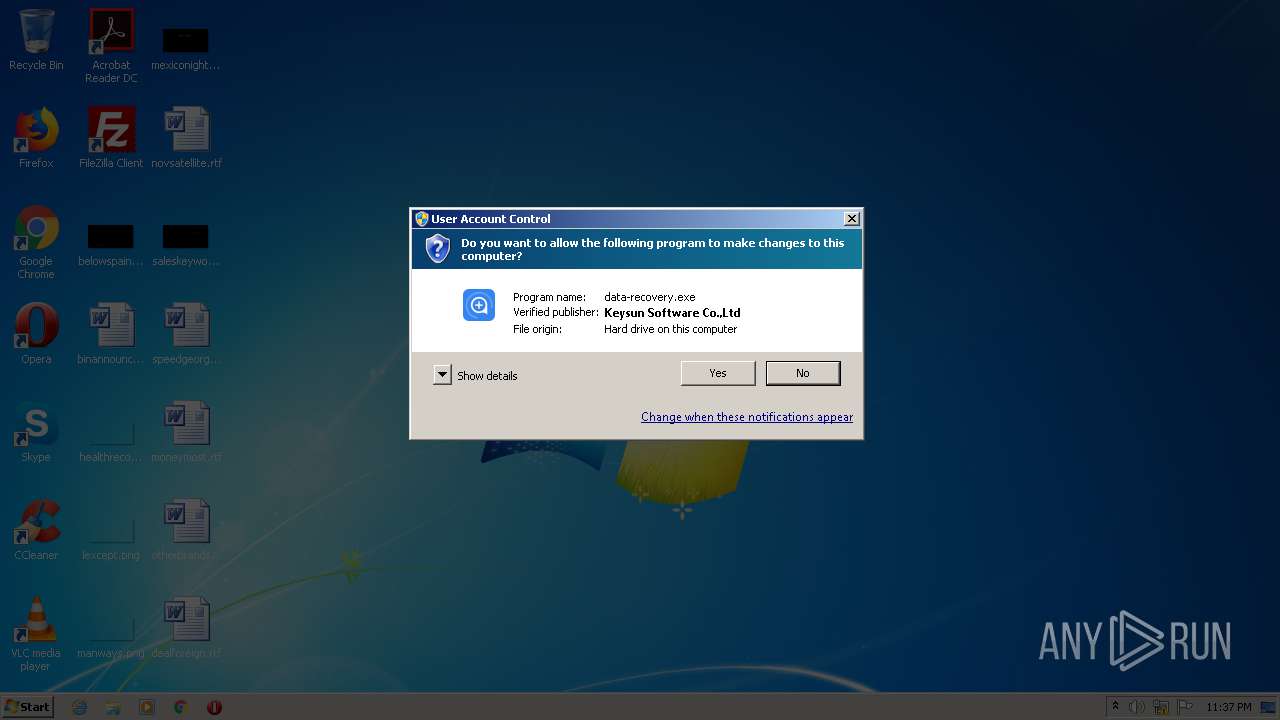
| File name: | data-recovery.exe |
| Full analysis: | https://app.any.run/tasks/75c60728-8463-4a0c-a16b-94f6d6bc9259 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2021, 22:37:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | ECCF49CF2972508A60F6BD2E1CAA297E |
| SHA1: | 81CB76E320184EDF774CEB9BE197AF126489C876 |
| SHA256: | 432A88E04D8A4263347498A23A93947FB29ED43A82B9F9429AB3A156F1A4F74E |
| SSDEEP: | 49152:ACJH9Cx9evgGWIz+Sq5Yaymq22se96li+6+n9+q:A0E2vgdd0/22sYYUW |
MALICIOUS
Drops executable file immediately after starts
- data-recovery.exe (PID: 2788)
- data-recovery.tmp (PID: 1276)
- data-recovery-x86.tmp (PID: 3592)
- data-recovery-x86.exe (PID: 1200)
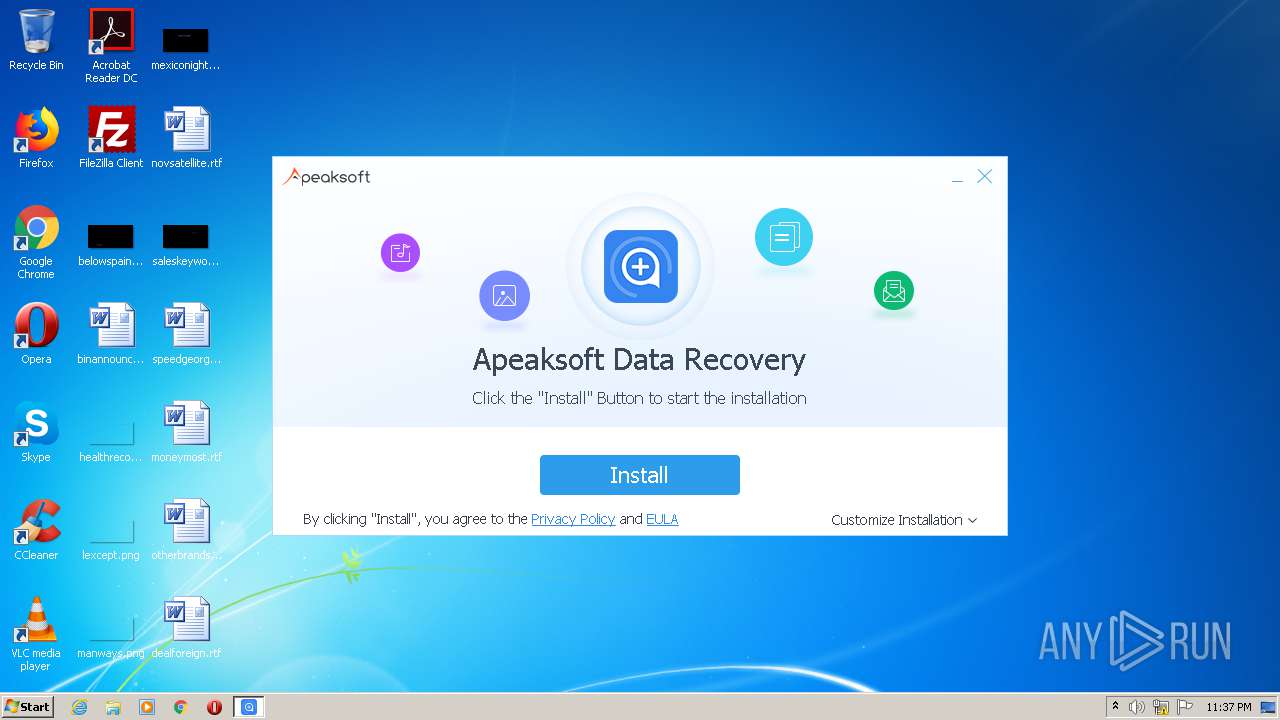
Application was dropped or rewritten from another process
- data-recovery-x86.exe (PID: 1200)
- Apeaksoft Data Recovery.exe (PID: 4052)
- Apeaksoft Data Recovery.exe (PID: 1360)
- Apeaksoft Data Recovery.exe (PID: 972)
- Apeaksoft Data Recovery.exe (PID: 2668)
- CEIPPost.exe (PID: 1948)
- splashScreen.exe (PID: 3608)
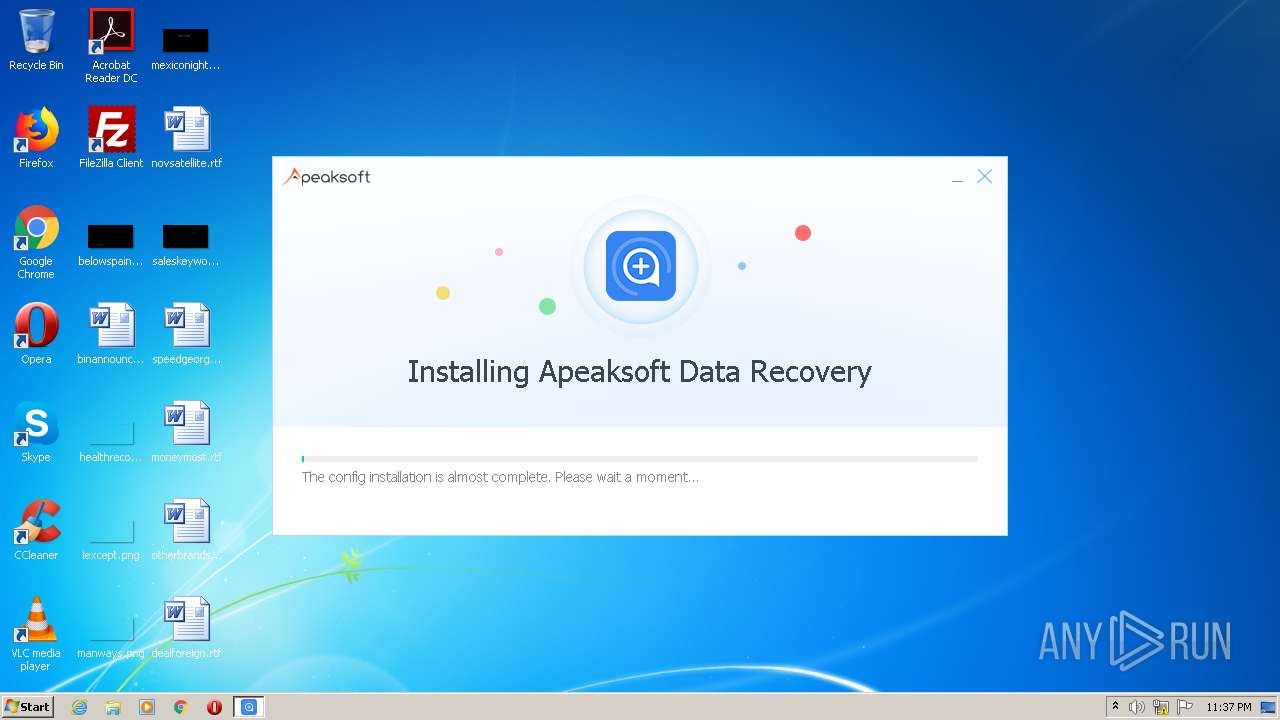
Loads dropped or rewritten executable
- Apeaksoft Data Recovery.exe (PID: 4052)
- Apeaksoft Data Recovery.exe (PID: 1360)
- Apeaksoft Data Recovery.exe (PID: 972)
- CEIPPost.exe (PID: 1948)
- Apeaksoft Data Recovery.exe (PID: 2668)
- splashScreen.exe (PID: 3608)
SUSPICIOUS
Executable content was dropped or overwritten
- data-recovery.exe (PID: 2788)
- data-recovery.tmp (PID: 1276)
- data-recovery-x86.exe (PID: 1200)
- data-recovery-x86.tmp (PID: 3592)
Reads Windows owner or organization settings
- data-recovery.tmp (PID: 1276)
- data-recovery-x86.tmp (PID: 3592)
Drops a file that was compiled in debug mode
- data-recovery.tmp (PID: 1276)
- data-recovery-x86.tmp (PID: 3592)
Reads the Windows organization settings
- data-recovery.tmp (PID: 1276)
- data-recovery-x86.tmp (PID: 3592)
Creates a directory in Program Files
- data-recovery.tmp (PID: 1276)
- data-recovery-x86.tmp (PID: 3592)
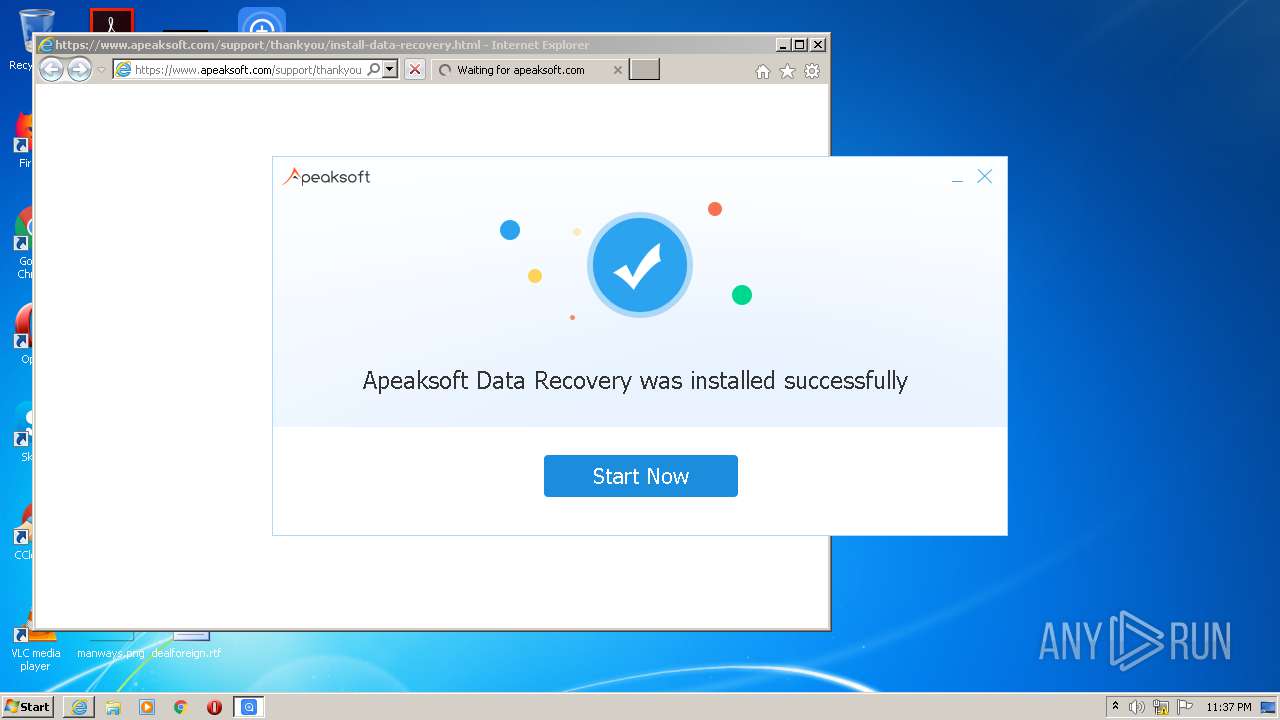
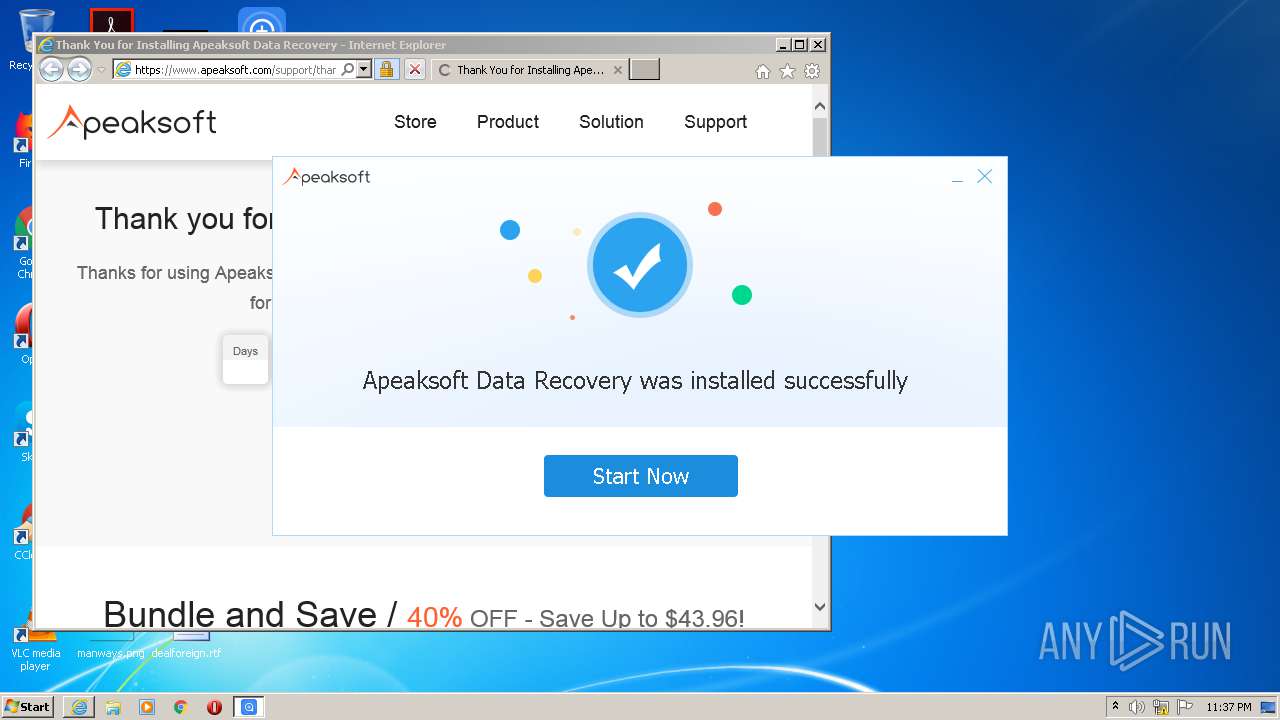
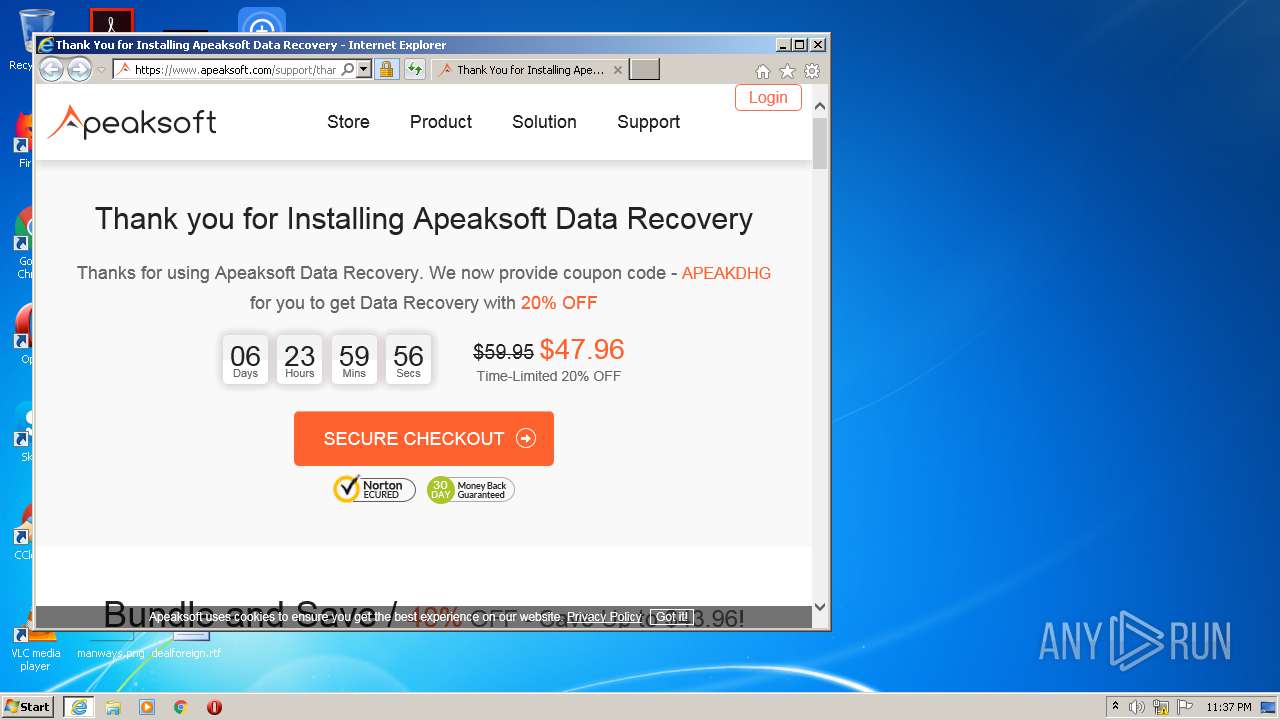
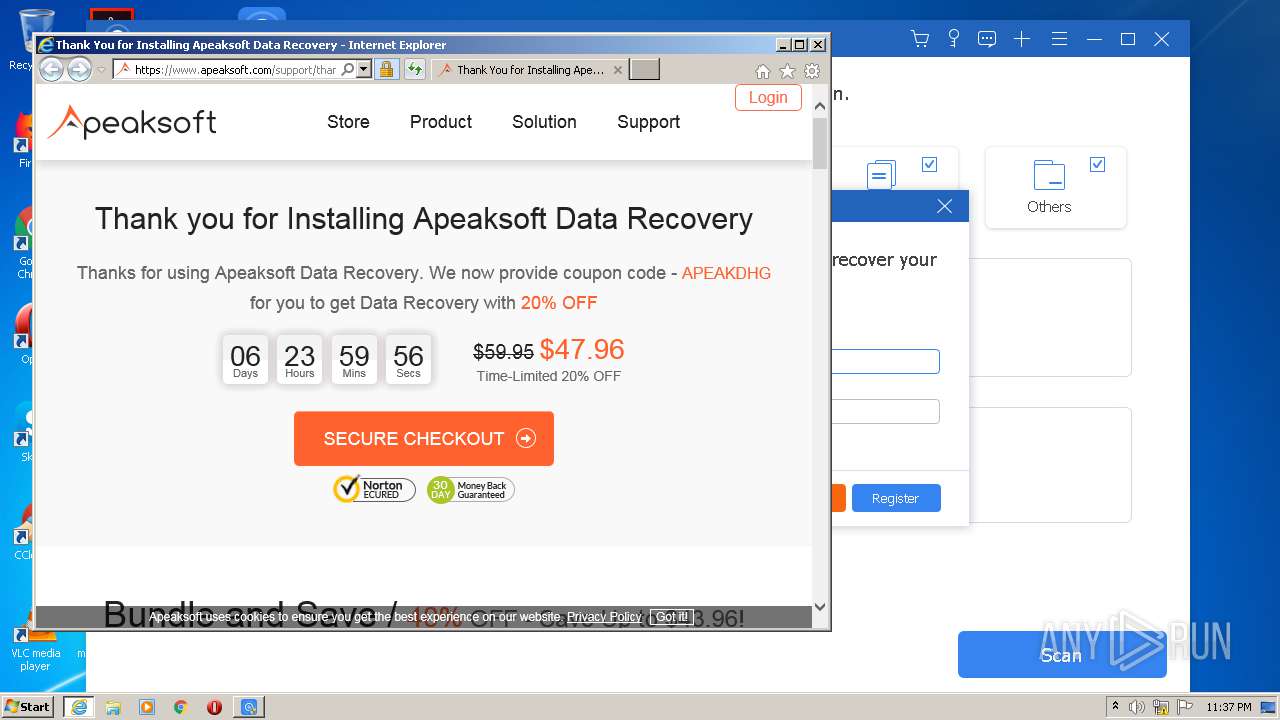
Starts Internet Explorer
- Apeaksoft Data Recovery.exe (PID: 4052)
Creates files in the user directory
- data-recovery-x86.tmp (PID: 3592)
Low-level read access rights to disk partition
- Apeaksoft Data Recovery.exe (PID: 2668)
INFO
Loads dropped or rewritten executable
- data-recovery.tmp (PID: 1276)
Reads the hosts file
- data-recovery.tmp (PID: 1276)
- CEIPPost.exe (PID: 1948)
Application was dropped or rewritten from another process
- data-recovery.tmp (PID: 1276)
- data-recovery-x86.tmp (PID: 3592)
Creates files in the program directory
- data-recovery.tmp (PID: 1276)
- data-recovery-x86.tmp (PID: 3592)
Dropped object may contain Bitcoin addresses
- data-recovery-x86.tmp (PID: 3592)
Creates a software uninstall entry
- data-recovery-x86.tmp (PID: 3592)
Changes internet zones settings
- iexplore.exe (PID: 3184)
Application launched itself
- iexplore.exe (PID: 3184)
Reads settings of System Certificates
- Apeaksoft Data Recovery.exe (PID: 972)
- iexplore.exe (PID: 124)
Changes settings of System certificates
- iexplore.exe (PID: 124)
Adds / modifies Windows certificates
- iexplore.exe (PID: 124)
Reads internet explorer settings
- iexplore.exe (PID: 124)
Creates files in the user directory
- iexplore.exe (PID: 124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (62.6) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (21.3) |
| .exe | | | Win32 Executable (generic) (6.7) |
| .exe | | | Win16/32 Executable Delphi generic (3.1) |
| .exe | | | Generic Win/DOS Executable (3) |
EXIF
EXE
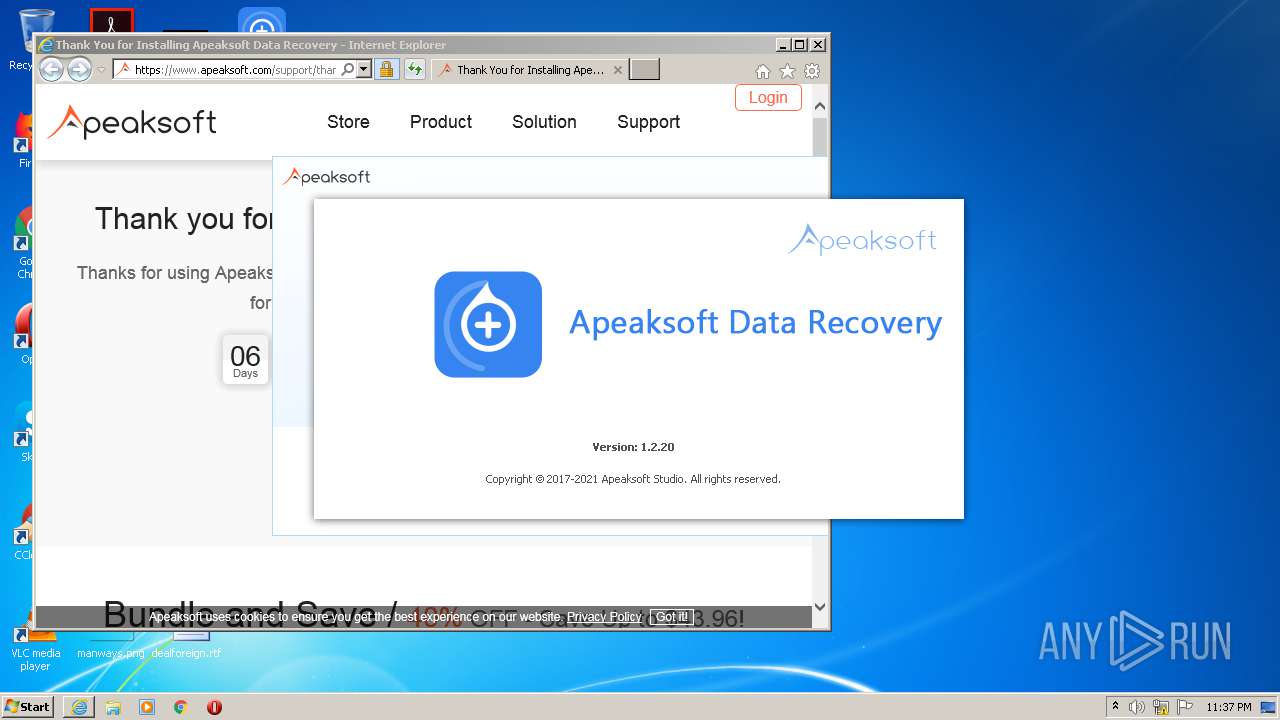
| ProductVersion: | 1.2.20 |
|---|---|
| ProductName: | |
| LegalCopyright: | |
| FileVersion: | 1.2.20 |
| FileDescription: | |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.2.20.0 |
| FileVersionNumber: | 1.2.20.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x177f4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 76288 |
| CodeSize: | 93696 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2017:01:09 10:57:06+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Jan-2017 09:57:06 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.2.20 |
| LegalCopyright: | - |
| ProductName: | - |
| ProductVersion: | 1.2.20 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 09-Jan-2017 09:57:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00015D54 | 0x00015E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31031 |
.itext | 0x00017000 | 0x00000F7C | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.80904 |
.data | 0x00018000 | 0x00000F0C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74007 |
.bss | 0x00019000 | 0x0000579C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001F000 | 0x00000F3E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.86171 |
.tls | 0x00020000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00021000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.170146 |
.rsrc | 0x00022000 | 0x00010734 | 0x00010800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.76417 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.15342 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.8922 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.85098 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.13696 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.29972 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.90633 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.85106 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.48574 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.77471 | 156 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.27116 | 204 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
53
Monitored processes
13
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3184 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 932 | "C:\Users\admin\AppData\Local\Temp\data-recovery.exe" | C:\Users\admin\AppData\Local\Temp\data-recovery.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 1.2.20 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Apeaksoft\Apeaksoft Data Recovery\Apeaksoft Data Recovery.exe" --access_after_install_counting_url | C:\Program Files\Apeaksoft\Apeaksoft Data Recovery\Apeaksoft Data Recovery.exe | data-recovery-x86.tmp | ||||||||||||
User: admin Company: Apeaksoft Integrity Level: HIGH Description: Apeaksoft Data Recovery Exit code: 0 Version: 1.2.20.105524 Modules
| |||||||||||||||
| 1200 | "C:\Users\admin\AppData\Local\Temp\Apeaksoft Data Recovery\data-recovery-x86.exe" /user:administrator /sp- /VerySilent /TASKS="forallusers,desktopicon,quicklaunchicon,ceip" /DIR="C:\Program Files\Apeaksoft\Apeaksoft Data Recovery" | C:\Users\admin\AppData\Local\Temp\Apeaksoft Data Recovery\data-recovery-x86.exe | data-recovery.tmp | ||||||||||||
User: admin Company: Apeaksoft Studio Integrity Level: HIGH Description: Exit code: 0 Version: 1.2.20 Modules
| |||||||||||||||
| 1276 | "C:\Users\admin\AppData\Local\Temp\is-2AQNP.tmp\data-recovery.tmp" /SL5="$6013C,1280576,171008,C:\Users\admin\AppData\Local\Temp\data-recovery.exe" | C:\Users\admin\AppData\Local\Temp\is-2AQNP.tmp\data-recovery.tmp | data-recovery.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Apeaksoft\Apeaksoft Data Recovery\Apeaksoft Data Recovery.exe" --register | C:\Program Files\Apeaksoft\Apeaksoft Data Recovery\Apeaksoft Data Recovery.exe | — | data-recovery-x86.tmp | |||||||||||
User: admin Company: Apeaksoft Integrity Level: HIGH Description: Apeaksoft Data Recovery Exit code: 0 Version: 1.2.20.105524 Modules
| |||||||||||||||
| 1948 | "C:\Users\admin\AppData\Local\Temp\Apeaksoft Data Recovery\CEIP\CEIPPost.exe" "C:\Users\admin\AppData\Local\Temp\Apeaksoft Data Recovery\CEIP" "https://ceip.apeaksoft.com/v1/?p=18" | C:\Users\admin\AppData\Local\Temp\Apeaksoft Data Recovery\CEIP\CEIPPost.exe | data-recovery.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Apeaksoft\Apeaksoft Data Recovery\Apeaksoft Data Recovery.exe" D | C:\Program Files\Apeaksoft\Apeaksoft Data Recovery\Apeaksoft Data Recovery.exe | data-recovery.tmp | ||||||||||||
User: admin Company: Apeaksoft Integrity Level: HIGH Description: Apeaksoft Data Recovery Exit code: 0 Version: 1.2.20.105524 Modules
| |||||||||||||||
| 2788 | "C:\Users\admin\AppData\Local\Temp\data-recovery.exe" | C:\Users\admin\AppData\Local\Temp\data-recovery.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 1 Version: 1.2.20 Modules
| |||||||||||||||
| 3184 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.apeaksoft.com/support/thankyou/install-data-recovery.html | C:\Program Files\Internet Explorer\iexplore.exe | Apeaksoft Data Recovery.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 403
Read events
1 253
Write events
140
Delete events
10
Modification events
| (PID) Process: | (1276) data-recovery.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: FC040000489E790EA44AD701 | |||
| (PID) Process: | (1276) data-recovery.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 6BC2225F0CE29B794C4032ECFE88C7BB108CA97A9EC50D59FEB2C3B9390258E6 | |||
| (PID) Process: | (1276) data-recovery.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1276) data-recovery.tmp | Key: | HKEY_CLASSES_ROOT\CLSID\{DB8A74C3-8F3E-4711-B152-436BDD91DAE1} |
| Operation: | write | Name: | CEIPIdentifier |
Value: 7318D20A-DC4A-491a-96B2-5FDAF4D9539E | |||
| (PID) Process: | (3592) data-recovery-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: 080E0000BAEE0015A44AD701 | |||
| (PID) Process: | (3592) data-recovery-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: FF300DE4DA2E1EED51E38B625F48F067529C1FD9AA96BD2D4DA7F72B8CD1A649 | |||
| (PID) Process: | (3592) data-recovery-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3592) data-recovery-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Apeaksoft\Apeaksoft Data Recovery\Apeaksoft Data Recovery.exe | |||
| (PID) Process: | (3592) data-recovery-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFilesHash |
Value: AE56037D5EF026D08BF252F12B6DCF0533218225E47D3FA1E3AD784E00ACA61E | |||
| (PID) Process: | (3592) data-recovery-x86.tmp | Key: | HKEY_CURRENT_USER\Software\Apeaksoft Studio\Apeaksoft Data Recovery |
| Operation: | write | Name: | Language |
Value: | |||
Executable files
61
Suspicious files
27
Text files
271
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1276 | data-recovery.tmp | C:\Users\admin\AppData\Local\Temp\is-HQDM9.tmp\affiliate.xml | xml | |
MD5:— | SHA256:— | |||
| 2788 | data-recovery.exe | C:\Users\admin\AppData\Local\Temp\is-2AQNP.tmp\data-recovery.tmp | executable | |
MD5:— | SHA256:— | |||
| 1276 | data-recovery.tmp | C:\Users\admin\AppData\Local\Temp\is-HQDM9.tmp\MessageBox_fr.xml | xml | |
MD5:— | SHA256:— | |||
| 1276 | data-recovery.tmp | C:\Users\admin\AppData\Local\Temp\is-HQDM9.tmp\MessageBox_de.xml | xml | |
MD5:— | SHA256:— | |||
| 1276 | data-recovery.tmp | C:\Users\admin\AppData\Local\Temp\is-HQDM9.tmp\MessageBox_ja.xml | xml | |
MD5:— | SHA256:— | |||
| 1276 | data-recovery.tmp | C:\Users\admin\AppData\Local\Temp\is-HQDM9.tmp\MessageBox_tw.xml | xml | |
MD5:— | SHA256:— | |||
| 1276 | data-recovery.tmp | C:\Users\admin\AppData\Local\Temp\is-HQDM9.tmp\MessageBox_pt.xml | xml | |
MD5:— | SHA256:— | |||
| 1276 | data-recovery.tmp | C:\Users\admin\AppData\Local\Temp\is-HQDM9.tmp\MessageBox.xml | xml | |
MD5:— | SHA256:— | |||
| 1276 | data-recovery.tmp | C:\Users\admin\AppData\Local\Temp\is-HQDM9.tmp\skin_de.xml | xml | |
MD5:— | SHA256:— | |||
| 1276 | data-recovery.tmp | C:\Users\admin\AppData\Local\Temp\is-HQDM9.tmp\MessageBox_zh.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
36
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
124 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
124 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
124 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
124 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
124 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
124 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
124 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDvBKQuWMzhNCQAAAABiFes%3D | US | der | 471 b | whitelisted |
124 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
124 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDvBKQuWMzhNCQAAAABiFes%3D | US | der | 471 b | whitelisted |
124 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1276 | data-recovery.tmp | 99.86.2.25:443 | downloads.apeaksoft.com | AT&T Services, Inc. | US | unknown |
1276 | data-recovery.tmp | 99.86.2.19:443 | downloads.apeaksoft.com | AT&T Services, Inc. | US | suspicious |
1276 | data-recovery.tmp | 99.86.2.61:443 | downloads.apeaksoft.com | AT&T Services, Inc. | US | suspicious |
972 | Apeaksoft Data Recovery.exe | 208.43.242.90:443 | stats.apeaksoft.net | SoftLayer Technologies Inc. | US | unknown |
124 | iexplore.exe | 208.43.242.88:443 | www.apeaksoft.com | SoftLayer Technologies Inc. | US | unknown |
124 | iexplore.exe | 192.124.249.36:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
124 | iexplore.exe | 192.124.249.22:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
124 | iexplore.exe | 44.224.167.25:443 | member.apeaksoft.com | University of California, San Diego | US | unknown |
124 | iexplore.exe | 104.21.50.93:443 | gtranslate.net | Cloudflare Inc | US | malicious |
124 | iexplore.exe | 104.20.60.238:443 | cdn.paddle.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
downloads.apeaksoft.com |
| suspicious |
stats.apeaksoft.net |
| unknown |
www.apeaksoft.com |
| unknown |
ocsp.godaddy.com |
| whitelisted |
member.apeaksoft.com |
| unknown |
gtranslate.net |
| suspicious |
cdn.paddle.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |