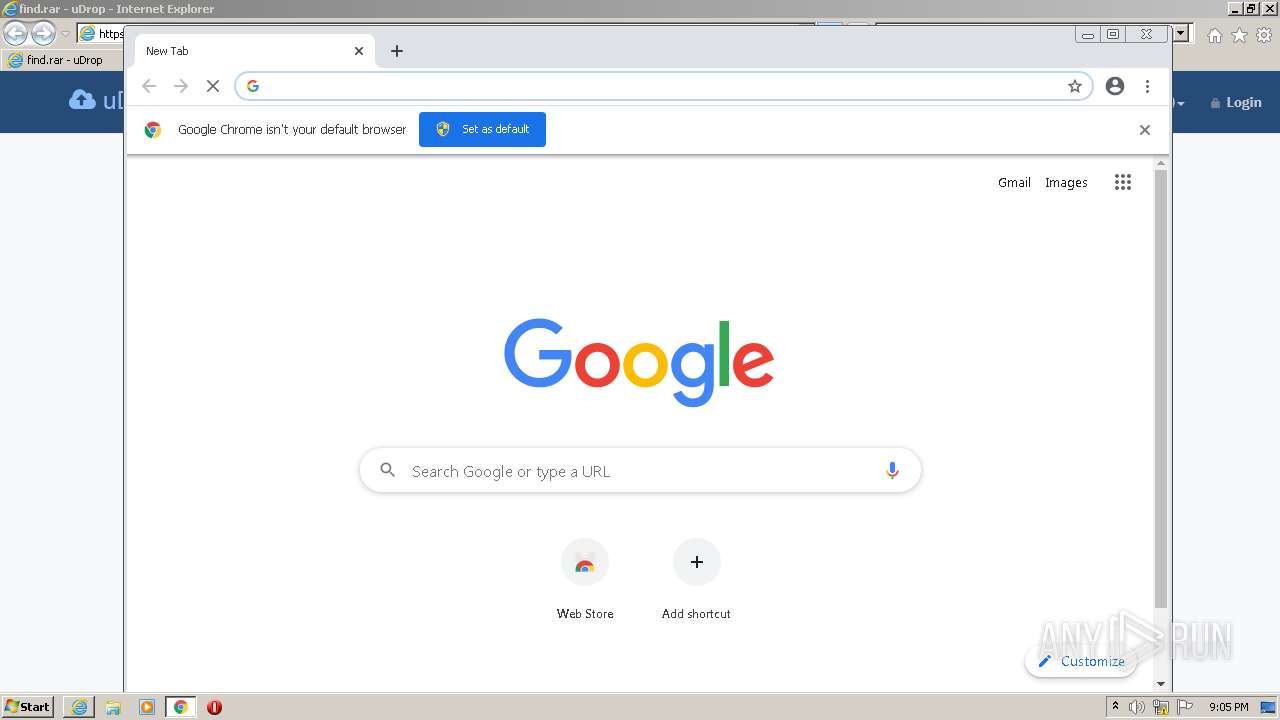
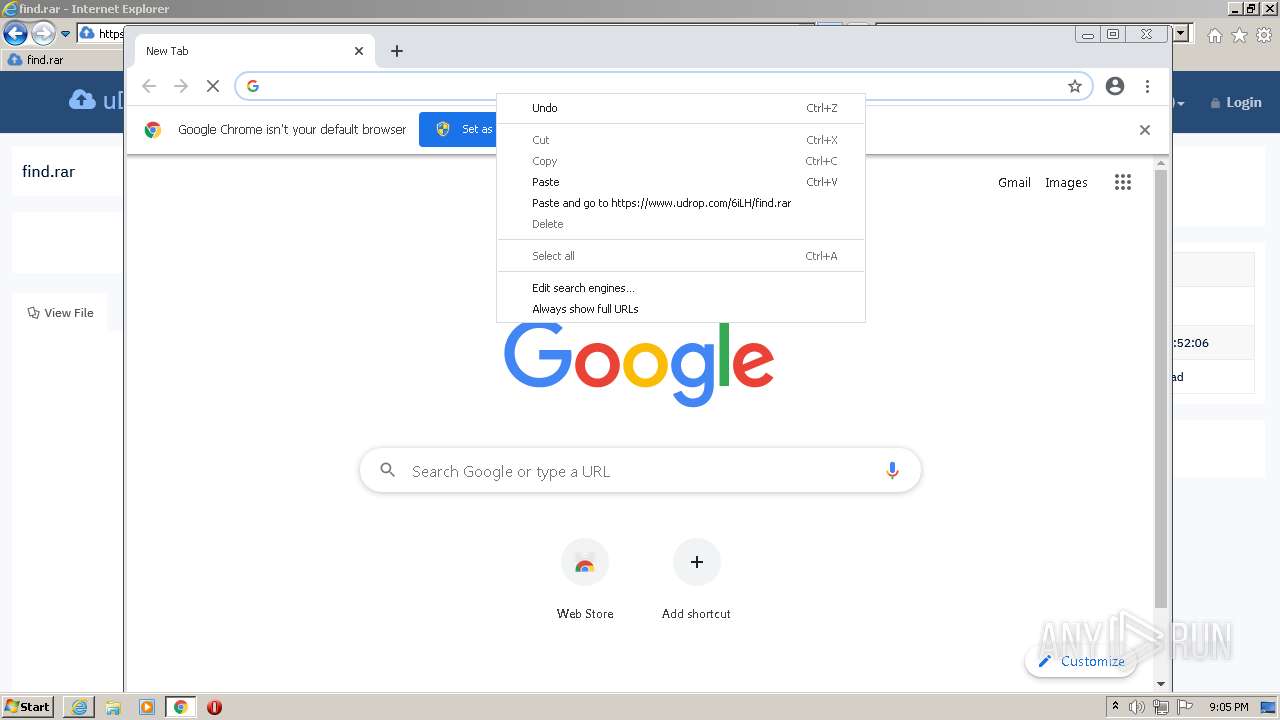
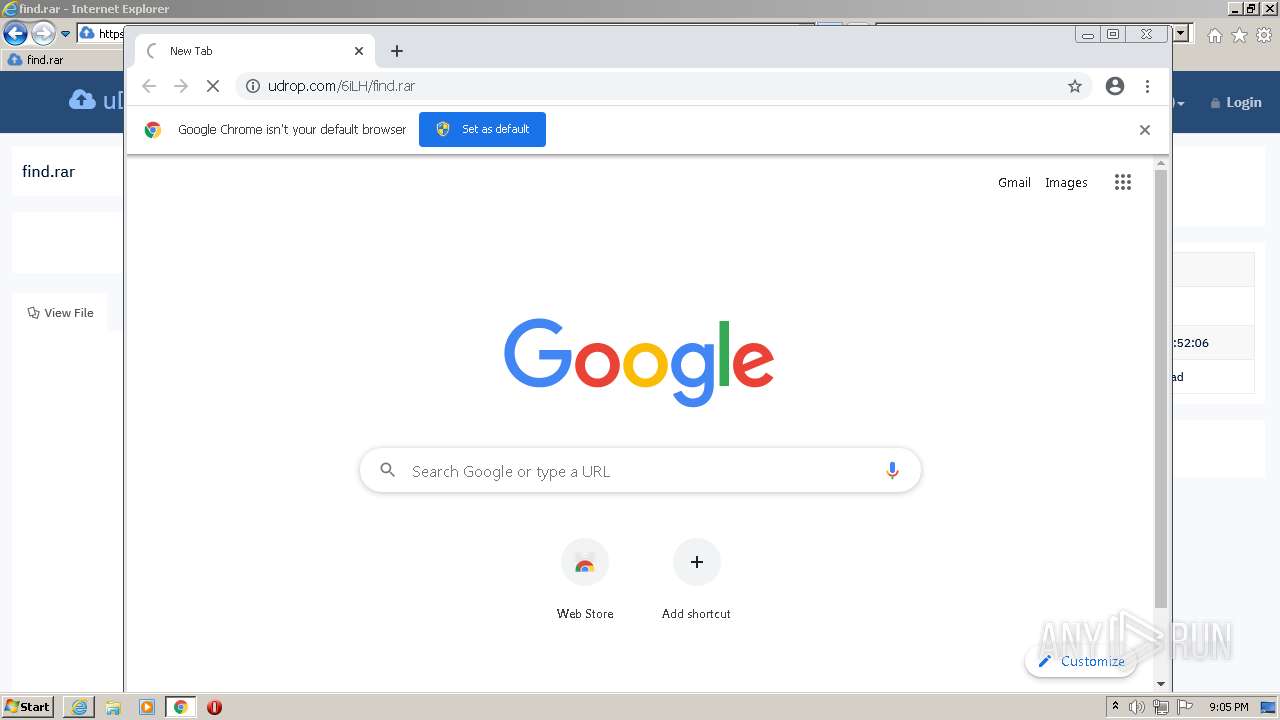
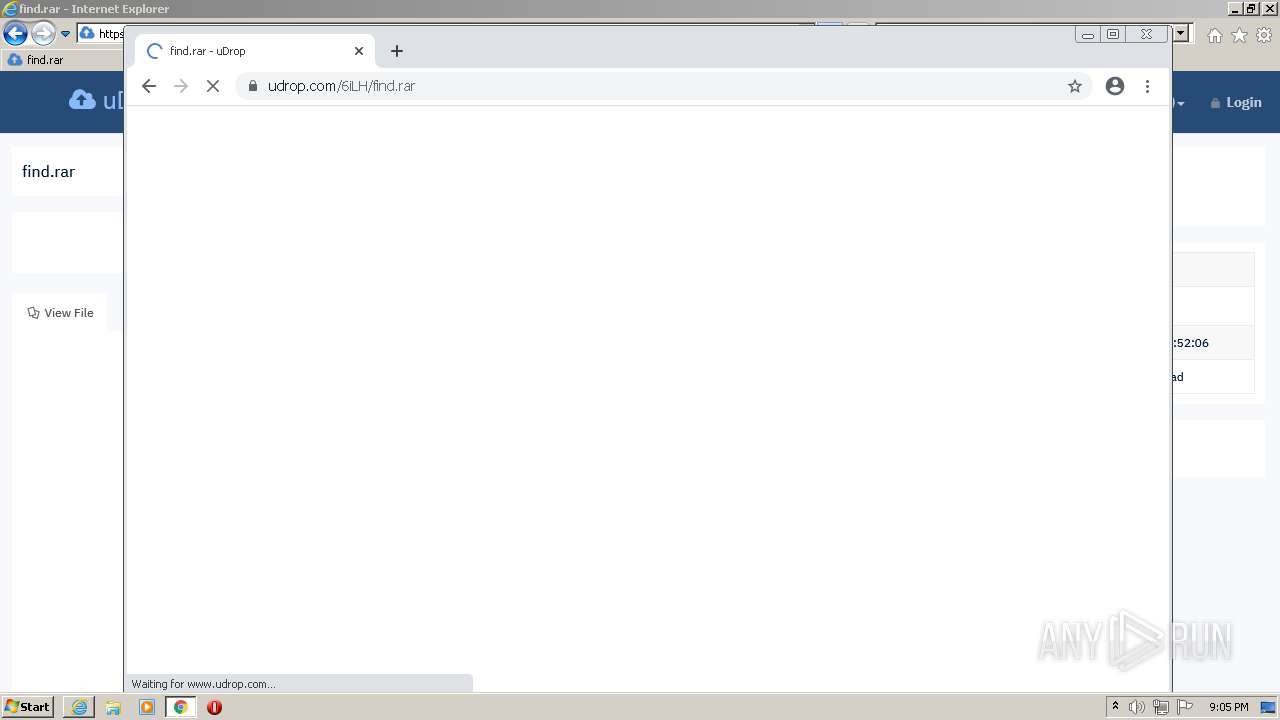
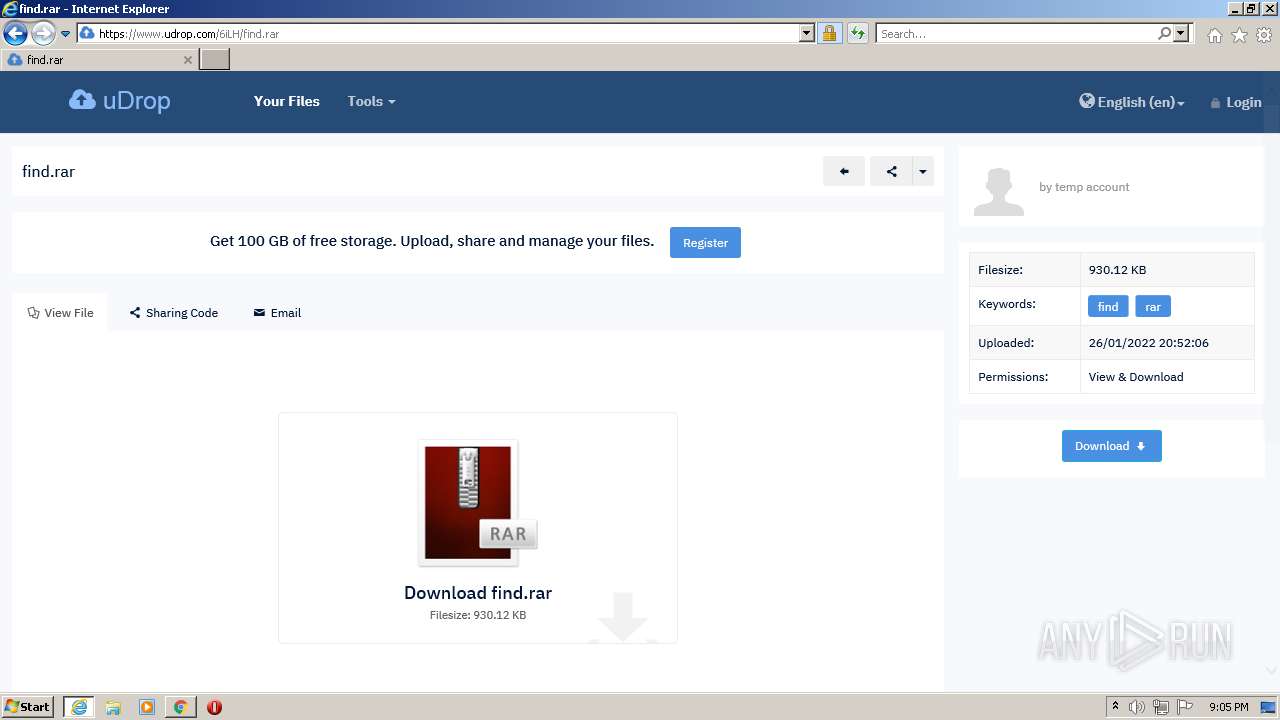
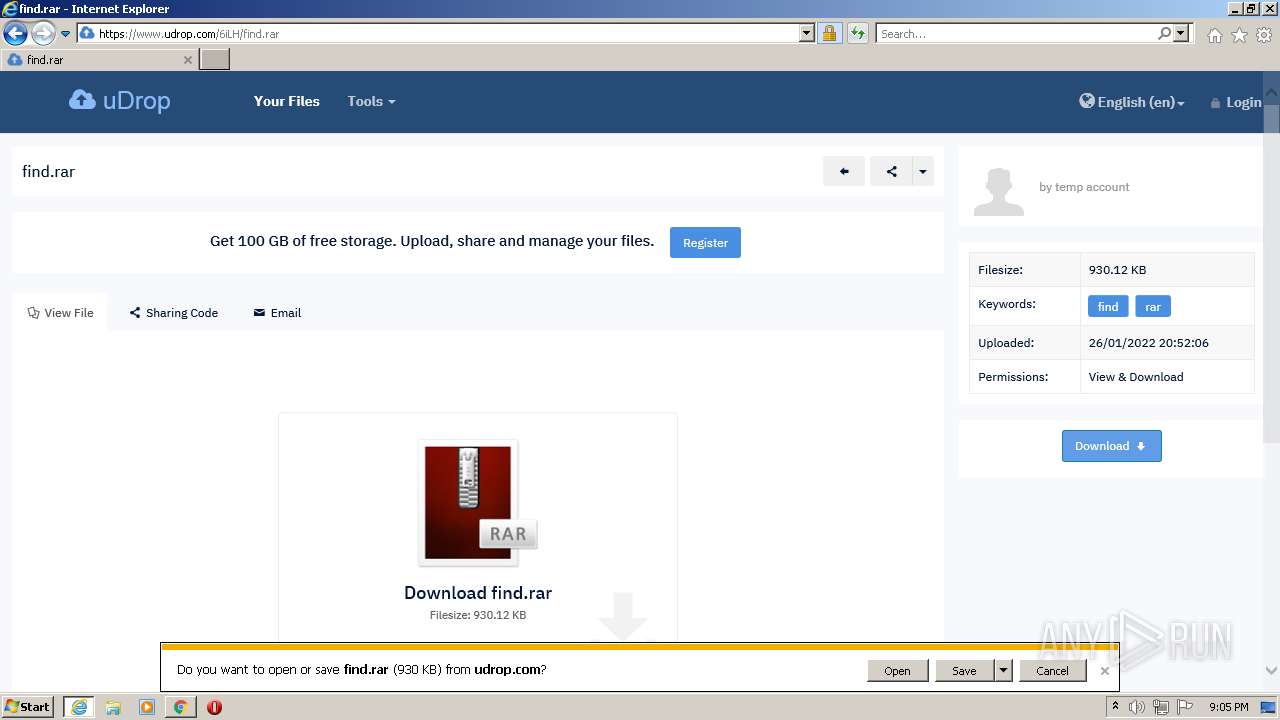
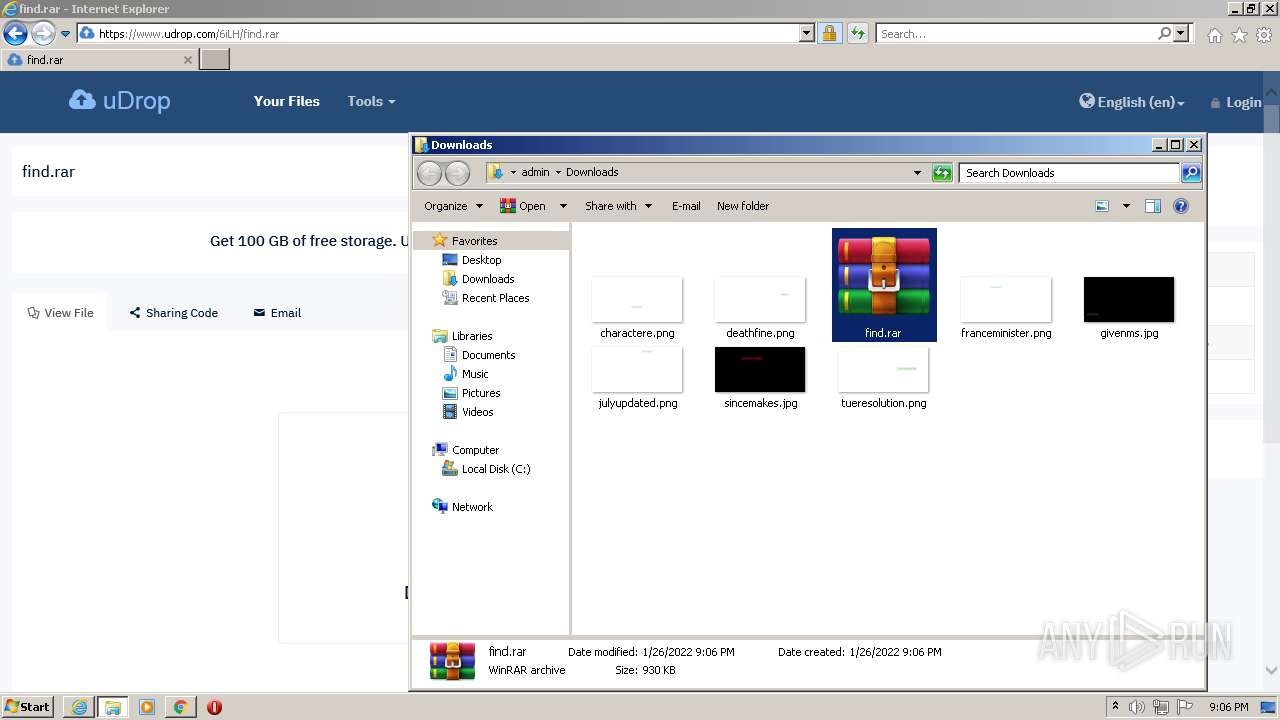
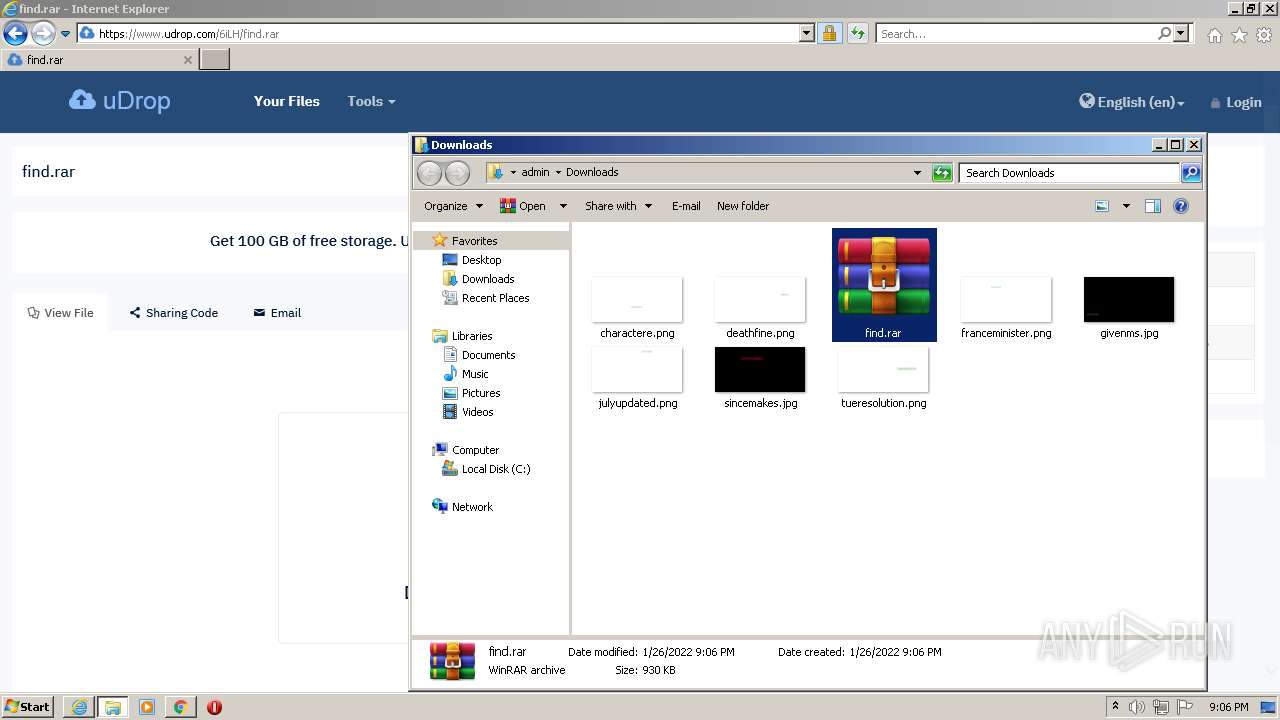
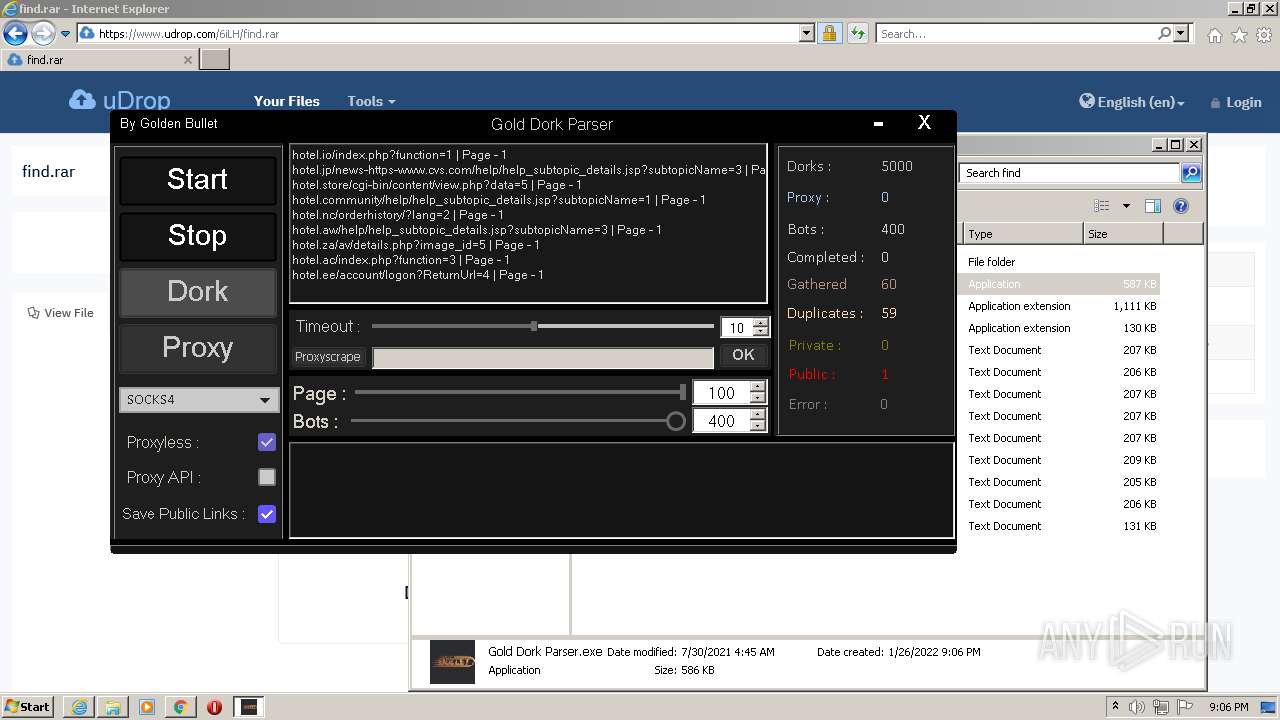
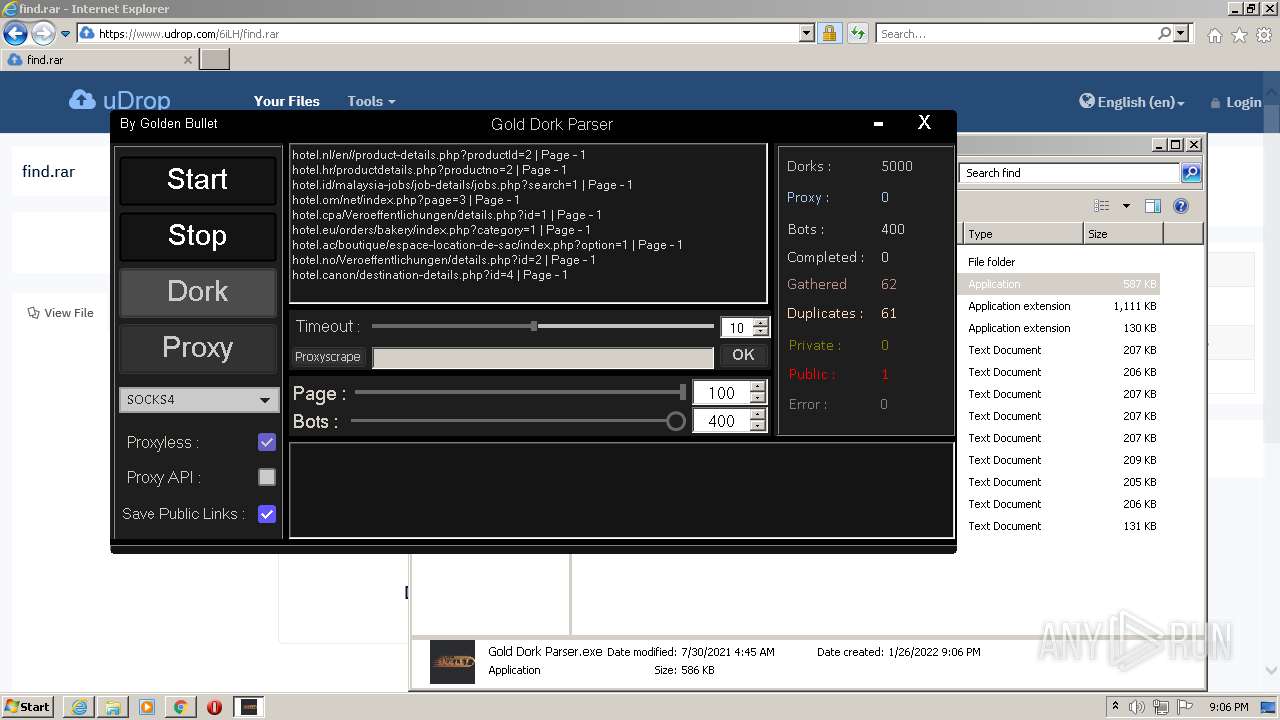
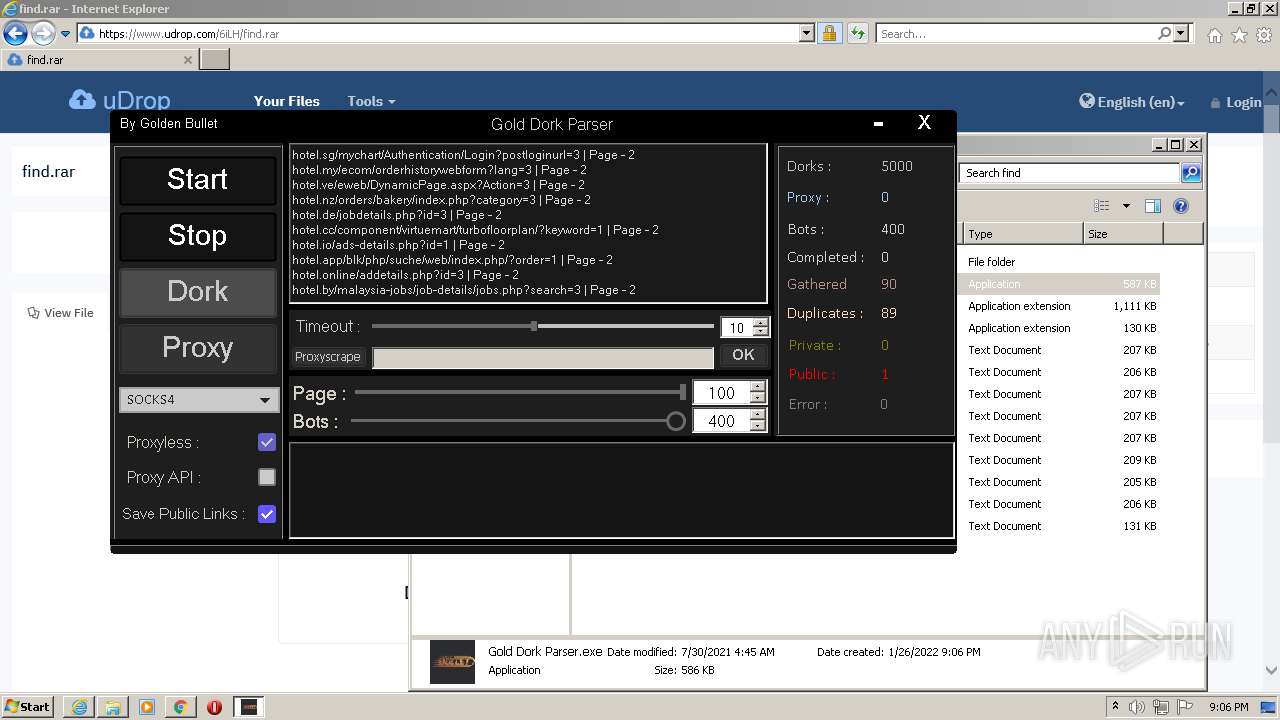
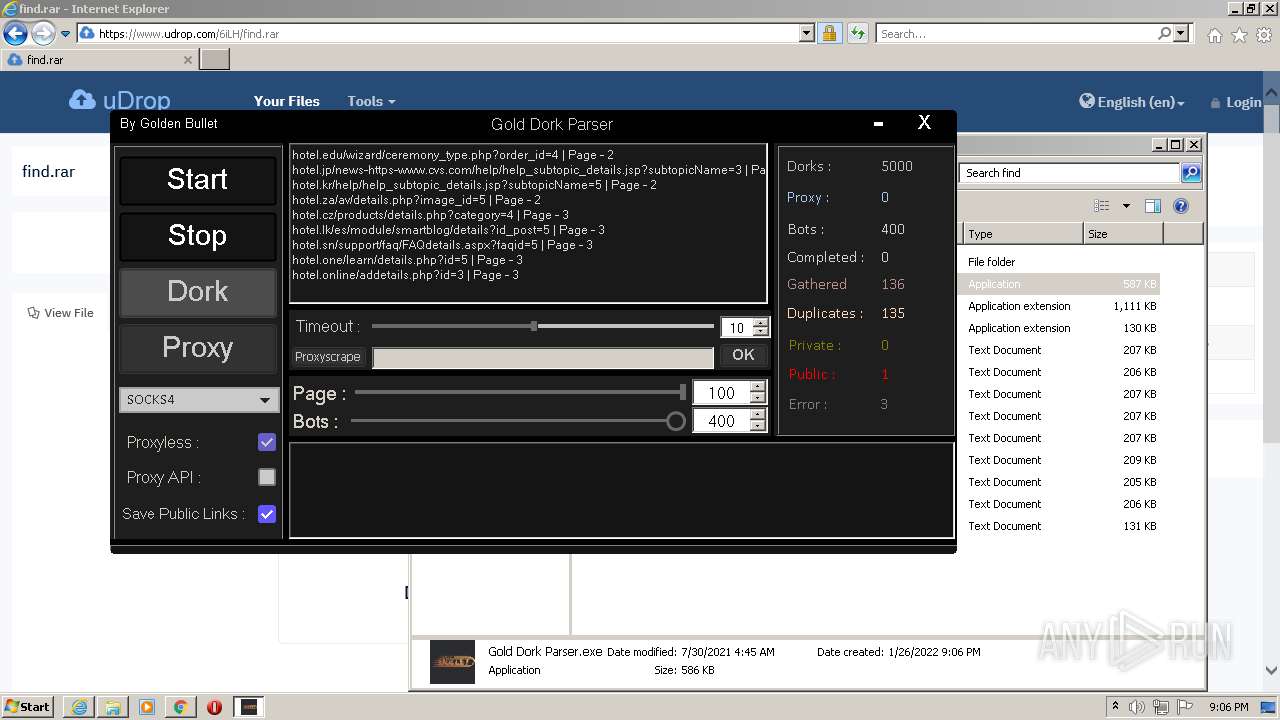
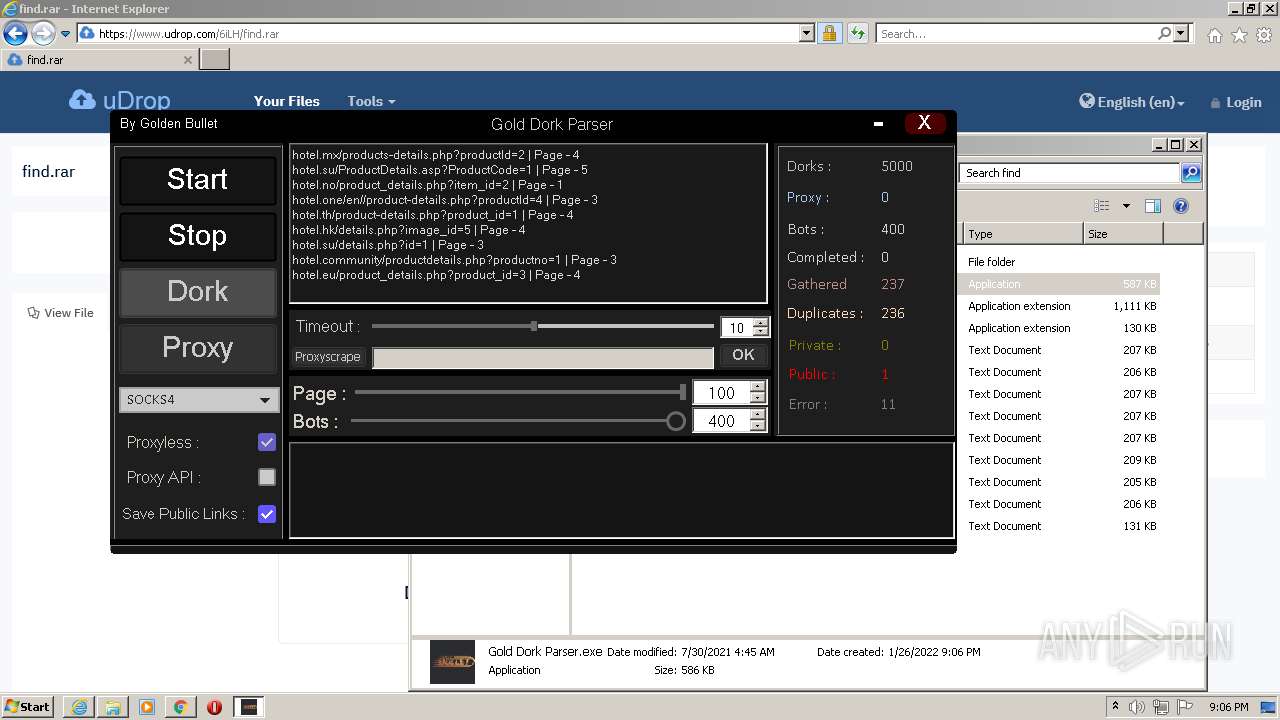
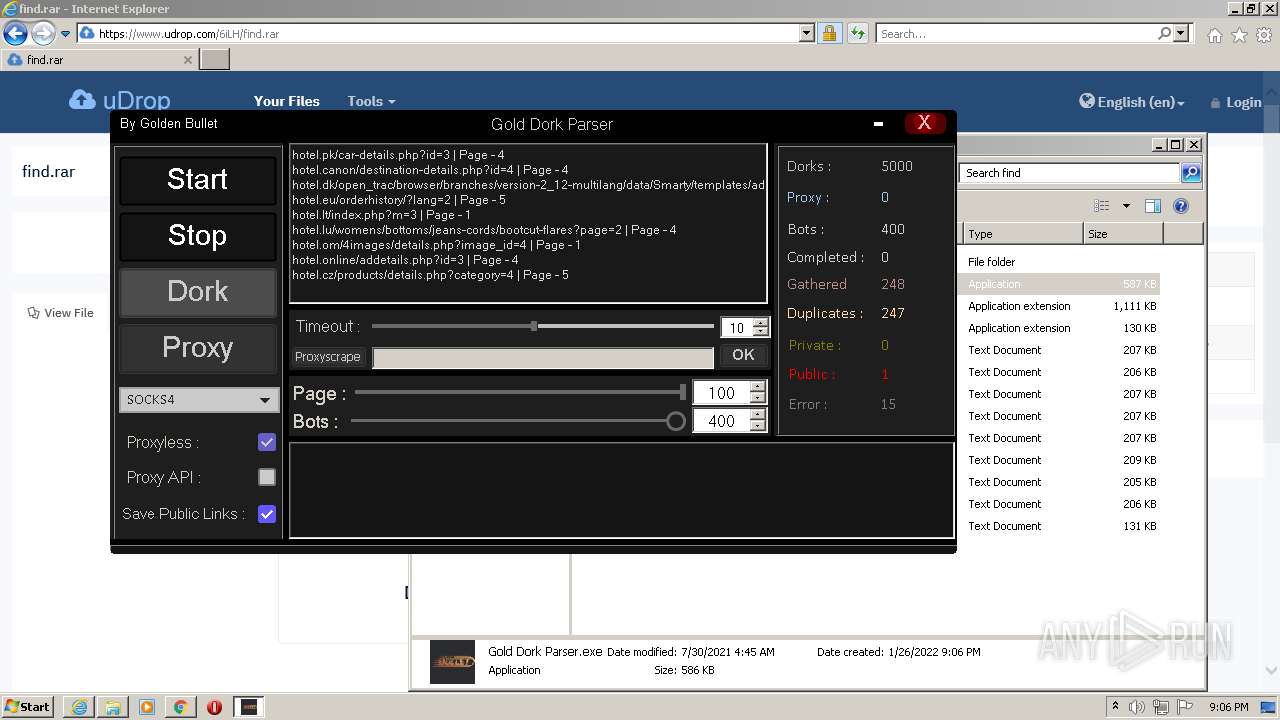
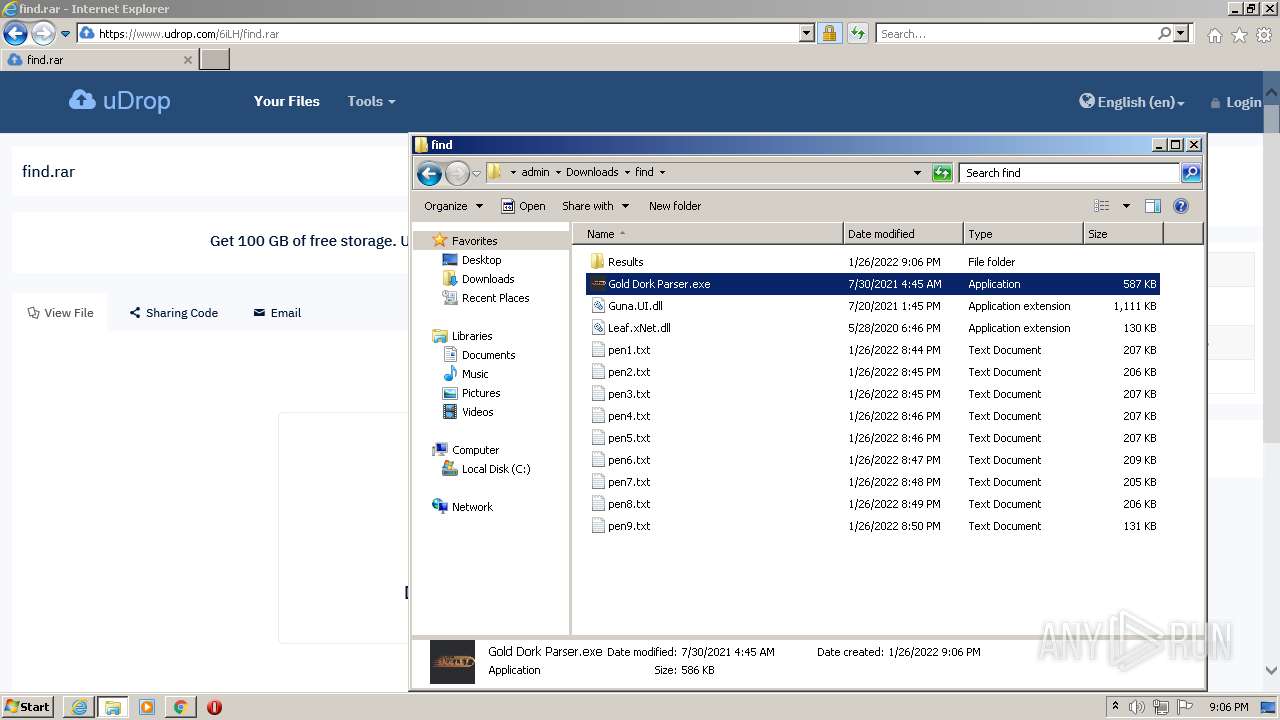
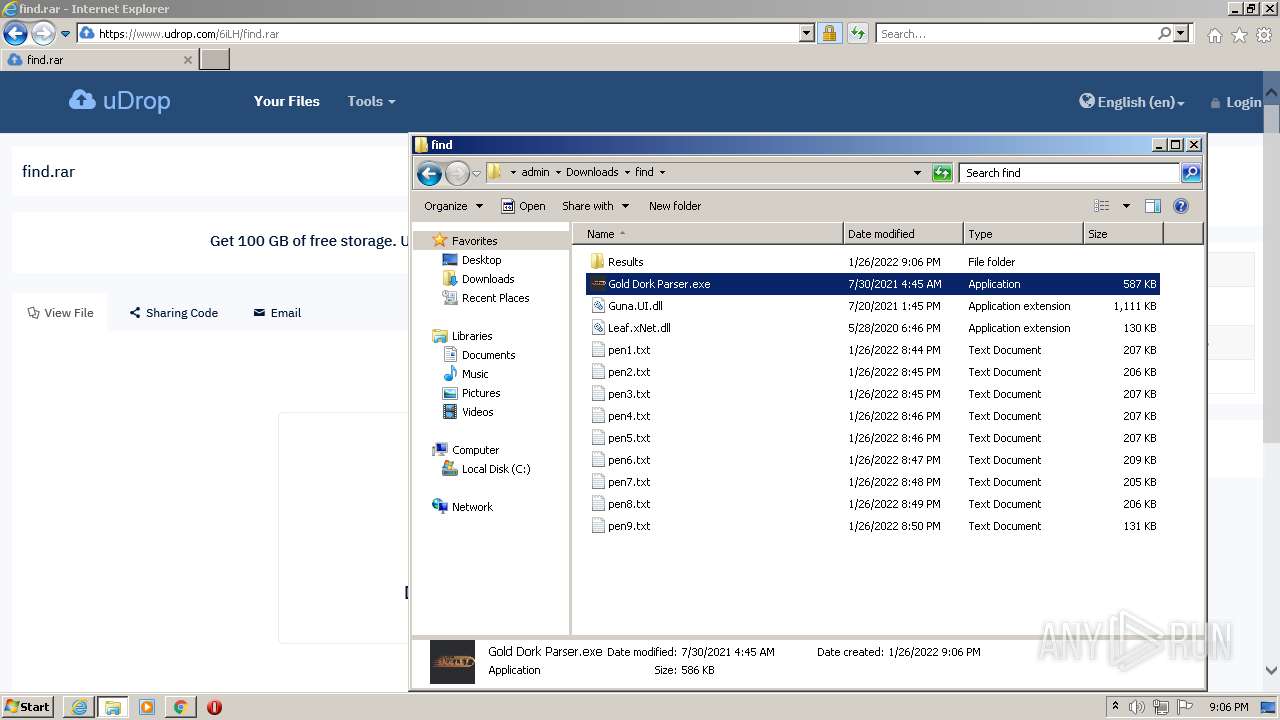
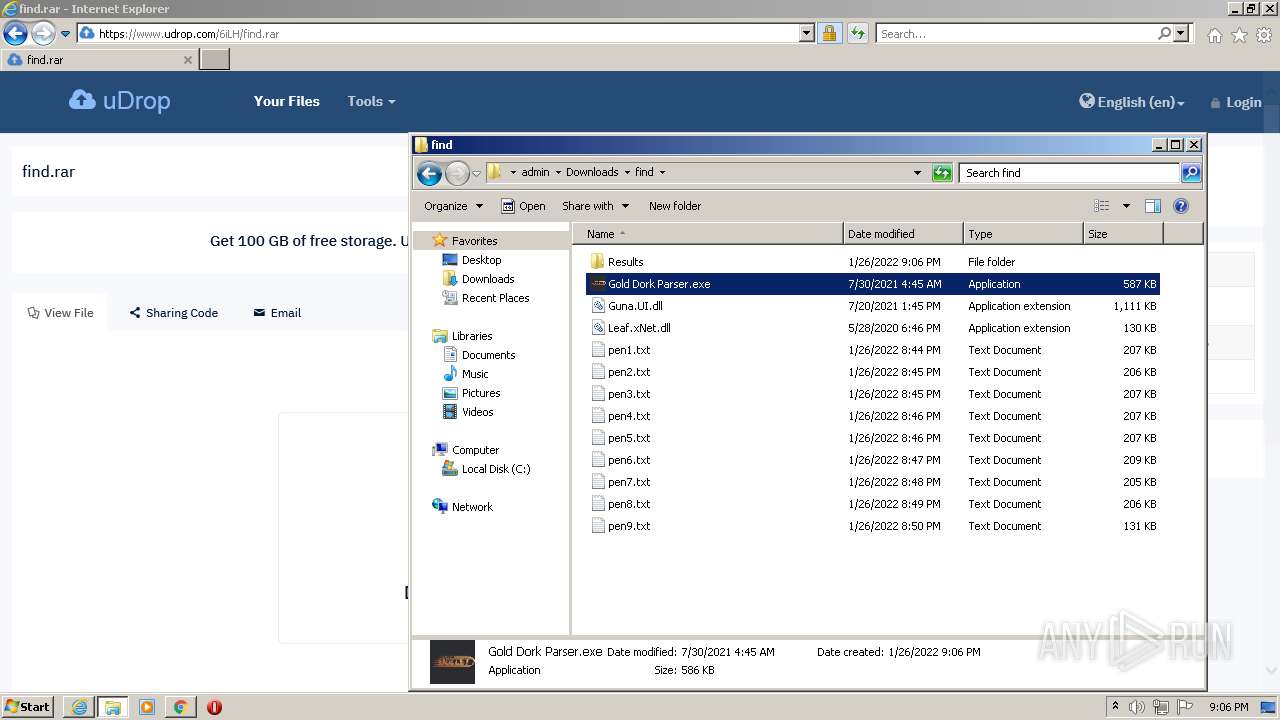
| URL: | https://www.udrop.com/6iLH/find.rar |
| Full analysis: | https://app.any.run/tasks/ab77ae68-5a5d-4c81-906b-dccda06514c9 |
| Verdict: | Malicious activity |
| Analysis date: | January 26, 2022, 21:05:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 38ED366298008A0724EC391176959017 |
| SHA1: | D8277F2F6913D018DAD4126977FBC68A3D30D86B |
| SHA256: | 432AB3A49632C7D571D0F39CEDA3093FBBC0DB242F8346C87027926B4963D4AF |
| SSDEEP: | 3:N8DSLzGTKiEX:2OLzKKX |
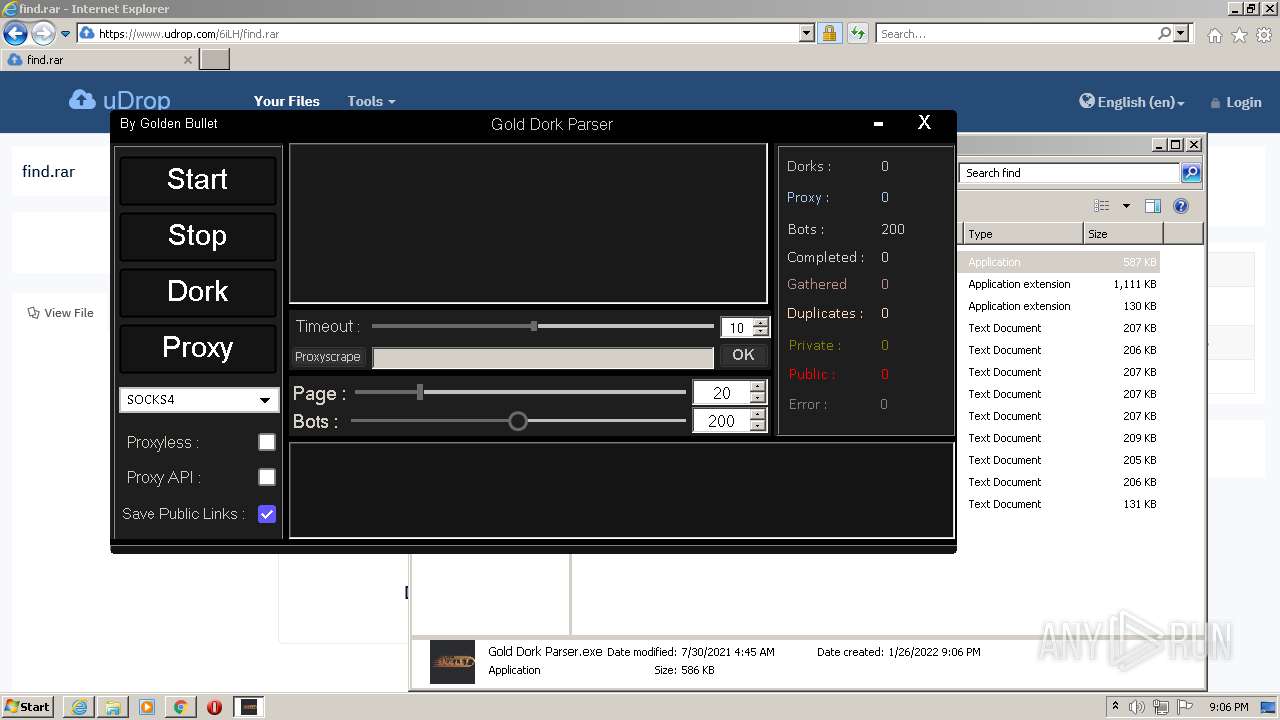
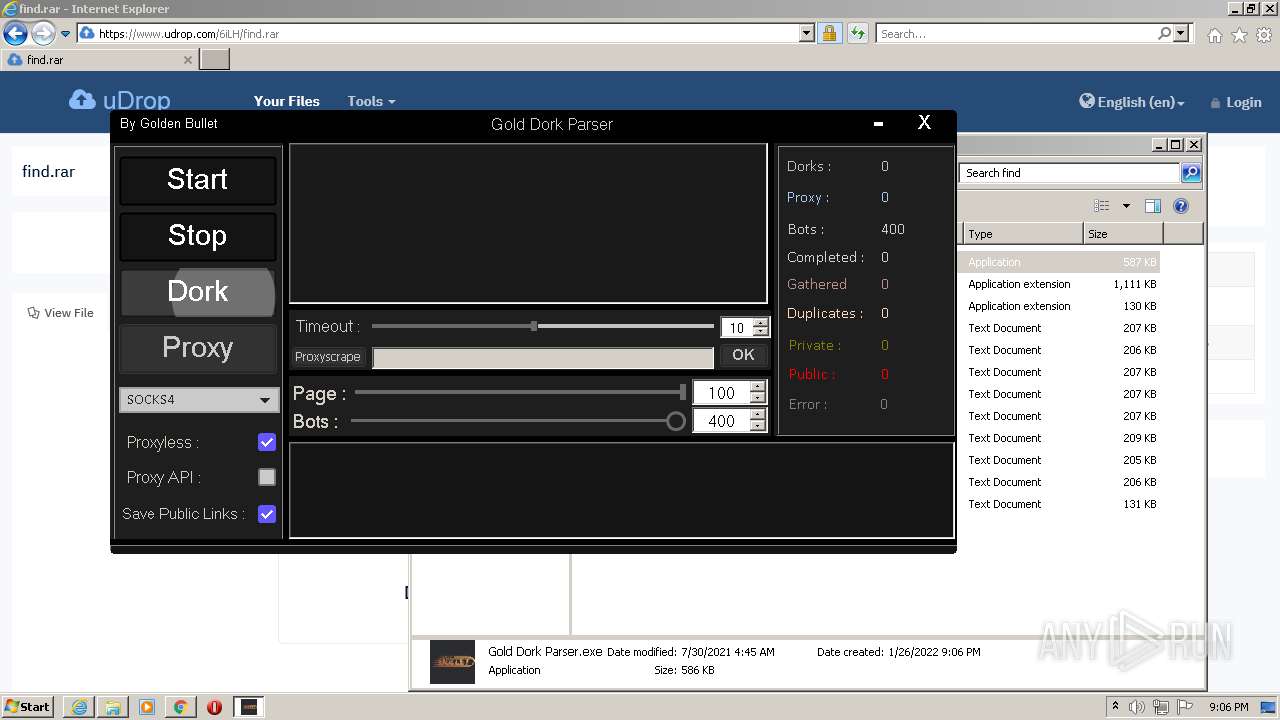
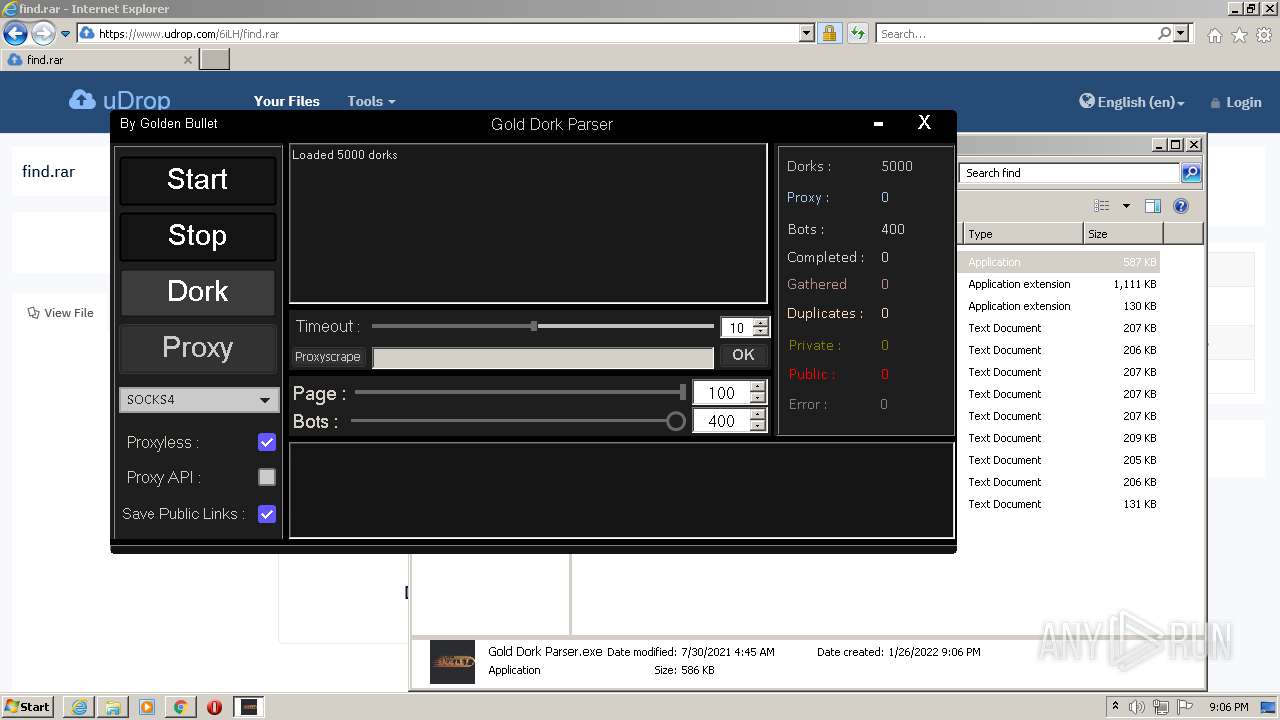
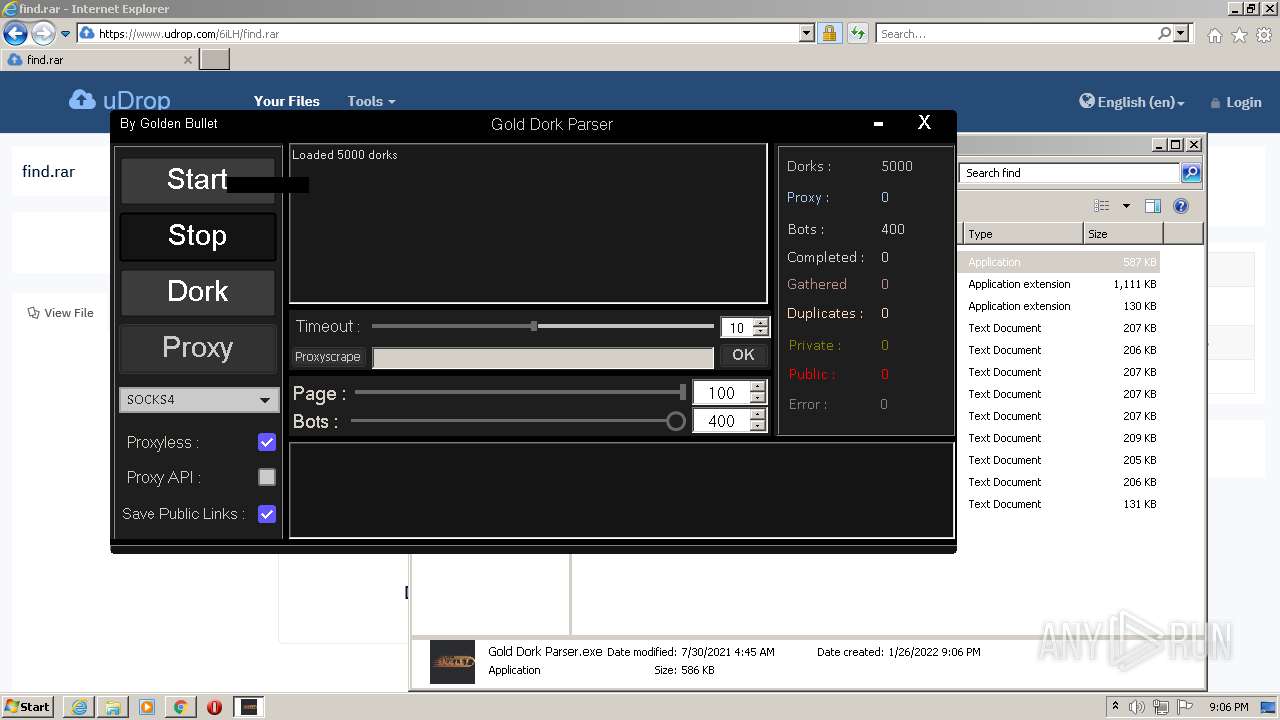
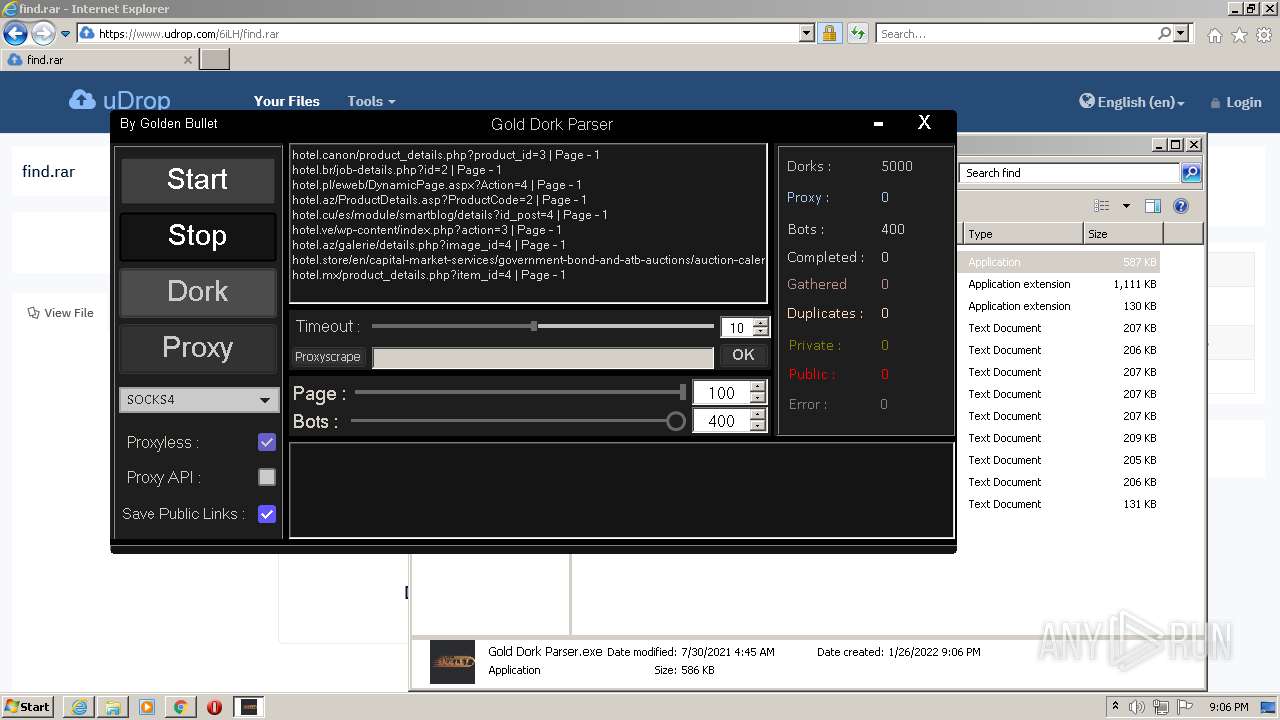
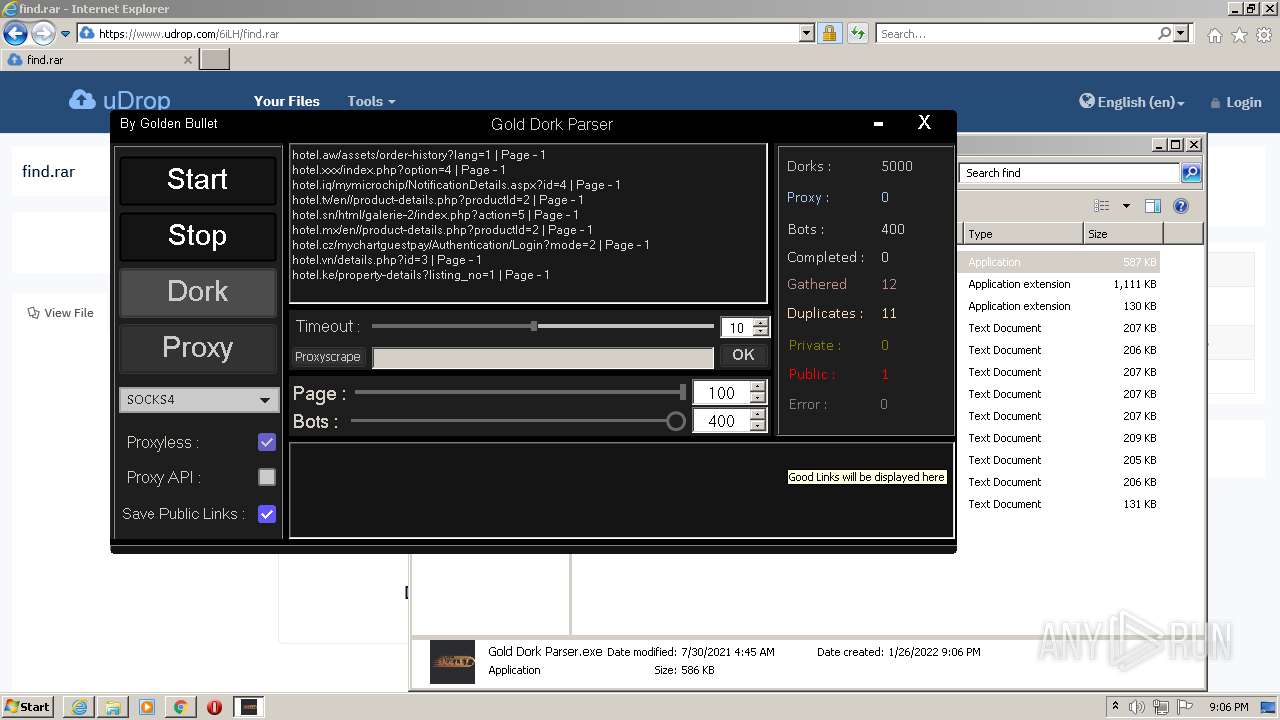
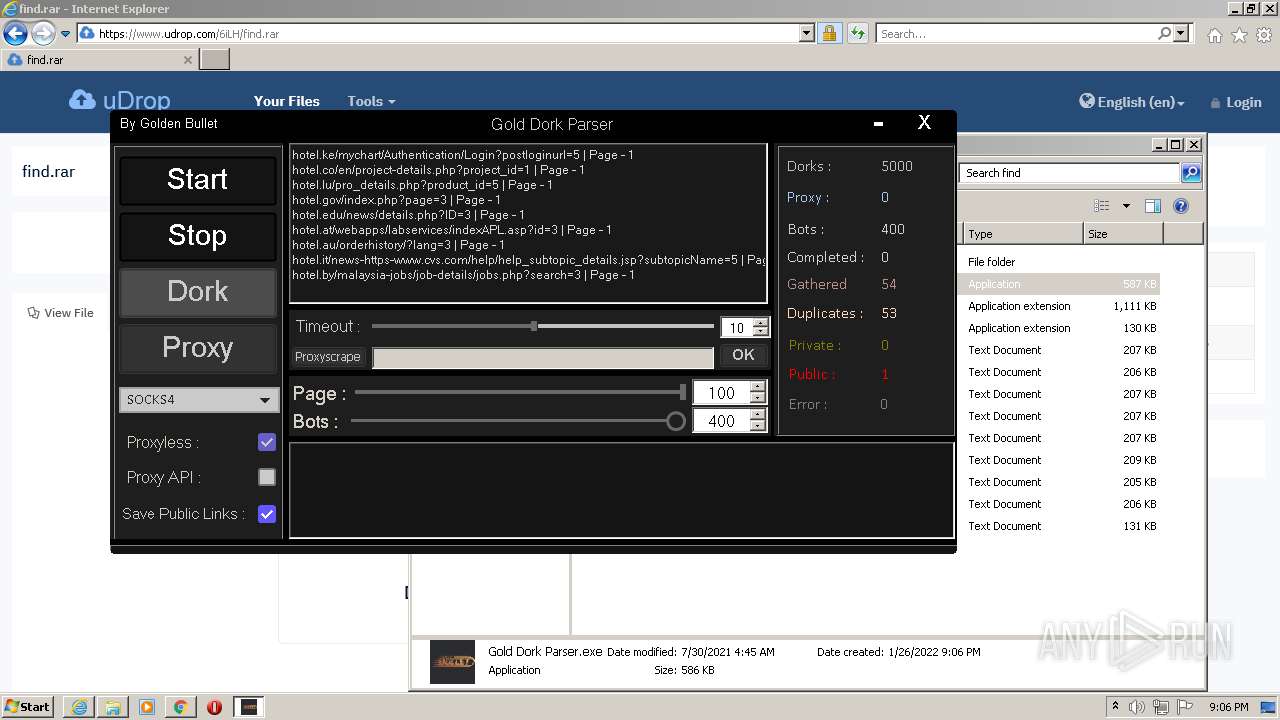
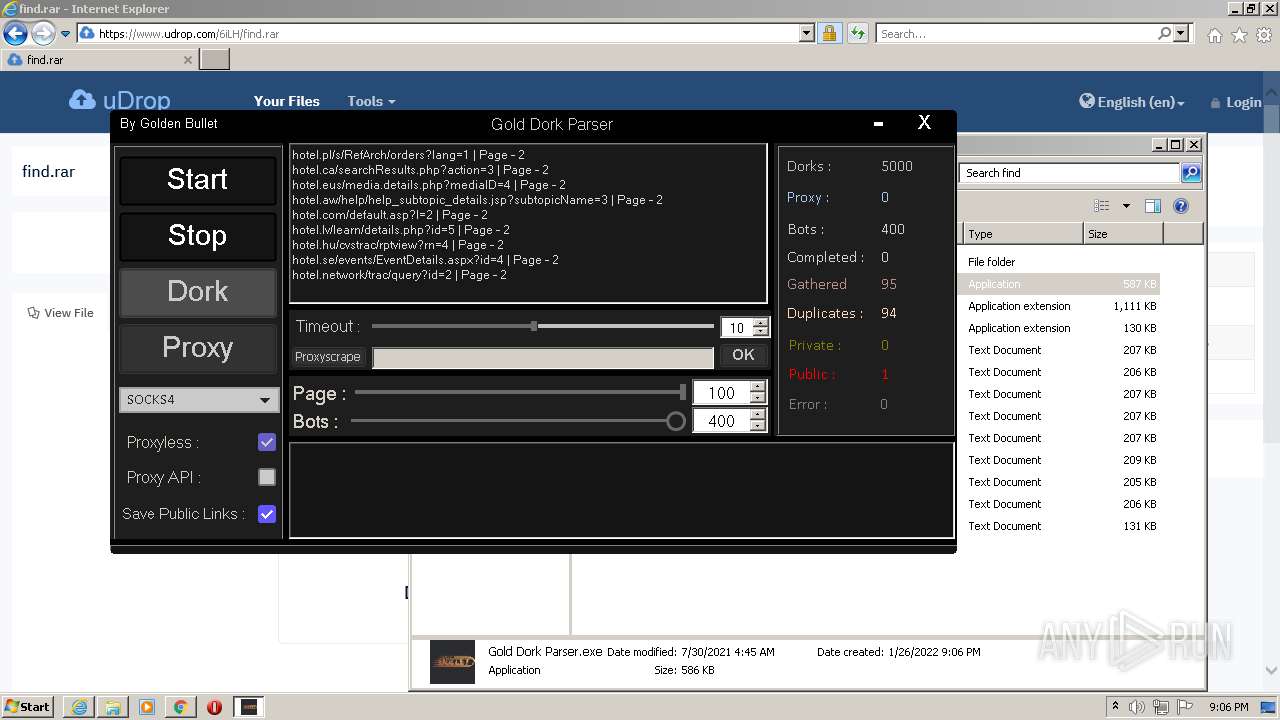
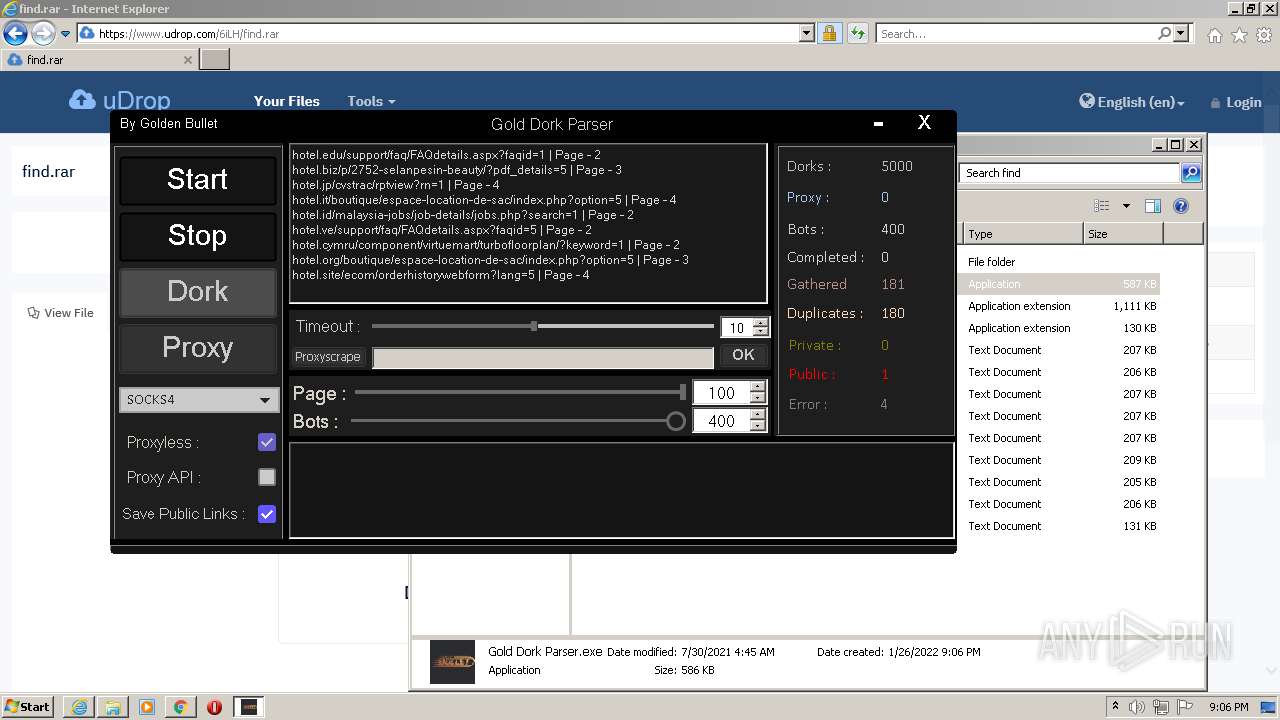
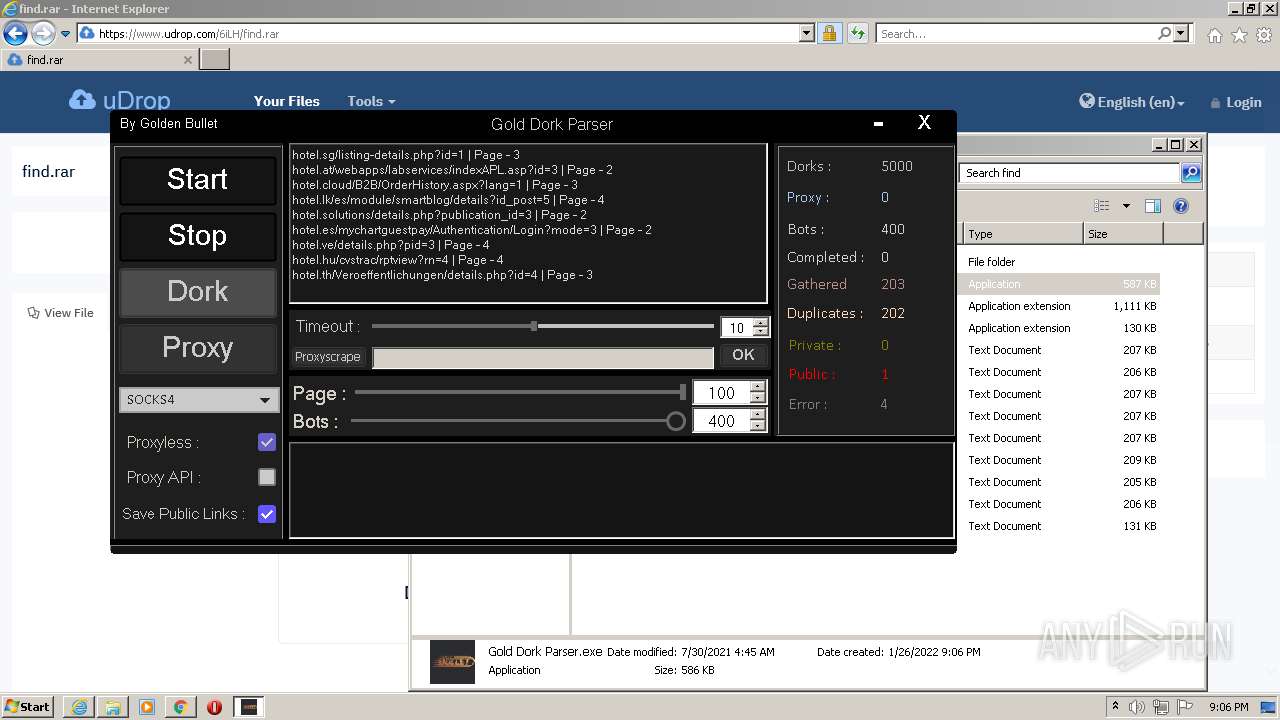
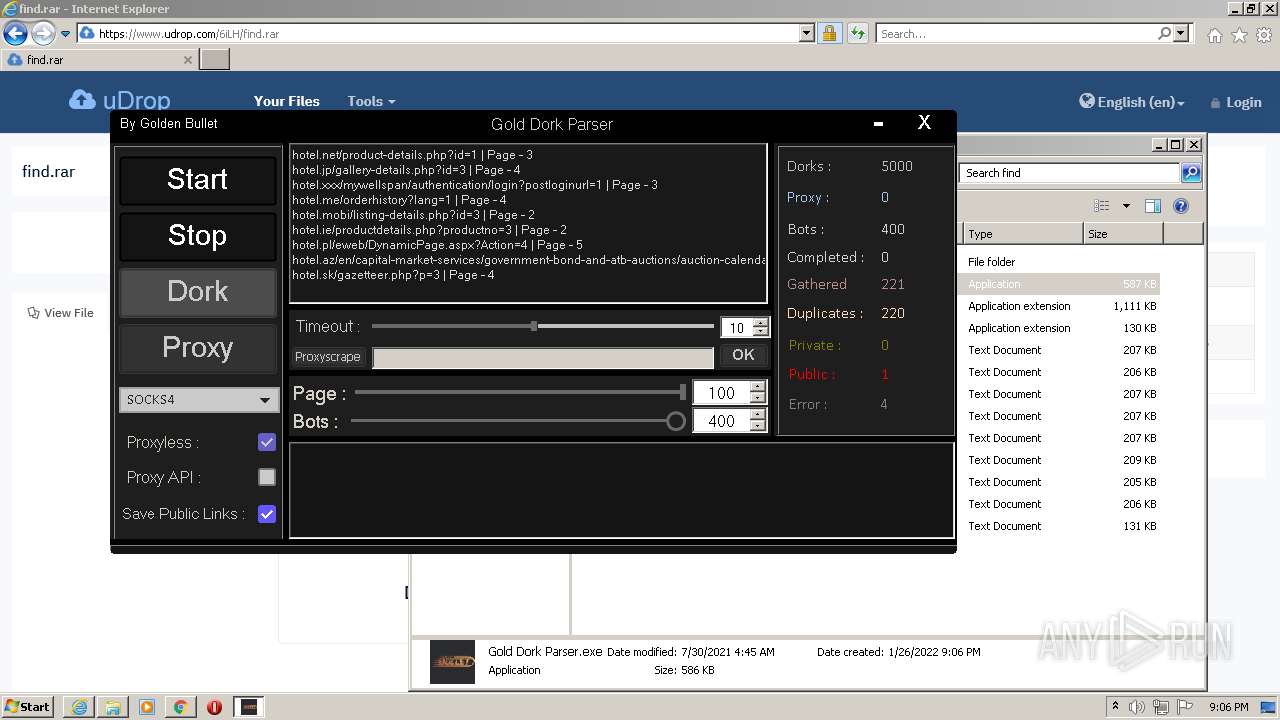
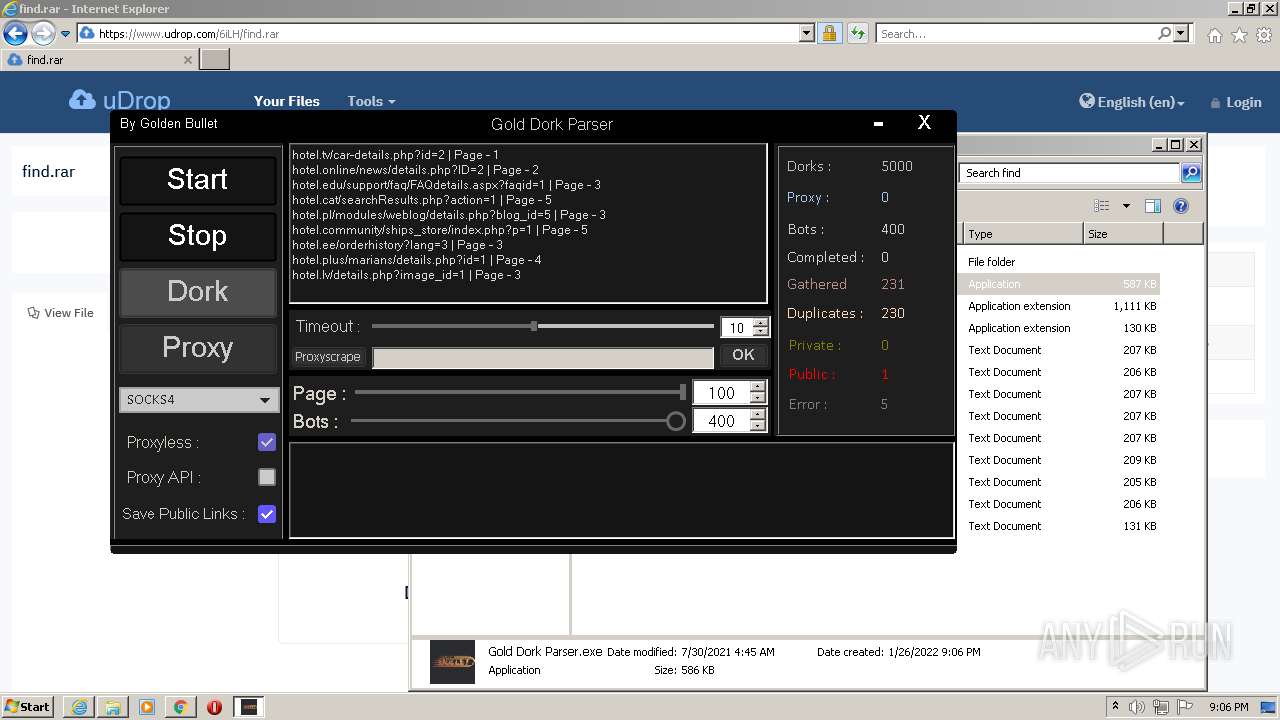
MALICIOUS
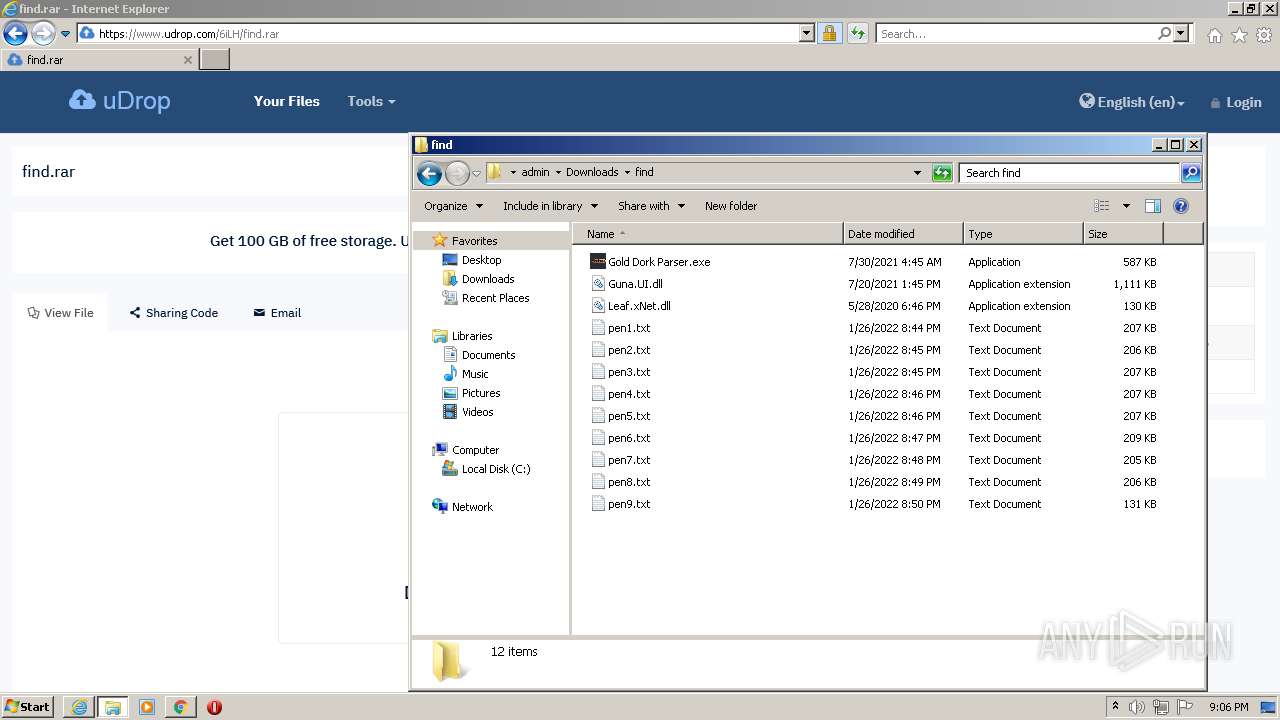
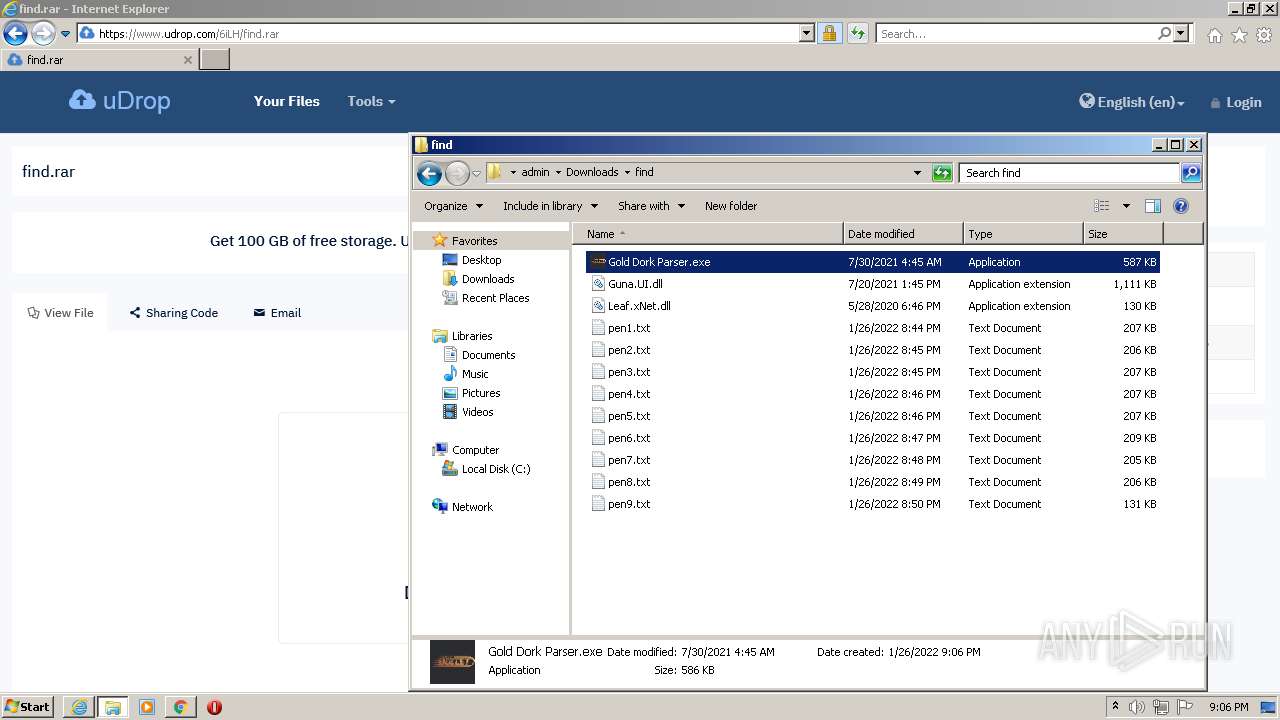
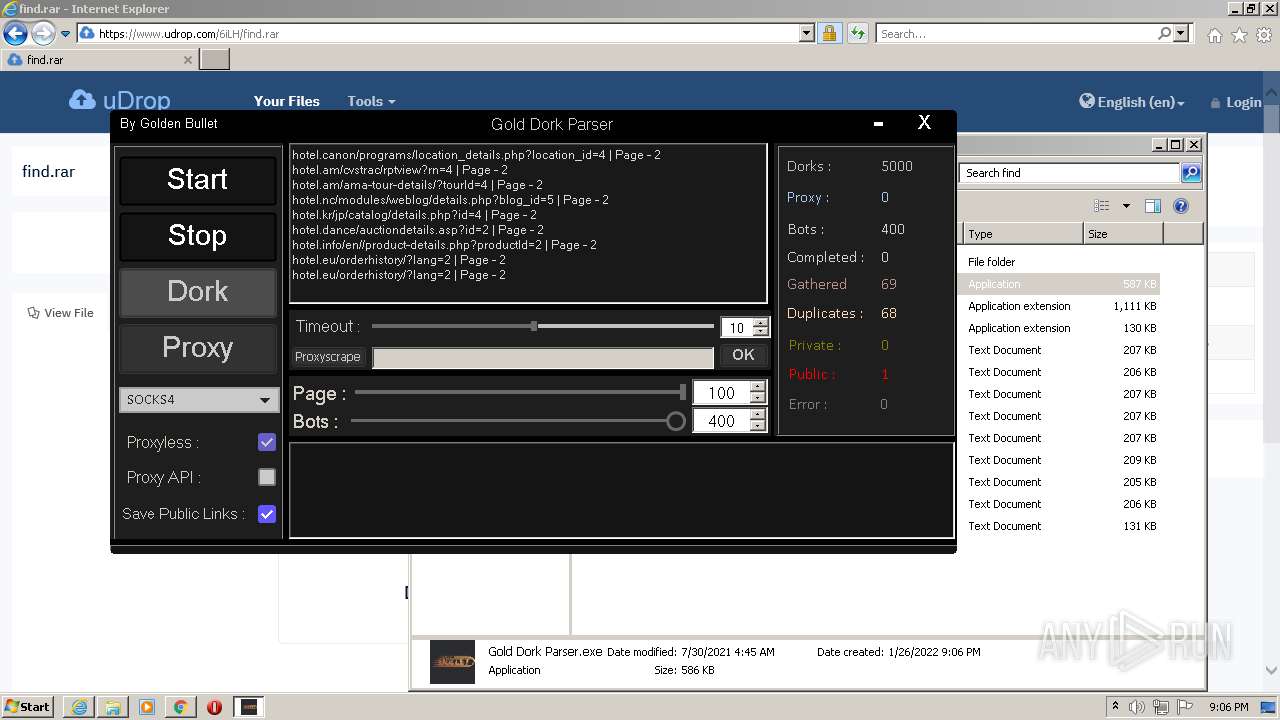
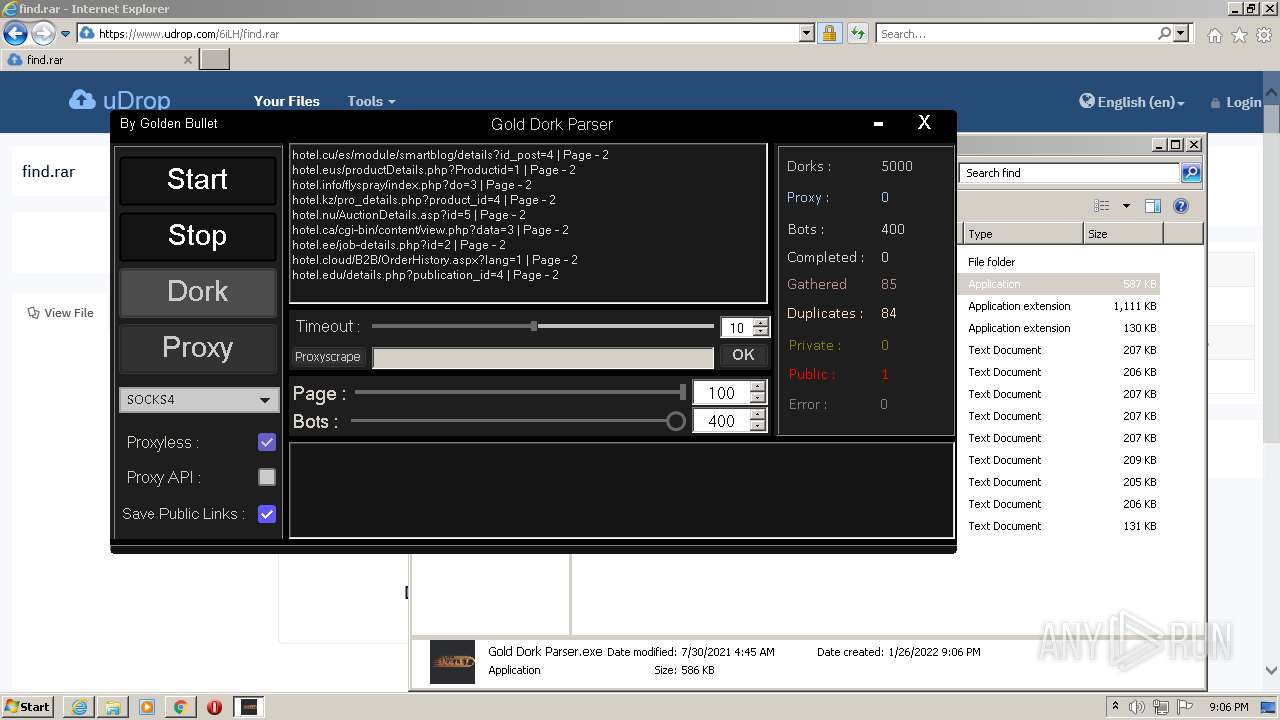
Application was dropped or rewritten from another process
- Gold Dork Parser.exe (PID: 1000)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3036)
- Gold Dork Parser.exe (PID: 1000)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 532)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3932)
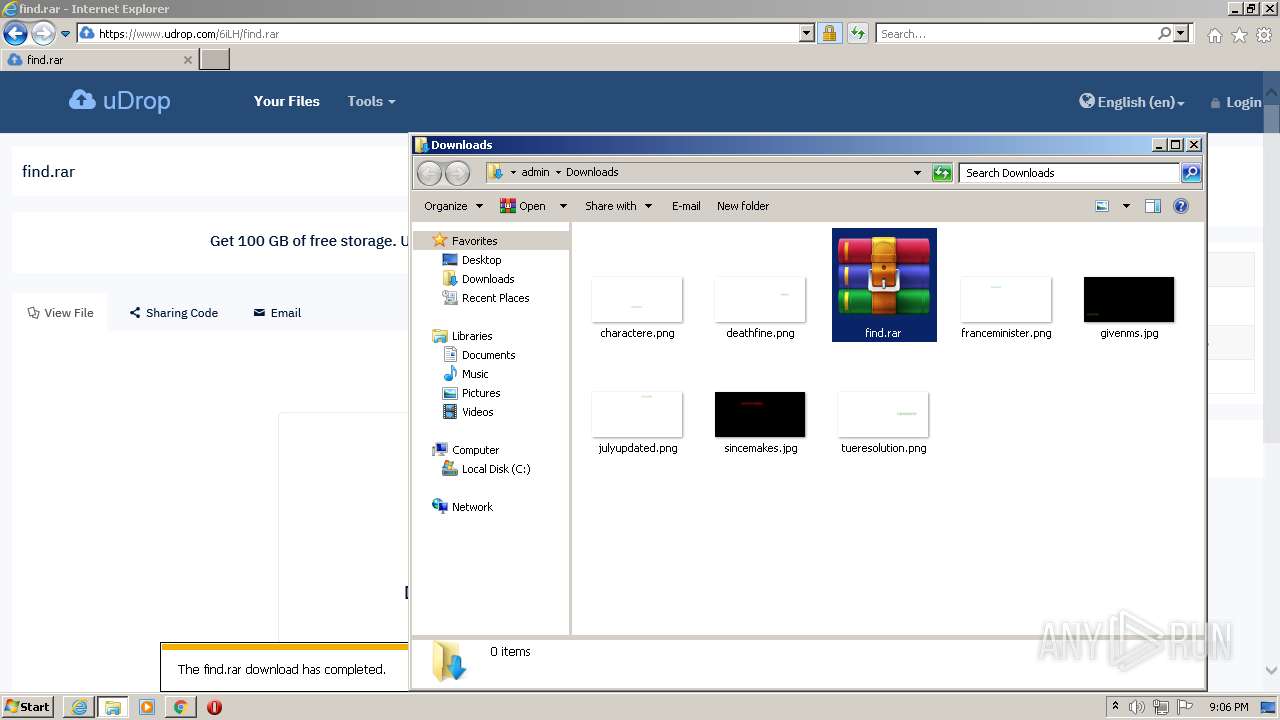
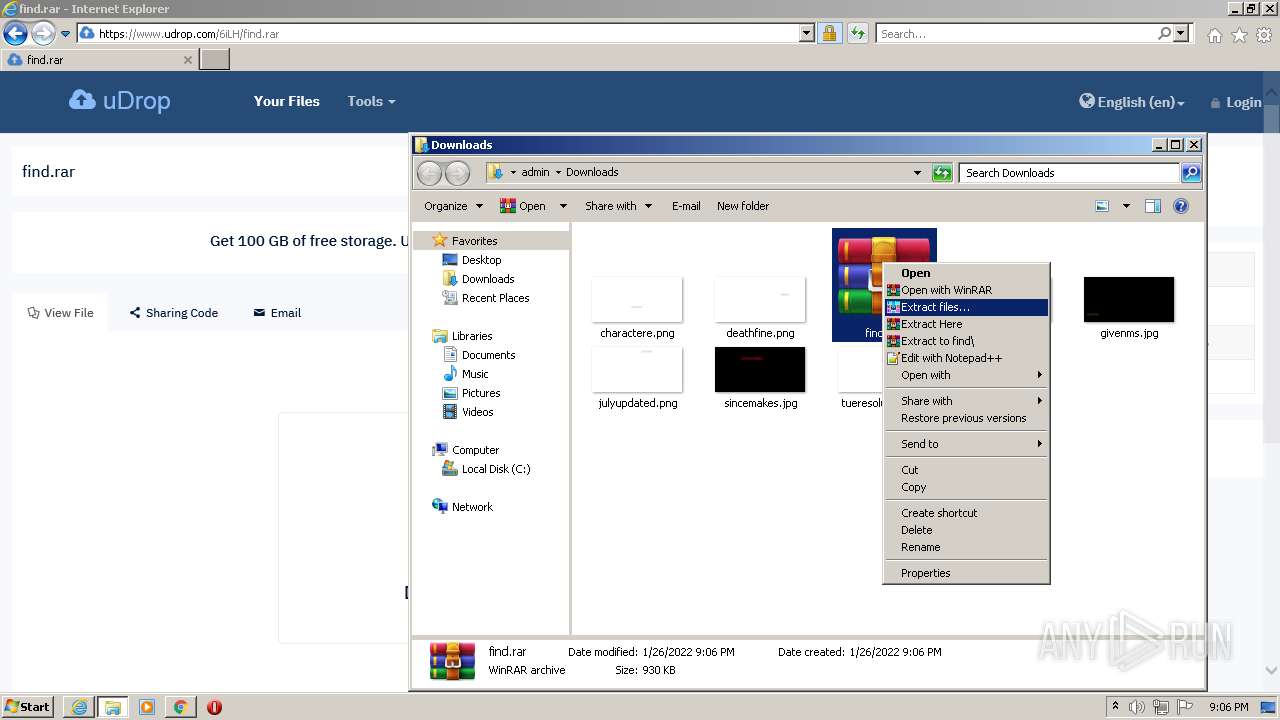
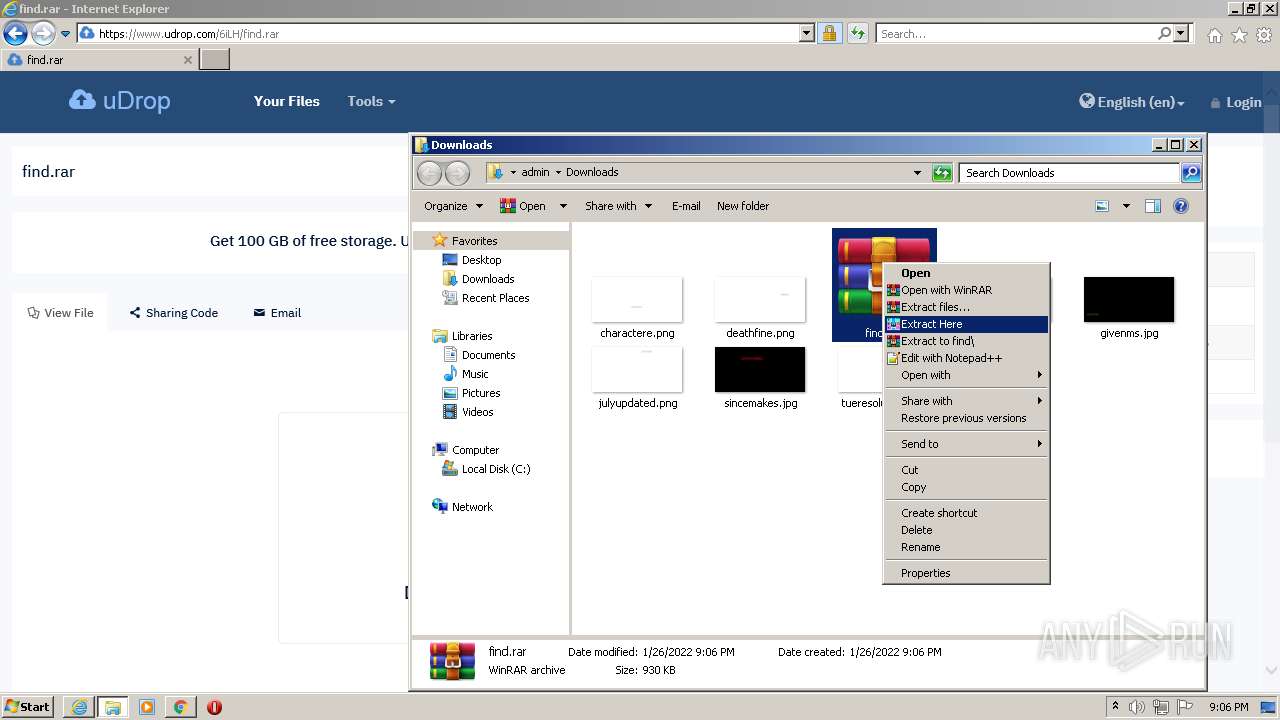
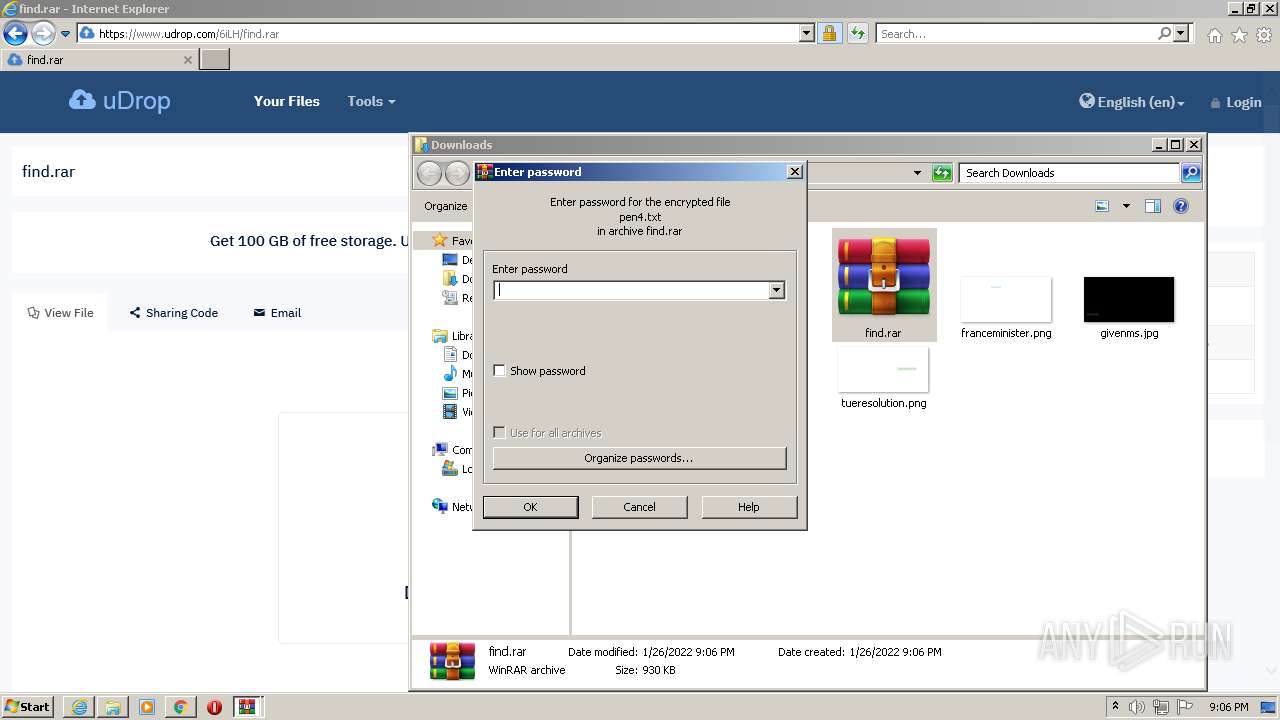
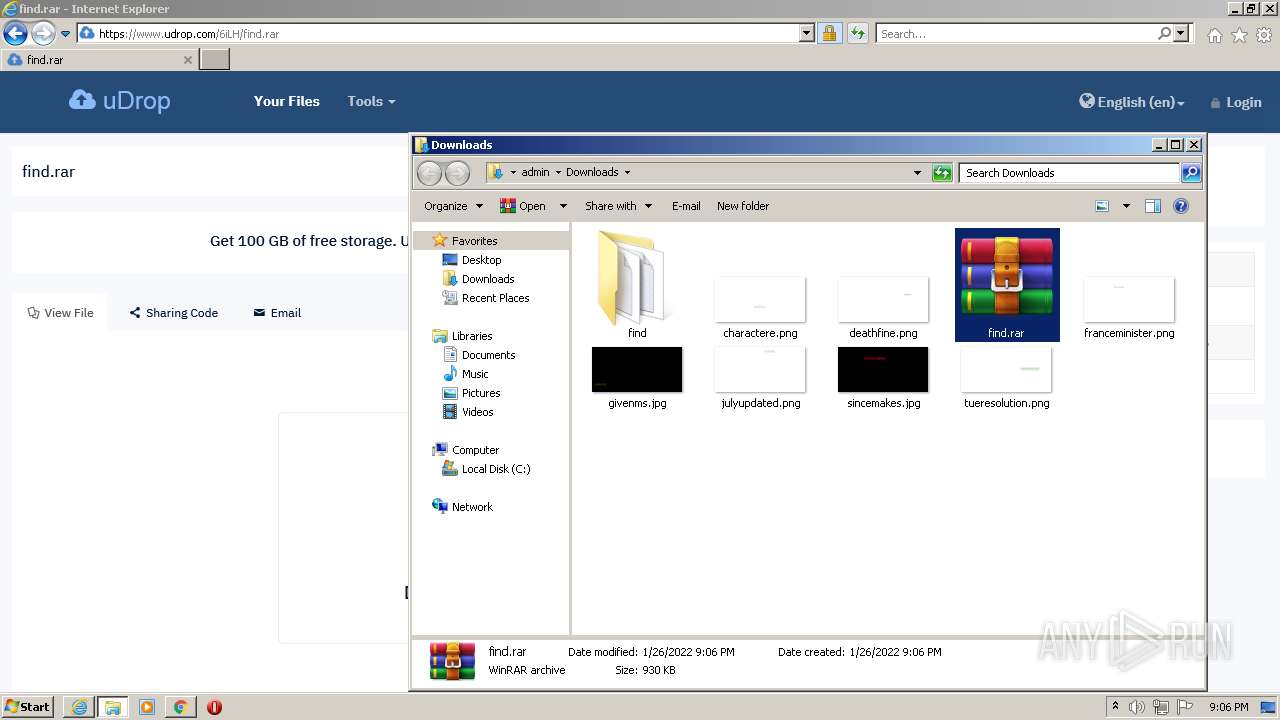
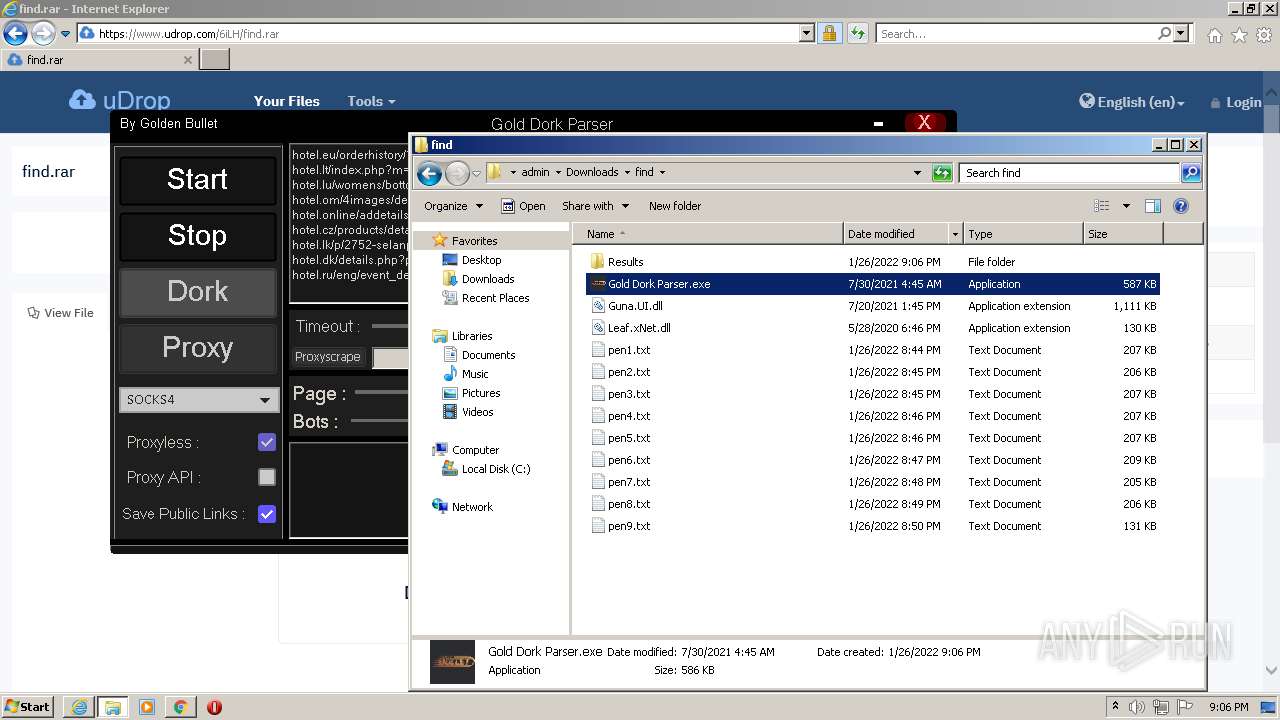
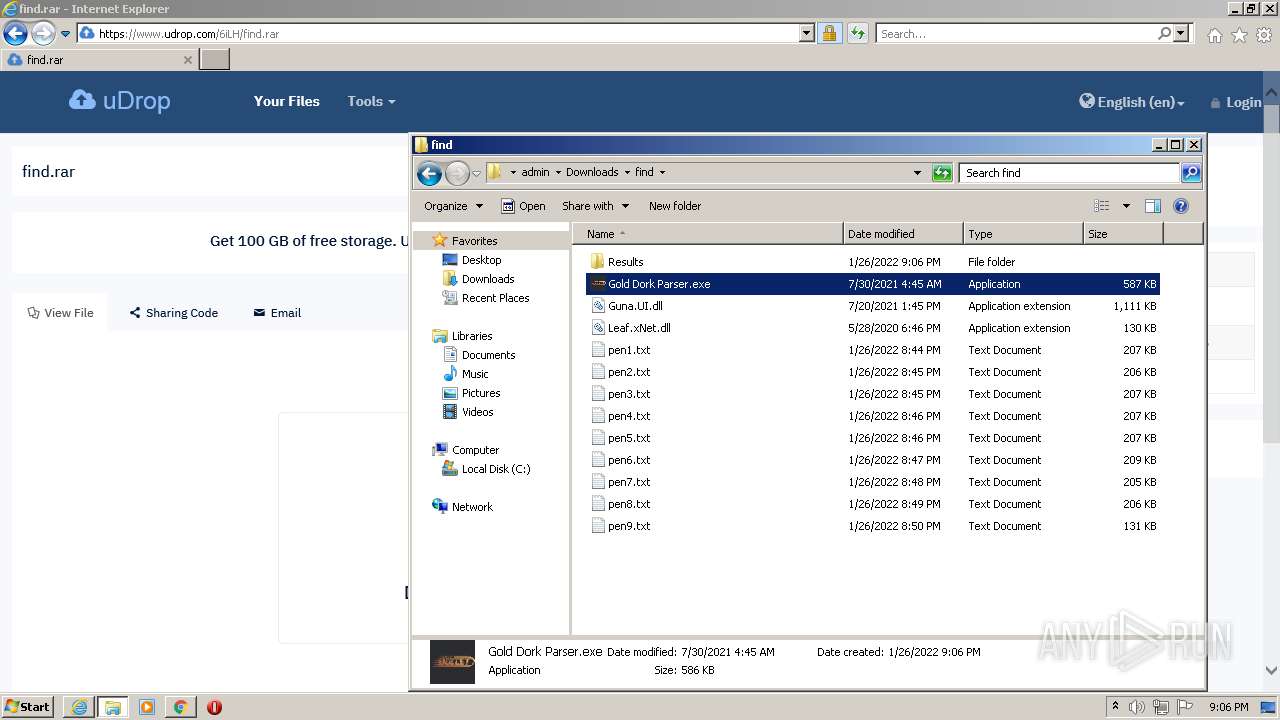
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3300)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3300)
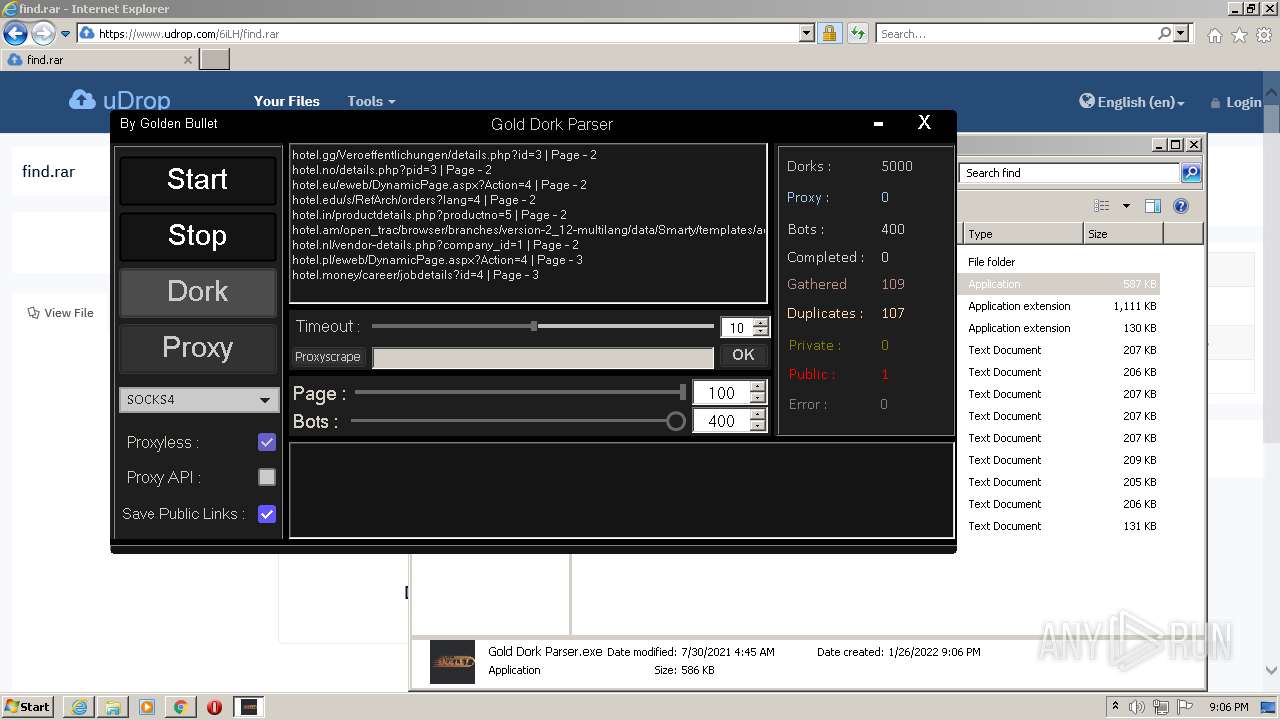
Checks supported languages
- Gold Dork Parser.exe (PID: 1000)
- WinRAR.exe (PID: 3300)
Reads the computer name
- WinRAR.exe (PID: 3300)
- Gold Dork Parser.exe (PID: 1000)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3300)
Reads Environment values
- Gold Dork Parser.exe (PID: 1000)
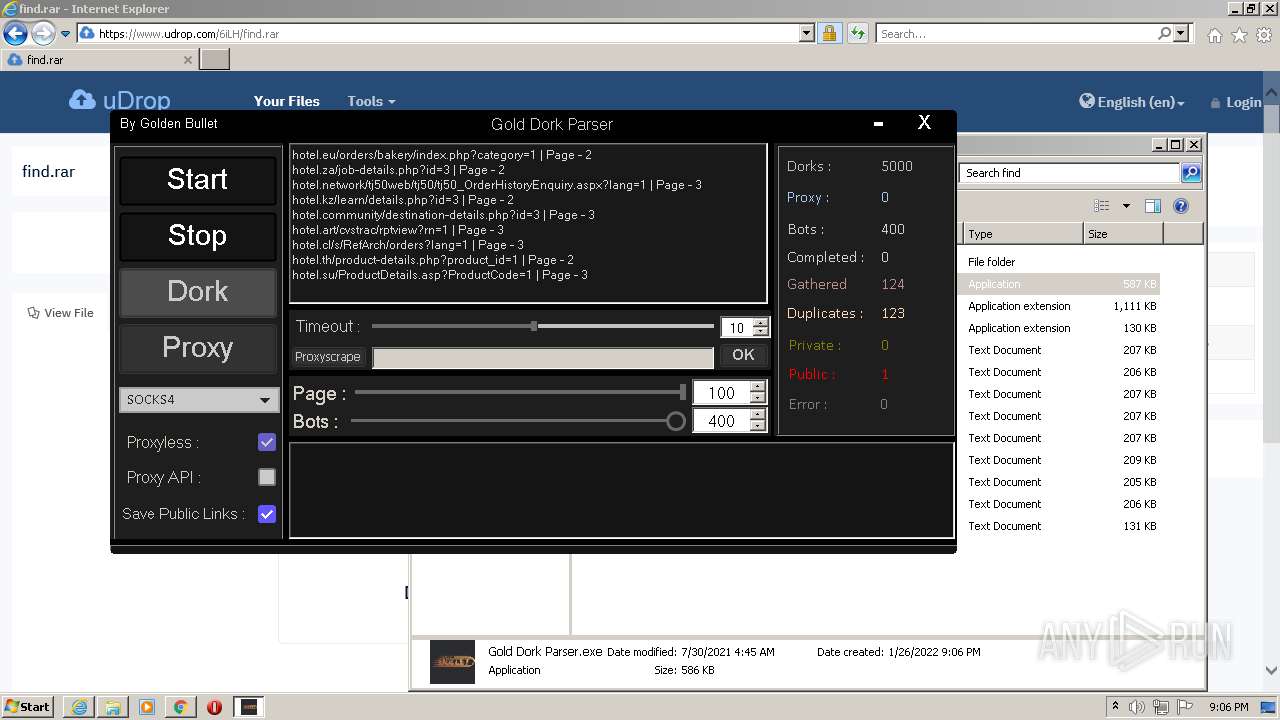
INFO
Checks Windows Trust Settings
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 3004)
Creates files in the user directory
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 3004)
Reads internet explorer settings
- iexplore.exe (PID: 532)
Manual execution by user
- chrome.exe (PID: 3932)
- WinRAR.exe (PID: 3300)
- Gold Dork Parser.exe (PID: 1000)
Checks supported languages
- iexplore.exe (PID: 3004)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 580)
- iexplore.exe (PID: 532)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 832)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 1004)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 1888)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 5016)
- chrome.exe (PID: 2476)
- chrome.exe (PID: 4956)
- chrome.exe (PID: 5908)
Reads the computer name
- iexplore.exe (PID: 3004)
- chrome.exe (PID: 3932)
- iexplore.exe (PID: 532)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 5016)
- chrome.exe (PID: 5908)
Changes internet zones settings
- iexplore.exe (PID: 3004)
Reads settings of System Certificates
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 3004)
- chrome.exe (PID: 3780)
- Gold Dork Parser.exe (PID: 1000)
Application launched itself
- iexplore.exe (PID: 3004)
- chrome.exe (PID: 3932)
Reads the hosts file
- chrome.exe (PID: 3932)
- chrome.exe (PID: 3780)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3004)
Reads the date of Windows installation
- chrome.exe (PID: 5016)
Drops Coronavirus (possible) decoy
- Gold Dork Parser.exe (PID: 1000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
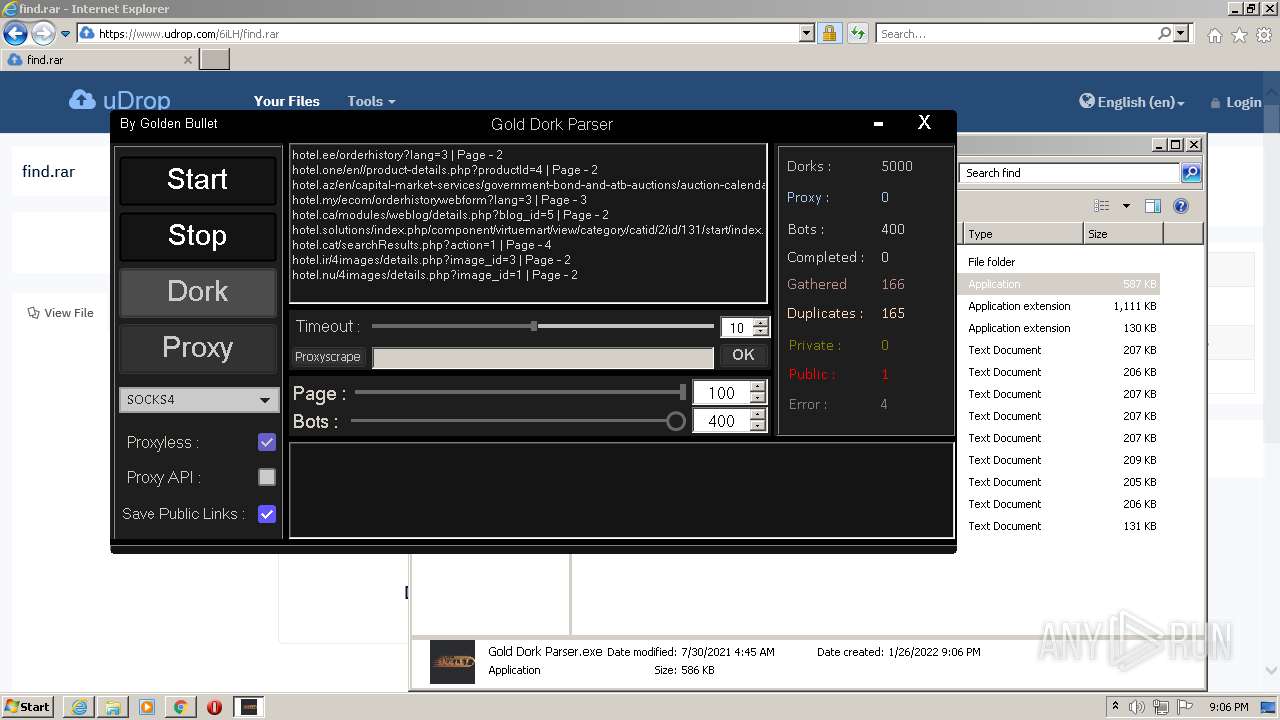
Total processes
62
Monitored processes
24
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3004 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x71a3d988,0x71a3d998,0x71a3d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,13198665882789658150,12360185764567399508,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1000 | "C:\Users\admin\Downloads\find\Gold Dork Parser.exe" | C:\Users\admin\Downloads\find\Gold Dork Parser.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Gold Dork Parser Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,13198665882789658150,12360185764567399508,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2844 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,13198665882789658150,12360185764567399508,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3344 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,13198665882789658150,12360185764567399508,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,13198665882789658150,12360185764567399508,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2968 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,13198665882789658150,12360185764567399508,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2704 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.udrop.com/6iLH/find.rar" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
38 741
Read events
38 455
Write events
283
Delete events
3
Modification events
| (PID) Process: | (3004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937848 | |||
| (PID) Process: | (3004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937848 | |||
| (PID) Process: | (3004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3004) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
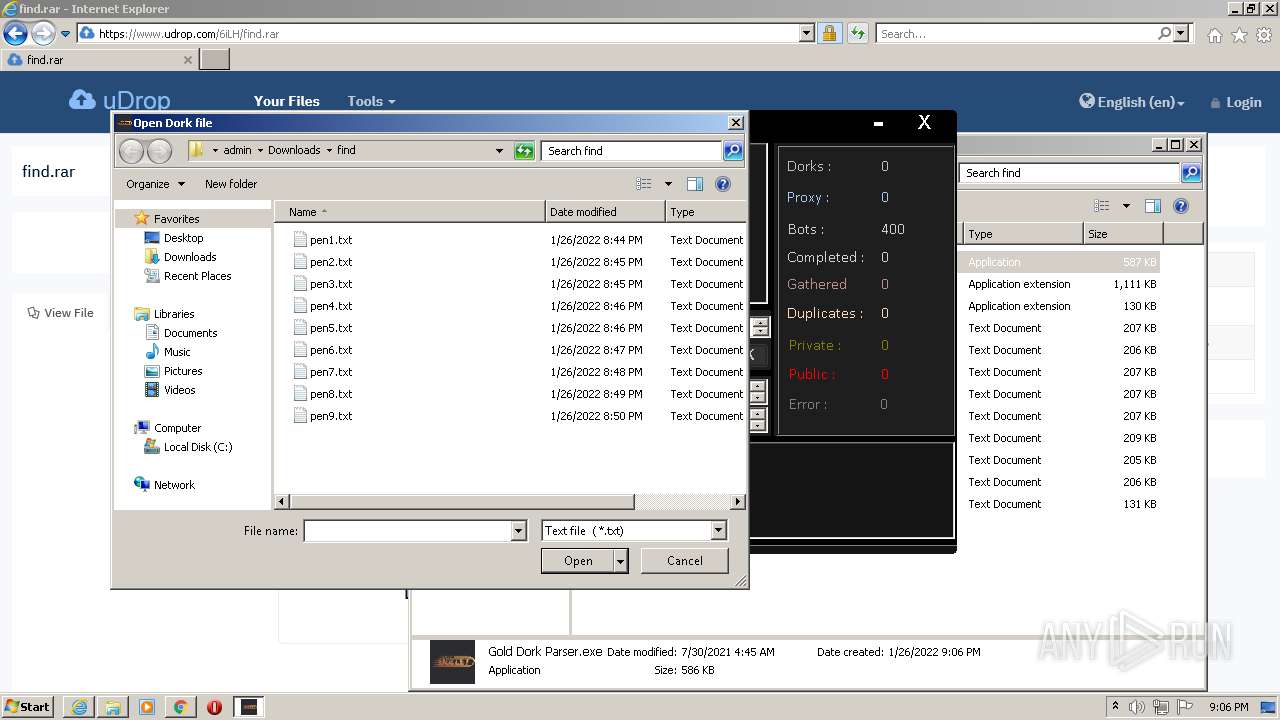
Executable files
3
Suspicious files
188
Text files
205
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RQ9S7RGC.txt | text | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5BC0F345944148EB6CA31E060E457F9D_DEFB822B92348051F4B31FFEA0106719 | binary | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\find[1].htm | html | |
MD5:— | SHA256:— | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3004 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5BC0F345944148EB6CA31E060E457F9D_DEFB822B92348051F4B31FFEA0106719 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
845
TCP/UDP connections
1 635
DNS requests
41
Threats
2
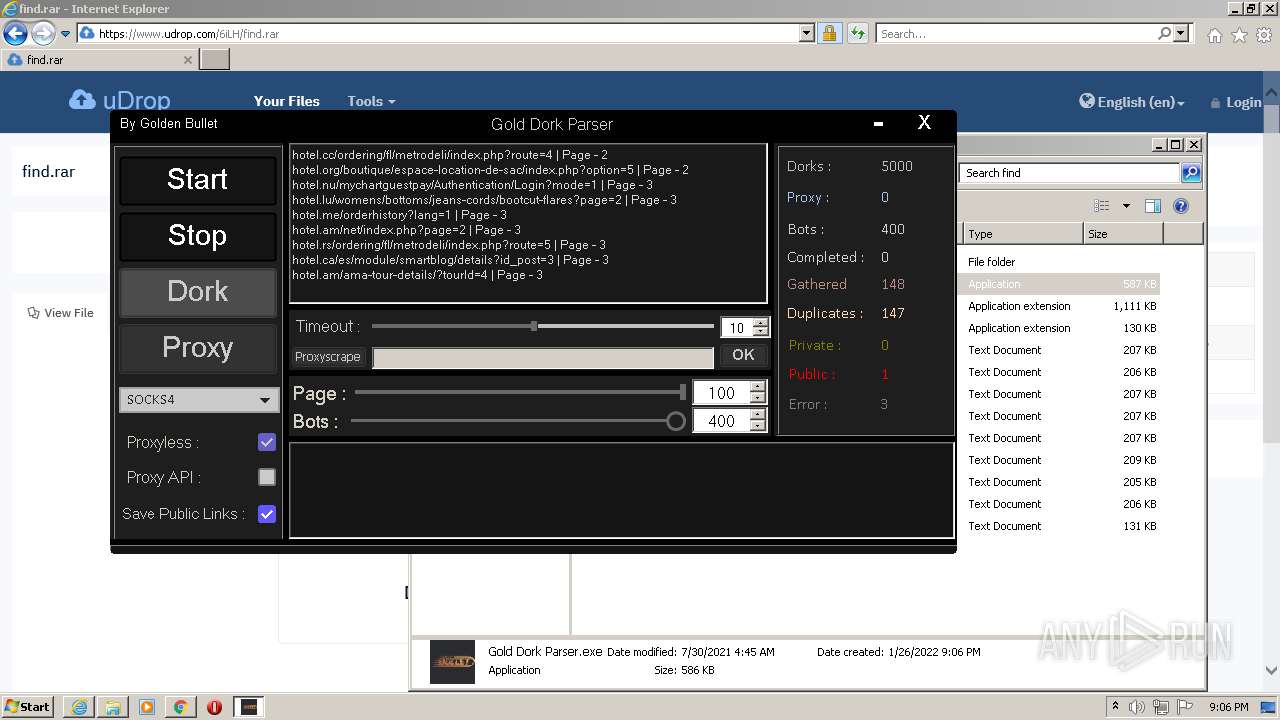
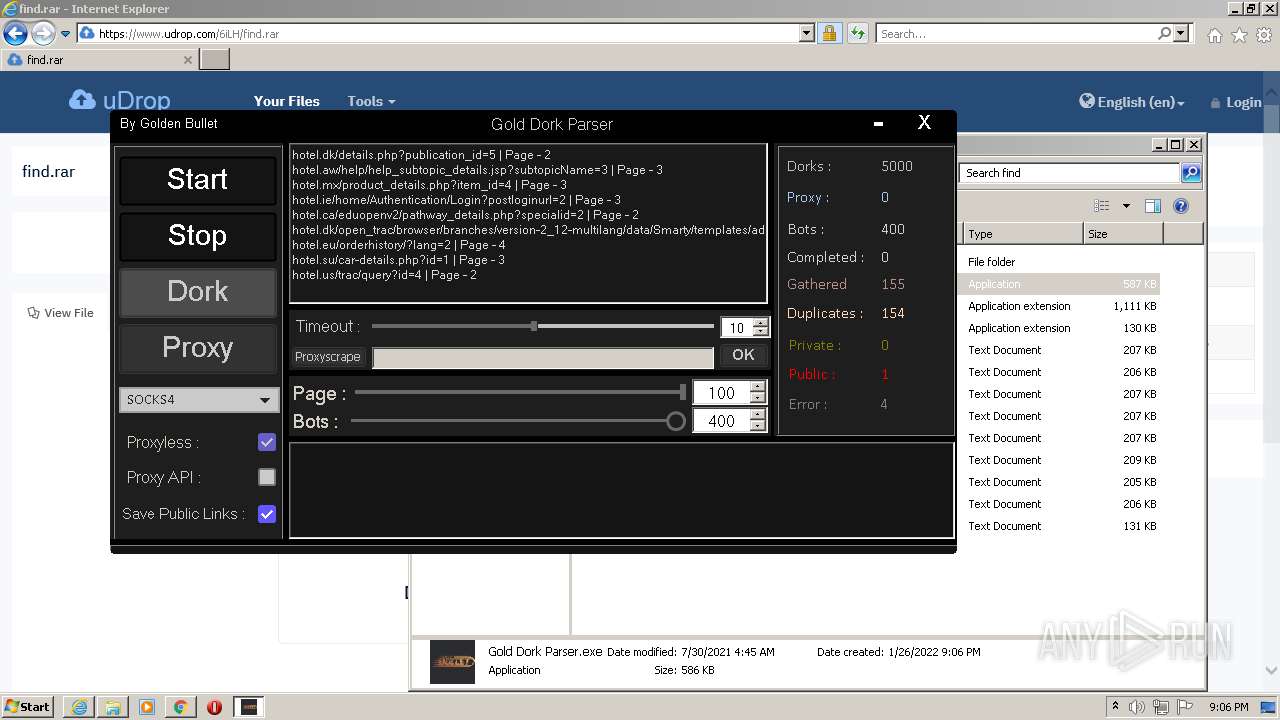
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1000 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=hotel.rs%2fs%2fRefArch%2forders%3flang%3d4&first=0&last=50&count=50 | US | — | — | whitelisted |
1000 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=hotel.gg%2fcvstrac%2frptview%3frn%3d4&first=0&last=50&count=50 | US | — | — | whitelisted |
1000 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=hotel.ca%2fcgi-bin%2fcontent%2fview.php%3fdata%3d3&first=0&last=50&count=50 | US | — | — | whitelisted |
1000 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=hotel.lk%2fProductDetails.asp%3fProductCode%3d4&first=0&last=50&count=50 | US | — | — | whitelisted |
1000 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=hotel.th%2fproduct-details.php%3fproduct_id%3d1&first=0&last=50&count=50 | US | — | — | whitelisted |
1000 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=hotel.pk%2fcar-details.php%3fid%3d3&first=0&last=50&count=50 | US | — | — | whitelisted |
1000 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=hotel.kr%2fjp%2fcatalog%2fdetails.php%3fid%3d4&first=0&last=50&count=50 | US | — | — | whitelisted |
1000 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=hotel.am%2fcvstrac%2frptview%3frn%3d4&first=0&last=50&count=50 | US | — | — | whitelisted |
3004 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3004 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
532 | iexplore.exe | 192.124.249.36:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3004 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3780 | chrome.exe | 142.250.186.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3780 | chrome.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
532 | iexplore.exe | 65.103.40.169:443 | www.udrop.com | Qwest Communications Company, LLC | US | suspicious |
3780 | chrome.exe | 142.250.185.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3780 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
3780 | chrome.exe | 142.250.186.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3780 | chrome.exe | 142.250.185.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3780 | chrome.exe | 142.250.186.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.udrop.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1000 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M2 |
1000 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M2 |