| File name: | Sample1.zip |
| Full analysis: | https://app.any.run/tasks/f4ed23c1-4b0b-4aba-94ec-b2aba42816d2 |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 13:51:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4EDD939C0314A6C12F3CFC7D012C32E8 |
| SHA1: | ACBD132E1E24611407C5AA28351D83D2175A3B1A |
| SHA256: | 430CAF8E9A4B88919AF7C5E02C29D6DF78CEADB03C6F9324257D705DC71299AA |
| SSDEEP: | 768:MhZh/uh4PP3ir6IVJobyNTTdYhw8TUM3+5Xey7VGXdotU5SLv8M1pDylt6vSM96T:ODP/AbNHd/M3+5XeyRISLvNpmT |
MALICIOUS
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 3000)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2264)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 3000)
Creates files in the user directory
- EQNEDT32.EXE (PID: 3000)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2264)
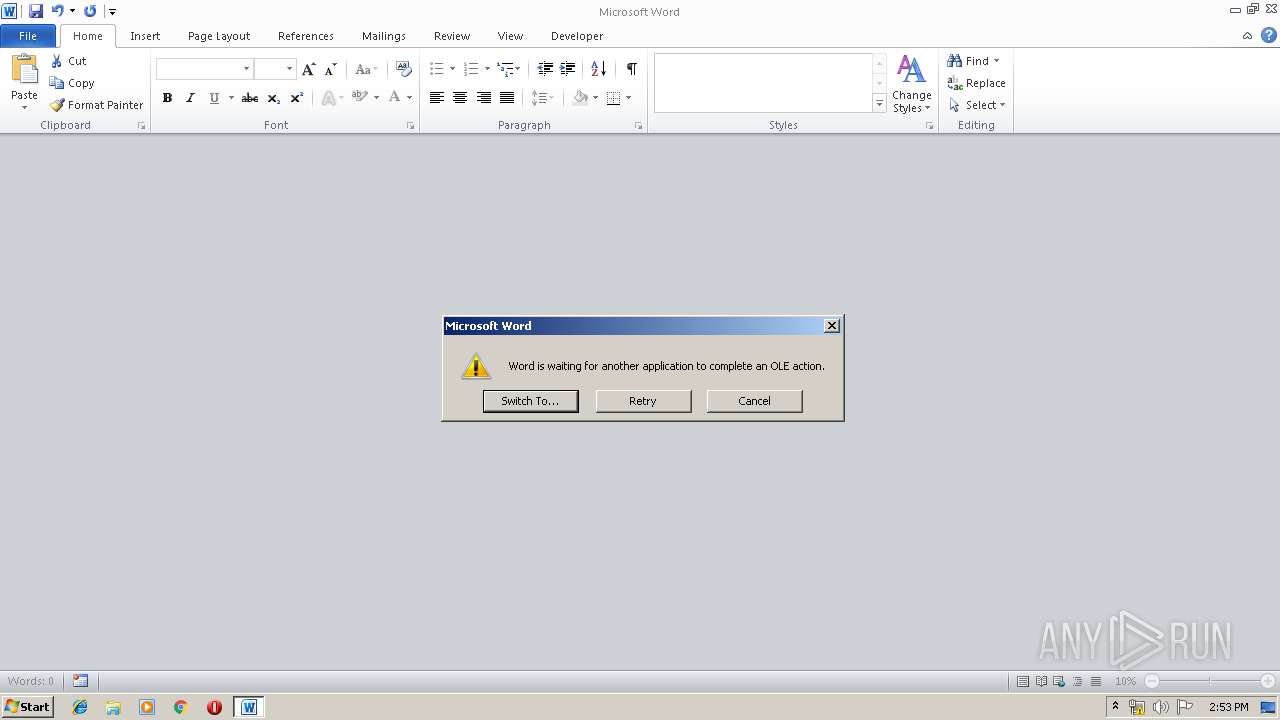
Application was crashed
- EQNEDT32.EXE (PID: 3000)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2264)
Manual execution by user
- WINWORD.EXE (PID: 2264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
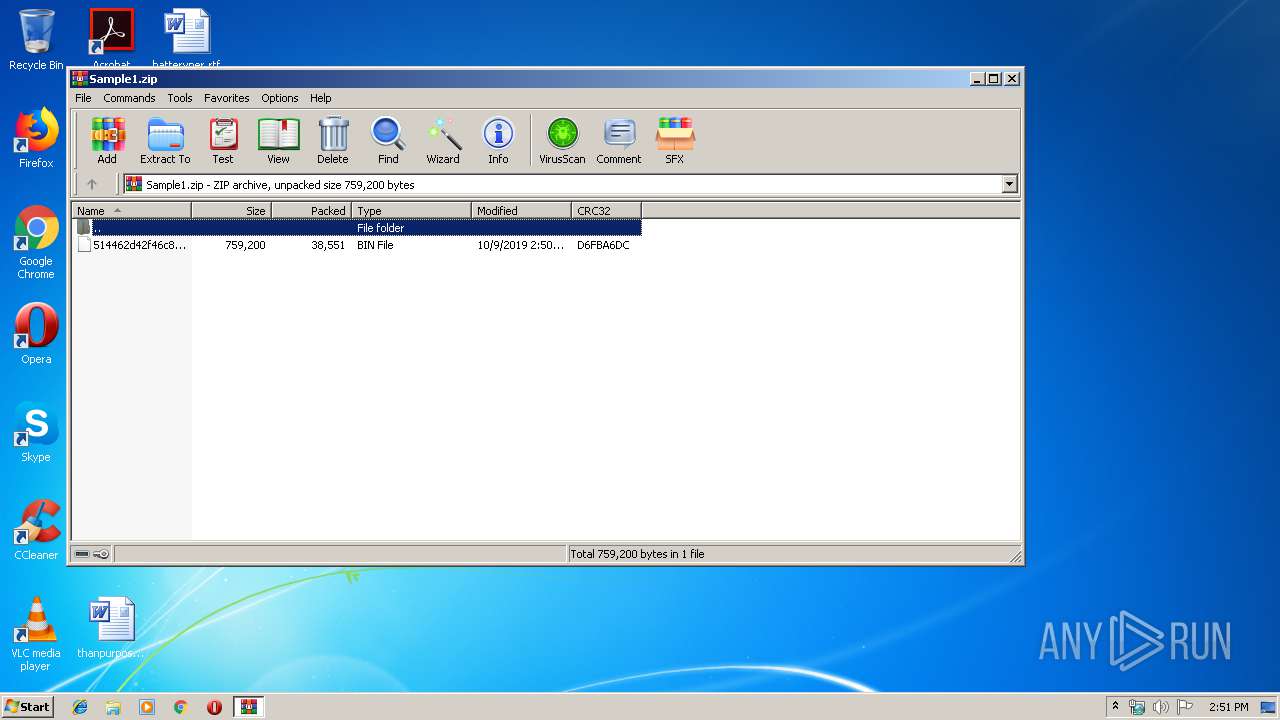
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
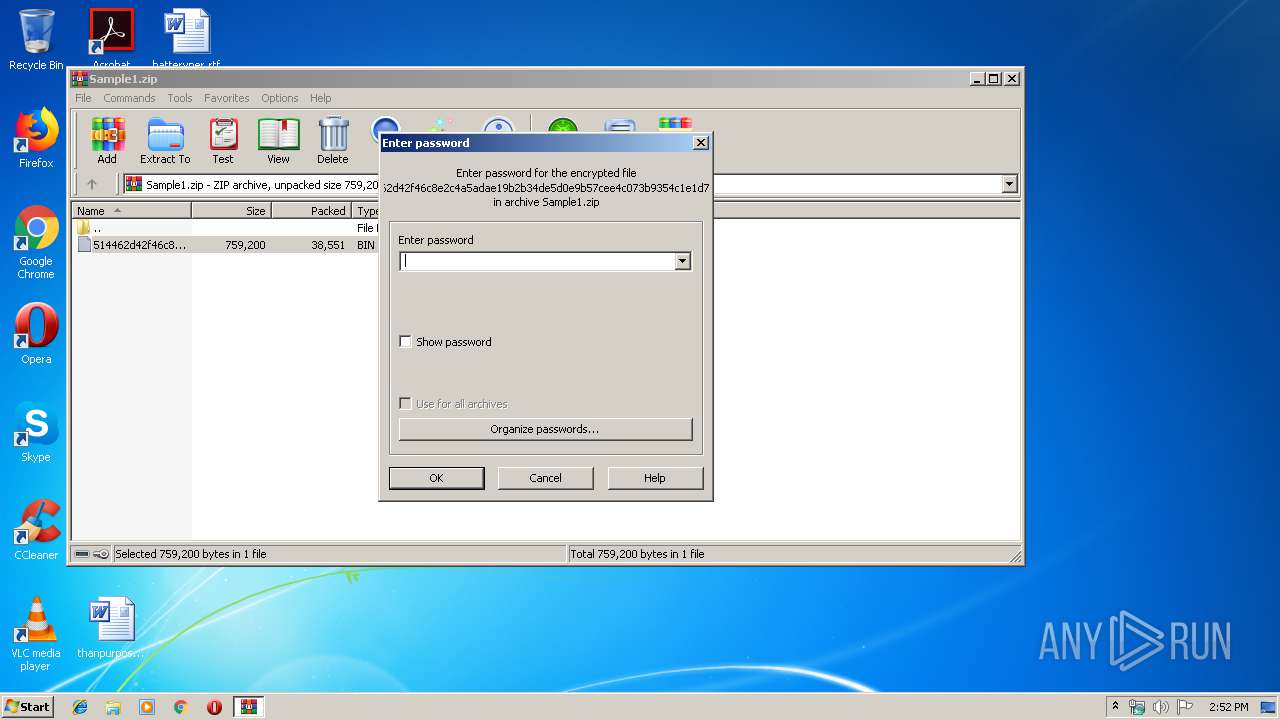
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:09 13:50:24 |
| ZipCRC: | 0xd6fba6dc |
| ZipCompressedSize: | 38551 |
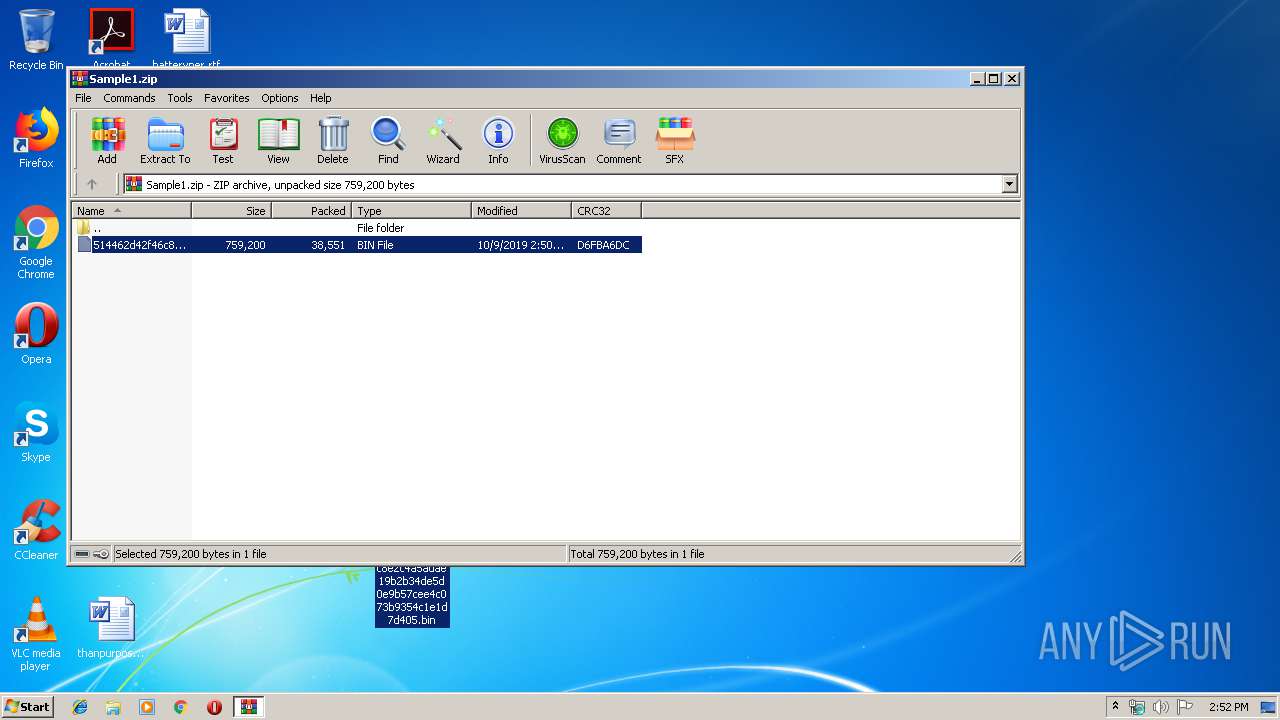
| ZipUncompressedSize: | 759200 |
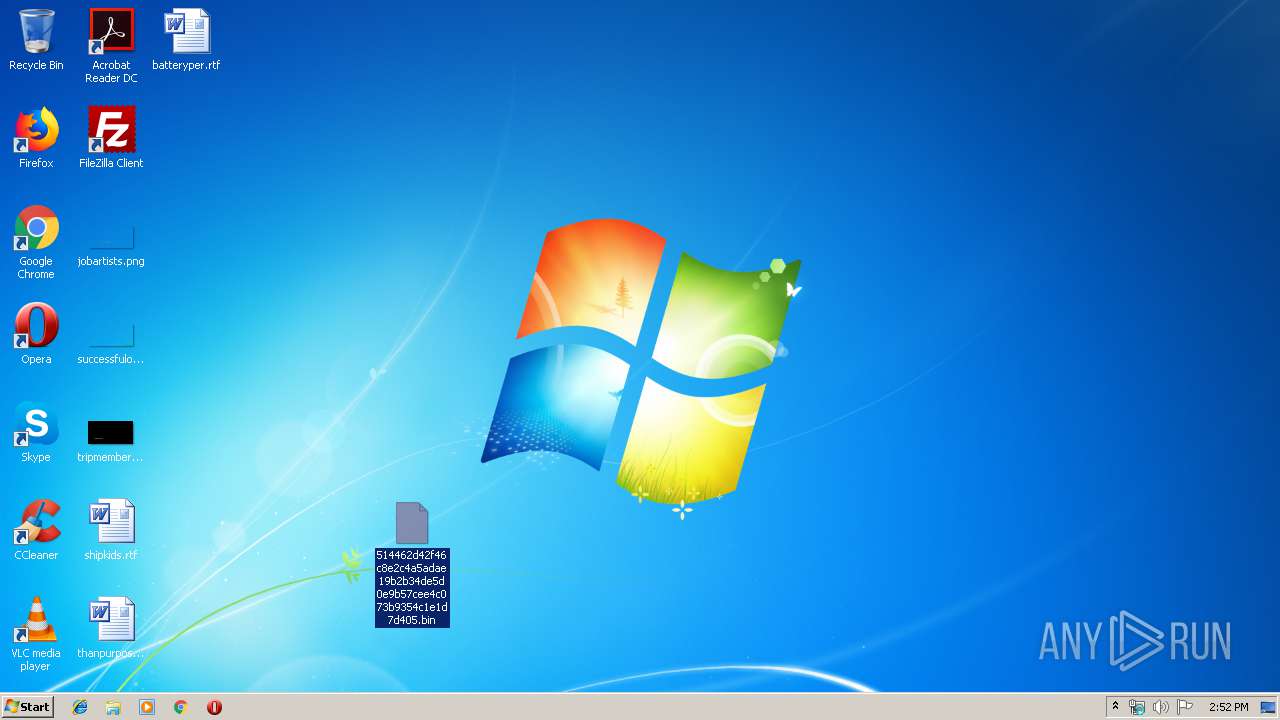
| ZipFileName: | 514462d42f46c8e2c4a5adae19b2b34de5d0e9b57cee4c073b9354c1e1d7d405.bin |
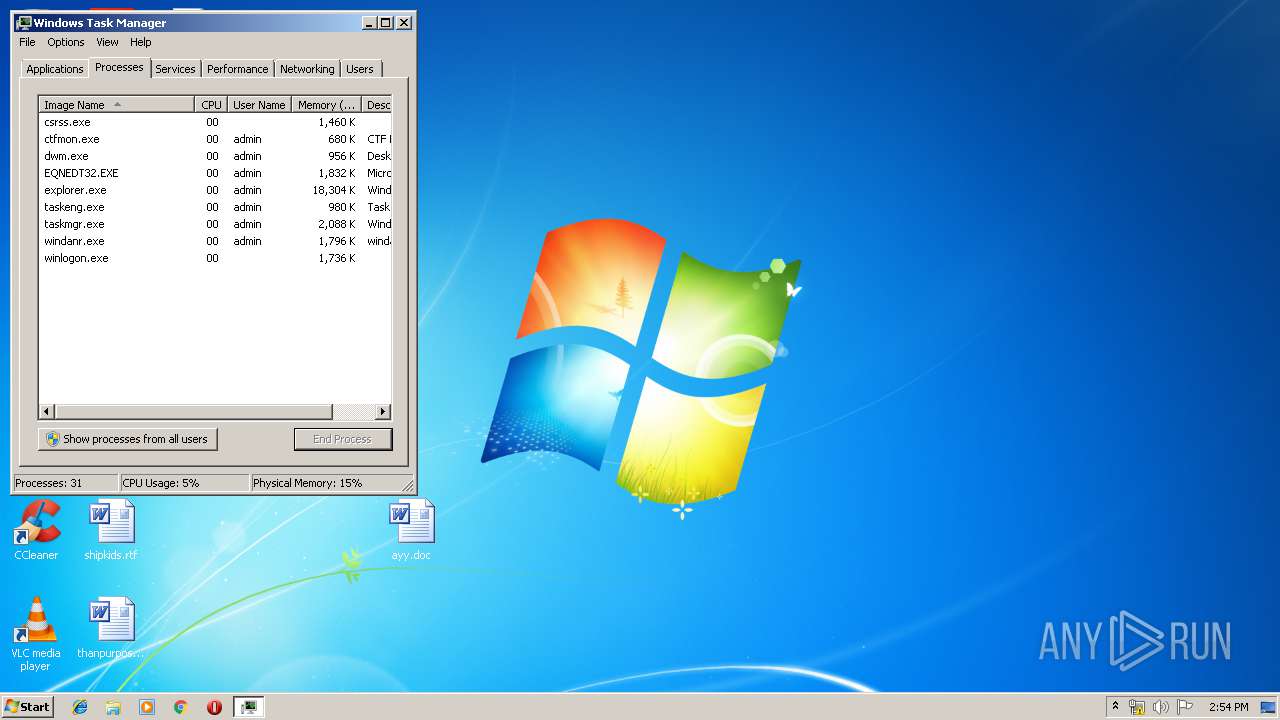
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
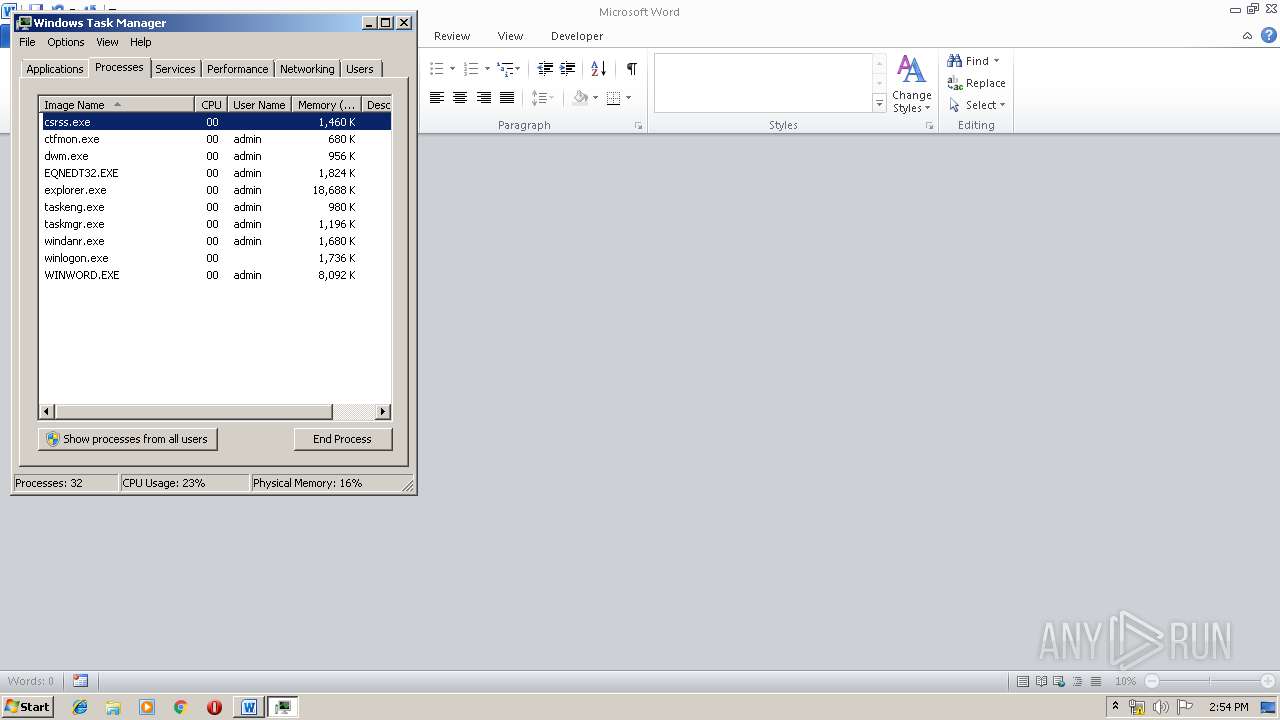
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
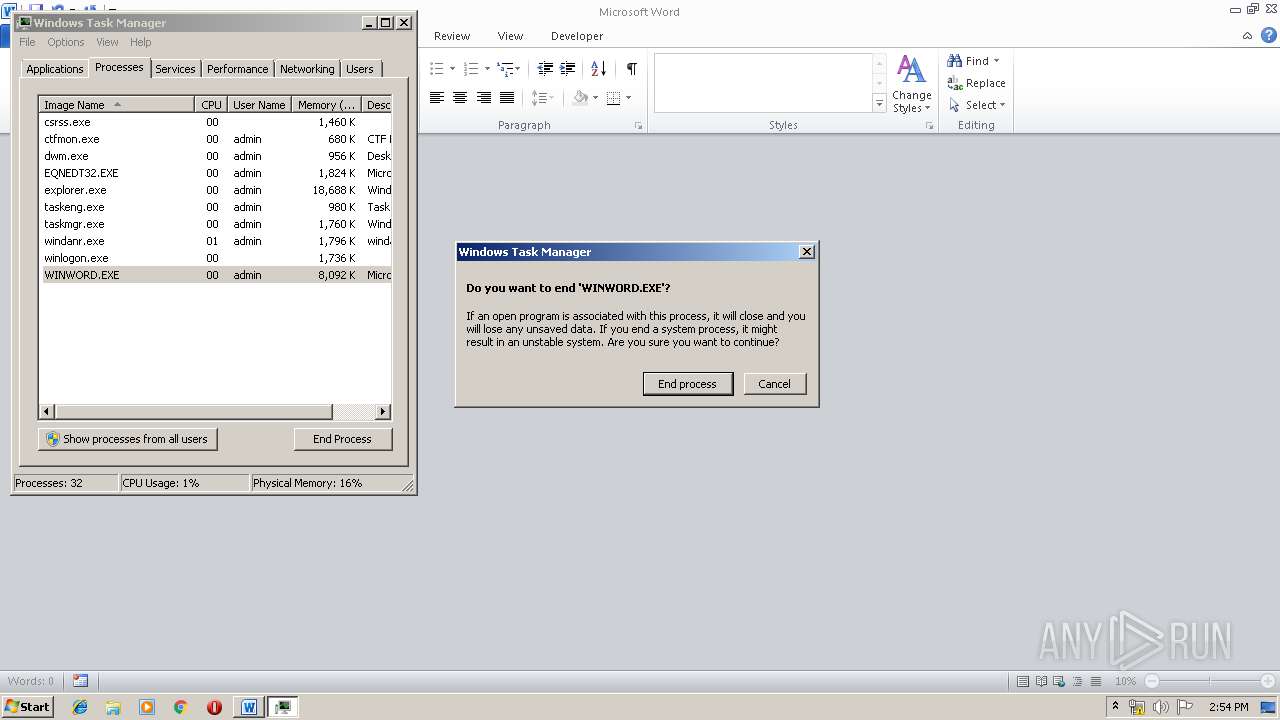
| 2264 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\ayy.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 1 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2824 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Sample1.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
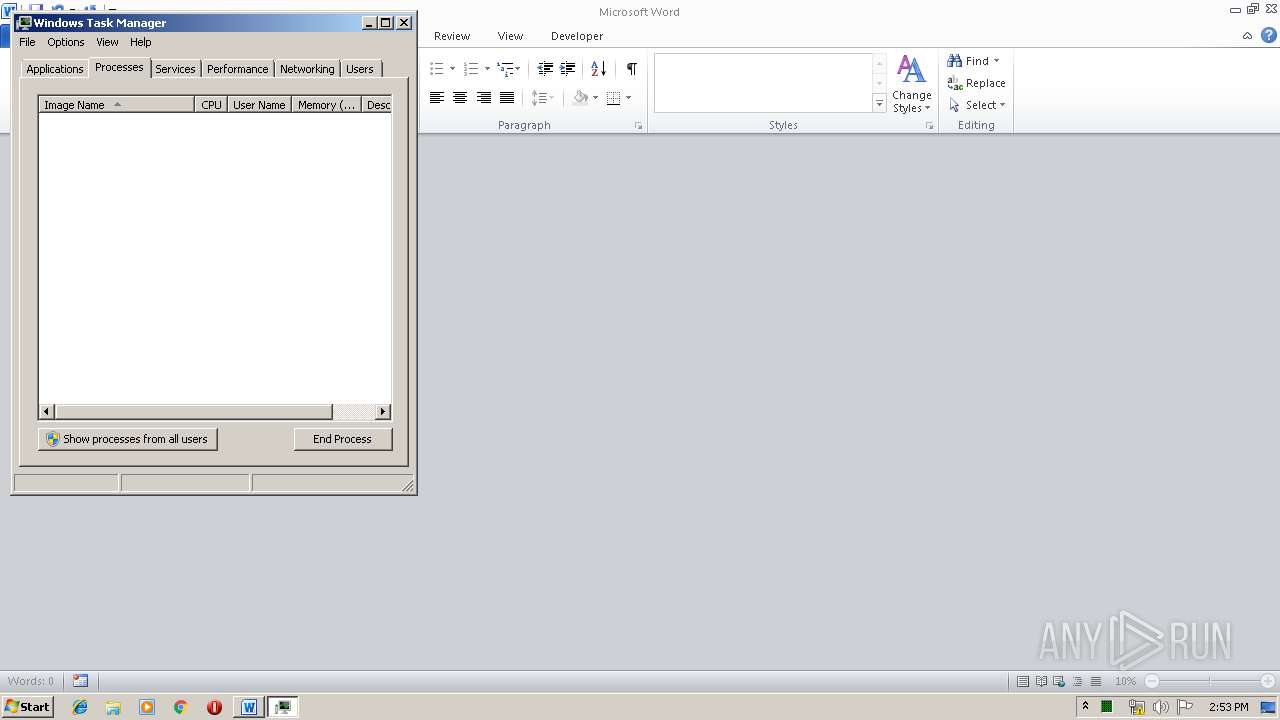
| 3052 | "C:\Windows\system32\taskmgr.exe" | C:\Windows\system32\taskmgr.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3376 | "C:\Windows\system32\taskmgr.exe" | C:\Windows\system32\taskmgr.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
764
Read events
704
Write events
59
Delete events
1
Modification events
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Sample1.zip | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2824) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
3
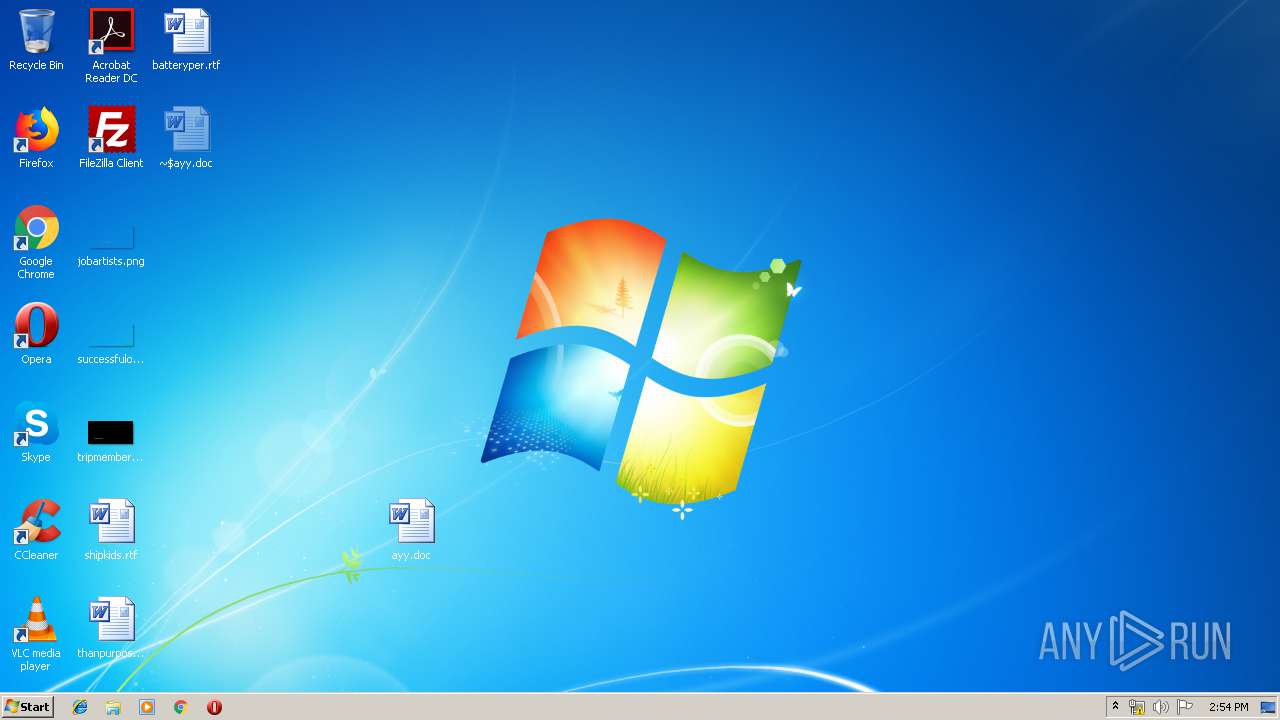
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2824 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2824.12641\514462d42f46c8e2c4a5adae19b2b34de5d0e9b57cee4c073b9354c1e1d7d405.bin | — | |
MD5:— | SHA256:— | |||
| 2264 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR73B0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2264 | WINWORD.EXE | C:\Users\admin\Desktop\~$ayy.doc | pgc | |
MD5:— | SHA256:— | |||
| 2264 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2264 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{4A74C59B-685E-4012-A235-782079EDA88C}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2264 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{21AFF458-4911-4277-9F13-8731A5FEEF4F}.tmp | binary | |
MD5:— | SHA256:— | |||
| 3000 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@bit[1].txt | text | |
MD5:— | SHA256:— | |||
| 2264 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{17CF9AE0-4864-4149-B693-A1084B28B62C}.tmp | smt | |
MD5:5D4D94EE7E06BBB0AF9584119797B23A | SHA256:4826C0D860AF884D3343CA6460B0006A7A2CE7DBCCC4D743208585D997CC5FD1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3000 | EQNEDT32.EXE | GET | — | 51.91.175.221:80 | http://51.91.175.221/Di/10-9.jpg | GB | — | — | malicious |
3000 | EQNEDT32.EXE | GET | 301 | 67.199.248.11:80 | http://bit.ly/2MtYzrJ | US | html | 119 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | EQNEDT32.EXE | 67.199.248.11:80 | bit.ly | Bitly Inc | US | shared |
3000 | EQNEDT32.EXE | 51.91.175.221:80 | — | — | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bit.ly |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3000 | EQNEDT32.EXE | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |