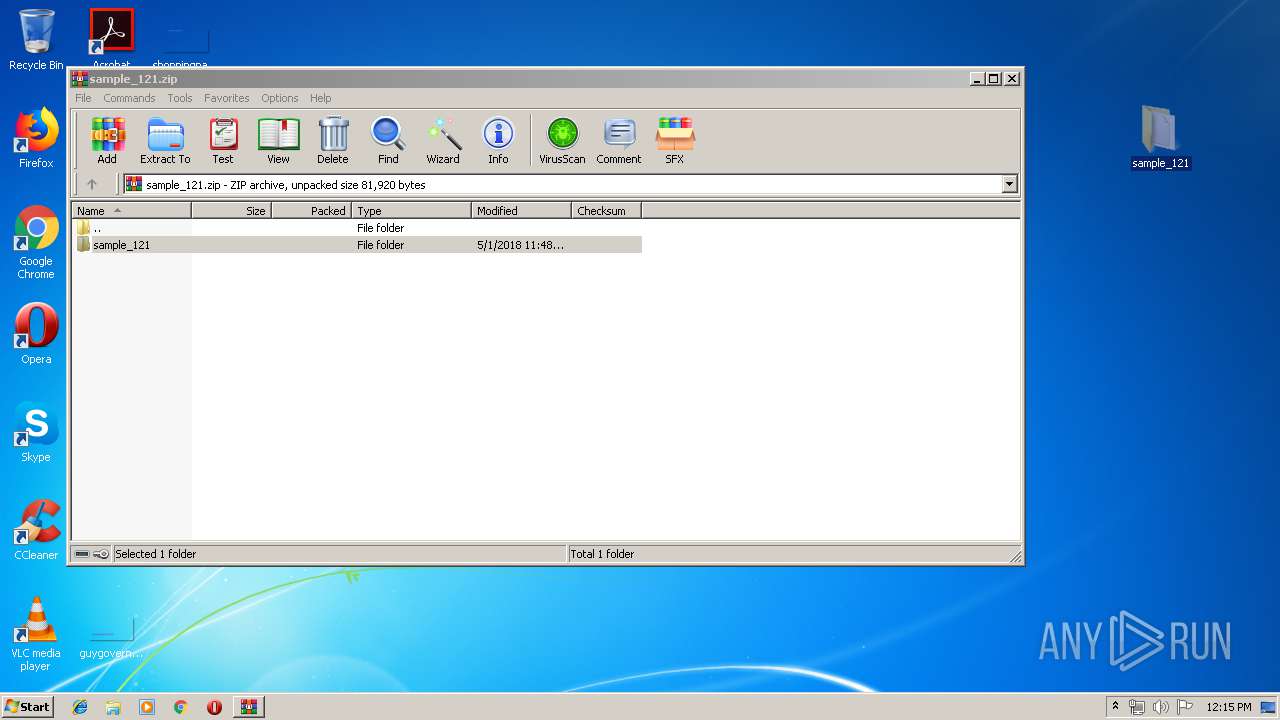
| File name: | sample_121.zip |
| Full analysis: | https://app.any.run/tasks/bad6fbba-7da6-4abb-9e7c-ec75cb92a86e |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 11:14:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9D1D67004E2C15FA0B76BA11E69DEA7F |
| SHA1: | 9BCEC9CC4AFF2F2E669855621ADA42AB1F13FB6D |
| SHA256: | 43142AC1D06684C0AFA10ACB9B5E1DA08396DBFA40EB6251EB3F3FB4A504CE23 |
| SSDEEP: | 1536:KNRNQLbyQ3/YOFZmn8XPbRaKyF4f8EPUh39mwITQE8i3LFlH7K7ie:KNRmLbRY2OwUKi4/Udx6QE8i7b7i |
MALICIOUS
Changes the autorun value in the registry
- sample_121.exe (PID: 2608)
Starts NET.EXE for service management
- sample_121.exe (PID: 2608)
Application was dropped or rewritten from another process
- sample_121.exe (PID: 2608)
SUSPICIOUS
No suspicious indicators.INFO
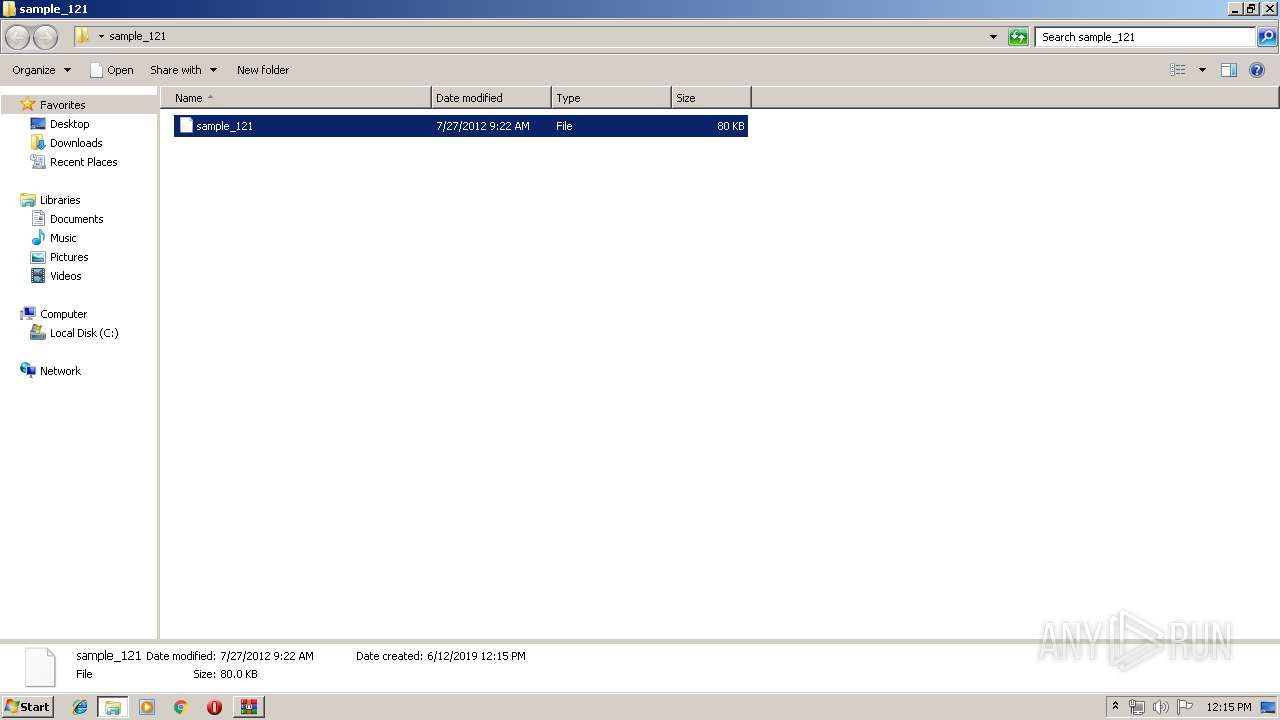
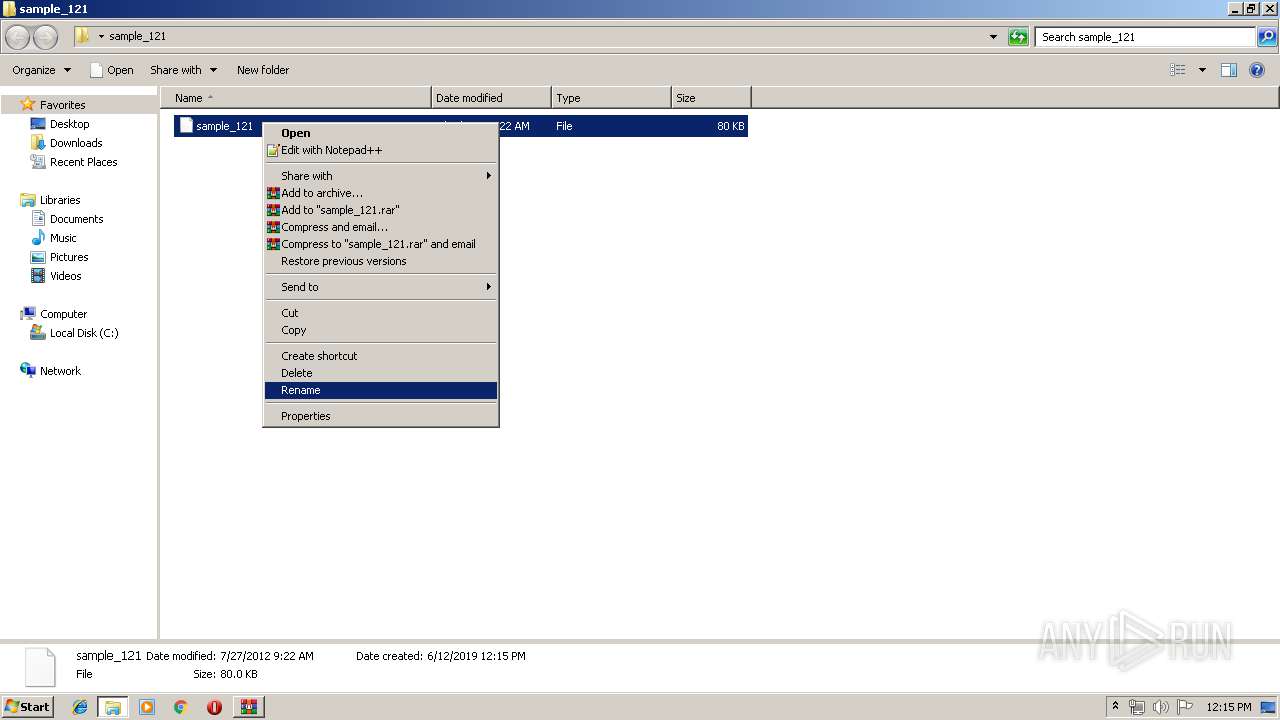
Manual execution by user
- sample_121.exe (PID: 2608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:01 18:48:23 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_121/ |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2320 | net start "Task Scheduler" | C:\Windows\system32\net.exe | — | sample_121.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2460 | C:\Windows\system32\net1 start "Task Scheduler" | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
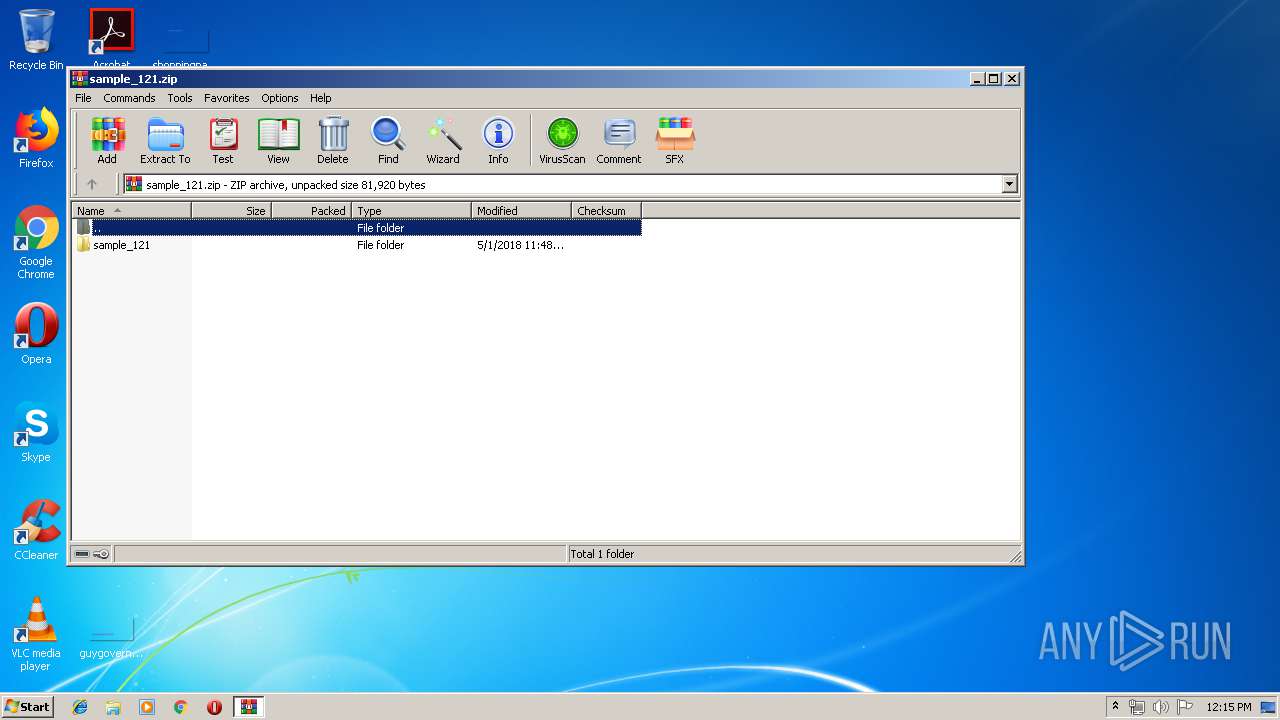
| 2464 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample_121.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
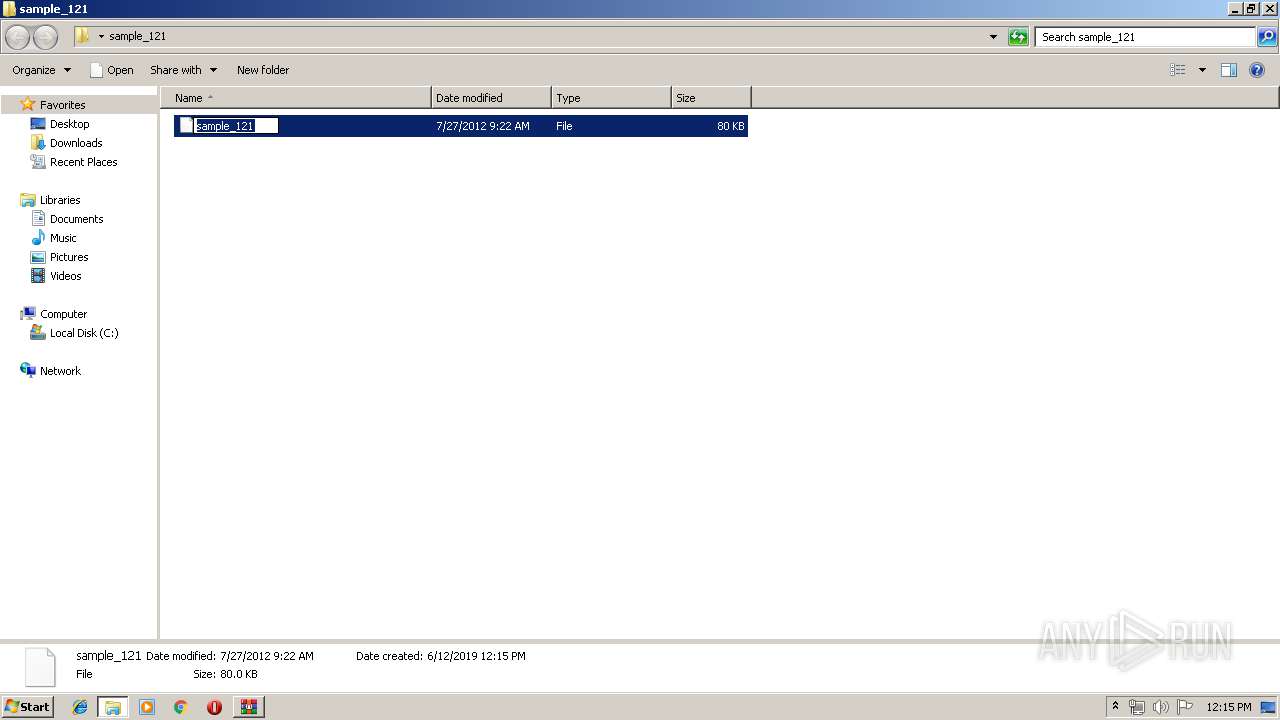
| 2608 | "C:\Users\admin\Desktop\sample_121\sample_121.exe" | C:\Users\admin\Desktop\sample_121\sample_121.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
438
Read events
428
Write events
10
Delete events
0
Modification events
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_121.zip | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
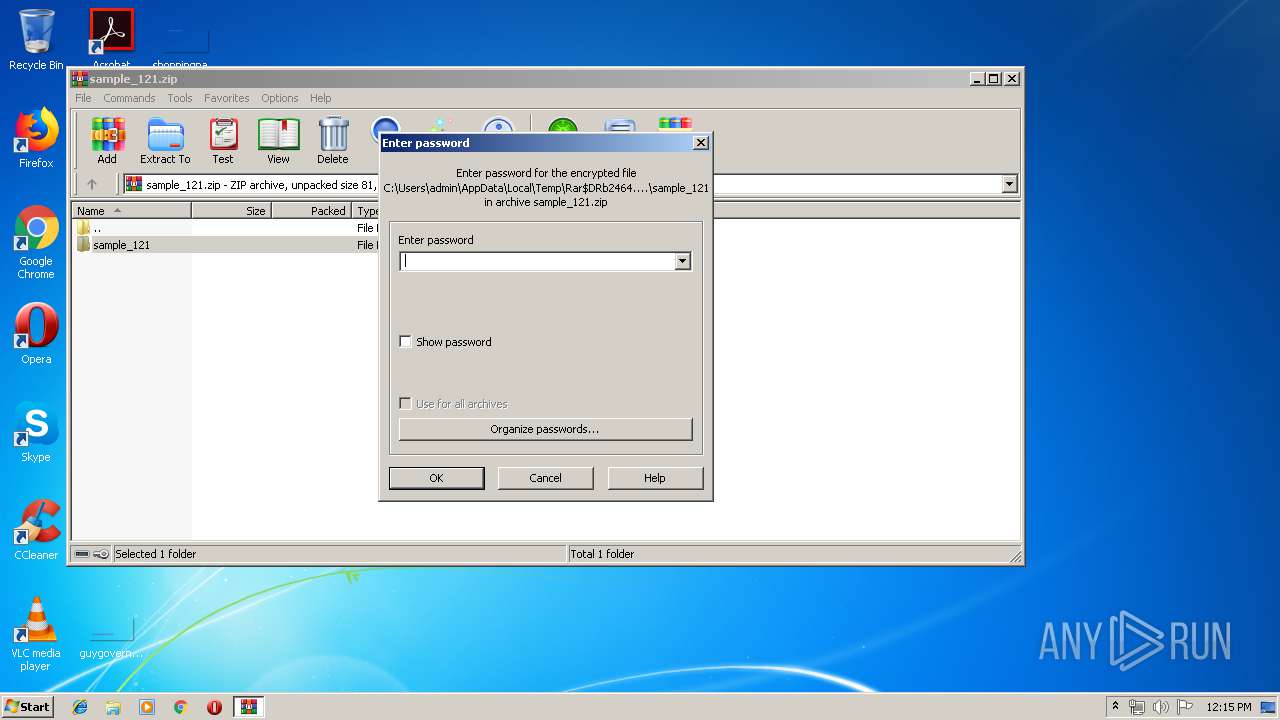
| (PID) Process: | (2464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2608) sample_121.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 07428BE0 |
Value: C:\Windows\07428BE0\svchsot.exe | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
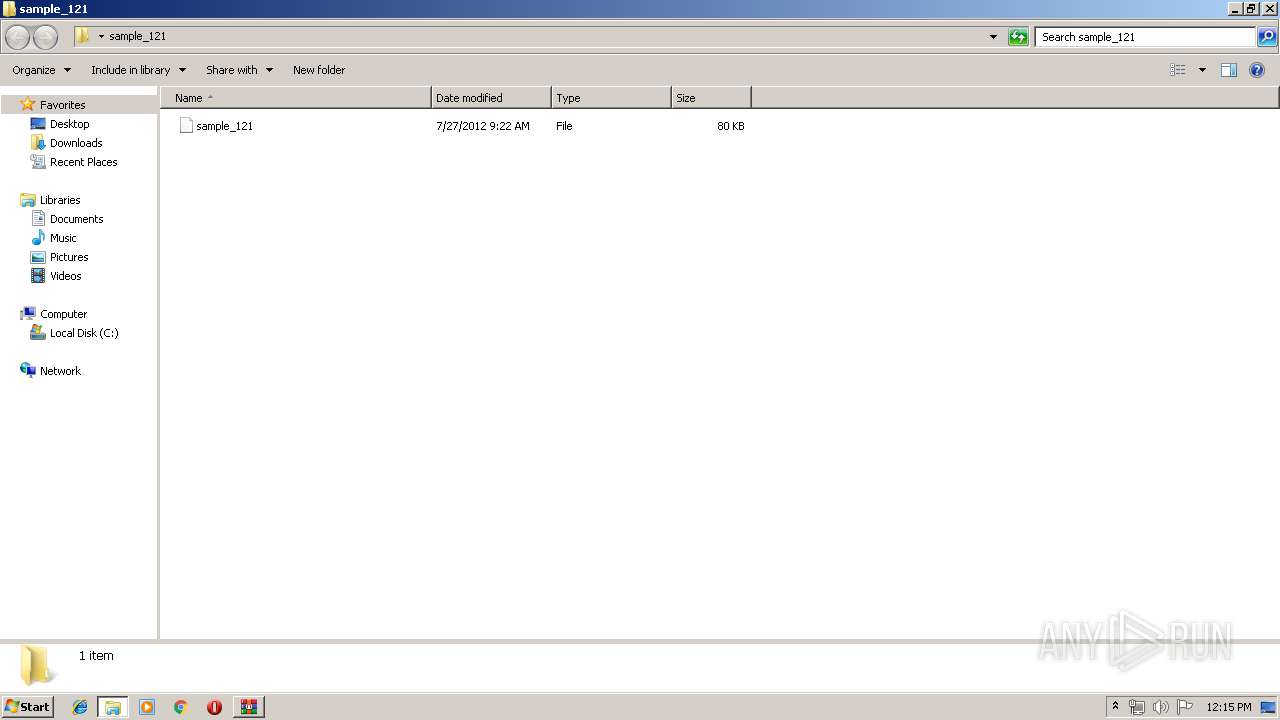
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2464.10675\sample_121\sample_121 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
3
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2608 | sample_121.exe | 157.122.62.205:512 | pmx09.3322.org | China Unicom Guangzhou network | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pmx09.3322.org |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to 3322.org Domain |