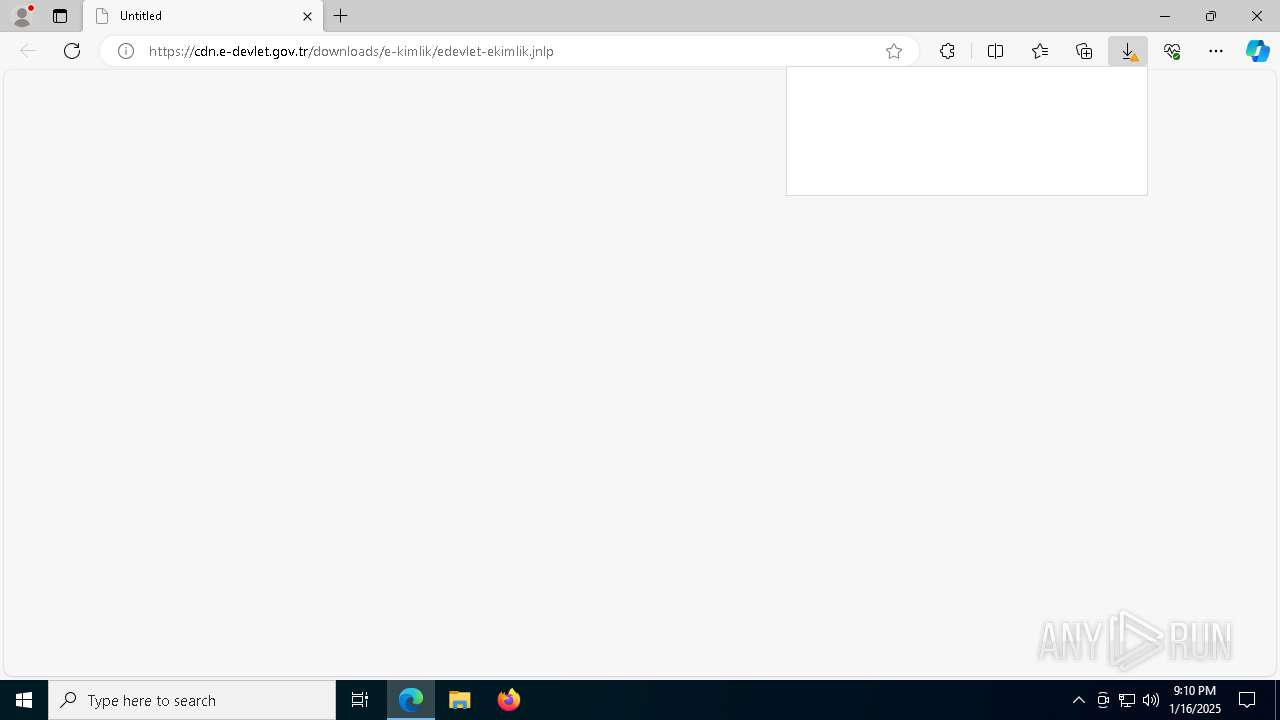
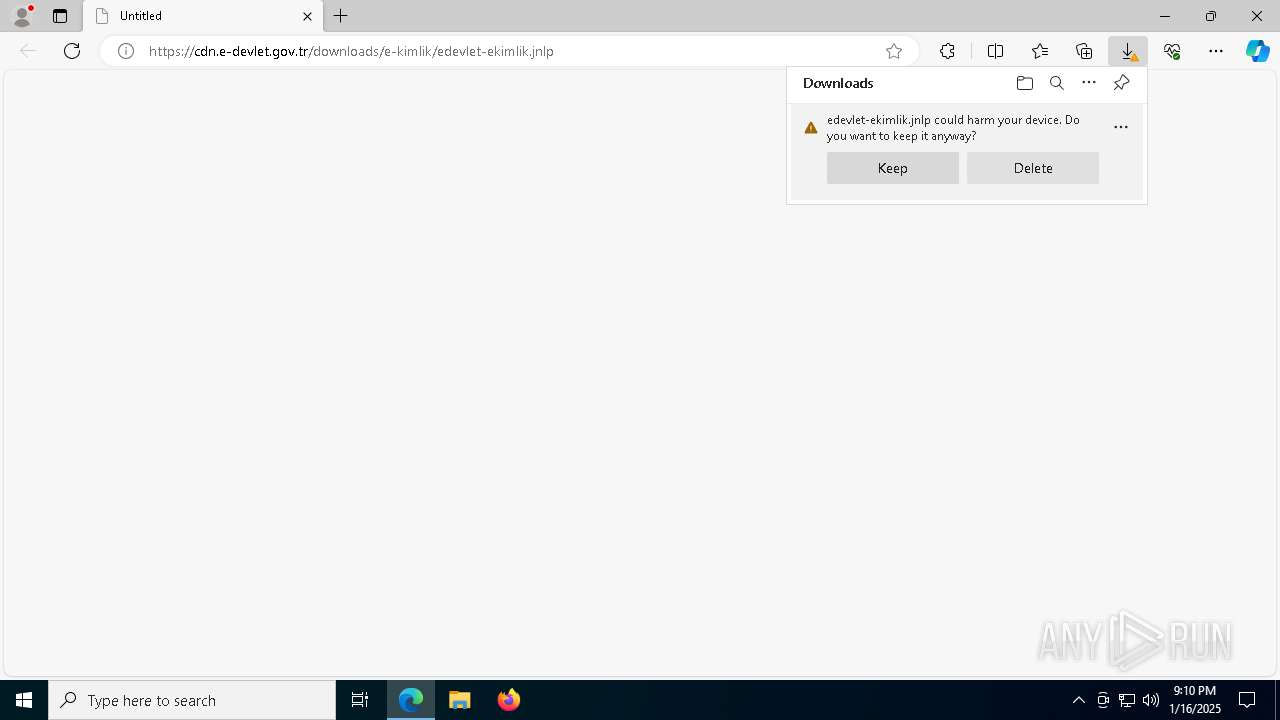
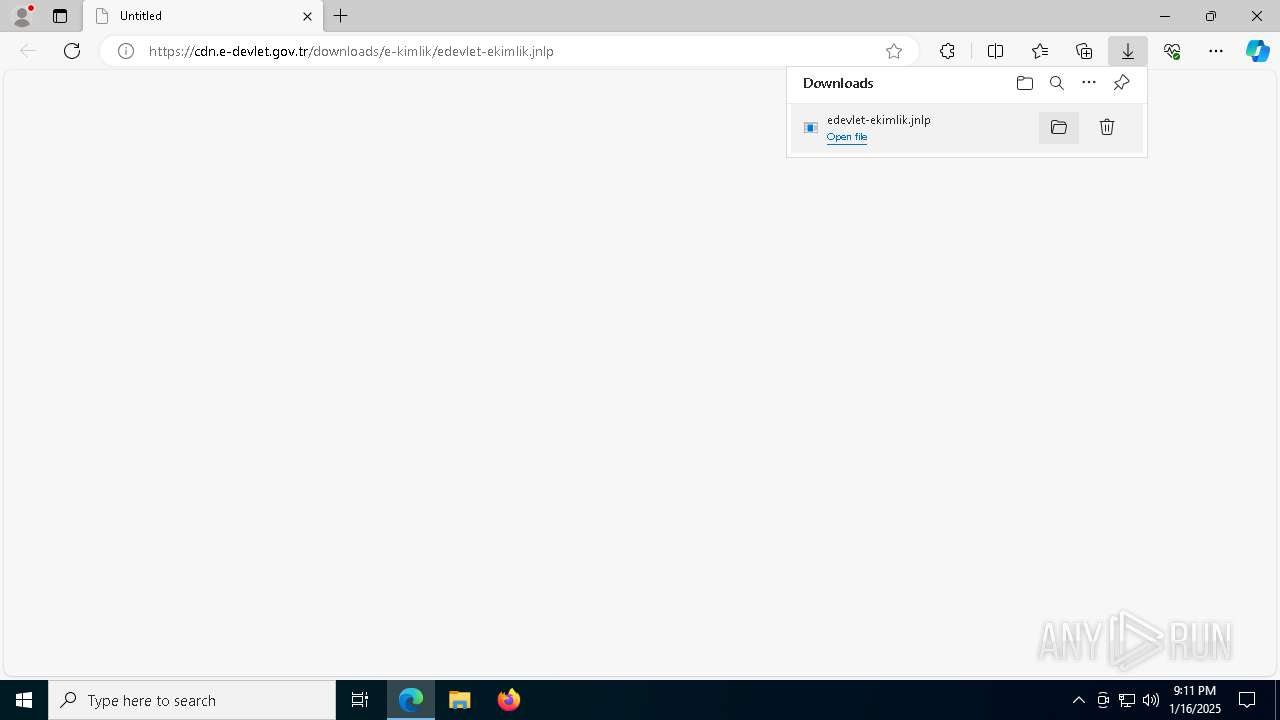
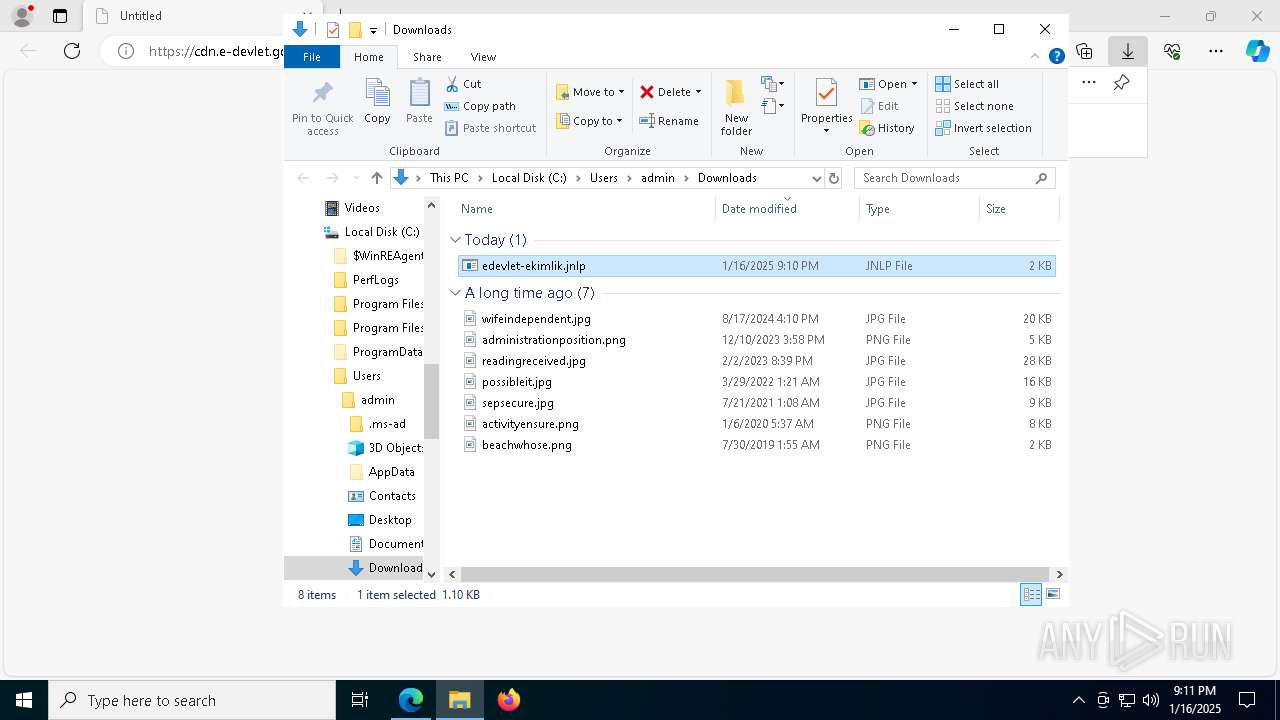
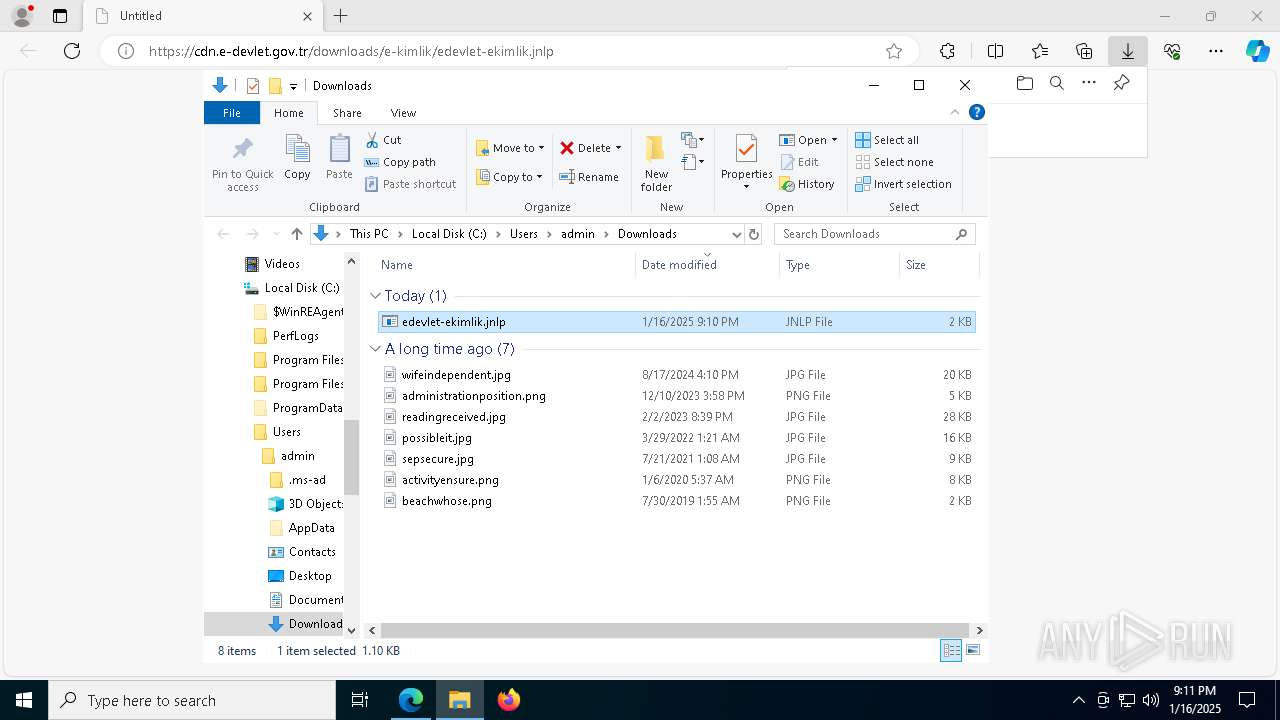
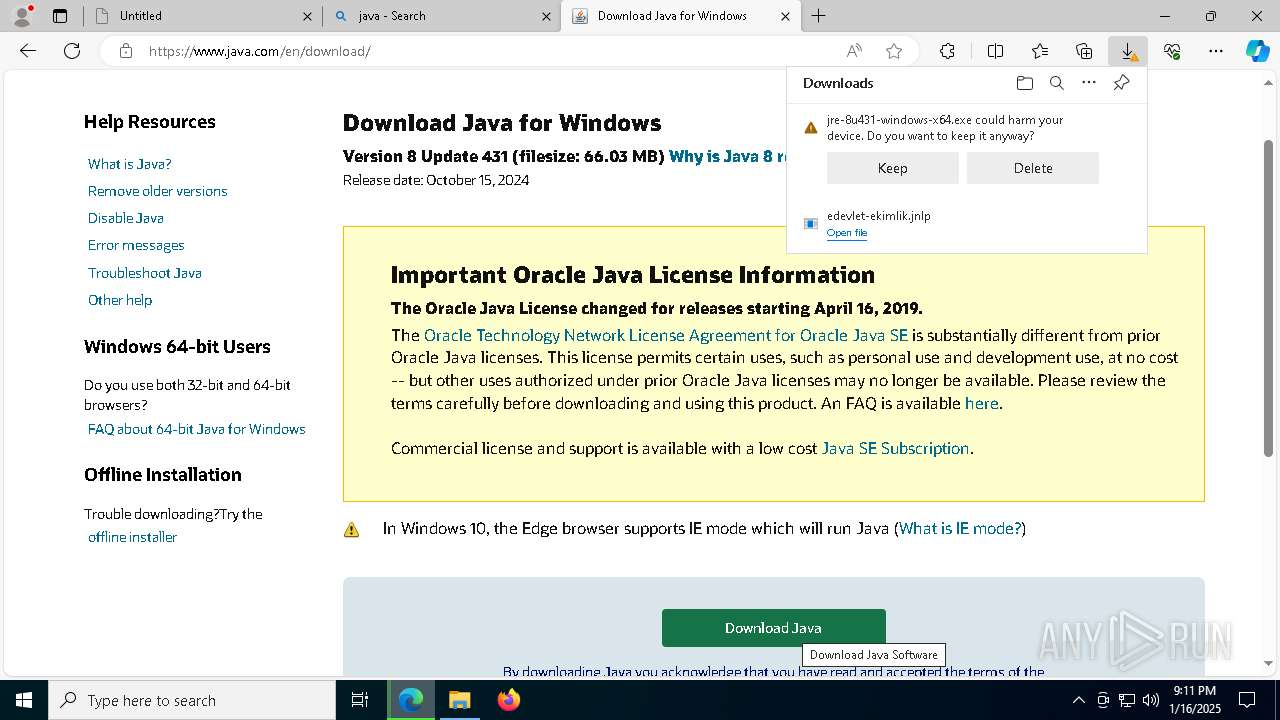
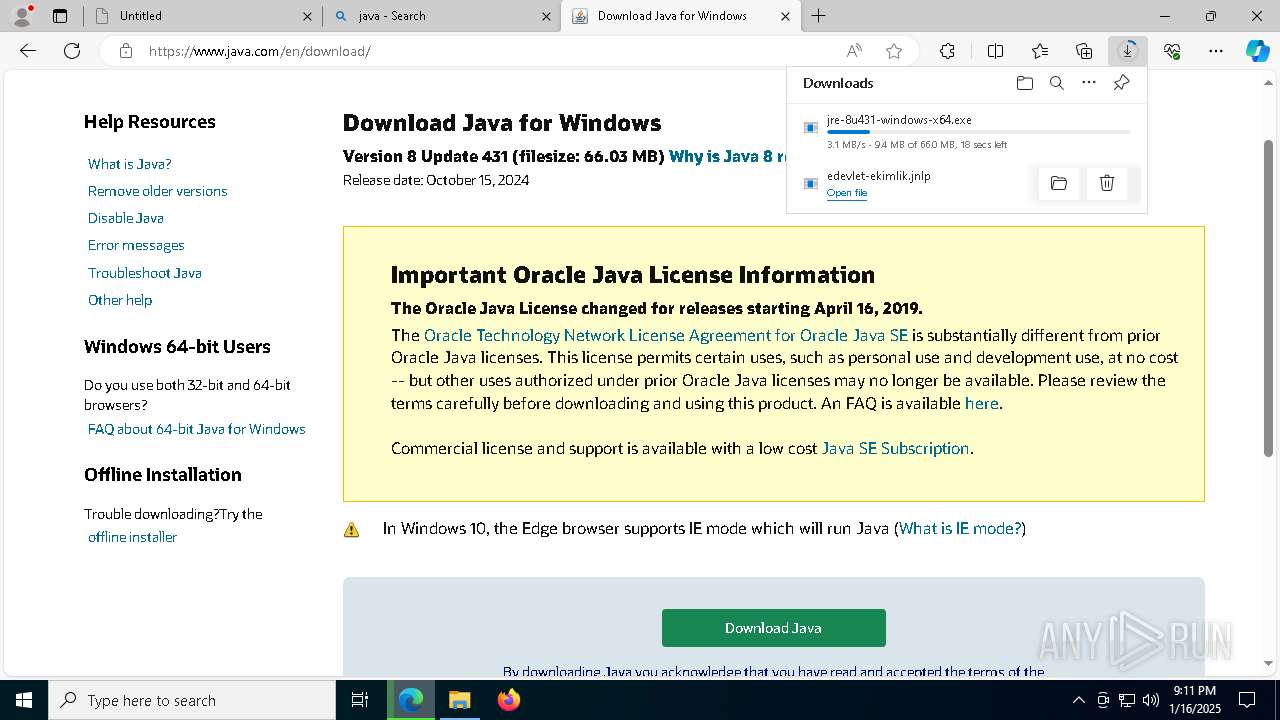
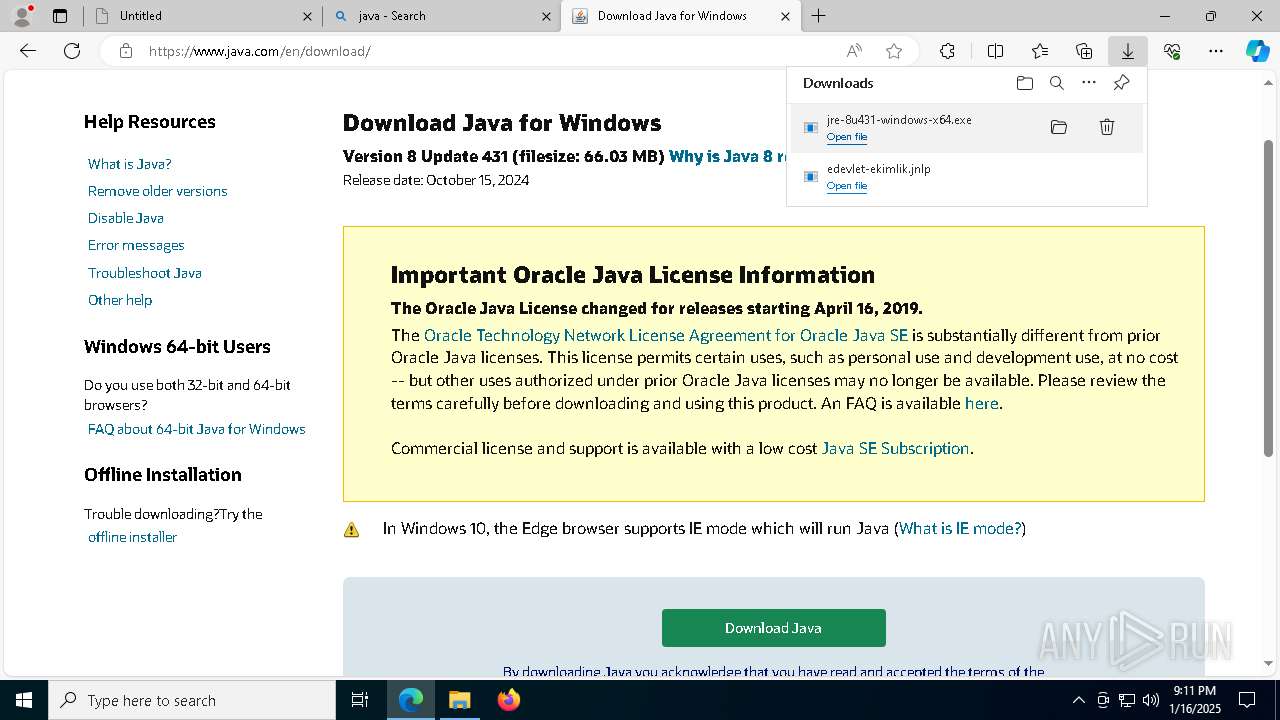
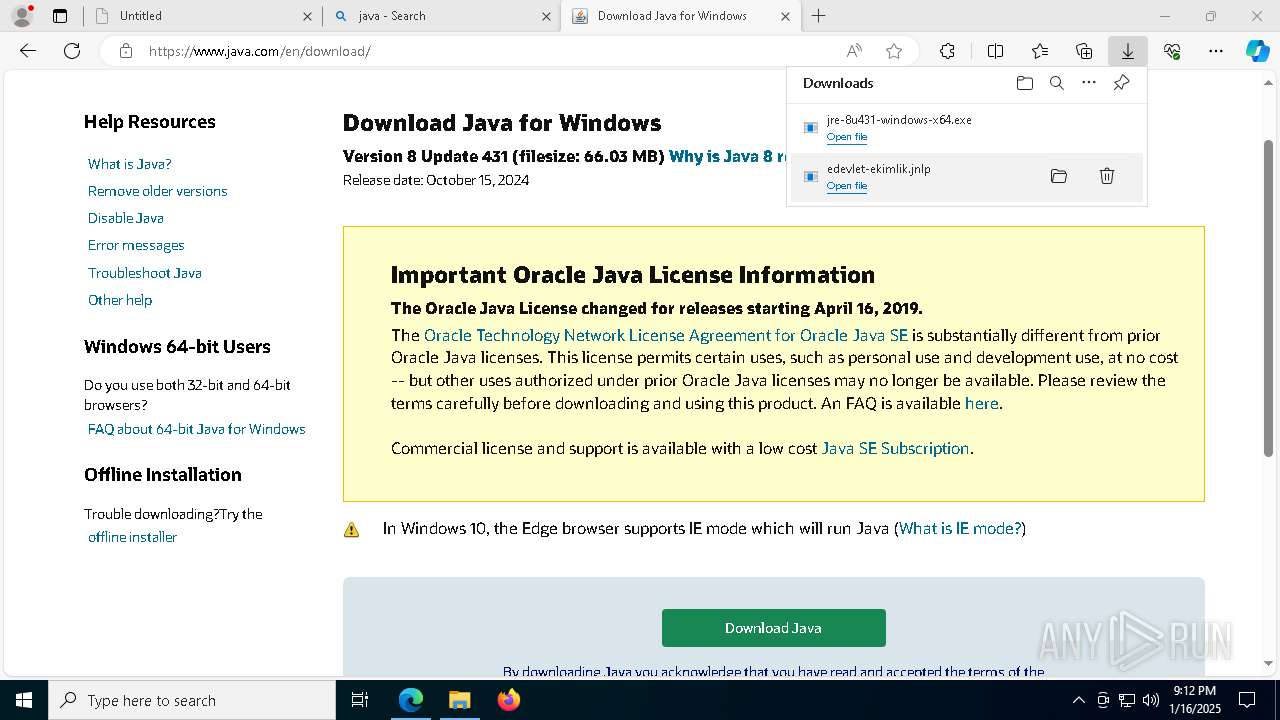
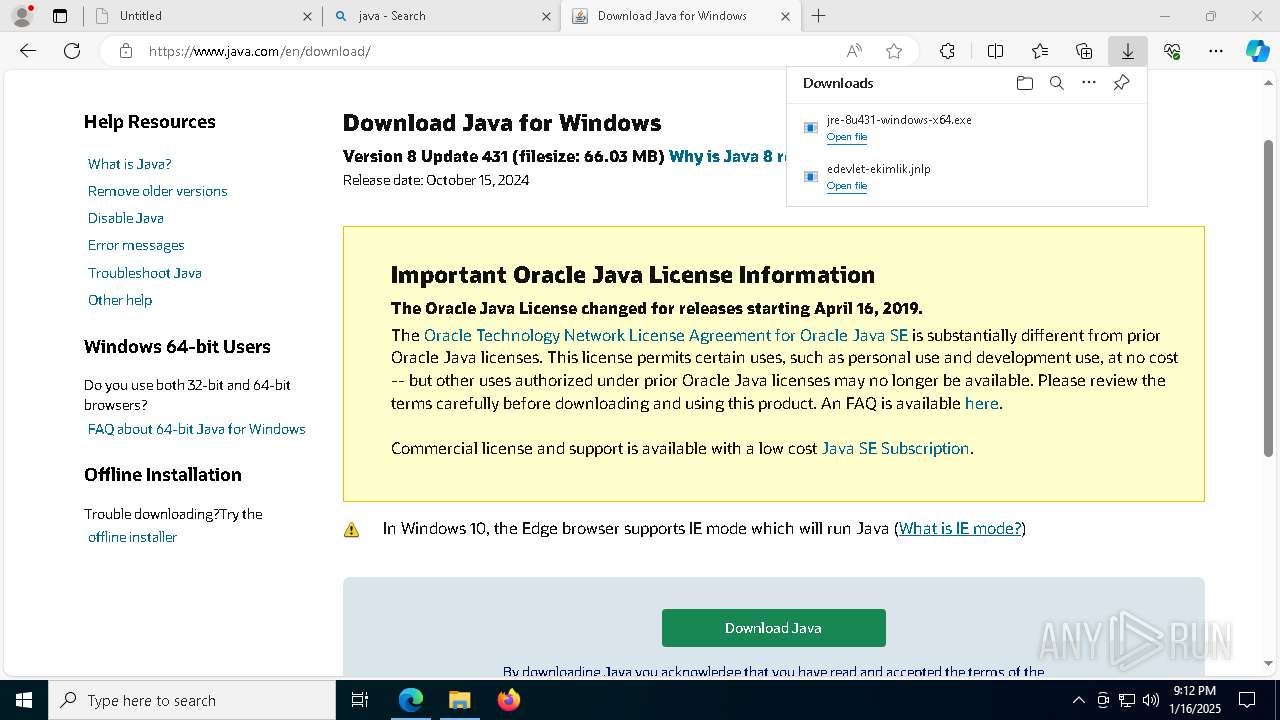
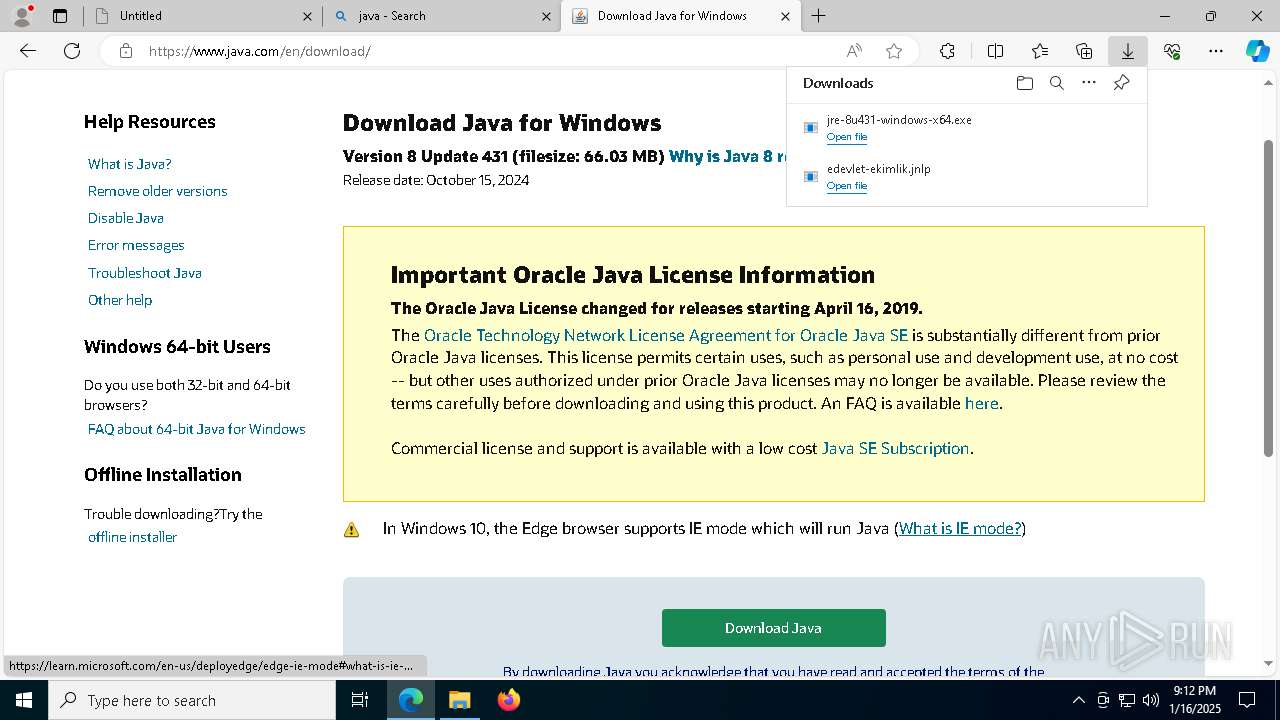
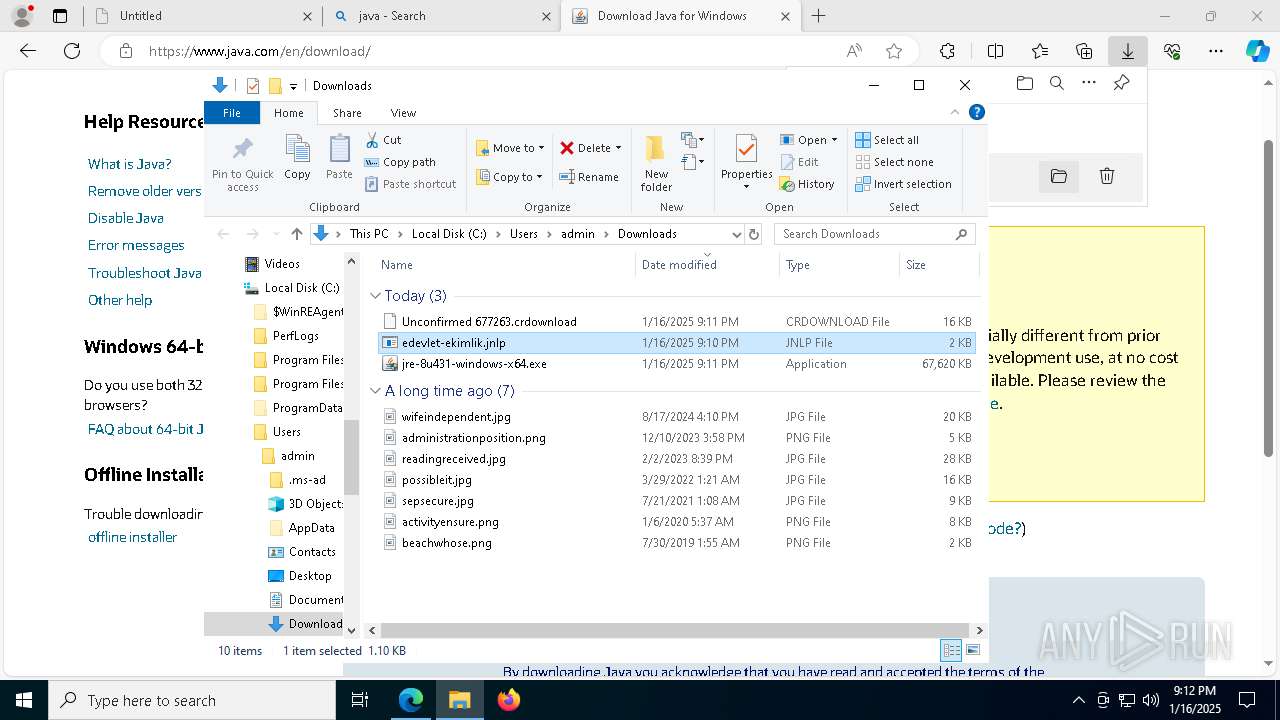
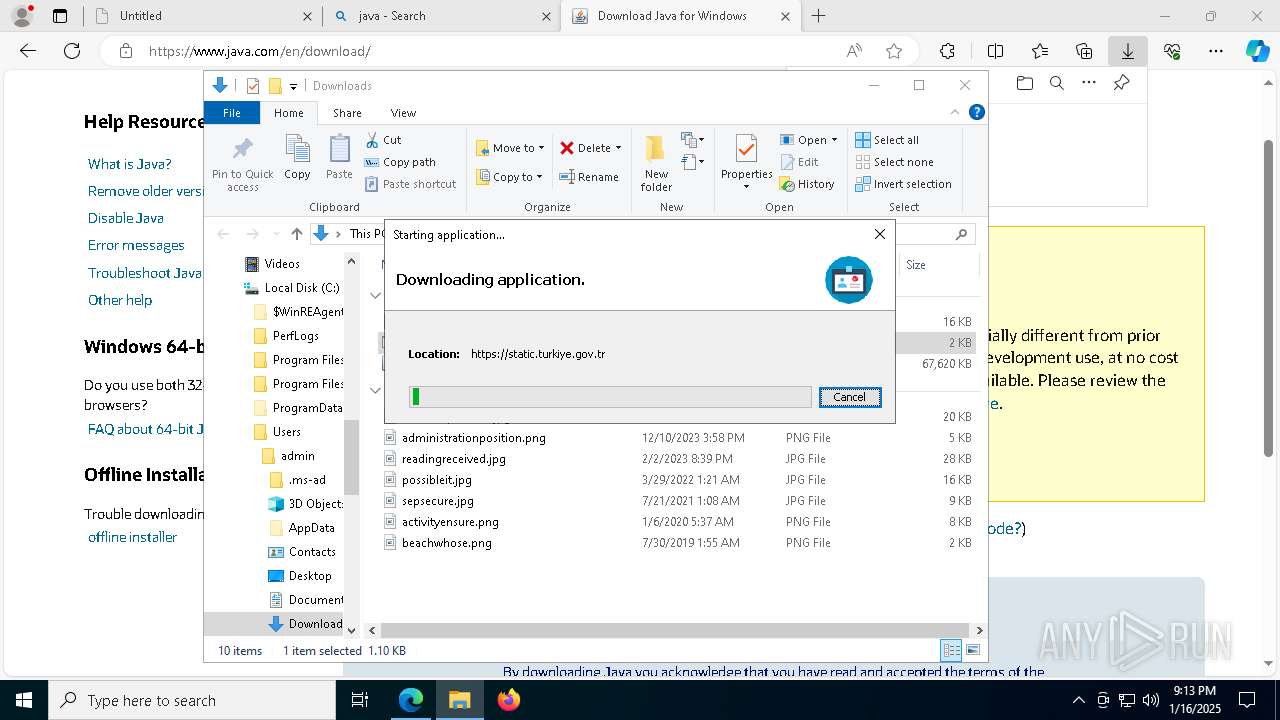
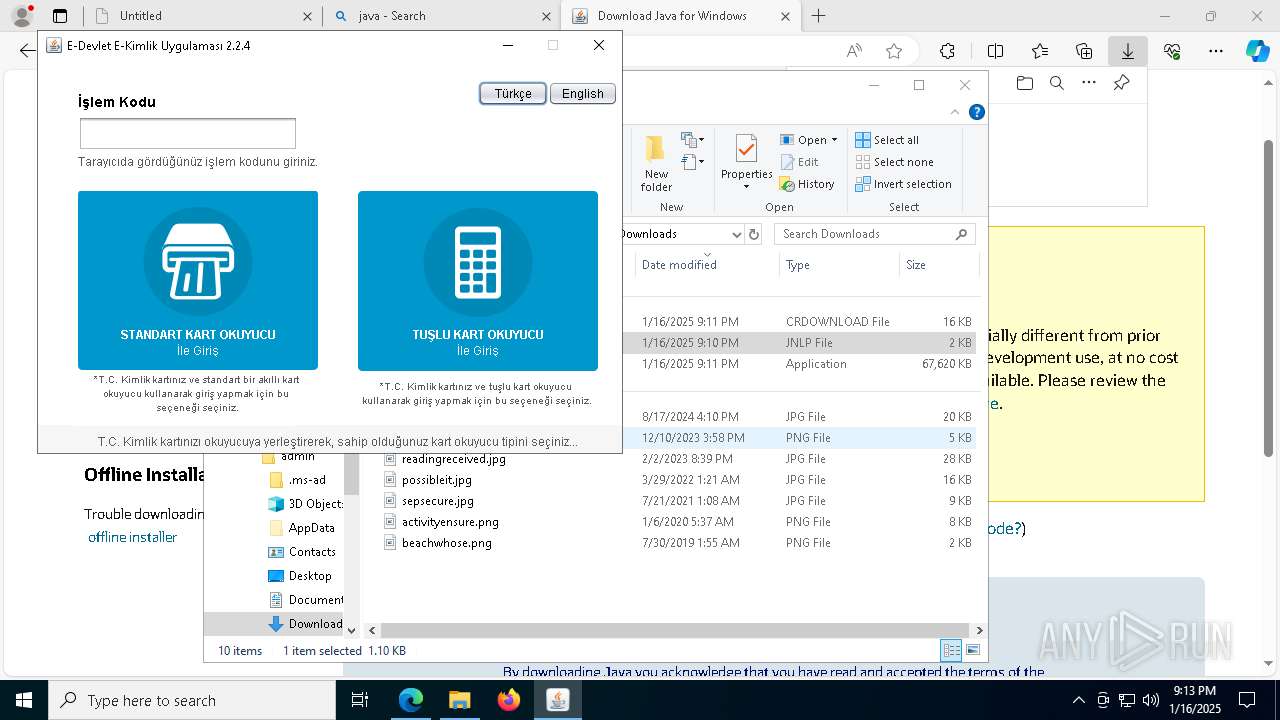
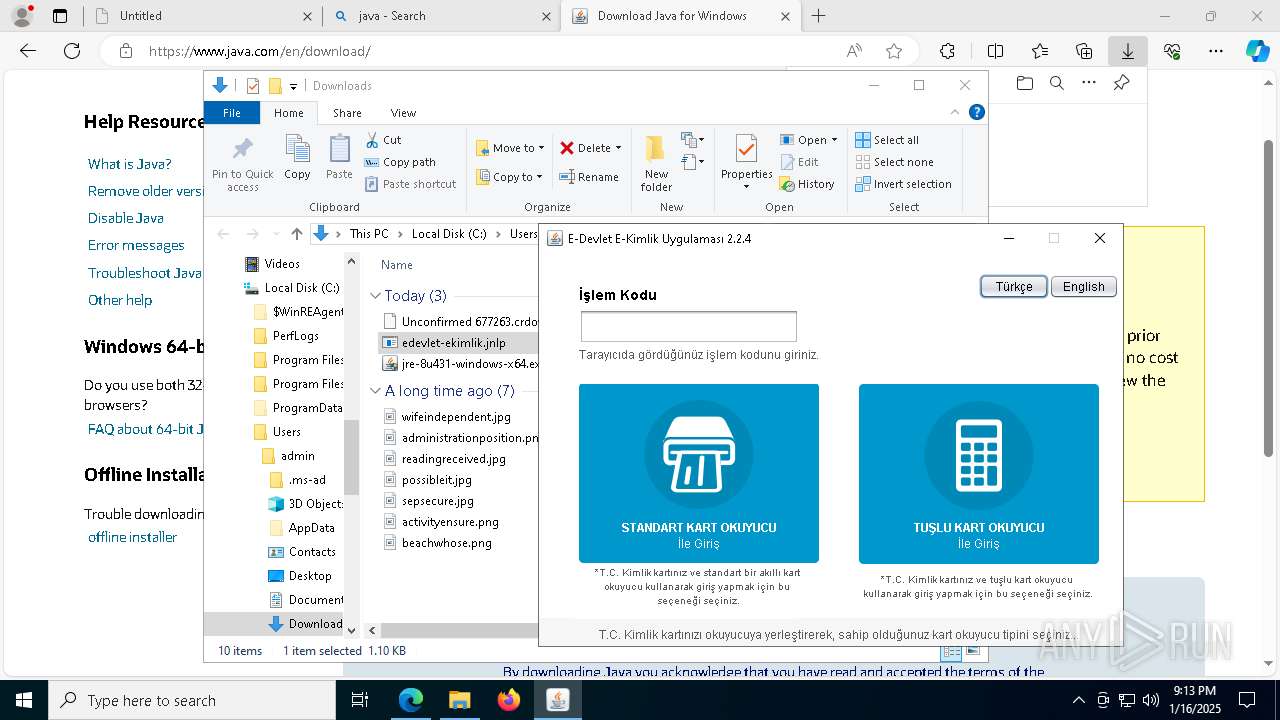
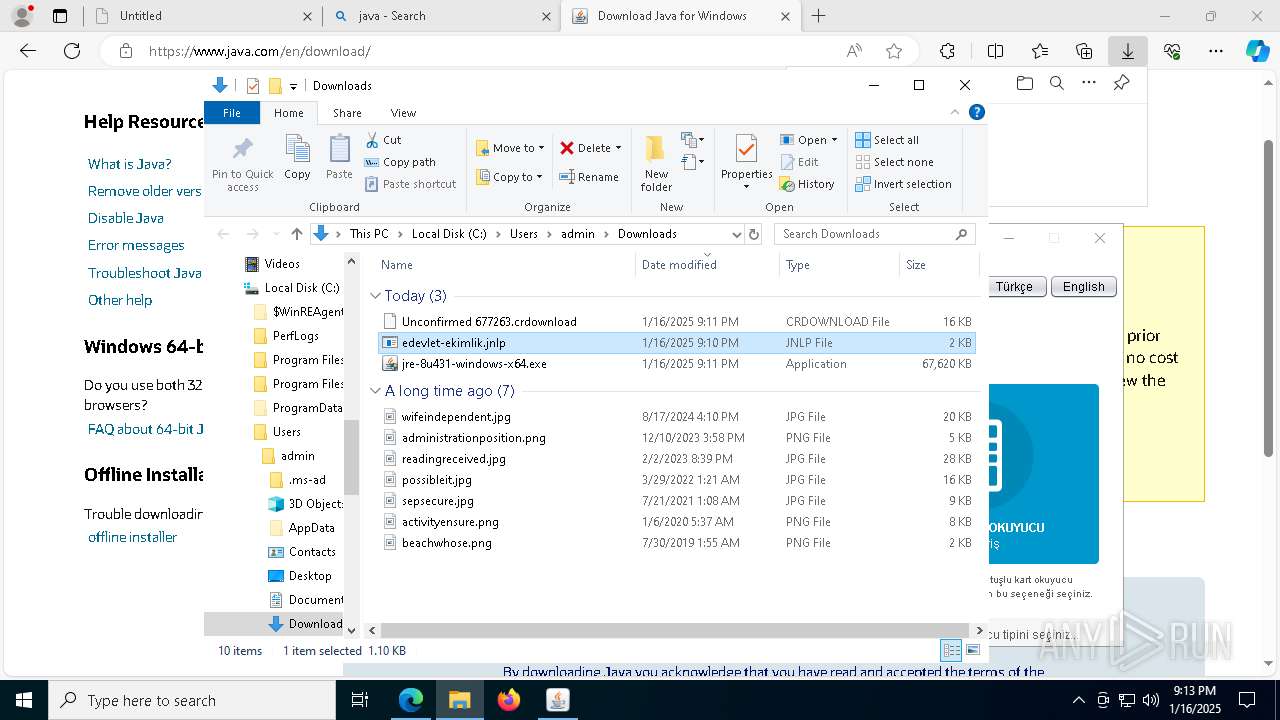
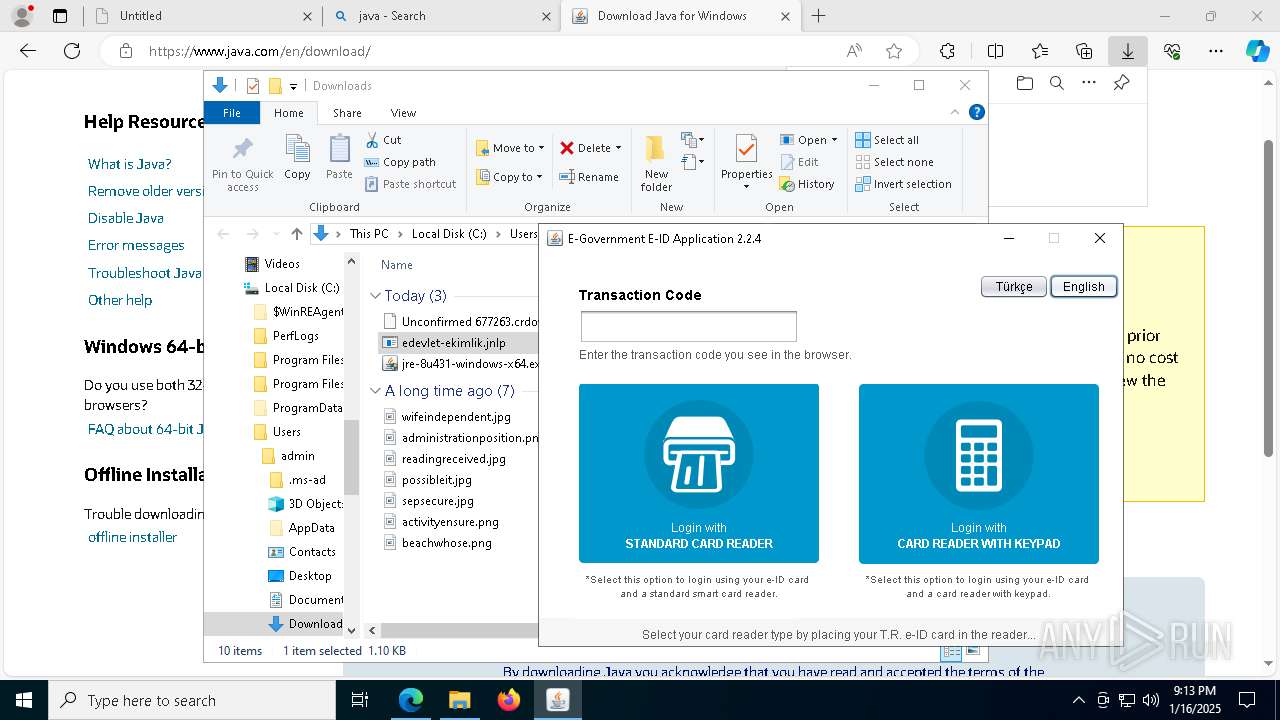
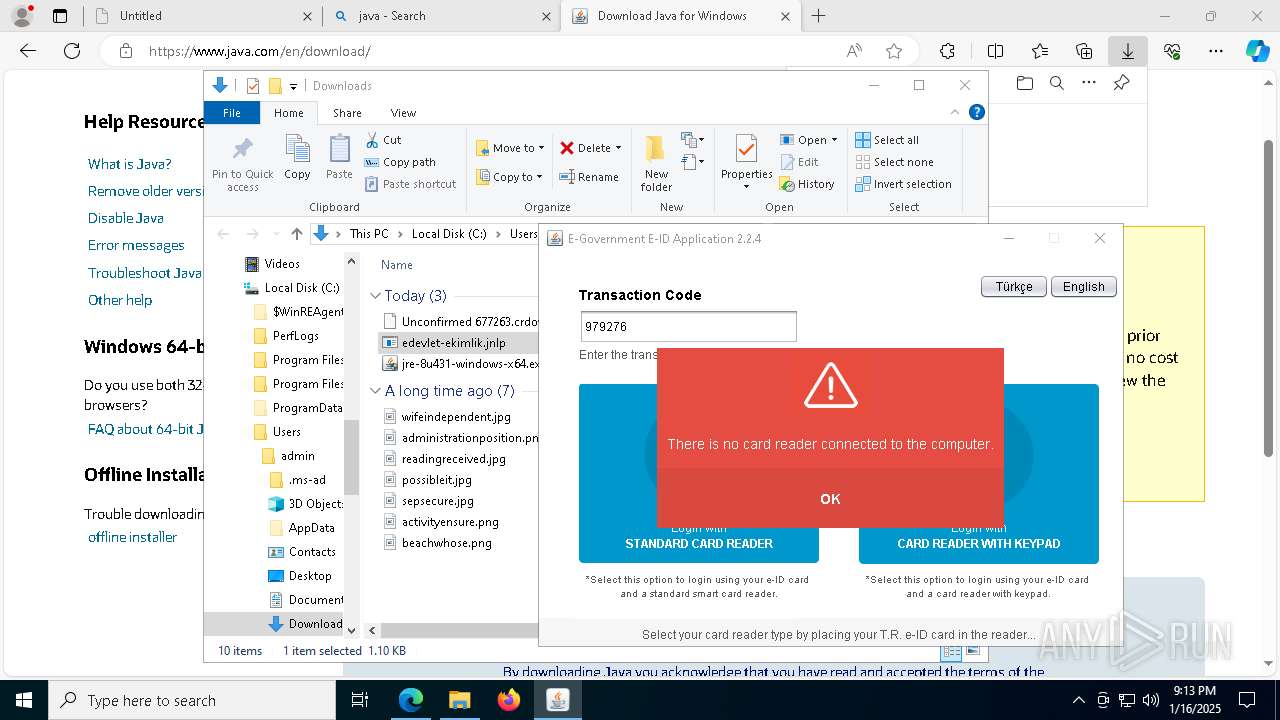
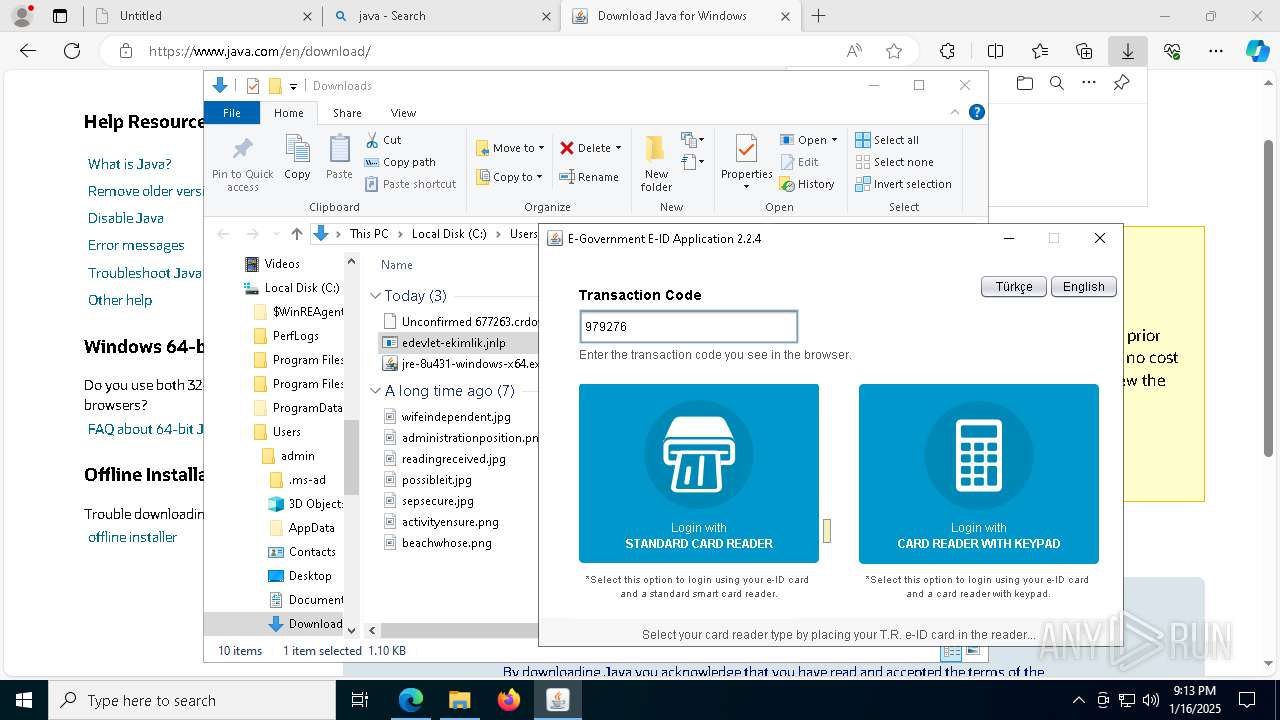
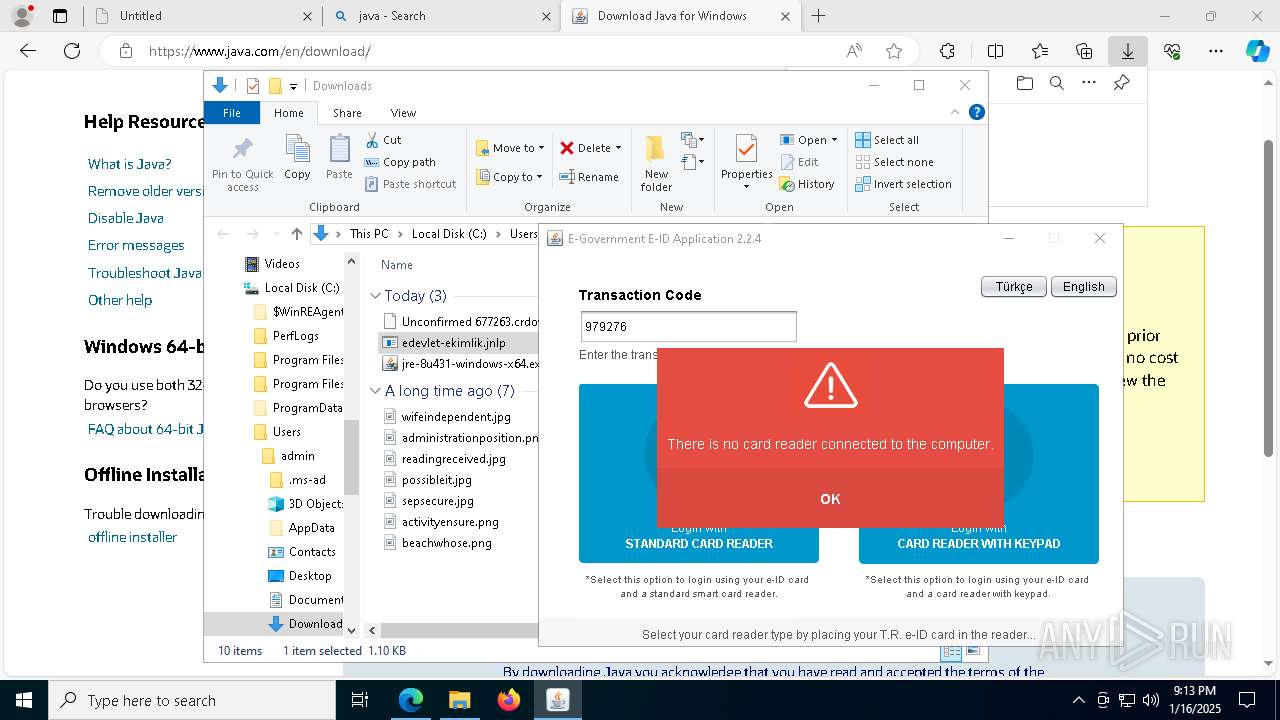
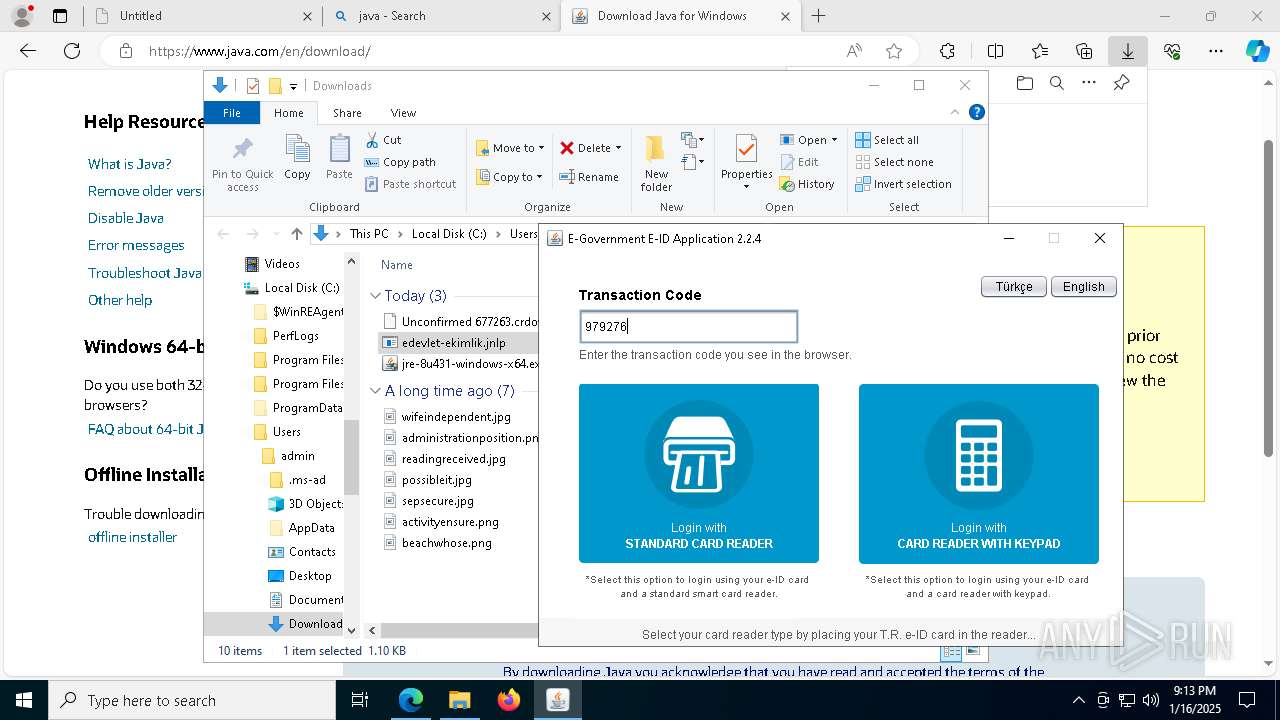
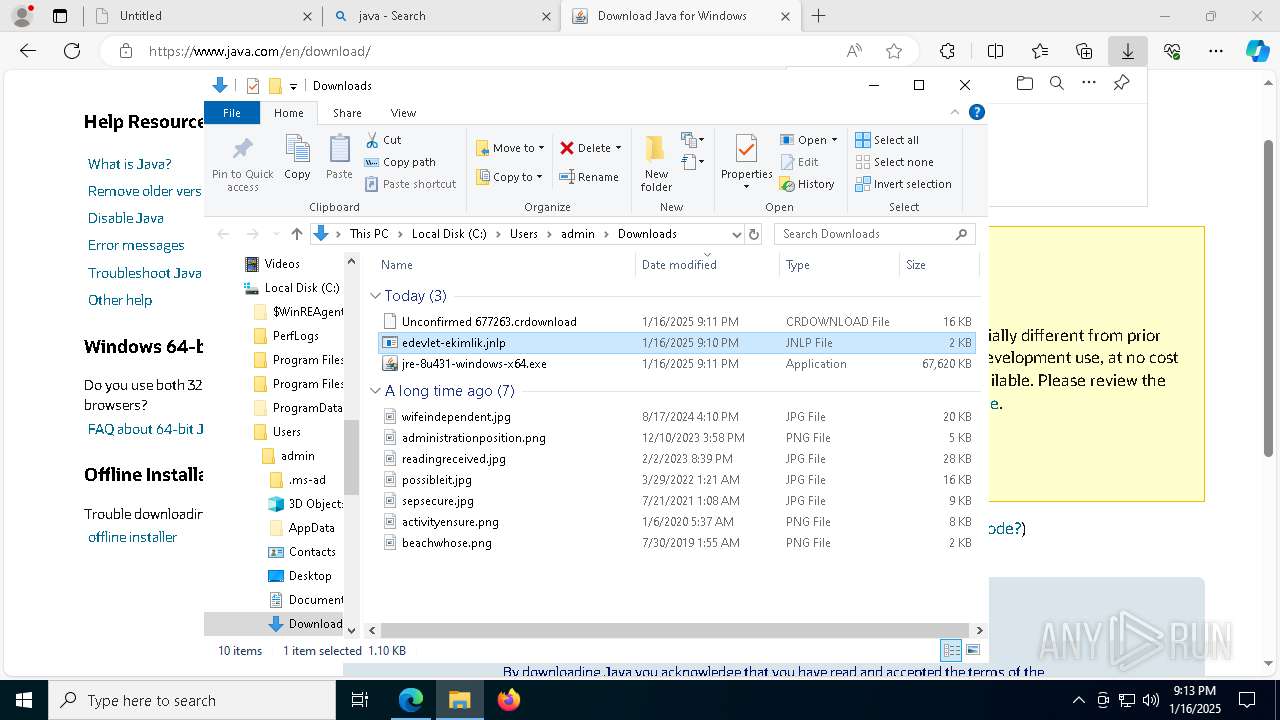
| URL: | https://cdn.e-devlet.gov.tr/downloads/e-kimlik/edevlet-ekimlik.jnlp |
| Full analysis: | https://app.any.run/tasks/1dd69e8d-477b-4f28-931d-d27532c6c429 |
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2025, 21:10:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E922B01344BD2472BEEE08F72E63D96B |
| SHA1: | 48B4549112A70A9DD0CEA0575D3AD1E64F9D8B65 |
| SHA256: | 43227EDB4BB70C357A013830CA2E71F8449D6CFC1DCA41AB72663DE47B5DCBD8 |
| SSDEEP: | 3:N8cTJaBz4KCb9S:2cTJKDG9S |
MALICIOUS
No malicious indicators.SUSPICIOUS
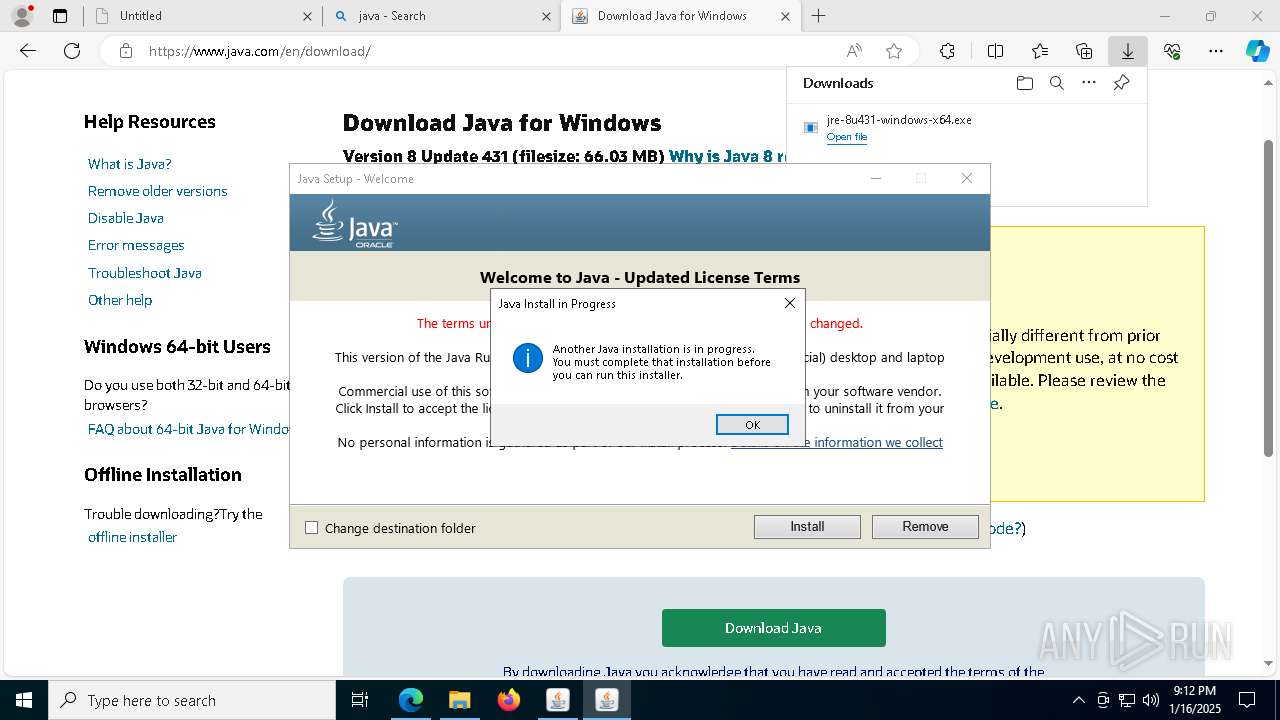
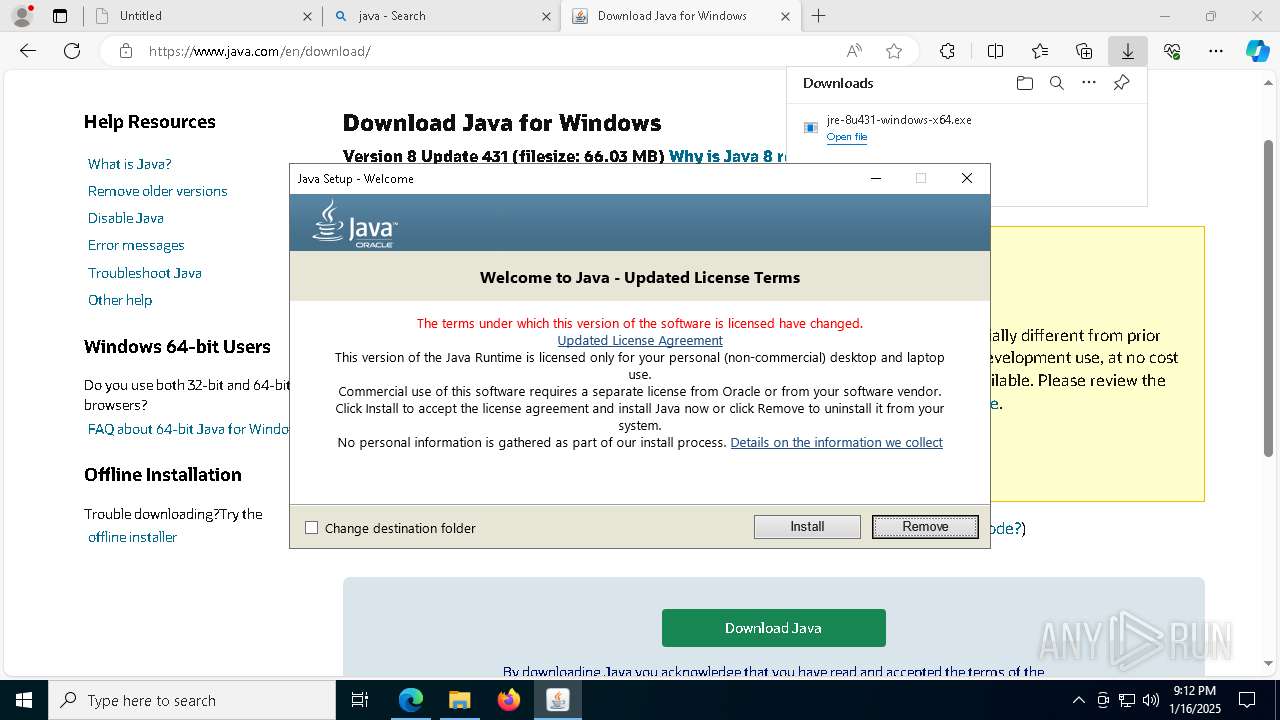
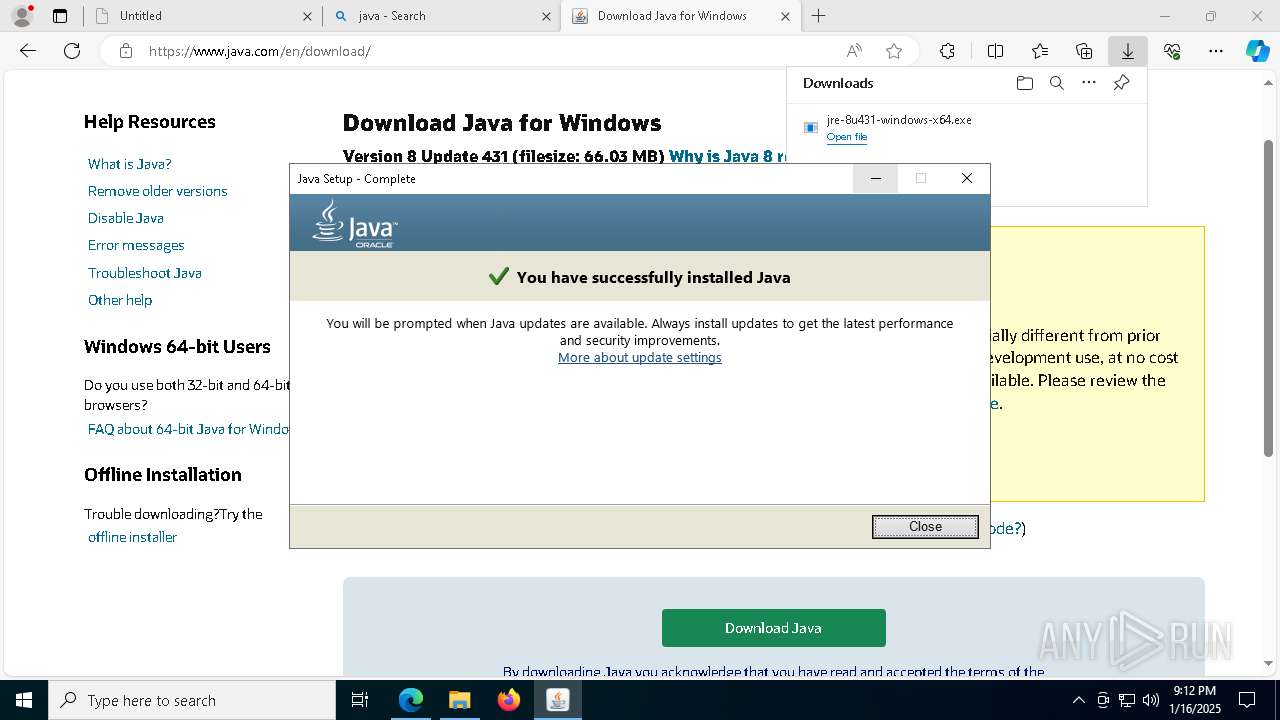
Checks for Java to be installed
- jre-8u431-windows-x64.exe (PID: 7300)
- jre-8u431-windows-x64.exe (PID: 1144)
- msiexec.exe (PID: 4628)
- msiexec.exe (PID: 2904)
- installer.exe (PID: 3828)
- ssvagent.exe (PID: 640)
- jp2launcher.exe (PID: 2456)
- jp2launcher.exe (PID: 2084)
- msiexec.exe (PID: 7832)
- javaw.exe (PID: 736)
- javaws.exe (PID: 7564)
- jp2launcher.exe (PID: 7544)
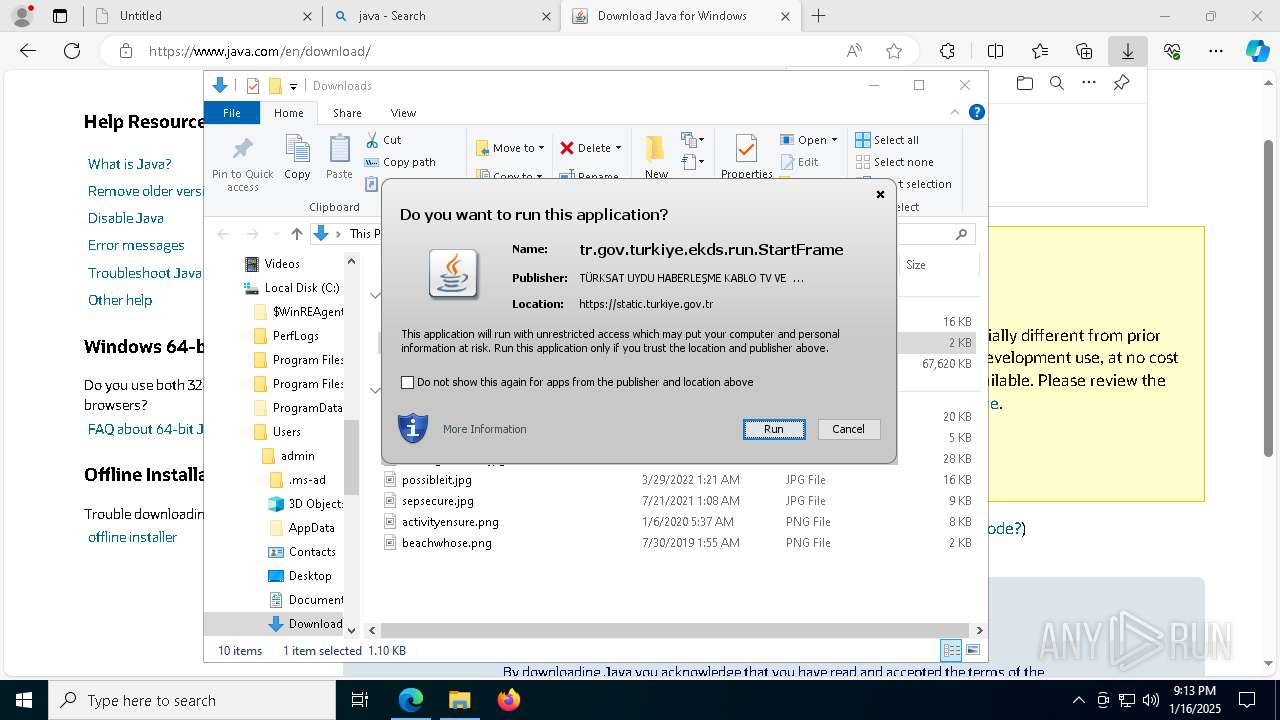
Checks Windows Trust Settings
- jre-8u431-windows-x64.exe (PID: 7300)
- msiexec.exe (PID: 2904)
Reads security settings of Internet Explorer
- jre-8u431-windows-x64.exe (PID: 7300)
- jp2launcher.exe (PID: 2084)
- jp2launcher.exe (PID: 7544)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 2904)
Reads Internet Explorer settings
- jre-8u431-windows-x64.exe (PID: 7300)
The process drops C-runtime libraries
- msiexec.exe (PID: 2904)
Executable content was dropped or overwritten
- installer.exe (PID: 3828)
- jre-8u431-windows-x64.exe (PID: 7300)
Reads Mozilla Firefox installation path
- installer.exe (PID: 3828)
Process drops legitimate windows executable
- msiexec.exe (PID: 2904)
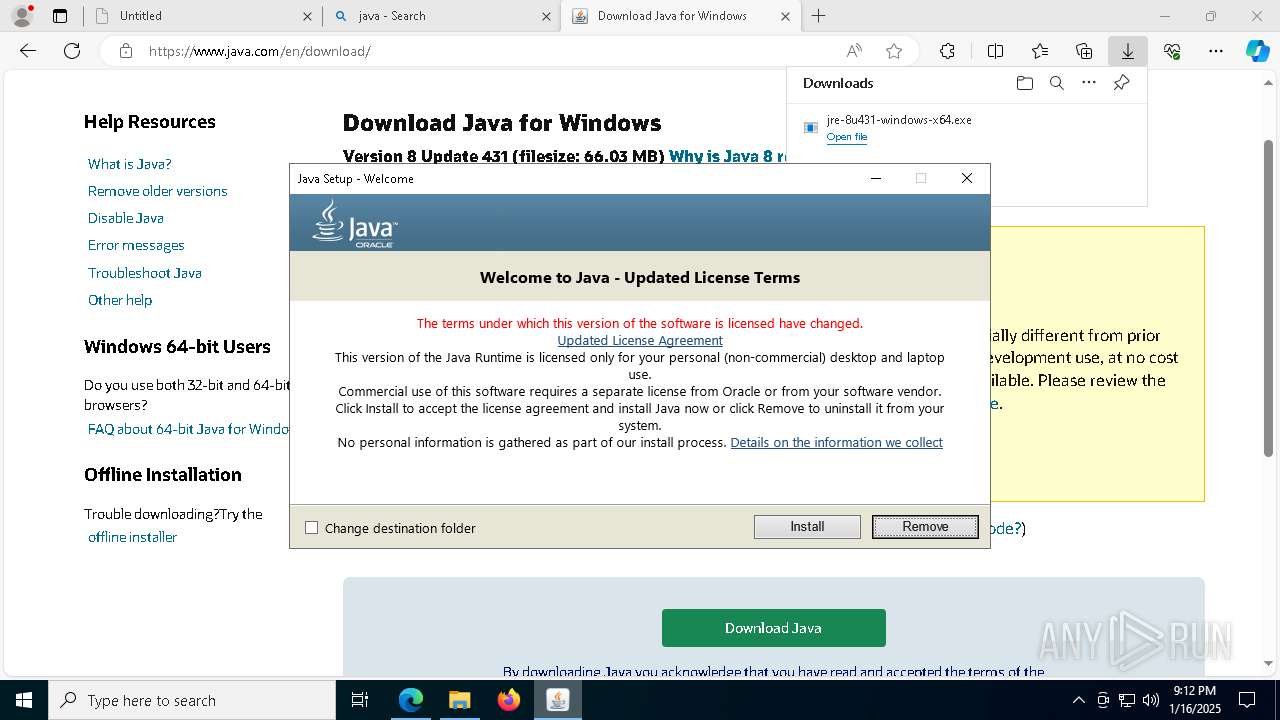
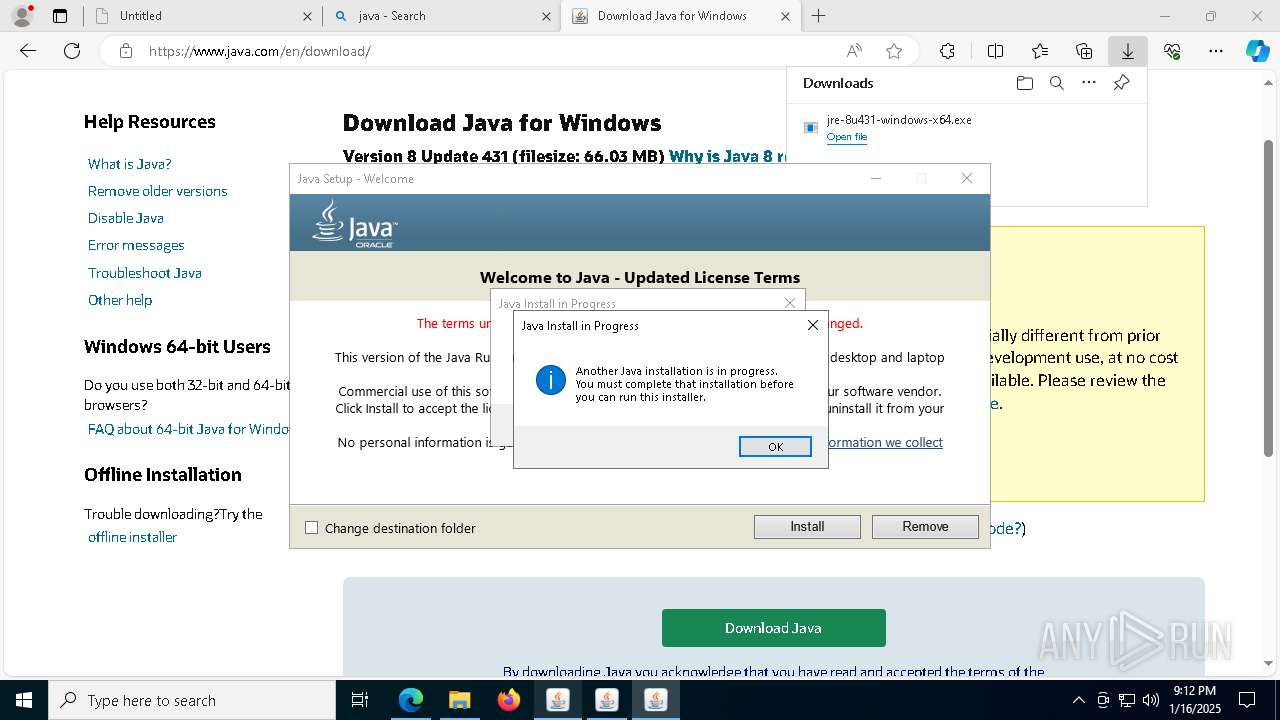
Application launched itself
- javaws.exe (PID: 7564)
Creates/Modifies COM task schedule object
- ssvagent.exe (PID: 640)
- installer.exe (PID: 3828)
Uses ICACLS.EXE to modify access control lists
- jp2launcher.exe (PID: 7544)
INFO
Application launched itself
- msedge.exe (PID: 6324)
- msiexec.exe (PID: 2904)
Reads the computer name
- identity_helper.exe (PID: 7616)
- jre-8u431-windows-x64.exe (PID: 7888)
- jre-8u431-windows-x64.exe (PID: 540)
- jre-8u431-windows-x64.exe (PID: 3208)
- jre-8u431-windows-x64.exe (PID: 1144)
- msiexec.exe (PID: 2904)
- msiexec.exe (PID: 4628)
- installer.exe (PID: 3828)
- javaws.exe (PID: 7960)
- msiexec.exe (PID: 7832)
- javaw.exe (PID: 736)
- jp2launcher.exe (PID: 2084)
- msiexec.exe (PID: 7872)
- msiexec.exe (PID: 6068)
- javaw.exe (PID: 6032)
- jp2launcher.exe (PID: 7544)
Reads Environment values
- identity_helper.exe (PID: 7616)
Checks supported languages
- identity_helper.exe (PID: 7616)
- jre-8u431-windows-x64.exe (PID: 7888)
- jre-8u431-windows-x64.exe (PID: 7300)
- jre-8u431-windows-x64.exe (PID: 1144)
- jre-8u431-windows-x64.exe (PID: 540)
- msiexec.exe (PID: 2904)
- msiexec.exe (PID: 4628)
- MSIB1F6.tmp (PID: 2632)
- installer.exe (PID: 3828)
- javaw.exe (PID: 3824)
- javaws.exe (PID: 5880)
- javaws.exe (PID: 7960)
- jp2launcher.exe (PID: 2084)
- javaw.exe (PID: 736)
- msiexec.exe (PID: 7884)
- msiexec.exe (PID: 7832)
- msiexec.exe (PID: 7872)
- javaw.exe (PID: 6032)
- javaws.exe (PID: 7564)
- jp2launcher.exe (PID: 7544)
- msiexec.exe (PID: 6068)
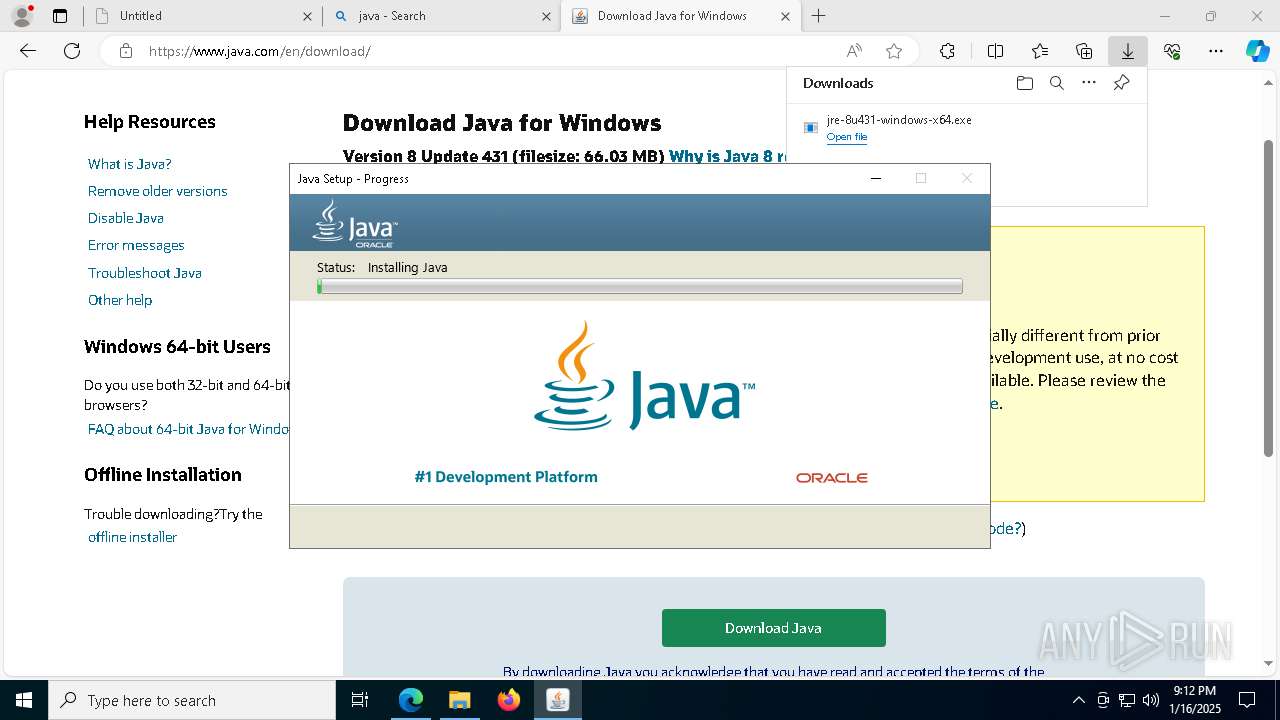
Java executable
- jre-8u431-windows-x64.exe (PID: 6916)
- jre-8u431-windows-x64.exe (PID: 7888)
- jre-8u431-windows-x64.exe (PID: 7300)
- jre-8u431-windows-x64.exe (PID: 2076)
- jre-8u431-windows-x64.exe (PID: 4908)
- jre-8u431-windows-x64.exe (PID: 3208)
- jre-8u431-windows-x64.exe (PID: 540)
- jre-8u431-windows-x64.exe (PID: 5080)
- jre-8u431-windows-x64.exe (PID: 1144)
- installer.exe (PID: 3828)
- MSIB1F6.tmp (PID: 2632)
Executable content was dropped or overwritten
- msedge.exe (PID: 6324)
- msiexec.exe (PID: 2904)
- msedge.exe (PID: 2324)
The process uses the downloaded file
- msedge.exe (PID: 5536)
- msedge.exe (PID: 6324)
- jre-8u431-windows-x64.exe (PID: 7300)
Create files in a temporary directory
- jre-8u431-windows-x64.exe (PID: 7888)
- jre-8u431-windows-x64.exe (PID: 5080)
- MSIB1F6.tmp (PID: 2632)
Reads the machine GUID from the registry
- jre-8u431-windows-x64.exe (PID: 7300)
- jre-8u431-windows-x64.exe (PID: 1144)
- msiexec.exe (PID: 2904)
- jp2launcher.exe (PID: 7544)
Reads the software policy settings
- jre-8u431-windows-x64.exe (PID: 7300)
- msiexec.exe (PID: 2904)
Checks proxy server information
- jre-8u431-windows-x64.exe (PID: 7300)
- jp2launcher.exe (PID: 2456)
- jp2launcher.exe (PID: 2084)
- jp2launcher.exe (PID: 7544)
Creates files or folders in the user directory
- jre-8u431-windows-x64.exe (PID: 7300)
- jp2launcher.exe (PID: 7544)
The sample compiled with english language support
- msiexec.exe (PID: 2904)
- installer.exe (PID: 3828)
- jre-8u431-windows-x64.exe (PID: 7300)
Starts application with an unusual extension
- msiexec.exe (PID: 2904)
Reads CPU info
- msiexec.exe (PID: 2904)
Creates a software uninstall entry
- msiexec.exe (PID: 2904)
Local mutex for internet shortcut management
- installer.exe (PID: 3828)
Creates files in the program directory
- installer.exe (PID: 3828)
- jp2launcher.exe (PID: 7544)
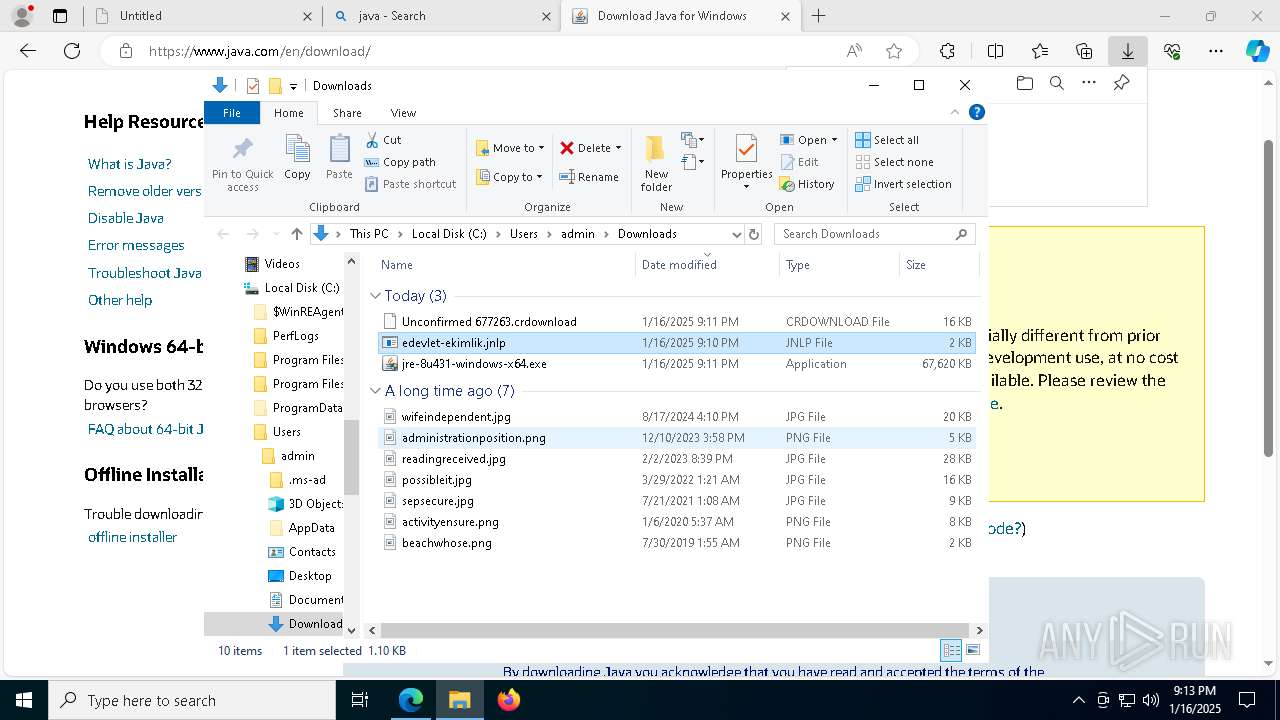
Manual execution by a user
- jp2launcher.exe (PID: 1296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
243
Monitored processes
106
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=8324 --field-trial-handle=2348,i,4030168839053239866,8039502733515860598,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 396 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7636 --field-trial-handle=2348,i,4030168839053239866,8039502733515860598,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 540 | "C:\Users\admin\Downloads\jre-8u431-windows-x64.exe" | C:\Users\admin\Downloads\jre-8u431-windows-x64.exe | msedge.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 4294967295 Version: 8.0.4310.10 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Java\jre1.8.0_431\bin\ssvagent.exe" -doHKCUSSVSetup | C:\Program Files\Java\jre1.8.0_431\bin\ssvagent.exe | — | installer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 11.431.2.10 Modules
| |||||||||||||||
| 736 | -Djdk.disableLastUsageTracking -cp "C:\Program Files\Java\jre1.8.0_431\bin\..\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -getUserWebJavaStatus | C:\Program Files\Java\jre1.8.0_431\bin\javaw.exe | — | jre-8u431-windows-x64.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.4310.10 | |||||||||||||||
| 1144 | "C:\Users\admin\AppData\Local\Temp\jds1346171.tmp\jre-8u431-windows-x64.exe" | C:\Users\admin\AppData\Local\Temp\jds1346171.tmp\jre-8u431-windows-x64.exe | — | jre-8u431-windows-x64.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 4294967295 Version: 8.0.4310.10 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Java\jre1.8.0_431\bin\jp2launcher.exe" -securejws "C:\Users\admin\Downloads\edevlet-ekimlik.jnlp" | C:\Program Files\Java\jre1.8.0_431\bin\jp2launcher.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.431.2.10 | |||||||||||||||
| 1468 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7380 --field-trial-handle=2348,i,4030168839053239866,8039502733515860598,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1796 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1564 --field-trial-handle=2348,i,4030168839053239866,8039502733515860598,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 2076 | "C:\Users\admin\Downloads\jre-8u431-windows-x64.exe" | C:\Users\admin\Downloads\jre-8u431-windows-x64.exe | — | msedge.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java Platform SE binary Exit code: 3221226540 Version: 8.0.4310.10 Modules
| |||||||||||||||
Total events
55 660
Read events
28 321
Write events
12 743
Delete events
14 596
Modification events
| (PID) Process: | (6176) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6176) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6176) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6176) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (6176) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (6176) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
416
Suspicious files
1 115
Text files
403
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\bf9ad671-be05-4639-914e-333bc786c98b.tmp | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF13598d.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13599d.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13599d.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13598d.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1359bc.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
160
DNS requests
184
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3952 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6180 | svchost.exe | HEAD | 200 | 2.16.168.112:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1737537180&P2=404&P3=2&P4=fyRy3jOQ4Z%2fasGqRuv2YsYjBbtIZH1vsqR7mFdFfvmL04LCzcSdgtPI1Pqy1%2fY27qCnOpzqhwLGAmx0X2F881Q%3d%3d | unknown | — | — | whitelisted |
6180 | svchost.exe | GET | 206 | 2.16.168.112:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1737537180&P2=404&P3=2&P4=fyRy3jOQ4Z%2fasGqRuv2YsYjBbtIZH1vsqR7mFdFfvmL04LCzcSdgtPI1Pqy1%2fY27qCnOpzqhwLGAmx0X2F881Q%3d%3d | unknown | — | — | whitelisted |
6180 | svchost.exe | GET | 206 | 2.16.168.112:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1737537180&P2=404&P3=2&P4=fyRy3jOQ4Z%2fasGqRuv2YsYjBbtIZH1vsqR7mFdFfvmL04LCzcSdgtPI1Pqy1%2fY27qCnOpzqhwLGAmx0X2F881Q%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
448 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 104.126.37.168:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6576 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6324 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.e-devlet.gov.tr |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7544 | jp2launcher.exe | Potentially Bad Traffic | ET INFO Vulnerable Java Version 1.8.x Detected |
7544 | jp2launcher.exe | Potentially Bad Traffic | ET INFO Vulnerable Java Version 1.8.x Detected |