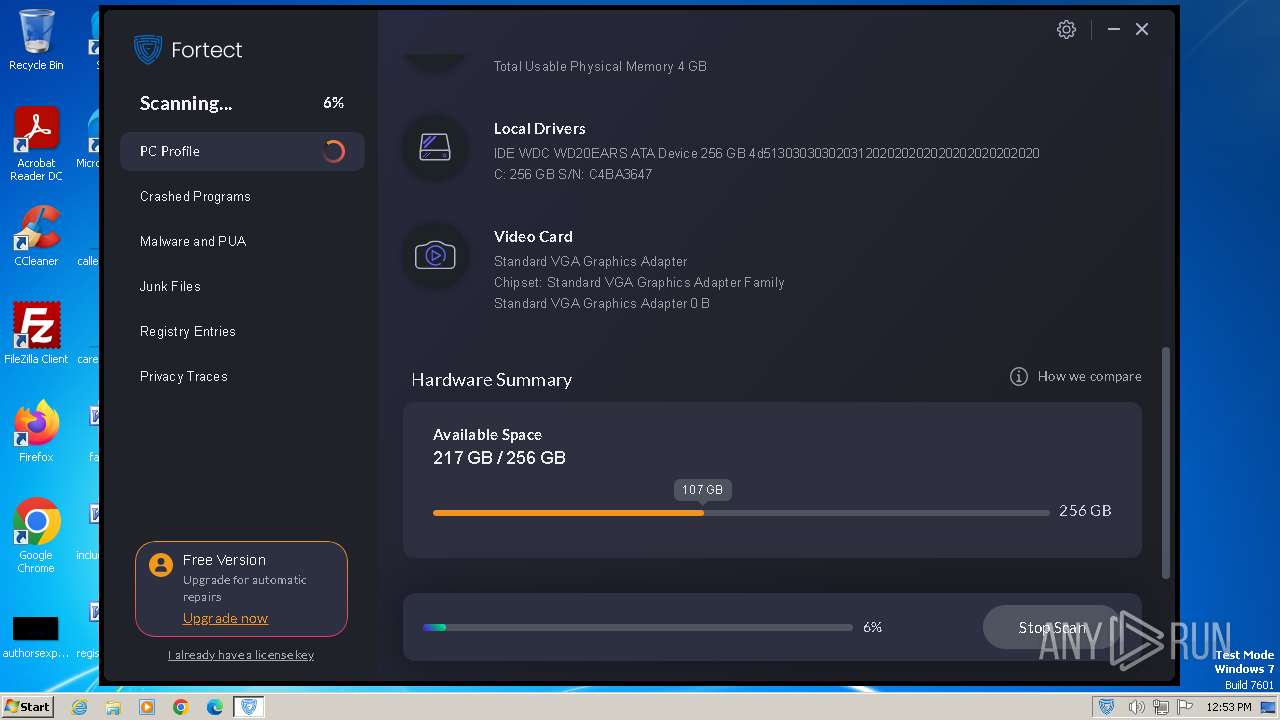
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D490ACD20DB48A99ED61402CF1F6F317 |
| SHA1: | 5BD0800E32A8EFD4E43415AB06770355AD40AD31 |
| SHA256: | 433E5948553092579A70DB9BFF042F69DCDC06E397C8C61B75E01542C27D0294 |
| SSDEEP: | 3:N8ULBLQX5EJKRL+yXqP2GOA:2UBKRLY2k |
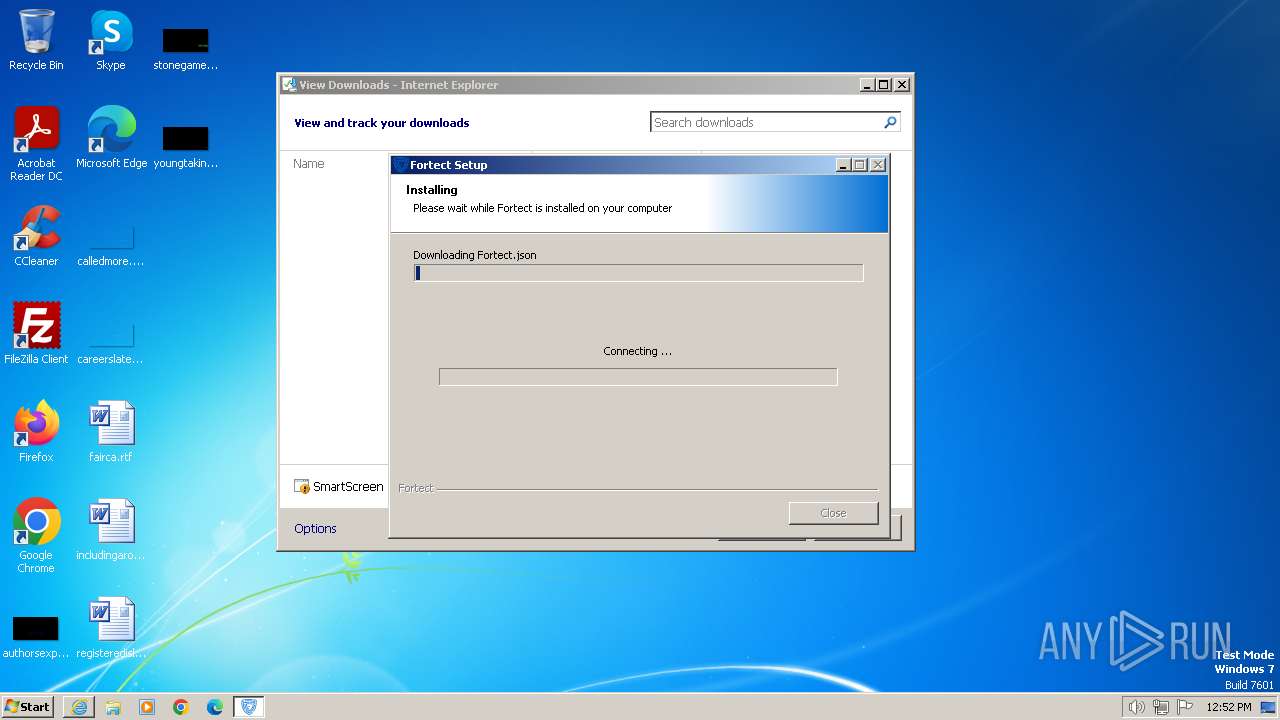
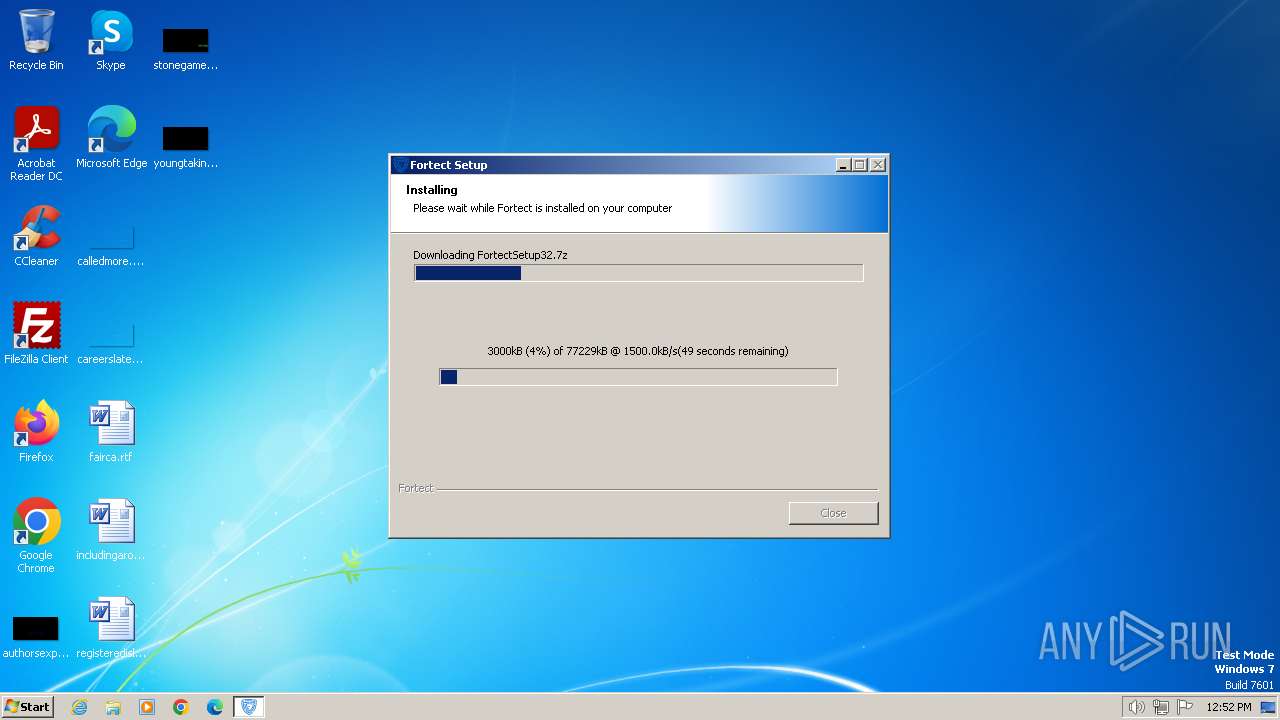
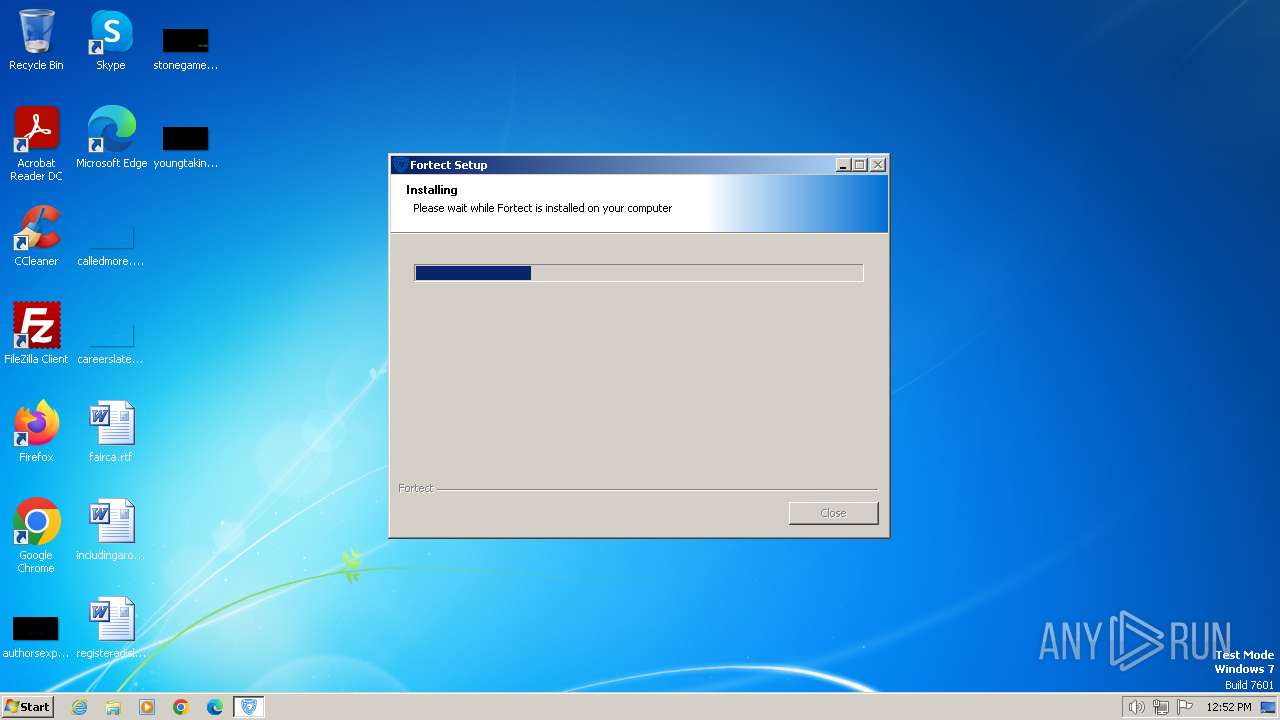
MALICIOUS
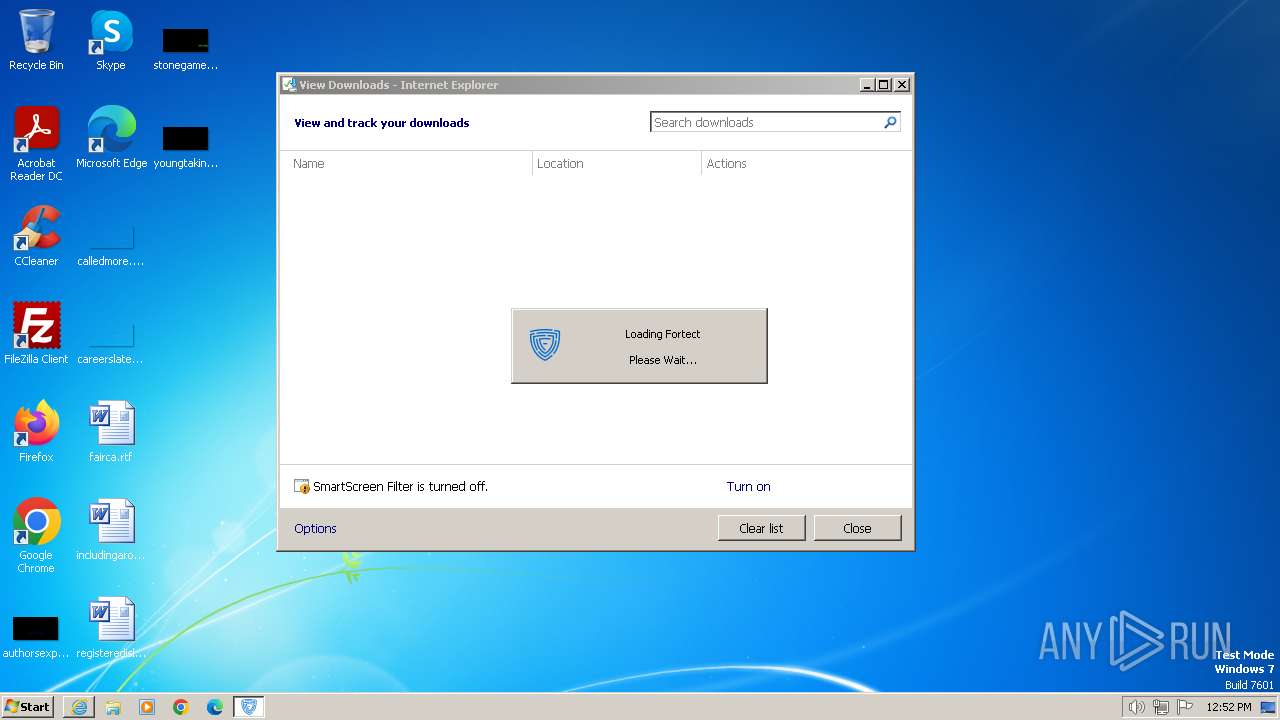
Drops the executable file immediately after the start
- Fortect.exe (PID: 1112)
- FortectMain.exe (PID: 1172)
Changes the autorun value in the registry
- Fortect.exe (PID: 1112)
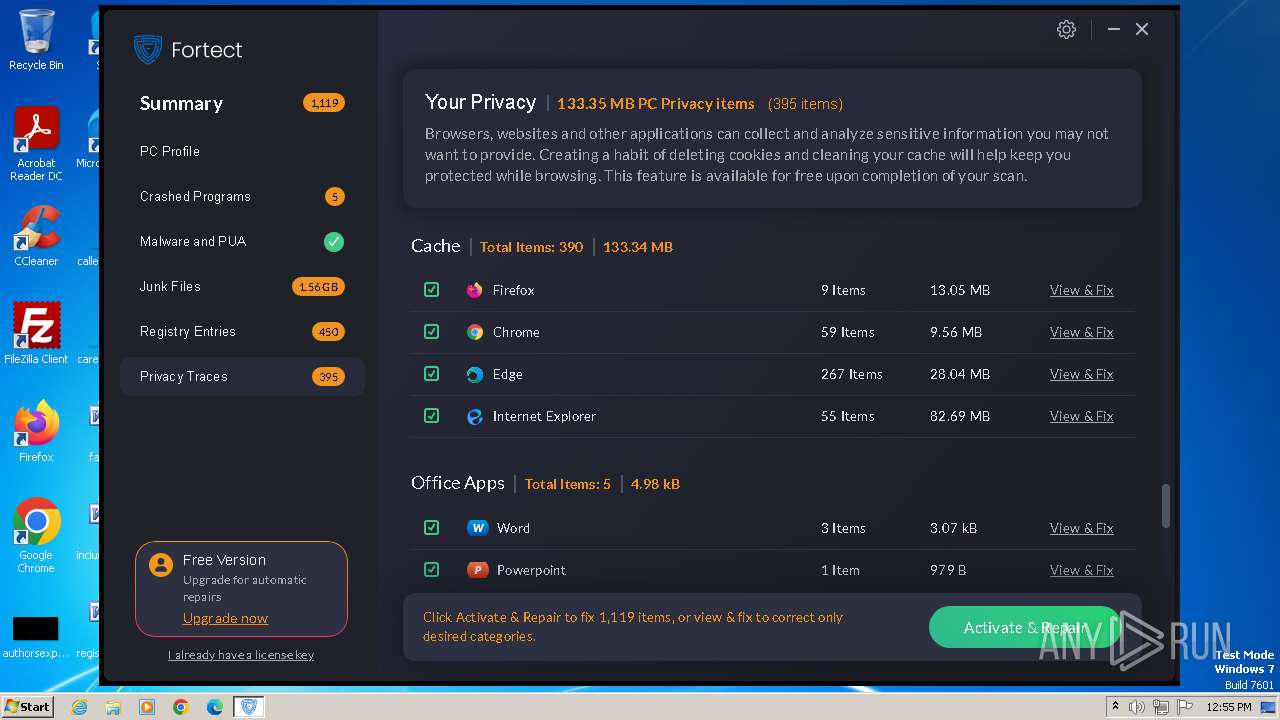
Actions looks like stealing of personal data
- MainService.exe (PID: 3128)
SUSPICIOUS
The process creates files with name similar to system file names
- Fortect.exe (PID: 1112)
Reads the Internet Settings
- Fortect.exe (PID: 1112)
- FortectMain.exe (PID: 1172)
- FortectMain.exe (PID: 2784)
Reads security settings of Internet Explorer
- Fortect.exe (PID: 1112)
- MainDaemon.exe (PID: 1484)
Checks Windows Trust Settings
- Fortect.exe (PID: 1112)
- MainDaemon.exe (PID: 1484)
- MainDaemon.exe (PID: 924)
- MainService.exe (PID: 3128)
Drops 7-zip archiver for unpacking
- Fortect.exe (PID: 1112)
Reads settings of System Certificates
- Fortect.exe (PID: 1112)
- MainDaemon.exe (PID: 1484)
- FortectMain.exe (PID: 1172)
Executes as Windows Service
- MainDaemon.exe (PID: 924)
- MainService.exe (PID: 3128)
Process drops legitimate windows executable
- Fortect.exe (PID: 1112)
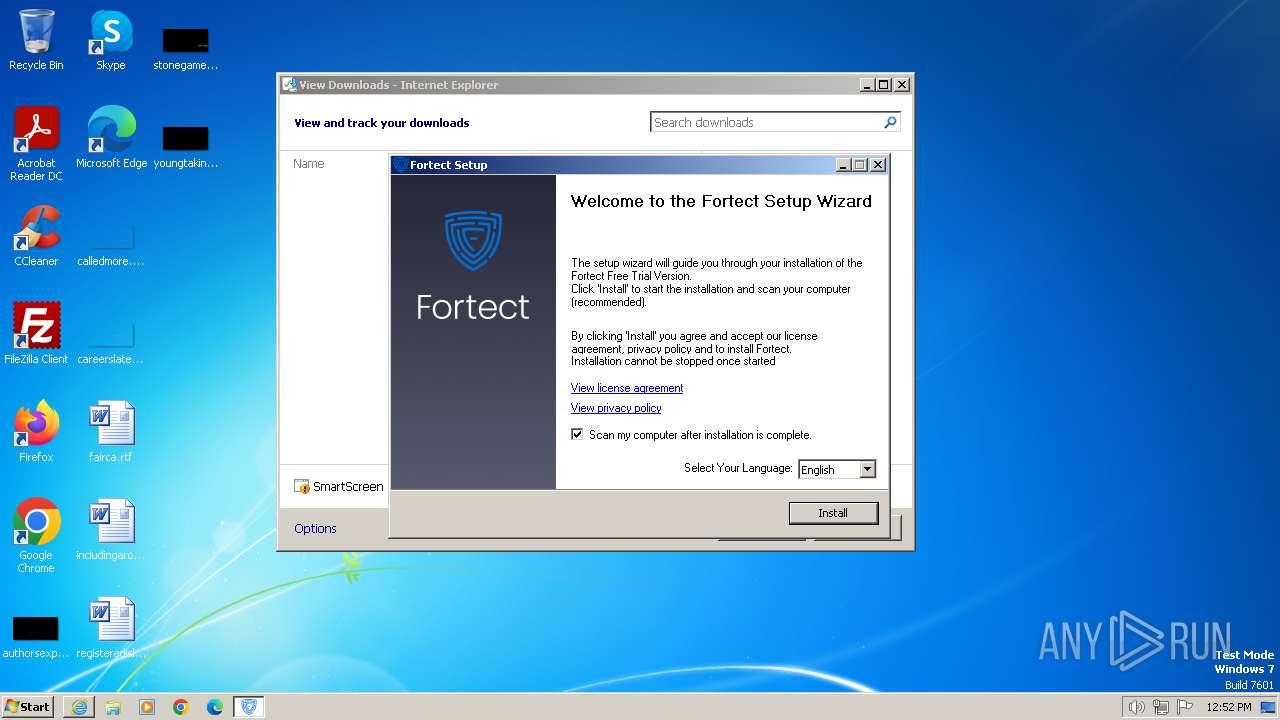
Creates a software uninstall entry
- Fortect.exe (PID: 1112)
Searches for installed software
- MainDaemon.exe (PID: 924)
- MainService.exe (PID: 3128)
Application launched itself
- FortectMain.exe (PID: 1172)
Reads Internet Explorer settings
- MainService.exe (PID: 3128)
Read startup parameters
- MainService.exe (PID: 3128)
Reads Microsoft Outlook installation path
- MainService.exe (PID: 3128)
Reads the date of Windows installation
- MainService.exe (PID: 3128)
Adds/modifies Windows certificates
- MainService.exe (PID: 3128)
INFO
Application launched itself
- iexplore.exe (PID: 2120)
- msedge.exe (PID: 3912)
Drops the executable file immediately after the start
- iexplore.exe (PID: 3092)
- iexplore.exe (PID: 2120)
Reads the computer name
- Fortect.exe (PID: 1112)
- MainDaemon.exe (PID: 1484)
- MainDaemon.exe (PID: 924)
- MainService.exe (PID: 948)
- MainService.exe (PID: 3128)
- FortectMain.exe (PID: 3332)
- FortectMain.exe (PID: 3020)
- FortectMain.exe (PID: 1172)
- FortectMain.exe (PID: 3480)
- FortectMain.exe (PID: 2784)
Checks supported languages
- Fortect.exe (PID: 1112)
- MainDaemon.exe (PID: 924)
- MainDaemon.exe (PID: 1484)
- MainService.exe (PID: 948)
- MainService.exe (PID: 3128)
- FortectMain.exe (PID: 1172)
- FortectMain.exe (PID: 3332)
- FortectMain.exe (PID: 3020)
- fortecttray.exe (PID: 4072)
- FortectMain.exe (PID: 3480)
- FortectMain.exe (PID: 2784)
Reads Environment values
- Fortect.exe (PID: 1112)
- MainDaemon.exe (PID: 1484)
- MainService.exe (PID: 948)
- MainService.exe (PID: 3128)
- MainDaemon.exe (PID: 924)
- FortectMain.exe (PID: 1172)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2120)
The process uses the downloaded file
- iexplore.exe (PID: 2120)
- Fortect.exe (PID: 1112)
Reads the machine GUID from the registry
- Fortect.exe (PID: 1112)
- MainDaemon.exe (PID: 1484)
- MainDaemon.exe (PID: 924)
- MainService.exe (PID: 3128)
- FortectMain.exe (PID: 1172)
Create files in a temporary directory
- Fortect.exe (PID: 1112)
- FortectMain.exe (PID: 1172)
Checks proxy server information
- Fortect.exe (PID: 1112)
Creates files or folders in the user directory
- Fortect.exe (PID: 1112)
- FortectMain.exe (PID: 1172)
- FortectMain.exe (PID: 3020)
Reads the software policy settings
- Fortect.exe (PID: 1112)
- MainDaemon.exe (PID: 1484)
- MainDaemon.exe (PID: 924)
- MainService.exe (PID: 3128)
- FortectMain.exe (PID: 1172)
Creates files in the program directory
- Fortect.exe (PID: 1112)
- MainDaemon.exe (PID: 1484)
- MainService.exe (PID: 948)
- MainDaemon.exe (PID: 924)
- MainService.exe (PID: 3128)
Dropped object may contain TOR URL's
- Fortect.exe (PID: 1112)
Reads product name
- FortectMain.exe (PID: 1172)
Manual execution by a user
- FortectMain.exe (PID: 1172)
Process checks computer location settings
- FortectMain.exe (PID: 1172)
- FortectMain.exe (PID: 2784)
- MainService.exe (PID: 3128)
Process checks the number of cached credentials
- MainService.exe (PID: 3128)
Reads mouse settings
- MainService.exe (PID: 3128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
29
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1664 --field-trial-handle=1352,i,8821779581273277261,13118486205959858648,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Fortect\bin\MainDaemon.exe" | C:\Program Files\Fortect\bin\MainDaemon.exe | services.exe | ||||||||||||
User: SYSTEM Company: Fortect Ltd. Integrity Level: SYSTEM Description: Fortect Daemon Version: 6.2.0.0 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Fortect\MainService.exe" --install | C:\Program Files\Fortect\MainService.exe | — | Fortect.exe | |||||||||||
User: admin Company: Fortect LTD. Integrity Level: HIGH Description: Fortect Service Exit code: 0 Version: 6.2.0.0 Modules
| |||||||||||||||
| 1112 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Fortect.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Fortect.exe | iexplore.exe | ||||||||||||
User: admin Company: Fortect Integrity Level: HIGH Description: Fortect Setup Exit code: 0 Version: 6.2.0.0 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Fortect\FortectMain.exe" --lang=en --firstRun --runId=33b887c0-6b4d-487d-bb9b-979635ce3afc | C:\Program Files\Fortect\FortectMain.exe | — | explorer.exe | |||||||||||
User: admin Company: Fortect LTD® Integrity Level: MEDIUM Description: Fortect Main Version: 6.2.0.0 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Fortect\bin\MainDaemon.exe" --install | C:\Program Files\Fortect\bin\MainDaemon.exe | Fortect.exe | ||||||||||||
User: admin Company: Fortect Ltd. Integrity Level: HIGH Description: Fortect Daemon Exit code: 0 Version: 6.2.0.0 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1520 --field-trial-handle=1352,i,8821779581273277261,13118486205959858648,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3932 --field-trial-handle=1352,i,8821779581273277261,13118486205959858648,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2376 --field-trial-handle=1352,i,8821779581273277261,13118486205959858648,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1272 --field-trial-handle=1352,i,8821779581273277261,13118486205959858648,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
127 559
Read events
127 247
Write events
261
Delete events
51
Modification events
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31099105 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 146348874 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31099106 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
61
Suspicious files
163
Text files
114
Unknown types
114
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Fortect[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Fortect.exe.ha0kfei.partial | executable | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9E66C44DBB004D39.TMP | binary | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{347A7ABF-F4D5-11EE-AE0A-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Fortect.exe.ha0kfei.partial:Zone.Identifier | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
114
DNS requests
62
Threats
54
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3092 | iexplore.exe | GET | 304 | 2.16.100.168:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b150b552b216e1f4 | unknown | — | — | unknown |
3092 | iexplore.exe | GET | 304 | 2.16.100.168:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d3ebf5ce555ba18b | unknown | — | — | unknown |
3092 | iexplore.exe | GET | 200 | 216.58.206.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | — | — | unknown |
3092 | iexplore.exe | GET | 200 | 216.58.206.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
1112 | Fortect.exe | GET | 304 | 2.16.100.168:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6838fae63b9d0d3c | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 2.16.100.168:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1b8fee253118cbef | unknown | — | — | unknown |
3128 | MainService.exe | GET | 200 | 172.67.75.40:80 | http://app.fortect.com/events/cloud-scan.php?param1=su4W7rMMkzwO7NpxGmPB6H+/cOmB3EGw//ML38Wgt7xwe24SoMKN8gtTIfEk0PCsWFvflk2LD1CbJYE4DRXiq6a3xuoucFvi8VTfmTvzabMZJb9u/Lc5oN4AvOo8EROEXwR5lq7FUDCrfVVOU1CCAi86C8HXbTm6bJ3R+UZzot5luLI2fUAVyK9wyinNkTSet/CPQMn5h8ZrMZug/IycYuPSx7L7b4RLA08FyfFQatfzQiwjw8XI5Bo0DsuflLDW8LR+Q2QxZBgVFNbArtIYUA== | unknown | — | — | unknown |
3128 | MainService.exe | GET | 200 | 172.67.75.40:80 | http://app.fortect.com/events/cloud-scan.php?param1=su4W7rMMkzwO7NpxGmPB6ARg5LehjV8wnJuErb4ivGmCvYhdyTEHObOYXh6xK766fIWmOdd4E9McGiCPeLC7xaLXtoW6J4BmPDVGVb06OPbbQ36AUnv3Ud8GOTeIEe9oO1HQCvosGe4uVgIqQfy+Lrtu/m8x5TwlEIr6dyVaCQlhAfvCuIcxEUshqRsvSu3aOOgQq/K7FowvHIIWQLwXhg+OmVfcYd4eEYdd36IkTqiIWAJgxfMUWU4Krf/bOqRzeERjccCN5bnj9LGPbJ+zNQ== | unknown | — | — | unknown |
3128 | MainService.exe | GET | 200 | 172.67.75.40:80 | http://app.fortect.com/events/cloud-scan.php?param1=su4W7rMMkzwO7NpxGmPB6FRtAyZ0imDfuTWfROu7ZC0ySnKnzHEsnIcUY5uQtJKy/uoI7bE/lsEvRwFR9VaqNoR8K8NMS+No18vOfUGceUyw8HF9VIwibbE3XW46PmDzIAVzF+qdVT/9Fs+9V7hpmV+4zMkB299f/xQw/MCUA2WACSF5ZZZsiBui23IcrYyISVZdbriS6mk+xnfHEmbv44m8Zuywymu9QJFma6pR5Jdchc0UERpu6hRtA5NmhtqzY2m73z1sb0vdtBbaJom43g== | unknown | — | — | unknown |
3128 | MainService.exe | GET | 200 | 172.67.75.40:80 | http://app.fortect.com/events/cloud-scan.php?param1=su4W7rMMkzwO7NpxGmPB6ADuTU29OXWF8zJmb2N7QXqJ3SbFrXvmzmEMbZwdjgVDRmnp8oVysv4TqnpFkbRkFHVPVaA8964EvrUtAl/r5mVxBTmiVpTFkDhB18g2S7LdHQeH9Z1CiiCUHMVYuTvnJlQLPBEFTJ+bOiAa2xOJtlq3vigr0FmcWkUUmL1GAIN9PQDDOUs6R9SE+3dKNOpfY9RJSu1m/u6iFA68Mnh9+860Ay3JZFJKoougMtvnwILkeFNARlM4a4sPzKXg3Jd3CGHEsB0X66yJSPfQgfvasJUR3MS9VUXVlXTpH1COz8FX | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3092 | iexplore.exe | 172.67.75.40:443 | cloud.fortect.com | CLOUDFLARENET | US | unknown |
3092 | iexplore.exe | 2.16.100.168:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
3092 | iexplore.exe | 216.58.206.35:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1112 | Fortect.exe | 172.67.75.40:443 | cloud.fortect.com | CLOUDFLARENET | US | unknown |
1112 | Fortect.exe | 2.16.100.168:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
1080 | svchost.exe | 2.16.100.168:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cloud.fortect.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
app.fortect.com |
| unknown |
service.fortect.com |
| unknown |
redirector.gvt1.com |
| whitelisted |
r1---sn-5hneknek.gvt1.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
secure.fortect.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
3092 | iexplore.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
3092 | iexplore.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
1112 | Fortect.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1112 | Fortect.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
1484 | MainDaemon.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1484 | MainDaemon.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1484 | MainDaemon.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
Process | Message |
|---|---|
Fortect.exe | ExecShellAsUser: got desktop |
Fortect.exe | ExecShellAsUser: elevated process detected |
Fortect.exe | ExecShellAsUser: thread finished |
Fortect.exe | ExecShellAsUser: DLL_PROCESS_DETACH |