| File name: | Inst_DnevZDDS_v904.exe |
| Full analysis: | https://app.any.run/tasks/c9ac75fe-be93-43de-87fc-cfbfaf69df27 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 06:02:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C71E8FD816E71E1EE157CCB538A2185E |
| SHA1: | B246D89E23655FCBE85DA6EDC298F6F67D4F679D |
| SHA256: | 4309DEA7B21F97C89CE7C320FE64960754E4FEBE9E635C29D0CD8B5C52D4B6FB |
| SSDEEP: | 49152:GuDpxFfWb52OUTv+JZjDoFVzaNGcNnxsaYipulun8pDQxk:3xFfWb52L4ZjUaN/uaYipuLpQ2 |
MALICIOUS
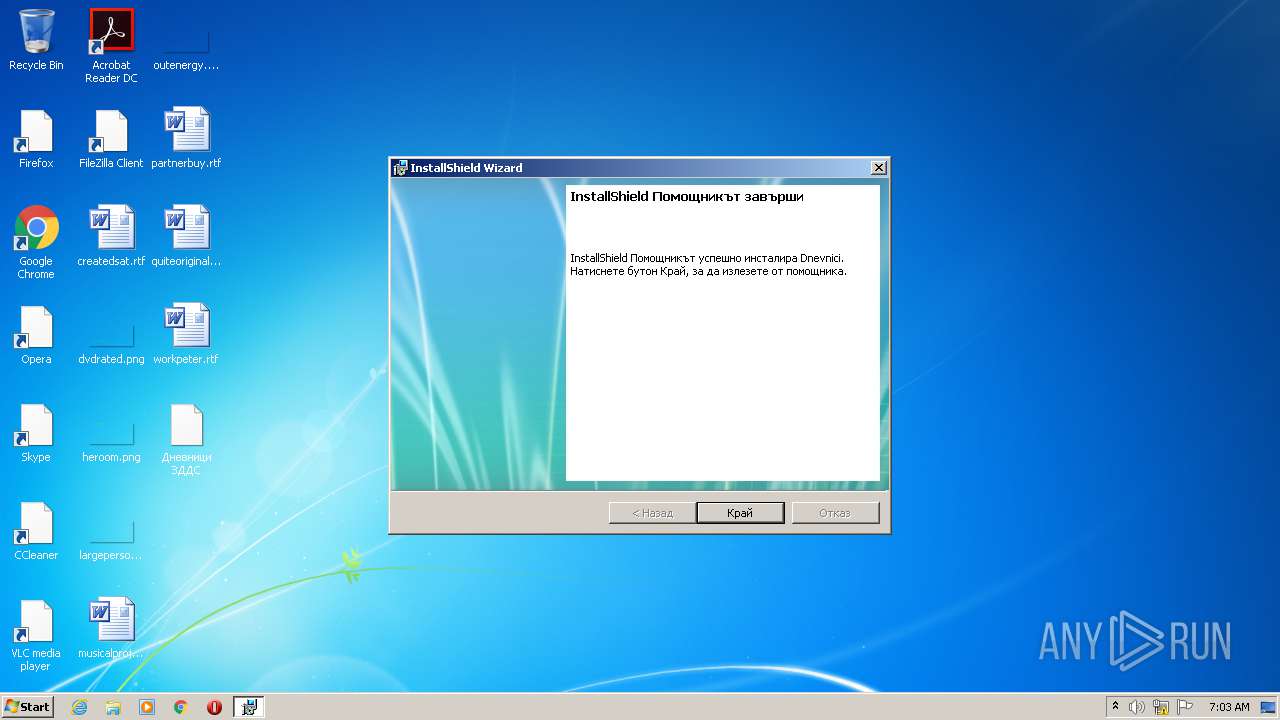
Application was dropped or rewritten from another process
- Dnevnici.exe (PID: 3868)
SUSPICIOUS
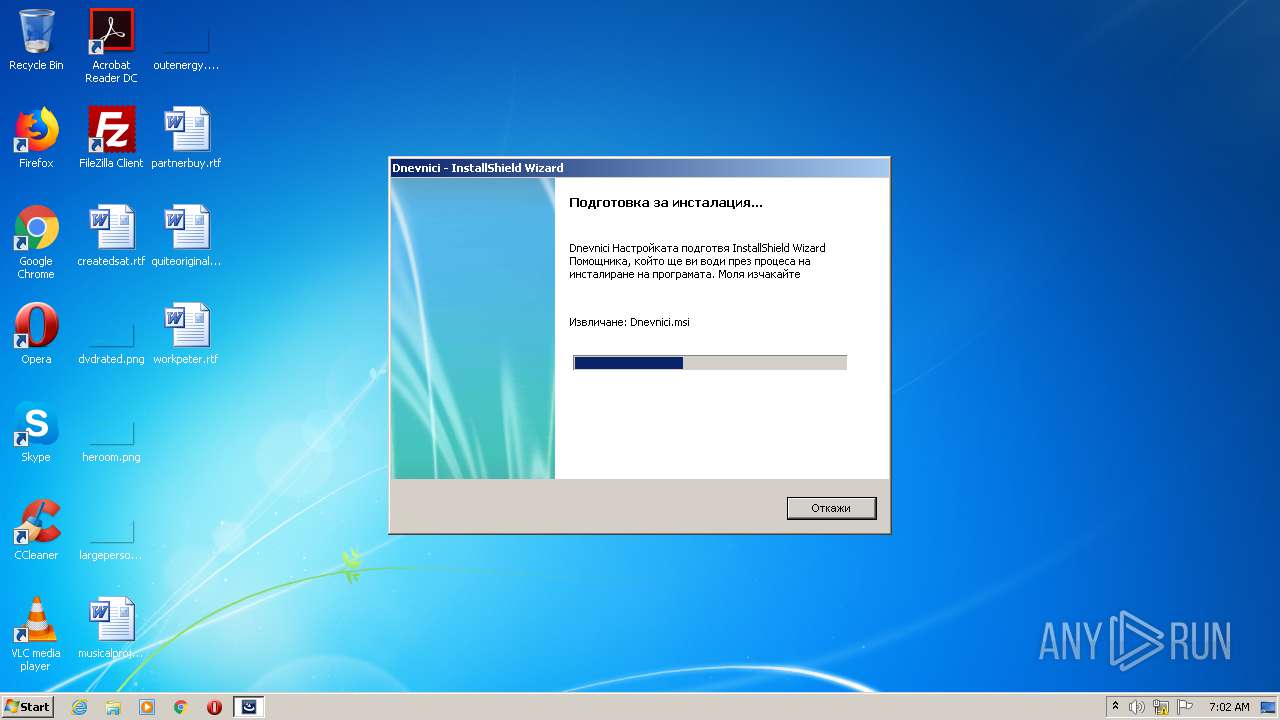
Starts Microsoft Installer
- Inst_DnevZDDS_v904.exe (PID: 960)
Executable content was dropped or overwritten
- Inst_DnevZDDS_v904.exe (PID: 960)
- msiexec.exe (PID: 1316)
Creates files in the Windows directory
- msiexec.exe (PID: 1316)
Executed as Windows Service
- vssvc.exe (PID: 3796)
INFO
Searches for installed software
- msiexec.exe (PID: 1316)
Creates files in the program directory
- msiexec.exe (PID: 1316)
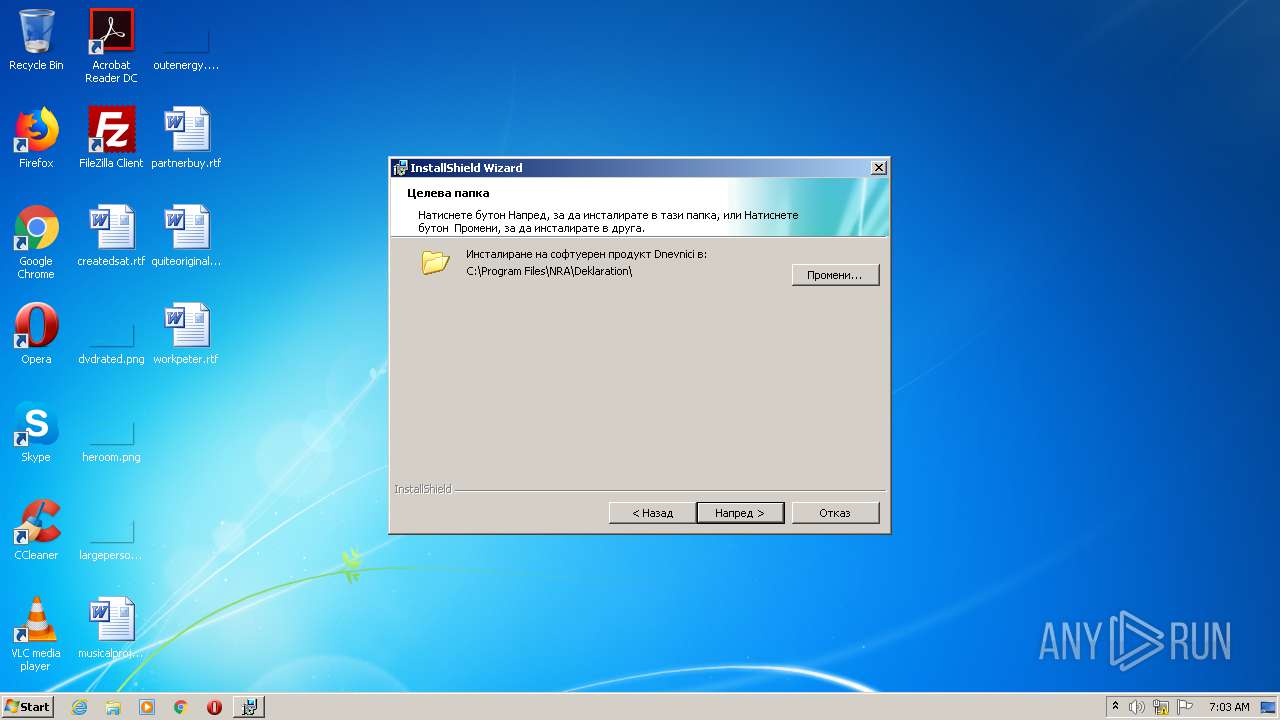
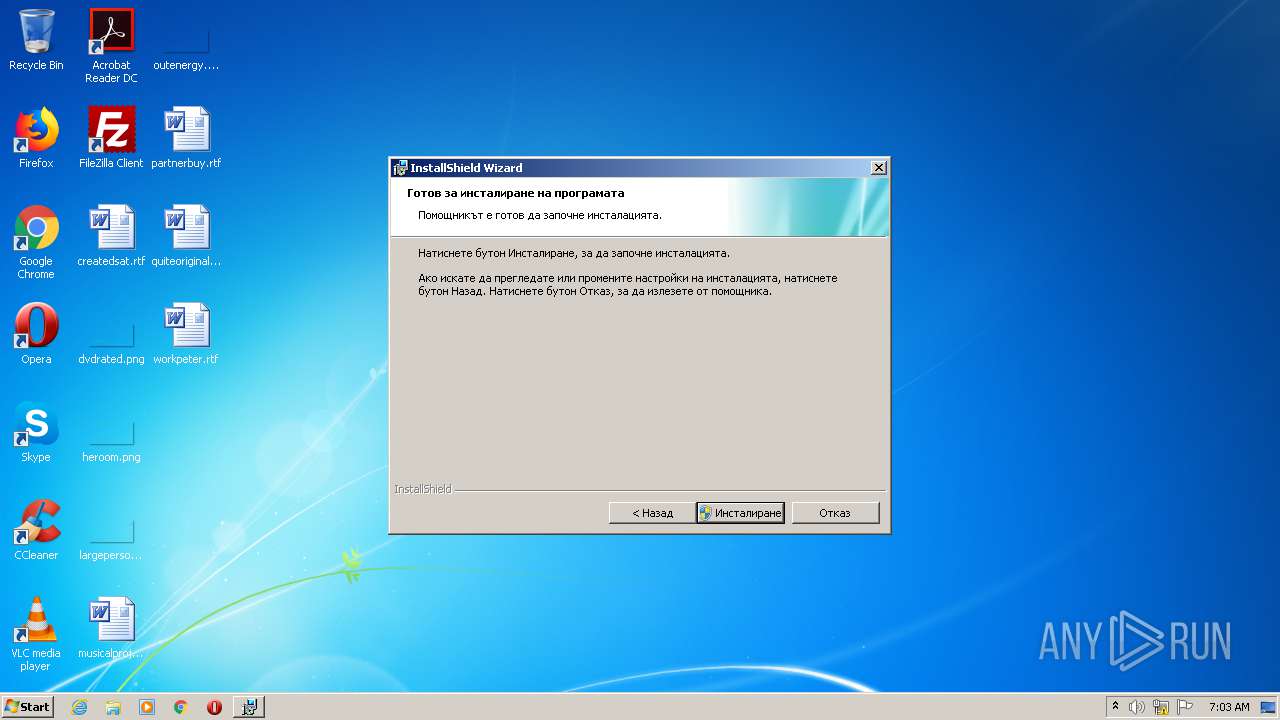
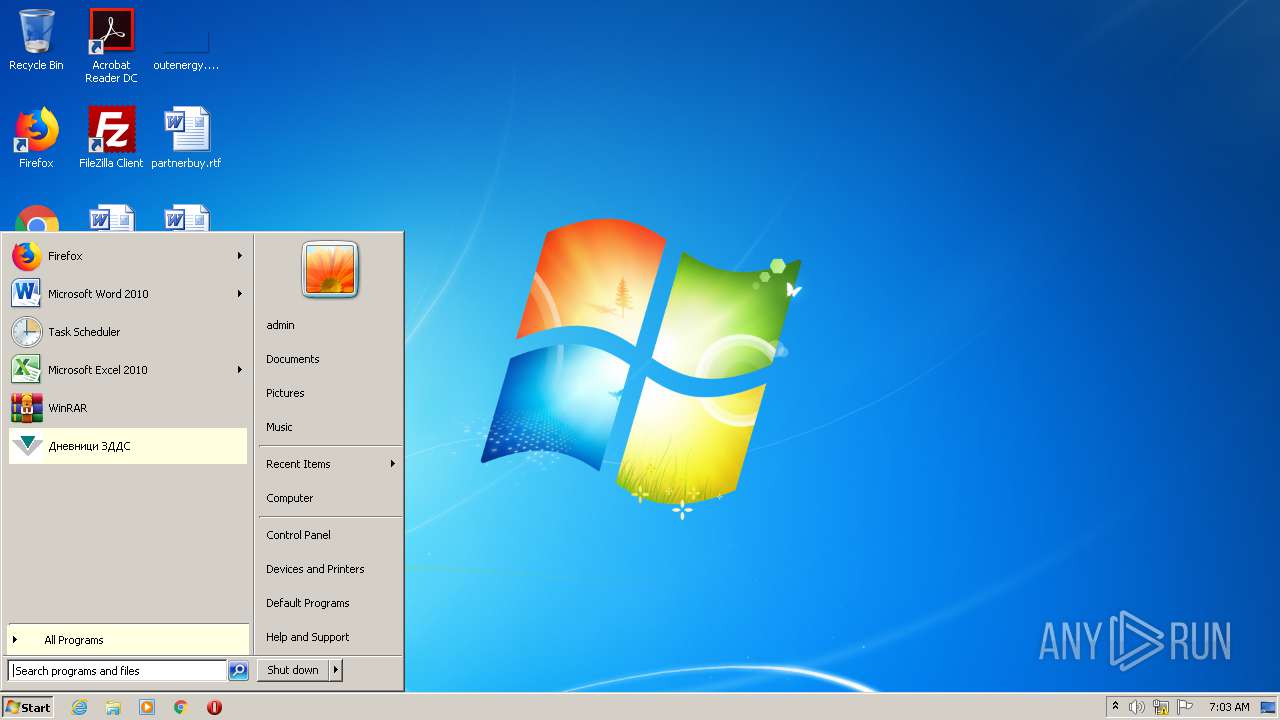
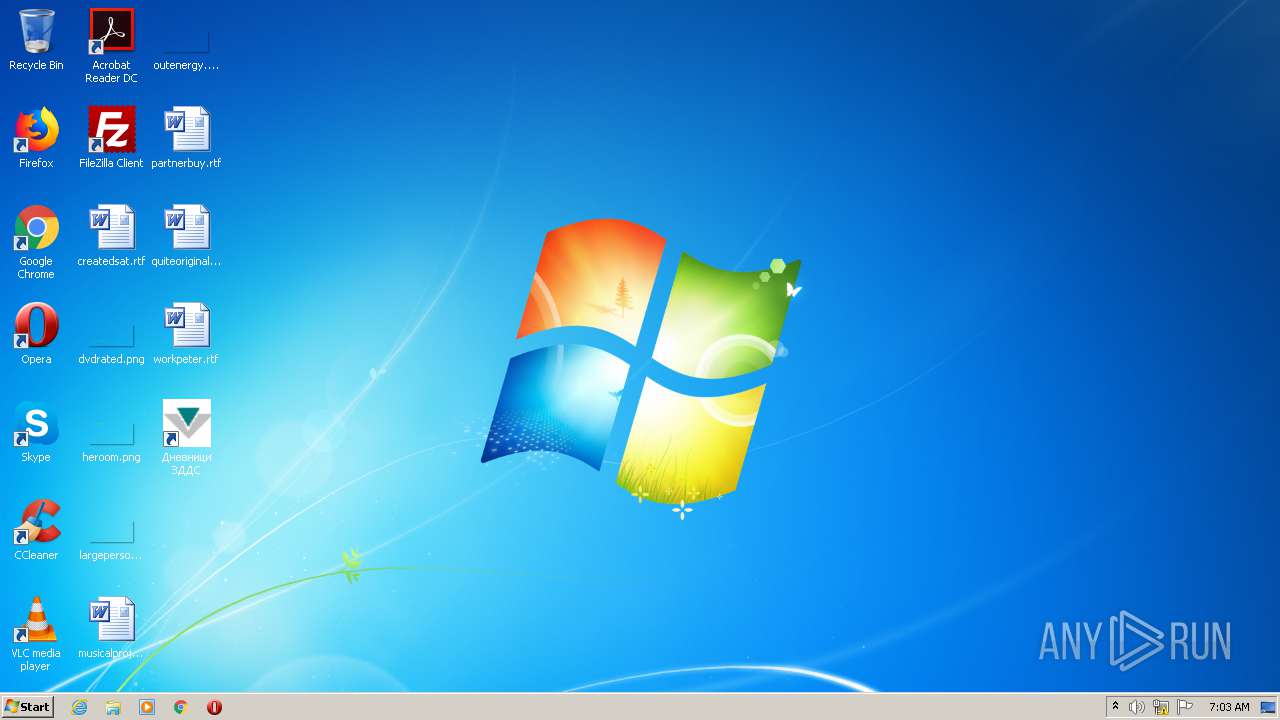
Manual execution by user
- Dnevnici.exe (PID: 3868)
Creates a software uninstall entry
- msiexec.exe (PID: 1316)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:11:02 06:08:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 713216 |
| InitializedDataSize: | 497664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a96b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.4.0.0 |
| ProductVersionNumber: | 9.4.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
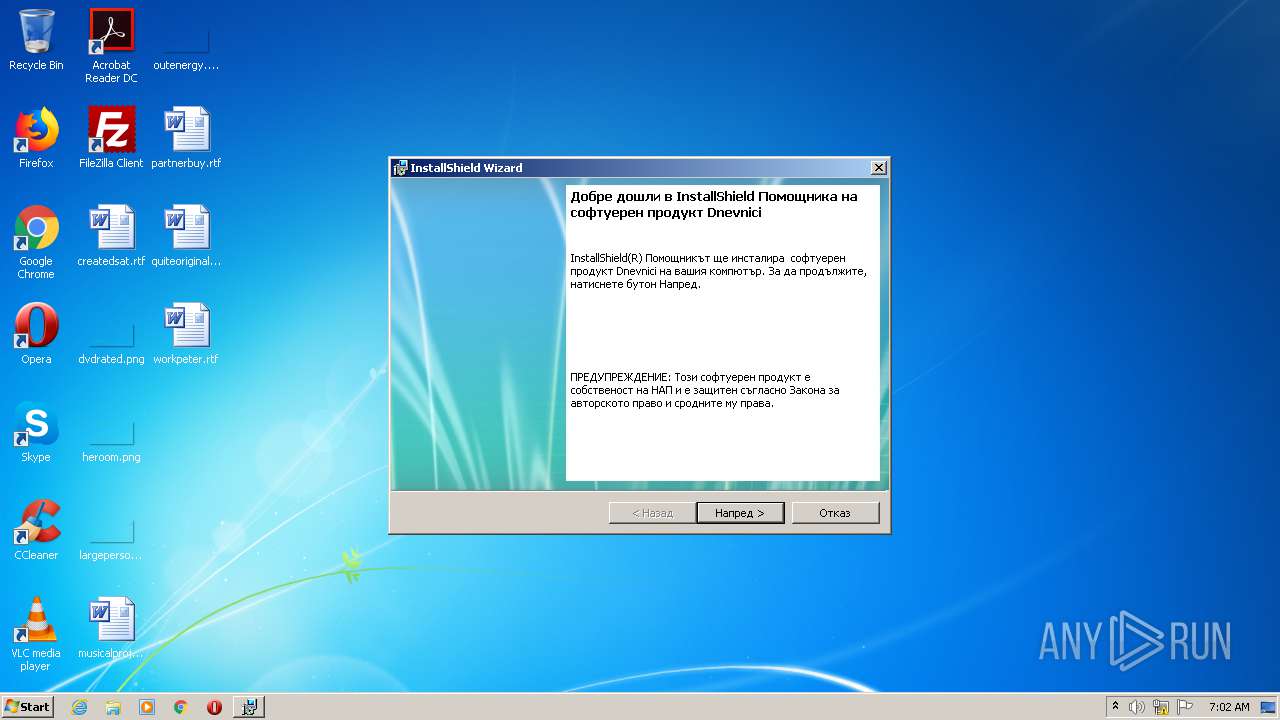
| CompanyName: | NRA |
| FileDescription: | Setup Launcher Unicode |
| FileVersion: | 9.04 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (C) 2011 Flexera Software, Inc. and/or InstallShield Co. Inc. All Rights Reserved. |
| OriginalFileName: | InstallShield Setup.exe |
| ProductName: | Dnevnici |
| ProductVersion: | 9.04 |
| InternalBuildNumber: | 110150 |
| ISInternalVersion: | 18.0.368 |
| ISInternalDescription: | Setup Launcher Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Nov-2011 05:08:04 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | NRA |
| FileDescription: | Setup Launcher Unicode |
| FileVersion: | 9.04 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (C) 2011 Flexera Software, Inc. and/or InstallShield Co. Inc. All Rights Reserved. |
| OriginalFilename: | InstallShield Setup.exe |
| ProductName: | Dnevnici |
| ProductVersion: | 9.04 |
| Internal Build Number: | 110150 |
| ISInternalVersion: | 18.0.368 |
| ISInternalDescription: | Setup Launcher Unicode |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Nov-2011 05:08:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000AE02D | 0x000AE200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58711 |
.rdata | 0x000B0000 | 0x000291A0 | 0x00029200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.91178 |
.data | 0x000DA000 | 0x00008828 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.56032 |
.rsrc | 0x000E3000 | 0x0004DC34 | 0x0004DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.56883 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19214 | 1136 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.835 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.35696 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 6.14965 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.18448 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.85842 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.57777 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.81004 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 6.06596 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 3.22977 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
msi.dll (delay-loaded) |
Total processes
43
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Users\admin\AppData\Local\Temp\Inst_DnevZDDS_v904.exe" | C:\Users\admin\AppData\Local\Temp\Inst_DnevZDDS_v904.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1316 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3516 | MSIEXEC.EXE /i "C:\Users\admin\AppData\Local\Temp\{D16BC9CB-82C9-498D-8E6D-E2BA19ED1A45}\Dnevnici.msi" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp" SETUPEXENAME="Inst_DnevZDDS_v904.exe" | C:\Windows\system32\MSIEXEC.EXE | — | Inst_DnevZDDS_v904.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3796 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
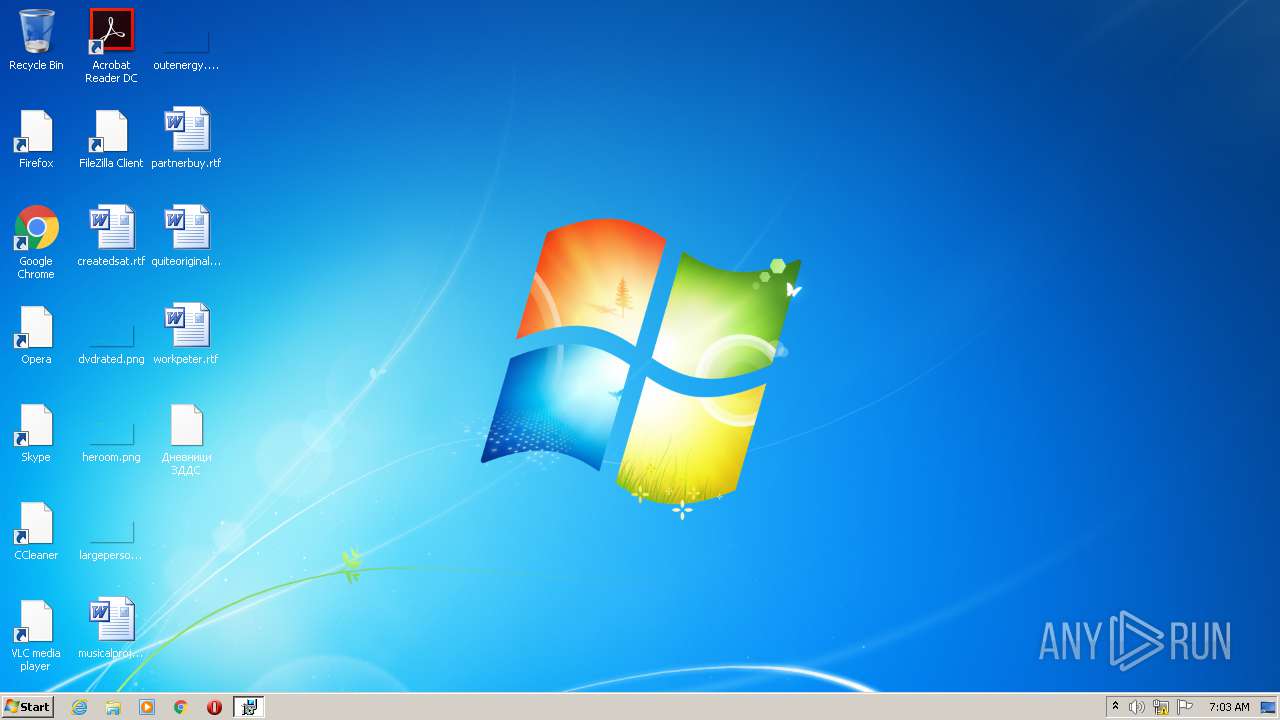
| 3868 | "C:\Program Files\NRA\Deklaration\ZDDS\Dnevnici.exe" | C:\Program Files\NRA\Deklaration\ZDDS\Dnevnici.exe | — | explorer.exe | |||||||||||
User: admin Company: НАП Integrity Level: MEDIUM Description: Дневници по ЗДДС Exit code: 0 Version: 9.0.4.0 Modules
| |||||||||||||||
Total events
824
Read events
565
Write events
247
Delete events
12
Modification events
| (PID) Process: | (1316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000005CEF97B0A6A6D60124050000C40E0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000005CEF97B0A6A6D60124050000C40E0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 43 | |||
| (PID) Process: | (1316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000009C3AE4B0A6A6D60124050000C40E0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1316) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000009C3AE4B0A6A6D60124050000640D0000E8030000010000000000000000000000143E2C91BC45C04AA297FACCB236BE1F0000000000000000 | |||
| (PID) Process: | (3796) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007A74FEB0A6A6D601D40E0000480D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3796) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007A74FEB0A6A6D601D40E0000240A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3796) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007A74FEB0A6A6D601D40E0000500D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3796) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007A74FEB0A6A6D601D40E0000D80D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3796) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000889B05B1A6A6D601D40E0000D80D0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
9
Suspicious files
4
Text files
5
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 960 | Inst_DnevZDDS_v904.exe | C:\Users\admin\AppData\Local\Temp\~4367.tmp | — | |
MD5:— | SHA256:— | |||
| 960 | Inst_DnevZDDS_v904.exe | C:\Users\admin\AppData\Local\Temp\~4377.tmp | — | |
MD5:— | SHA256:— | |||
| 1316 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1316 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF8CE35778770C2F03.TMP | — | |
MD5:— | SHA256:— | |||
| 3796 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 960 | Inst_DnevZDDS_v904.exe | C:\Users\admin\AppData\Local\Temp\{D16BC9CB-82C9-498D-8E6D-E2BA19ED1A45}\Dnevnici.msi | executable | |
MD5:— | SHA256:— | |||
| 1316 | msiexec.exe | C:\Windows\Installer\MSID8FF.tmp | binary | |
MD5:— | SHA256:— | |||
| 1316 | msiexec.exe | C:\Config.Msi\2dd1ae.rbs | — | |
MD5:— | SHA256:— | |||
| 1316 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF6311E432F13CA7B9.TMP | — | |
MD5:— | SHA256:— | |||
| 1316 | msiexec.exe | C:\Program Files\NRA\Deklaration\ZDDS\Dnevnici.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report