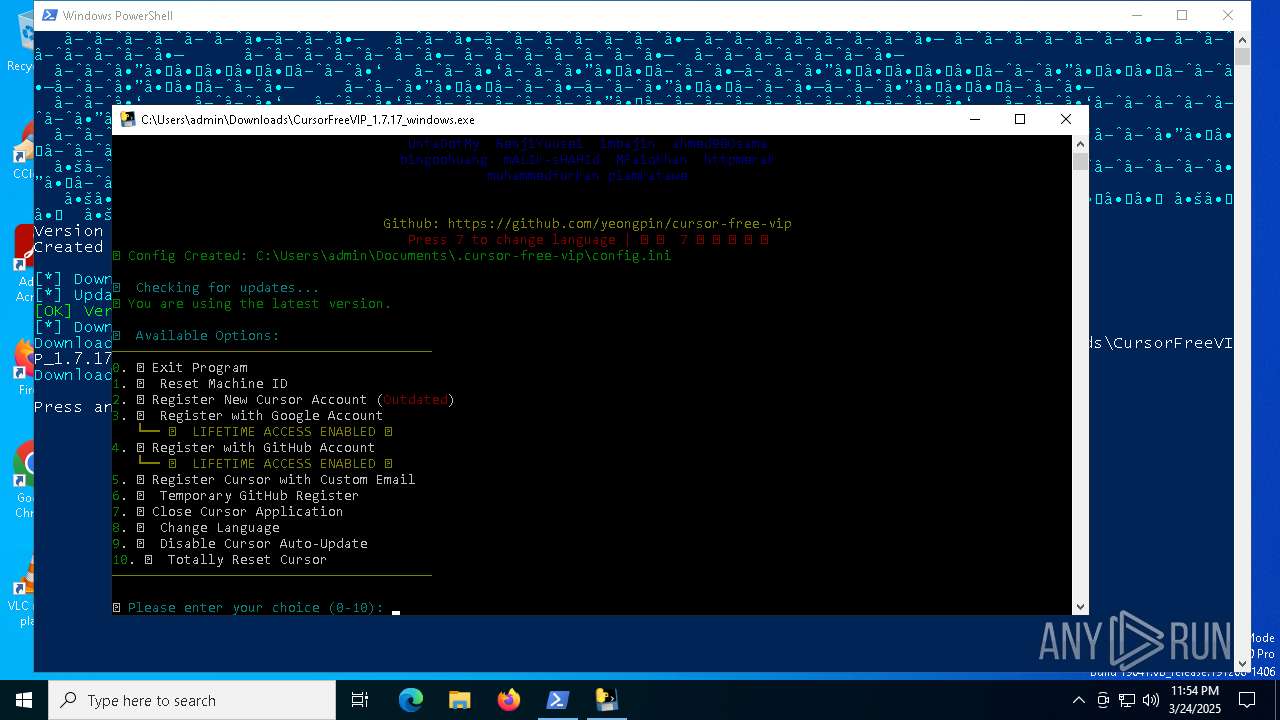
| download: | /yeongpin/cursor-free-vip/main/scripts/install.ps1 |
| Full analysis: | https://app.any.run/tasks/1c3fc189-6c84-4254-ade2-14b12a983c7a |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 23:53:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text |
| MD5: | C383FE46E2FAA3D7E59FA1D15026624A |
| SHA1: | 33C9667E4A9BF755C934368AEEA7CED4DB8C7C4D |
| SHA256: | 4314D773937FA789BD0659870CB499DFDFED1571B8EA1F88E71C0EBF82118D0C |
| SSDEEP: | 192:xDZZffZeiAzziikvdeOe4FKRc1tP24E9mRMIxwNBC1M8xlhPDAw5nONCZzSllf/g:xcc9bvLvwqUCT |
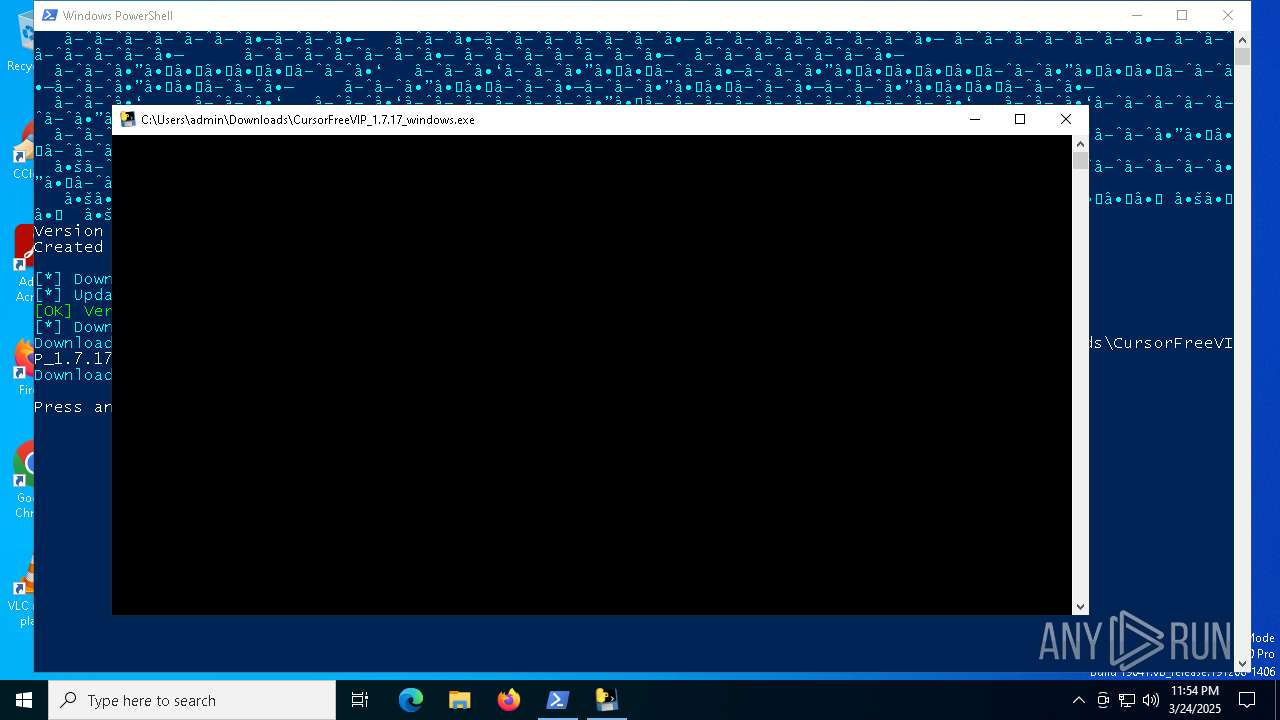
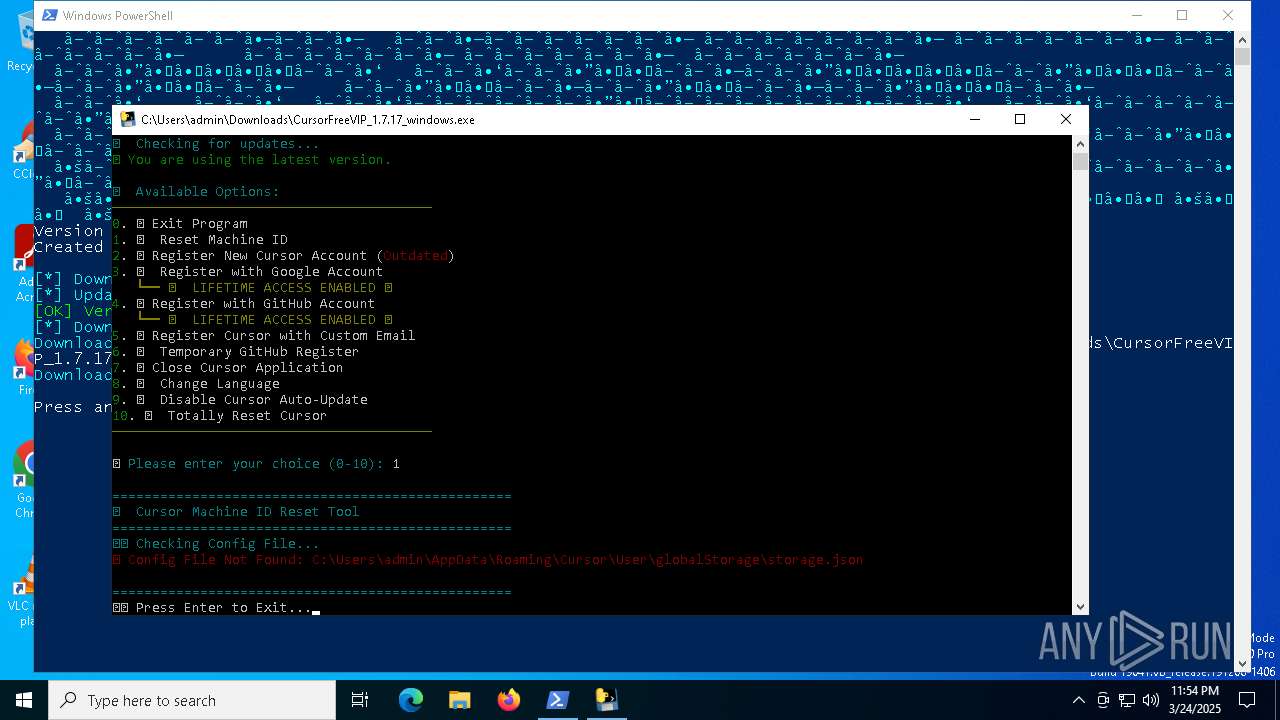
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 5364)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 5364)
SUSPICIOUS
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5364)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 5364)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 5364)
The process drops C-runtime libraries
- CursorFreeVIP_1.7.17_windows.exe (PID: 7592)
- CursorFreeVIP_1.7.17_windows.exe (PID: 2096)
Executable content was dropped or overwritten
- CursorFreeVIP_1.7.17_windows.exe (PID: 7592)
- powershell.exe (PID: 5364)
- CursorFreeVIP_1.7.17_windows.exe (PID: 2096)
Process drops python dynamic module
- CursorFreeVIP_1.7.17_windows.exe (PID: 7592)
- CursorFreeVIP_1.7.17_windows.exe (PID: 2096)
Process drops legitimate windows executable
- CursorFreeVIP_1.7.17_windows.exe (PID: 7592)
- CursorFreeVIP_1.7.17_windows.exe (PID: 2096)
Application launched itself
- CursorFreeVIP_1.7.17_windows.exe (PID: 7592)
- CursorFreeVIP_1.7.17_windows.exe (PID: 2096)
- CursorFreeVIP_1.7.17_windows.exe (PID: 8152)
Loads Python modules
- CursorFreeVIP_1.7.17_windows.exe (PID: 8152)
- CursorFreeVIP_1.7.17_windows.exe (PID: 1660)
Reads security settings of Internet Explorer
- CursorFreeVIP_1.7.17_windows.exe (PID: 8152)
- ShellExperienceHost.exe (PID: 7872)
Reads the date of Windows installation
- CursorFreeVIP_1.7.17_windows.exe (PID: 8152)
INFO
Checks proxy server information
- powershell.exe (PID: 5364)
- BackgroundTransferHost.exe (PID: 7256)
- CursorFreeVIP_1.7.17_windows.exe (PID: 1660)
Disables trace logs
- powershell.exe (PID: 5364)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5008)
- BackgroundTransferHost.exe (PID: 7436)
- BackgroundTransferHost.exe (PID: 7256)
- BackgroundTransferHost.exe (PID: 7728)
- BackgroundTransferHost.exe (PID: 7956)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7256)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7256)
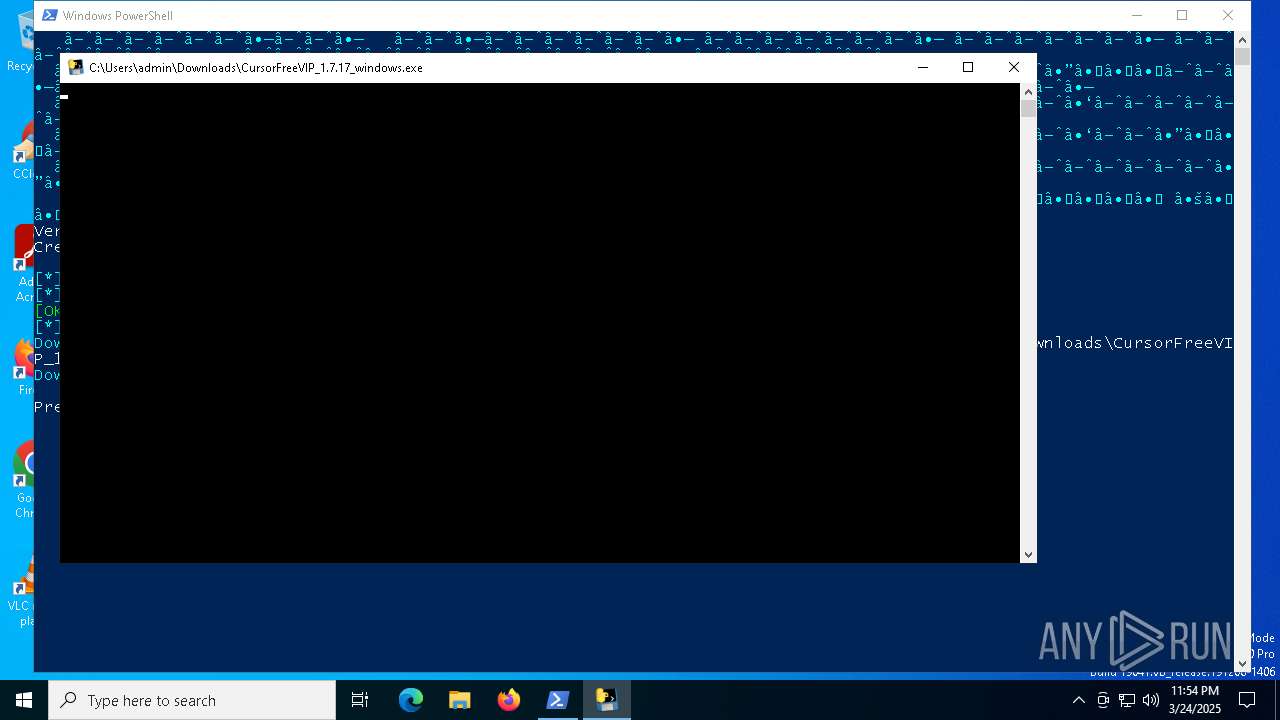
The executable file from the user directory is run by the Powershell process
- CursorFreeVIP_1.7.17_windows.exe (PID: 7592)
Create files in a temporary directory
- CursorFreeVIP_1.7.17_windows.exe (PID: 7592)
- CursorFreeVIP_1.7.17_windows.exe (PID: 2096)
Reads the computer name
- CursorFreeVIP_1.7.17_windows.exe (PID: 7592)
- CursorFreeVIP_1.7.17_windows.exe (PID: 8152)
- CursorFreeVIP_1.7.17_windows.exe (PID: 1660)
- ShellExperienceHost.exe (PID: 7872)
- CursorFreeVIP_1.7.17_windows.exe (PID: 2096)
Checks supported languages
- CursorFreeVIP_1.7.17_windows.exe (PID: 7592)
- CursorFreeVIP_1.7.17_windows.exe (PID: 8152)
- CursorFreeVIP_1.7.17_windows.exe (PID: 1660)
- ShellExperienceHost.exe (PID: 7872)
- CursorFreeVIP_1.7.17_windows.exe (PID: 2096)
The sample compiled with english language support
- CursorFreeVIP_1.7.17_windows.exe (PID: 7592)
- CursorFreeVIP_1.7.17_windows.exe (PID: 2096)
Process checks computer location settings
- CursorFreeVIP_1.7.17_windows.exe (PID: 8152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
153
Monitored processes
16
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1660 | "C:\Users\admin\Downloads\CursorFreeVIP_1.7.17_windows.exe" "C:\Users\admin\Downloads\CursorFreeVIP_1.7.17_windows.exe" | C:\Users\admin\Downloads\CursorFreeVIP_1.7.17_windows.exe | CursorFreeVIP_1.7.17_windows.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1760 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\Downloads\CursorFreeVIP_1.7.17_windows.exe" "C:\Users\admin\Downloads\CursorFreeVIP_1.7.17_windows.exe" | C:\Users\admin\Downloads\CursorFreeVIP_1.7.17_windows.exe | CursorFreeVIP_1.7.17_windows.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 5008 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5156 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5364 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\install.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CursorFreeVIP_1.7.17_windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7256 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7436 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 607
Read events
11 590
Write events
17
Delete events
0
Modification events
| (PID) Process: | (5008) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5008) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5008) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7256) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7256) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7256) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7728) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7728) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7728) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7436) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
166
Suspicious files
50
Text files
78
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7256 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\8a0968a4-ac11-4708-a70a-b343ebf2a5e3.down_data | — | |
MD5:— | SHA256:— | |||
| 5364 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:677551E7E1DAD92C8B26C30623F00E44 | SHA256:3E5DE8A17163402AC839DA3753141499EBDC86EEAAD040B922FC21B16D893785 | |||
| 5364 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10b160.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 5364 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9MA13MXD64C098H3TWTP.temp | binary | |
MD5:677551E7E1DAD92C8B26C30623F00E44 | SHA256:3E5DE8A17163402AC839DA3753141499EBDC86EEAAD040B922FC21B16D893785 | |||
| 5364 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_apmc0wla.bpg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7592 | CursorFreeVIP_1.7.17_windows.exe | C:\Users\admin\AppData\Local\Temp\_MEI75922\PBlock\manifest.json | binary | |
MD5:3274E2D9736AA341B9DC1A861099F319 | SHA256:C9D258F4089A3ACFD76F50DE766FA55C3B7292E78E40CAAFF89890BDF8AA1698 | |||
| 7256 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:AE93A8B551E07C33ED96A79FBD031250 | SHA256:04FA56FC73A1089D8AED7AF40CE603FF81A6CD54DC555DBCF1C8B5DDD6BE2AF9 | |||
| 7592 | CursorFreeVIP_1.7.17_windows.exe | C:\Users\admin\AppData\Local\Temp\_MEI75922\PBlock\background.js | text | |
MD5:88ABD0F1892A5338FD51A0176DE9C635 | SHA256:63F6ED30F9794980A152B3338EC6F13EC7574D411BF4DB9A28636BAA39985A10 | |||
| 7256 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\10c18b62-a6d7-4f4e-bda2-2841b4f6edc6.up_meta_secure | binary | |
MD5:E34F94CE285052E0D812E2D6B26FC06C | SHA256:C18A7AF96FC76562B5BE26C2429C6367A1E1F20C86F5F3E69019C34E648DBAFC | |||
| 7256 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
28
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7256 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7288 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7288 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
920 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5364 | powershell.exe | 140.82.121.5:443 | api.github.com | GITHUB | US | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5364 | powershell.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
5364 | powershell.exe | 185.199.110.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
api.github.com |
| whitelisted |
github.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |