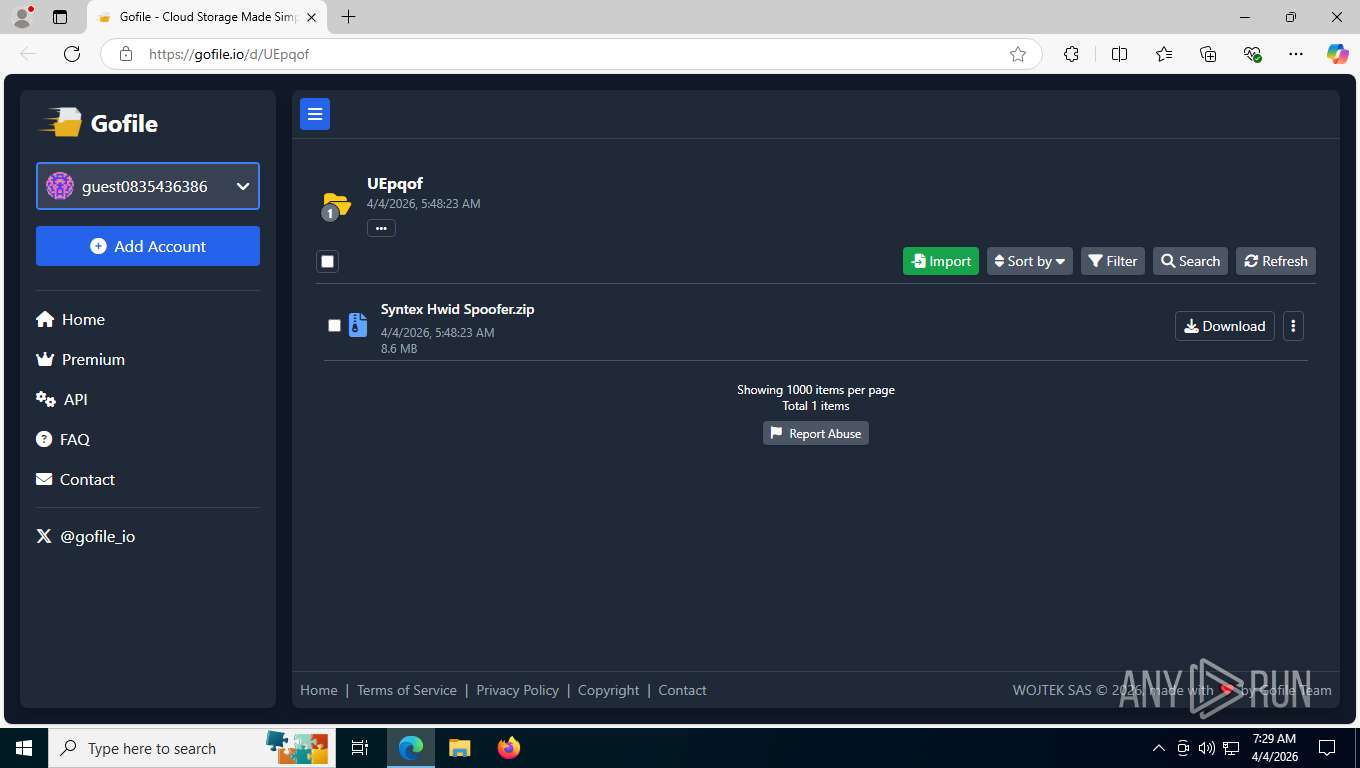
| URL: | transfer.short.gy/Syntex-Hwid-Spoofer |
| Full analysis: | https://app.any.run/tasks/dadd0ed4-7bcb-4849-af88-4e0498c07ad3 |
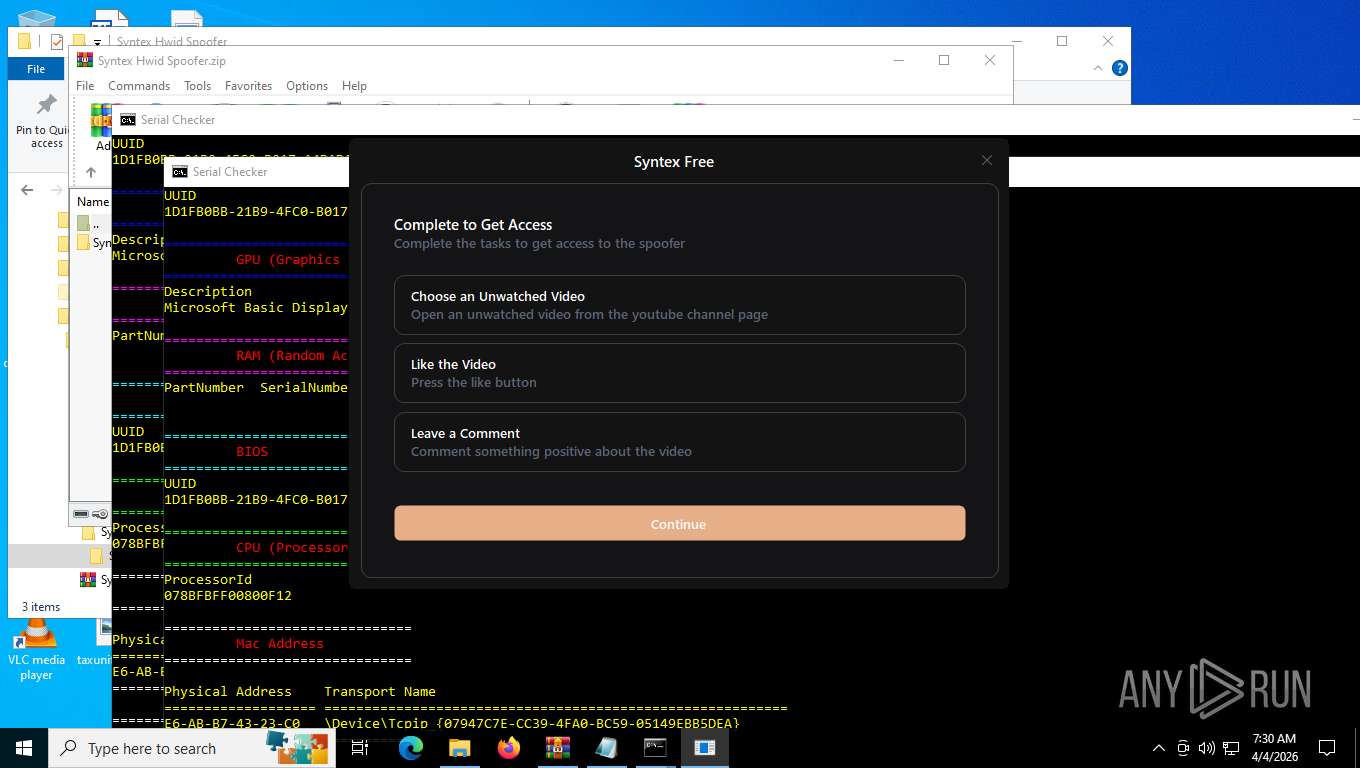
| Verdict: | Malicious activity |
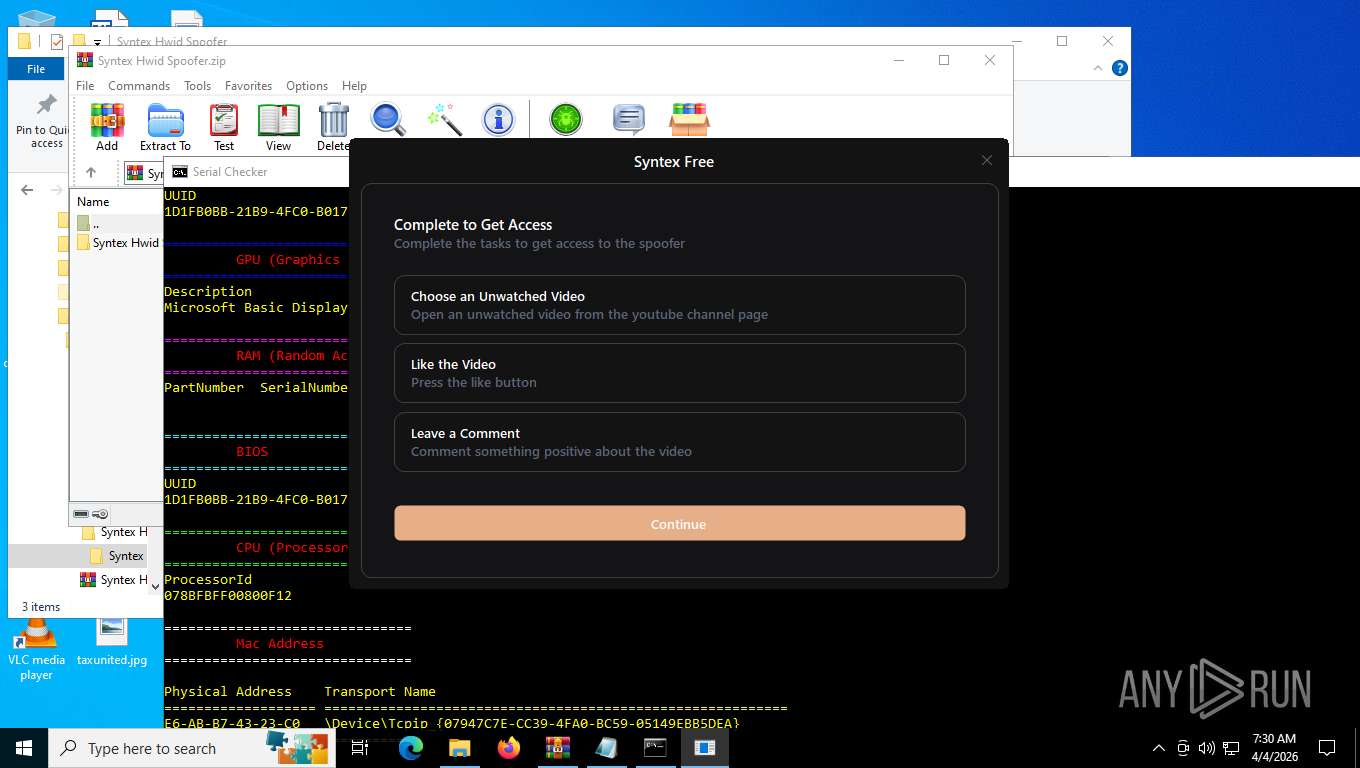
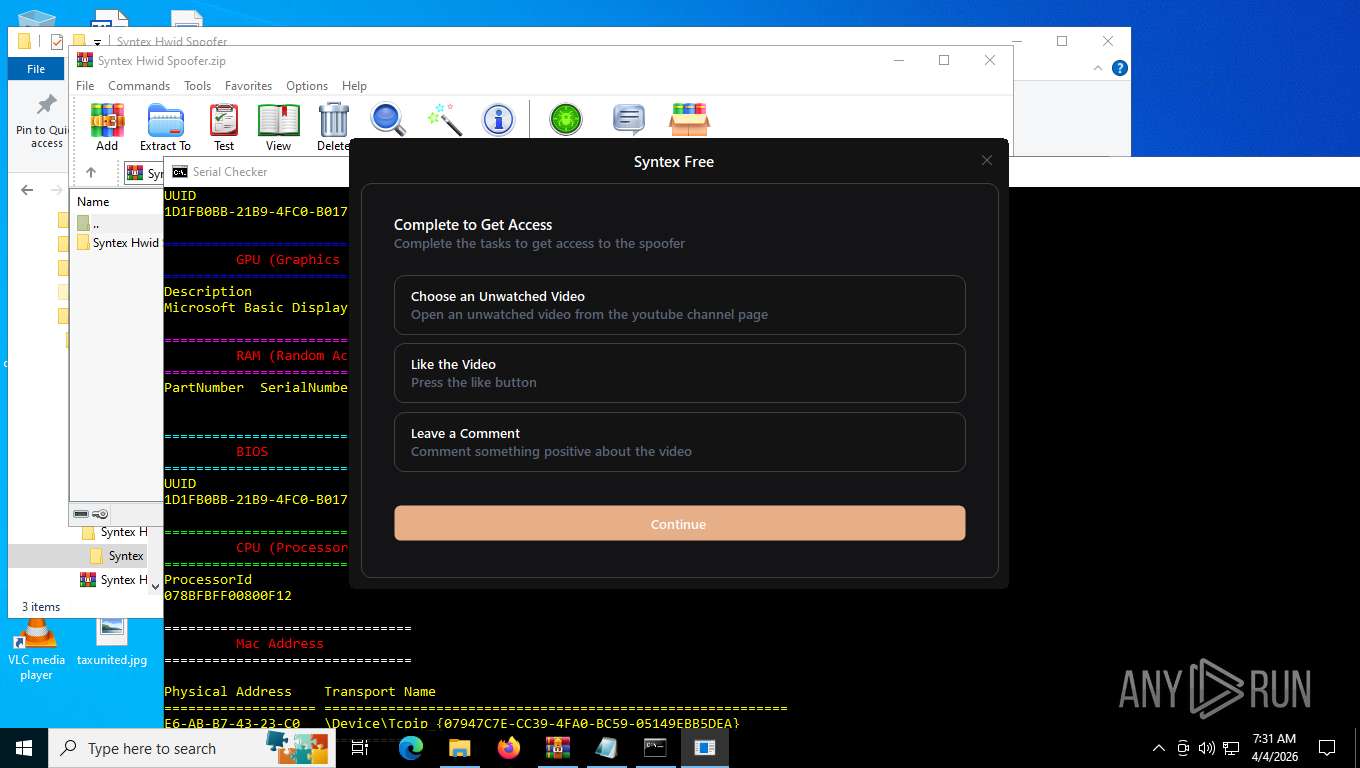
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | April 04, 2026, 11:29:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 61DF61F7432829A67958627C3B9794F7 |
| SHA1: | 8FE3E96193623F688702A60FAAC1242FE9F4A49A |
| SHA256: | 42EA7C1C6CBB03D3F0658F3774275749C93C81CF453BAC83A8161732080F8832 |
| SSDEEP: | 3:rHNef4AdQSEEX:rHNeN1EEX |
MALICIOUS
Executing a file with an untrusted certificate
- Syntex Spoofer.exe (PID: 8396)
- Syntex Spoofer.exe (PID: 7516)
- Syntex Spoofer.exe (PID: 8368)
- Syntex Spoofer.exe (PID: 8460)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8220)
- cmd.exe (PID: 5160)
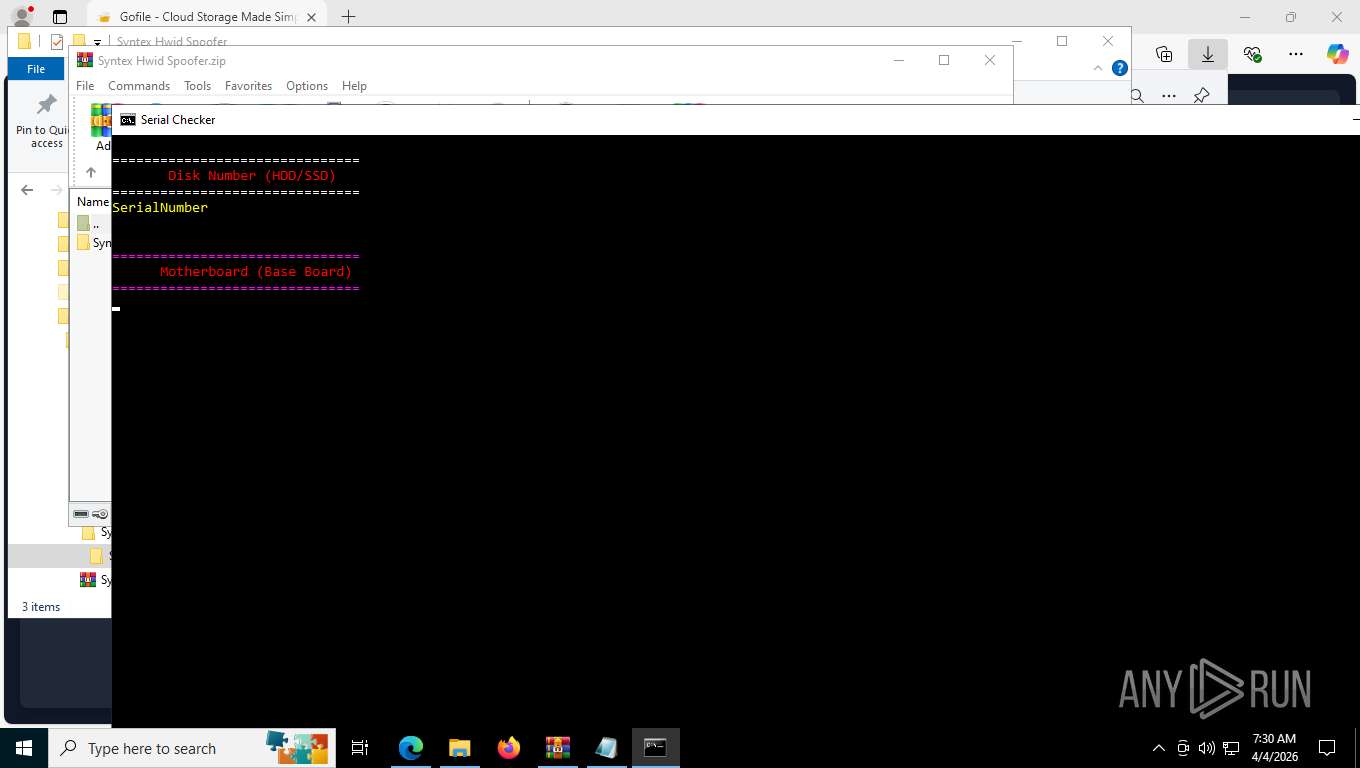
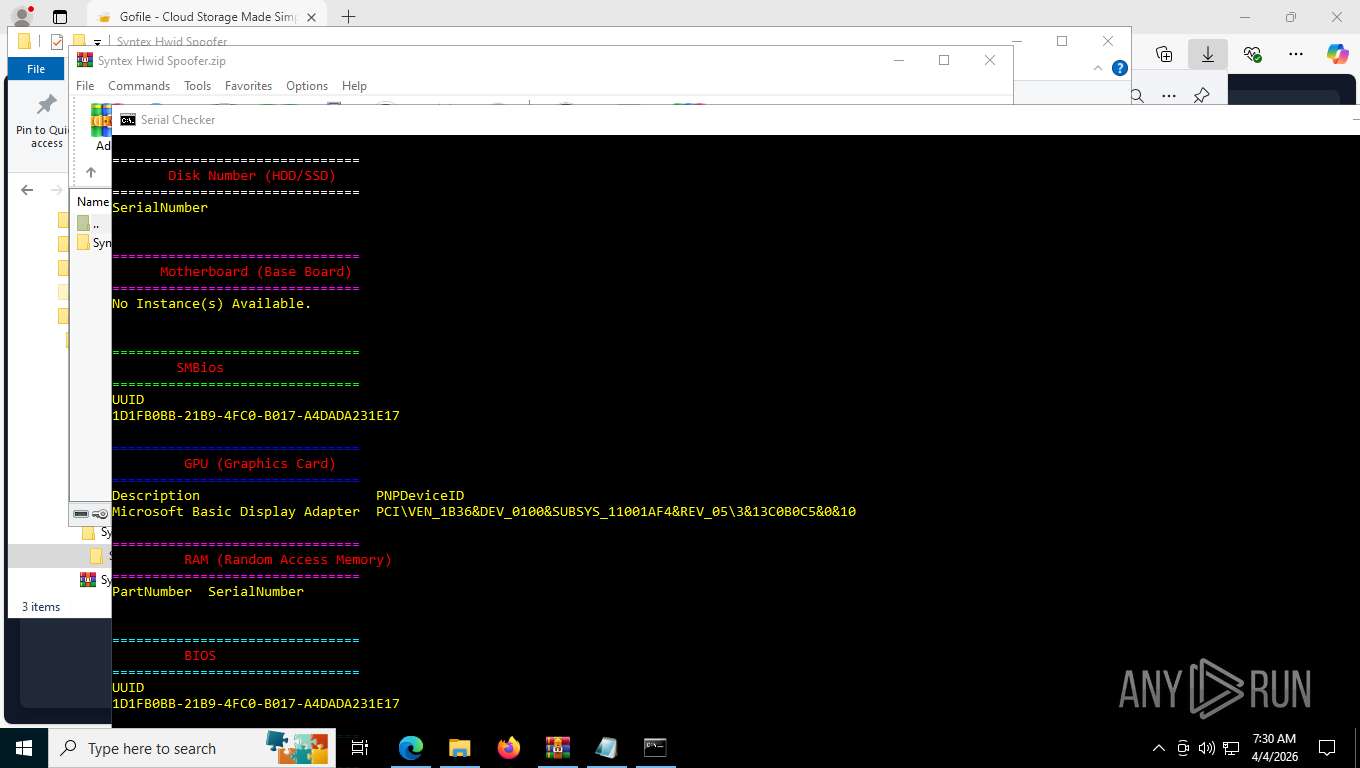
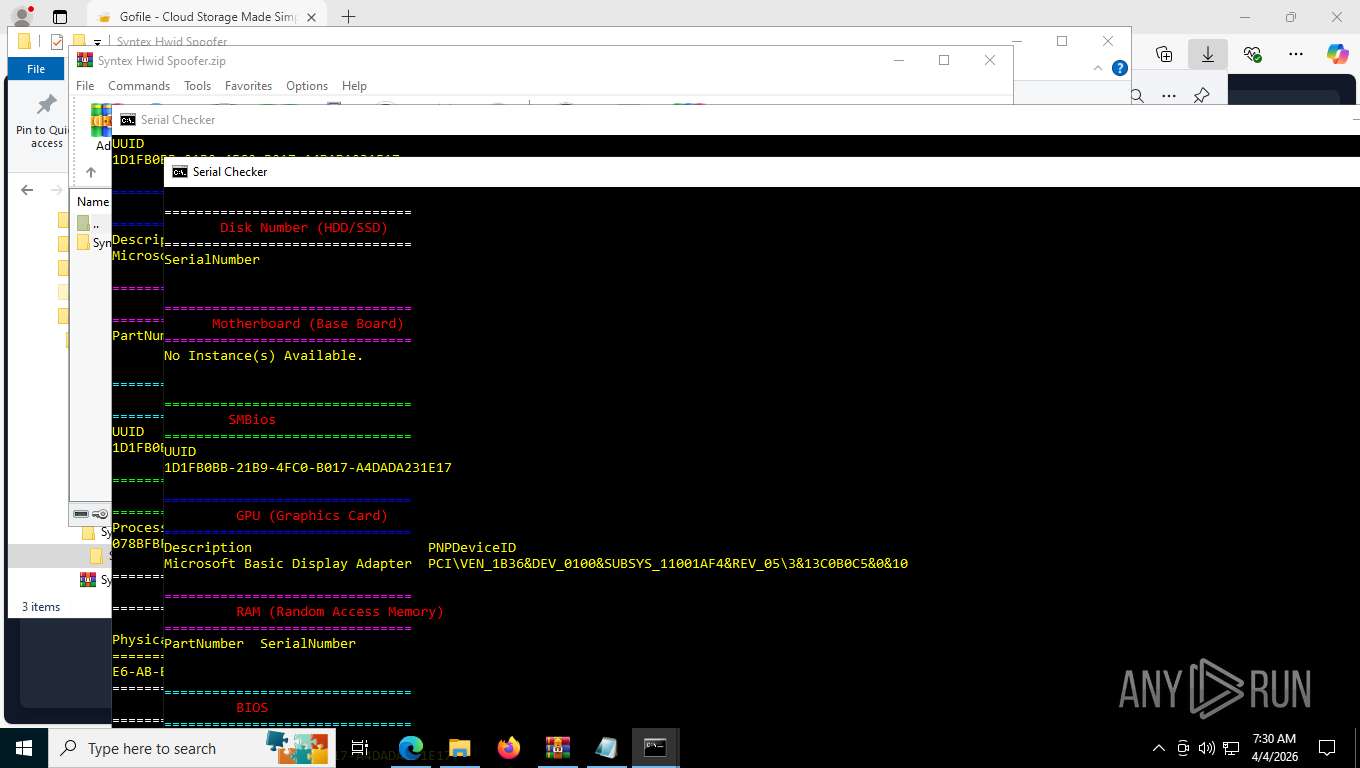
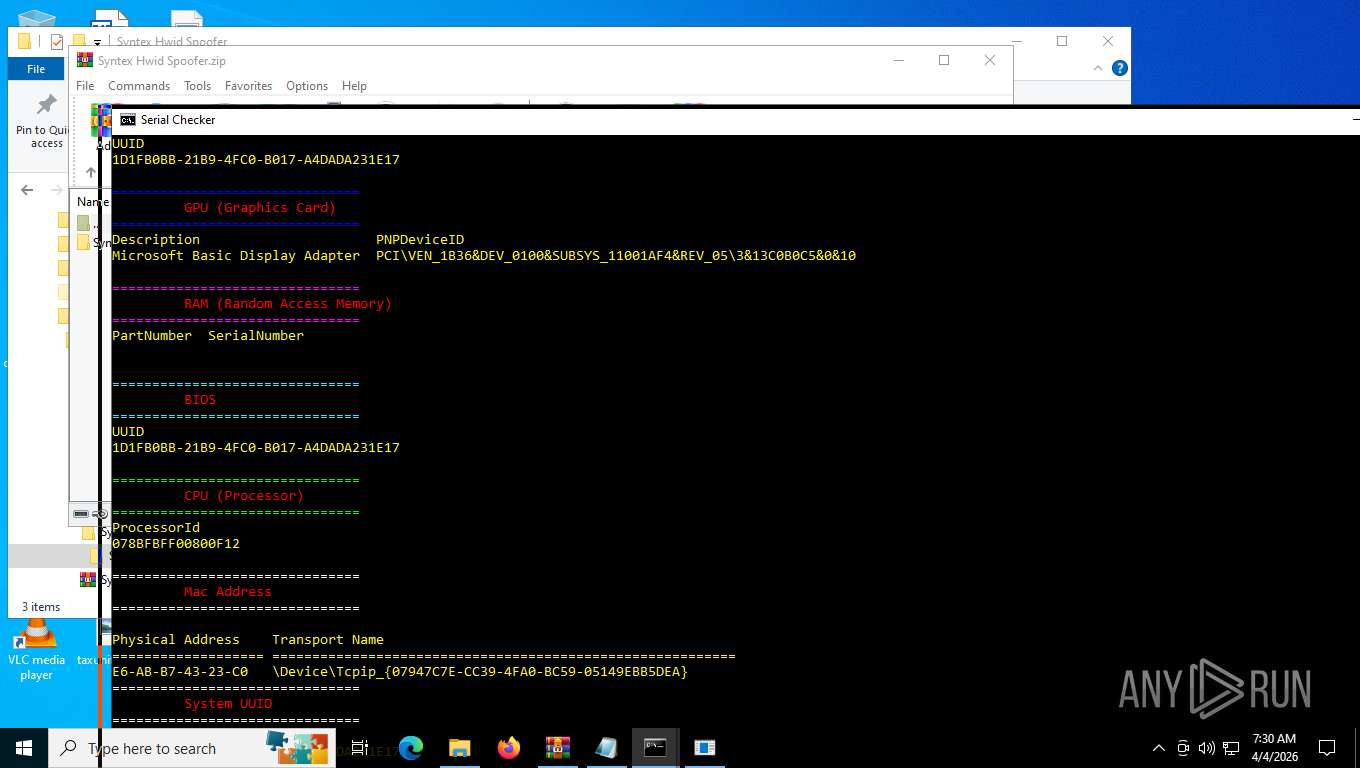
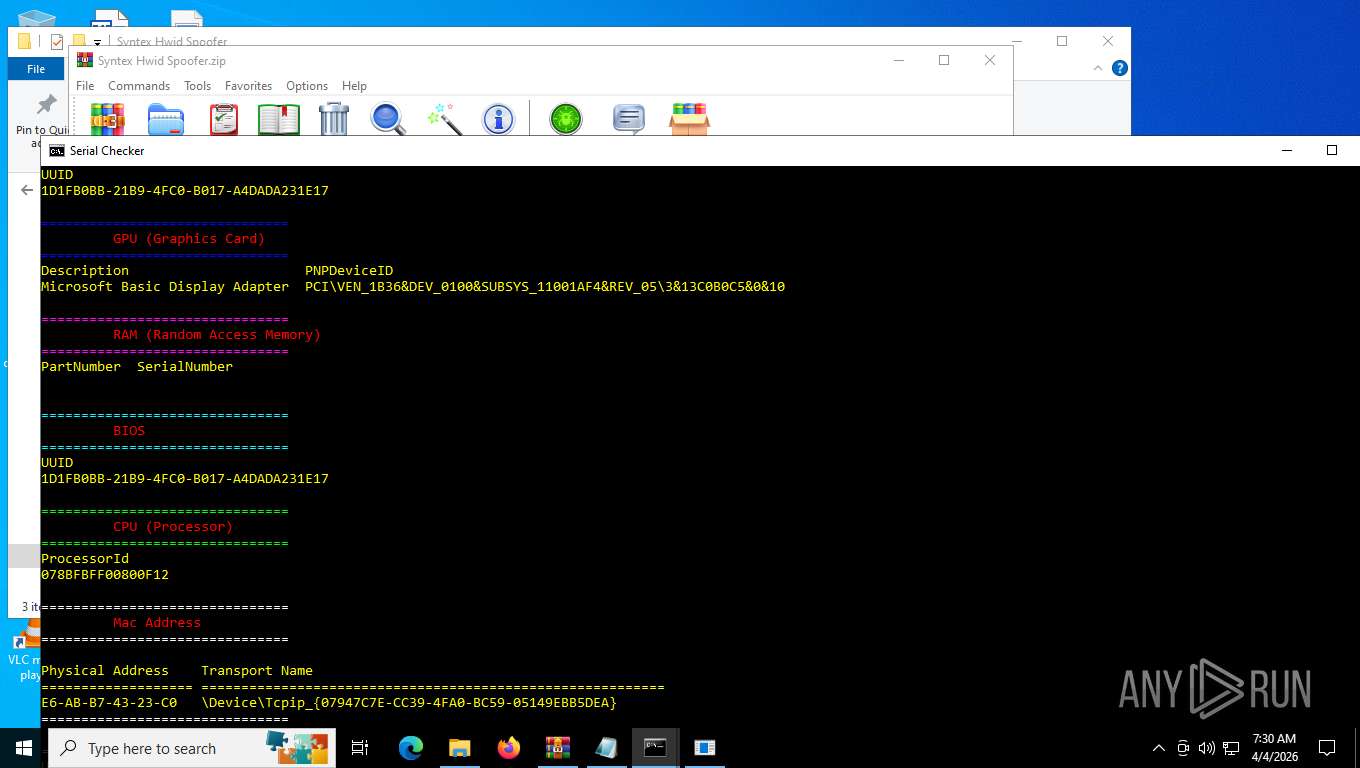
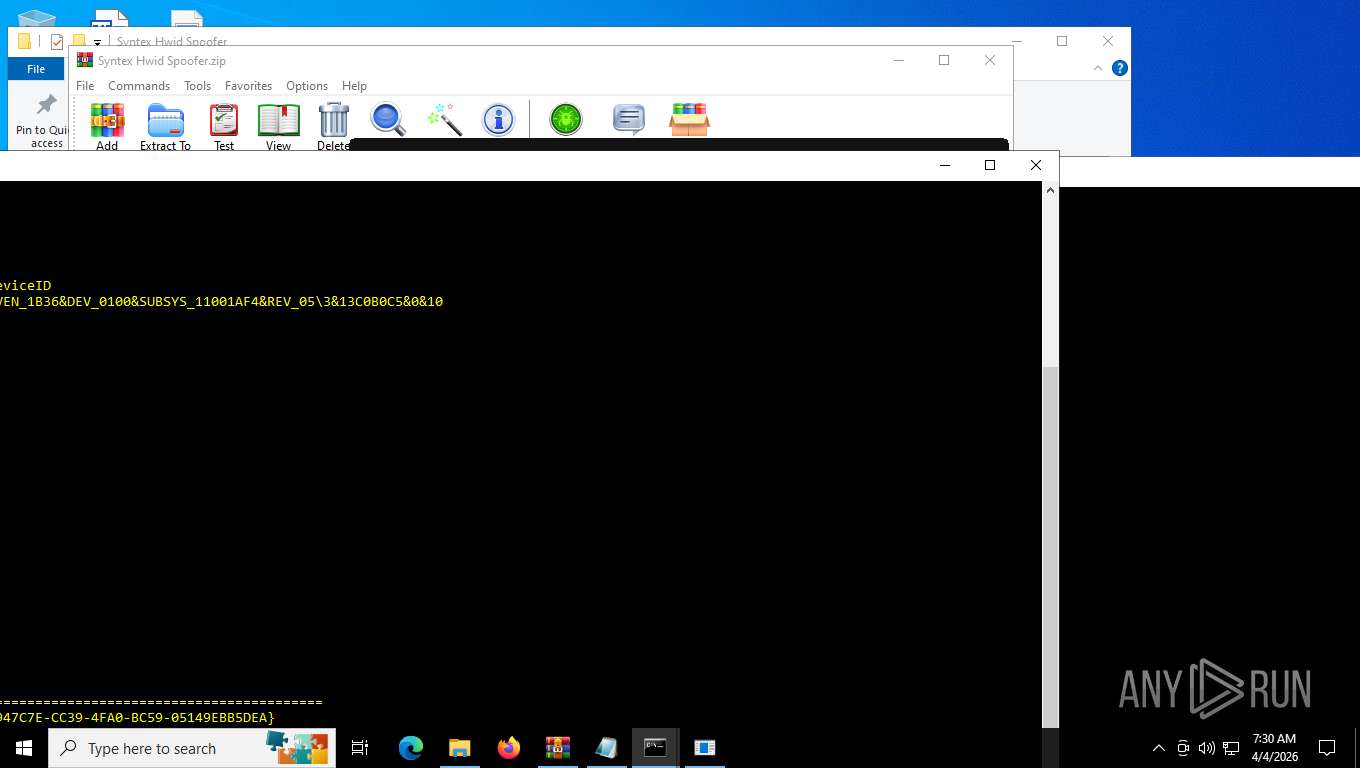
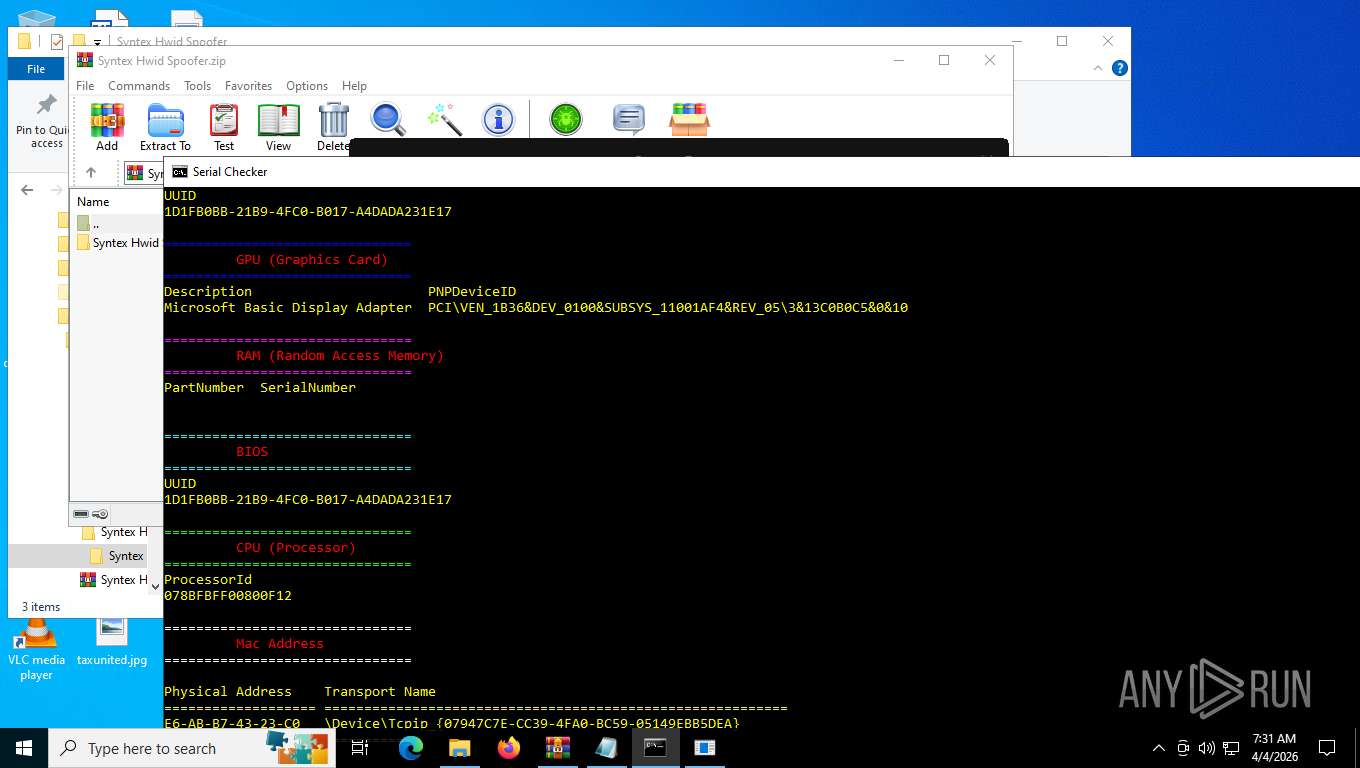
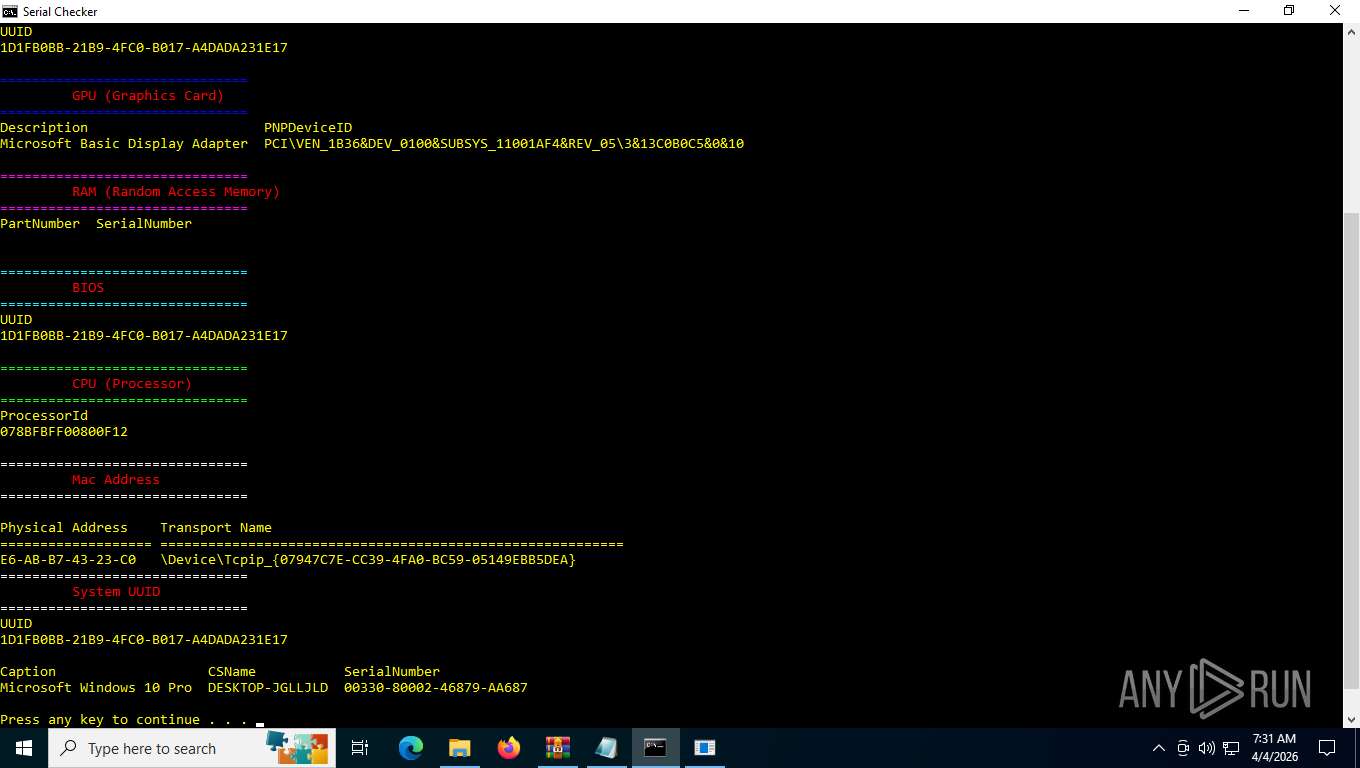
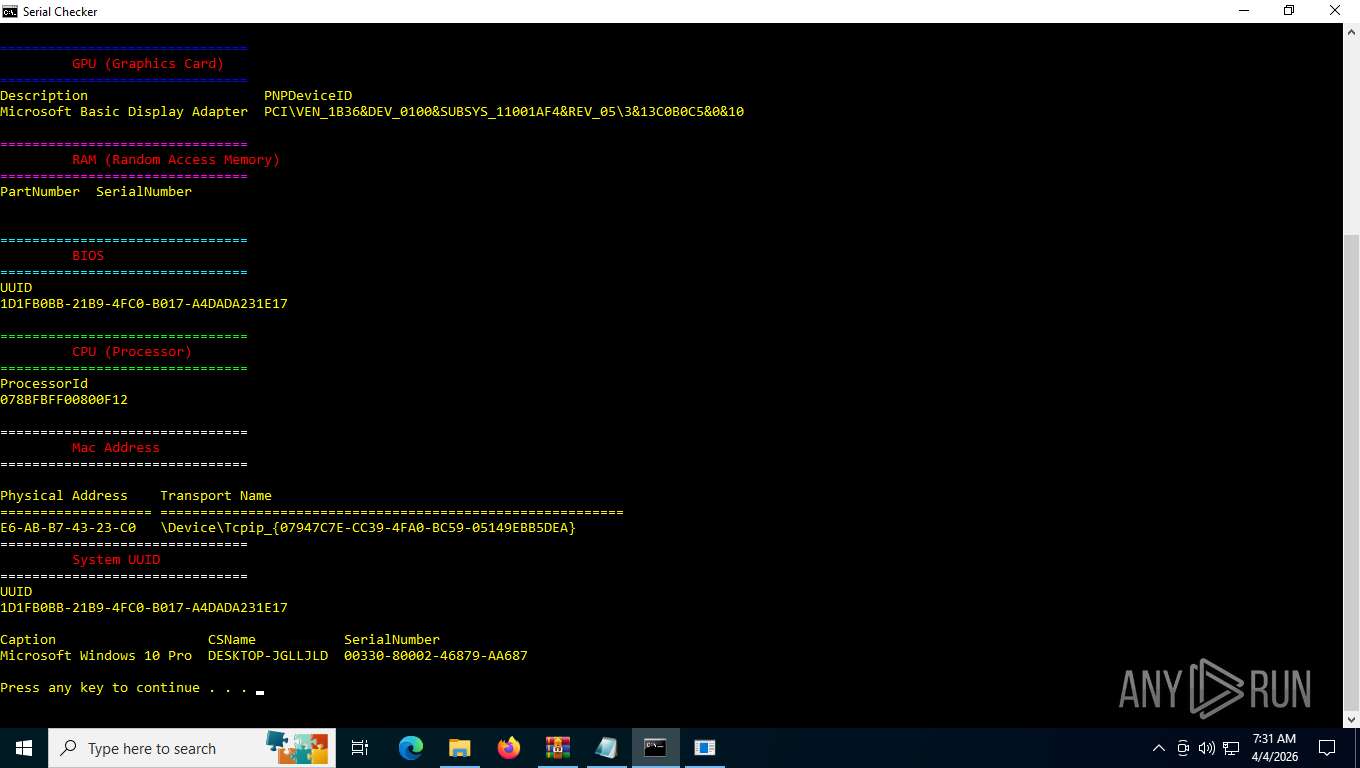
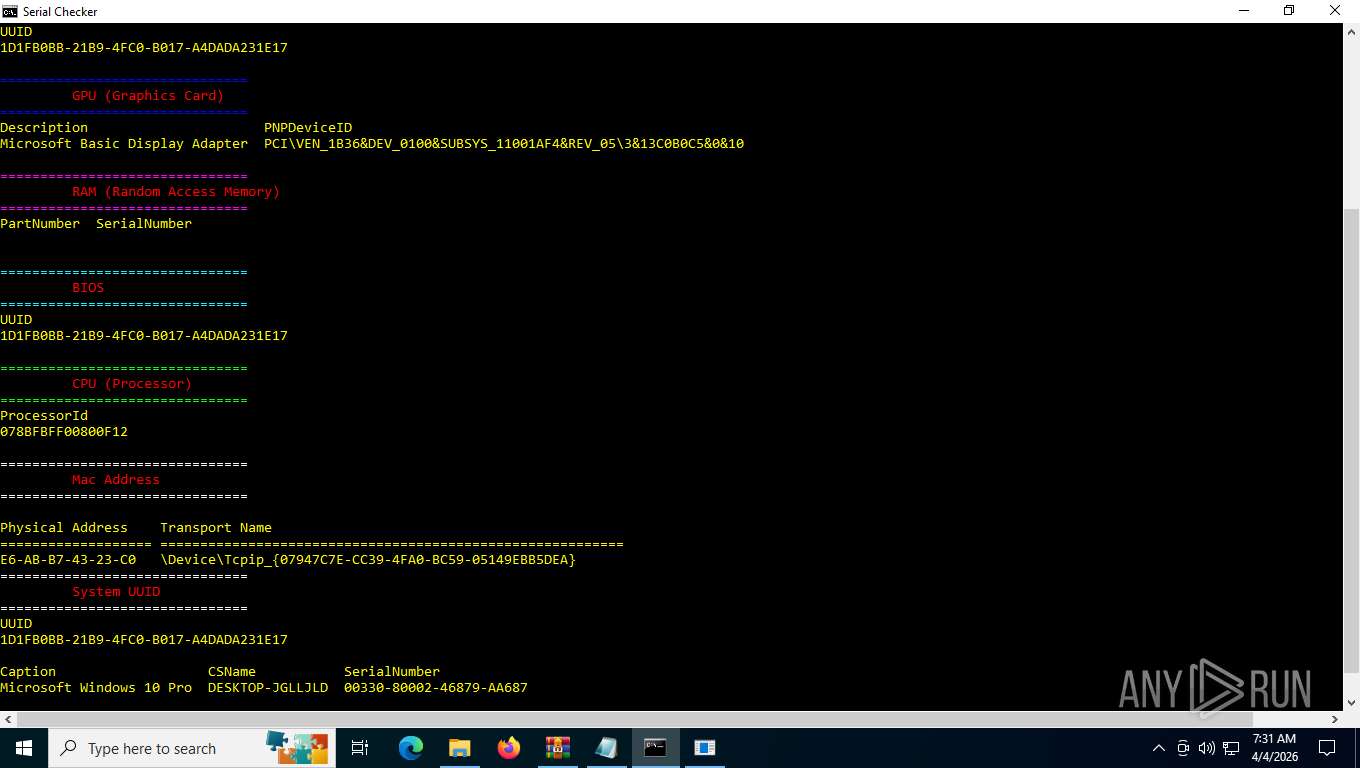
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 8220)
- cmd.exe (PID: 5160)
PowerShell remote script execution via IRM piped to IEX
- Syntex Spoofer.exe (PID: 7516)
Starts POWERSHELL.EXE for commands execution
- Syntex Spoofer.exe (PID: 7516)
Uses WMIC.EXE to obtain data on the base board management (motherboard or system board)
- cmd.exe (PID: 8220)
- cmd.exe (PID: 5160)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 8220)
- cmd.exe (PID: 5160)
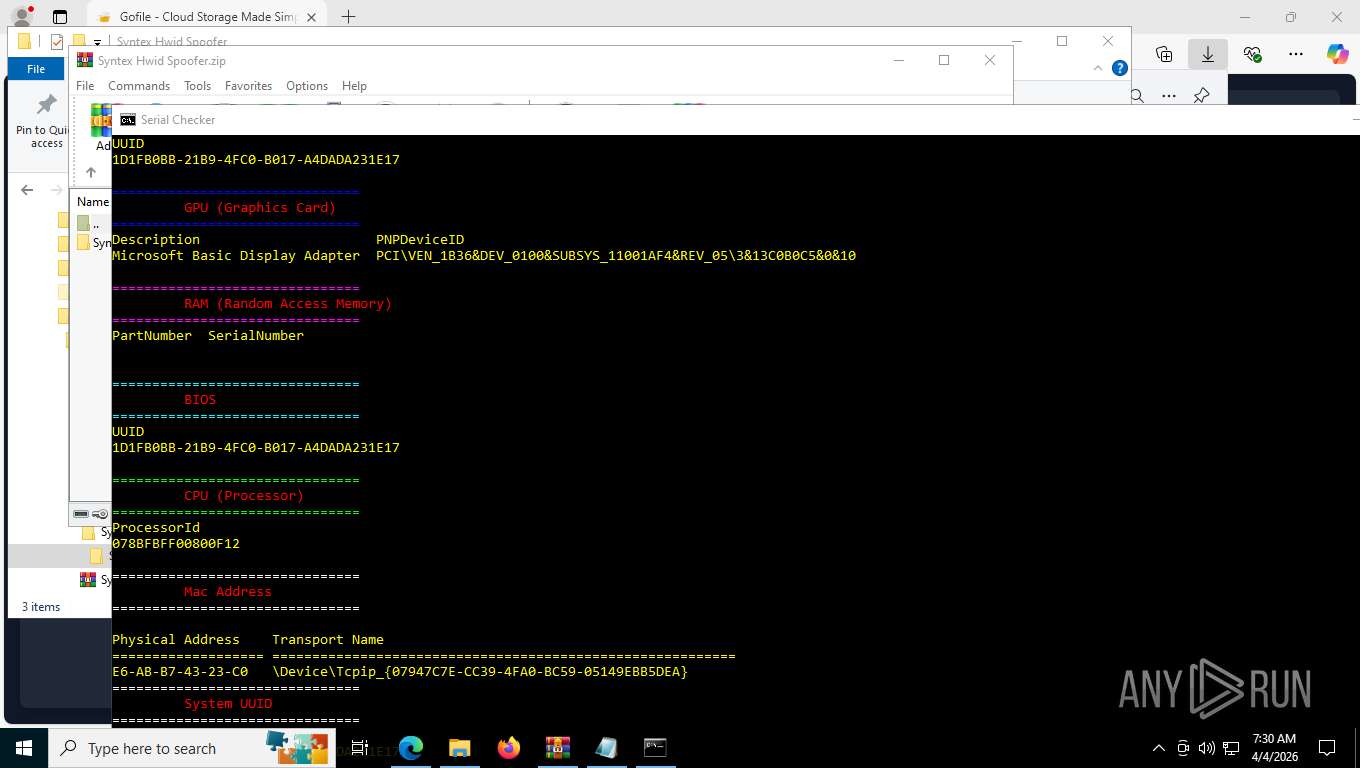
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 5404)
- WMIC.exe (PID: 8776)
- WMIC.exe (PID: 8976)
- WMIC.exe (PID: 8484)
- WMIC.exe (PID: 2032)
- WMIC.exe (PID: 8920)
- WMIC.exe (PID: 6812)
- WMIC.exe (PID: 3416)
- WMIC.exe (PID: 6508)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 8724)
- WMIC.exe (PID: 8536)
- WMIC.exe (PID: 784)
Accesses computer name via WMI (SCRIPT)
- WMIC.exe (PID: 8724)
- WMIC.exe (PID: 4128)
- WMIC.exe (PID: 8536)
- WMIC.exe (PID: 8956)
- WMIC.exe (PID: 784)
- WMIC.exe (PID: 7204)
Uses WMIC.EXE to obtain memory chip information
- cmd.exe (PID: 8220)
- cmd.exe (PID: 5160)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 8220)
- cmd.exe (PID: 5160)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 8220)
- cmd.exe (PID: 5160)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 8220)
- cmd.exe (PID: 5160)
Accesses system license id via WMI (SCRIPT)
- WMIC.exe (PID: 4128)
- WMIC.exe (PID: 8956)
- WMIC.exe (PID: 7204)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 4128)
- WMIC.exe (PID: 8956)
- WMIC.exe (PID: 7204)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 7404)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8824)
Executable content was dropped or overwritten
- csc.exe (PID: 8824)
- powershell.exe (PID: 7404)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7404)
INFO
Checks supported languages
- identity_helper.exe (PID: 6832)
- mode.com (PID: 8348)
- Syntex Spoofer.exe (PID: 7516)
- mode.com (PID: 9156)
- csc.exe (PID: 8824)
- cvtres.exe (PID: 7708)
- tempcache.exe (PID: 4592)
- identity_helper.exe (PID: 2368)
- mode.com (PID: 4712)
- Syntex Spoofer.exe (PID: 8460)
The sample compiled with english language support
- WinRAR.exe (PID: 8772)
- msedge.exe (PID: 2956)
- msedge.exe (PID: 3996)
Application launched itself
- msedge.exe (PID: 2956)
- msedge.exe (PID: 7008)
Reads the computer name
- identity_helper.exe (PID: 6832)
- Syntex Spoofer.exe (PID: 7516)
- Syntex Spoofer.exe (PID: 8460)
- tempcache.exe (PID: 4592)
- identity_helper.exe (PID: 2368)
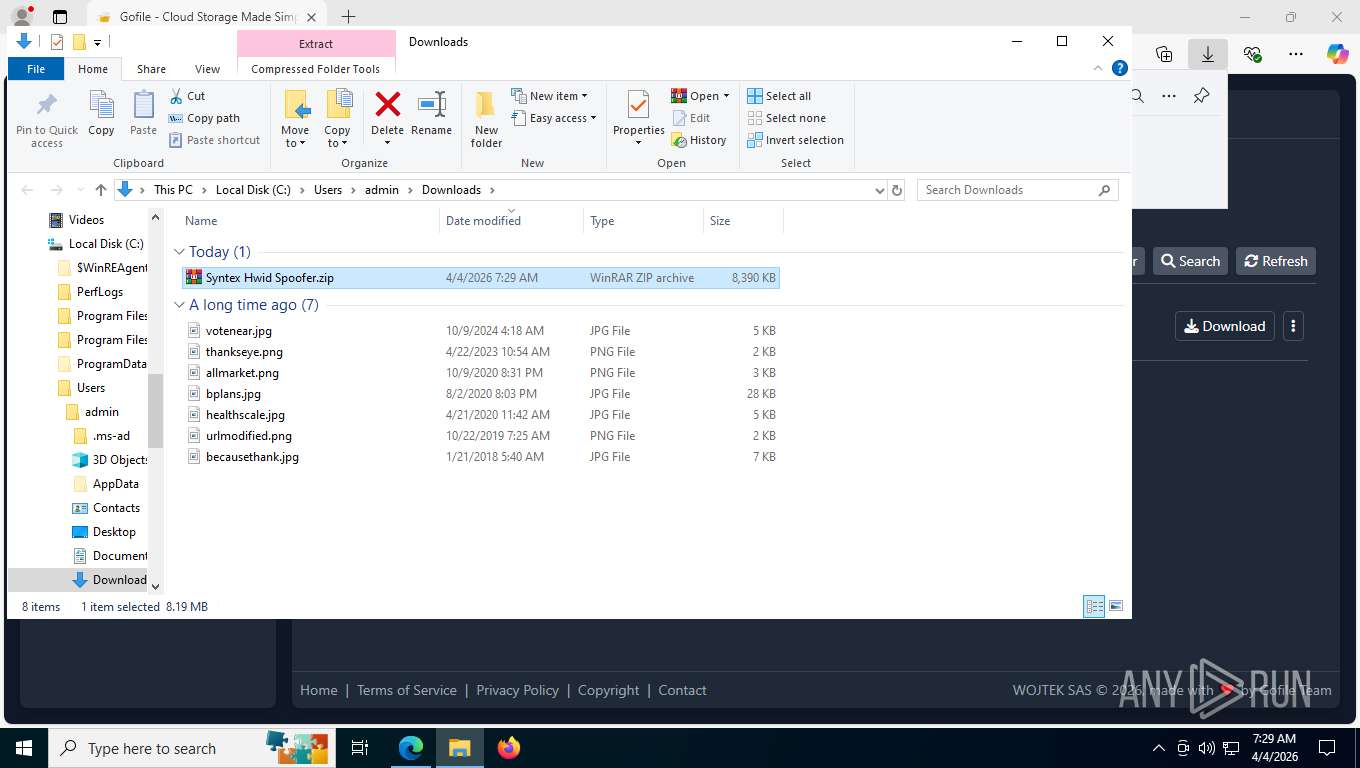
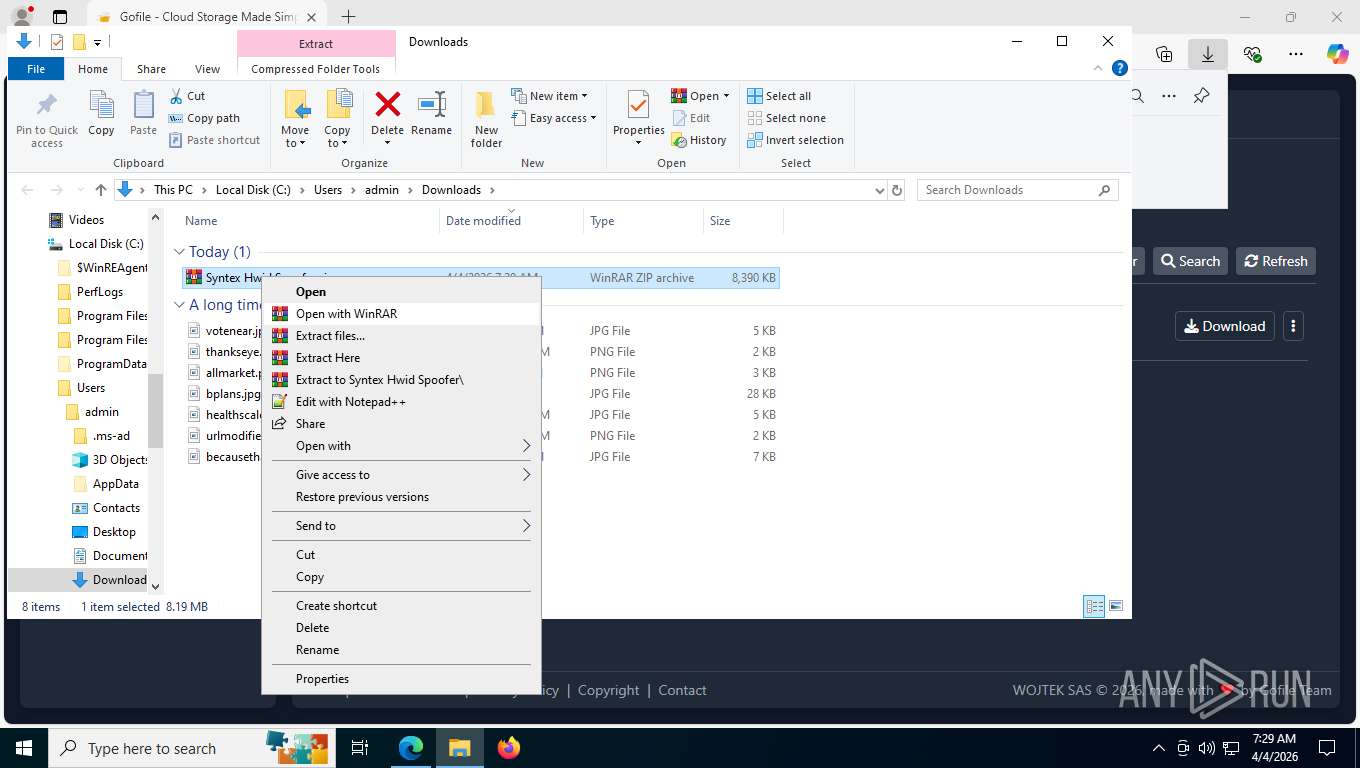
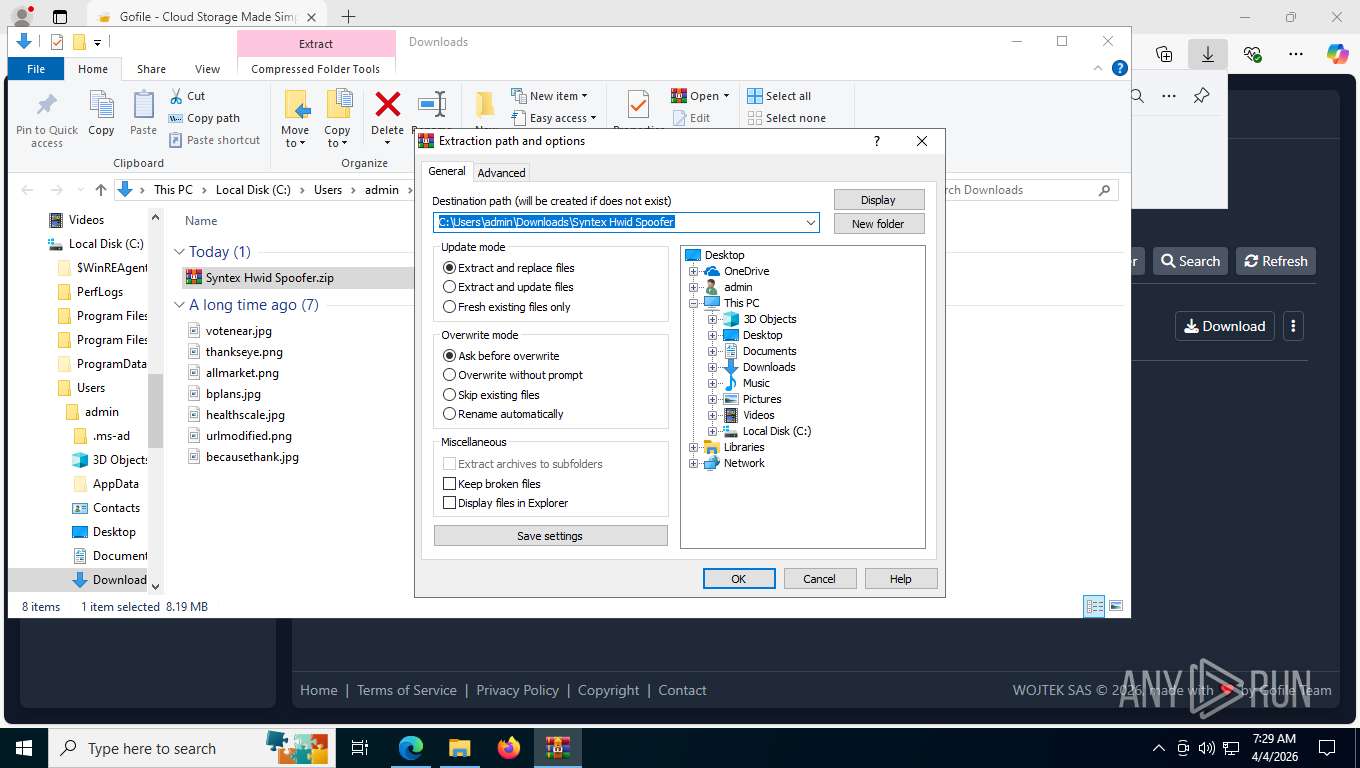
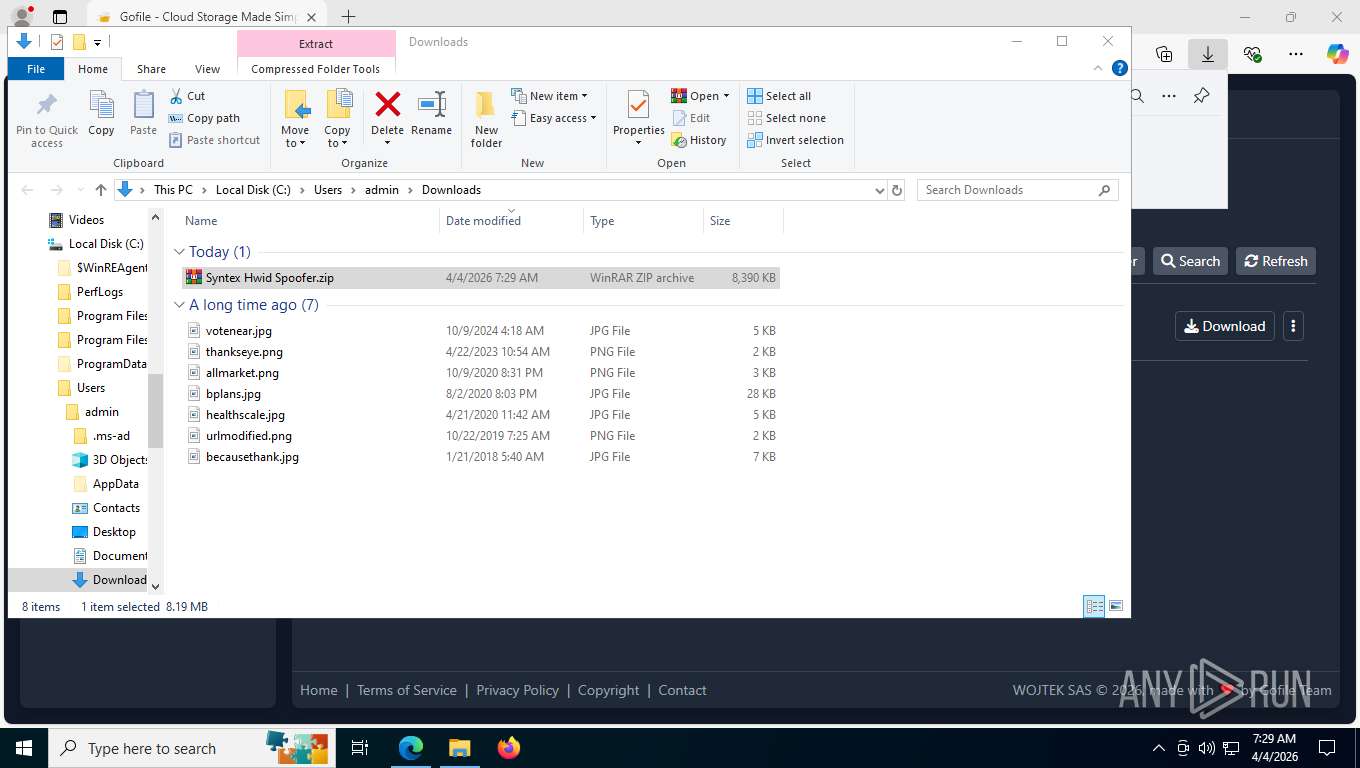
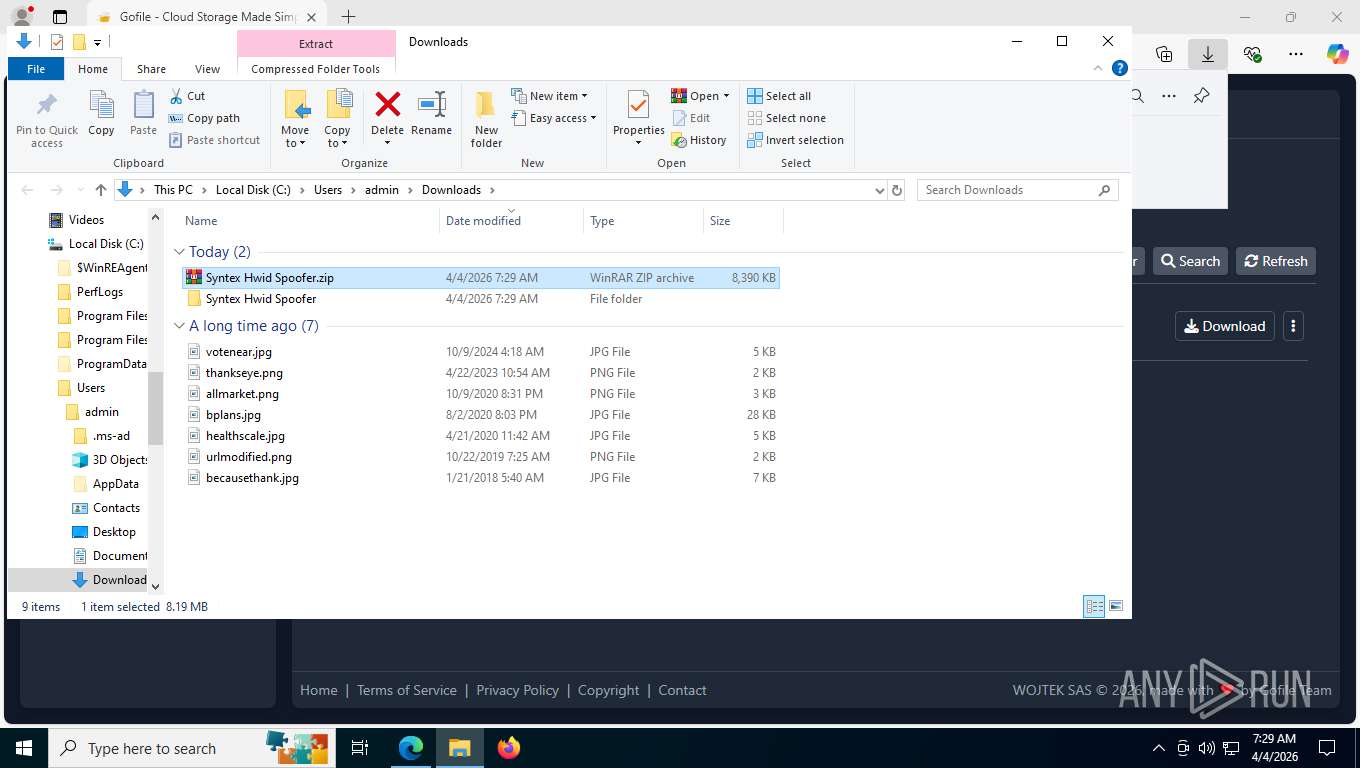
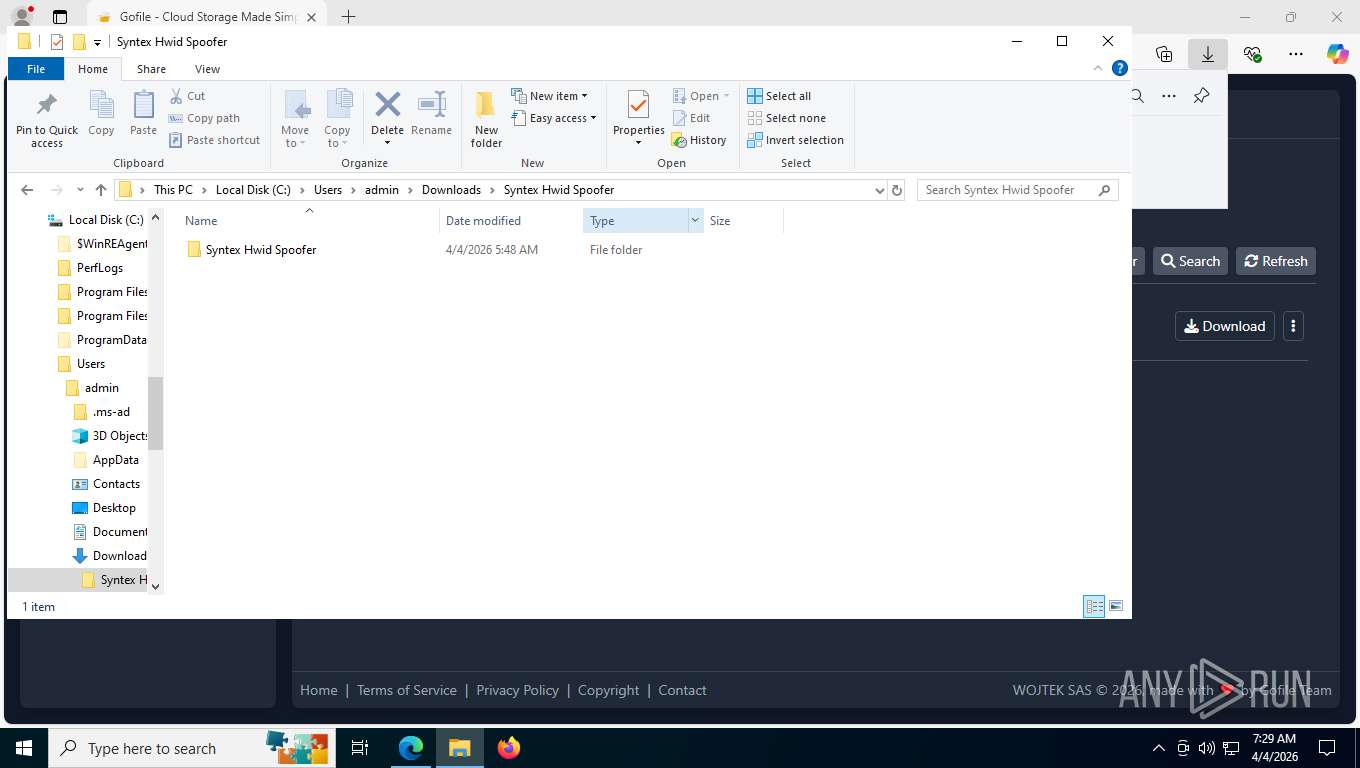
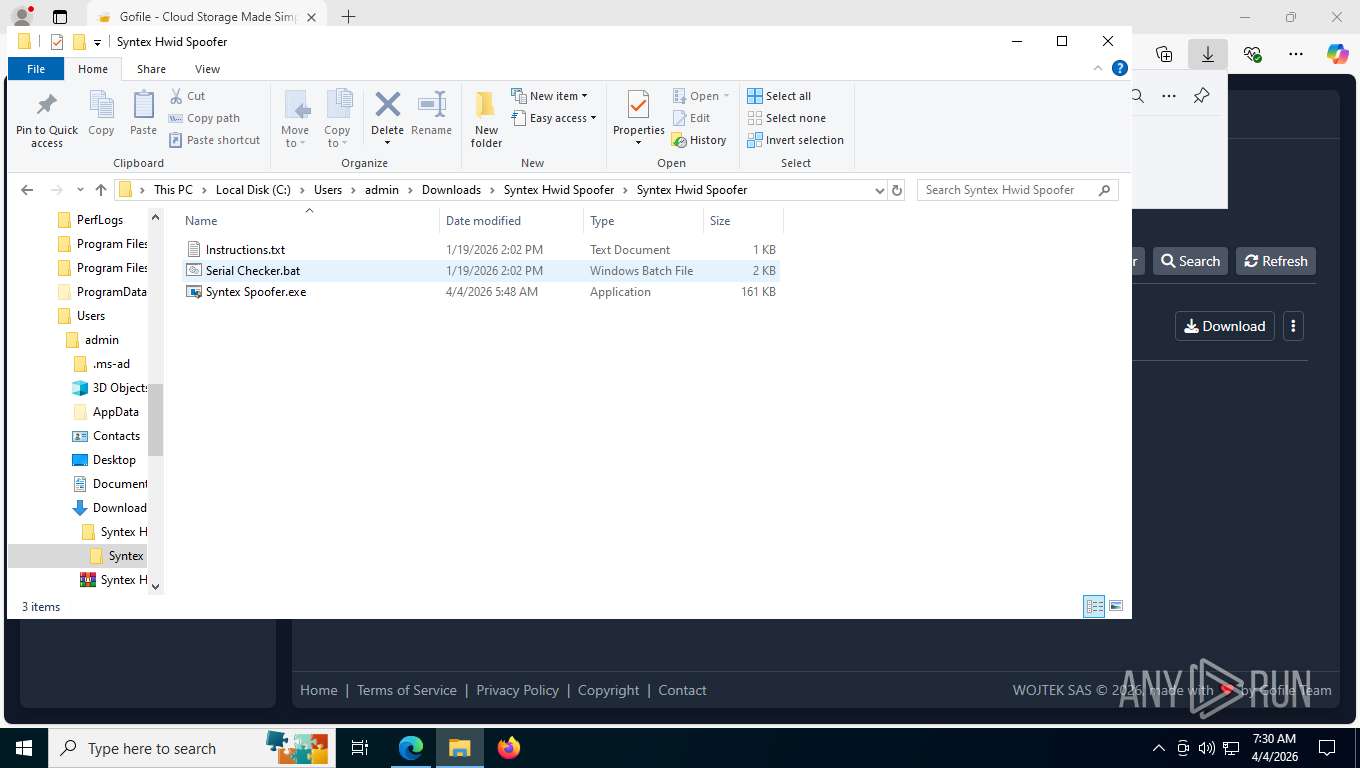
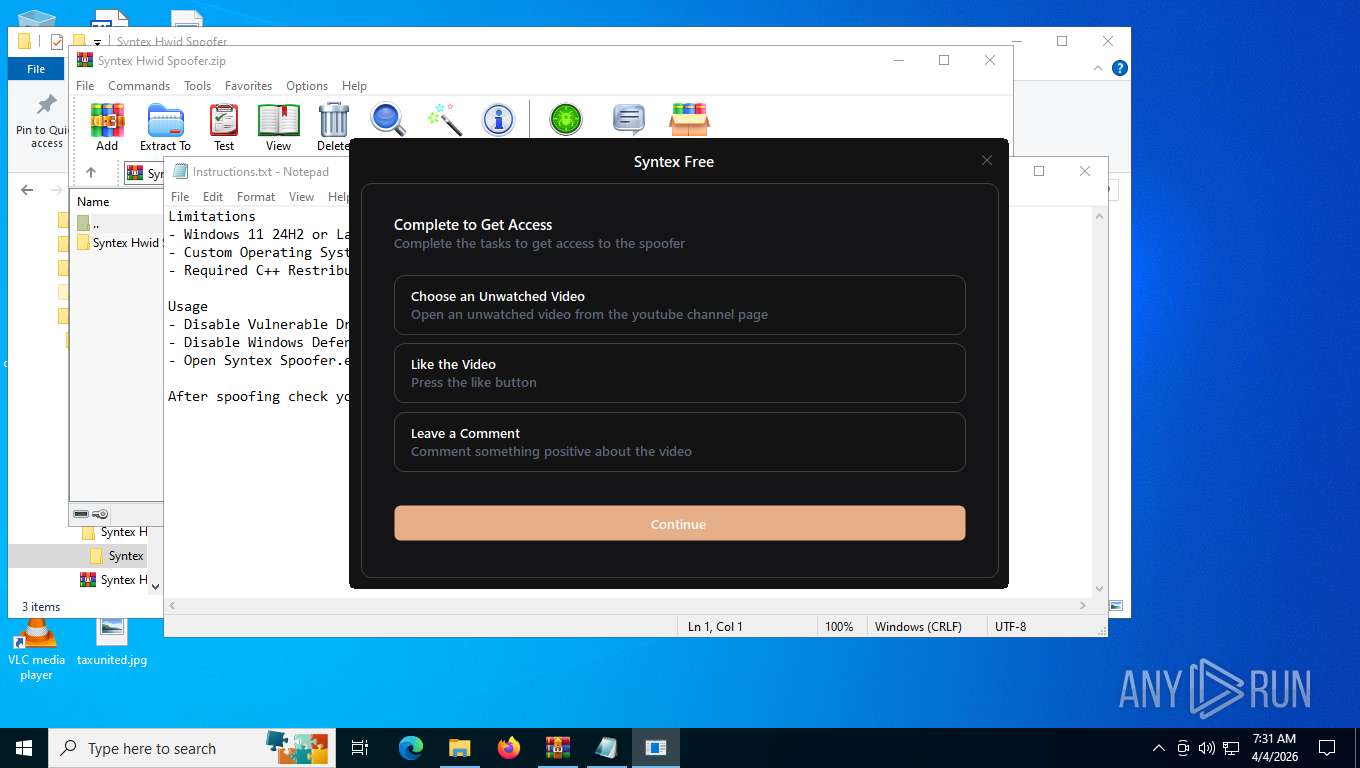
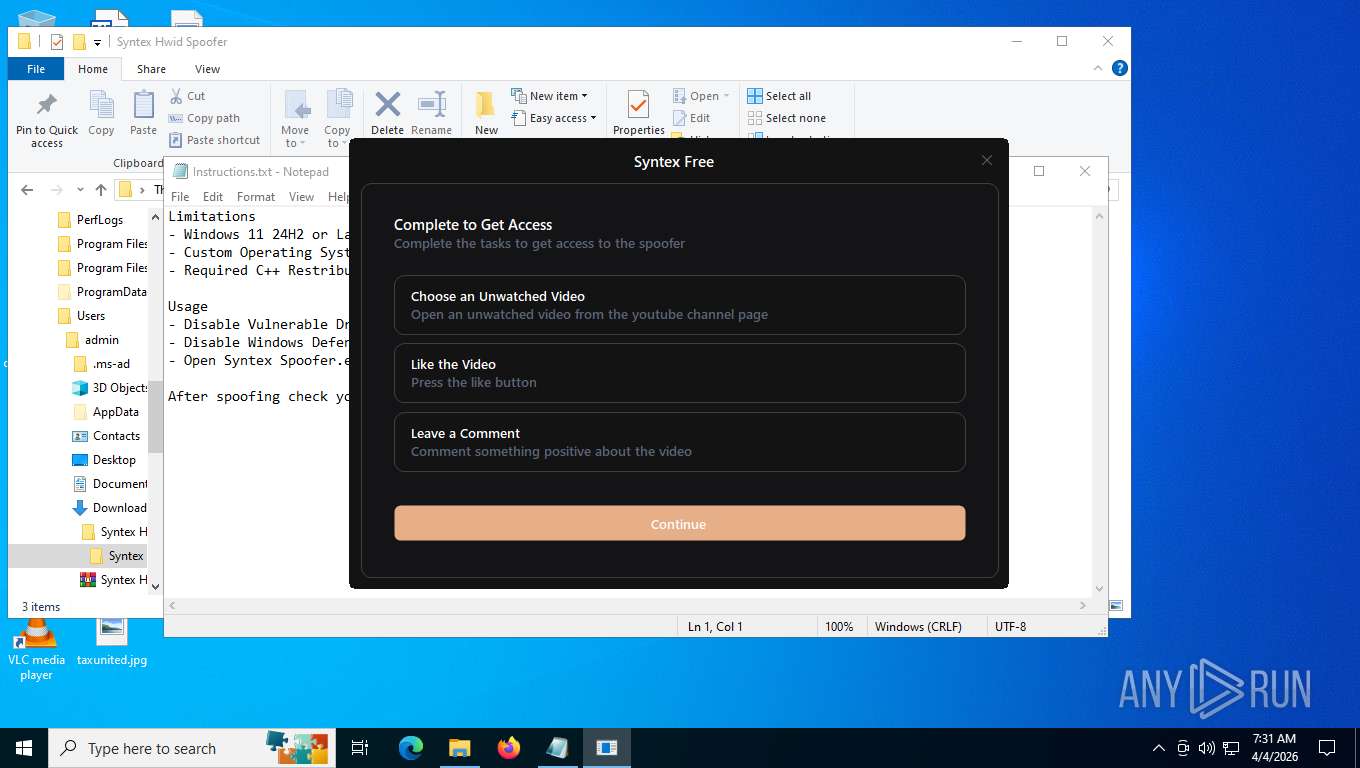
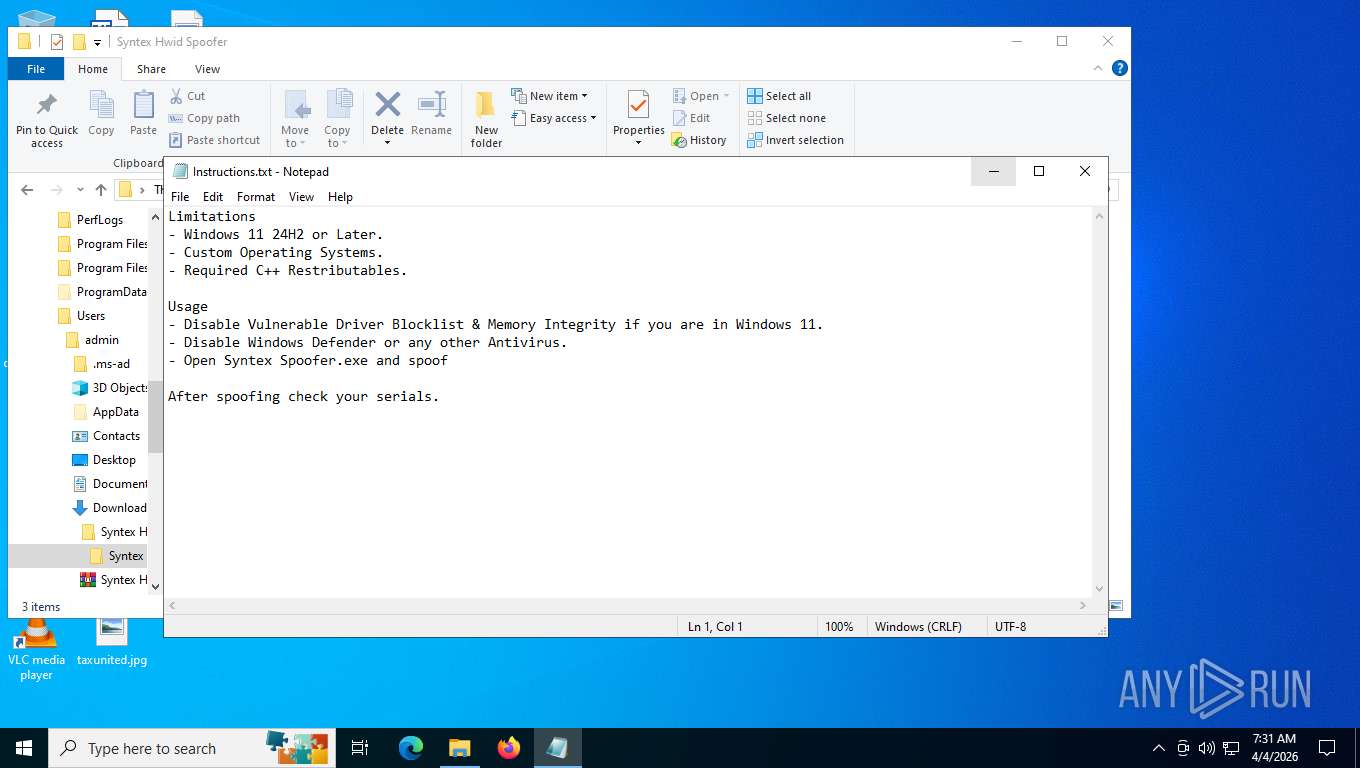
Manual execution by a user
- cmd.exe (PID: 8220)
- WinRAR.exe (PID: 9192)
- notepad.exe (PID: 6404)
- Syntex Spoofer.exe (PID: 8396)
- Syntex Spoofer.exe (PID: 7516)
- cmd.exe (PID: 5160)
- Syntex Spoofer.exe (PID: 8368)
- WinRAR.exe (PID: 8772)
- Syntex Spoofer.exe (PID: 8460)
- notepad.exe (PID: 7520)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6404)
- WMIC.exe (PID: 8572)
- WMIC.exe (PID: 5404)
- WMIC.exe (PID: 1132)
- WMIC.exe (PID: 8724)
- WMIC.exe (PID: 8028)
- WMIC.exe (PID: 8776)
- WMIC.exe (PID: 8856)
- WMIC.exe (PID: 8976)
- WMIC.exe (PID: 4128)
- WMIC.exe (PID: 8216)
- WMIC.exe (PID: 8484)
- WMIC.exe (PID: 8536)
- WMIC.exe (PID: 8392)
- WMIC.exe (PID: 2032)
- WMIC.exe (PID: 8496)
- WMIC.exe (PID: 8920)
- WMIC.exe (PID: 8956)
- WMIC.exe (PID: 8276)
- notepad.exe (PID: 7520)
- tempcache.exe (PID: 4592)
- WMIC.exe (PID: 8932)
- WMIC.exe (PID: 6812)
- WMIC.exe (PID: 5484)
- WMIC.exe (PID: 8508)
- WMIC.exe (PID: 784)
- WMIC.exe (PID: 3416)
- WMIC.exe (PID: 7268)
- WMIC.exe (PID: 7204)
- WMIC.exe (PID: 6508)
Starts MODE.COM to configure console settings
- mode.com (PID: 8348)
- mode.com (PID: 9156)
- mode.com (PID: 4712)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 8956)
- getmac.exe (PID: 6912)
- getmac.exe (PID: 7684)
Disables trace logs
- powershell.exe (PID: 7404)
Reads Environment values
- identity_helper.exe (PID: 6832)
- identity_helper.exe (PID: 2368)
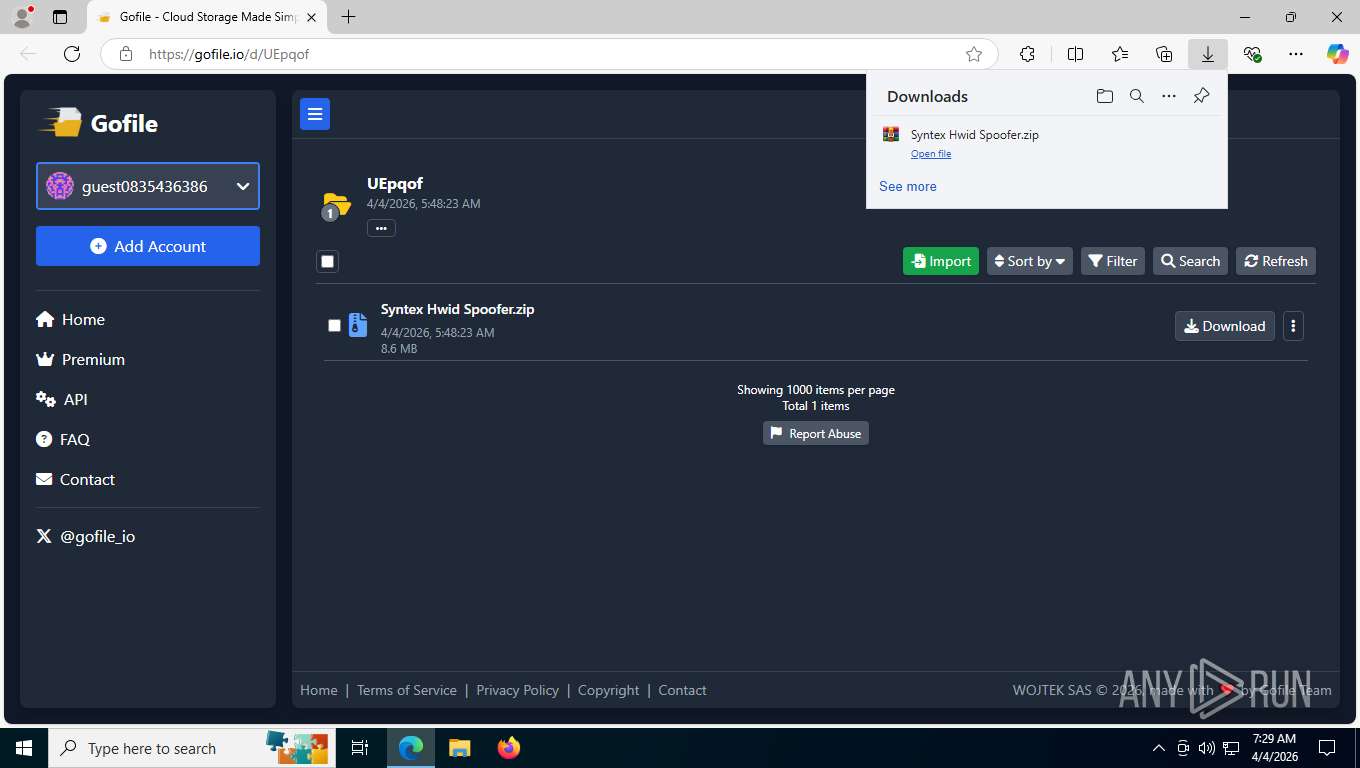
Launching a file from the Downloads directory
- msedge.exe (PID: 2956)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8772)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7404)
Reads the machine GUID from the registry
- csc.exe (PID: 8824)
- tempcache.exe (PID: 4592)
Create files in a temporary directory
- csc.exe (PID: 8824)
- cvtres.exe (PID: 7708)
Creates files or folders in the user directory
- WerFault.exe (PID: 8848)
The executable file from the user directory is run by the Powershell process
- tempcache.exe (PID: 4592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
242
Monitored processes
99
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 784 | wmic PATH Win32_VideoController GET Description,PNPDeviceID | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | wmic baseboard get serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5108,i,2754571263385818748,11118433416549119715,262144 --variations-seed-version --mojo-platform-channel-handle=5112 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3640,i,2877865116915591157,17160720646274639084,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3672 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
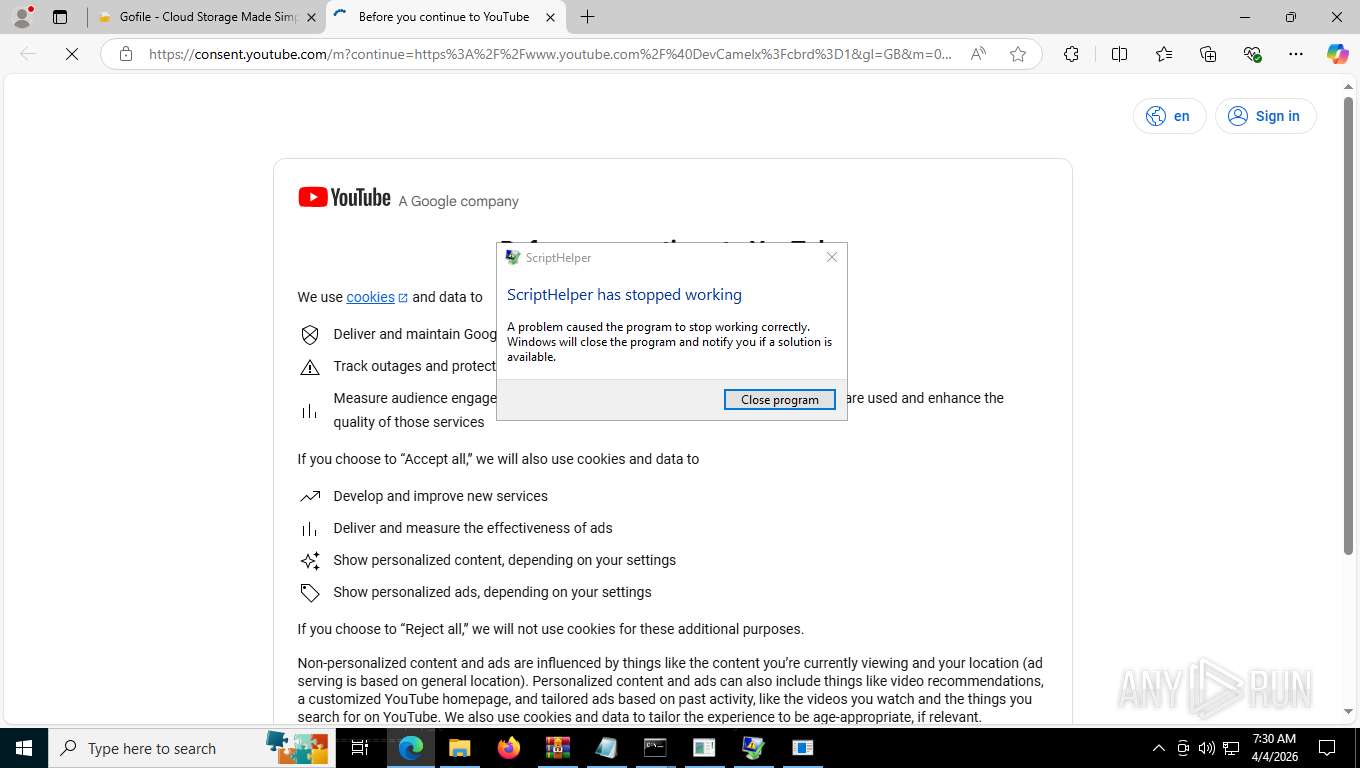
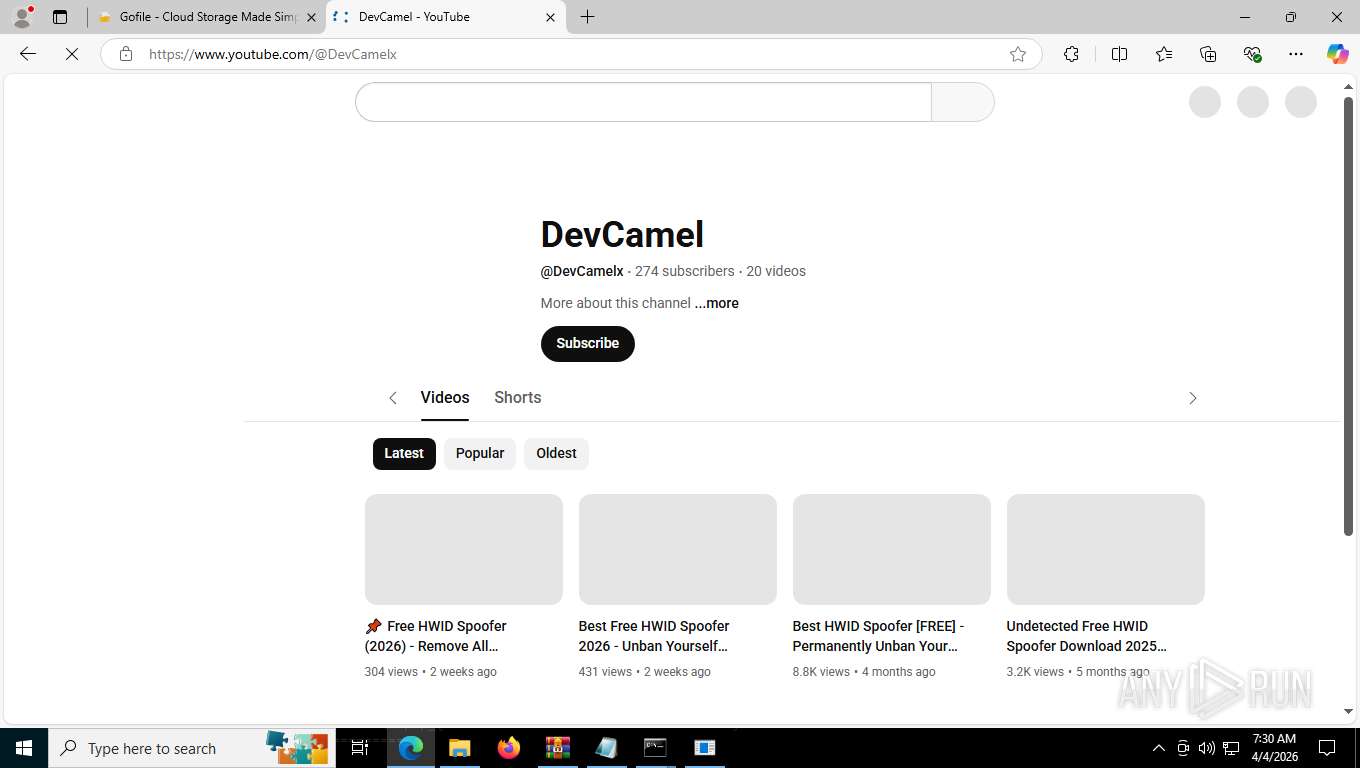
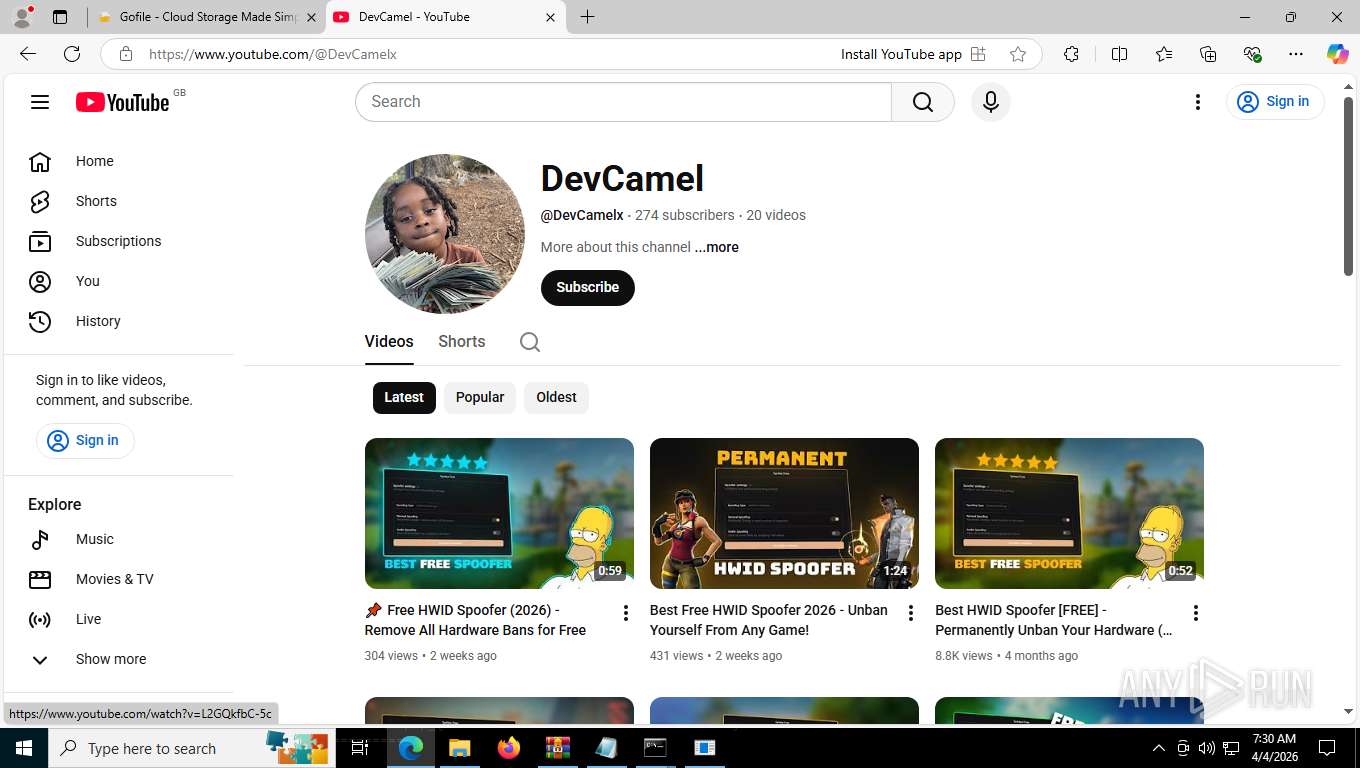
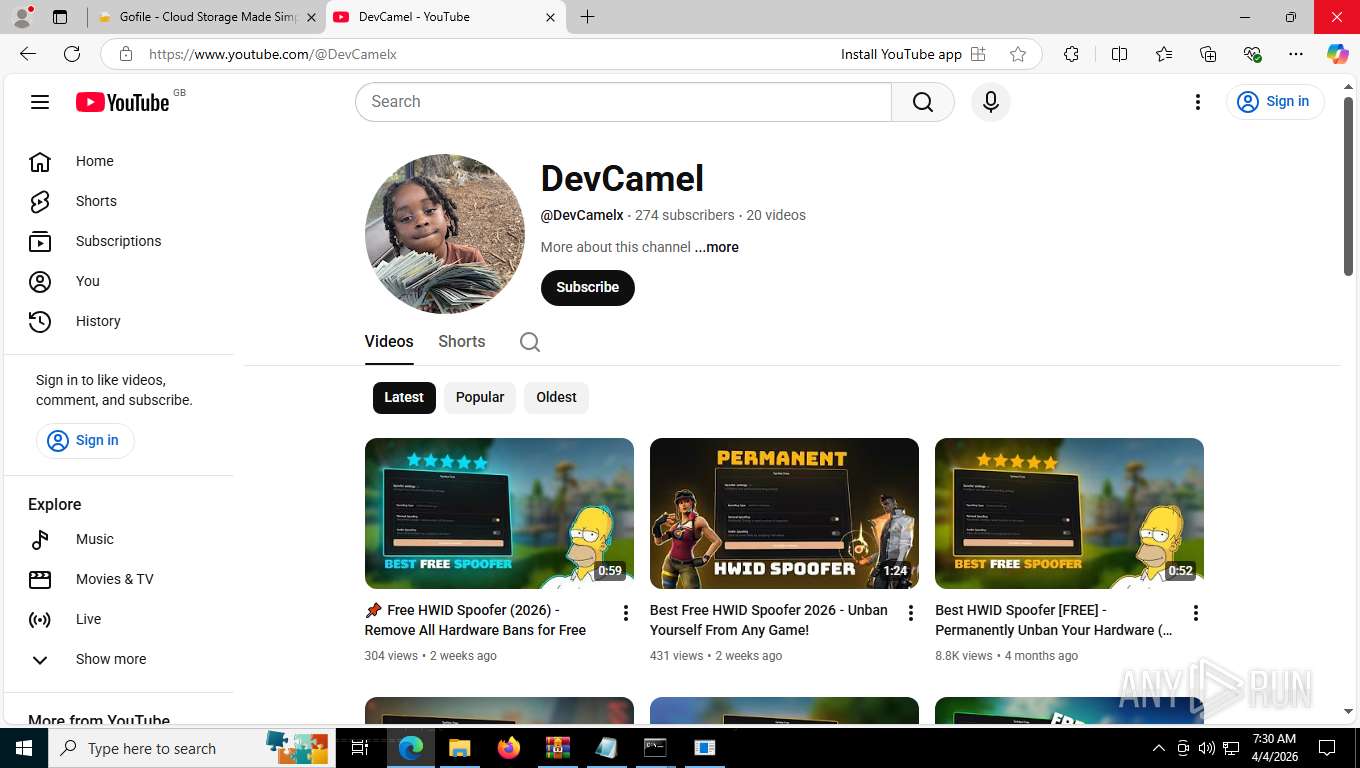
| 1656 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.youtube.com/@DevCamelx | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | tempcache.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2016 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2524,i,2877865116915591157,17160720646274639084,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2760 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6080,i,2877865116915591157,17160720646274639084,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6108 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2032 | wmic csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2312 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2316,i,2754571263385818748,11118433416549119715,262144 --variations-seed-version --mojo-platform-channel-handle=2456 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2340 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4104,i,2877865116915591157,17160720646274639084,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4808 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
22 276
Read events
22 225
Write events
35
Delete events
16
Modification events
| (PID) Process: | (8772) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (8772) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (8772) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (8772) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
| (PID) Process: | (8772) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 11 |
Value: | |||
| (PID) Process: | (8772) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 10 |
Value: | |||
| (PID) Process: | (8772) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 9 |
Value: | |||
| (PID) Process: | (8772) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 8 |
Value: | |||
| (PID) Process: | (8772) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 7 |
Value: | |||
| (PID) Process: | (8772) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 6 |
Value: | |||
Executable files
12
Suspicious files
338
Text files
356
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFe0098.TMP | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe00a7.TMP | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFe00a7.TMP | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe00b7.TMP | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe00c7.TMP | — | |
MD5:— | SHA256:— | |||
| 2956 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
450
TCP/UDP connections
117
DNS requests
139
Threats
33
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | msedge.exe | GET | 302 | 207.174.61.1:80 | http://transfer.short.gy/Syntex-Hwid-Spoofer | US | — | — | unknown |
3996 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.60 Kb | whitelisted |
3996 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:uh0BfAx6ccECvwCmC0SIpWNpFaBZwSJeo2SXf8V8ca0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
3996 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | — | 314 b | whitelisted |
3996 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | — | 25 b | whitelisted |
3996 | msedge.exe | GET | 200 | 13.107.253.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | — | 82 b | whitelisted |
3996 | msedge.exe | GET | 200 | 45.112.123.126:443 | https://gofile.io/d/UEpqof | FR | html | 8.27 Kb | unknown |
3996 | msedge.exe | GET | 200 | 45.112.123.126:443 | https://gofile.io/dist/css/output.css | FR | text | 54.0 Kb | unknown |
3996 | msedge.exe | GET | 200 | 45.112.123.126:443 | https://gofile.io/plugins/fontawesome/css/all.min.css | FR | text | 94.2 Kb | unknown |
3996 | msedge.exe | GET | 200 | 45.112.123.126:443 | https://gofile.io/dist/js/config.js | FR | text | 1.74 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4680 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.146:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3996 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3996 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3996 | msedge.exe | 207.174.61.1:80 | transfer.short.gy | AMAZON-02 | US | whitelisted |
3996 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
transfer.short.gy |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
gofile.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3996 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] WEB Link Shortener (.short .gy) |
3996 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (short .gy) |
3996 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (short .gy) |
3996 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] WEB Link Shortener (.short .gy) |
3996 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
3996 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
3996 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
3996 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
3996 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
3996 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
Process | Message |
|---|---|
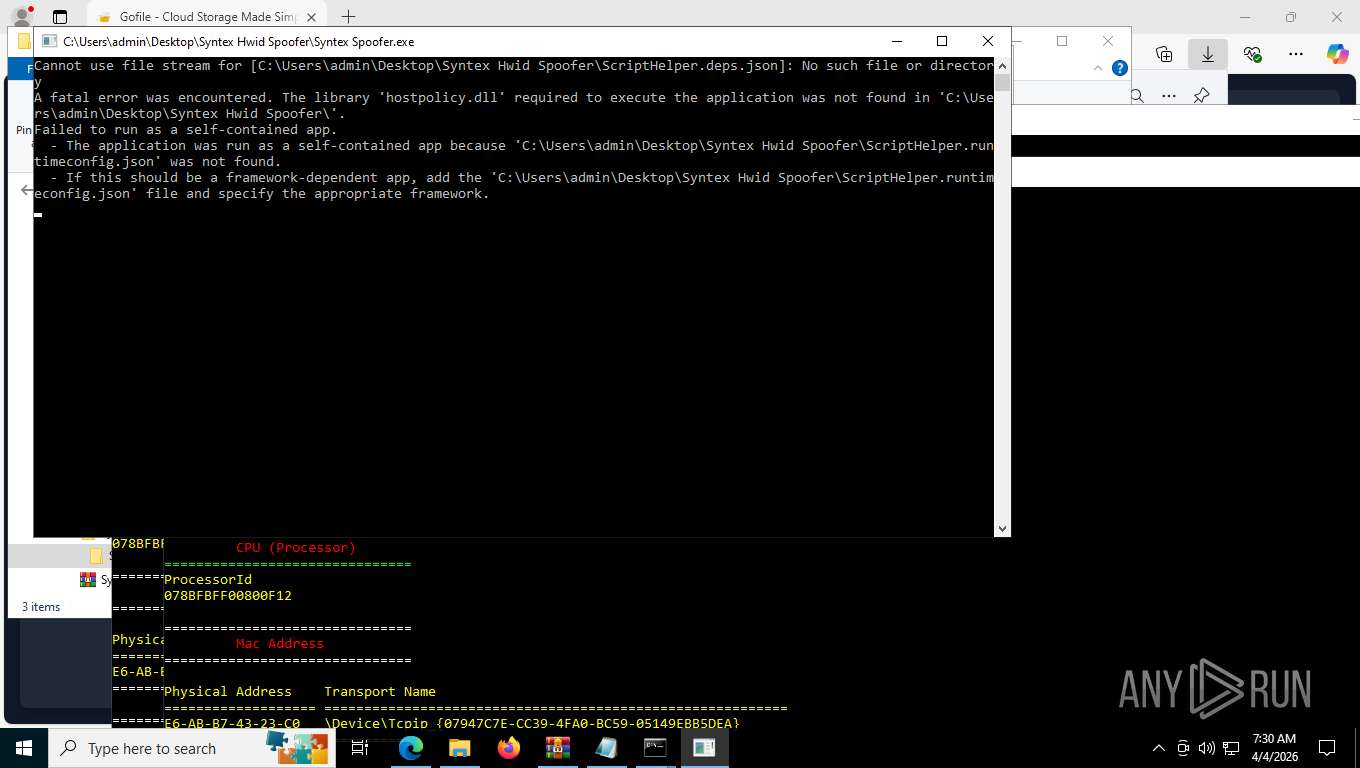
Syntex Spoofer.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 7516. Message ID: [0x2509].
|
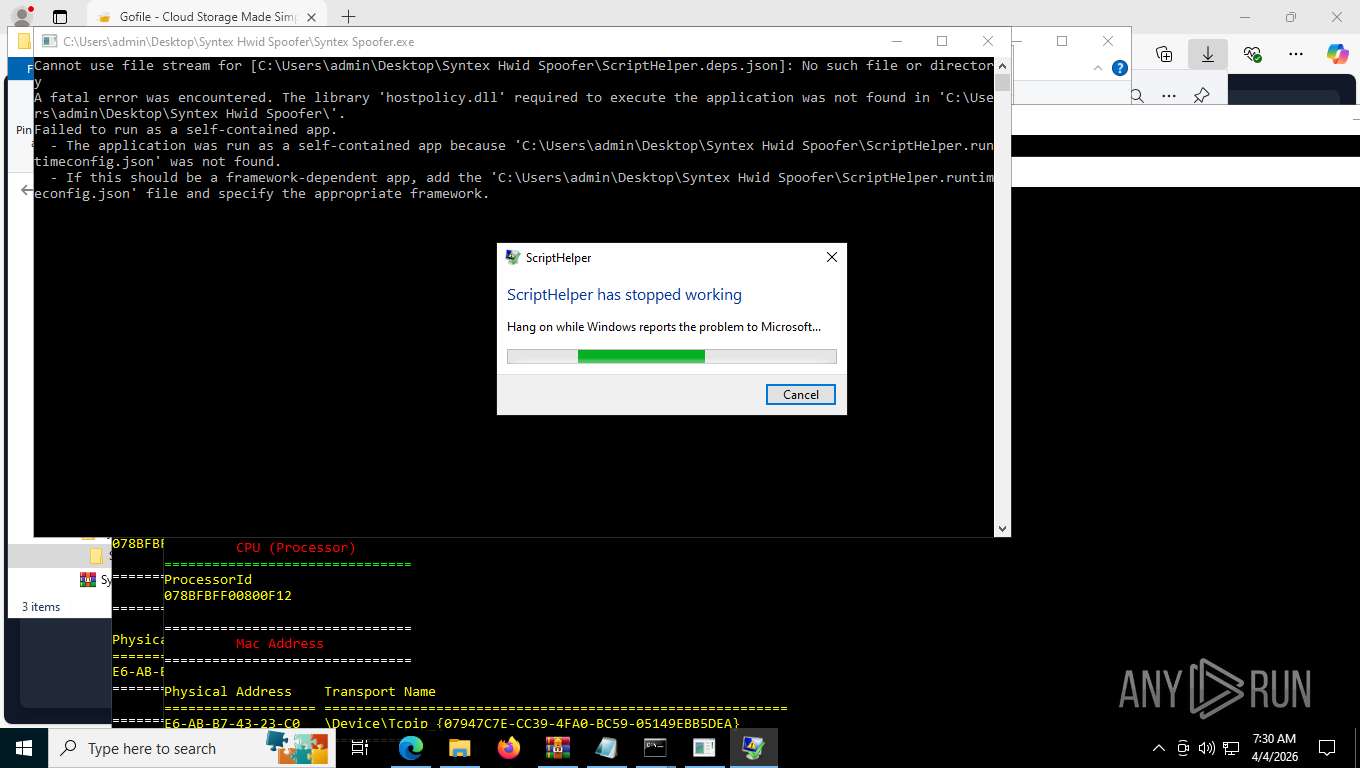
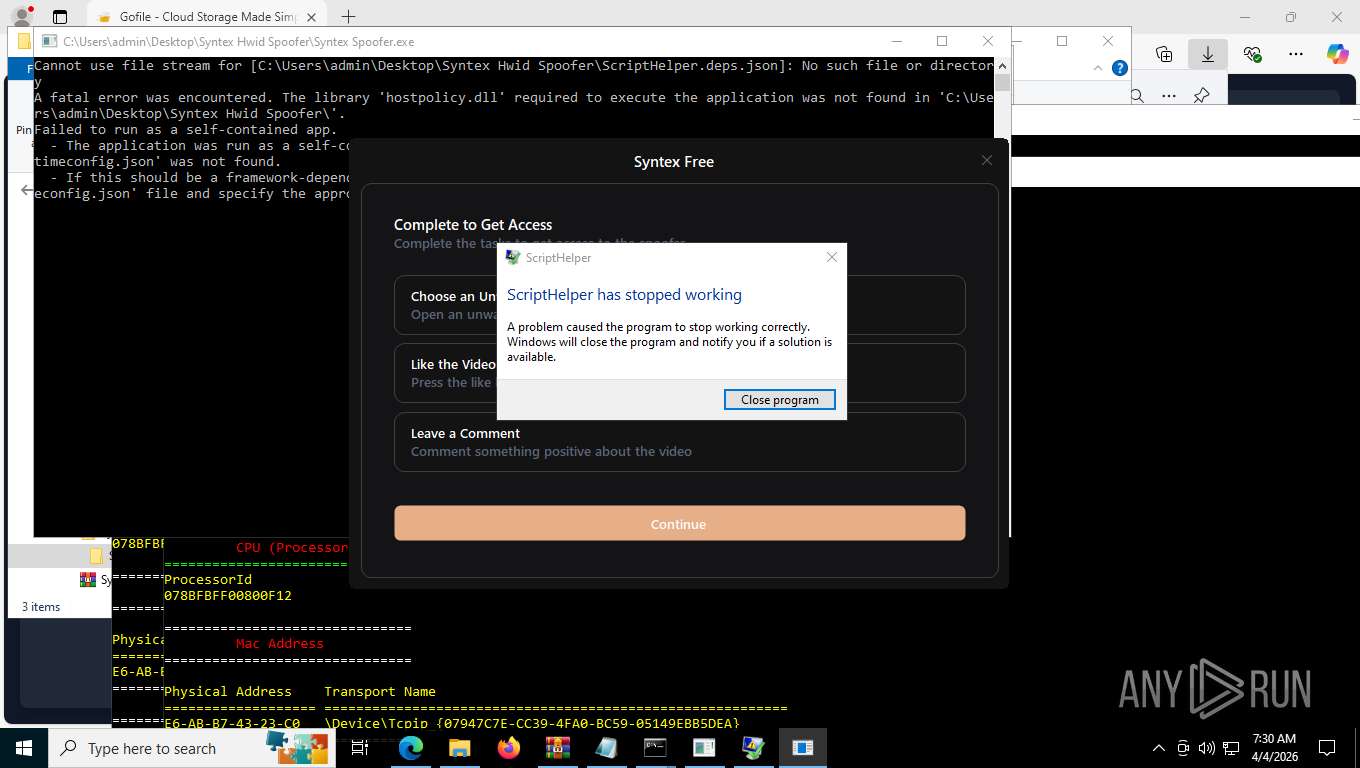
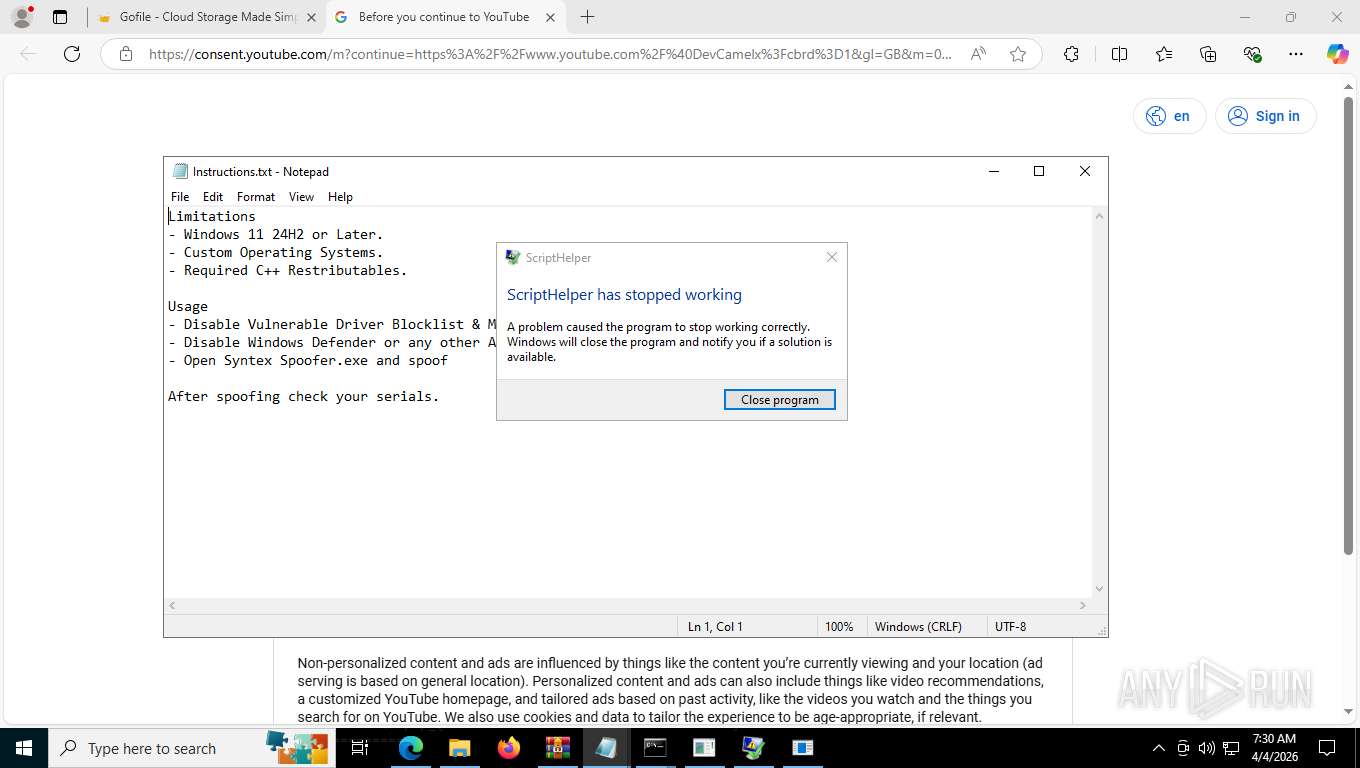
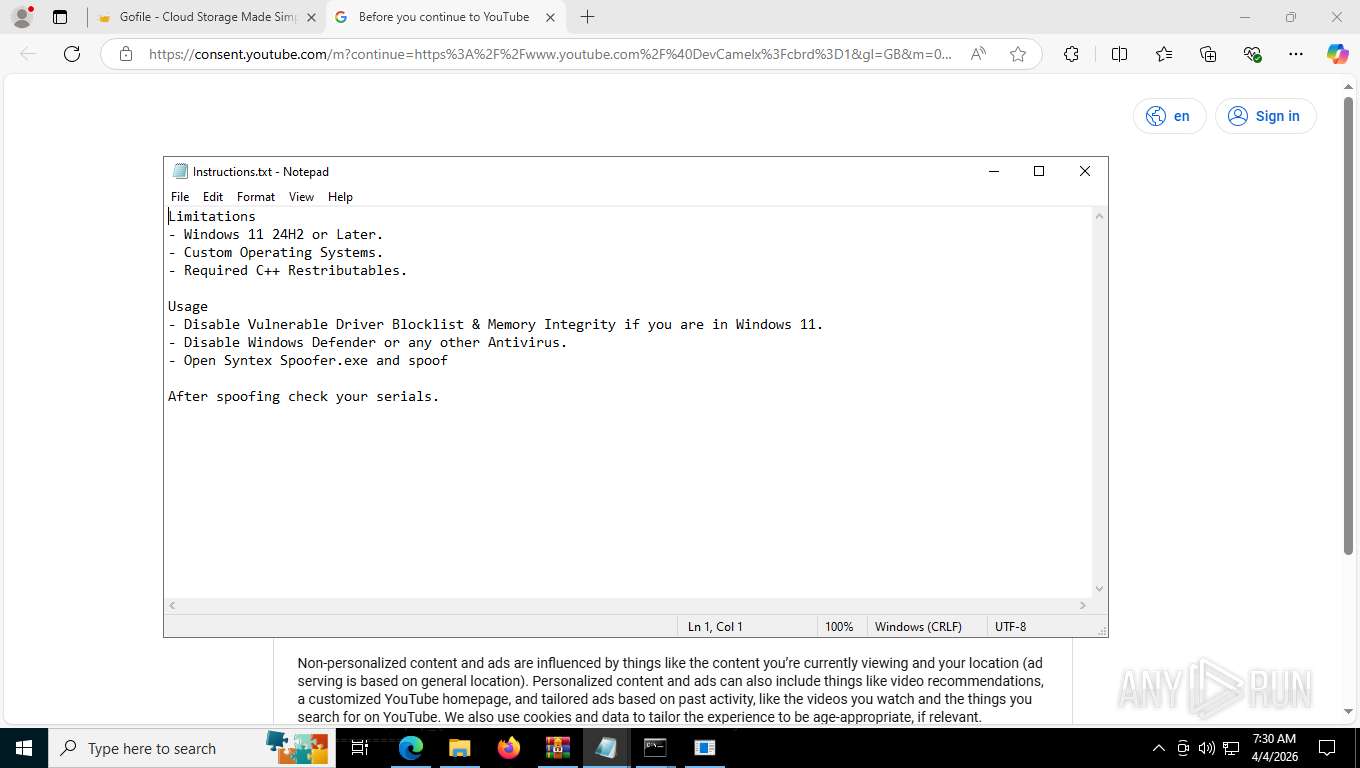
Syntex Spoofer.exe | A fatal error was encountered. The library 'hostpolicy.dll' required to execute the application was not found in 'C:\Users\admin\Desktop\Syntex Hwid Spoofer\'. |
Syntex Spoofer.exe | Cannot use file stream for [C:\Users\admin\Desktop\Syntex Hwid Spoofer\ScriptHelper.deps.json]: No such file or directory |
Syntex Spoofer.exe | - The application was run as a self-contained app because 'C:\Users\admin\Desktop\Syntex Hwid Spoofer\ScriptHelper.runtimeconfig.json' was not found. |
Syntex Spoofer.exe | Failed to run as a self-contained app. |
Syntex Spoofer.exe | - If this should be a framework-dependent app, add the 'C:\Users\admin\Desktop\Syntex Hwid Spoofer\ScriptHelper.runtimeconfig.json' file and specify the appropriate framework. |