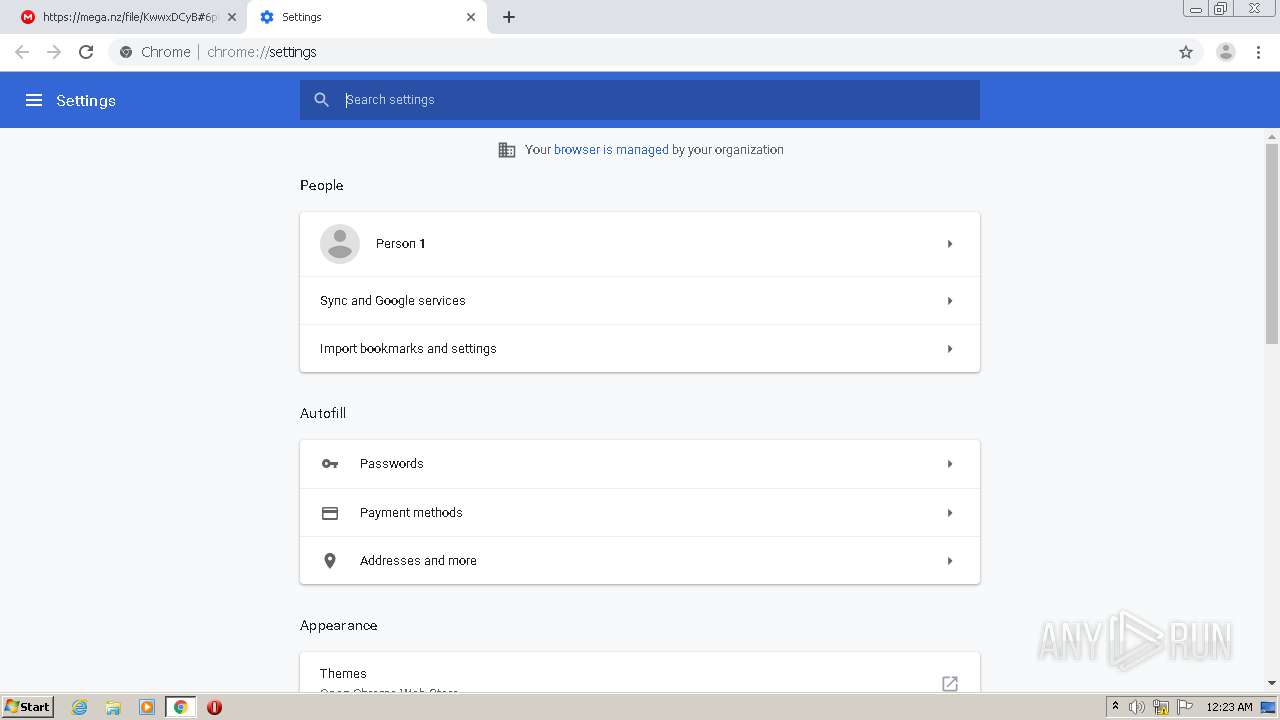
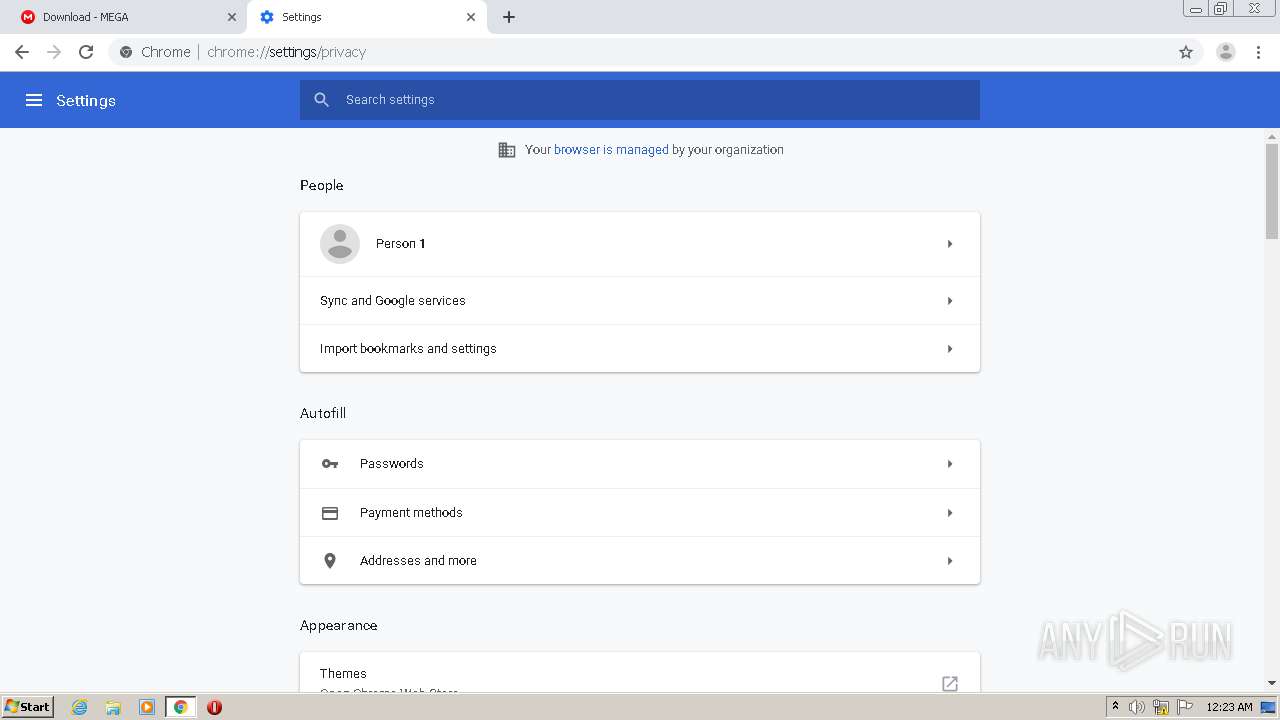
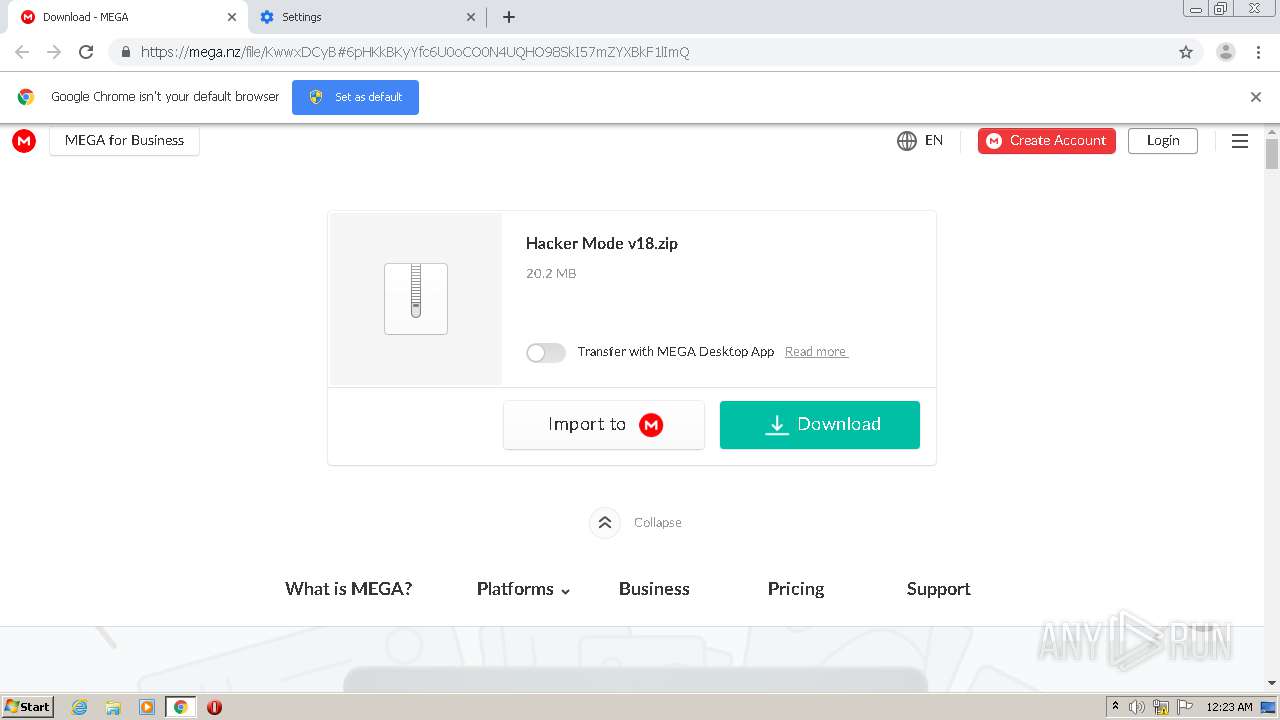
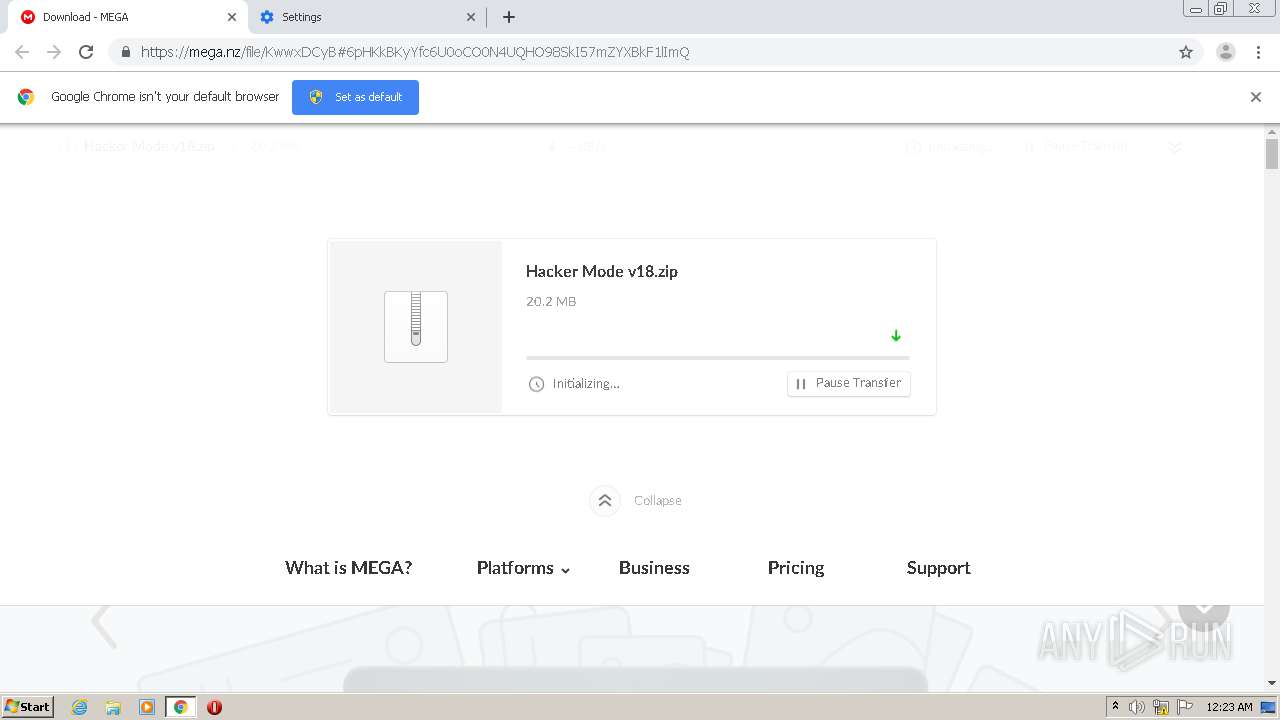
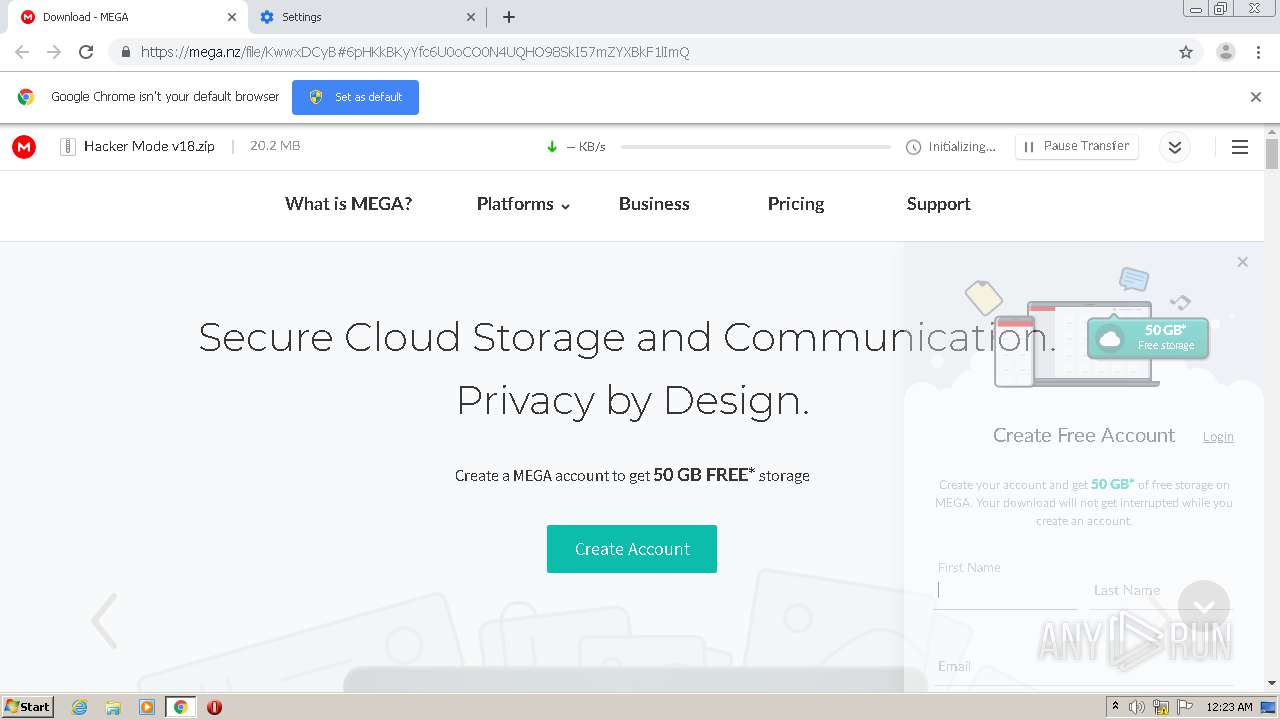
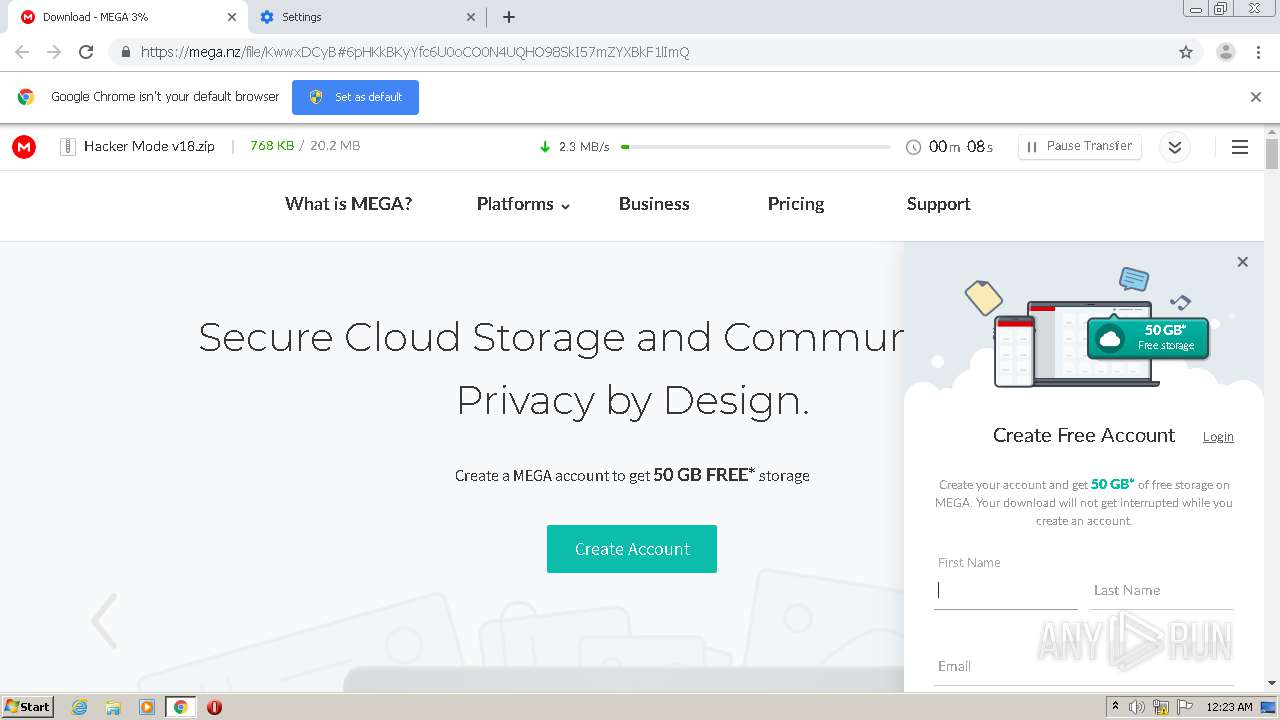
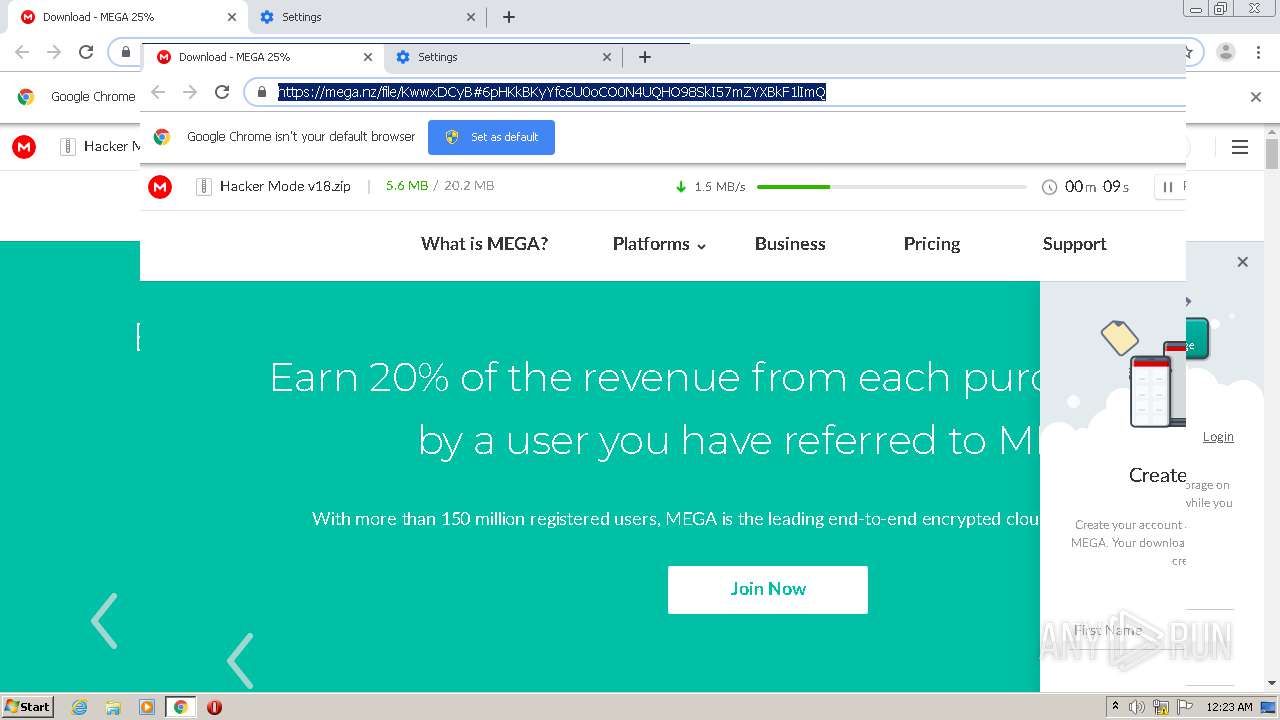
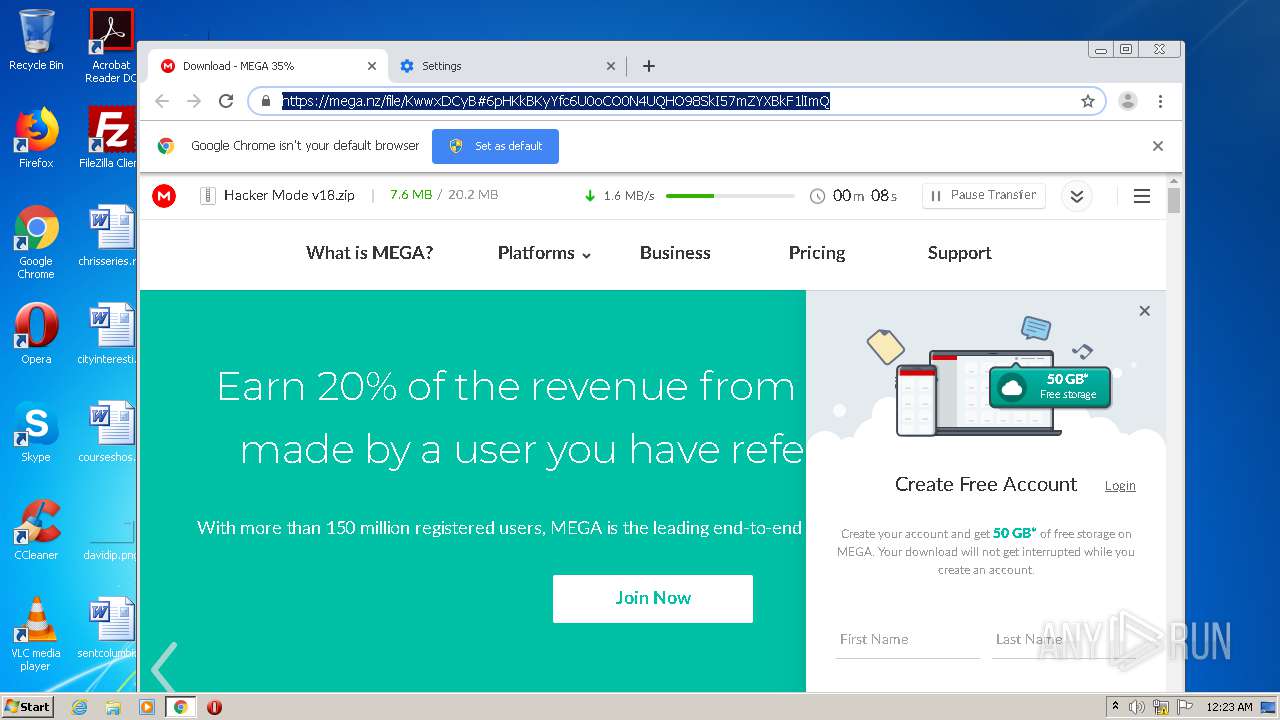
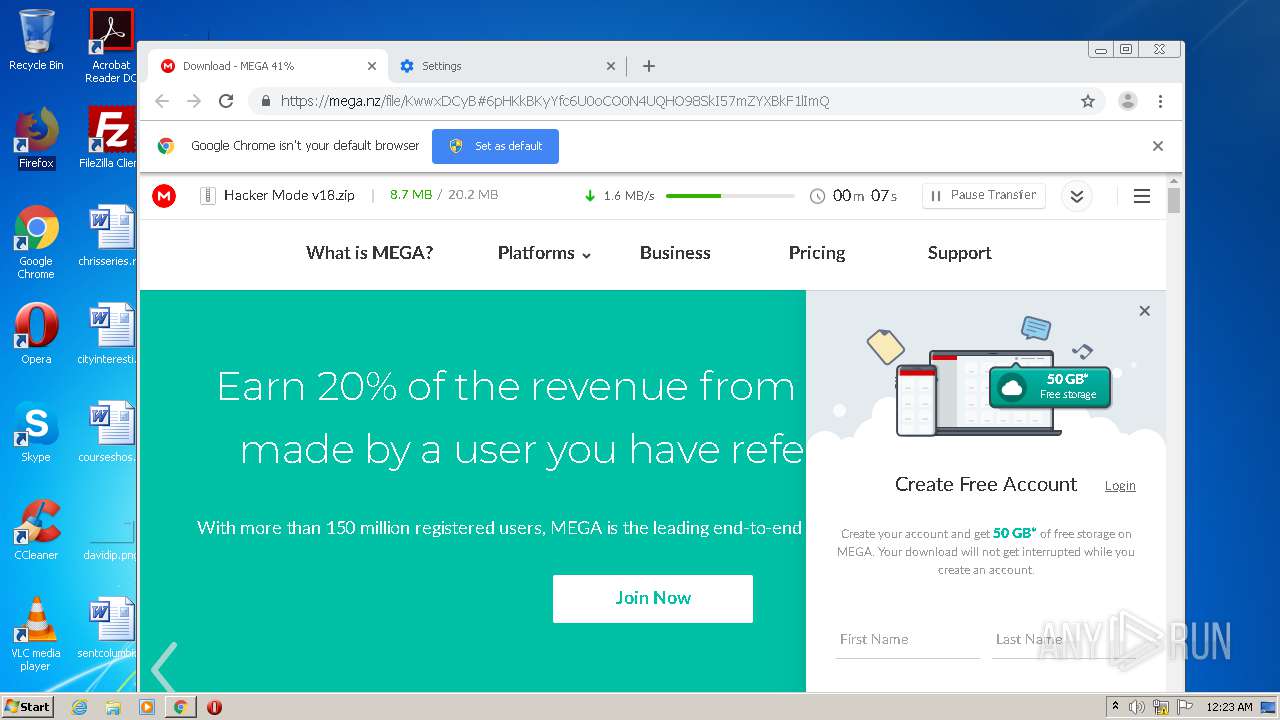
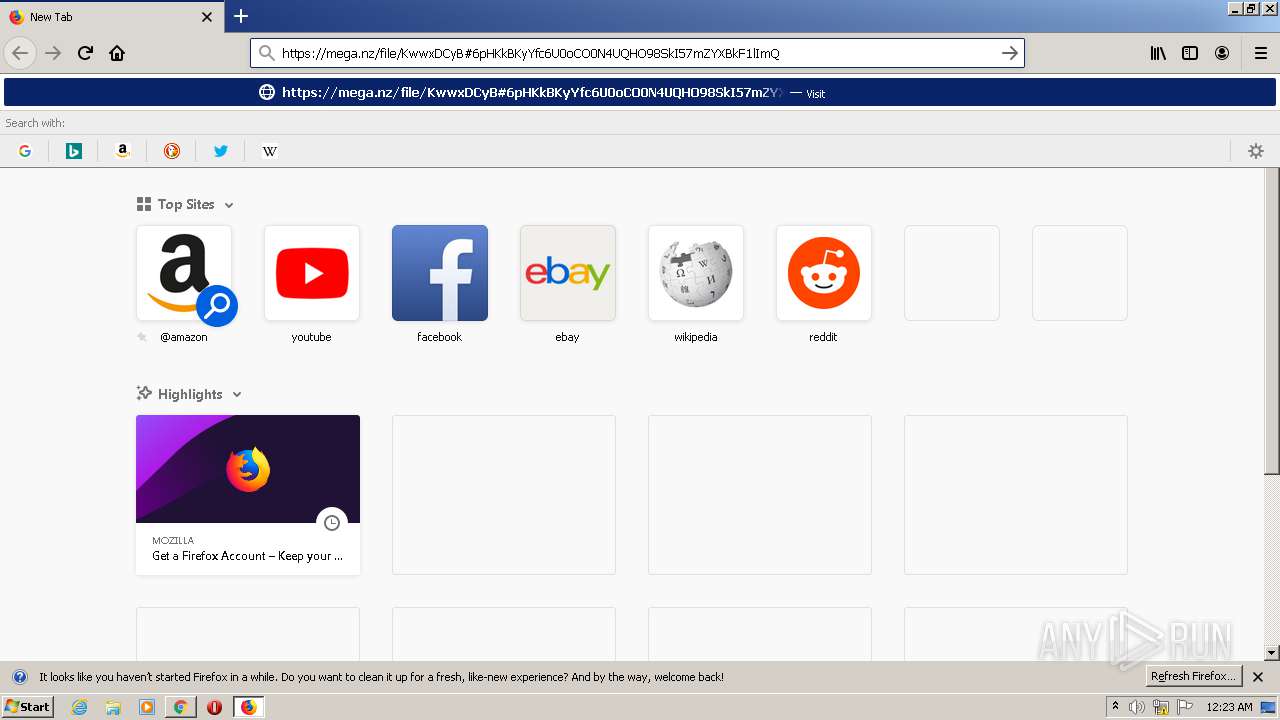
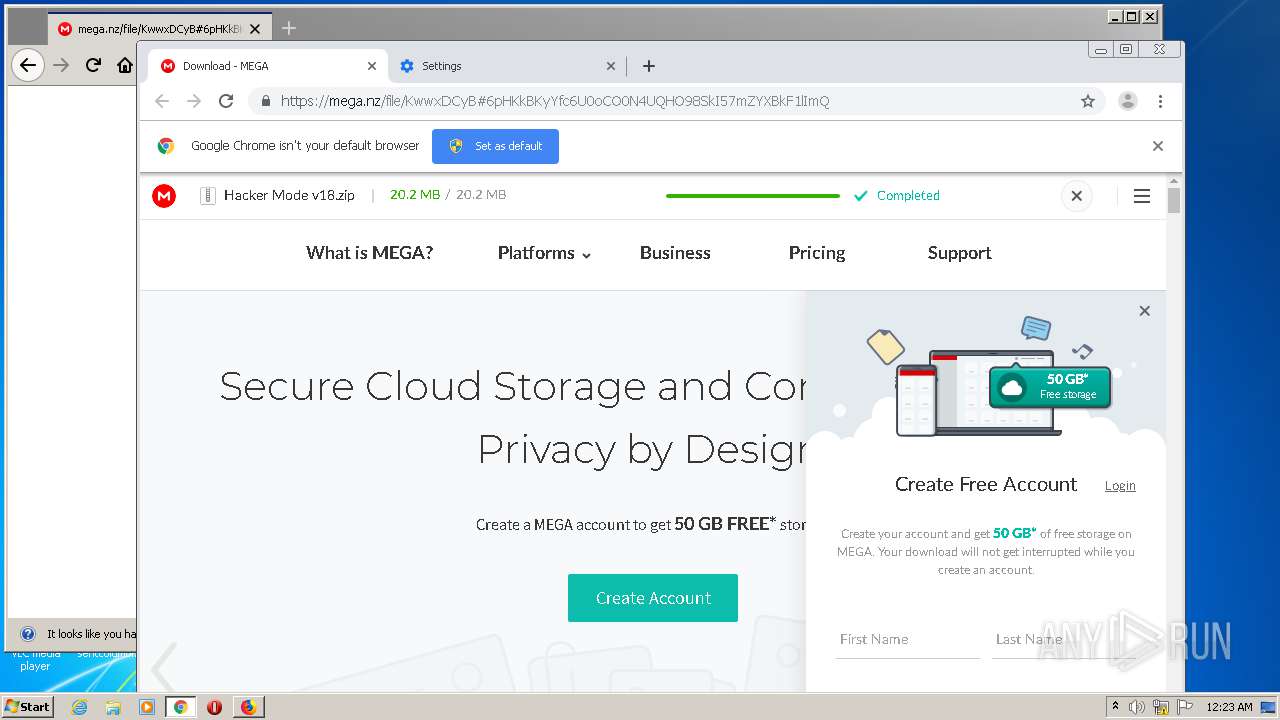
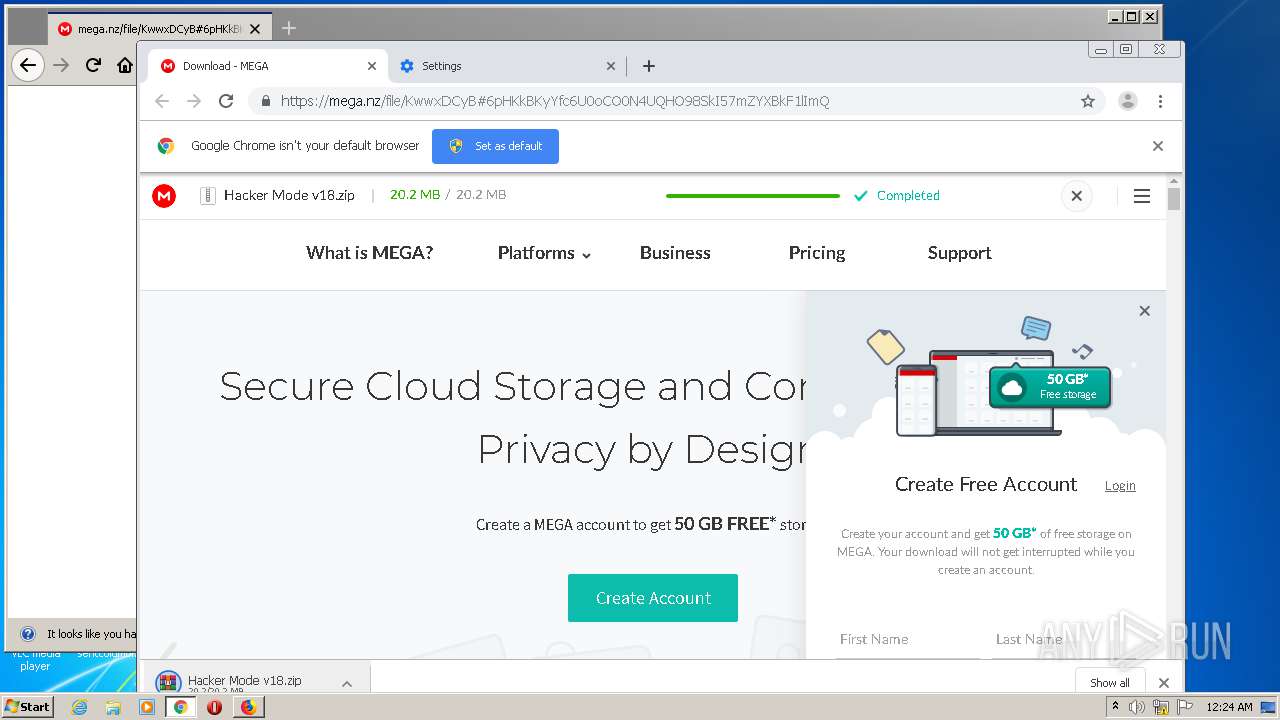
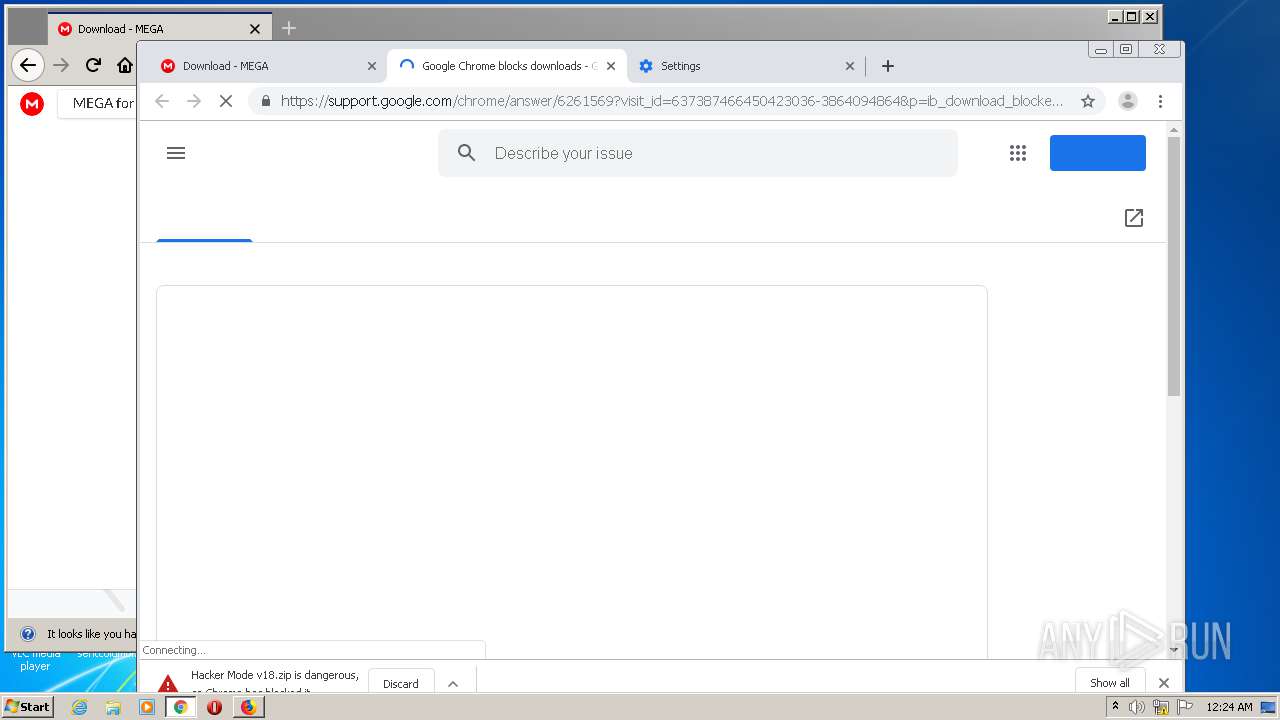
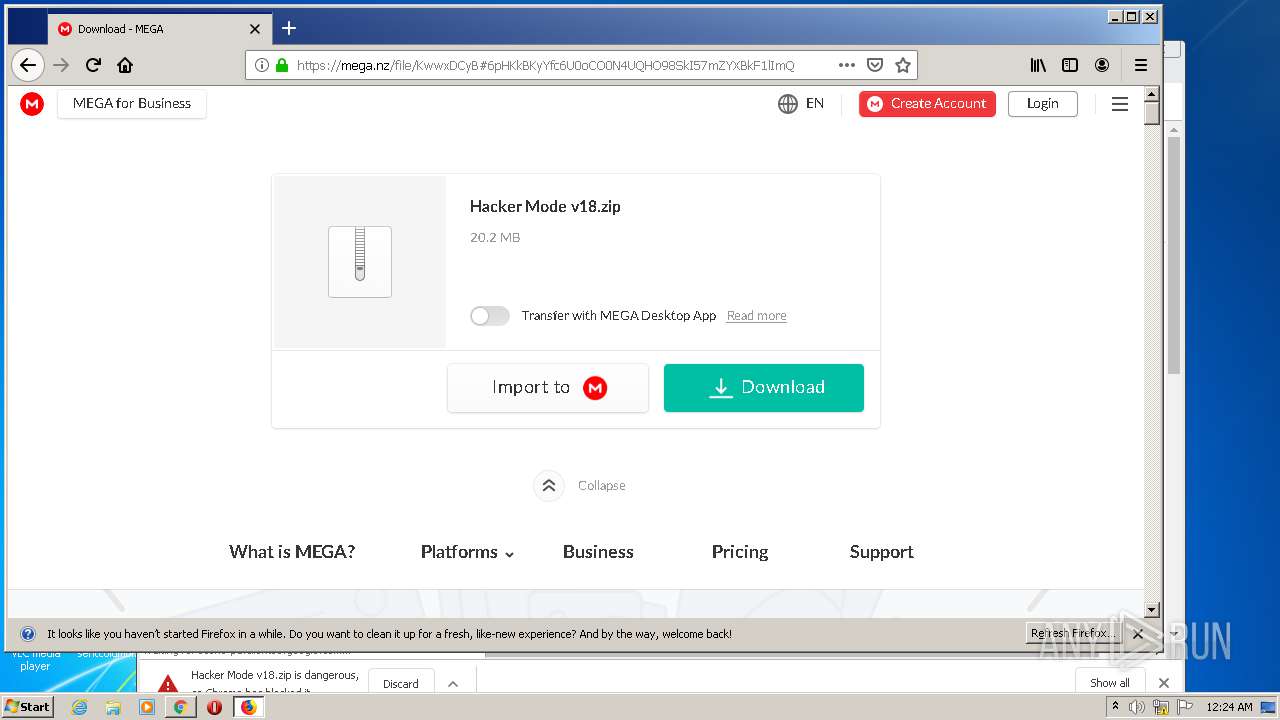
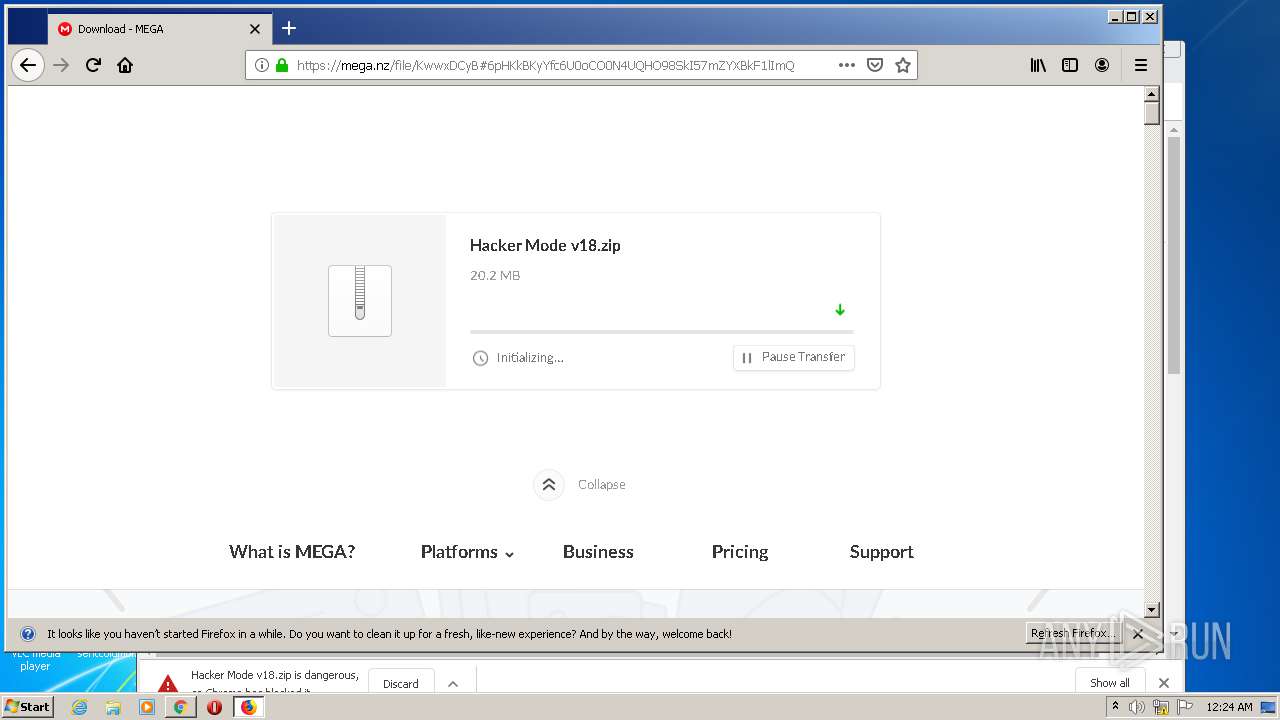
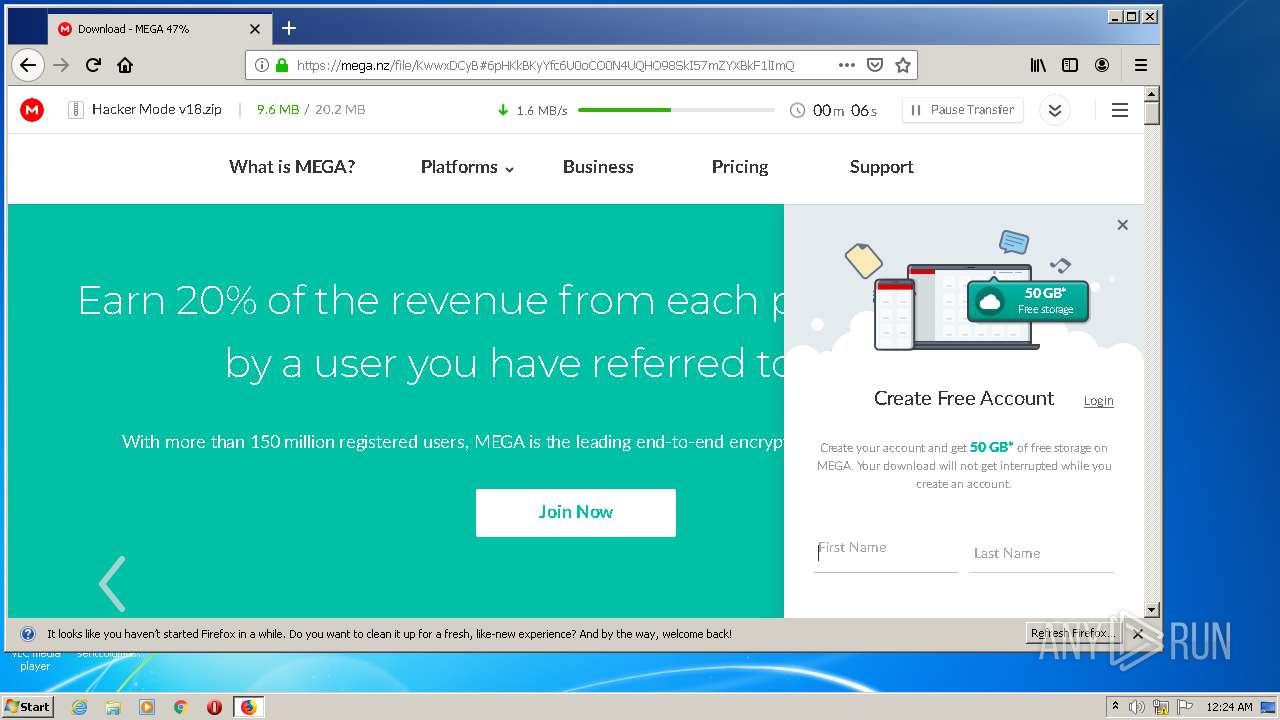
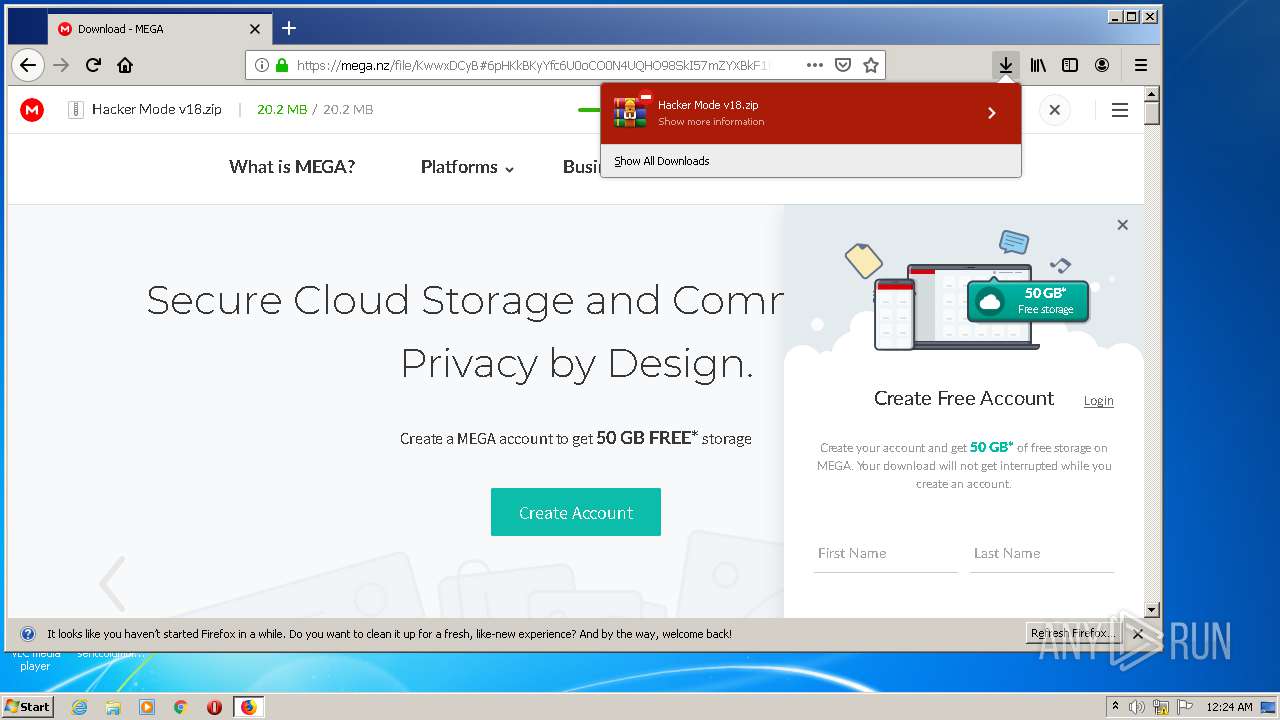
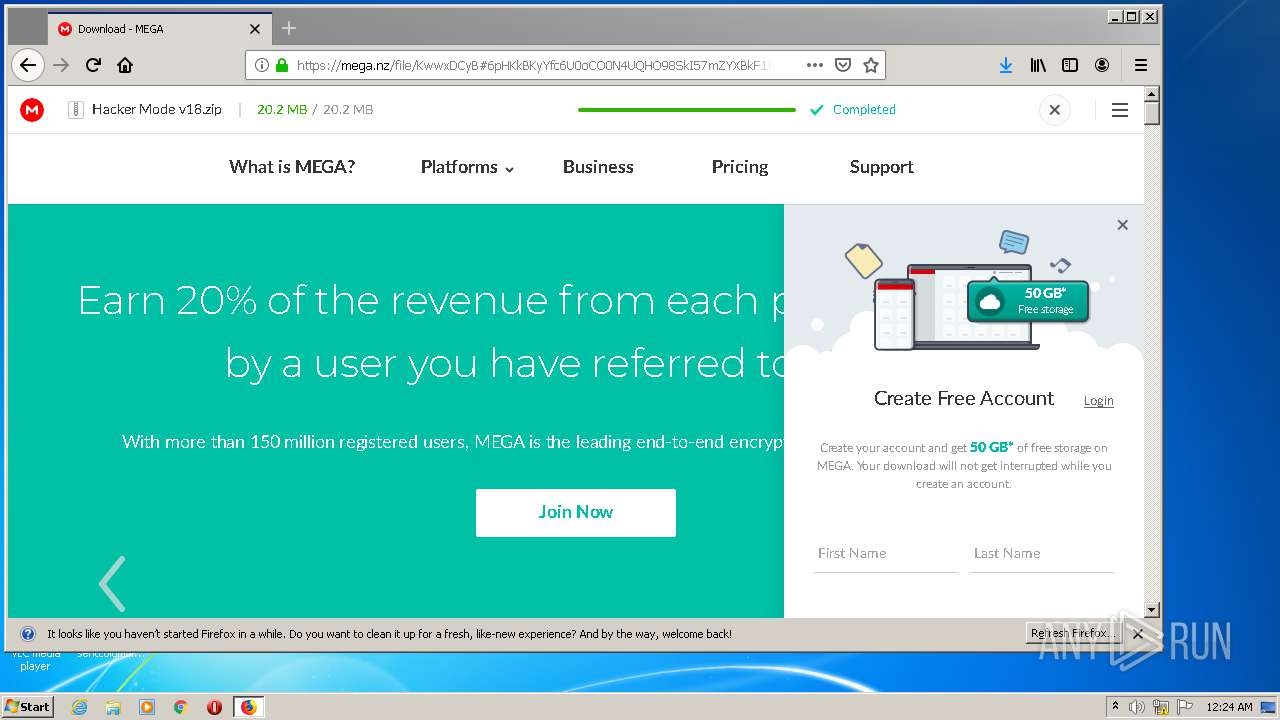
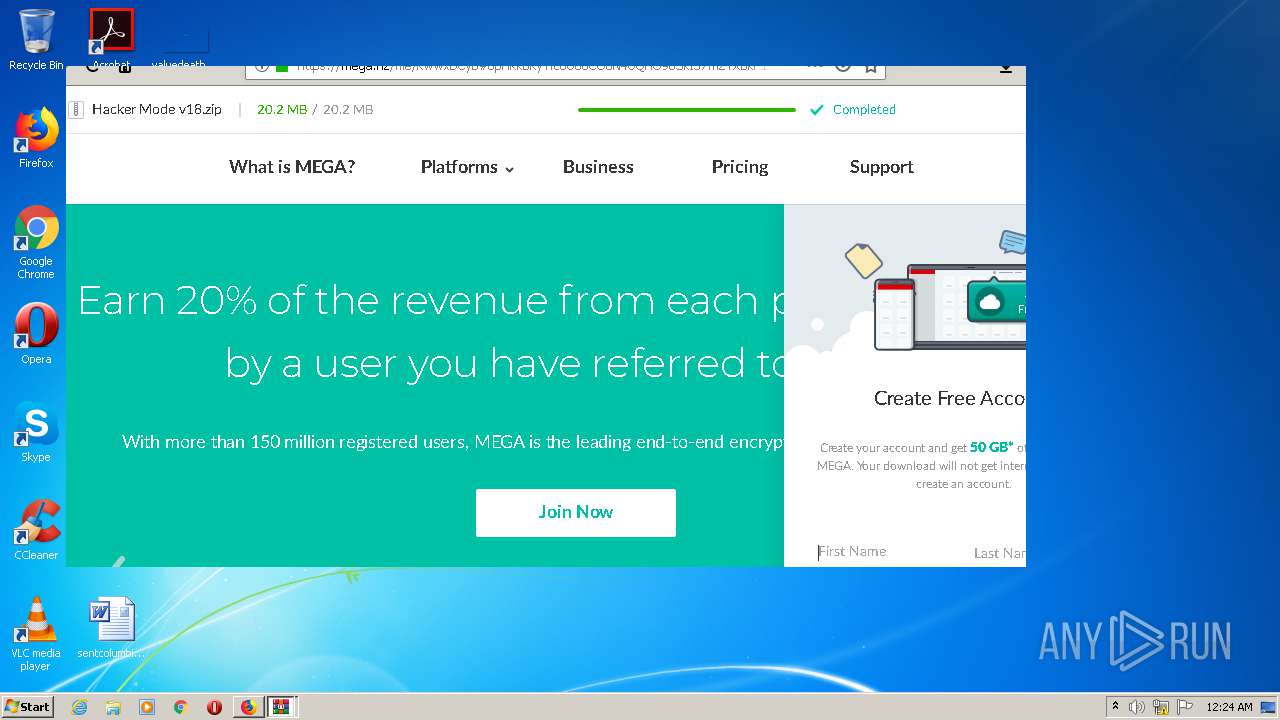
| URL: | https://mega.nz/file/KwwxDCyB#6pHKkBKyYfc6U0oCO0N4UQHO98SkI57mZYXBkF1lImQ |
| Full analysis: | https://app.any.run/tasks/2392d2fe-4c92-44f2-bda6-267dc6afdcfb |
