| File name: | OInstall.exe |
| Full analysis: | https://app.any.run/tasks/a6a10a3d-43a2-40e2-ac11-8596a39784e6 |
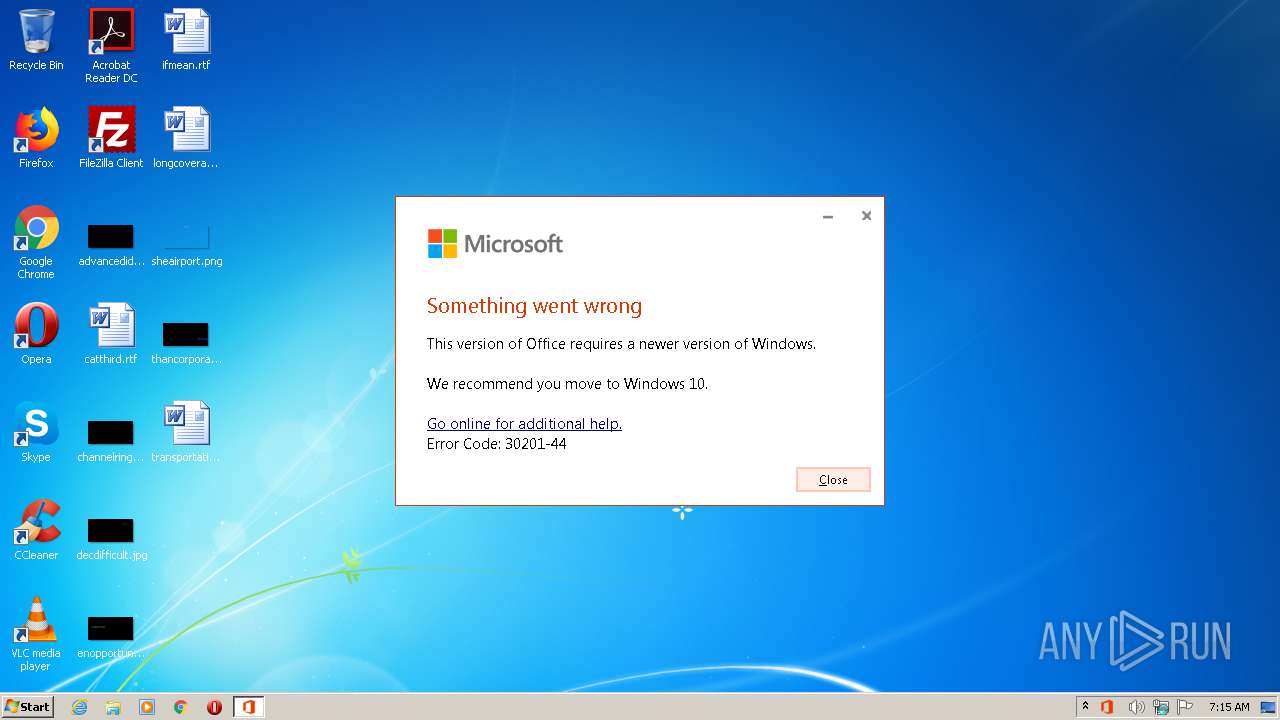
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2021, 06:14:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | B99644C768E6315872D833CE7856BAA9 |
| SHA1: | E0463E339FF5DF41D3188DBA9FA2A5354E466C08 |
| SHA256: | 43149F733842776FA3DBDF77CD752A3523D023EB74F4250F274C66740F677B26 |
| SSDEEP: | 196608:fyss4nE1GB6TOBQ23gLJSankV6mou1x03Gtyw5uCYEq4S7C4qjgOlGNRdw4ZhPpo:fyss4IGB6TOBjgtSmkImoeymuCS44q8M |
MALICIOUS
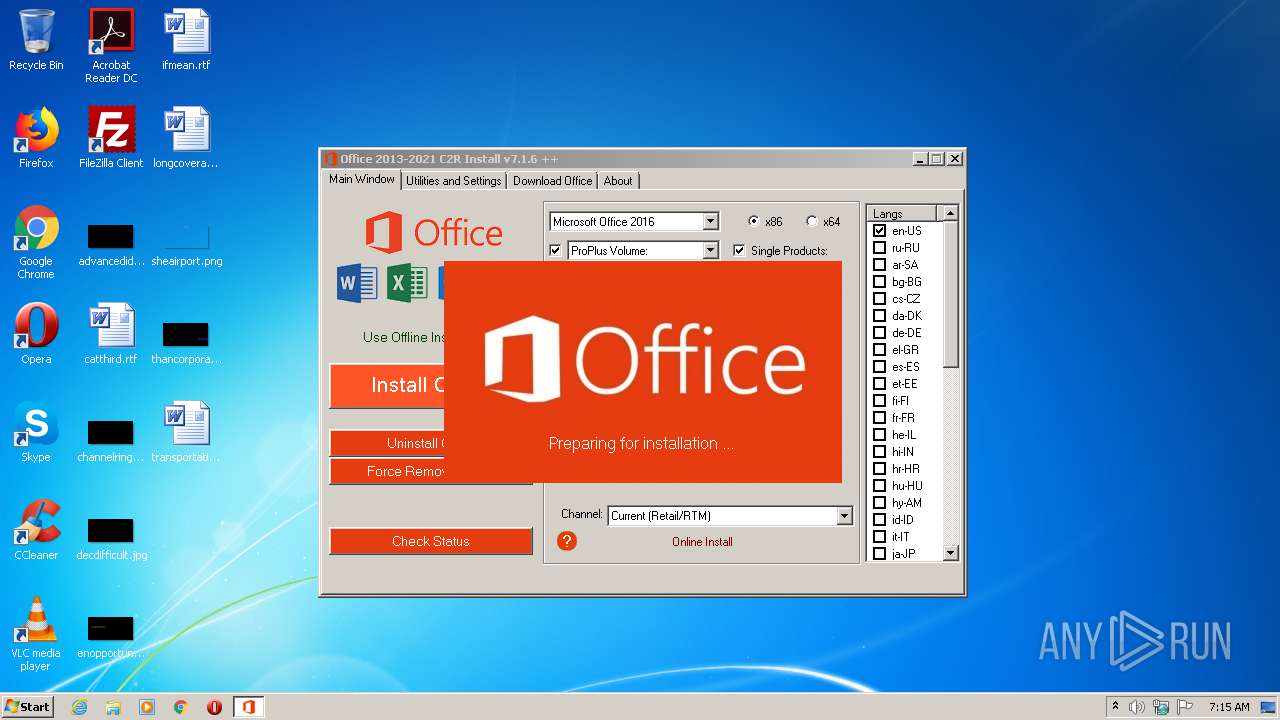
Drops executable file immediately after starts
- OInstall.exe (PID: 3324)
- files.dat (PID: 3152)
- OfficeClickToRun.exe (PID: 3100)
Application was dropped or rewritten from another process
- files.dat (PID: 3152)
- OfficeClickToRun.exe (PID: 2500)
- OfficeClickToRun.exe (PID: 3100)
Loads dropped or rewritten executable
- OfficeClickToRun.exe (PID: 2500)
- OfficeClickToRun.exe (PID: 3100)
Changes settings of System certificates
- OfficeClickToRun.exe (PID: 3100)
SUSPICIOUS
Executable content was dropped or overwritten
- OInstall.exe (PID: 3324)
- files.dat (PID: 3152)
- OfficeClickToRun.exe (PID: 3100)
- expand.exe (PID: 2140)
Drops a file that was compiled in debug mode
- OInstall.exe (PID: 3324)
- files.dat (PID: 3152)
- expand.exe (PID: 2140)
- OfficeClickToRun.exe (PID: 3100)
Starts CMD.EXE for commands execution
- OInstall.exe (PID: 3324)
Executes PowerShell scripts
- OInstall.exe (PID: 3324)
Creates files in the Windows directory
- expand.exe (PID: 2188)
- OfficeClickToRun.exe (PID: 3100)
Creates files in the user directory
- powershell.exe (PID: 1564)
- powershell.exe (PID: 352)
- powershell.exe (PID: 3636)
- powershell.exe (PID: 3632)
Starts application with an unusual extension
- cmd.exe (PID: 952)
Uses REG.EXE to modify Windows registry
- OInstall.exe (PID: 3324)
- cmd.exe (PID: 2072)
- cmd.exe (PID: 2744)
- cmd.exe (PID: 2916)
- cmd.exe (PID: 2944)
- cmd.exe (PID: 1444)
Creates a directory in Program Files
- OInstall.exe (PID: 3324)
- expand.exe (PID: 2140)
- expand.exe (PID: 3408)
- OfficeClickToRun.exe (PID: 3100)
Creates files in the program directory
- expand.exe (PID: 2140)
- expand.exe (PID: 3408)
- OfficeClickToRun.exe (PID: 3100)
Drops a file with too old compile date
- expand.exe (PID: 2140)
Drops a file with a compile date too recent
- expand.exe (PID: 2140)
- OfficeClickToRun.exe (PID: 3100)
Executed as Windows Service
- OfficeClickToRun.exe (PID: 3100)
Removes files from Windows directory
- OfficeClickToRun.exe (PID: 3100)
Adds / modifies Windows certificates
- OfficeClickToRun.exe (PID: 3100)
INFO
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 2500)
- OfficeClickToRun.exe (PID: 3100)
Reads settings of System Certificates
- OfficeClickToRun.exe (PID: 3100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
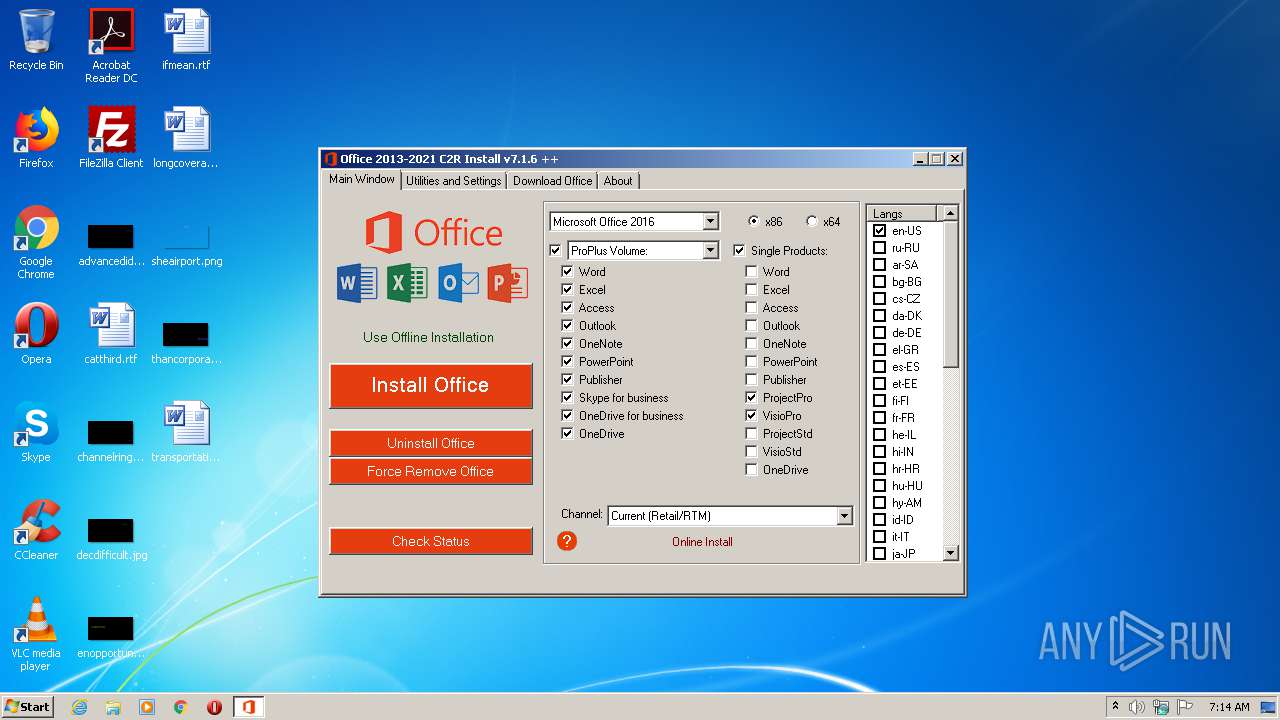
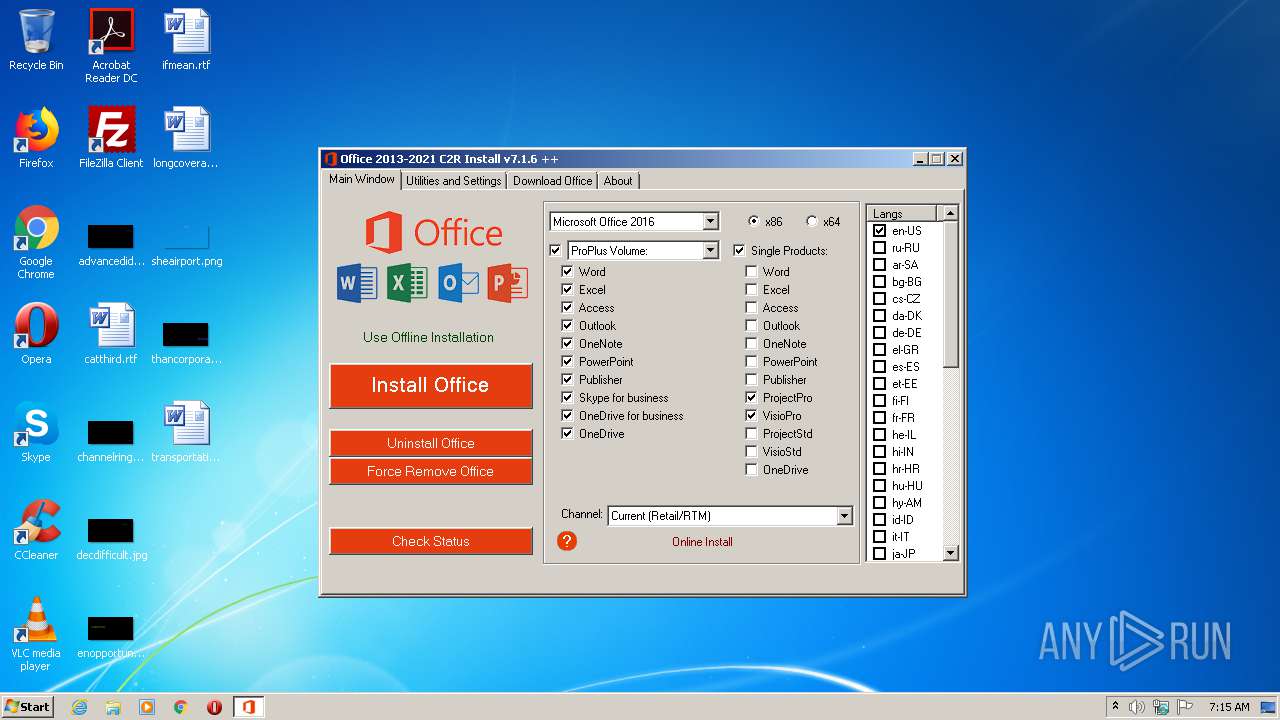
| FileDescription: | Office 2013-2021 C2R Install |
|---|---|
| ProductName: | Office 2013-2021 C2R Install |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Unknown (0) |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 7.1.6.0 |
| FileVersionNumber: | 7.1.6.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1482640 |
| UninitializedDataSize: | 11198464 |
| InitializedDataSize: | 90112 |
| CodeSize: | 10305536 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| TimeStamp: | 2021:02:26 13:48:09+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Feb-2021 12:48:09 |
| Detected languages: |
|
| ProductName: | Office 2013-2021 C2R Install |
| FileDescription: | Office 2013-2021 C2R Install |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 26-Feb-2021 12:48:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00AAE000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00AAF000 | 0x009D4000 | 0x009D3800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.90202 |
.rsrc | 0x01483000 | 0x00016000 | 0x00015200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.96757 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94291 | 1117 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.96082 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.20562 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.87138 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
ICMP.DLL |
IMAGEHLP.DLL |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSI.DLL |
MSVCRT.dll |
NETAPI32.DLL |
Total processes
75
Monitored processes
24
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Windows\System32\reg.exe" add HKLM\Software\Policies\Microsoft\Office\16.0\Common\OfficeUpdate /v UpdateBranch /d Current /f | C:\Windows\System32\reg.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | "powershell" -command "& { (New-Object Net.WebClient).DownloadFile('http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.14026.20308/i320.cab', 'C:\Users\admin\AppData\Local\Temp\over294306\i320.cab') }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | OInstall.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | "C:\Windows\System32\cmd.exe" /D /c files.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1444 | "C:\Windows\System32\cmd.exe" /D /c reg.exe add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Office\ClickToRun\Configuration" /f /v "UpdateChannelChanged" /t REG_SZ /d True | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1564 | "powershell" -command "& { (New-Object Net.WebClient).DownloadFile('http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32.cab', 'C:\Users\admin\AppData\Local\Temp\over294306\v32.cab') }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | OInstall.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | "C:\Windows\System32\cmd.exe" /D /c reg.exe add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Office\ClickToRun\Configuration" /f /v "AudienceId" /t REG_SZ /d 492350f6-3a01-4f97-b9c0-c7c6ddf67d60 | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2140 | "expand" i320.cab -F:* "C:\Program Files\Common Files\microsoft Shared\ClickToRun" | C:\Windows\system32\expand.exe | OInstall.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2188 | "expand" v32.cab -F:VersionDescriptor.xml C:\Users\admin\AppData\Local\Temp\over294306 | C:\Windows\system32\expand.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | reg.exe add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Office\ClickToRun\Configuration" /f /v "UpdateChannelChanged" /t REG_SZ /d True | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | reg.exe add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Office\ClickToRun\Configuration" /f /v "CDNBaseUrl" /t REG_SZ /d http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60 | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 463
Read events
1 033
Write events
417
Delete events
13
Modification events
| (PID) Process: | (3324) OInstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (184) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Office\16.0\Common\OfficeUpdate |
| Operation: | write | Name: | UpdateBranch |
Value: Current | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1564) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
111
Suspicious files
11
Text files
21
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1564 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\96AIRM16ULSY5GT64JFS.temp | — | |
MD5:— | SHA256:— | |||
| 2188 | expand.exe | C:\Users\admin\AppData\Local\Temp\over294306\$dpx$.tmp\90014edbb5515e43b7d1e92a9ef5328c.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | expand.exe | C:\Windows\Logs\DPX\setuperr.log | — | |
MD5:— | SHA256:— | |||
| 3636 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FTXCUPKM7W9FIZ8RI2H4.temp | — | |
MD5:— | SHA256:— | |||
| 352 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\30FXH3JFSXCW531GYFPN.temp | — | |
MD5:— | SHA256:— | |||
| 352 | powershell.exe | C:\Users\admin\AppData\Local\Temp\over294306\i320.cab | — | |
MD5:— | SHA256:— | |||
| 2140 | expand.exe | C:\Program Files\Common Files\microsoft Shared\ClickToRun\$dpx$.tmp\aad336ed4744da458ff3d6724cdbc675.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | OInstall.exe | C:\Users\admin\AppData\Local\Temp\files\files.dat | executable | |
MD5:55D21B2C272A5D6B9F54FA9ED82BF9EB | SHA256:7A1C82E264258470D14CA345EA1A9B6FC34FA19B393A92077A01BE5F1AD08F47 | |||
| 2140 | expand.exe | C:\Program Files\Common Files\microsoft Shared\ClickToRun\$dpx$.tmp\8dfc3114d0a03042afd464c5cca0f327.tmp | — | |
MD5:— | SHA256:— | |||
| 1564 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF18e951.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
14
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1564 | powershell.exe | GET | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32.cab | unknown | — | — | whitelisted |
352 | powershell.exe | GET | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.14026.20308/i320.cab | unknown | — | — | whitelisted |
1564 | powershell.exe | GET | 200 | 23.32.238.187:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32.cab | US | compressed | 9.68 Kb | whitelisted |
3100 | OfficeClickToRun.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | der | 471 b | whitelisted |
3632 | powershell.exe | GET | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.14026.20308/i321033.cab | unknown | — | — | whitelisted |
352 | powershell.exe | GET | 200 | 23.32.238.187:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.14026.20308/i320.cab | US | compressed | 23.6 Mb | whitelisted |
3632 | powershell.exe | GET | 200 | 23.32.238.208:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.14026.20308/i321033.cab | US | compressed | 8.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1564 | powershell.exe | 2.18.232.120:80 | officecdn.microsoft.com | Akamai International B.V. | — | whitelisted |
352 | powershell.exe | 2.18.232.120:80 | officecdn.microsoft.com | Akamai International B.V. | — | whitelisted |
3632 | powershell.exe | 2.18.232.120:80 | officecdn.microsoft.com | Akamai International B.V. | — | whitelisted |
3632 | powershell.exe | 23.32.238.208:80 | officecdn.microsoft.com.edgesuite.net | XO Communications | US | unknown |
2500 | OfficeClickToRun.exe | 52.113.194.132:443 | ecs.office.com | Microsoft Corporation | US | suspicious |
3100 | OfficeClickToRun.exe | 52.113.194.132:443 | ecs.office.com | Microsoft Corporation | US | suspicious |
3100 | OfficeClickToRun.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3100 | OfficeClickToRun.exe | 51.140.157.153:443 | self.events.data.microsoft.com | Microsoft Corporation | GB | unknown |
1564 | powershell.exe | 23.32.238.187:80 | officecdn.microsoft.com.edgesuite.net | XO Communications | US | suspicious |
352 | powershell.exe | 23.32.238.187:80 | officecdn.microsoft.com.edgesuite.net | XO Communications | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officecdn.microsoft.com |
| whitelisted |
officecdn.microsoft.com.edgesuite.net |
| whitelisted |
ecs.office.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |