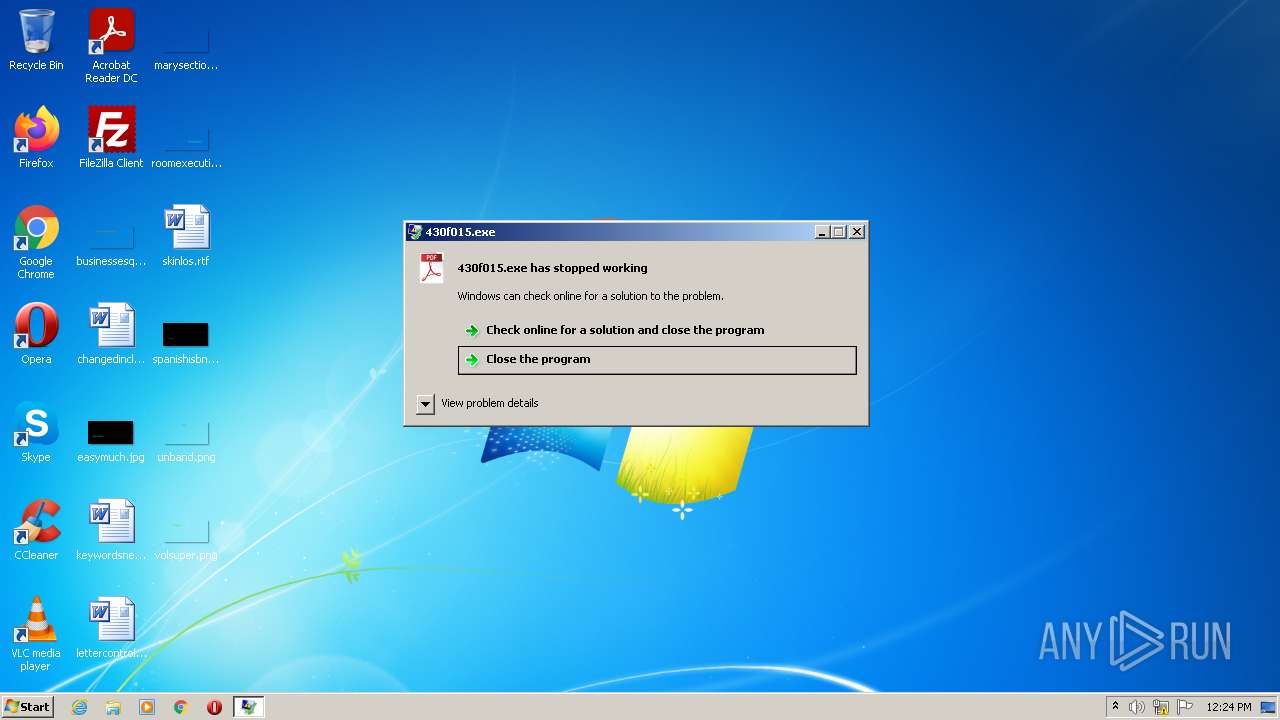
| File name: | 430f015.exe |
| Full analysis: | https://app.any.run/tasks/45e358f0-4807-466b-906c-62063d529048 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 11:23:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 74A53D9DB6B2358D3E5FE3ACCF0CB738 |
| SHA1: | CFB548D9F55AEEE9EFAB29969BFDBFD6CF2F6494 |
| SHA256: | 430F015E62C1A1063E98EE14980649957FFC1D481D6DC0F51A68E6E6A9E25820 |
| SSDEEP: | 24576:CI88WzEMohhJjvT+QPSBx5fCi6yX6N/9XSiOMEYAV20FZMTDH8W:CI8LoMuaQPSBxpF6yX6N/dS1MEYAjZmt |
MALICIOUS
Drops executable file immediately after starts
- 430f015.exe (PID: 2764)
- 430f015.exe (PID: 2672)
- 430f015.exe (PID: 2520)
Loads dropped or rewritten executable
- 430f015.exe (PID: 2764)
- 430f015.exe (PID: 2672)
Changes the autorun value in the registry
- 430f015.exe (PID: 2520)
Deletes shadow copies
- cmd.exe (PID: 3428)
SUSPICIOUS
Reads the computer name
- 430f015.exe (PID: 2764)
- 430f015.exe (PID: 4092)
- 430f015.exe (PID: 2672)
- 430f015.exe (PID: 2520)
Executable content was dropped or overwritten
- 430f015.exe (PID: 2764)
- 430f015.exe (PID: 2672)
Checks supported languages
- 430f015.exe (PID: 2764)
- 430f015.exe (PID: 4092)
- 430f015.exe (PID: 2672)
- cmd.exe (PID: 3428)
- 430f015.exe (PID: 2520)
Drops a file with a compile date too recent
- 430f015.exe (PID: 2764)
- 430f015.exe (PID: 2672)
- 430f015.exe (PID: 2520)
Application launched itself
- 430f015.exe (PID: 2764)
- 430f015.exe (PID: 2672)
Executed via COM
- DllHost.exe (PID: 1624)
- DllHost.exe (PID: 2324)
Creates files in the Windows directory
- 430f015.exe (PID: 2520)
Starts CMD.EXE for commands execution
- 430f015.exe (PID: 2520)
Executed as Windows Service
- vssvc.exe (PID: 4072)
Creates files in the program directory
- 430f015.exe (PID: 2520)
INFO
Checks supported languages
- DllHost.exe (PID: 1624)
- DllHost.exe (PID: 2324)
- vssadmin.exe (PID: 3616)
- vssvc.exe (PID: 4072)
Reads the computer name
- DllHost.exe (PID: 1624)
- DllHost.exe (PID: 2324)
- vssadmin.exe (PID: 3616)
- vssvc.exe (PID: 4072)
Dropped object may contain TOR URL's
- 430f015.exe (PID: 2520)
Dropped object may contain Bitcoin addresses
- 430f015.exe (PID: 2520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x3348 |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 572928 |
| CodeSize: | 26112 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2020:08:01 04:44:50+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2020 02:44:50 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2020 02:44:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006457 | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43499 |
.rdata | 0x00008000 | 0x00001380 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.261 |
.data | 0x0000A000 | 0x00025538 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.13373 |
.ndata | 0x00030000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003A000 | 0x00064C74 | 0x00064E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.19333 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30219 | 832 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.59263 | 2440 | UNKNOWN | English - United States | RT_ICON |
3 | 4.51327 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.37771 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.30359 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 4.25205 | 38056 | UNKNOWN | English - United States | RT_ICON |
7 | 4.18998 | 67624 | UNKNOWN | English - United States | RT_ICON |
8 | 4.10815 | 270376 | UNKNOWN | English - United States | RT_ICON |
103 | 2.94794 | 118 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
53
Monitored processes
11
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1624 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2324 | C:\Windows\system32\DllHost.exe /Processid:{D2E7041B-2927-42FB-8E9F-7CE93B6DC937} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2356 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
| 2520 | "C:\Users\admin\AppData\Local\Temp\430f015.exe" | C:\Users\admin\AppData\Local\Temp\430f015.exe | 430f015.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2672 | "C:\Users\admin\AppData\Local\Temp\430f015.exe" | C:\Users\admin\AppData\Local\Temp\430f015.exe | DllHost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Local\Temp\430f015.exe" | C:\Users\admin\AppData\Local\Temp\430f015.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3060 | wmic shadowcopy delete | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 3428 | "C:\Windows\System32\cmd.exe" /c vssadmin delete shadows /all /quiet & wmic shadowcopy delete & bcdedit /set {default} bootstatuspolicy ignoreallfailures & bcdedit /set {default} recoveryenabled no | C:\Windows\System32\cmd.exe | — | 430f015.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3616 | vssadmin delete shadows /all /quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4072 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 497
Read events
2 475
Write events
22
Delete events
0
Modification events
| (PID) Process: | (1624) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ICM\Calibration |
| Operation: | write | Name: | DisplayCalibrator |
Value: C:\Users\admin\AppData\Local\Temp\430f015.exe | |||
| (PID) Process: | (2324) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2324) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2324) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2324) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2520) 430f015.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | {34432044-3F3F-02AE-334E-332A4479FE28} |
Value: "C:\Users\admin\AppData\Local\Temp\430f015.exe" | |||
| (PID) Process: | (2520) 430f015.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.lockbit\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\windows\system32\0A4324.ico | |||
| (PID) Process: | (2520) 430f015.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 101 | |||
| (PID) Process: | (2520) 430f015.exe | Key: | HKEY_CURRENT_USER\Software\0A4324443FA44E |
| Operation: | write | Name: | Private |
Value: 0AE97897BDBE8A36E612D11304D2F4FFF54136DBB8E30AA58262459A28C5A03914505064C152CBAB11140DE341BD8EE3D01F97943806C09213F1C042E3EFA28B3176B68572D0CC71334F78D4AF96C3508B805C2836B8AB84F33120ABB9AC8D6B9C853DDEE62822D374A69F171E6A14BE | |||
| (PID) Process: | (2520) 430f015.exe | Key: | HKEY_CURRENT_USER\Software\0A4324443FA44E |
| Operation: | write | Name: | Public |
Value: 3EDF5324839949516CE57C9B06296C9D1A1DA0F5BF8D1FF393BDE43F5BB65843 | |||
Executable files
2
Suspicious files
235
Text files
22
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2764 | 430f015.exe | C:\Users\admin\AppData\Local\Temp\162809383 | — | |
MD5:— | SHA256:— | |||
| 2520 | 430f015.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\actions_r_rhp.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2520 | 430f015.exe | C:\program files\adobe\acrobat reader dc\reader\acroapp\enu\Restore-My-Files.txt | text | |
MD5:— | SHA256:— | |||
| 2520 | 430f015.exe | C:\program files\adobe\acrobat reader dc\reader\1494870c-9912-c184-4cc9-b401-a53f4d8de290.pdf | binary | |
MD5:— | SHA256:— | |||
| 2520 | 430f015.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\accessibility_r_rhp.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2520 | 430f015.exe | C:\program files\adobe\acrobat reader dc\reader\acroapp\enu\accessibility_r_rhp.aapp | binary | |
MD5:— | SHA256:— | |||
| 2520 | 430f015.exe | C:\program files\adobe\acrobat reader dc\reader\Restore-My-Files.txt | text | |
MD5:— | SHA256:— | |||
| 2520 | 430f015.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\1494870c-9912-c184-4cc9-b401-a53f4d8de290.pdf.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2672 | 430f015.exe | C:\Users\admin\AppData\Local\Temp\nslAD3A.tmp\System.dll | executable | |
MD5:FCCFF8CB7A1067E23FD2E2B63971A8E1 | SHA256:6FCEA34C8666B06368379C6C402B5321202C11B00889401C743FB96C516C679E | |||
| 2520 | 430f015.exe | C:\program files\adobe\acrobat reader dc\reader\acroapp\enu\collectsignatures.aapp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report