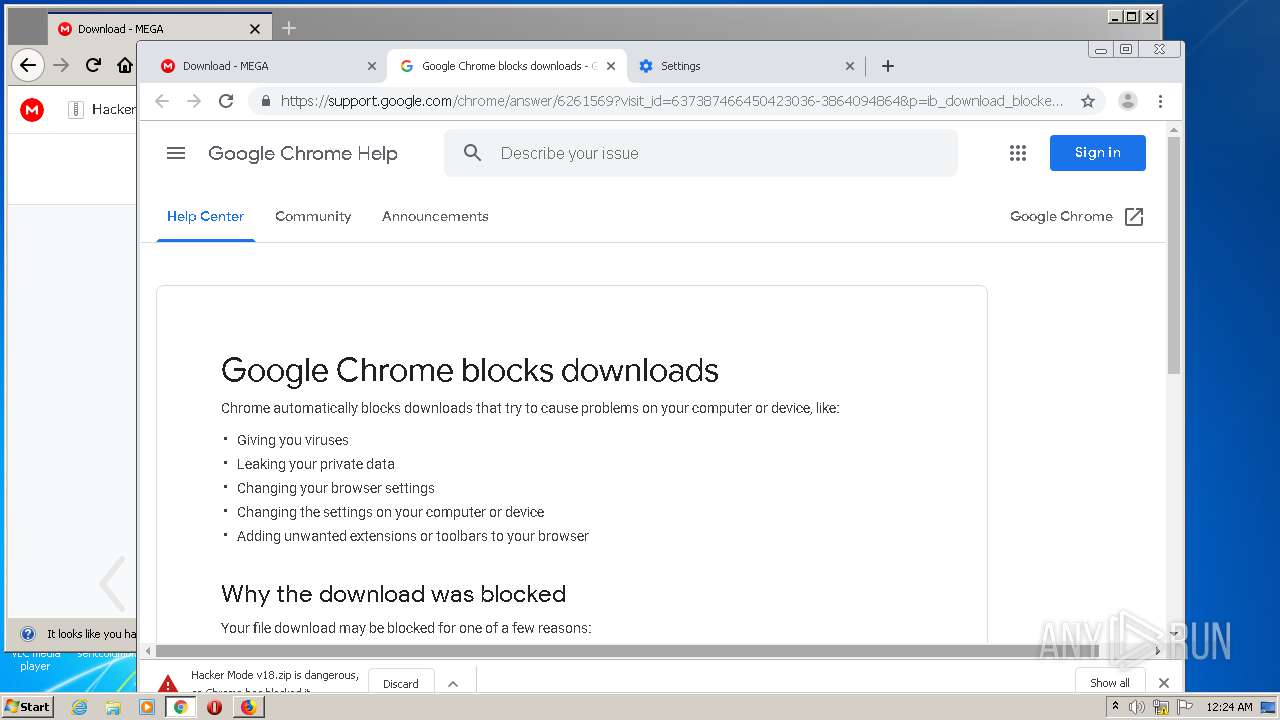
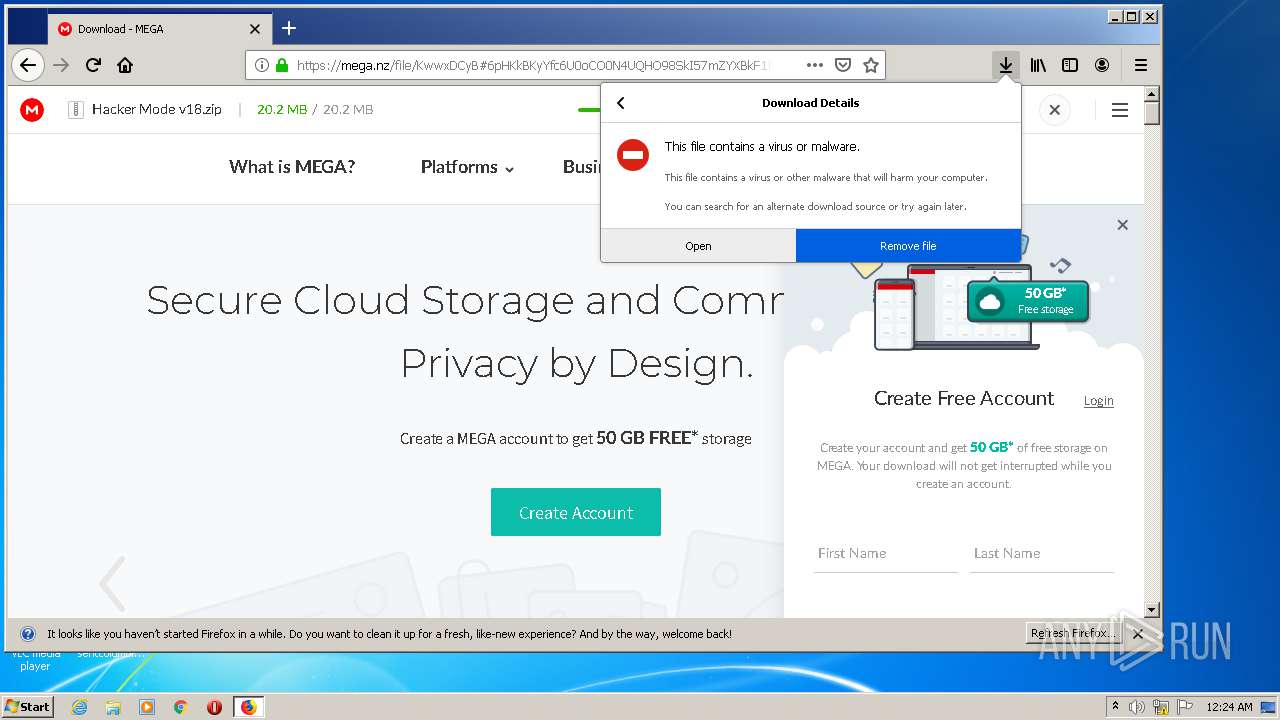
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 23:22:50 |
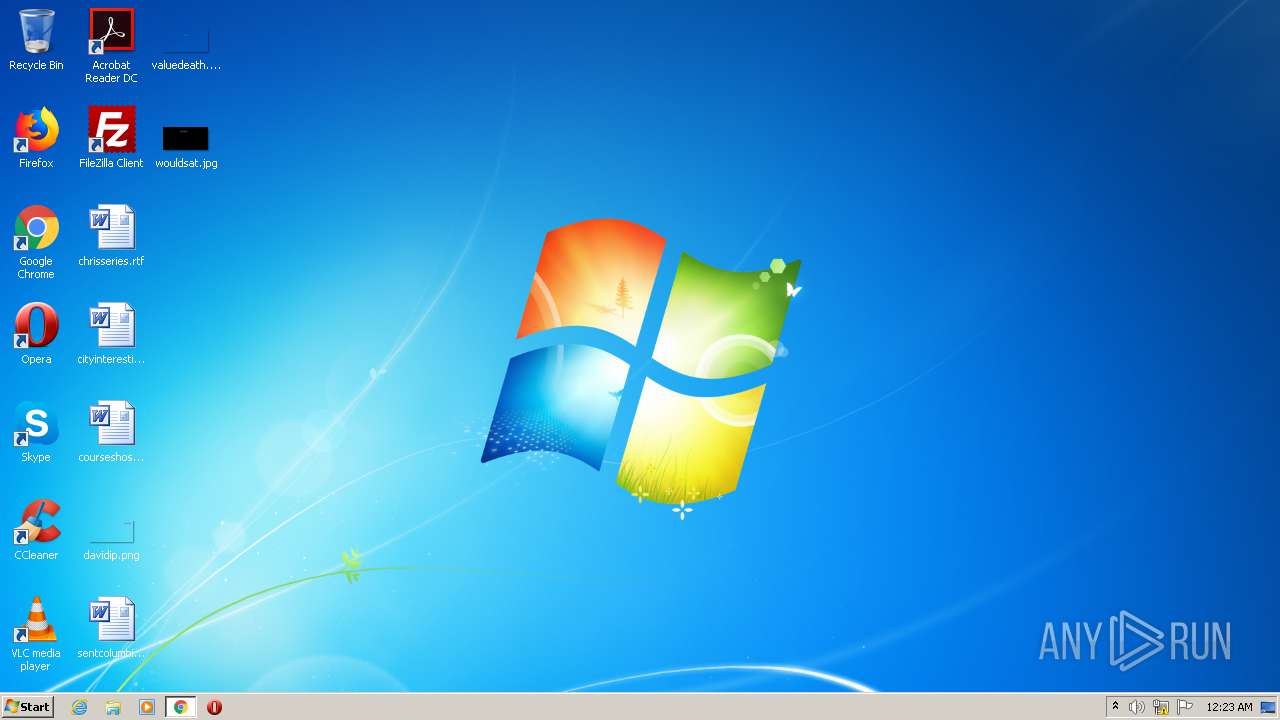
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F0B2769126B4562EFB2556791C46B91C |
| SHA1: | 5F5941B2C289AD06F865C27DF1C0AC927F295BE7 |
| SHA256: | 430F71CCEC7B21BA45A41B89E5F3E366F5C8B3C673DDF93B340C460C8C0C86AF |
| SSDEEP: | 3:N8X/iKuJGuWgKdVFwUndpxSI/t:24wFgKX1n3UCt |
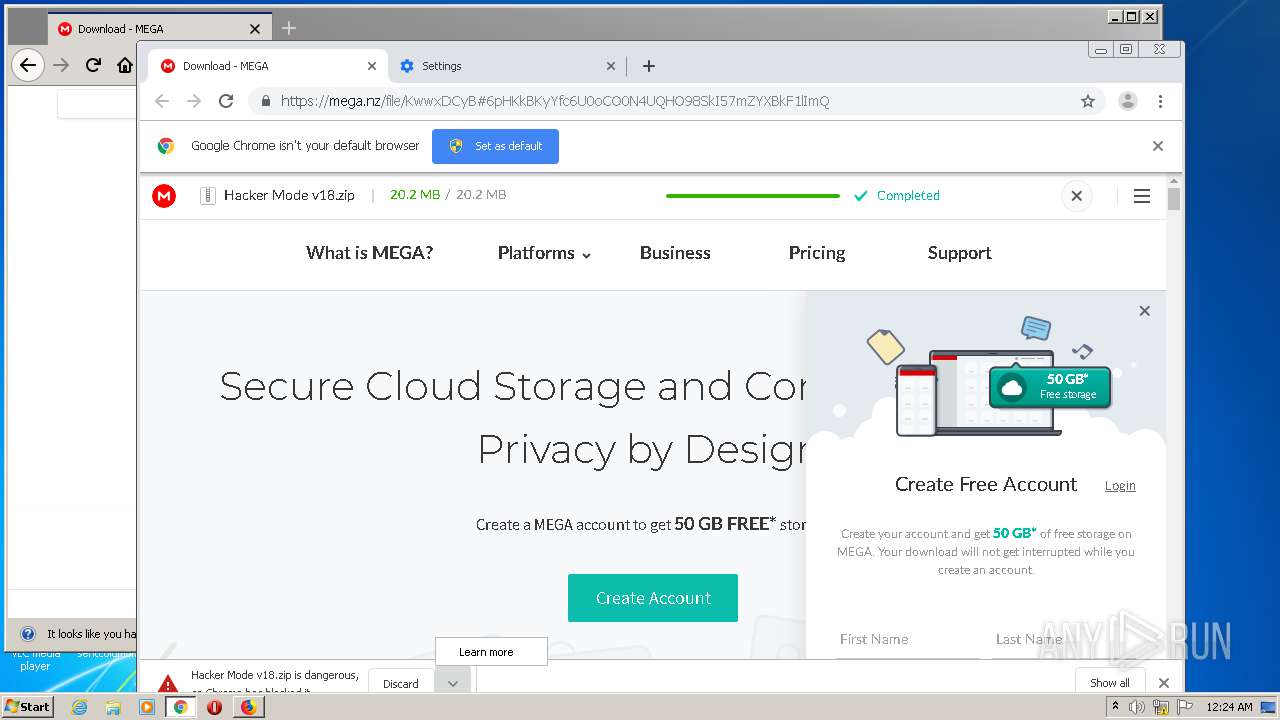
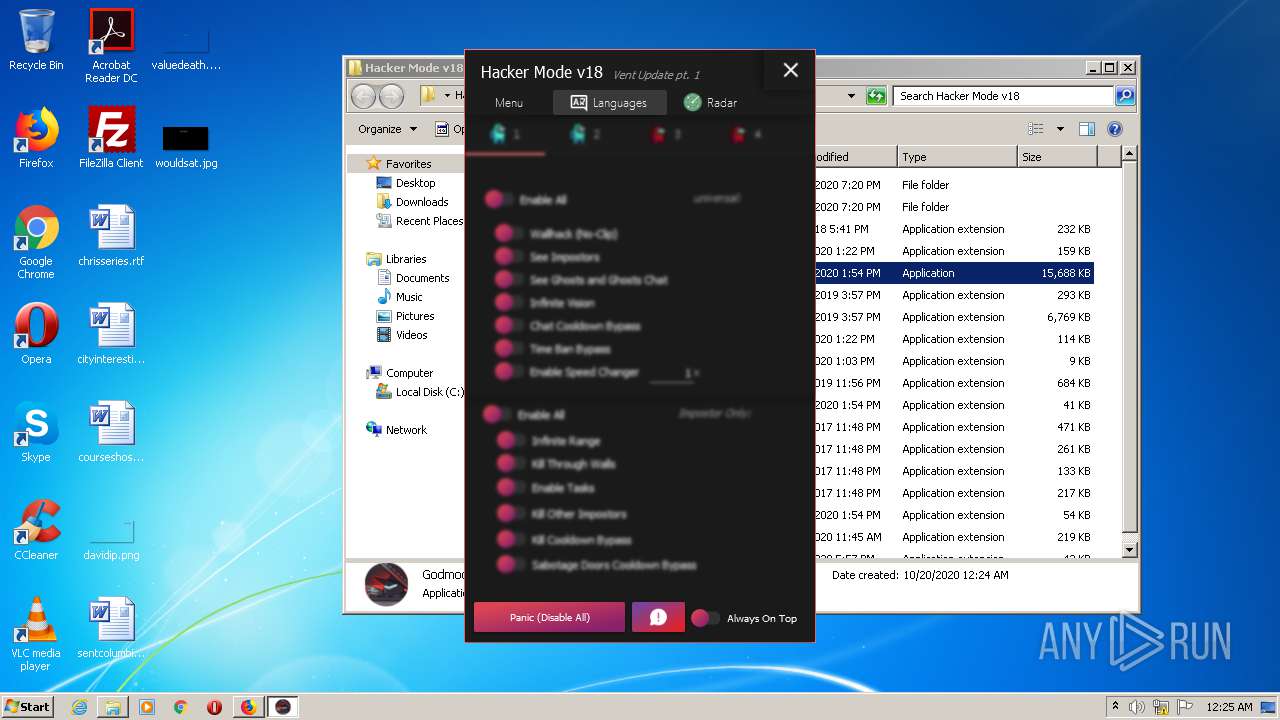
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 4020)
SUSPICIOUS
Reads Environment values
- Godmode v18 Among Us 9.22s.exe (PID: 1940)
Executed via COM
- MsSpellCheckingFacility.exe (PID: 3744)
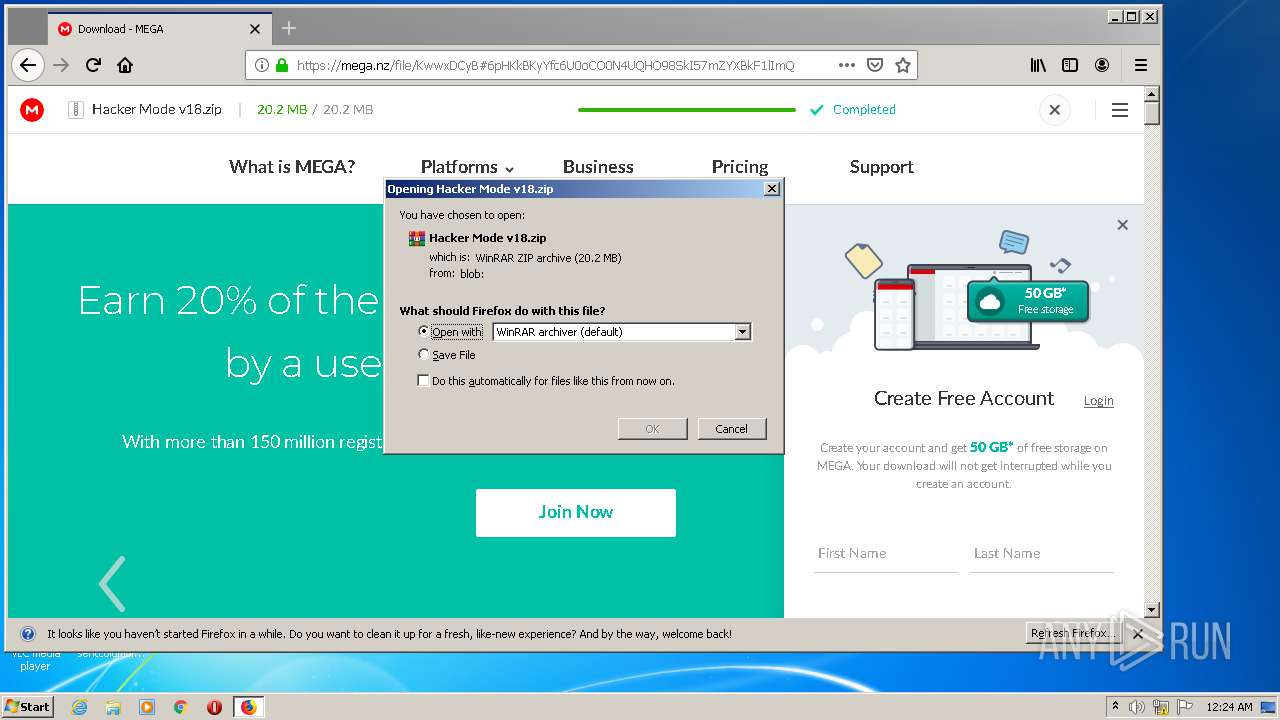
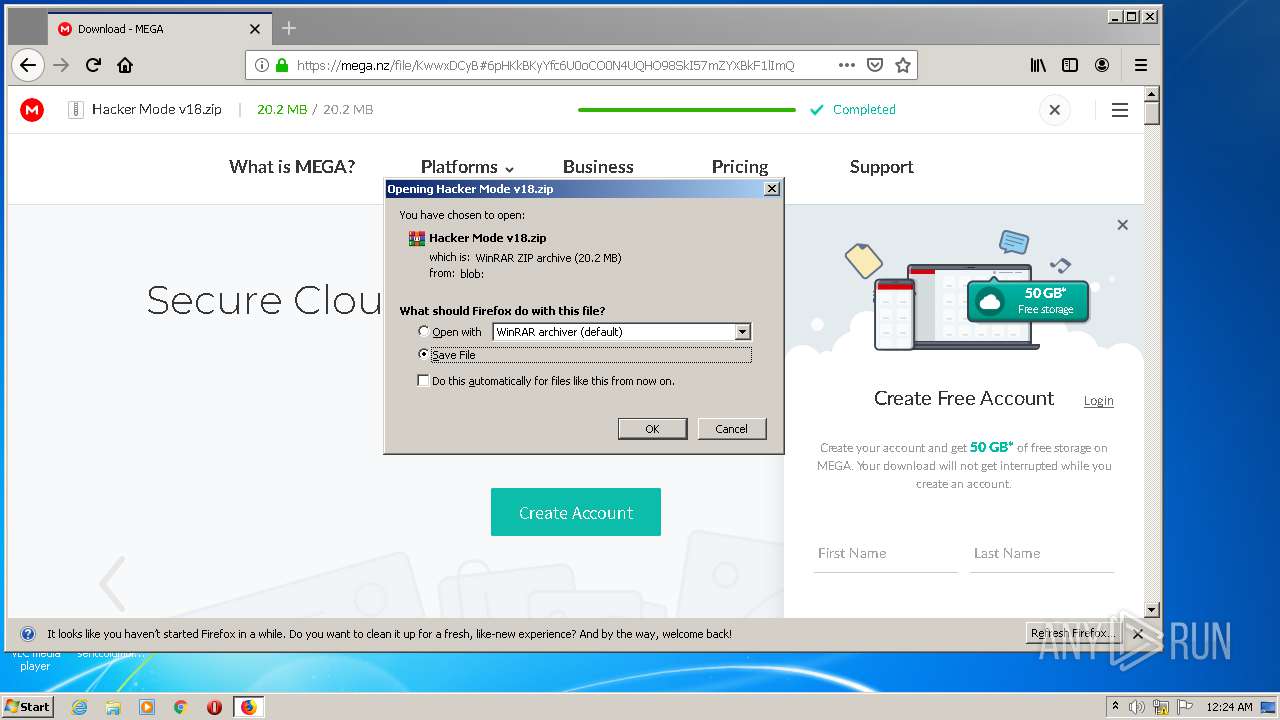
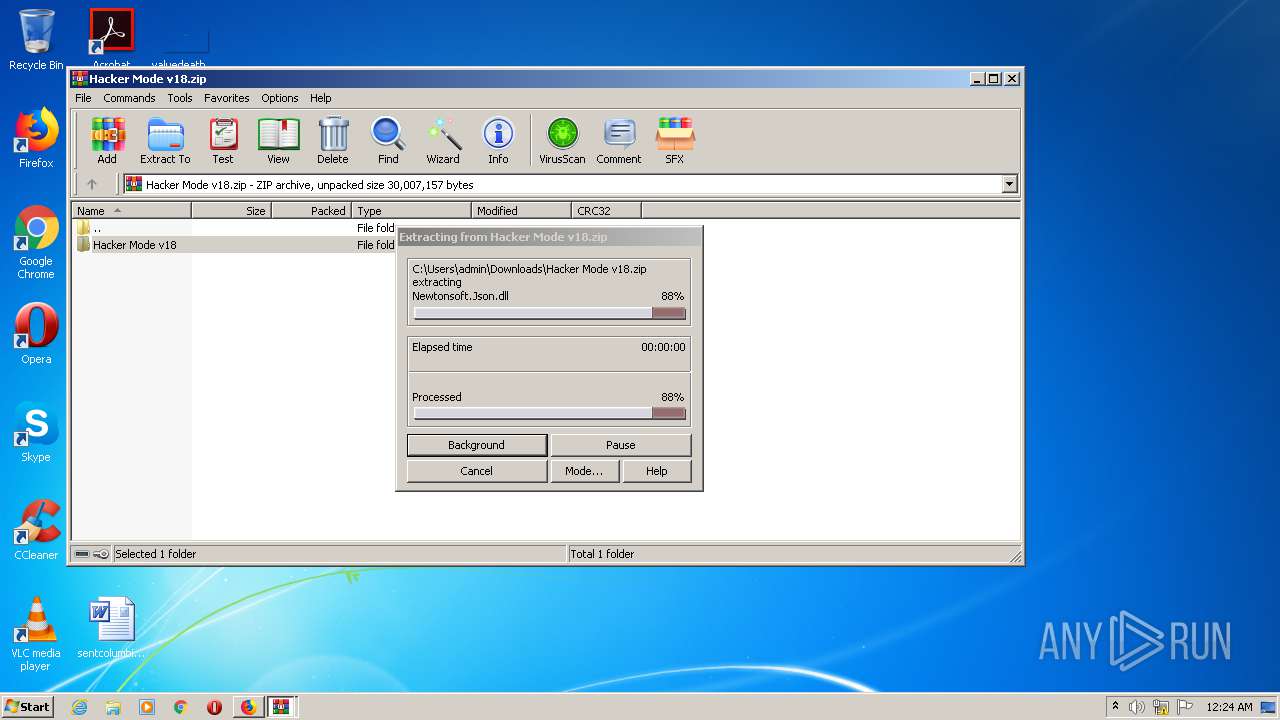
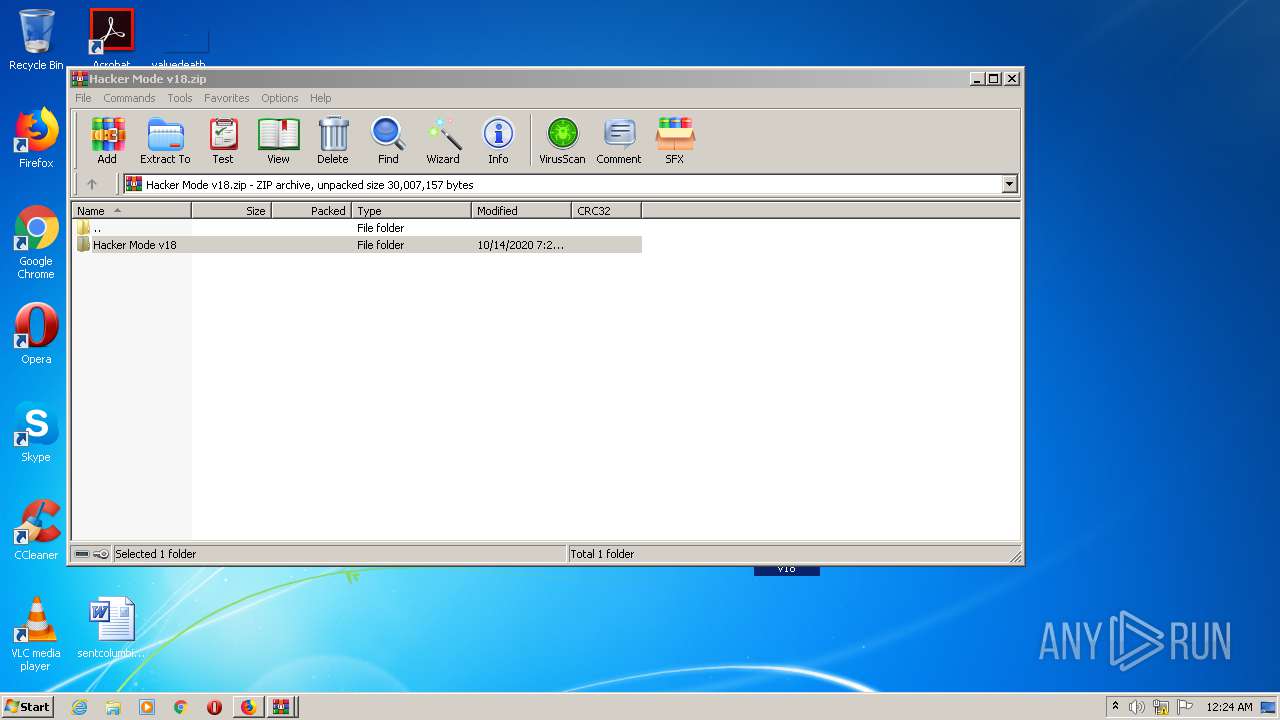
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2872)
INFO
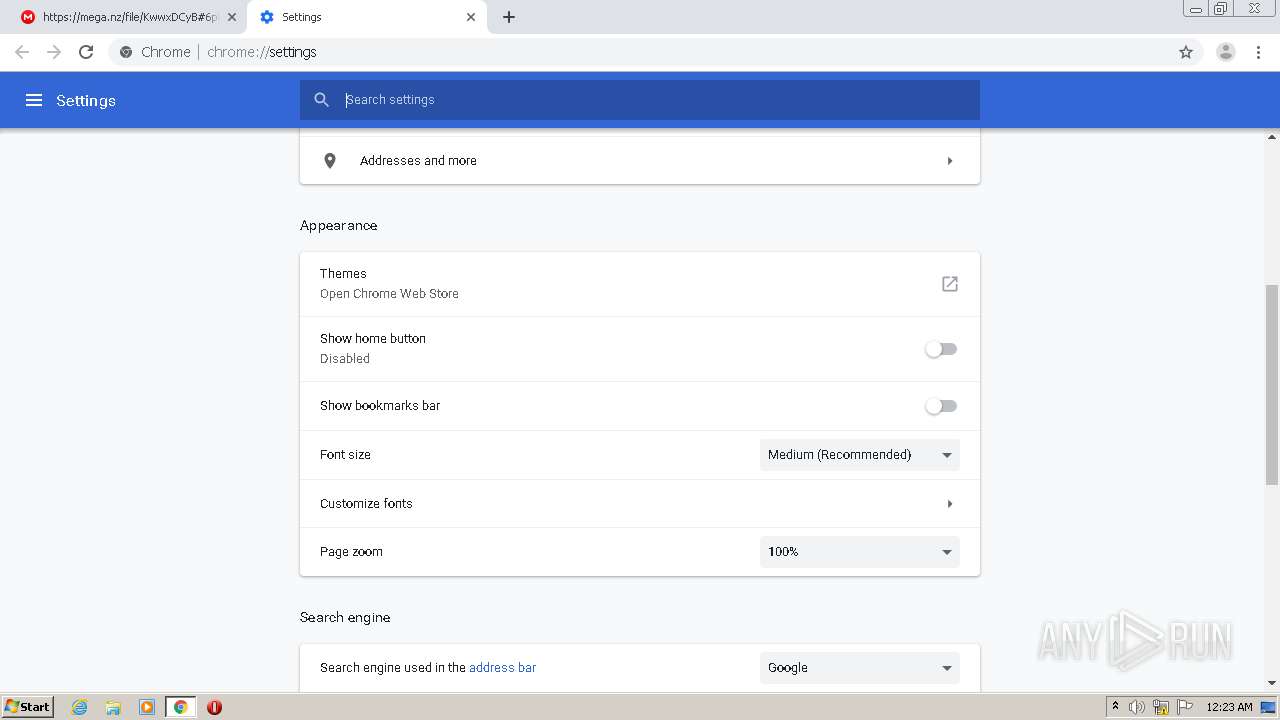
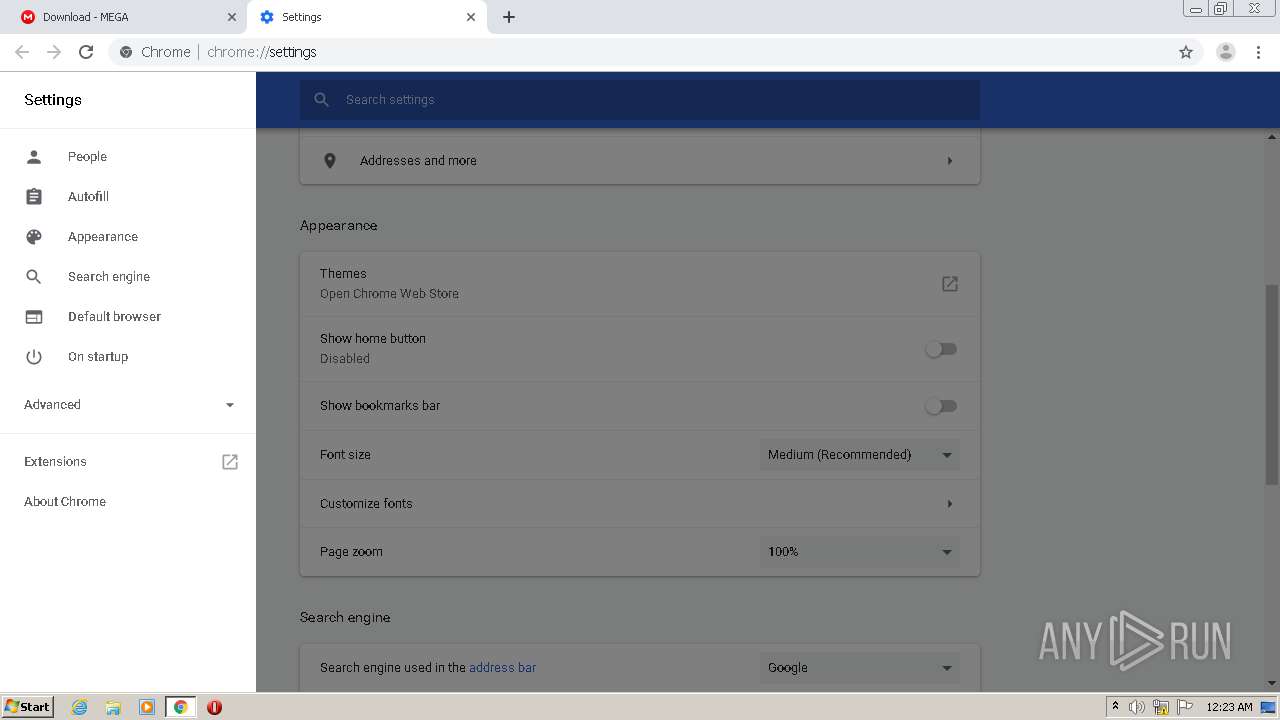
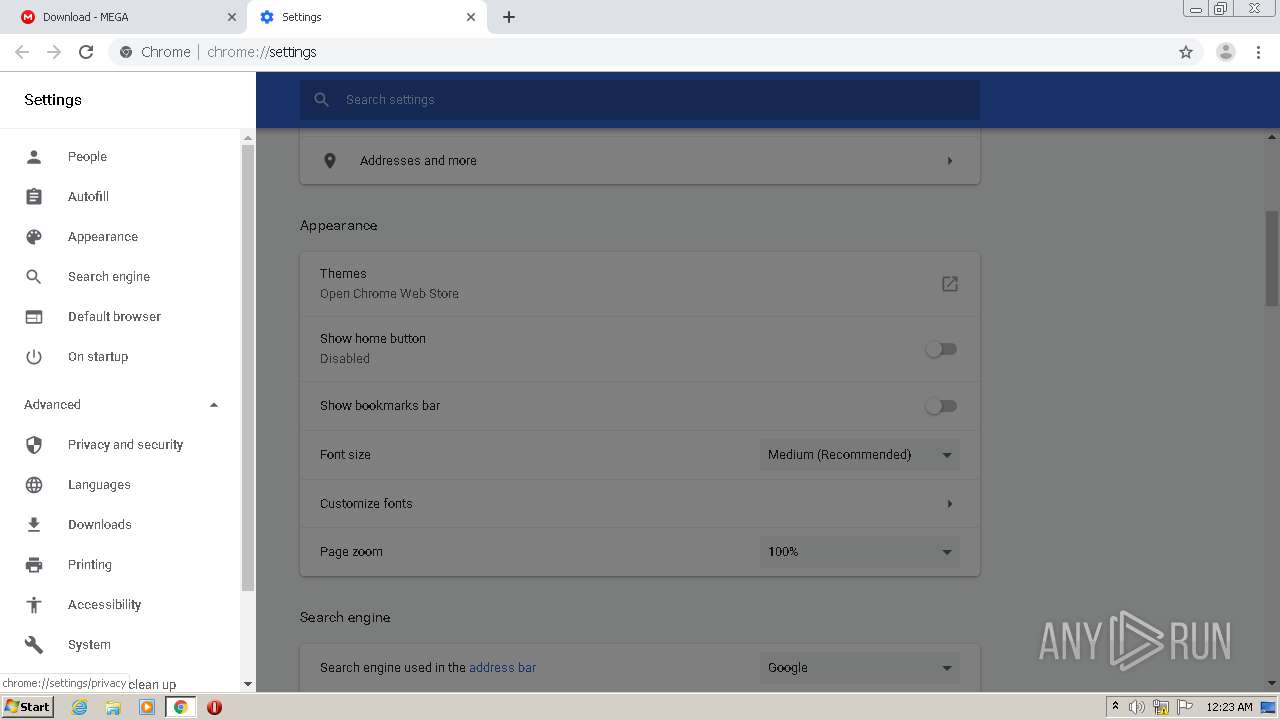
Reads the hosts file
- chrome.exe (PID: 3392)
- chrome.exe (PID: 3808)
Creates files in the user directory
- firefox.exe (PID: 4004)
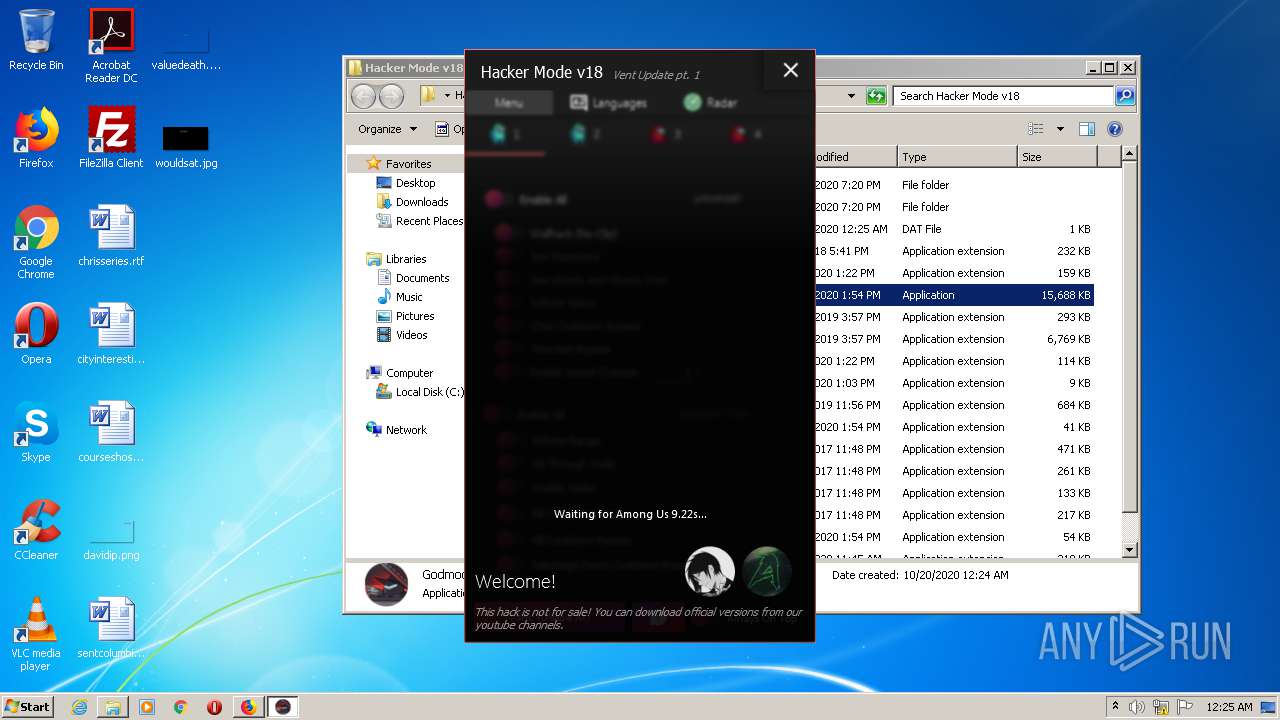
Manual execution by user
- Godmode v18 Among Us 9.22s.exe (PID: 1940)
- firefox.exe (PID: 924)
Application launched itself
- chrome.exe (PID: 3392)
- firefox.exe (PID: 924)
- firefox.exe (PID: 4004)
Reads Internet Cache Settings
- firefox.exe (PID: 4004)
Reads settings of System Certificates
- Godmode v18 Among Us 9.22s.exe (PID: 1940)
Creates files in the program directory
- firefox.exe (PID: 4004)
Reads CPU info
- firefox.exe (PID: 4004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
31
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,14031612125974912197,16472090217208693144,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11760828451518190767 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3864 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4004.20.1964471277\8554094" -childID 3 -isForBrowser -prefsHandle 3728 -prefMapHandle 3744 -prefsLen 6785 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 4004 "\\.\pipe\gecko-crash-server-pipe.4004" 3760 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
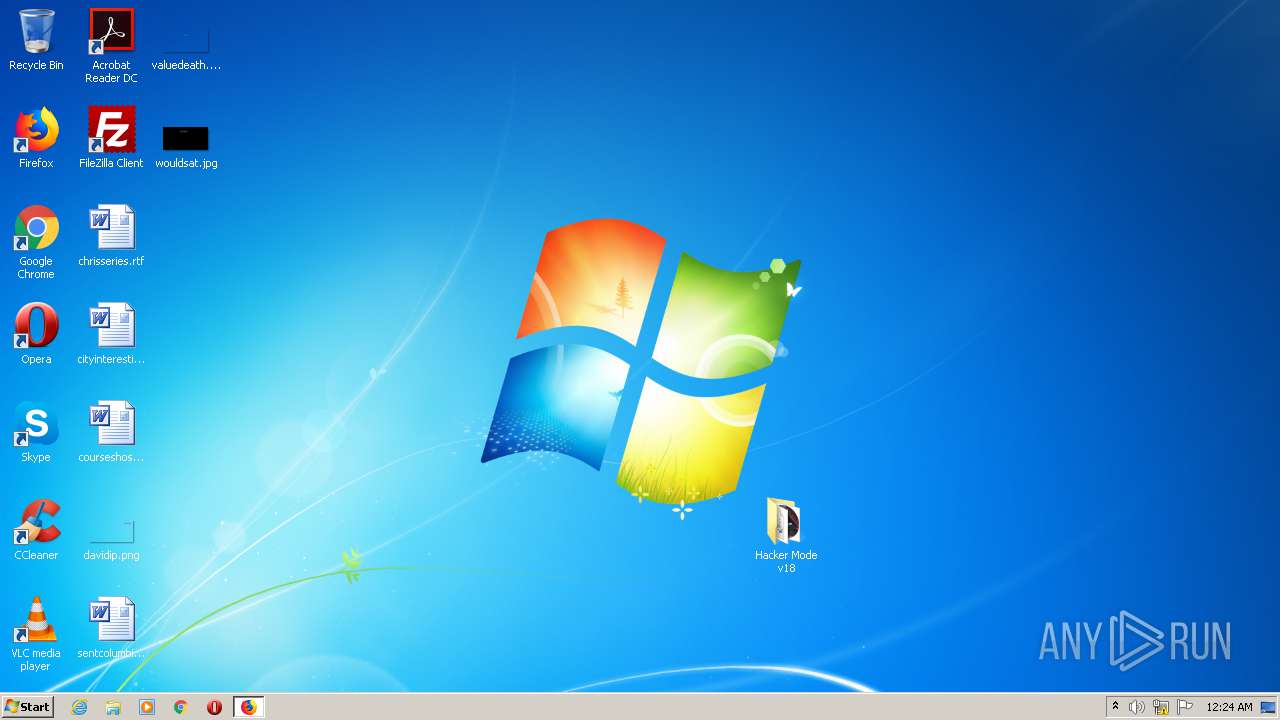
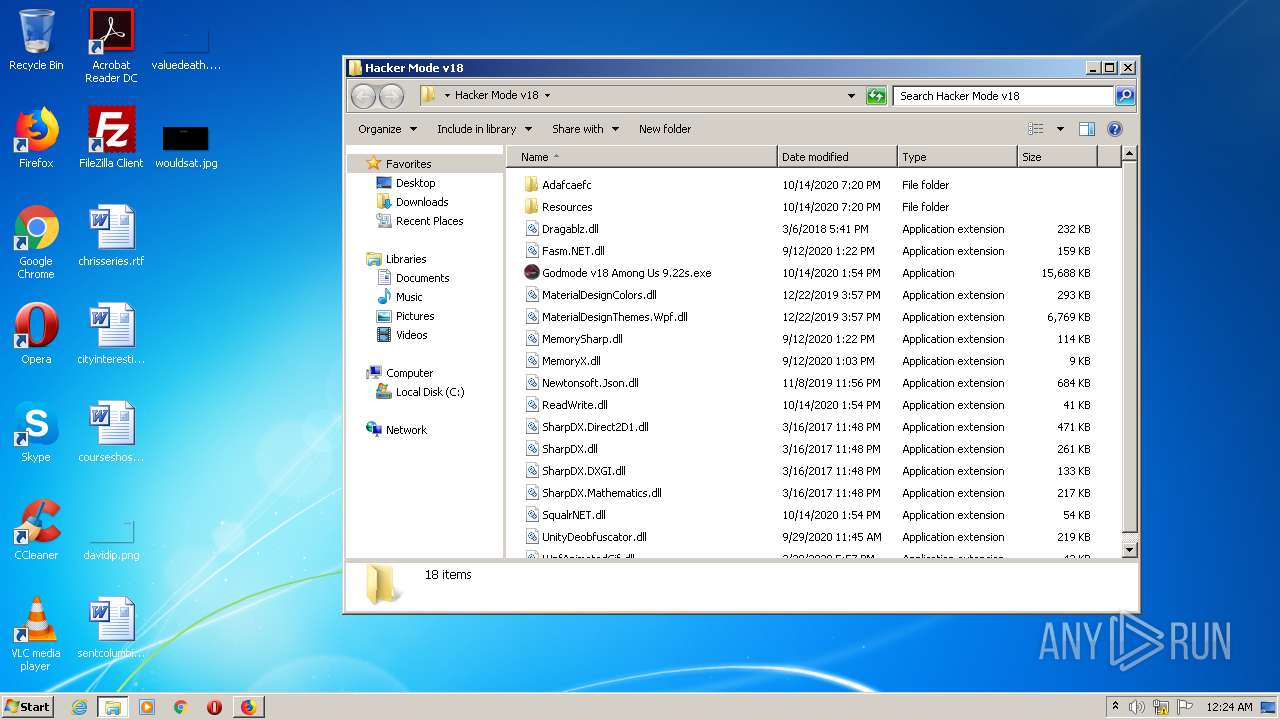
| 1940 | "C:\Users\admin\Desktop\Hacker Mode v18\Godmode v18 Among Us 9.22s.exe" | C:\Users\admin\Desktop\Hacker Mode v18\Godmode v18 Among Us 9.22s.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Hacker Mode (Among Us) Exit code: 0 Version: 1.0.9.0 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,14031612125974912197,16472090217208693144,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16657272107071730245 --mojo-platform-channel-handle=3840 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,14031612125974912197,16472090217208693144,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12877197655585149529 --mojo-platform-channel-handle=2236 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,14031612125974912197,16472090217208693144,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9147706750475975543 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4004.3.606149338\1319113944" -childID 1 -isForBrowser -prefsHandle 788 -prefMapHandle 792 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 4004 "\\.\pipe\gecko-crash-server-pipe.4004" 1776 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
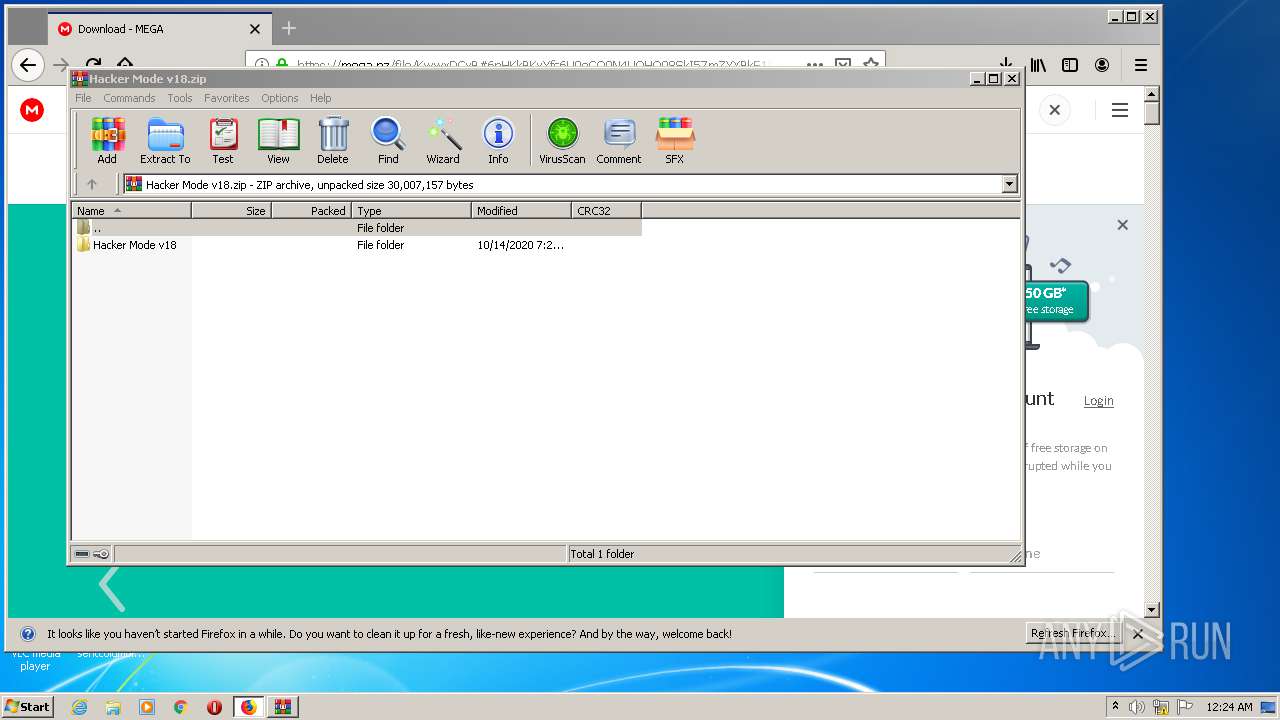
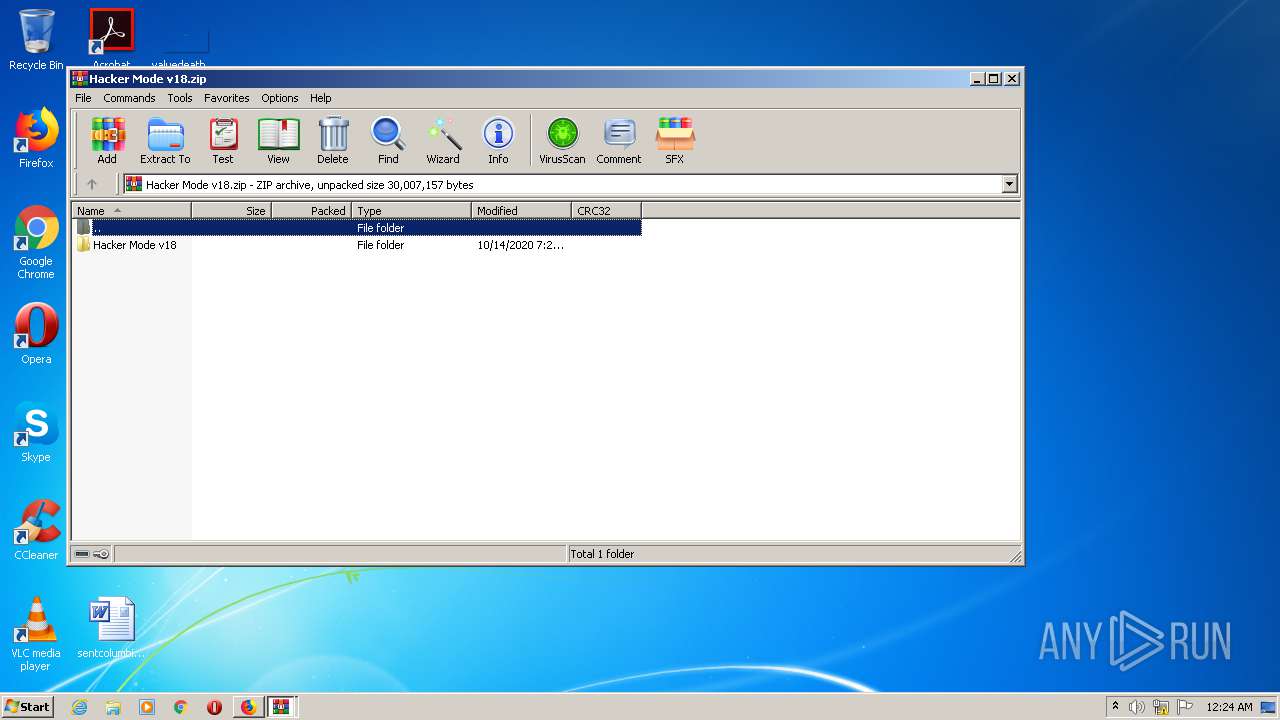
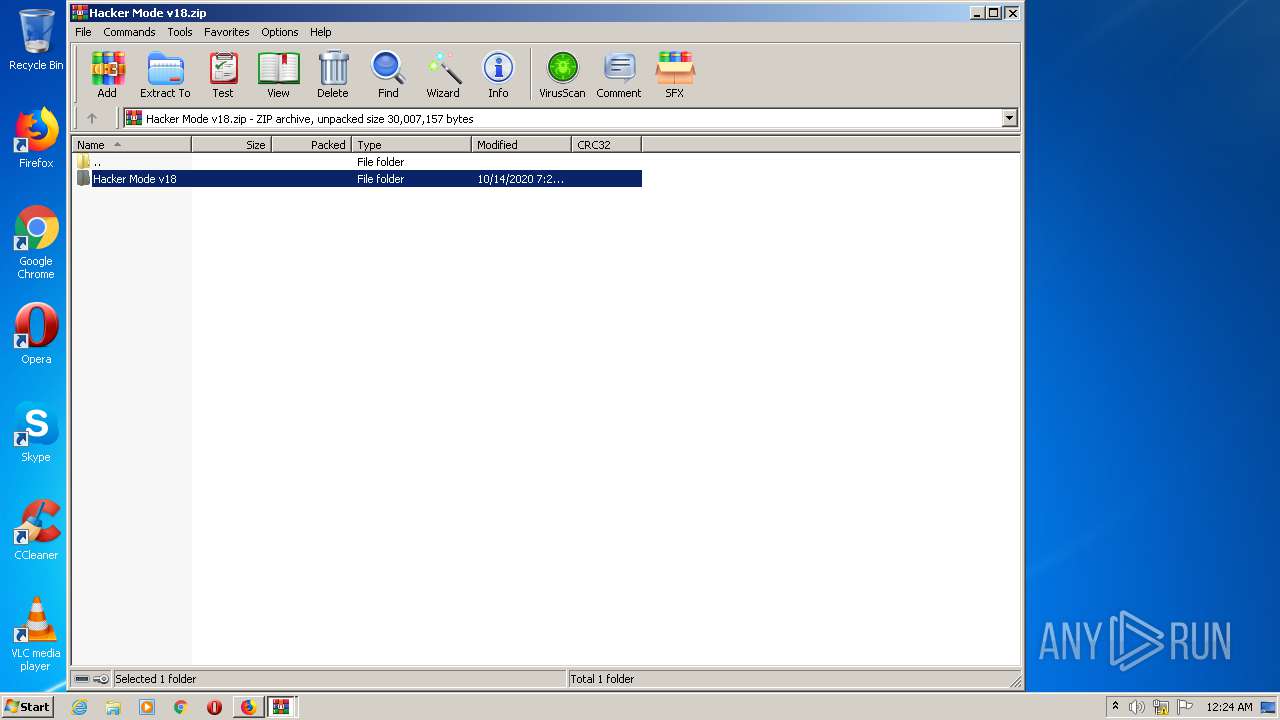
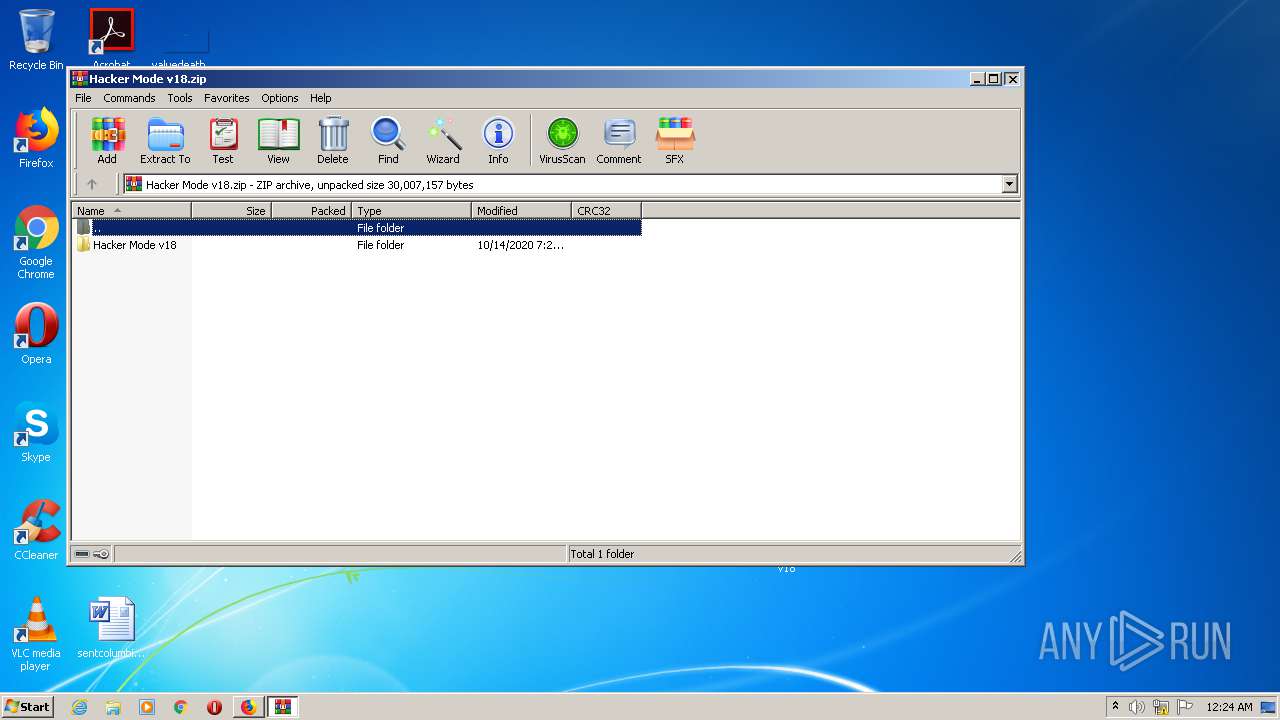
| 2872 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Hacker Mode v18.zip" | C:\Program Files\WinRAR\WinRAR.exe | firefox.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
3 082
Read events
2 929
Write events
149
Delete events
4
Modification events
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3392-13247623385961250 |
Value: 259 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
15
Suspicious files
164
Text files
203
Unknown types
95
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E1FDA-D40.pma | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9d58ba61-52f0-45d0-84d1-b8c3c006b5d2.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF2d41ff.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d4124.TMP | text | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d4144.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
76
DNS requests
139
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4004 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/ | US | der | 472 b | whitelisted |
4004 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/ | US | der | 472 b | whitelisted |
4004 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4004 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/ | US | der | 471 b | whitelisted |
4004 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/ | US | der | 471 b | whitelisted |
4004 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
4004 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/ | US | der | 471 b | whitelisted |
4004 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4004 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/ | US | der | 472 b | whitelisted |
4004 | firefox.exe | POST | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/ | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3808 | chrome.exe | 89.44.169.135:443 | mega.nz | Datacenter Luxembourg S.A. | LU | suspicious |
3808 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3808 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3808 | chrome.exe | 216.58.206.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
3808 | chrome.exe | 172.217.18.170:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3808 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3808 | chrome.exe | 216.58.207.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3808 | chrome.exe | 89.44.169.134:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | suspicious |
3808 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3808 | chrome.exe | 89.44.168.78:443 | gfs270n368.userstorage.mega.co.nz | Datacenter Luxembourg S.A. | LU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mega.nz |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
translate.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |