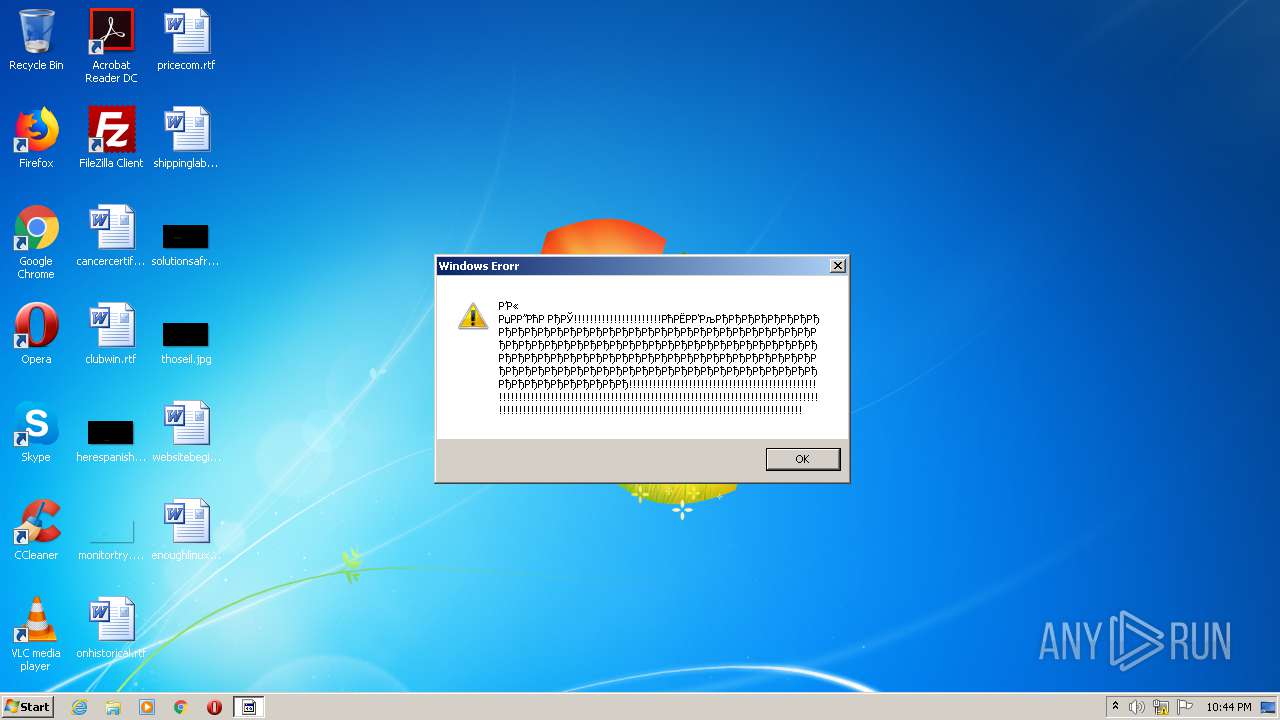
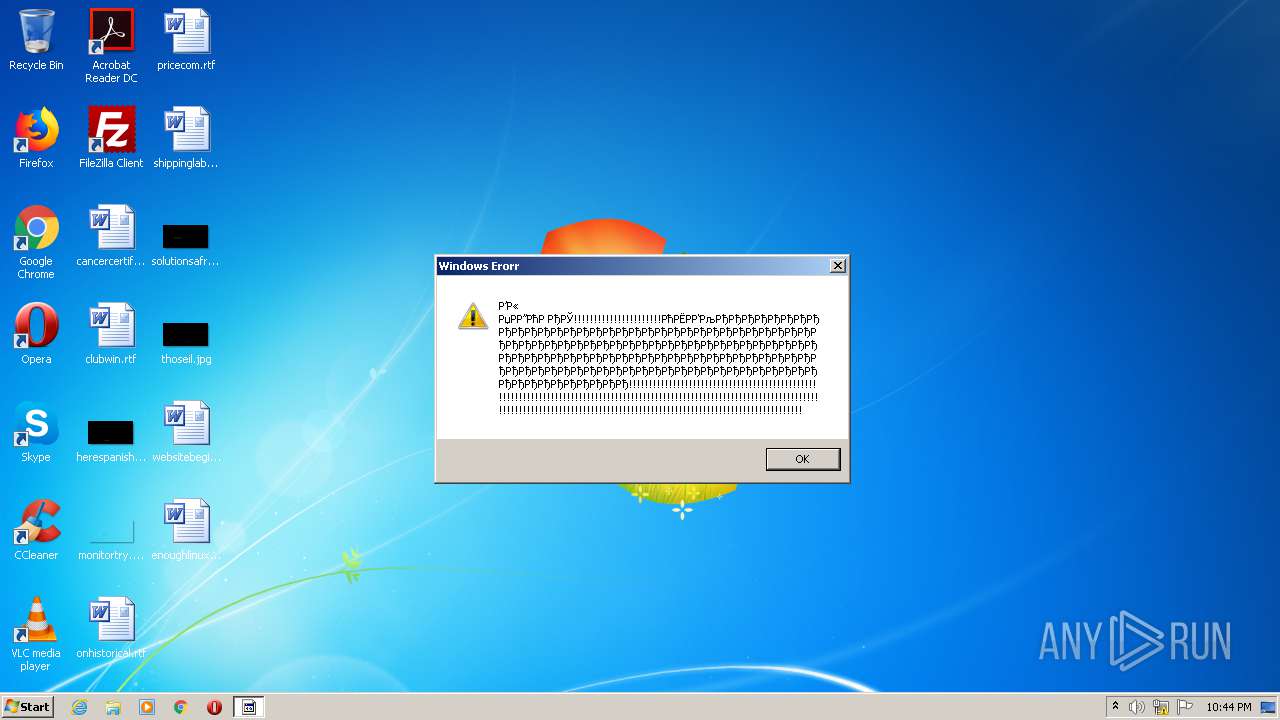
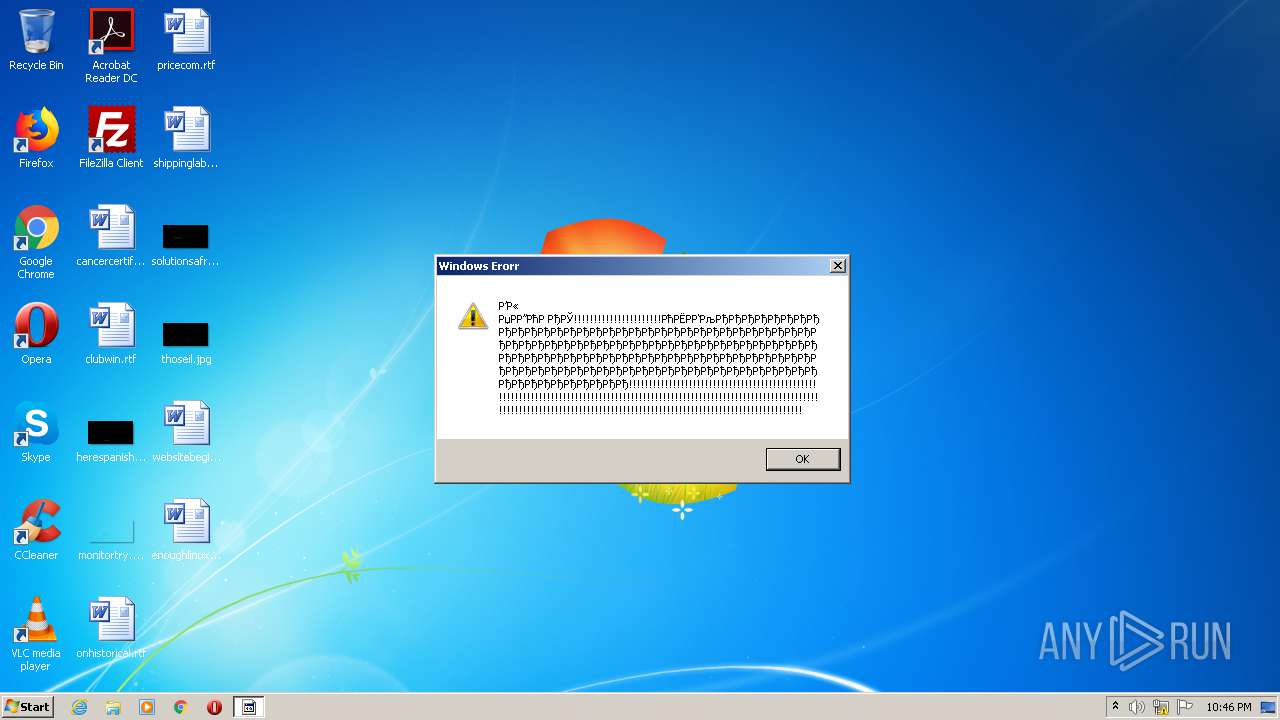
| File name: | Servfffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffer.exe |
| Full analysis: | https://app.any.run/tasks/5f487966-1d6e-465b-8247-2d5876ea2e54 |
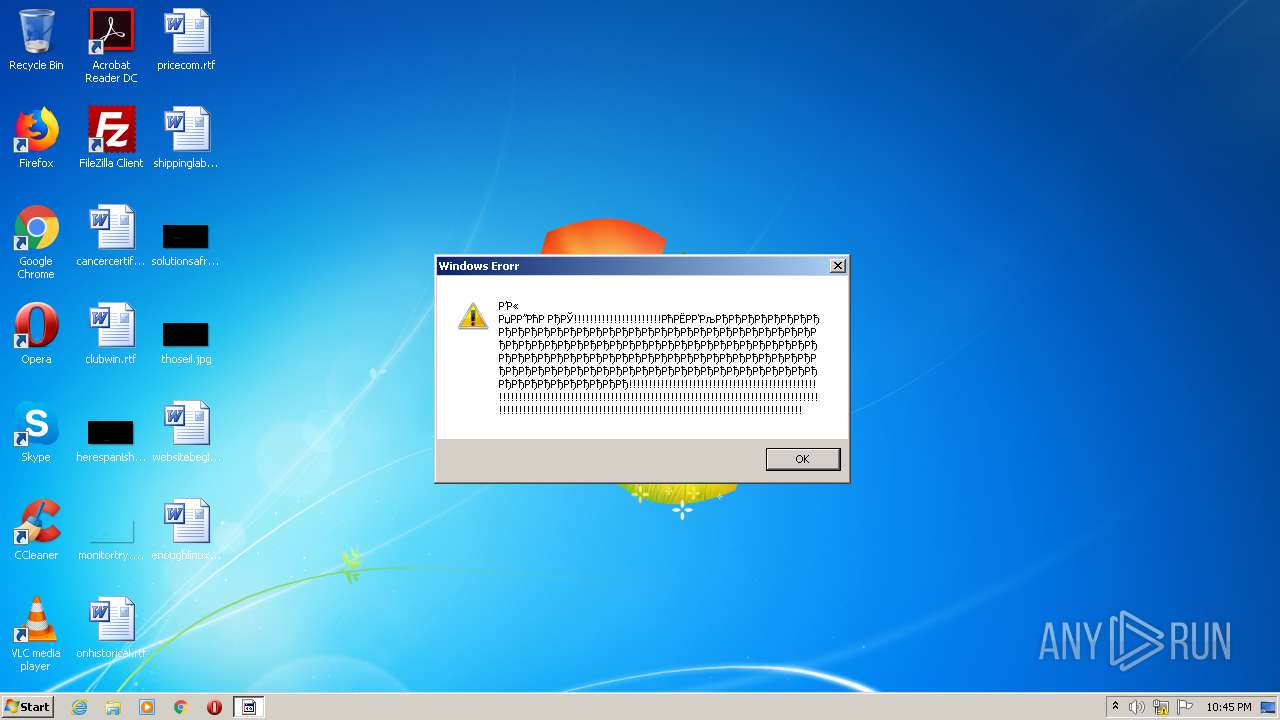
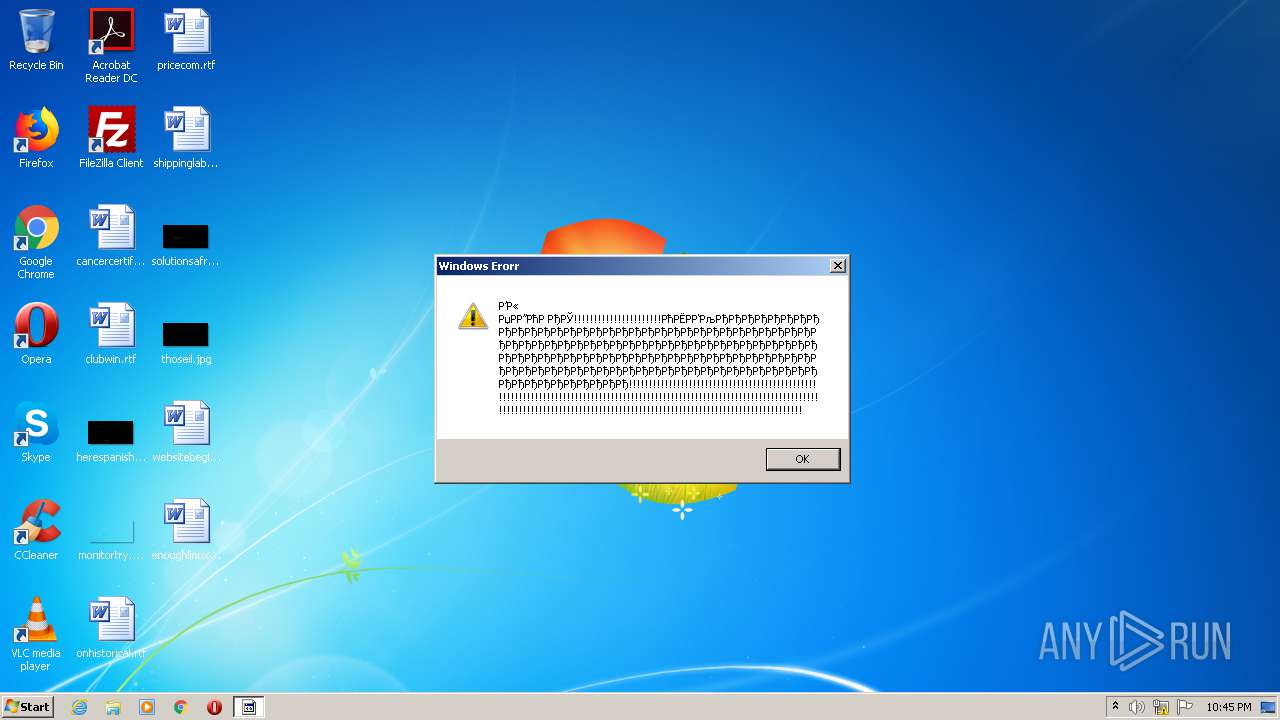
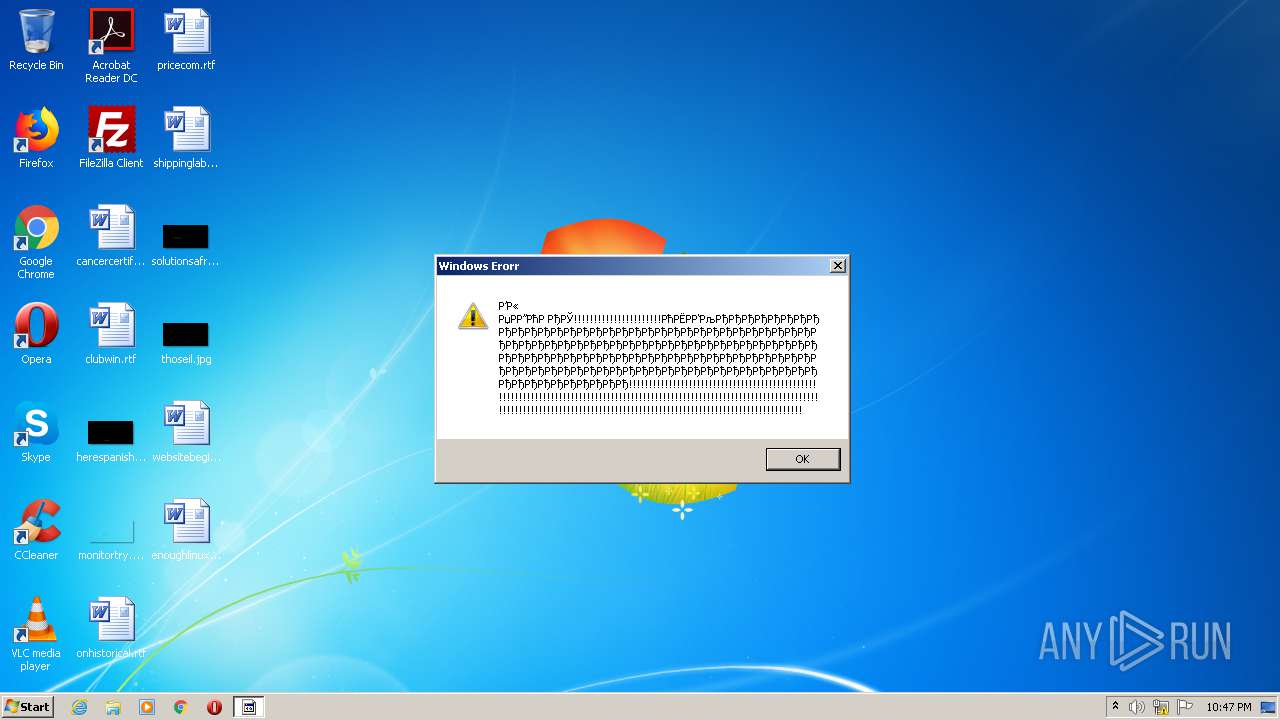
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 21:44:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | CCB7382E298E3AF4455625D3357782BD |
| SHA1: | BBE2554C9A2F206DD0D9B22A24894D9D80AF53CD |
| SHA256: | 4311CE24CDC83B3425CEB47665E8B10062DE6B21A35DE24B393196EAD572B643 |
| SSDEEP: | 1536:Bq9stZxxBiXtB8dwbJjEwzGi1dD4DigS:Bq6xBiXtBQ4Gi1dmH |
MALICIOUS
Writes to a start menu file
- server.exe (PID: 2432)
- server.exe (PID: 2604)
- server.exe (PID: 3760)
- server.exe (PID: 2496)
- server.exe (PID: 2752)
- server.exe (PID: 1792)
- server.exe (PID: 2908)
- server.exe (PID: 2780)
- server.exe (PID: 2300)
SUSPICIOUS
Starts itself from another location
- Servfffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffer.exe (PID: 2540)
- server.exe (PID: 2432)
- svchost.exe (PID: 2800)
- server.exe (PID: 2604)
- svchost.exe (PID: 3988)
- server.exe (PID: 3760)
- svchost.exe (PID: 3716)
- server.exe (PID: 2496)
- server.exe (PID: 1792)
- server.exe (PID: 2752)
- svchost.exe (PID: 2292)
- svchost.exe (PID: 2696)
- server.exe (PID: 2908)
- svchost.exe (PID: 1772)
- server.exe (PID: 2780)
- svchost.exe (PID: 1544)
- svchost.exe (PID: 2864)
Creates files in the user directory
- Servfffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffer.exe (PID: 2540)
- svchost.exe (PID: 2800)
- server.exe (PID: 2432)
- server.exe (PID: 2604)
- svchost.exe (PID: 3988)
- server.exe (PID: 3760)
- svchost.exe (PID: 3716)
- server.exe (PID: 2496)
- server.exe (PID: 2752)
- svchost.exe (PID: 2292)
- server.exe (PID: 1792)
- svchost.exe (PID: 2696)
- svchost.exe (PID: 1544)
- server.exe (PID: 2908)
- svchost.exe (PID: 1772)
- server.exe (PID: 2780)
- svchost.exe (PID: 2864)
Executable content was dropped or overwritten
- Servfffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffer.exe (PID: 2540)
- server.exe (PID: 2432)
- svchost.exe (PID: 2800)
- server.exe (PID: 2604)
- svchost.exe (PID: 3988)
- server.exe (PID: 3760)
- svchost.exe (PID: 3716)
- server.exe (PID: 2496)
- server.exe (PID: 2752)
- svchost.exe (PID: 2292)
- server.exe (PID: 1792)
- svchost.exe (PID: 2696)
- svchost.exe (PID: 1544)
- svchost.exe (PID: 1772)
- server.exe (PID: 2908)
- svchost.exe (PID: 2864)
- server.exe (PID: 2780)
- server.exe (PID: 2300)
Creates executable files which already exist in Windows
- server.exe (PID: 2432)
- server.exe (PID: 2604)
- server.exe (PID: 3760)
- server.exe (PID: 2496)
- server.exe (PID: 2752)
- server.exe (PID: 1792)
- server.exe (PID: 2908)
- server.exe (PID: 2780)
Uses NETSH.EXE for network configuration
- server.exe (PID: 2432)
- server.exe (PID: 2604)
- server.exe (PID: 3760)
- server.exe (PID: 2496)
- server.exe (PID: 2752)
- server.exe (PID: 2908)
- server.exe (PID: 2780)
- server.exe (PID: 2300)
- server.exe (PID: 1792)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:10:19 23:34:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 95232 |
| InitializedDataSize: | 512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x192ae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Oct-2020 21:34:19 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 19-Oct-2020 21:34:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000172B4 | 0x00017400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.60366 |
.reloc | 0x0001A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Imports
mscoree.dll |
Total processes
103
Monitored processes
43
Malicious processes
16
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | netsh firewall delete allowedprogram "C:\Users\admin\AppData\Roaming\server.exe" | C:\Windows\system32\netsh.exe | — | server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | netsh firewall add allowedprogram "C:\Users\admin\AppData\Roaming\server.exe" "server.exe" ENABLE | C:\Windows\system32\netsh.exe | — | server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 776 | netsh firewall add allowedprogram "C:\Users\admin\AppData\Roaming\server.exe" "server.exe" ENABLE | C:\Windows\system32\netsh.exe | — | server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 824 | netsh firewall add allowedprogram "C:\Users\admin\AppData\Roaming\server.exe" "server.exe" ENABLE | C:\Windows\system32\netsh.exe | — | server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | netsh firewall add allowedprogram "C:\Users\admin\AppData\Roaming\server.exe" "server.exe" ENABLE | C:\Windows\system32\netsh.exe | — | server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | netsh firewall add allowedprogram "C:\Users\admin\AppData\Roaming\server.exe" "server.exe" ENABLE | C:\Windows\system32\netsh.exe | — | server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | netsh firewall delete allowedprogram "C:\Users\admin\AppData\Roaming\server.exe" | C:\Windows\system32\netsh.exe | — | server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1544 | "C:\Users\admin\AppData\Roaming\Microsoft\svchost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\svchost.exe | server.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1772 | "C:\Users\admin\AppData\Roaming\Microsoft\svchost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\svchost.exe | server.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1792 | "C:\Users\admin\AppData\Roaming\server.exe" | C:\Users\admin\AppData\Roaming\server.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 352
Read events
6 209
Write events
1 143
Delete events
0
Modification events
| (PID) Process: | (2540) Servfffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2540) Servfffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2432) server.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | SEE_MASK_NOZONECHECKS |
Value: 1 | |||
| (PID) Process: | (584) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (584) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (584) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (584) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (584) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (584) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (584) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
Executable files
34
Suspicious files
0
Text files
26
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2432 | server.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Microsoft Corporation.exe | executable | |
MD5:— | SHA256:— | |||
| 2432 | server.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\3f0da42740f5dbf34fd80bc0cf8dbb78Windows Update.exe | executable | |
MD5:— | SHA256:— | |||
| 2540 | Servfffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffer.exe | C:\Users\admin\AppData\Roaming\server.exe | executable | |
MD5:— | SHA256:— | |||
| 2540 | Servfffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffffer.exe | C:\Users\admin\AppData\Roaming\app | text | |
MD5:2099BB64FD1770D321DF364F99B658D1 | SHA256:D53CE6BDBD0C3CB4596AC3103F15824570A9858DA95F63CEDF64CEC11DC44E2D | |||
| 2432 | server.exe | C:\Users\admin\AppData\Roaming\app | text | |
MD5:2099BB64FD1770D321DF364F99B658D1 | SHA256:D53CE6BDBD0C3CB4596AC3103F15824570A9858DA95F63CEDF64CEC11DC44E2D | |||
| 2432 | server.exe | C:\Users\admin\AppData\Local\Temp\melt.txt | text | |
MD5:D00A7F86BAEE94F9158759A5E8365D9F | SHA256:96B8C60EE2B166CF709E15CE27E44EE8D6511540B2CF26C0605504B1EC0DC0A3 | |||
| 2604 | server.exe | C:\Users\admin\AppData\Roaming\Microsoft\svchost.exe | executable | |
MD5:— | SHA256:— | |||
| 2432 | server.exe | C:\Users\admin\AppData\Roaming\Microsoft\svchost.exe | executable | |
MD5:— | SHA256:— | |||
| 2800 | svchost.exe | C:\Users\admin\AppData\Roaming\server.exe | executable | |
MD5:— | SHA256:— | |||
| 2604 | server.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Microsoft Corporation.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report